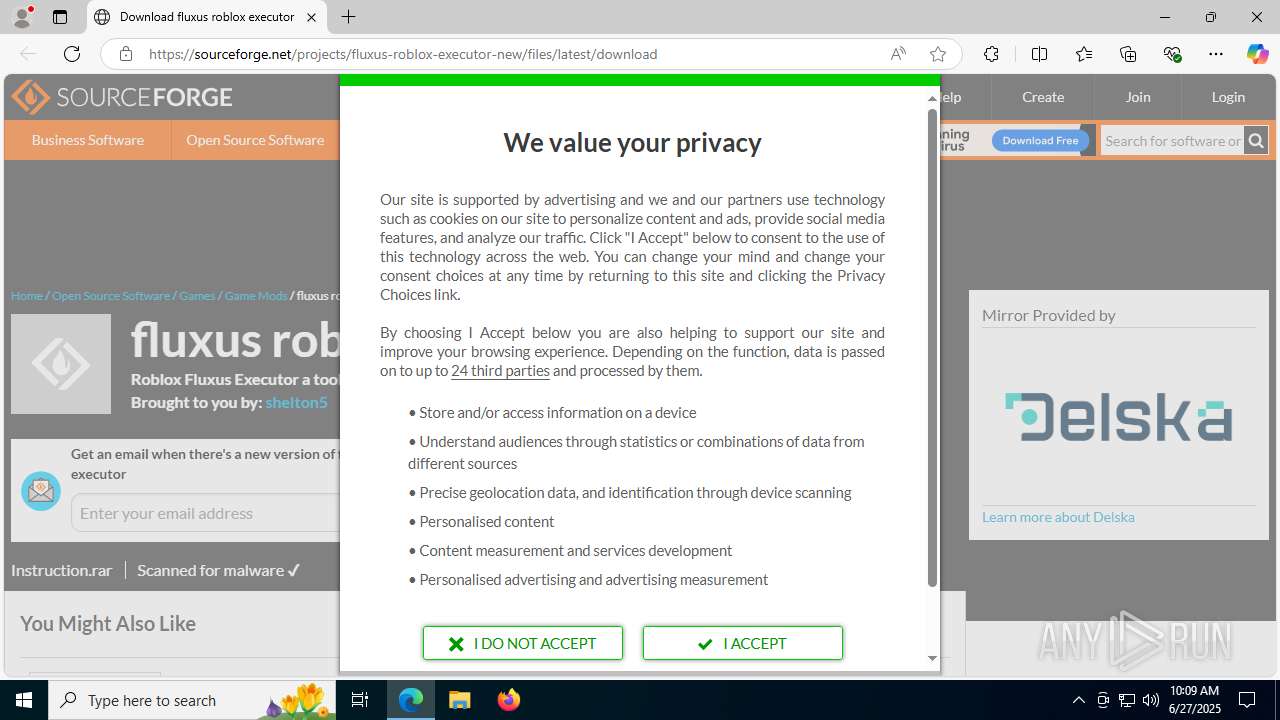
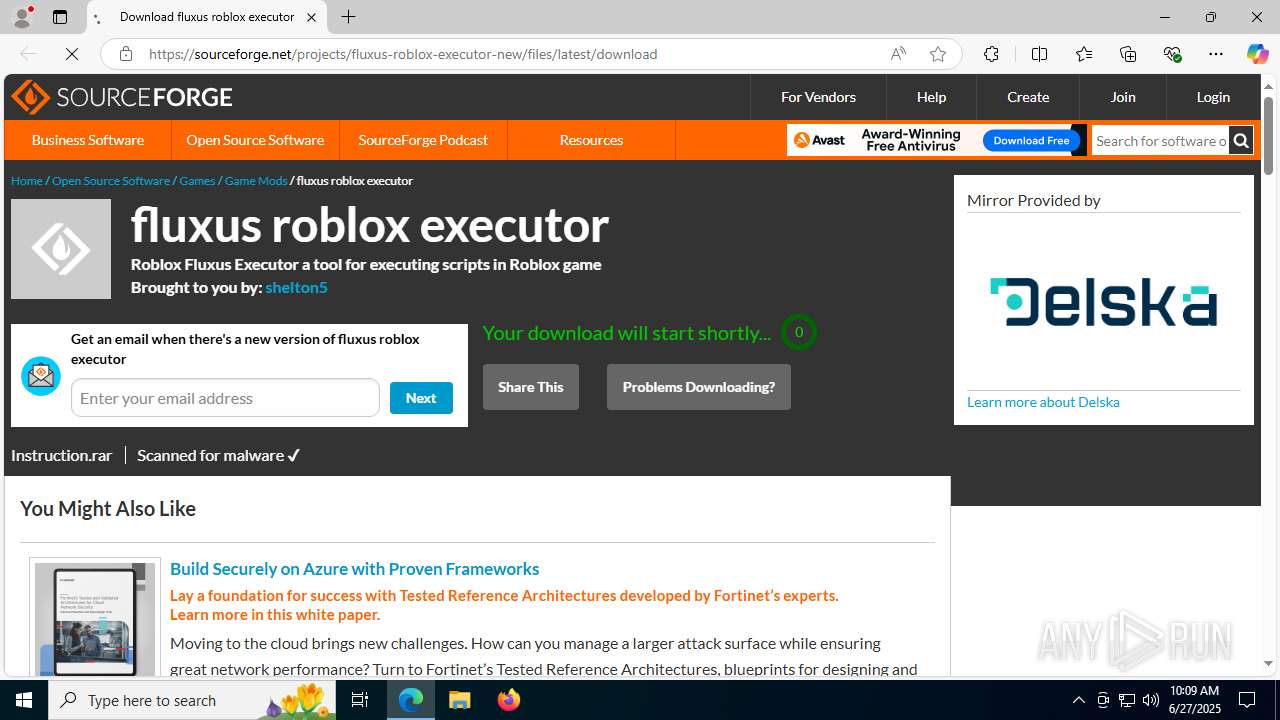
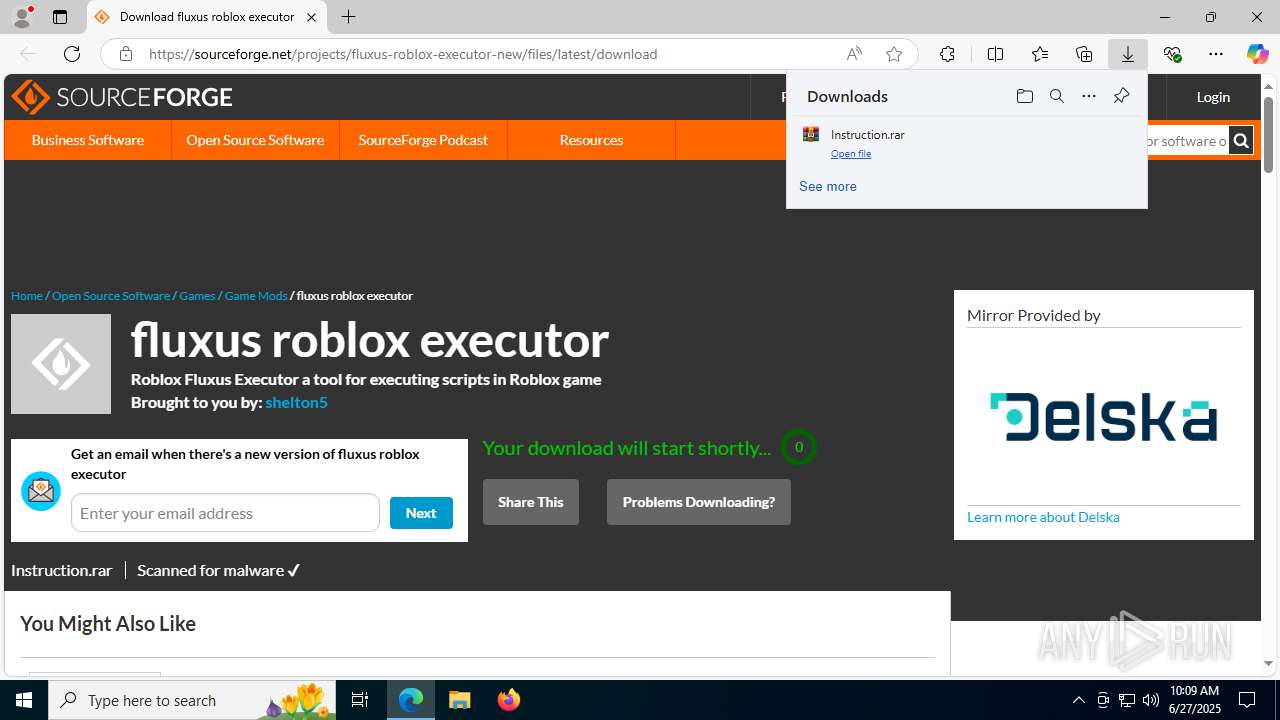
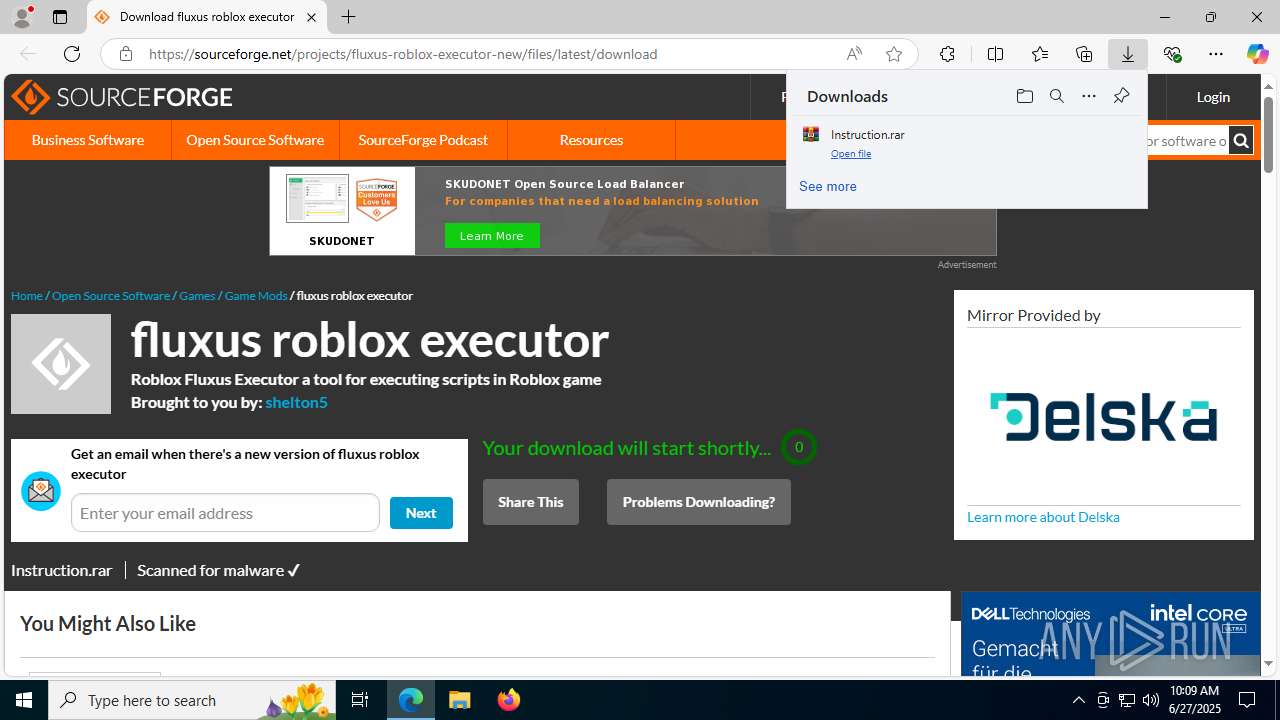
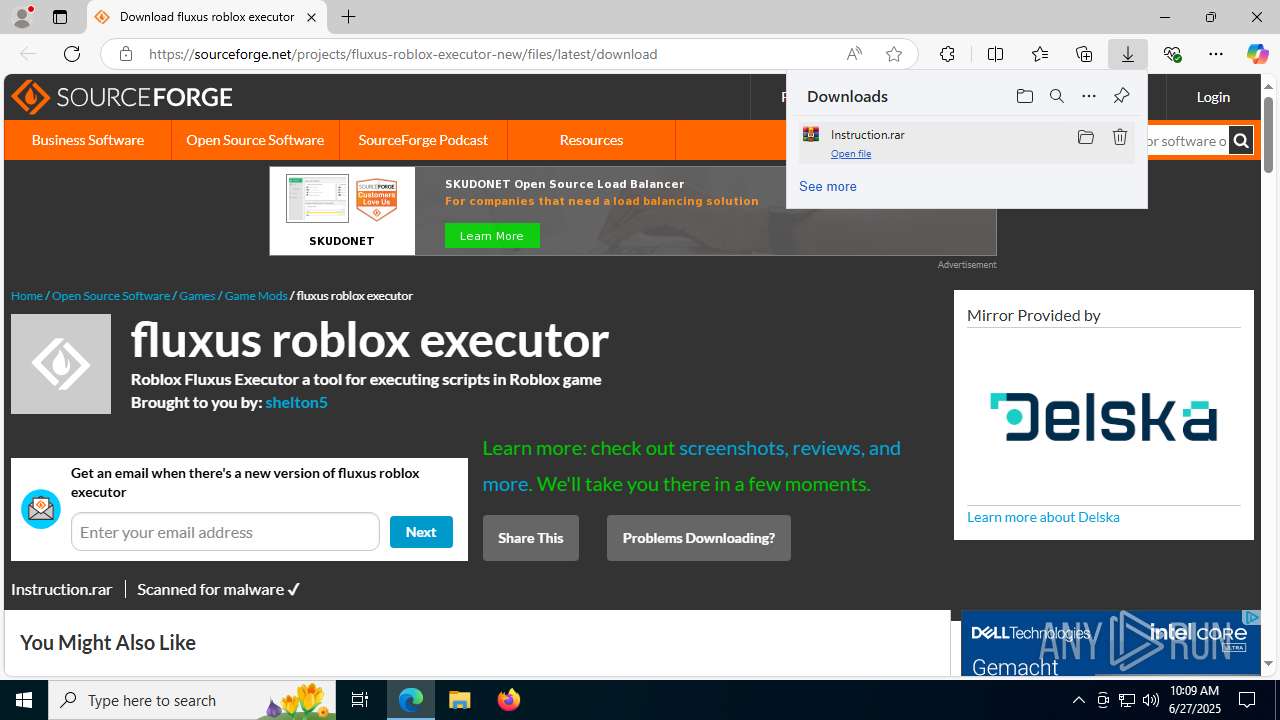
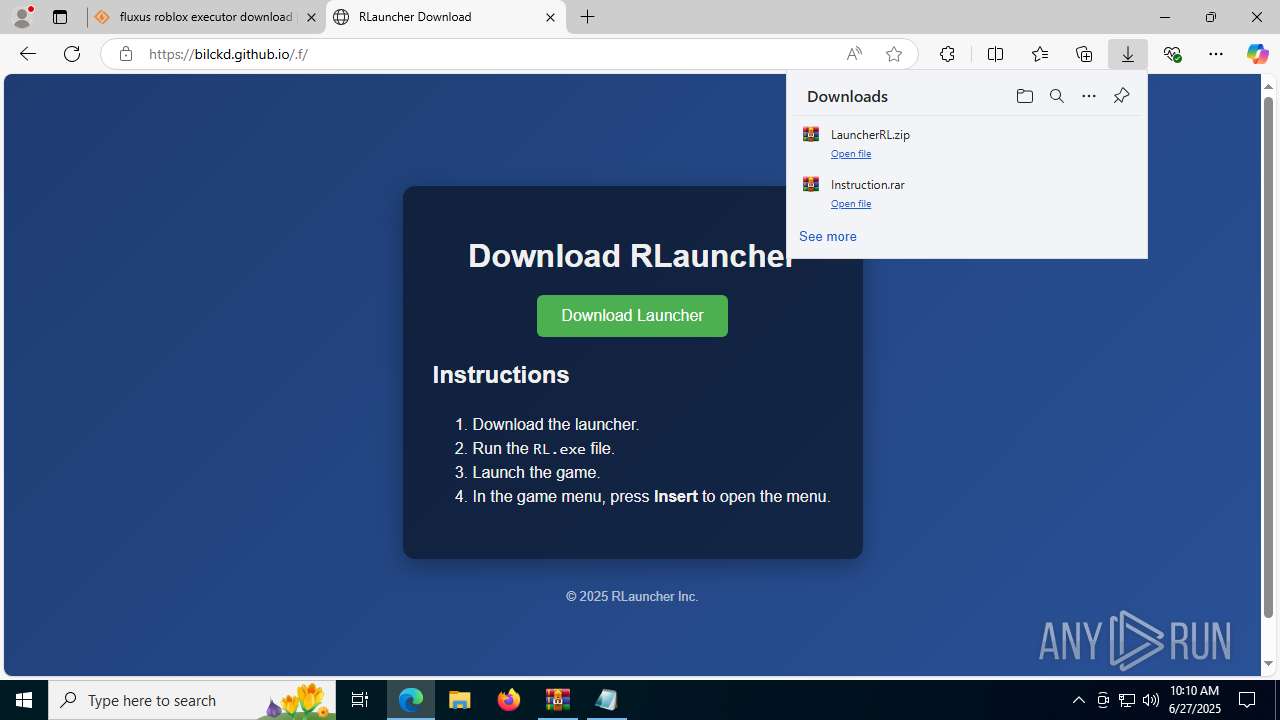
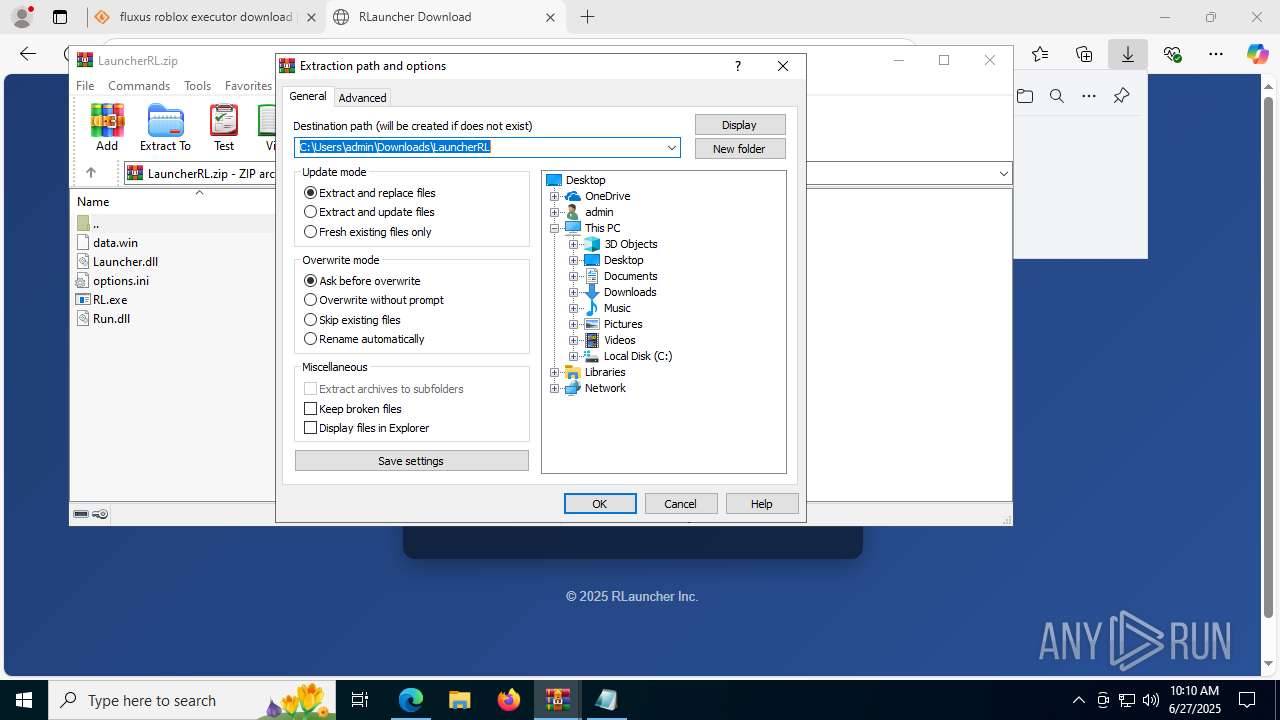
| URL: | https://sourceforge.net/projects/fluxus-roblox-executor-new/files/latest/download |
| Full analysis: | https://app.any.run/tasks/e9c3c55b-90f2-4946-8428-a28c56f9235a |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | June 27, 2025, 10:09:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6E78D8E5E083600132BB5598EDEB78D0 |
| SHA1: | FF3715CFF5FCB8F4DF3CA2BC5B939795BFB5C1CC |
| SHA256: | ACBB909198C73303B9194599502EE9B7DAC7BAB2537BC64A13975E5337186A0B |
| SSDEEP: | 3:N8HCGSuLAuUtISXKk5AxFAdzywz:2iGnCtpH5AxFAd5z |
MALICIOUS
Adds path to the Windows Defender exclusion list
- RL.exe (PID: 768)
- cmd.exe (PID: 1612)
Changes Windows Defender settings
- cmd.exe (PID: 1612)
Connects to the CnC server
- svchost.exe (PID: 2200)
LUMMA mutex has been found
- MSBuild.exe (PID: 868)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2200)
- MSBuild.exe (PID: 868)
SUSPICIOUS
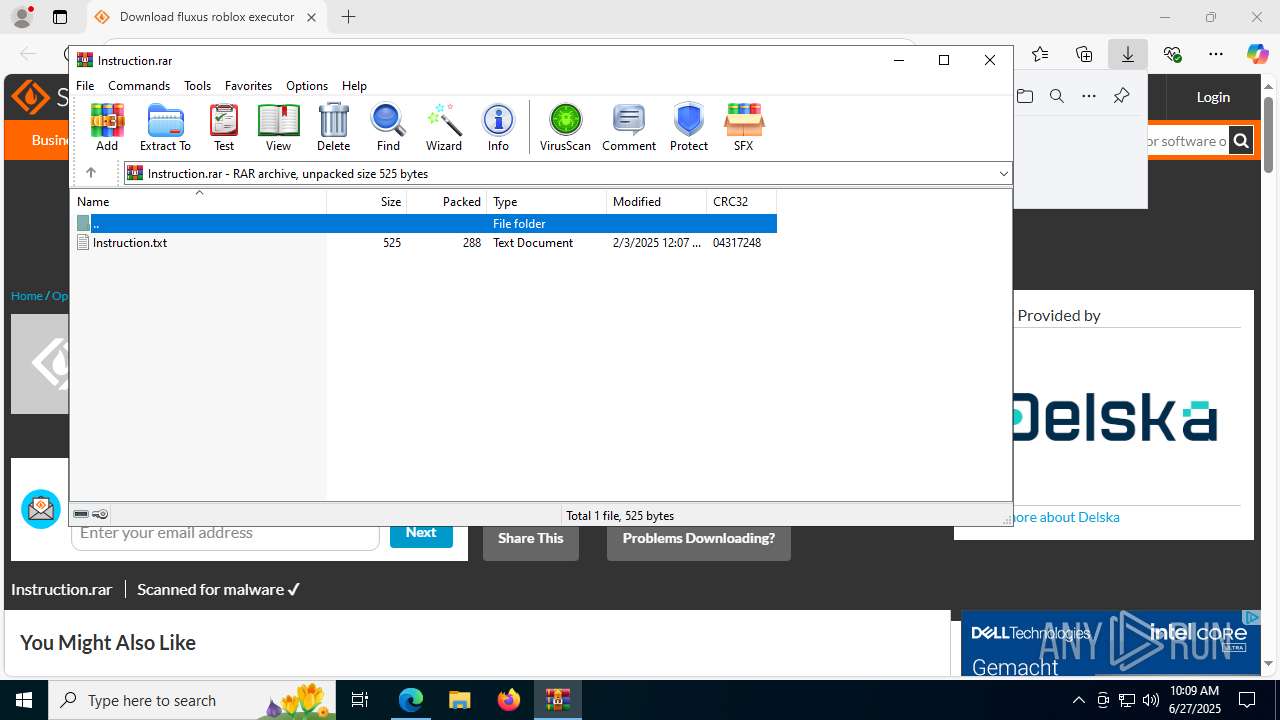
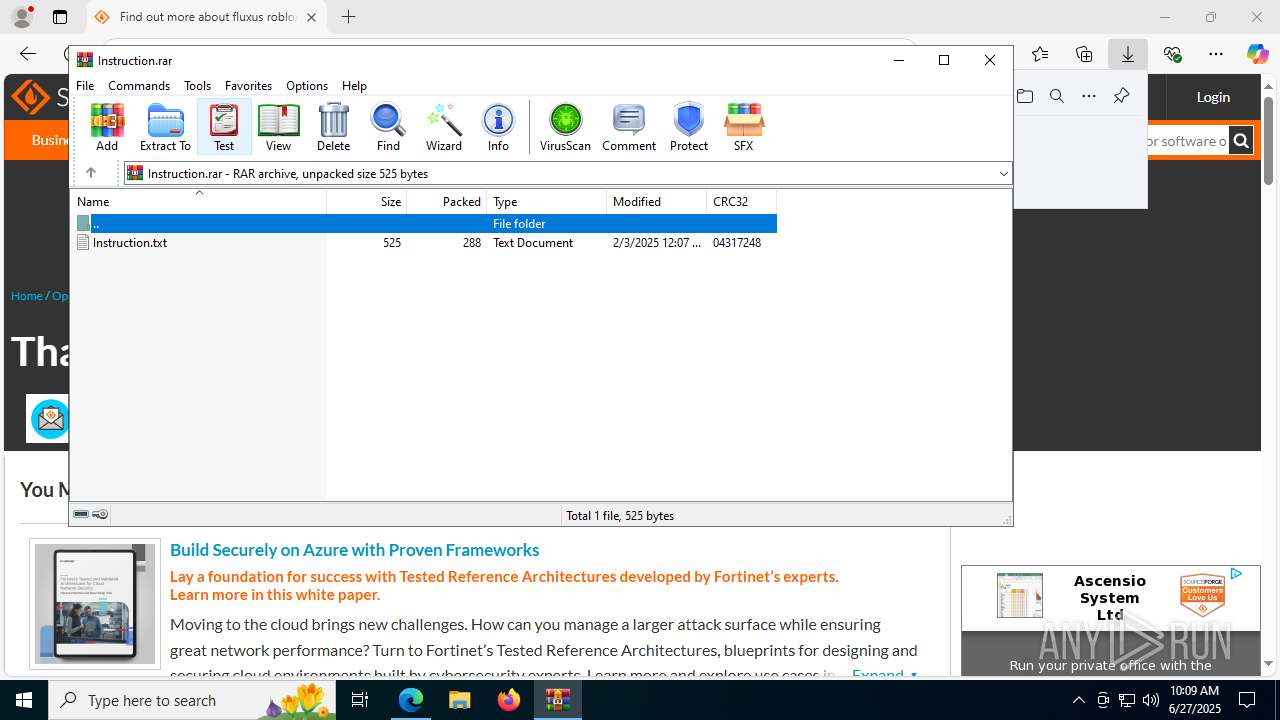
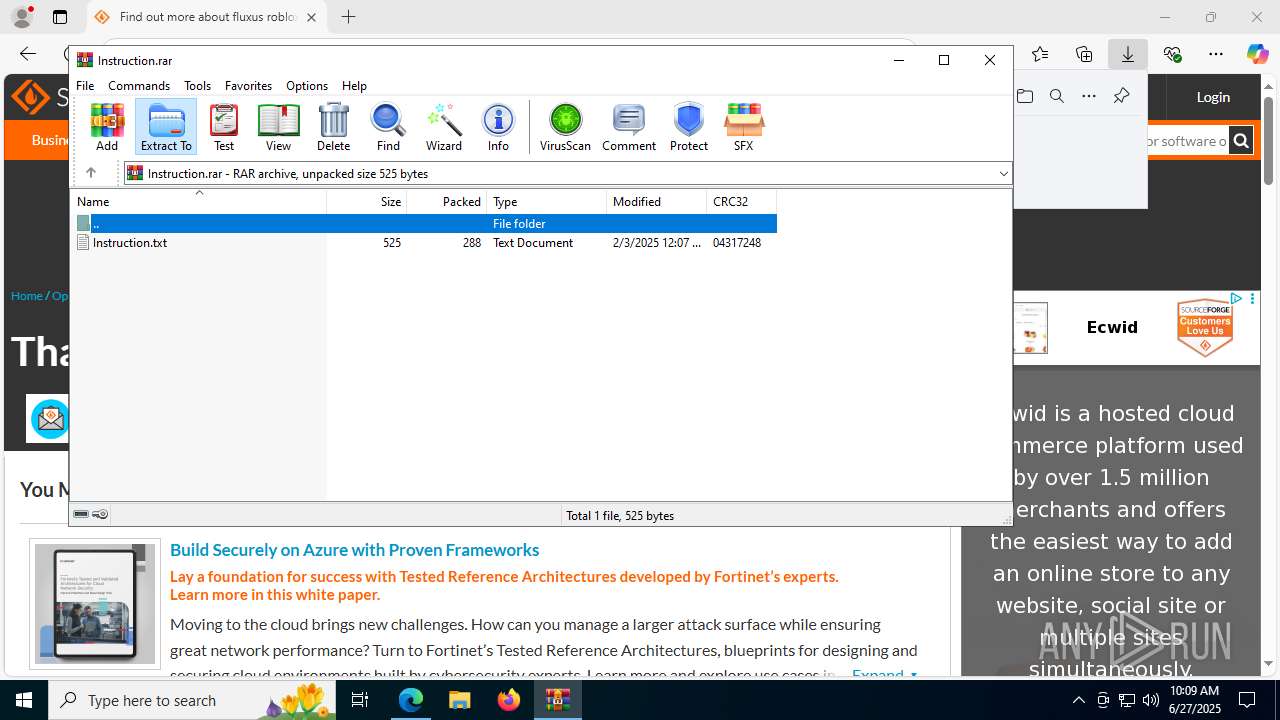
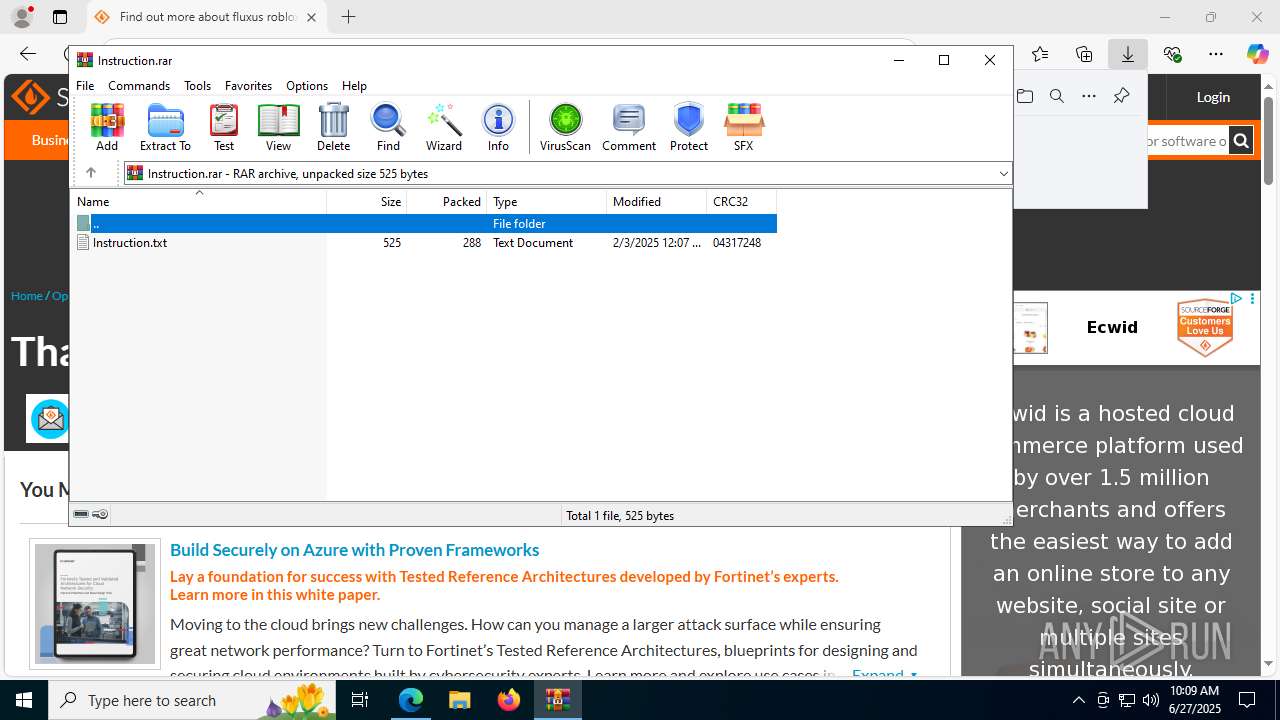
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8576)
- WinRAR.exe (PID: 1512)
- RL.exe (PID: 768)
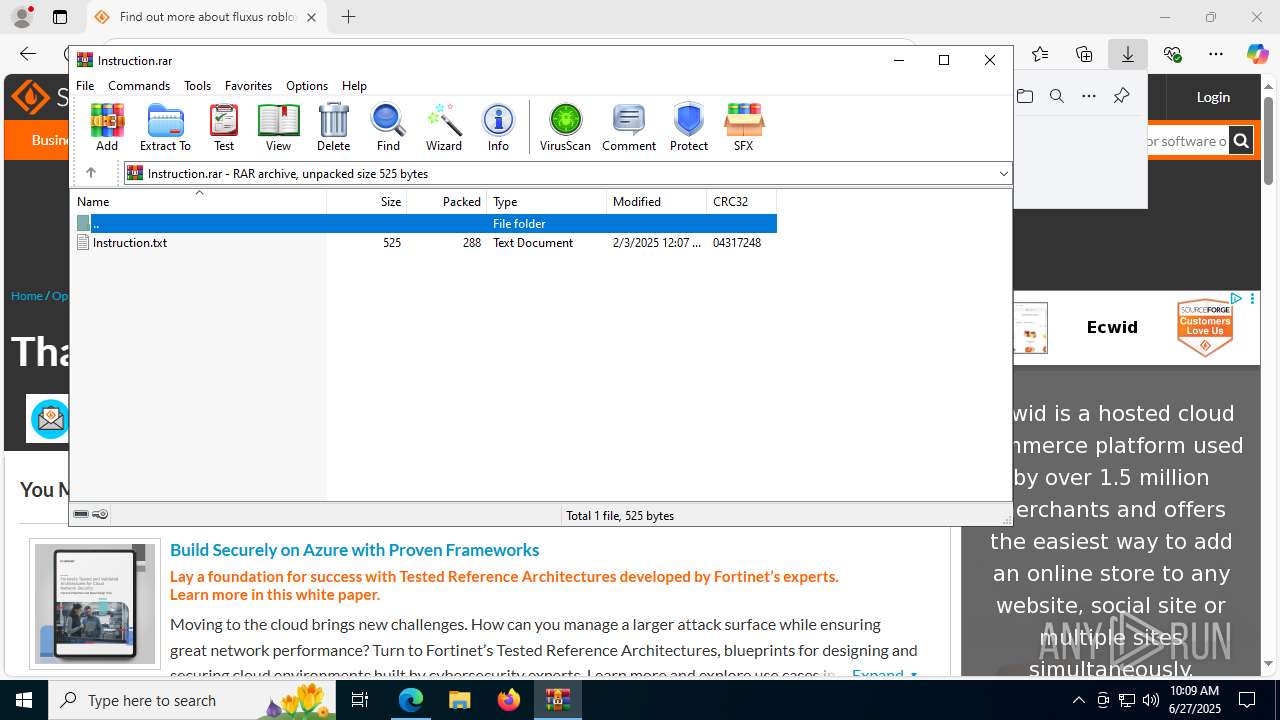
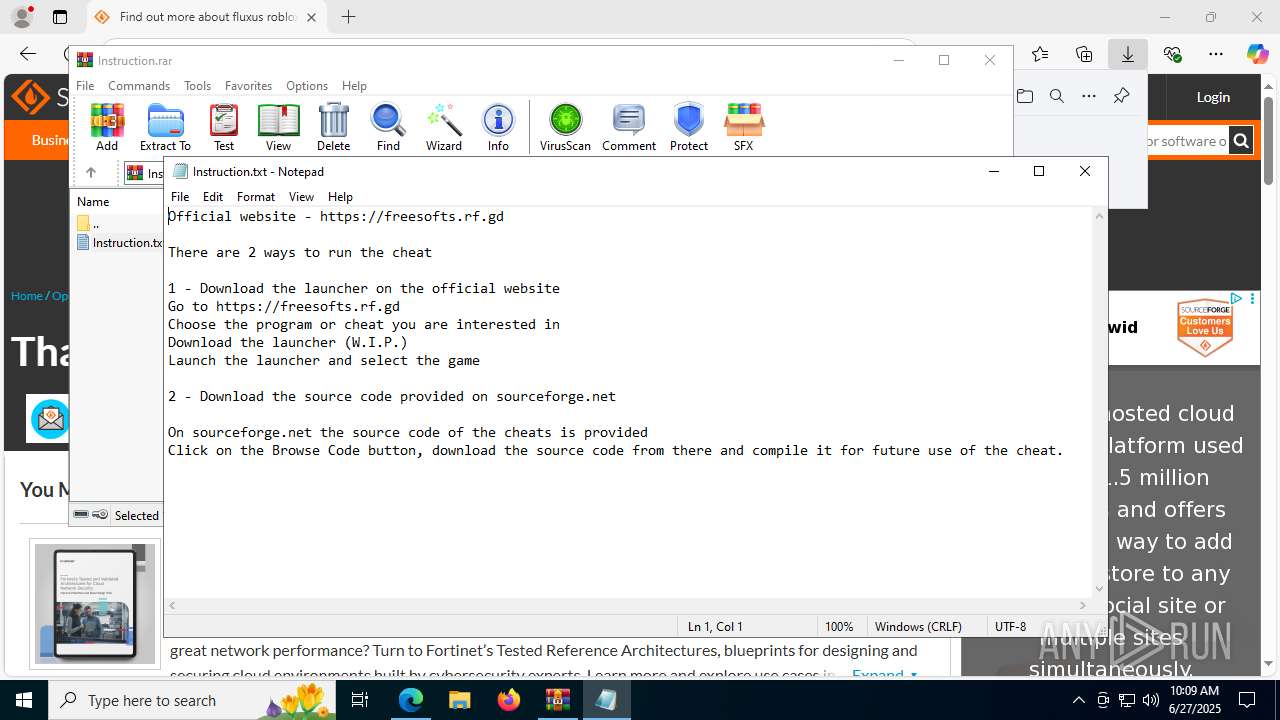
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 8576)
Reads the date of Windows installation
- RL.exe (PID: 768)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 1612)
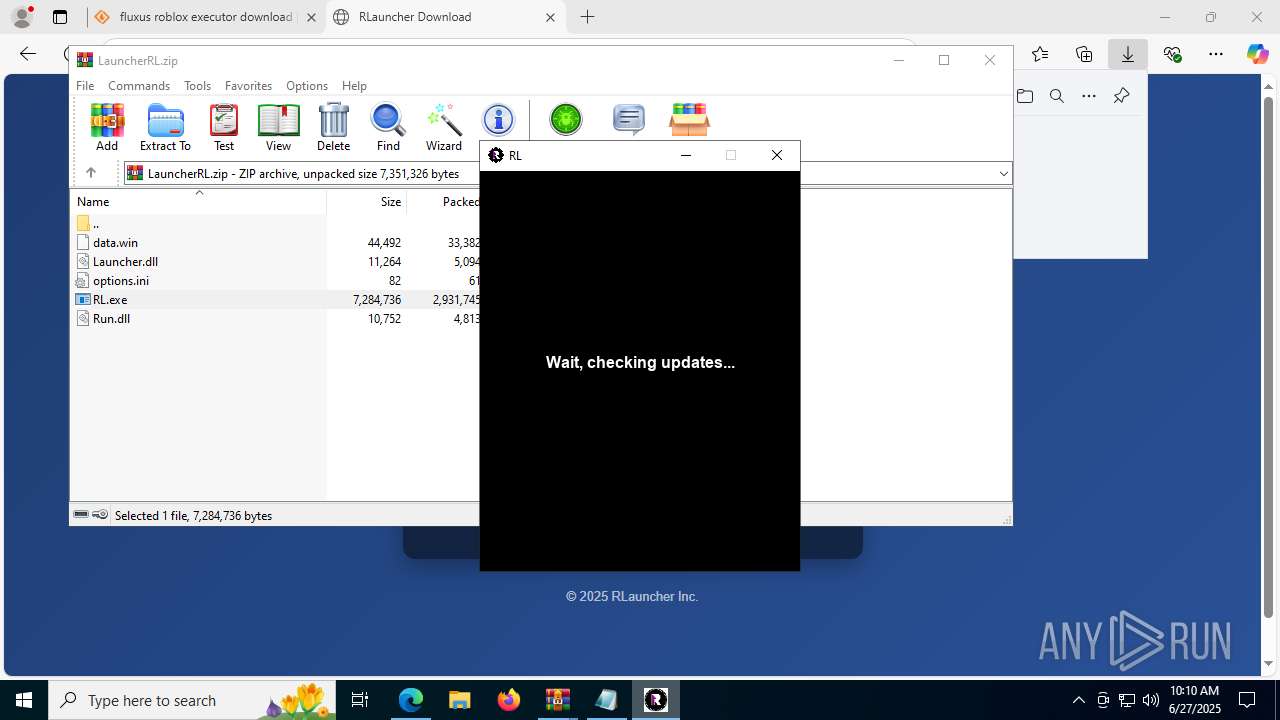
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1612)
Starts CMD.EXE for commands execution
- RL.exe (PID: 768)
Executable content was dropped or overwritten
- RL.exe (PID: 768)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2200)
- MSBuild.exe (PID: 868)
Searches for installed software
- MSBuild.exe (PID: 868)
There is functionality for taking screenshot (YARA)
- RL.exe (PID: 768)
INFO
Application launched itself
- msedge.exe (PID: 3976)
- msedge.exe (PID: 1100)
Checks supported languages
- identity_helper.exe (PID: 7672)
- RL.exe (PID: 768)
- kosdko0.exe (PID: 7924)
- MSBuild.exe (PID: 868)
- identity_helper.exe (PID: 7576)
Reads Environment values
- identity_helper.exe (PID: 7672)
- identity_helper.exe (PID: 7576)
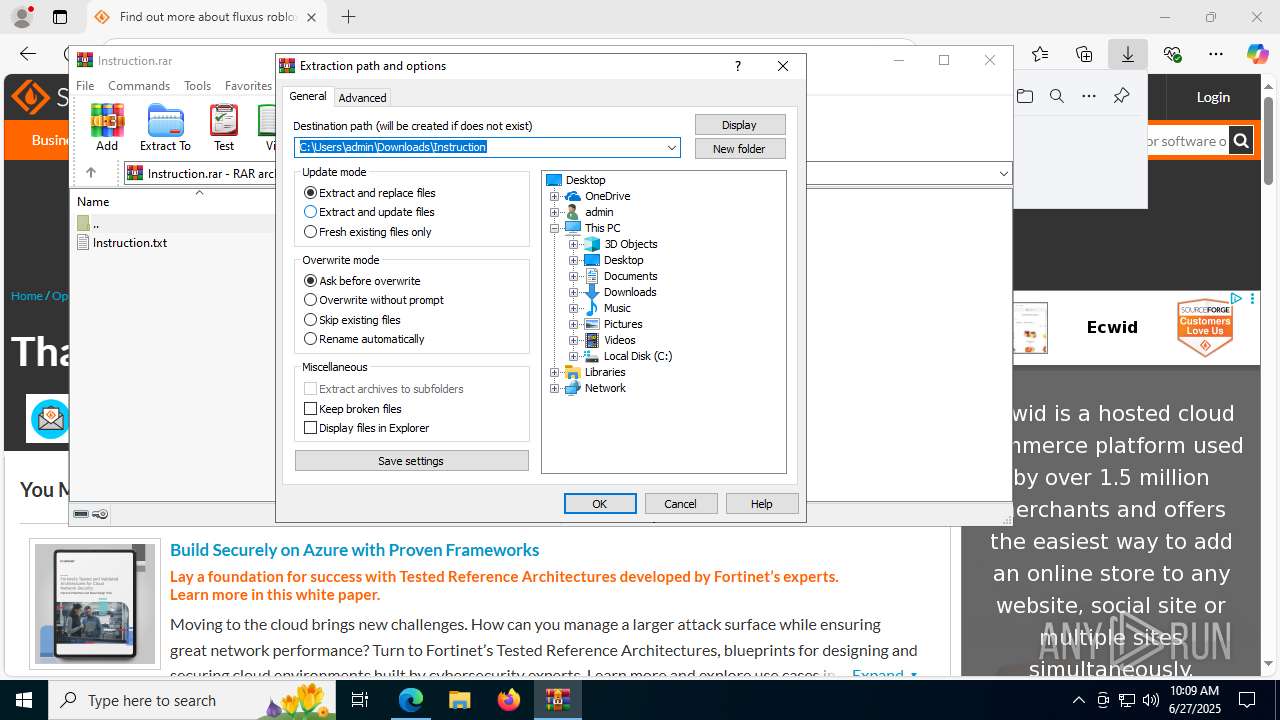
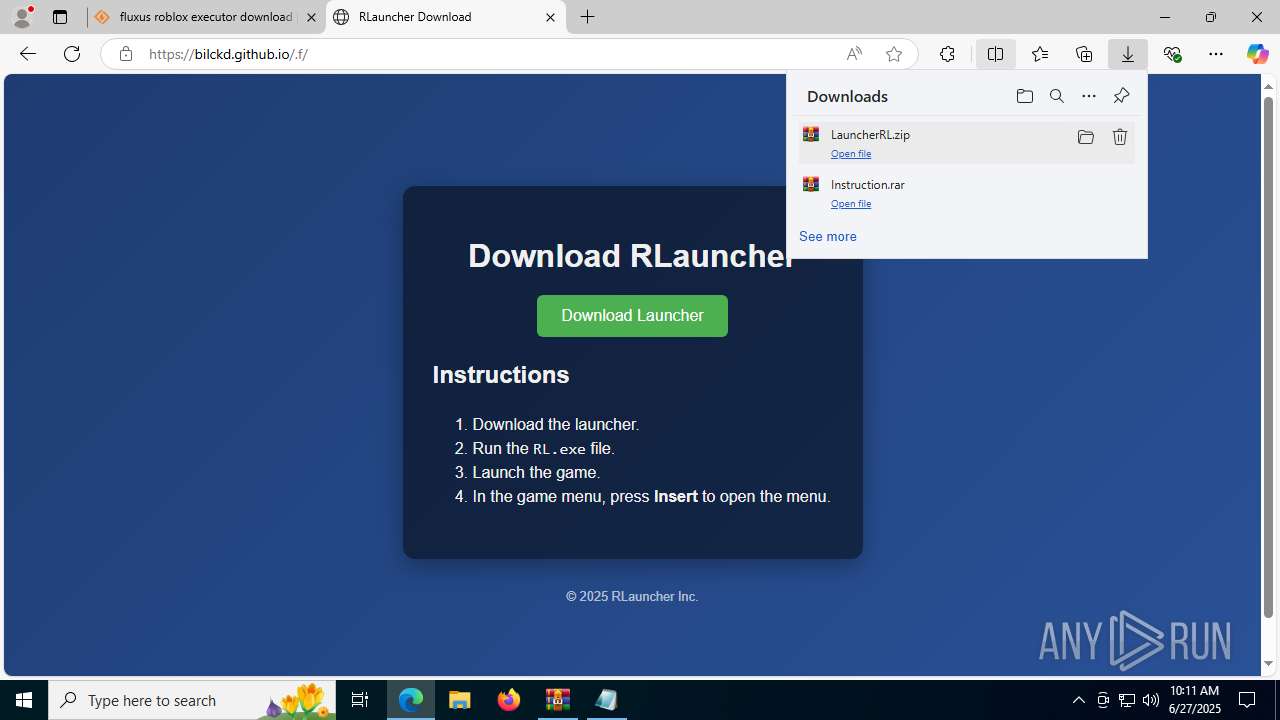
Launching a file from the Downloads directory
- msedge.exe (PID: 3976)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3976)
- WinRAR.exe (PID: 8576)
Reads security settings of Internet Explorer
- notepad.exe (PID: 9160)
The sample compiled with english language support
- msedge.exe (PID: 5456)
- WinRAR.exe (PID: 1512)
- msedge.exe (PID: 3976)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1512)
Reads the computer name
- RL.exe (PID: 768)
- MSBuild.exe (PID: 868)
- identity_helper.exe (PID: 7576)
- identity_helper.exe (PID: 7672)
Process checks computer location settings
- RL.exe (PID: 768)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8392)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8392)
Reads the software policy settings
- RL.exe (PID: 768)
- MSBuild.exe (PID: 868)
- slui.exe (PID: 8712)
Reads the machine GUID from the registry
- RL.exe (PID: 768)
- MSBuild.exe (PID: 868)
Checks proxy server information
- RL.exe (PID: 768)
- slui.exe (PID: 8712)
Creates files or folders in the user directory
- RL.exe (PID: 768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
216
Monitored processes
73
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
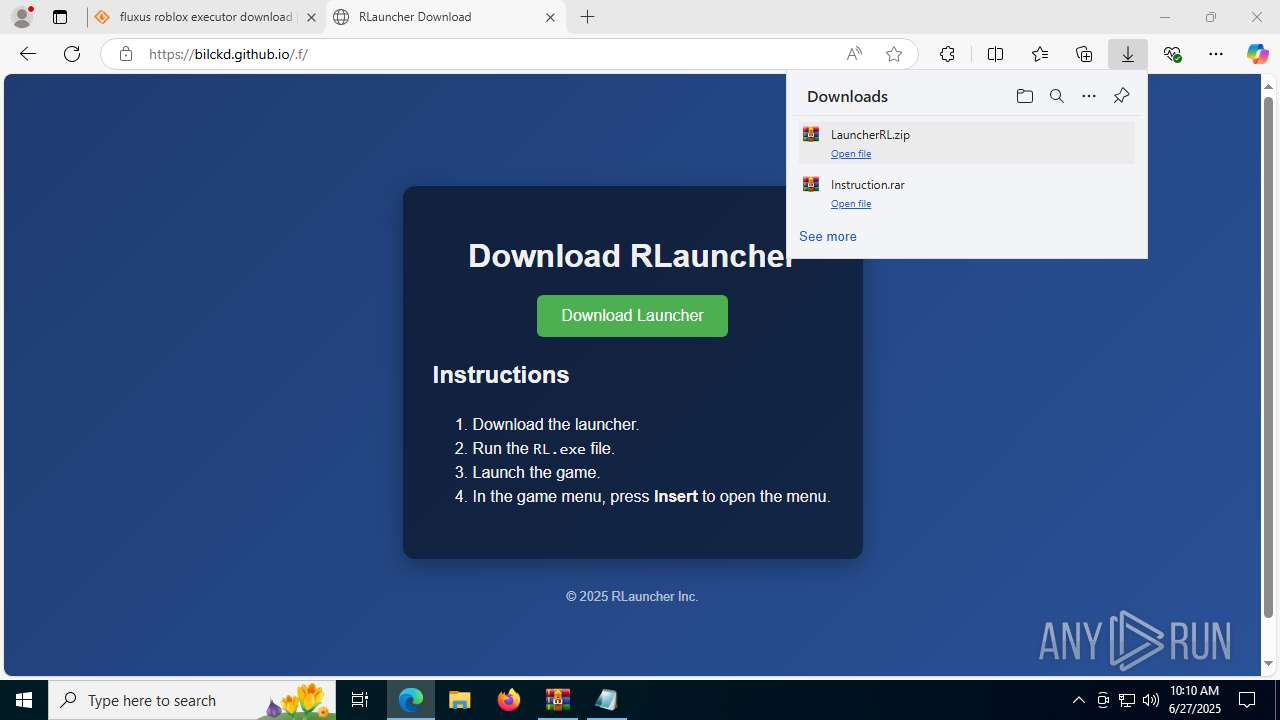
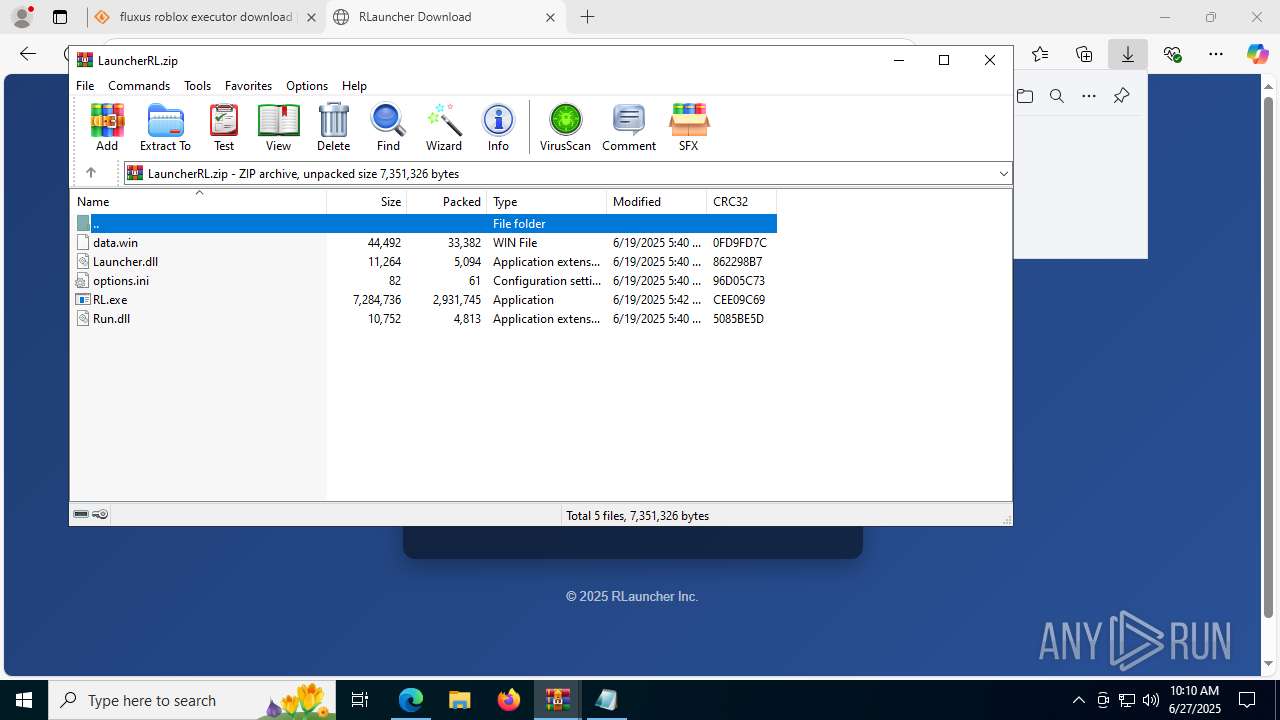
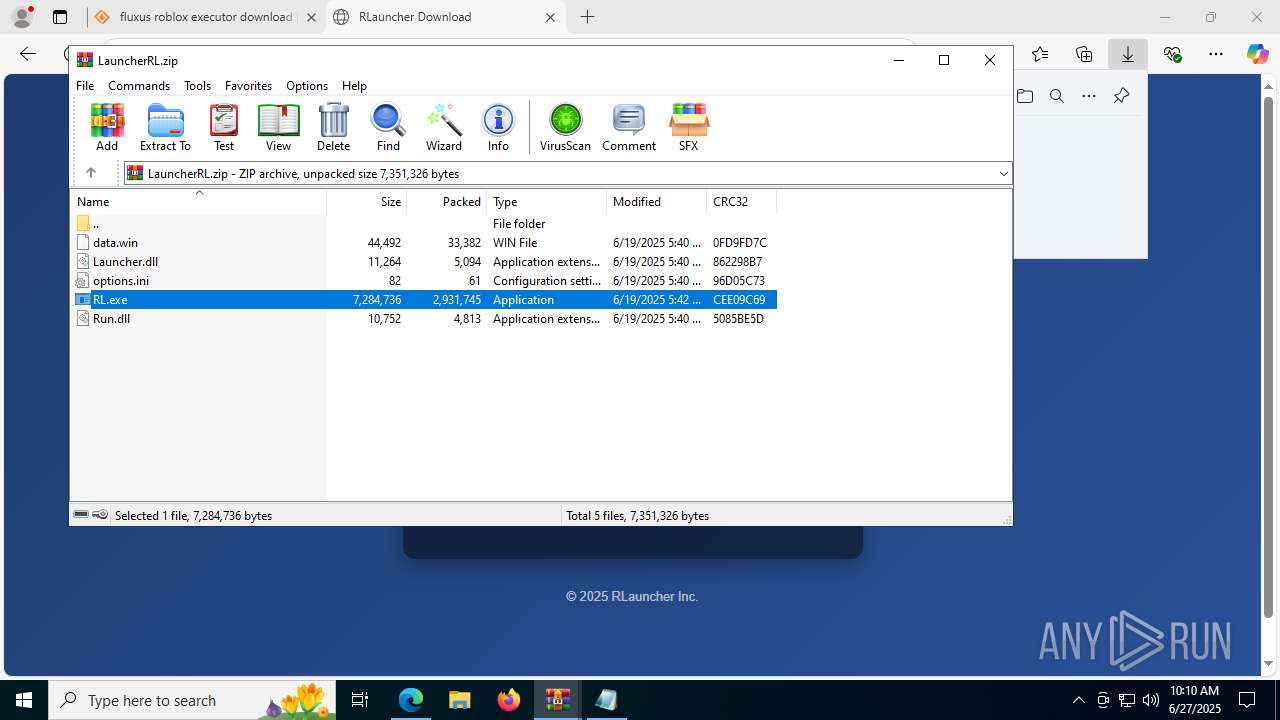
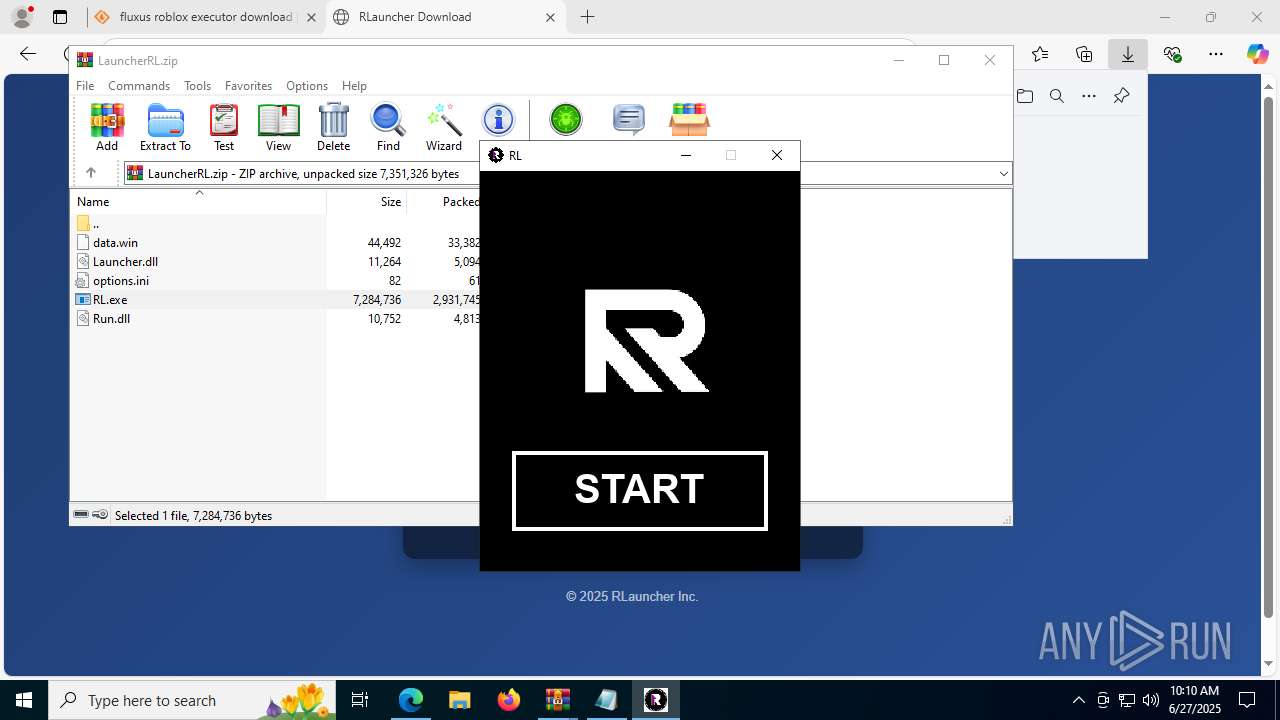
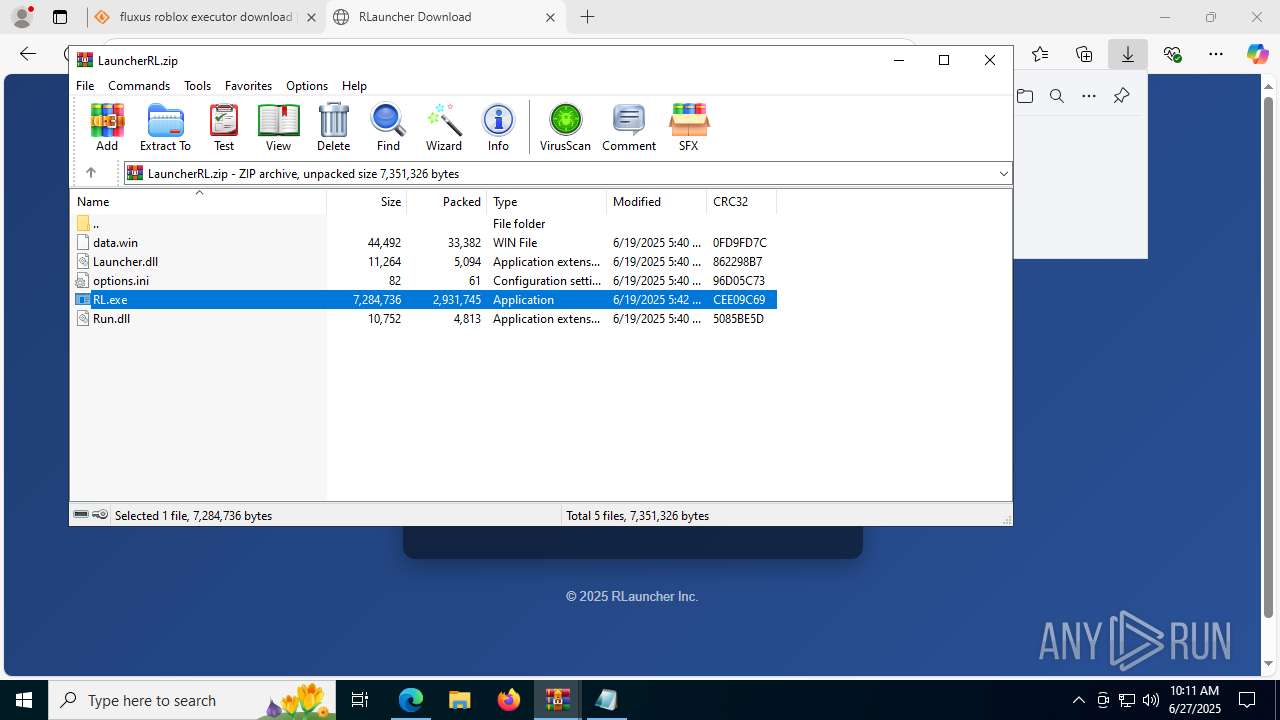
| 768 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1512.33266\RL.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1512.33266\RL.exe | WinRAR.exe | ||||||||||||
User: admin Company: YoYo Games Ltd Integrity Level: HIGH Description: A GameMaker Game Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 868 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | kosdko0.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --always-read-main-dll --field-trial-handle=7380,i,18278267693266139174,9822093039650483868,262144 --variations-seed-version --mojo-platform-channel-handle=7668 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1100 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --always-read-main-dll --field-trial-handle=7840,i,18278267693266139174,9822093039650483868,262144 --variations-seed-version --mojo-platform-channel-handle=7784 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1440 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5692,i,18278267693266139174,9822093039650483868,262144 --variations-seed-version --mojo-platform-channel-handle=8488 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
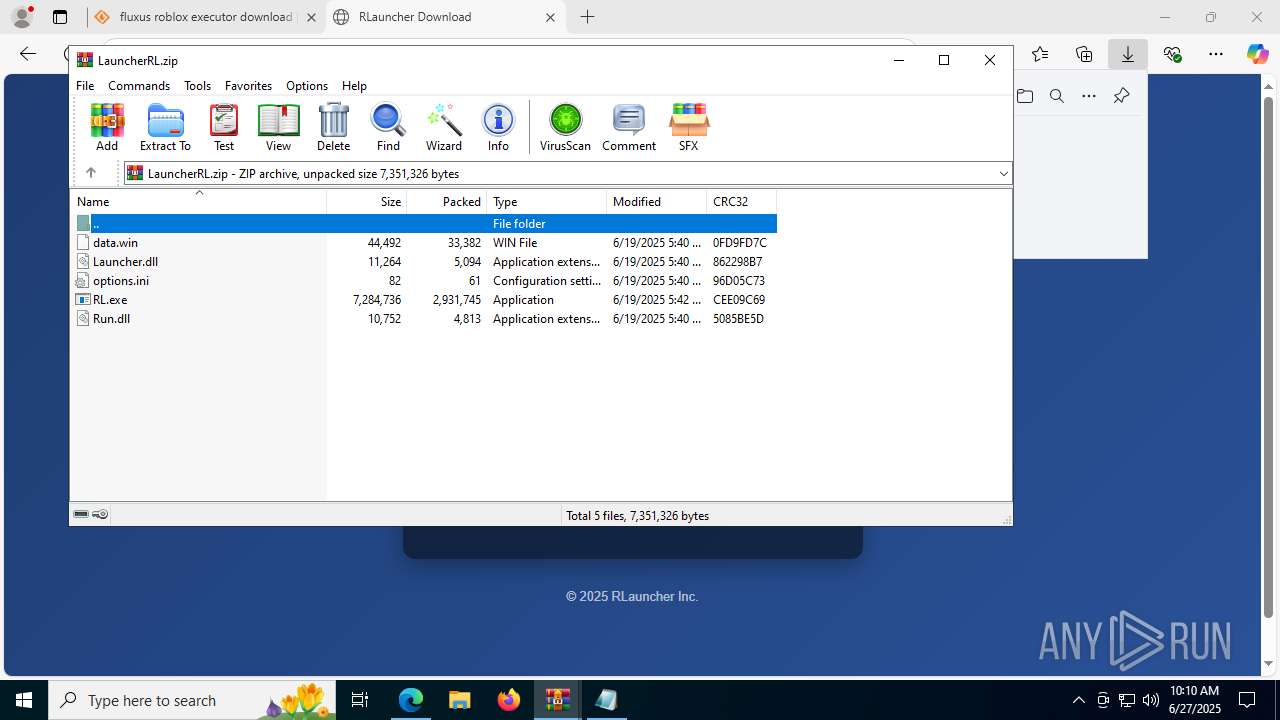
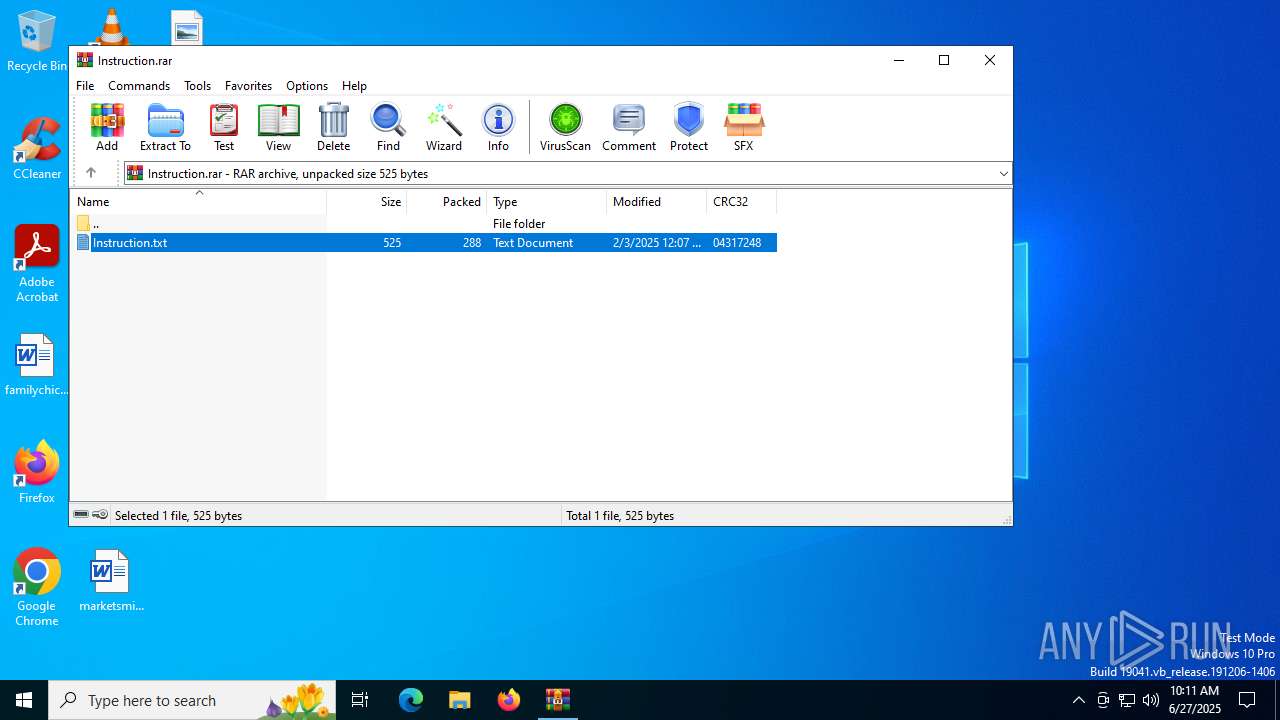
| 1512 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\LauncherRL.zip" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1612 | "C:\Windows\System32\cmd.exe" /c powershell Add-MpPreference -ExclusionPath 'C:\' | C:\Windows\System32\cmd.exe | — | RL.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=35 --always-read-main-dll --field-trial-handle=8236,i,18278267693266139174,9822093039650483868,262144 --variations-seed-version --mojo-platform-channel-handle=8764 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 938
Read events
25 807
Write events
106
Delete events
25
Modification events
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B3BF702721972F00 | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590702 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {00D0D24F-C460-4A16-9F97-3D8EF1305E27} | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590702 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {55D3F2E2-23D0-4CCB-9083-FC01329A865A} | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590702 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DE694F6F-F463-40C7-9836-5BCFAA43E8CF} | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590702 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1BFA2B30-5781-4473-B40E-E2CA23A1F52C} | |||
| (PID) Process: | (3976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
43
Suspicious files
701
Text files
147
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF175a45.TMP | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF175a55.TMP | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF175a74.TMP | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF175a45.TMP | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF175a84.TMP | — | |
MD5:— | SHA256:— | |||
| 3976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF175a84.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
289
DNS requests
362
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5456 | msedge.exe | GET | — | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:tHuAPh5Y8OHBSvlRYND6sImWBkjYk10AGnx9h2kIT3Y&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6320 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8828 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8340 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751618457&P2=404&P3=2&P4=AFVaeUMe6RRvcpzWzv6rw2Iox3VzlFNoDxYbXUSKDgeNbjJrCofcAnMhnpnCrSEYoG%2fAoRyKP1jlfHAS5Sfi0g%3d%3d | unknown | — | — | whitelisted |
8340 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751618457&P2=404&P3=2&P4=AFVaeUMe6RRvcpzWzv6rw2Iox3VzlFNoDxYbXUSKDgeNbjJrCofcAnMhnpnCrSEYoG%2fAoRyKP1jlfHAS5Sfi0g%3d%3d | unknown | — | — | whitelisted |
8828 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8340 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751618457&P2=404&P3=2&P4=AFVaeUMe6RRvcpzWzv6rw2Iox3VzlFNoDxYbXUSKDgeNbjJrCofcAnMhnpnCrSEYoG%2fAoRyKP1jlfHAS5Sfi0g%3d%3d | unknown | — | — | whitelisted |
8340 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1751618458&P2=404&P3=2&P4=LBQVMKQxAYQbGiwraEoRXS0CXRxSIcV4BX%2bAydet04PglmFZ93lJ0mycy0MDmZiidu9gv8PS7lN0bkozT0KKZg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4040 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5456 | msedge.exe | 92.123.104.53:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
5456 | msedge.exe | 104.18.17.56:443 | a.fsdn.com | CLOUDFLARENET | — | whitelisted |
5456 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5456 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5456 | msedge.exe | 104.18.13.149:443 | sourceforge.net | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
sourceforge.net |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
a.fsdn.com |
| whitelisted |
www.bing.com |
| whitelisted |
c.amazon-adsystem.com |
| whitelisted |
d.delivery.consentmanager.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
5456 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5456 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5456 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5456 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
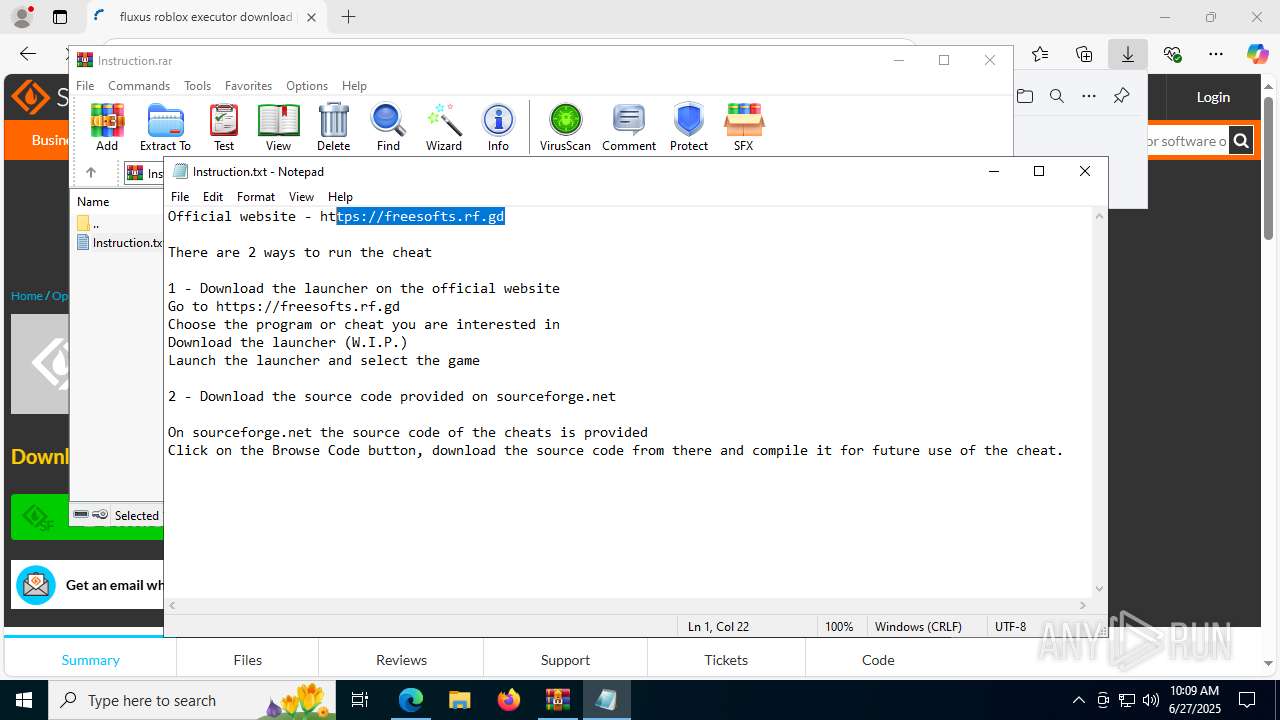
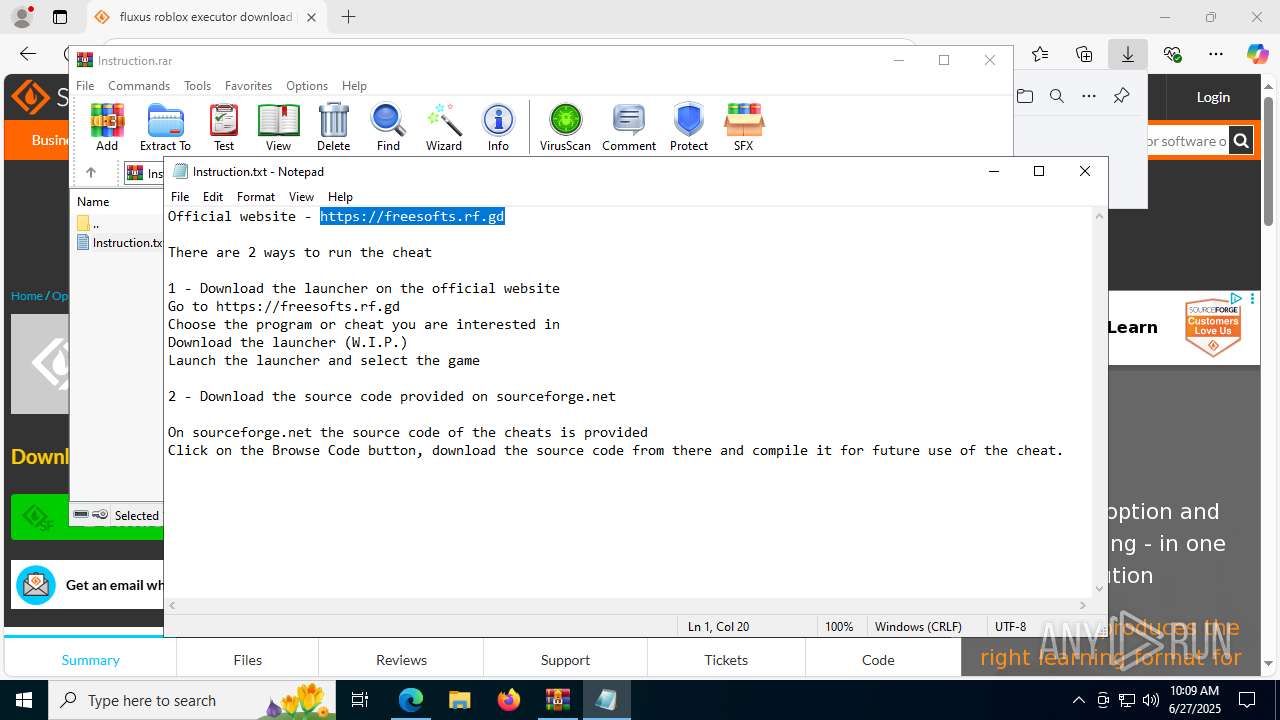
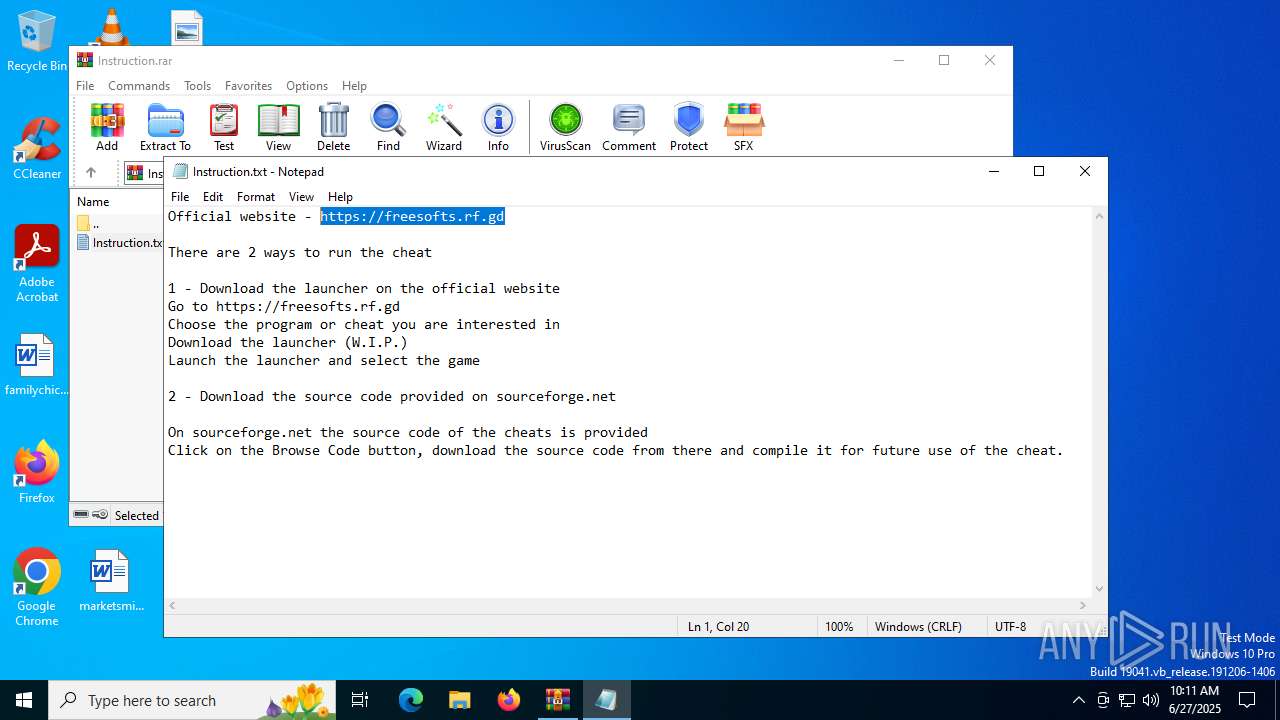
5456 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Commonly Abused Web Hosting domain observed (* .rf .gd) |
5456 | msedge.exe | Potentially Bad Traffic | ET TA_ABUSED_SERVICES Commonly Abused Domain in DNS Lookup (rf .gd) |
5456 | msedge.exe | Potentially Bad Traffic | ET TA_ABUSED_SERVICES Commonly Abused Domain in DNS Lookup (rf .gd) |
5456 | msedge.exe | Potentially Bad Traffic | ET TA_ABUSED_SERVICES Commonly Abused Domain in DNS Lookup (rf .gd) |
5456 | msedge.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Commonly Abused Web Hosting domain observed (* .rf .gd) |