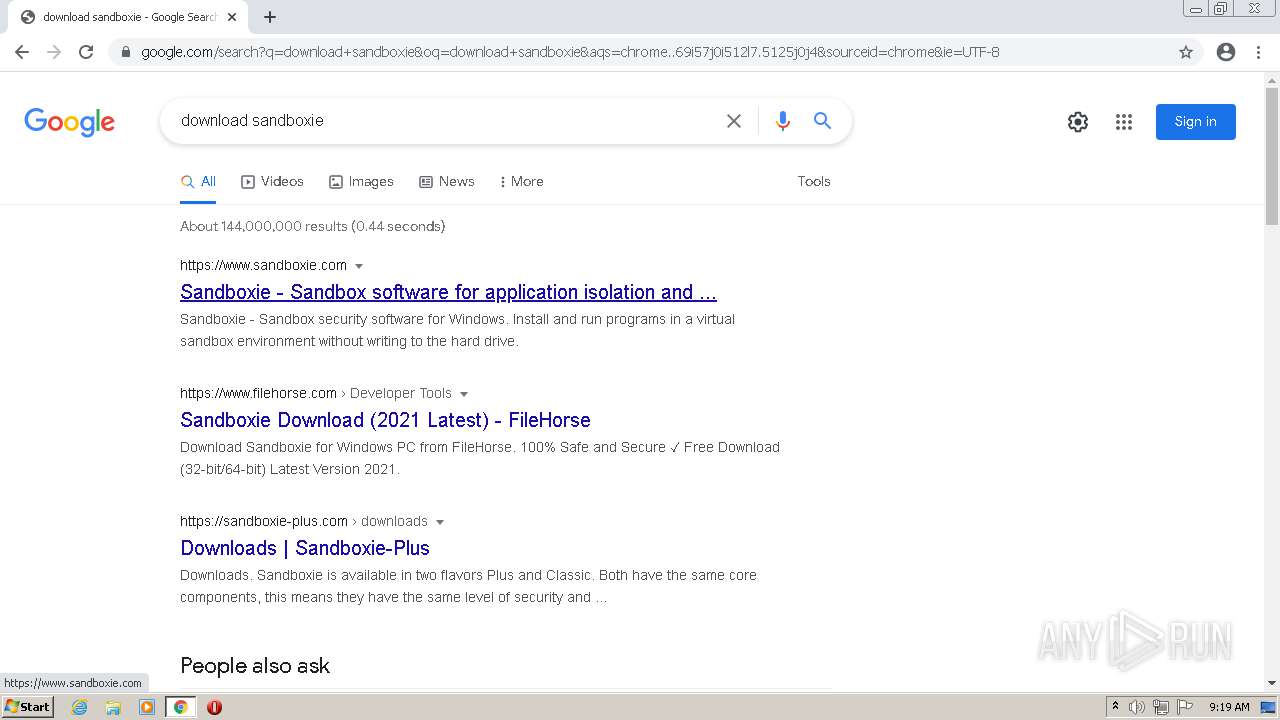
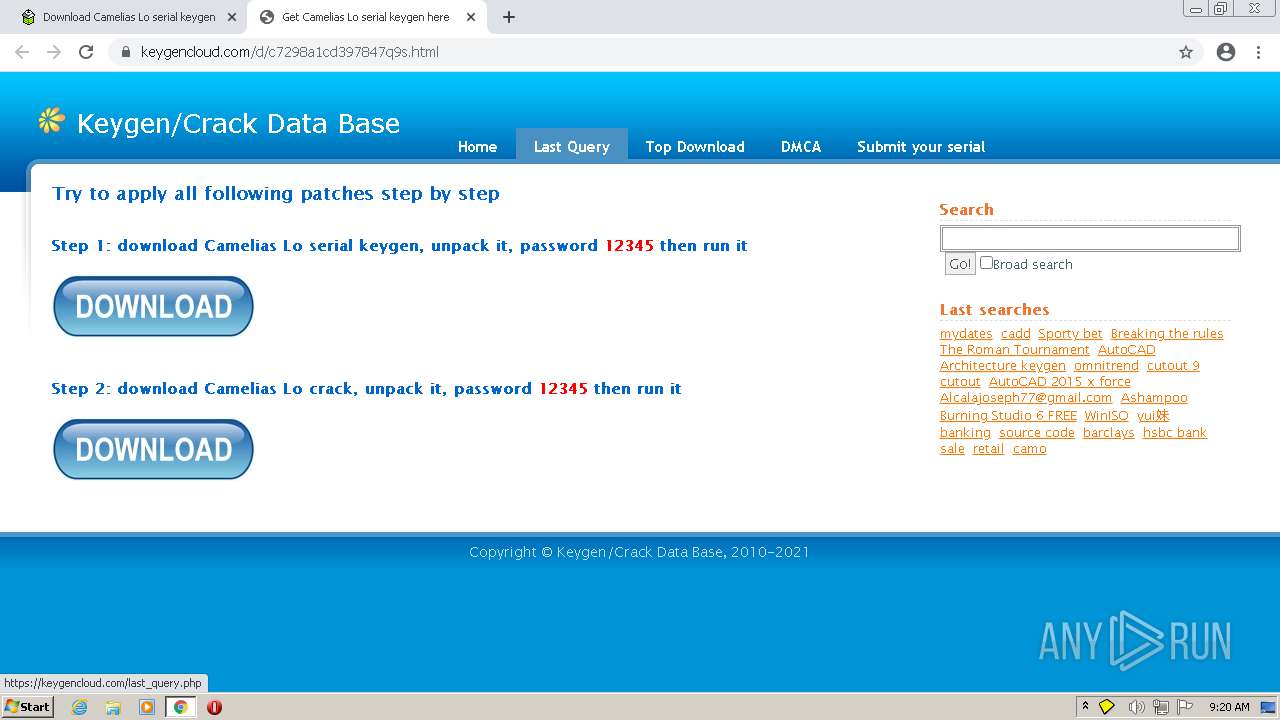
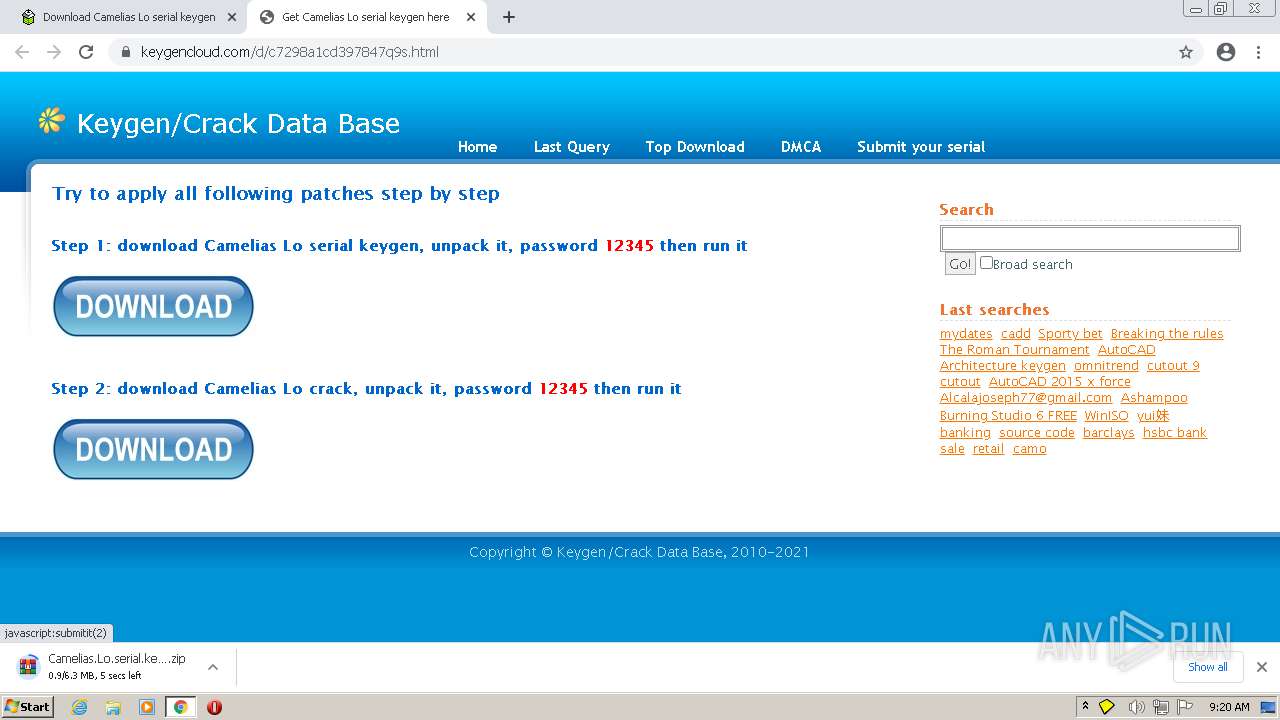
| URL: | https://www.google.com |
| Full analysis: | https://app.any.run/tasks/09e0fd34-fa6f-473e-920c-b3b3cde6d2a8 |
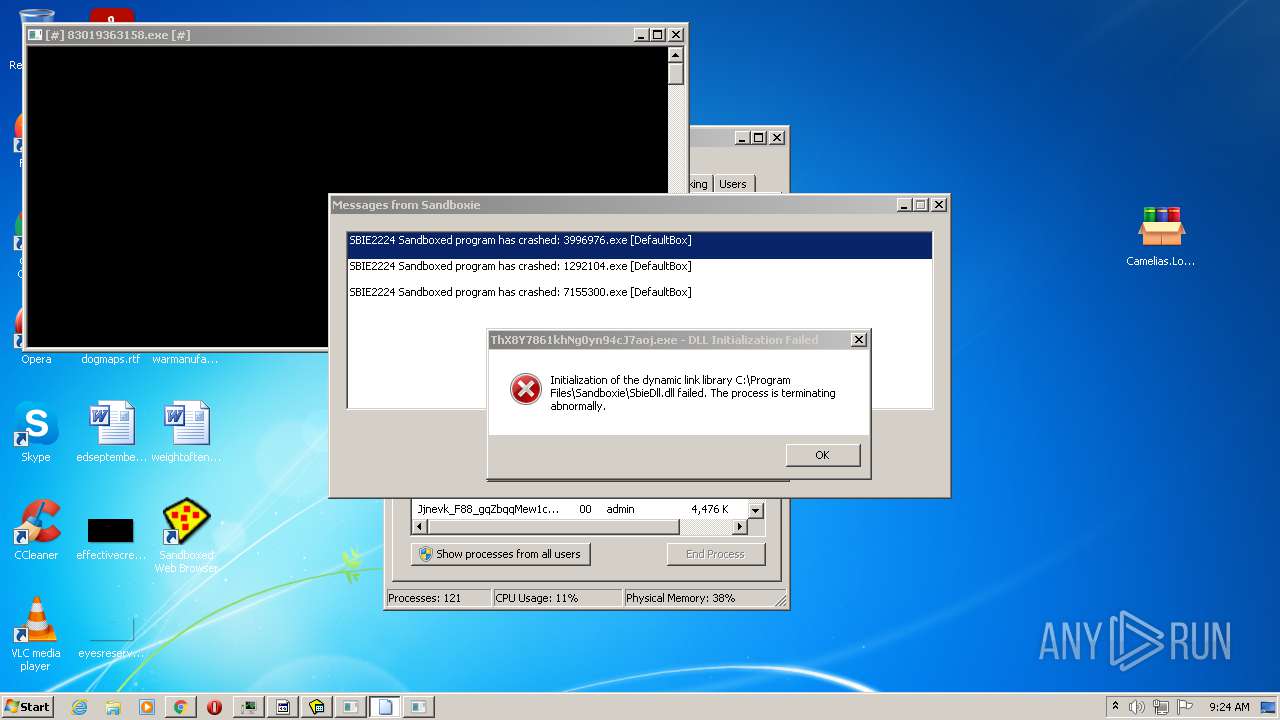
| Verdict: | Malicious activity |
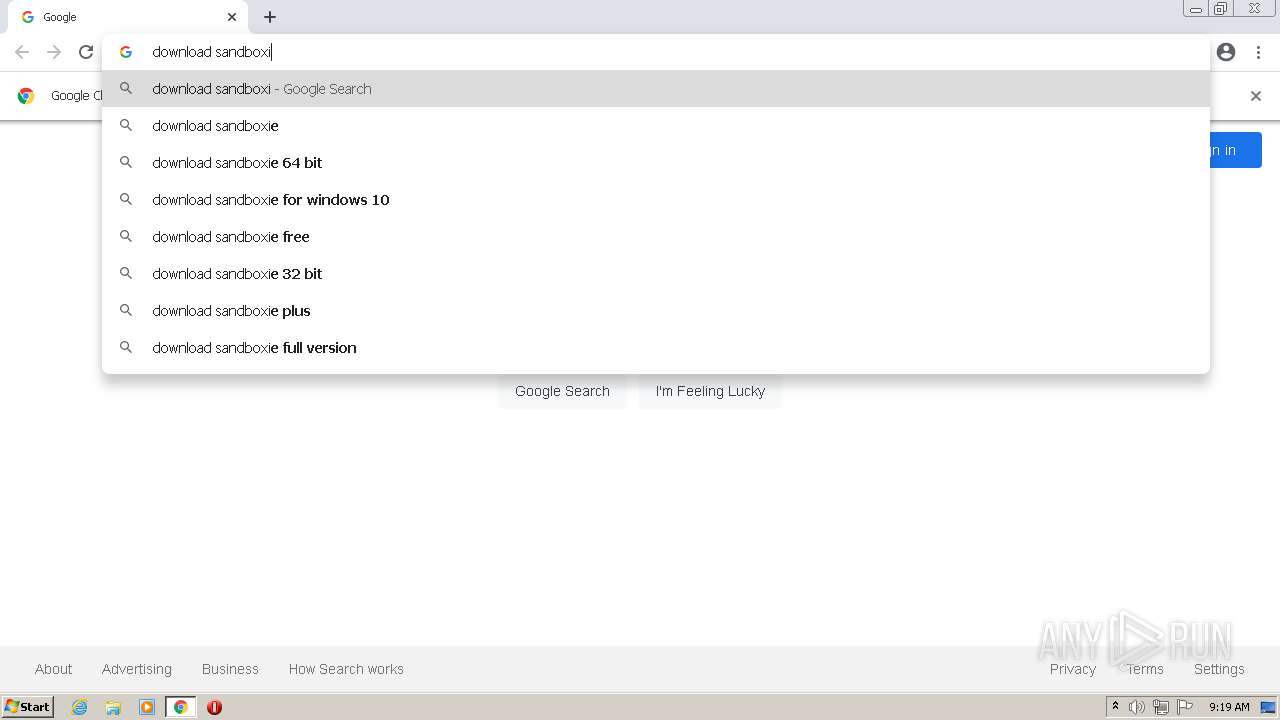
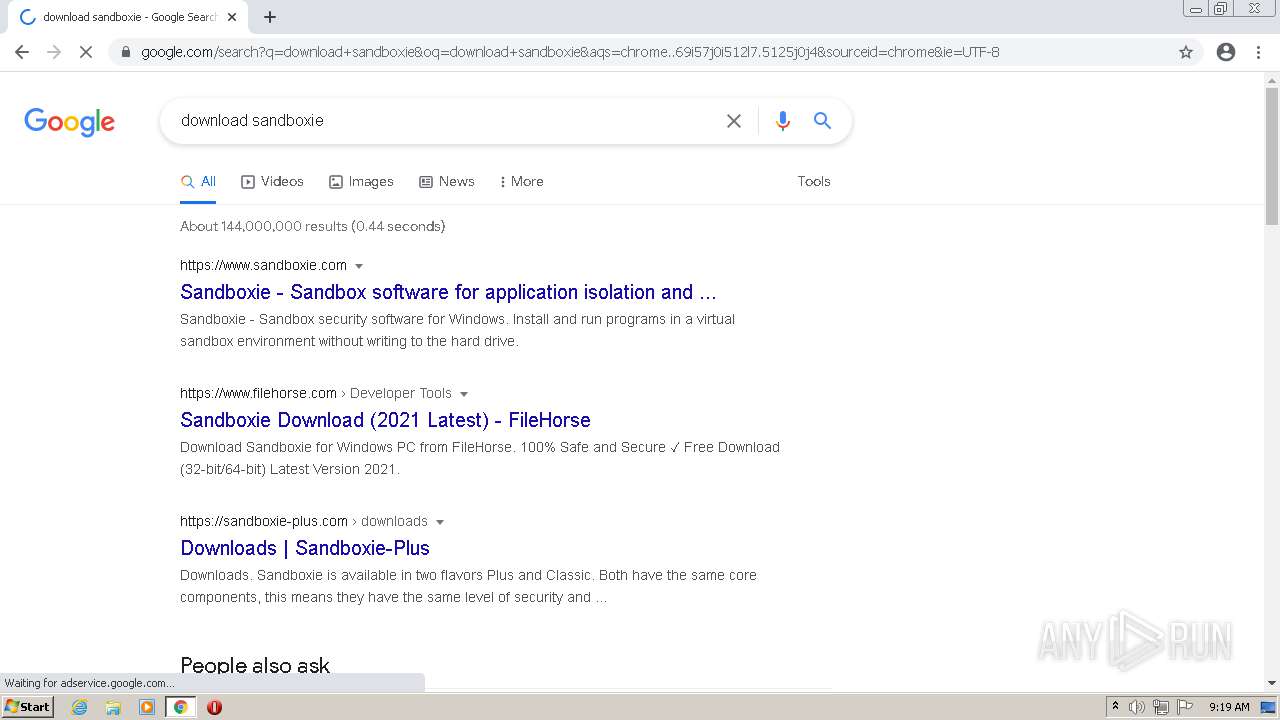
| Threats: | AZORult can steal banking information, including passwords and credit card details, as well as cryptocurrency. This constantly updated information stealer malware should not be taken lightly, as it continues to be an active threat. |
| Analysis date: | August 27, 2021, 08:19:14 |
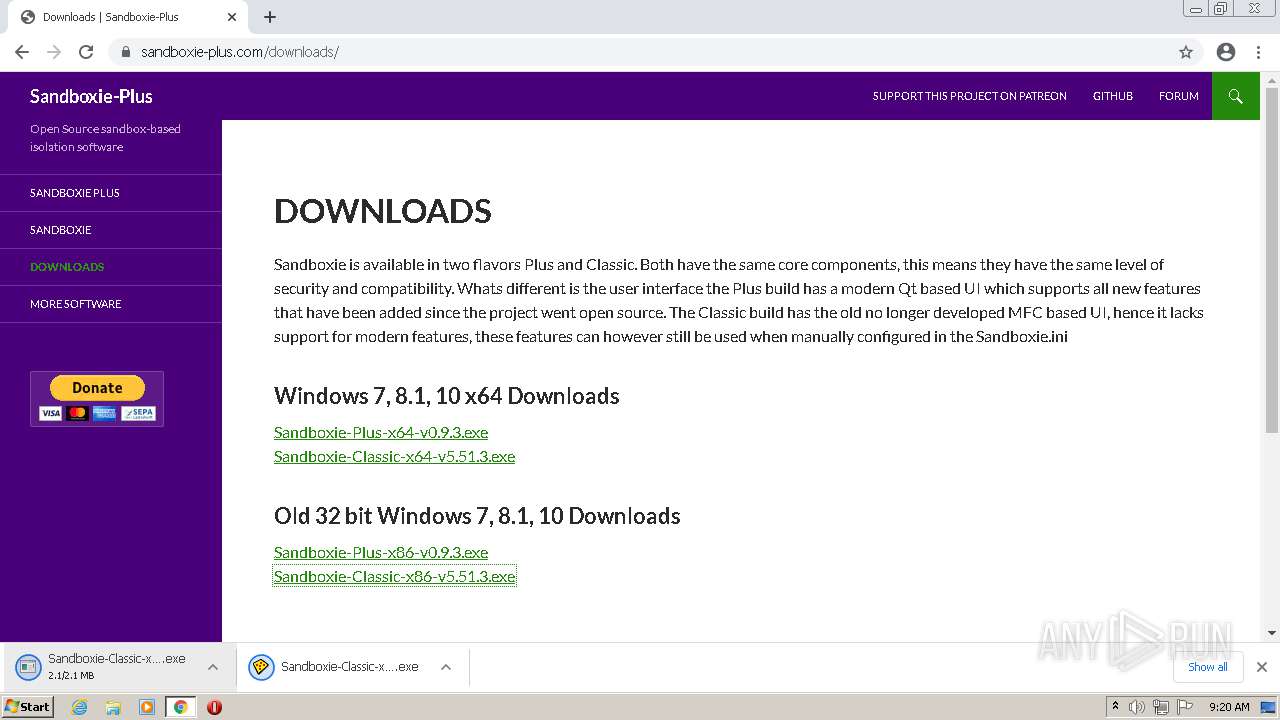
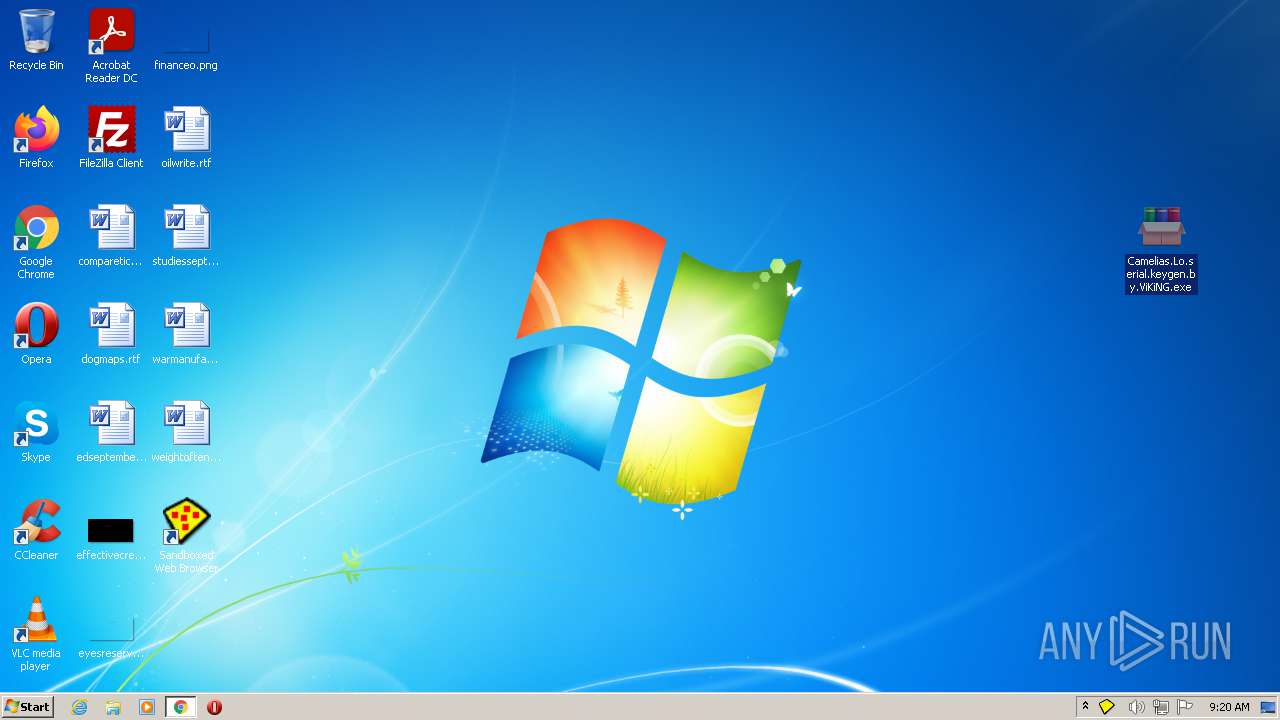
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8FFDEFBDEC956B595D257F0AAEEFD623 |
| SHA1: | EF7EFC9839C3EE036F023E9635BC3B056D6EE2DB |
| SHA256: | AC6BB669E40E44A8D9F8F0C94DFC63734049DCF6219AAC77F02EDF94B9162C09 |
| SSDEEP: | 3:N8DSLIK:2OLIK |
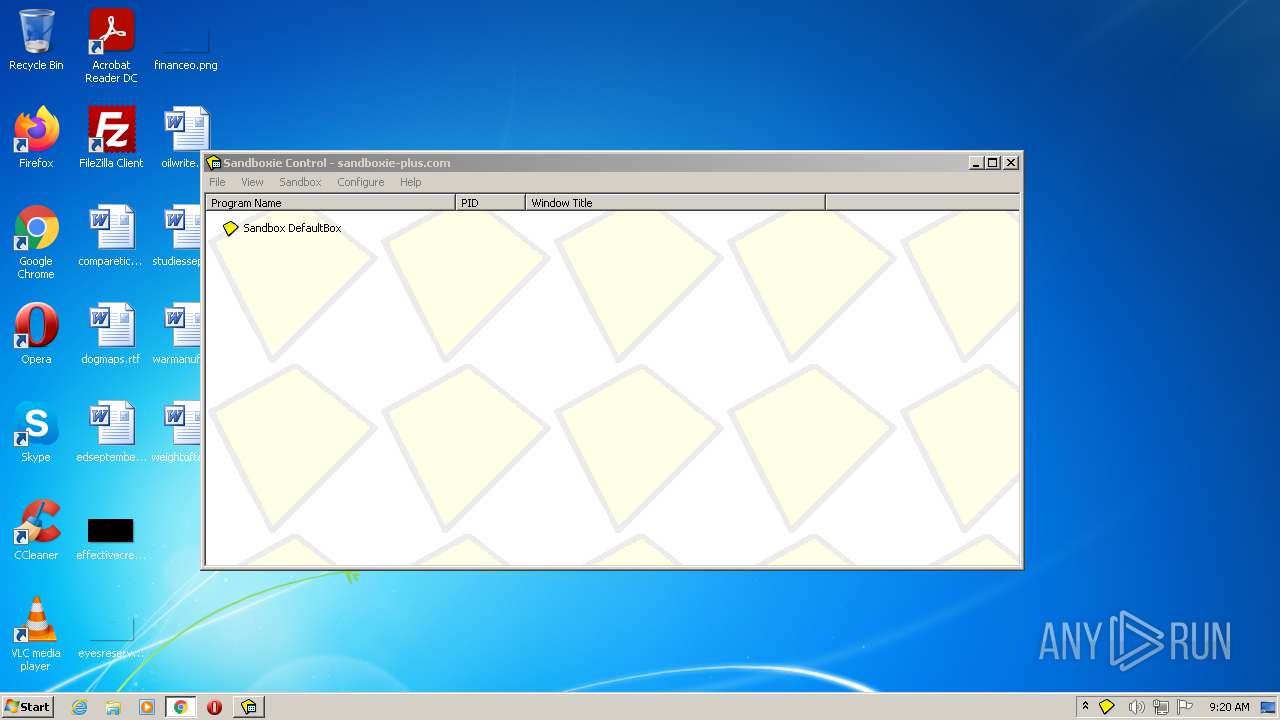
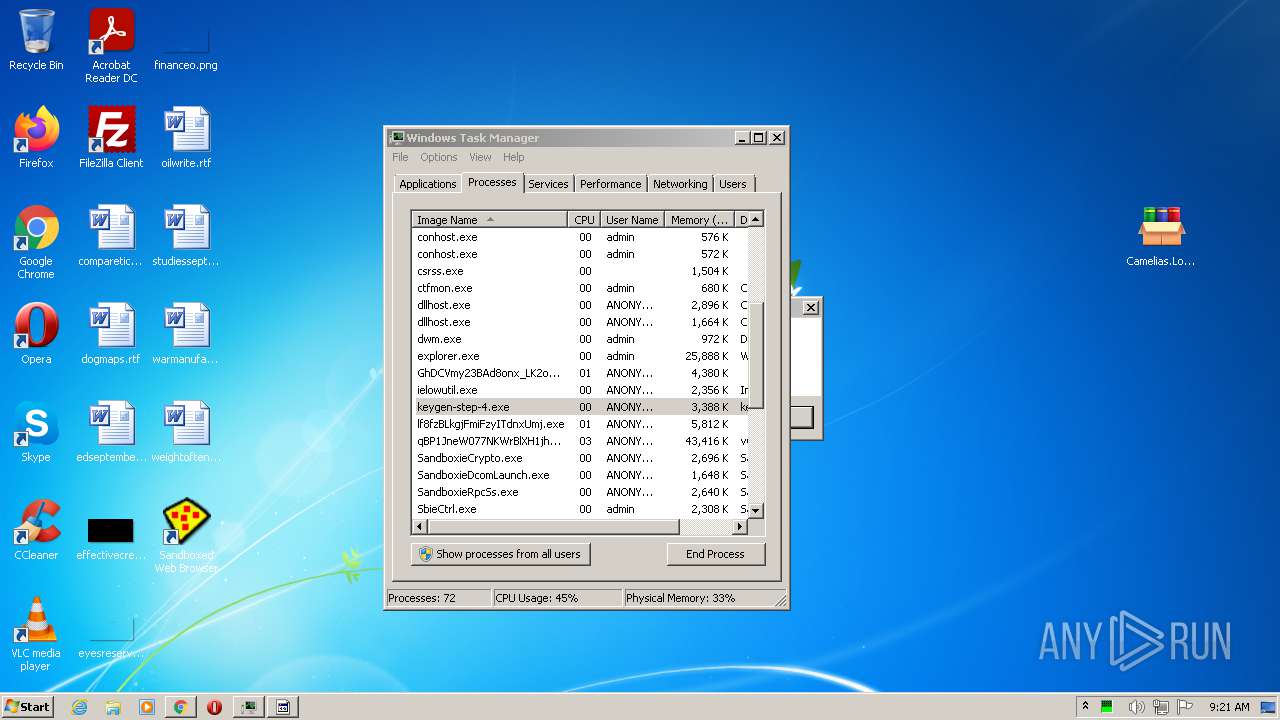
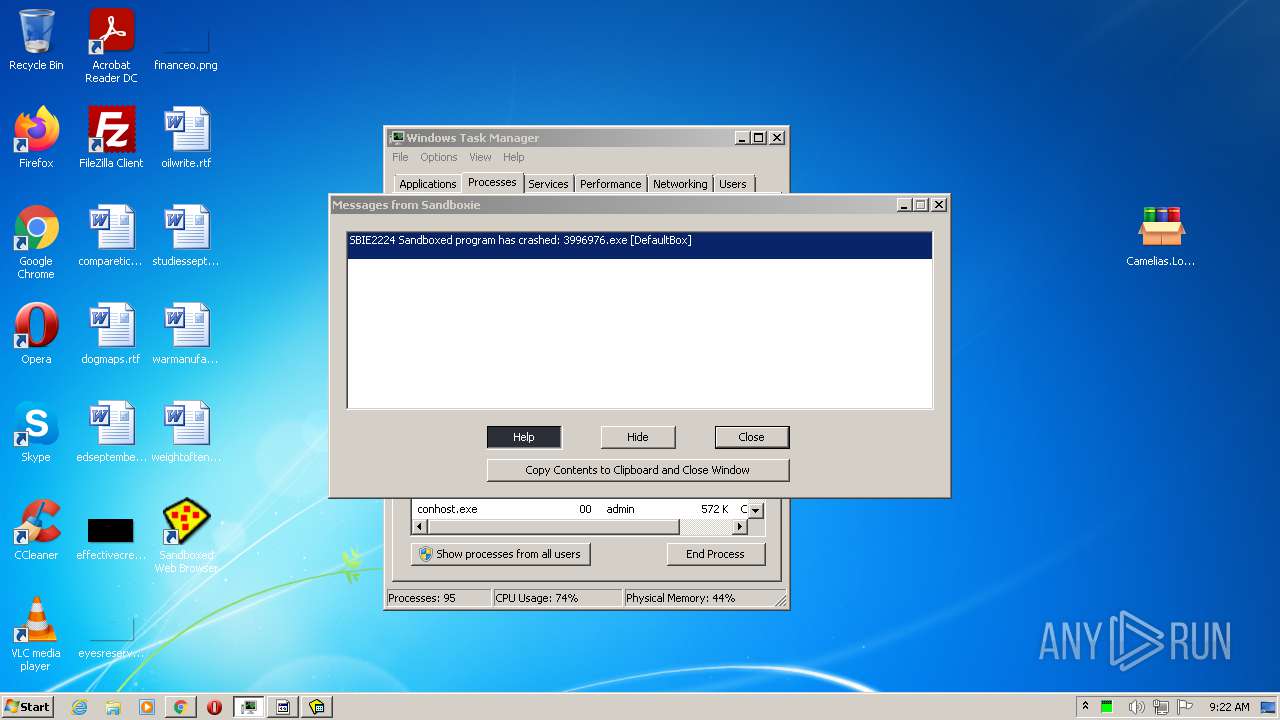
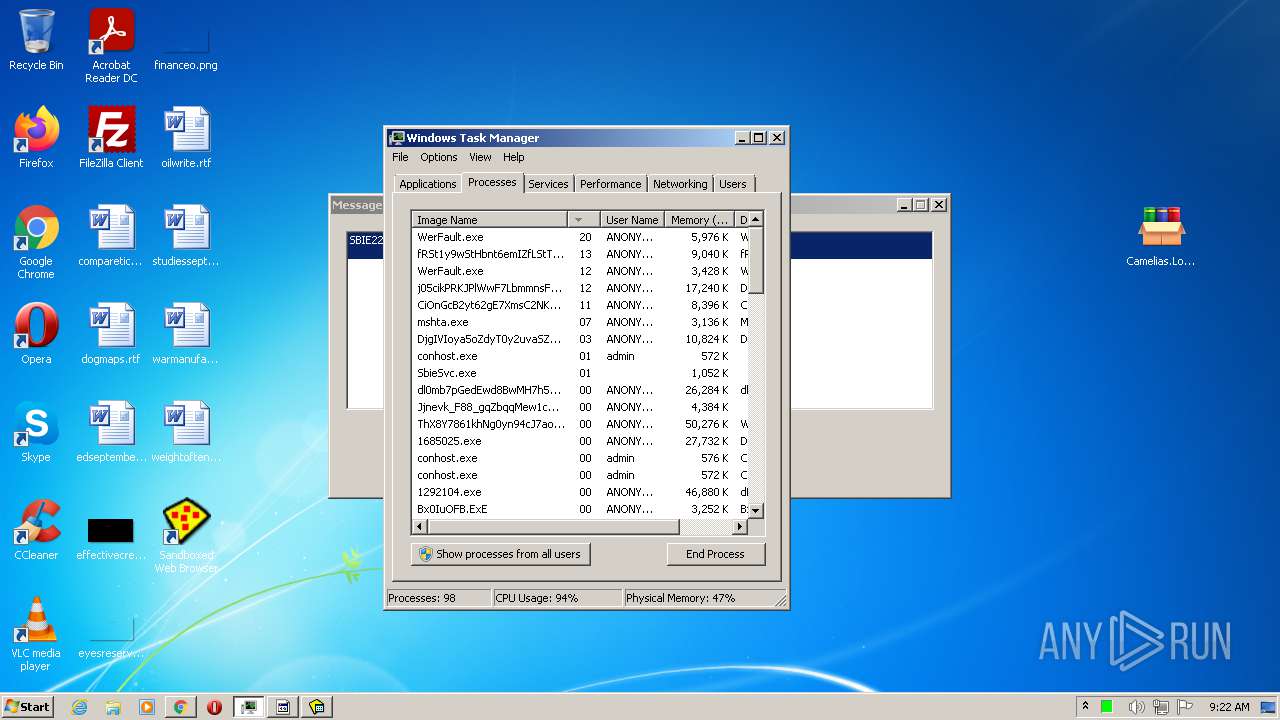
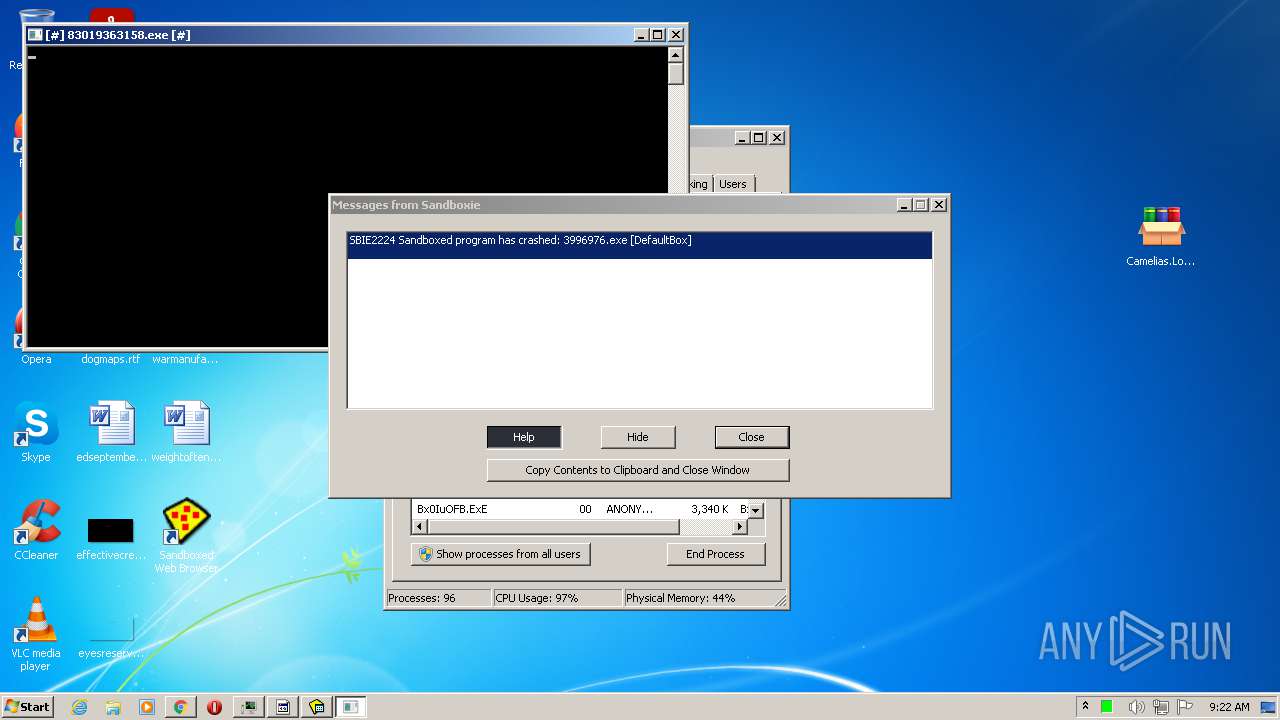
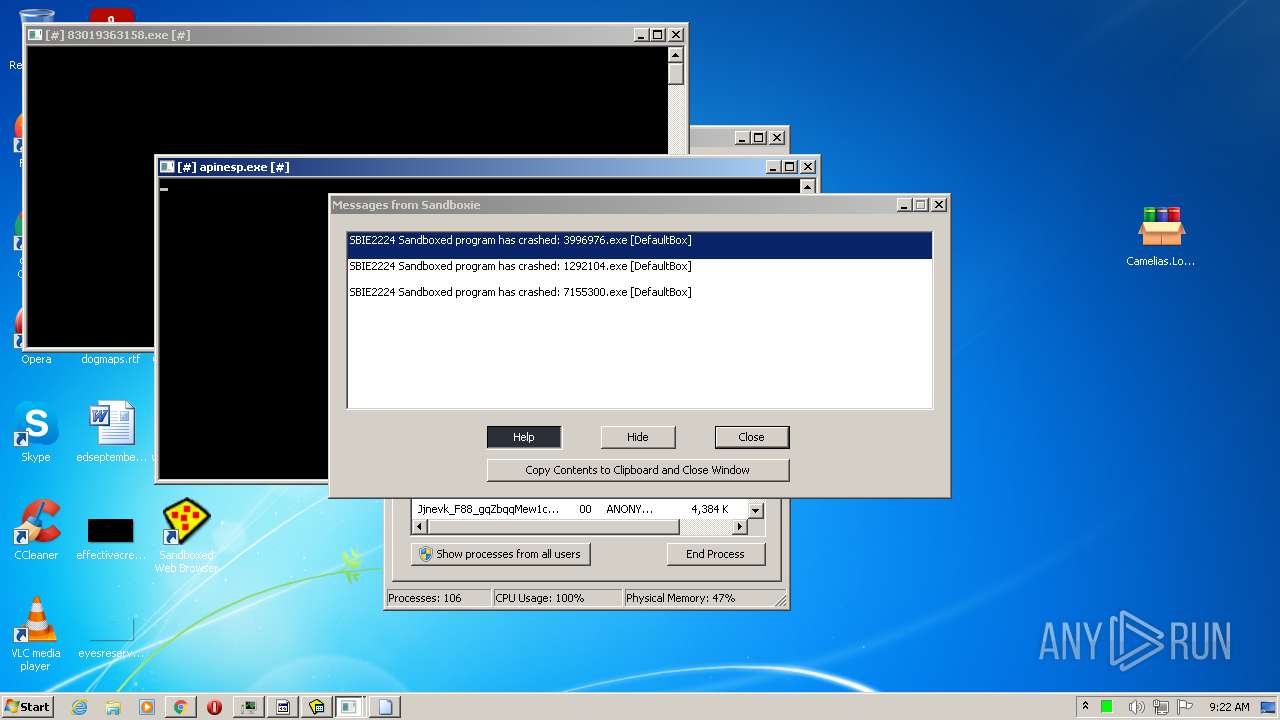
MALICIOUS
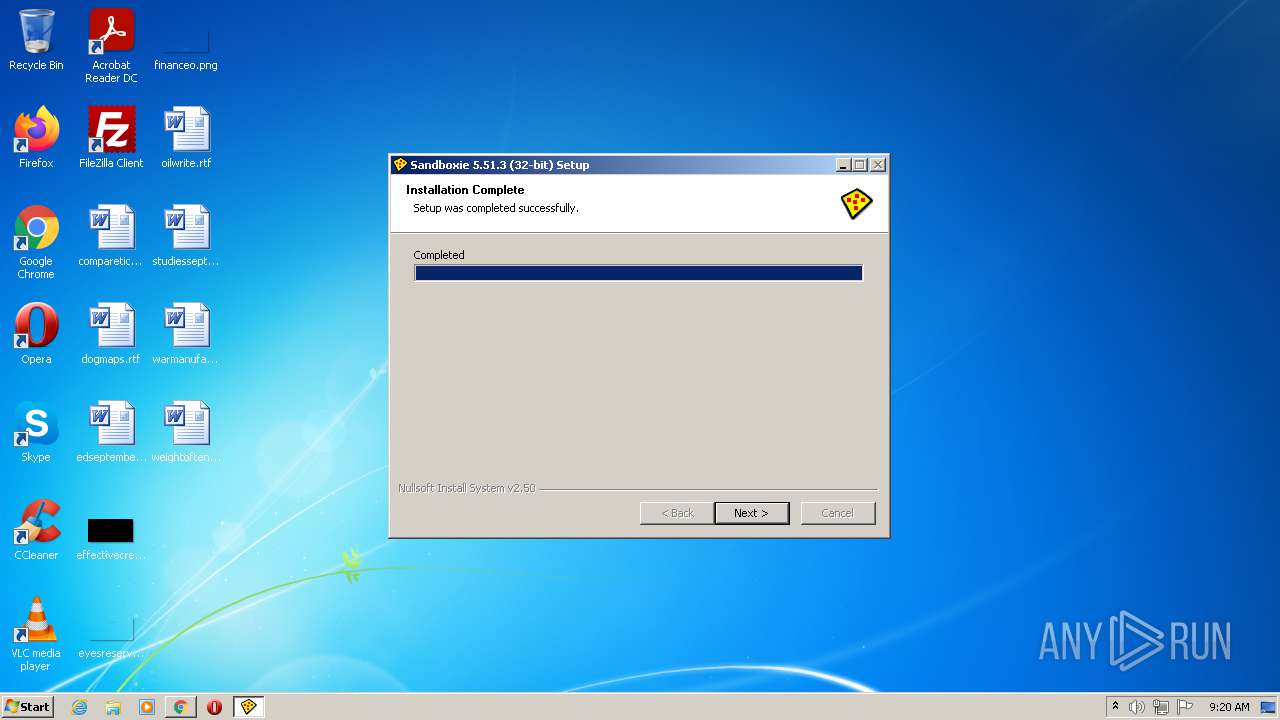
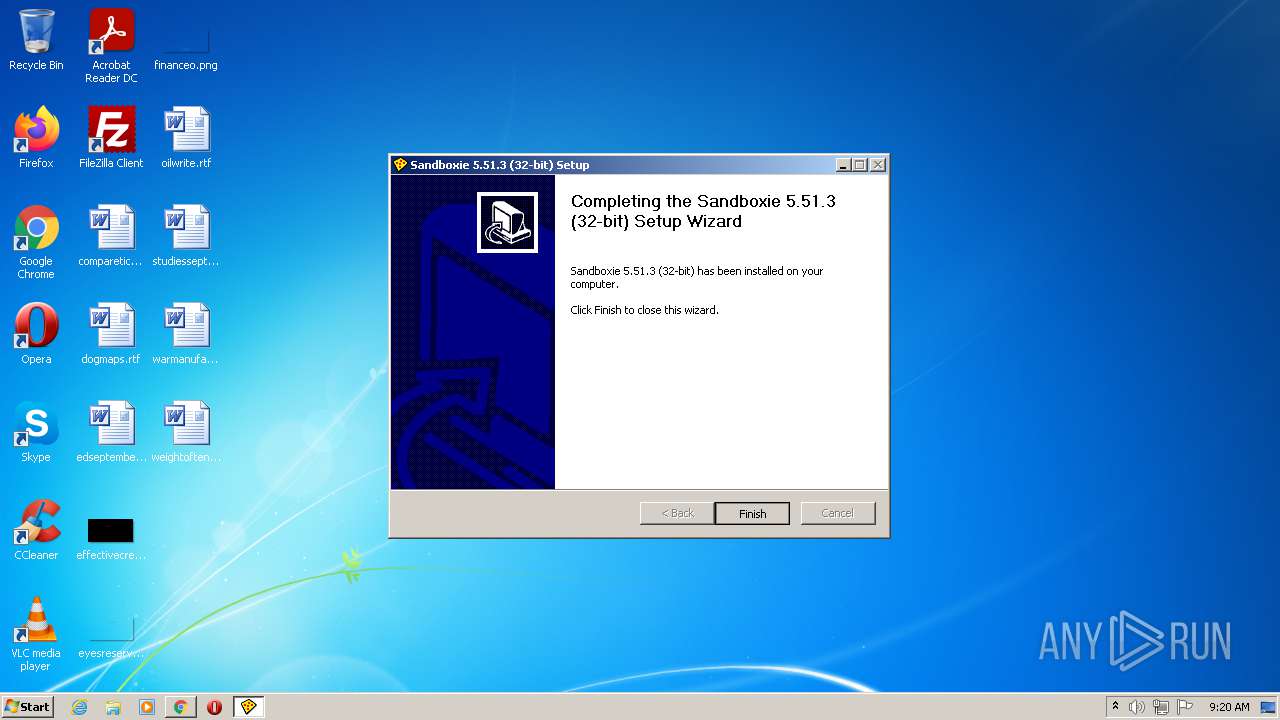
Application was dropped or rewritten from another process
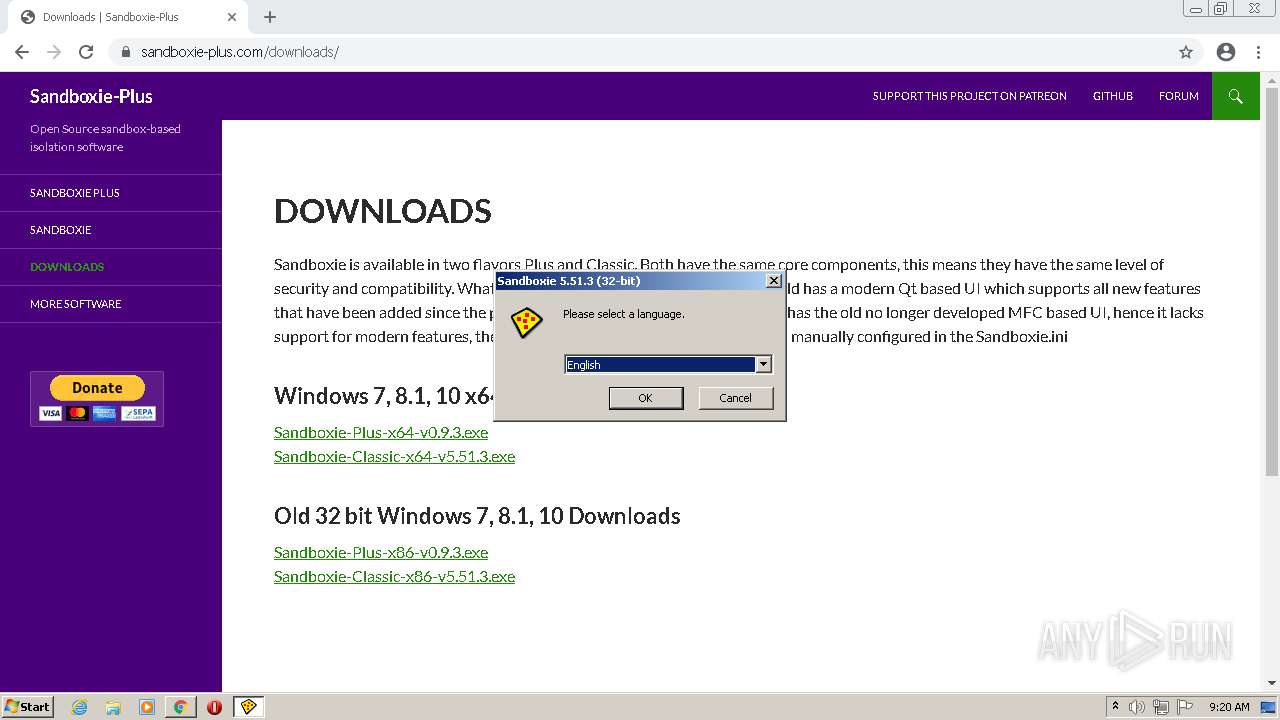
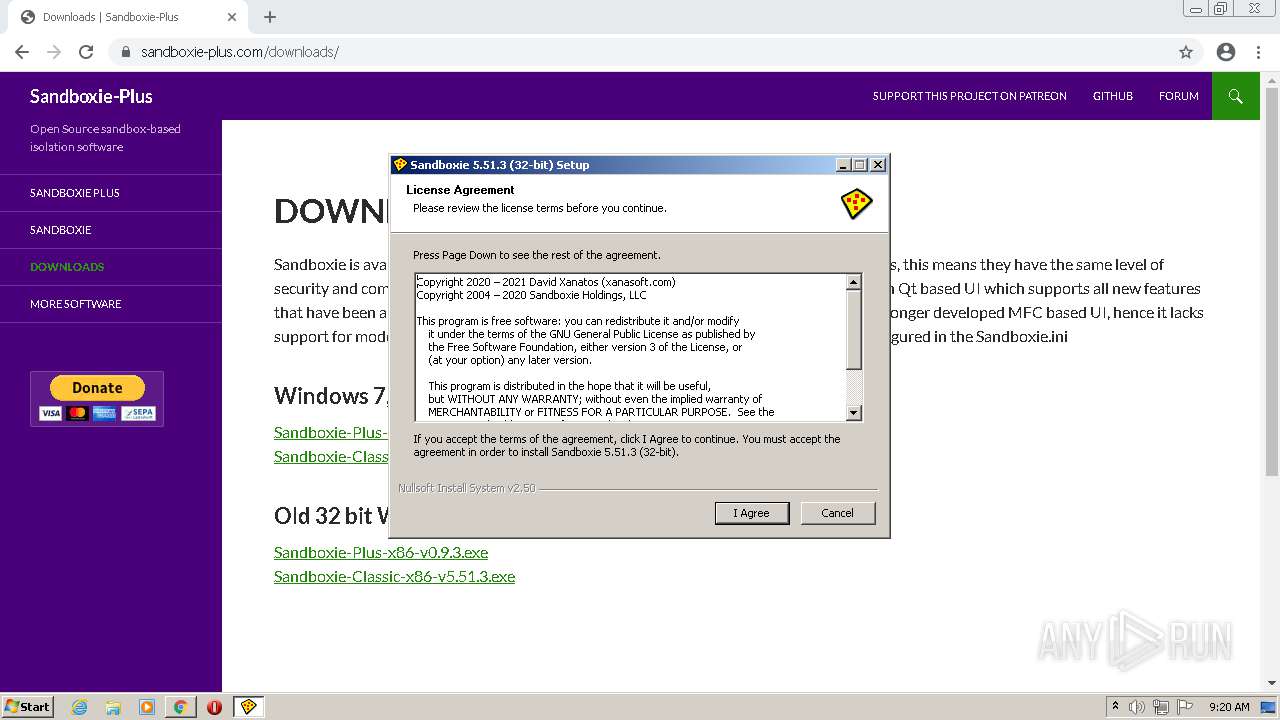
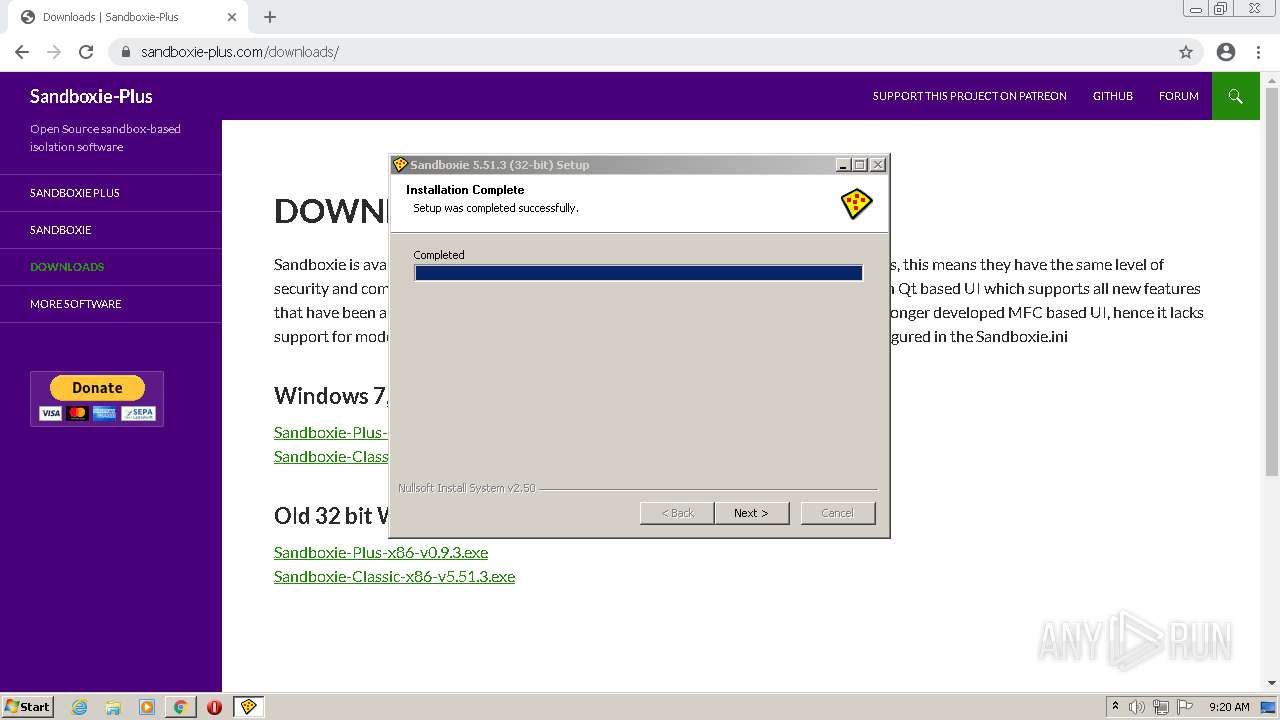
- Sandboxie-Classic-x86-v5.51.3.exe (PID: 2112)
- Sandboxie-Classic-x86-v5.51.3.exe (PID: 2588)
- KmdUtil.exe (PID: 2548)
- KmdUtil.exe (PID: 4060)
- KmdUtil.exe (PID: 2644)
- KmdUtil.exe (PID: 1260)
- KmdUtil.exe (PID: 1684)
- KmdUtil.exe (PID: 3396)
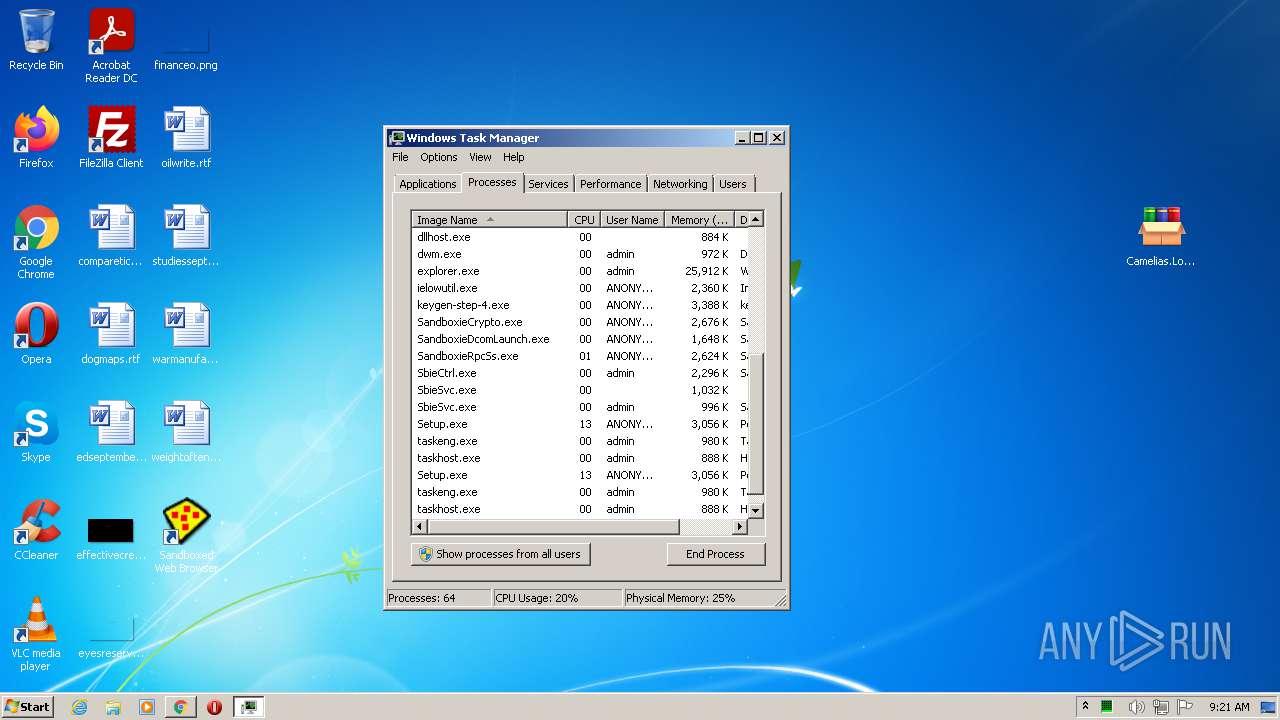
- SbieCtrl.exe (PID: 3252)
- Start.exe (PID: 2840)
- SbieSvc.exe (PID: 1984)
- Start.exe (PID: 3172)
- Start.exe (PID: 2456)
- SbieSvc.exe (PID: 3260)
- SandboxieRpcSs.exe (PID: 2580)
- SandboxieDcomLaunch.exe (PID: 3724)
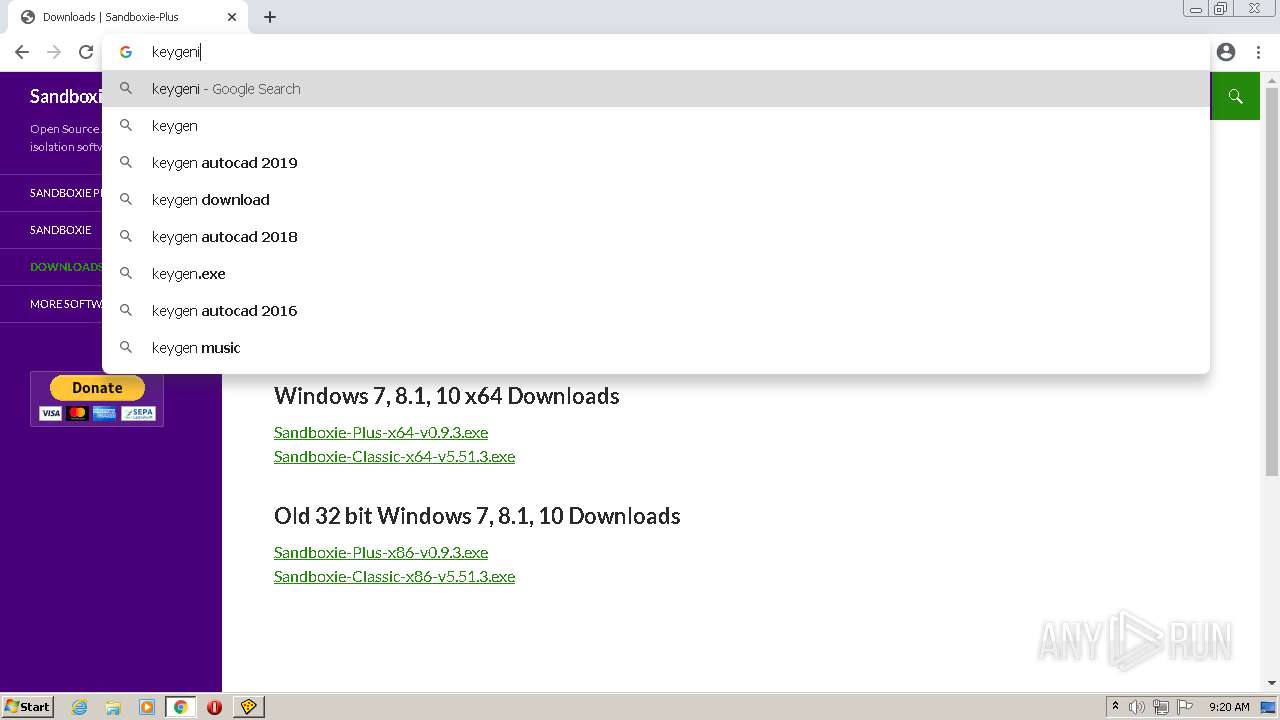
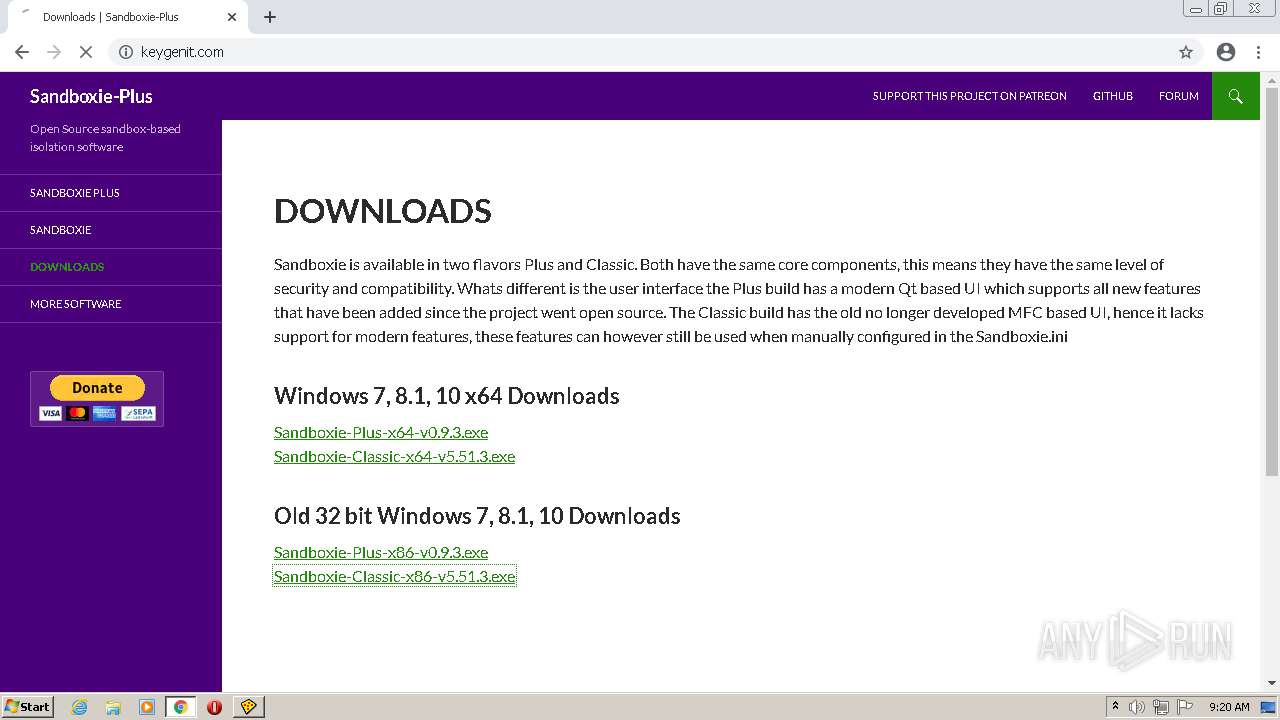
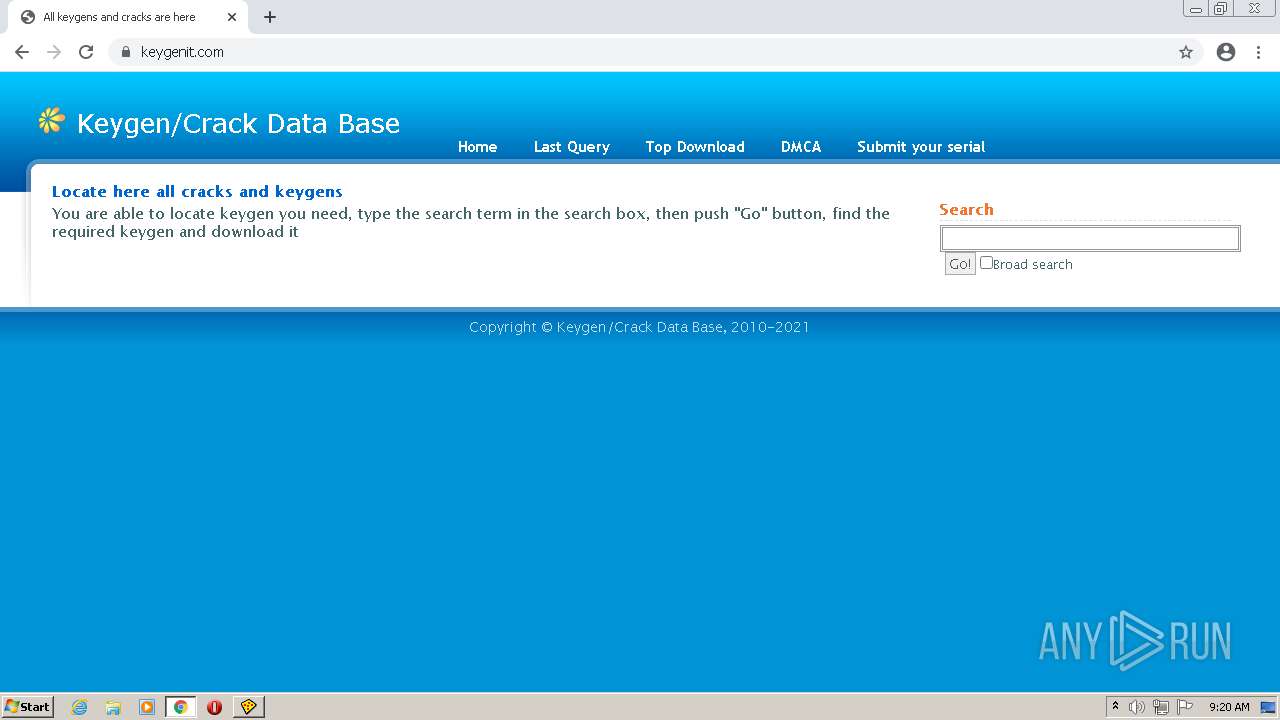
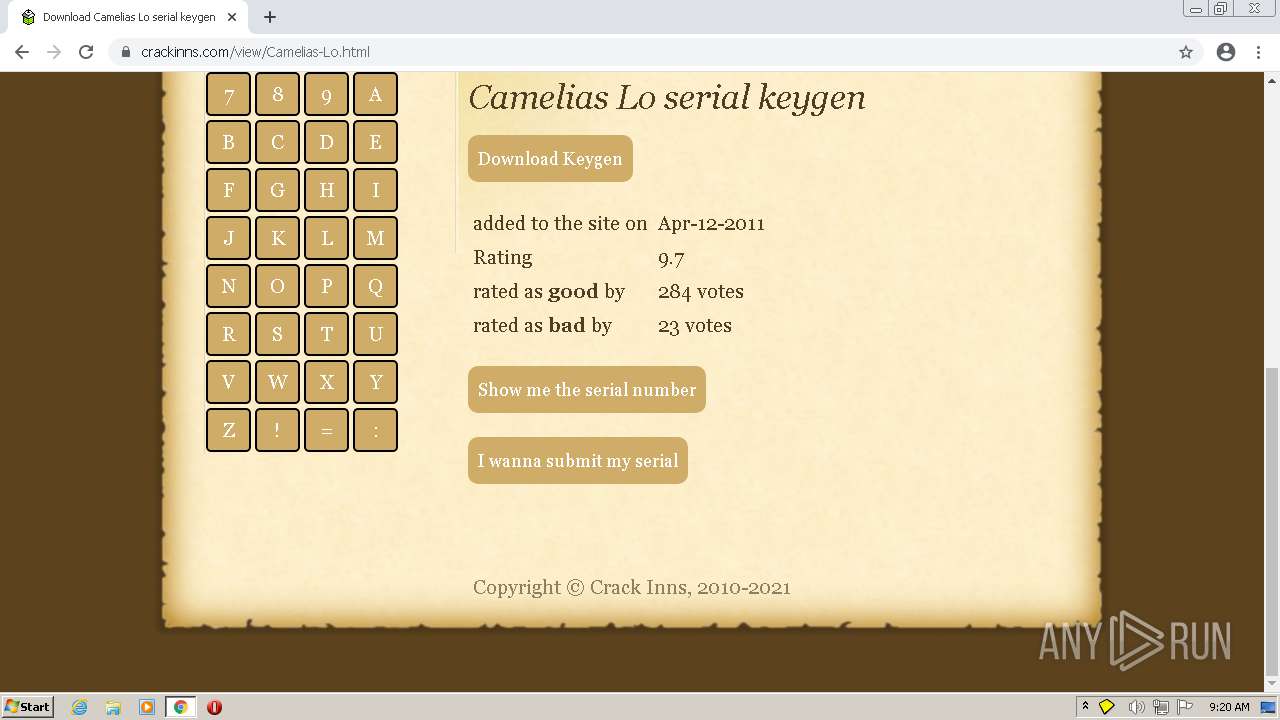
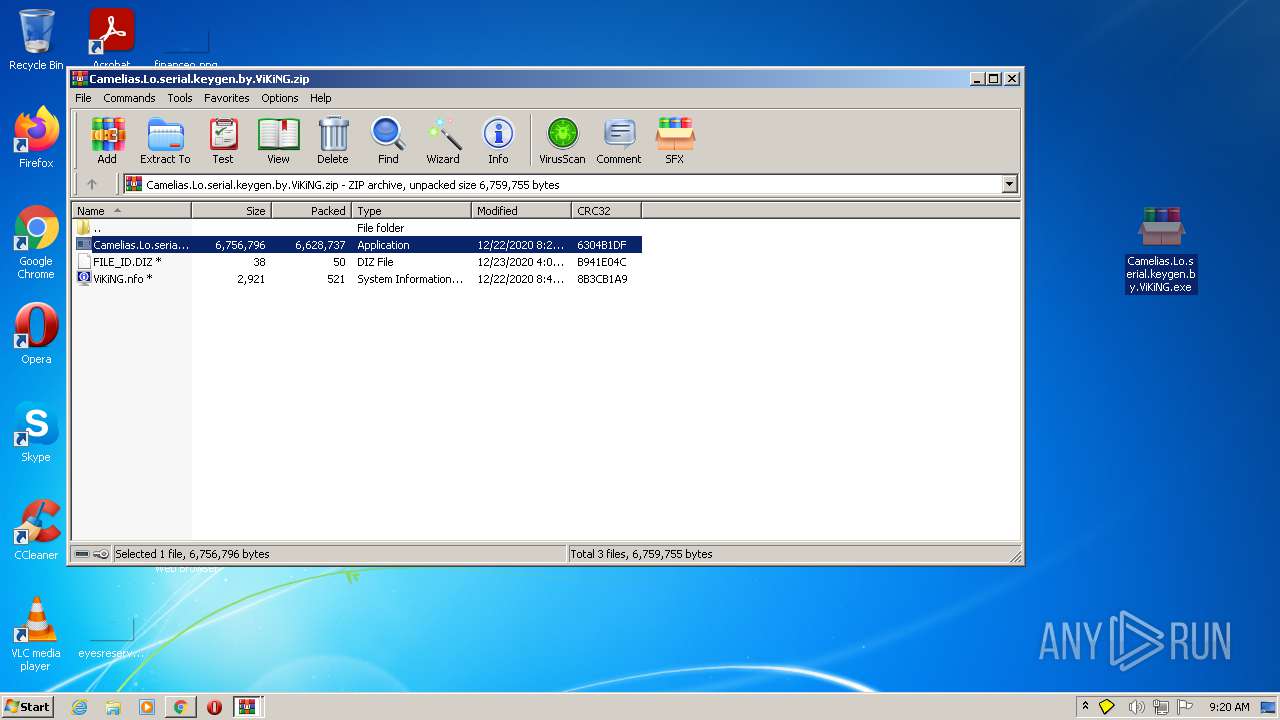
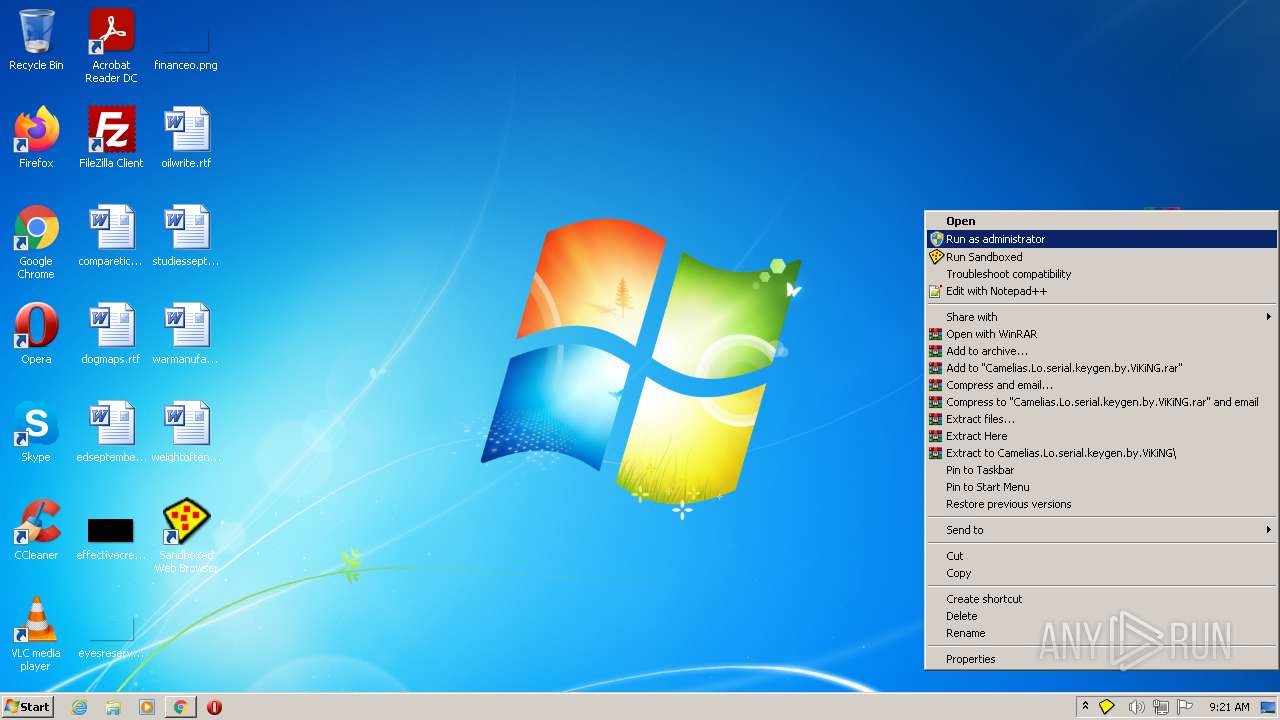
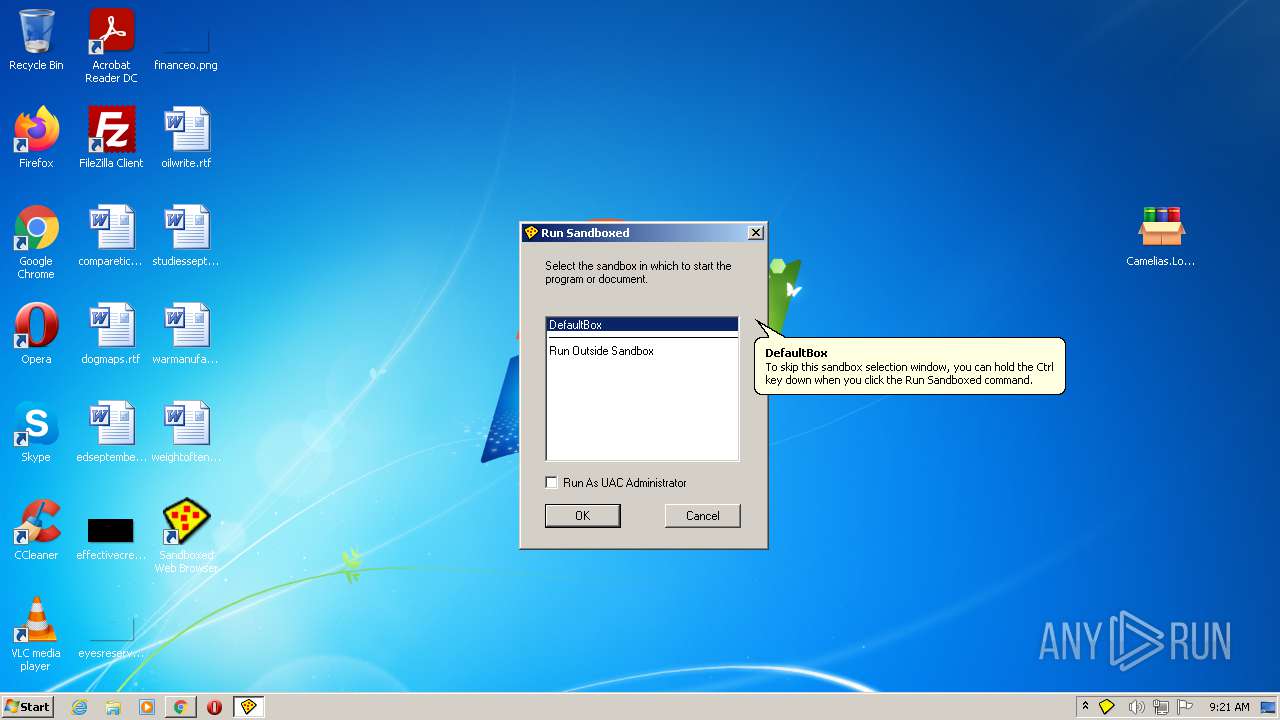
- Camelias.Lo.serial.keygen.by.ViKiNG.exe (PID: 2560)
- SbieSvc.exe (PID: 2392)
- SbieSvc.exe (PID: 3796)
- SbieSvc.exe (PID: 1344)
- SbieSvc.exe (PID: 2292)
- keygen-pr.exe (PID: 2608)
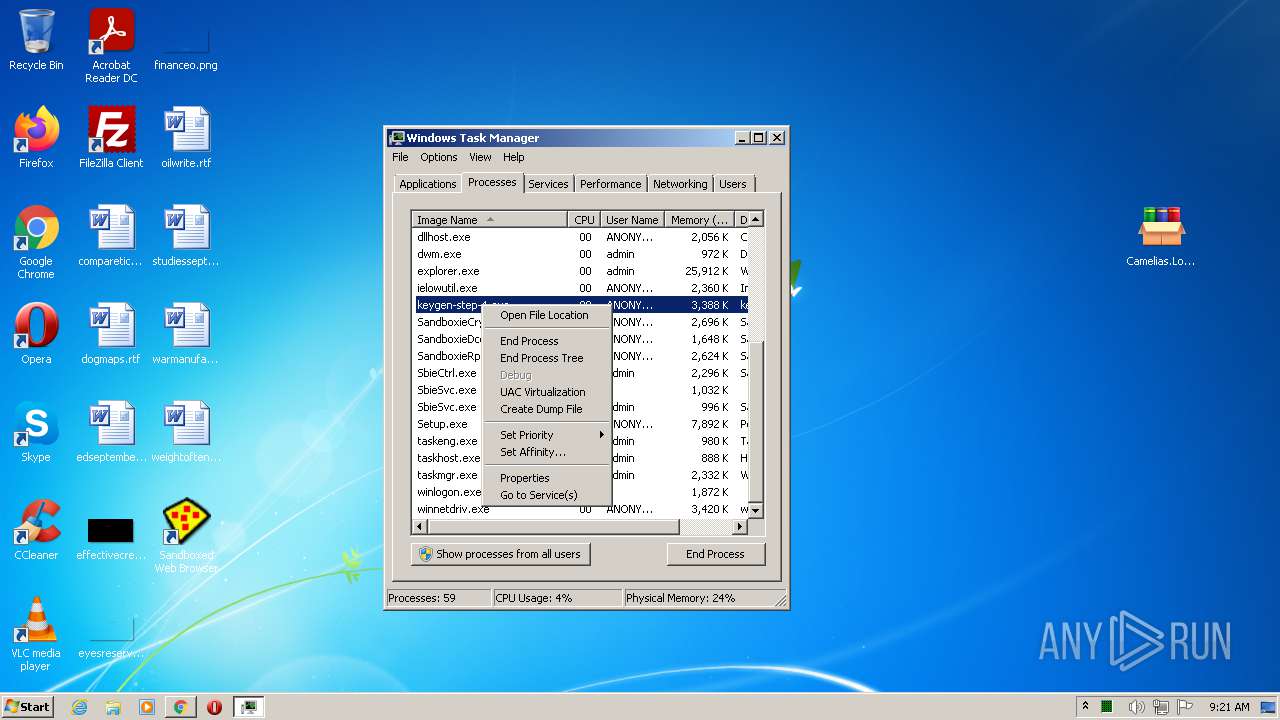
- keygen-step-5.exe (PID: 3628)
- keygen-step-1.exe (PID: 1676)
- keygen-step-6.exe (PID: 2956)
- Start.exe (PID: 2412)
- Start.exe (PID: 2464)
- SandboxieCrypto.exe (PID: 2420)
- SbieSvc.exe (PID: 4088)
- keygen-step-4.exe (PID: 2228)
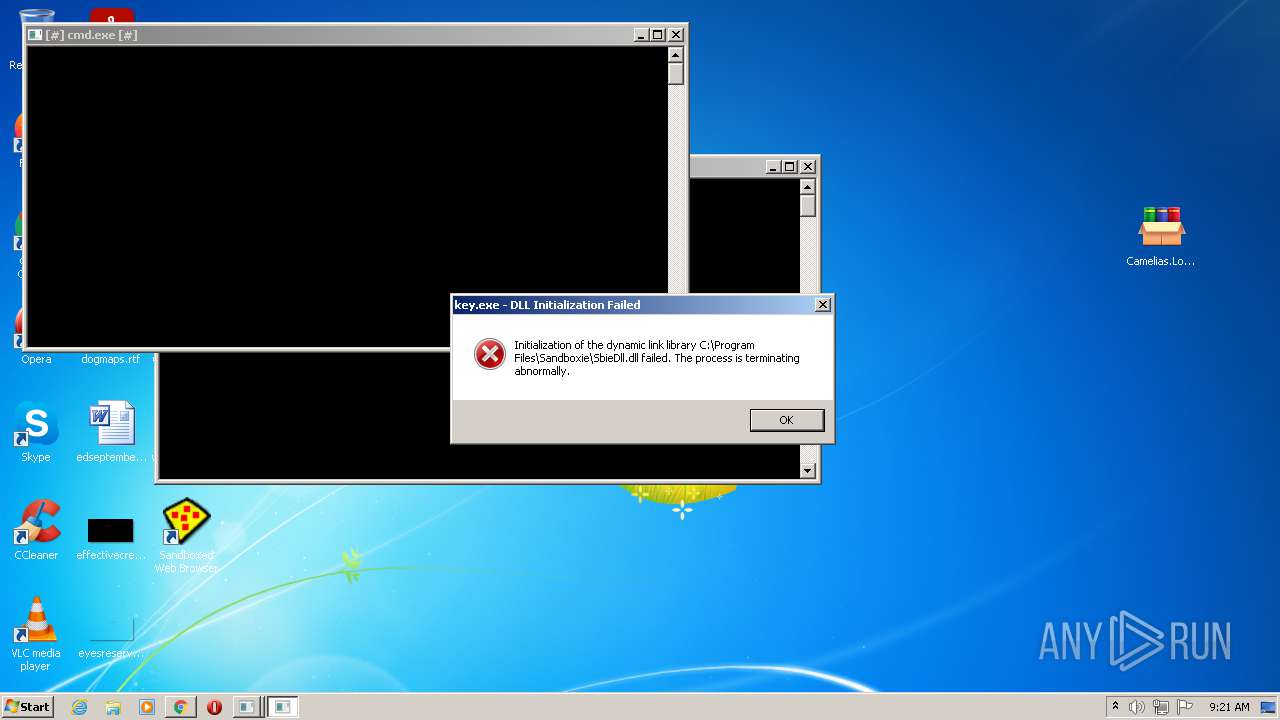
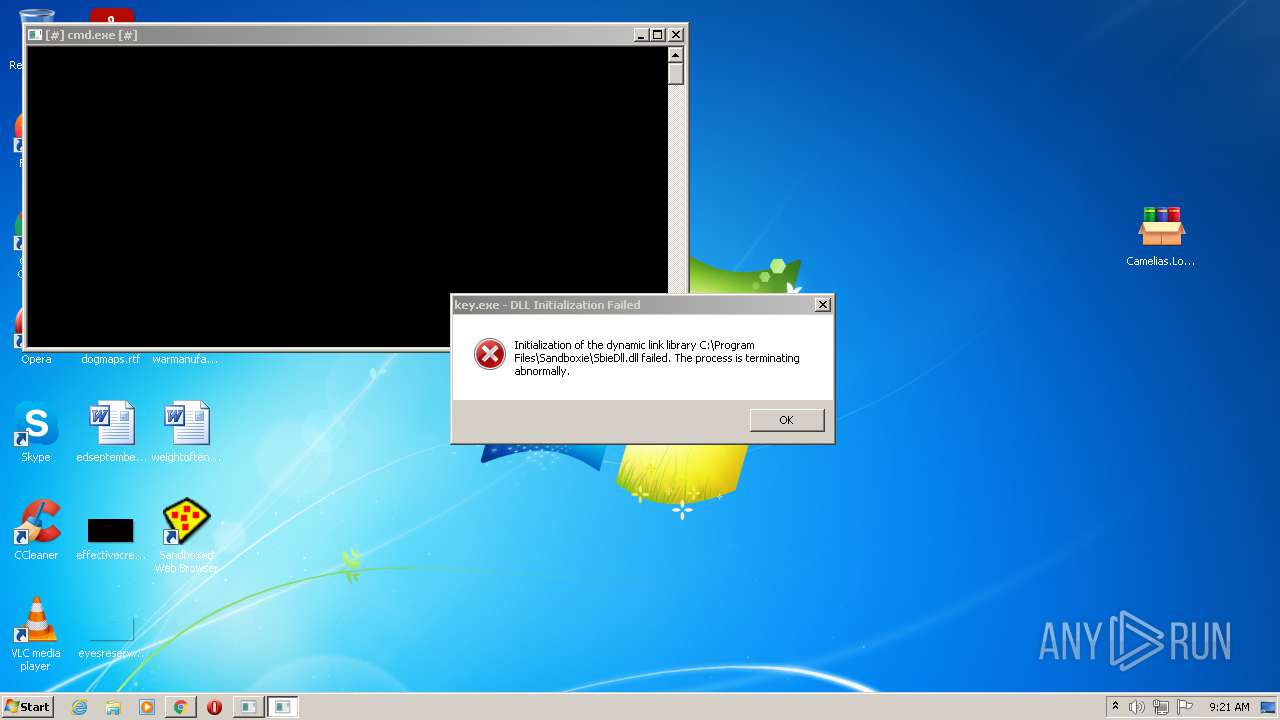
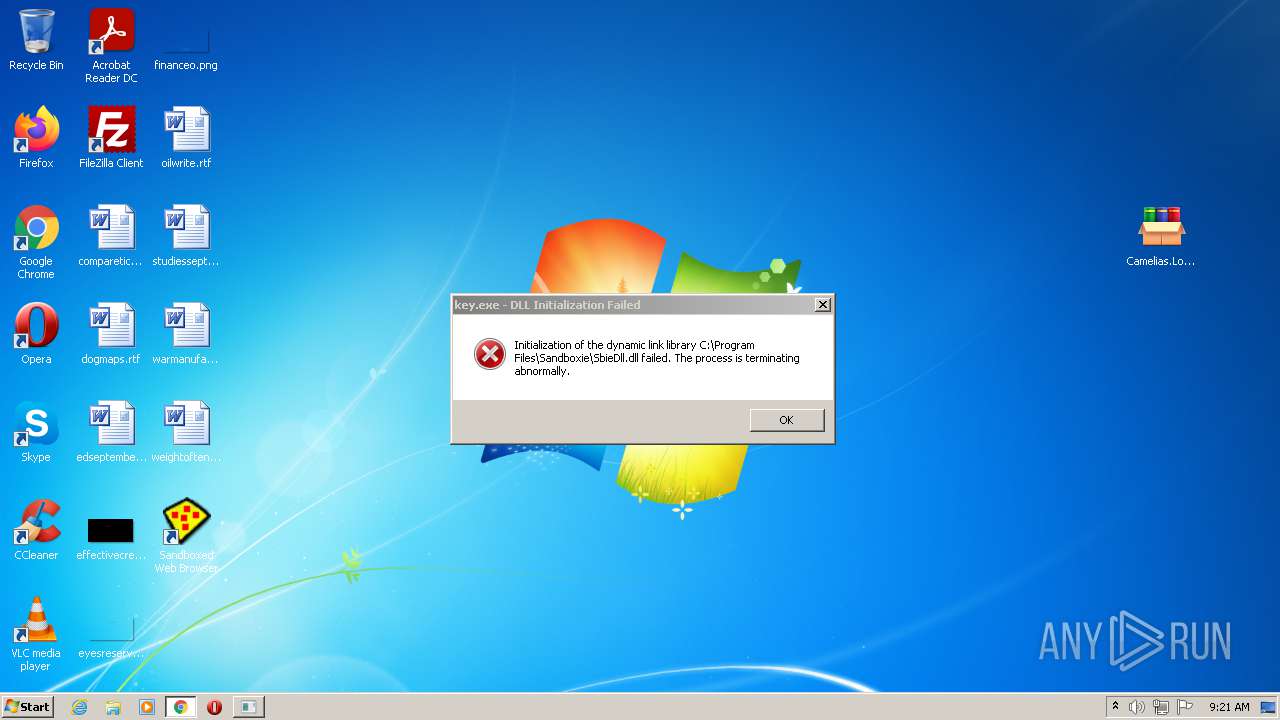
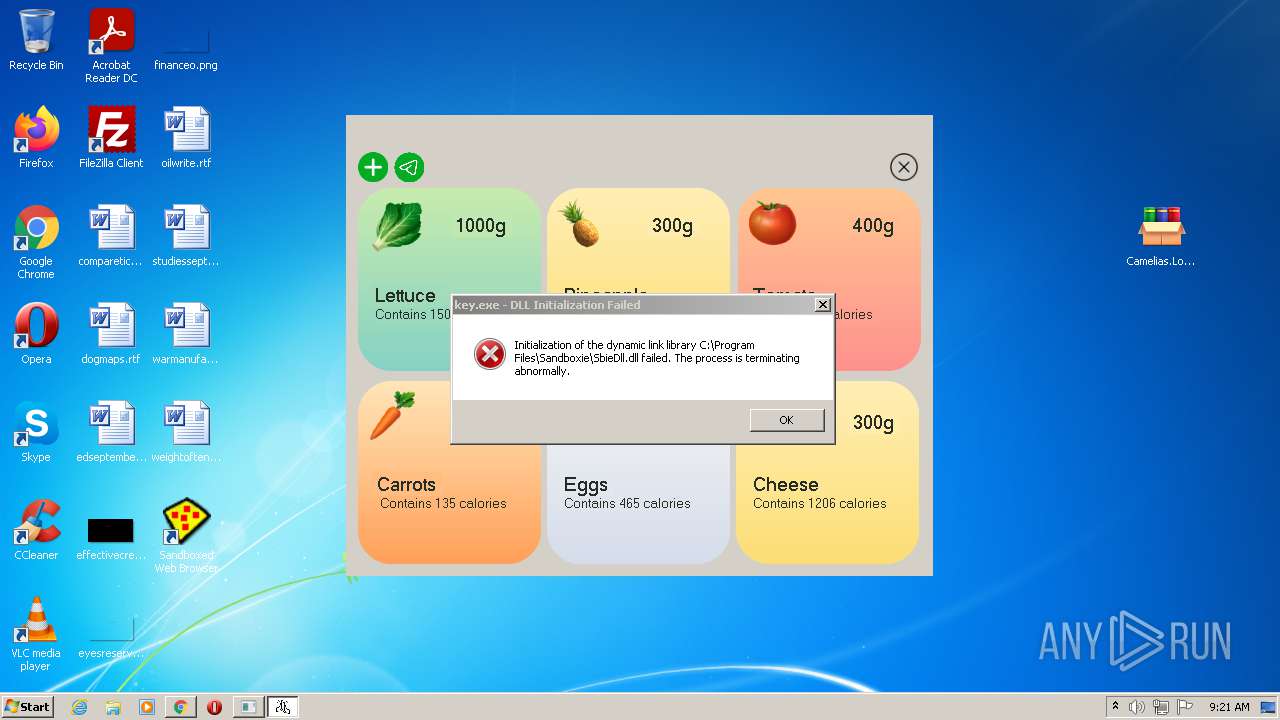
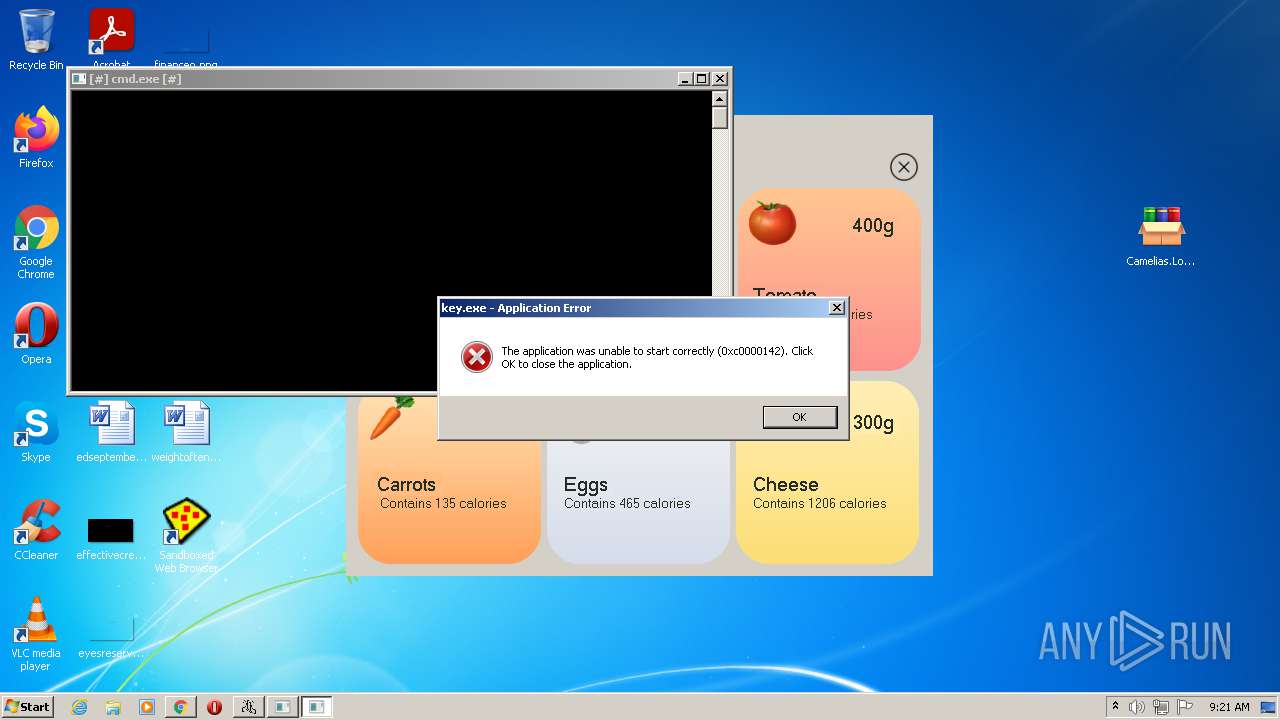
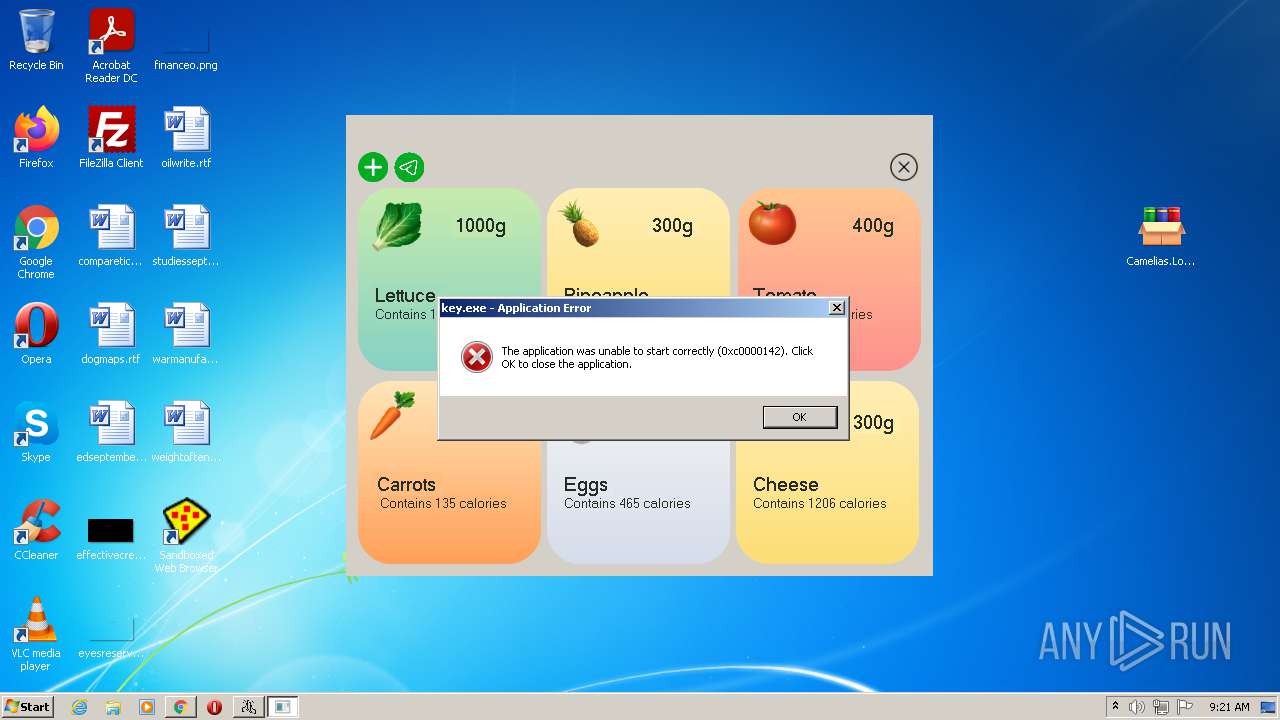
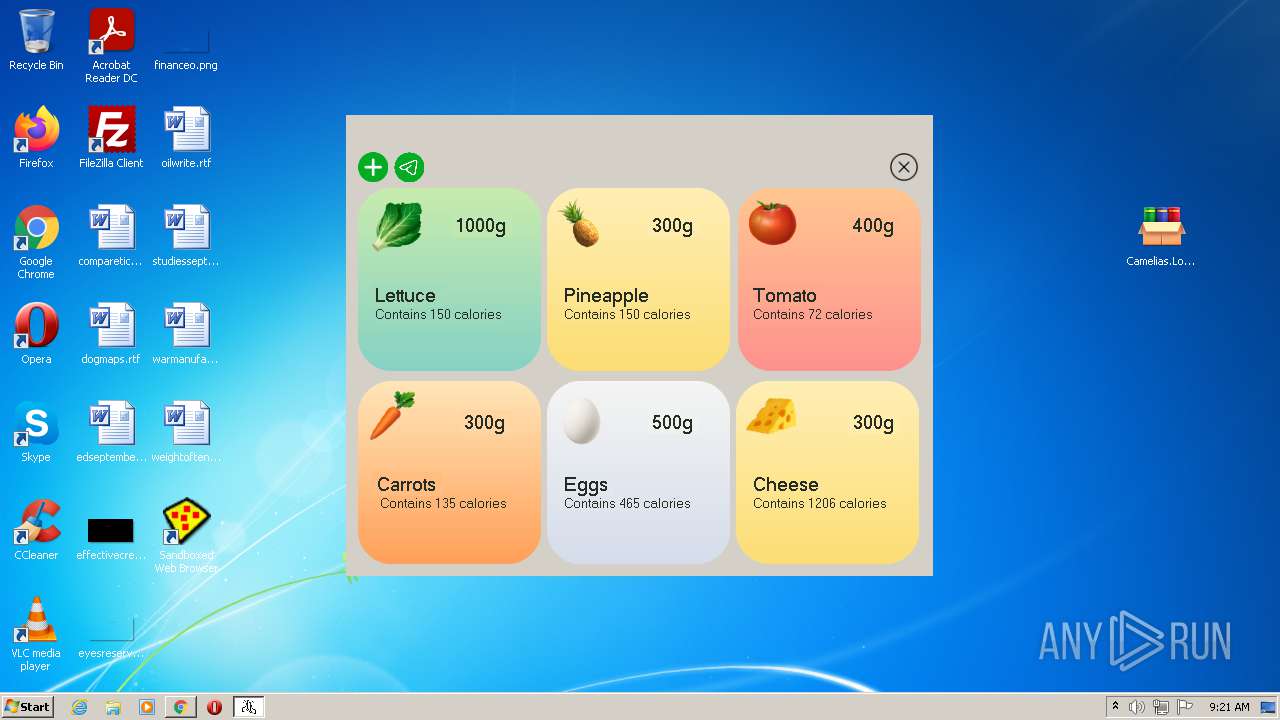
- key.exe (PID: 3044)
- FvD9kOs1J.ExE (PID: 1552)
- key.exe (PID: 2428)
- SbieSvc.exe (PID: 2392)
- SbieSvc.exe (PID: 2552)
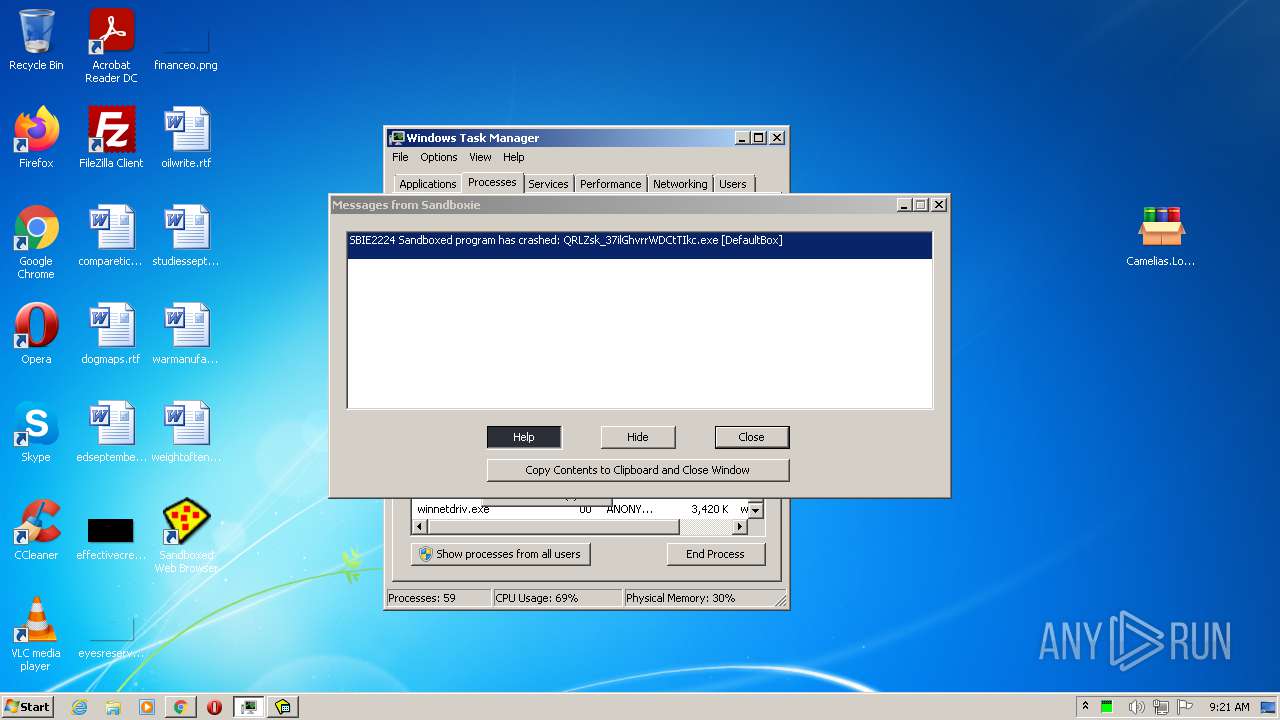
- winnetdriv.exe (PID: 2416)
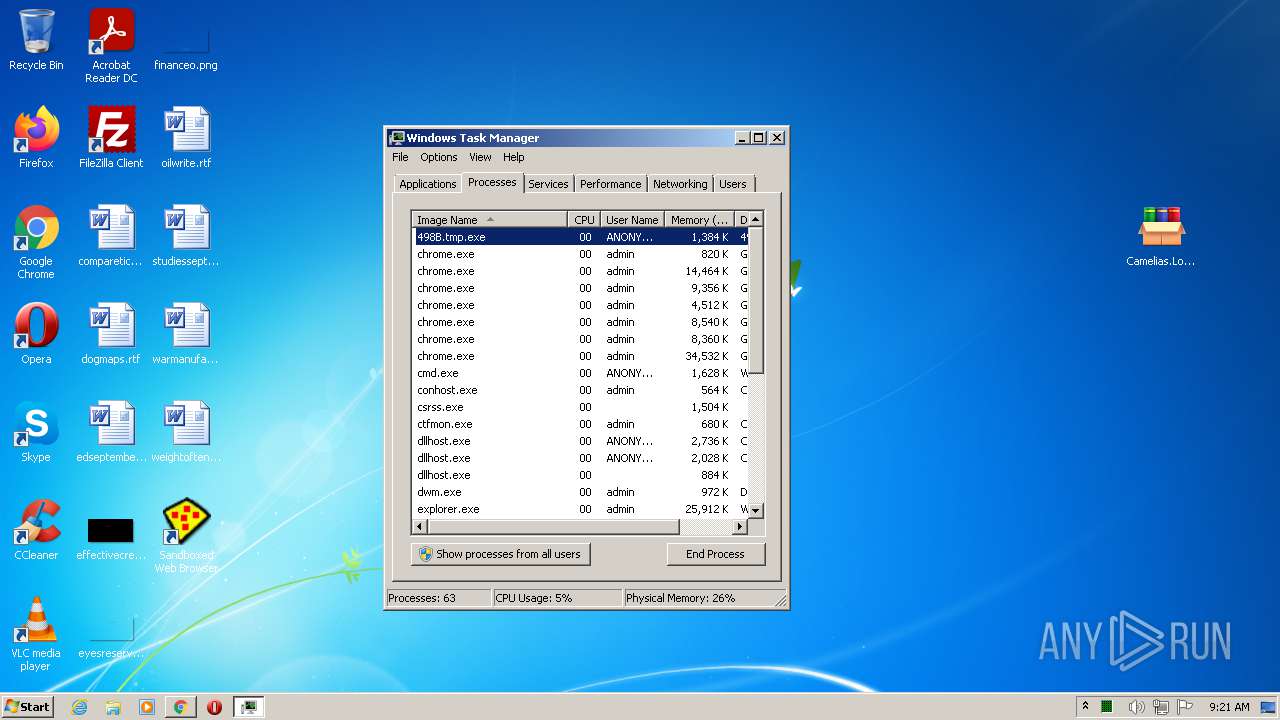
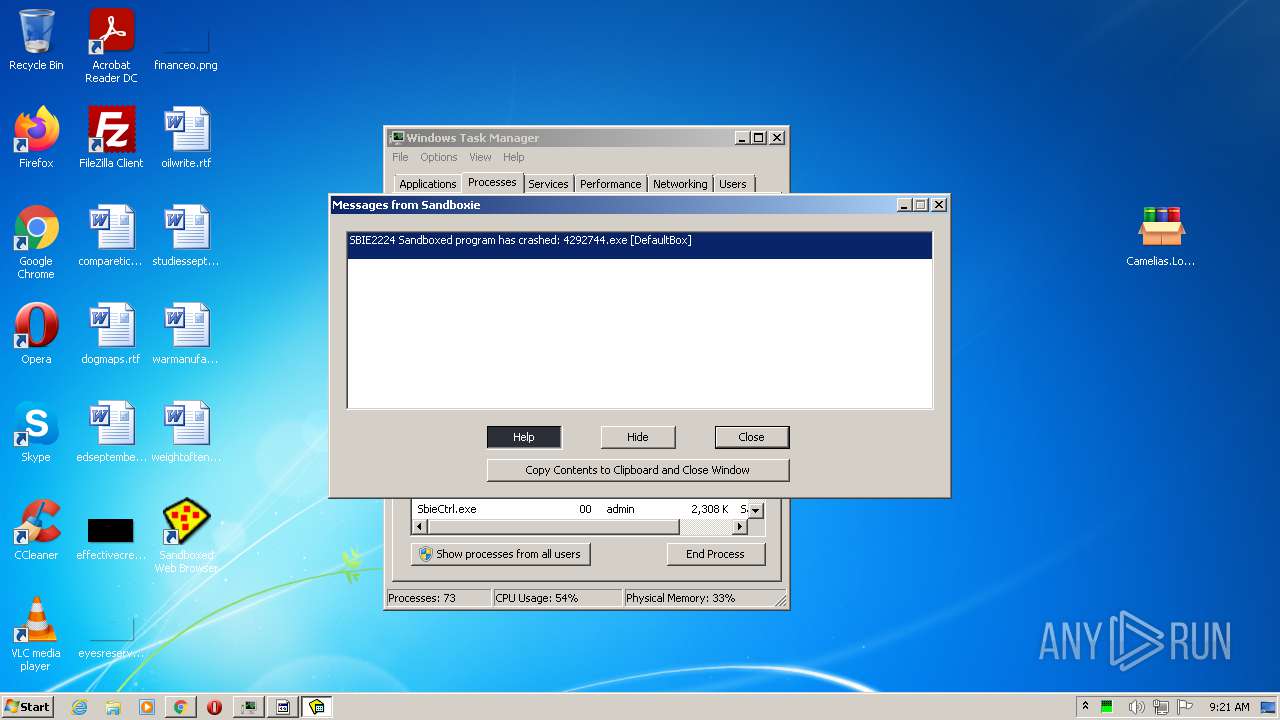
- 4285.tmp.exe (PID: 3088)
- SbieSvc.exe (PID: 3812)
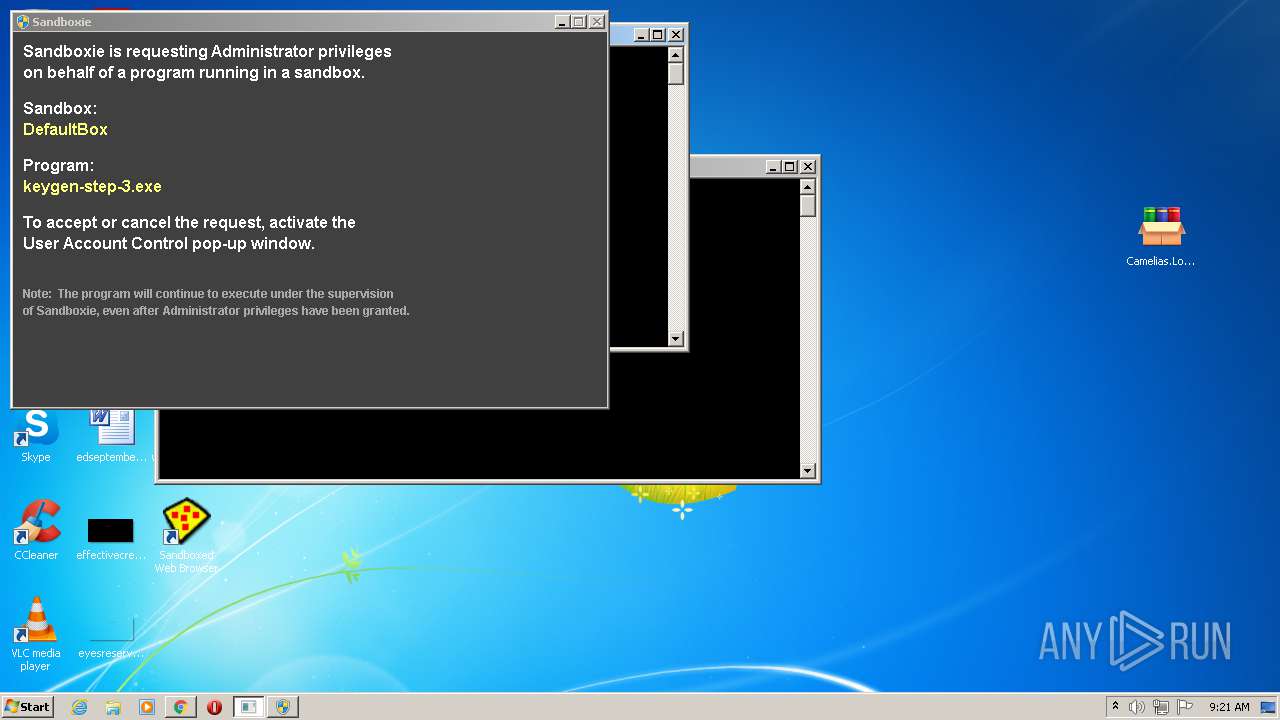
- keygen-step-3.exe (PID: 2936)
- 498B.tmp.exe (PID: 3276)
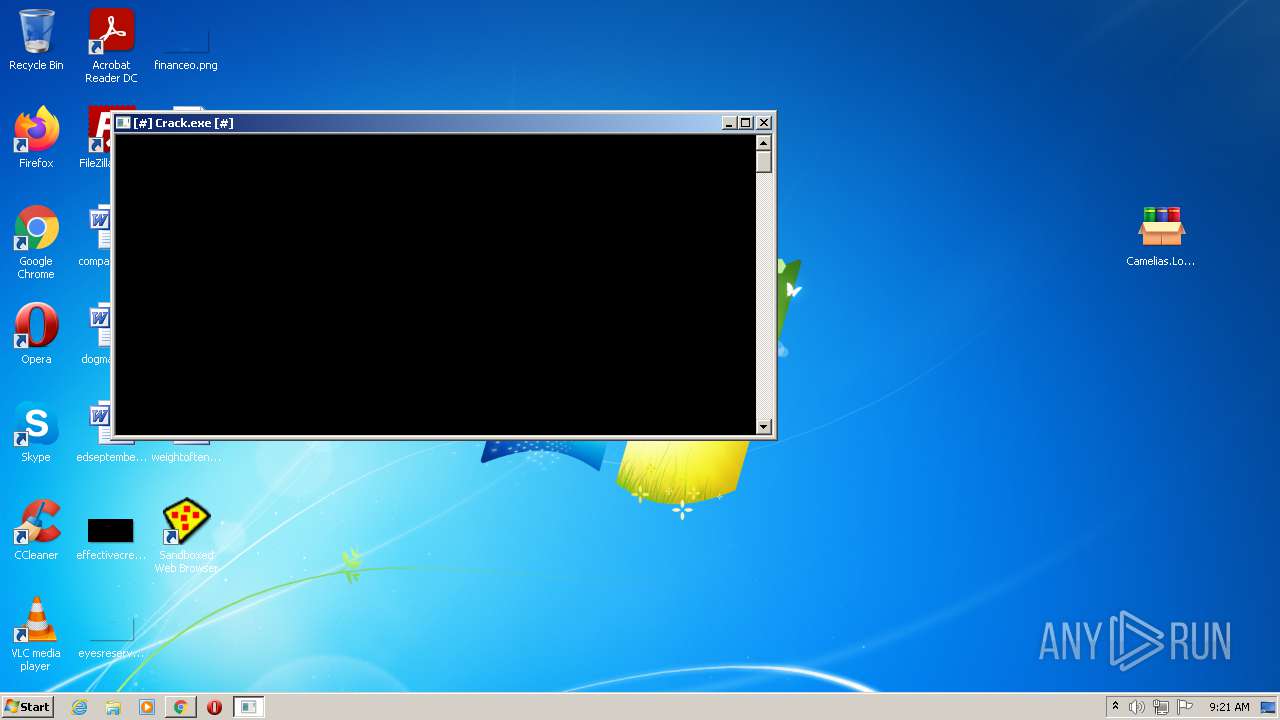
- Crack.exe (PID: 3716)
- KiffApp2.exe (PID: 2932)
- SbieSvc.exe (PID: 1780)
Drops executable file immediately after starts
- Sandboxie-Classic-x86-v5.51.3.exe (PID: 2588)
- keygen-step-4.exe (PID: 2228)
Loads dropped or rewritten executable
- Sandboxie-Classic-x86-v5.51.3.exe (PID: 2588)
- KmdUtil.exe (PID: 2548)
- KmdUtil.exe (PID: 4060)
- KmdUtil.exe (PID: 2644)
- KmdUtil.exe (PID: 1260)
- KmdUtil.exe (PID: 3396)
- KmdUtil.exe (PID: 1684)
- SbieSvc.exe (PID: 1984)
- SbieCtrl.exe (PID: 3252)
- Start.exe (PID: 2840)
- Start.exe (PID: 3172)
- SbieSvc.exe (PID: 3260)
- SandboxieRpcSs.exe (PID: 2580)
- Start.exe (PID: 2456)
- SandboxieDcomLaunch.exe (PID: 3724)
- Camelias.Lo.serial.keygen.by.ViKiNG.exe (PID: 2560)
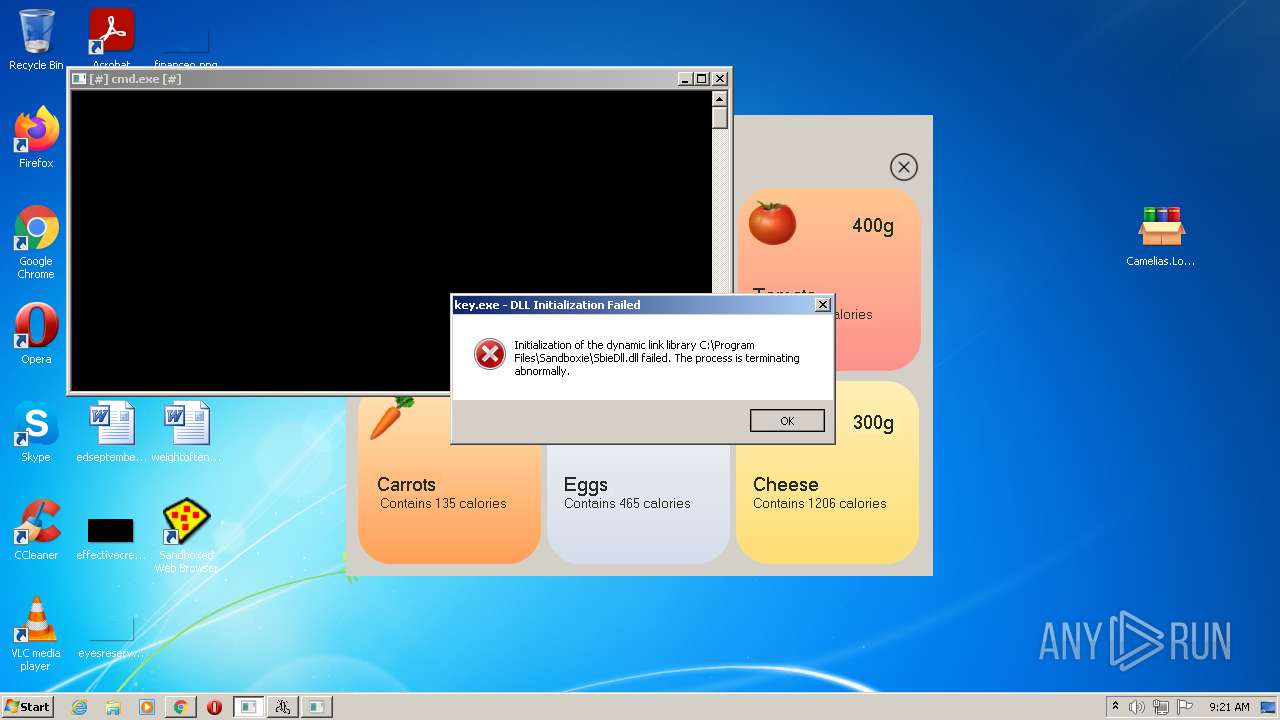
- cmd.exe (PID: 948)
- SbieSvc.exe (PID: 2392)
- keygen-step-1.exe (PID: 1676)
- keygen-pr.exe (PID: 2608)
- keygen-step-5.exe (PID: 3628)
- keygen-step-6.exe (PID: 2956)
- dllhost.exe (PID: 1200)
- SbieSvc.exe (PID: 3796)
- SbieSvc.exe (PID: 1344)
- dllhost.exe (PID: 3820)
- SbieSvc.exe (PID: 2292)
- cmd.exe (PID: 2160)
- key.exe (PID: 3044)
- Start.exe (PID: 2464)
- Start.exe (PID: 2412)
- SandboxieCrypto.exe (PID: 2420)
- key.exe (PID: 2428)
- SbieSvc.exe (PID: 4088)
- keygen-step-3.exe (PID: 2936)
- keygen-step-4.exe (PID: 2228)
- KiffApp2.exe (PID: 2932)
- taskkill.exe (PID: 2052)
- FvD9kOs1J.ExE (PID: 1552)
- cmd.exe (PID: 1476)
- SbieSvc.exe (PID: 2392)
- SbieSvc.exe (PID: 2552)
- cmd.exe (PID: 1792)
- winnetdriv.exe (PID: 2416)
- cmd.exe (PID: 3696)
- cmd.exe (PID: 2908)
- 498B.tmp.exe (PID: 3276)
- cmd.exe (PID: 2876)
- SbieSvc.exe (PID: 3812)
- PING.EXE (PID: 2452)
- rundll32.exe (PID: 2648)
- Crack.exe (PID: 3716)
- 4285.tmp.exe (PID: 3088)
Changes the autorun value in the registry
- SbieCtrl.exe (PID: 3252)
Stealing of credential data
- keygen-step-3.exe (PID: 2936)
- SbieSvc.exe (PID: 1984)
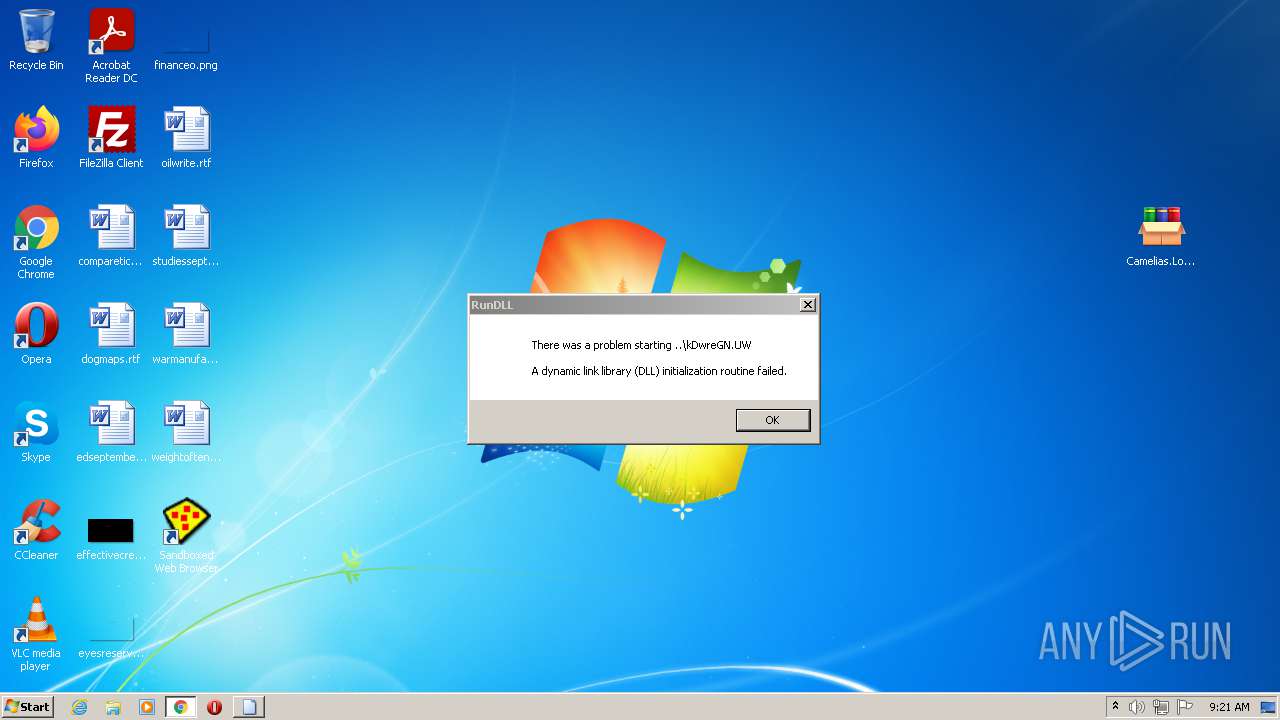
Changes settings of System certificates
- keygen-step-6.exe (PID: 2956)
Connects to CnC server
- keygen-step-1.exe (PID: 1676)
- key.exe (PID: 3044)
- keygen-step-3.exe (PID: 2936)
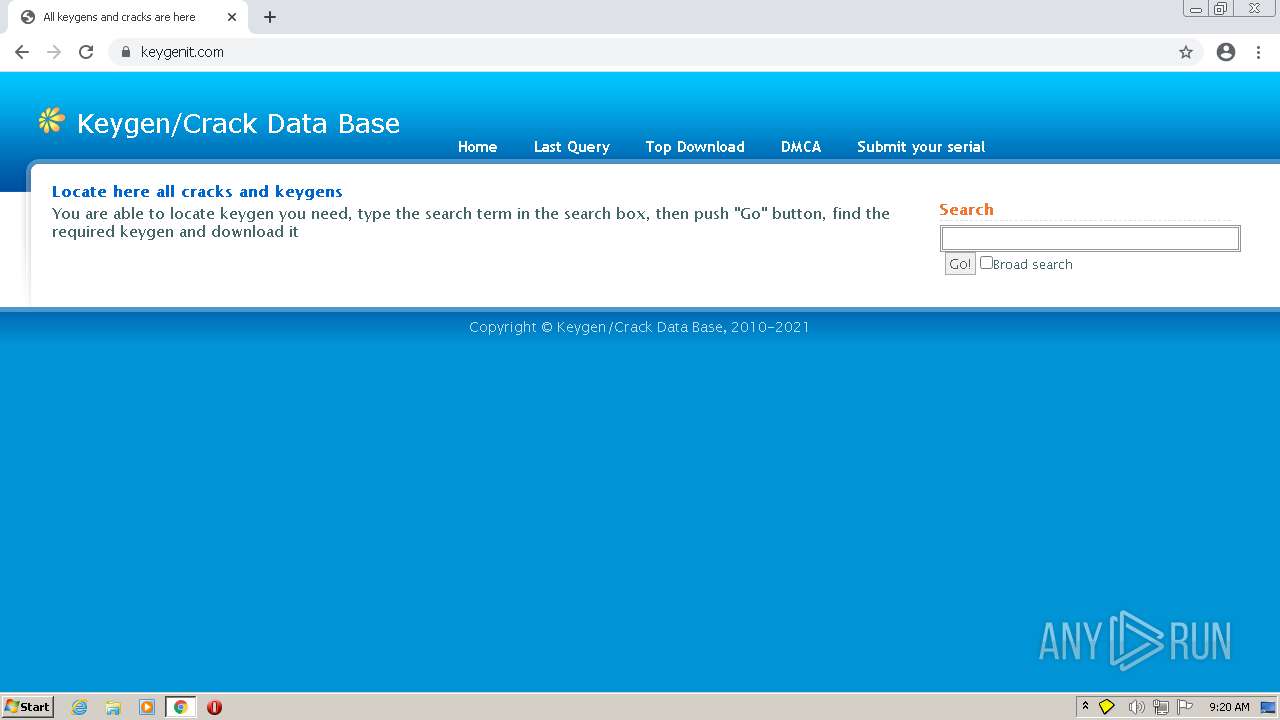
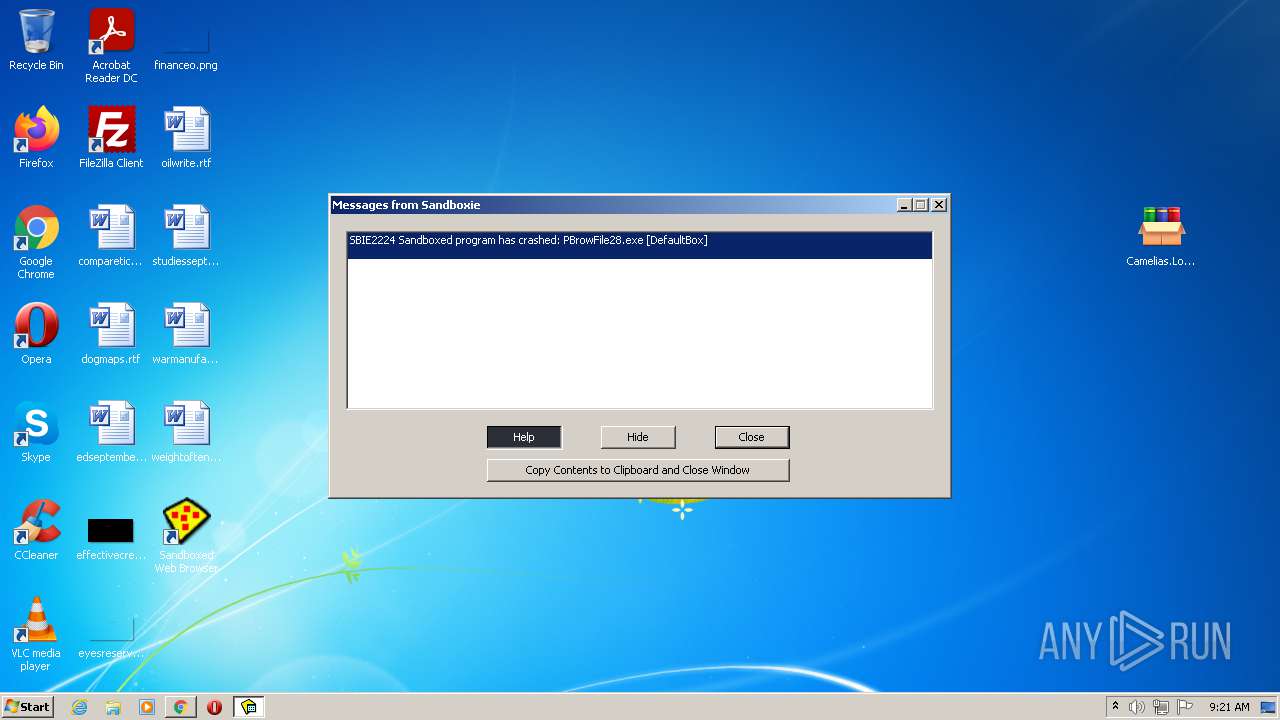
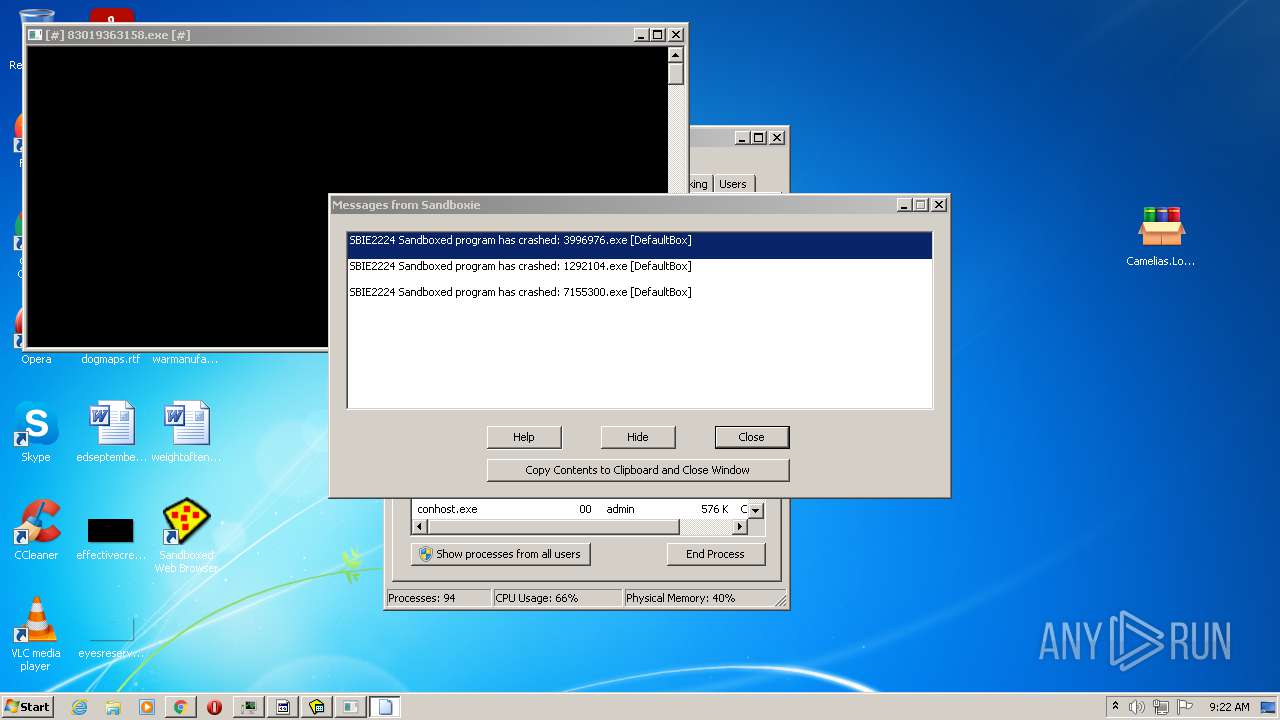
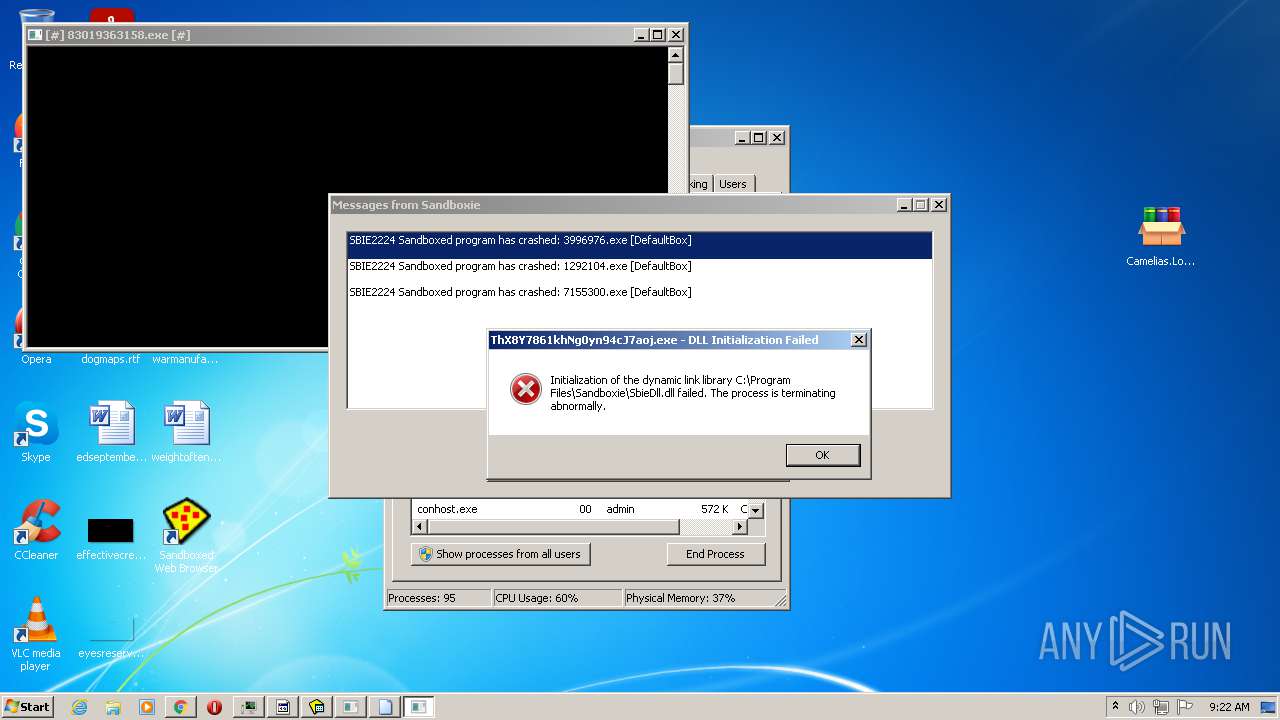
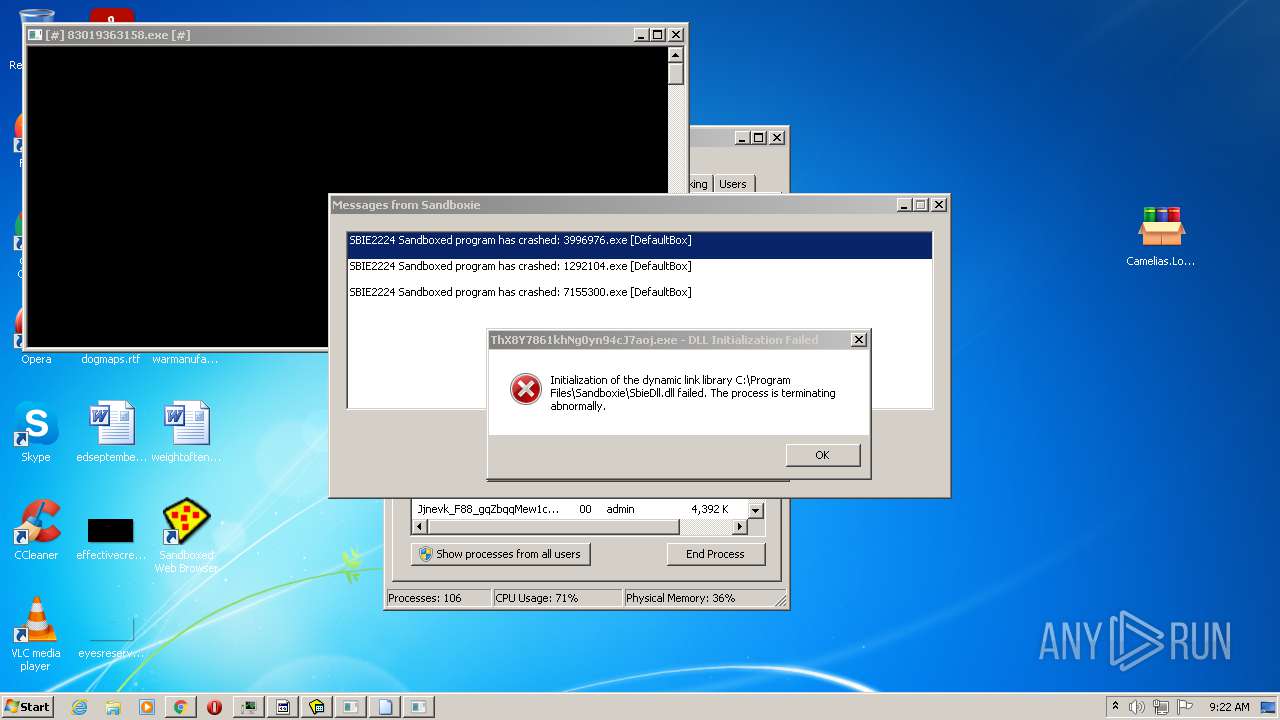
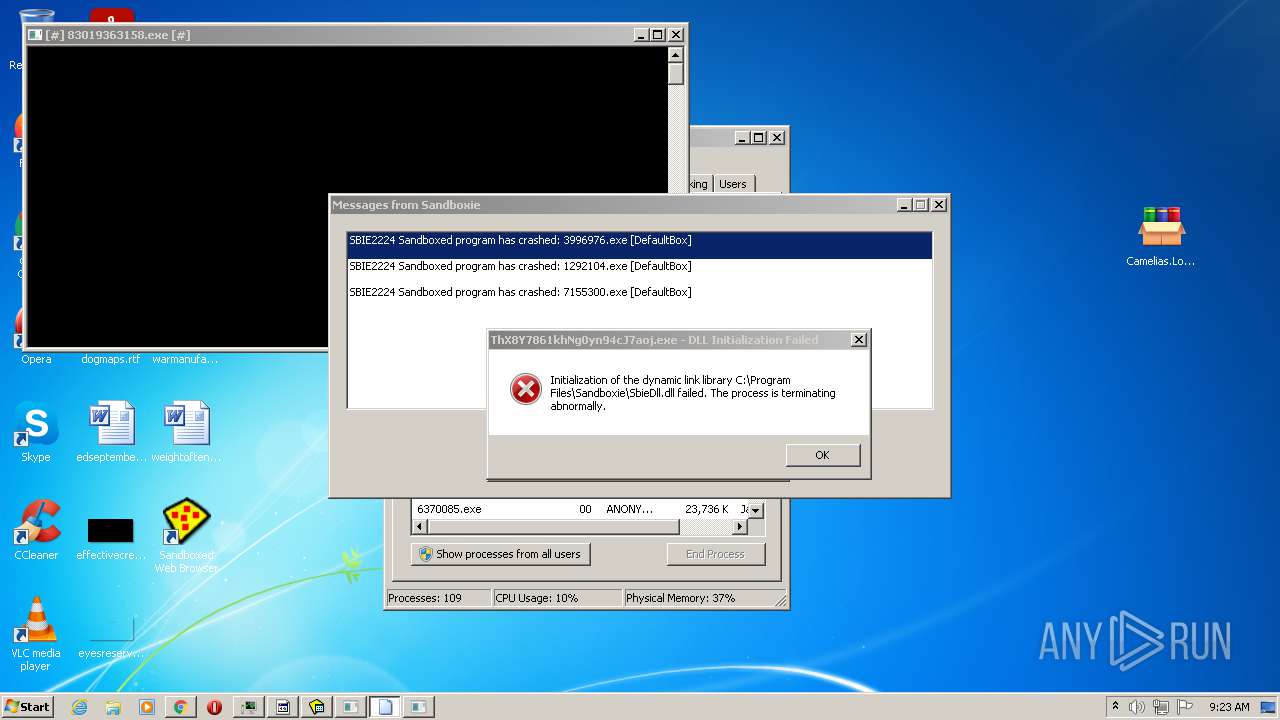
AZORULT was detected
- keygen-step-1.exe (PID: 1676)
Writes to a start menu file
- 498B.tmp.exe (PID: 3276)
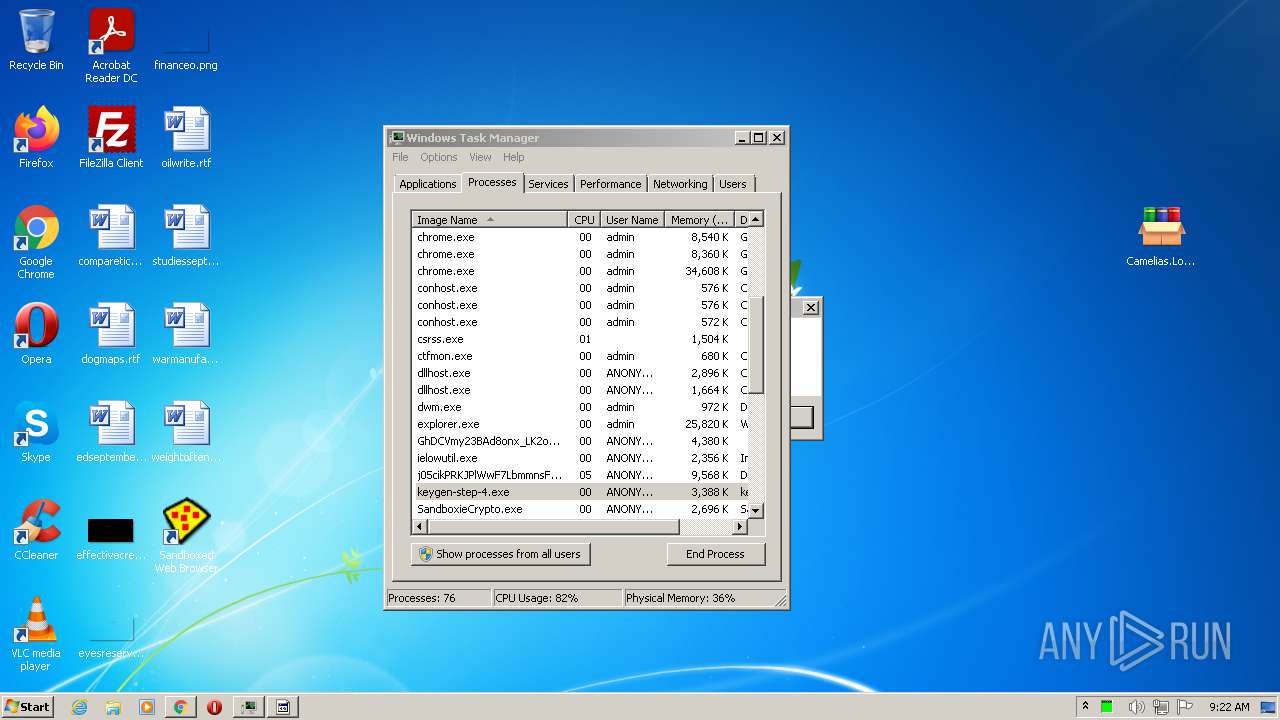
Steals credentials from Web Browsers
- key.exe (PID: 3044)
Actions looks like stealing of personal data
- key.exe (PID: 3044)
SUSPICIOUS
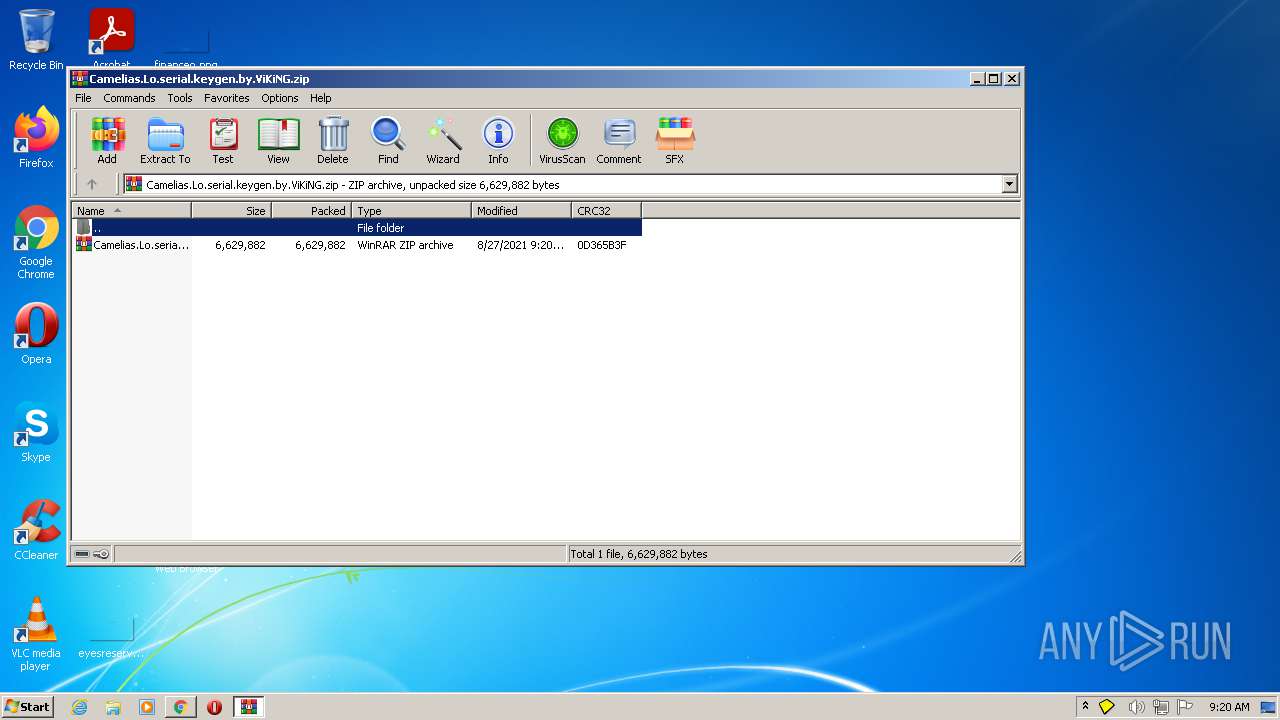
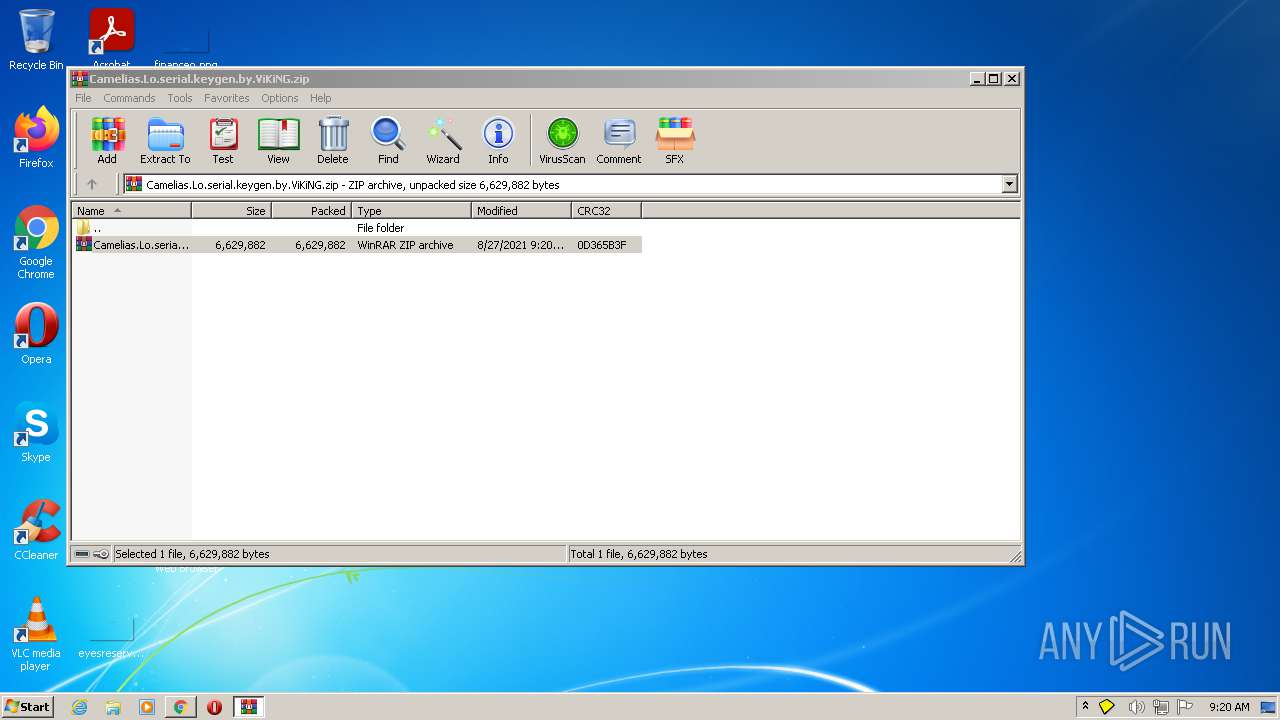
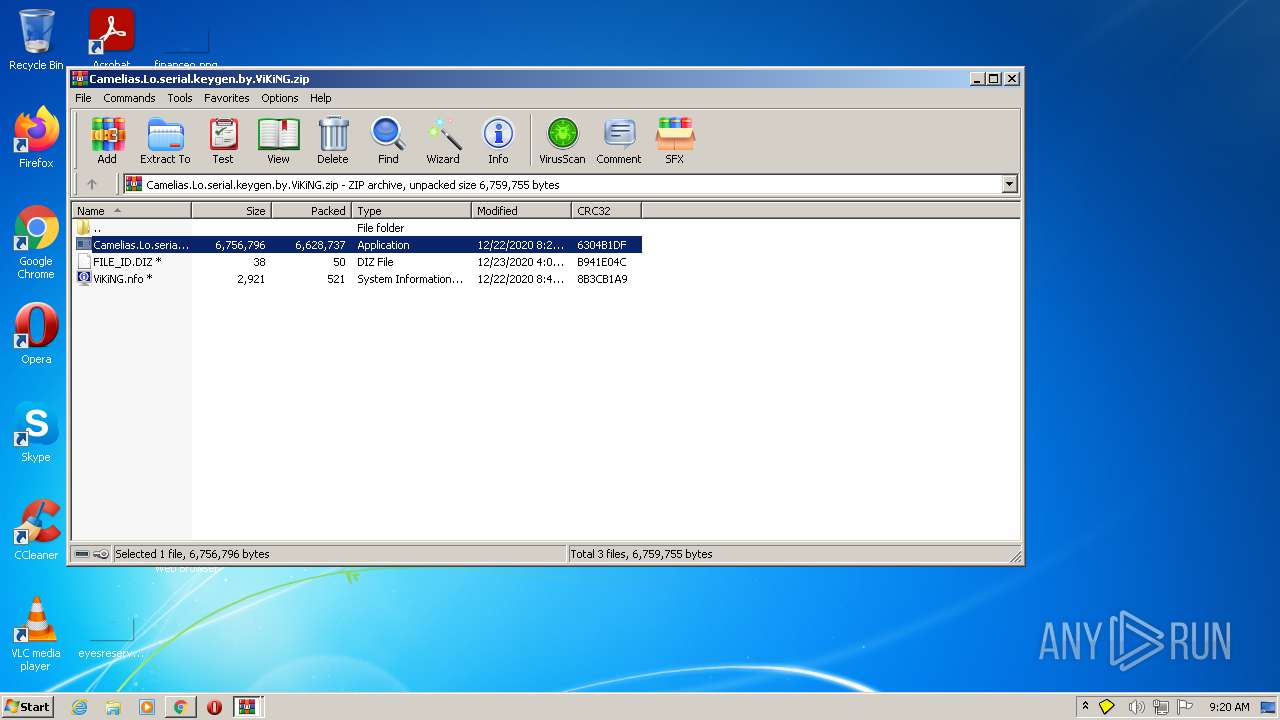
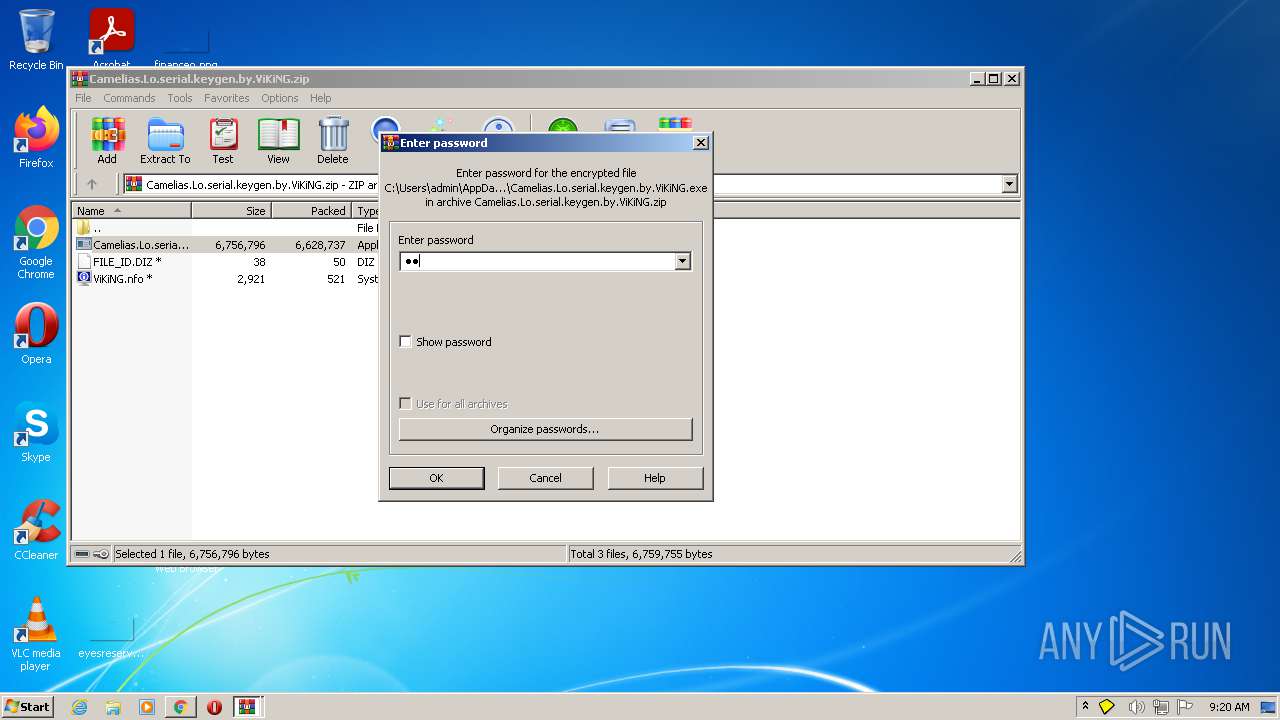
Executable content was dropped or overwritten
- chrome.exe (PID: 3000)
- Sandboxie-Classic-x86-v5.51.3.exe (PID: 2588)
- WinRAR.exe (PID: 1476)
- Camelias.Lo.serial.keygen.by.ViKiNG.exe (PID: 2560)
- keygen-pr.exe (PID: 2608)
- keygen-step-4.exe (PID: 2228)
- cmd.exe (PID: 2160)
- keygen-step-6.exe (PID: 2956)
- keygen-step-3.exe (PID: 2936)
Drops a file with a compile date too recent
- chrome.exe (PID: 3000)
- Sandboxie-Classic-x86-v5.51.3.exe (PID: 2588)
- Camelias.Lo.serial.keygen.by.ViKiNG.exe (PID: 2560)
- keygen-step-4.exe (PID: 2228)
- keygen-step-3.exe (PID: 2936)
- keygen-step-6.exe (PID: 2956)
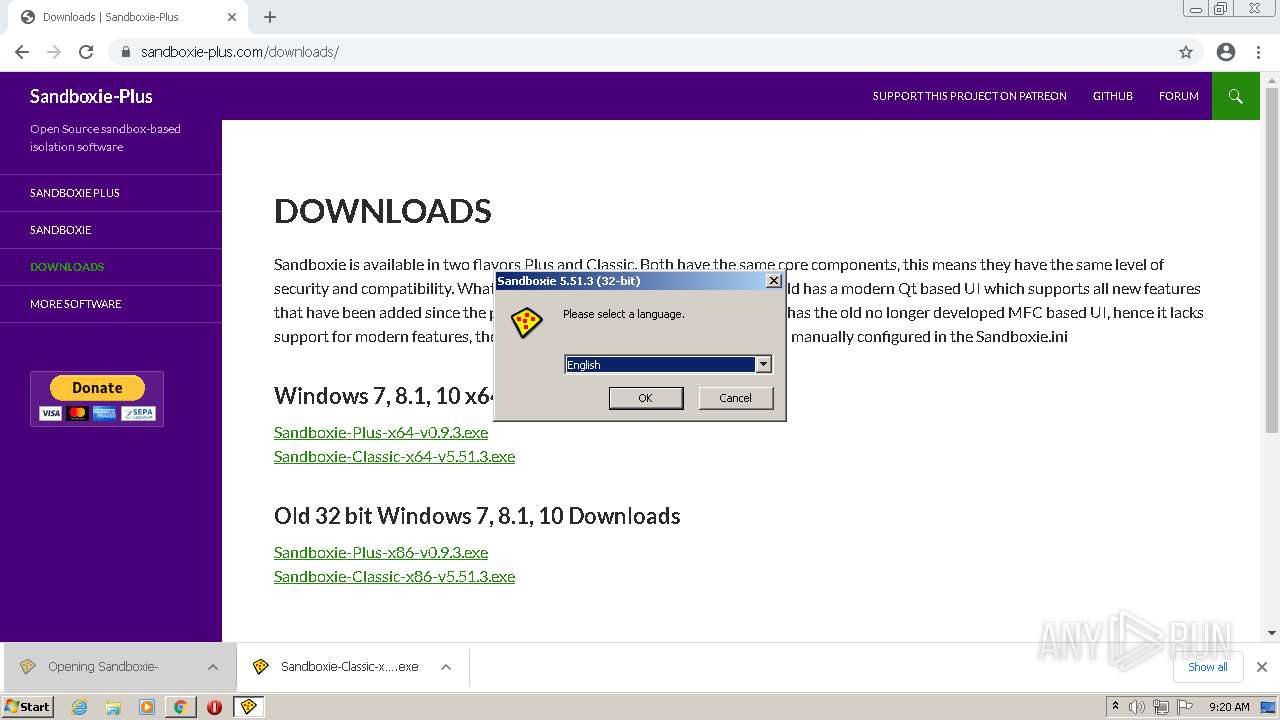
Checks supported languages
- Sandboxie-Classic-x86-v5.51.3.exe (PID: 2588)
- KmdUtil.exe (PID: 4060)
- KmdUtil.exe (PID: 2548)
- KmdUtil.exe (PID: 2644)
- KmdUtil.exe (PID: 1260)
- KmdUtil.exe (PID: 3396)
- Start.exe (PID: 2840)
- SbieCtrl.exe (PID: 3252)
- SbieSvc.exe (PID: 1984)
- WinRAR.exe (PID: 1800)
- WinRAR.exe (PID: 1476)
- KmdUtil.exe (PID: 1684)
- Start.exe (PID: 3172)
- SandboxieRpcSs.exe (PID: 2580)
- Start.exe (PID: 2456)
- SandboxieDcomLaunch.exe (PID: 3724)
- Camelias.Lo.serial.keygen.by.ViKiNG.exe (PID: 2560)
- SbieSvc.exe (PID: 3260)
- SbieSvc.exe (PID: 2392)
- cmd.exe (PID: 948)
- keygen-pr.exe (PID: 2608)
- keygen-step-1.exe (PID: 1676)
- keygen-step-6.exe (PID: 2956)
- keygen-step-5.exe (PID: 3628)
- SbieSvc.exe (PID: 3796)
- SbieSvc.exe (PID: 1344)
- SbieSvc.exe (PID: 2292)
- key.exe (PID: 3044)
- cmd.exe (PID: 2160)
- Start.exe (PID: 2464)
- SandboxieCrypto.exe (PID: 2420)
- Start.exe (PID: 2412)
- SbieSvc.exe (PID: 4088)
- keygen-step-3.exe (PID: 2936)
- keygen-step-4.exe (PID: 2228)
- FvD9kOs1J.ExE (PID: 1552)
- KiffApp2.exe (PID: 2932)
- SbieSvc.exe (PID: 2392)
- cmd.exe (PID: 1476)
- 4285.tmp.exe (PID: 3088)
- SbieSvc.exe (PID: 2552)
- cmd.exe (PID: 1792)
- cmd.exe (PID: 2908)
- winnetdriv.exe (PID: 2416)
- cmd.exe (PID: 3696)
- 498B.tmp.exe (PID: 3276)
- SbieSvc.exe (PID: 3812)
- cmd.exe (PID: 2876)
- SbieSvc.exe (PID: 1780)
- Crack.exe (PID: 3716)
Reads the computer name
- Sandboxie-Classic-x86-v5.51.3.exe (PID: 2588)
- KmdUtil.exe (PID: 2548)
- KmdUtil.exe (PID: 4060)
- KmdUtil.exe (PID: 2644)
- KmdUtil.exe (PID: 3396)
- KmdUtil.exe (PID: 1684)
- KmdUtil.exe (PID: 1260)
- SbieSvc.exe (PID: 1984)
- SbieCtrl.exe (PID: 3252)
- WinRAR.exe (PID: 1476)
- WinRAR.exe (PID: 1800)
- SbieSvc.exe (PID: 3260)
- SandboxieRpcSs.exe (PID: 2580)
- SandboxieDcomLaunch.exe (PID: 3724)
- Start.exe (PID: 2456)
- Camelias.Lo.serial.keygen.by.ViKiNG.exe (PID: 2560)
- keygen-step-1.exe (PID: 1676)
- keygen-step-6.exe (PID: 2956)
- keygen-pr.exe (PID: 2608)
- keygen-step-5.exe (PID: 3628)
- SbieSvc.exe (PID: 3796)
- SbieSvc.exe (PID: 1344)
- SandboxieCrypto.exe (PID: 2420)
- Start.exe (PID: 2412)
- keygen-step-3.exe (PID: 2936)
- keygen-step-4.exe (PID: 2228)
- FvD9kOs1J.ExE (PID: 1552)
- KiffApp2.exe (PID: 2932)
- cmd.exe (PID: 948)
- 4285.tmp.exe (PID: 3088)
- key.exe (PID: 3044)
Reads Environment values
- Sandboxie-Classic-x86-v5.51.3.exe (PID: 2588)
- keygen-step-1.exe (PID: 1676)
- KiffApp2.exe (PID: 2932)
Drops a file that was compiled in debug mode
- Sandboxie-Classic-x86-v5.51.3.exe (PID: 2588)
- WinRAR.exe (PID: 1476)
- Camelias.Lo.serial.keygen.by.ViKiNG.exe (PID: 2560)
- keygen-step-4.exe (PID: 2228)
- cmd.exe (PID: 2160)
- keygen-step-6.exe (PID: 2956)
- keygen-step-3.exe (PID: 2936)
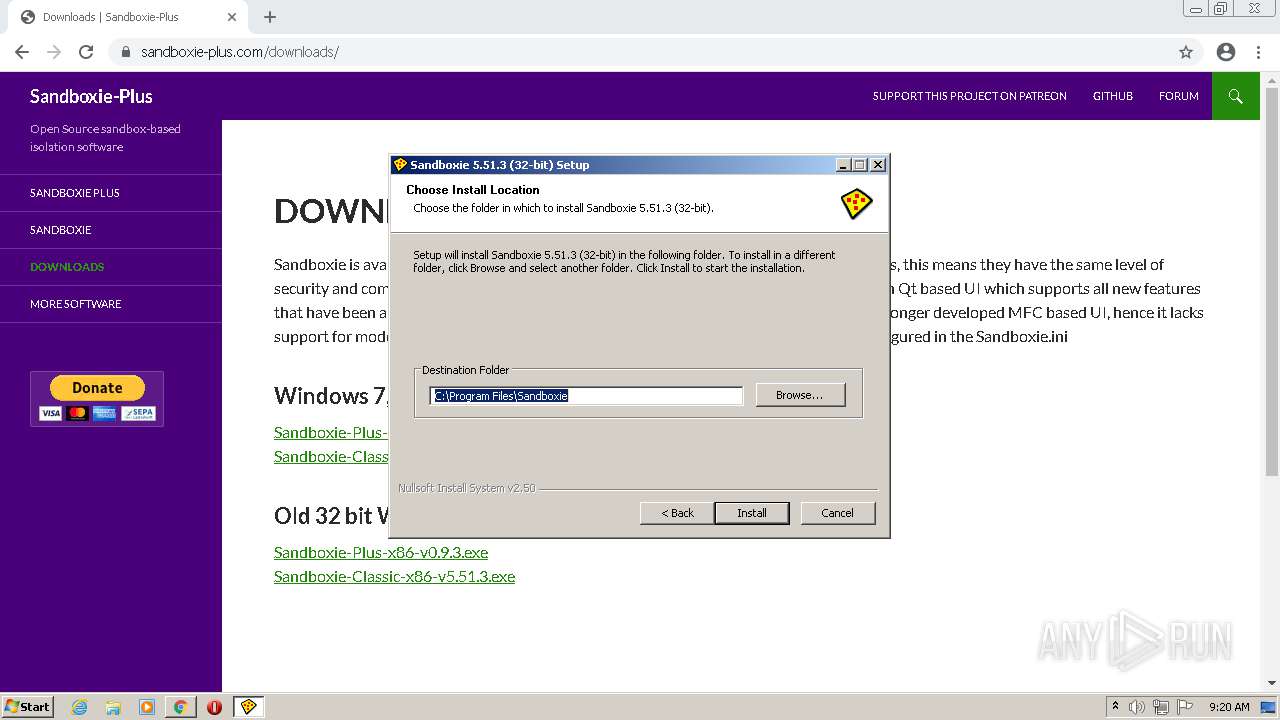
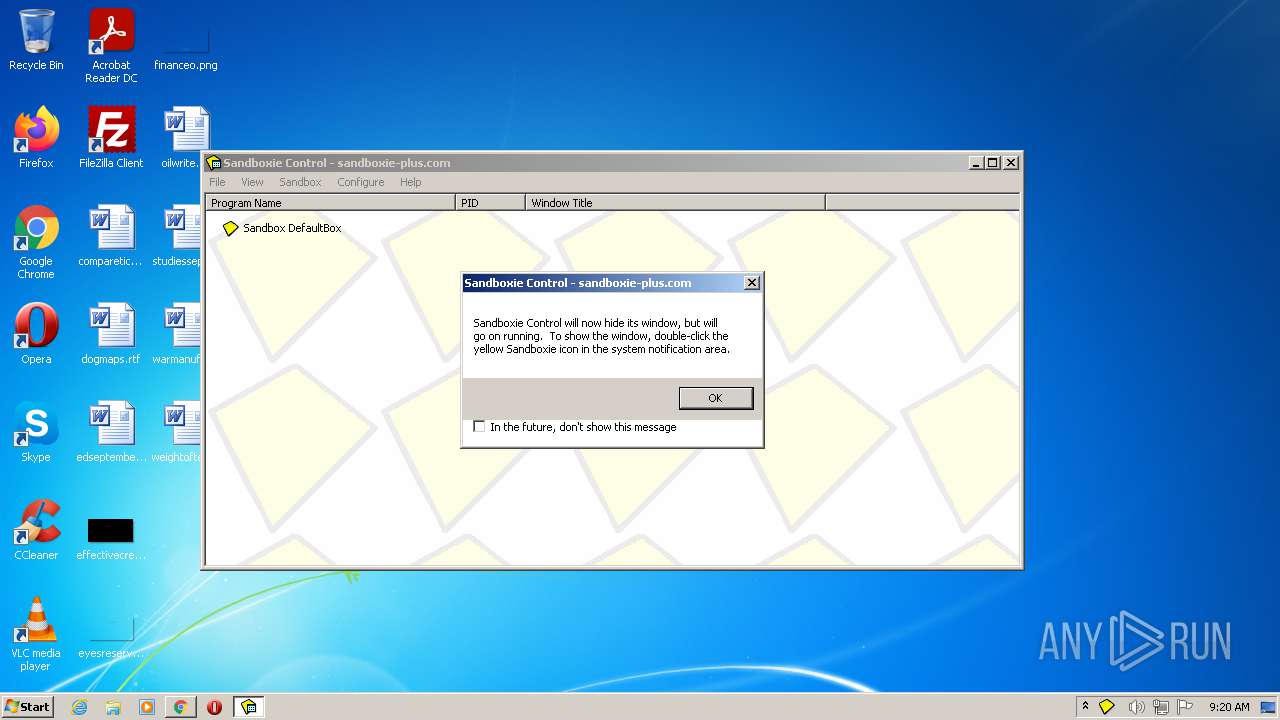
Creates a directory in Program Files
- Sandboxie-Classic-x86-v5.51.3.exe (PID: 2588)
Creates files in the program directory
- Sandboxie-Classic-x86-v5.51.3.exe (PID: 2588)
Creates a software uninstall entry
- Sandboxie-Classic-x86-v5.51.3.exe (PID: 2588)
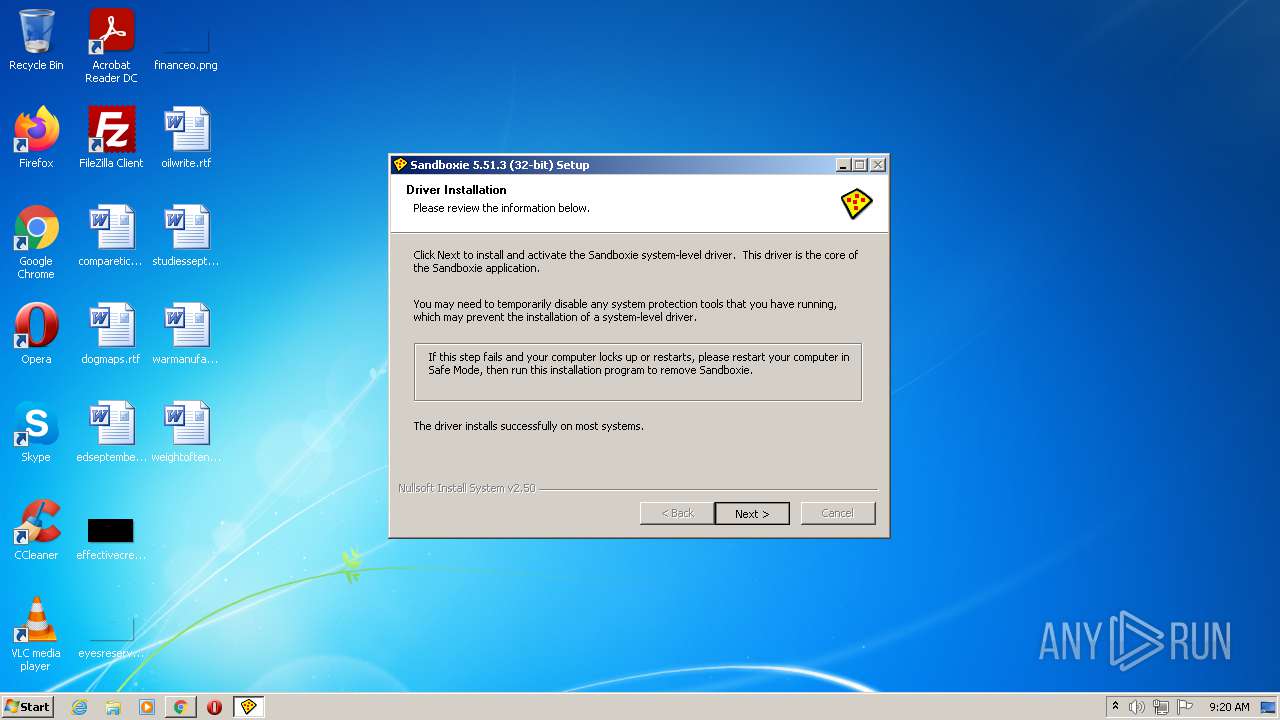
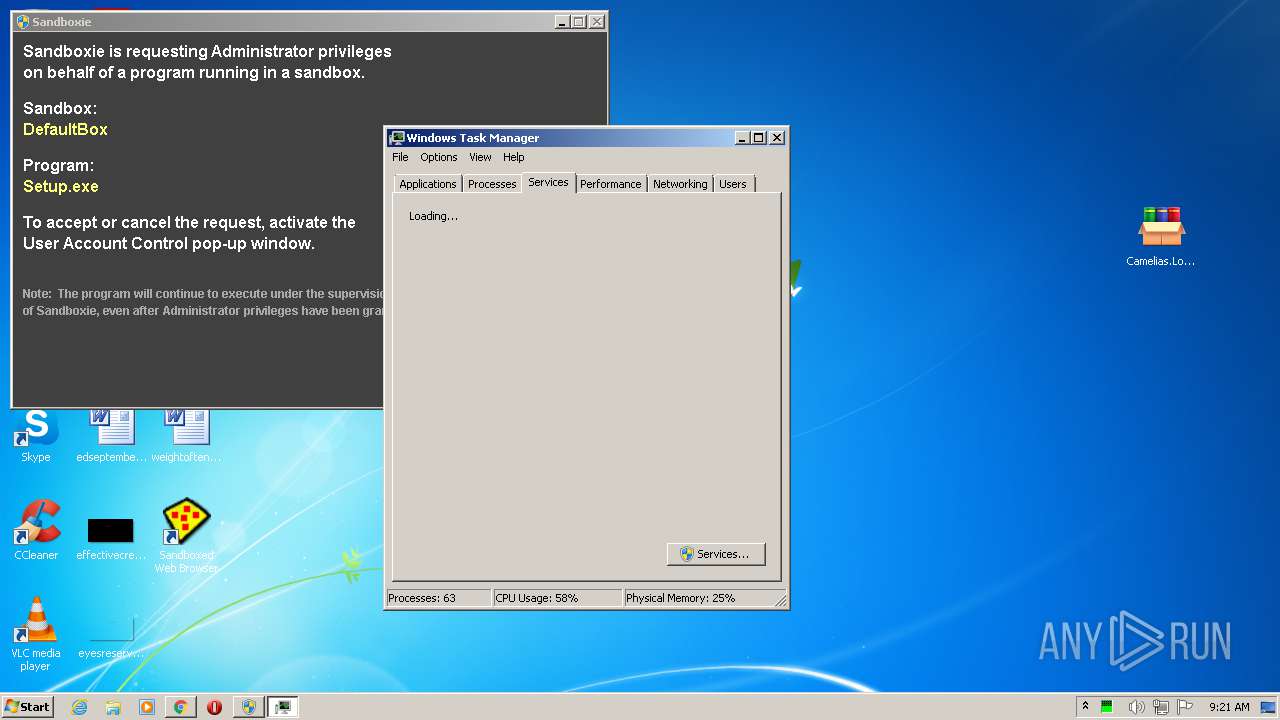
Creates or modifies windows services
- KmdUtil.exe (PID: 1260)
- Sandboxie-Classic-x86-v5.51.3.exe (PID: 2588)
Executed as Windows Service
- SbieSvc.exe (PID: 1984)
Creates files in the user directory
- SbieCtrl.exe (PID: 3252)
Removes files from Windows directory
- SbieSvc.exe (PID: 1984)
Changes default file association
- SbieCtrl.exe (PID: 3252)
Creates files in the Windows directory
- SbieSvc.exe (PID: 1984)
Application launched itself
- WinRAR.exe (PID: 1800)
- SbieSvc.exe (PID: 1984)
- SbieSvc.exe (PID: 3260)
- key.exe (PID: 3044)
- cmd.exe (PID: 1792)
Writes to a desktop.ini file (may be used to cloak folders)
- Start.exe (PID: 2456)
Drops a file with too old compile date
- Camelias.Lo.serial.keygen.by.ViKiNG.exe (PID: 2560)
- keygen-step-4.exe (PID: 2228)
Starts CMD.EXE for commands execution
- Camelias.Lo.serial.keygen.by.ViKiNG.exe (PID: 2560)
- keygen-step-5.exe (PID: 3628)
- FvD9kOs1J.ExE (PID: 1552)
- cmd.exe (PID: 1792)
- keygen-step-6.exe (PID: 2956)
Adds / modifies Windows certificates
- keygen-step-6.exe (PID: 2956)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2160)
Starts itself from another location
- keygen-step-3.exe (PID: 2936)
Starts CMD.EXE for self-deleting
- keygen-step-6.exe (PID: 2956)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 1792)
Loads DLL from Mozilla Firefox
- key.exe (PID: 3044)
Checks for external IP
- keygen-step-6.exe (PID: 2956)
Searches for installed software
- key.exe (PID: 3044)
INFO
Application launched itself
- chrome.exe (PID: 3000)
Reads the hosts file
- chrome.exe (PID: 3000)
- chrome.exe (PID: 2732)
Checks supported languages
- chrome.exe (PID: 2580)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 908)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 2732)
- chrome.exe (PID: 3000)
- chrome.exe (PID: 760)
- chrome.exe (PID: 2644)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 1248)
- chrome.exe (PID: 2280)
- chrome.exe (PID: 2120)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 2368)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 2644)
- chrome.exe (PID: 2144)
- chrome.exe (PID: 2920)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 3748)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 3808)
- chrome.exe (PID: 1860)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 2432)
- chrome.exe (PID: 2492)
- chrome.exe (PID: 2464)
- chrome.exe (PID: 2408)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 2240)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 1404)
- chrome.exe (PID: 3784)
- chrome.exe (PID: 1328)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 3600)
- chrome.exe (PID: 3104)
- chrome.exe (PID: 1568)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 2132)
- chrome.exe (PID: 1260)
- chrome.exe (PID: 2920)
- chrome.exe (PID: 2144)
- chrome.exe (PID: 2432)
- chrome.exe (PID: 3272)
- dllhost.exe (PID: 1200)
- dllhost.exe (PID: 3820)
- taskkill.exe (PID: 2052)
- chrome.exe (PID: 3692)
- rundll32.exe (PID: 2648)
- chrome.exe (PID: 2644)
- PING.EXE (PID: 2452)
Reads the computer name
- chrome.exe (PID: 2732)
- chrome.exe (PID: 3000)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 760)
- chrome.exe (PID: 2644)
- chrome.exe (PID: 2644)
- chrome.exe (PID: 3748)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 2408)
- chrome.exe (PID: 1328)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 1260)
- chrome.exe (PID: 2920)
- dllhost.exe (PID: 1200)
- dllhost.exe (PID: 3820)
- taskkill.exe (PID: 2052)
Reads settings of System Certificates
- chrome.exe (PID: 2732)
- chrome.exe (PID: 3000)
- keygen-step-6.exe (PID: 2956)
- SandboxieCrypto.exe (PID: 2420)
- KiffApp2.exe (PID: 2932)
- 4285.tmp.exe (PID: 3088)
Checks Windows Trust Settings
- chrome.exe (PID: 3000)
- keygen-step-6.exe (PID: 2956)
Reads the date of Windows installation
- chrome.exe (PID: 3188)
Manual execution by user
- Start.exe (PID: 3172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
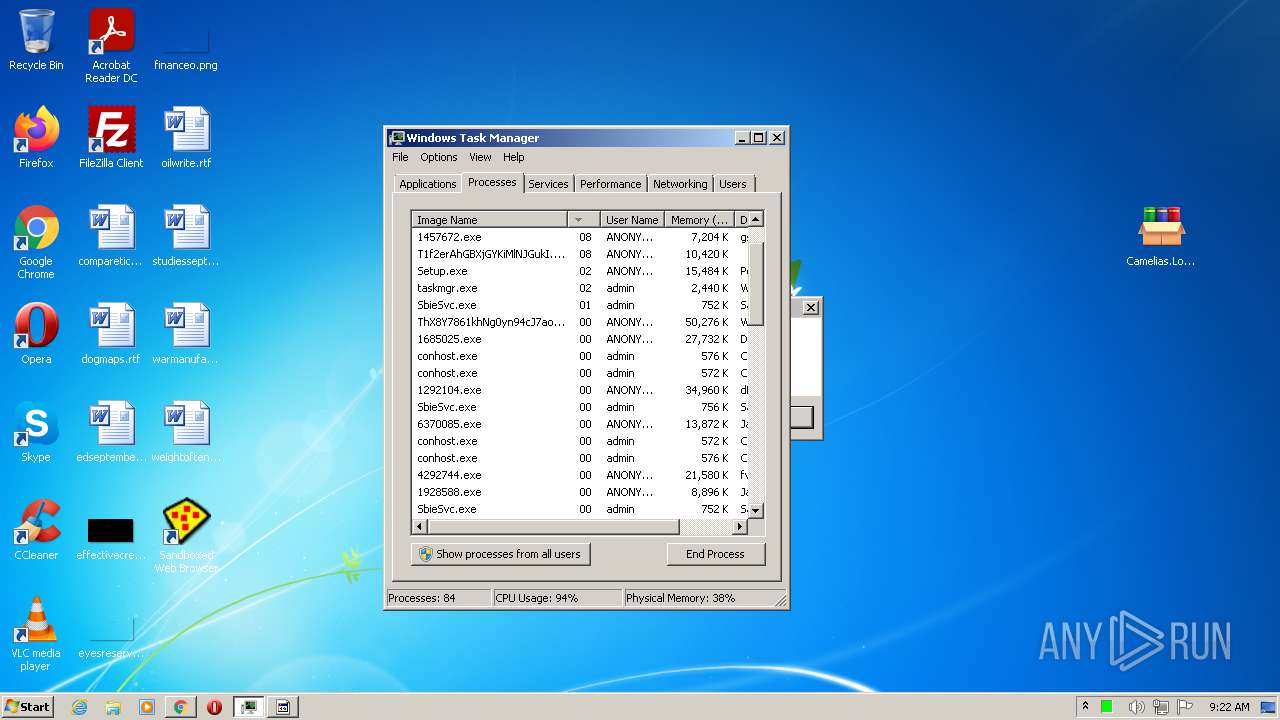
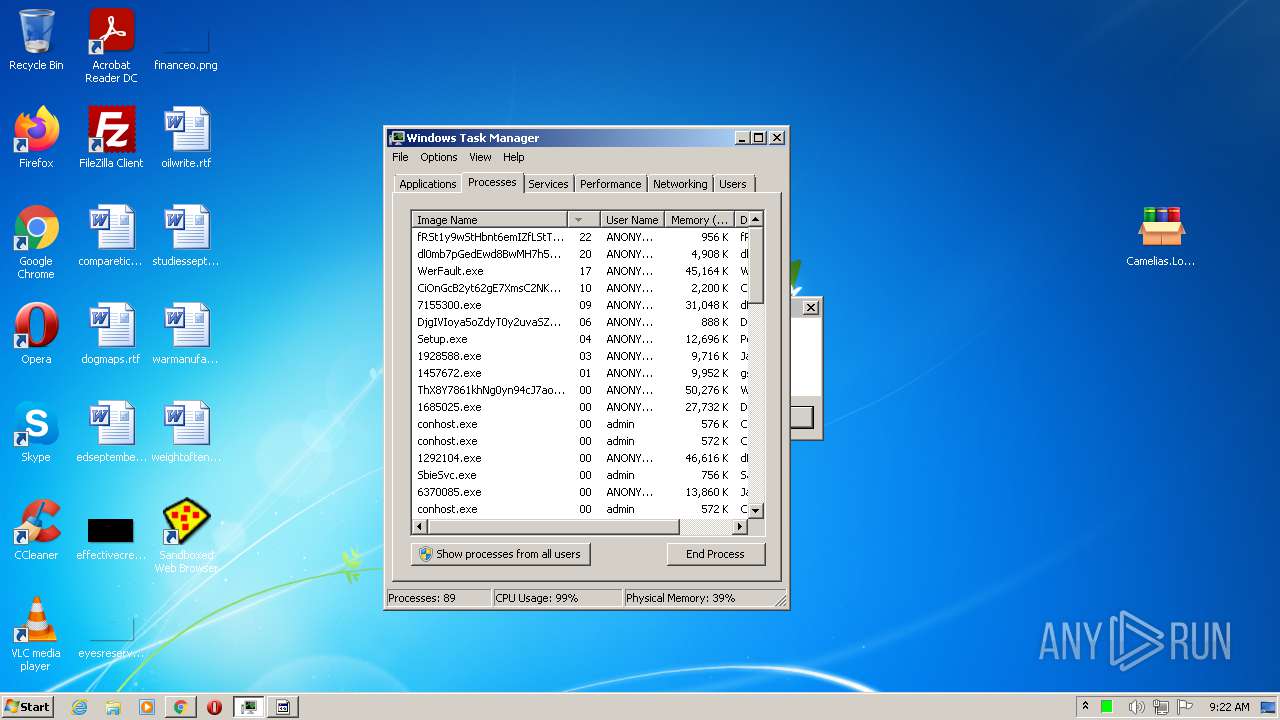
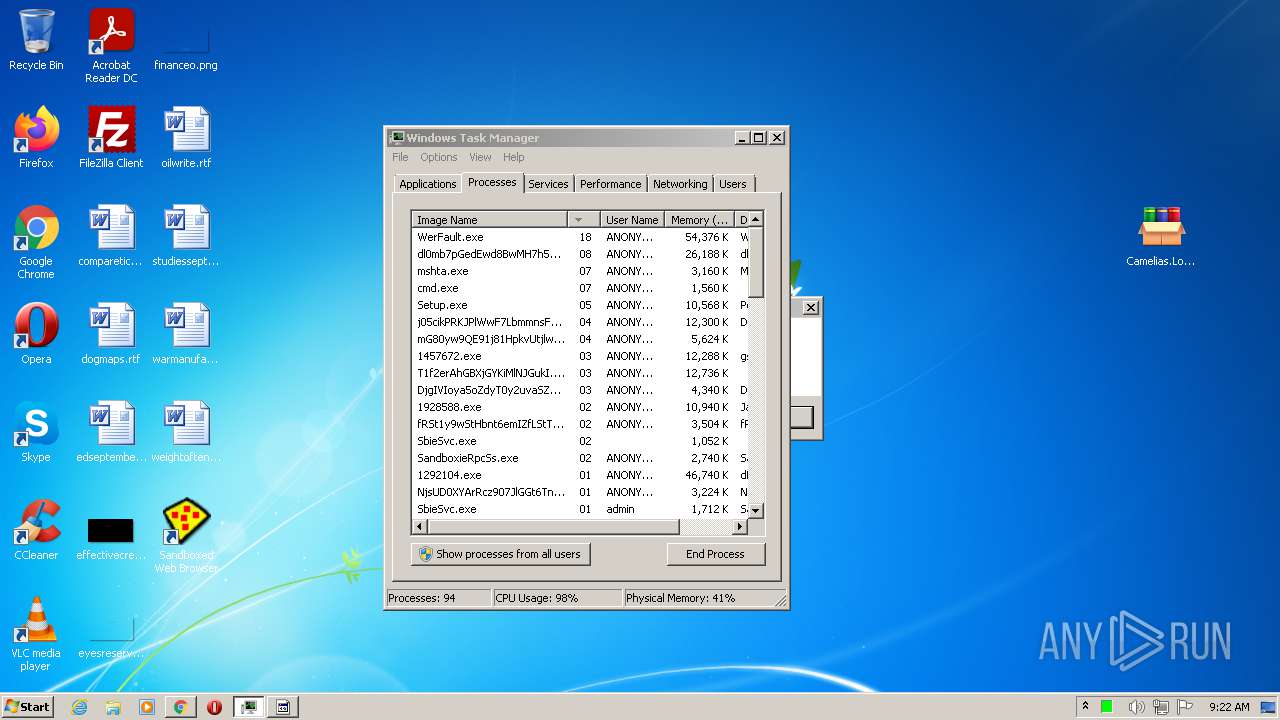
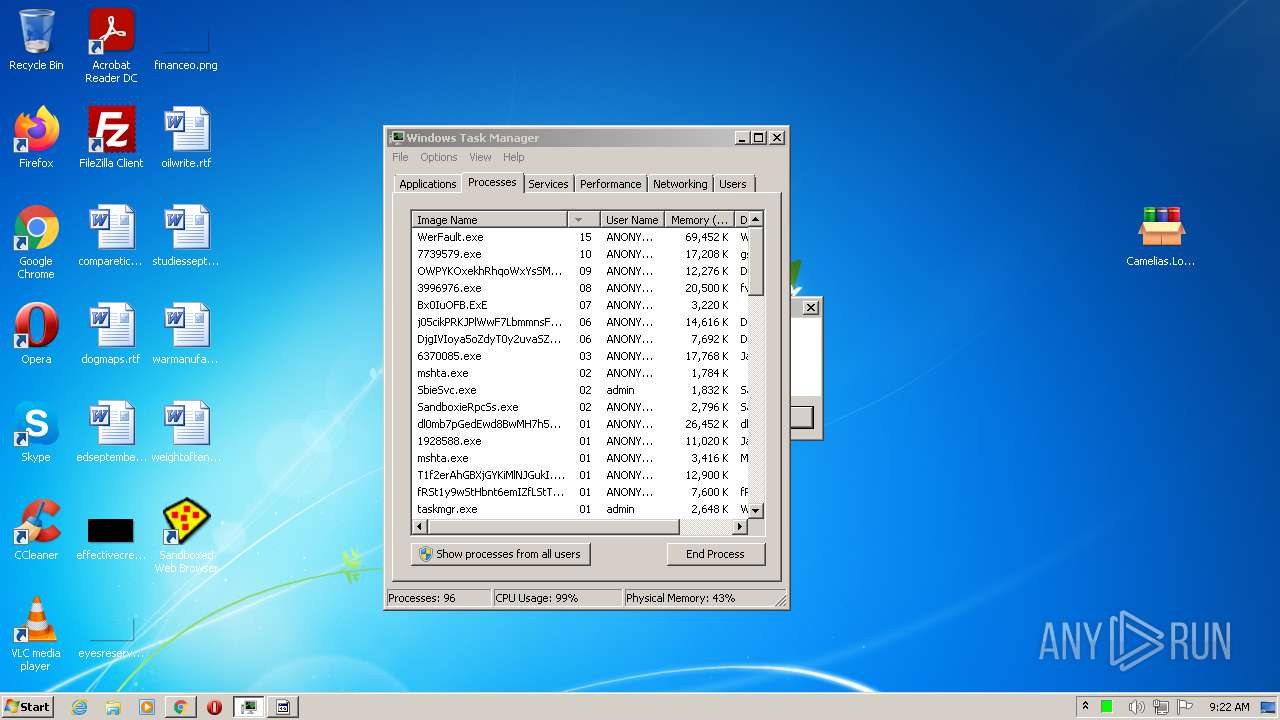
Total processes
160
Monitored processes
108
Malicious processes
25
Suspicious processes
14
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,1523654150083315469,8807180883606094471,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1044 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x7172d988,0x7172d998,0x7172d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 948 | C:\Windows\system32\cmd.exe /c ""C:\Sandbox\admin\DefaultBox\user\current\AppData\Local\Temp\RarSFX0\keygen.bat" " | C:\Windows\system32\cmd.exe | — | Camelias.Lo.serial.keygen.by.ViKiNG.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1200 | C:\Windows\system32\DllHost.exe /Processid:{3EB3C877-1F16-487C-9050-104DBCD66683} | C:\Windows\System32\dllhost.exe | — | SandboxieDcomLaunch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,1523654150083315469,8807180883606094471,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1836 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1260 | "C:\Users\admin\AppData\Local\Temp\nse2724.tmp\KmdUtil.exe" /lang=1033 install SbieDrv "C:\Program Files\Sandboxie\SbieDrv.sys" type=kernel start=demand "msgfile=C:\Program Files\Sandboxie\SbieMsg.dll" altitude=86900 | C:\Users\admin\AppData\Local\Temp\nse2724.tmp\KmdUtil.exe | — | Sandboxie-Classic-x86-v5.51.3.exe | |||||||||||
User: admin Company: sandboxie-plus.com Integrity Level: HIGH Description: Sandboxie configuration file utility Exit code: 0 Version: 5.51.3 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1016,1523654150083315469,8807180883606094471,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2808 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1016,1523654150083315469,8807180883606094471,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3864 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Sandboxie\SbieSvc.exe" Sandboxie_UacProxy:000003B4_00000000_7FF00884_00000192_@\Sessions\0\DosDevices\00000000-0004fd8d | C:\Program Files\Sandboxie\SbieSvc.exe | — | SbieSvc.exe | |||||||||||
User: admin Company: sandboxie-plus.com Integrity Level: MEDIUM Description: Sandboxie Service Exit code: 0 Version: 5.51.3 Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1016,1523654150083315469,8807180883606094471,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=980 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
45 304
Read events
44 785
Write events
513
Delete events
6
Modification events
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3000) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
49
Suspicious files
65
Text files
184
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6128A013-BB8.pma | — | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\62cf68ab-6df8-46d9-b4b2-2d55b2d6abea.tmp | text | |
MD5:— | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4173394f-d65c-49e7-8413-6bb2e0f9d3e3.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF1ca7e0.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3000 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\CURRENT | text | |
MD5:46295CAC801E5D4857D09837238A6394 | SHA256:0F1BAD70C7BD1E0A69562853EC529355462FCD0423263A3D39D6D0D70B780443 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
157
TCP/UDP connections
296
DNS requests
97
Threats
267
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1672 | svchost.exe | GET | 304 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?64fe7653fc4b5288 | US | — | — | whitelisted |
1772 | svchost.exe | HEAD | 200 | 188.120.127.140:80 | http://r1---sn-nvm-cxbz.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3?cms_redirect=yes&mh=DH&mip=45.86.200.17&mm=28&mn=sn-nvm-cxbz&ms=nvh&mt=1630052175&mv=m&mvi=1&pl=24&shardbypass=yes | RS | — | — | whitelisted |
1772 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | — | — | whitelisted |
1772 | svchost.exe | HEAD | 302 | 216.58.201.78:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | — | — | whitelisted |
1672 | svchost.exe | GET | 304 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?1cea66fcf4d81270 | US | — | — | whitelisted |
1772 | svchost.exe | GET | 206 | 188.120.127.140:80 | http://r1---sn-nvm-cxbz.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3?cms_redirect=yes&mh=DH&mip=45.86.200.17&mm=28&mn=sn-nvm-cxbz&ms=nvh&mt=1630052175&mv=m&mvi=1&pl=24&shardbypass=yes | RS | binary | 9.50 Kb | whitelisted |
1772 | svchost.exe | GET | 302 | 216.58.201.78:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | html | 537 b | whitelisted |
1772 | svchost.exe | GET | 206 | 188.120.127.140:80 | http://r1---sn-nvm-cxbz.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3?cms_redirect=yes&mh=DH&mip=45.86.200.17&mm=28&mn=sn-nvm-cxbz&ms=nvh&mt=1630052175&mv=m&mvi=1&pl=24&shardbypass=yes | RS | binary | 5.64 Kb | whitelisted |
1772 | svchost.exe | GET | 206 | 188.120.127.140:80 | http://r1---sn-nvm-cxbz.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3?cms_redirect=yes&mh=DH&mip=45.86.200.17&mm=28&mn=sn-nvm-cxbz&ms=nvh&mt=1630052175&mv=m&mvi=1&pl=24&shardbypass=yes | RS | binary | 9.49 Kb | whitelisted |
1772 | svchost.exe | GET | 302 | 216.58.201.78:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/gpe7ohs3f5omwhxxpxvcdvkwva_1.3.36.101/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.101_win_adeodp7n5nw3wgk7xjdln2w2sgsq.crx3 | US | html | 537 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2732 | chrome.exe | 172.217.23.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
2732 | chrome.exe | 216.58.201.68:443 | www.google.com | Google Inc. | US | whitelisted |
2732 | chrome.exe | 172.217.23.202:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
2732 | chrome.exe | 216.58.201.78:443 | apis.google.com | Google Inc. | US | whitelisted |
2732 | chrome.exe | 172.217.23.238:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
2732 | chrome.exe | 216.58.201.66:443 | adservice.google.com | Google Inc. | US | whitelisted |
2732 | chrome.exe | 216.58.201.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
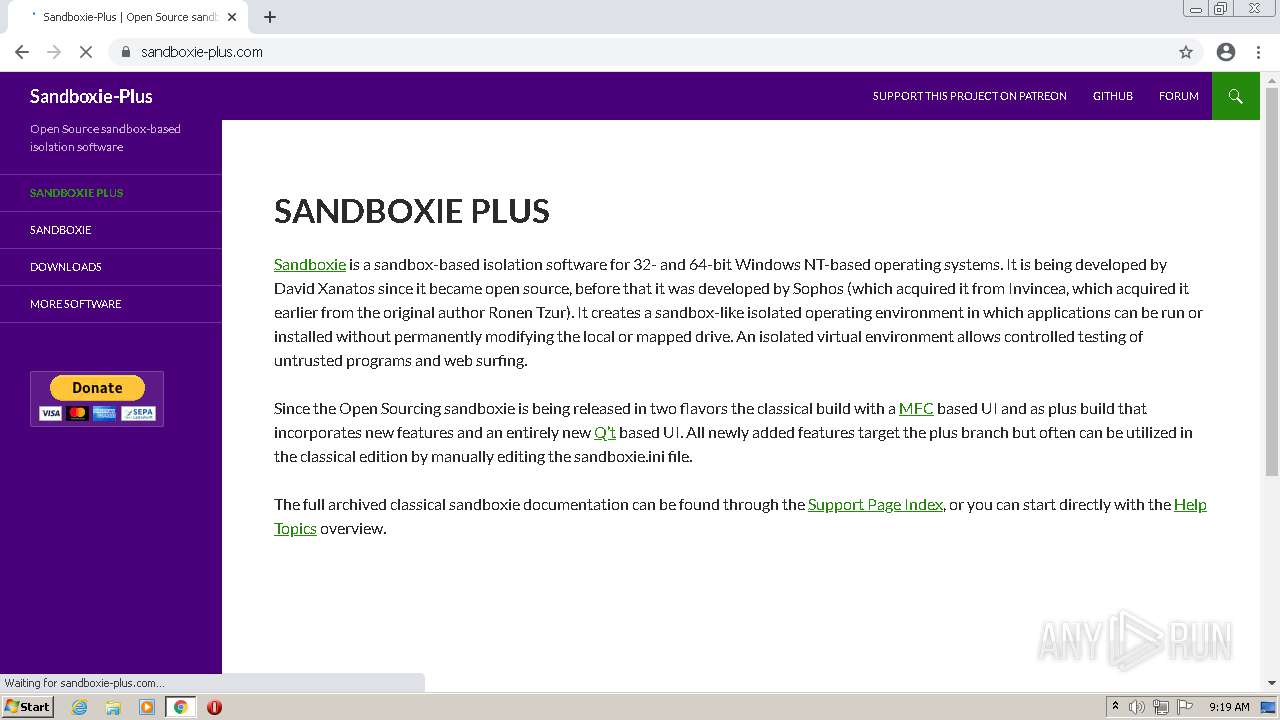
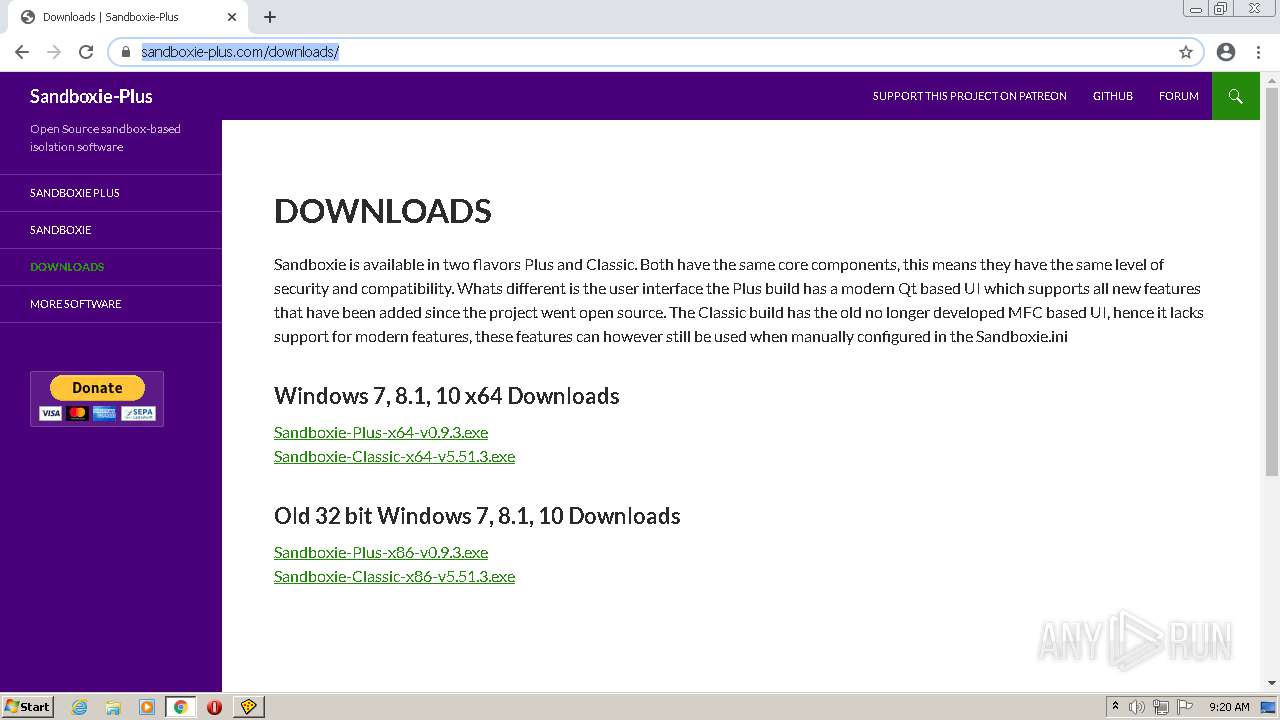
— | — | 172.67.191.99:443 | sandboxie-plus.com | — | US | malicious |
2732 | chrome.exe | 172.217.23.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.238:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
apis.google.com |
| whitelisted |
adservice.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1676 | keygen-step-1.exe | A Network Trojan was detected | ET TROJAN Win32/AZORult V3.3 Client Checkin M2 |
1676 | keygen-step-1.exe | A Network Trojan was detected | AV TROJAN Azorult CnC Beacon |
2956 | keygen-step-6.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2956 | keygen-step-6.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2932 | KiffApp2.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.xyz) |
— | — | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
— | — | Generic Protocol Command Decode | SURICATA HTTP invalid response chunk len |
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
— | — | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
— | — | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
118 ETPRO signatures available at the full report