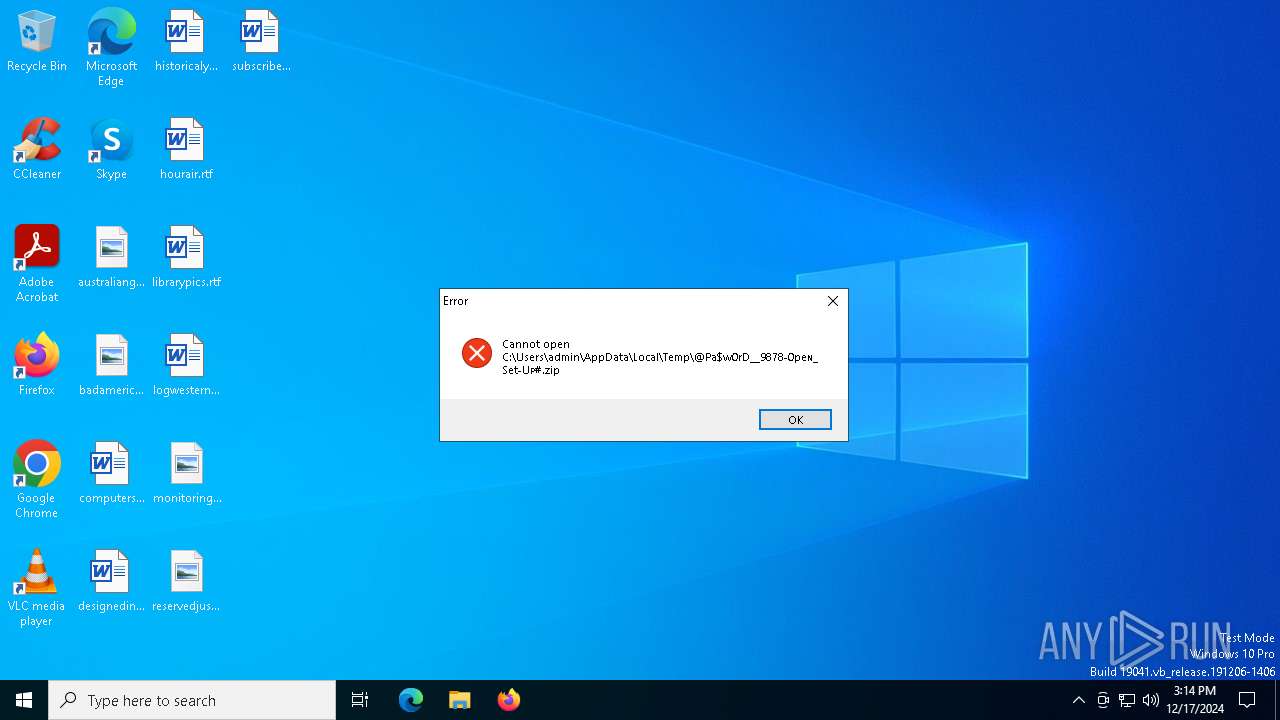
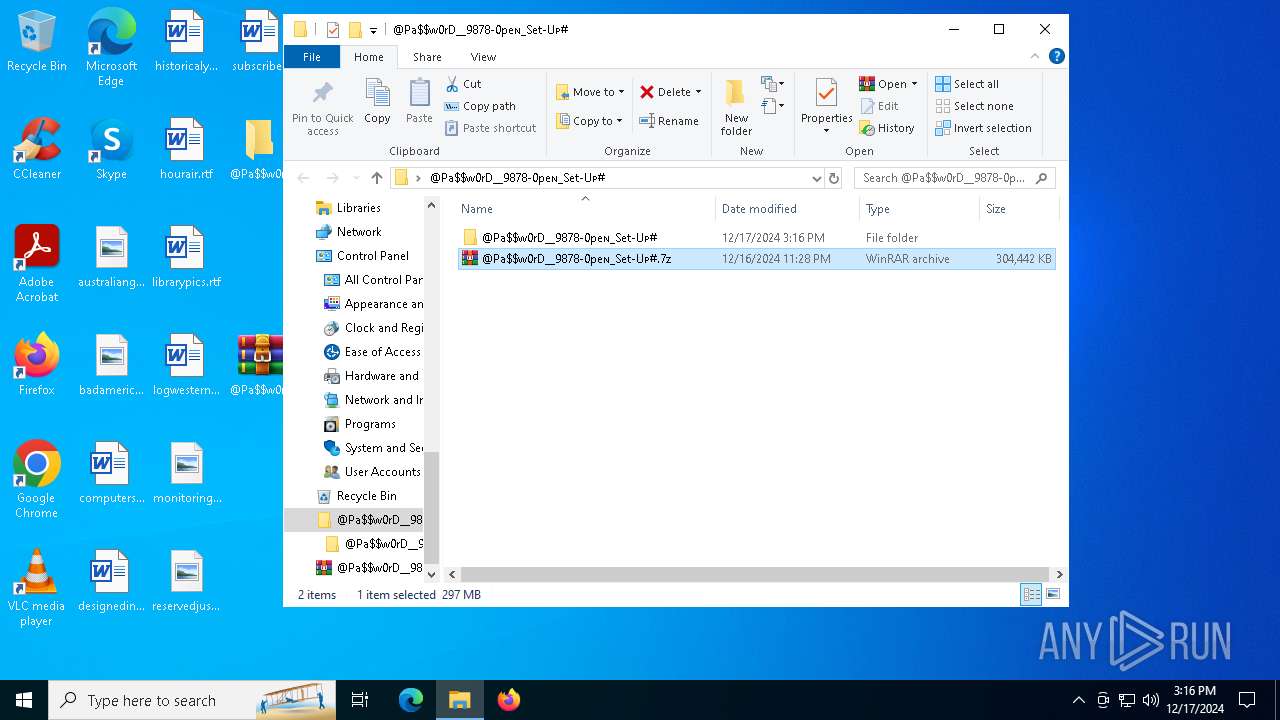
| File name: | @Pa$w0rD__9878-0peɴ_Set-Uᴘ#.zip |
| Full analysis: | https://app.any.run/tasks/3f7ae044-4490-49c7-804e-c14e84948488 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
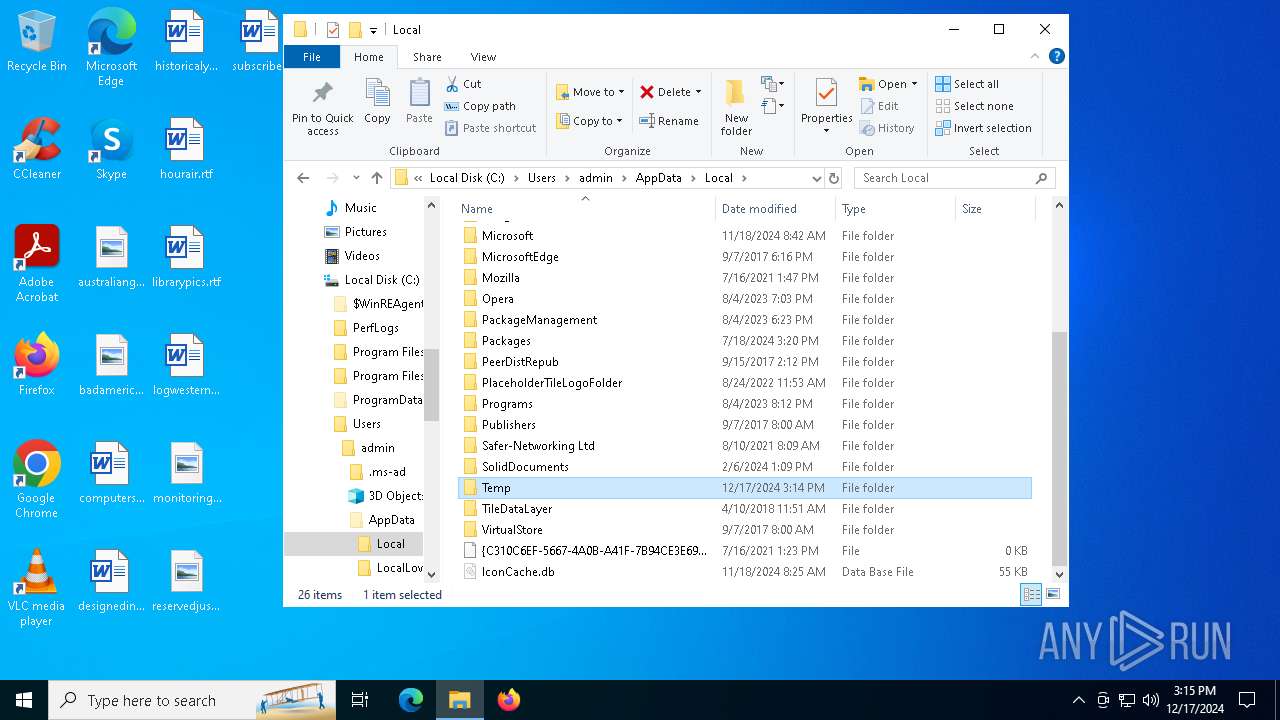
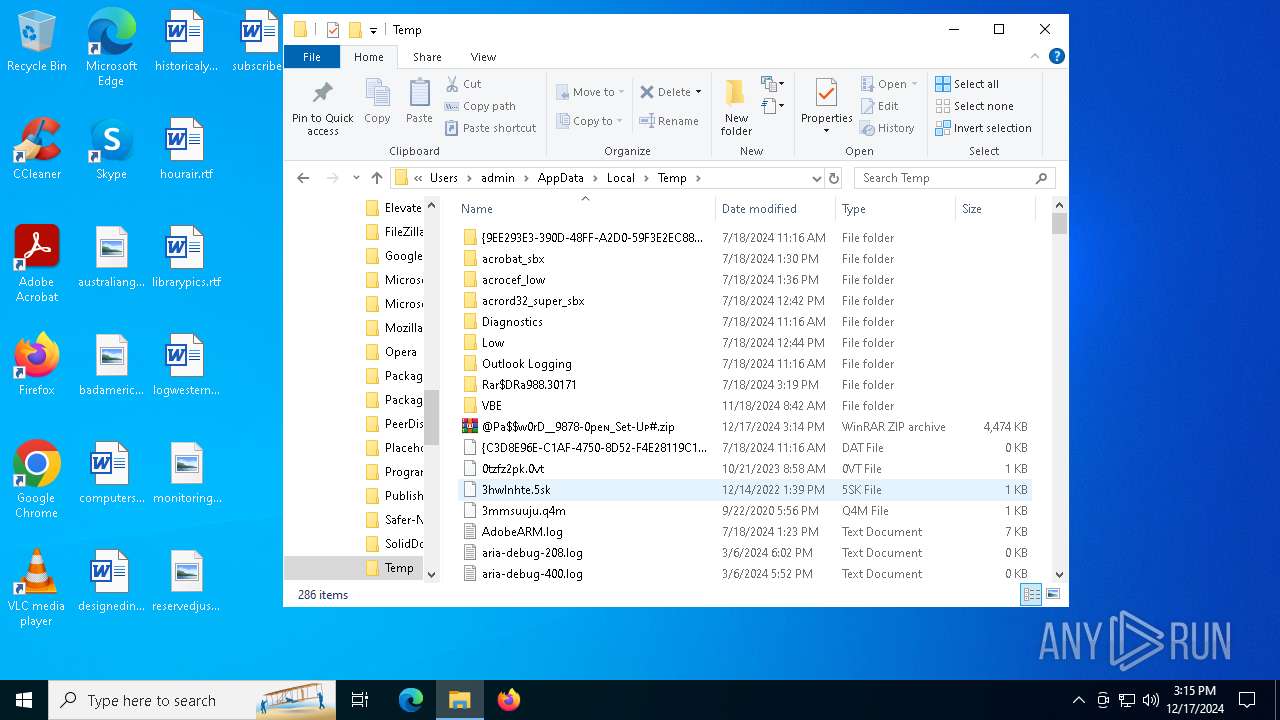
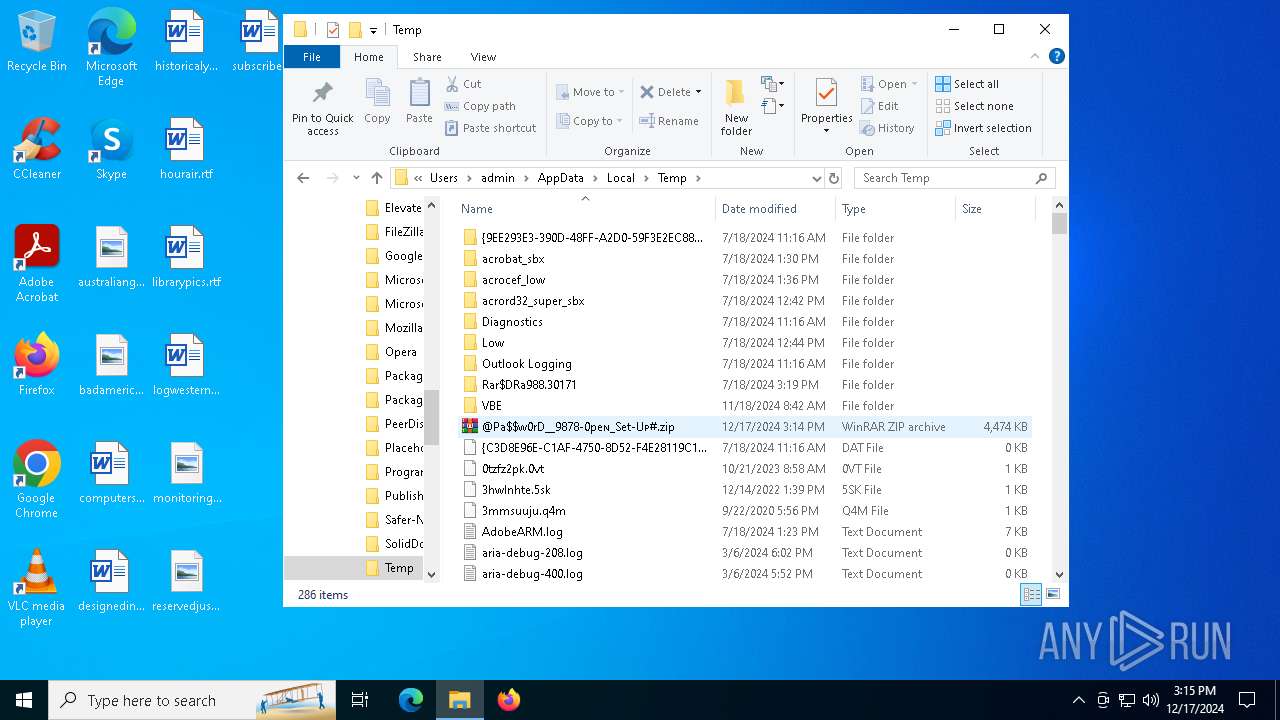
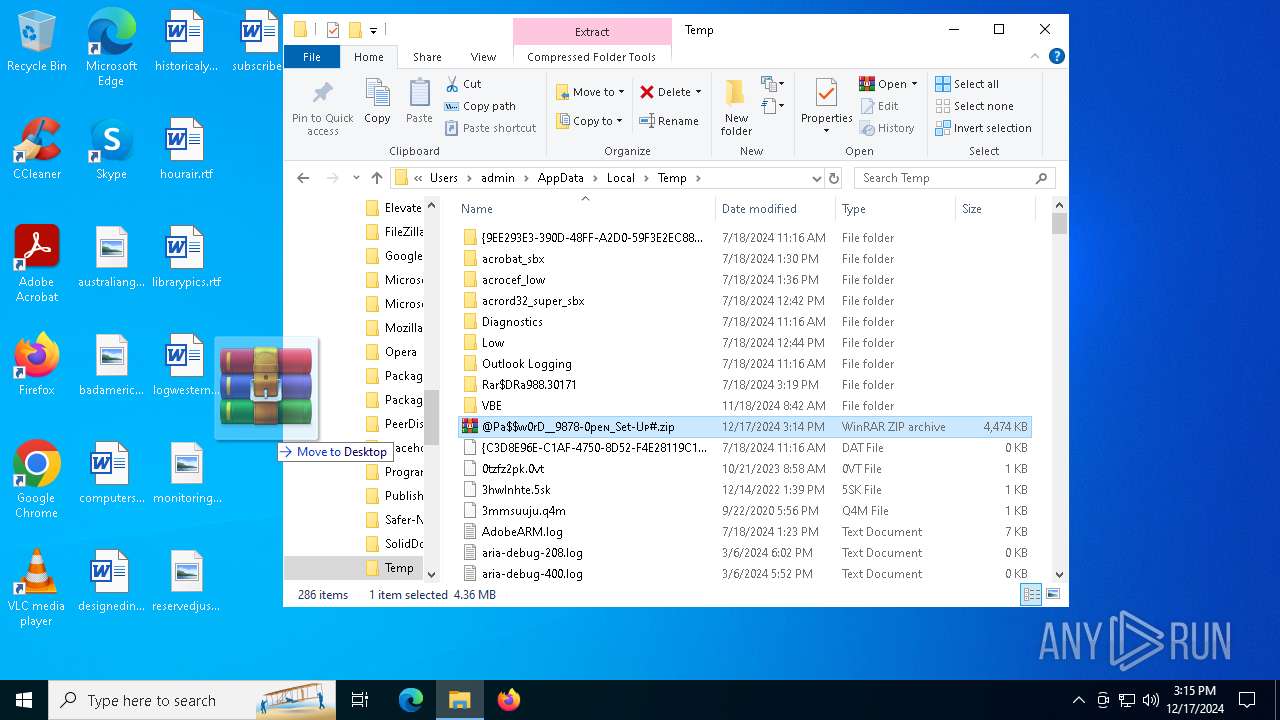
| Analysis date: | December 17, 2024, 15:14:47 |
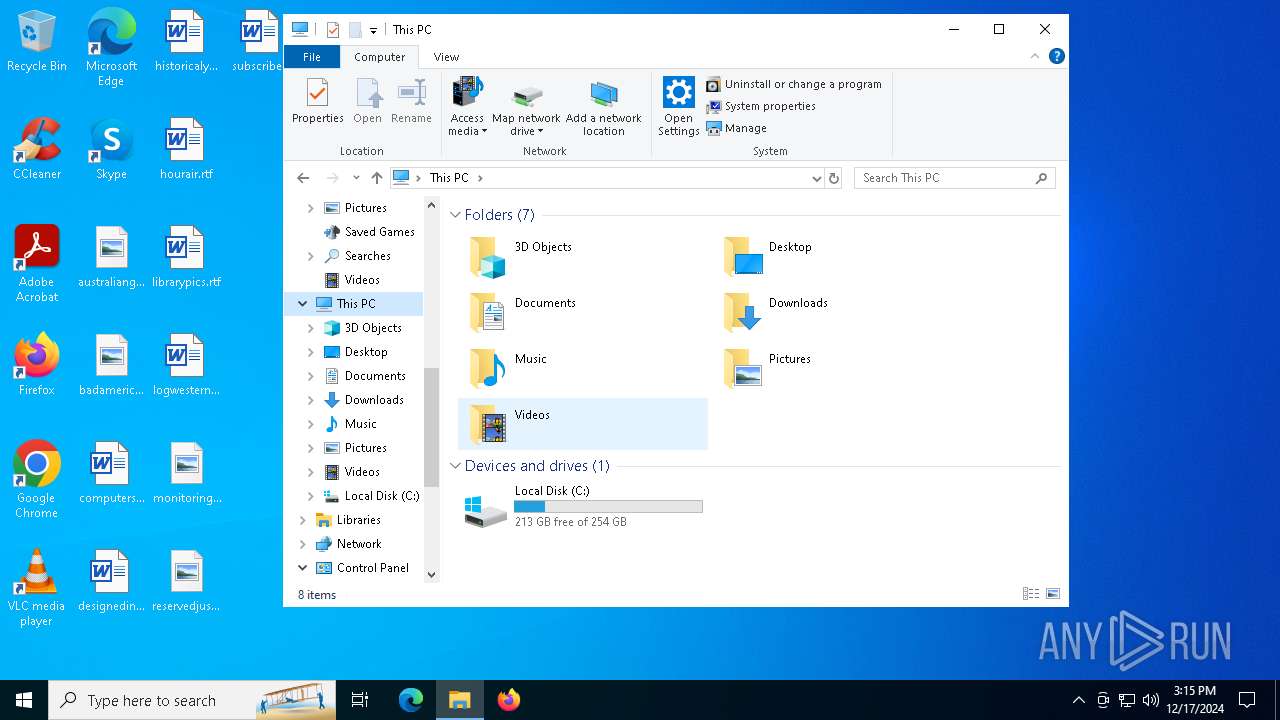
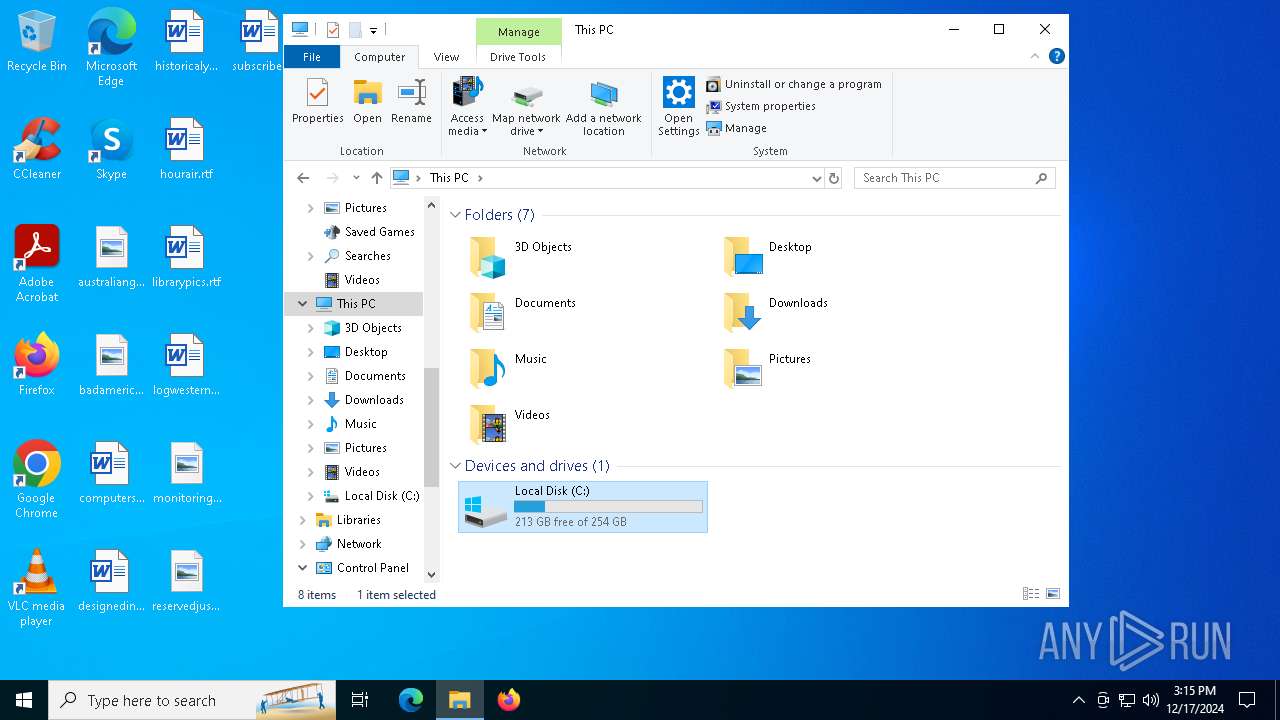
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.1 to extract, compression method=deflate64 |
| MD5: | B377905E40AFA1F5DF061B7353E47E00 |
| SHA1: | CF536150D279641B8474967316151B09F5B015DF |
| SHA256: | AC67D99449F06824CB9DB565EBA4B6DAB655647EEFF0C38B935C01C276F432FD |
| SSDEEP: | 98304:KwH21rS+5njM1S8cRWGDH41xixXTLPOUIJSneIbLg9QO9zGkqP1IiQP4fe9IZIHk:Fg7ym |
MALICIOUS
LUMMA mutex has been found
- BitLockerToGo.exe (PID: 3952)
Actions looks like stealing of personal data
- BitLockerToGo.exe (PID: 3952)
Steals credentials from Web Browsers
- BitLockerToGo.exe (PID: 3952)
LUMMA has been detected (YARA)
- BitLockerToGo.exe (PID: 3952)
SUSPICIOUS
Found regular expressions for crypto-addresses (YARA)
- Setup.exe (PID: 5876)
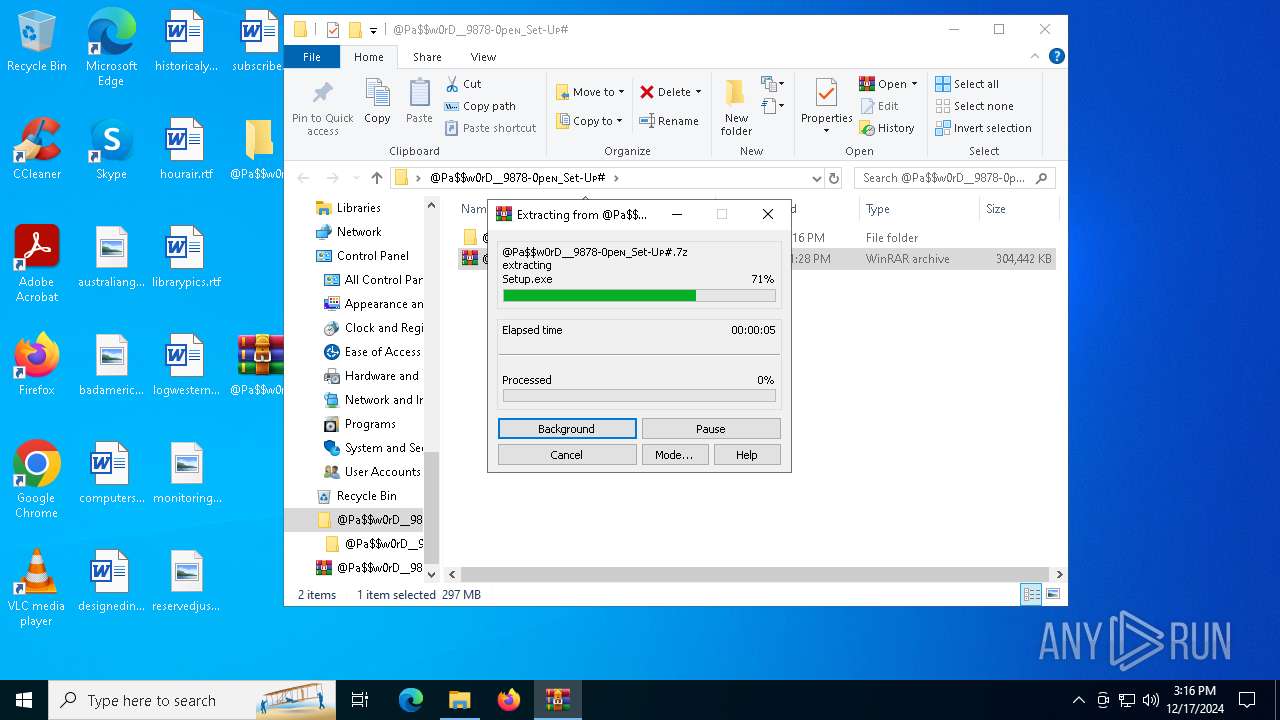
Executable content was dropped or overwritten
- Setup.exe (PID: 5876)
INFO
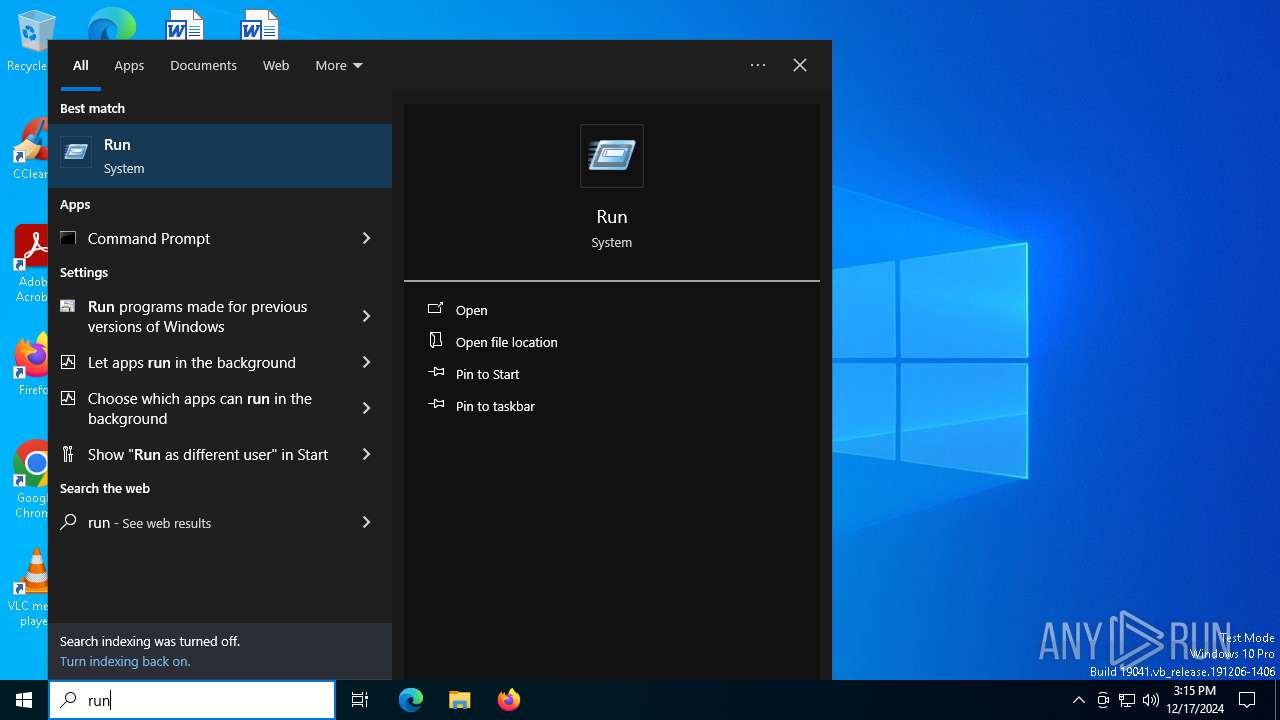
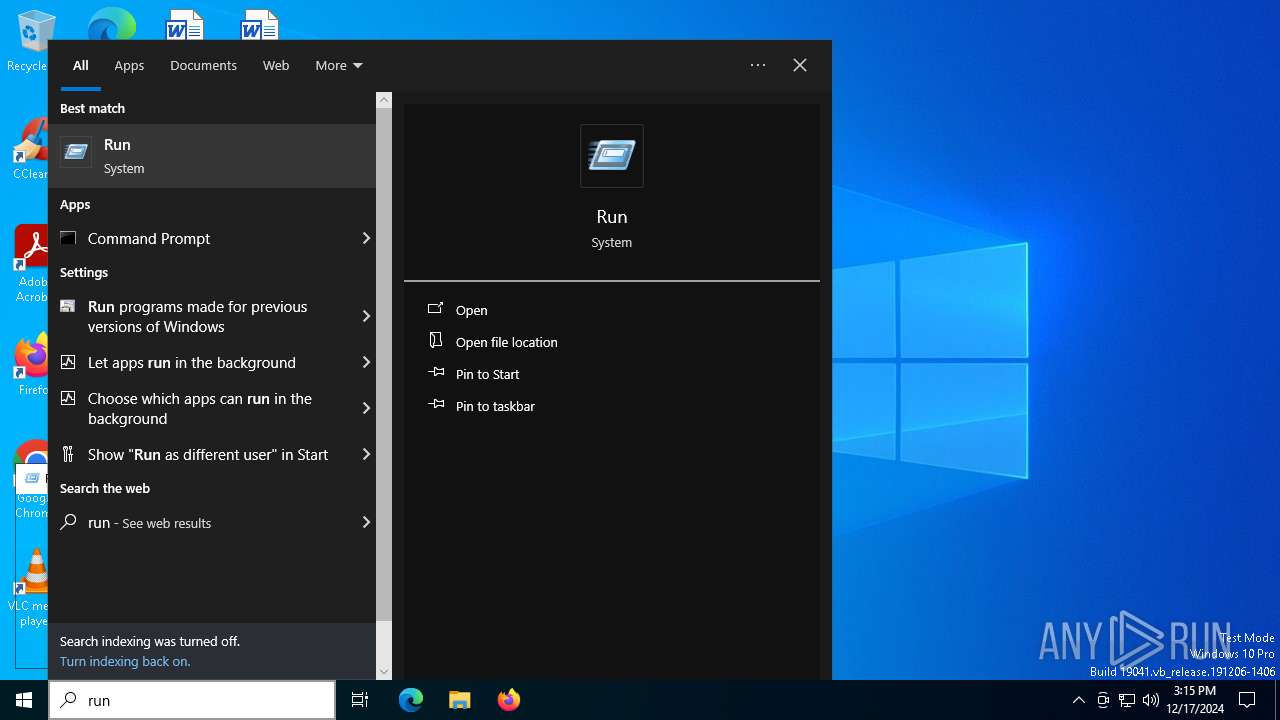
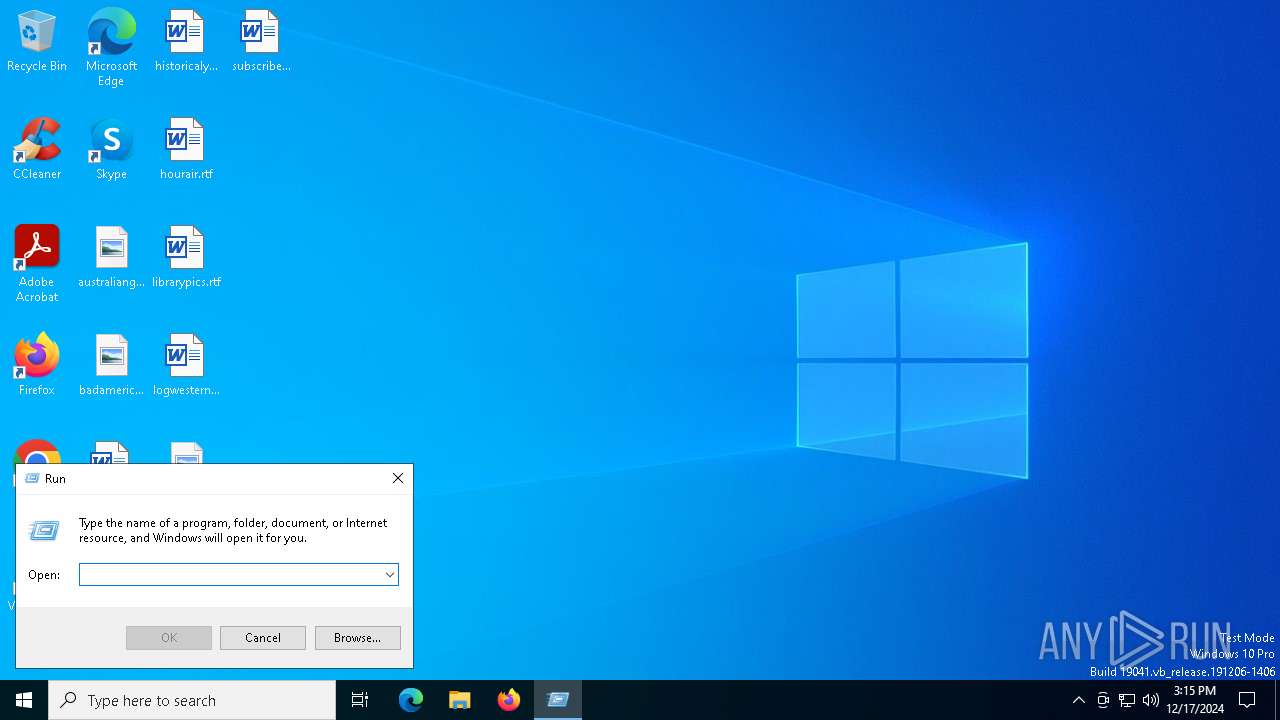
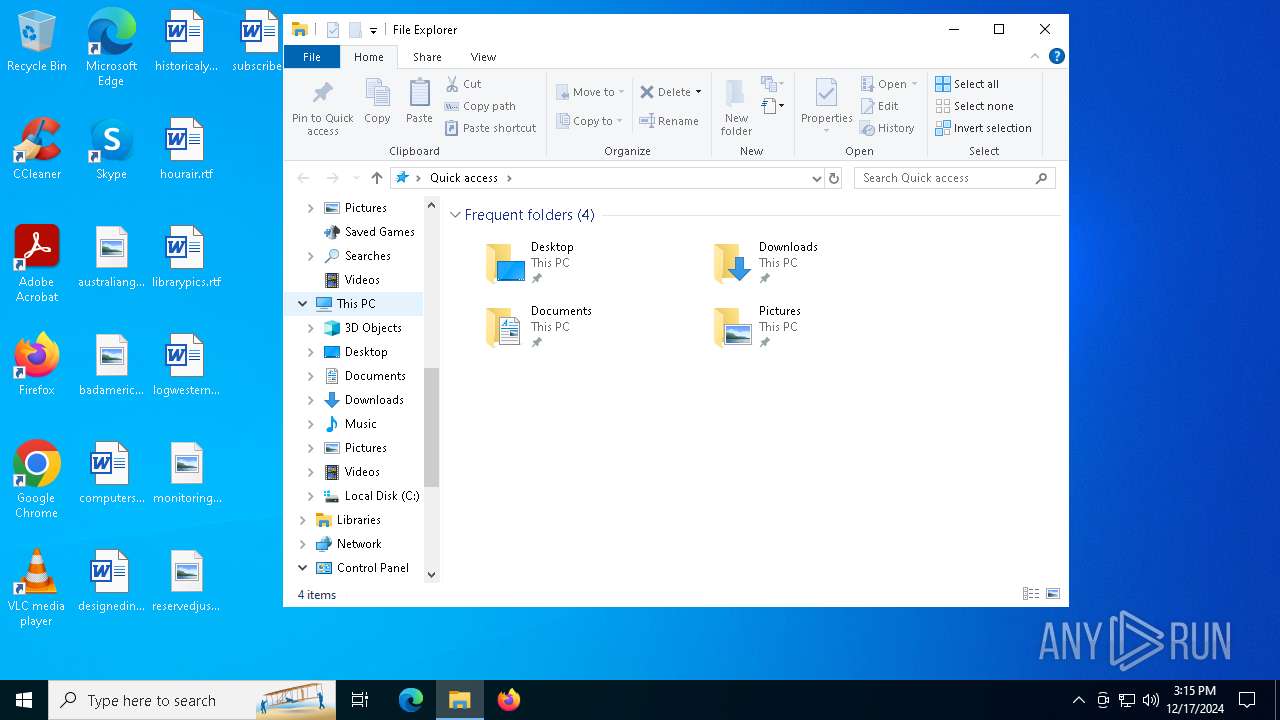
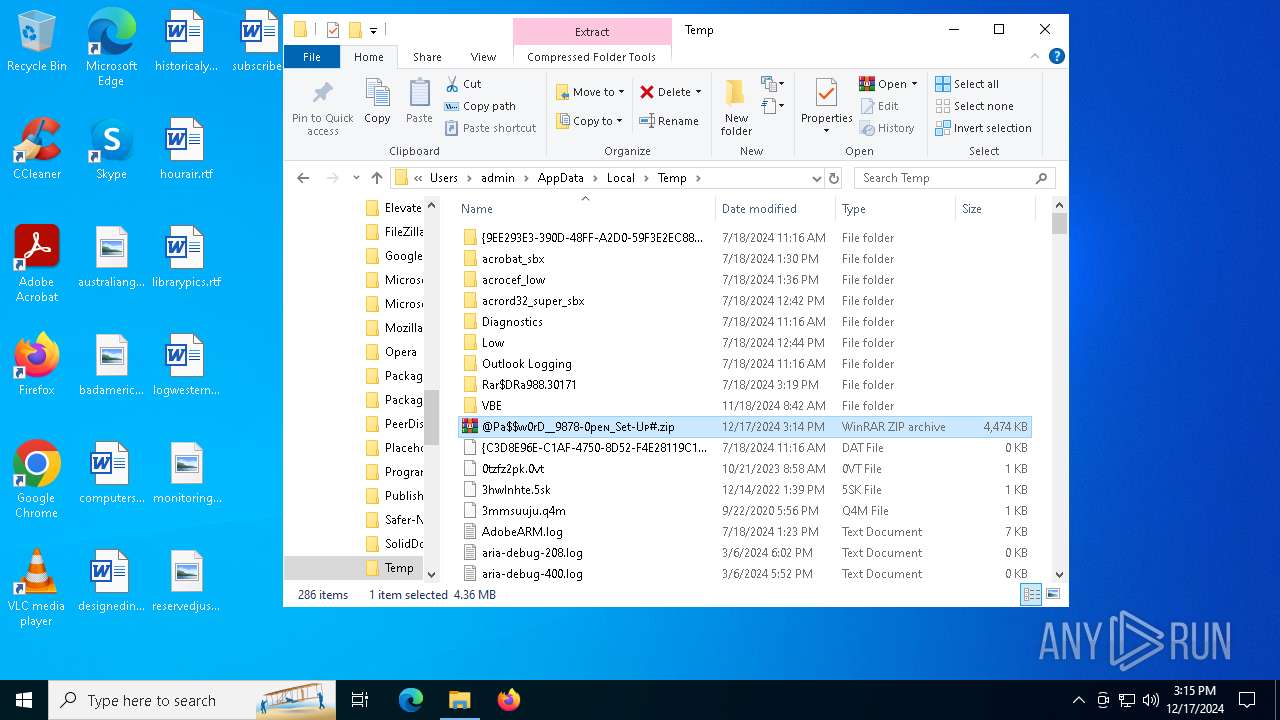
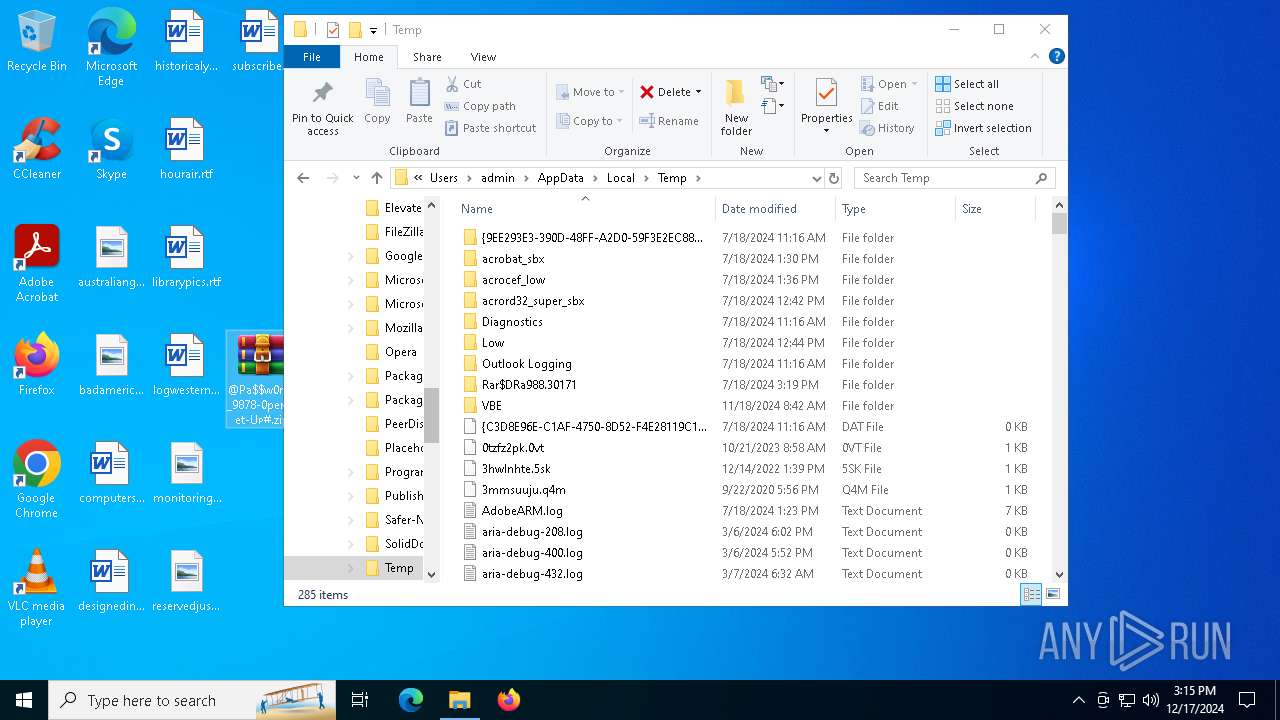
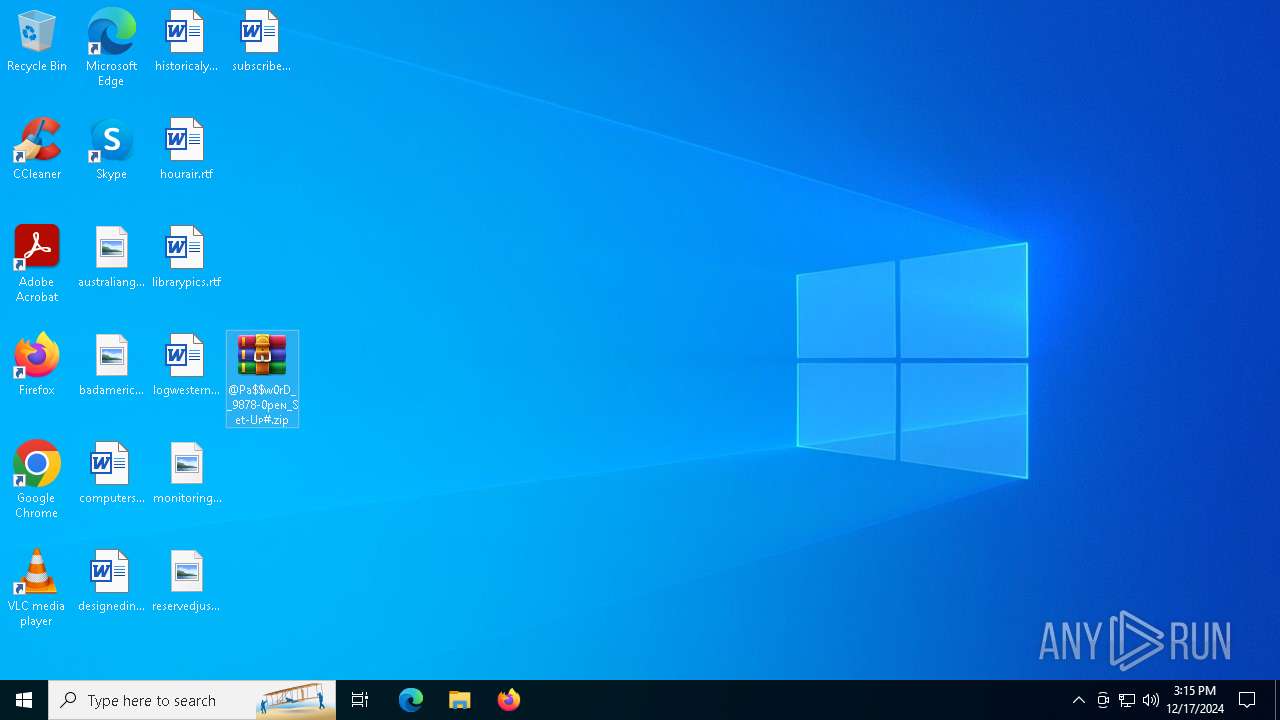
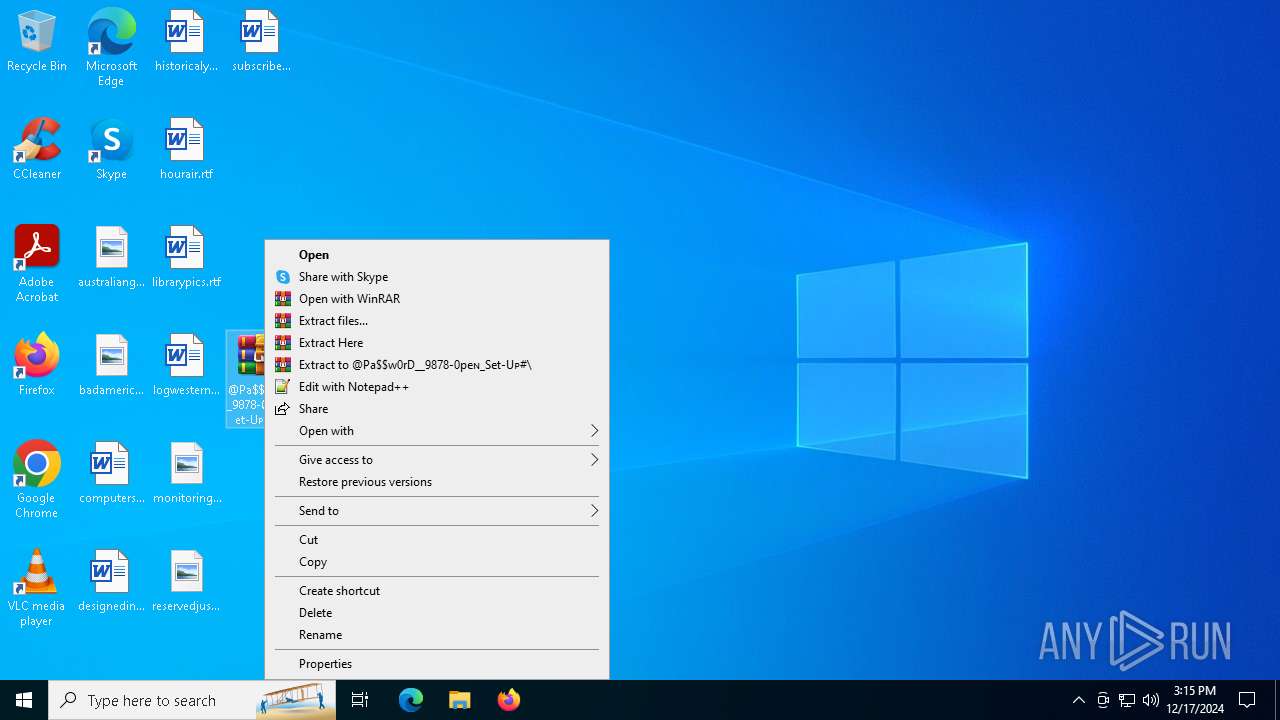
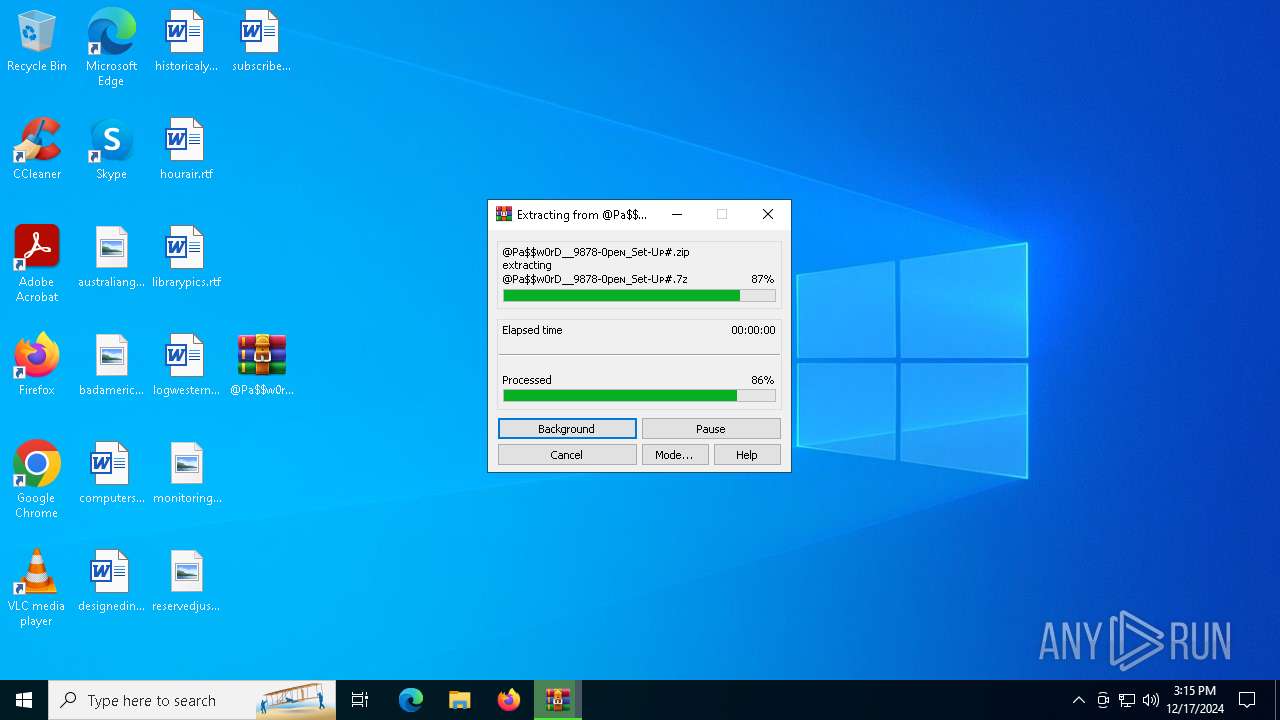
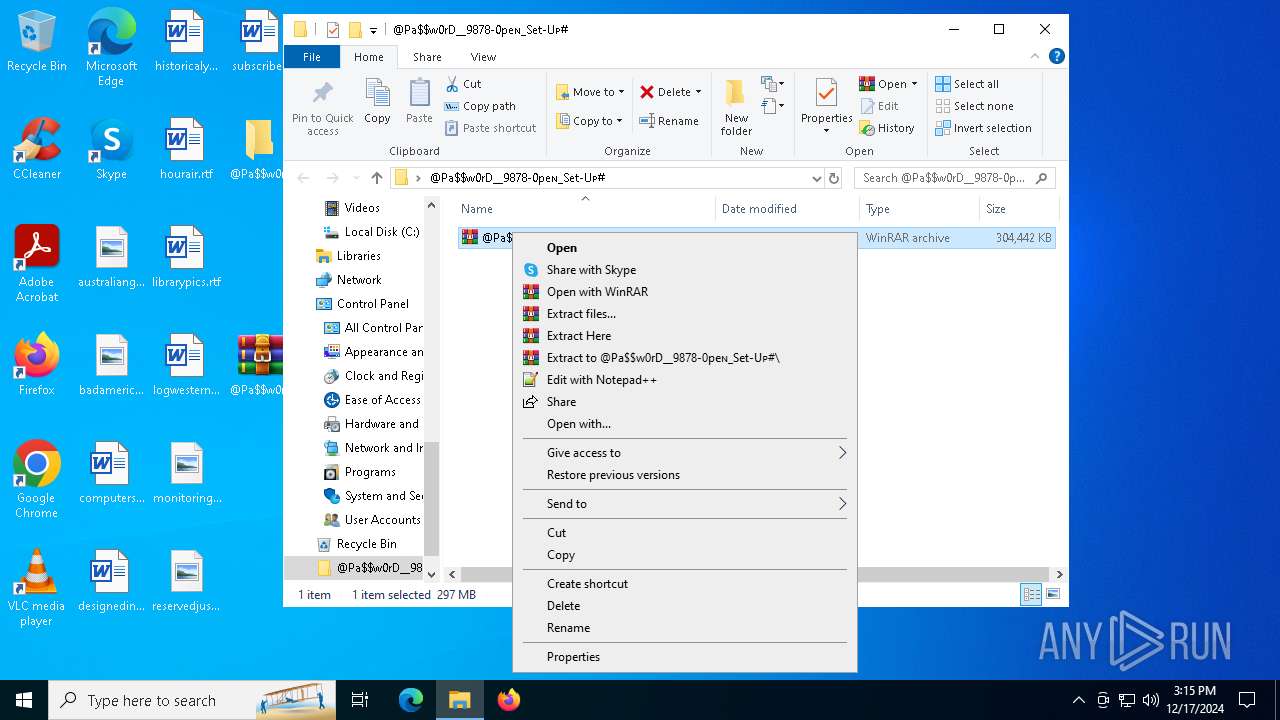
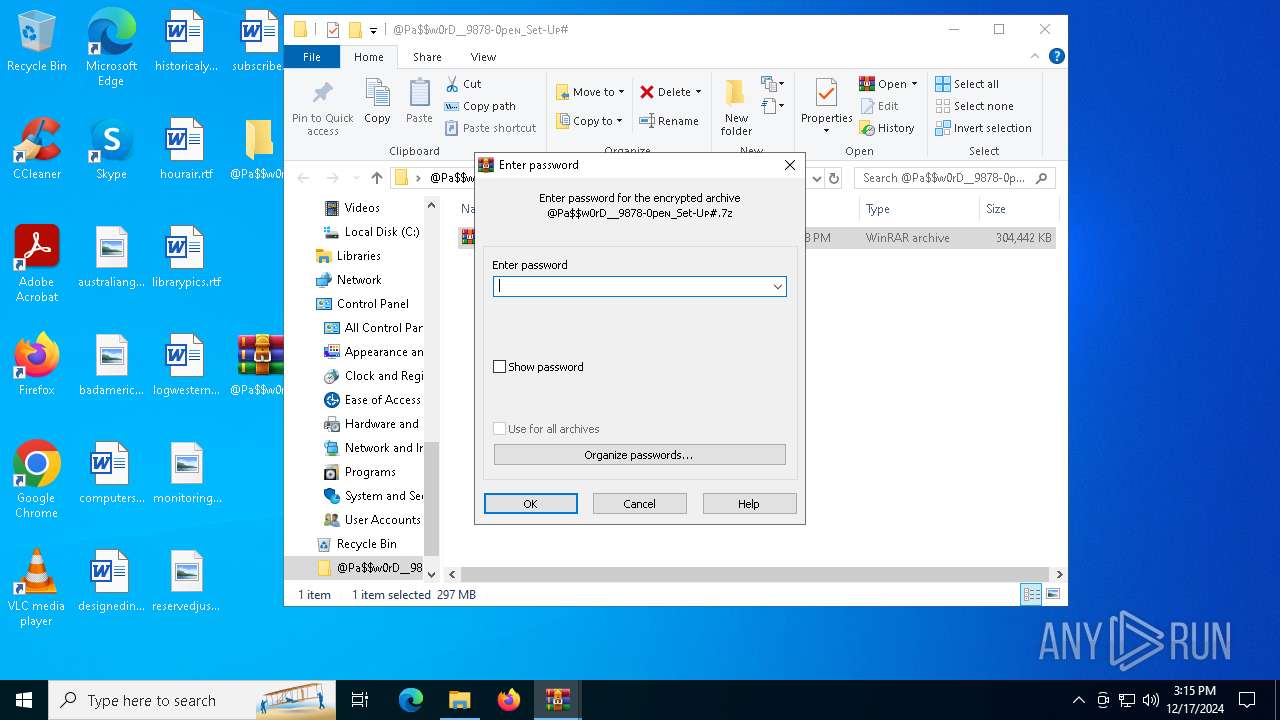
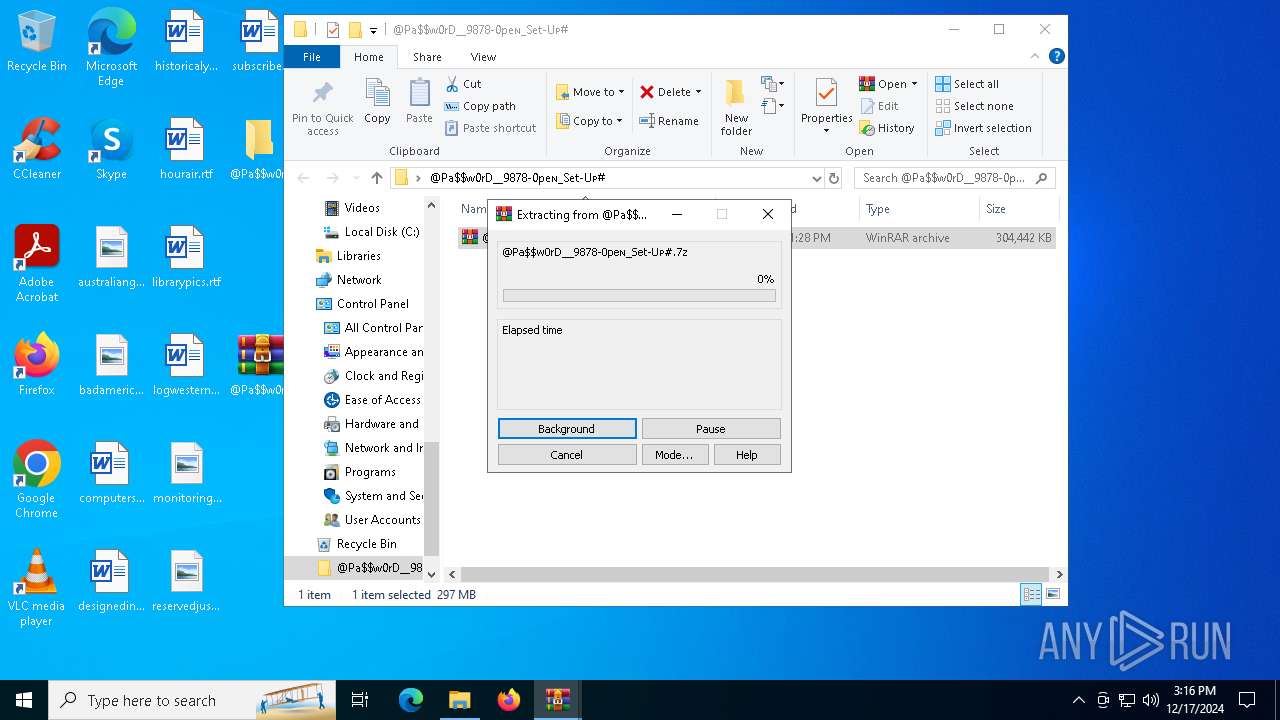
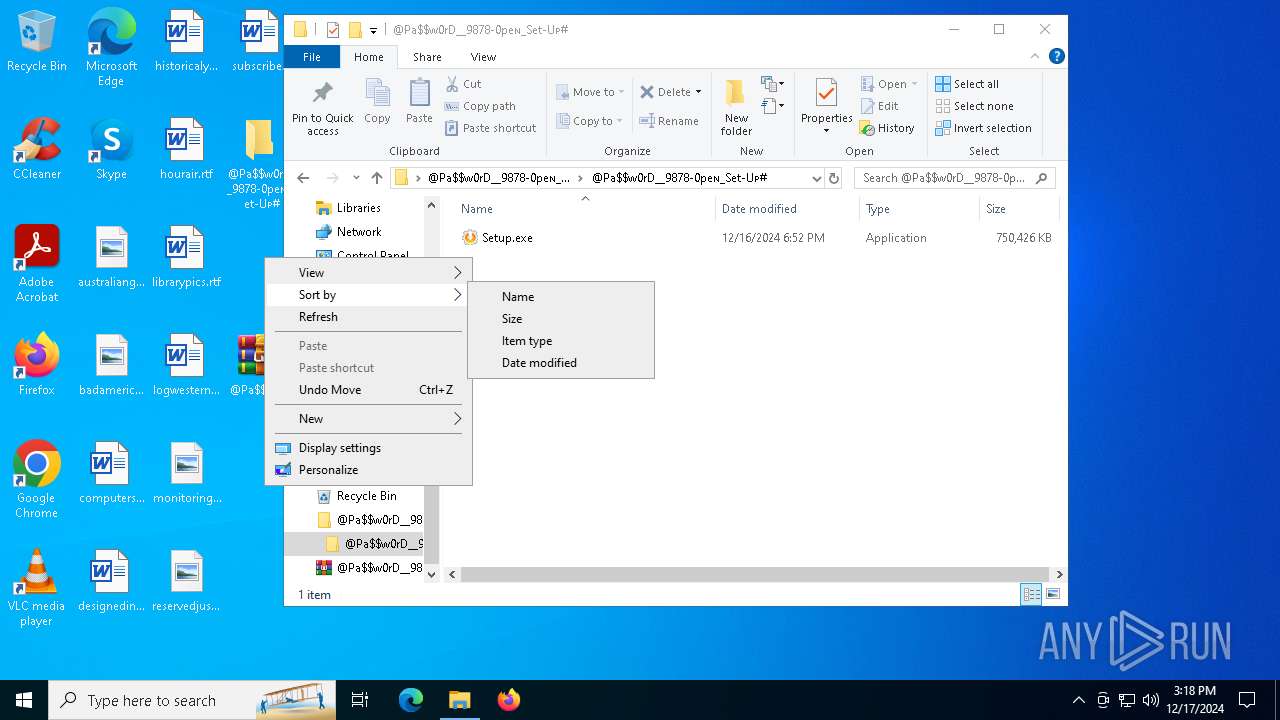
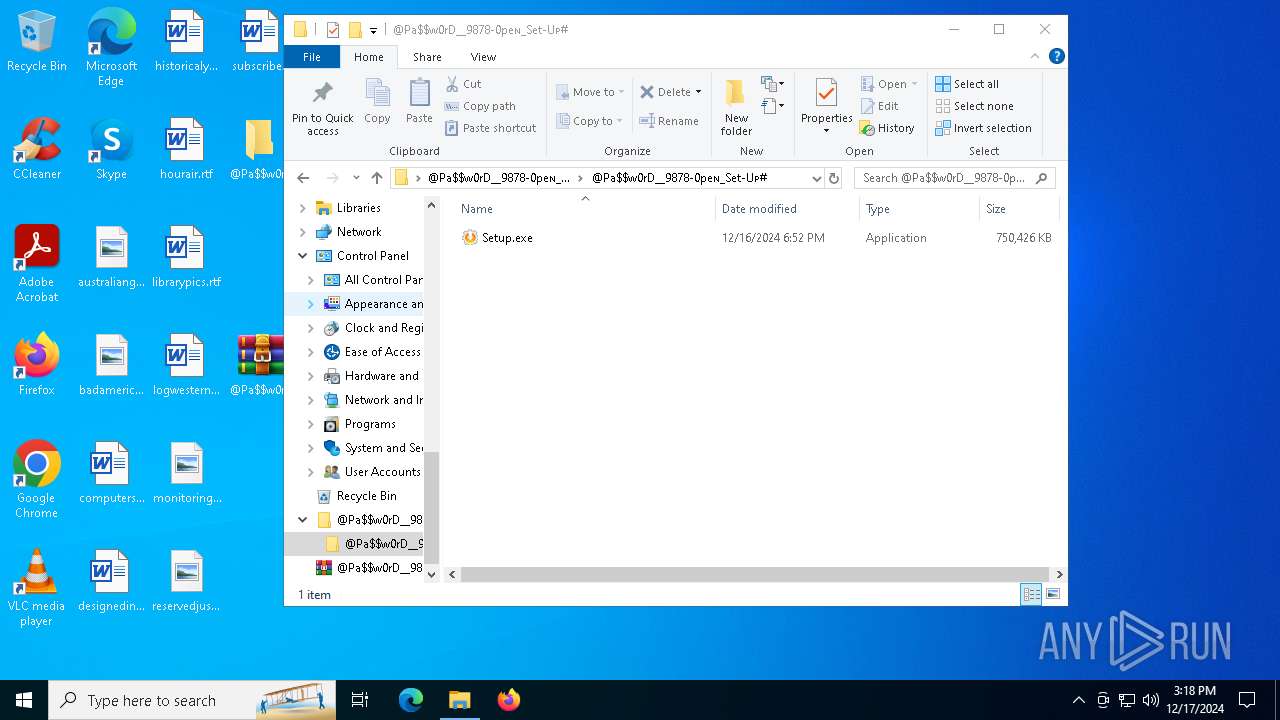
Manual execution by a user
- WinRAR.exe (PID: 6932)
- WinRAR.exe (PID: 6780)
- Setup.exe (PID: 5876)
The process uses the downloaded file
- WinRAR.exe (PID: 6932)
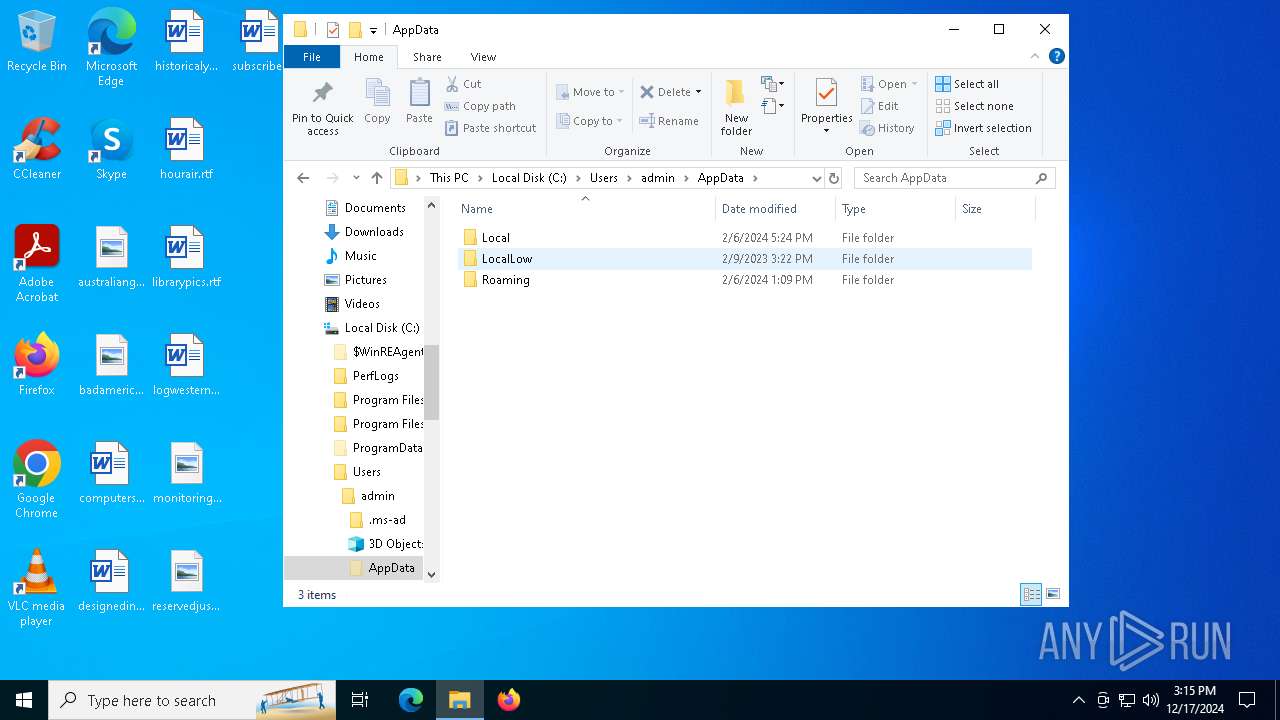
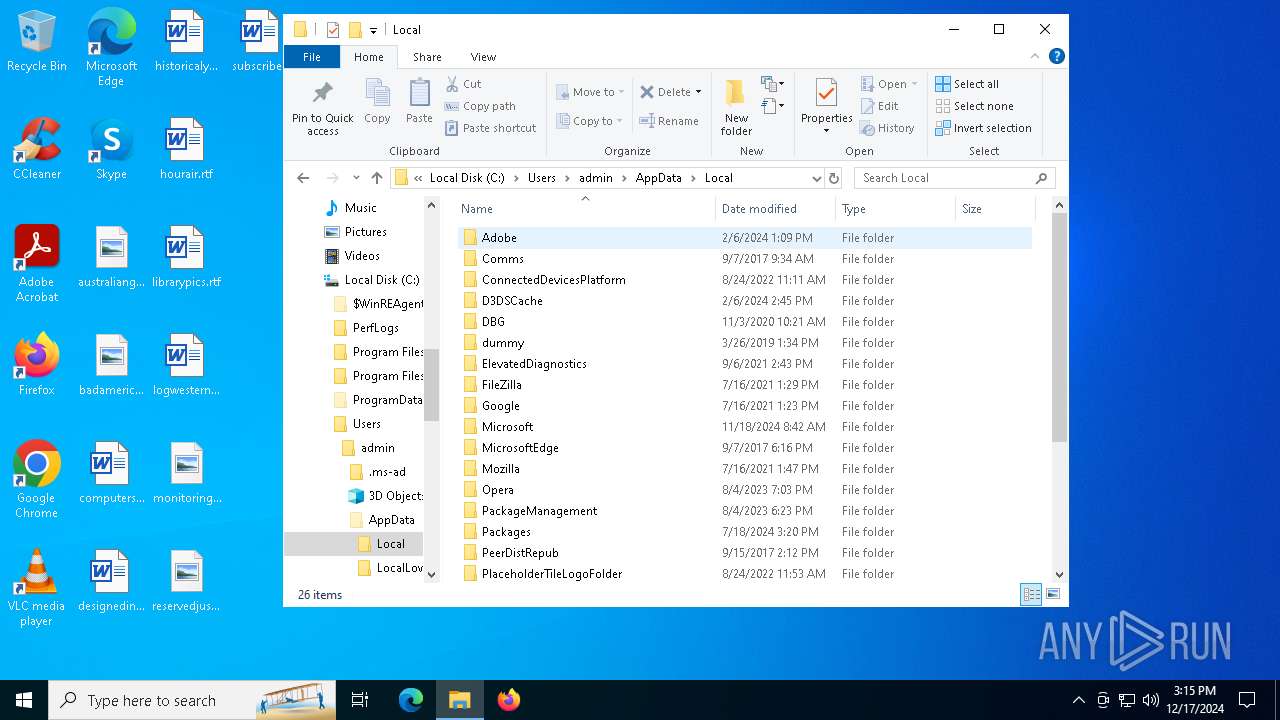
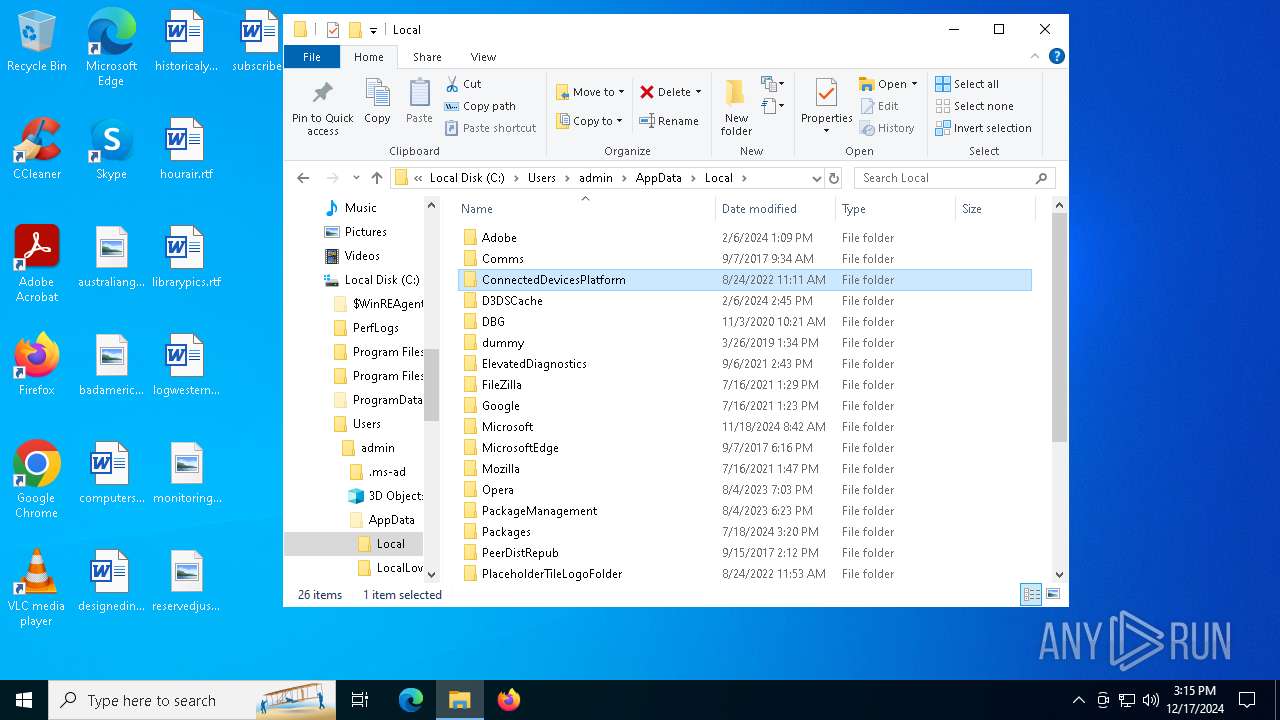
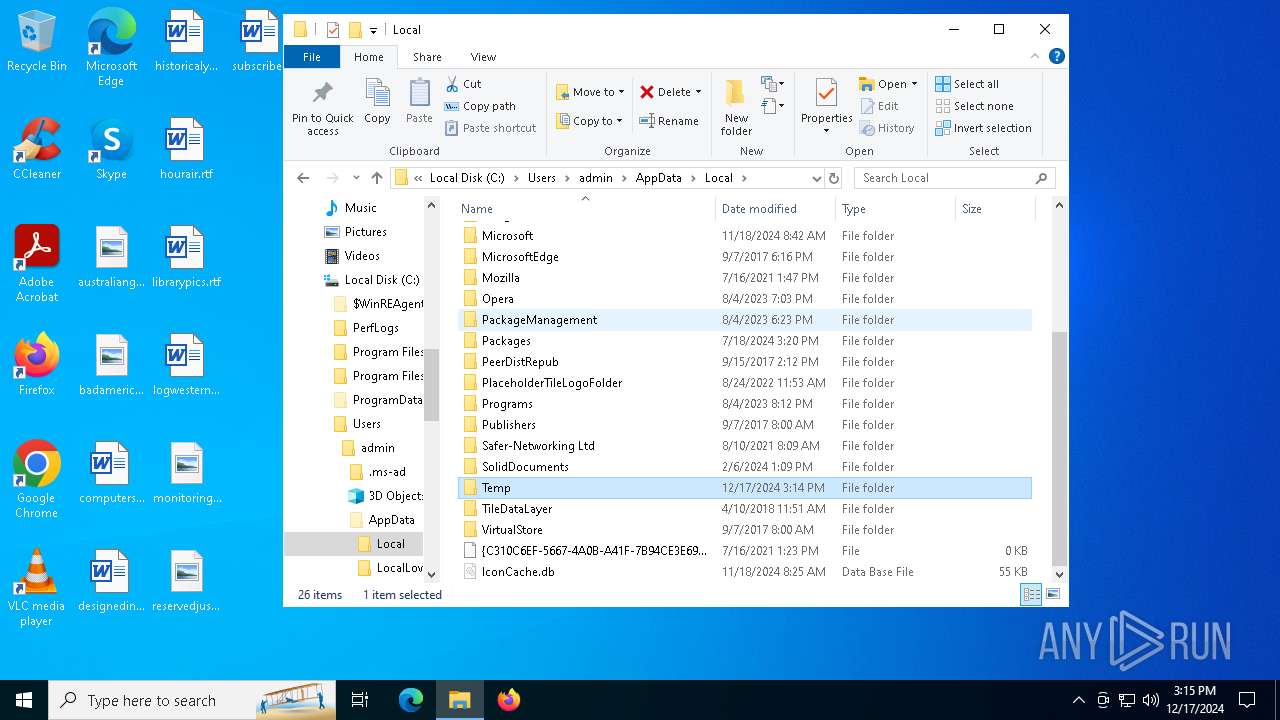
Create files in a temporary directory
- Setup.exe (PID: 5876)
Reads the machine GUID from the registry
- Setup.exe (PID: 5876)
Checks supported languages
- Setup.exe (PID: 5876)
- BitLockerToGo.exe (PID: 3952)
Reads the computer name
- BitLockerToGo.exe (PID: 3952)
Reads the software policy settings
- BitLockerToGo.exe (PID: 3952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 21 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | Enhanced Deflate using Deflate64(tm) |
| ZipModifyDate: | 2024:12:17 04:28:14 |
| ZipCRC: | 0x4a7bf473 |
| ZipCompressedSize: | 4580163 |
| ZipUncompressedSize: | 311748467 |
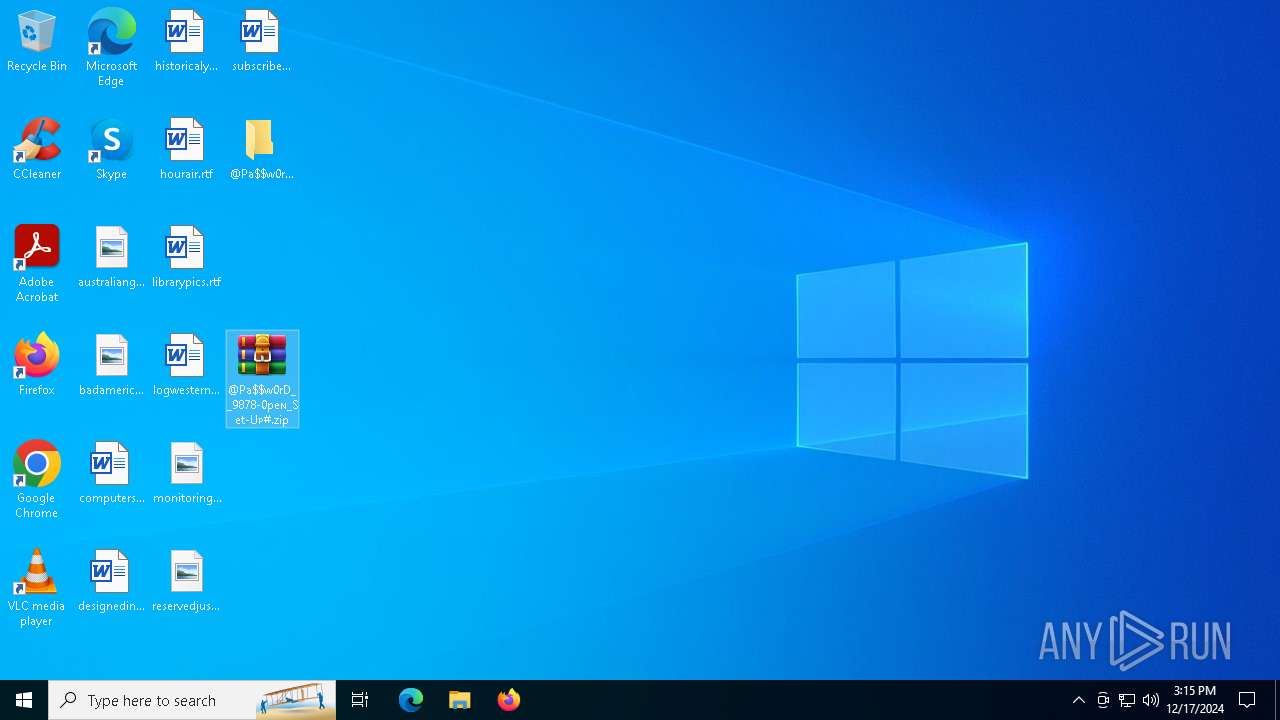
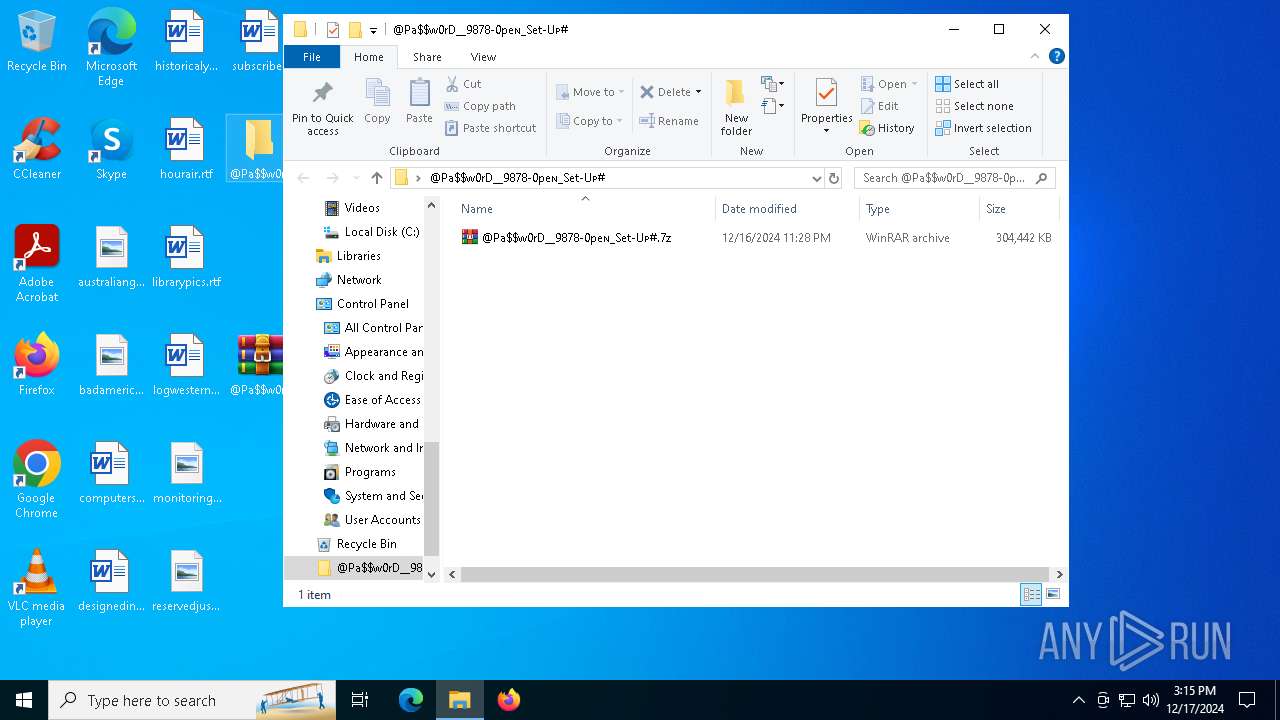
| ZipFileName: | @Pa$w0rD__9878-0peɴ_Set-Uᴘ#.7z |
Total processes
131
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
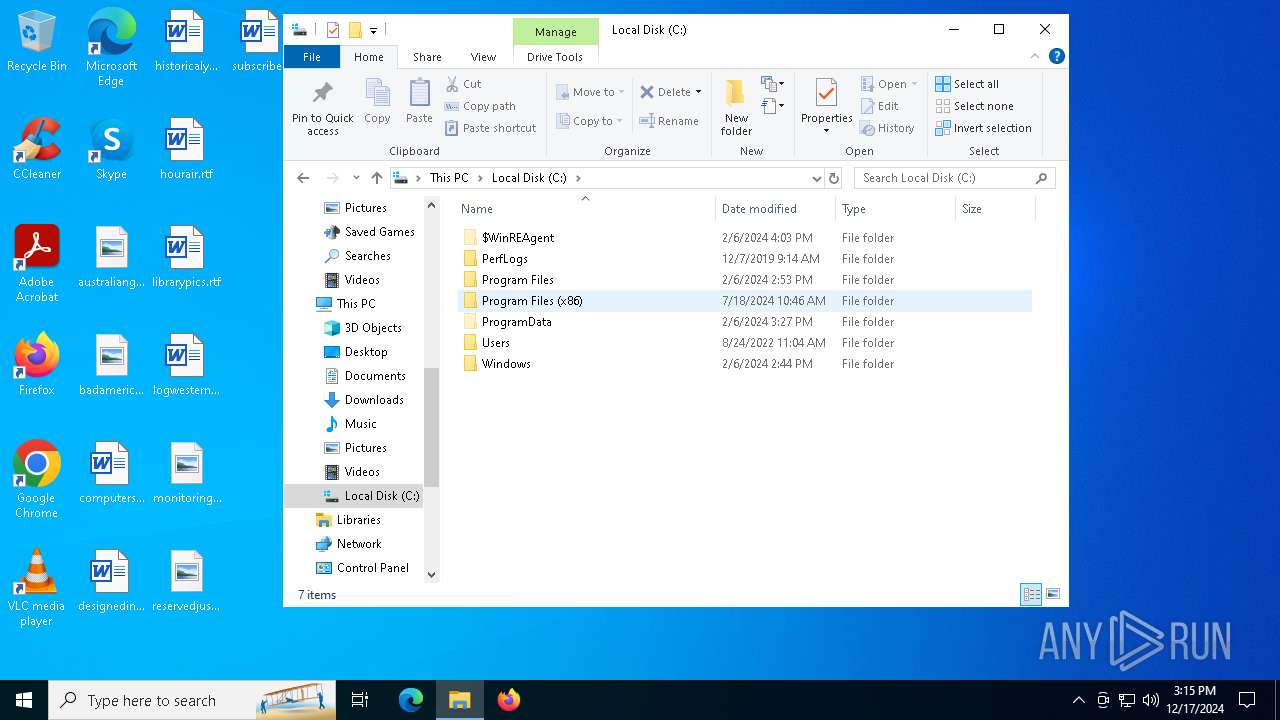
| 3952 | "C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe" | C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | Setup.exe | ||||||||||||
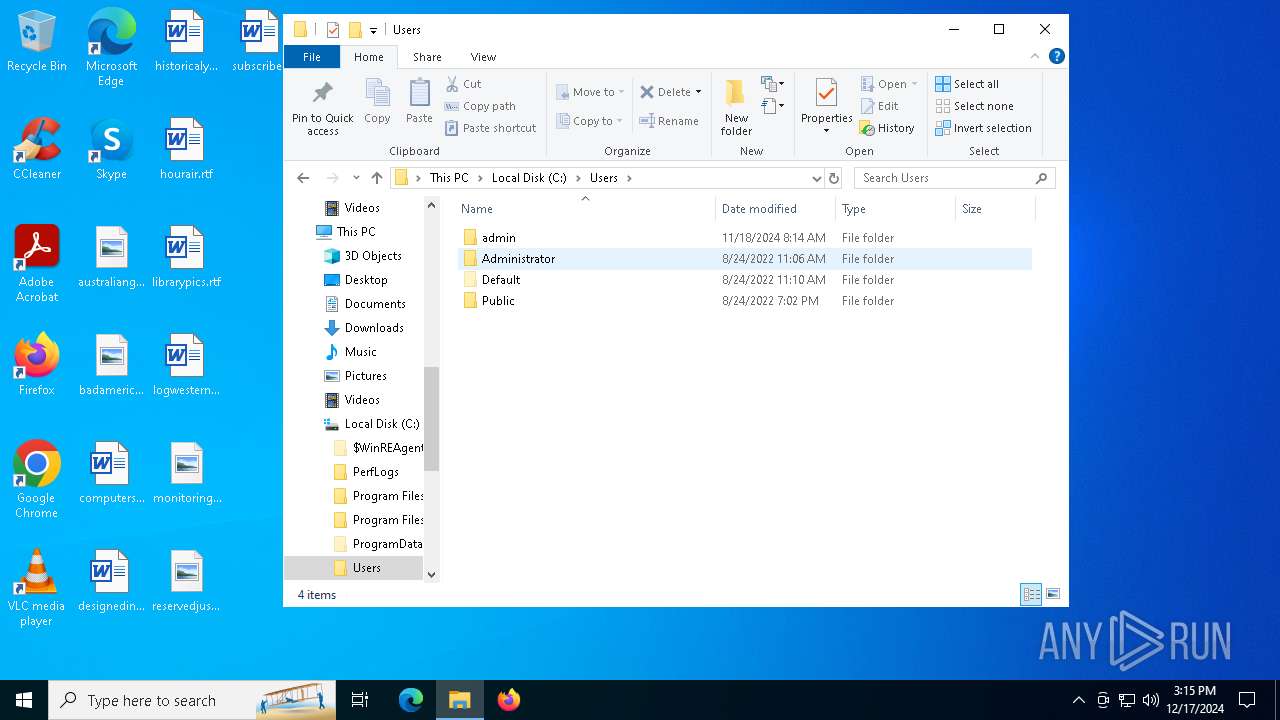
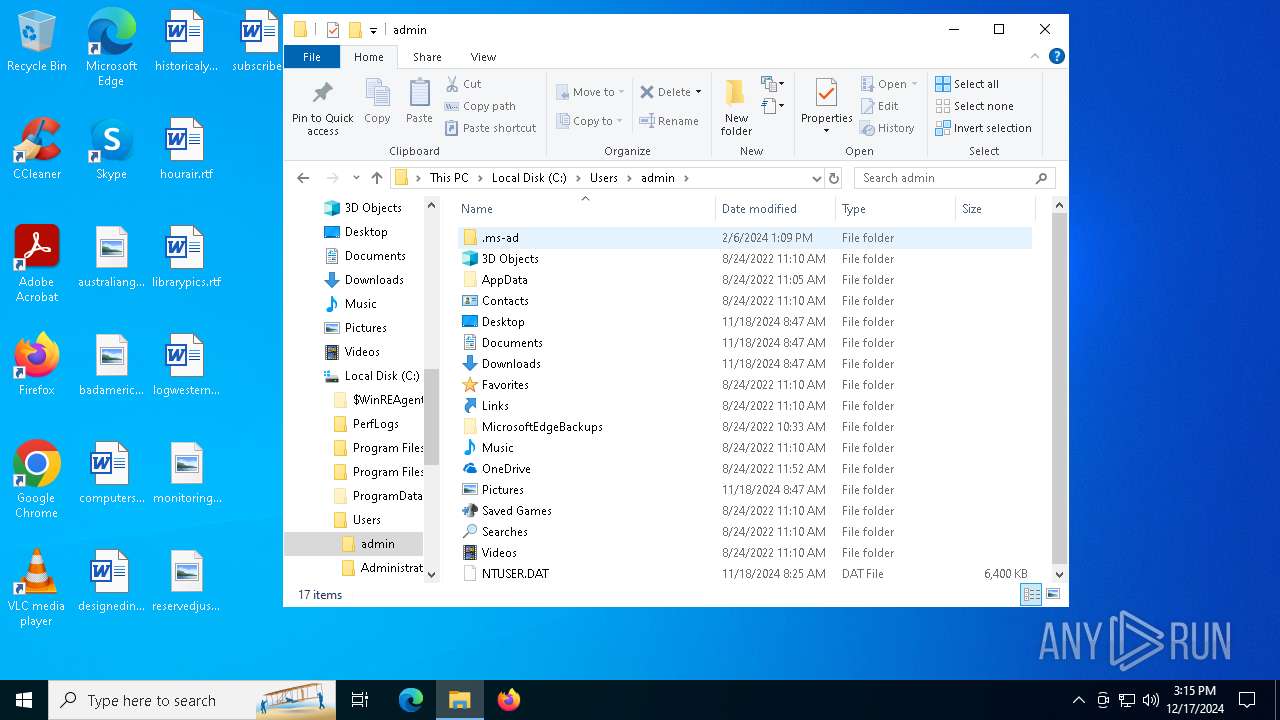
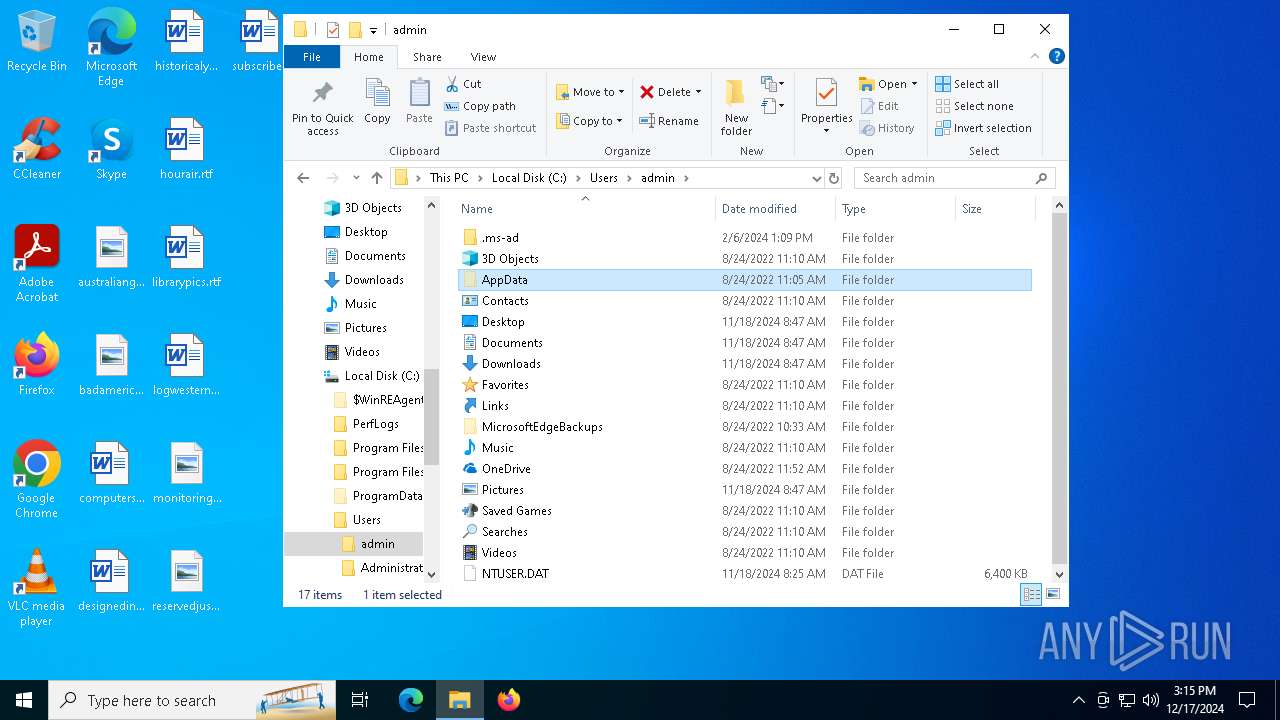
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BitLocker To Go Reader Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
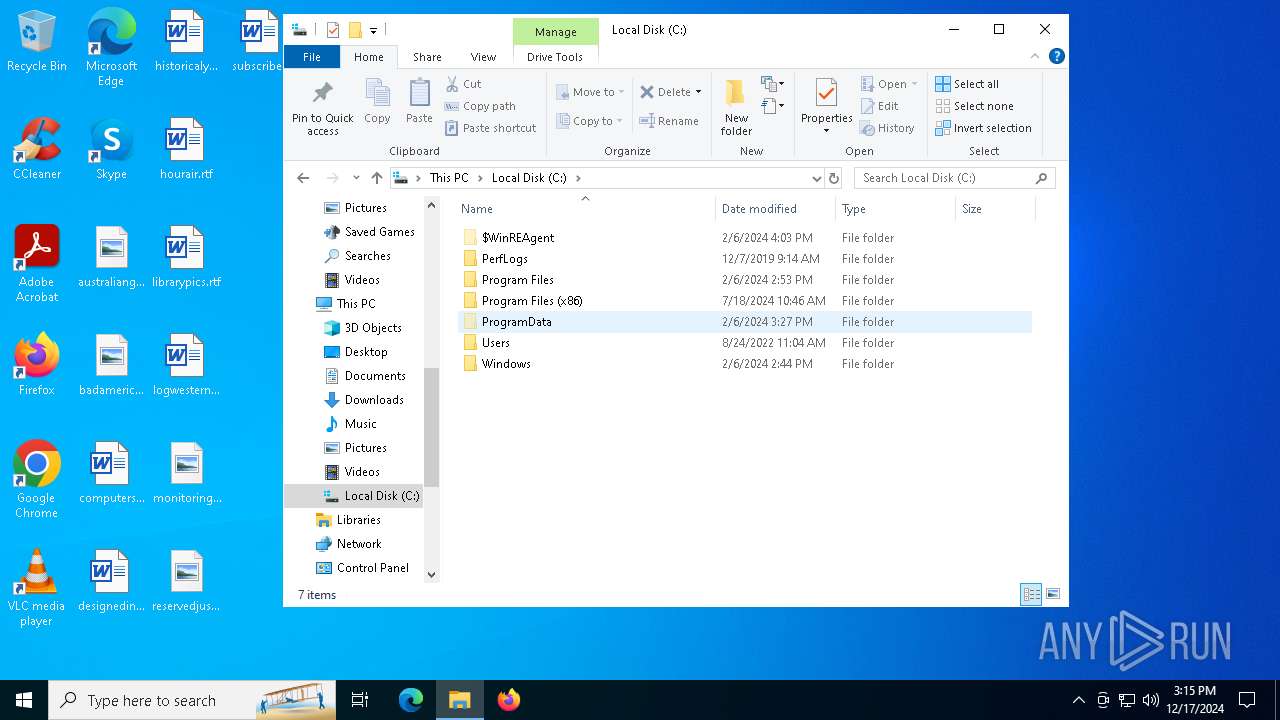
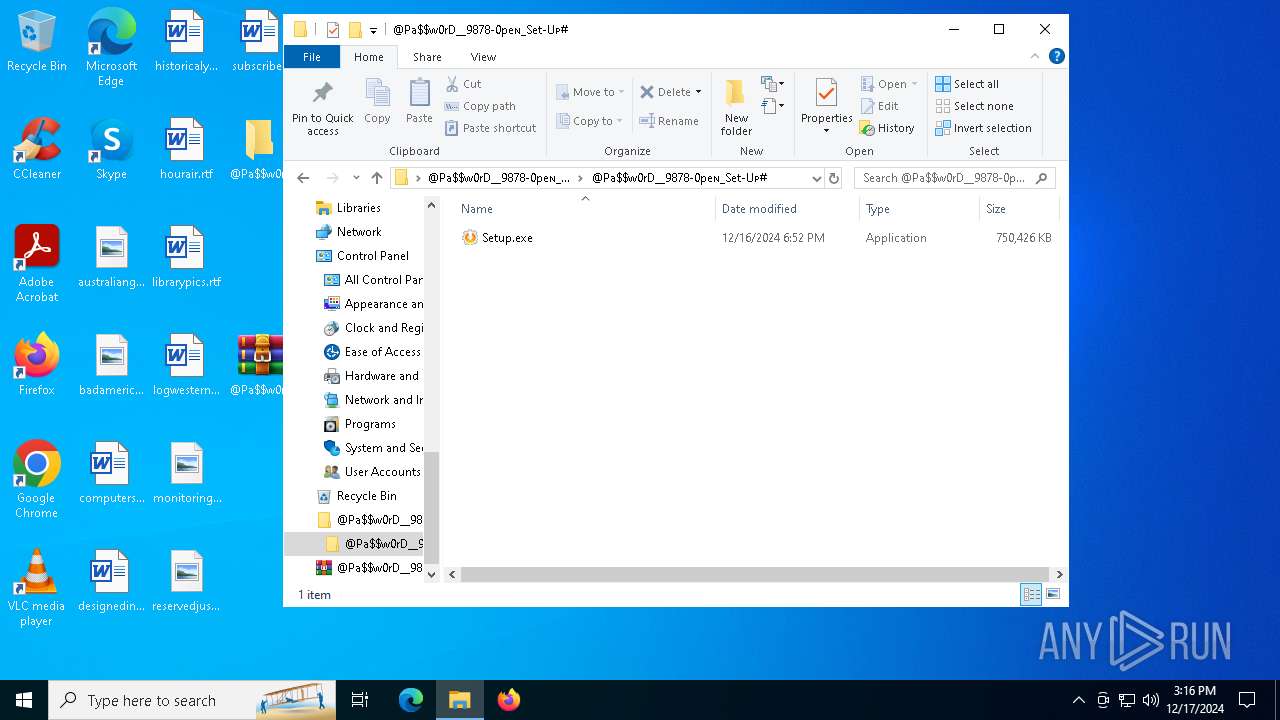
| 5876 | "C:\Users\admin\Desktop\@Pa$w0rD__9878-0peɴ_Set-Uᴘ#\@Pa$w0rD__9878-0peɴ_Set-Uᴘ#\Setup.exe" | C:\Users\admin\Desktop\@Pa$w0rD__9878-0peɴ_Set-Uᴘ#\@Pa$w0rD__9878-0peɴ_Set-Uᴘ#\Setup.exe | explorer.exe | ||||||||||||
User: admin Company: Systweak Software, 1999-2020 All rights reserved. Integrity Level: MEDIUM Description: Advanced Driver Updater Exit code: 666 Version: Advanced Driver Upda Modules
| |||||||||||||||
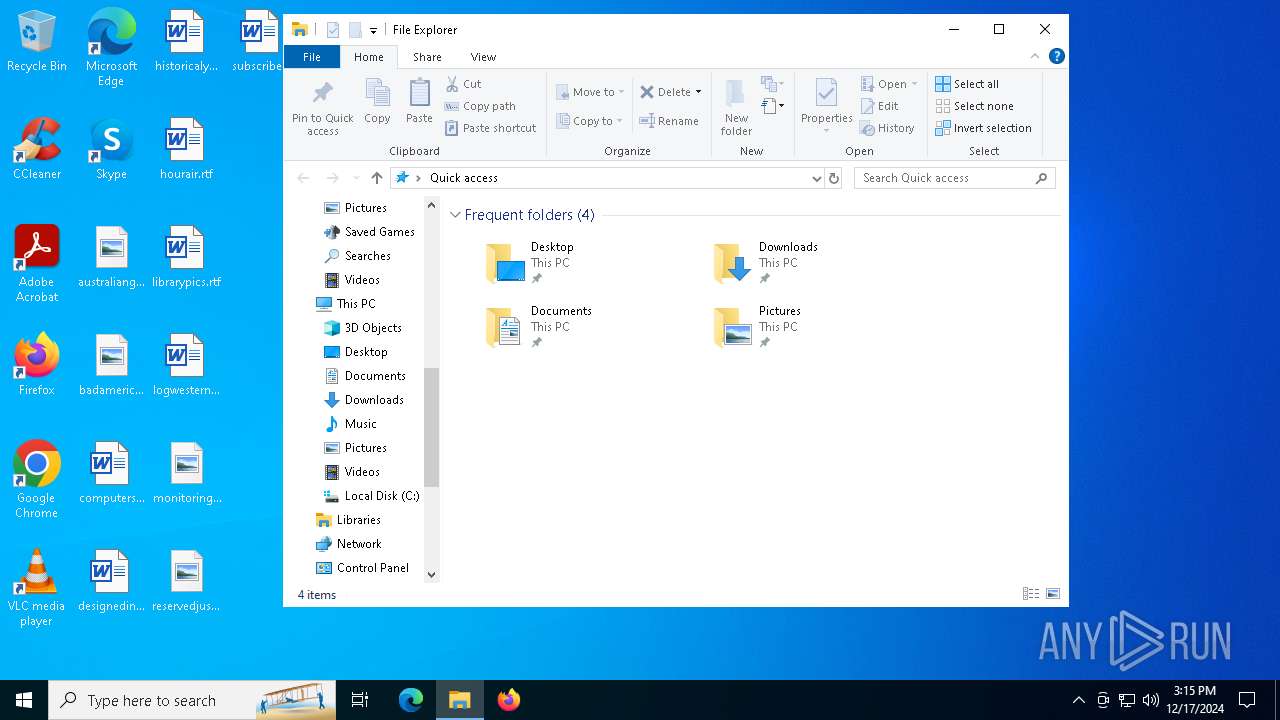
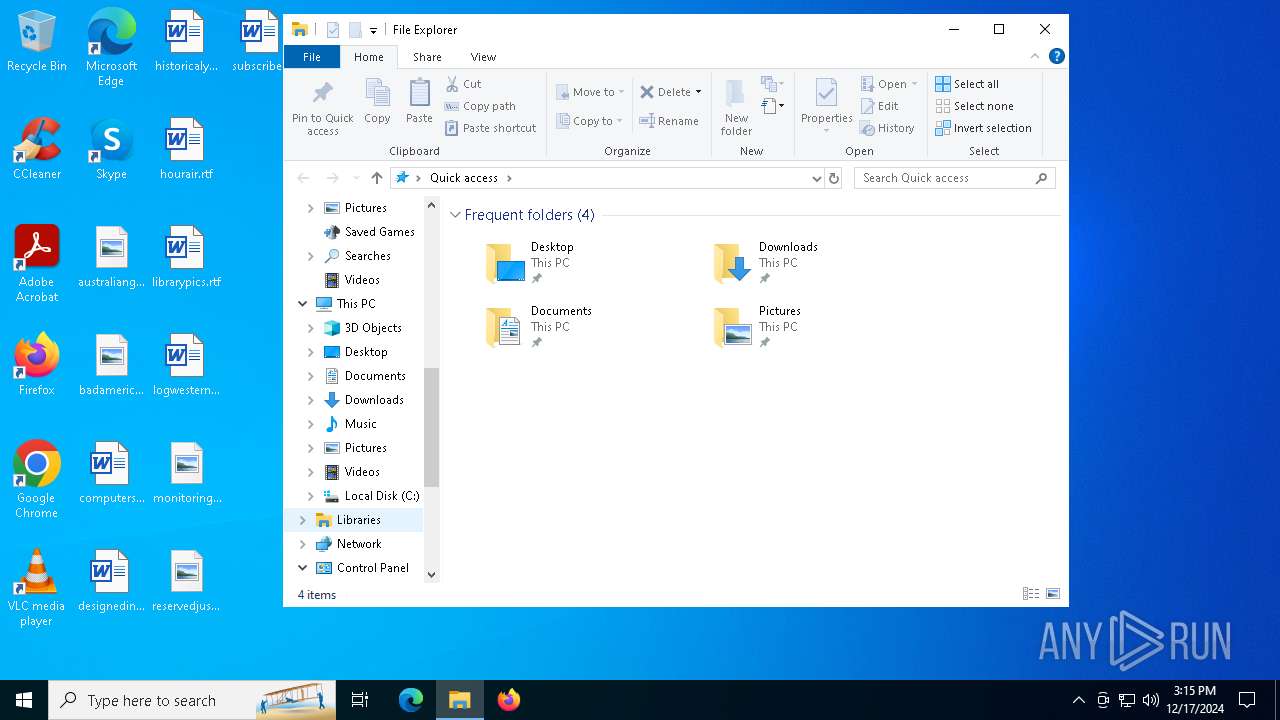
| 6500 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\@Pa$w0rD__9878-0peɴ_Set-Uᴘ#.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.91.0 Modules
| |||||||||||||||
| 6708 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
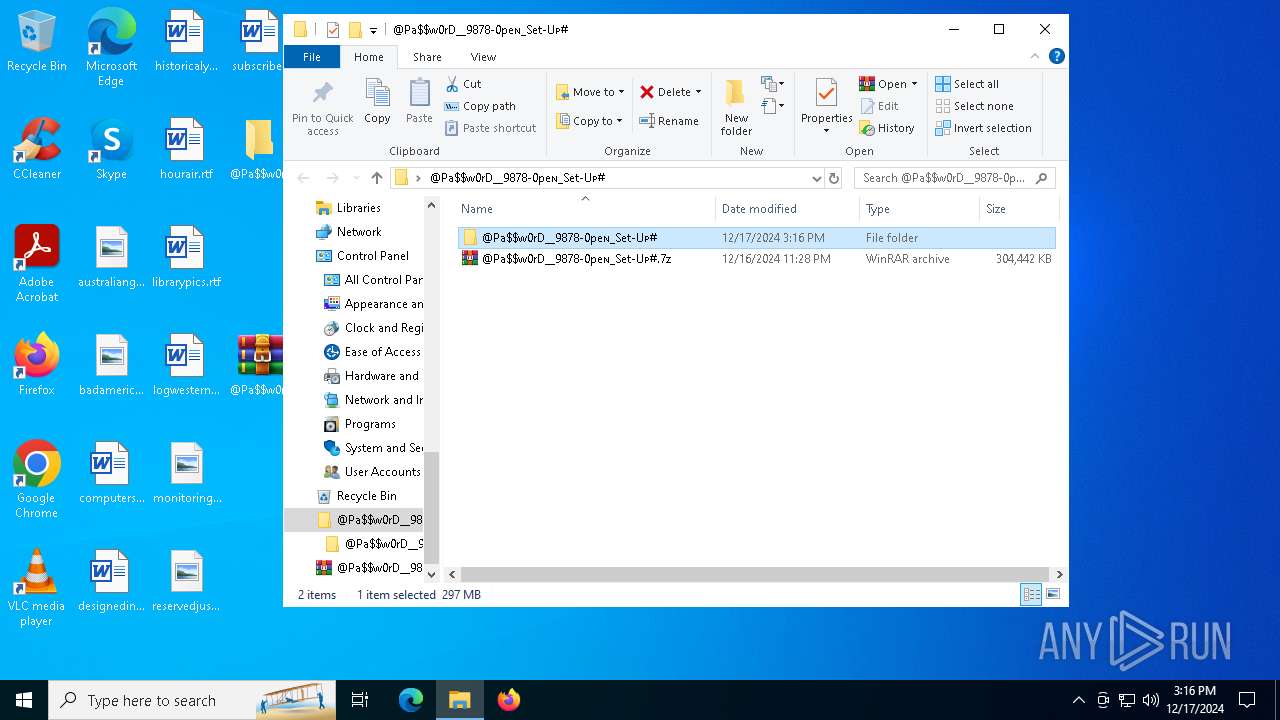
| 6780 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\@Pa$w0rD__9878-0peɴ_Set-Uᴘ#.zip" C:\Users\admin\Desktop\@Pa$w0rD__9878-0peɴ_Set-Uᴘ#\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6932 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\@Pa$w0rD__9878-0peɴ_Set-Uᴘ#\@Pa$w0rD__9878-0peɴ_Set-Uᴘ#.7z" C:\Users\admin\Desktop\@Pa$w0rD__9878-0peɴ_Set-Uᴘ#\@Pa$w0rD__9878-0peɴ_Set-Uᴘ#\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
3 388
Read events
3 365
Write events
23
Delete events
0
Modification events
| (PID) Process: | (6500) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6500) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6500) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6500) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6500) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_0 |
Value: 4C000000730100000402000000000000F0F0F00000000000000000000000000000000000000000007E00090000000000000000003B000000B402000000000000000000000000000001000000 | |||
| (PID) Process: | (6500) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_1 |
Value: 4C000000730100000500000000000000F0F0F00000000000000000000000000000000000000000009E0205000000000000000000180000002A00000000000000000000000000000002000000 | |||
| (PID) Process: | (6500) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_2 |
Value: 4C000000730100000400000000000000F0F0F0000000000000000000000000000000000000000000940205000000000000000000180000006400000000000000000000000000000003000000 | |||
| (PID) Process: | (6780) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6780) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6780) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6780 | WinRAR.exe | C:\Users\admin\Desktop\@Pa$w0rD__9878-0peɴ_Set-Uᴘ#\@Pa$w0rD__9878-0peɴ_Set-Uᴘ#.7z | — | |
MD5:— | SHA256:— | |||
| 6932 | WinRAR.exe | C:\Users\admin\Desktop\@Pa$w0rD__9878-0peɴ_Set-Uᴘ#\@Pa$w0rD__9878-0peɴ_Set-Uᴘ#\Setup.exe | — | |
MD5:— | SHA256:— | |||
| 5876 | Setup.exe | C:\Users\admin\AppData\Local\Temp\glfw.3936688304.dll | executable | |
MD5:4EC2D5A48D44C814F6AD68011E83A32B | SHA256:93CE68219CB0E920A0B9F04A38BBEFF104F530A643FD0A792215572525869F90 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
46
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
4544 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4544 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6408 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 92.123.104.29:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1076 | svchost.exe | 69.192.162.125:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
r.bing.com |
| whitelisted |
fp.msedge.net |
| whitelisted |