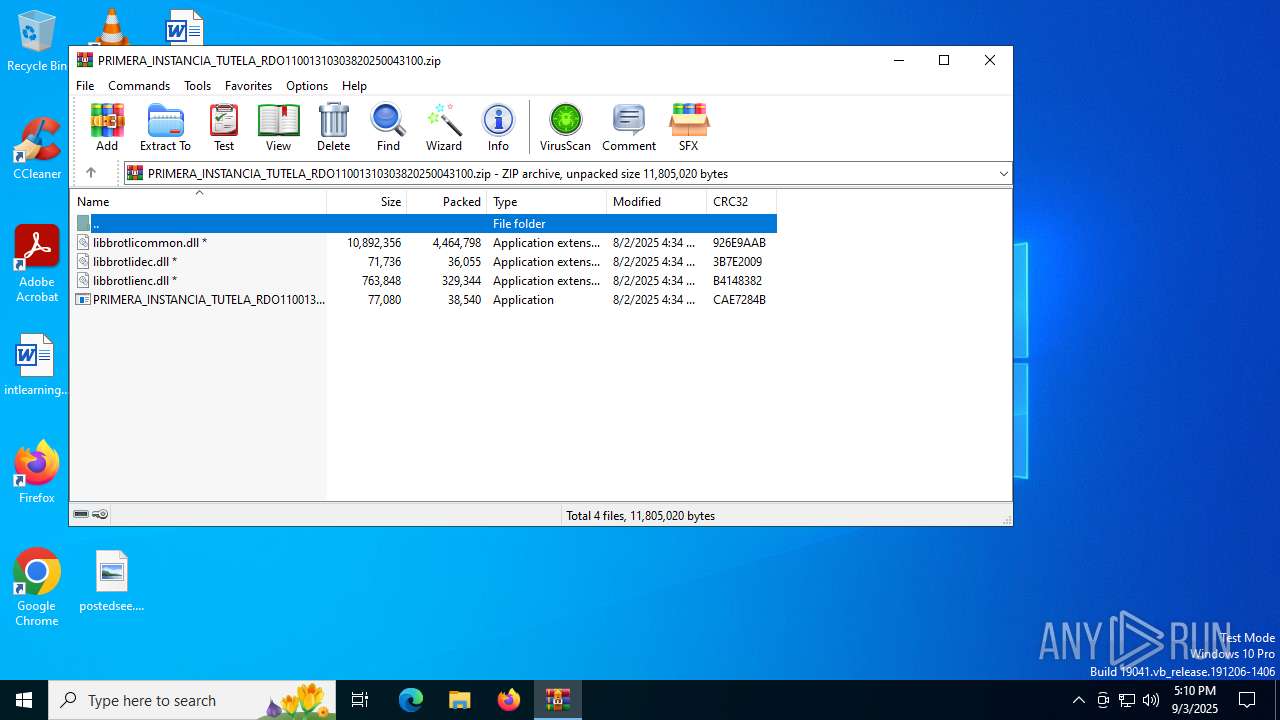
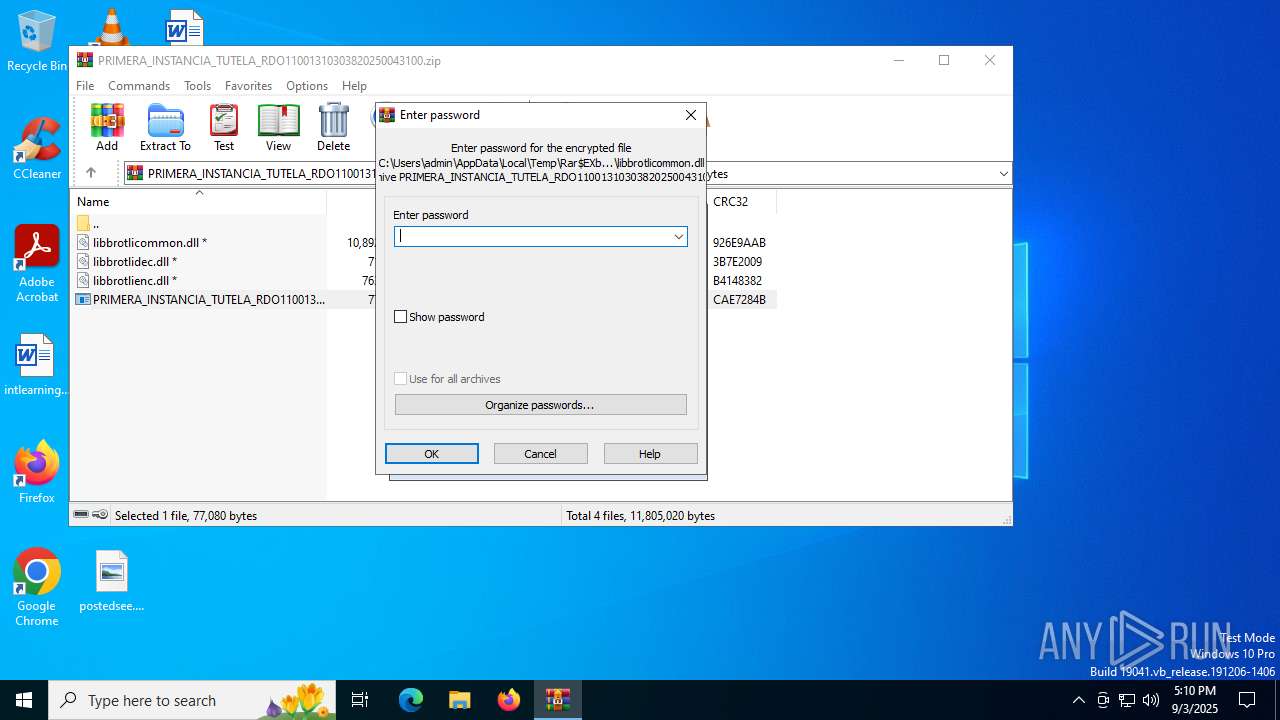
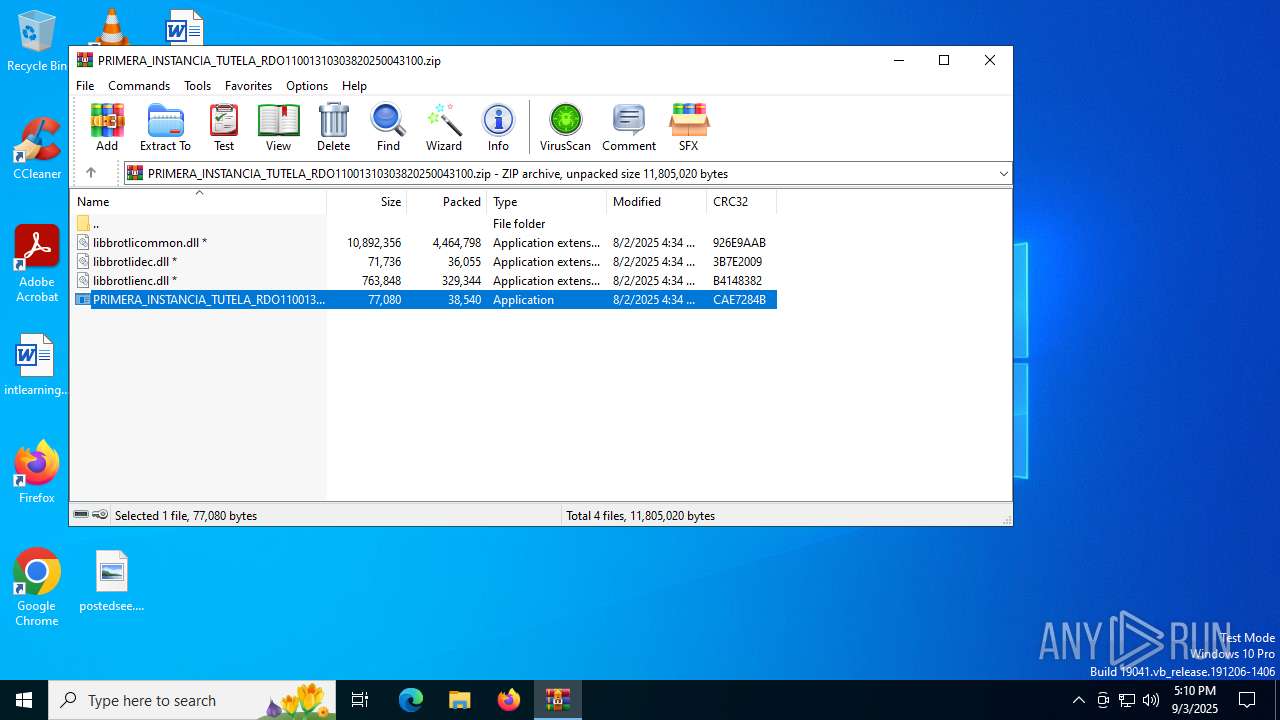
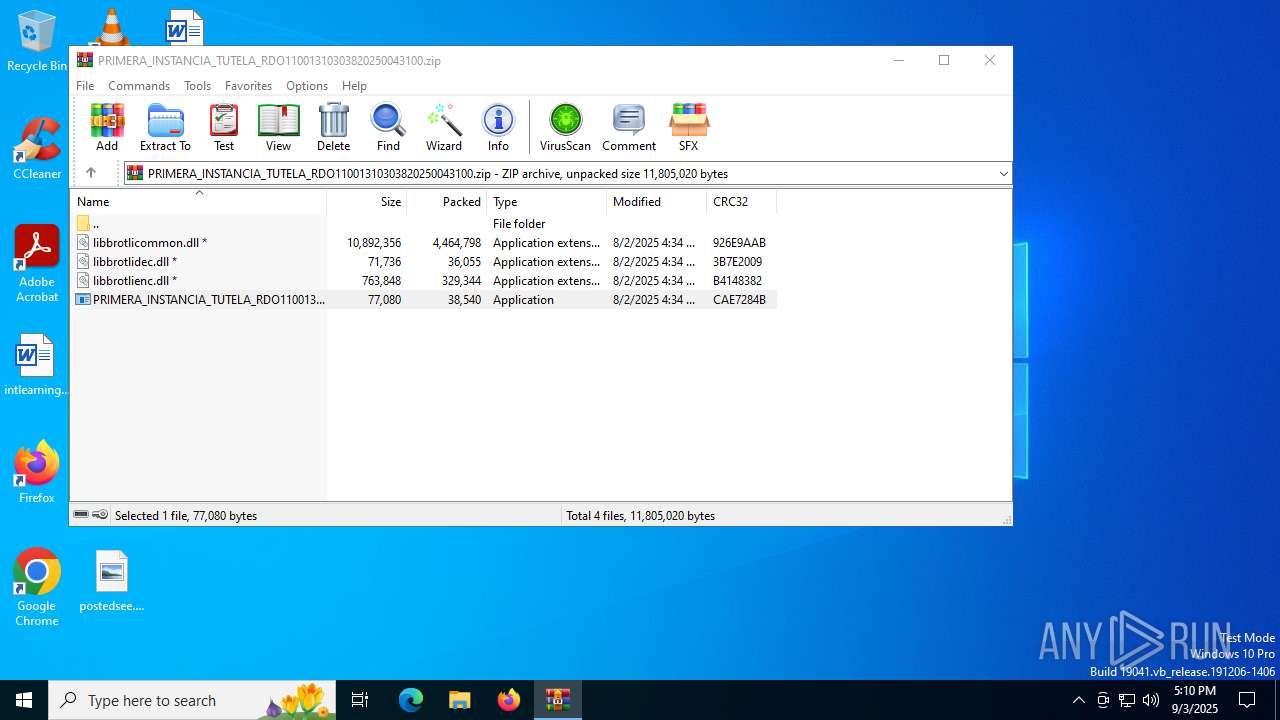
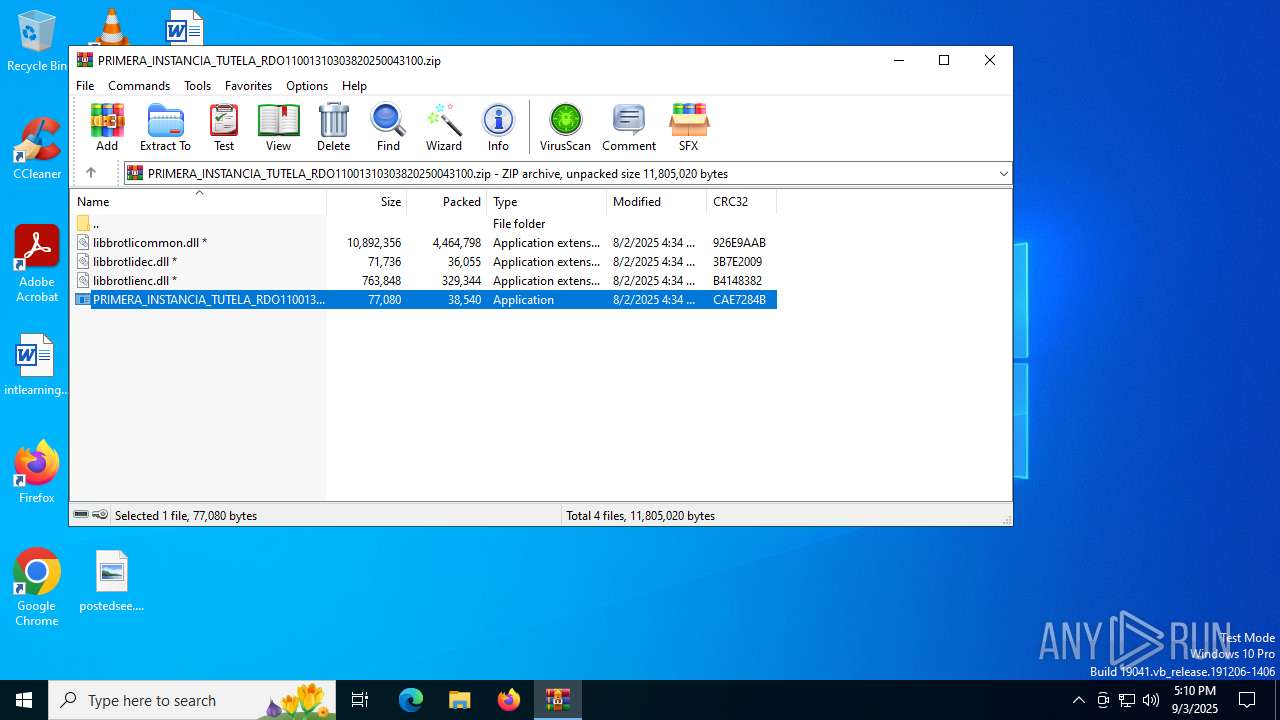
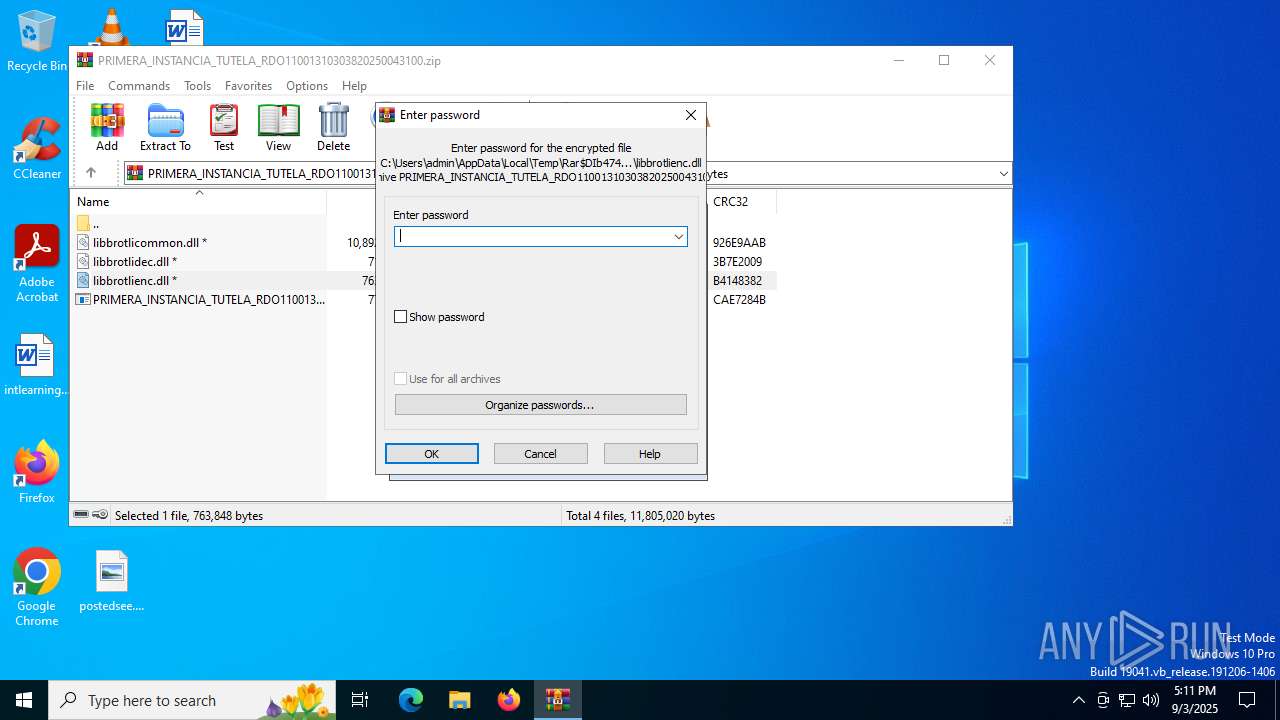
| File name: | PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.zip |
| Full analysis: | https://app.any.run/tasks/46648019-0403-4080-b4b3-532954be0658 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | September 03, 2025, 17:10:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
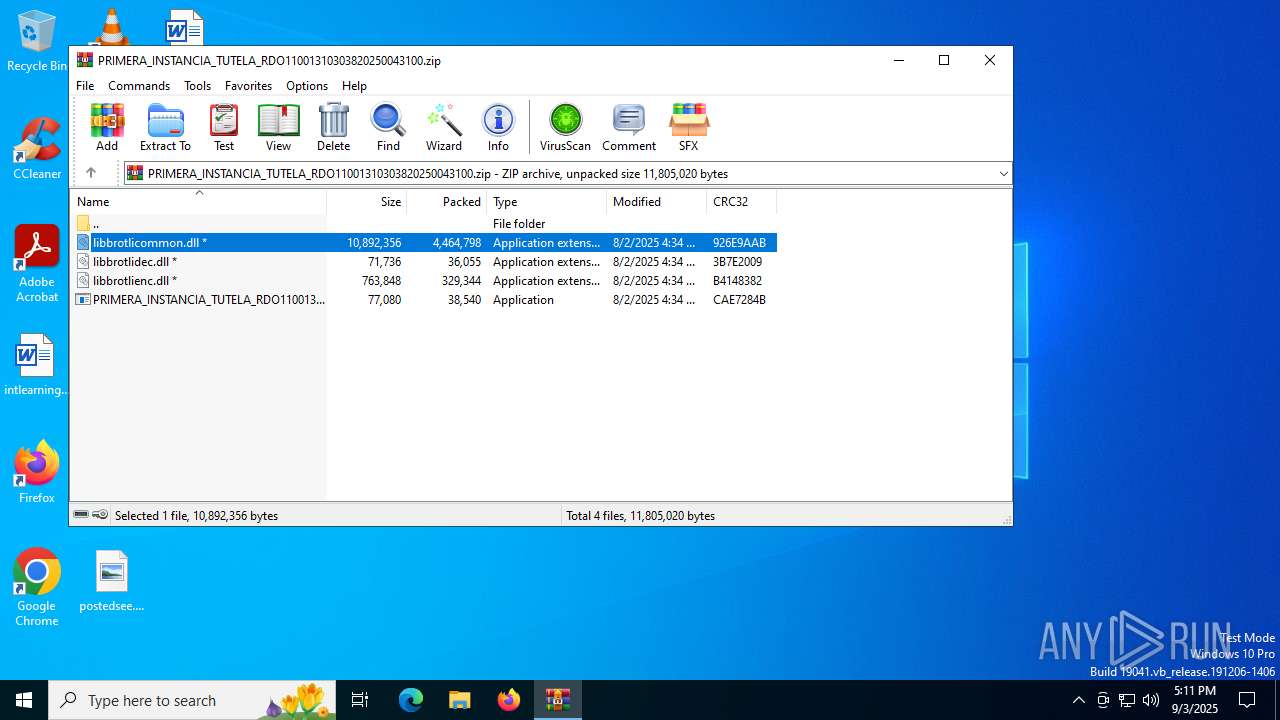
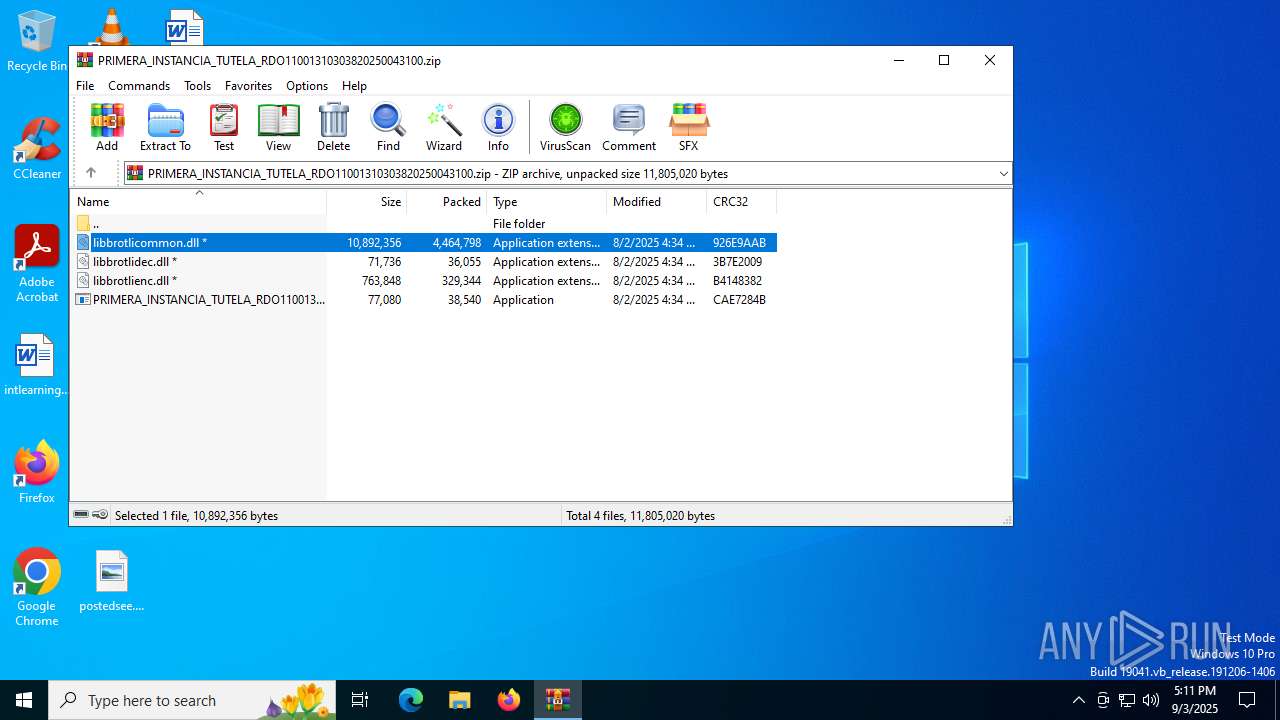
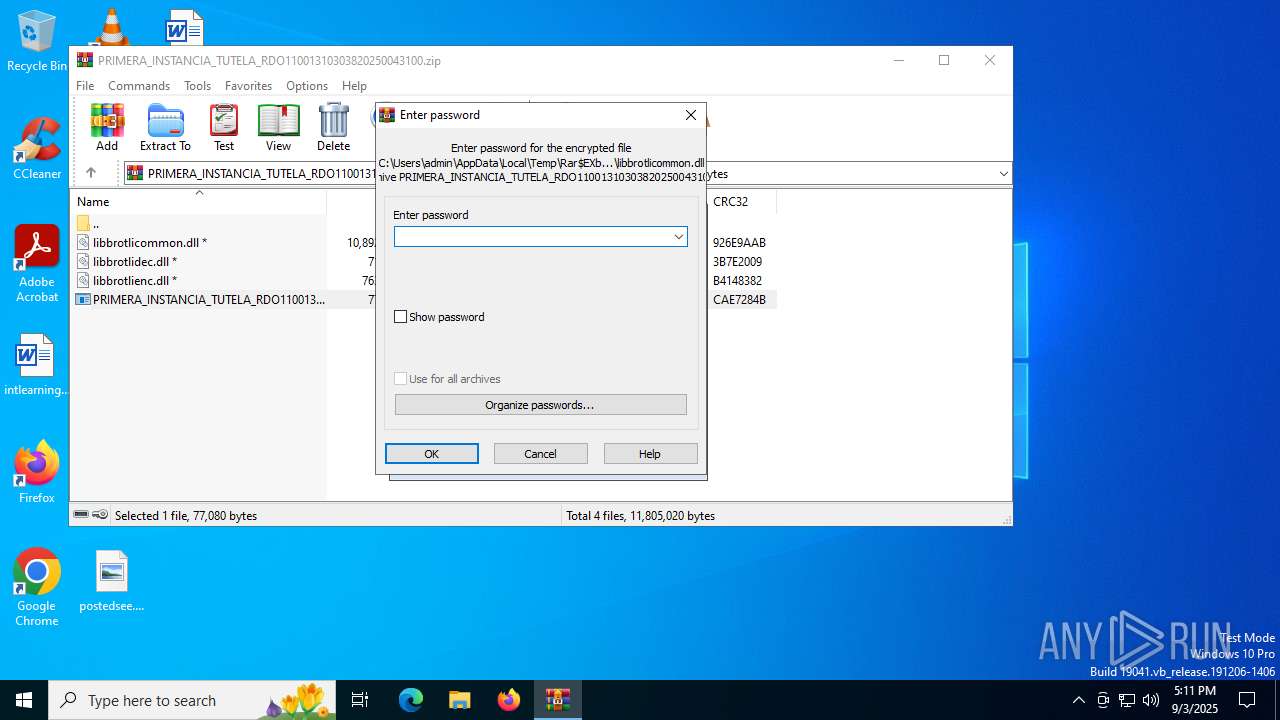
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 53CF4178B3CD378309994E42947734F1 |
| SHA1: | C247389794CEAD2E3268517C022A7362995620E4 |
| SHA256: | ABD3C7DD4F88807EBB68C2EDA852BFB1D18CABC8000987E9970DB0195637EDF1 |
| SSDEEP: | 98304:hnI+KONWwsSULKGZ7oUgSkXxsW4Mp4aE+3X+XsWa1vfcgdZlWlOhr88yzlclqokn:CtPpCM |
MALICIOUS
Changes the autorun value in the registry
- PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe (PID: 1800)
- PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe (PID: 684)
DCRAT mutex has been found
- AddInProcess32.exe (PID: 1212)
- AddInProcess32.exe (PID: 6940)
ASYNCRAT has been detected (SURICATA)
- AddInProcess32.exe (PID: 1212)
ASYNCRAT has been detected (YARA)
- AddInProcess32.exe (PID: 1212)
SUSPICIOUS
Executable content was dropped or overwritten
- PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe (PID: 1800)
Executes application which crashes
- PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe (PID: 1800)
- PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe (PID: 684)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4744)
Connects to unusual port
- AddInProcess32.exe (PID: 1212)
Contacting a server suspected of hosting an CnC
- AddInProcess32.exe (PID: 1212)
INFO
Checks supported languages
- PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe (PID: 1800)
- AddInProcess32.exe (PID: 1212)
- AddInProcess32.exe (PID: 6940)
- PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe (PID: 684)
Launching a file from a Registry key
- PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe (PID: 1800)
- PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe (PID: 684)
Reads the computer name
- AddInProcess32.exe (PID: 1212)
- AddInProcess32.exe (PID: 6940)
Reads the machine GUID from the registry
- AddInProcess32.exe (PID: 1212)
- AddInProcess32.exe (PID: 6940)
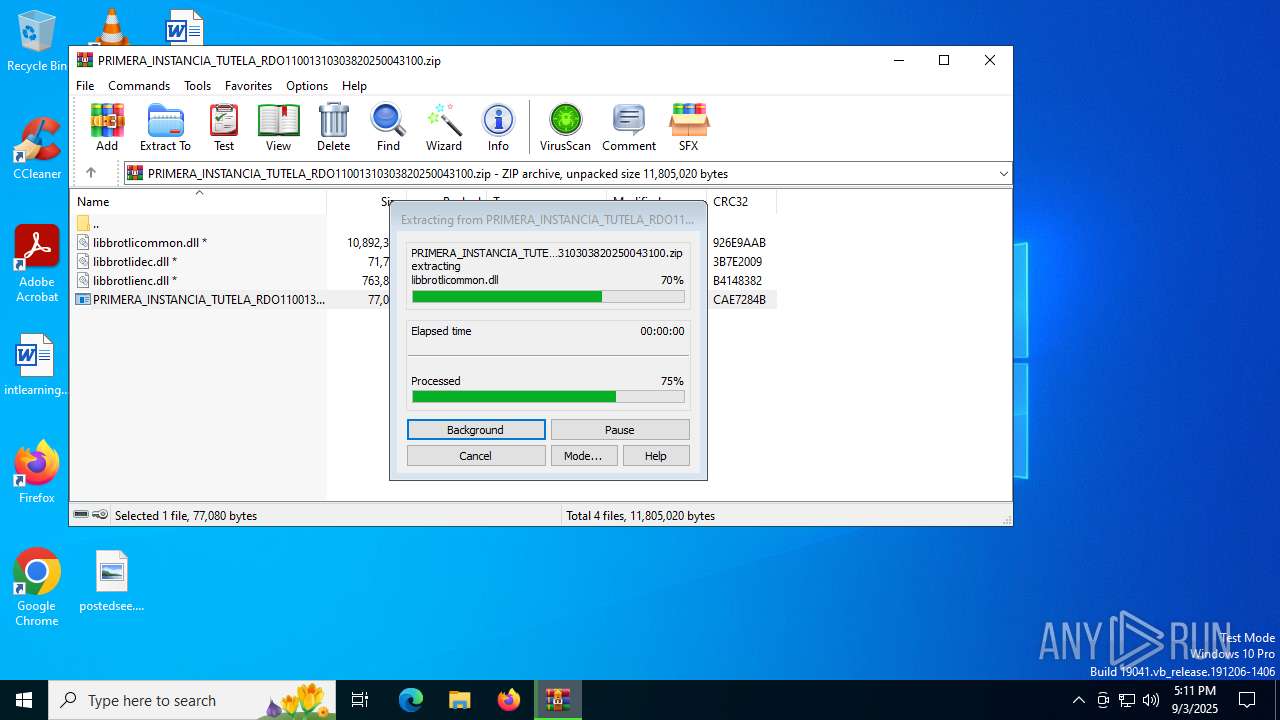
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4744)
Creates files or folders in the user directory
- WerFault.exe (PID: 5576)
- WerFault.exe (PID: 6356)
Checks proxy server information
- WerFault.exe (PID: 5576)
- WerFault.exe (PID: 6356)
Reads the software policy settings
- WerFault.exe (PID: 5576)
- WerFault.exe (PID: 6356)
- AddInProcess32.exe (PID: 1212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(1212) AddInProcess32.exe
C2 (1)167.160.161.43
Ports (1)1888
Version1.0.7
Options
AutoRunfalse
MutexDcRatMutex_qwqdanchun
InstallFolder%AppData%
Certificates
Cert1MIICMDCCAZmgAwIBAgIVAIjqTtxWY28K26eGFx+B3Y5GvrZvMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDERjUmF0IFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTI0MDkyNzEzMTI1MVoXDTM1MDcwNzEzMTI1MVowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A...
Server_SignaturecqSfFiIV9iQ8EHZHCBIkbnUcqWILJv83v9OvWkFOT1NSU42/JeJbOxOP6mviQxv/CyX3Exyu91r5sWSWp3nAs7Fz26DzEa2hWM9Rr2yUi71/GrmbMtVOG9nkHwMrC92wrXTwV+Ja62Ym9rcUpSOFBy5aZCcWwgHMguo/0h6ilOc=
Keys
AES4f499245f7569363776215d51f07169e8c78c3162830425005c0b72fa4081af0
SaltDcRatByqwqdanchun
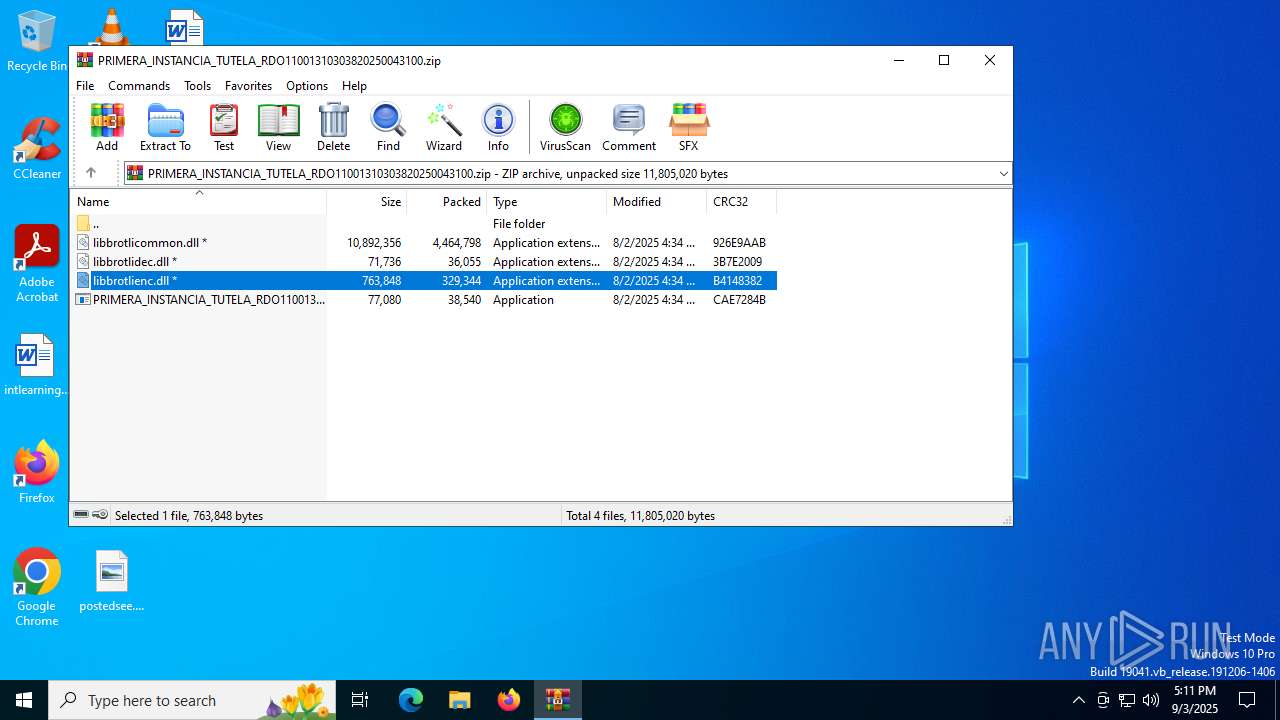
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:08:02 11:34:28 |
| ZipCRC: | 0x926e9aab |
| ZipCompressedSize: | 4464798 |
| ZipUncompressedSize: | 10892356 |
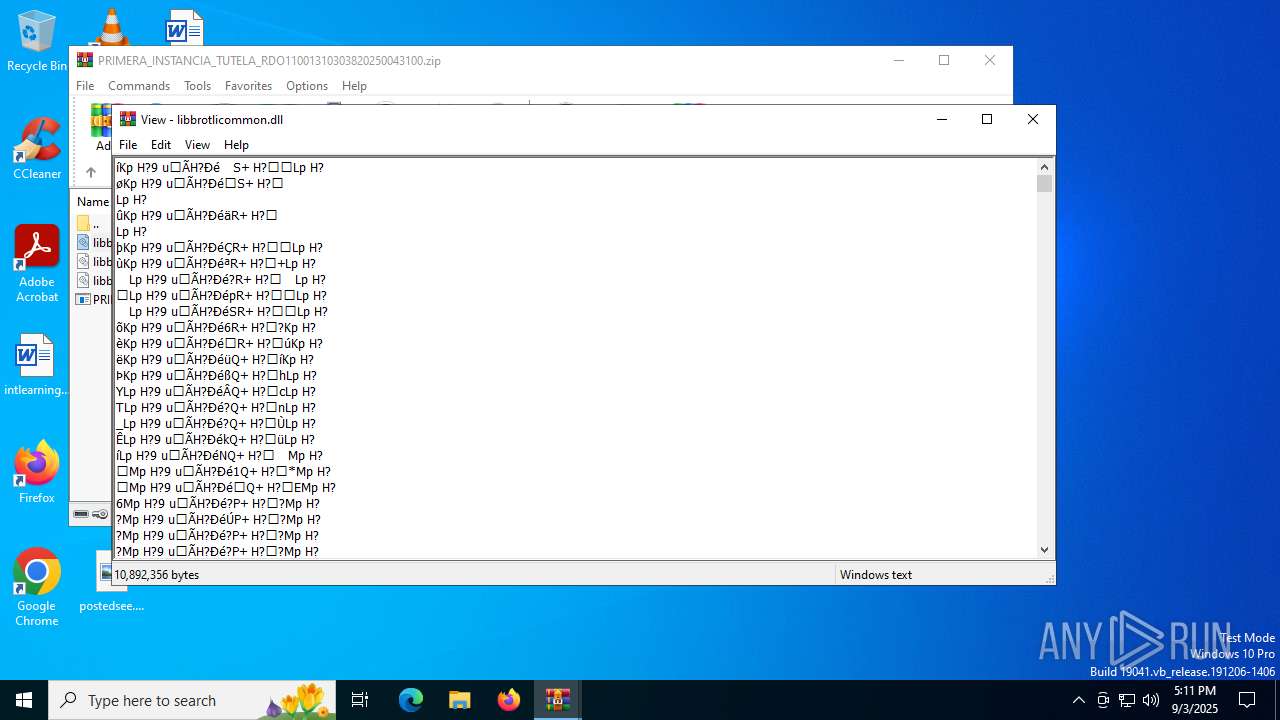
| ZipFileName: | libbrotlicommon.dll |
Total processes
147
Monitored processes
10
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
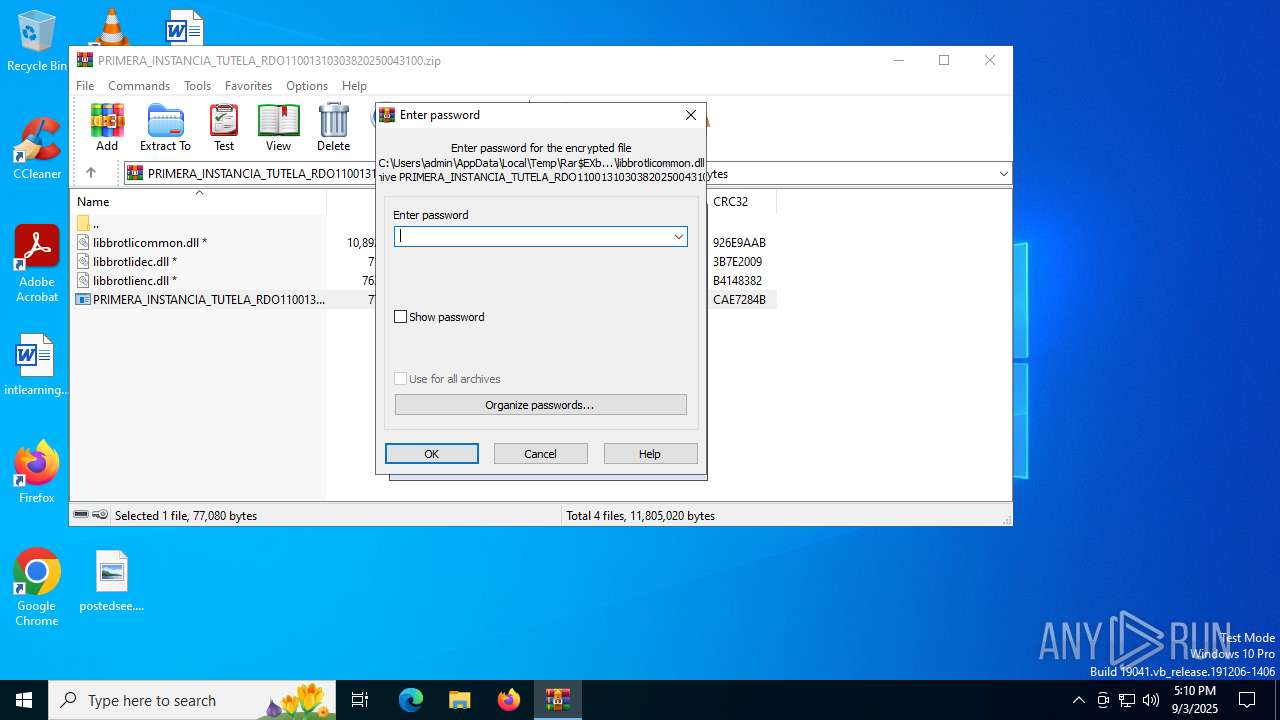
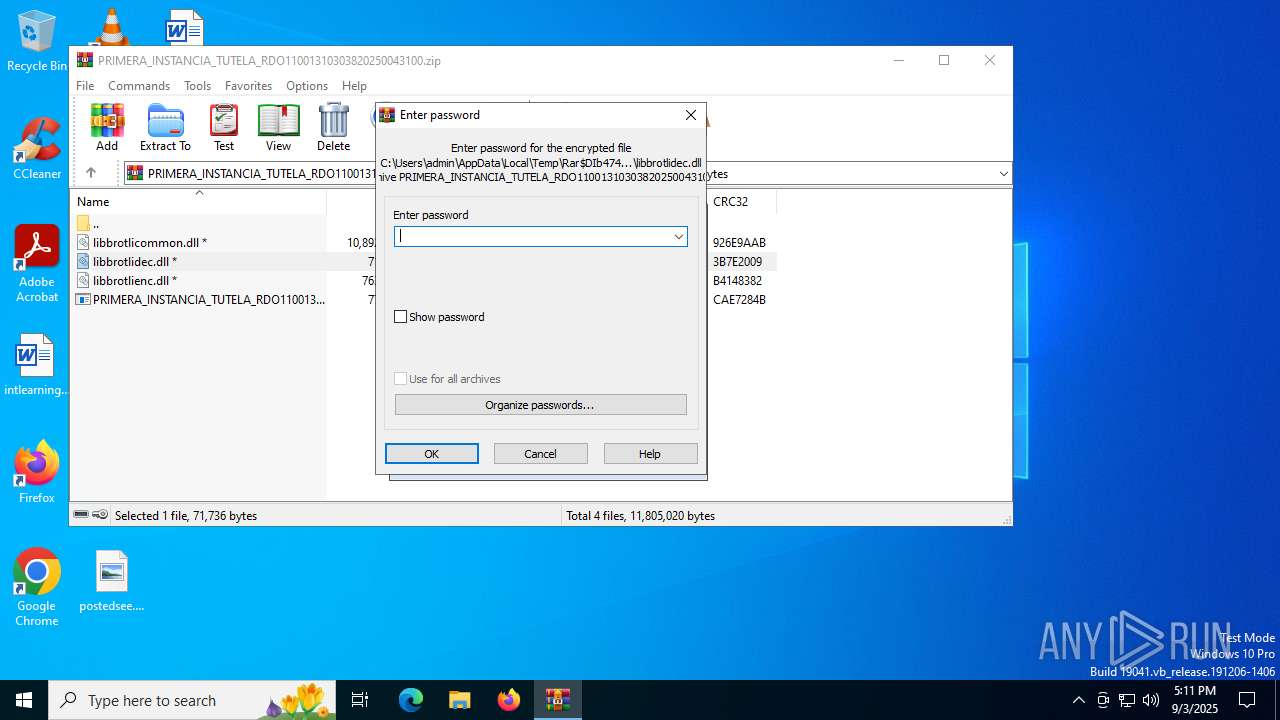
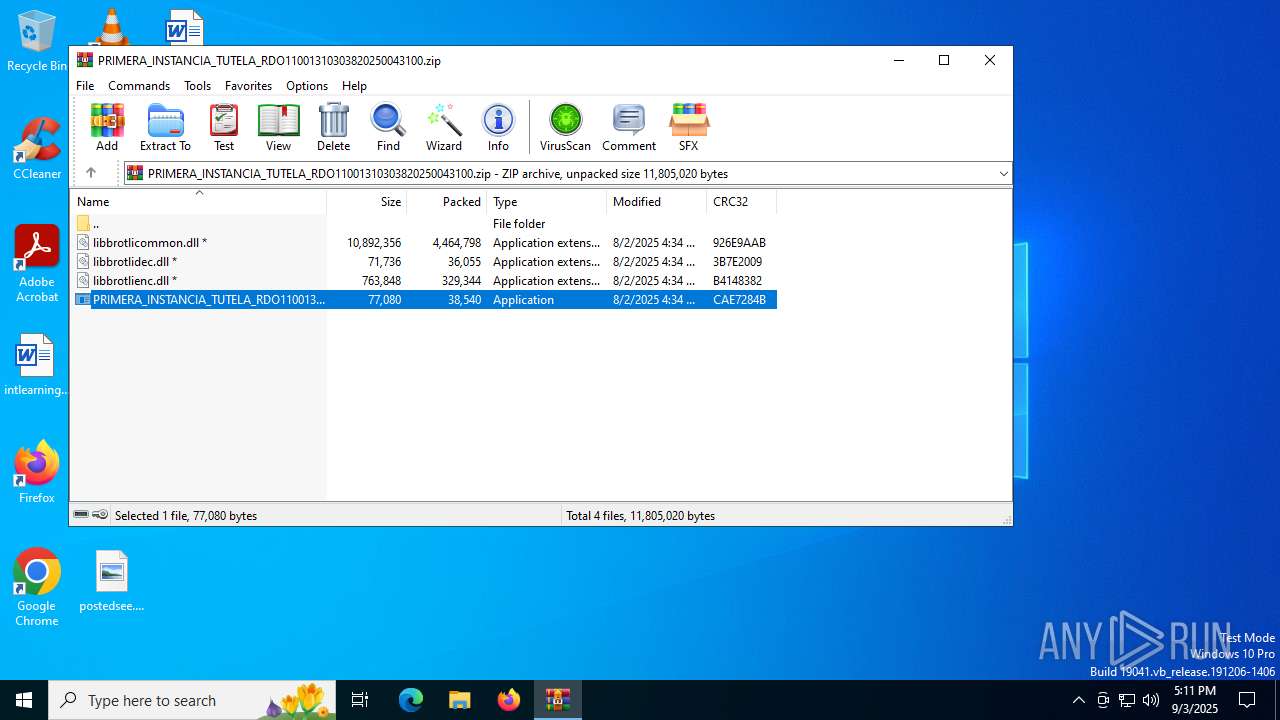
| 684 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb4744.13473\PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb4744.13473\PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 1212 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
AsyncRat(PID) Process(1212) AddInProcess32.exe C2 (1)167.160.161.43 Ports (1)1888 Version1.0.7 Options AutoRunfalse MutexDcRatMutex_qwqdanchun InstallFolder%AppData% Certificates Cert1MIICMDCCAZmgAwIBAgIVAIjqTtxWY28K26eGFx+B3Y5GvrZvMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDERjUmF0IFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTI0MDkyNzEzMTI1MVoXDTM1MDcwNzEzMTI1MVowEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A... Server_SignaturecqSfFiIV9iQ8EHZHCBIkbnUcqWILJv83v9OvWkFOT1NSU42/JeJbOxOP6mviQxv/CyX3Exyu91r5sWSWp3nAs7Fz26DzEa2hWM9Rr2yUi71/GrmbMtVOG9nkHwMrC92wrXTwV+Ja62Ym9rcUpSOFBy5aZCcWwgHMguo/0h6ilOc= Keys AES4f499245f7569363776215d51f07169e8c78c3162830425005c0b72fa4081af0 SaltDcRatByqwqdanchun | |||||||||||||||
| 1644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1800 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb4744.6913\PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb4744.6913\PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 2692 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4744 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5468 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5576 | C:\WINDOWS\system32\WerFault.exe -u -p 684 -s 568 | C:\Windows\System32\WerFault.exe | PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6356 | C:\WINDOWS\system32\WerFault.exe -u -p 1800 -s 596 | C:\Windows\System32\WerFault.exe | PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6940 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\AddInProcess32.exe | PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
15 864
Read events
15 844
Write events
20
Delete events
0
Modification events
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.zip | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4744) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
15
Suspicious files
8
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6356 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_PRIMERA_INSTANCI_293ee7955b4f7df0d68feaaeb7e9cc37a7745b3_8d3271f7_c414fac3-172b-4e59-af02-054568181d55\Report.wer | — | |
MD5:— | SHA256:— | |||
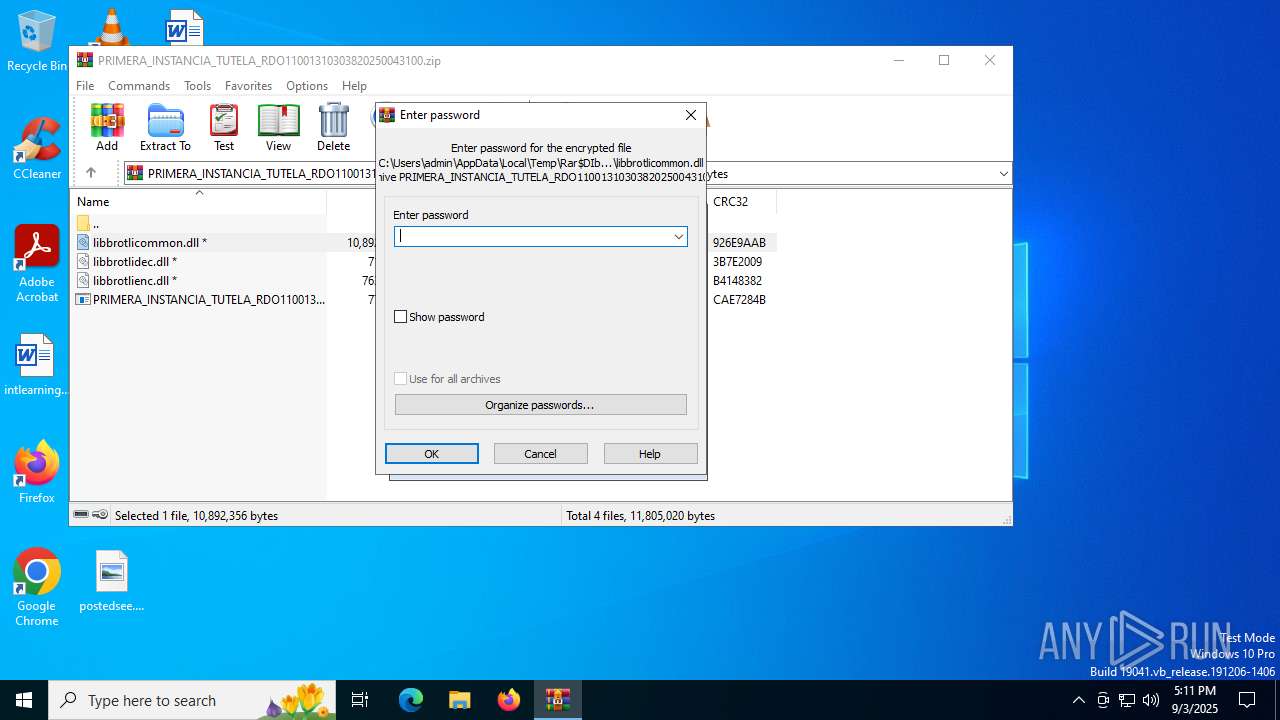
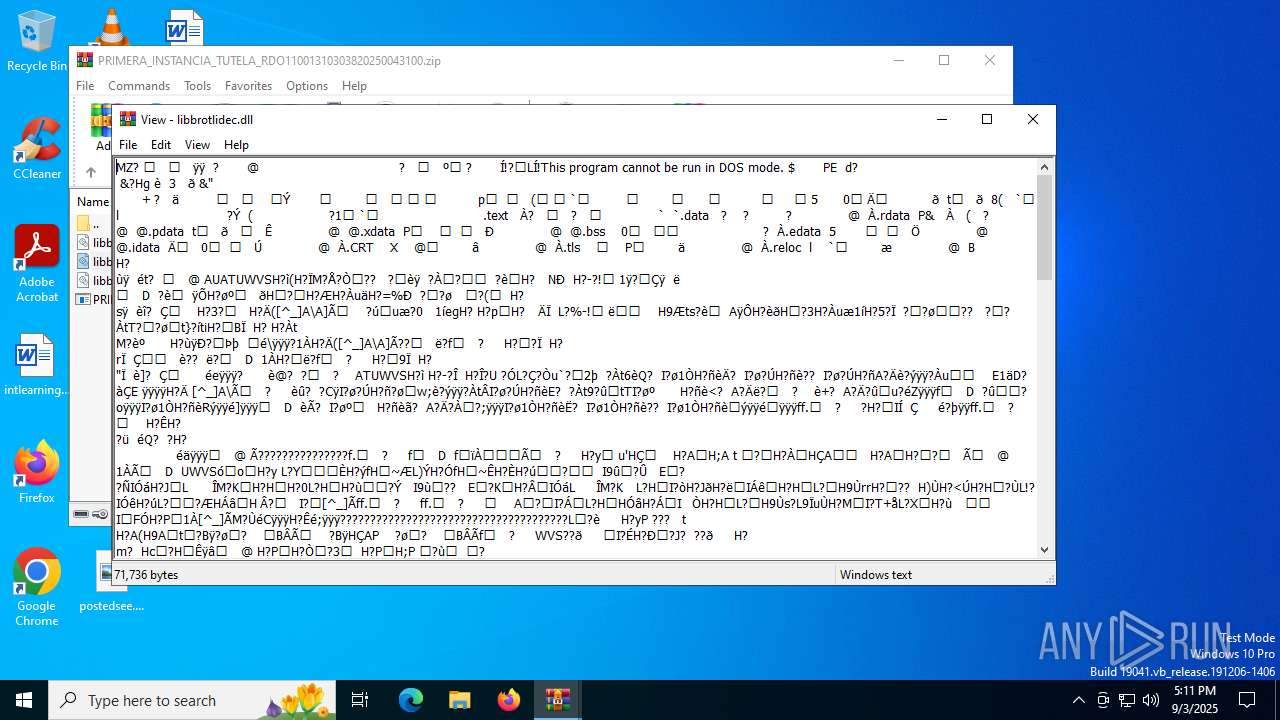
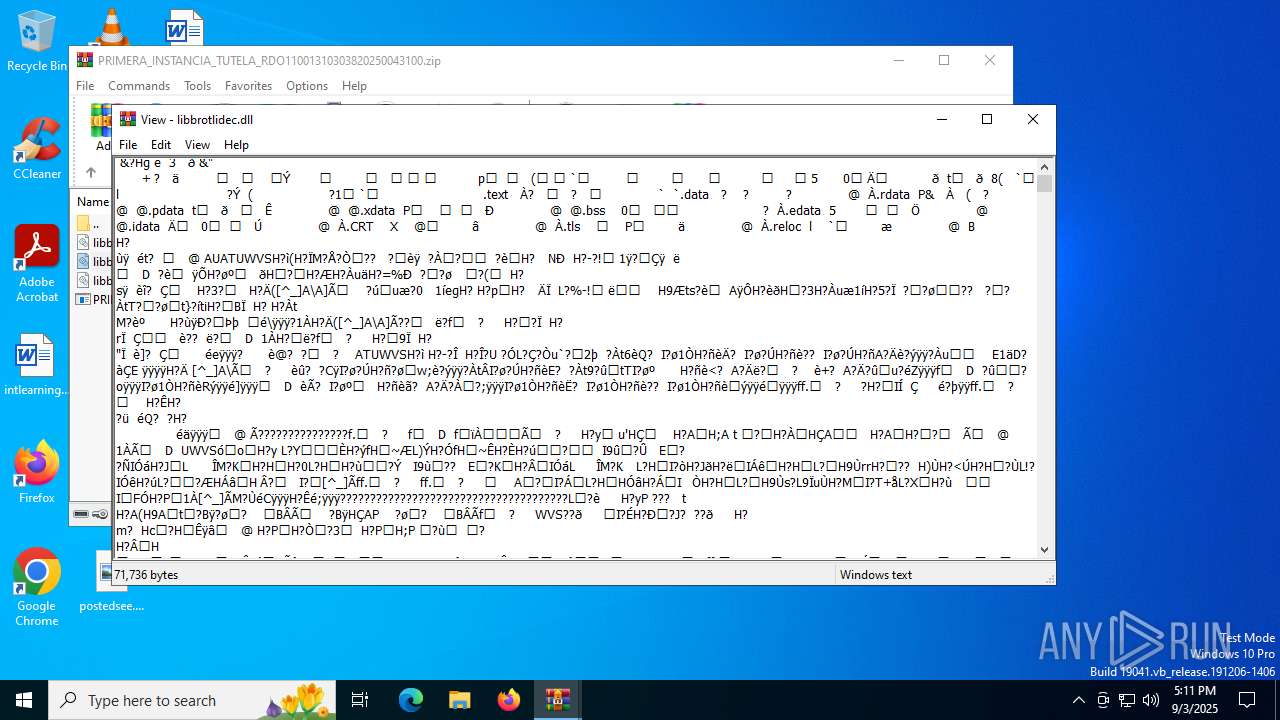
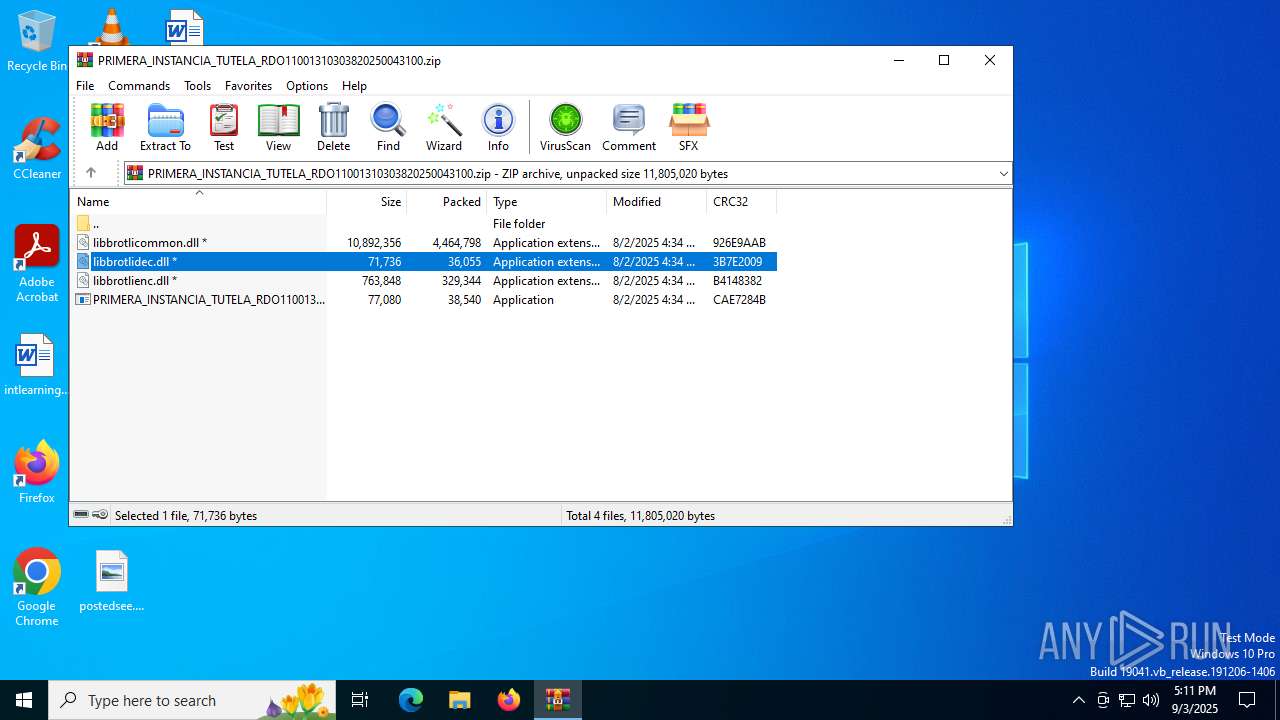
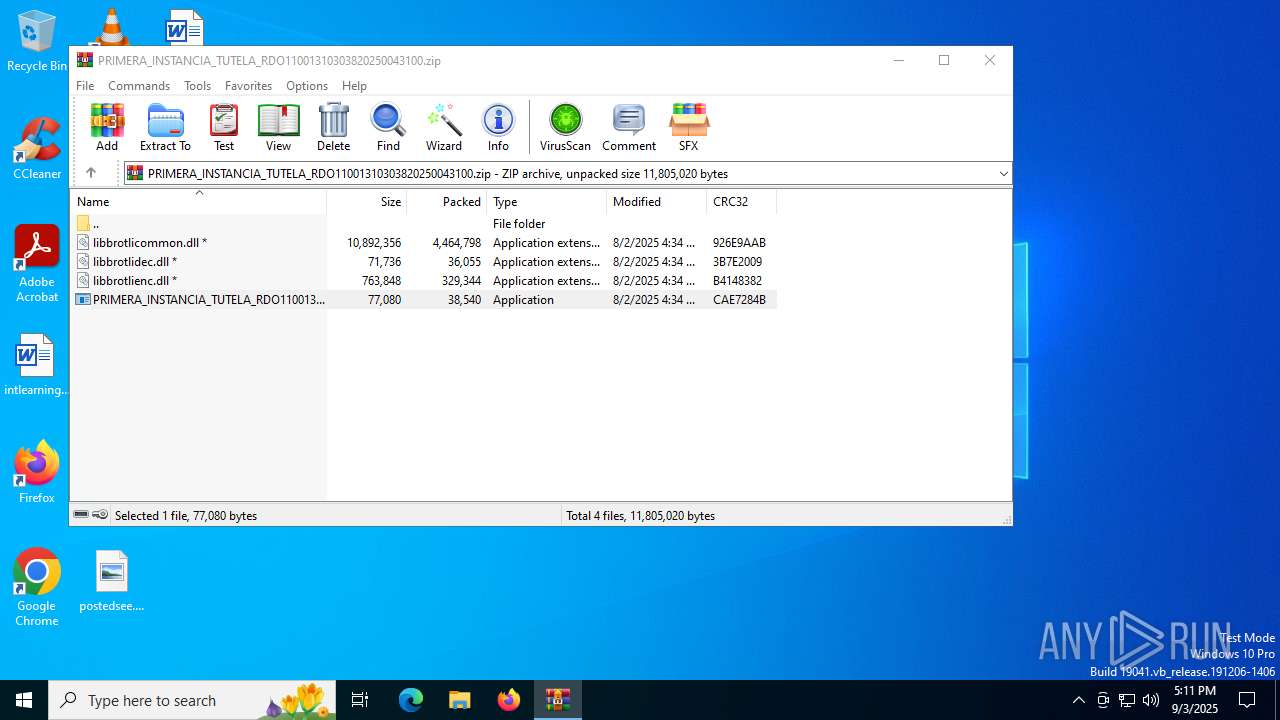
| 4744 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb4744.6913\libbrotlidec.dll | executable | |
MD5:D59263D16943BFACEB6892BC1A502DBD | SHA256:FD08E5D99A511311E852F206532E2A2E2F2C6B43B277F00A405F4AEFA32177F0 | |||
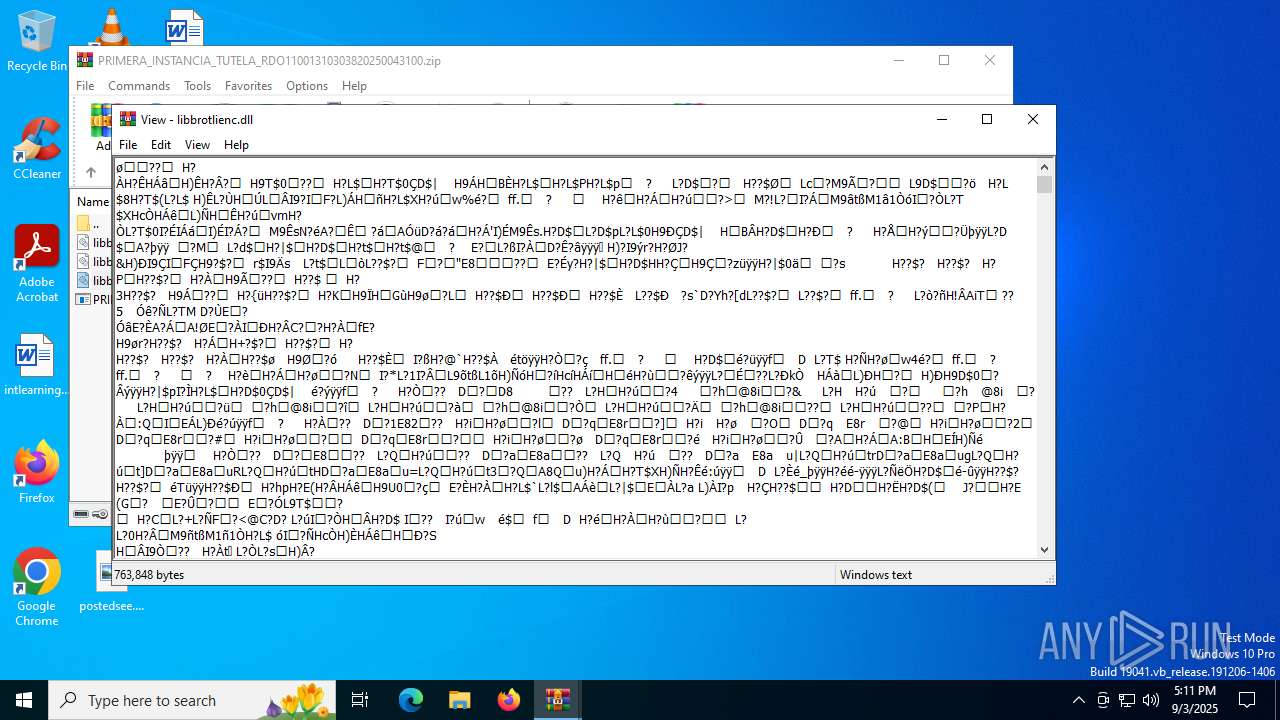
| 4744 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb4744.6913\libbrotlienc.dll | executable | |
MD5:D29D6C34D0764FA49FC6024C42DC497D | SHA256:E56B83F9582DF145BF5B952BED593A919EB3D348DFA8C17B1516C8C1922D4794 | |||
| 1800 | PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe | C:\Users\admin\ThreadAbortExceptionTryReadLittleEndianDMN\PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe | executable | |
MD5:CB3F2900380531E0682661721E20900E | SHA256:D12FE65742A2CD9DAD6445889FA7ECB58302BE10F60F24705BF974F30815FD46 | |||
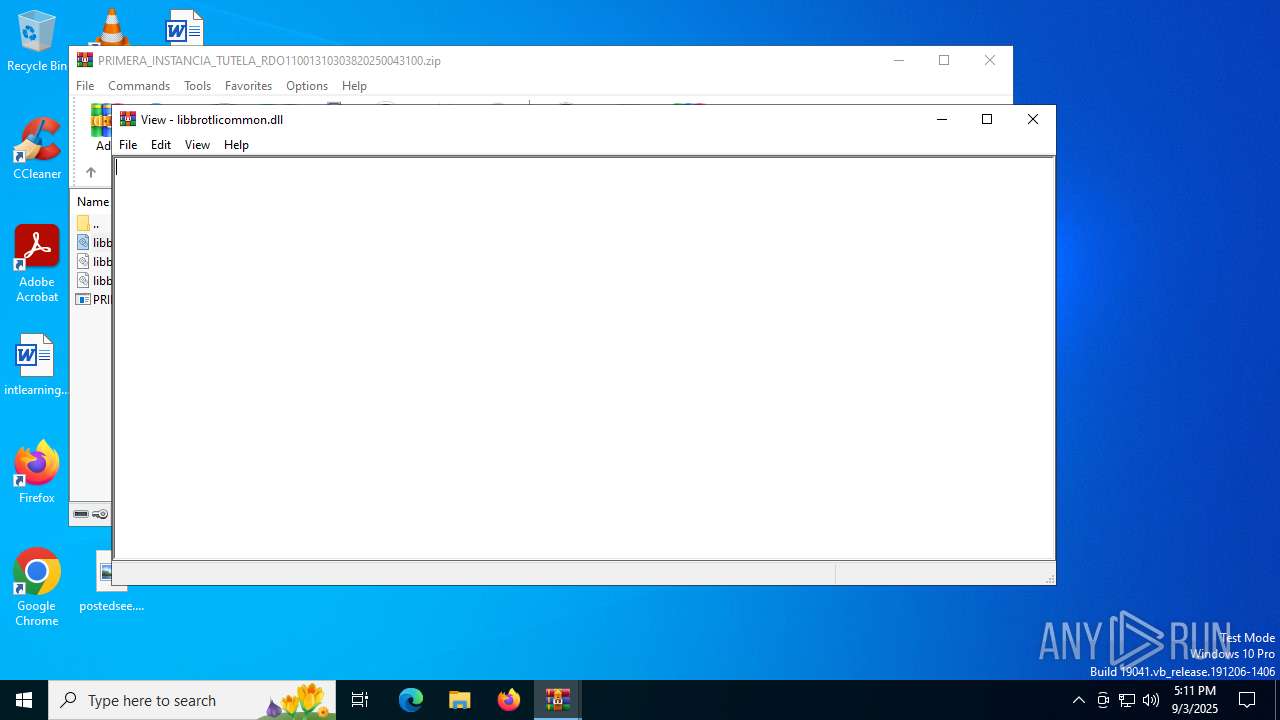
| 4744 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb4744.6913\libbrotlicommon.dll | executable | |
MD5:70B7F7AF7C38EAD7384B27A1AEEE8AE0 | SHA256:C01C4C882D432003CCF162410890D73C6CA6B9CD349B003F6DFDE35456F521D2 | |||
| 4744 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb4744.12523\libbrotlidec.dll | executable | |
MD5:D59263D16943BFACEB6892BC1A502DBD | SHA256:FD08E5D99A511311E852F206532E2A2E2F2C6B43B277F00A405F4AEFA32177F0 | |||
| 1800 | PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe | C:\Users\admin\ThreadAbortExceptionTryReadLittleEndianDMN\libbrotlienc.dll | executable | |
MD5:D29D6C34D0764FA49FC6024C42DC497D | SHA256:E56B83F9582DF145BF5B952BED593A919EB3D348DFA8C17B1516C8C1922D4794 | |||
| 6356 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\PRIMERA_INSTANCIA_TUTELA_RDO11001310303820250043100.exe.1800.dmp | binary | |
MD5:29305DE1809552ABEE034B88D51193AF | SHA256:5E25FC7BBF752C923F84EC10222D2D684C7ECEA33C593C722C241C5510DA9795 | |||
| 5576 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_PRIMERA_INSTANCI_293ee7955b4f7df0d68feaaeb7e9cc37a7745b3_8d3271f7_fe169e84-2f13-410c-bfcc-4f7fe84a8a84\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6356 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:45B153BDEDAC6E751A4B1C3886D30F54 | SHA256:6EEBB810B2240BB36E7BFDC3B3BCF0CA4FF65CA680008098FF4ADA1EDE9EFEE9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
27
DNS requests
22
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7104 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4156 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4156 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6356 | WerFault.exe | GET | 200 | 2.16.164.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6356 | WerFault.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 72.246.169.163:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4836 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1212 | AddInProcess32.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 30 |
1212 | AddInProcess32.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
1212 | AddInProcess32.exe | A Network Trojan was detected | ET MALWARE Observed Malicious SSL Cert (Various RAT) |
1212 | AddInProcess32.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT) |
1212 | AddInProcess32.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |