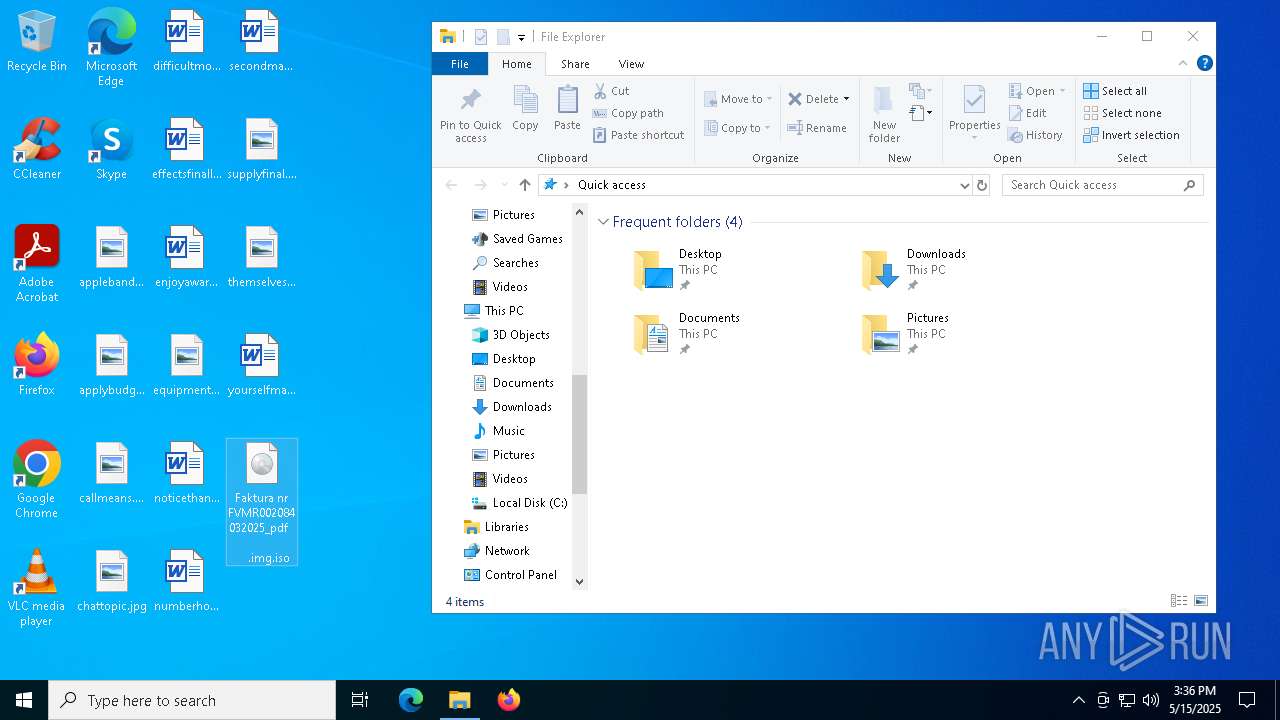
| File name: | Faktura nr FVMR002084032025_pdf .img |
| Full analysis: | https://app.any.run/tasks/fa7798e7-f62d-45d6-b436-d36a75086b2c |
| Verdict: | Malicious activity |
| Threats: | First identified in March 2021, PureCrypter is a .NET-based loader that employs obfuscation techniques, such as SmartAssembly, to evade detection. It has been used to distribute malware families including AgentTesla, RedLine Stealer, and SnakeKeylogger. The malware is typically delivered through phishing campaigns and malicious downloads, often masquerading as legitimate files with extensions like .mp4 or .pdf. PureCrypter utilizes encryption and compression to conceal its payloads and can inject malicious code into legitimate processes to maintain persistence on the infected system. |
| Analysis date: | May 15, 2025, 15:36:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-iso9660-image |
| File info: | ISO 9660 CD-ROM filesystem data 'Faktura nr FVMR002084032025_pdf' |
| MD5: | 2D67A02C6FF12F388C710CAE164DC19B |
| SHA1: | 06BC33C515EE0099042A2F422153682B8A7E9702 |
| SHA256: | ABC41560BC58CC8BC7C496BD6E13FBF99A42554887E4CFDB9C8DFFDF8967869A |
| SSDEEP: | 384:2sYsNCjPyYeQevgLwjjQkekZqU0arpE/qdJVWsUtO7w6t:fe5eQevEwjjQk7ZFi/qdGsuOz |
MALICIOUS
Scans artifacts that could help determine the target
- InstallUtil.exe (PID: 5588)
- InstallUtil.exe (PID: 3304)
PURECRYPTER has been detected (SURICATA)
- InstallUtil.exe (PID: 5588)
- InstallUtil.exe (PID: 3304)
Steals credentials from Web Browsers
- InstallUtil.exe (PID: 3304)
- InstallUtil.exe (PID: 5588)
Actions looks like stealing of personal data
- InstallUtil.exe (PID: 3304)
- InstallUtil.exe (PID: 5588)
PURECRYPTER has been detected (YARA)
- InstallUtil.exe (PID: 5588)
- InstallUtil.exe (PID: 3304)
[YARA] zgRAT detected by memory dumps
- InstallUtil.exe (PID: 5588)
- InstallUtil.exe (PID: 3304)
SUSPICIOUS
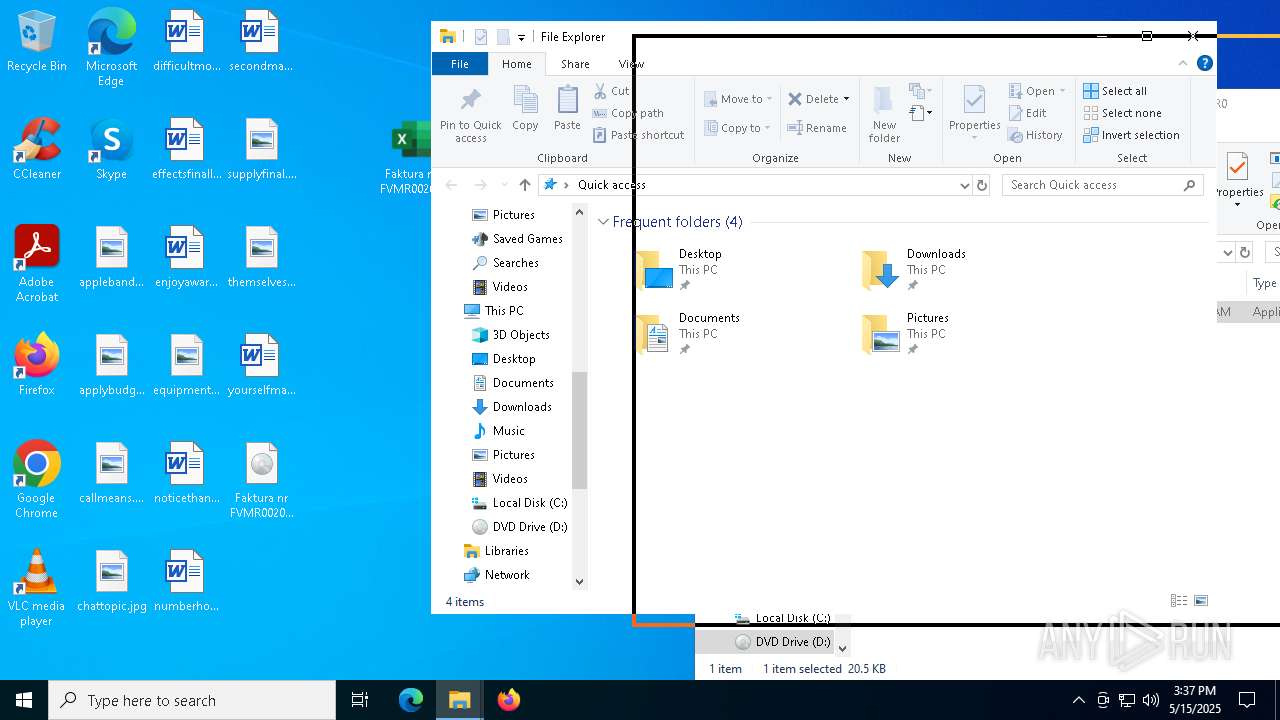
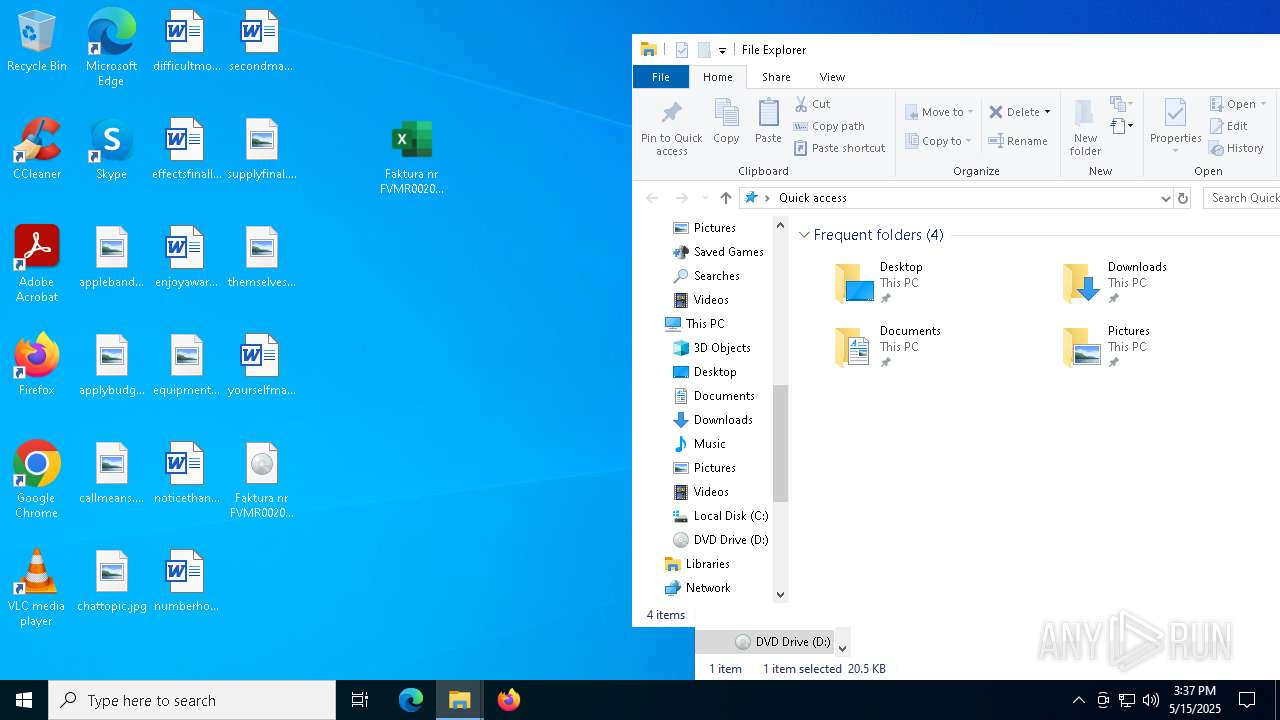
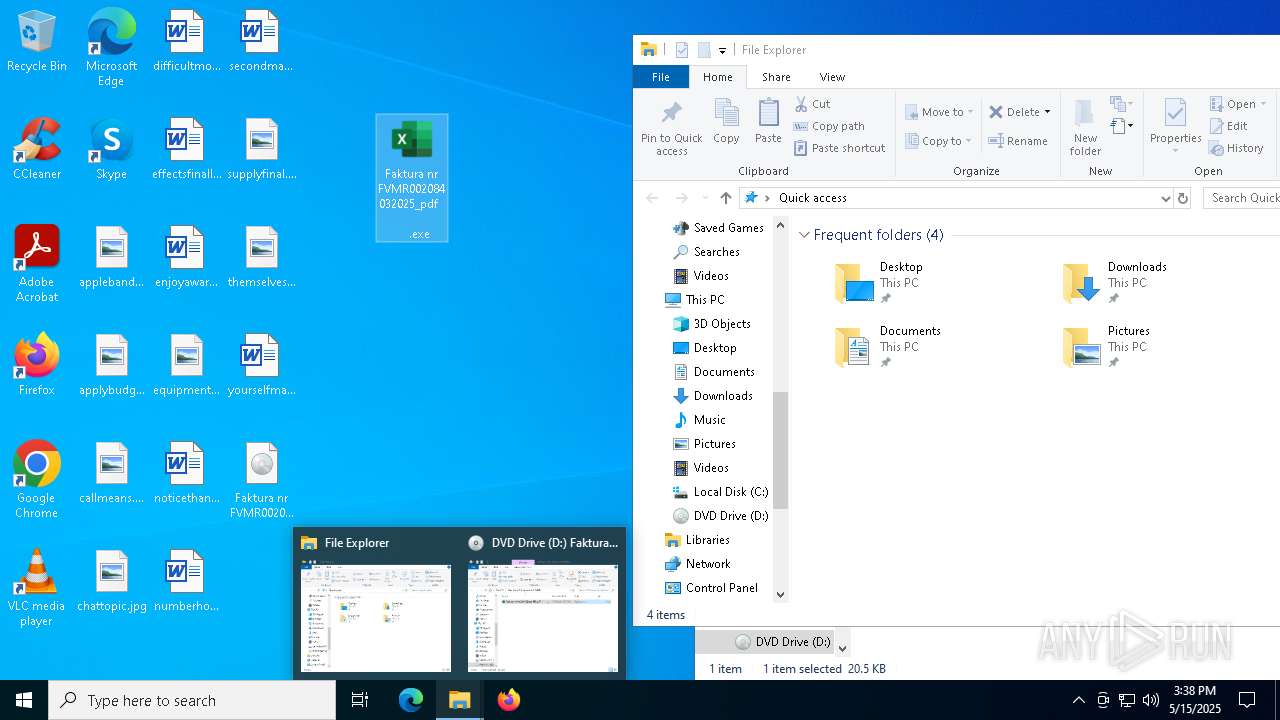
Application launched itself
- explorer.exe (PID: 5492)
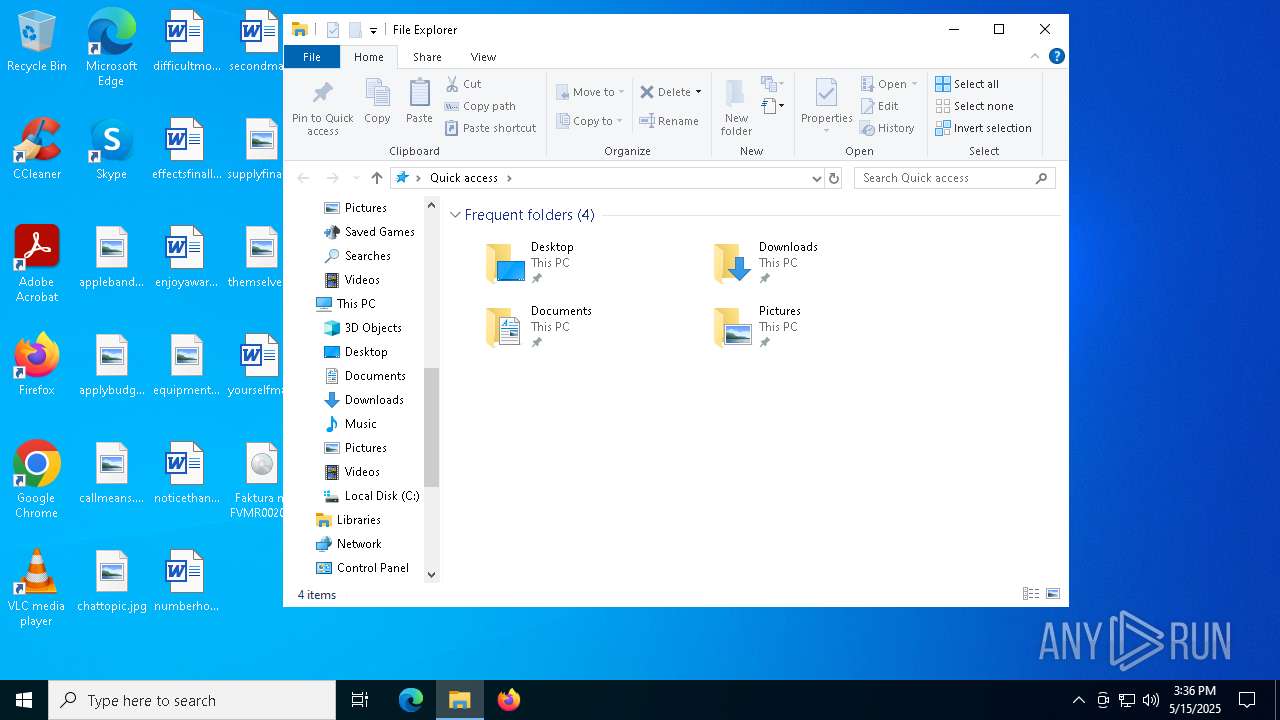
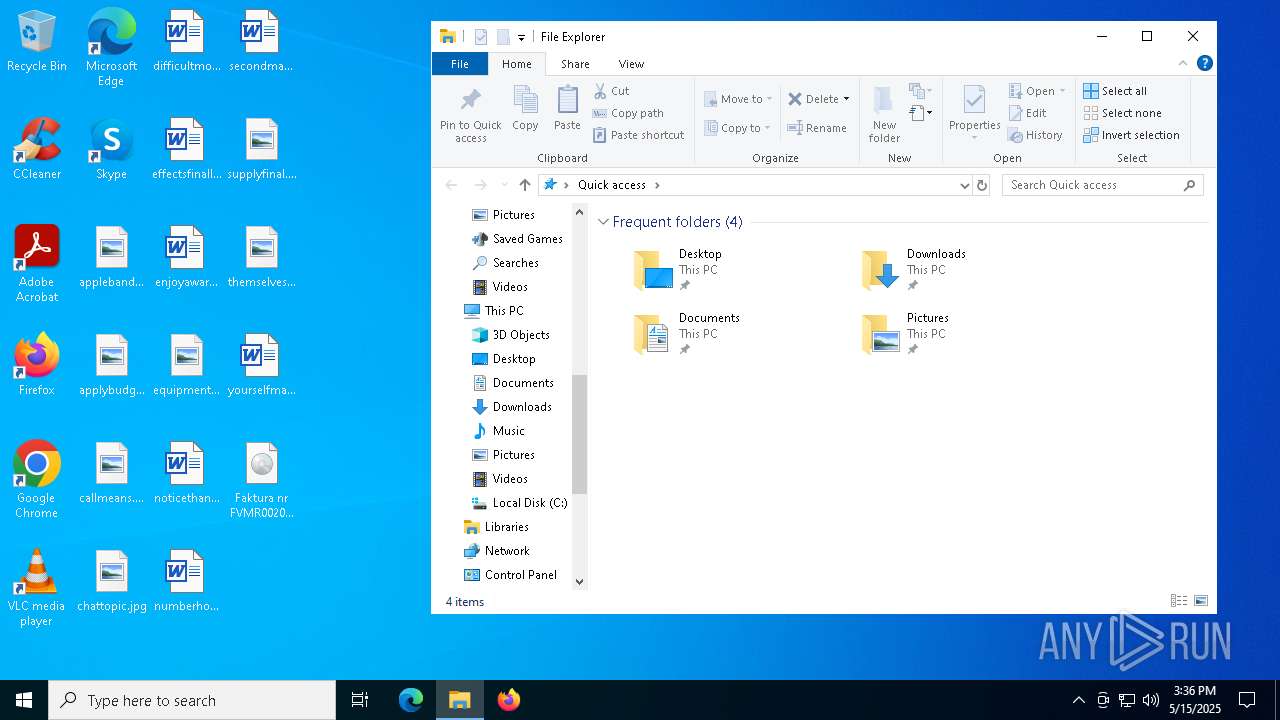
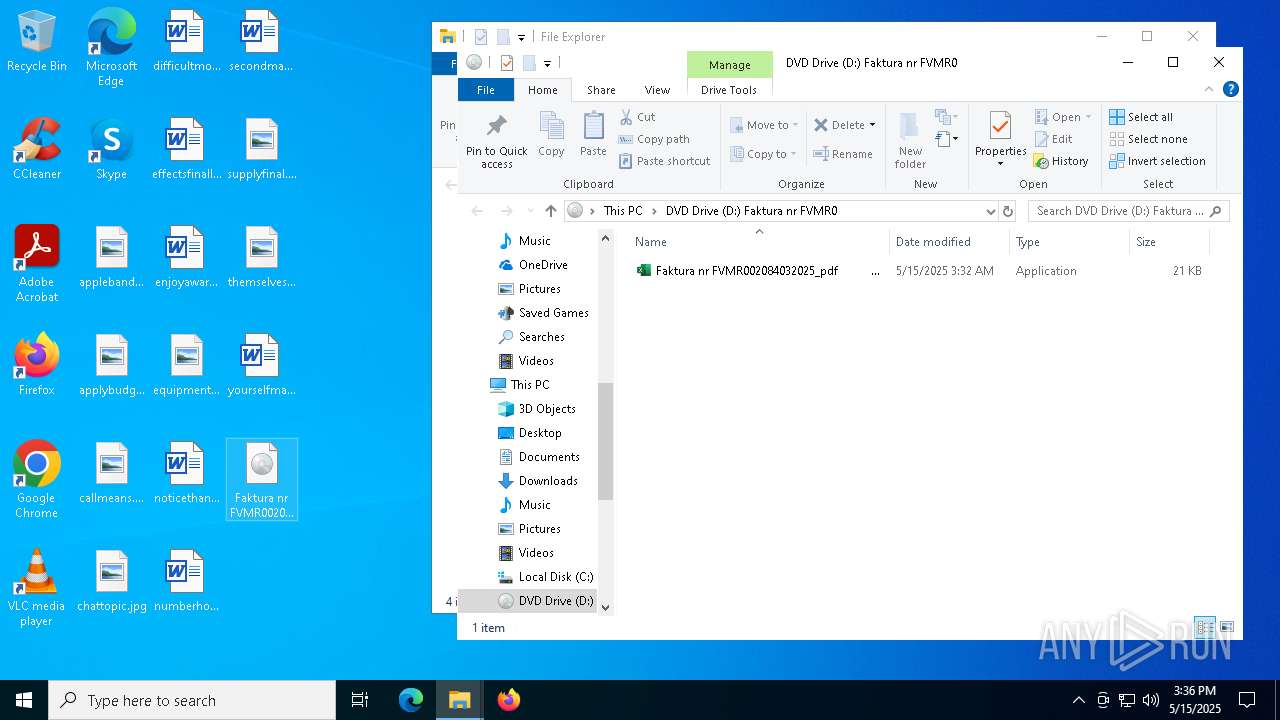
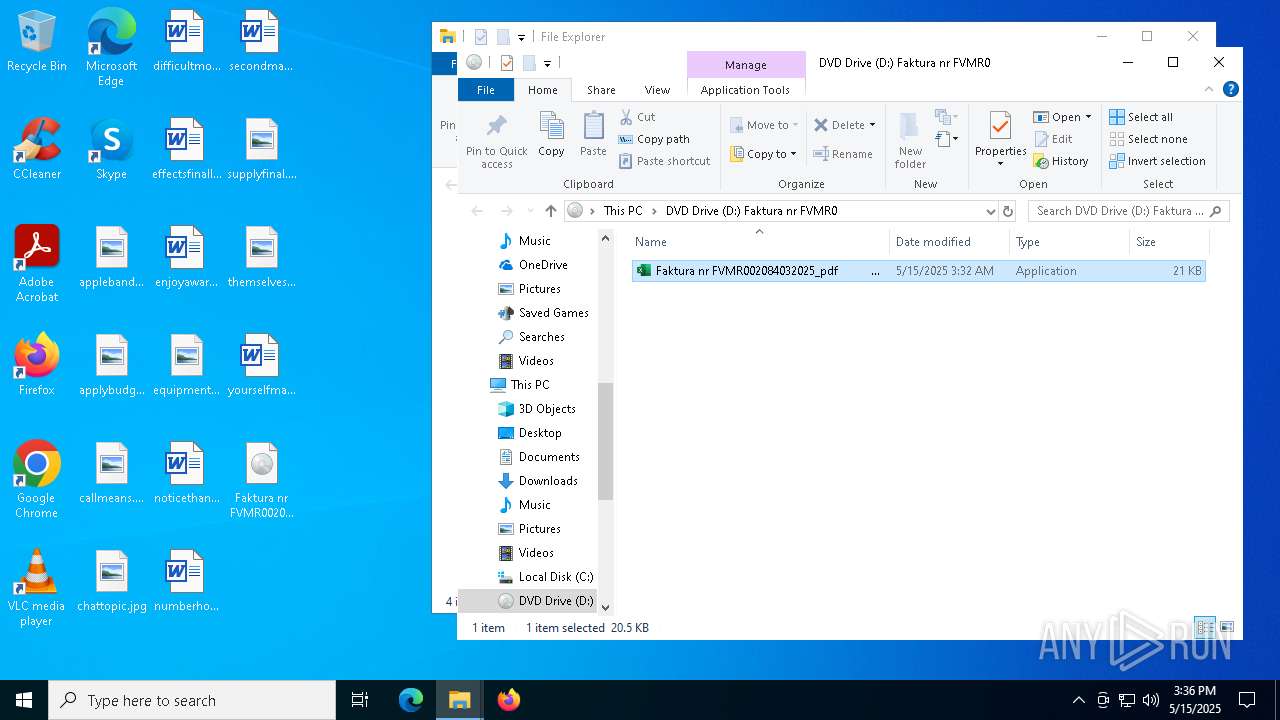
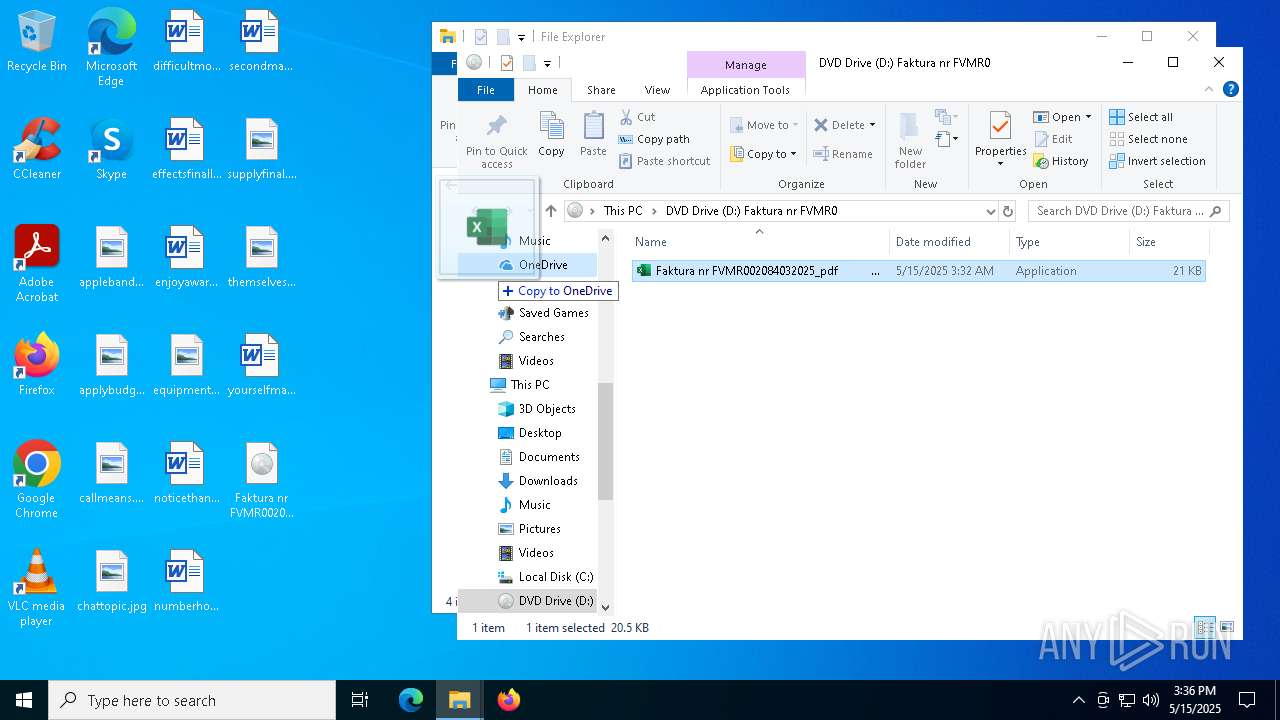
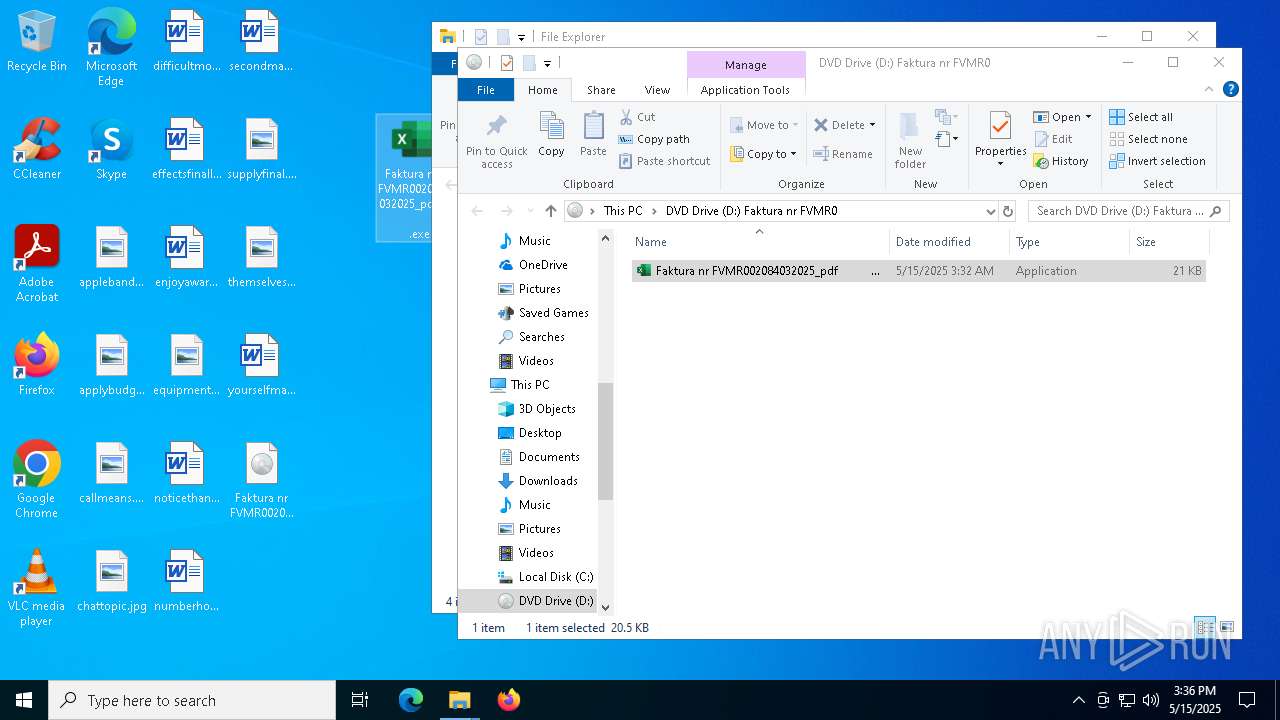
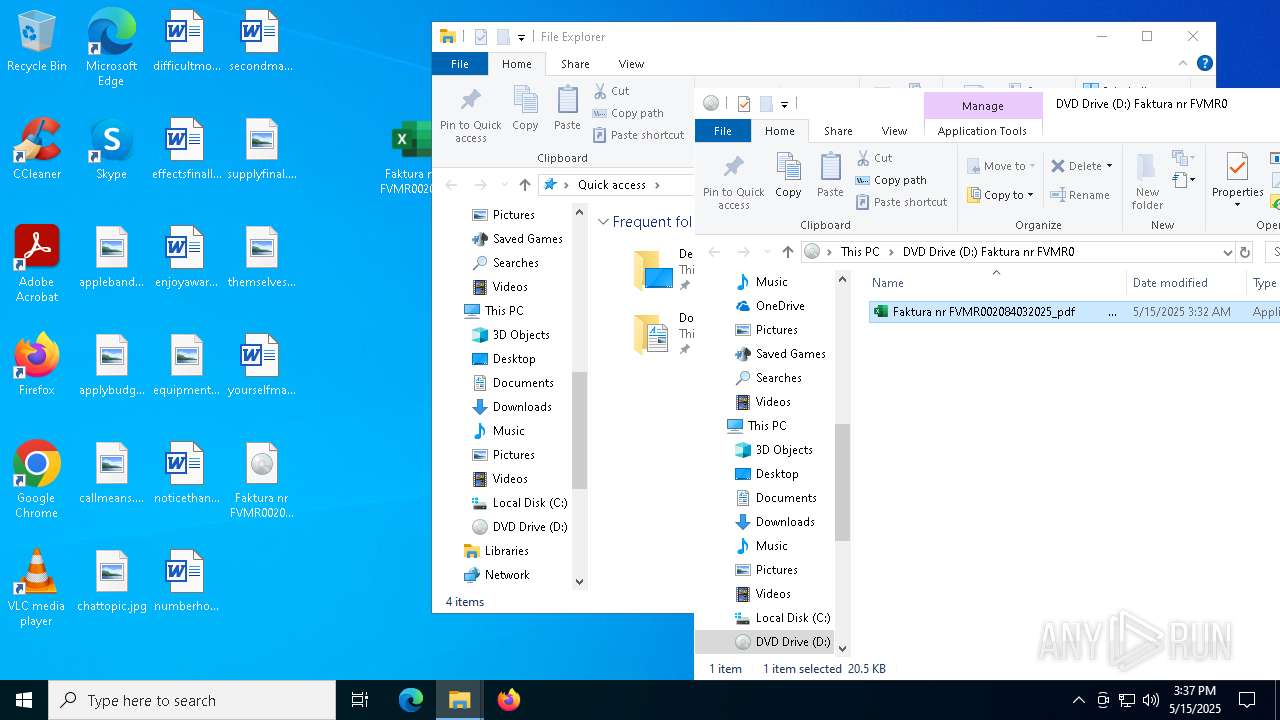
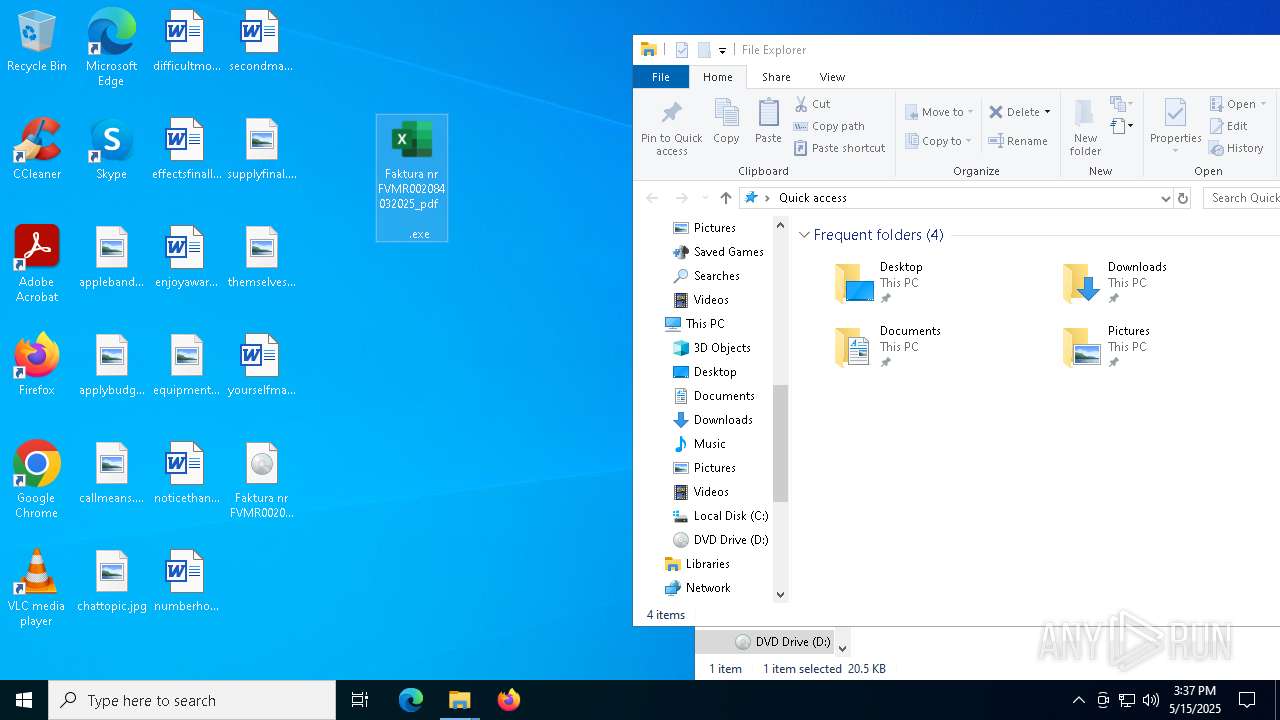
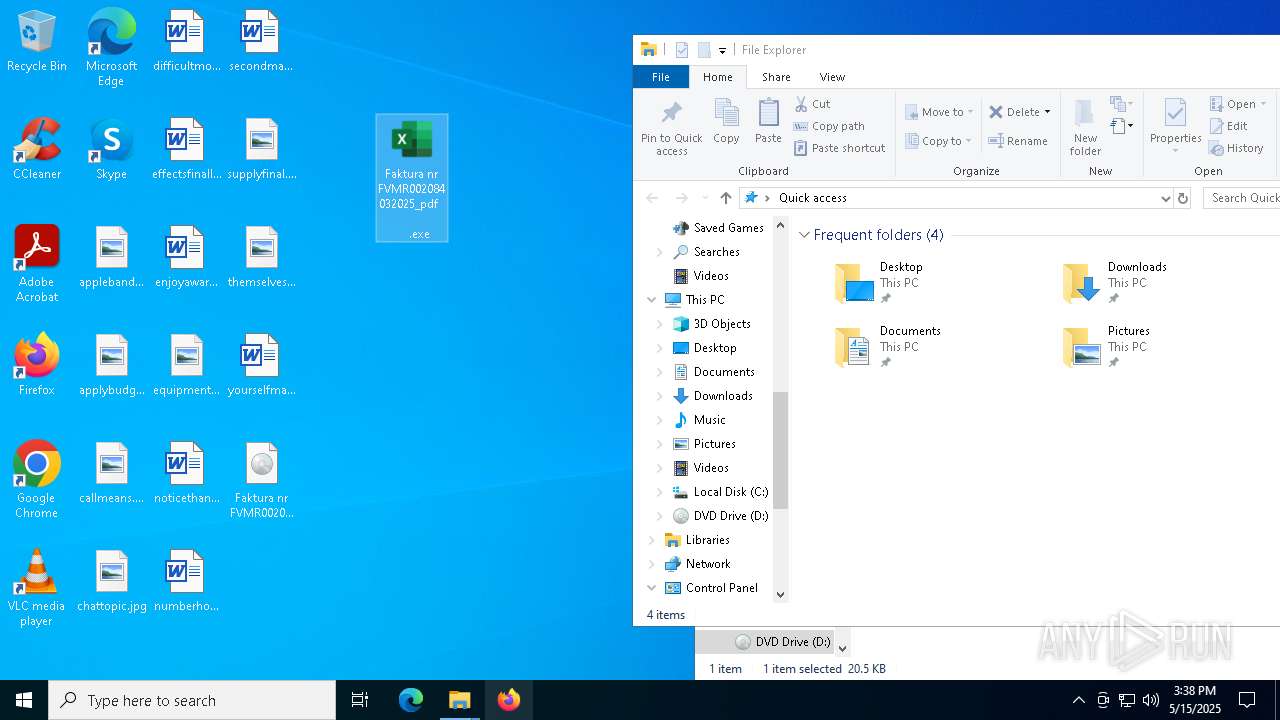
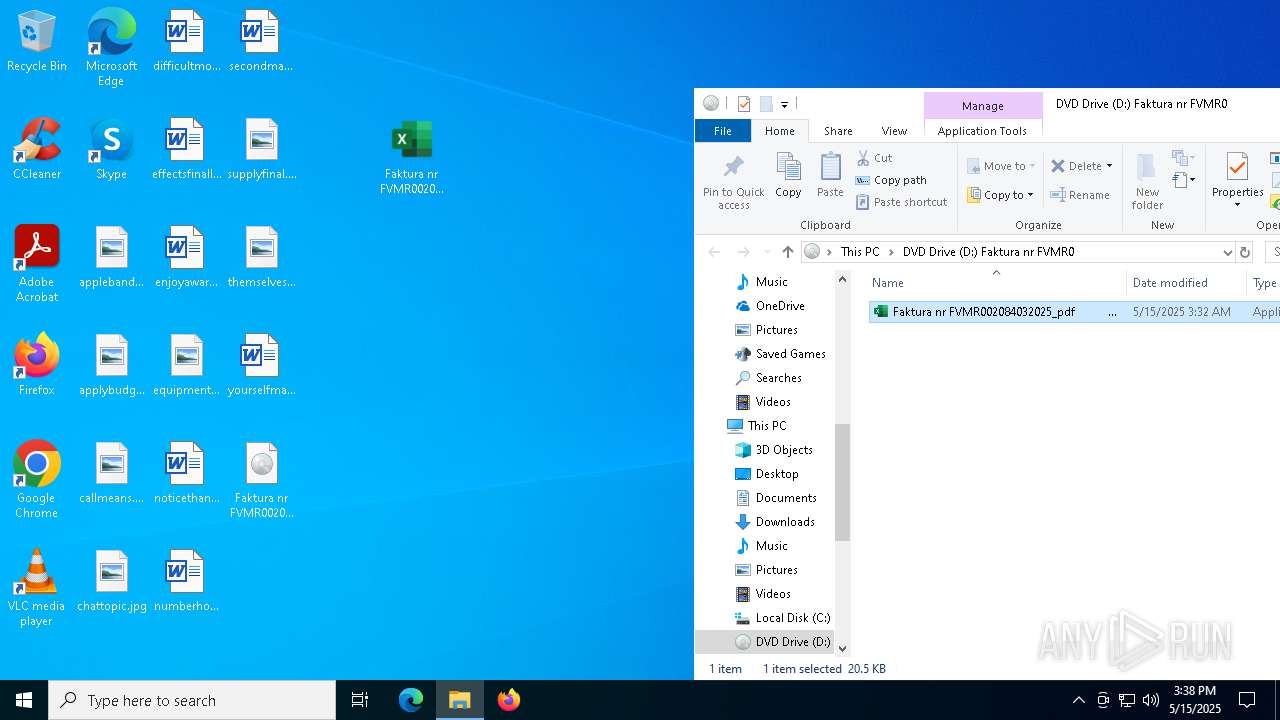
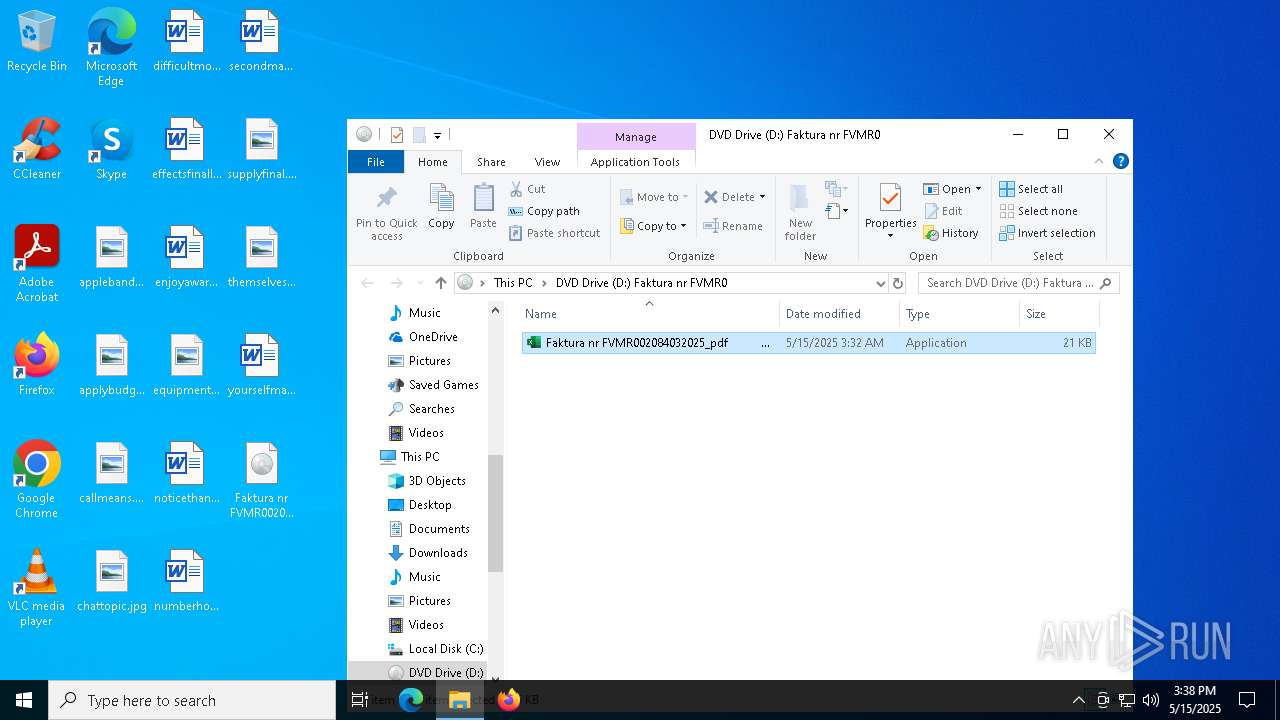
Image mount has been detect
- explorer.exe (PID: 5492)
Loading modules from mounted disk drive
- Faktura nr FVMR002084032025_pdf .exe (PID: 6620)
Connects to the server without a host name
- Faktura nr FVMR002084032025_pdf .exe (PID: 6620)
- Faktura nr FVMR002084032025_pdf .exe (PID: 4980)
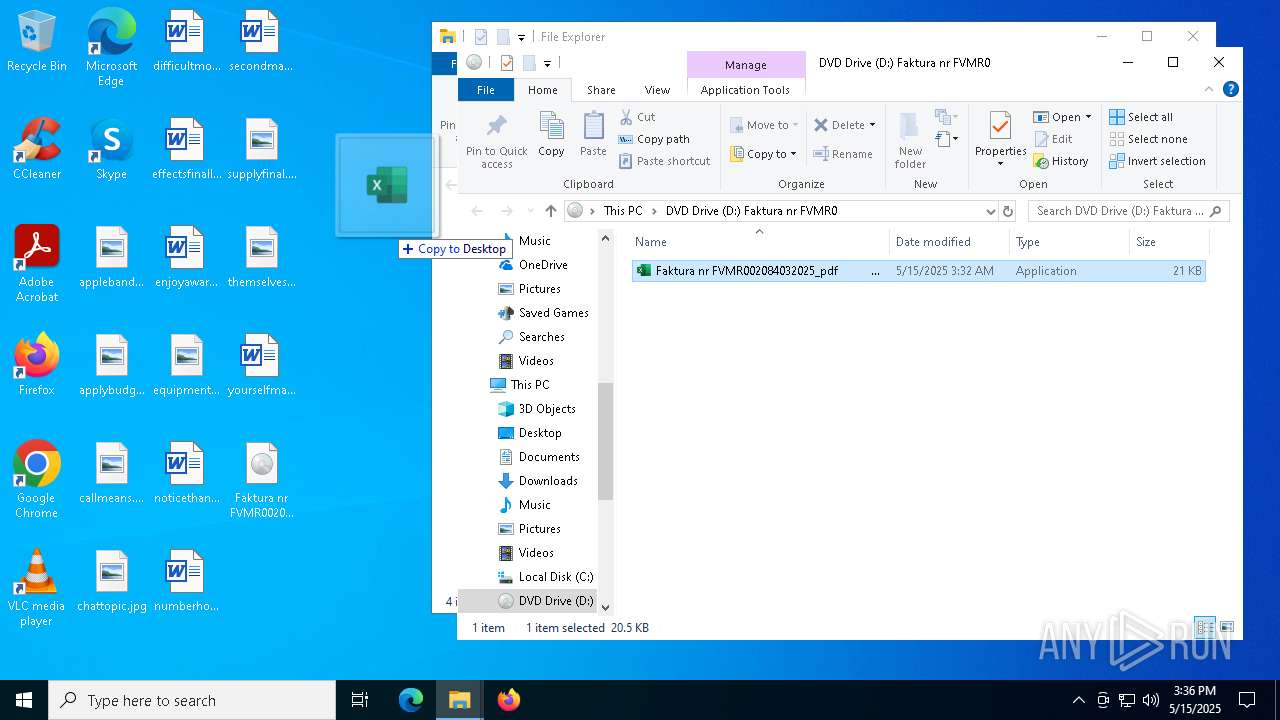
Executable content was dropped or overwritten
- explorer.exe (PID: 5492)
Connects to unusual port
- InstallUtil.exe (PID: 5588)
- InstallUtil.exe (PID: 3304)
Multiple wallet extension IDs have been found
- InstallUtil.exe (PID: 5588)
- InstallUtil.exe (PID: 3304)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 5492)
Manual execution by a user
- Faktura nr FVMR002084032025_pdf .exe (PID: 6620)
- InstallUtil.exe (PID: 5588)
- Faktura nr FVMR002084032025_pdf .exe (PID: 4980)
- InstallUtil.exe (PID: 3304)
Reads the computer name
- Faktura nr FVMR002084032025_pdf .exe (PID: 6620)
- InstallUtil.exe (PID: 5588)
- Faktura nr FVMR002084032025_pdf .exe (PID: 4980)
- InstallUtil.exe (PID: 3304)
Disables trace logs
- Faktura nr FVMR002084032025_pdf .exe (PID: 6620)
- Faktura nr FVMR002084032025_pdf .exe (PID: 4980)
Checks supported languages
- Faktura nr FVMR002084032025_pdf .exe (PID: 6620)
- Faktura nr FVMR002084032025_pdf .exe (PID: 4980)
- InstallUtil.exe (PID: 5588)
- InstallUtil.exe (PID: 3304)
Checks proxy server information
- Faktura nr FVMR002084032025_pdf .exe (PID: 6620)
- Faktura nr FVMR002084032025_pdf .exe (PID: 4980)
- slui.exe (PID: 660)
Reads the machine GUID from the registry
- Faktura nr FVMR002084032025_pdf .exe (PID: 6620)
- InstallUtil.exe (PID: 5588)
- Faktura nr FVMR002084032025_pdf .exe (PID: 4980)
- InstallUtil.exe (PID: 3304)
Reads Microsoft Office registry keys
- InstallUtil.exe (PID: 5588)
- InstallUtil.exe (PID: 3304)
.NET Reactor protector has been detected
- InstallUtil.exe (PID: 5588)
Reads the software policy settings
- slui.exe (PID: 660)
- slui.exe (PID: 7700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .atn | | | Photoshop Action (37.5) |
|---|---|---|
| .gmc | | | Game Music Creator Music (8.4) |
| .abr | | | Adobe PhotoShop Brush (7.5) |
EXIF
ISO
| System: | Win32 |
|---|---|
| VolumeName: | Faktura nr FVMR002084032025_pdf |
| VolumeBlockCount: | 41 |
| VolumeBlockSize: | 2048 |
| RootDirectoryCreateDate: | 2025:05:15 05:41:45+01:00 |
| Software: | PowerISO |
| VolumeCreateDate: | 2025:05:15 05:41:45.00+01:00 |
| VolumeModifyDate: | 2025:05:15 05:41:45.00+01:00 |
Composite
| VolumeSize: | 84 kB |
|---|
Total processes
139
Monitored processes
9
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3304 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 4980 | "C:\Users\admin\Desktop\Faktura nr FVMR002084032025_pdf .exe" | C:\Users\admin\Desktop\Faktura nr FVMR002084032025_pdf .exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Woxcwganpw Exit code: 4294967295 Version: 1.0.1323.3653 Modules
| |||||||||||||||
| 5492 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5588 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 6620 | "D:\Faktura nr FVMR002084032025_pdf .exe" | D:\Faktura nr FVMR002084032025_pdf .exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Woxcwganpw Exit code: 4294967295 Version: 1.0.1323.3653 Modules
| |||||||||||||||
| 7500 | "C:\WINDOWS\Explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7668 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7700 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 203
Read events
21 037
Write events
162
Delete events
4
Modification events
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 00000000000000000000000000000000030001000100010017000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C0000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C0000000D0000000000000053006B007900700065002E006C006E006B003E0020007C00000011000000000000006100700070006C006500620061006E0064002E0070006E0067003E0020002000000013000000000000006100700070006C0079006200750064006700650074002E0070006E0067003E002000200000001100000000000000630061006C006C006D00650061006E0073002E006A00700067003E002000200000001100000000000000630068006100740074006F007000690063002E006A00700067003E00200020000000160000000000000064006900660066006900630075006C0074006D006F007600690065002E007200740066003E0020002000000016000000000000006500660066006500630074007300660069006E0061006C006C0079002E007200740066003E00200020000000130000000000000065006E006A006F0079006100770061007200640073002E007200740066003E002000200000001700000000000000650071007500690070006D0065006E00740066006F0072006D00610074002E006A00700067003E0020002000000013000000000000006E006F0074006900630065007400680061006E006B002E007200740066003E0020002000000011000000000000006E0075006D0062006500720068006F0077002E007200740066003E0020002000000014000000000000007300650063006F006E0064006D0061006E00750061006C002E007200740066003E00200020000000130000000000000073007500700070006C007900660069006E0061006C002E006A00700067003E0020002000000018000000000000007400680065006D00730065006C007600650073007400680065006F00720079002E006A00700067003E00200020000000140000000000000079006F0075007200730065006C0066006D00610069006C002E007200740066003E002000200000004B00000000000000460061006B00740075007200610020006E0072002000460056004D0052003000300032003000380034003000330032003000320035005F00700064006600200020002000200020002000200020002000200020002000200020002000200020002000200020002000200020002000200020002000200020002000200020002E0069006D0067002E00690073006F003E00200020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000001700000000000000000000000000000000000000803F0000004008000000803F0000404009000000803F000080400A000000803F0000A0400B0000000040000000000C00000000400000803F0D0000000040000000400E0000000040000040400F0000000040000080401000000000400000A040110000004040000000001200000040400000803F13000000404000000040140000004040000040401500000000000000803F0100000000000000004002000000000000004040030000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F070000004040000080401600 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconNameVersion |
Value: 1 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: F209266800000000 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000007500690000000000 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 03000000040000000E00000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Ribbon |
| Operation: | write | Name: | MinimizedStateTabletModeOff |
Value: 0 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Ribbon |
| Operation: | write | Name: | QatItems |
Value: 3C7369713A637573746F6D554920786D6C6E733A7369713D22687474703A2F2F736368656D61732E6D6963726F736F66742E636F6D2F77696E646F77732F323030392F726962626F6E2F716174223E3C7369713A726962626F6E206D696E696D697A65643D2266616C7365223E3C7369713A71617420706F736974696F6E3D2230223E3C7369713A736861726564436F6E74726F6C733E3C7369713A636F6E74726F6C206964513D227369713A3136313238222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3136313239222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333532222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333834222076697369626C653D22747275652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333336222076697369626C653D22747275652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333537222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C2F7369713A736861726564436F6E74726F6C733E3C2F7369713A7161743E3C2F7369713A726962626F6E3E3C2F7369713A637573746F6D55493E | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar\ShellBrowser |
| Operation: | write | Name: | ITBar7Layout |
Value: 13000000000000000000000020000000100000000000000001000000010700005E01000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5492 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\f01b4d95cf55d32a.automaticDestinations-ms | binary | |
MD5:8B97E9B8AD4FAAD3A273A243A031FC04 | SHA256:71282E8DE1684C3EAC3F870D21871F6D19E91AFB9F177AC74E3873B2D9E4FC2E | |||
| 5492 | explorer.exe | C:\Users\admin\Desktop\Faktura nr FVMR002084032025_pdf .exe | executable | |
MD5:DC8B99F1D719CBFF82E4CE95CC7277F6 | SHA256:B305160E1C7E573042A3571F0F8B2C59147BB207C415B27F2228CCF29964974A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
38
DNS requests
18
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.140:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.140:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6620 | Faktura nr FVMR002084032025_pdf .exe | GET | 200 | 193.34.212.113:80 | http://193.34.212.113/sk/Ptzknhpum.mp4 | unknown | — | — | unknown |
7448 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7448 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4980 | Faktura nr FVMR002084032025_pdf .exe | GET | 200 | 193.34.212.113:80 | http://193.34.212.113/sk/Ptzknhpum.mp4 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.140:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.140:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5588 | InstallUtil.exe | A Network Trojan was detected | LOADER [ANY.RUN] PureLogs Download Attempt (LOAD) |
3304 | InstallUtil.exe | A Network Trojan was detected | LOADER [ANY.RUN] PureLogs Download Attempt (LOAD) |