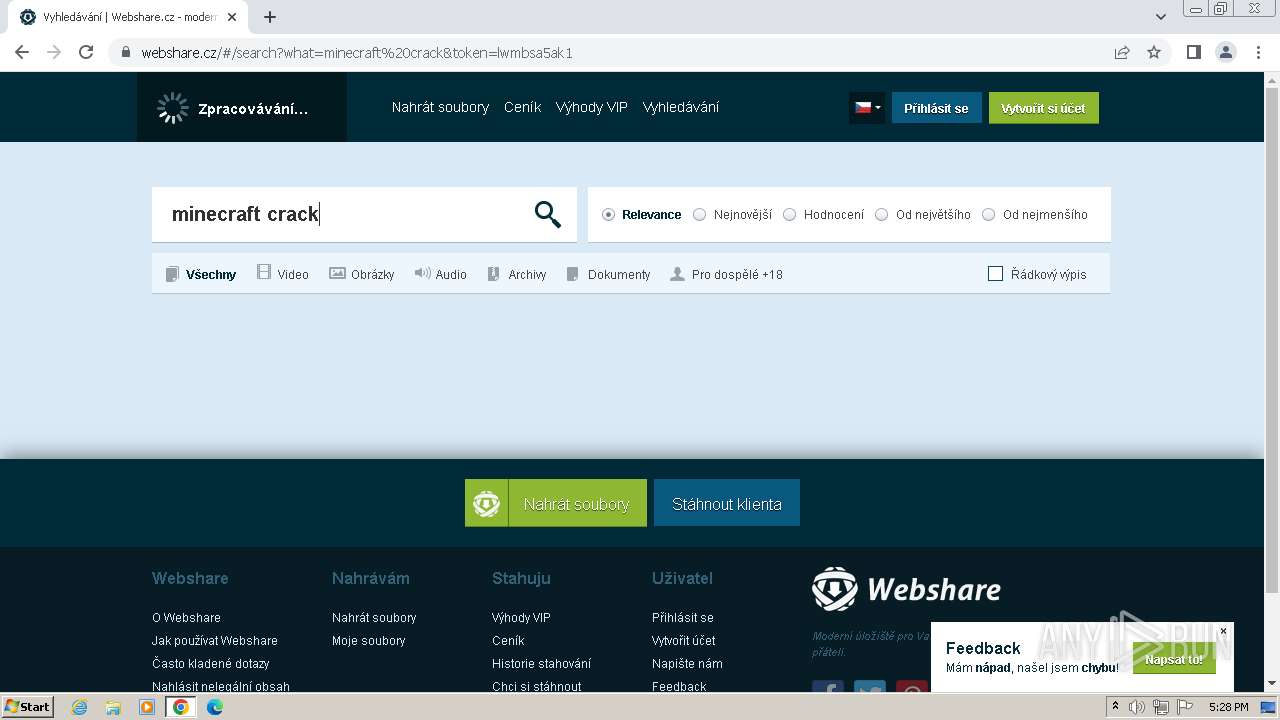
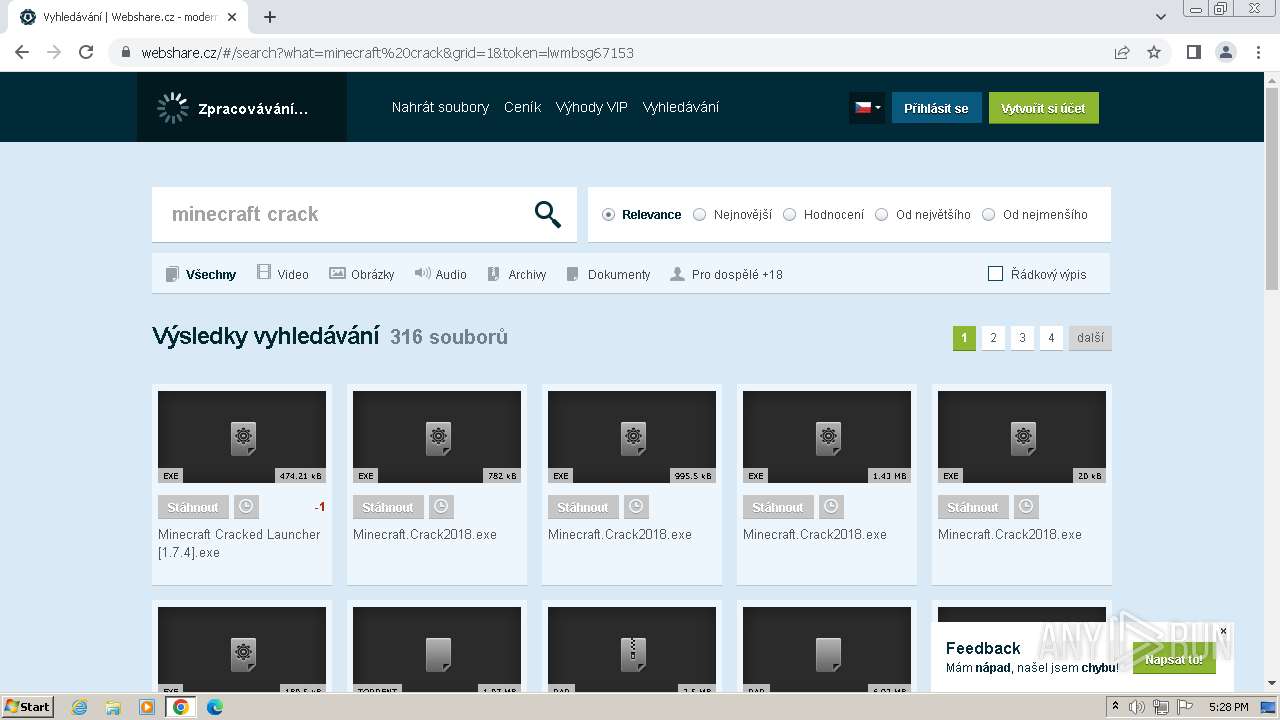
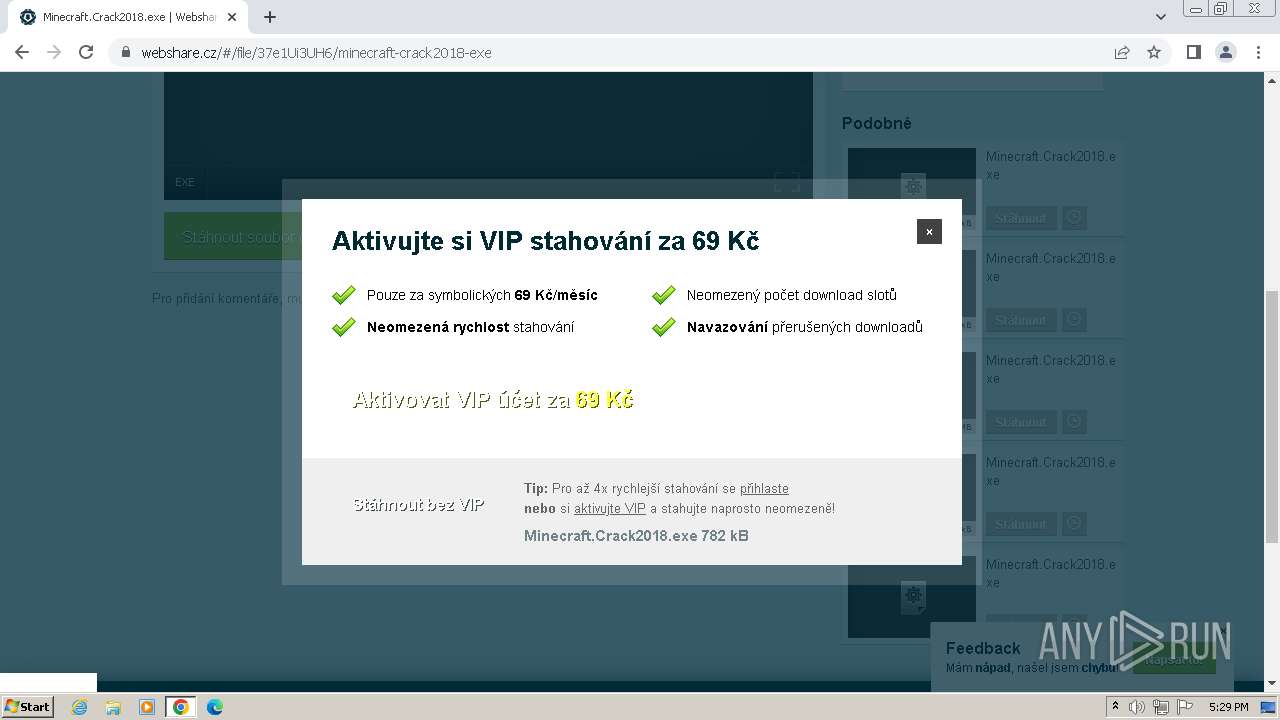
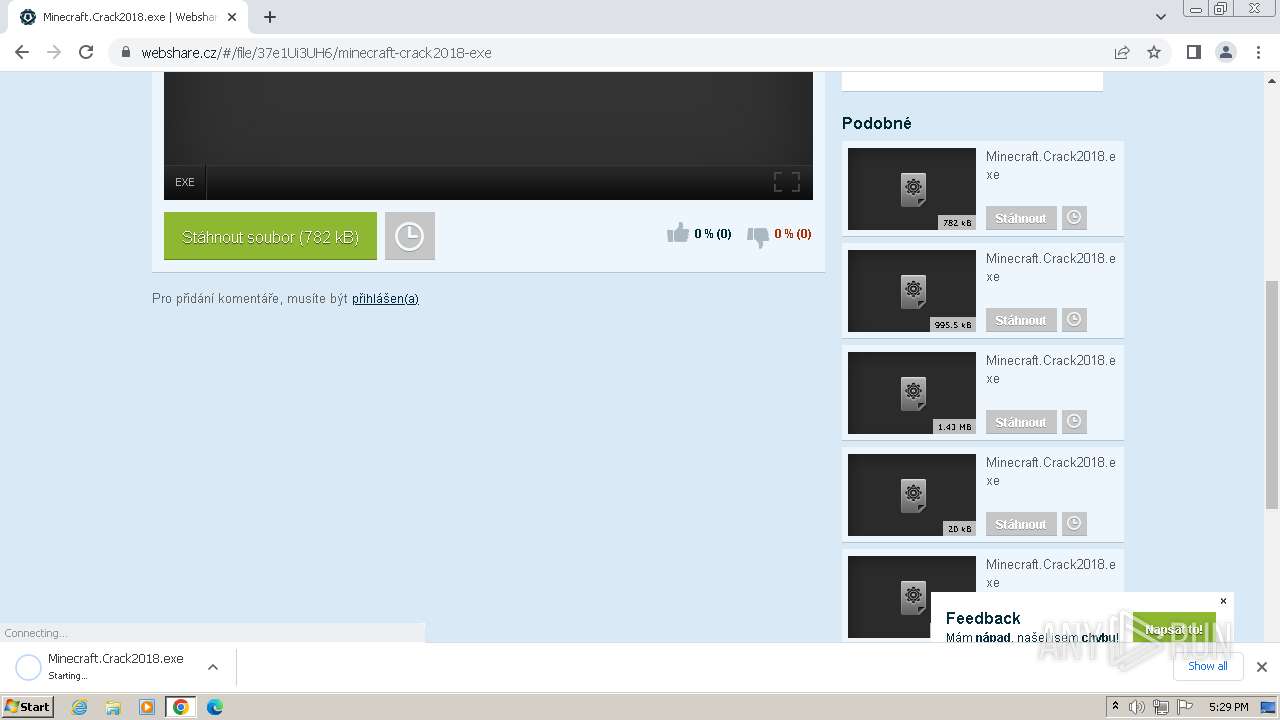
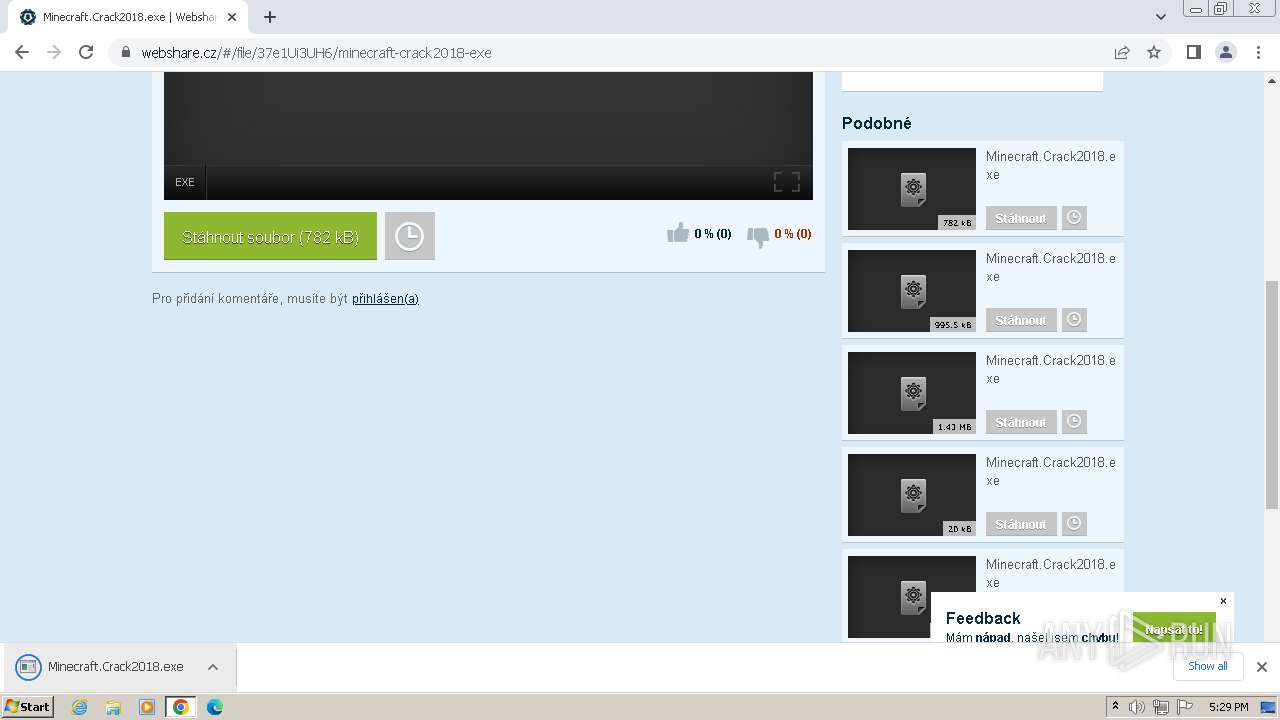
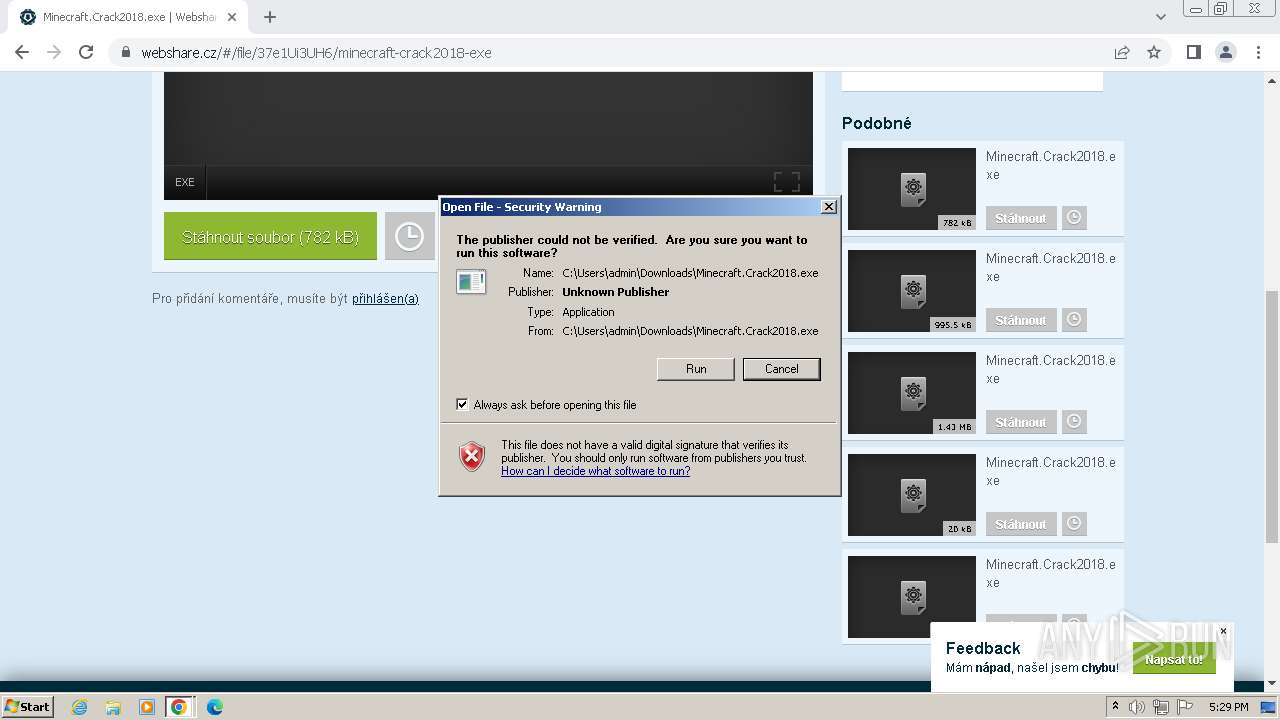
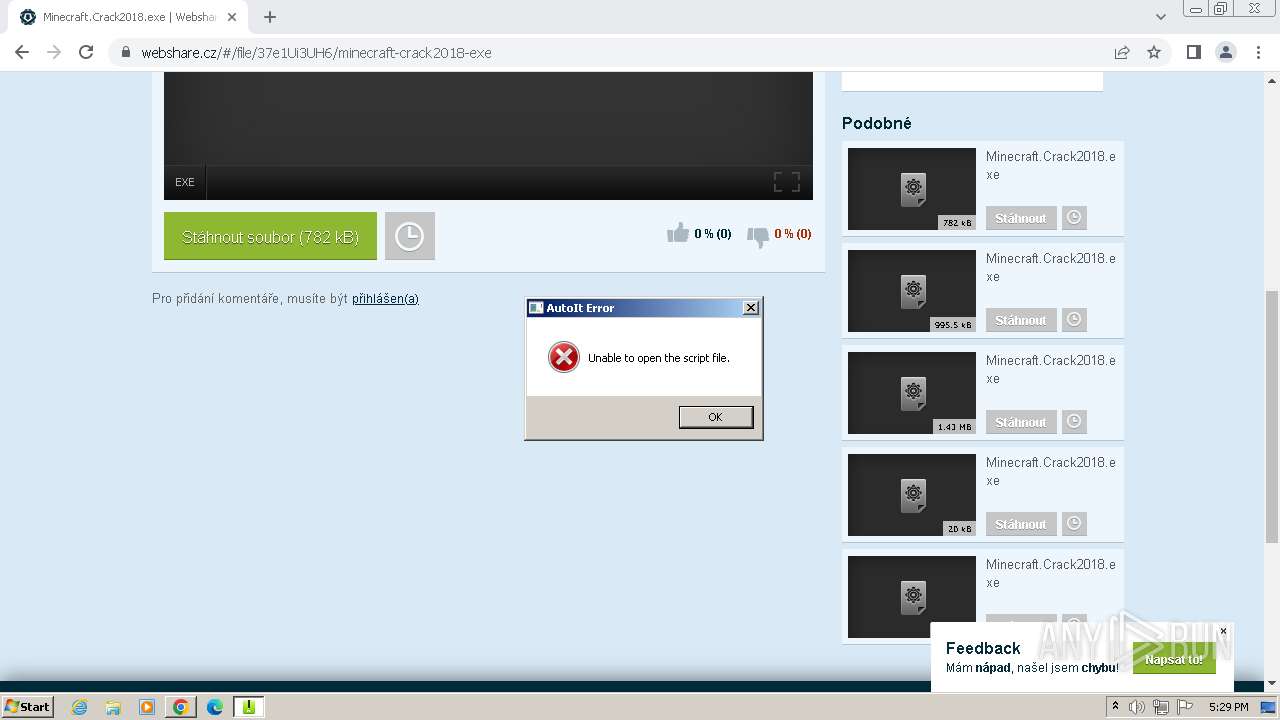
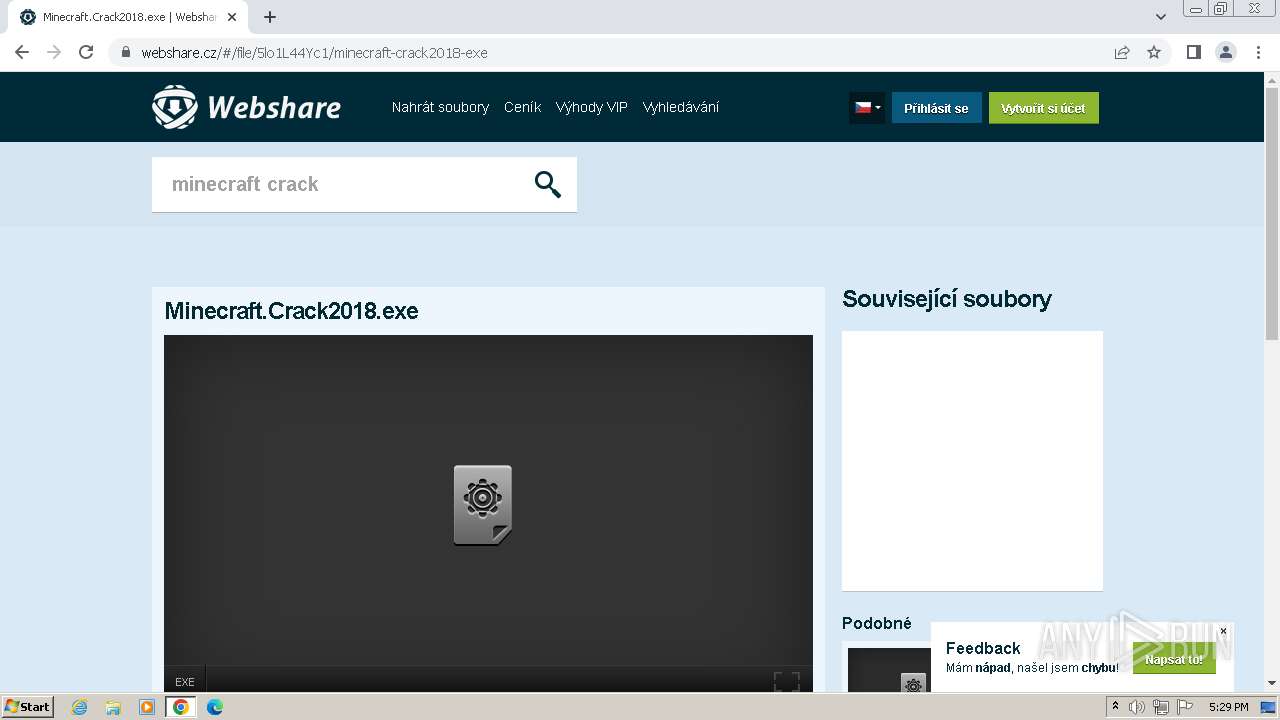
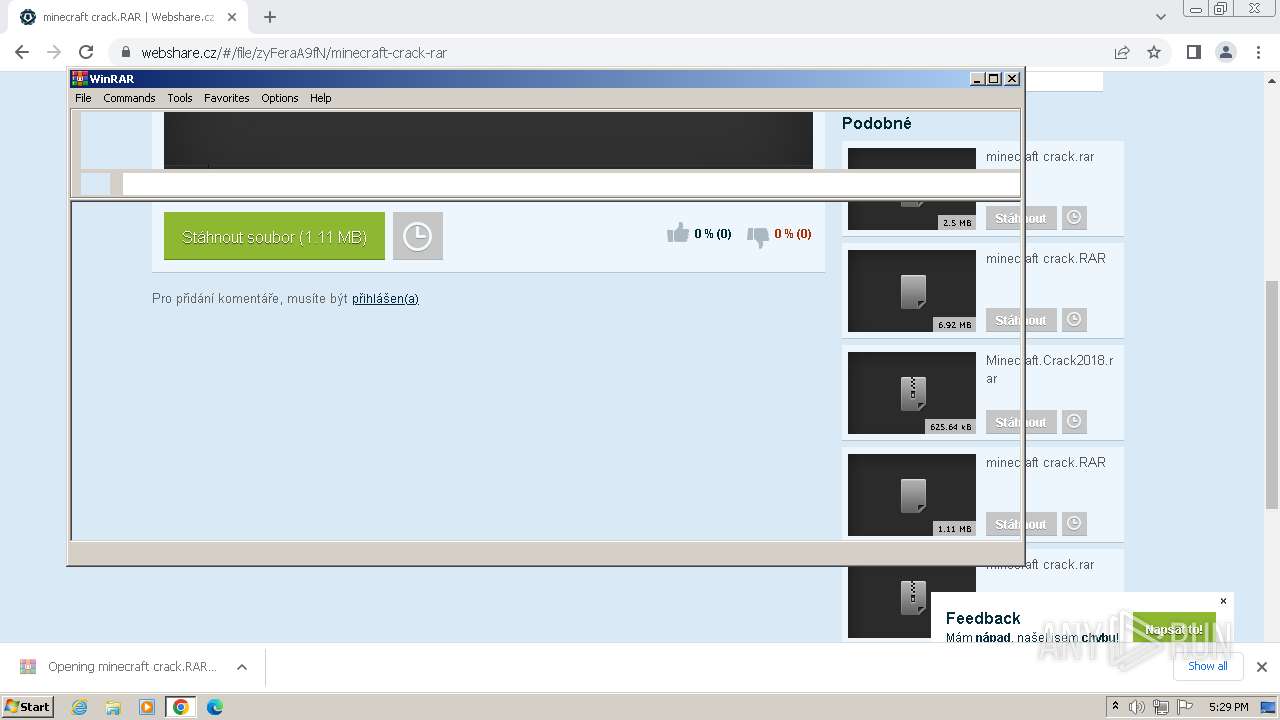
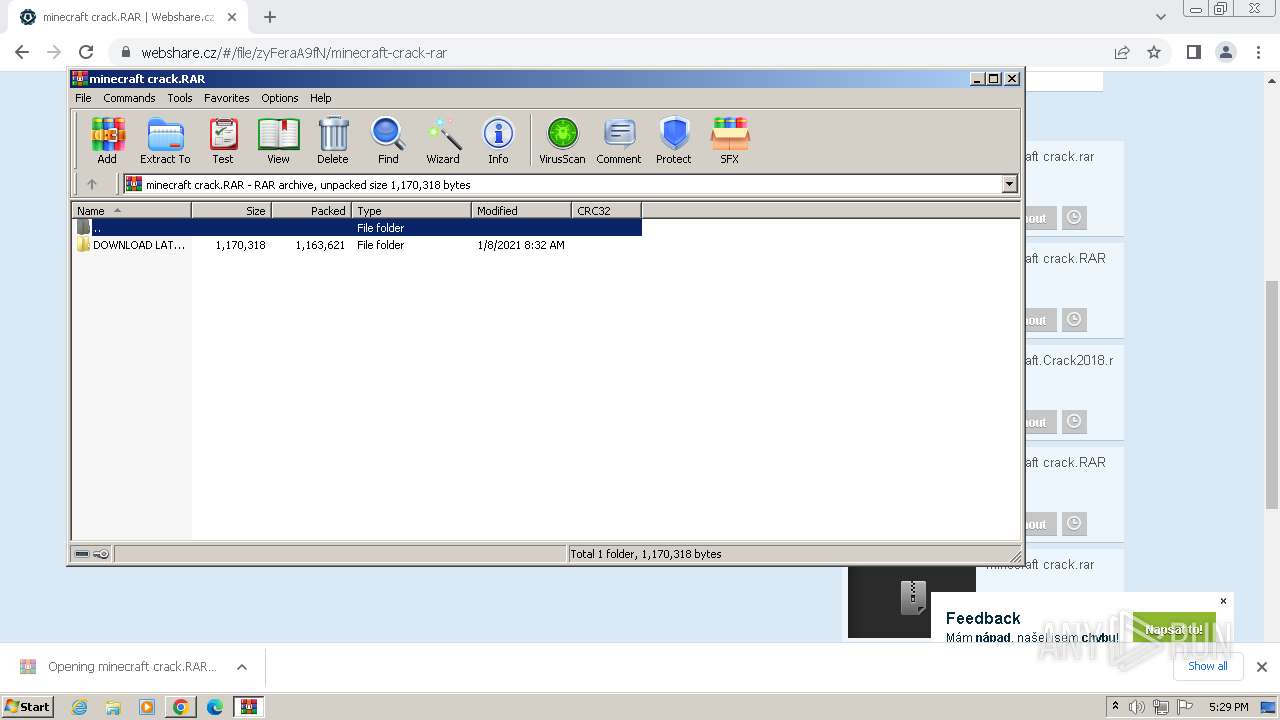
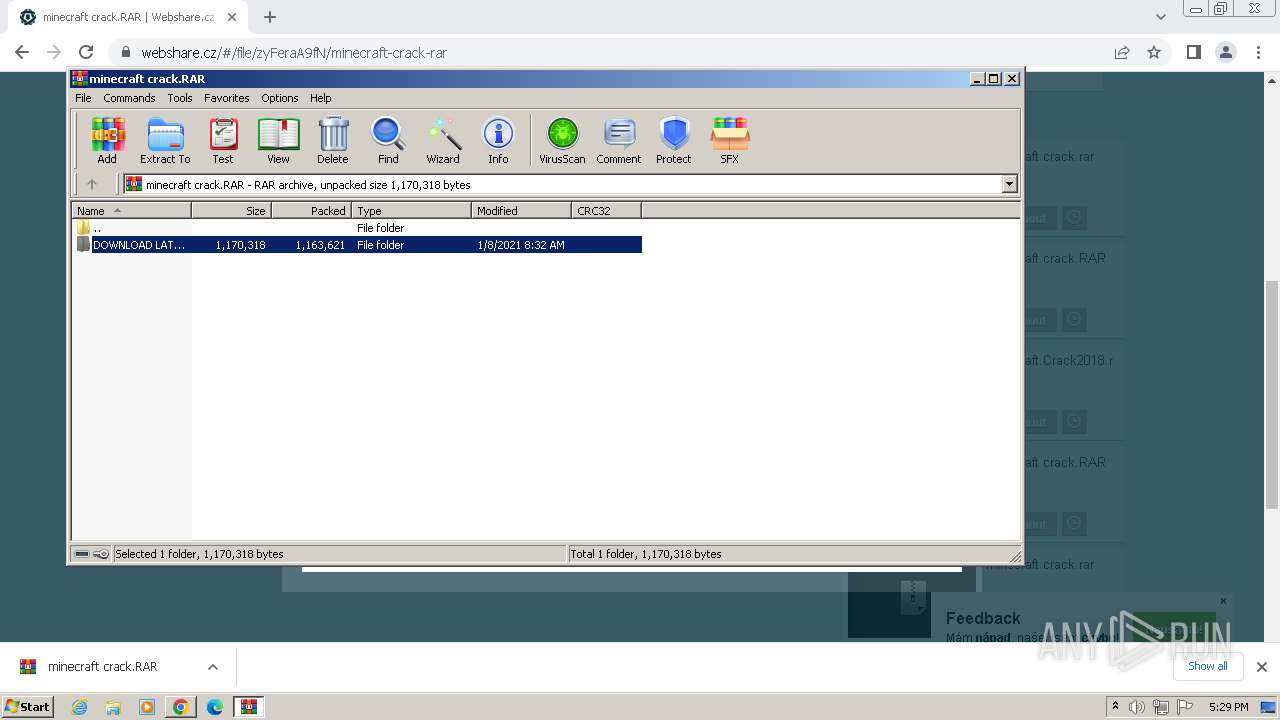
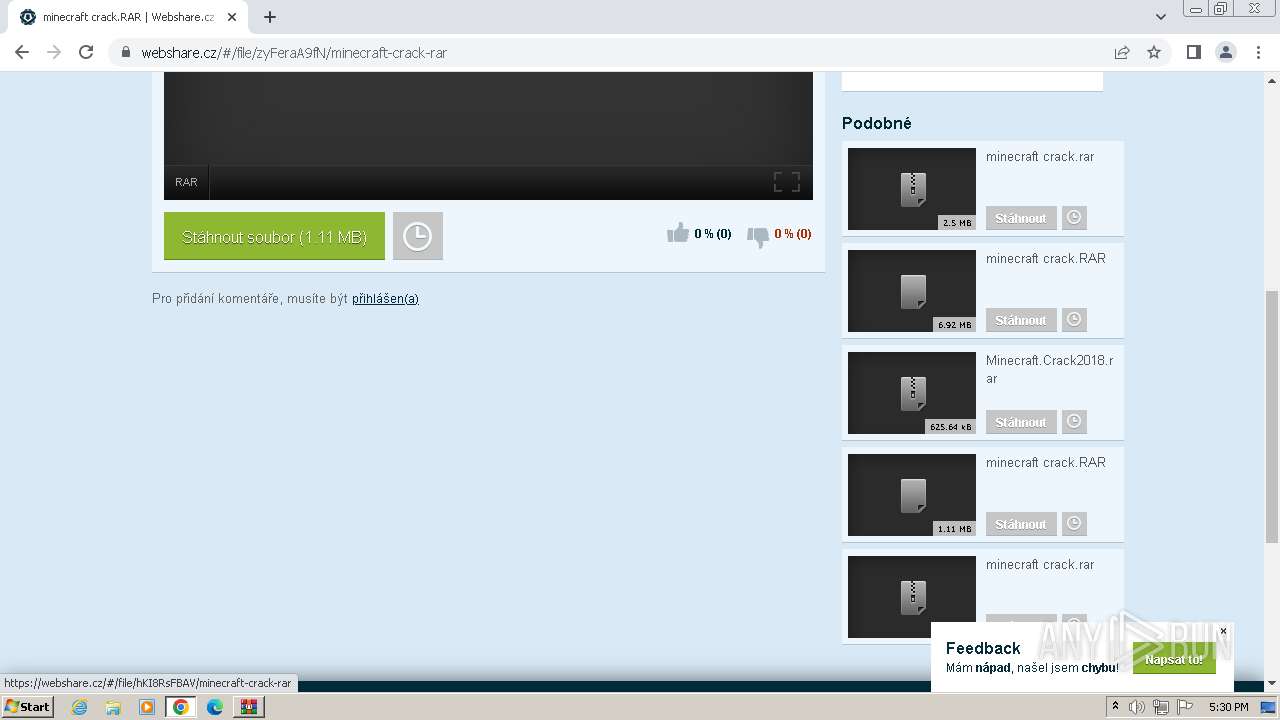
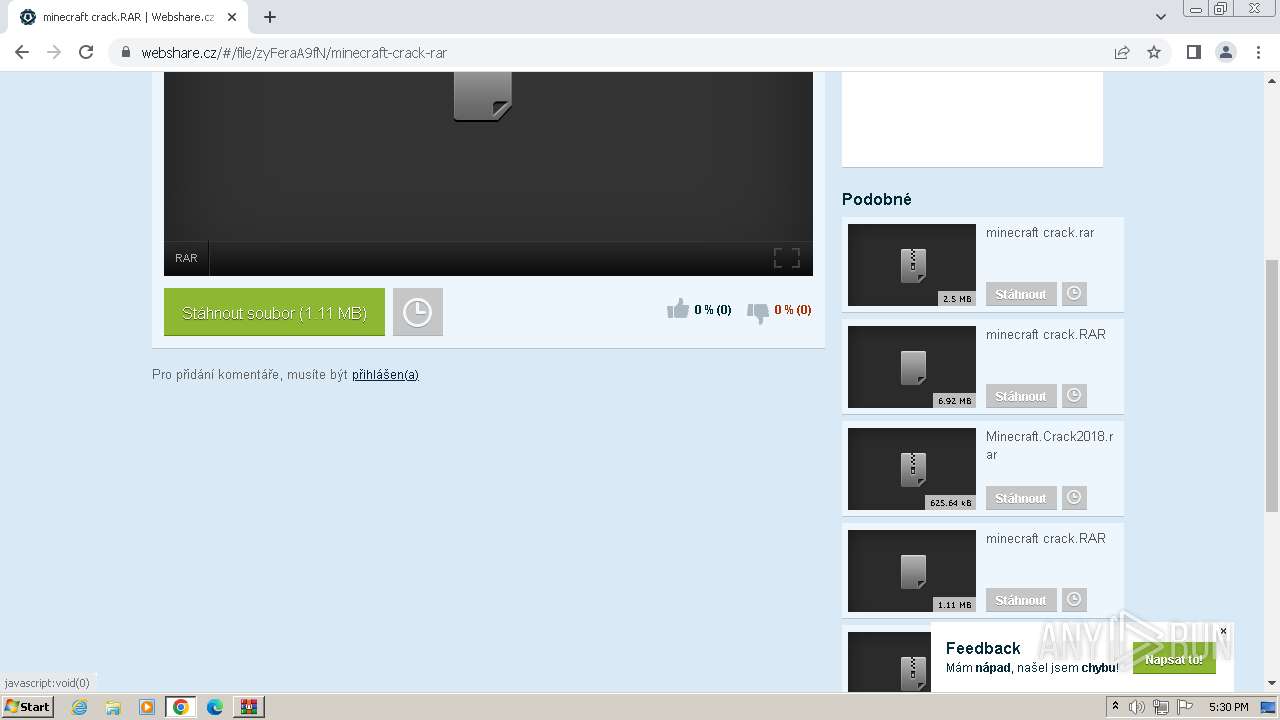
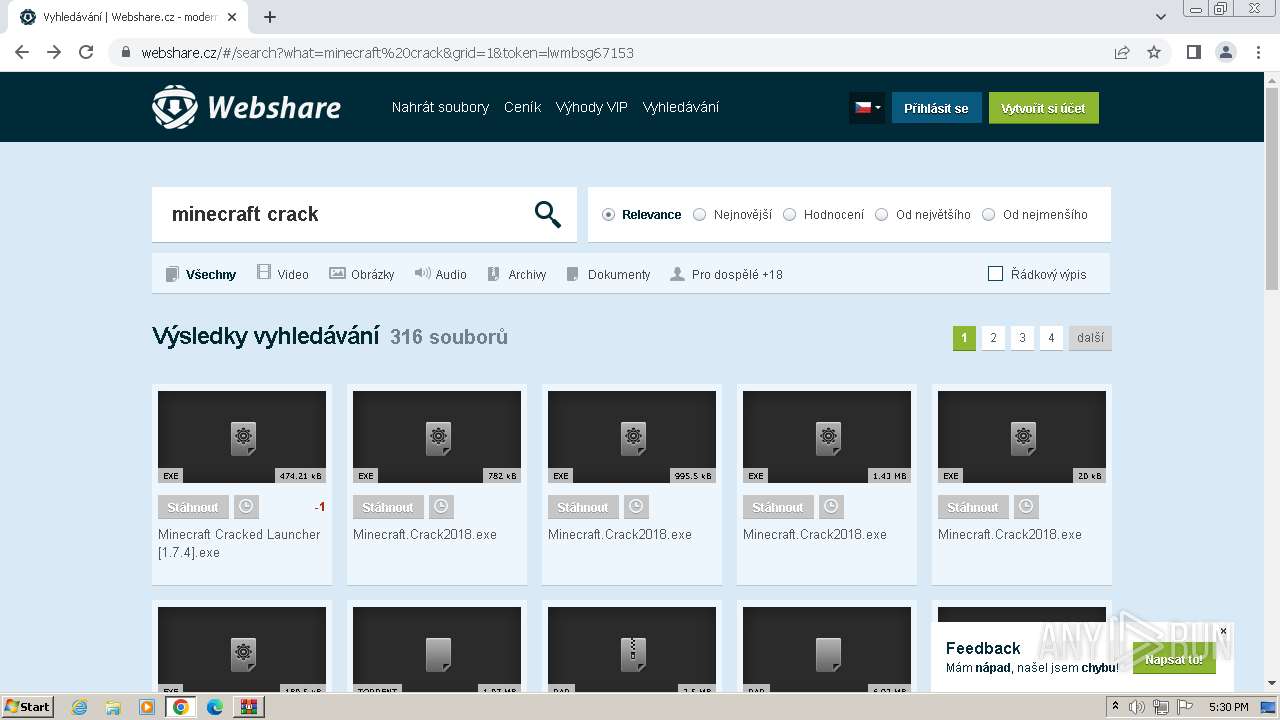
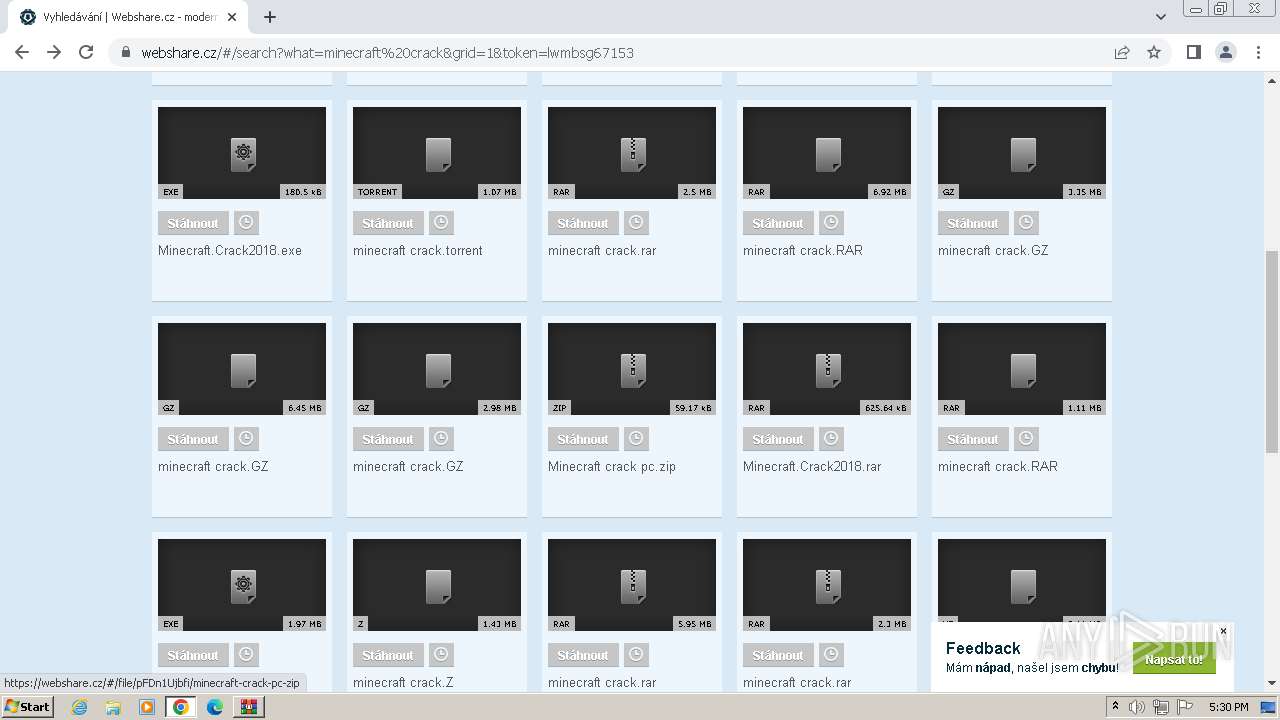
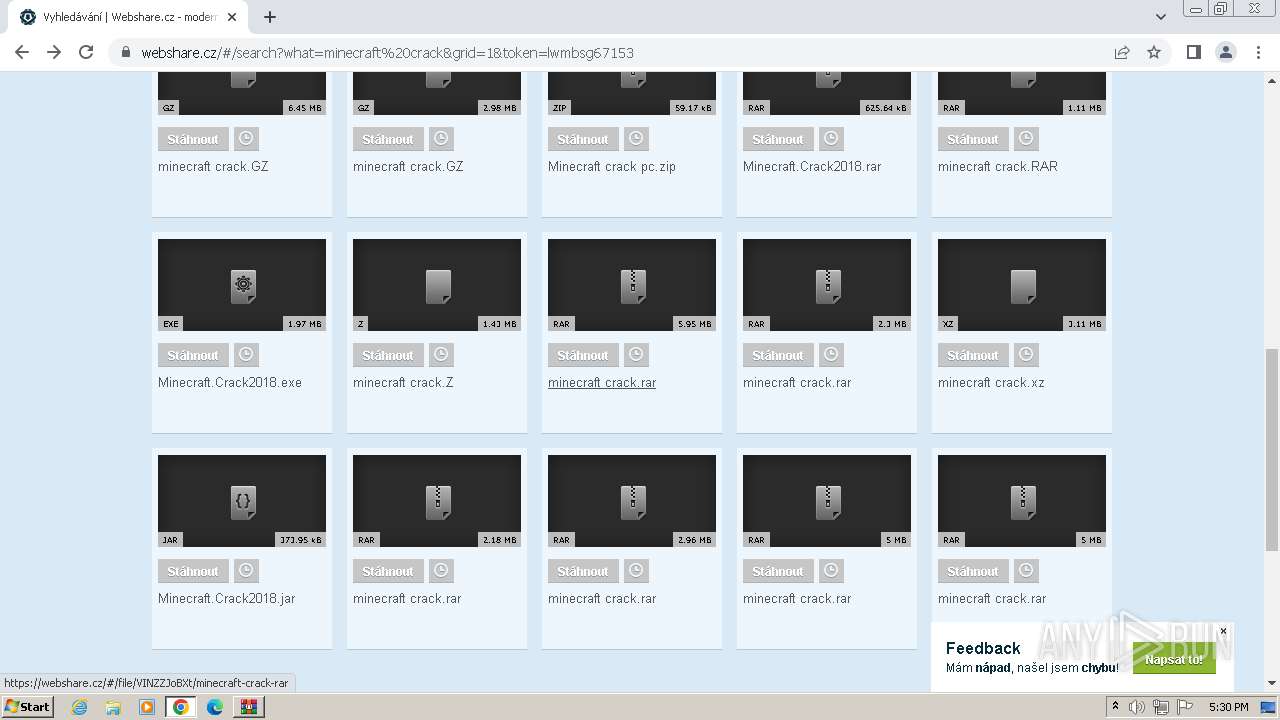
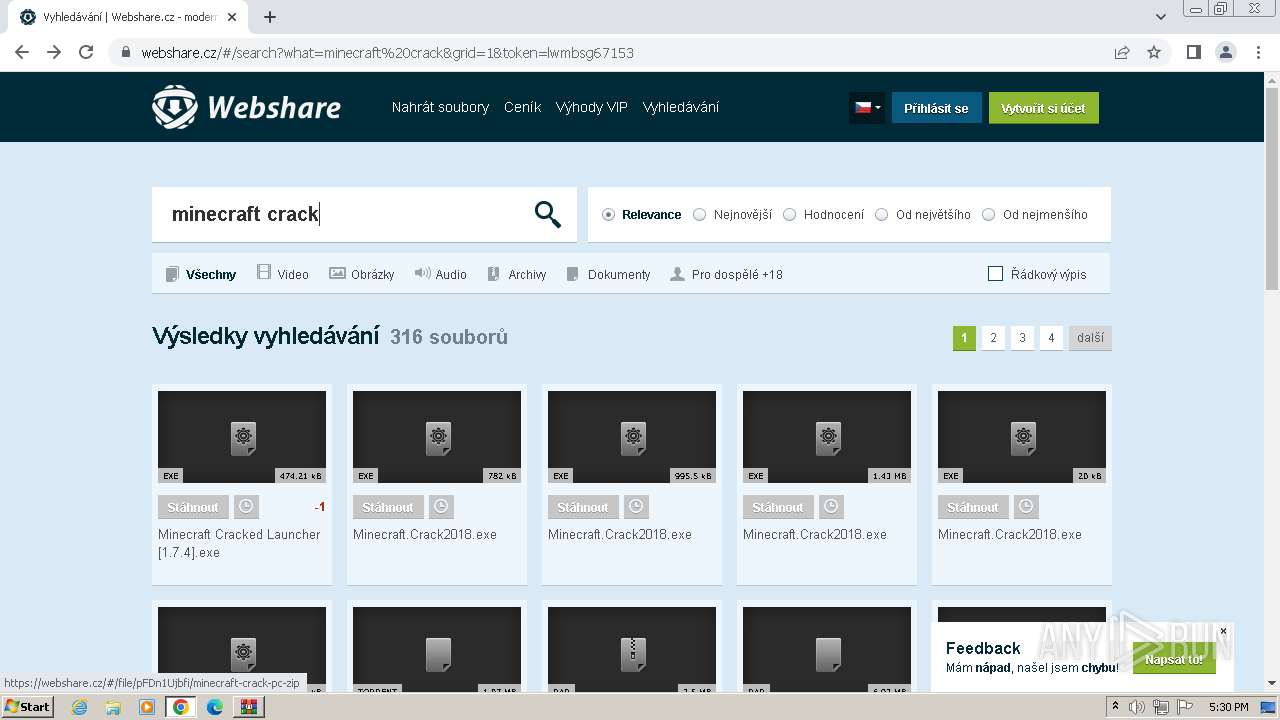
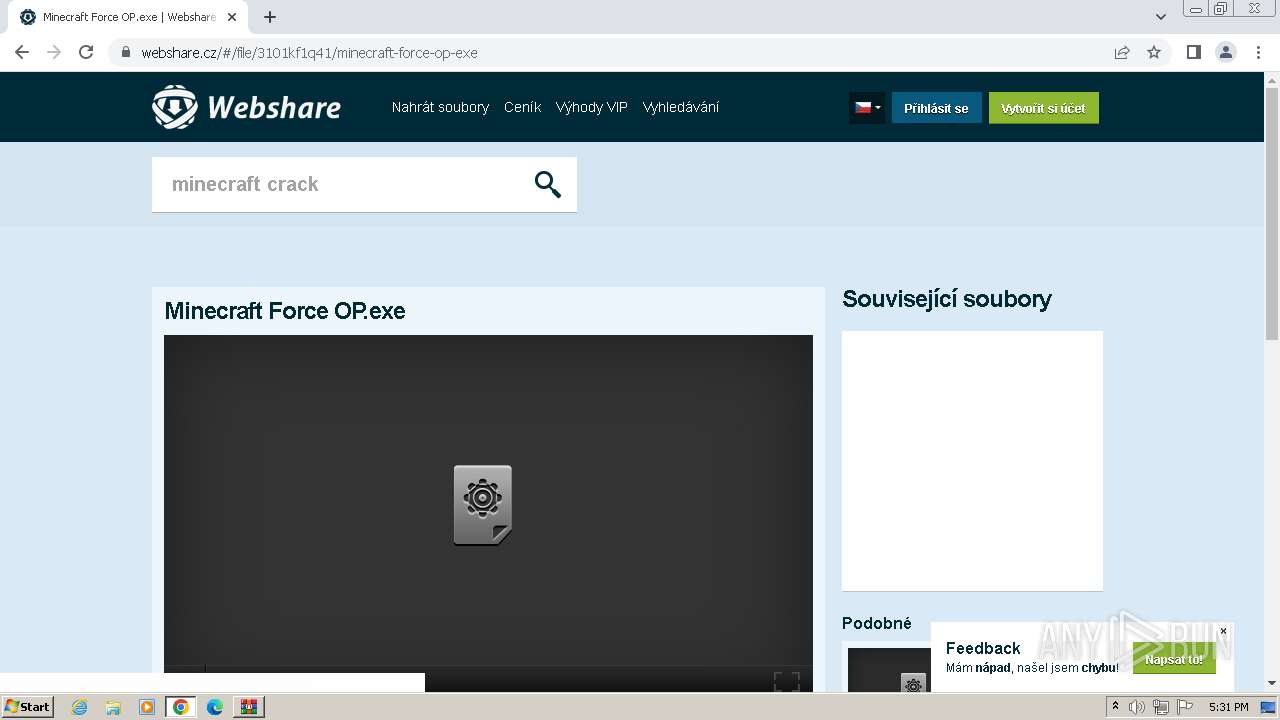
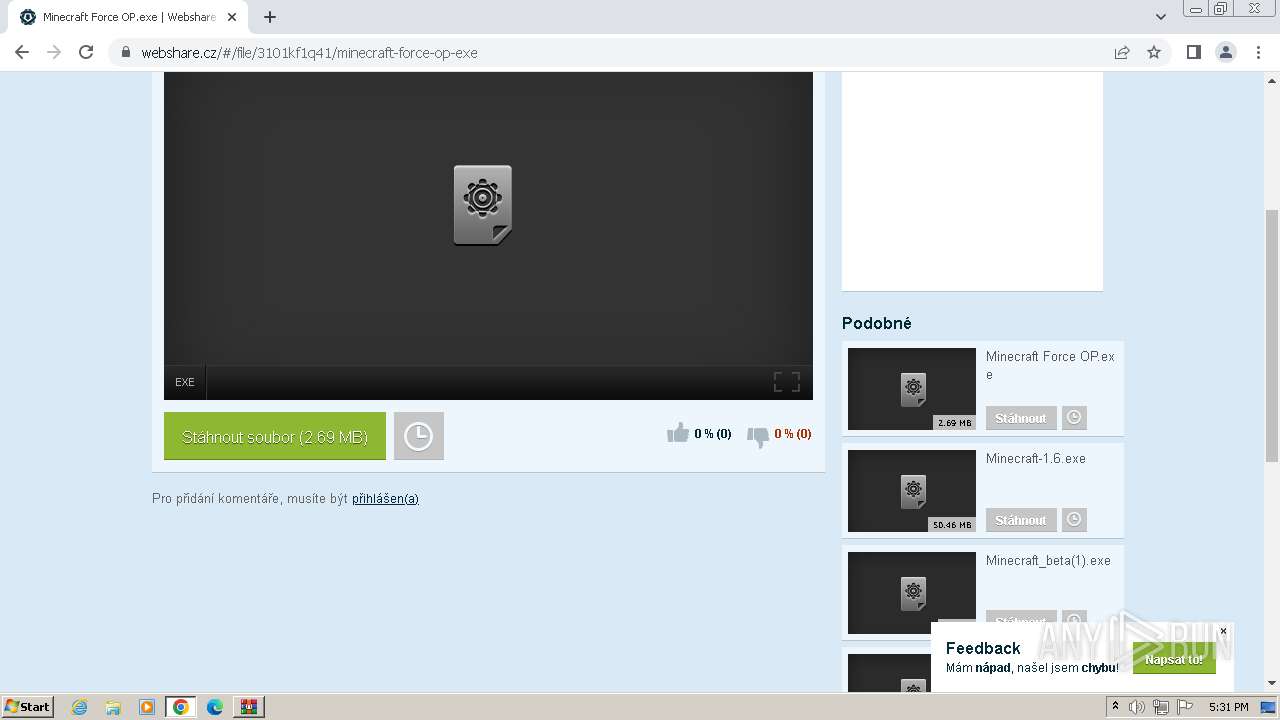
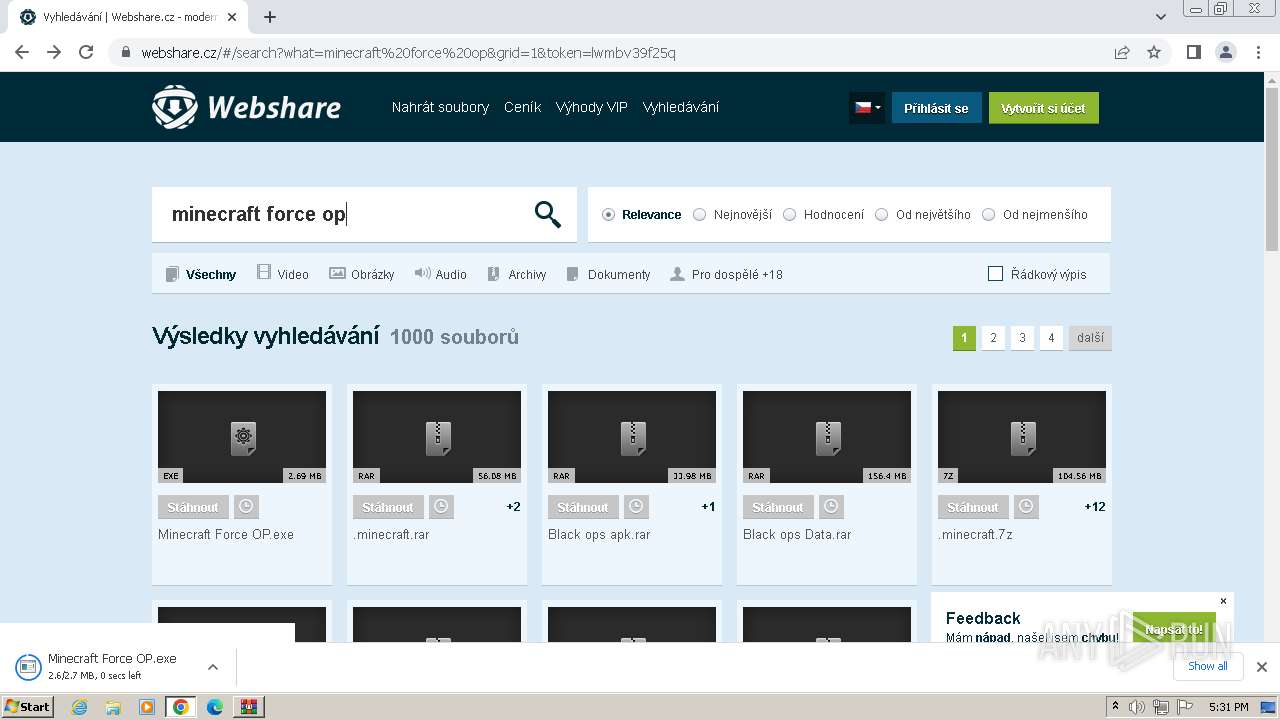
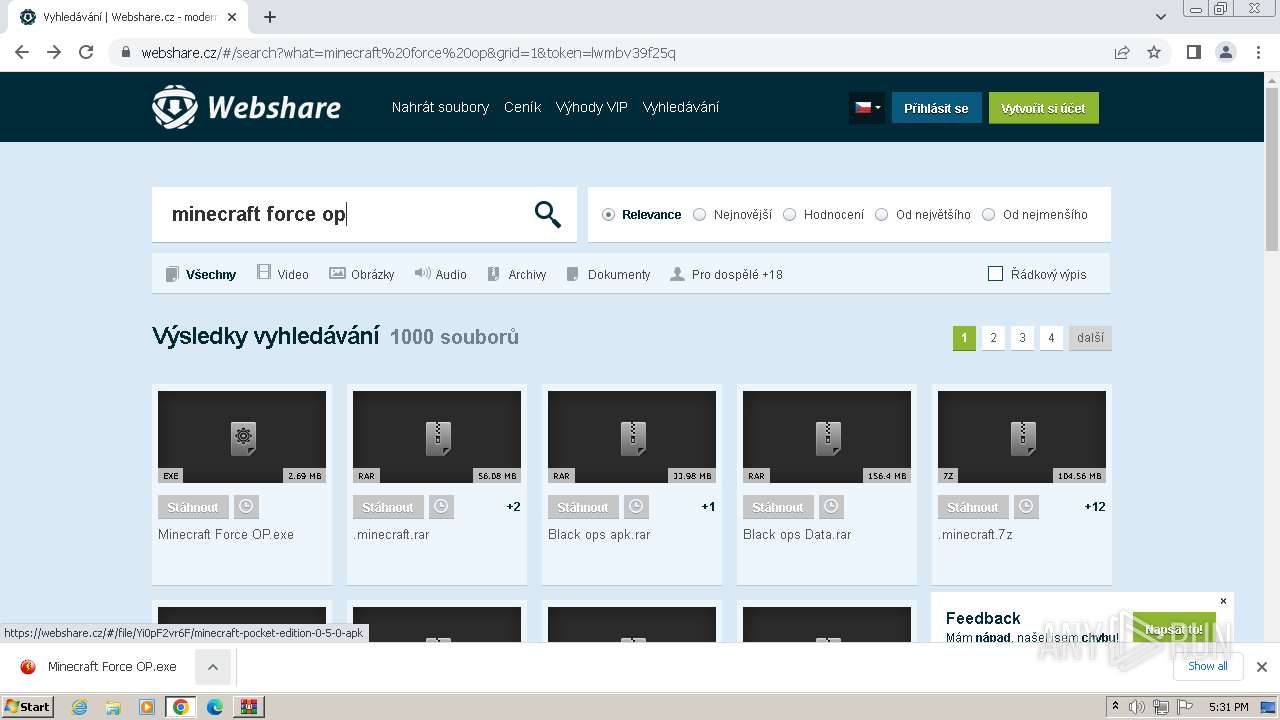
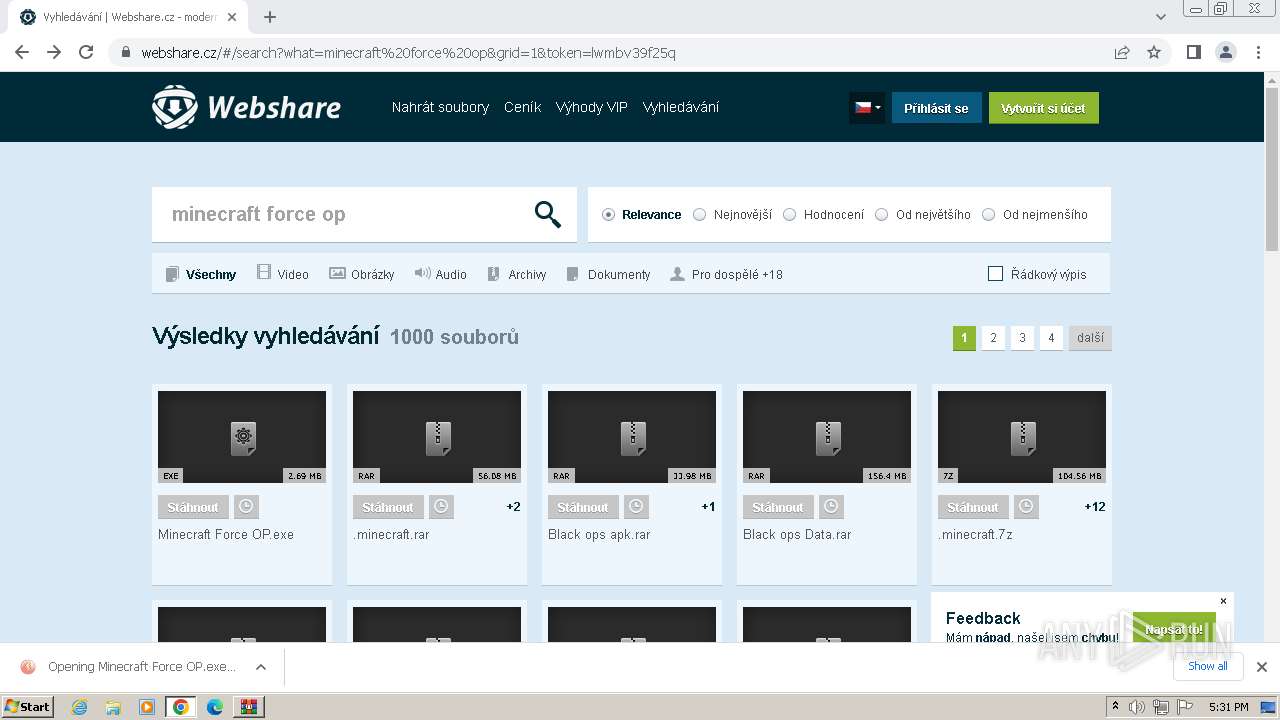
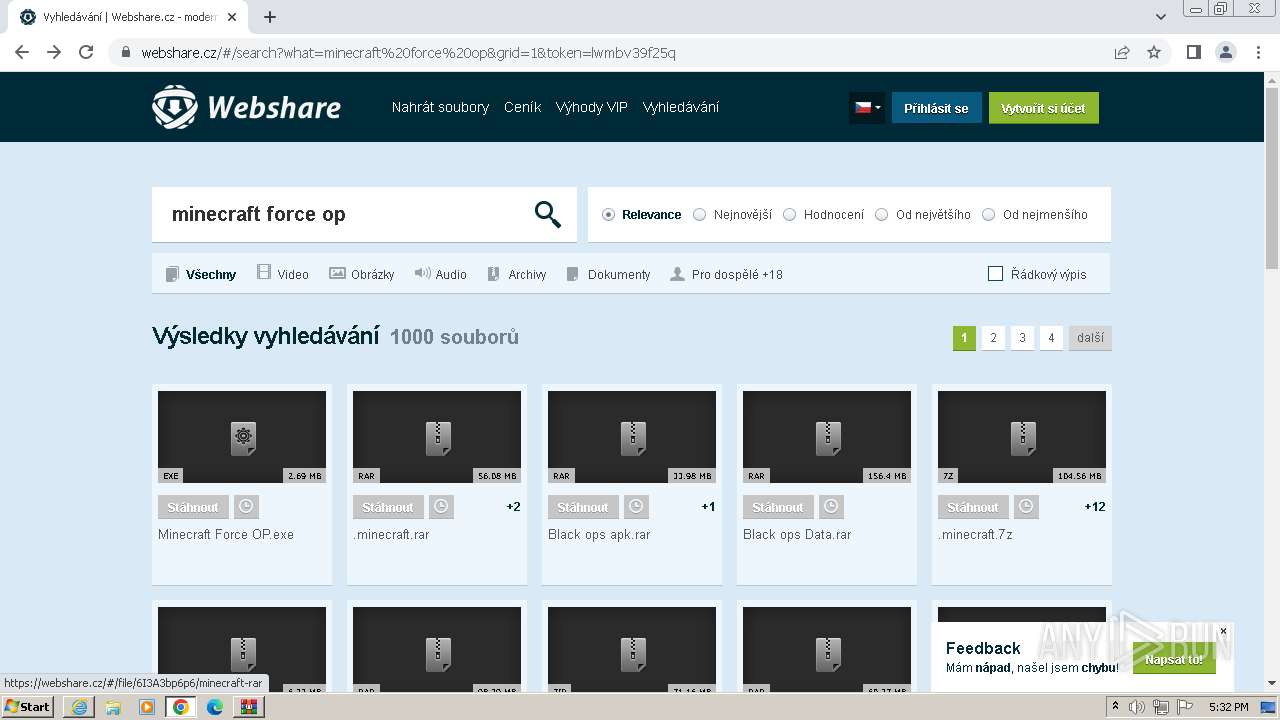
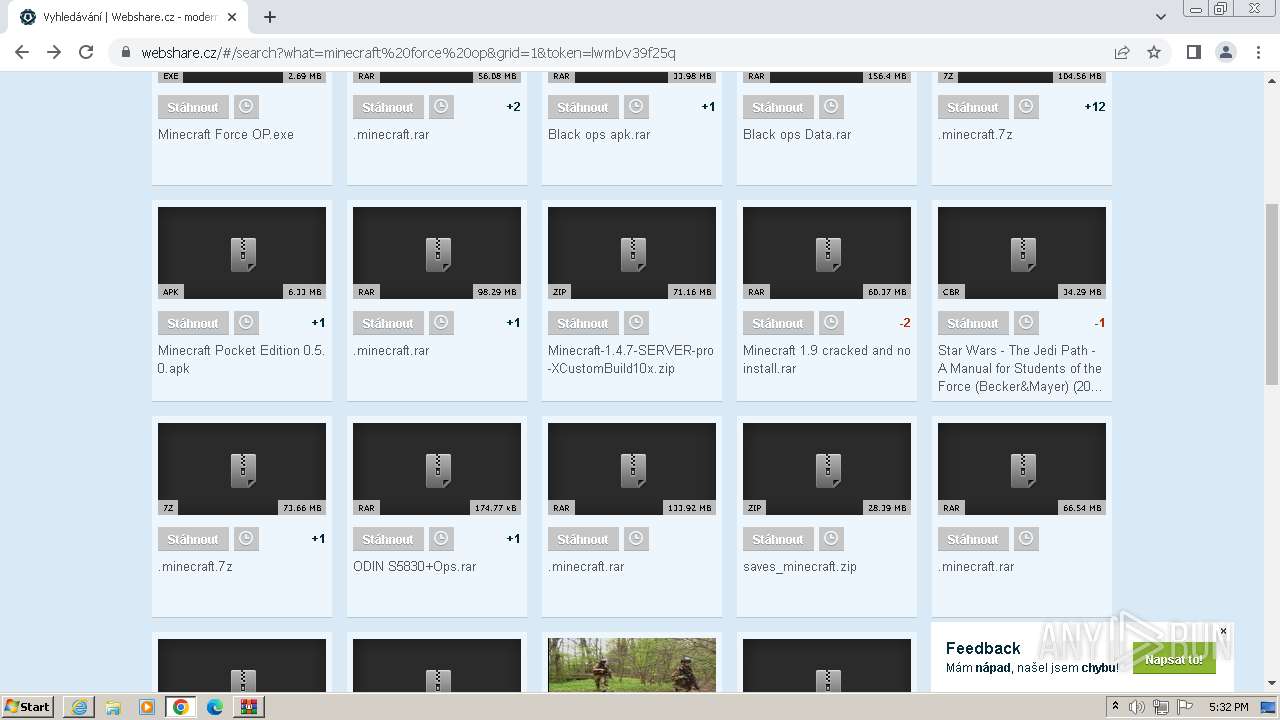
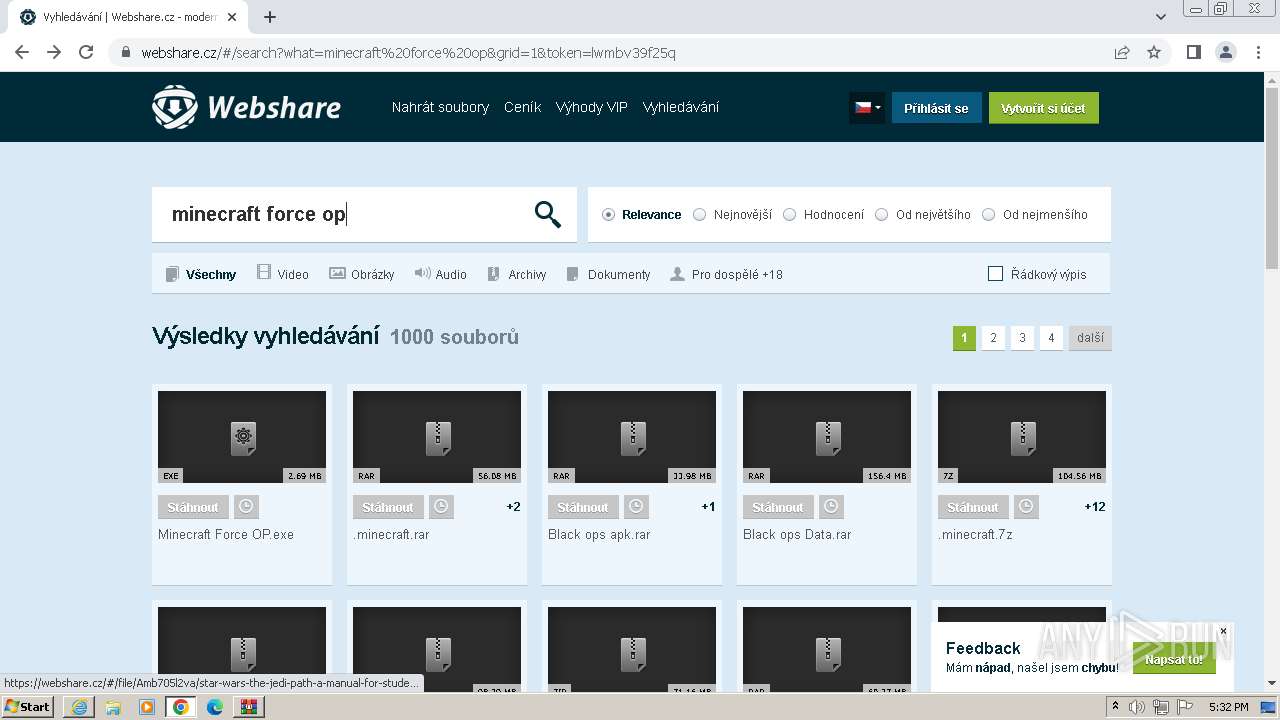
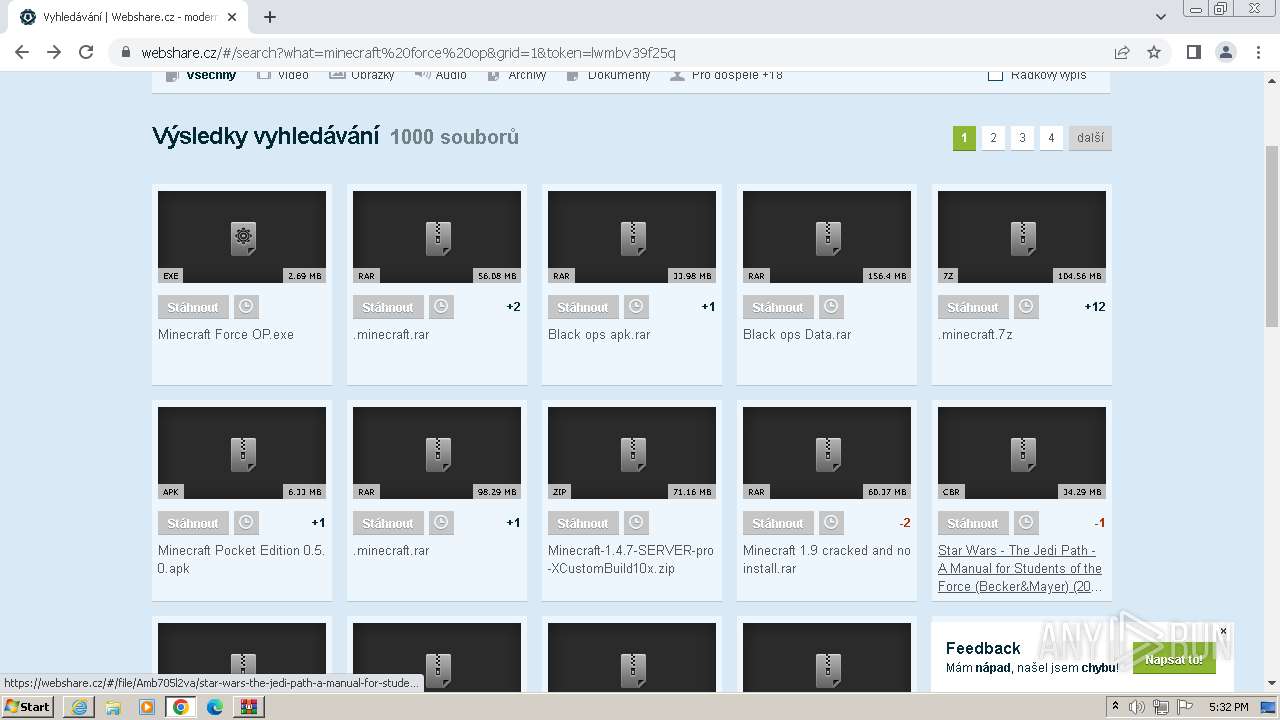
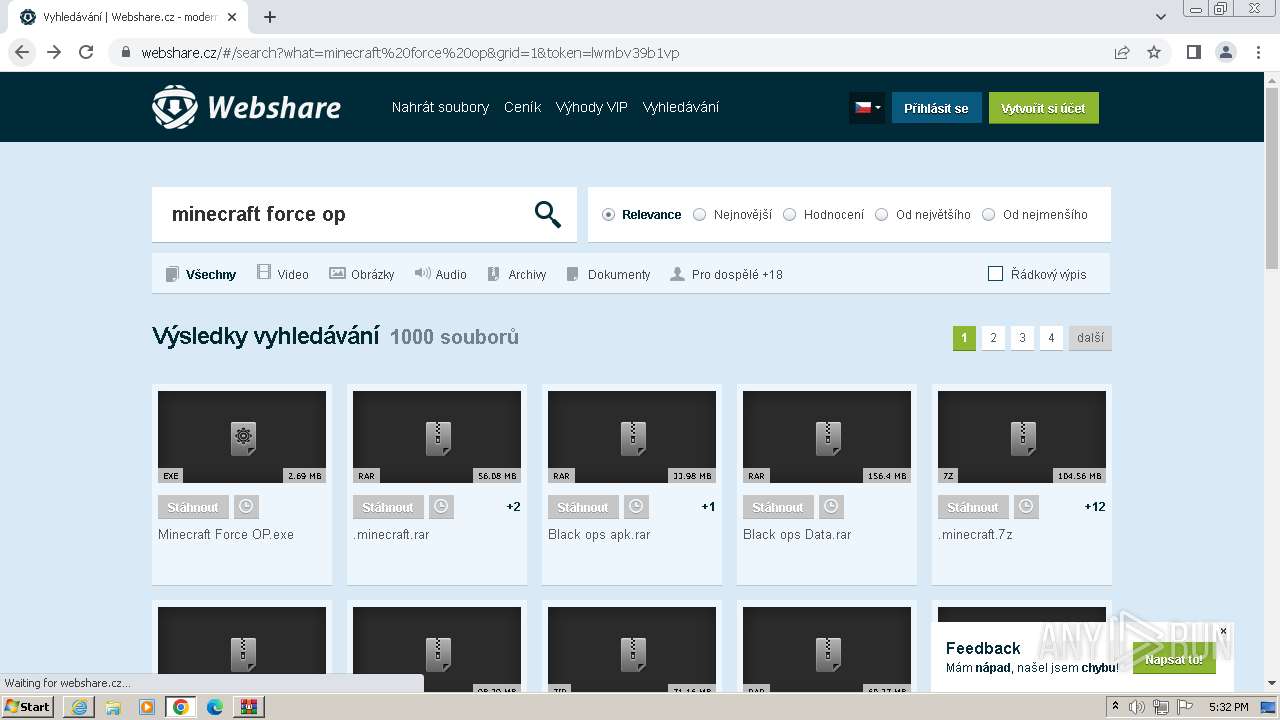
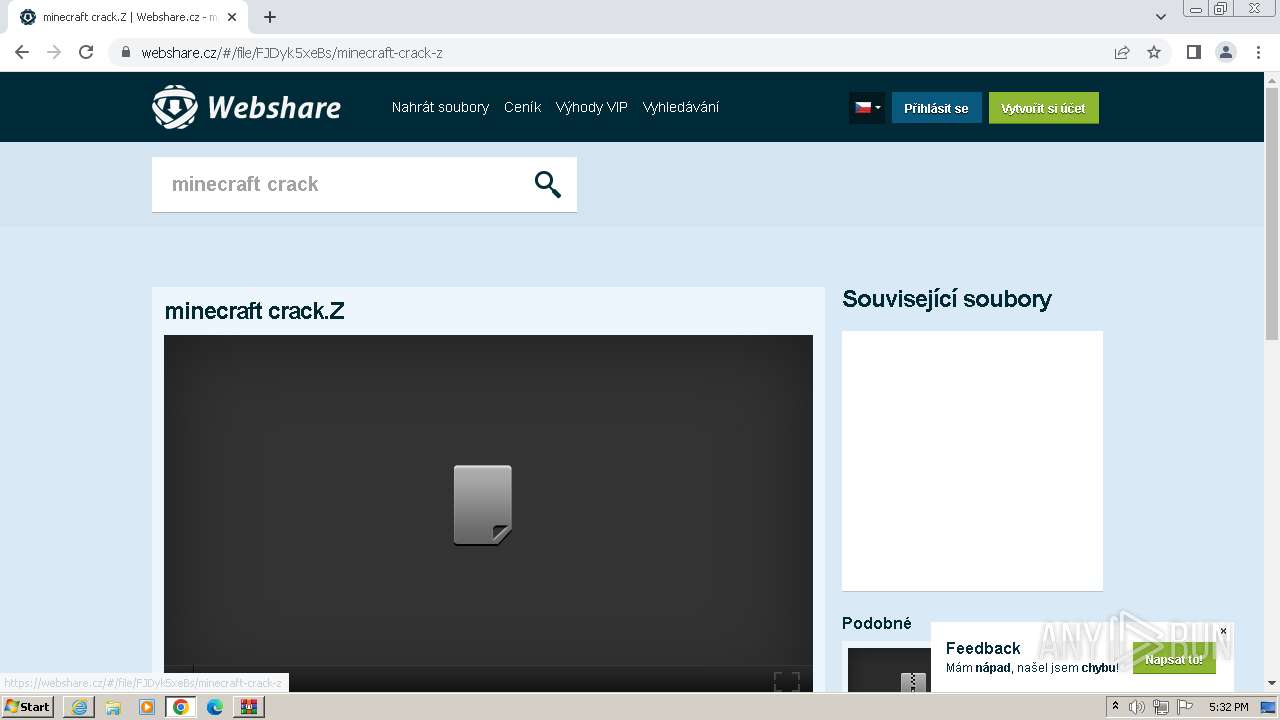
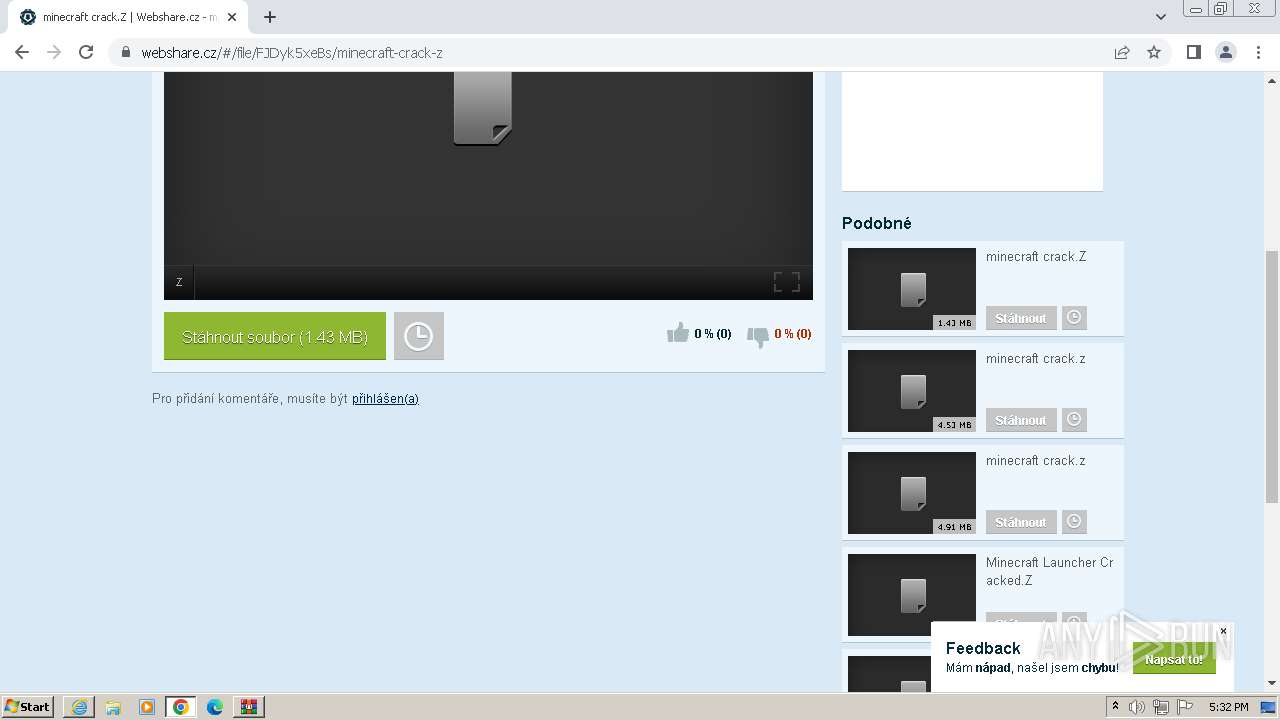
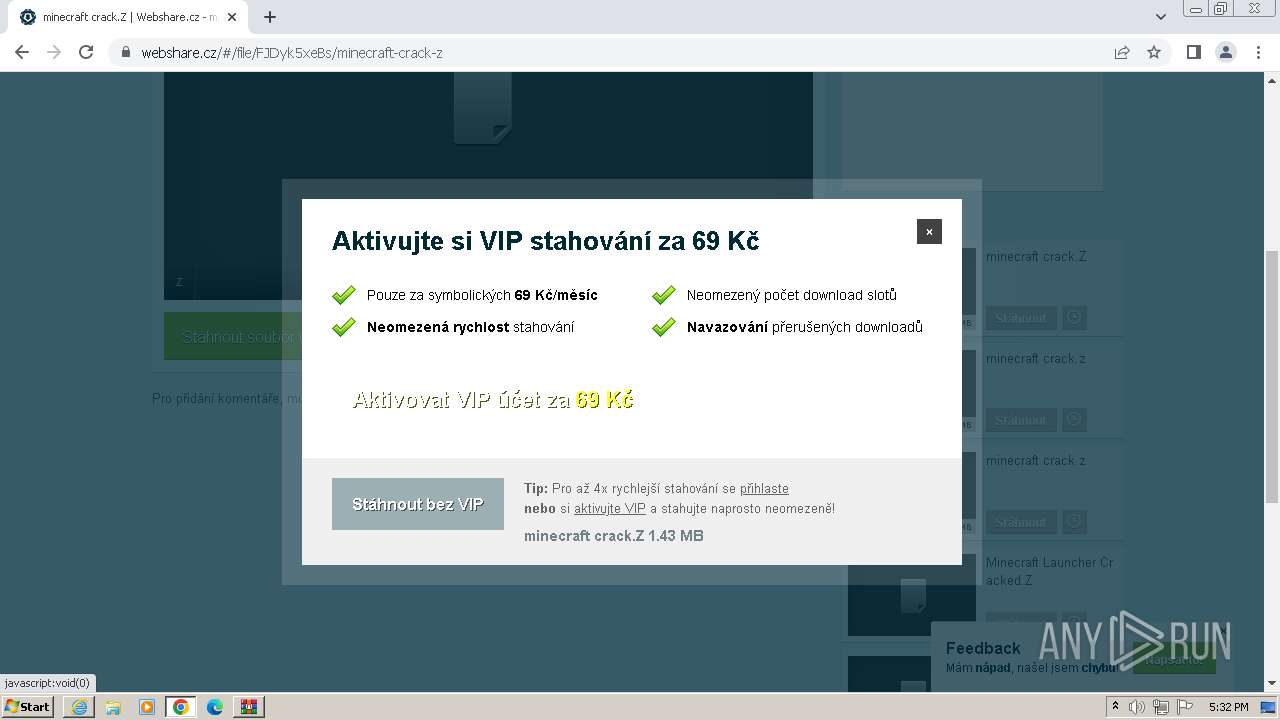
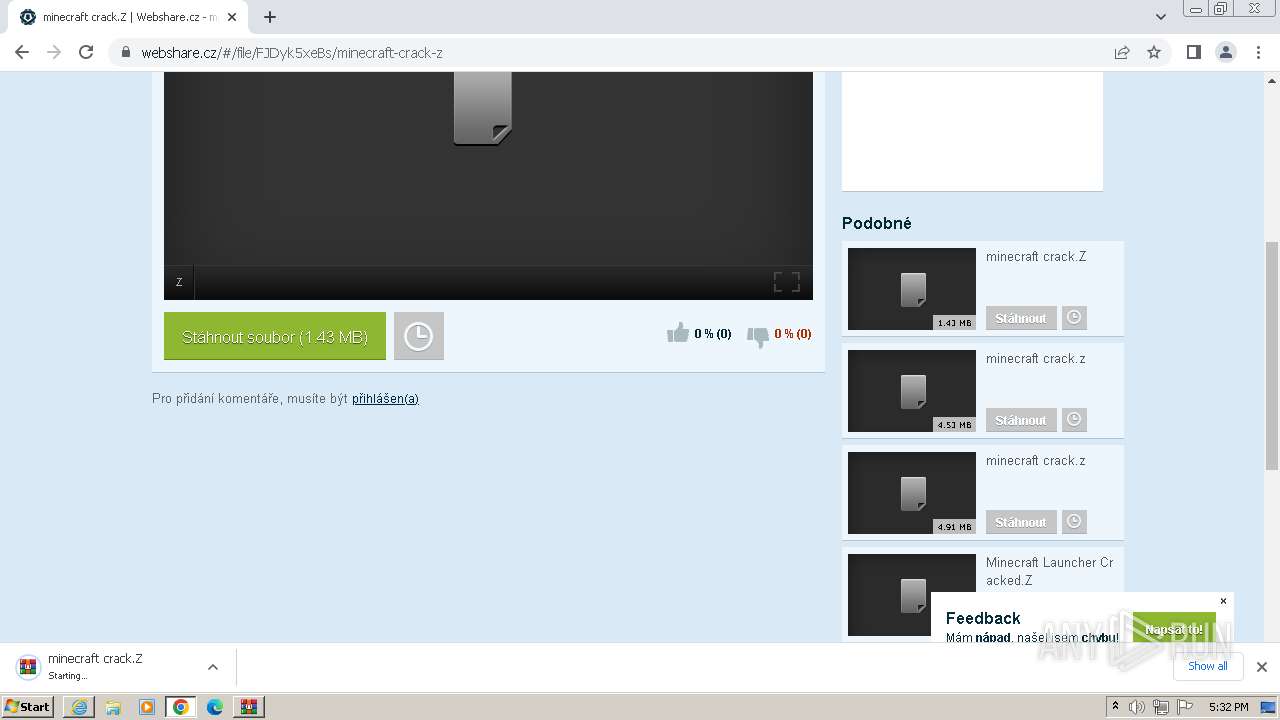
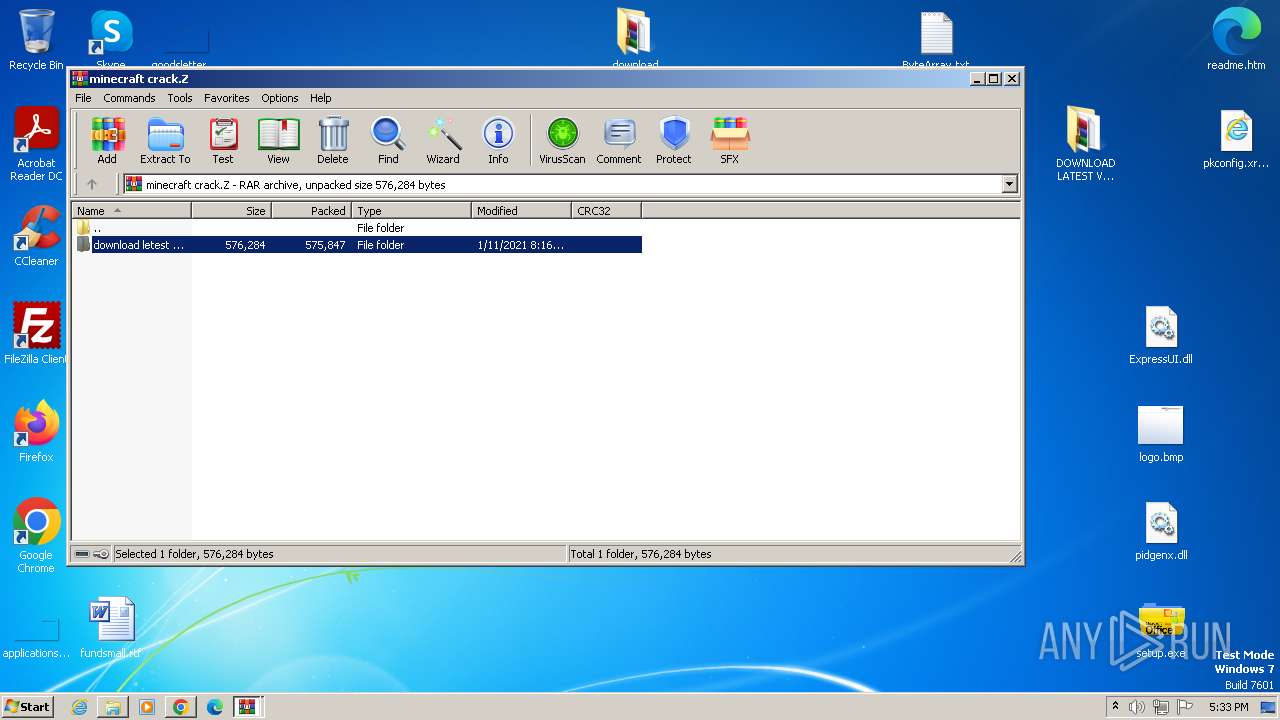
| URL: | https://webshare.cz/#/file/3142VS6bb4/minecraft-cracked-launcher-1-7-4-exe |
| Full analysis: | https://app.any.run/tasks/92f5459f-0e8b-4973-9c67-cc0cb7ce8454 |
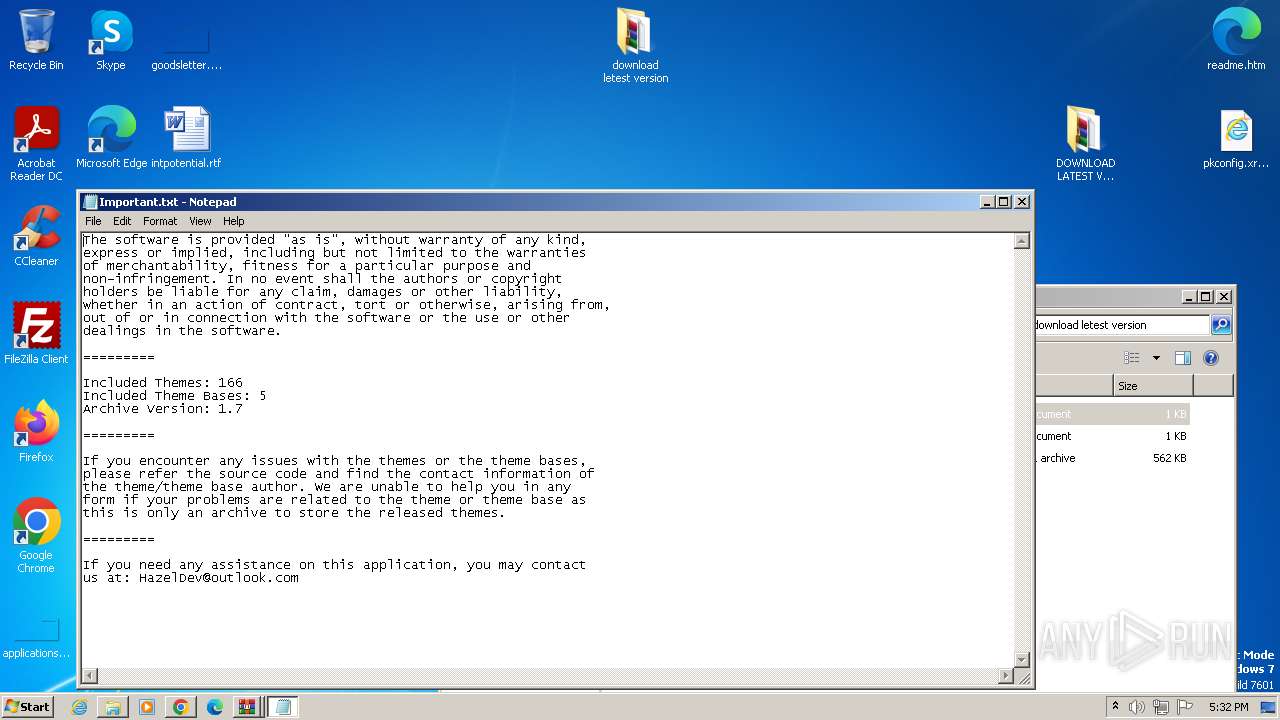
| Verdict: | Malicious activity |
| Threats: | njRAT is a remote access trojan. It is one of the most widely accessible RATs on the market that features an abundance of educational information. Interested attackers can even find tutorials on YouTube. This allows it to become one of the most popular RATs in the world. |
| Analysis date: | May 25, 2024, 16:28:33 |
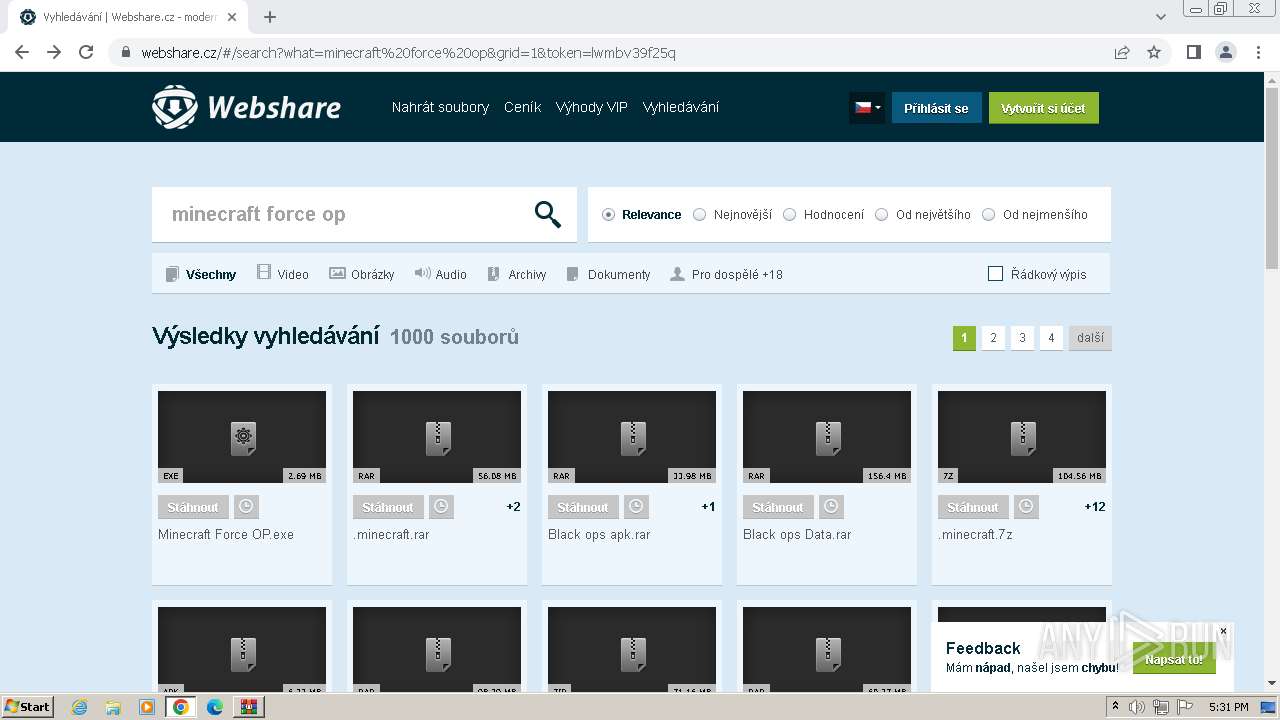
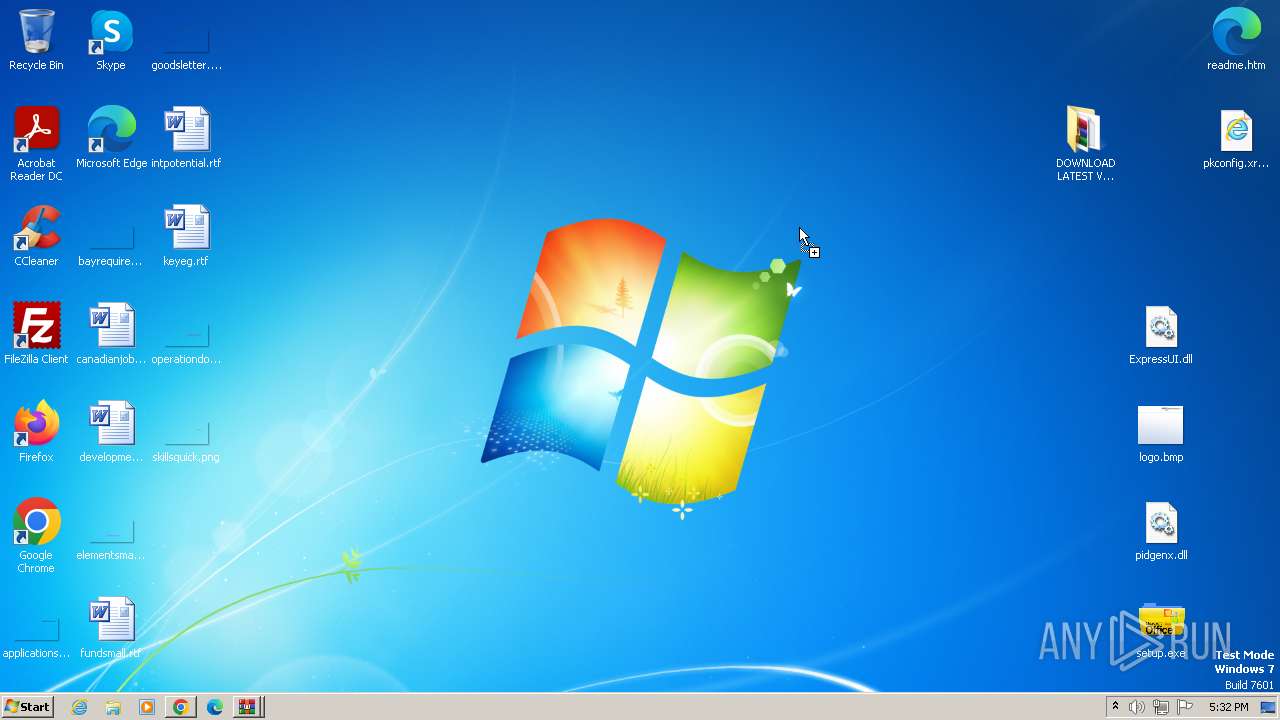
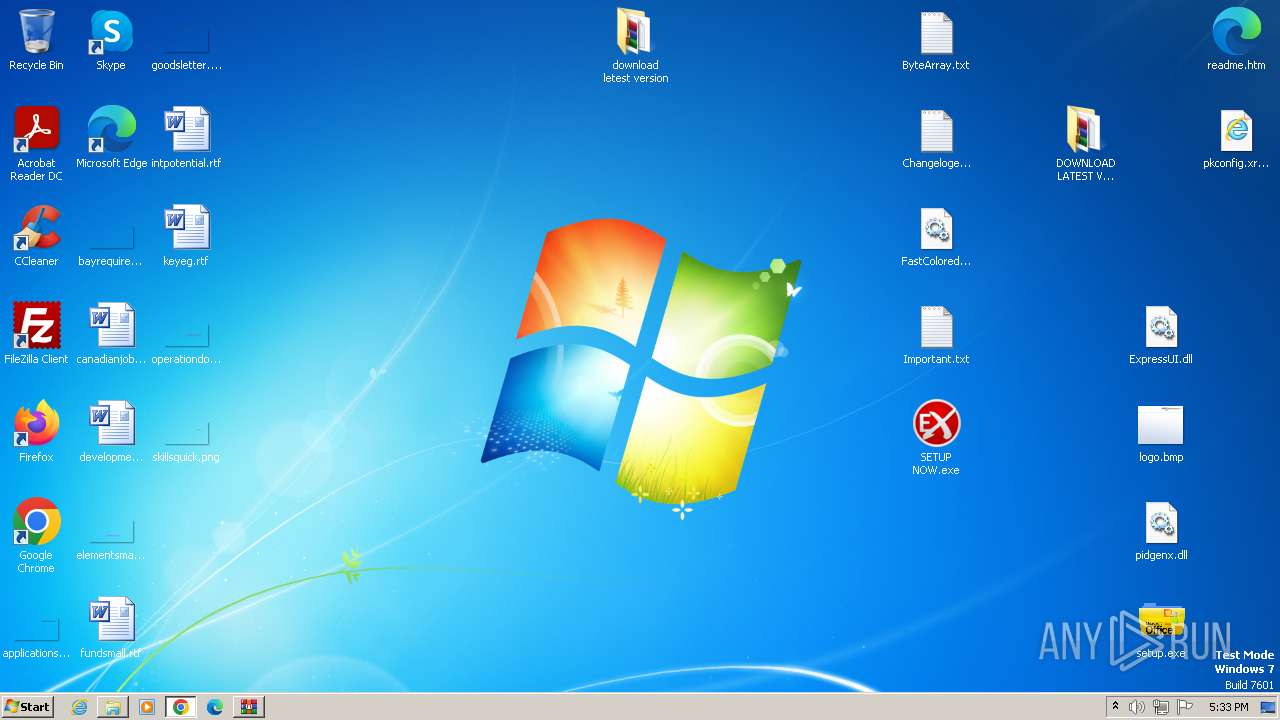
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6F29950228D4CB601784E7855CDEB60B |
| SHA1: | 428CACD05798EF6738012E359DF3598A1B36E4C0 |
| SHA256: | ABC262D6F3D26F1E723852E0AD7F6D4F84423C7F9AA42454BB66B388DE64097D |
| SSDEEP: | 3:N8R2WZf+IANIsRuAGUr9zAbAdA:2AQf+IS7+N |
MALICIOUS
Drops the executable file immediately after the start
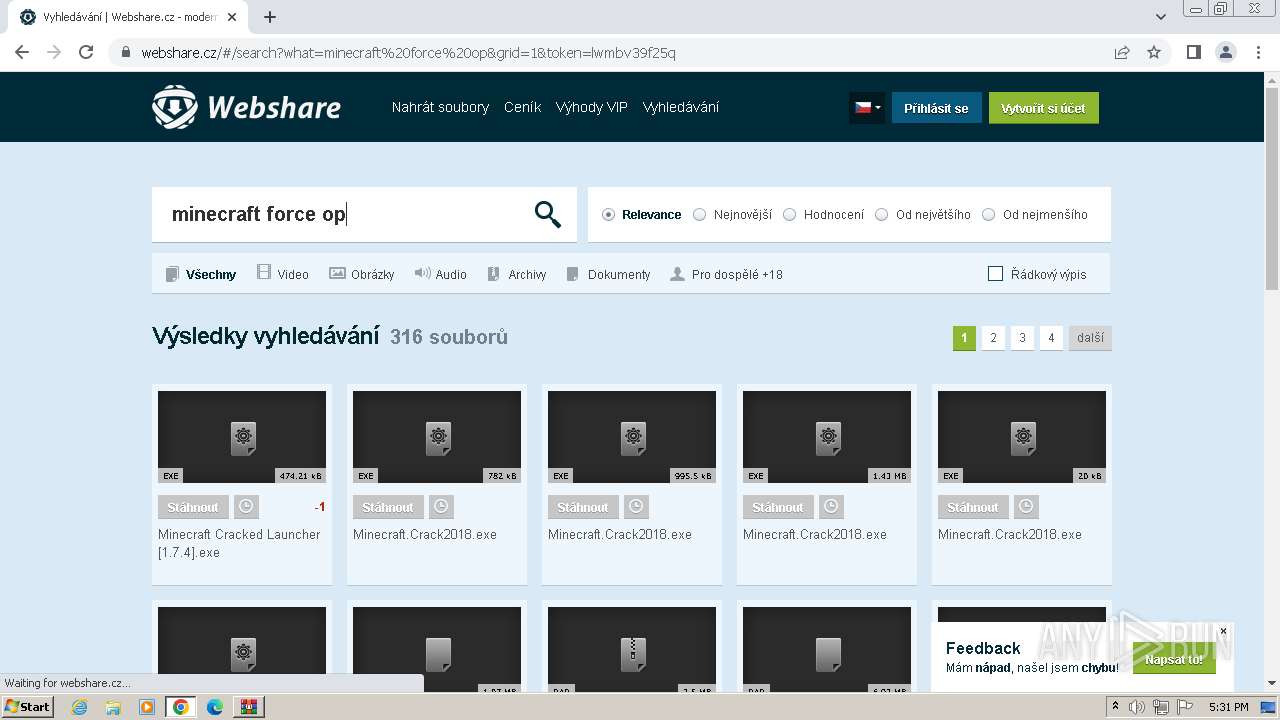
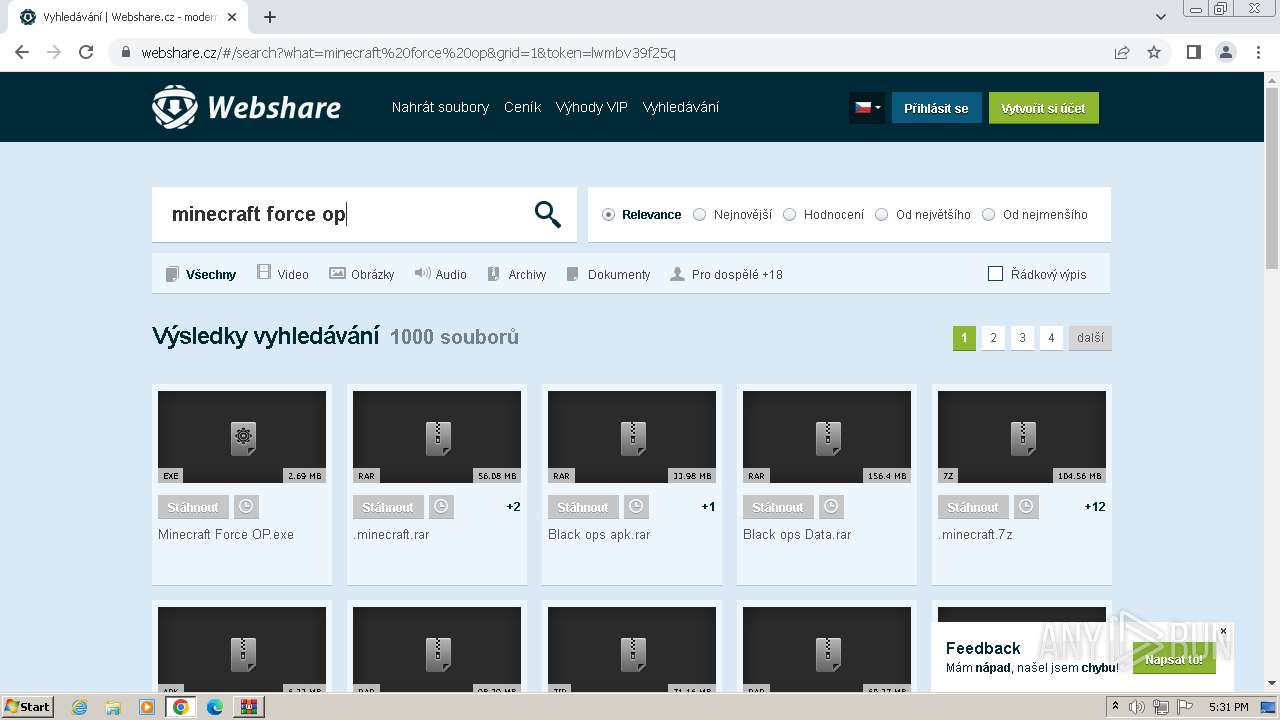
- Minecraft Force OP.exe (PID: 1028)
- lnsecsl.exe (PID: 2344)
Changes the autorun value in the registry
- Minecraft Force OP.exe (PID: 1028)
- lnsecsl.exe (PID: 2344)
Creates a writable file in the system directory
- Minecraft Force OP.exe (PID: 1028)
Change Internet Settings
- lnsecsl.exe (PID: 2344)
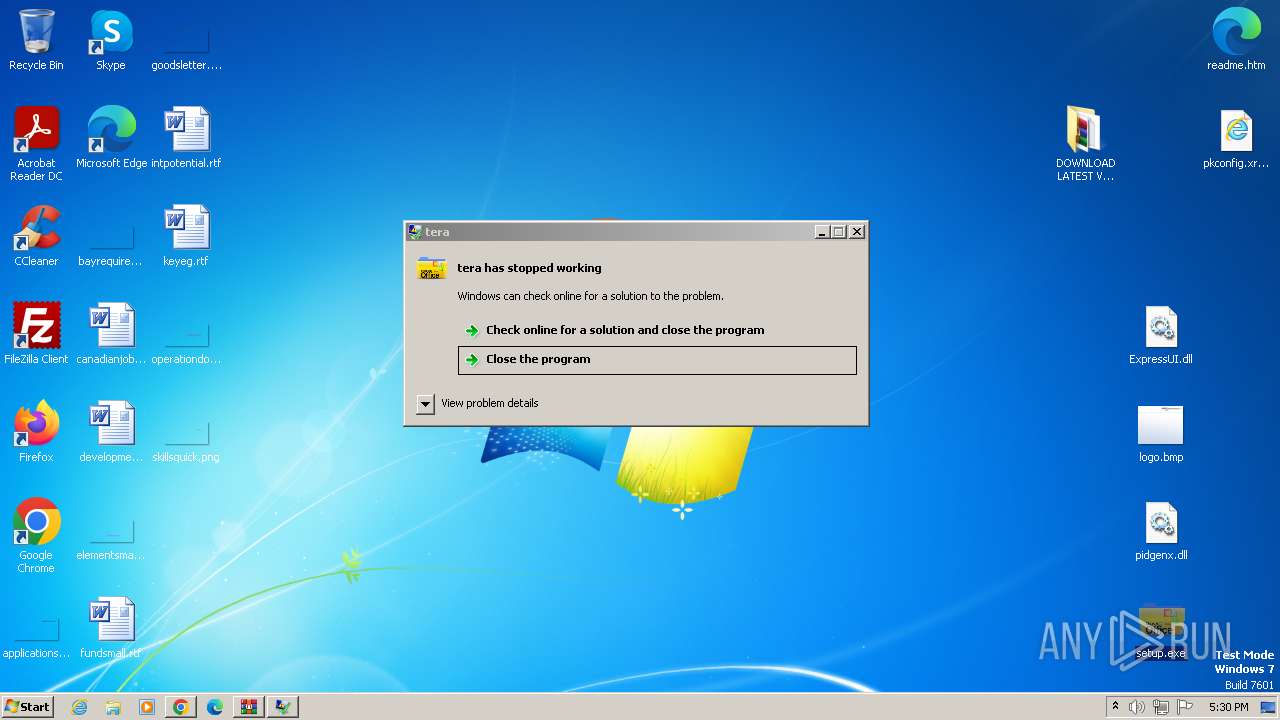
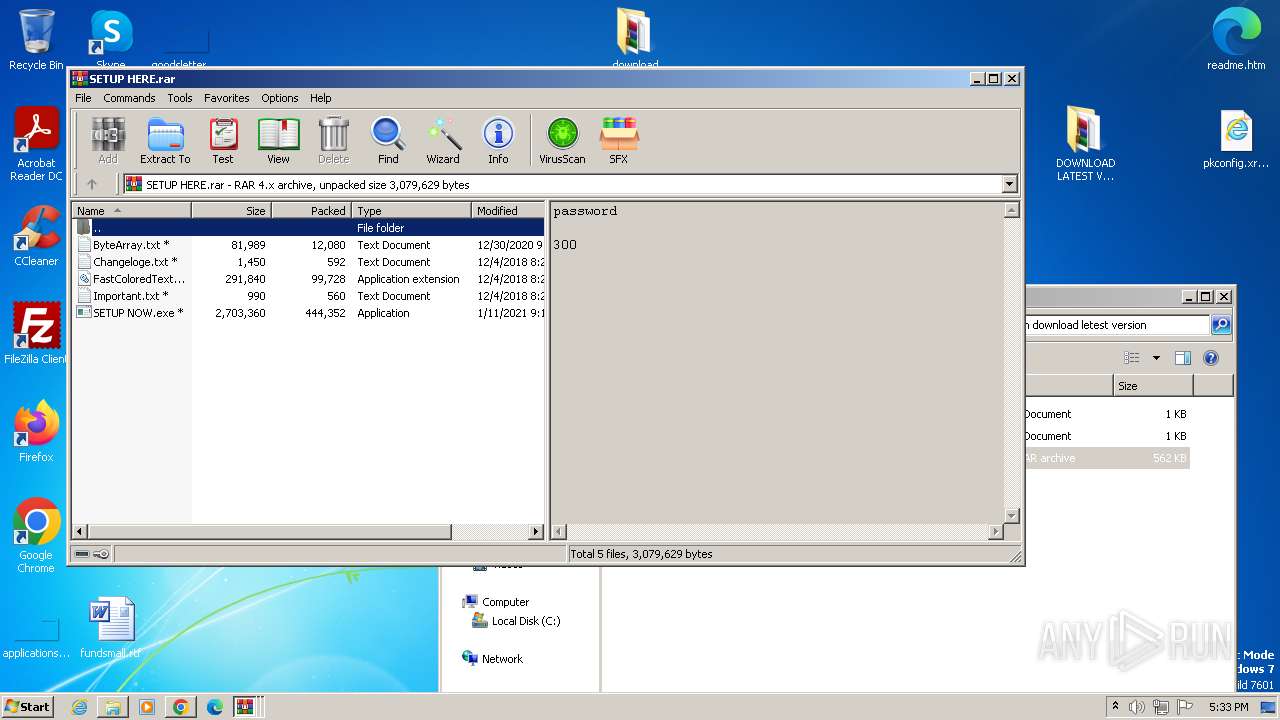
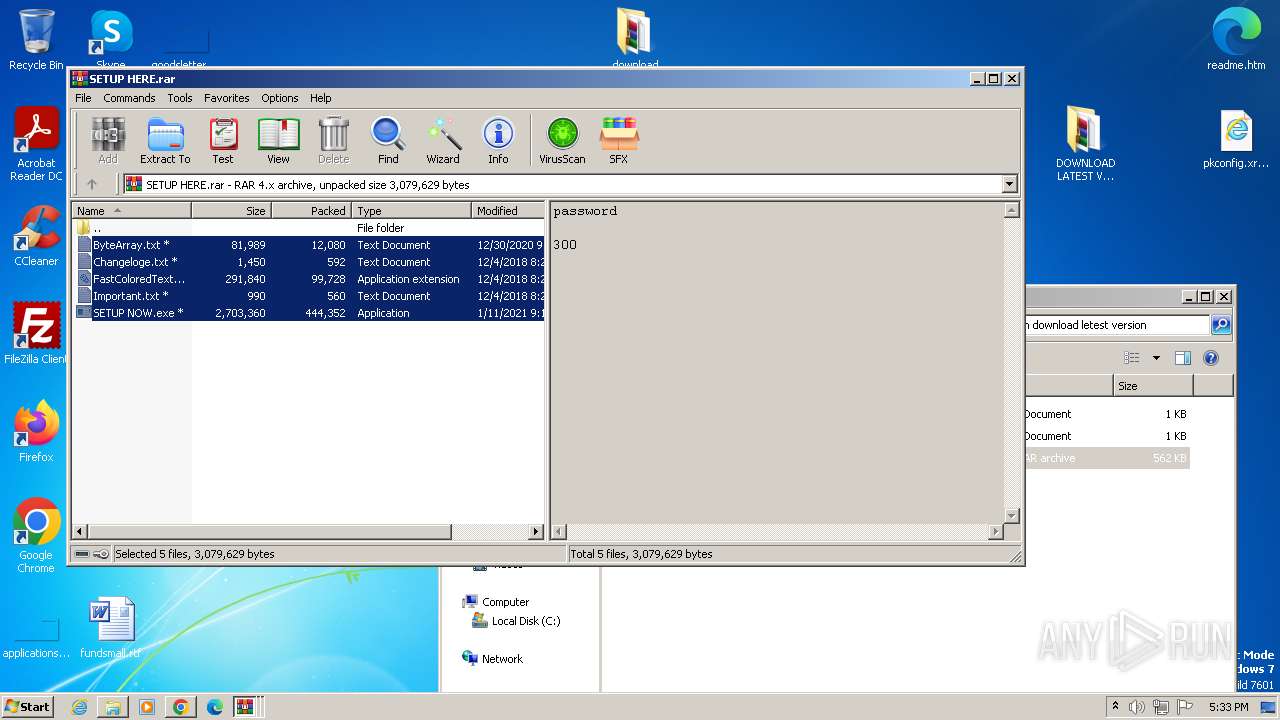
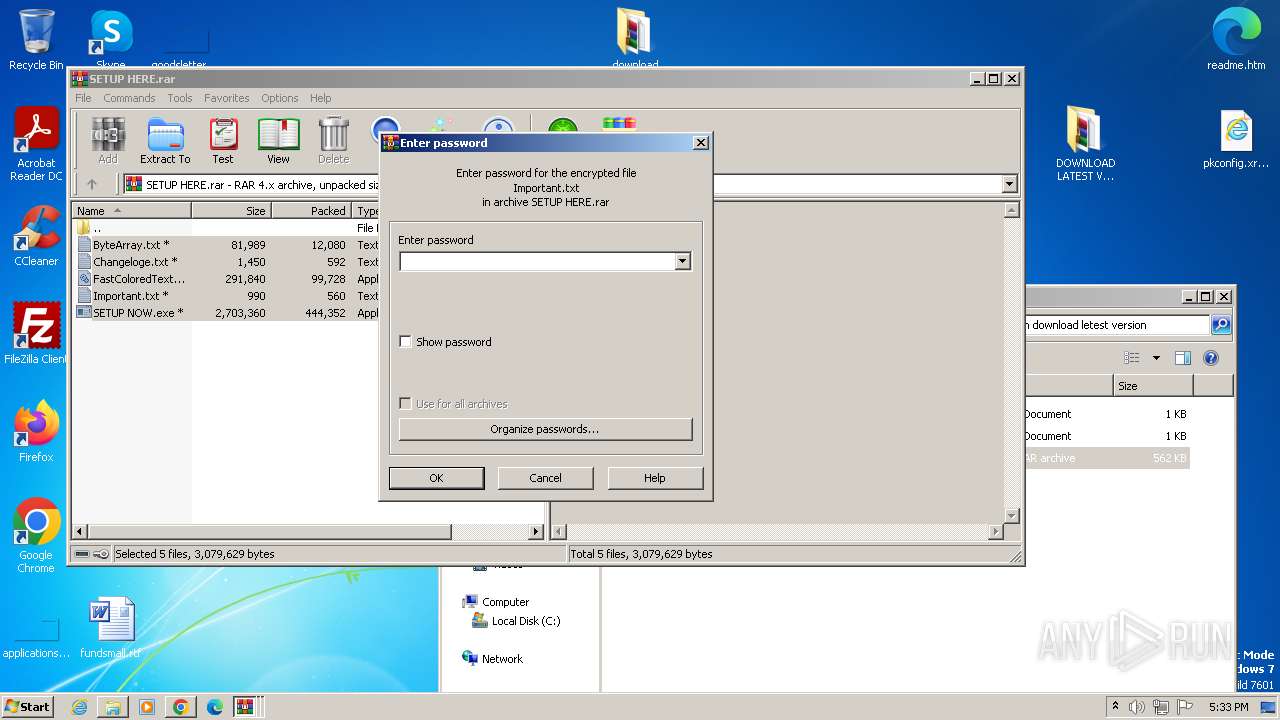
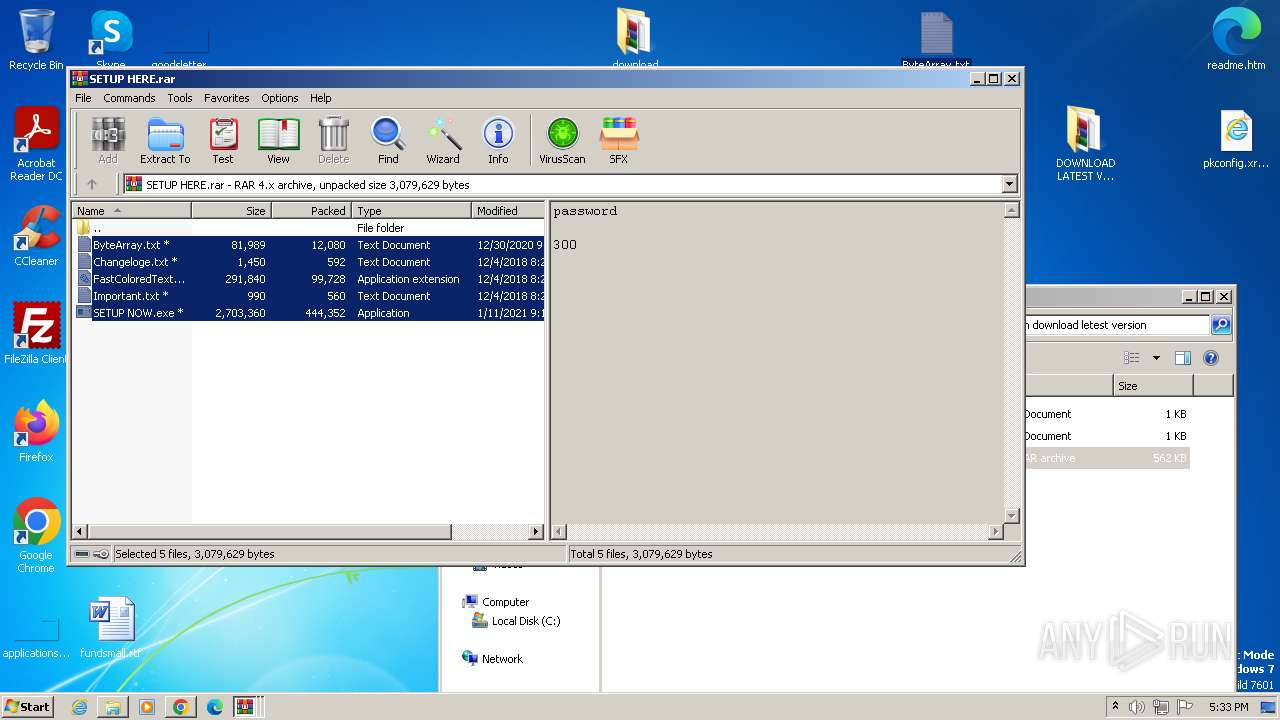
NjRAT is detected
- SETUP NOW.exe (PID: 820)
SUSPICIOUS
Reads the Internet Settings
- setup.exe (PID: 3856)
- Minecraft Force OP.exe (PID: 1028)
- setup.exe (PID: 2260)
- lnsecsl.exe (PID: 2344)
Reads settings of System Certificates
- setup.exe (PID: 3856)
- setup.exe (PID: 2260)
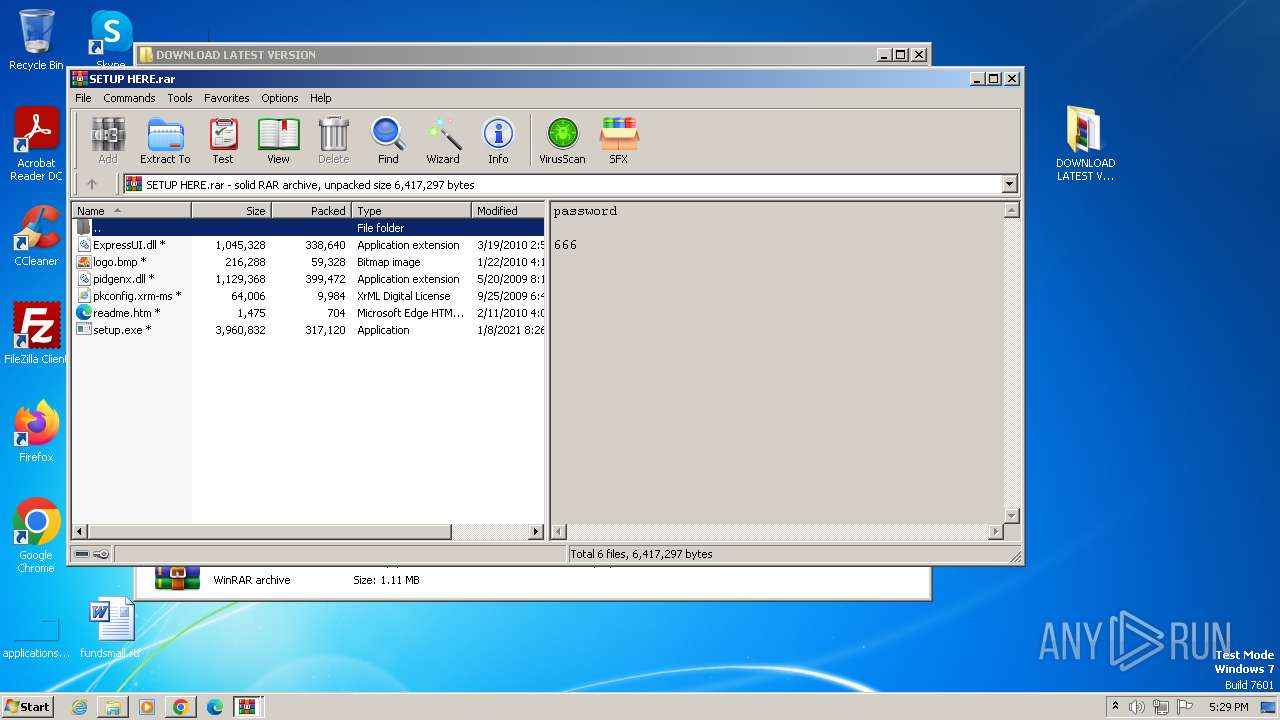
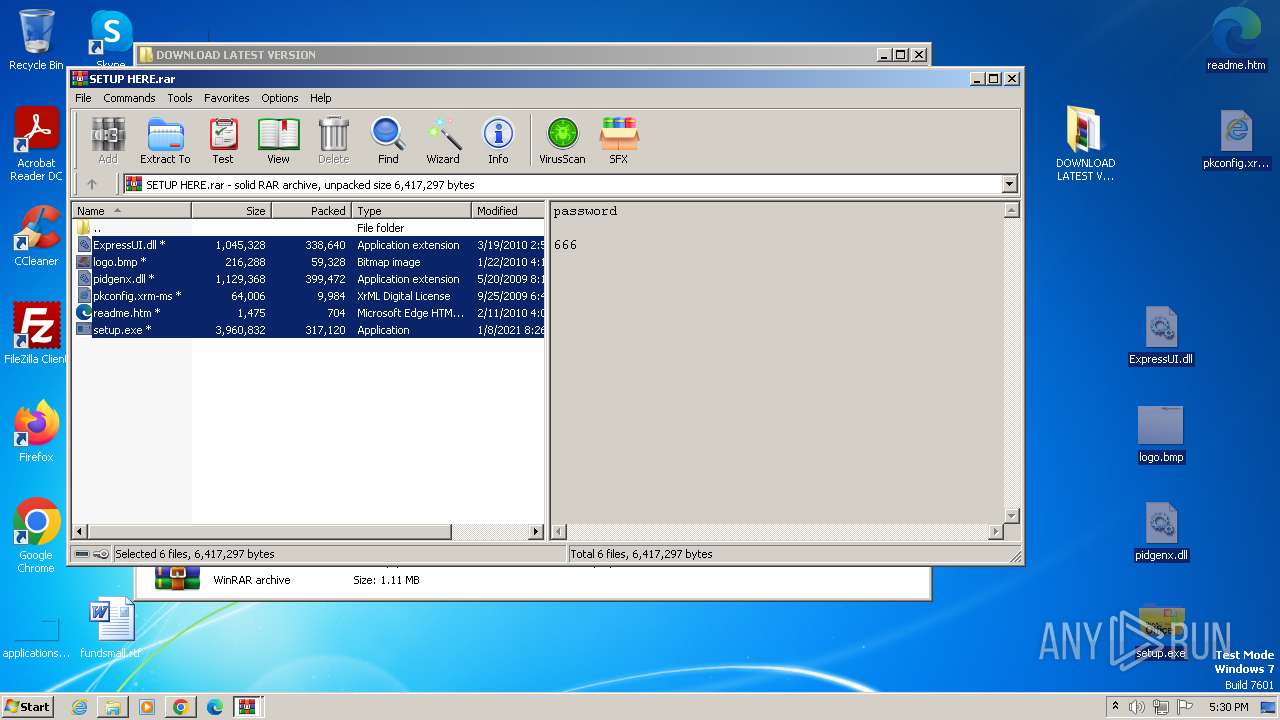
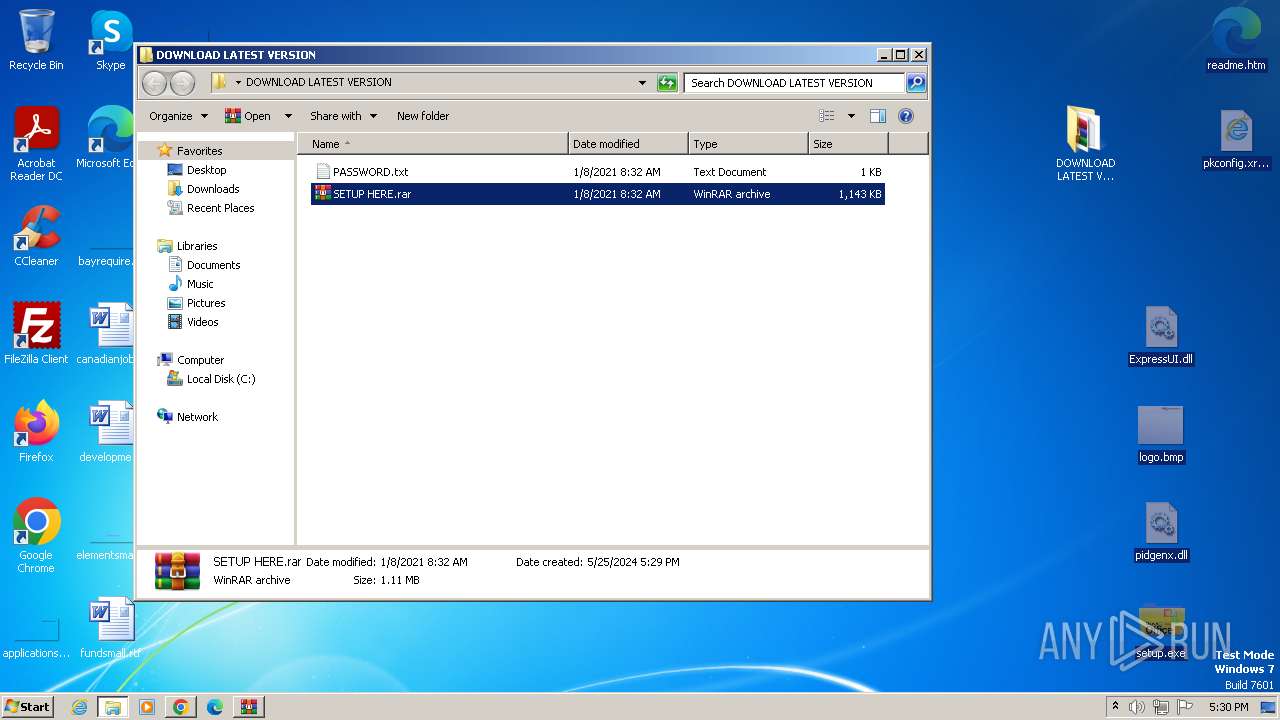
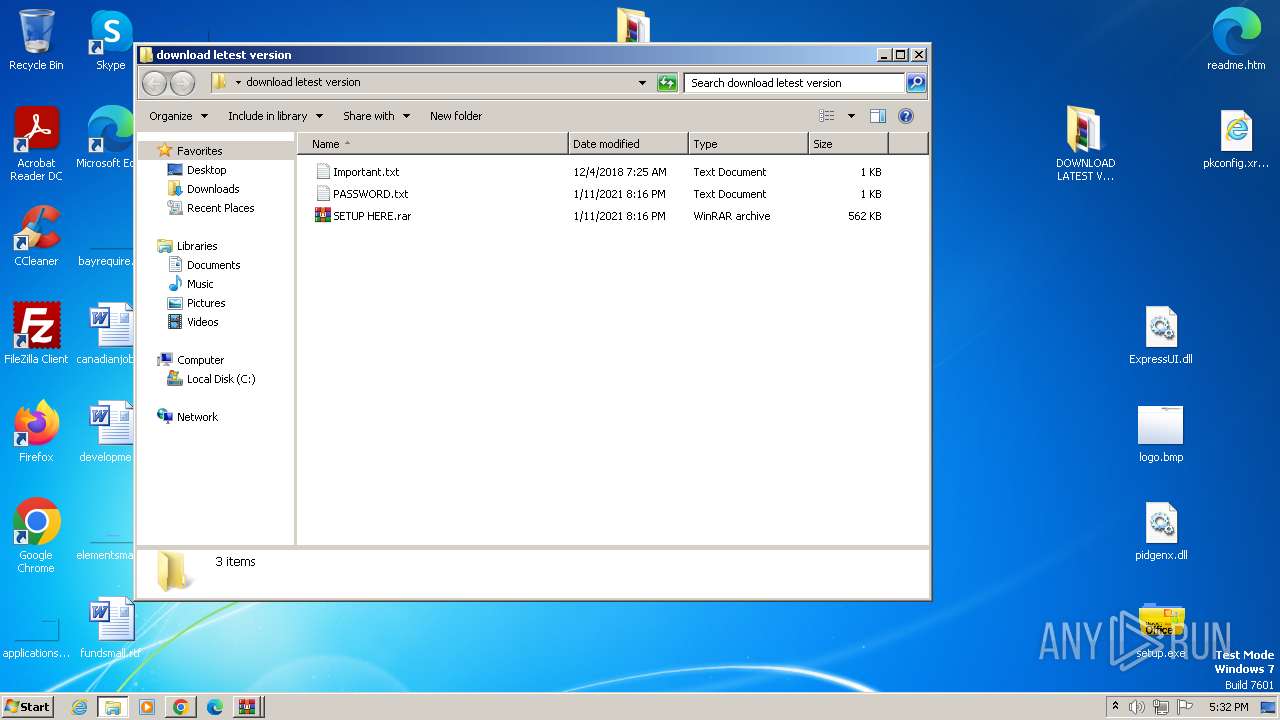
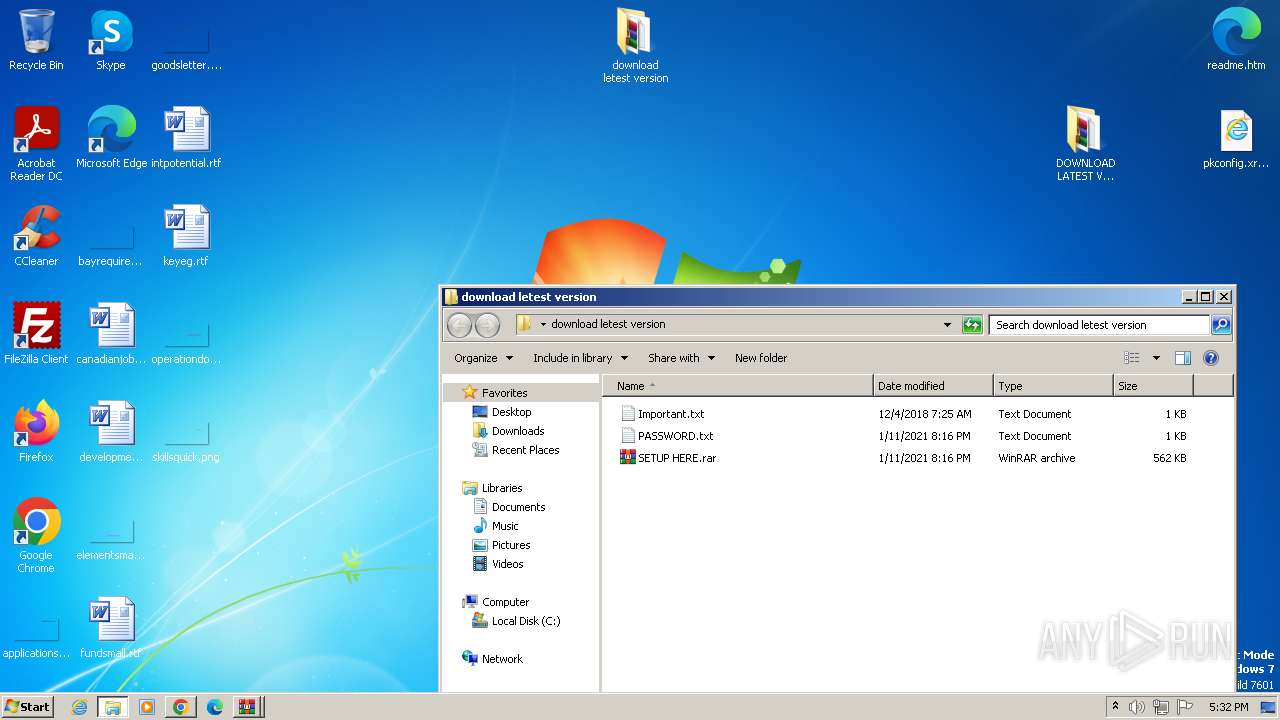
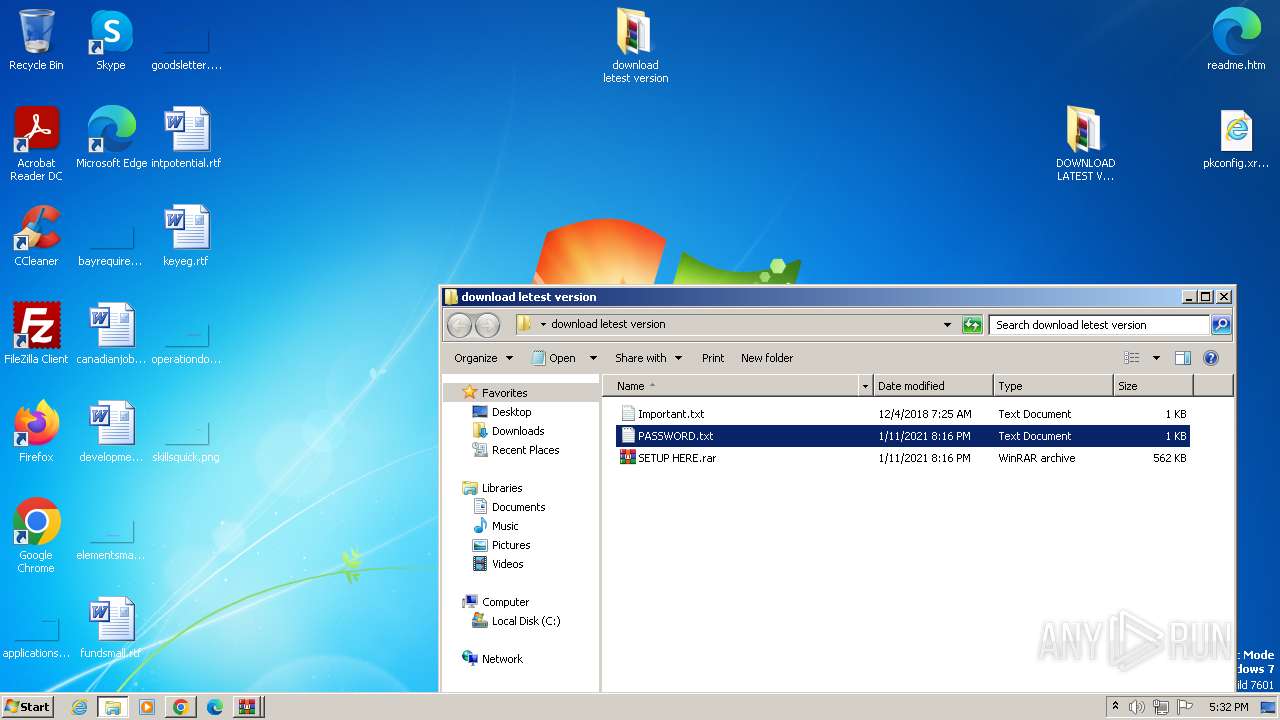
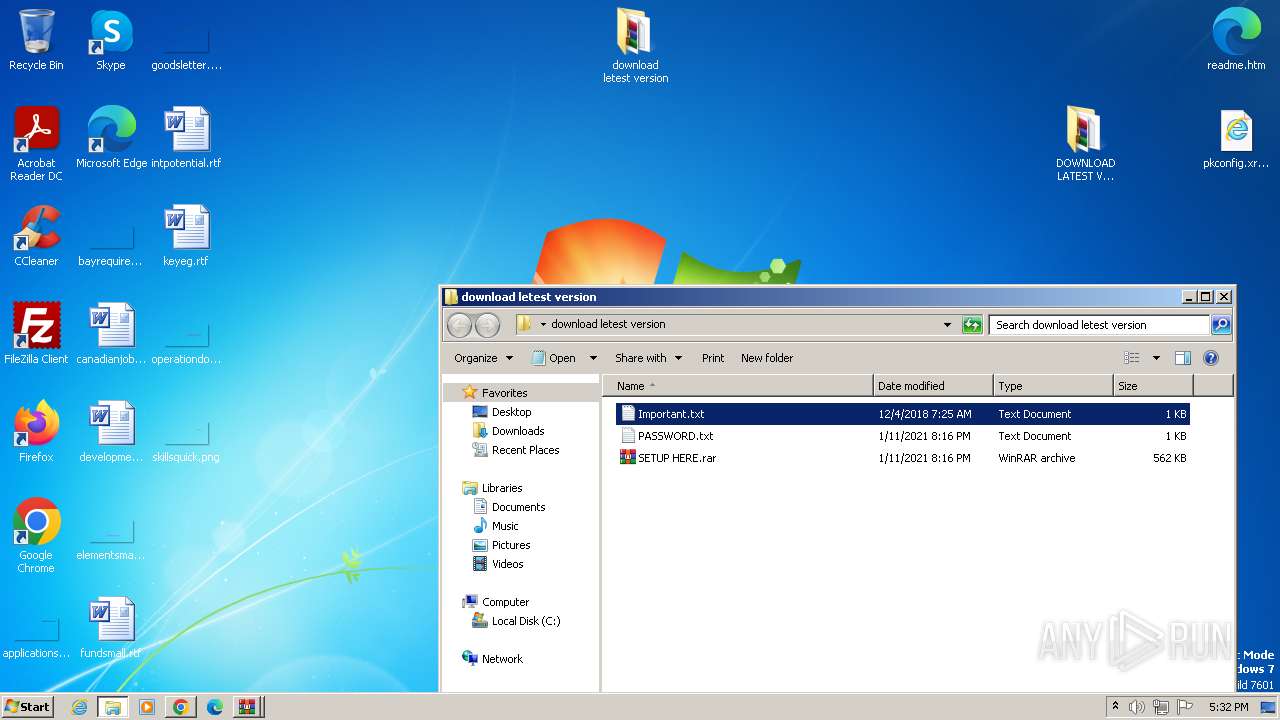
Process drops legitimate windows executable
- WinRAR.exe (PID: 3436)
Executable content was dropped or overwritten
- Minecraft Force OP.exe (PID: 1028)
- lnsecsl.exe (PID: 2344)
Reads security settings of Internet Explorer
- Minecraft Force OP.exe (PID: 1028)
- lnsecsl.exe (PID: 2344)
Starts itself from another location
- Minecraft Force OP.exe (PID: 1028)
Reads Internet Explorer settings
- lnsecsl.exe (PID: 2344)
Reads Microsoft Outlook installation path
- lnsecsl.exe (PID: 2344)
INFO
Drops the executable file immediately after the start
- chrome.exe (PID: 3988)
- WinRAR.exe (PID: 3436)
- chrome.exe (PID: 2456)
- chrome.exe (PID: 2728)
- WinRAR.exe (PID: 2320)
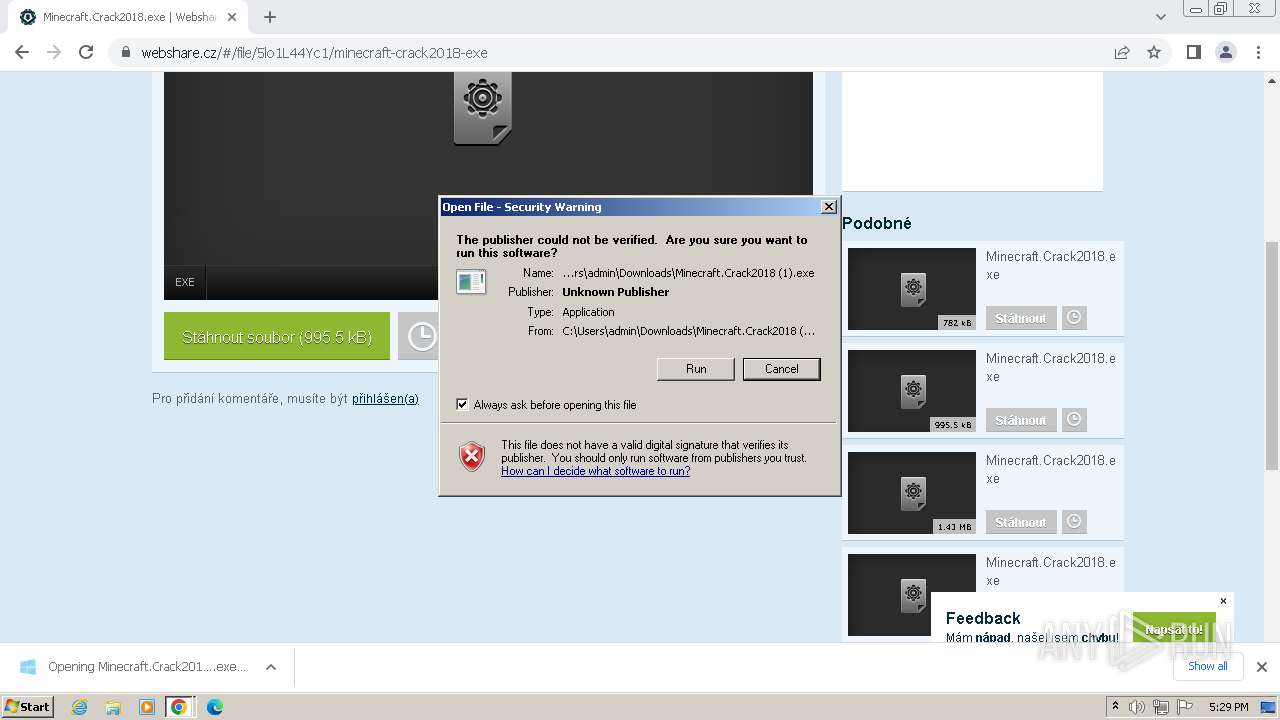
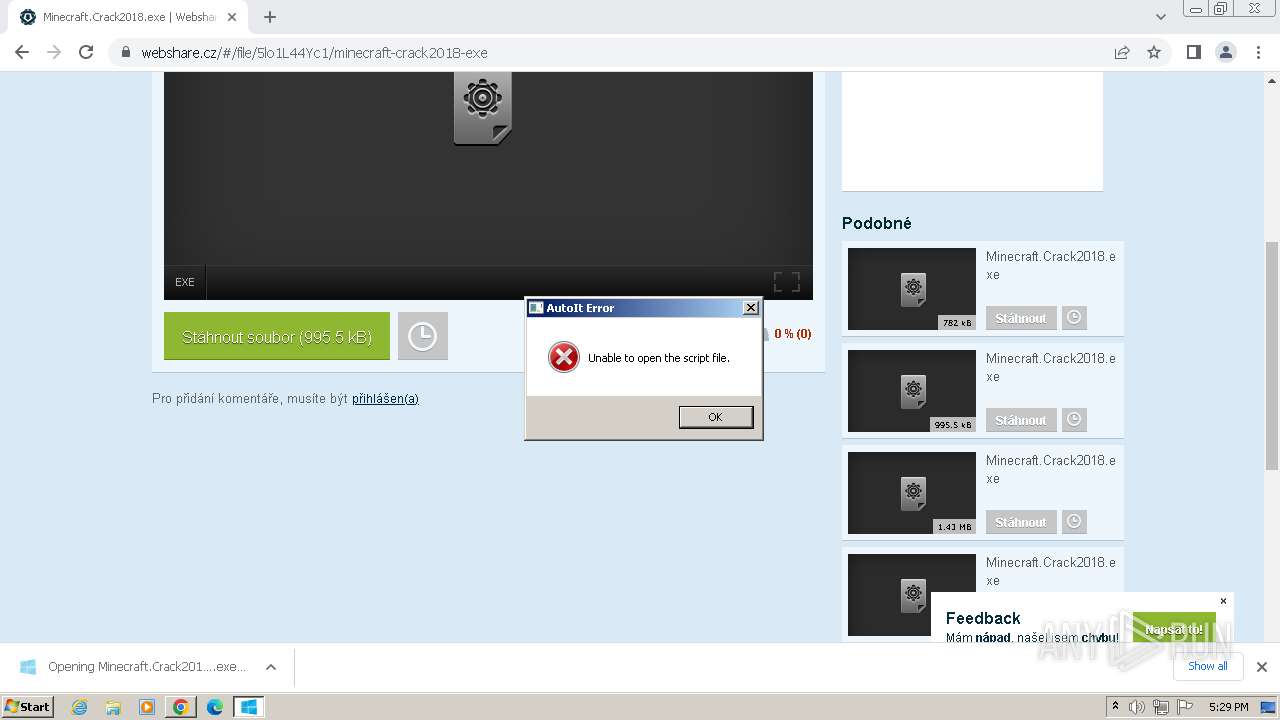
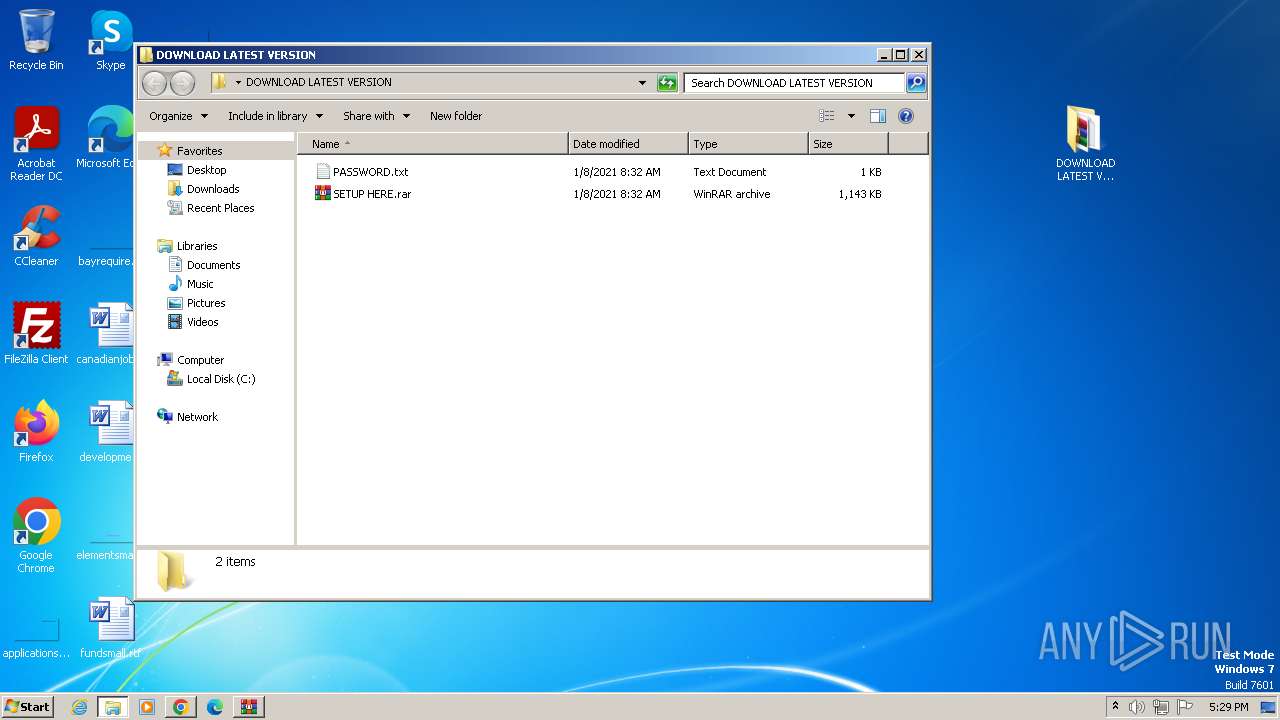
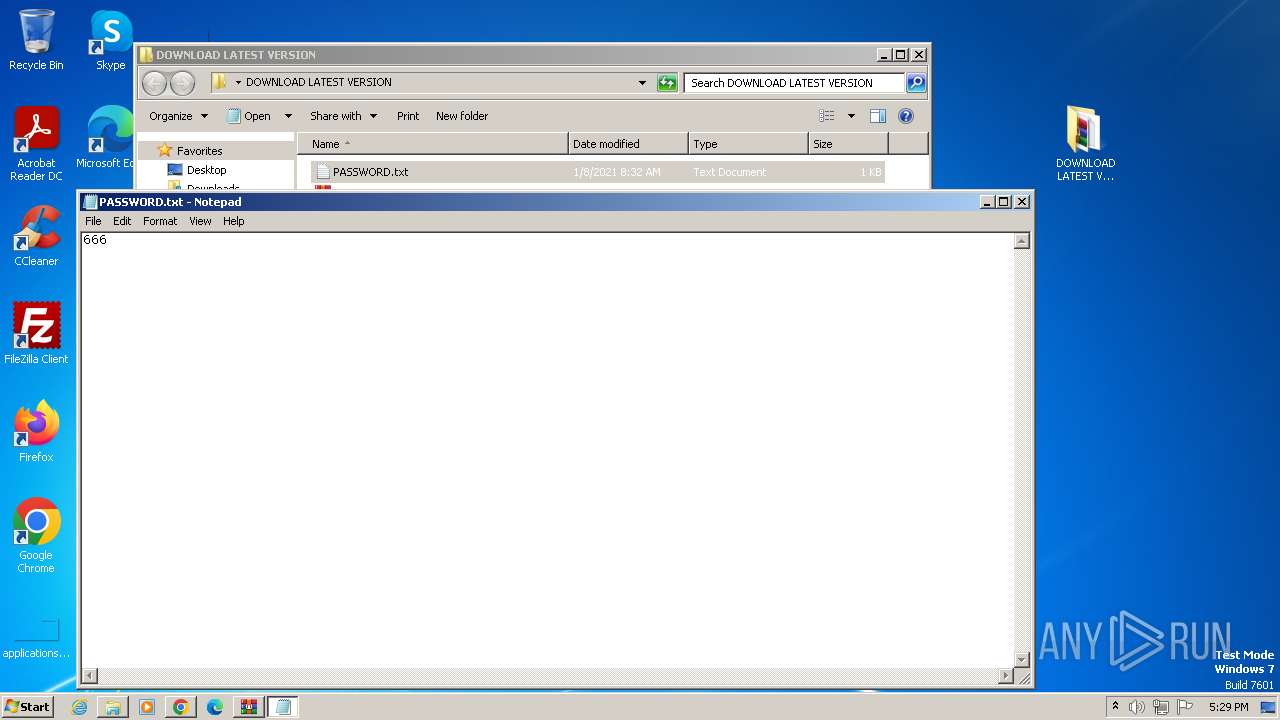
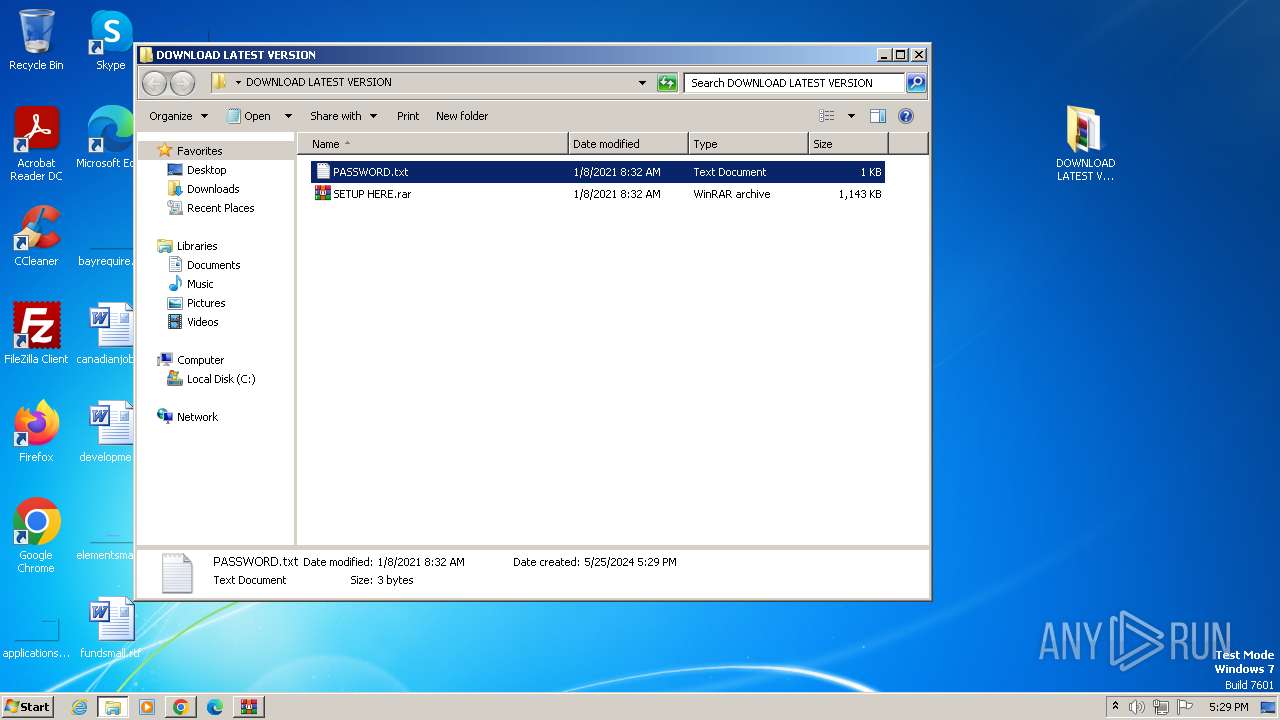
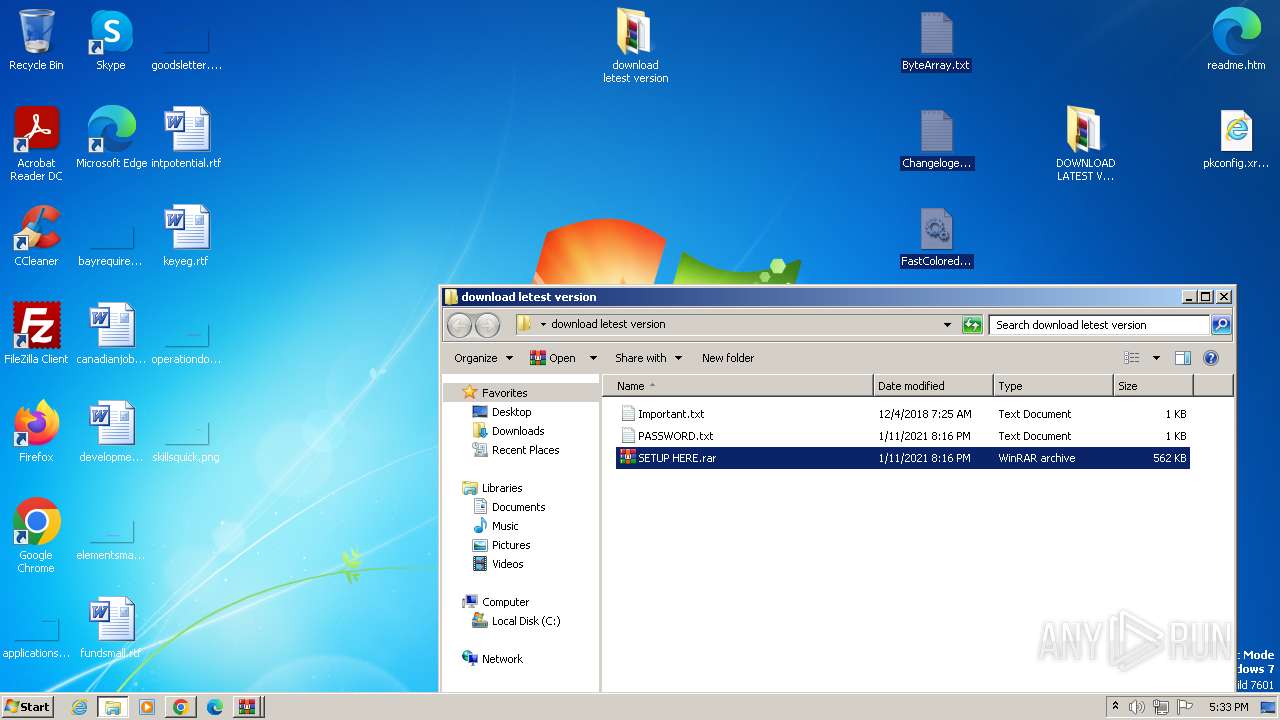
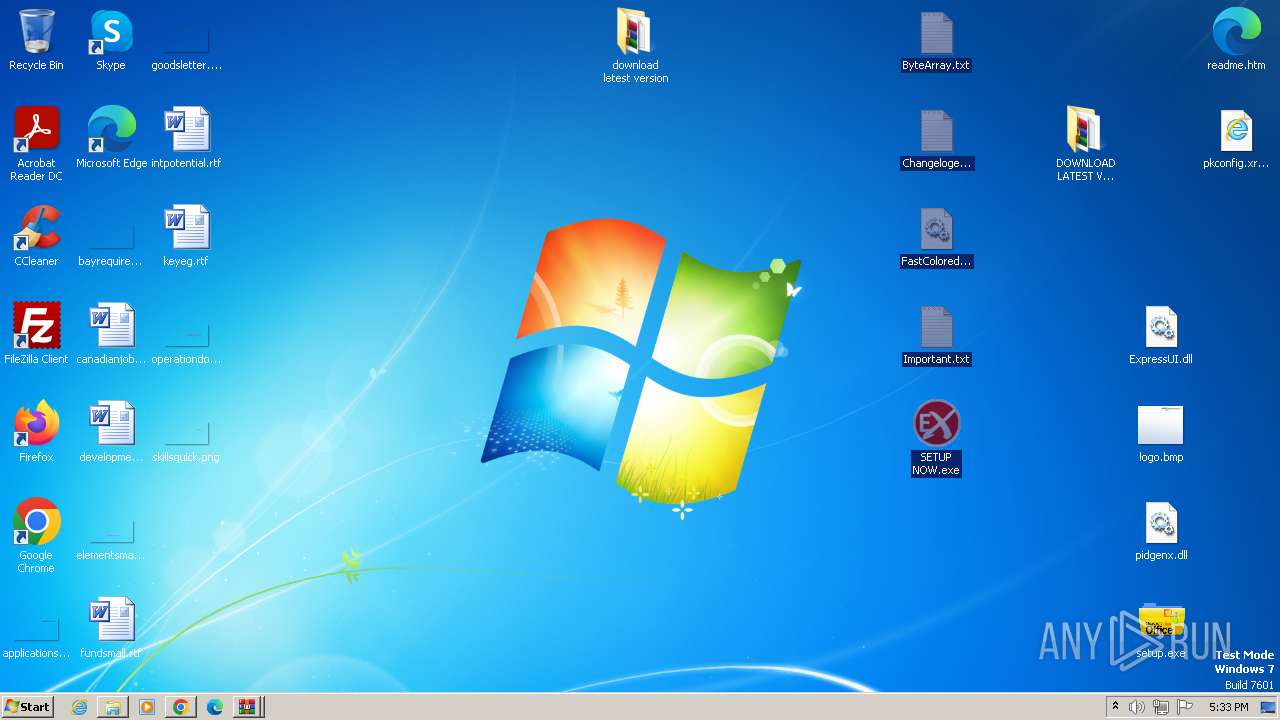
Manual execution by a user
- wmpnscfg.exe (PID: 2236)
- WinRAR.exe (PID: 3436)
- notepad.exe (PID: 3456)
- setup.exe (PID: 2260)
- setup.exe (PID: 3856)
- iexplore.exe (PID: 3200)
- notepad.exe (PID: 3736)
- SETUP NOW.exe (PID: 820)
- SETUP NOW.exe (PID: 904)
- SETUP NOW.exe (PID: 2732)
- SETUP NOW.exe (PID: 3672)
- notepad.exe (PID: 2484)
- WinRAR.exe (PID: 2320)
- SETUP NOW.exe (PID: 3408)
- SETUP NOW.exe (PID: 1280)
- SETUP NOW.exe (PID: 2552)
- SETUP NOW.exe (PID: 2636)
- SETUP NOW.exe (PID: 2748)
- SETUP NOW.exe (PID: 3048)
- SETUP NOW.exe (PID: 2784)
- SETUP NOW.exe (PID: 3040)
- SETUP NOW.exe (PID: 3020)
- SETUP NOW.exe (PID: 2672)
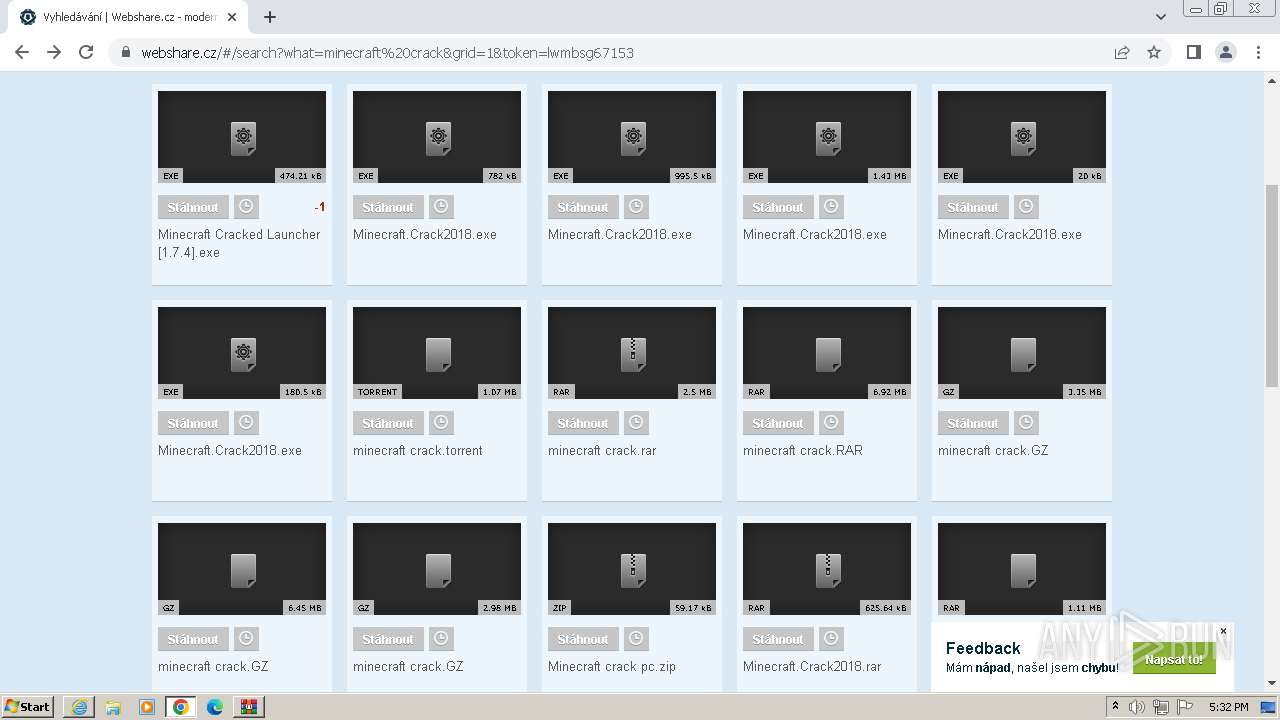
Reads the computer name
- wmpnscfg.exe (PID: 2236)
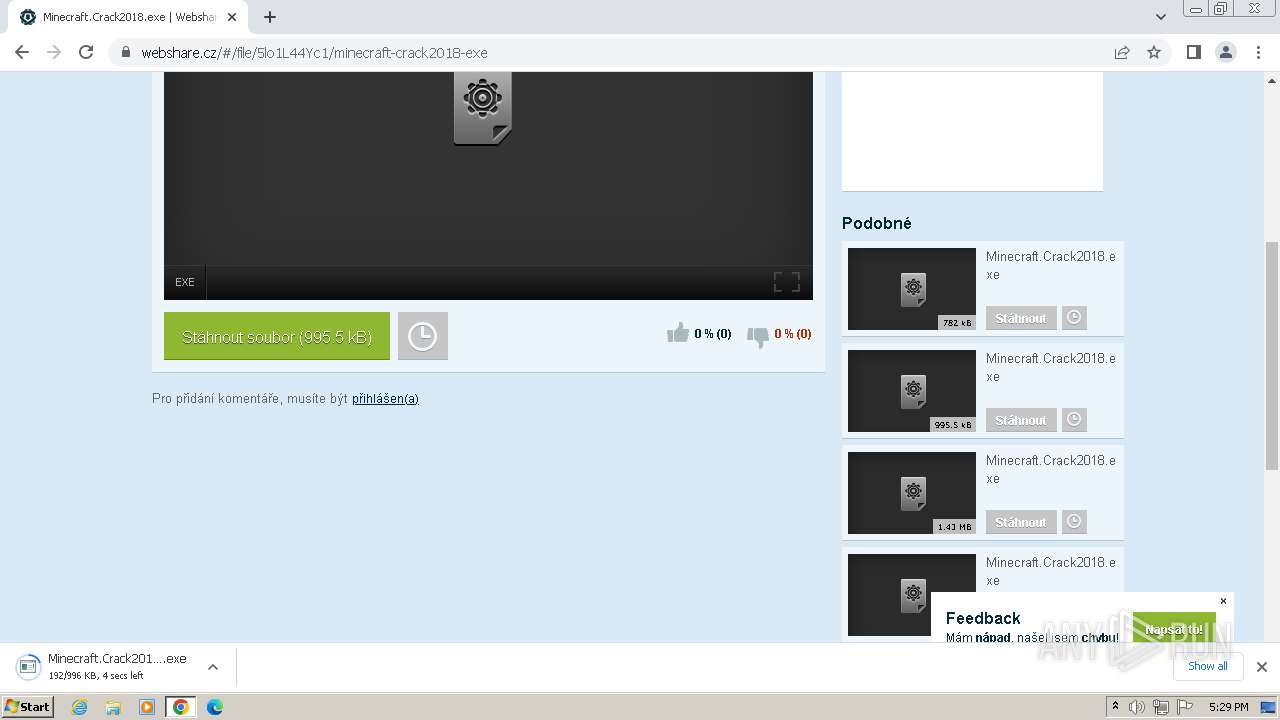
- Minecraft.Crack2018.exe (PID: 2688)
- Minecraft.Crack2018 (1).exe (PID: 2544)
- setup.exe (PID: 3856)
- setup.exe (PID: 2260)
- Minecraft Force OP.exe (PID: 1028)
- lnsecsl.exe (PID: 2344)
- SETUP NOW.exe (PID: 820)
- SETUP NOW.exe (PID: 904)
- SETUP NOW.exe (PID: 2732)
- SETUP NOW.exe (PID: 3672)
- SETUP NOW.exe (PID: 2552)
- SETUP NOW.exe (PID: 3408)
- SETUP NOW.exe (PID: 1280)
- SETUP NOW.exe (PID: 2636)
- SETUP NOW.exe (PID: 2748)
- SETUP NOW.exe (PID: 2784)
- SETUP NOW.exe (PID: 3048)
- SETUP NOW.exe (PID: 3040)
- SETUP NOW.exe (PID: 3020)
- SETUP NOW.exe (PID: 2672)
Checks supported languages
- wmpnscfg.exe (PID: 2236)
- Minecraft.Crack2018.exe (PID: 2688)
- Minecraft.Crack2018 (1).exe (PID: 2544)
- setup.exe (PID: 3856)
- setup.exe (PID: 2260)
- Minecraft Force OP.exe (PID: 1028)
- lnsecsl.exe (PID: 2344)
- SETUP NOW.exe (PID: 820)
- SETUP NOW.exe (PID: 904)
- SETUP NOW.exe (PID: 3672)
- SETUP NOW.exe (PID: 2732)
- SETUP NOW.exe (PID: 3408)
- SETUP NOW.exe (PID: 1280)
- SETUP NOW.exe (PID: 2552)
- SETUP NOW.exe (PID: 2636)
- SETUP NOW.exe (PID: 2748)
- SETUP NOW.exe (PID: 3048)
- SETUP NOW.exe (PID: 2784)
- SETUP NOW.exe (PID: 3040)
- SETUP NOW.exe (PID: 3020)
- SETUP NOW.exe (PID: 2672)
The process uses the downloaded file
- chrome.exe (PID: 2472)
- chrome.exe (PID: 1240)
- chrome.exe (PID: 2088)
- WinRAR.exe (PID: 2744)
- chrome.exe (PID: 3988)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 1944)
- WinRAR.exe (PID: 1600)
Reads mouse settings
- Minecraft.Crack2018.exe (PID: 2688)
- Minecraft.Crack2018 (1).exe (PID: 2544)
Executable content was dropped or overwritten
- chrome.exe (PID: 3988)
- WinRAR.exe (PID: 3436)
- chrome.exe (PID: 2456)
- chrome.exe (PID: 2728)
- WinRAR.exe (PID: 2320)
Application launched itself
- chrome.exe (PID: 3988)
- iexplore.exe (PID: 3200)
Disables trace logs
- setup.exe (PID: 3856)
- setup.exe (PID: 2260)
Reads the machine GUID from the registry
- setup.exe (PID: 3856)
- setup.exe (PID: 2260)
- lnsecsl.exe (PID: 2344)
- SETUP NOW.exe (PID: 820)
Reads the software policy settings
- setup.exe (PID: 3856)
- setup.exe (PID: 2260)
Reads Environment values
- setup.exe (PID: 3856)
- setup.exe (PID: 2260)
Create files in a temporary directory
- Minecraft Force OP.exe (PID: 1028)
- lnsecsl.exe (PID: 2344)
Checks proxy server information
- lnsecsl.exe (PID: 2344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
124
Monitored processes
73
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2016 --field-trial-handle=1132,i,4441269926220639598,7879798799191144391,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2036 --field-trial-handle=1132,i,4441269926220639598,7879798799191144391,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3268 --field-trial-handle=1132,i,4441269926220639598,7879798799191144391,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3628 --field-trial-handle=1132,i,4441269926220639598,7879798799191144391,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=1036 --field-trial-handle=1132,i,4441269926220639598,7879798799191144391,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 820 | "C:\Users\admin\Desktop\SETUP NOW.exe" | C:\Users\admin\Desktop\SETUP NOW.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ASTORE Version: 1.0.0.0 Modules
| |||||||||||||||
| 904 | "C:\Users\admin\Downloads\Minecraft Force OP.exe" | C:\Users\admin\Downloads\Minecraft Force OP.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 904 | "C:\Users\admin\Desktop\SETUP NOW.exe" | C:\Users\admin\Desktop\SETUP NOW.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ASTORE Version: 1.0.0.0 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3804 --field-trial-handle=1132,i,4441269926220639598,7879798799191144391,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1028 | "C:\Users\admin\Downloads\Minecraft Force OP.exe" | C:\Users\admin\Downloads\Minecraft Force OP.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
50 223
Read events
49 679
Write events
464
Delete events
80
Modification events
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3988) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
66
Suspicious files
175
Text files
60
Unknown types
224
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1043c1.TMP | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1043e1.TMP | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF104400.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF104e9f.TMP | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:23E954DCE0FB0ECF46A96FF4ACBE66F4 | SHA256:68F3B7AA8367C46273C296103B799A112DE3B70DE873C16F7166496CA31C3DDD | |||
| 3988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF106023.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
144
DNS requests
60
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
884 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1136 | chrome.exe | 142.250.145.84:443 | accounts.google.com | GOOGLE | US | unknown |
3988 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1136 | chrome.exe | 185.201.232.19:443 | webshare.cz | Tlap s.r.o. | CZ | unknown |
1136 | chrome.exe | 216.58.212.162:443 | www.googleadservices.com | GOOGLE | US | whitelisted |
1136 | chrome.exe | 77.75.77.163:443 | c.imedia.cz | Seznam.cz, a.s. | CZ | unknown |
1136 | chrome.exe | 77.75.77.172:443 | c.seznam.cz | Seznam.cz, a.s. | CZ | unknown |
1136 | chrome.exe | 216.58.206.66:443 | googleads.g.doubleclick.net | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
webshare.cz |
| whitelisted |
www.googleadservices.com |
| whitelisted |
c.imedia.cz |
| whitelisted |
c.seznam.cz |
| unknown |
googleads.g.doubleclick.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
www.google-analytics.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Potentially Bad Traffic | ET POLICY Observed DNS Query to DynDNS Domain (publicvm .com) |
Process | Message |
|---|---|
Minecraft Force OP.exe | Start app
|
Minecraft Force OP.exe | End app
|
lnsecsl.exe | Start app
|