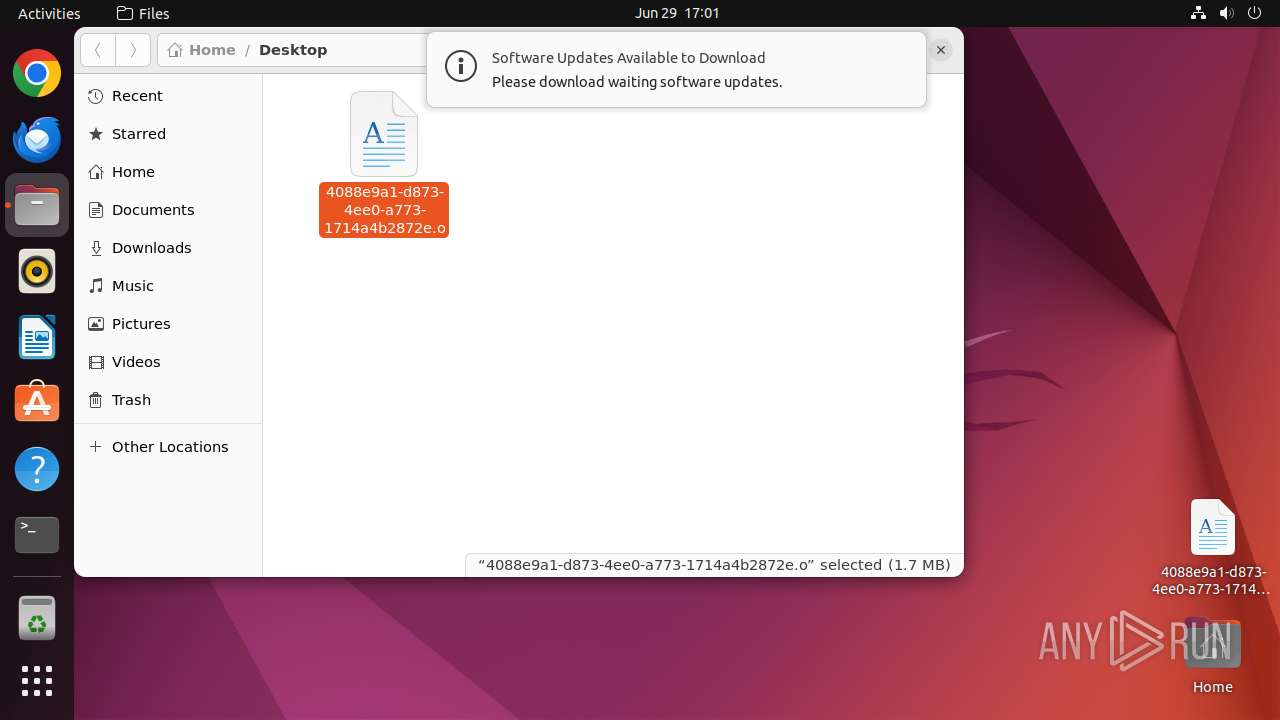
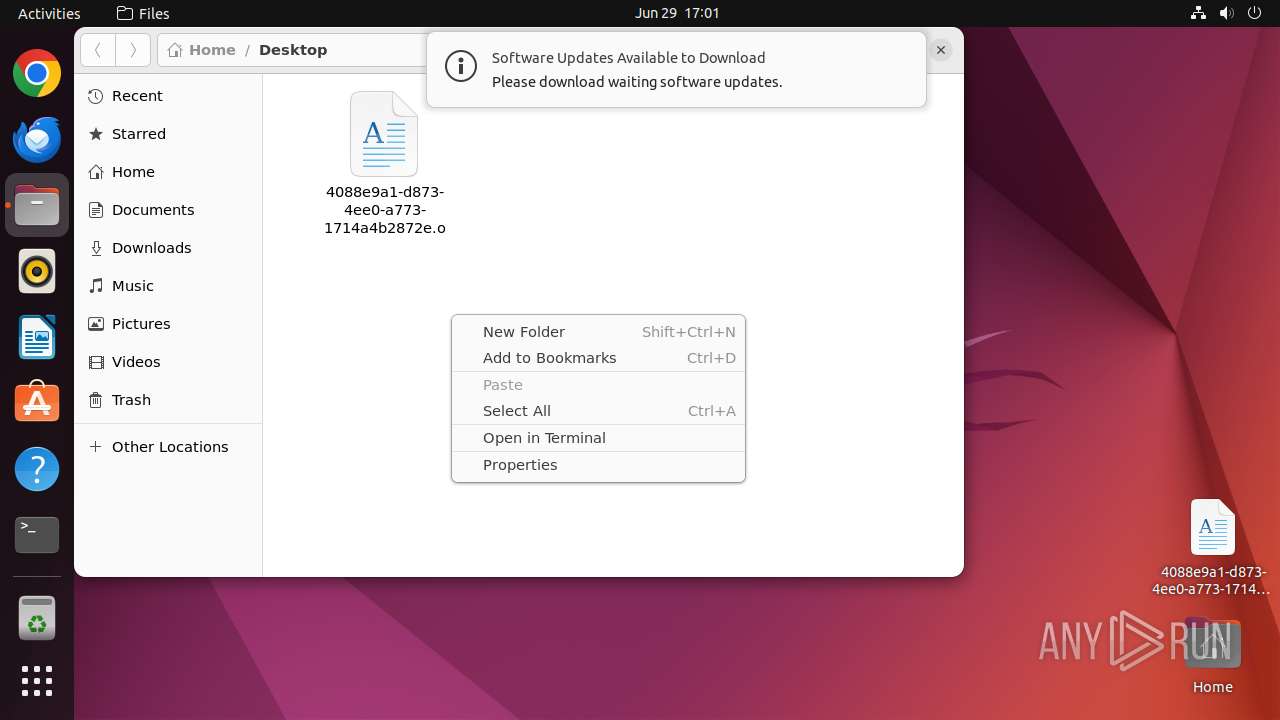
| File name: | .redtail |
| Full analysis: | https://app.any.run/tasks/4088e9a1-d873-4ee0-a773-1714a4b2872e |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | June 29, 2024, 16:01:26 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MIME: | application/x-sharedlib |
| File info: | ELF 64-bit LSB shared object, x86-64, version 1 (SYSV), statically linked, no section header |
| MD5: | 07DB7C34621453DB287722245085C5B4 |
| SHA1: | 9D4F2640B89C148E70953D49EB6D7D1867C182D2 |
| SHA256: | AB897157FDEF11B267E986EF286FD44A699E3699A458D90994E020619653D2CD |
| SSDEEP: | 49152:8rp/g+ezhxfndt+1H5PdNpwT9Z5BJqiSk/DHtPaqBBCMNGOfDX879DVxCT5SRMVh:OpY+khxf7cZFNW9BJqPk/7tyqBlNGOfJ |
MALICIOUS
Connects to the CnC server
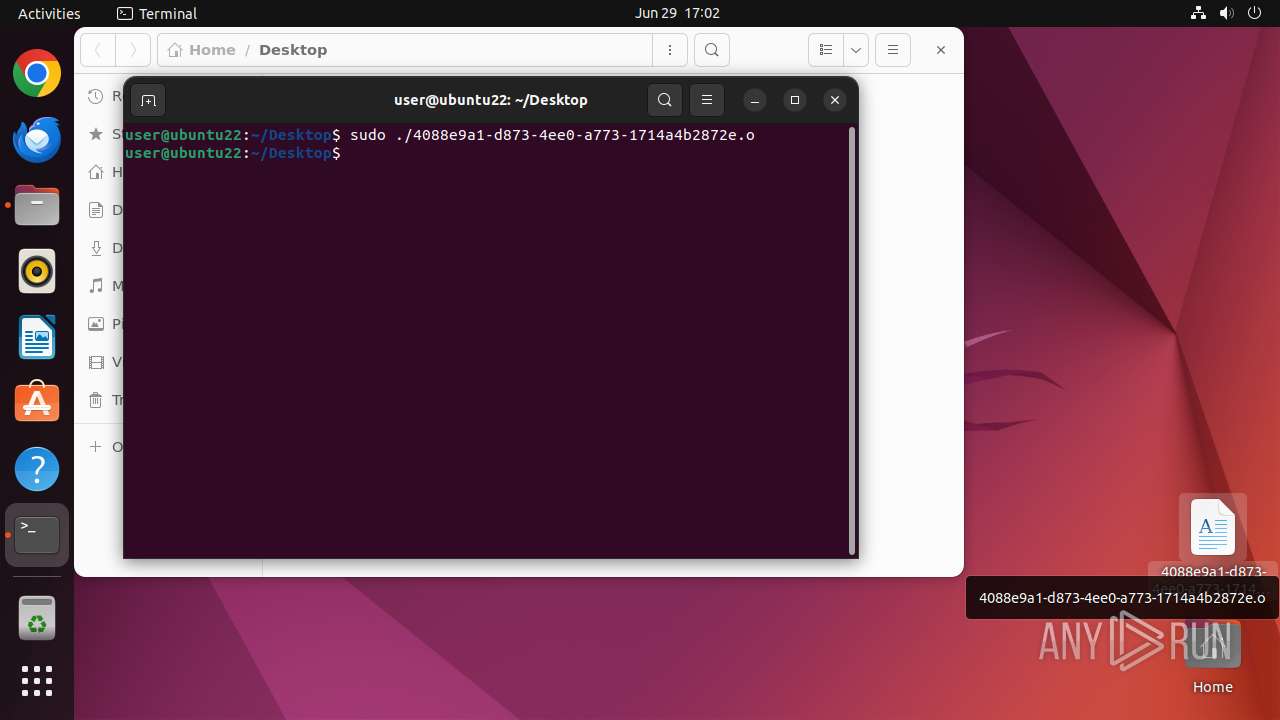
- 4088e9a1-d873-4ee0-a773-1714a4b2872e.o (PID: 13001)
MINER has been detected (SURICATA)
- 4088e9a1-d873-4ee0-a773-1714a4b2872e.o (PID: 13001)
SUSPICIOUS
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 12961)
- 4088e9a1-d873-4ee0-a773-1714a4b2872e.o (PID: 13000)
- udevadm (PID: 13010)
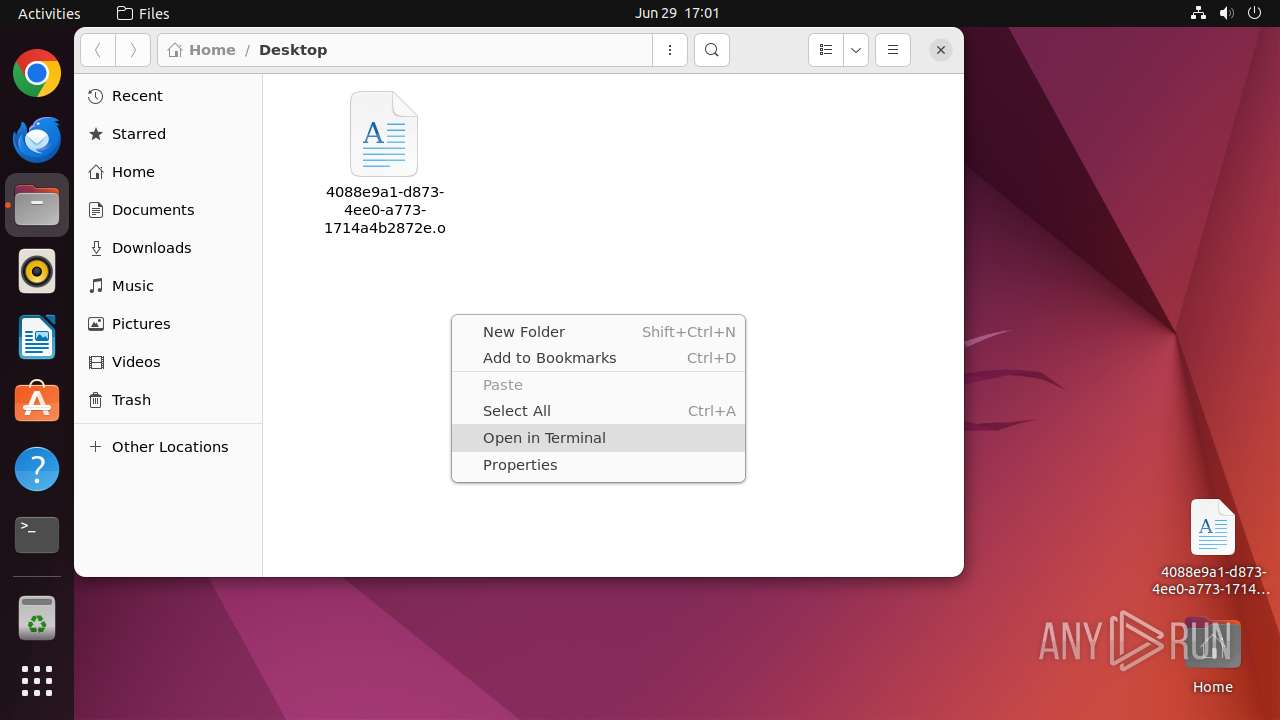
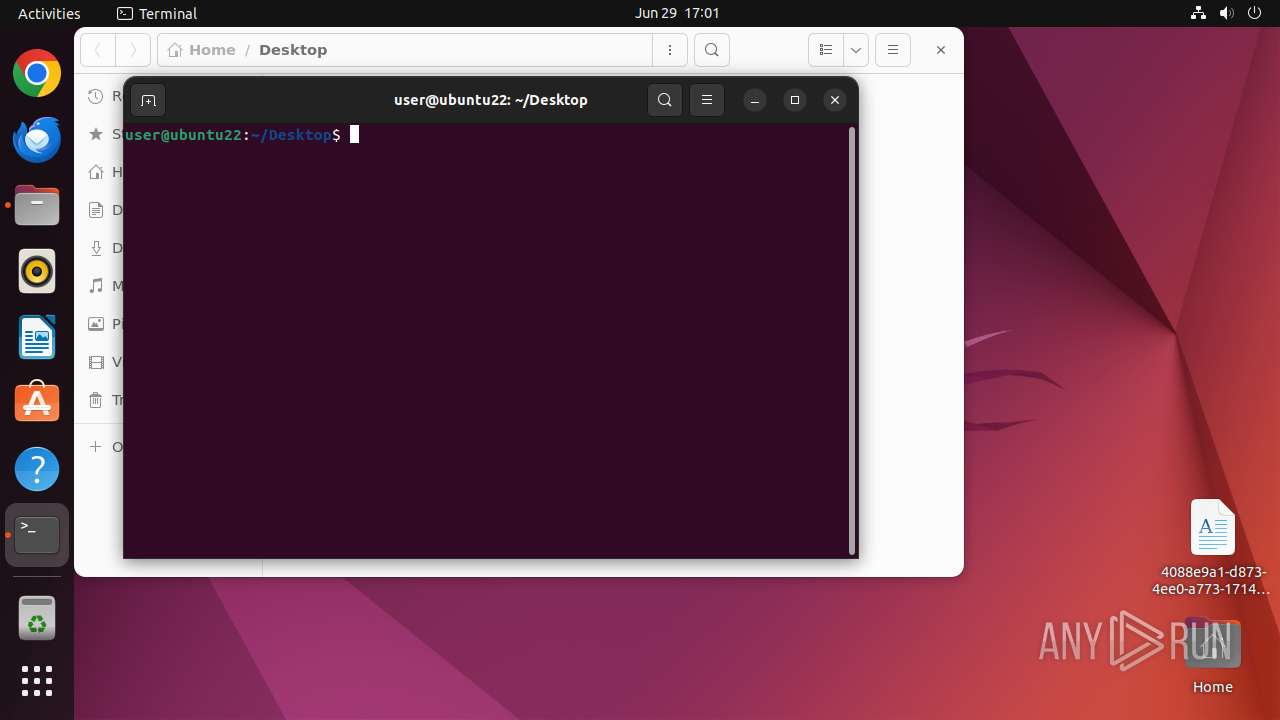
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 12973)
- 4088e9a1-d873-4ee0-a773-1714a4b2872e.o (PID: 13001)
Reads /proc/mounts (likely used to find writable filesystems)
- 4088e9a1-d873-4ee0-a773-1714a4b2872e.o (PID: 13000)
Modifies Cron jobs
- sh (PID: 13003)
Manipulating modules (likely to execute programs on system boot)
- modprobe (PID: 13009)
- modprobe (PID: 13011)
- modprobe (PID: 13012)
Potential Corporate Privacy Violation
- 4088e9a1-d873-4ee0-a773-1714a4b2872e.o (PID: 13001)
Connects to unusual port
- 4088e9a1-d873-4ee0-a773-1714a4b2872e.o (PID: 13001)
Crypto Currency Mining Activity Detected
- 4088e9a1-d873-4ee0-a773-1714a4b2872e.o (PID: 13001)
Connects to SSH
- 4088e9a1-d873-4ee0-a773-1714a4b2872e.o (PID: 13001)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .o | | | ELF Executable and Linkable format (generic) (100) |
|---|
EXIF
EXE
| CPUArchitecture: | 64 bit |
|---|---|
| CPUByteOrder: | Little endian |
| ObjectFileType: | Shared object file |
| CPUType: | AMD x86-64 |
Total processes
255
Monitored processes
42
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 12935 | /bin/sh -c "DISPLAY=:0 sudo -iu user nautilus /home/user/Desktop/4088e9a1-d873-4ee0-a773-1714a4b2872e\.o " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 12936 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12937 | sudo -iu user nautilus /home/user/Desktop/4088e9a1-d873-4ee0-a773-1714a4b2872e.o | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN | ||||
| 12938 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12939 | nautilus /home/user/Desktop/4088e9a1-d873-4ee0-a773-1714a4b2872e.o | /usr/bin/nautilus | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 12940 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12961 | /lib/systemd/systemd-hostnamed | /lib/systemd/systemd-hostnamed | — | systemd |
User: root Integrity Level: UNKNOWN Exit code: 13001 | ||||
| 12967 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
| 12968 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
| 12969 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 482 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
979
TCP/UDP connections
23 958
DNS requests
72
Threats
27 116
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | GET | — | 134.236.9.210:80 | http://134.236.9.210:80/vendor/phpunit/src/Util/PHP/eval-stdin.php | unknown | — | — | unknown |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | GET | — | 104.112.131.19:80 | http://104.112.131.19:80/vendor/phpunit/phpunit/LICENSE/eval-stdin.php | unknown | — | — | unknown |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | POST | — | 54.222.161.225:80 | http://54.222.161.225:80/cgi-bin/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/bin/sh | unknown | — | — | unknown |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | GET | — | 49.207.2.74:80 | http://49.207.2.74:80/vendor/phpunit/phpunit/LICENSE/eval-stdin.php | unknown | — | — | unknown |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | GET | 502 | 31.184.201.38:80 | http://31.184.201.38:80/phpunit/phpunit/src/Util/PHP/eval-stdin.php | unknown | — | — | unknown |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | POST | — | 2.17.229.68:80 | http://2.17.229.68:80/cgi-bin/.%2e/.%2e/.%2e/.%2e/.%2e/.%2e/.%2e/.%2e/.%2e/.%2e/bin/sh | unknown | — | — | unknown |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | GET | 403 | 196.207.45.100:80 | http://196.207.45.100:80/laravel/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php | unknown | — | — | unknown |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | GET | — | 23.7.32.68:80 | http://23.7.32.68:80/phpunit/phpunit/src/Util/PHP/eval-stdin.php | unknown | — | — | unknown |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | GET | — | 54.192.227.125:80 | http://54.192.227.125:80/lib/phpunit/phpunit/src/Util/PHP/eval-stdin.php | unknown | — | — | unknown |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | POST | — | 47.92.205.72:80 | http://47.92.205.72:80/cgi-bin/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/bin/sh | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | 95.215.19.53:853 | — | ab stract | FI | unknown |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | 1.1.1.1:853 | — | CLOUDFLARENET | — | malicious |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | 217.160.70.42:853 | — | IONOS SE | DE | unknown |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | 1.0.0.1:853 | — | CLOUDFLARENET | AU | unknown |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | 178.254.22.166:853 | — | EVANZO e-commerce GmbH | DE | unknown |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | 8.8.8.8:853 | — | GOOGLE | US | whitelisted |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | 81.169.136.222:853 | — | Strato AG | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.snapcraft.io |
| unknown |
45.100.168.192.in-addr.arpa |
| unknown |
proxies.internetshadow.org |
| unknown |
ktpc.bizphone.co.kr |
| unknown |
www.ersatzteile-online-bestellen.de |
| unknown |
sisierp.fenicio.com.uy |
| unknown |
www.finam.ru |
| unknown |
mx.machinedcastingsproduction.com |
| unknown |
britta-zuber.de |
| unknown |
eforms-dev.sh.ch |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | Misc Attack | ET COMPROMISED Known Compromised or Hostile Host Traffic group 7 |
13001 | 4088e9a1-d873-4ee0-a773-1714a4b2872e.o | Crypto Currency Mining Activity Detected | MINER [ANY.RUN] CoinMiner Agent CnC Initial Connection |
— | — | Attempted Information Leak | ET SCAN Potential SSH Scan OUTBOUND |
— | — | Attempted Information Leak | ET SCAN Potential SSH Scan OUTBOUND |
— | — | Attempted Information Leak | ET SCAN Potential SSH Scan OUTBOUND |
— | — | Attempted Information Leak | ET SCAN Potential SSH Scan OUTBOUND |
— | — | Attempted Information Leak | ET SCAN Potential SSH Scan OUTBOUND |
— | — | Attempted Information Leak | ET SCAN Potential SSH Scan OUTBOUND |
— | — | Attempted Information Leak | ET SCAN Potential SSH Scan OUTBOUND |
— | — | Attempted Information Leak | ET SCAN Potential SSH Scan OUTBOUND |
7 ETPRO signatures available at the full report