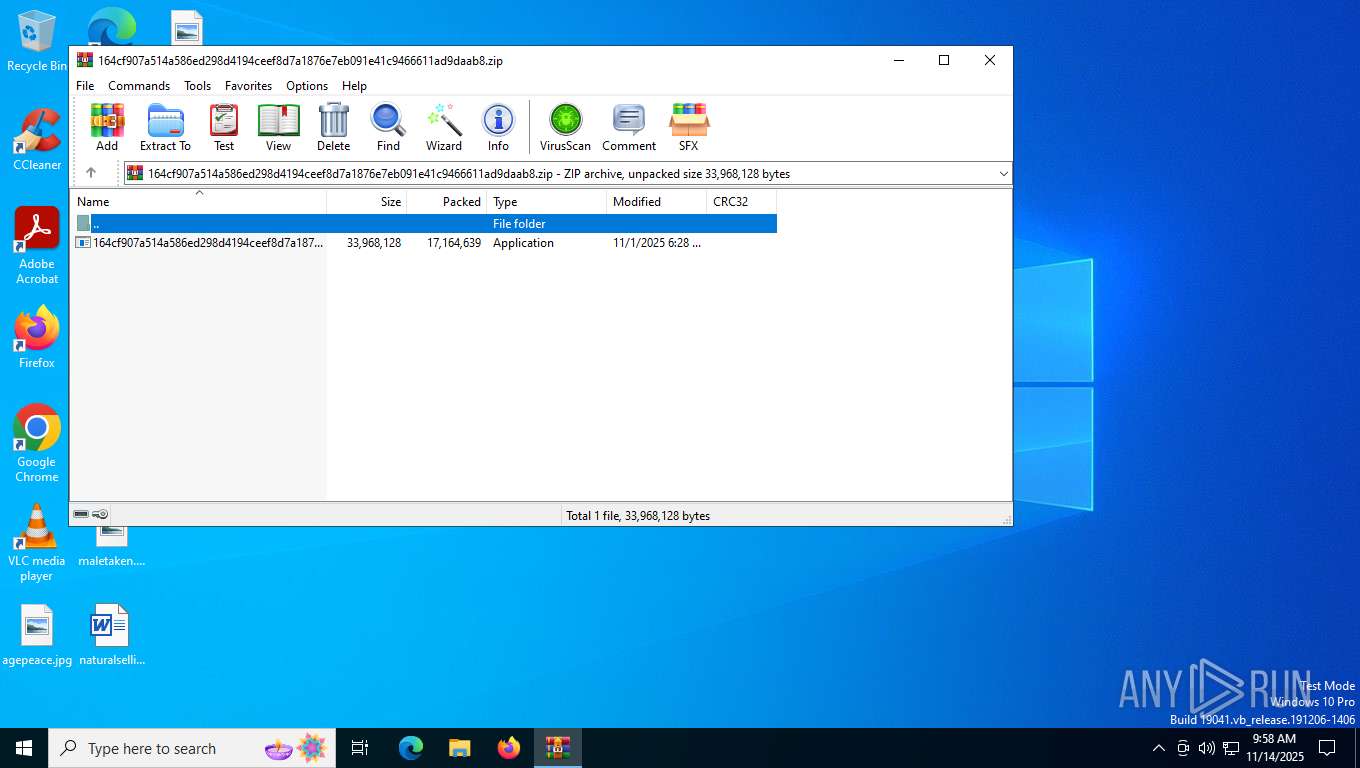
| File name: | 164cf907a514a586ed298d4194ceef8d7a1876e7eb091e41c9466611ad9daab8.zip |
| Full analysis: | https://app.any.run/tasks/a8e5903f-8a9b-4ba8-ae81-34160c7420eb |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | November 14, 2025, 09:58:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 0F293089EEF06714EA06F1D7F6B48E0D |
| SHA1: | E254B33EFB2A28ADD4852CB9330F72F927E93E97 |
| SHA256: | AB5FEFCADC5F5832E4A14BC73A435297E3B1197F2C7BA25368F7DB512CB0A8CD |
| SSDEEP: | 196608:r7wZwr+pSX/wivGRRBpXVyc8fWKdGOulmOWNX67duok:rUSypDpXVVQ5d5LlHok |
MALICIOUS
LUMMA has been found (auto)
- WinRAR.exe (PID: 5580)
SUSPICIOUS
Executing commands from a ".bat" file
- 164cf907a514a586ed298d4194ceef8d7a1876e7eb091e41c9466611ad9daab8.exe (PID: 4080)
Starts CMD.EXE for commands execution
- 164cf907a514a586ed298d4194ceef8d7a1876e7eb091e41c9466611ad9daab8.exe (PID: 4080)
Get information on the list of running processes
- cmd.exe (PID: 2284)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2284)
Starts application with an unusual extension
- cmd.exe (PID: 2284)
Starts the AutoIt3 executable file
- cmd.exe (PID: 2284)
The executable file from the user directory is run by the CMD process
- Tvs.scr (PID: 4644)
Executes application which crashes
- Tvs.scr (PID: 1128)
The process checks if it is being run in the virtual environment
- OpenWith.exe (PID: 5692)
INFO
Checks supported languages
- 164cf907a514a586ed298d4194ceef8d7a1876e7eb091e41c9466611ad9daab8.exe (PID: 4080)
- extrac32.exe (PID: 6120)
- Tvs.scr (PID: 4644)
- Tvs.scr (PID: 1128)
Manual execution by a user
- 164cf907a514a586ed298d4194ceef8d7a1876e7eb091e41c9466611ad9daab8.exe (PID: 4080)
- Tvs.scr (PID: 1128)
Reads the computer name
- extrac32.exe (PID: 6120)
- Tvs.scr (PID: 4644)
Create files in a temporary directory
- 164cf907a514a586ed298d4194ceef8d7a1876e7eb091e41c9466611ad9daab8.exe (PID: 4080)
- extrac32.exe (PID: 6120)
Reads mouse settings
- Tvs.scr (PID: 4644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:11:01 18:28:52 |
| ZipCRC: | 0x0566160f |
| ZipCompressedSize: | 17164639 |
| ZipUncompressedSize: | 33968128 |
| ZipFileName: | 164cf907a514a586ed298d4194ceef8d7a1876e7eb091e41c9466611ad9daab8.exe |
Total processes
158
Monitored processes
16
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1128 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\800530\Tvs.scr | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\800530\Tvs.scr | explorer.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 3221225477 Version: 3, 3, 17, 0 Modules
| |||||||||||||||
| 1264 | findstr /V "Skip" Attending | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | CheckNetIsolation.exe | C:\Windows\System32\CheckNetIsolation.exe | — | 164cf907a514a586ed298d4194ceef8d7a1876e7eb091e41c9466611ad9daab8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AppContainer Network Isolation Diagnostic Tool Exit code: 87 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2060 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | cmd /c move Respondent.psd Respondent.psd.bat && Respondent.psd.bat | C:\Windows\System32\cmd.exe | — | 164cf907a514a586ed298d4194ceef8d7a1876e7eb091e41c9466611ad9daab8.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3032 | findstr "bdservicehost ekrn AvastUI SophosHealth AVGUI nsWscSvc" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3236 | waitfor /T 5 eYYQFFTIIQURTKyXPqX | C:\Windows\System32\waitfor.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: waitfor - wait/send a signal over a network Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | CheckNetIsolation.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4080 | "C:\Users\admin\Desktop\164cf907a514a586ed298d4194ceef8d7a1876e7eb091e41c9466611ad9daab8.exe" | C:\Users\admin\Desktop\164cf907a514a586ed298d4194ceef8d7a1876e7eb091e41c9466611ad9daab8.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4568 | tasklist | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 207
Read events
6 197
Write events
10
Delete events
0
Modification events
| (PID) Process: | (5580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (5580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (5580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\164cf907a514a586ed298d4194ceef8d7a1876e7eb091e41c9466611ad9daab8.zip | |||
| (PID) Process: | (5580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5580) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
21
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4080 | 164cf907a514a586ed298d4194ceef8d7a1876e7eb091e41c9466611ad9daab8.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Chevy.psd | binary | |
MD5:D6594FC6429EE09988174388B7B84739 | SHA256:97FB3DBB72AD59275D71087400329038778B50E116B8EE9CE1AEF4C7FFEDE2E3 | |||
| 4080 | 164cf907a514a586ed298d4194ceef8d7a1876e7eb091e41c9466611ad9daab8.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Fda.psd | binary | |
MD5:280002D1843174FFD7A57C096D5F133F | SHA256:CBE7EA7A5F3C7C4E90060521DD0E256107EC9F3E0C43F8CC61E02454547D6EB9 | |||
| 4080 | 164cf907a514a586ed298d4194ceef8d7a1876e7eb091e41c9466611ad9daab8.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Swing.psd | binary | |
MD5:2BBAD57F9829F9C1C5D4D915ED7410D9 | SHA256:8287D24A90B7CD8FA286DCF53086419FFF1739C7AD2FF0BBCCB3A60C760FD1D4 | |||
| 2284 | cmd.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Respondent.psd.bat | text | |
MD5:2B131140BBC896FD81E58910866DBB93 | SHA256:08FEDCF2D3131F5A5B13A6632667C6EE914D5E53A3EF69CDB58A69AF36B4939F | |||
| 6120 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Presented | binary | |
MD5:692A43FDFF675D73B7A17B392D63C66F | SHA256:9F67FB323B7BC55FE0C9687779CC768C078CE3285149251F037959FD85DE5565 | |||
| 6120 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Avon | binary | |
MD5:406E2CAD1703BB61A3F1921DFD045E6E | SHA256:16F5D3343F4ADA77DB96F8D42E3880E4341B5694E35232B350533CE32FE97E15 | |||
| 6120 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Surgical | binary | |
MD5:0149ADD902ADAA30263487508CB62BE1 | SHA256:1D2EA9468BF82DB1B35DBDE01B0CE58A2C4C9703D9185EC2607ABC73F3B332E5 | |||
| 6120 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Ment | binary | |
MD5:437721419863AD35077DF57149E169A4 | SHA256:C4A07B7757FABCA2F5B462CD2C5B775E878A7DEF4110729B67735E3CC83DC513 | |||
| 6120 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Baker | binary | |
MD5:67D5F51BFF253D495169023BE14AD9DE | SHA256:C1CAB6C6C1033A585B62C5CBD63772A9F4BC32465F628158D05DA0C598D66F72 | |||
| 6120 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Murder | binary | |
MD5:3074B271342E4D2FF8A9597697132FF0 | SHA256:C5EF7F21D4966440DA160C19AB209957C0CC6B4CF24A026B2F3C2BF523410389 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
46
DNS requests
13
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | — | 341 b | whitelisted |
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | — | 341 b | whitelisted |
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | — | 341 b | whitelisted |
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | — | 341 b | whitelisted |
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | — | 341 b | whitelisted |
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | — | 341 b | whitelisted |
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | — | 341 b | whitelisted |
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | — | 341 b | whitelisted |
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | — | 341 b | whitelisted |
— | — | POST | 404 | 49.13.77.253:443 | https://49.13.77.253/RST2.srf | unknown | — | 341 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5232 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2972 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5232 | svchost.exe | 20.190.160.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3236 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5524 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4244 | SIHClient.exe | 74.178.240.61:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4244 | SIHClient.exe | 52.165.164.15:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ZVFVtcVCsVZDOyLbtlvVUO.ZVFVtcVCsVZDOyLbtlvVUO |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
15.164.165.52.in-addr.arpa |
| whitelisted |
7.4.8.4.4.3.1.4.0.0.0.0.0.0.0.0.0.0.0.a.0.0.1.f.1.1.1.0.1.0.a.2.ip6.arpa |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Rhadamanthys Stage Payload HTTP Request outbound |
— | — | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Rhadamanthys Stage Payload HTTP Request outbound |
— | — | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Rhadamanthys Stage Payload HTTP Request outbound |
— | — | A Network Trojan was detected | MALWARE [ANY.RUN] Win32/Rhadamanthys Stage Payload HTTP Request outbound |