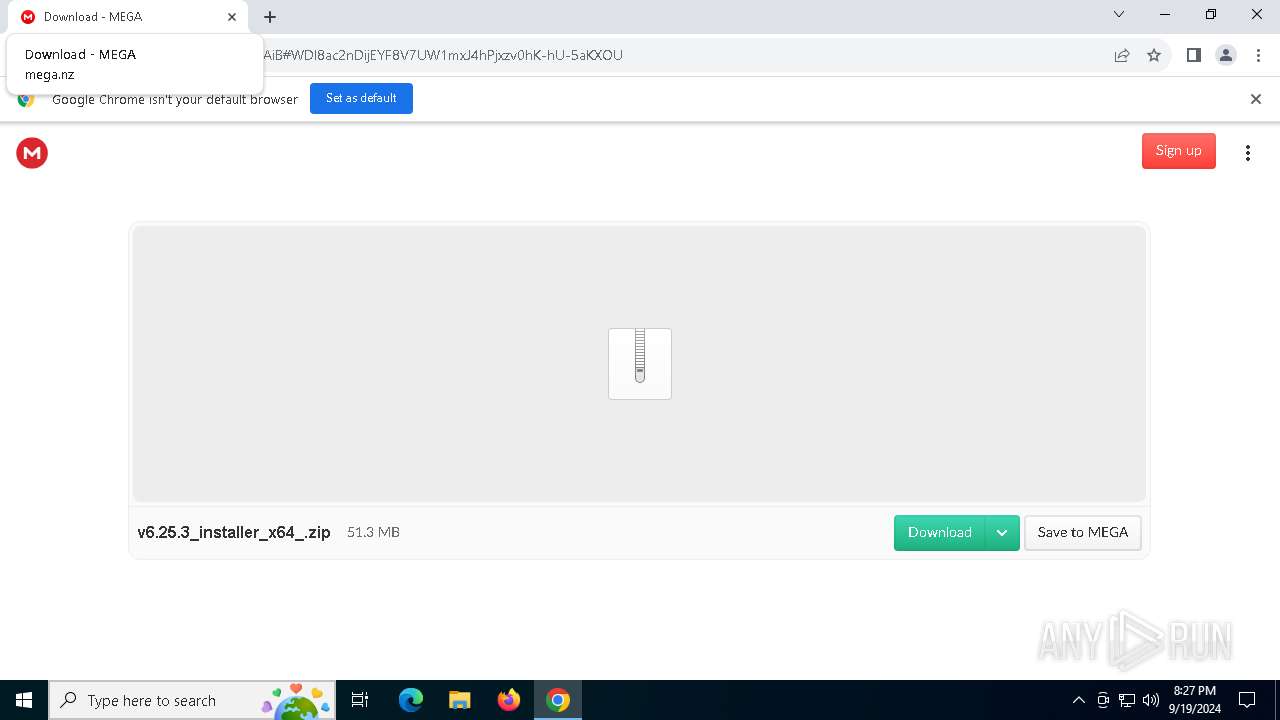
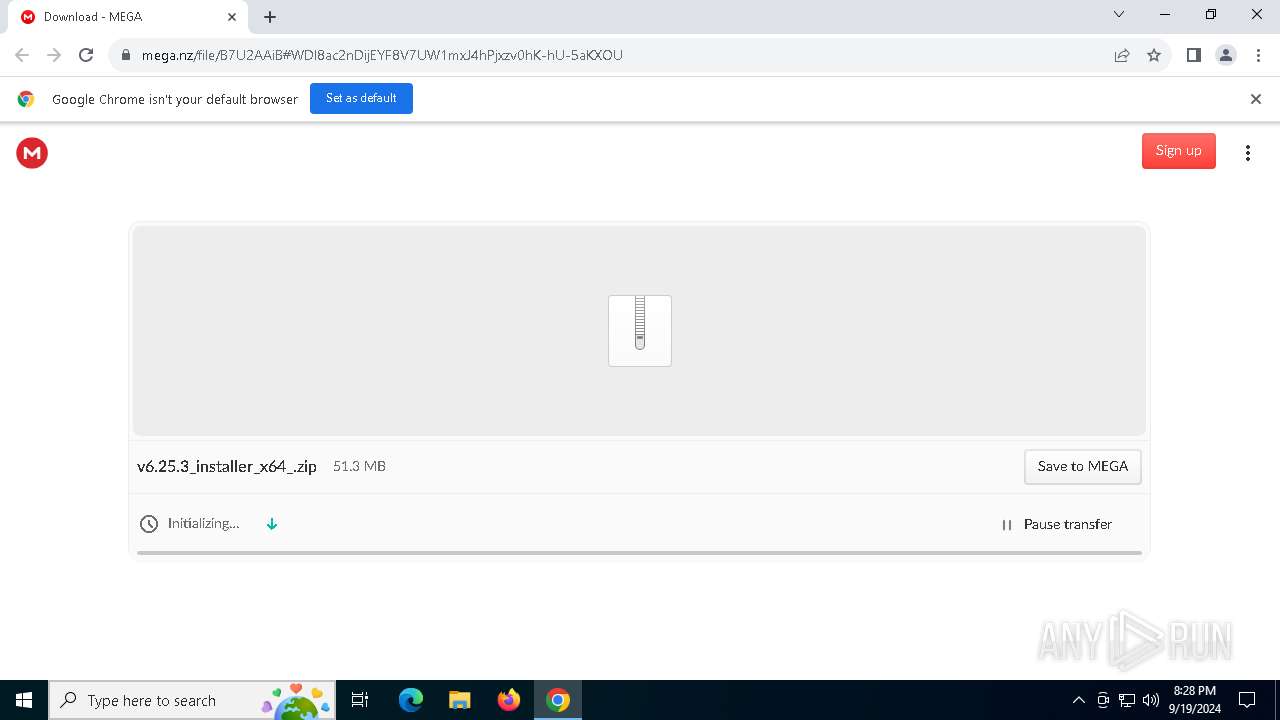
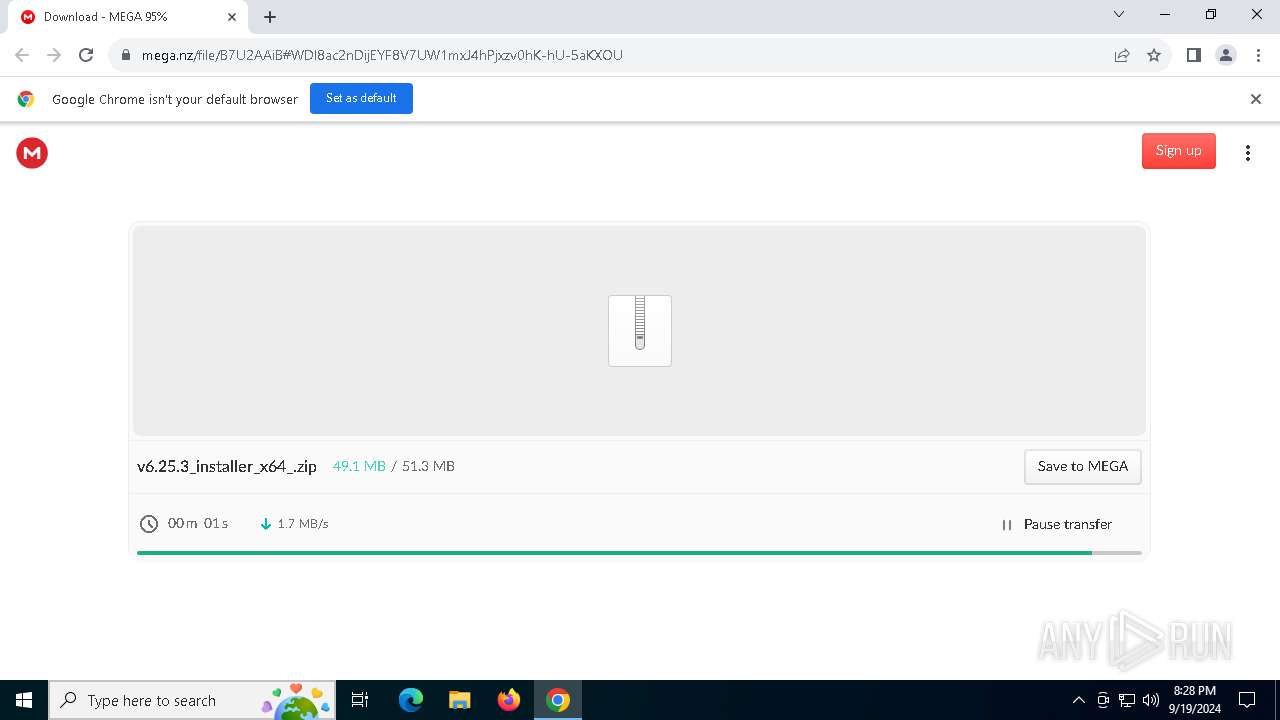
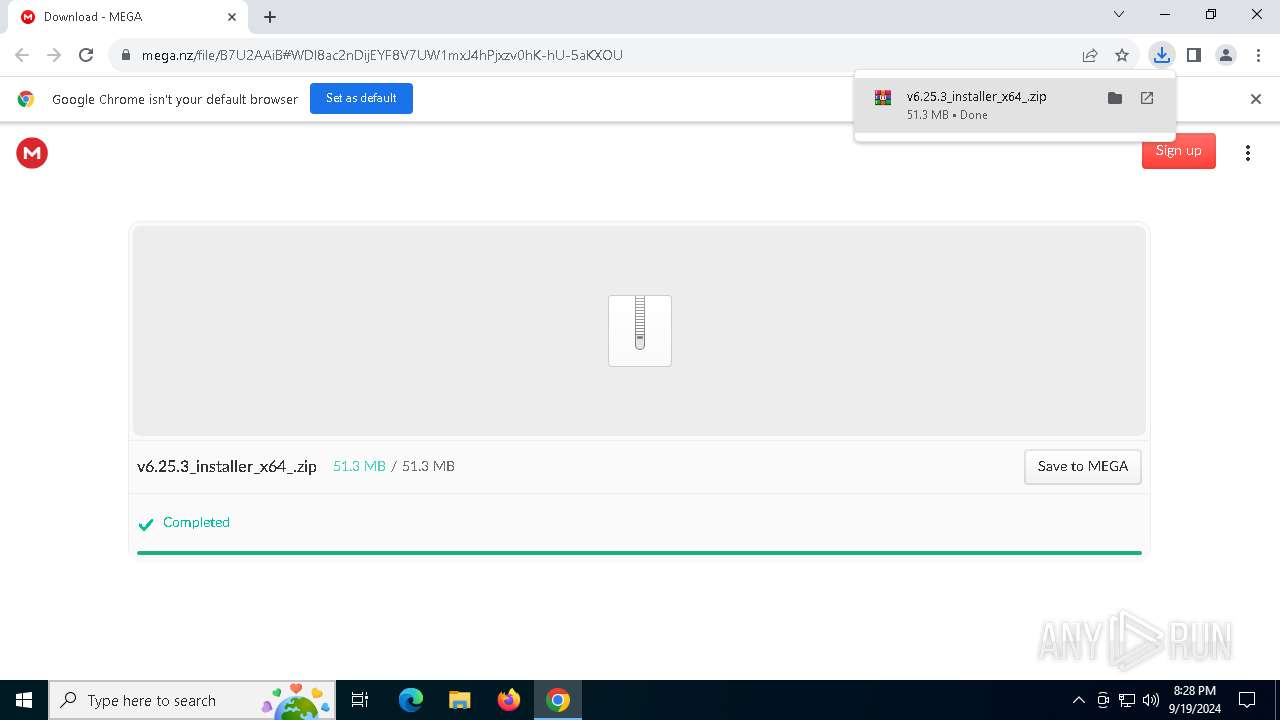
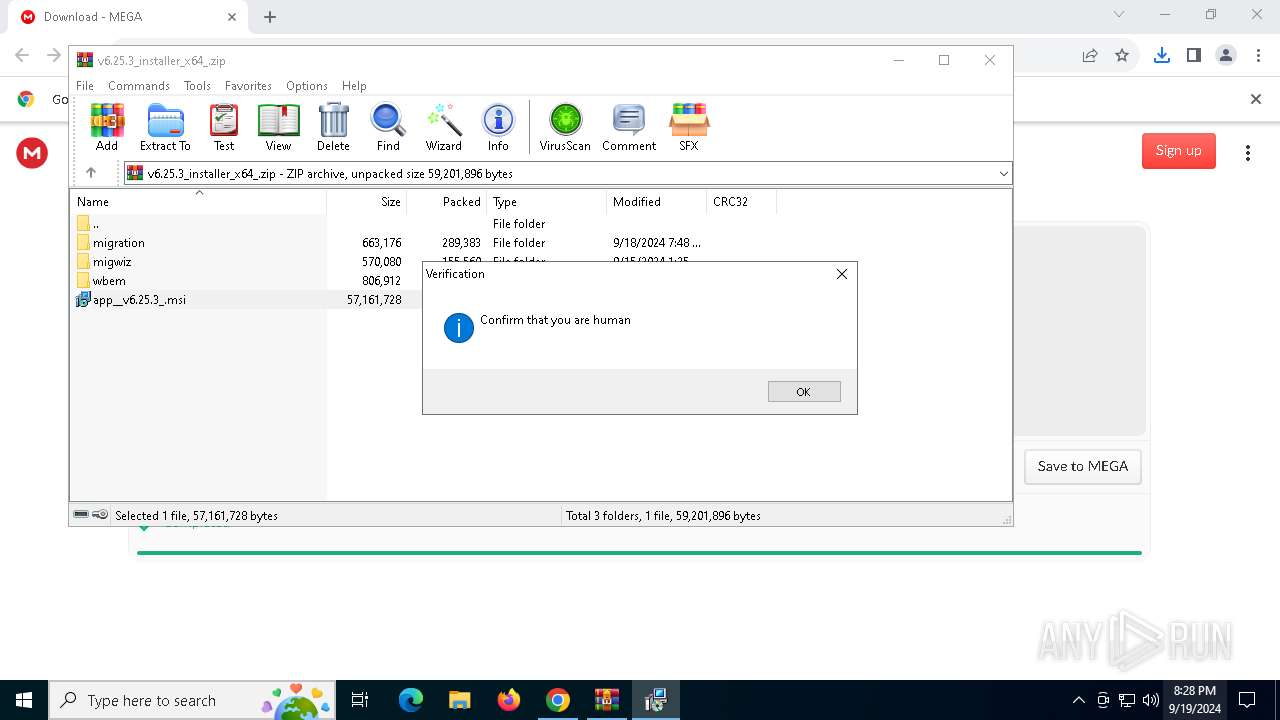
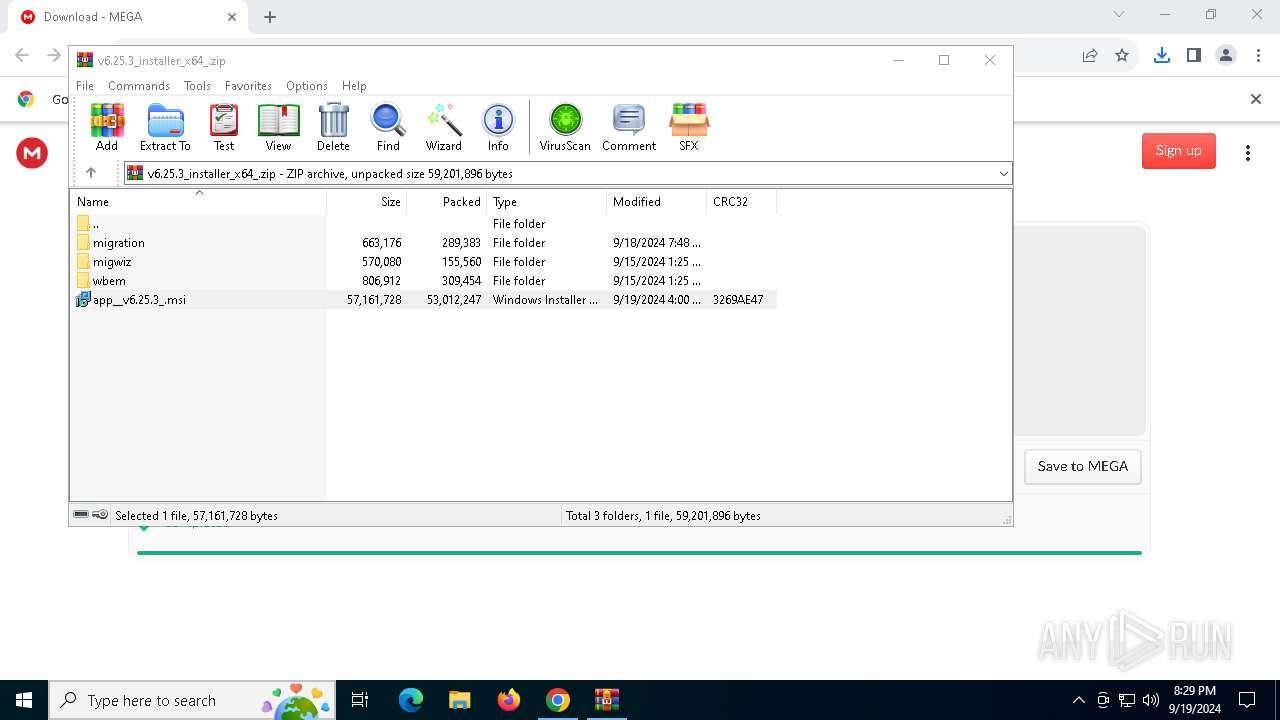
| URL: | https://mega.nz/file/B7U2AAiB#WDl8ac2nDijEYF8V7UW1mxJ4hPjxzv0hK-hU-5aKXOU |
| Full analysis: | https://app.any.run/tasks/ae18c863-4cf9-40ed-bb9d-7a2f7322ed2b |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | September 19, 2024, 20:27:47 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F865A15FA5B404A5B9731425E0BA14F5 |
| SHA1: | 915743312B1E901A20689C76559479E2E234BCA3 |
| SHA256: | AB0A00A0AF58E4C436012135E72E55A1A231D4C9B134DAB1F409C2C6B7B946BE |
| SSDEEP: | 3:N8X/ilwXtxaGukbgJnPdfzHiIIIw:2CwdYkbgplIIw |
MALICIOUS
Actions looks like stealing of personal data
- explorer.exe (PID: 5540)
- powershell.exe (PID: 6196)
Run PowerShell with an invisible window
- powershell.exe (PID: 6196)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6196)
LUMMA has been detected (SURICATA)
- explorer.exe (PID: 5540)
Stealers network behavior
- explorer.exe (PID: 5540)
SUSPICIOUS
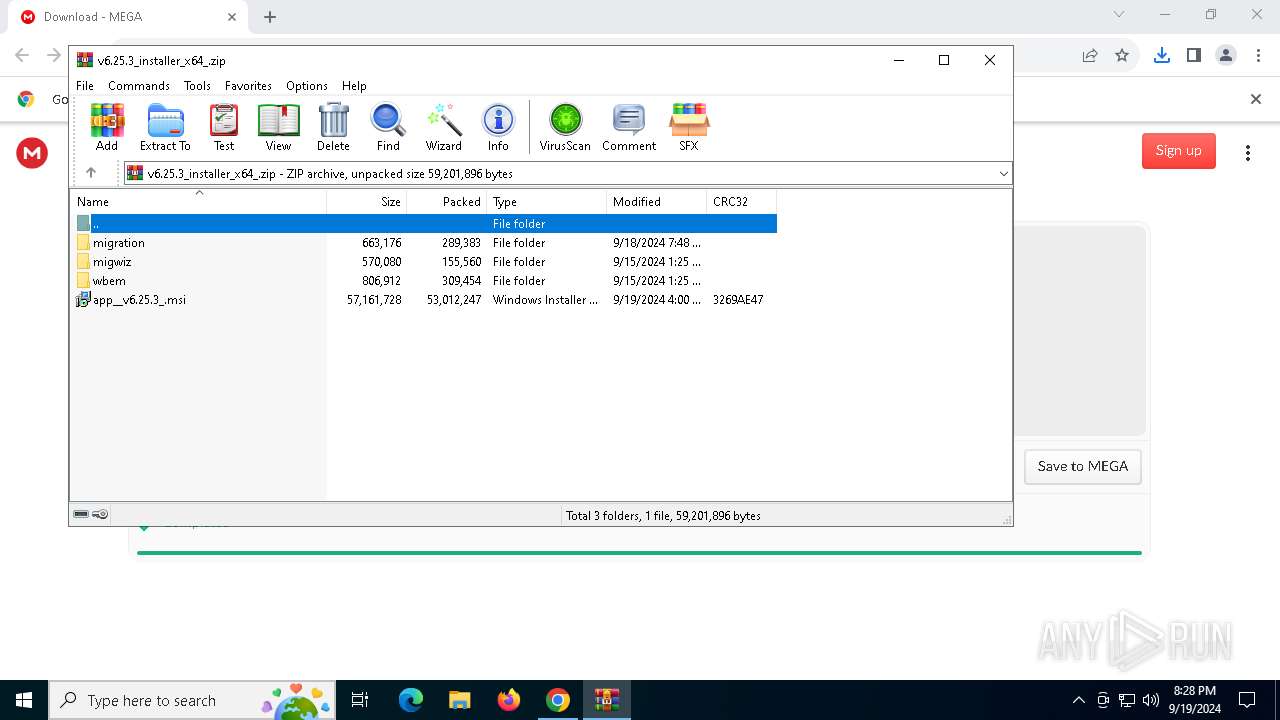
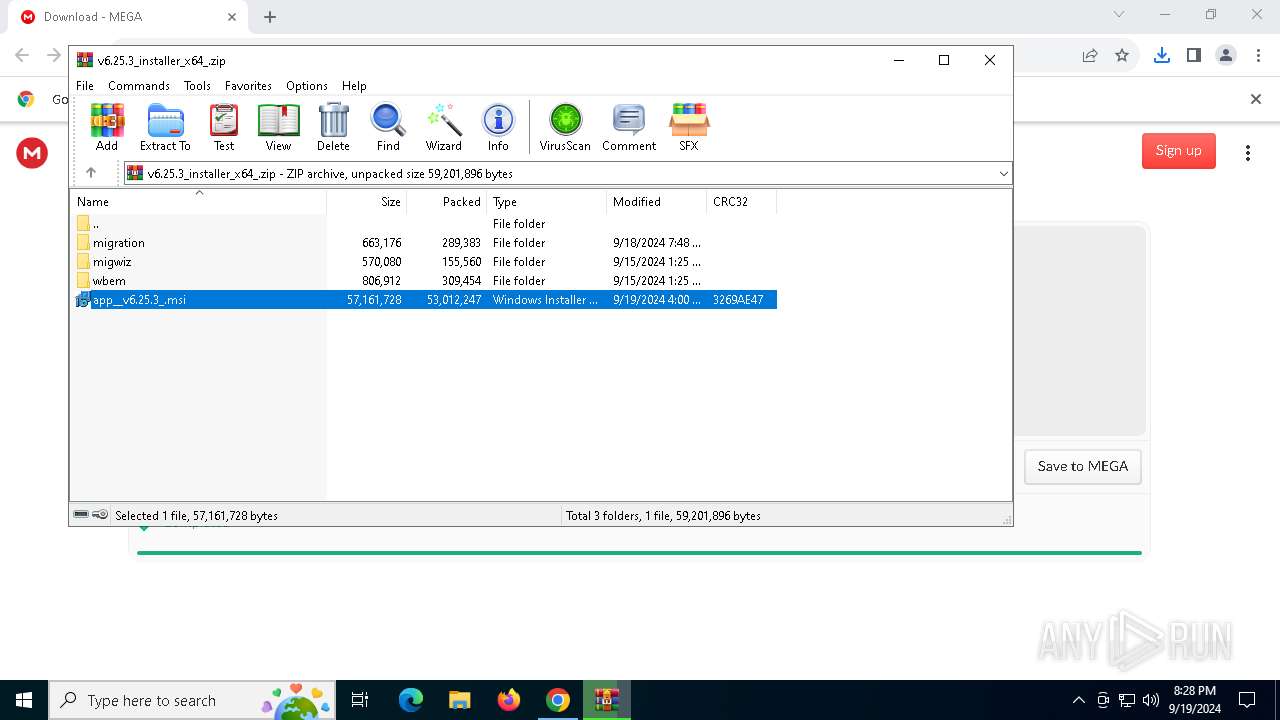
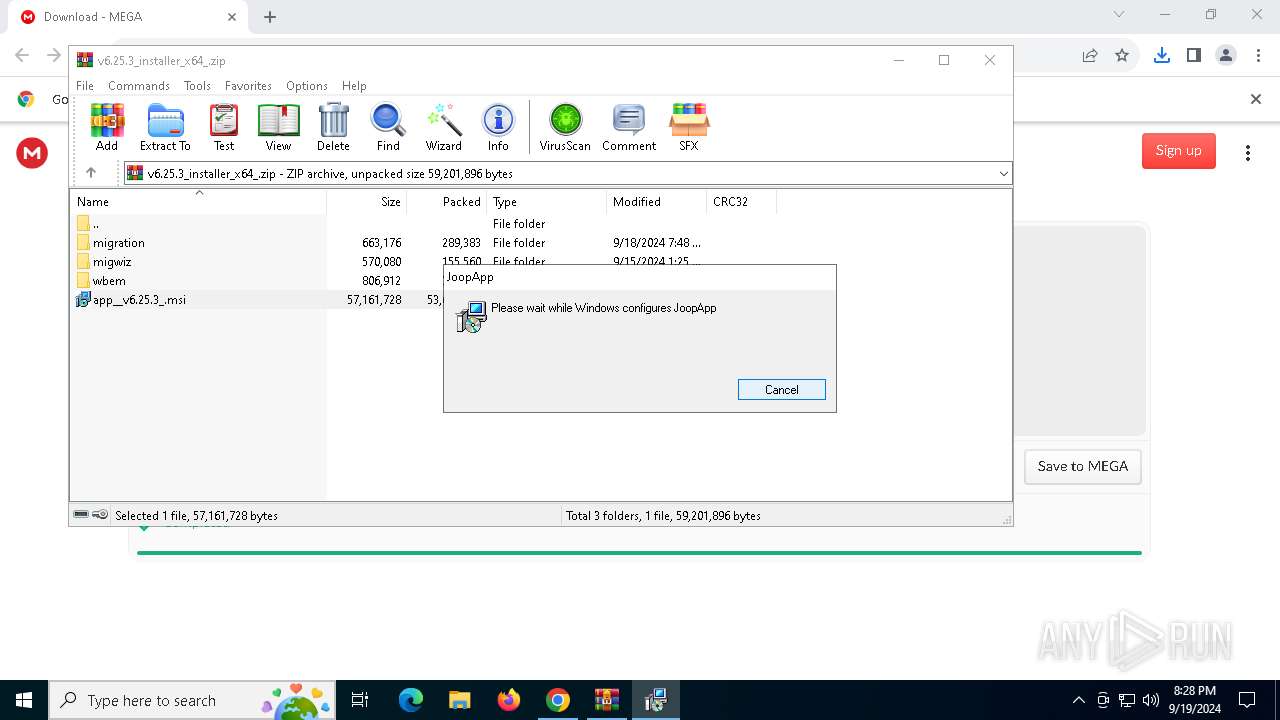
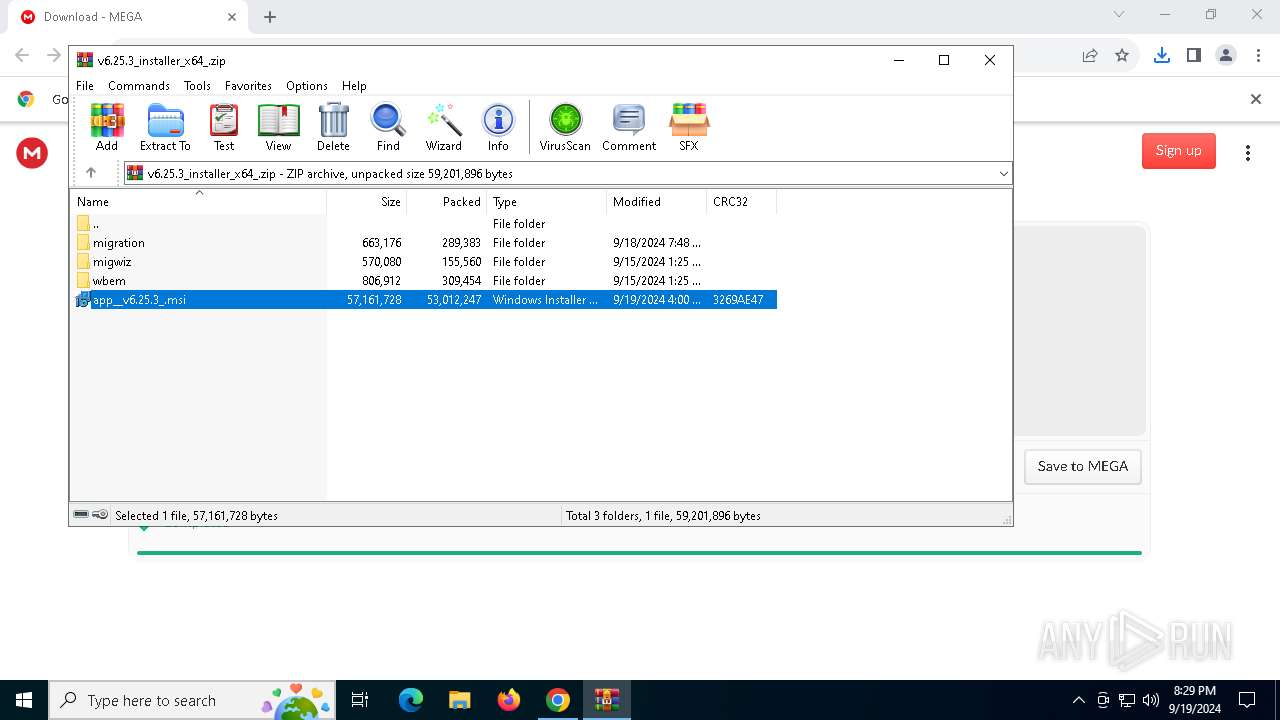
Process drops legitimate windows executable
- WinRAR.exe (PID: 3464)
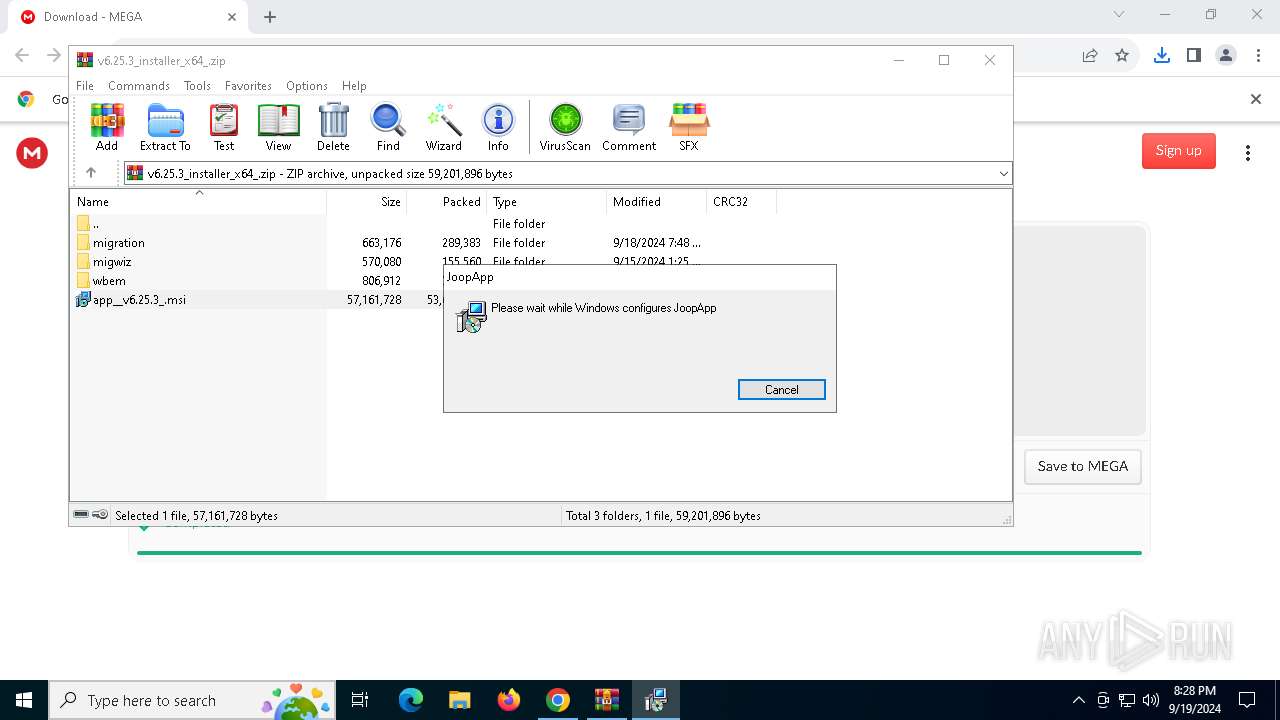
- msiexec.exe (PID: 6232)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6232)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3464)
- msiexec.exe (PID: 4160)
Checks Windows Trust Settings
- msiexec.exe (PID: 4160)
The process creates files with name similar to system file names
- msiexec.exe (PID: 6232)
Executable content was dropped or overwritten
- UnRAR.exe (PID: 6556)
BASE64 encoded PowerShell command has been detected
- explorer.exe (PID: 5540)
Executes application which crashes
- NVIDIA GeForce Experience.exe (PID: 7096)
Base64-obfuscated command line is found
- explorer.exe (PID: 5540)
Starts POWERSHELL.EXE for commands execution
- explorer.exe (PID: 5540)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 6196)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 6196)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6196)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 6196)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 6196)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 6196)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 6196)
INFO
Reads Microsoft Office registry keys
- chrome.exe (PID: 1680)
- WinRAR.exe (PID: 3464)
Application launched itself
- chrome.exe (PID: 1680)
- chrome.exe (PID: 2608)
The process uses the downloaded file
- chrome.exe (PID: 1680)
- chrome.exe (PID: 6764)
- WinRAR.exe (PID: 3464)
- powershell.exe (PID: 6196)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3464)
- msiexec.exe (PID: 6232)
- chrome.exe (PID: 5724)
Reads the computer name
- msiexec.exe (PID: 6232)
- msiexec.exe (PID: 4160)
Checks supported languages
- msiexec.exe (PID: 4160)
- msiexec.exe (PID: 6232)
- NVIDIA GeForce Experience.exe (PID: 7096)
- UnRAR.exe (PID: 6556)
Reads Environment values
- msiexec.exe (PID: 4160)
Reads the machine GUID from the registry
- msiexec.exe (PID: 4160)
Checks proxy server information
- msiexec.exe (PID: 4160)
- explorer.exe (PID: 5540)
- powershell.exe (PID: 6196)
Create files in a temporary directory
- msiexec.exe (PID: 4160)
- explorer.exe (PID: 5540)
Creates files or folders in the user directory
- msiexec.exe (PID: 4160)
- msiexec.exe (PID: 6232)
- UnRAR.exe (PID: 6556)
- explorer.exe (PID: 5540)
Reads the software policy settings
- msiexec.exe (PID: 4160)
- explorer.exe (PID: 5540)
Sends debugging messages
- NVIDIA GeForce Experience.exe (PID: 7096)
Creates a software uninstall entry
- msiexec.exe (PID: 6232)
Disables trace logs
- powershell.exe (PID: 6196)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6196)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6196)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 6196)
Reads security settings of Internet Explorer
- explorer.exe (PID: 5540)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6196)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 6196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
194
Monitored processes
58
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5936 --field-trial-handle=1644,i,10733136138438959611,15497317446714947757,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5548 --field-trial-handle=1644,i,10733136138438959611,15497317446714947757,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | |||||||||||||||
| 1084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5196 --field-trial-handle=1936,i,10547275955569687088,5506130883605200938,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5924 --field-trial-handle=1644,i,10733136138438959611,15497317446714947757,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | |||||||||||||||
| 1680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://mega.nz/file/B7U2AAiB#WDl8ac2nDijEYF8V7UW1mxJ4hPjxzv0hK-hU-5aKXOU" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 4294967295 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5128 --field-trial-handle=1936,i,10547275955569687088,5506130883605200938,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1944 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5760 --field-trial-handle=1644,i,10733136138438959611,15497317446714947757,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | |||||||||||||||
| 1988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5724 --field-trial-handle=1644,i,10733136138438959611,15497317446714947757,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | |||||||||||||||
| 2040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2064 --field-trial-handle=1936,i,10547275955569687088,5506130883605200938,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 4294967295 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
17 691
Read events
17 512
Write events
170
Delete events
9
Modification events
| (PID) Process: | (1680) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1680) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1680) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1680) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1680) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6764) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000005E708F86D20ADB01 | |||
| (PID) Process: | (1680) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
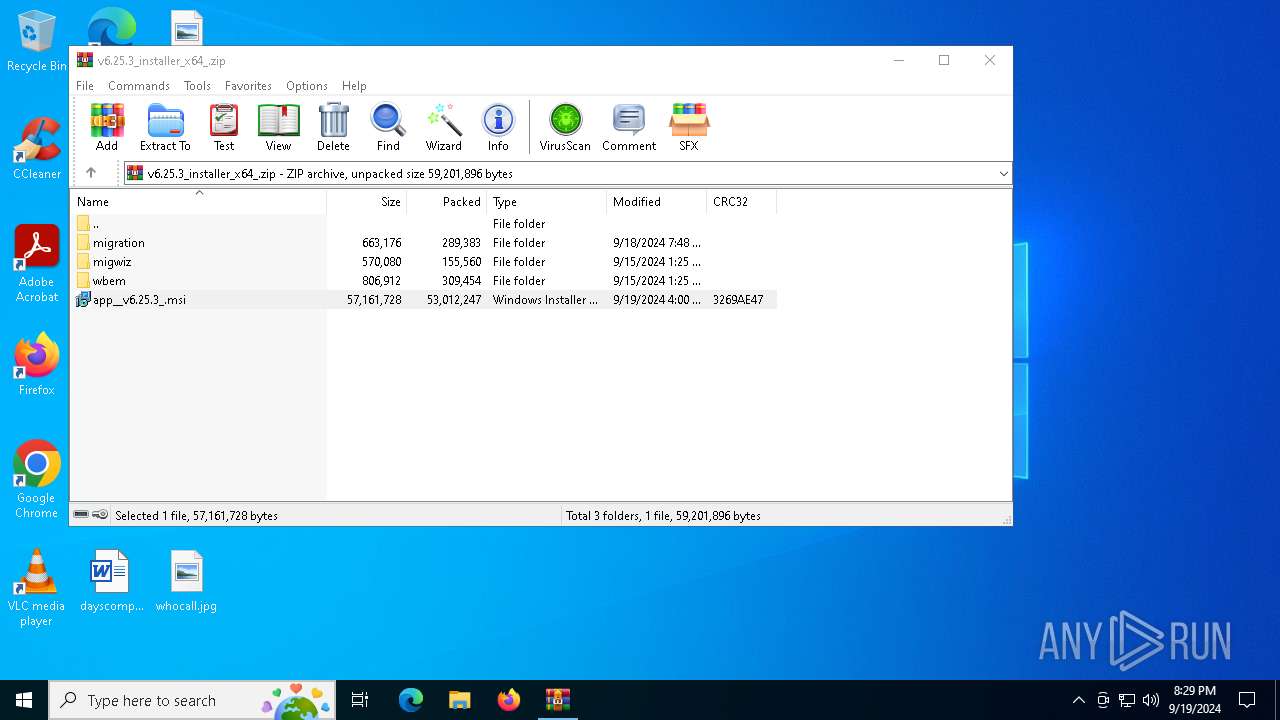
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\v6.25.3_installer_x64_.zip | |||
| (PID) Process: | (3464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
Executable files
74
Suspicious files
368
Text files
161
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1fb6a7.TMP | — | |
MD5:— | SHA256:— | |||
| 1680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1fb6a7.TMP | — | |
MD5:— | SHA256:— | |||
| 1680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:FC81892AC822DCBB09441D3B58B47125 | SHA256:FB077C966296D02D50CCBF7F761D2A3311A206A784A7496F331C2B0D6AD205C8 | |||
| 1680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1fb687.TMP | text | |
MD5:8F45965291AB2DA10EEB049FB6E917C6 | SHA256:8A0DE526945B27CDBBD87357C85FDDD37B572370F894CB0A5AC533FD465D2166 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
91
DNS requests
71
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3116 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6272 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
5408 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5408 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6272 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
4160 | msiexec.exe | GET | 200 | 142.250.186.67:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
4160 | msiexec.exe | GET | 200 | 142.250.186.67:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
6272 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
6272 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4040 | svchost.exe | 40.119.249.228:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.119.249.228:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
— | — | 40.119.249.228:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
— | — | 20.42.73.24:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2040 | chrome.exe | 31.216.144.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
1680 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
mega.nz |
| whitelisted |
accounts.google.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
g.api.mega.co.nz |
| shared |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2040 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
2040 | chrome.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
2040 | chrome.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
2040 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2040 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2040 | chrome.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
2040 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2040 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2040 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
2040 | chrome.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
Process | Message |
|---|---|
NVIDIA GeForce Experience.exe | Folder has been created! |