| File name: | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359 |
| Full analysis: | https://app.any.run/tasks/8ce2b318-d315-4169-b61b-3244497c5029 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | May 15, 2025, 14:00:35 |
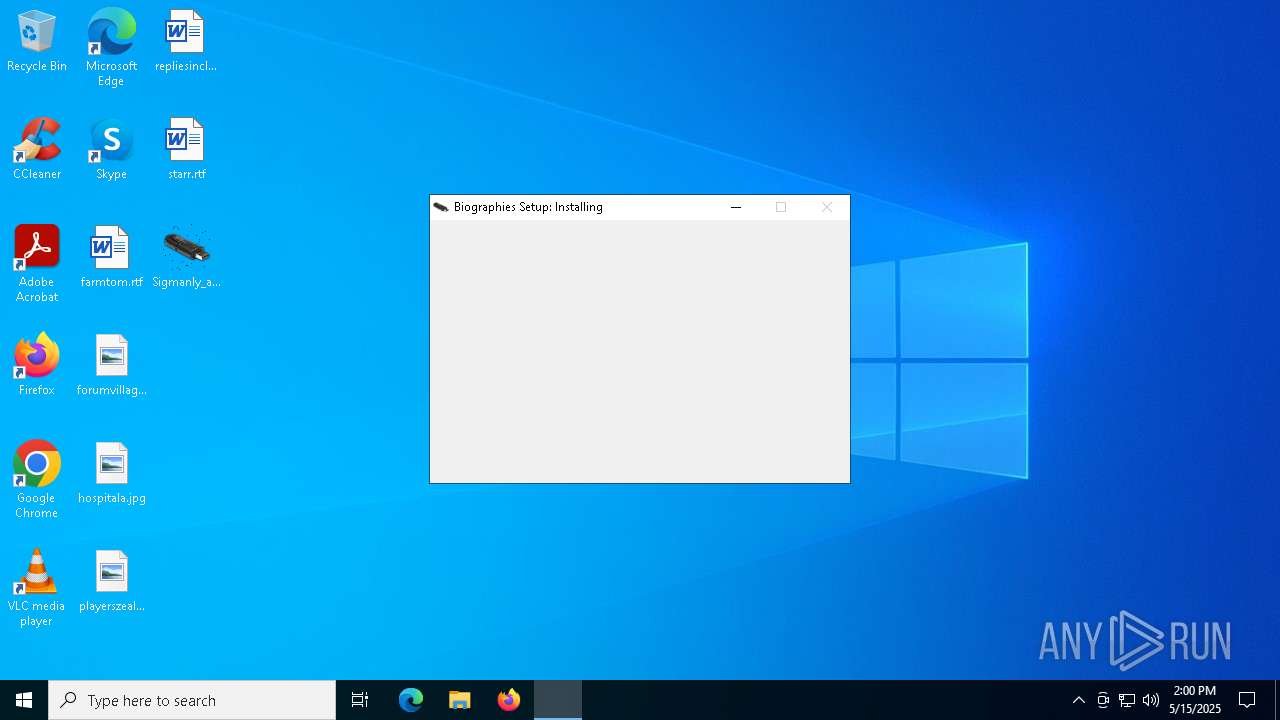
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 8FC6E4D9327E1B173D932575033E7D75 |
| SHA1: | 465F955868361CF32783CD341BE2CAC7F0EDF475 |
| SHA256: | AAA12E52BB0438EFE76E51FEABC2DCA12F37B34BAEB3B83F5F584F6130639359 |
| SSDEEP: | 24576:jwew8LUeWCPUD7f4d0Skz+2ep+Ef9YcciPOLkWM9Da3lqLQTb6pGvfq2KwYLJPQc:jwew8LUeWCPUDj4d0Skz+2ep+Ef9Yccy |
MALICIOUS
Actions looks like stealing of personal data
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
AGENTTESLA has been detected (YARA)
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
AGENTTESLA has been detected (SURICATA)
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
Stealers network behavior
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
Steals credentials from Web Browsers
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
SUSPICIOUS
The process creates files with name similar to system file names
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 5640)
Malware-specific behavior (creating "System.dll" in Temp)
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 5640)
Executable content was dropped or overwritten
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 5640)
Application launched itself
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 5640)
Reads security settings of Internet Explorer
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
Connects to unusual port
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
Checks for external IP
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
- svchost.exe (PID: 2196)
Connects to FTP
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
Connects to the server without a host name
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
There is functionality for taking screenshot (YARA)
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
INFO
Reads the computer name
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 5640)
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
Checks supported languages
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 5640)
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
The sample compiled with english language support
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 5640)
Create files in a temporary directory
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 5640)
Checks proxy server information
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
- slui.exe (PID: 1812)
Reads the machine GUID from the registry
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
Reads the software policy settings
- slui.exe (PID: 1812)
Disables trace logs
- Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe (PID: 1180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:16 00:50:53+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x350d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.3.0.0 |
| ProductVersionNumber: | 2.3.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | powerset |
| CompanyName: | masjas shakable |
| FileDescription: | upgirds protuberous |
| ProductName: | spandes gaardhavehus unnumbed |
Total processes
127
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | "C:\Users\admin\Desktop\Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe" | C:\Users\admin\Desktop\Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | ||||||||||||
User: admin Company: masjas shakable Integrity Level: MEDIUM Description: upgirds protuberous Modules
| |||||||||||||||
| 1812 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5640 | "C:\Users\admin\Desktop\Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe" | C:\Users\admin\Desktop\Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | explorer.exe | ||||||||||||
User: admin Company: masjas shakable Integrity Level: MEDIUM Description: upgirds protuberous Exit code: 0 Modules
| |||||||||||||||
Total events
6 160
Read events
4 830
Write events
1 330
Delete events
0
Modification events
| (PID) Process: | (5640) Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Key: | HKEY_CURRENT_USER\alkali\Uninstall\Iconically95 |
| Operation: | write | Name: | yesternight |
Value: 1 | |||
| (PID) Process: | (5640) Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: u | |||
| (PID) Process: | (5640) Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: us | |||
| (PID) Process: | (5640) Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: use | |||
| (PID) Process: | (5640) Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user | |||
| (PID) Process: | (5640) Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user3 | |||
| (PID) Process: | (5640) Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user32 | |||
| (PID) Process: | (5640) Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user32: | |||
| (PID) Process: | (5640) Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user32:: | |||
| (PID) Process: | (5640) Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user32::S | |||
Executable files
1
Suspicious files
4
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5640 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | C:\Users\admin\AppData\Local\Temp\nsaD0F1.tmp\System.dll | executable | |
MD5:8CF2AC271D7679B1D68EEFC1AE0C5618 | SHA256:6950991102462D84FDC0E3B0AE30C95AF8C192F77CE3D78E8D54E6B22F7C09BA | |||
| 5640 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | C:\Users\admin\AppData\Local\Temp\ostene\Isorosindone.Tri | abr | |
MD5:1878B131BDA603284F692C12849375C5 | SHA256:8E04C8855B66927E6E9DD3444B4BA53CA6020C27072207D0B5CFA34B70502D9F | |||
| 5640 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | C:\Users\admin\AppData\Local\Temp\ostene\libertinerens.trk | binary | |
MD5:EAD518D3C64C03D2D94DB19D7E650EFF | SHA256:F677AB6FDA35EE637C7CAC9DC5A9EF8D06DEDA2B37C67EC21A4DD36F417E565E | |||
| 5640 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | C:\Users\admin\AppData\Local\Temp\ostene\tatchy.sti | binary | |
MD5:8D879505BD68E608A20B75B0B4A493CD | SHA256:766540C36B244E4DEBF17A600C5E602D156BEBFA29B54D34B1F525A9C7AAEF94 | |||
| 5640 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | C:\Users\admin\AppData\Local\Temp\Settings.ini | text | |
MD5:A6216EF9FBE57B11DEEB1B1FD840C392 | SHA256:EDF6C9DA71DAF3B3DA2E89A1BC6B9F4B812F18FC133CF4706A3AE983E4040946 | |||
| 5640 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | C:\Users\admin\AppData\Local\Temp\nsiCA77.tmp | binary | |
MD5:07B2A3D0D42623810190696C714DAD32 | SHA256:B3BD2E88BA71842B5DC03952CE9A7D2AAD00BBD22DDD4F1967D5EB1C9A24E131 | |||
| 5640 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | C:\Users\admin\AppData\Local\Temp\ostene\snetykning.jpg | image | |
MD5:5C16C56F093146AE96CD40F58062D40D | SHA256:4C52D8B84F837BA3A57F3C2799C864CFC5ABA4B891A7849AB46CE1384179AF9A | |||
| 5640 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | C:\Users\admin\AppData\Local\Temp\ostene\amtsplejehjem.ftc | binary | |
MD5:703A3F5142242E63C1ABA6C1A4494028 | SHA256:3B0D585D3841E0FE254D2296A589252955290F6DC52A7A700ACFF31EE8DA4878 | |||
| 5640 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | C:\Users\admin\AppData\Local\Temp\ostene\undersgelseskommision.jpg | image | |
MD5:64913A1D2CAA43204A7293BAD88E9E13 | SHA256:8FAFCDB3462454BE61FE3586AAA7897577E16743164C8840C68780A58718B91A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
56
DNS requests
17
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1180 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | GET | 200 | 192.210.214.133:80 | http://192.210.214.133/YhqRFelno235.bin | unknown | — | — | unknown |
2104 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1180 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
664 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
664 | SIHClient.exe | GET | 200 | 23.48.23.190:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
664 | SIHClient.exe | GET | 200 | 23.48.23.190:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
664 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
664 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
664 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
2104 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.66:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1180 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | 192.210.214.133:80 | — | AS-COLOCROSSING | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ip-api.com |
| whitelisted |
ftp.lampadari.gr |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1180 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Potentially Bad Traffic | ET HUNTING Generic .bin download from Dotted Quad |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
1180 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
1180 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
1180 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | A Network Trojan was detected | ET MALWARE AgentTesla Exfil via FTP |
1180 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Misc activity | INFO [ANY.RUN] FTP protocol command for uploading a file |
1180 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration (raw TCP) |
1180 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration (raw TCP) |
1180 | Sigmanly_aaa12e52bb0438efe76e51feabc2dca12f37b34baeb3b83f5f584f6130639359.exe | Misc activity | INFO [ANY.RUN] FTP server is ready for the new user |