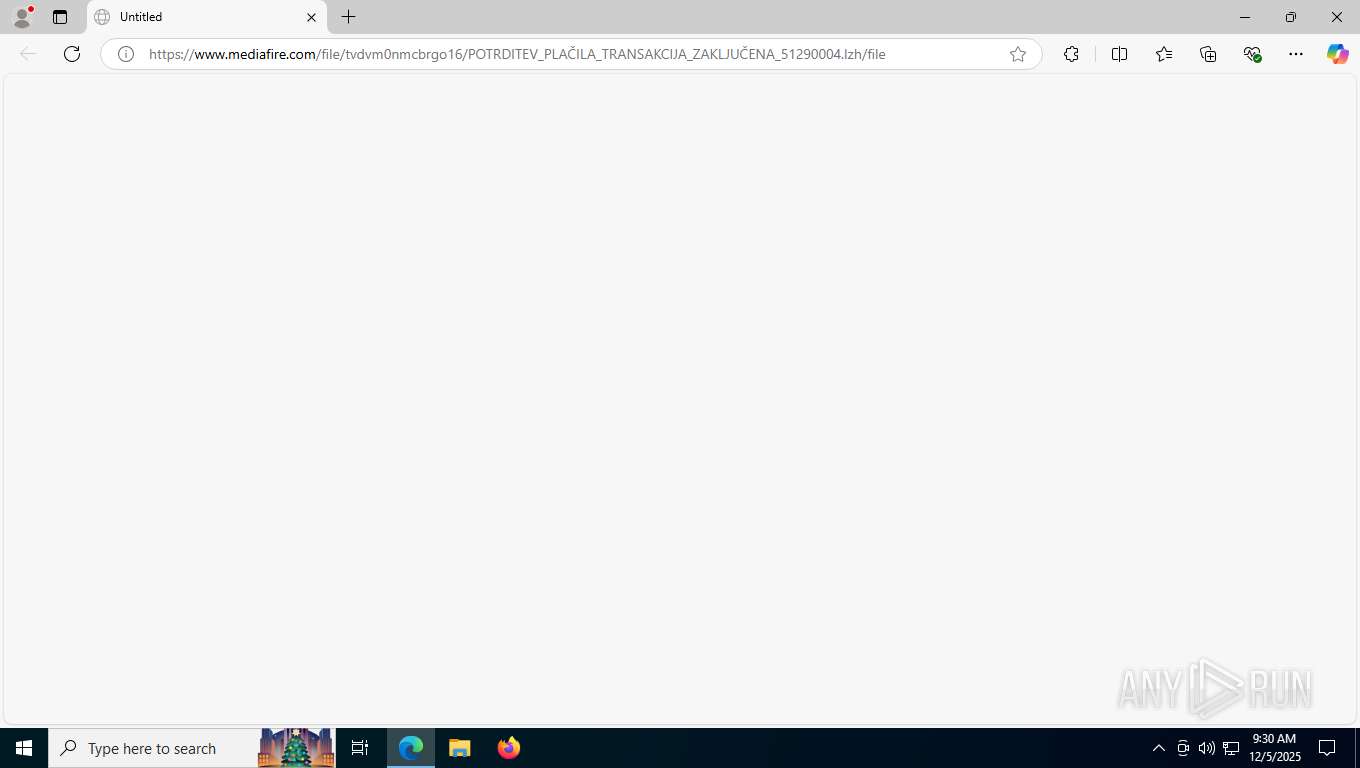
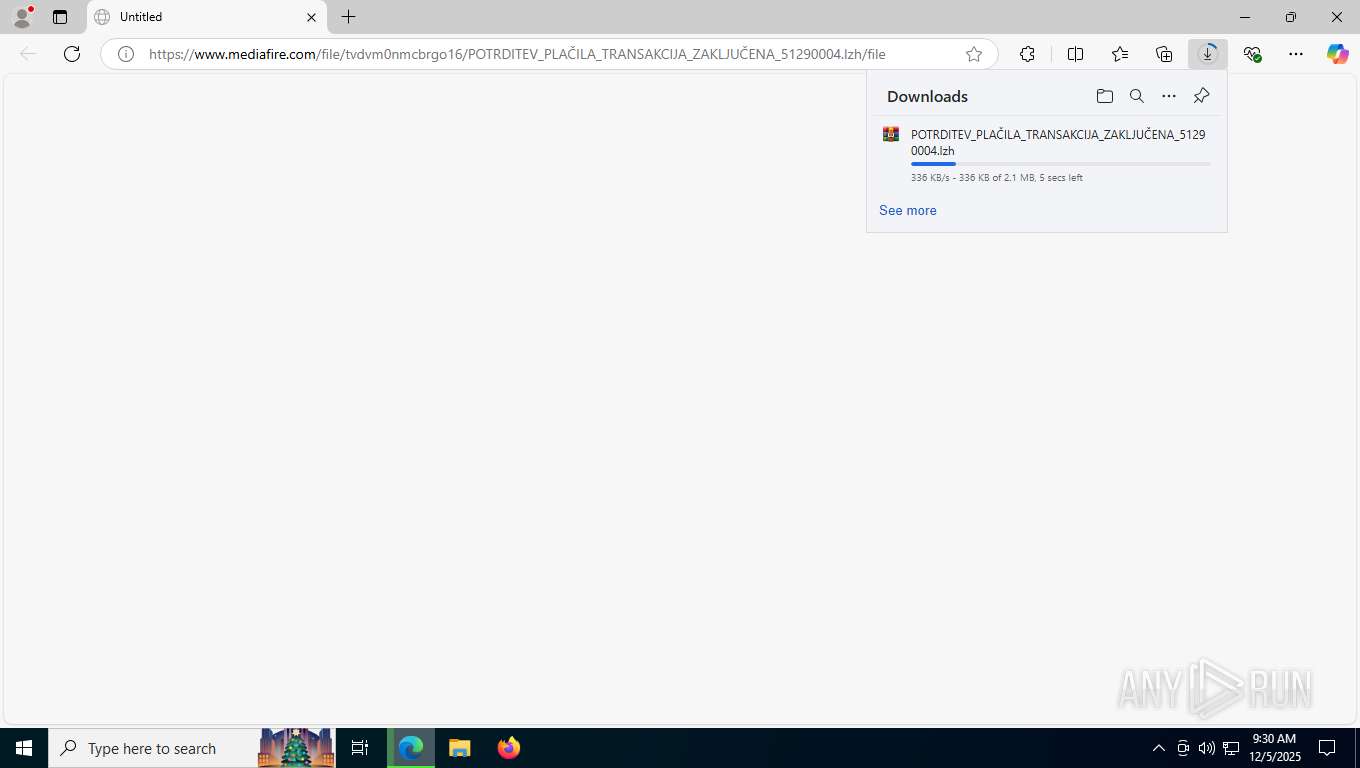
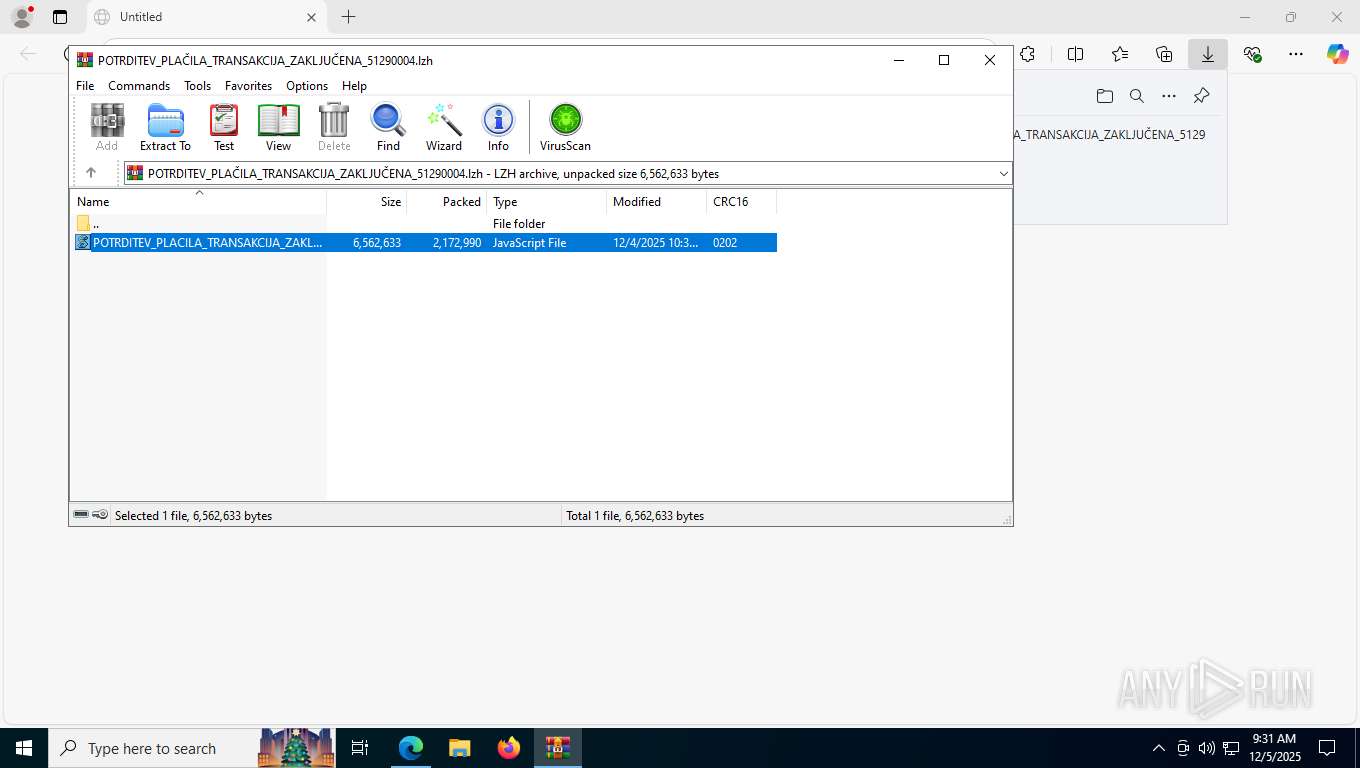
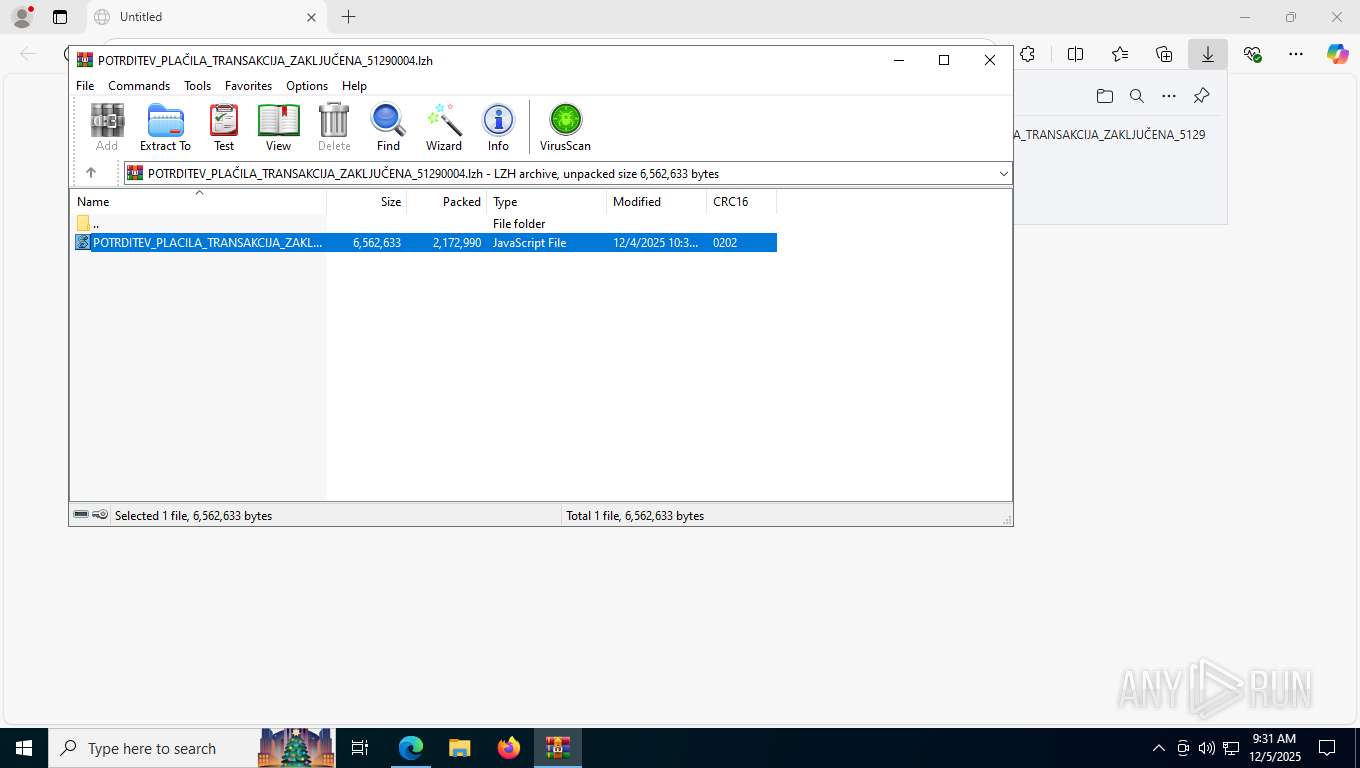
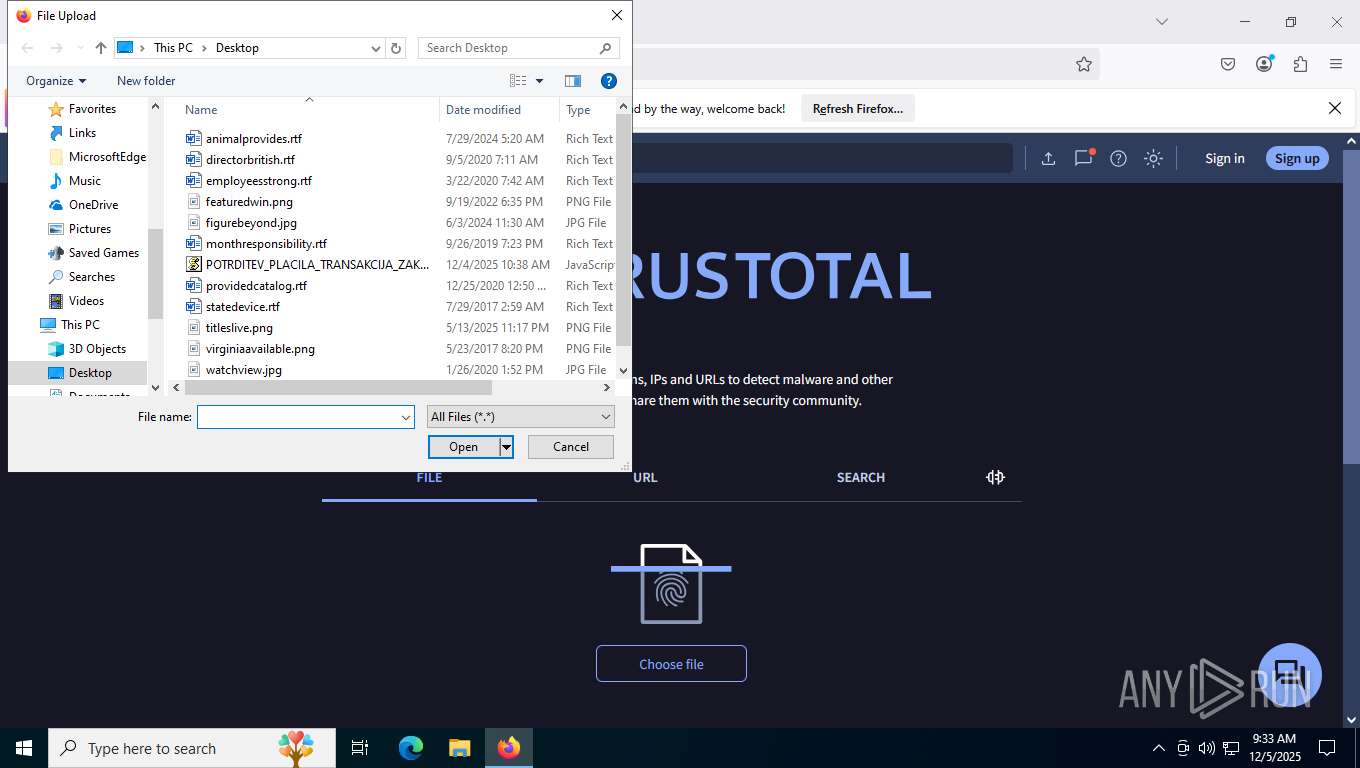
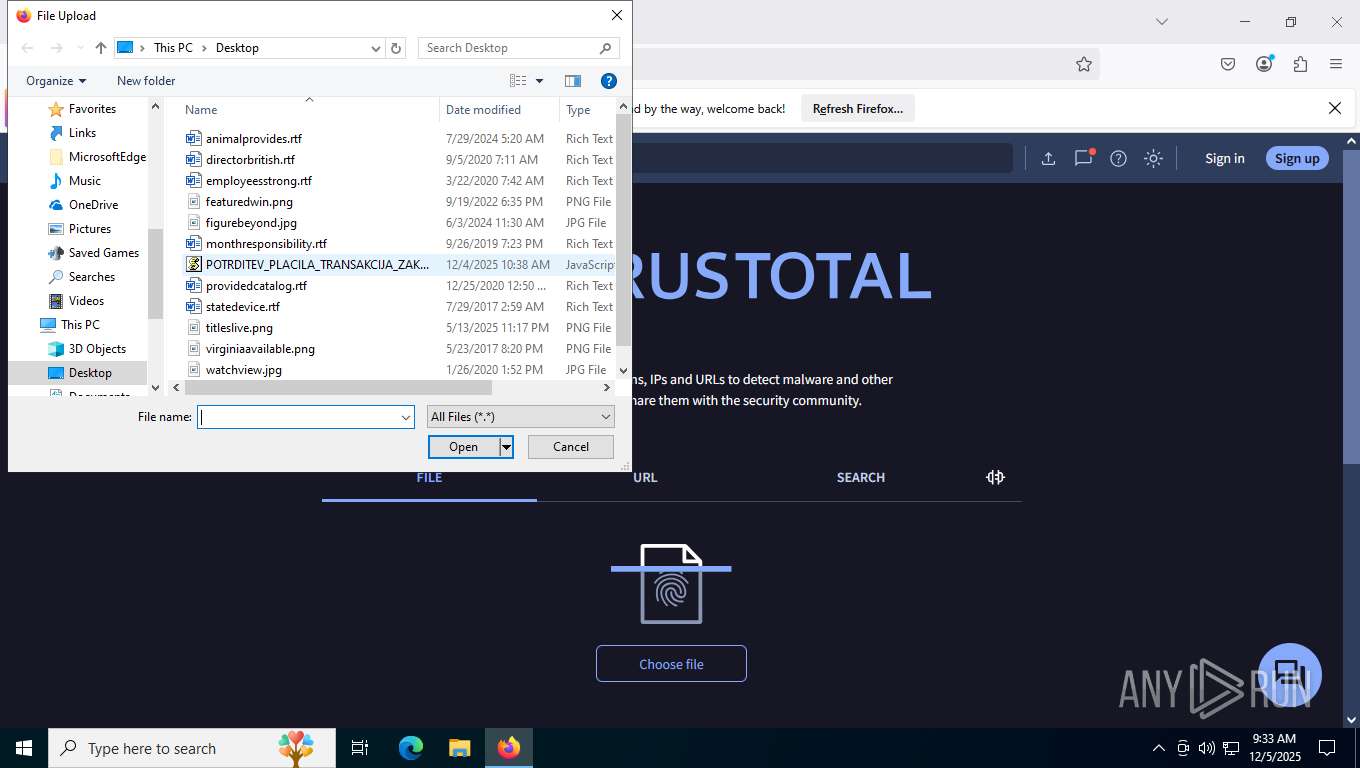
| URL: | https://www.mediafire.com/file/tvdvm0nmcbrgo16/POTRDITEV_PLA%C4%8CILA_TRANSAKCIJA_ZAKLJU%C4%8CENA_51290004.lzh/file |
| Full analysis: | https://app.any.run/tasks/0f7c1244-a863-4607-9e9c-8025c629c011 |
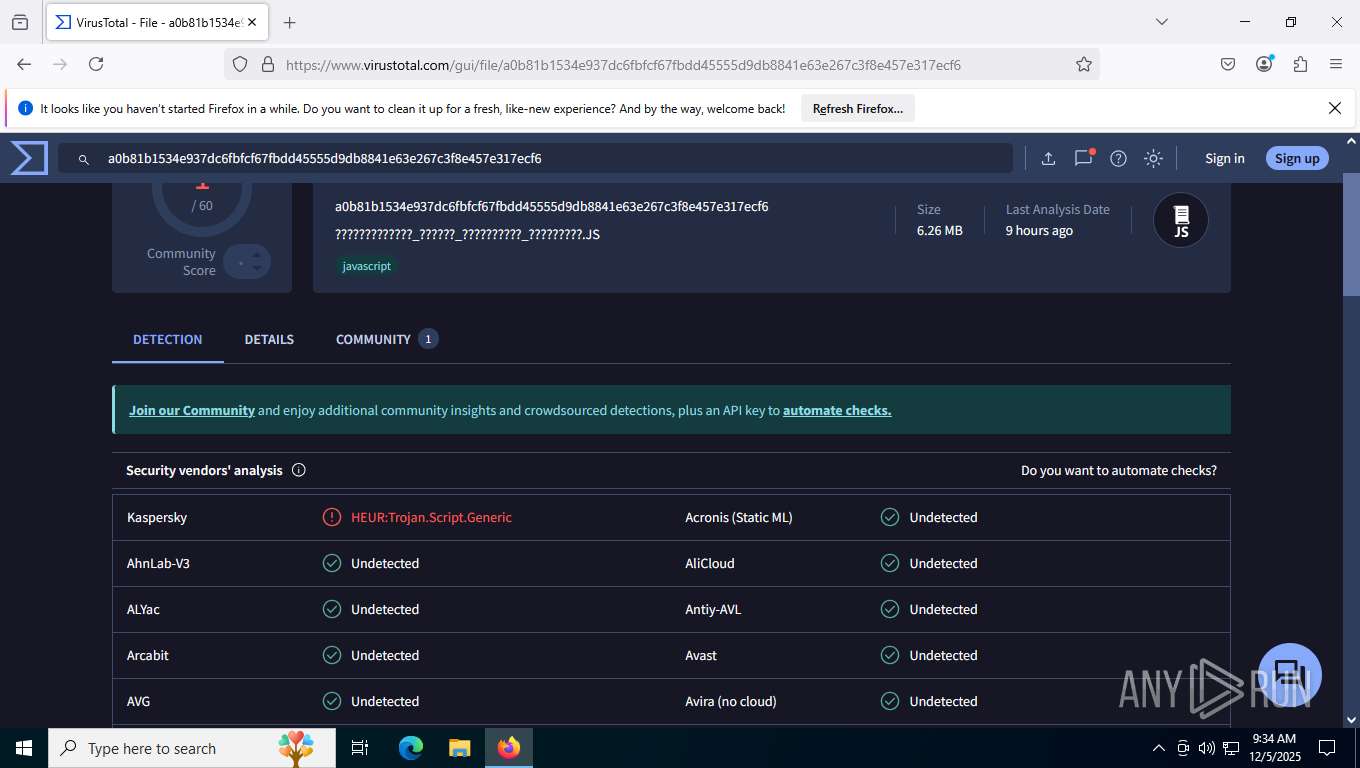
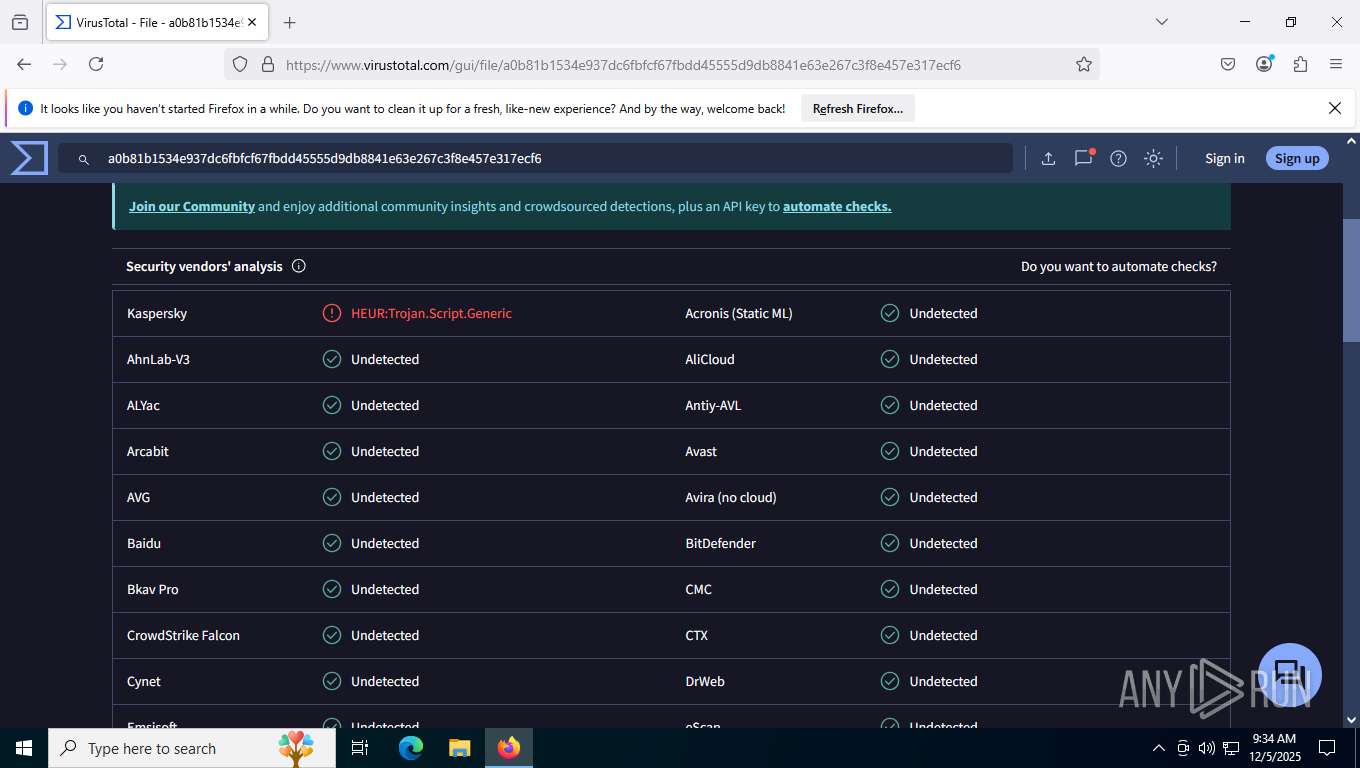
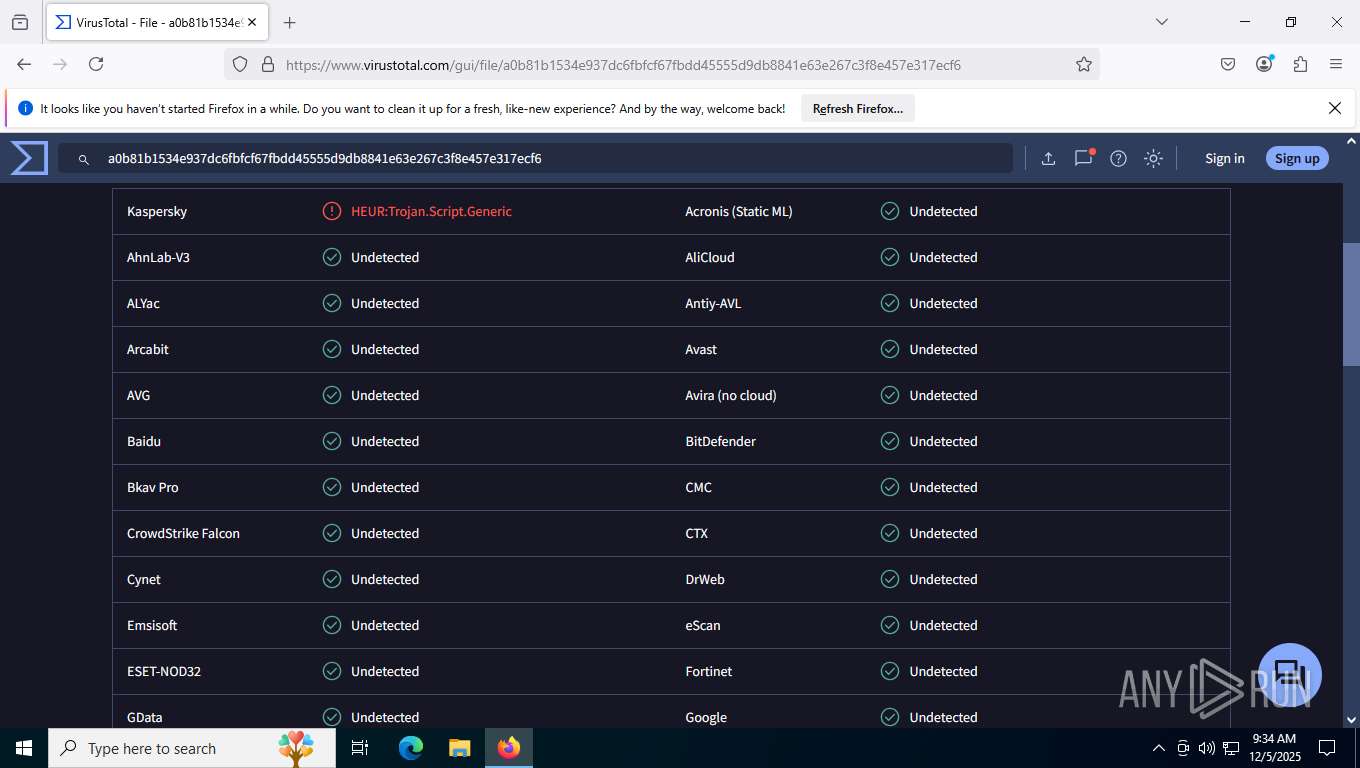
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
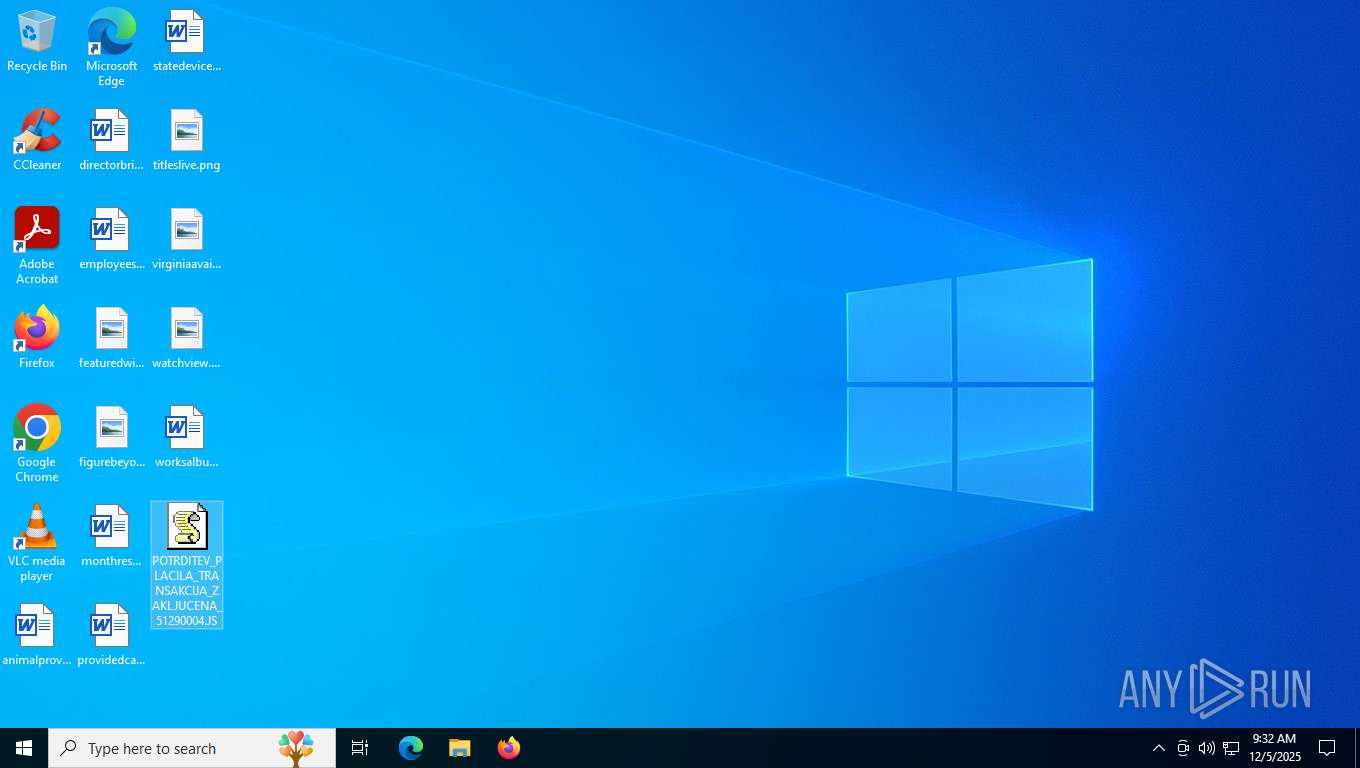
| Analysis date: | December 05, 2025, 09:30:49 |
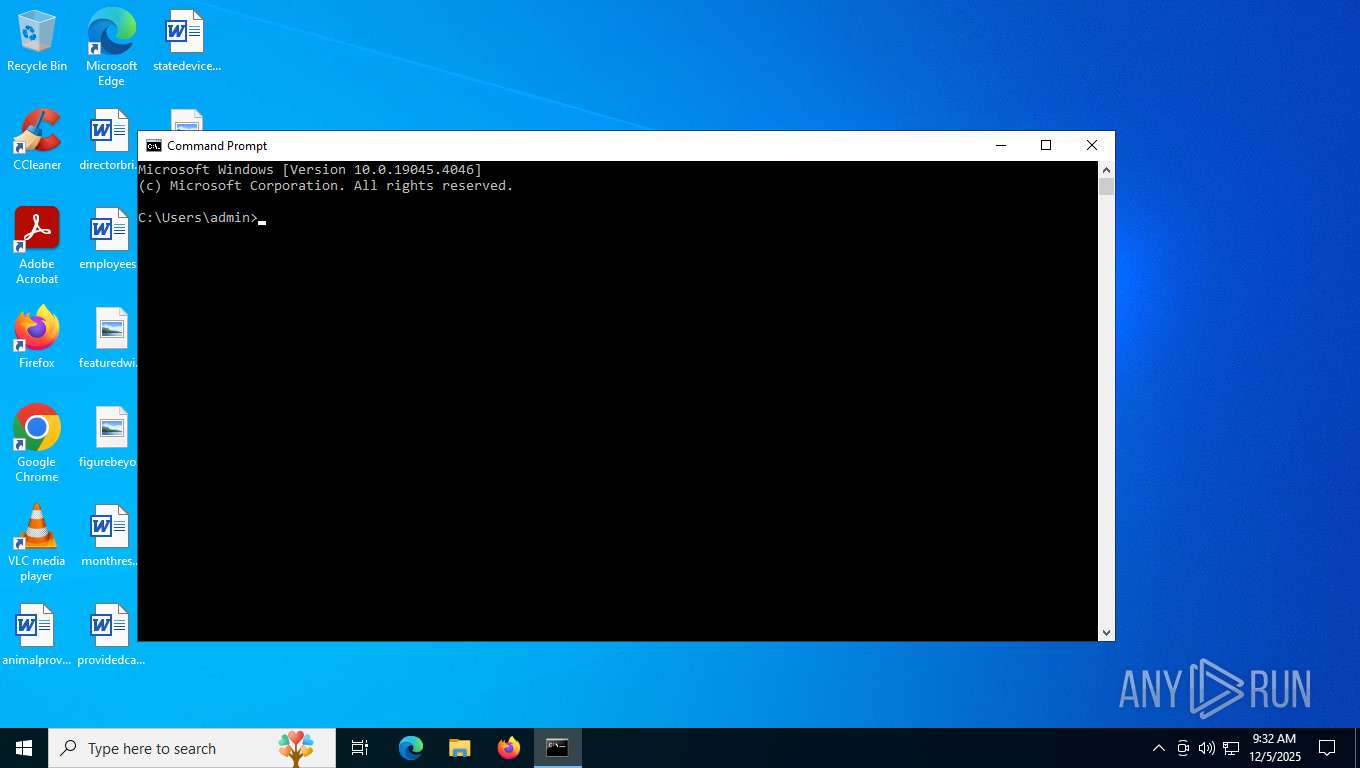
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
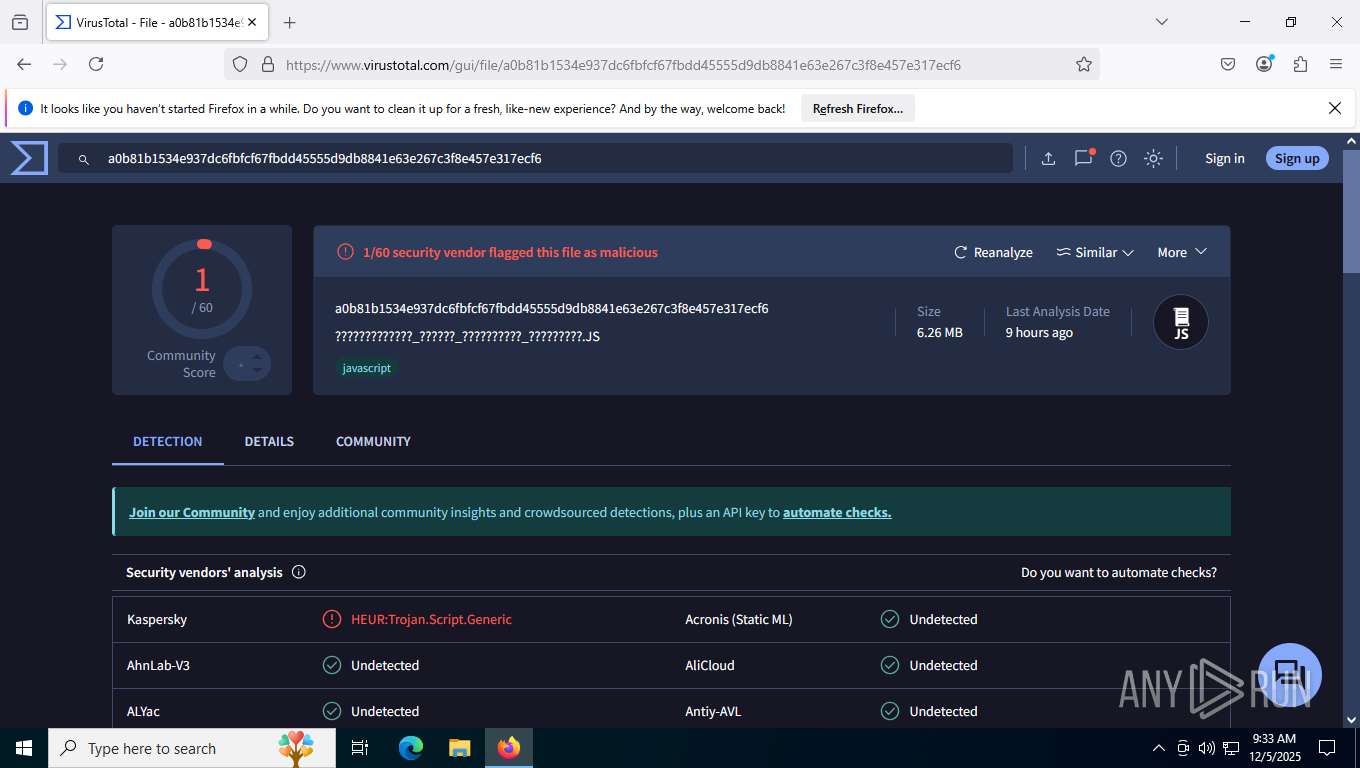
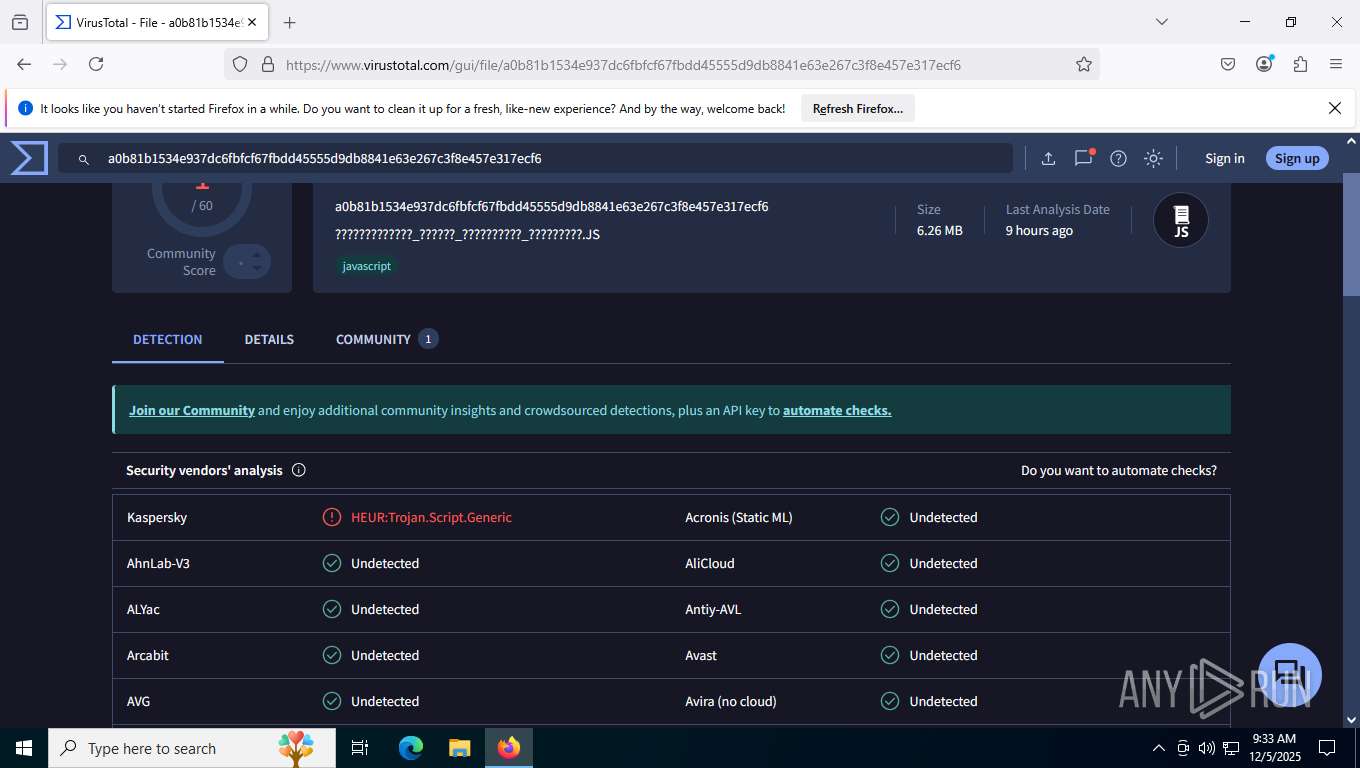
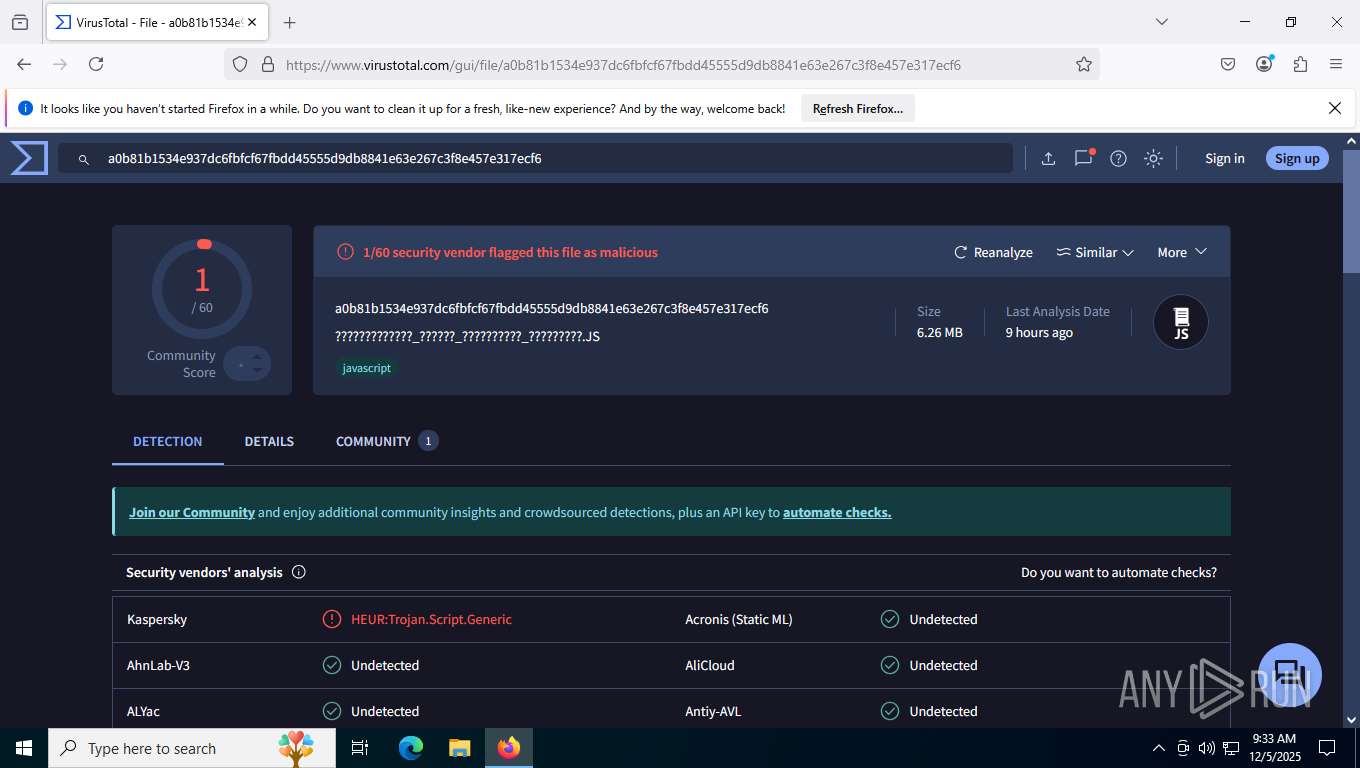
| MD5: | CD3715B6C5A1A767A2D27BE243CF295E |
| SHA1: | E66B47385C49FA1FE4AF788D2A4DE2E8A66CDD9D |
| SHA256: | AA9F9D32DF8215063D4553F3F92B061566A713AED41BF97C278A129A566FA330 |
| SSDEEP: | 3:N8DSLw3eGUo+3JUTuqxRsxgzeKA3kEx5vzGAt/OVPrhO:2OLw3eGeJUiKKmyKSPvzXt/OVP9O |
MALICIOUS
Uses base64 encoding (SCRIPT)
- wscript.exe (PID: 8552)
Detects the decoding of a binary file from Base64 (SCRIPT)
- wscript.exe (PID: 8552)
REMCOS has been detected
- colorcpl.exe (PID: 8808)
REMCOS mutex has been found
- colorcpl.exe (PID: 8808)
REMCOS has been detected (SURICATA)
- colorcpl.exe (PID: 8808)
REMCOS has been detected (YARA)
- colorcpl.exe (PID: 8808)
SUSPICIOUS
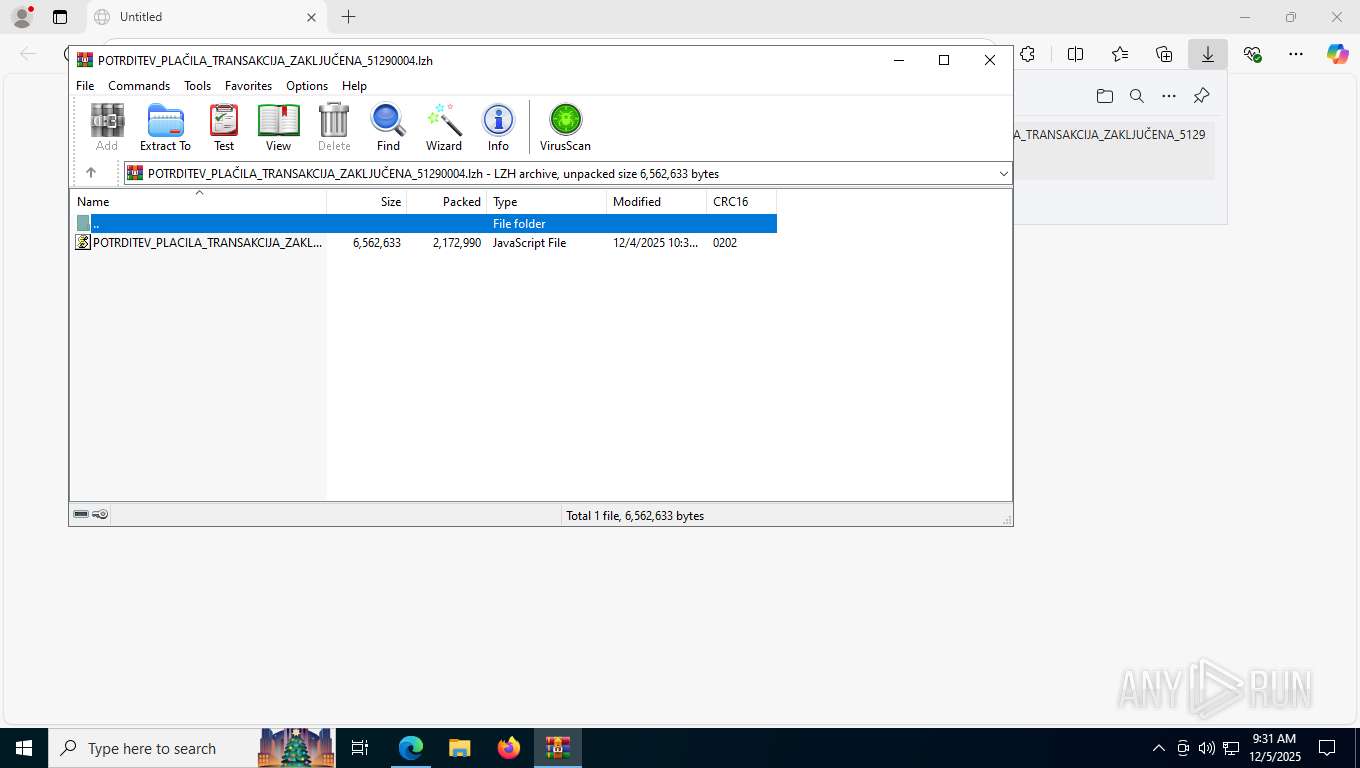
The process executes JS scripts
- WinRAR.exe (PID: 8496)
Gets name of the script (SCRIPT)
- wscript.exe (PID: 8552)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 8552)
- wscript.exe (PID: 8276)
- wscript.exe (PID: 3332)
- wscript.exe (PID: 8376)
- wscript.exe (PID: 8740)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8496)
Script creates XML DOM node (SCRIPT)
- wscript.exe (PID: 8552)
Creates XML DOM element (SCRIPT)
- wscript.exe (PID: 8552)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 8552)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 8552)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 8552)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 8552)
Executable content was dropped or overwritten
- wscript.exe (PID: 8552)
Likely accesses (executes) a file from the Public directory
- AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe (PID: 8784)
- AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe (PID: 8316)
- AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe (PID: 408)
- AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe (PID: 8432)
- AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe (PID: 8596)
Starts the AutoIt3 executable file
- wscript.exe (PID: 8552)
- wscript.exe (PID: 8276)
- wscript.exe (PID: 3332)
- wscript.exe (PID: 8376)
- wscript.exe (PID: 8740)
There is functionality for taking screenshot (YARA)
- colorcpl.exe (PID: 8808)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8552)
- wscript.exe (PID: 8276)
- wscript.exe (PID: 3332)
- wscript.exe (PID: 8376)
- wscript.exe (PID: 8740)
Connects to unusual port
- colorcpl.exe (PID: 8808)
Contacting a server suspected of hosting an CnC
- colorcpl.exe (PID: 8808)
INFO
Application launched itself
- msedge.exe (PID: 7520)
- firefox.exe (PID: 8648)
- firefox.exe (PID: 5408)
Reads Environment values
- identity_helper.exe (PID: 7280)
Reads the computer name
- identity_helper.exe (PID: 7280)
- TextInputHost.exe (PID: 9048)
Checks supported languages
- identity_helper.exe (PID: 7280)
- AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe (PID: 8784)
- AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe (PID: 8316)
- AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe (PID: 8432)
- AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe (PID: 408)
- AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe (PID: 8596)
- TextInputHost.exe (PID: 9048)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 8496)
The sample compiled with english language support
- wscript.exe (PID: 8552)
- firefox.exe (PID: 8648)
Reads mouse settings
- AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe (PID: 8784)
- AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe (PID: 8316)
- AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe (PID: 408)
- AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe (PID: 8432)
- AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe (PID: 8596)
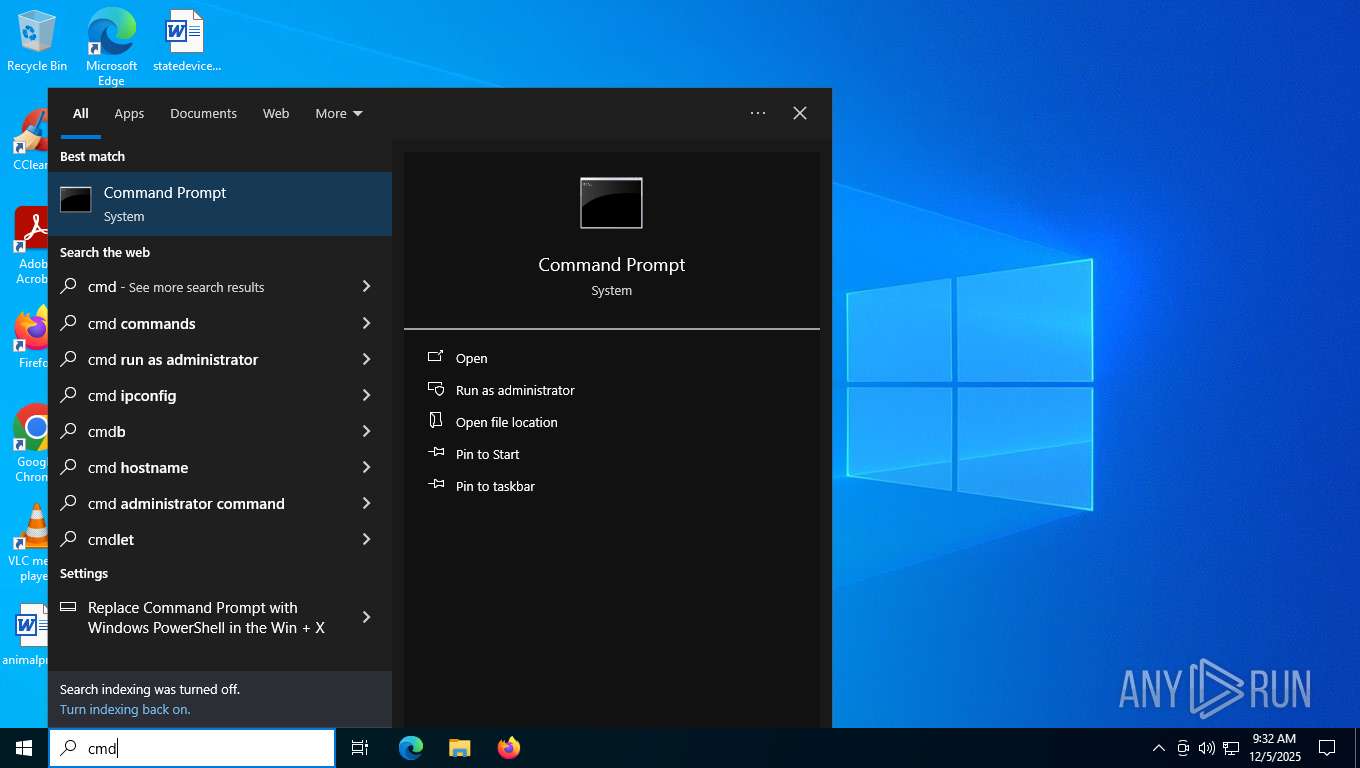
Manual execution by a user
- wscript.exe (PID: 8276)
- wscript.exe (PID: 3332)
- wscript.exe (PID: 8376)
- wscript.exe (PID: 8740)
- cmd.exe (PID: 8280)
- firefox.exe (PID: 5408)
Checks proxy server information
- slui.exe (PID: 3136)
Executable content was dropped or overwritten
- firefox.exe (PID: 8648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Remcos
(PID) Process(8808) colorcpl.exe
C2 (3)manymandyills.duckdns.org:9301
vuloinsioscollid.duckdns.org:9301
tallymostfavor.duckdns.org:9301
BotnetDEC - RemoteHost
Options
Connect_interval1
Install_flagFalse
Install_HKCU\RunTrue
Install_HKLM\RunTrue
Install_HKLM\Explorer\Run1
Install_HKLM\Winlogon\Shell100000
Setup_path%LOCALAPPDATA%
Copy_fileremcos.exe
Startup_valueFalse
Hide_fileFalse
Mutex_nameRmc-SNJQTR
Keylog_flag0
Keylog_path%LOCALAPPDATA%
Keylog_filelogs.dat
Keylog_cryptFalse
Hide_keylogFalse
Screenshot_flagFalse
Screenshot_time5
Take_ScreenshotFalse
Screenshot_path%APPDATA%
Screenshot_fileScreenshots
Screenshot_cryptFalse
Mouse_optionFalse
Delete_fileFalse
Audio_record_time5
Audio_path1
Audio_dirMicRecords
Connect_delay0
Copy_dirRemcos
Keylog_dirremcos
Total processes
213
Monitored processes
63
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | "C:\Users\Public\Libraries\AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe" C:\Users\Public\Libraries\AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.png | C:\Users\Public\Libraries\AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe | — | wscript.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 16, 1 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 2648 -prefsLen 39120 -prefMapHandle 5064 -prefMapSize 273045 -jsInitHandle 5088 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5104 -initialChannelId {30fa52ad-1243-47da-8fee-489a0b0ebf54} -parentPid 8648 -crashReporter "\\.\pipe\gecko-crash-server-pipe.8648" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 7 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -prefsHandle 2240 -prefsLen 36580 -prefMapHandle 2244 -prefMapSize 273045 -ipcHandle 2252 -initialChannelId {381540ad-d09a-4ab8-91e4-a90f7a258a3d} -parentPid 8648 -crashReporter "\\.\pipe\gecko-crash-server-pipe.8648" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 2 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1956 | C:\Windows\Syswow64\colorcpl.exe | C:\Windows\SysWOW64\colorcpl.exe | — | AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Color Control Panel Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3132 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -prefsHandle 3428 -prefsLen 37056 -prefMapHandle 3432 -prefMapSize 273045 -ipcHandle 3296 -initialChannelId {2345ef25-0188-45d5-9275-bb175d5a460c} -parentPid 8648 -crashReporter "\\.\pipe\gecko-crash-server-pipe.8648" -appDir "C:\Program Files\Mozilla Firefox\browser" - 4 rdd | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 3136 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3332 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\POTRDITEV_PLACILA_TRANSAKCIJA_ZAKLJUCENA_51290004.JS" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 3700 | C:\Windows\Syswow64\colorcpl.exe | C:\Windows\SysWOW64\colorcpl.exe | — | AHRFETJEWZNGETQUHSMBVJYBBUZZXSJHCFIVIBATKFYFJUWDOSUPATK.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Color Control Panel Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5724,i,17240342232478815404,9913614238730670578,262144 --variations-seed-version --mojo-platform-channel-handle=5860 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
9 670
Read events
9 629
Write events
28
Delete events
13
Modification events
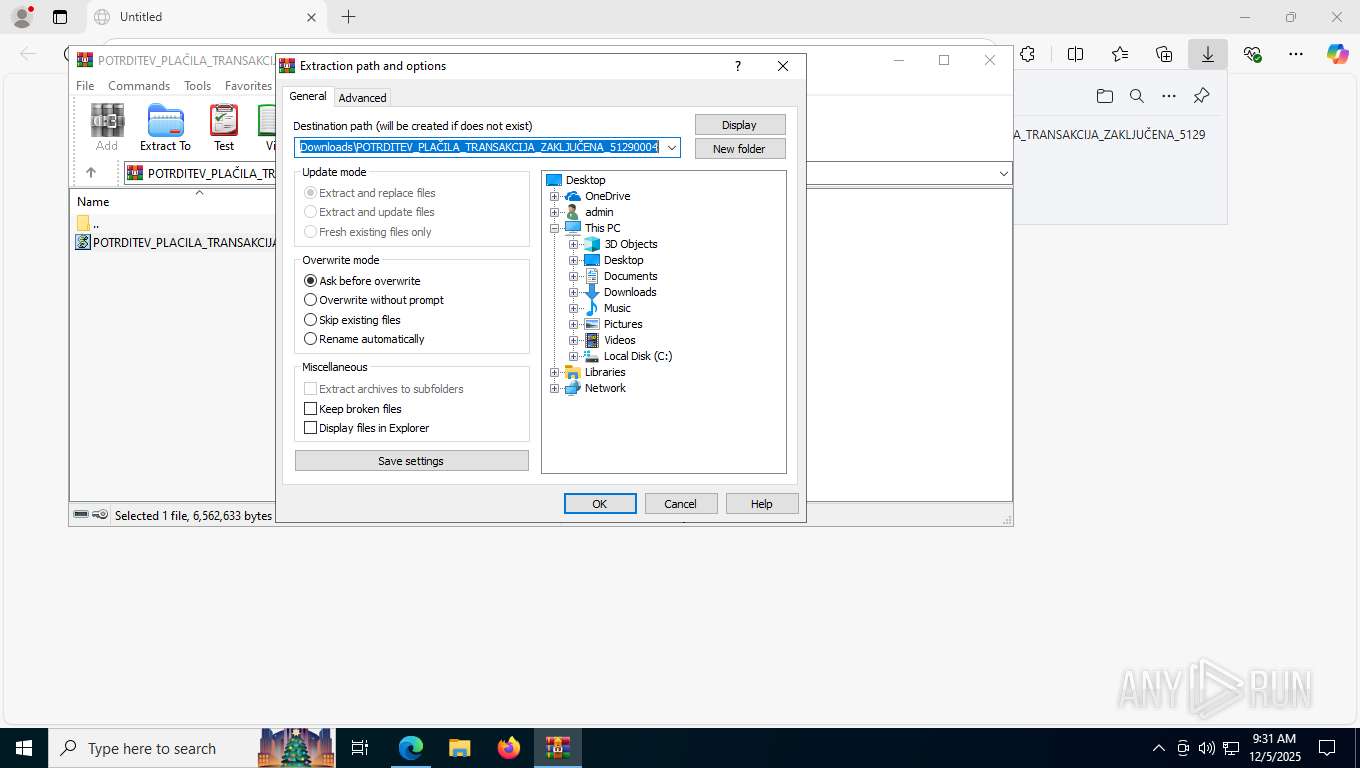
| (PID) Process: | (8496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\POTRDITEV_PLAČILA_TRANSAKCIJA_ZAKLJUČENA_51290004.lzh | |||
| (PID) Process: | (8496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8496) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.js\OpenWithProgids |
| Operation: | write | Name: | JSFile |
Value: | |||
| (PID) Process: | (8552) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 0BB30F0000000000 | |||
Executable files
36
Suspicious files
695
Text files
131
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFf6f7a.TMP | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFf6f89.TMP | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFf6f89.TMP | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFf6f99.TMP | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFf6fa9.TMP | — | |
MD5:— | SHA256:— | |||
| 7520 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
154
DNS requests
206
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7860 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:zaV_MkWg4kRkoofKOugqqxe6lVwYVyxg11RqiVabvEc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
4576 | svchost.exe | GET | 200 | 2.16.164.66:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5888 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4576 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8920 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8920 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8920 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
8920 | SIHClient.exe | GET | 200 | 2.16.164.130:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
8920 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
8920 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2484 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4576 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 23.3.88.185:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7860 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7860 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7860 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7860 | msedge.exe | 104.17.147.83:443 | www.mediafire.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.mediafire.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
download2388.mediafire.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7860 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
7860 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7860 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7860 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
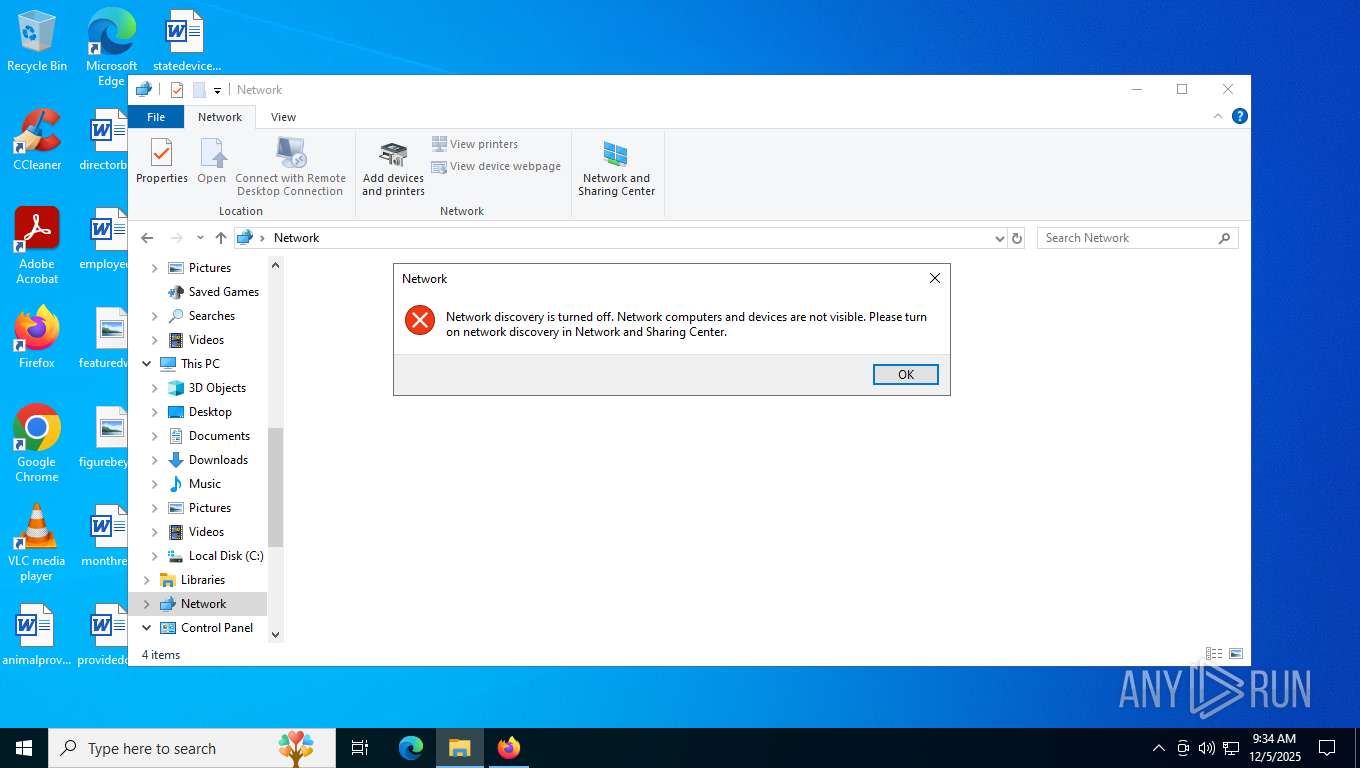
2292 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2292 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2292 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2292 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
8808 | colorcpl.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS TLS Connection JA3 Hash |