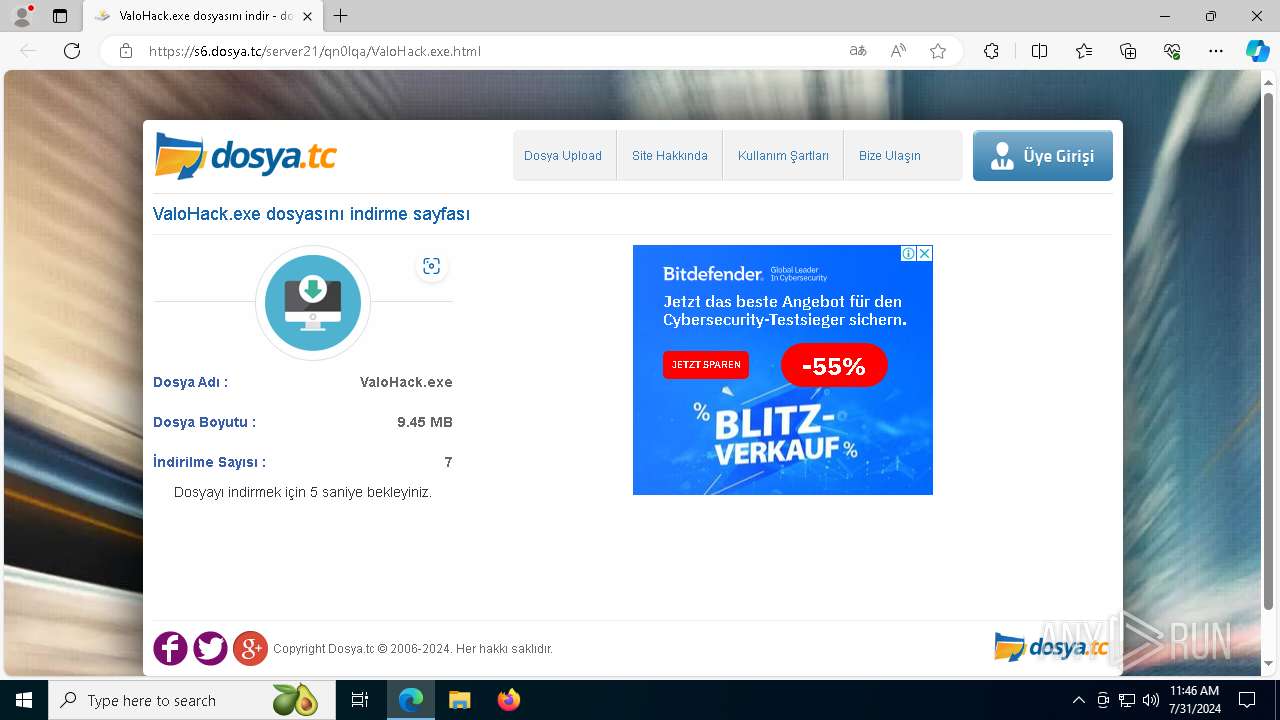
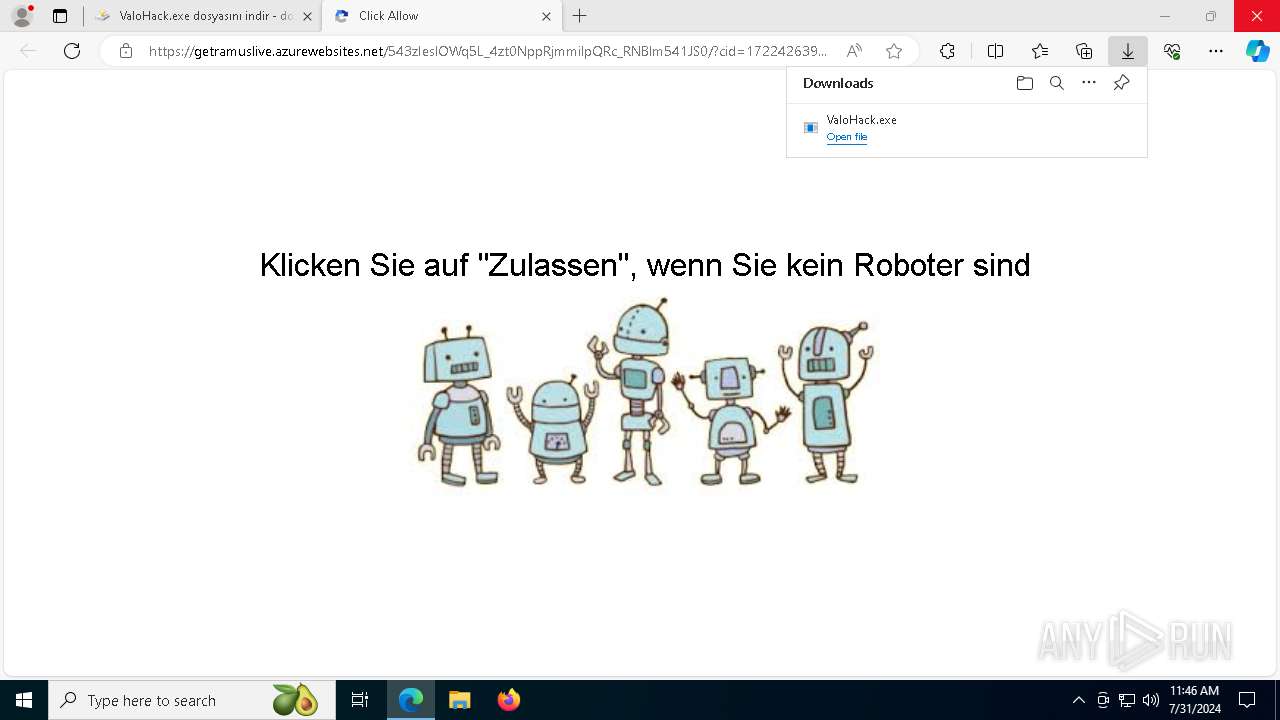
| URL: | https://s6.dosya.tc/server21/qn0lqa/ValoHack.exe.html |
| Full analysis: | https://app.any.run/tasks/8d1fc2ea-73ce-4443-8bc4-b8bf7edc28ca |
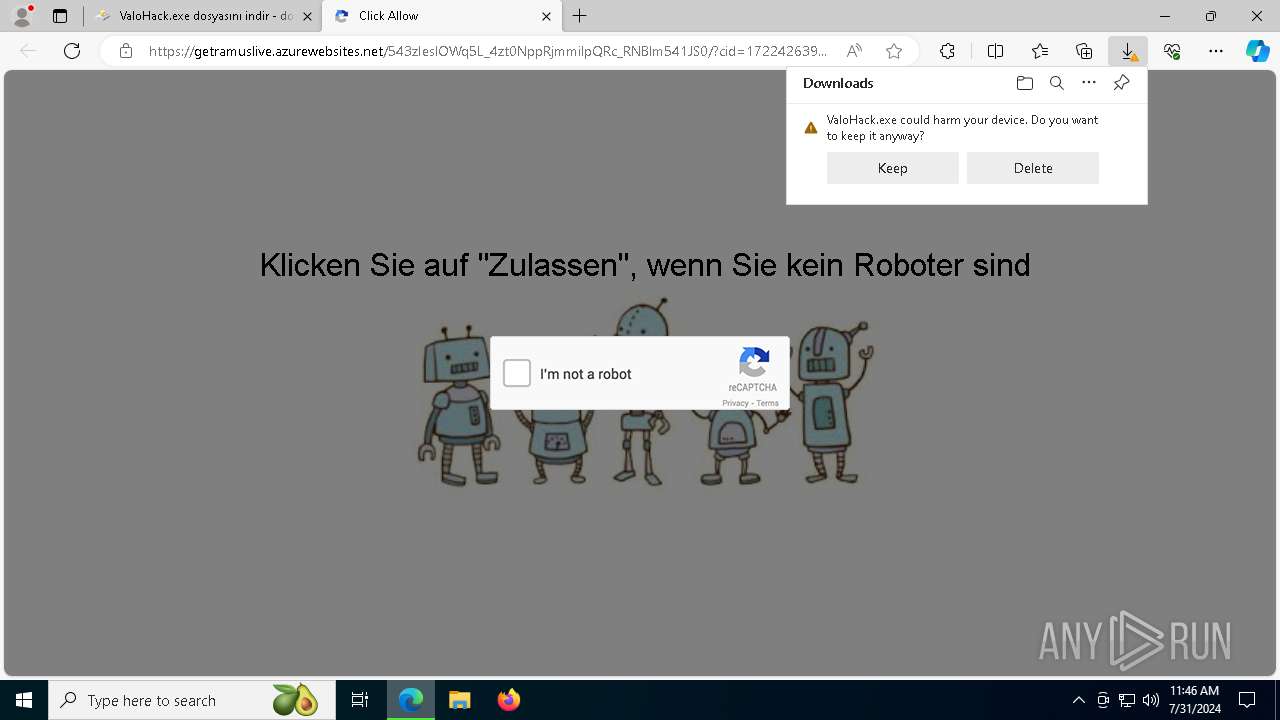
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | July 31, 2024, 11:46:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 35C07708999EFD2A050A61A9F67F72DB |
| SHA1: | E39F20EF327AC9623862AE140E3E24062EFF3C64 |
| SHA256: | AA4C1CCAF993960E692577F58D3BA4473F8CEA89CFB74142F320D737E63942F7 |
| SSDEEP: | 3:N8UHcVLXWVJLJ5G:2UHGLCw |
MALICIOUS
Drops the executable file immediately after the start
- ValoHack.exe (PID: 7872)
- Built.exe (PID: 6788)
- Builtt.exe (PID: 2088)
- Built.exe (PID: 7852)
BlankGrabber has been detected
- Built.exe (PID: 6788)
- Built.exe (PID: 7852)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 6620)
- MpCmdRun.exe (PID: 6736)
- cmd.exe (PID: 6156)
- MpCmdRun.exe (PID: 8160)
Adds path to the Windows Defender exclusion list
- Built.exe (PID: 6516)
- cmd.exe (PID: 6604)
- Built.exe (PID: 6760)
- cmd.exe (PID: 7880)
Windows Defender preferences modified via 'Set-MpPreference'
- cmd.exe (PID: 6620)
- cmd.exe (PID: 6156)
Adds extension to the Windows Defender exclusion list
- Builtt.exe (PID: 2088)
- elnugpigmxmh.exe (PID: 6952)
- Builtt.exe (PID: 6044)
- elnugpigmxmh.exe (PID: 7092)
SUSPICIOUS
Reads security settings of Internet Explorer
- ValoHack.exe (PID: 7872)
- ValoHack.exe (PID: 1692)
Reads the date of Windows installation
- ValoHack.exe (PID: 7872)
- ValoHack.exe (PID: 1692)
BASE64 encoded PowerShell command has been detected
- ValoHack.exe (PID: 7872)
- ValoHack.exe (PID: 1692)
Starts POWERSHELL.EXE for commands execution
- ValoHack.exe (PID: 7872)
- cmd.exe (PID: 6620)
- cmd.exe (PID: 6604)
- Builtt.exe (PID: 2088)
- elnugpigmxmh.exe (PID: 6952)
- ValoHack.exe (PID: 1692)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 7880)
- Builtt.exe (PID: 6044)
- elnugpigmxmh.exe (PID: 7092)
Process drops legitimate windows executable
- ValoHack.exe (PID: 7872)
- Built.exe (PID: 6788)
- Built.exe (PID: 7852)
Base64-obfuscated command line is found
- ValoHack.exe (PID: 7872)
- ValoHack.exe (PID: 1692)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 6928)
Executable content was dropped or overwritten
- ValoHack.exe (PID: 7872)
- Built.exe (PID: 6788)
- Builtt.exe (PID: 2088)
- Built.exe (PID: 7852)
The process drops C-runtime libraries
- Built.exe (PID: 6788)
- Built.exe (PID: 7852)
Process drops python dynamic module
- Built.exe (PID: 6788)
- Built.exe (PID: 7852)
Starts a Microsoft application from unusual location
- Built.exe (PID: 6516)
- Built.exe (PID: 6788)
- Built.exe (PID: 7852)
- Built.exe (PID: 6760)
Application launched itself
- Built.exe (PID: 6788)
- Built.exe (PID: 7852)
Starts CMD.EXE for commands execution
- Built.exe (PID: 6516)
- Builtt.exe (PID: 2088)
- elnugpigmxmh.exe (PID: 6952)
- Built.exe (PID: 6760)
- Builtt.exe (PID: 6044)
- elnugpigmxmh.exe (PID: 7092)
Get information on the list of running processes
- Built.exe (PID: 6516)
- cmd.exe (PID: 6556)
- cmd.exe (PID: 7820)
- Built.exe (PID: 6760)
Loads Python modules
- Built.exe (PID: 6516)
- Built.exe (PID: 6760)
Found strings related to reading or modifying Windows Defender settings
- Built.exe (PID: 6516)
- Built.exe (PID: 6760)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 6620)
- cmd.exe (PID: 6156)
Script disables Windows Defender's IPS
- cmd.exe (PID: 6620)
- cmd.exe (PID: 6156)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6604)
- Builtt.exe (PID: 2088)
- elnugpigmxmh.exe (PID: 6952)
- cmd.exe (PID: 7880)
- Builtt.exe (PID: 6044)
- elnugpigmxmh.exe (PID: 7092)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6840)
- cmd.exe (PID: 6452)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 8152)
- WMIC.exe (PID: 7628)
Script adds exclusion extension to Windows Defender
- Builtt.exe (PID: 2088)
- elnugpigmxmh.exe (PID: 6952)
- Builtt.exe (PID: 6044)
- elnugpigmxmh.exe (PID: 7092)
Process uninstalls Windows update
- wusa.exe (PID: 3540)
- wusa.exe (PID: 8156)
- wusa.exe (PID: 232)
- wusa.exe (PID: 240)
Starts SC.EXE for service management
- Builtt.exe (PID: 2088)
- Builtt.exe (PID: 6044)
Executes as Windows Service
- elnugpigmxmh.exe (PID: 6952)
- elnugpigmxmh.exe (PID: 7092)
Checks for external IP
- svchost.exe (PID: 2256)
- Built.exe (PID: 6516)
- Built.exe (PID: 6760)
INFO
Checks supported languages
- identity_helper.exe (PID: 7600)
- identity_helper.exe (PID: 6484)
- identity_helper.exe (PID: 7328)
- ValoHack.exe (PID: 7872)
- Builtt.exe (PID: 2088)
- Built.exe (PID: 6516)
- MpCmdRun.exe (PID: 6736)
- elnugpigmxmh.exe (PID: 6952)
- ValoHack.exe (PID: 1692)
- Built.exe (PID: 6788)
- Built.exe (PID: 7852)
- Built.exe (PID: 6760)
- elnugpigmxmh.exe (PID: 7092)
- MpCmdRun.exe (PID: 8160)
- Builtt.exe (PID: 6044)
Application launched itself
- msedge.exe (PID: 6332)
- msedge.exe (PID: 3188)
Reads Environment values
- identity_helper.exe (PID: 7600)
- identity_helper.exe (PID: 6484)
- identity_helper.exe (PID: 7328)
Executable content was dropped or overwritten
- msedge.exe (PID: 6332)
- msedge.exe (PID: 6676)
Drops the executable file immediately after the start
- msedge.exe (PID: 6332)
- msedge.exe (PID: 6676)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6332)
- msedge.exe (PID: 3188)
The process uses the downloaded file
- msedge.exe (PID: 3864)
Reads the computer name
- identity_helper.exe (PID: 7600)
- identity_helper.exe (PID: 6484)
- identity_helper.exe (PID: 7328)
- ValoHack.exe (PID: 7872)
- Built.exe (PID: 6788)
- Built.exe (PID: 6516)
- MpCmdRun.exe (PID: 6736)
- ValoHack.exe (PID: 1692)
- Built.exe (PID: 7852)
- Built.exe (PID: 6760)
- MpCmdRun.exe (PID: 8160)
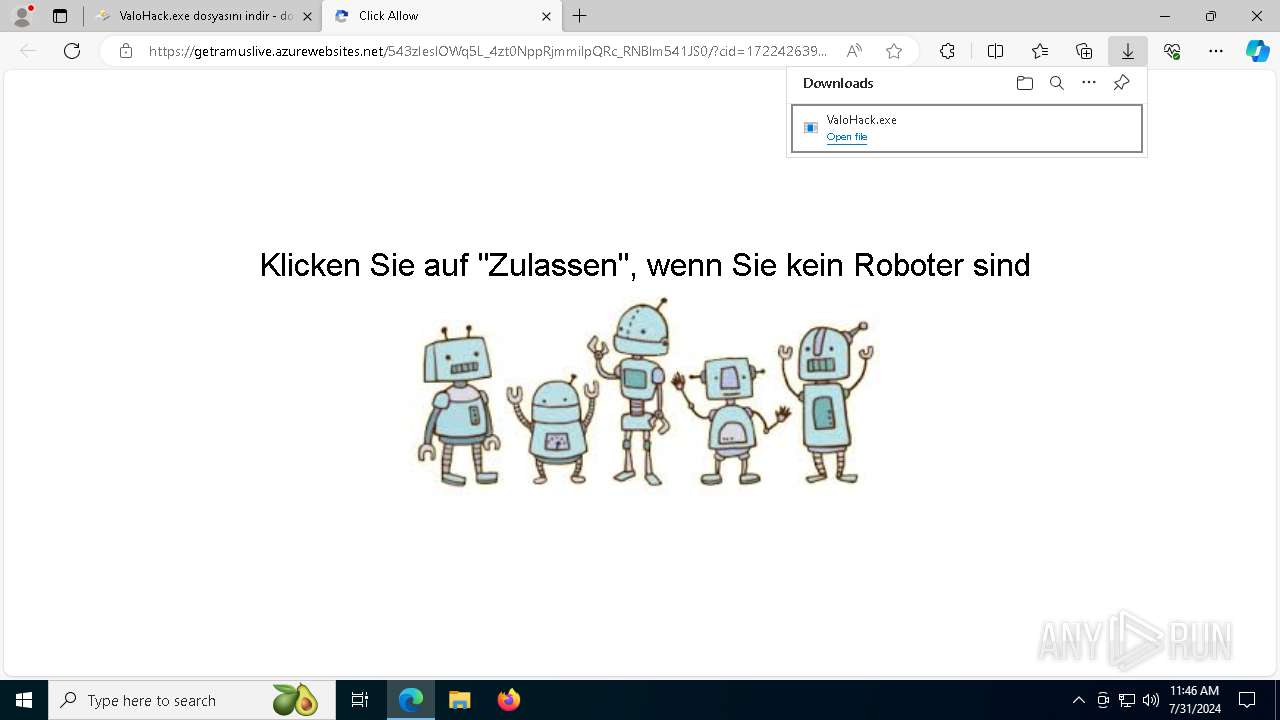
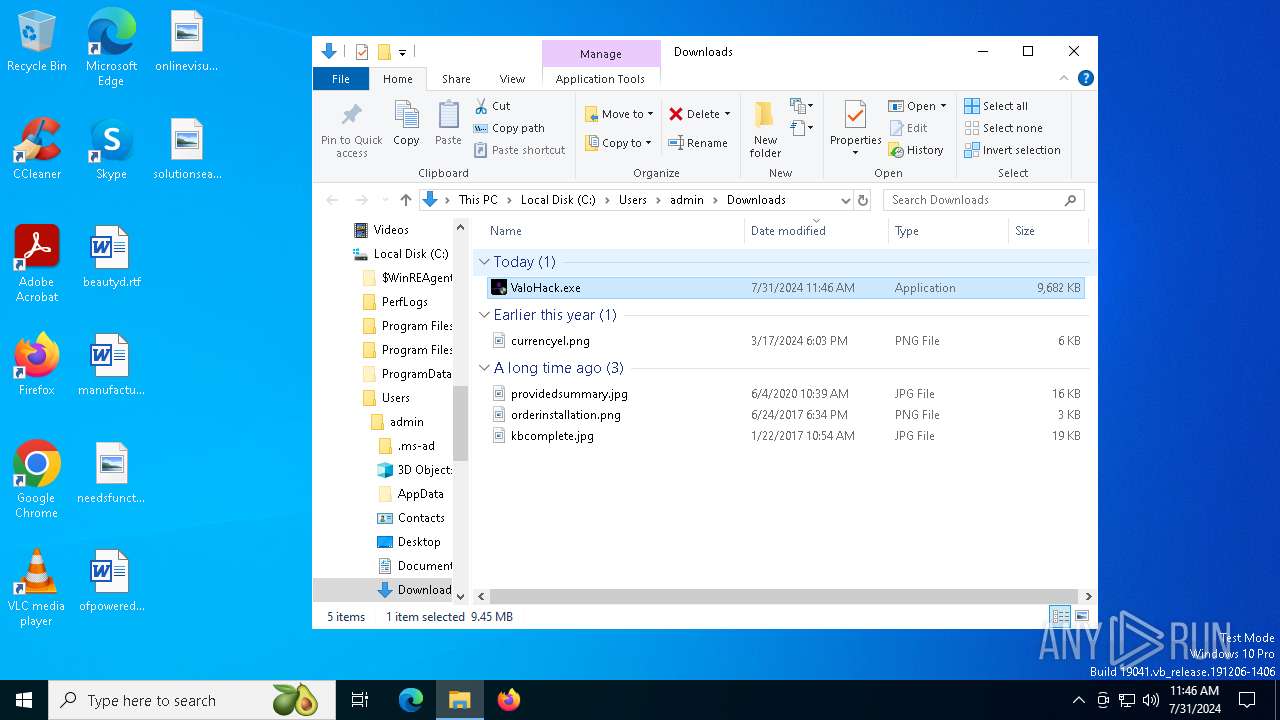
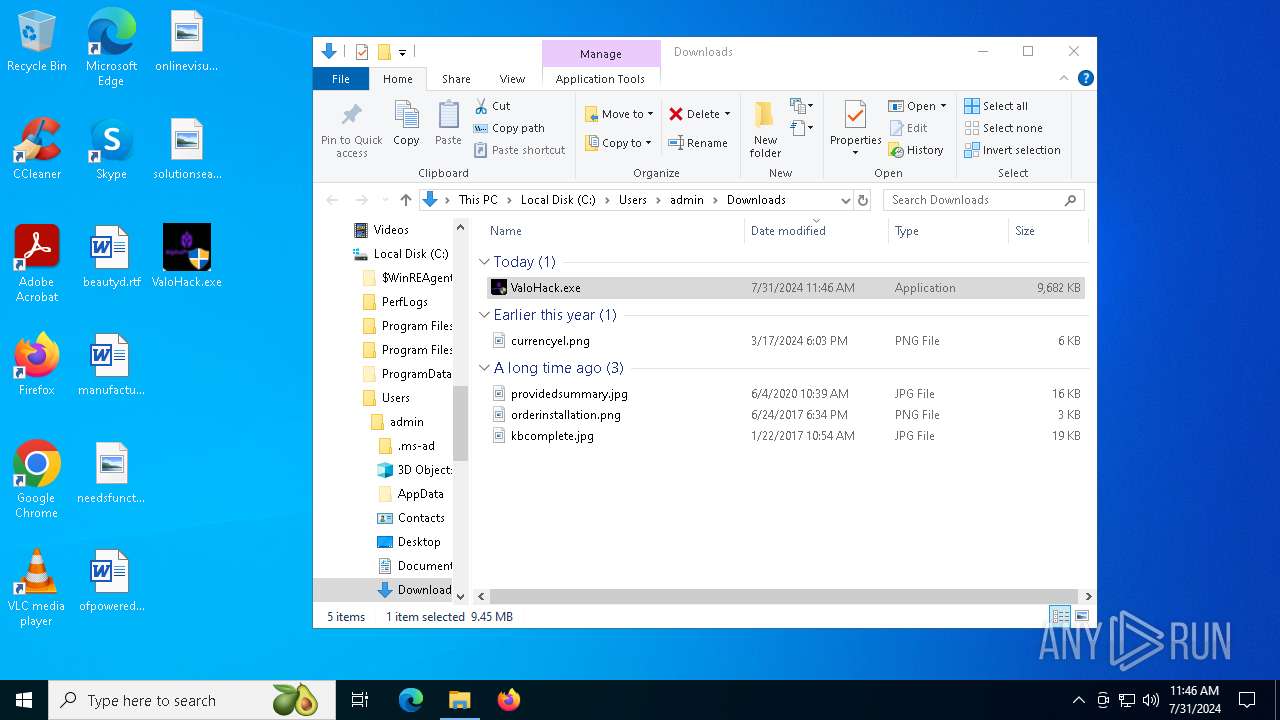
Manual execution by a user
- ValoHack.exe (PID: 7872)
- ValoHack.exe (PID: 7472)
- ValoHack.exe (PID: 6308)
- ValoHack.exe (PID: 1692)
Reads the machine GUID from the registry
- ValoHack.exe (PID: 7872)
- ValoHack.exe (PID: 1692)
Process checks computer location settings
- ValoHack.exe (PID: 7872)
- ValoHack.exe (PID: 1692)
Create files in a temporary directory
- Built.exe (PID: 6788)
- Built.exe (PID: 6516)
- MpCmdRun.exe (PID: 6736)
- ValoHack.exe (PID: 7872)
- ValoHack.exe (PID: 1692)
- Built.exe (PID: 6760)
- Built.exe (PID: 7852)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 8152)
- WMIC.exe (PID: 7628)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3508)
- powershell.exe (PID: 6928)
- powershell.exe (PID: 7484)
- powershell.exe (PID: 5300)
- powershell.exe (PID: 6820)
- powershell.exe (PID: 8164)
- powershell.exe (PID: 7040)
- powershell.exe (PID: 6164)
- powershell.exe (PID: 3672)
- powershell.exe (PID: 7336)
Creates files in the program directory
- Builtt.exe (PID: 2088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
289
Monitored processes
146
Malicious processes
13
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | wusa /uninstall /kb:890830 /quiet /norestart | C:\Windows\System32\wusa.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Standalone Installer Exit code: 87 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | wusa /uninstall /kb:890830 /quiet /norestart | C:\Windows\System32\wusa.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update Standalone Installer Exit code: 87 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1048 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --no-appcompat-clear --mojo-platform-channel-handle=8212 --field-trial-handle=2352,i,14304957855038711997,8453370653973488869,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=42 --mojo-platform-channel-handle=8824 --field-trial-handle=2352,i,14304957855038711997,8453370653973488869,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1452 | C:\WINDOWS\system32\sc.exe start "YNPHZKOJ" | C:\Windows\System32\sc.exe | — | Builtt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1053 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1692 | "C:\Users\admin\Desktop\ValoHack.exe" | C:\Users\admin\Desktop\ValoHack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1792 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5576 --field-trial-handle=2348,i,10708552049508807468,11595847199830928869,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1928 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5108 --field-trial-handle=2352,i,14304957855038711997,8453370653973488869,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1964 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1320 --field-trial-handle=2348,i,10708552049508807468,11595847199830928869,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2088 | "C:\Users\admin\AppData\Local\Temp\Builtt.exe" | C:\Users\admin\AppData\Local\Temp\Builtt.exe | ValoHack.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
87 971
Read events
87 845
Write events
124
Delete events
2
Modification events
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6332) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
45
Suspicious files
269
Text files
153
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe6492.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe64a1.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe64a1.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe64c0.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe64c0.TMP | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
138
DNS requests
159
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6676 | msedge.exe | GET | 304 | 184.24.77.69:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | unknown | — | — | malicious |
6676 | msedge.exe | GET | 304 | 69.192.161.44:80 | http://x1.i.lencr.org/ | unknown | — | — | whitelisted |
5484 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6676 | msedge.exe | GET | 304 | 69.192.161.44:80 | http://r3.i.lencr.org/ | unknown | — | — | whitelisted |
6300 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6324 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1640 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0b8df384-7776-4d34-92b7-bfc968353145?P1=1722993477&P2=404&P3=2&P4=WOWgg%2bW3oHCMLhT6Z%2bpZMPUFoHkc0gLoIv4FyQOznm6%2bU8CcPgLD1qe%2bVpLS0Lrea7hW12waskEWQ4zU1eDVpQ%3d%3d | unknown | — | — | whitelisted |
1640 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0b8df384-7776-4d34-92b7-bfc968353145?P1=1722993477&P2=404&P3=2&P4=WOWgg%2bW3oHCMLhT6Z%2bpZMPUFoHkc0gLoIv4FyQOznm6%2bU8CcPgLD1qe%2bVpLS0Lrea7hW12waskEWQ4zU1eDVpQ%3d%3d | unknown | — | — | whitelisted |
1640 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0b8df384-7776-4d34-92b7-bfc968353145?P1=1722993477&P2=404&P3=2&P4=WOWgg%2bW3oHCMLhT6Z%2bpZMPUFoHkc0gLoIv4FyQOznm6%2bU8CcPgLD1qe%2bVpLS0Lrea7hW12waskEWQ4zU1eDVpQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1184 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4708 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6332 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6676 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6676 | msedge.exe | 157.90.180.51:443 | s6.dosya.tc | Hetzner Online GmbH | DE | unknown |
6676 | msedge.exe | 142.250.186.34:443 | pagead2.googlesyndication.com | — | — | unknown |
6676 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
s6.dosya.tc |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6676 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6676 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2256 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
6516 | Built.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6760 | Built.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |