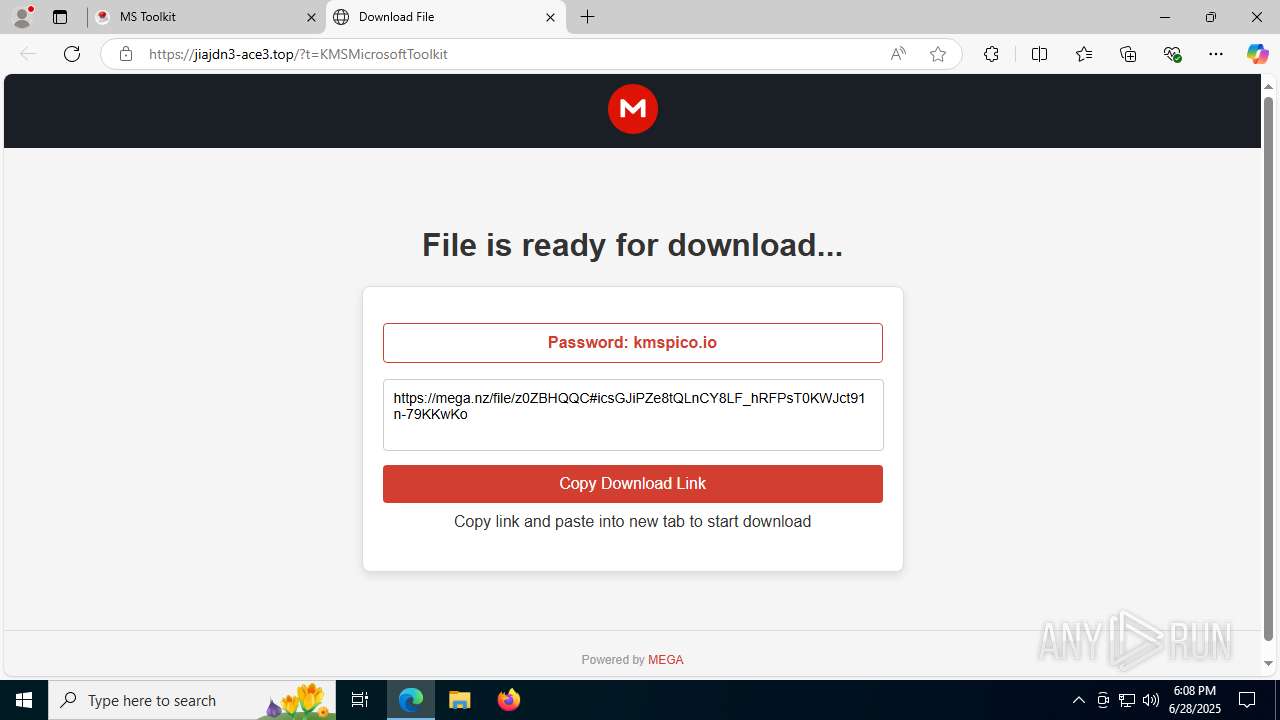
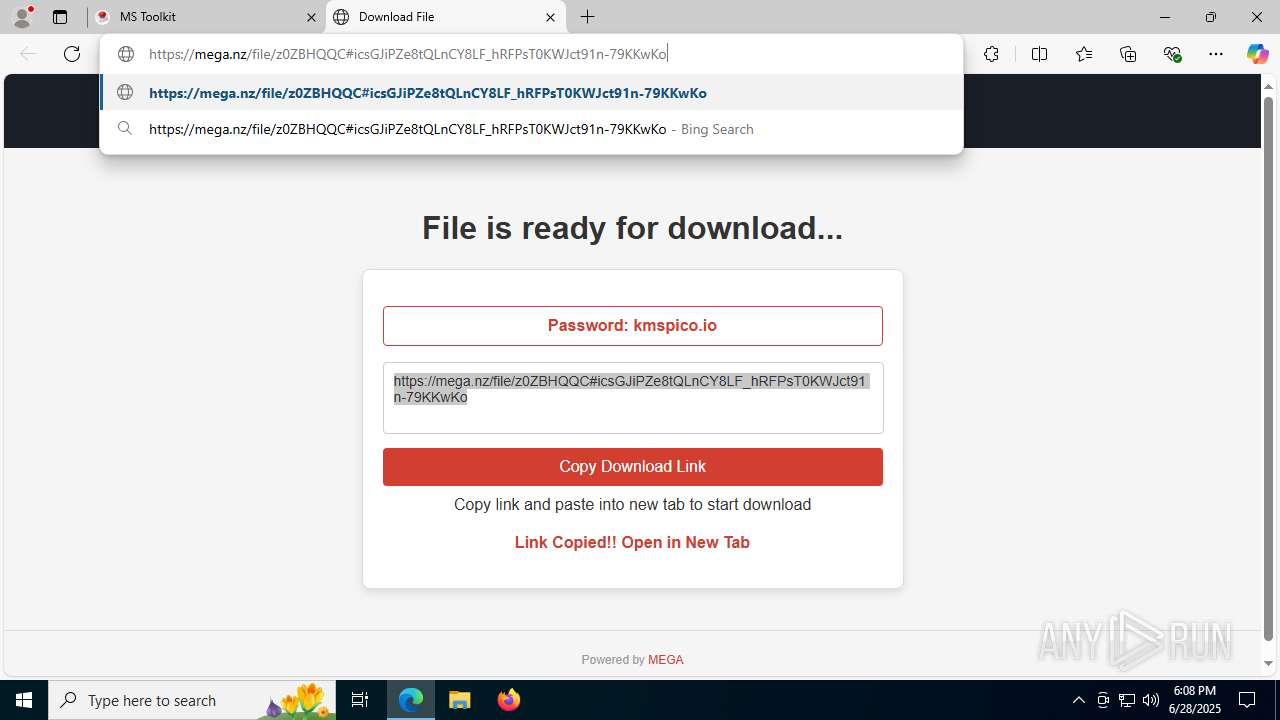
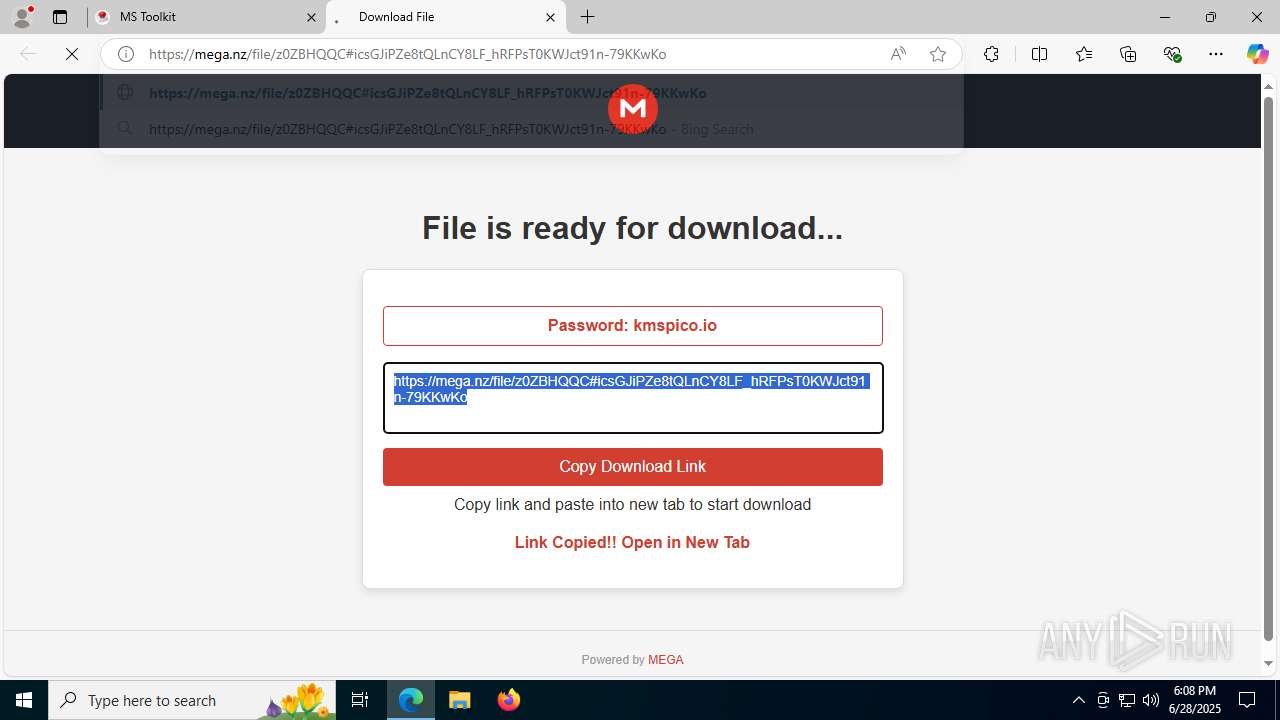
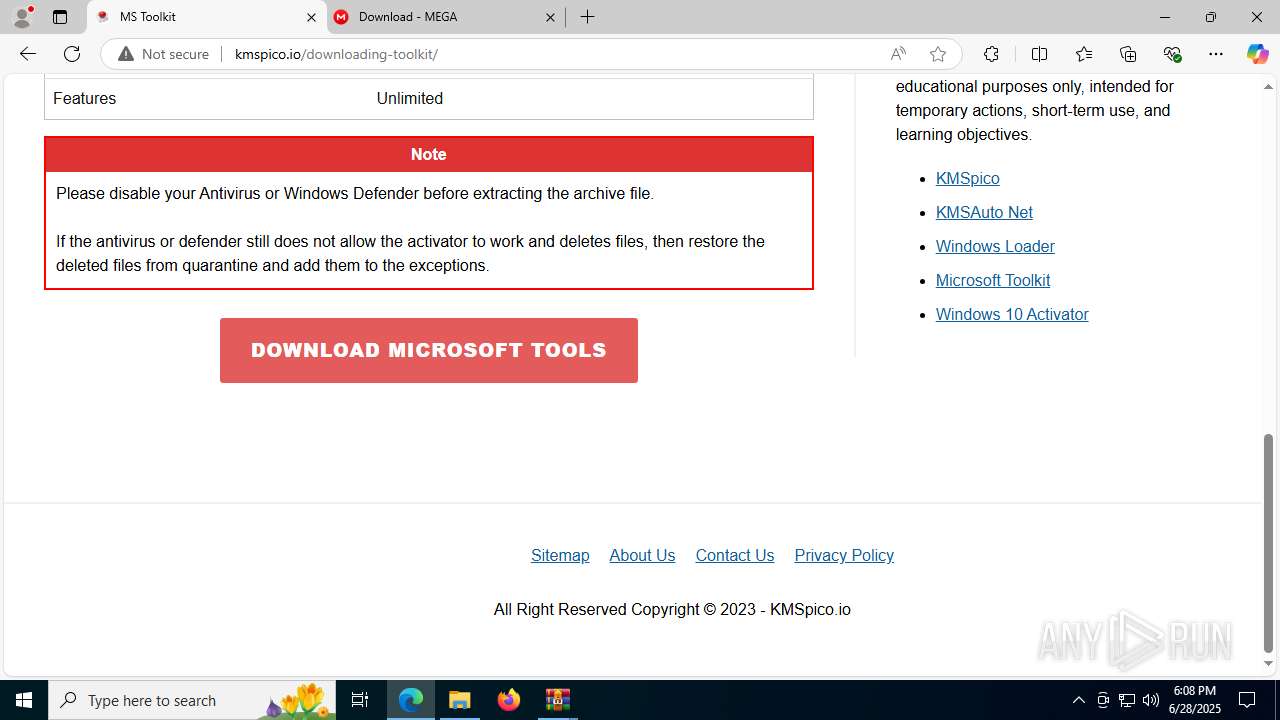
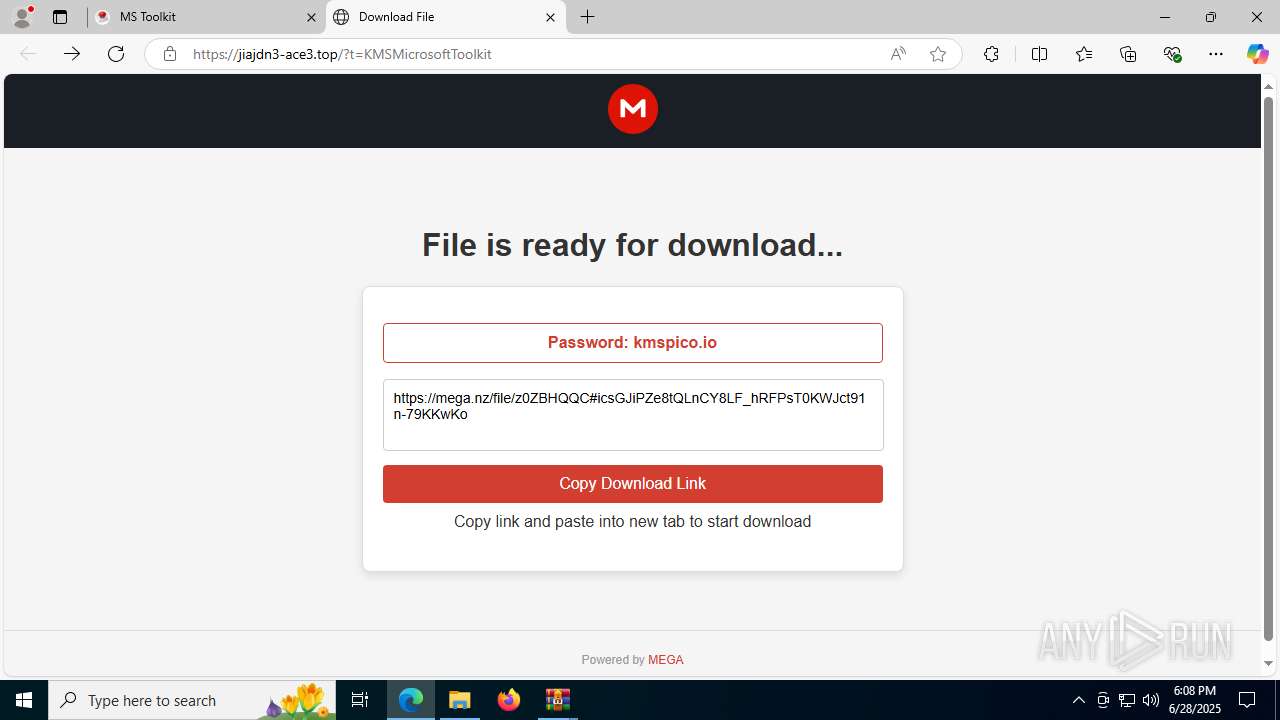
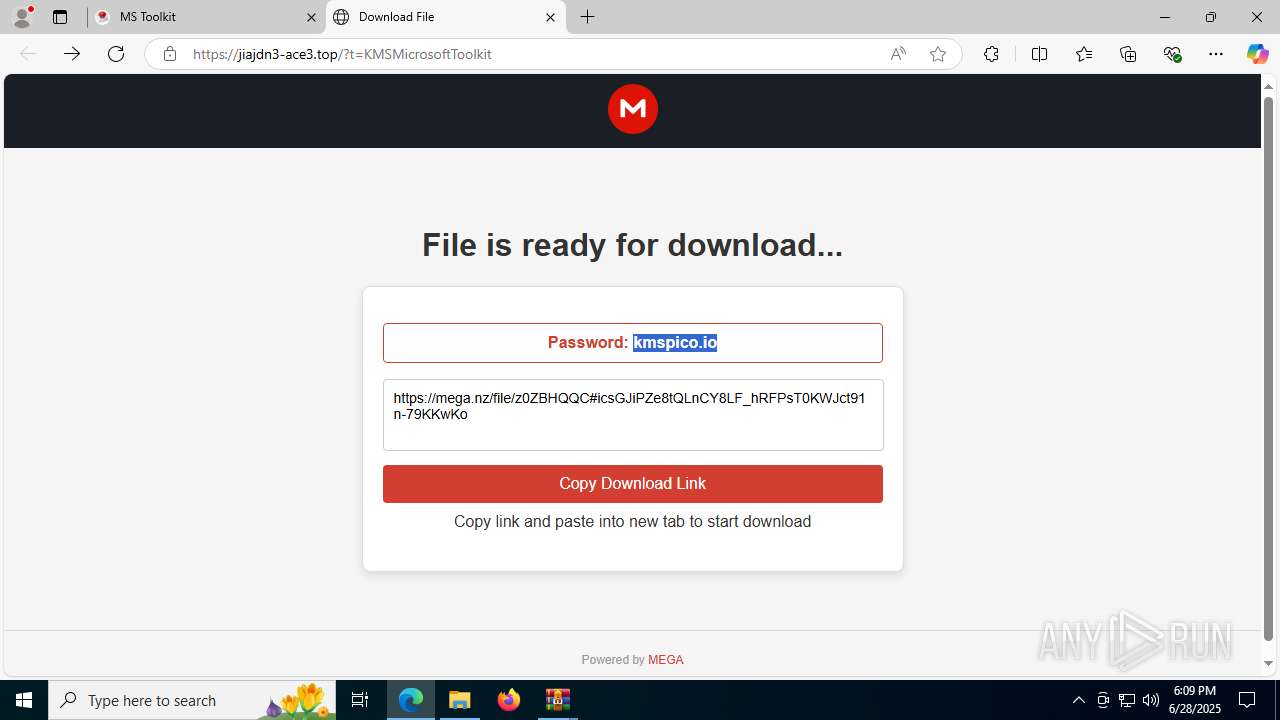
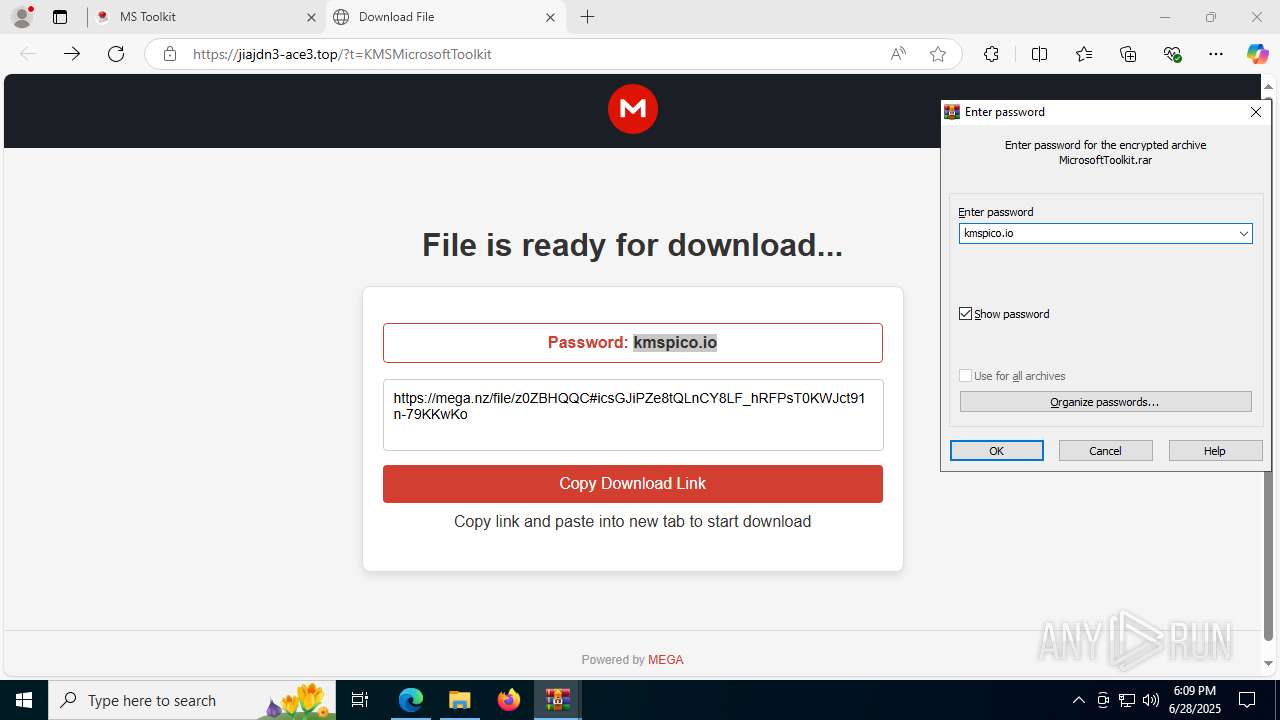
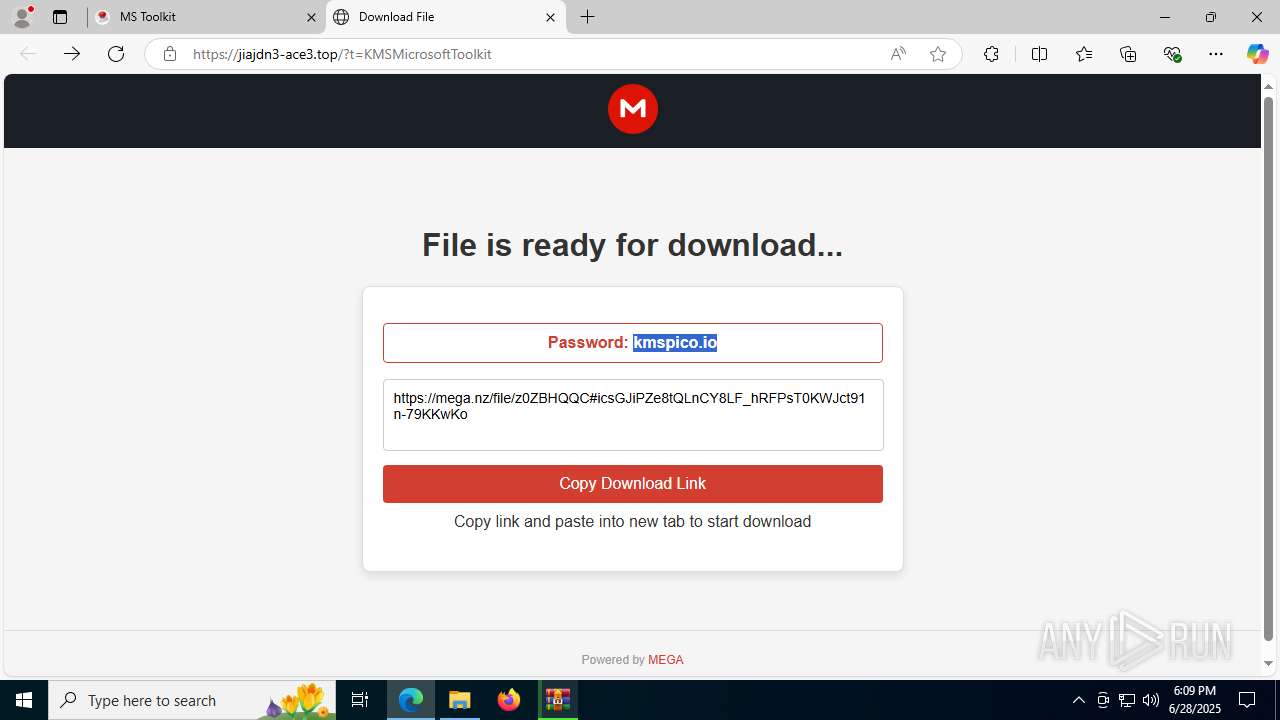
| URL: | kmspico.io |
| Full analysis: | https://app.any.run/tasks/56b938de-1e32-4ccb-bd72-00f7b5ccc7c4 |
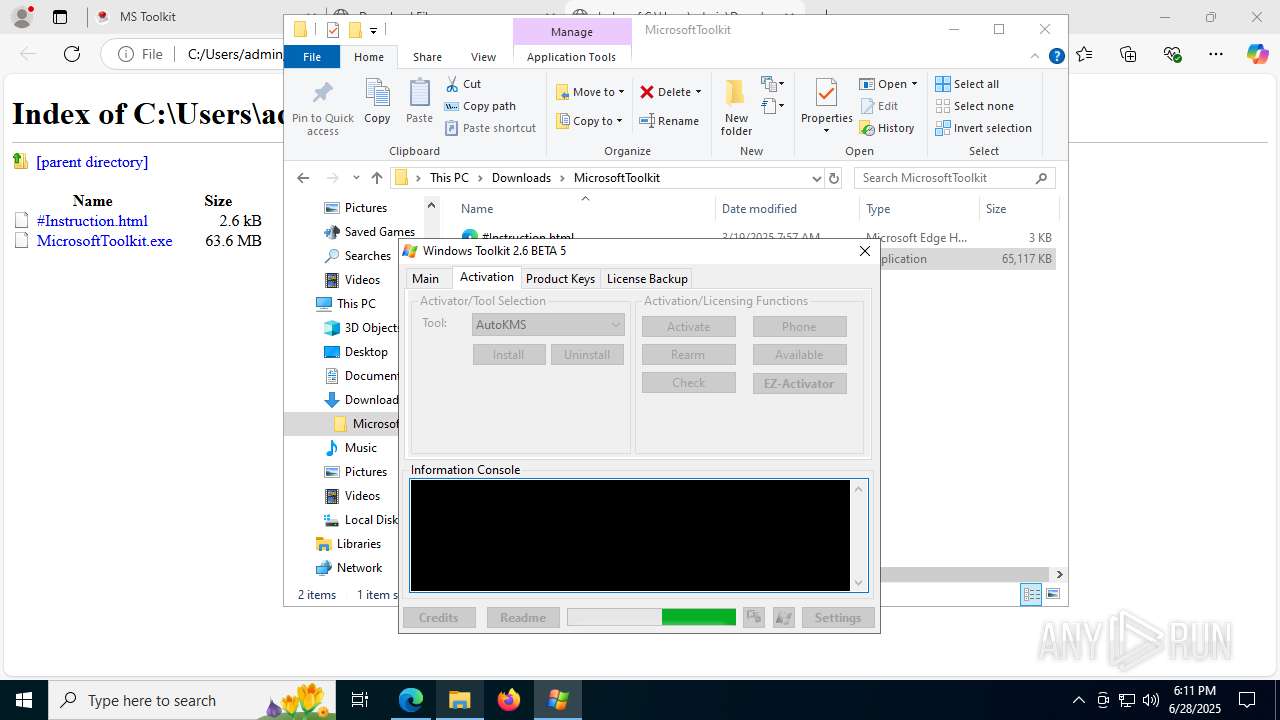
| Verdict: | Malicious activity |
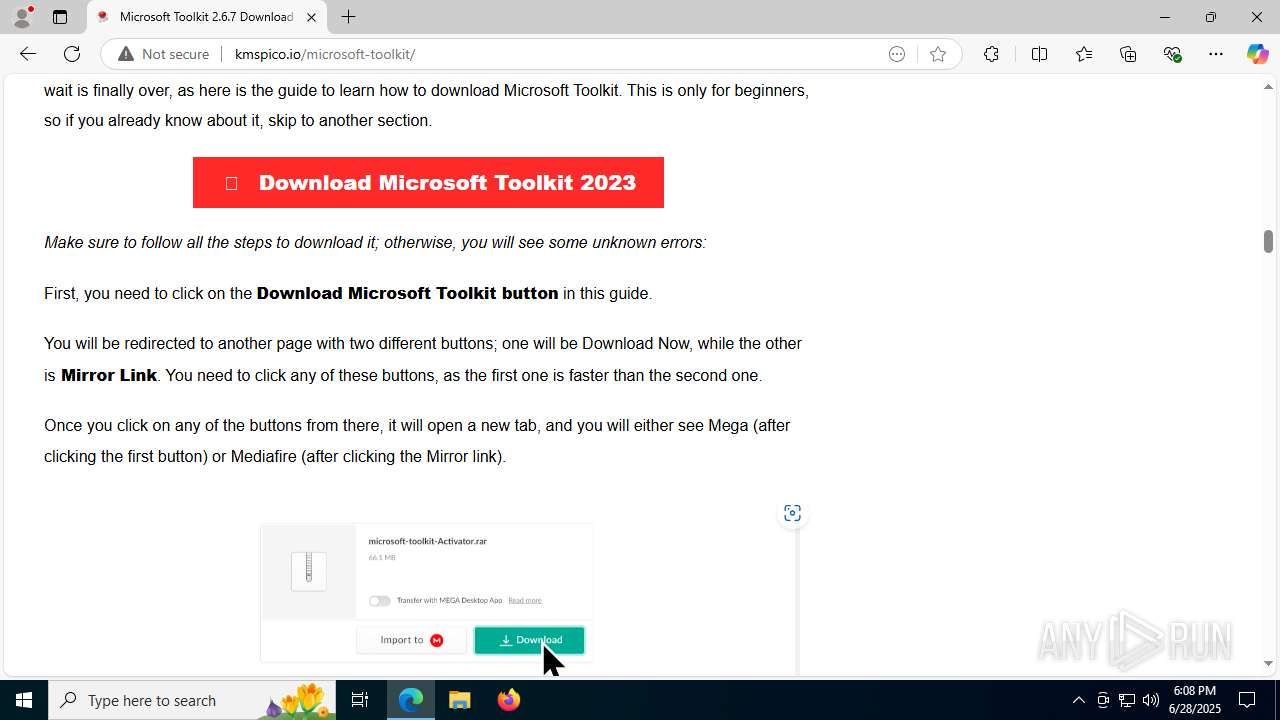
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | June 28, 2025, 18:07:42 |
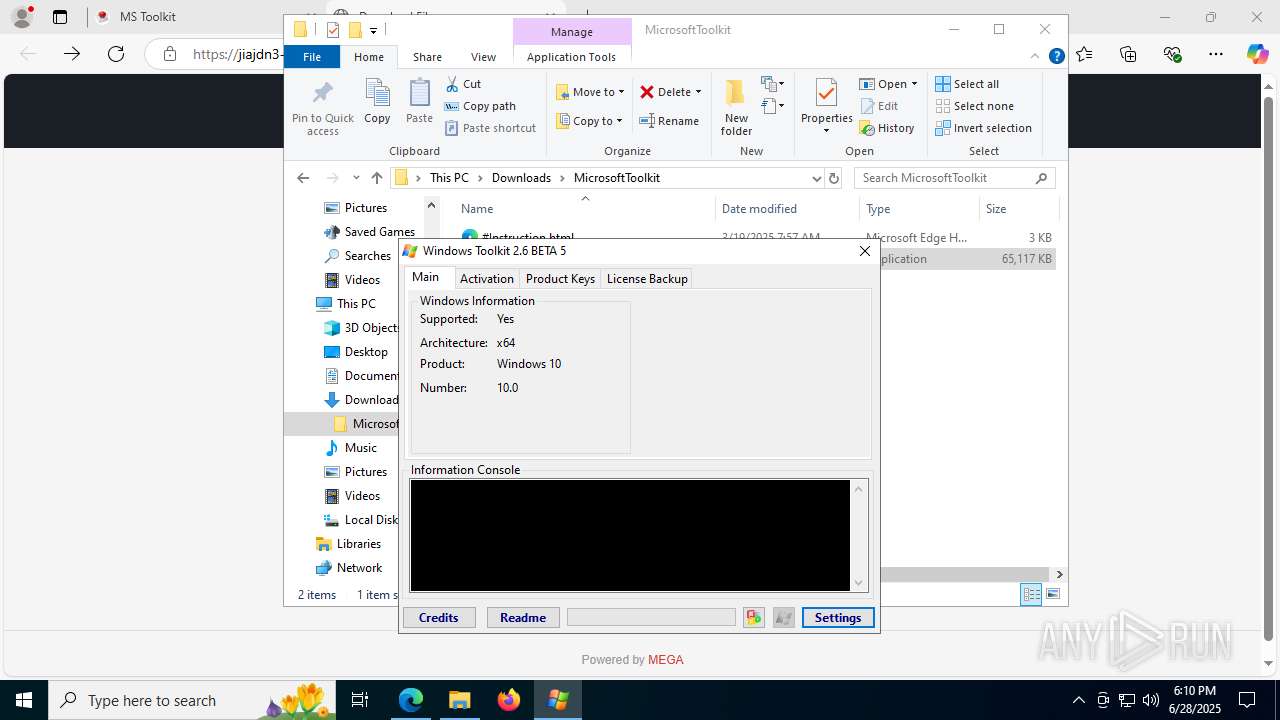
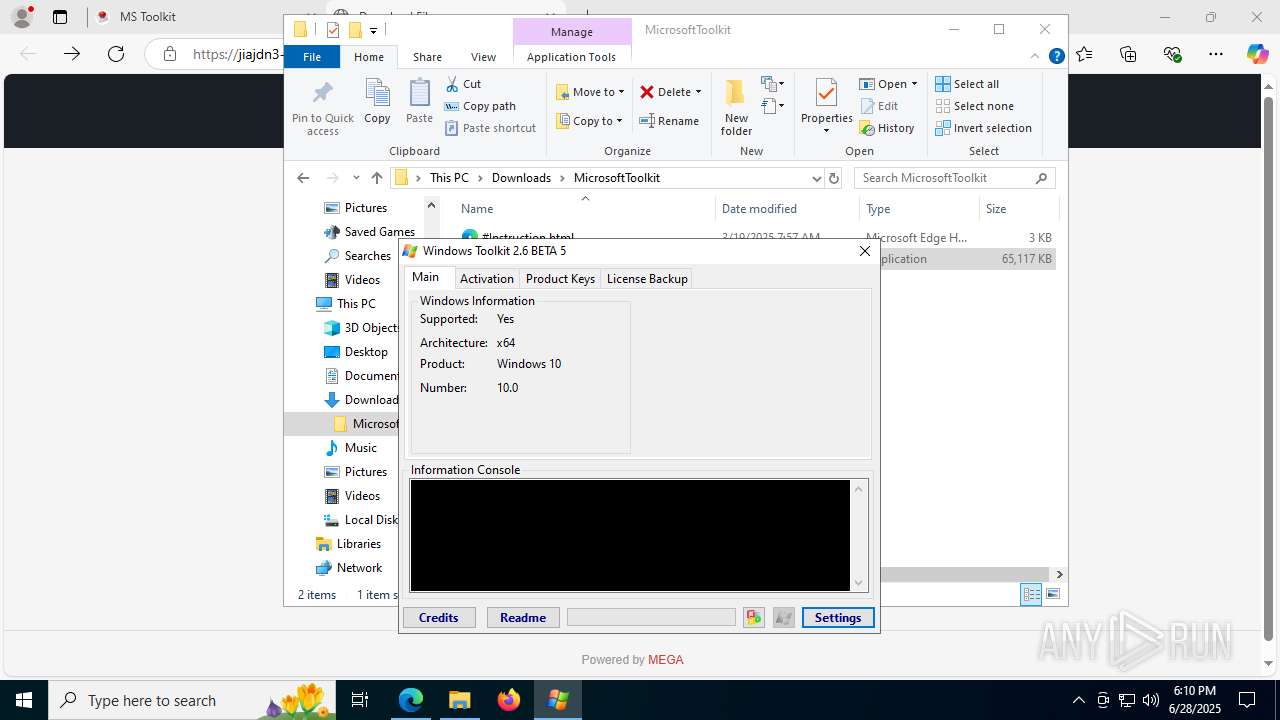
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
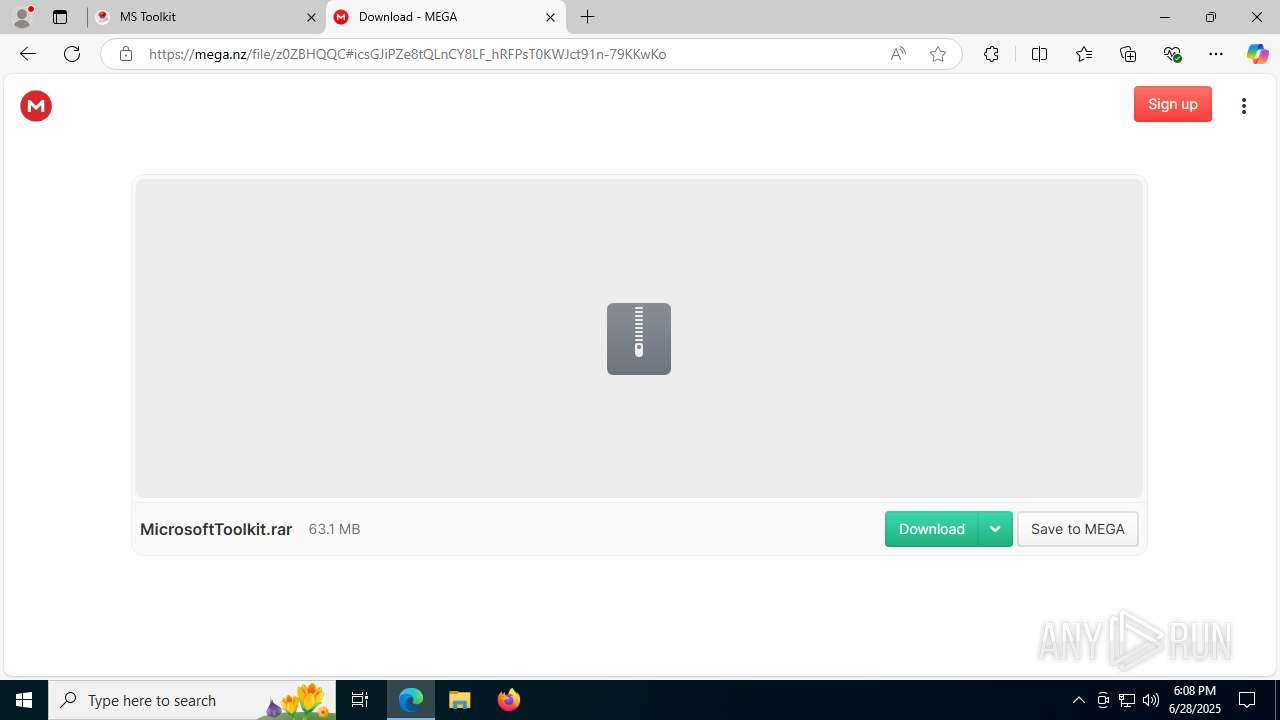
| MD5: | CDFA9B3709EE060A4BECE6FCCC5A9F66 |
| SHA1: | AD8ECBEB0C58236D94E85BE6FA7644647D2A87BD |
| SHA256: | AA0CFEA953F3EE084C0F287C2D06EF13DA9AC1CDF98A6F3493319852D95376DC |
| SSDEEP: | 3:/G0n:x |
MALICIOUS
Connects to the CnC server
- msedge.exe (PID: 2716)
- svchost.exe (PID: 2200)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2200)
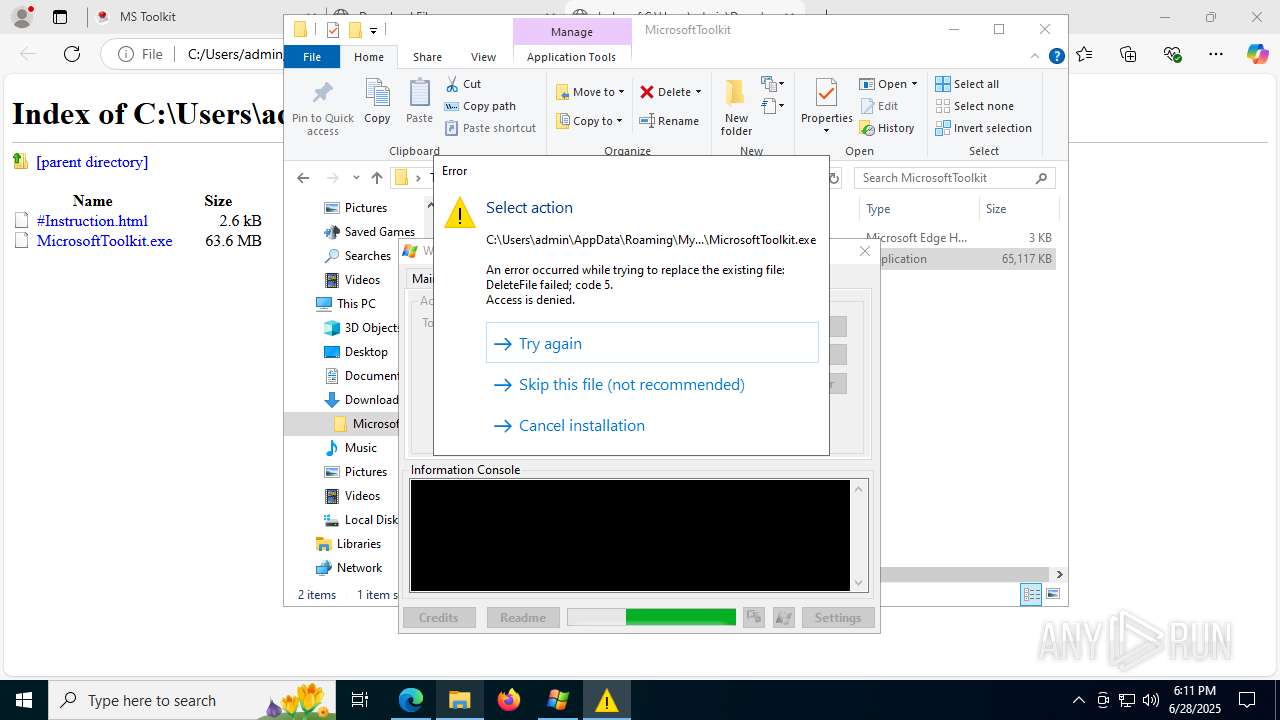
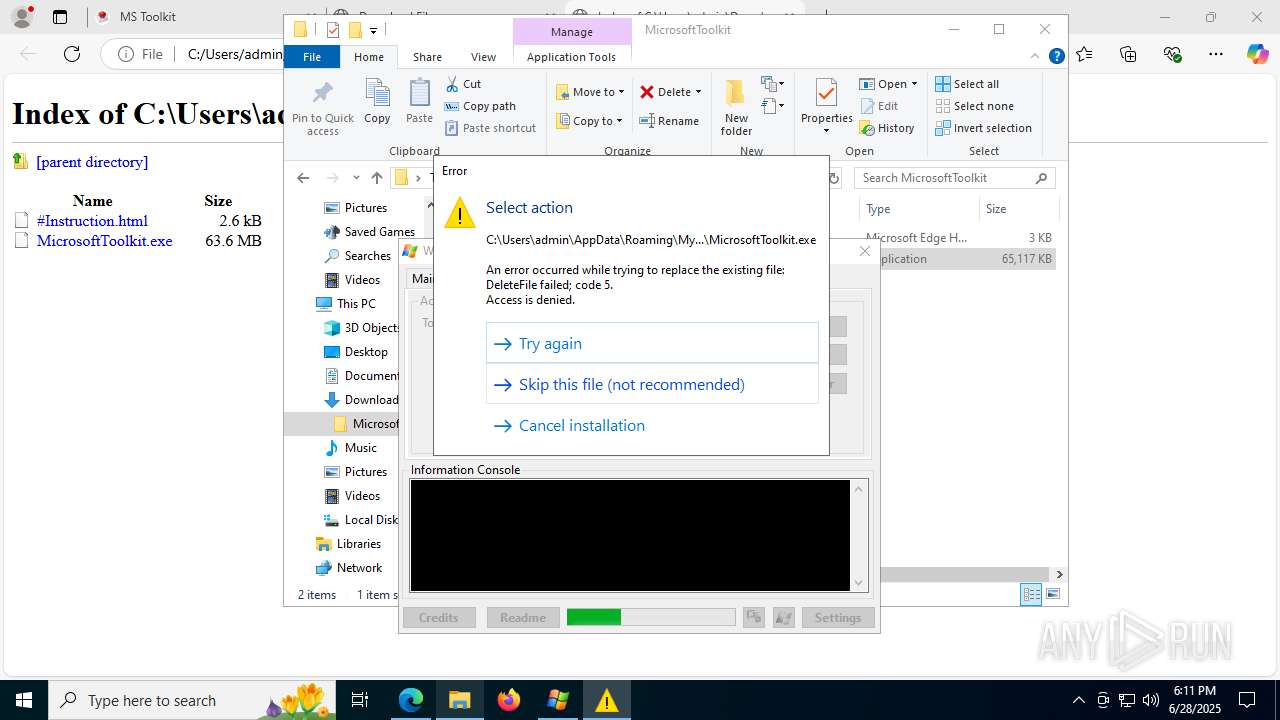
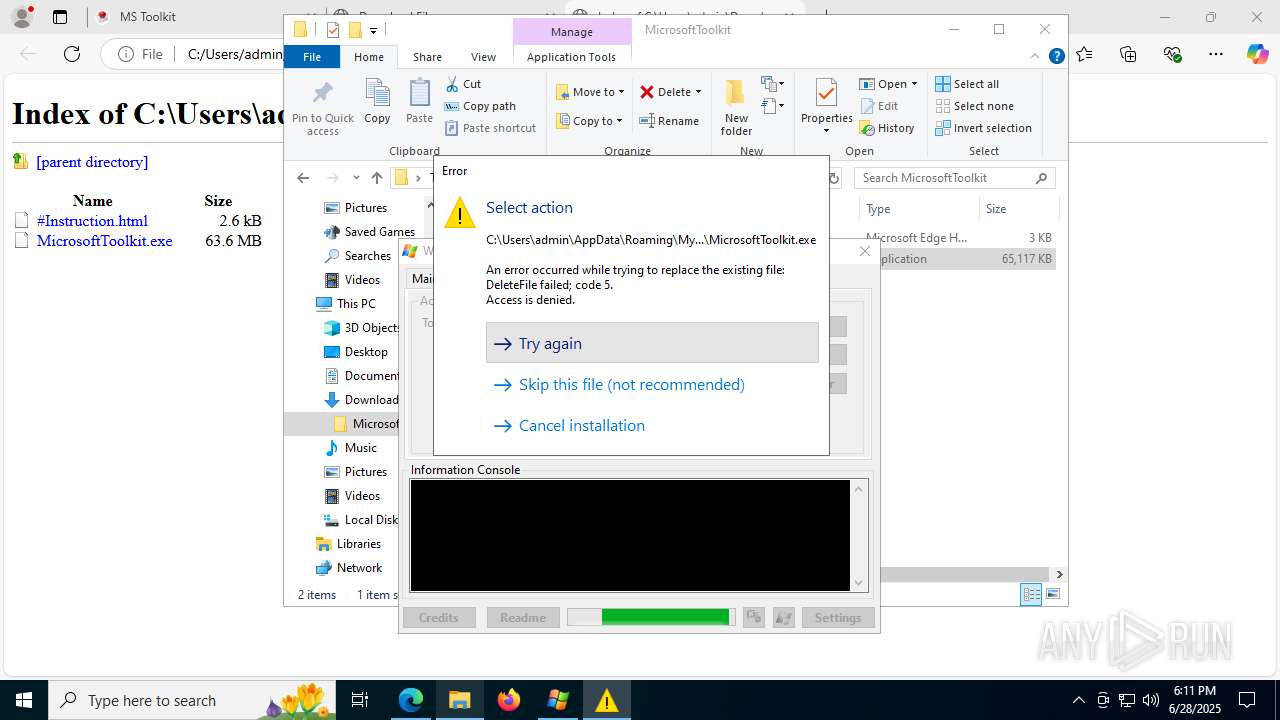
Application was injected by another process
- svchost.exe (PID: 880)
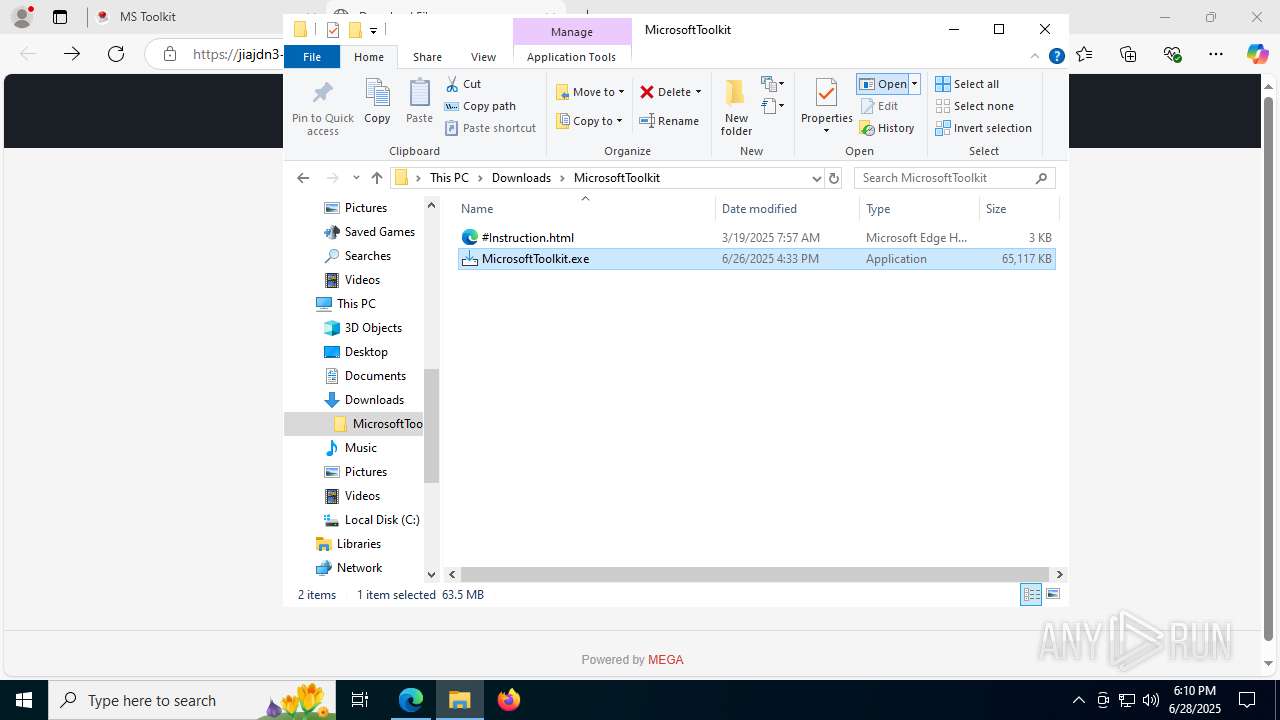
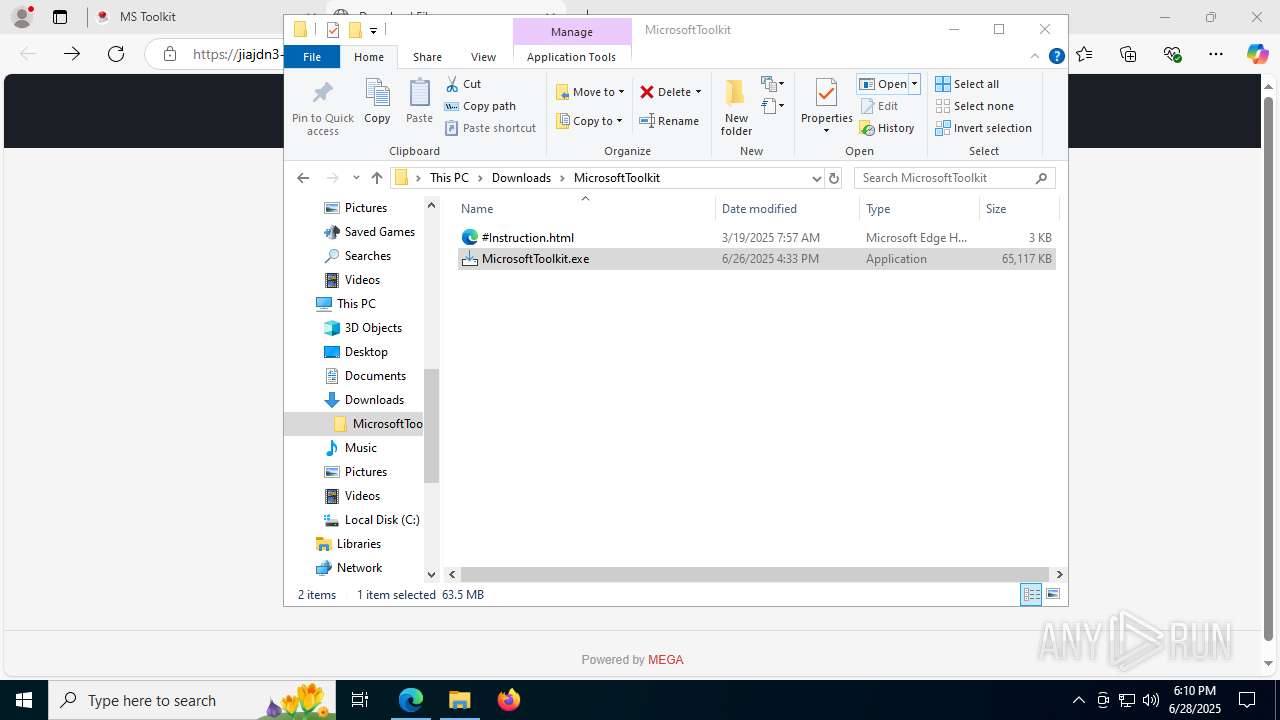
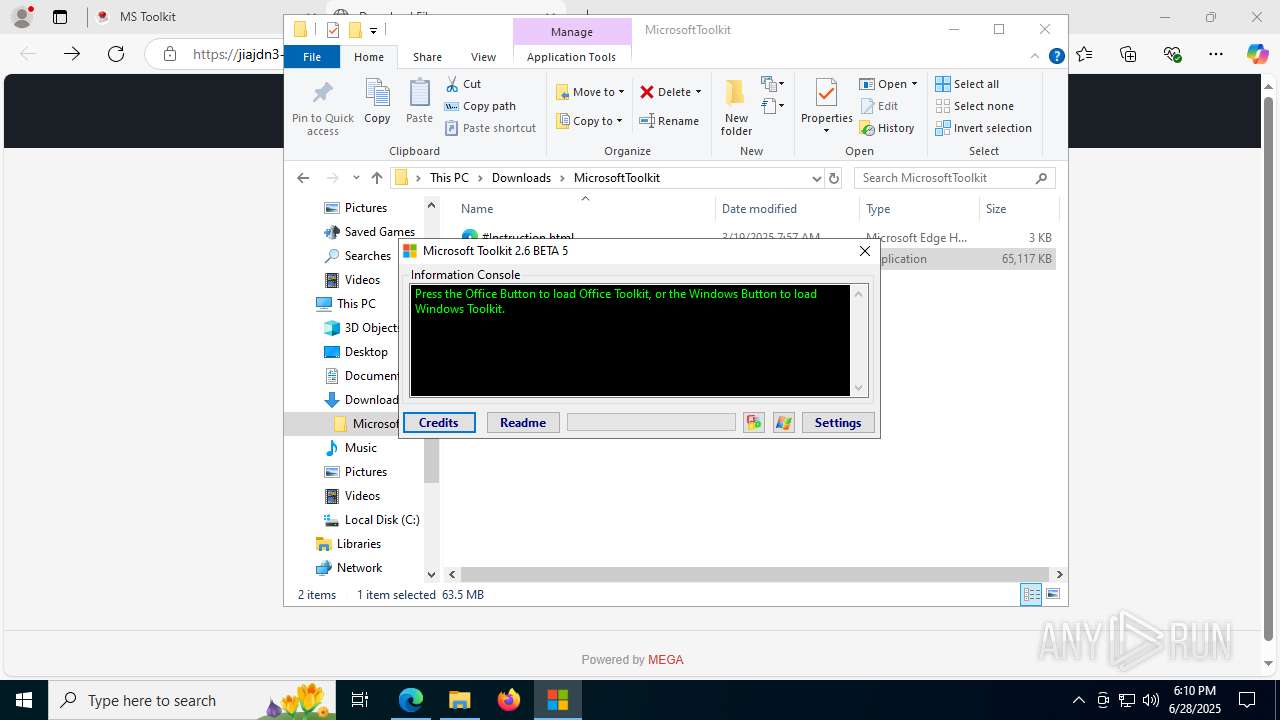
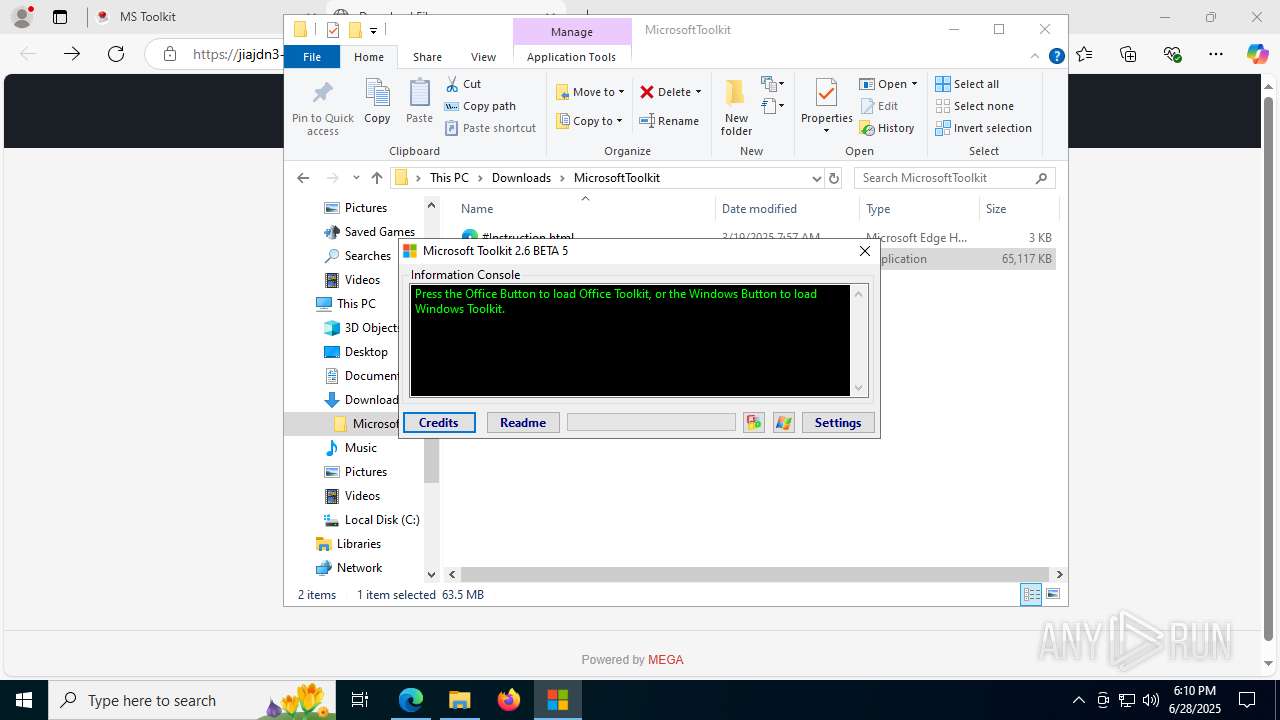
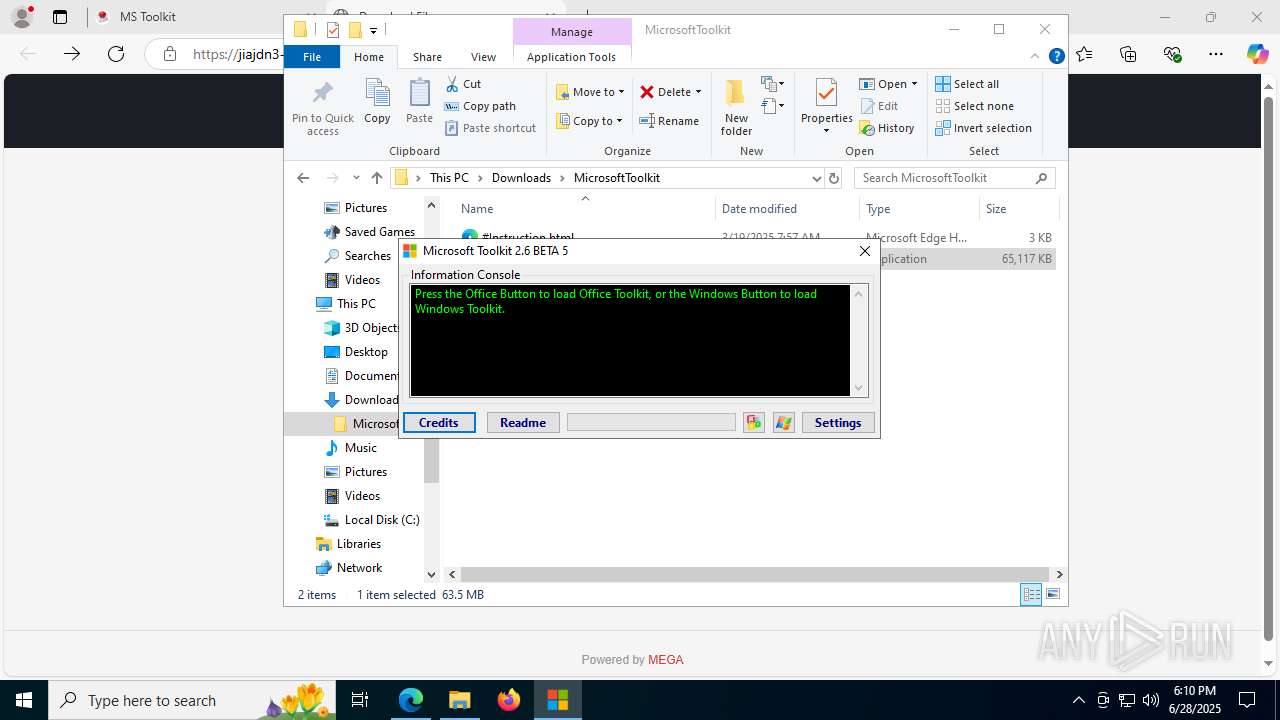
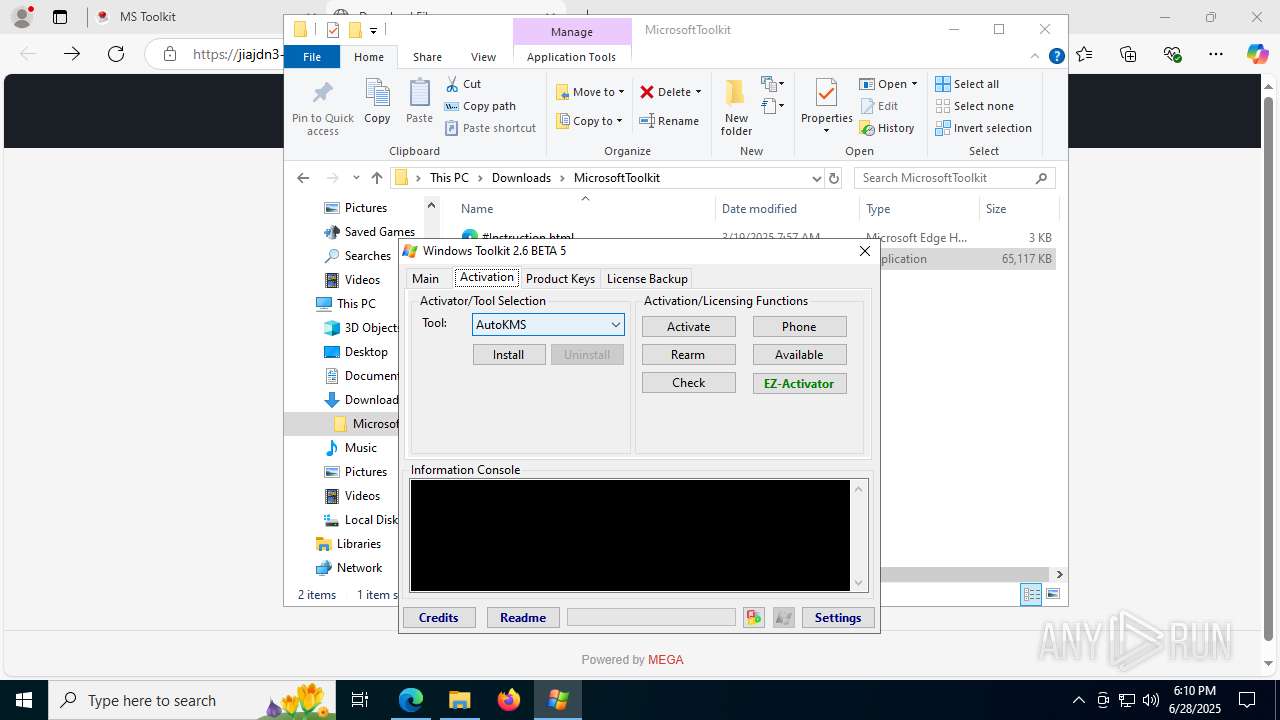
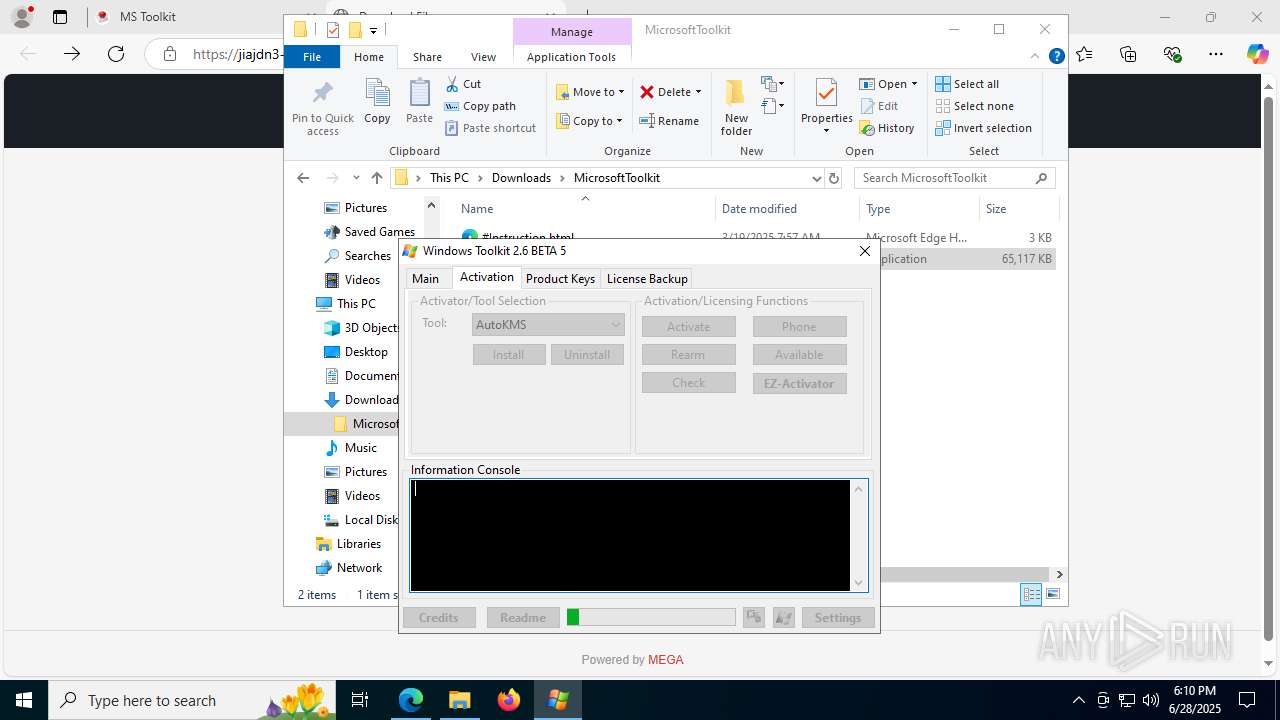
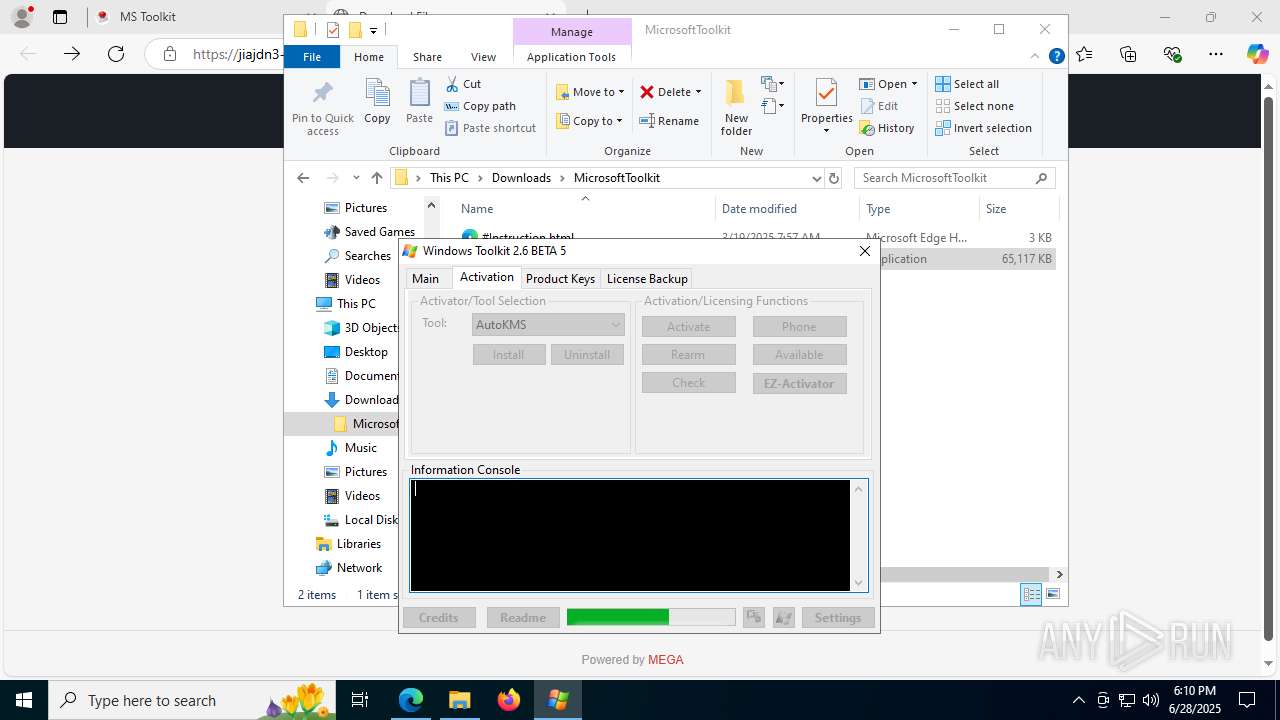
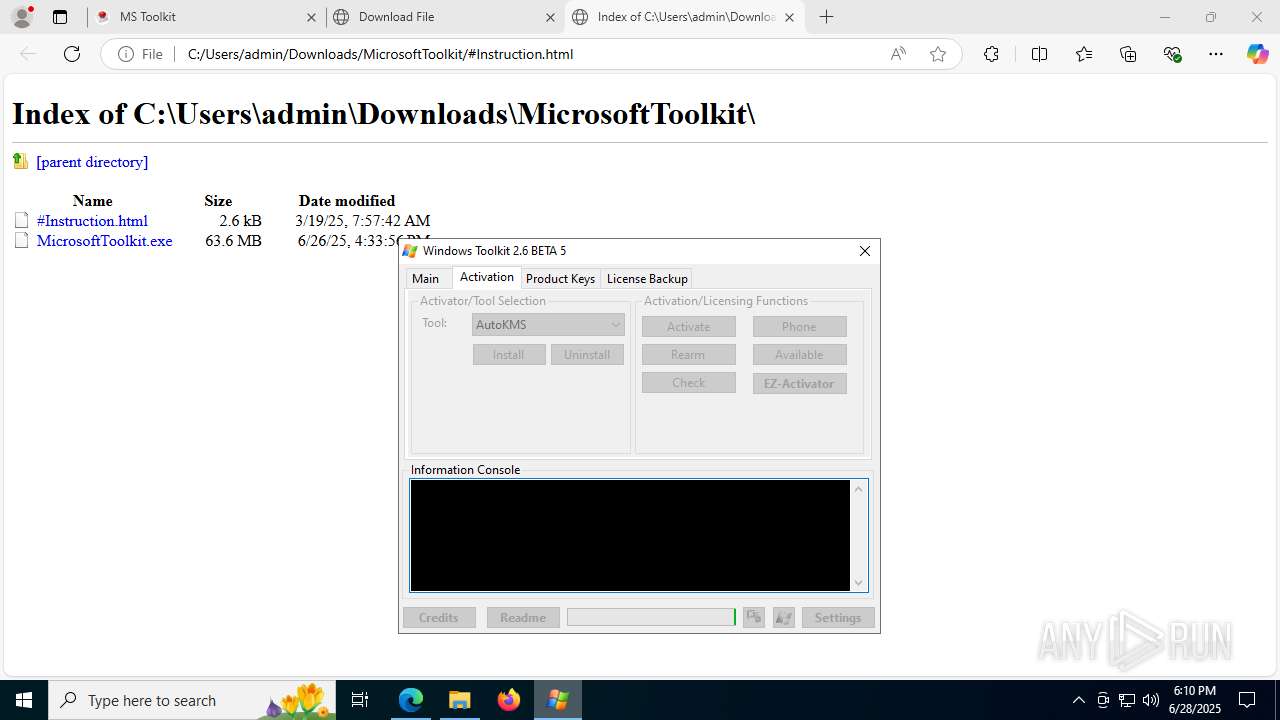
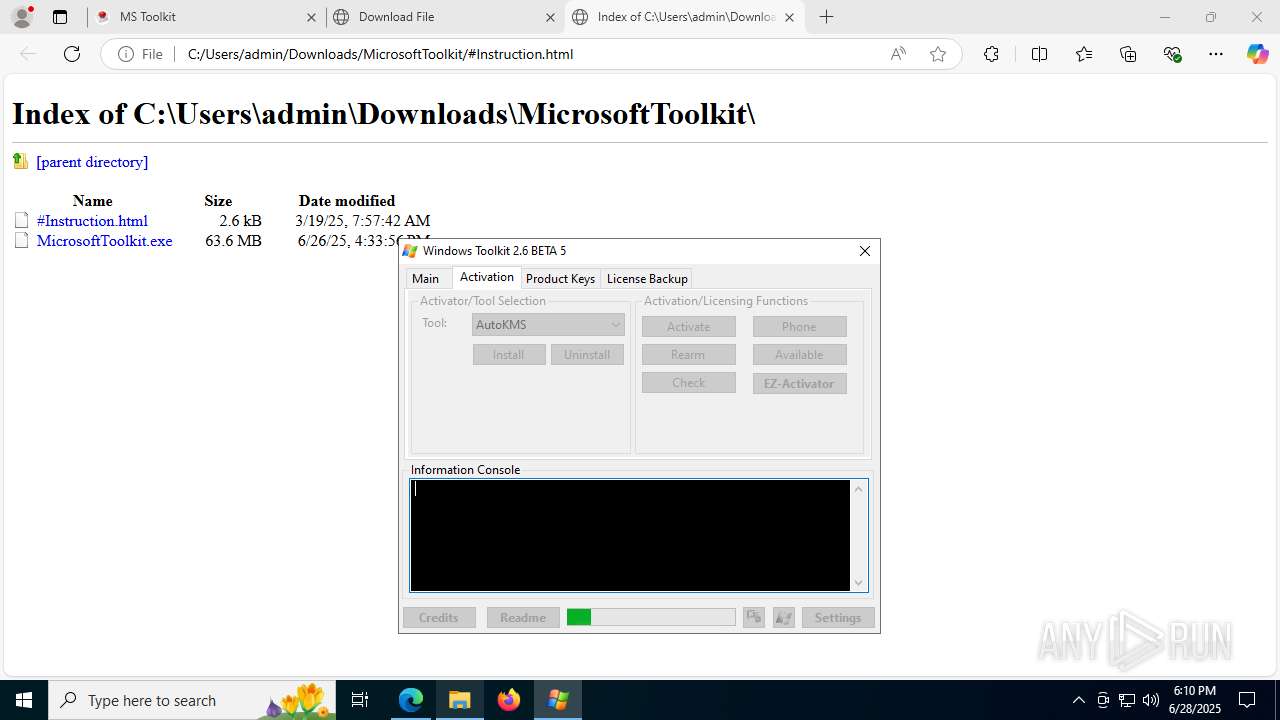
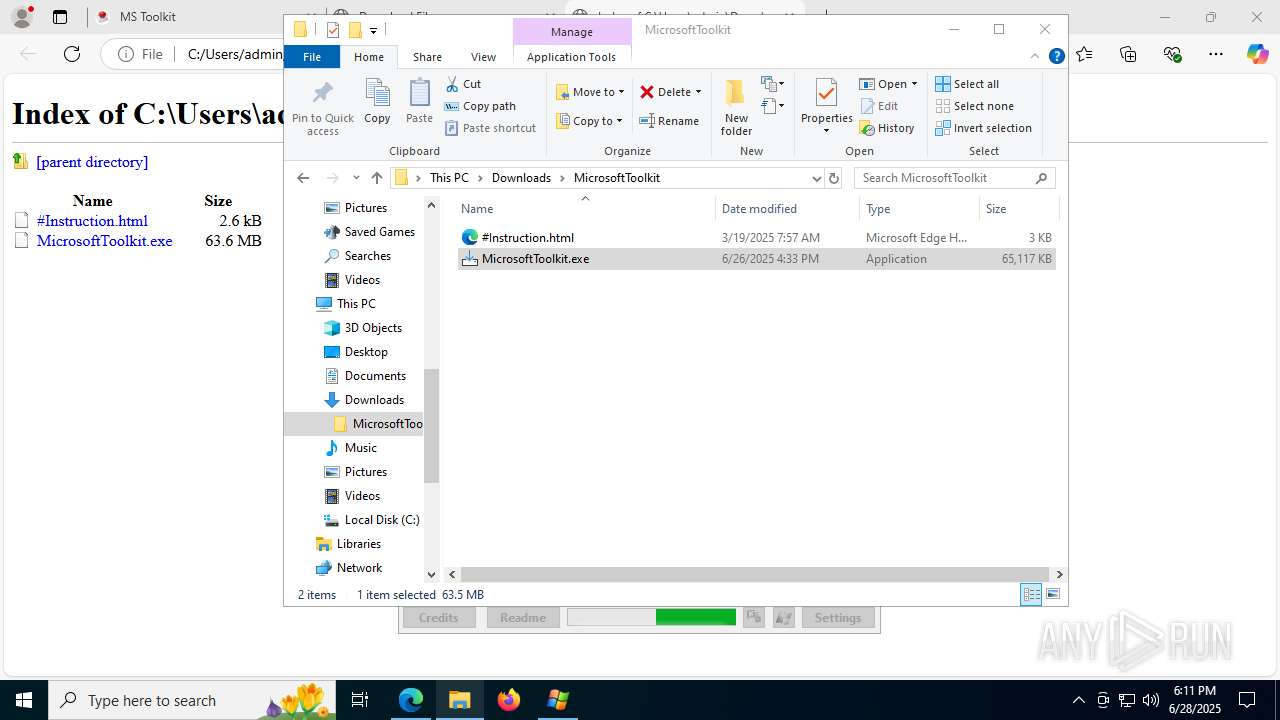
Runs injected code in another process
- MicrosoftToolkit.exe (PID: 6828)
SUSPICIOUS
Reads security settings of Internet Explorer
- MicrosoftToolkit.tmp (PID: 7456)
- MicrosoftToolkit.exe (PID: 6828)
Reads the Windows owner or organization settings
- MicrosoftToolkit.tmp (PID: 7456)
- MicrosoftToolkit.tmp (PID: 6812)
- MicrosoftToolkit.tmp (PID: 7520)
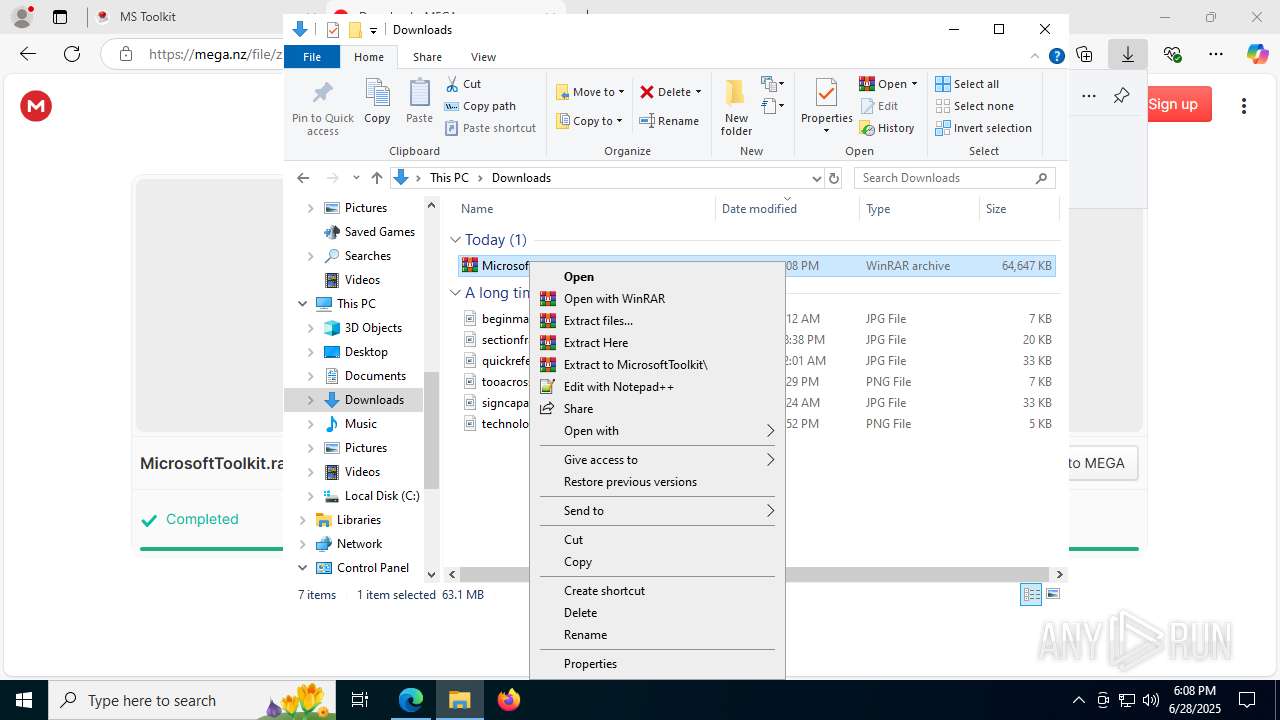
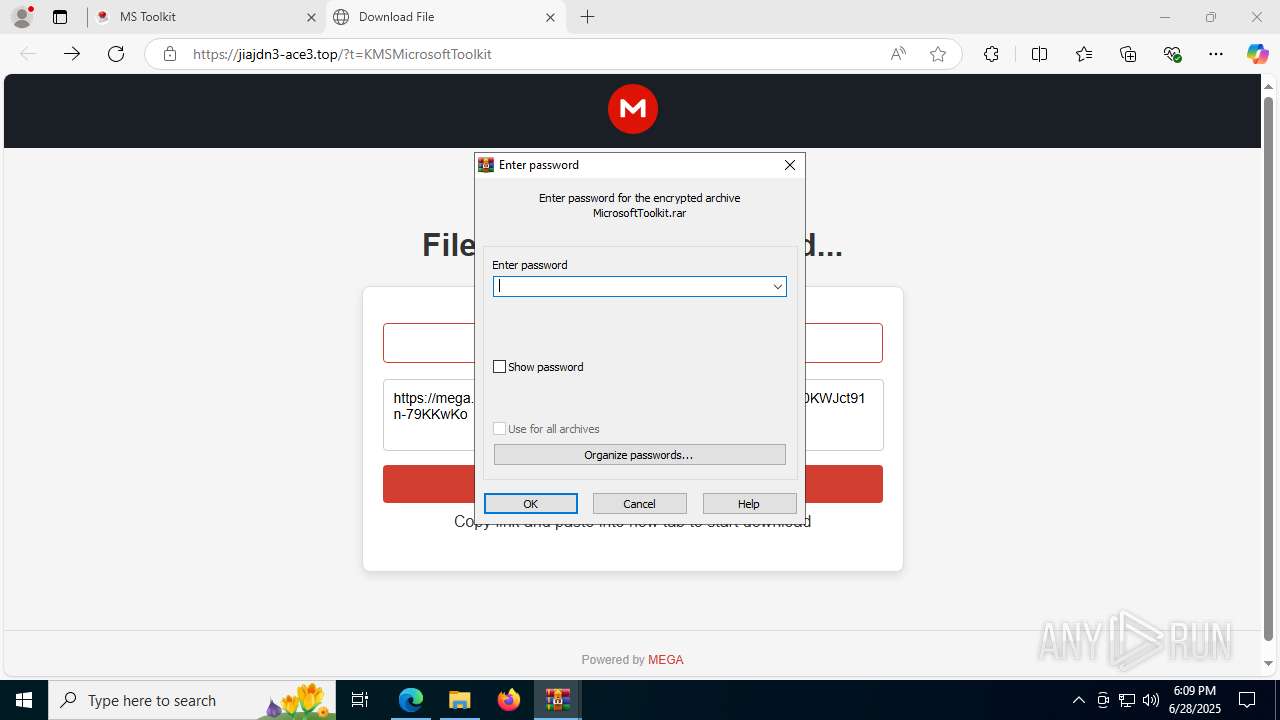
Executable content was dropped or overwritten
- MicrosoftToolkit.tmp (PID: 7456)
- MicrosoftToolkit.exe (PID: 6812)
- MicrosoftToolkit.exe (PID: 6828)
- MicrosoftToolkit.exe (PID: 4804)
- MicrosoftToolkit.tmp (PID: 6812)
- MicrosoftToolkit.exe (PID: 4032)
- MicrosoftToolkit.tmp (PID: 7520)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2200)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 5684)
- cmd.exe (PID: 5444)
Starts CMD.EXE for commands execution
- MicrosoftToolkit.exe (PID: 6828)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 7948)
- cmd.exe (PID: 8076)
Connects to unusual port
- SppExtComObj.Exe (PID: 6688)
Searches for installed software
- MicrosoftToolkit.tmp (PID: 6812)
- MicrosoftToolkit.tmp (PID: 7520)
INFO
Application launched itself
- msedge.exe (PID: 2128)
Checks supported languages
- identity_helper.exe (PID: 7900)
- MicrosoftToolkit.exe (PID: 6828)
- core.exe (PID: 4236)
- MicrosoftToolkit.tmp (PID: 7456)
- MicrosoftToolkit.exe (PID: 6812)
- MicrosoftToolkit.exe (PID: 4804)
- MicrosoftToolkit.tmp (PID: 6812)
- MicrosoftToolkit.exe (PID: 4032)
- MicrosoftToolkit.tmp (PID: 7520)
Reads Environment values
- identity_helper.exe (PID: 7900)
Reads the computer name
- identity_helper.exe (PID: 7900)
- MicrosoftToolkit.exe (PID: 6828)
- MicrosoftToolkit.tmp (PID: 7456)
- core.exe (PID: 4236)
- MicrosoftToolkit.tmp (PID: 6812)
- MicrosoftToolkit.tmp (PID: 7520)
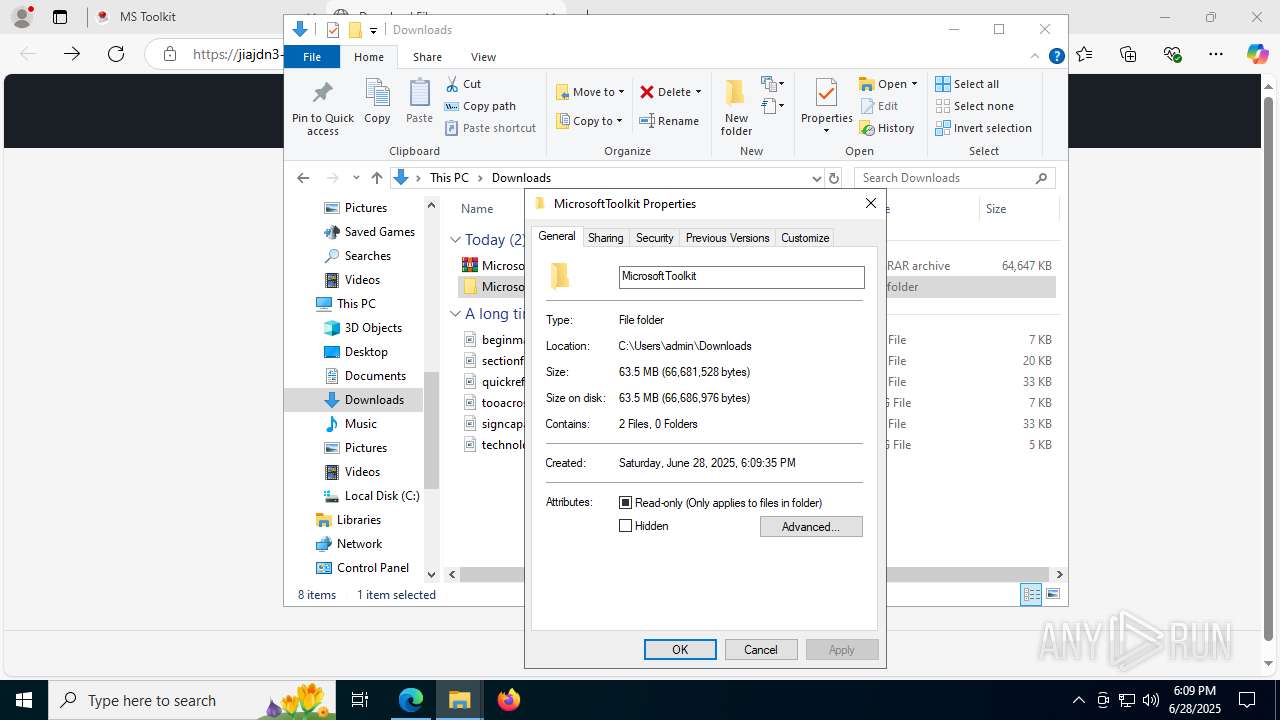
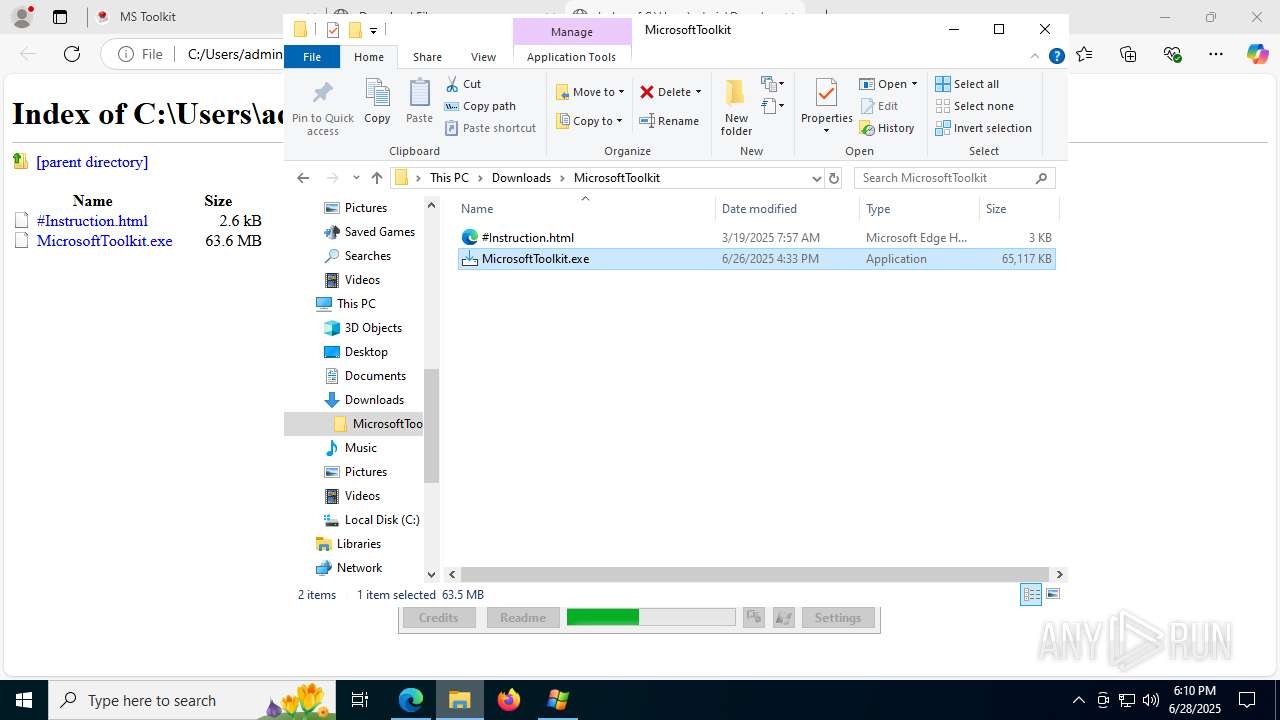
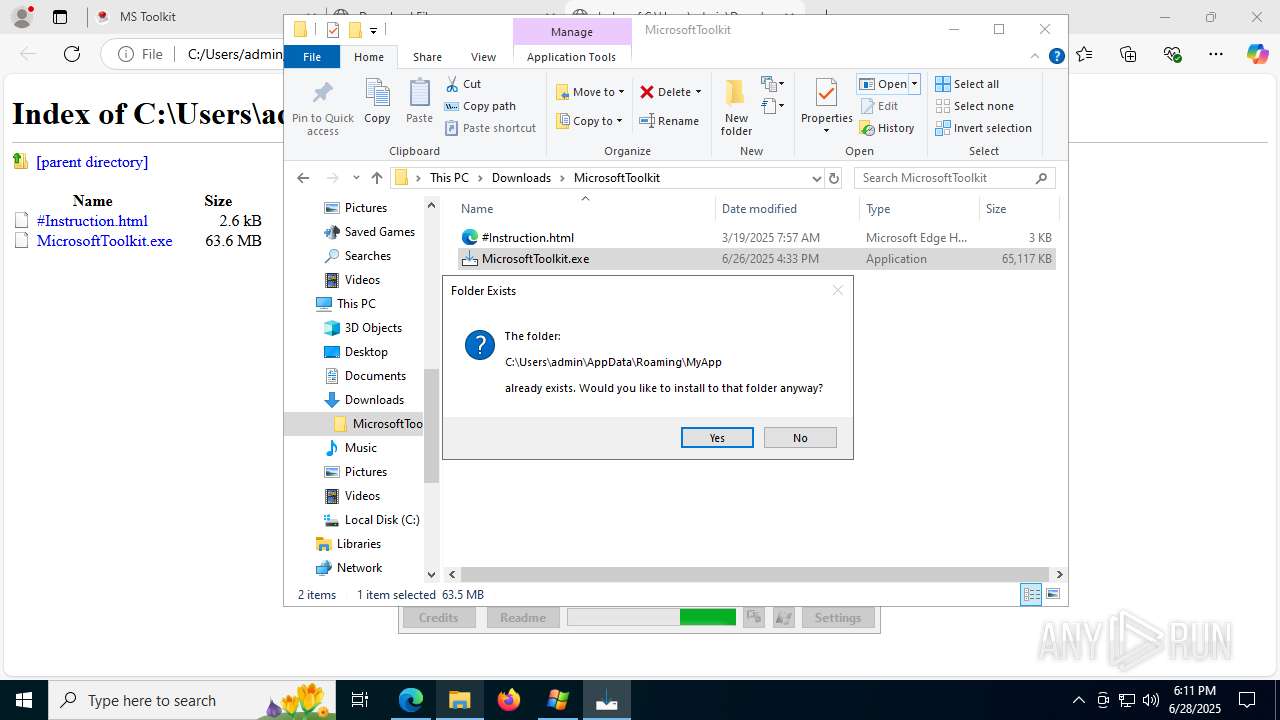
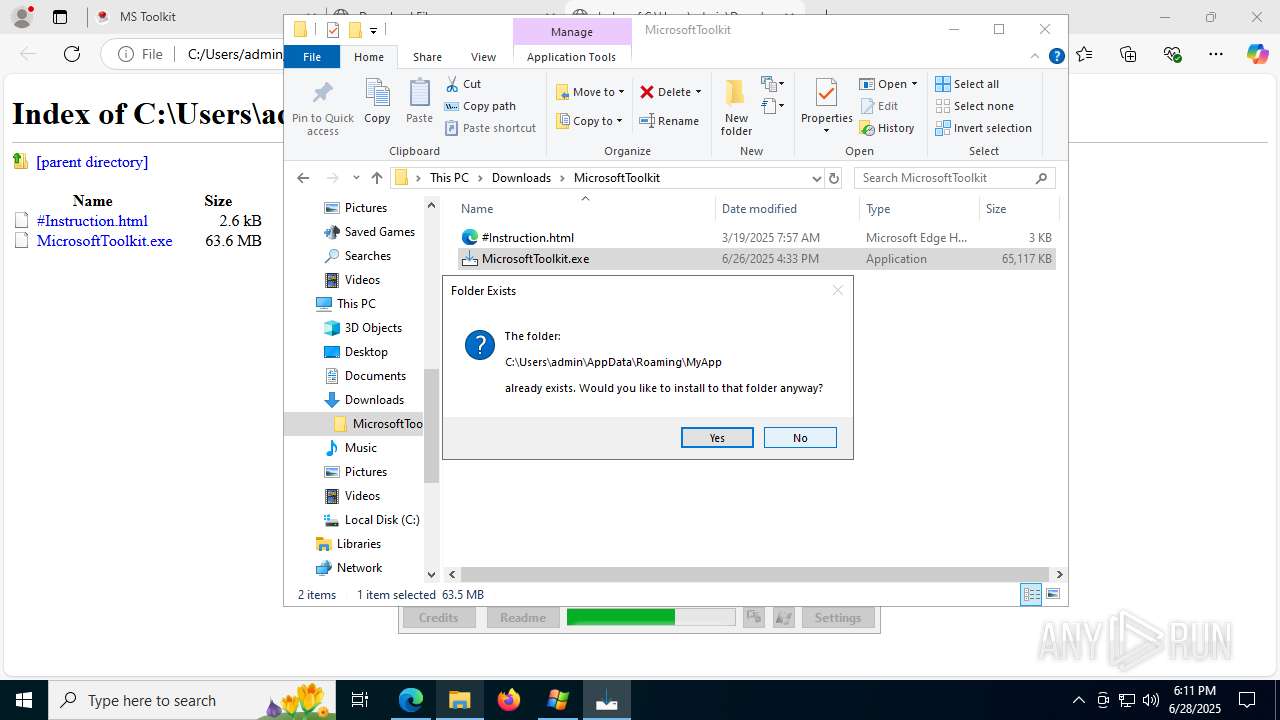
Creates a software uninstall entry
- MicrosoftToolkit.tmp (PID: 7456)
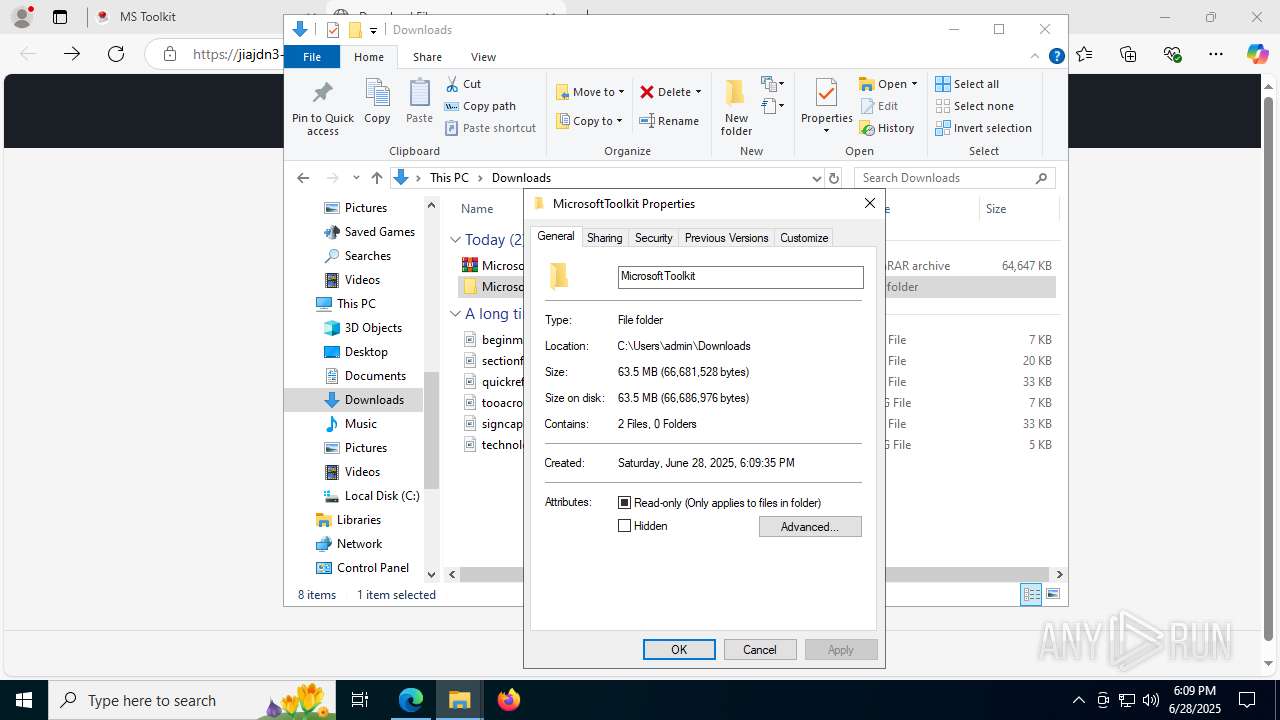
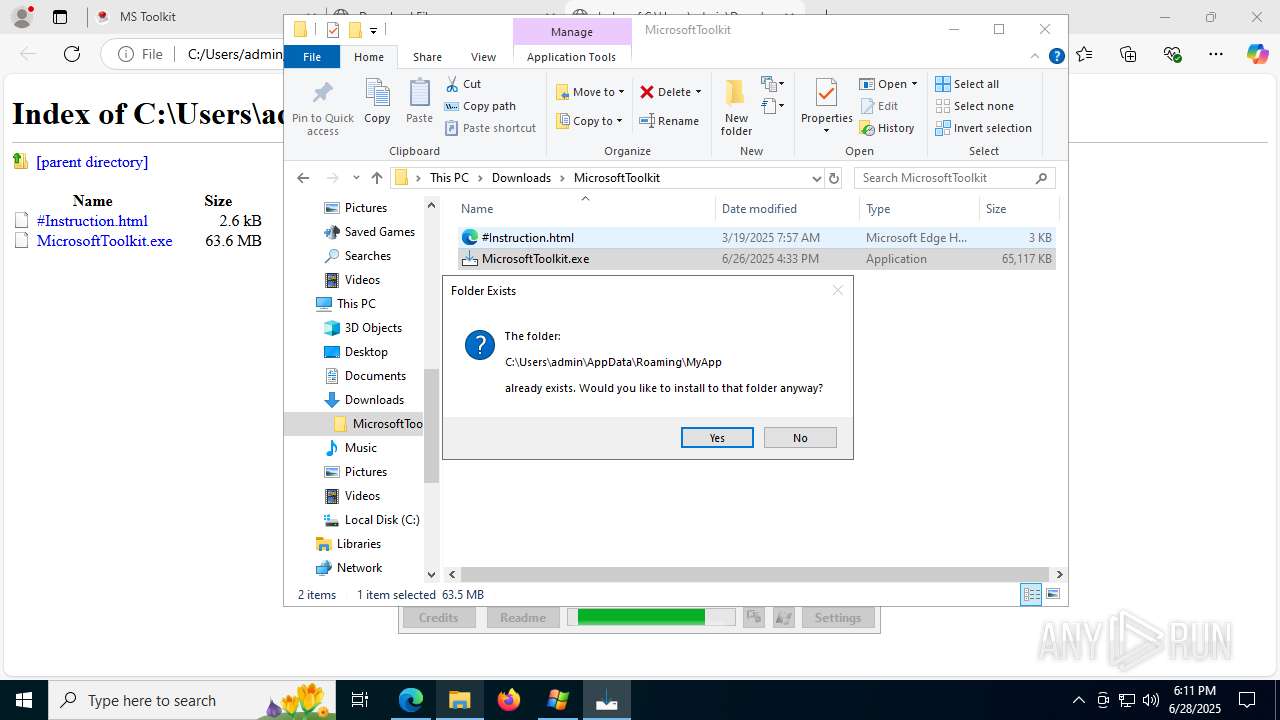
Creates files or folders in the user directory
- MicrosoftToolkit.tmp (PID: 7456)
- MicrosoftToolkit.tmp (PID: 7520)
The sample compiled with english language support
- MicrosoftToolkit.tmp (PID: 7456)
Process checks computer location settings
- MicrosoftToolkit.tmp (PID: 7456)
Creates files in the program directory
- MicrosoftToolkit.exe (PID: 6828)
Reads the machine GUID from the registry
- MicrosoftToolkit.exe (PID: 6828)
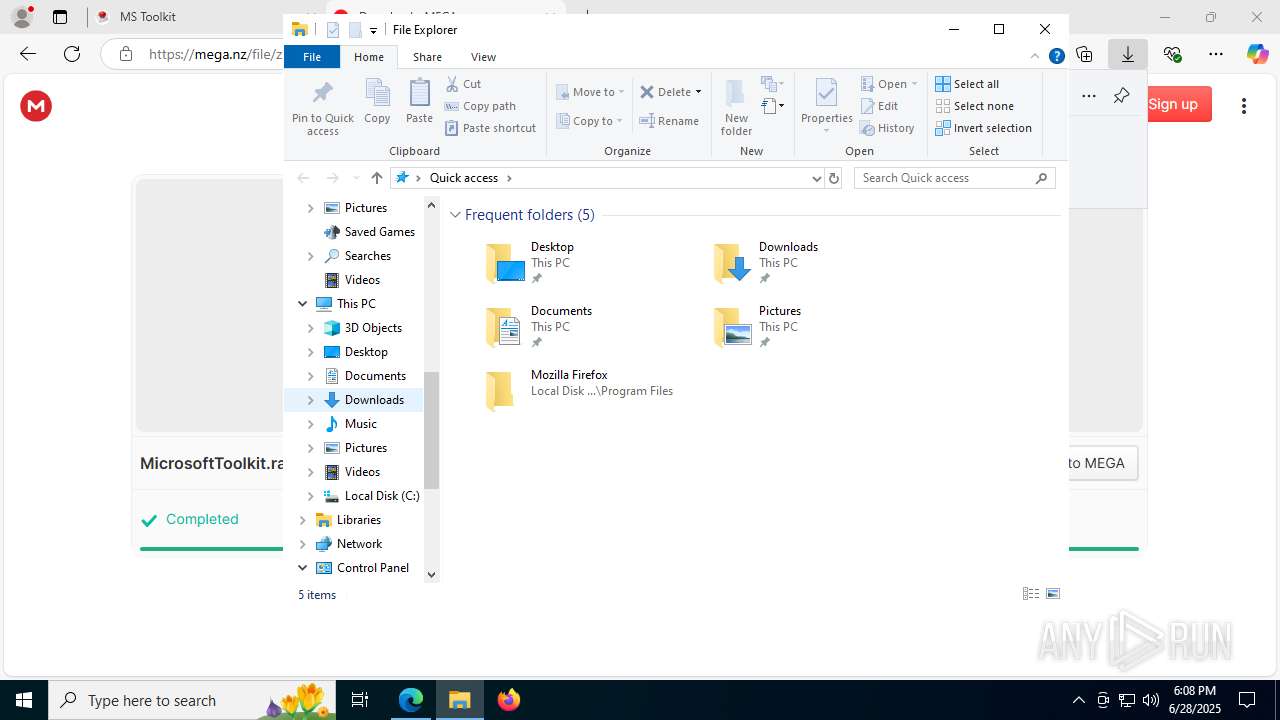
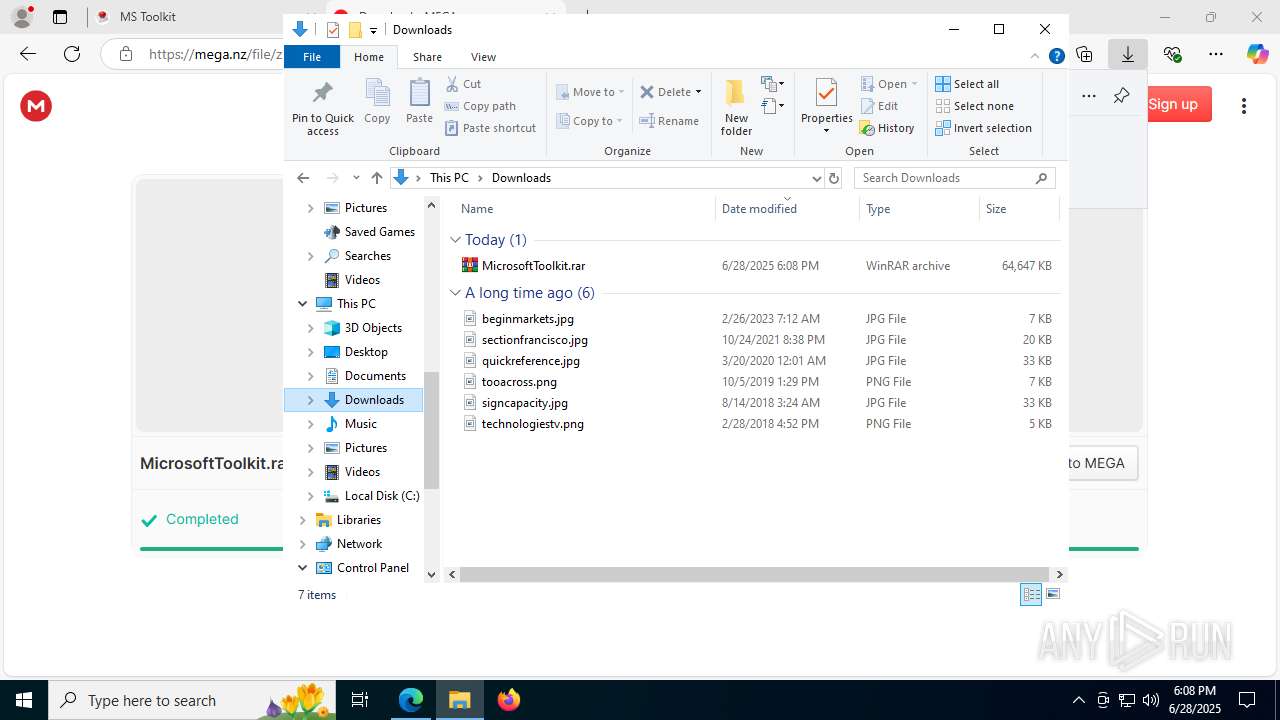
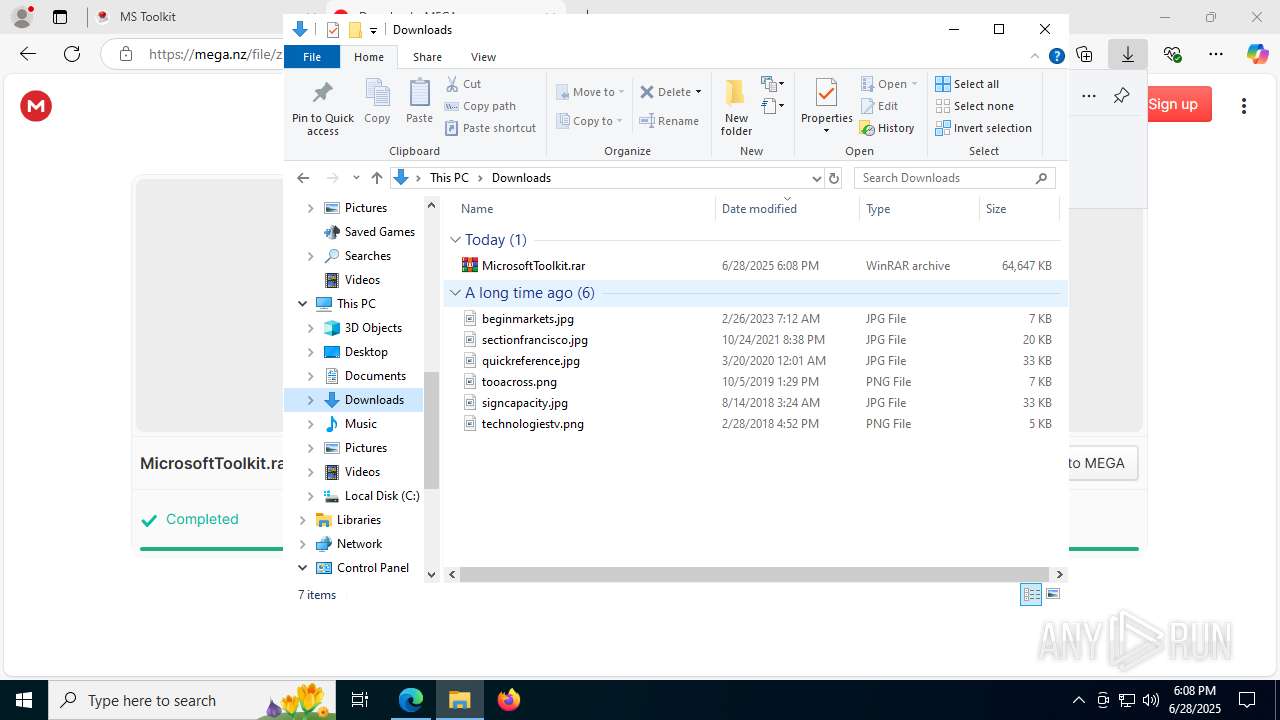
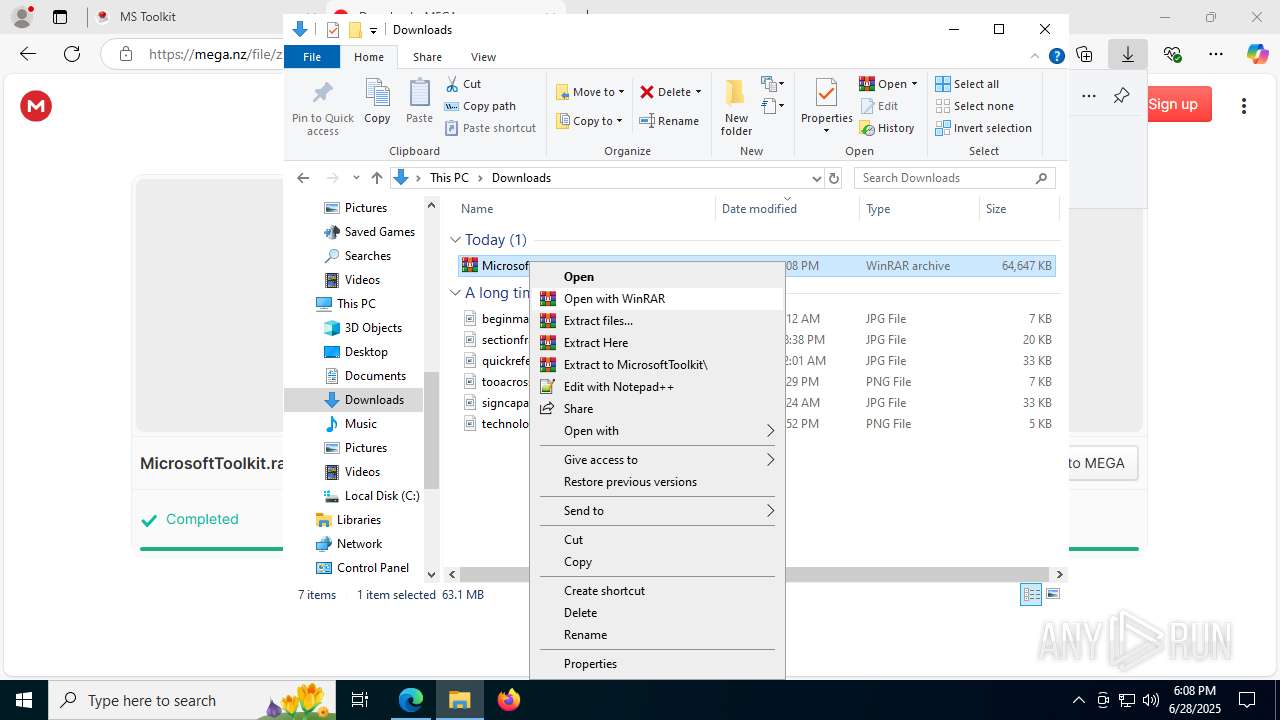
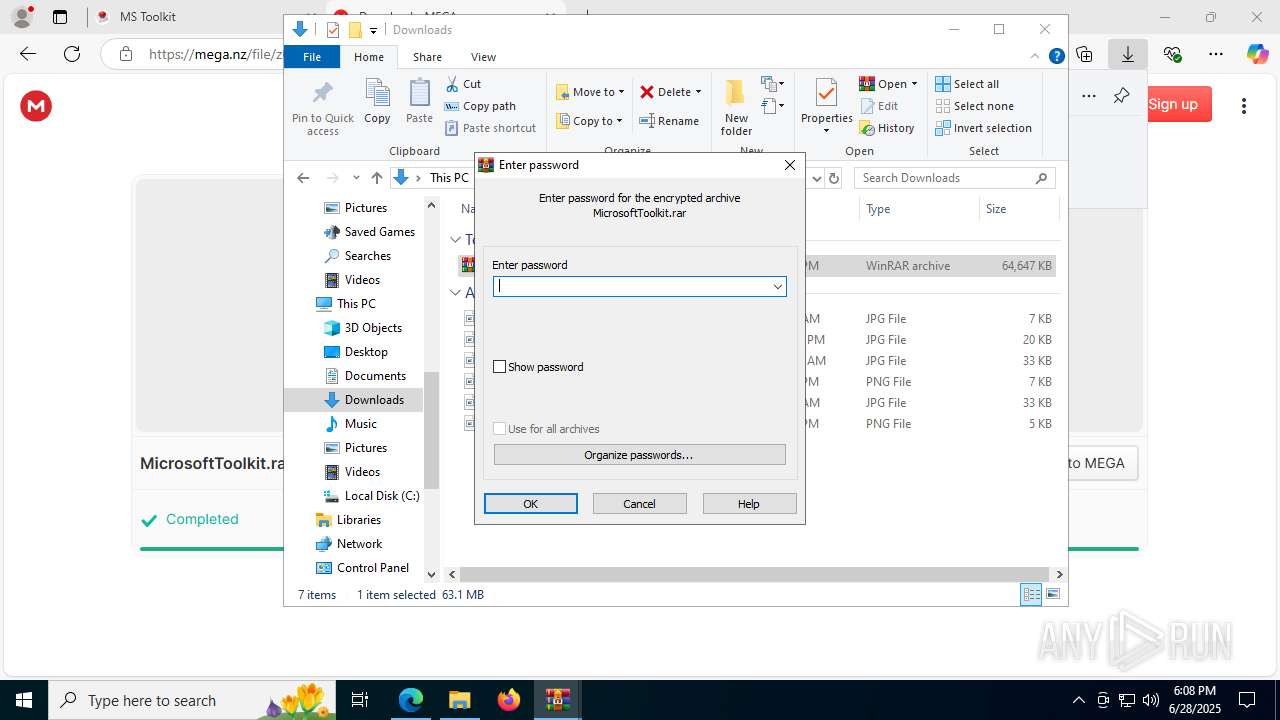
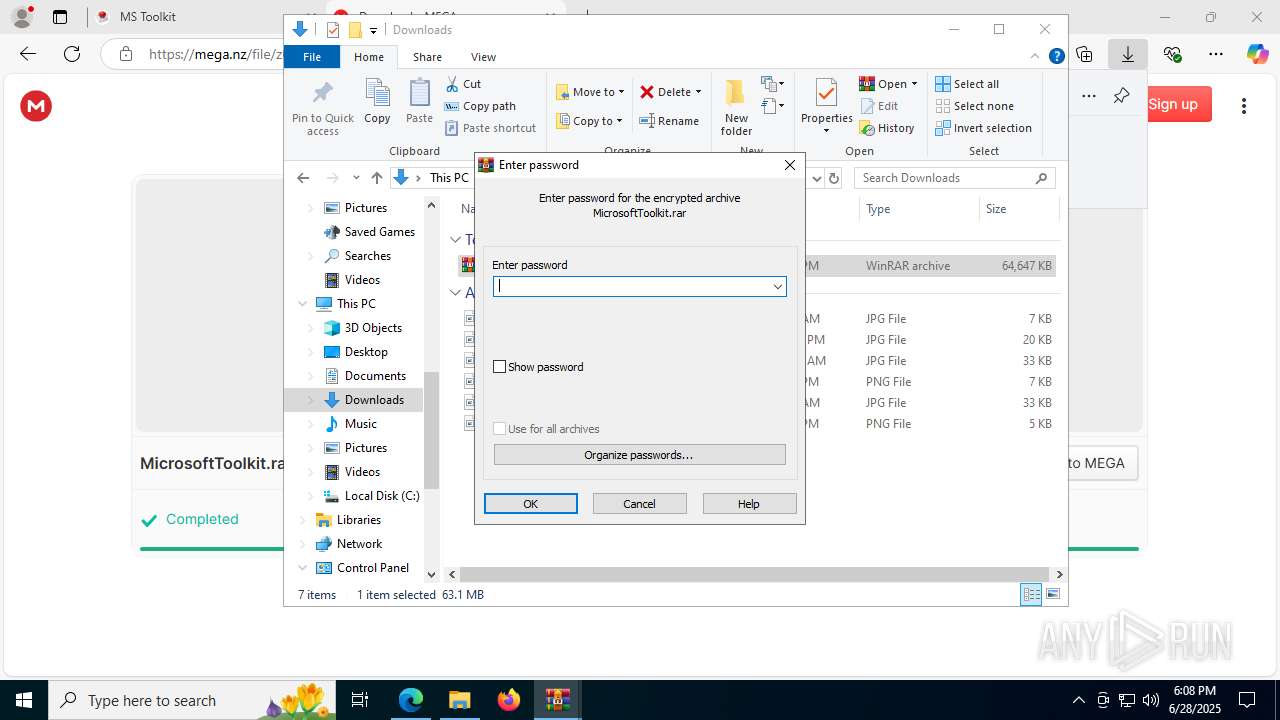
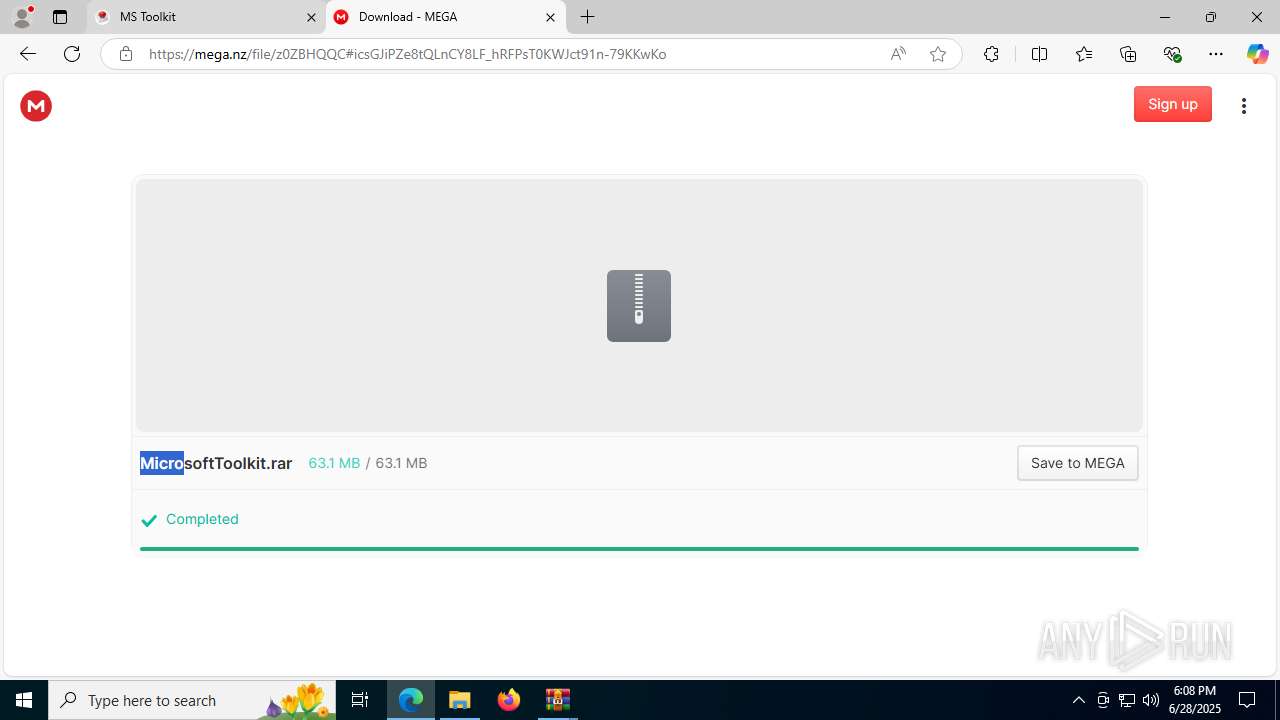
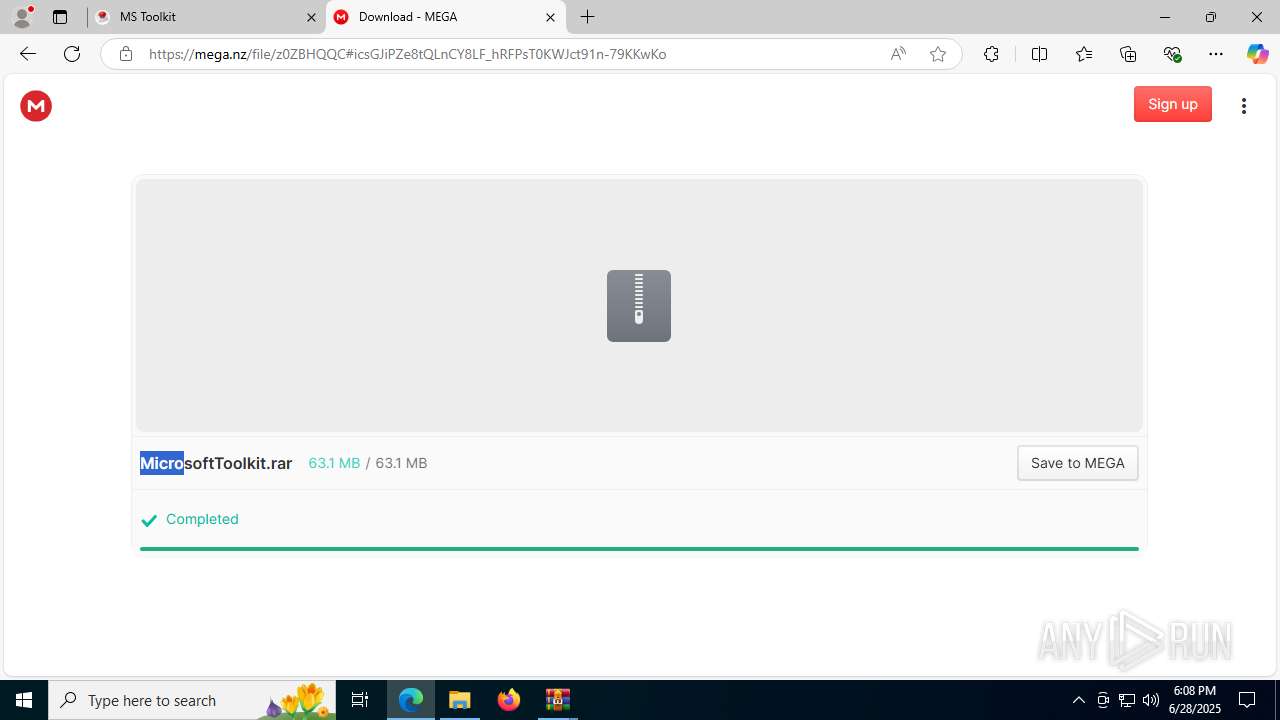
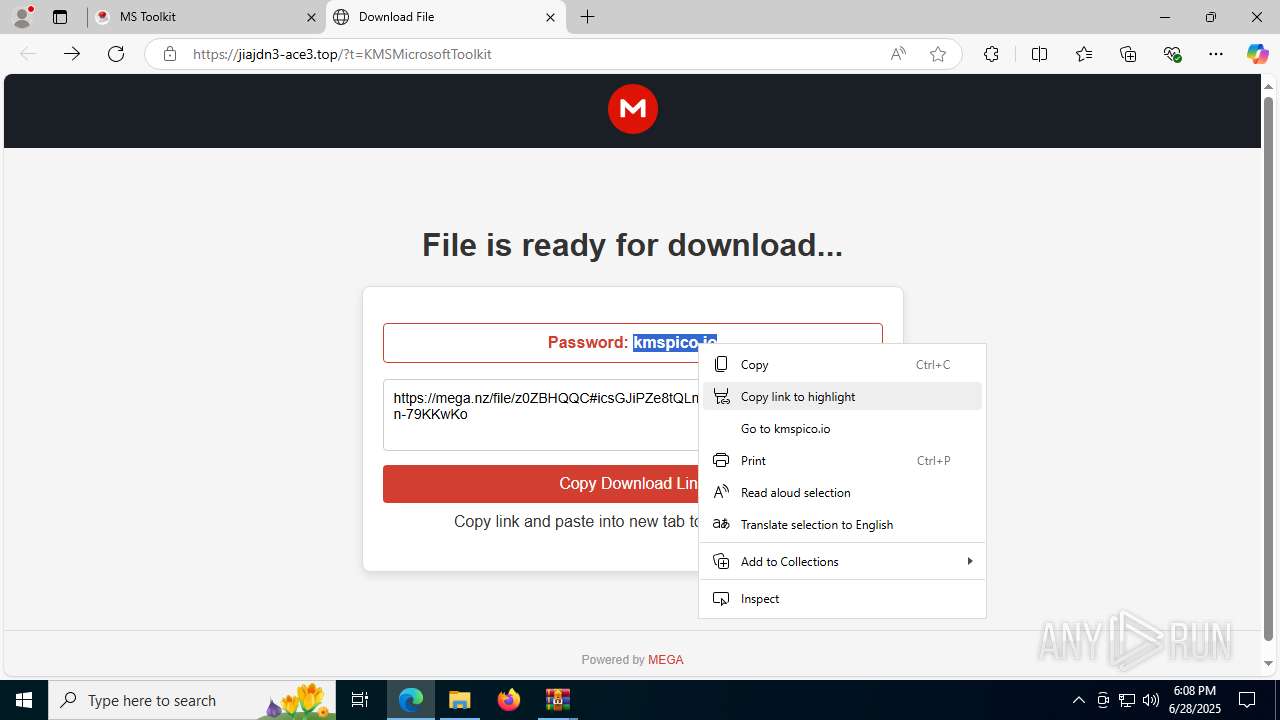
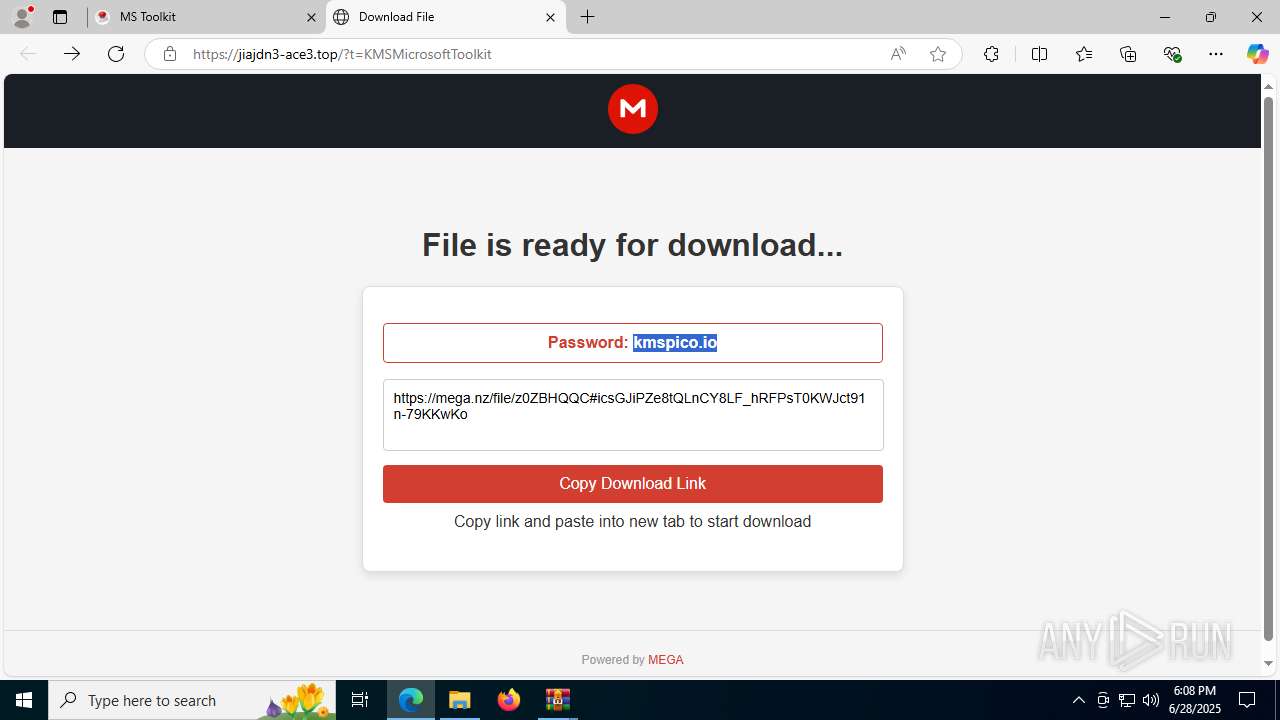
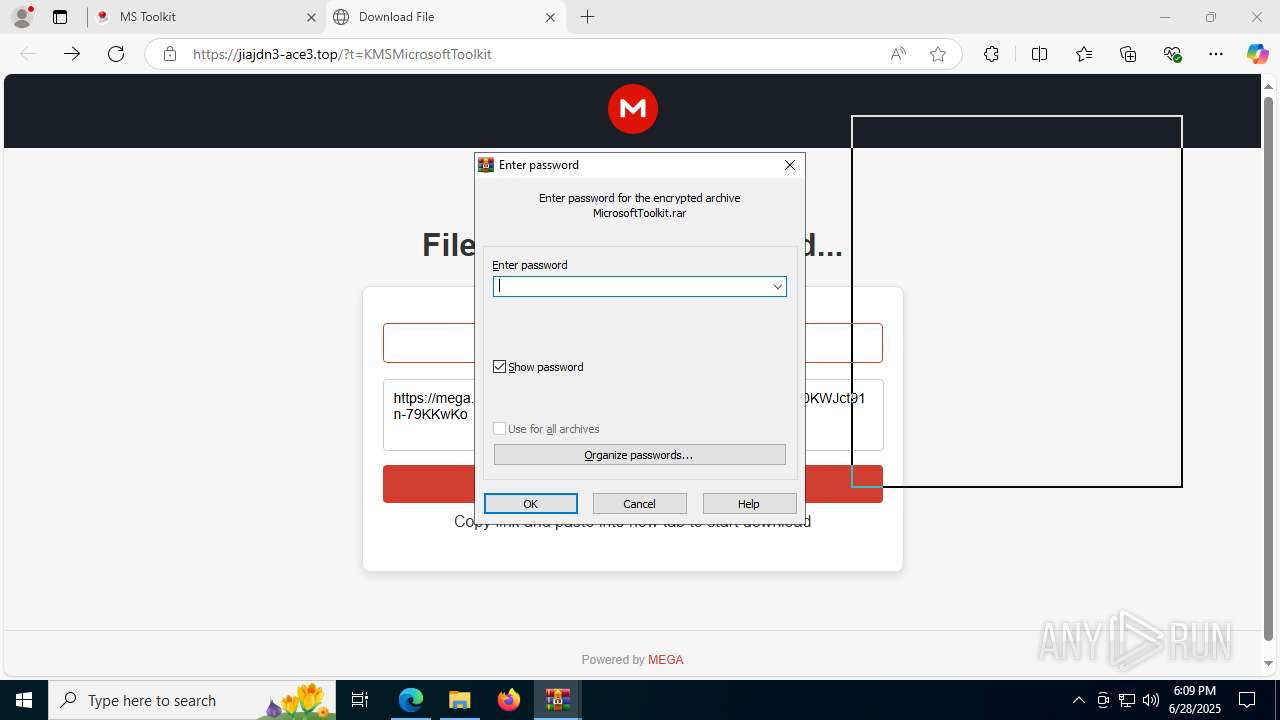
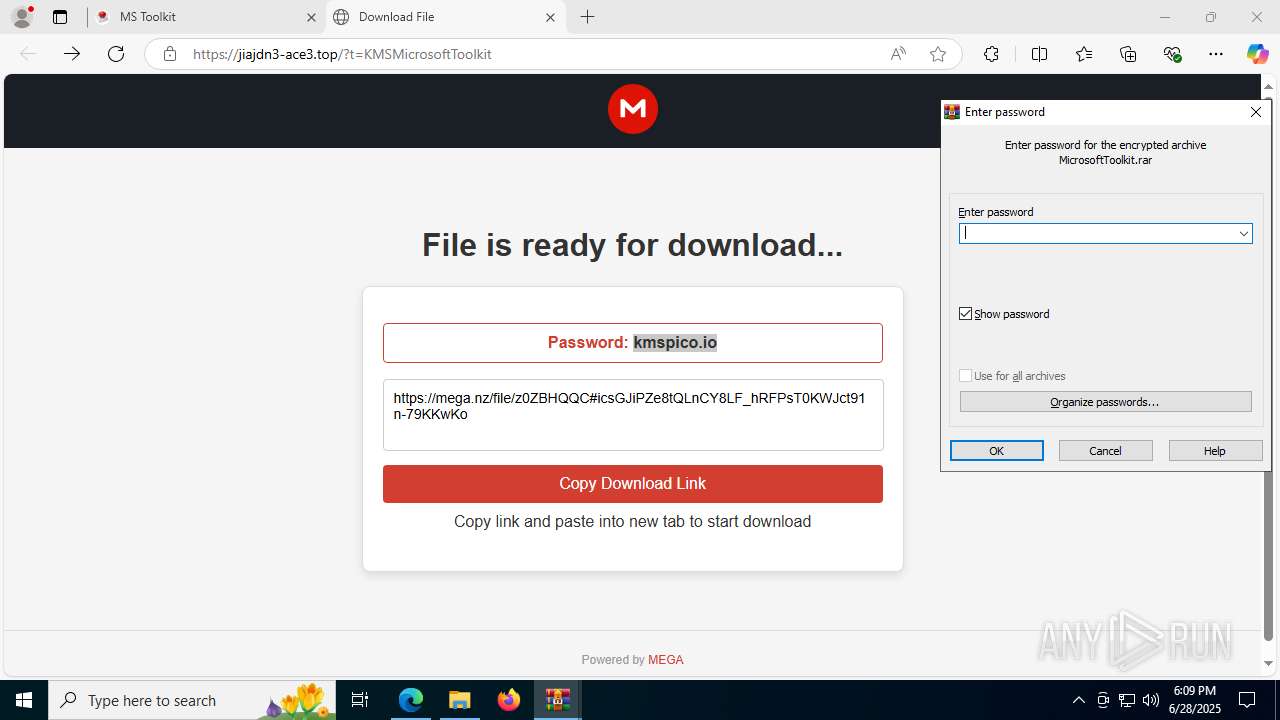
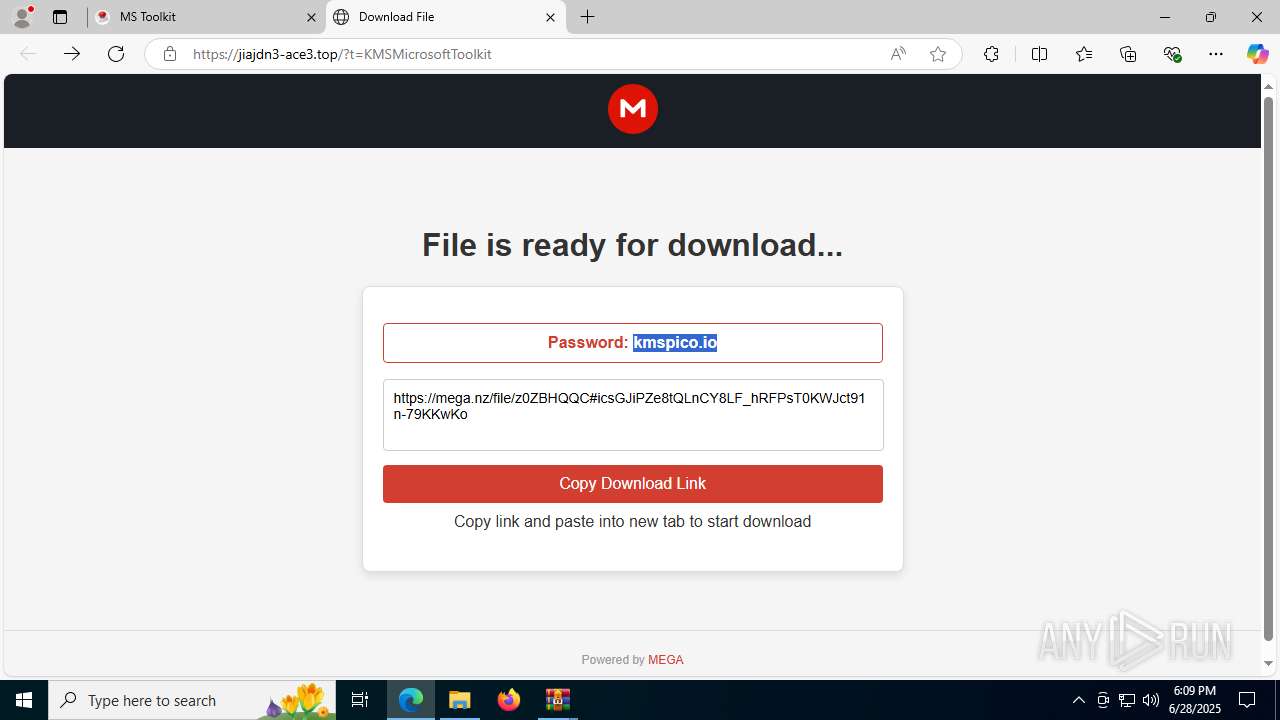
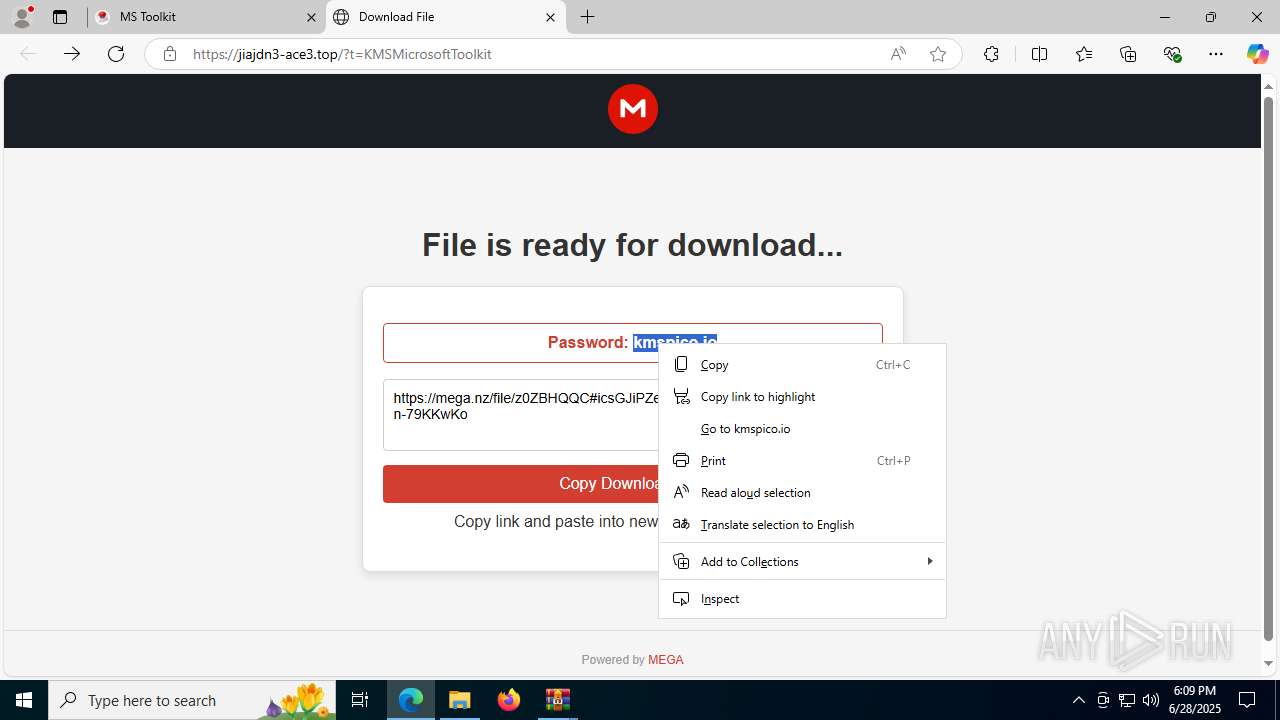
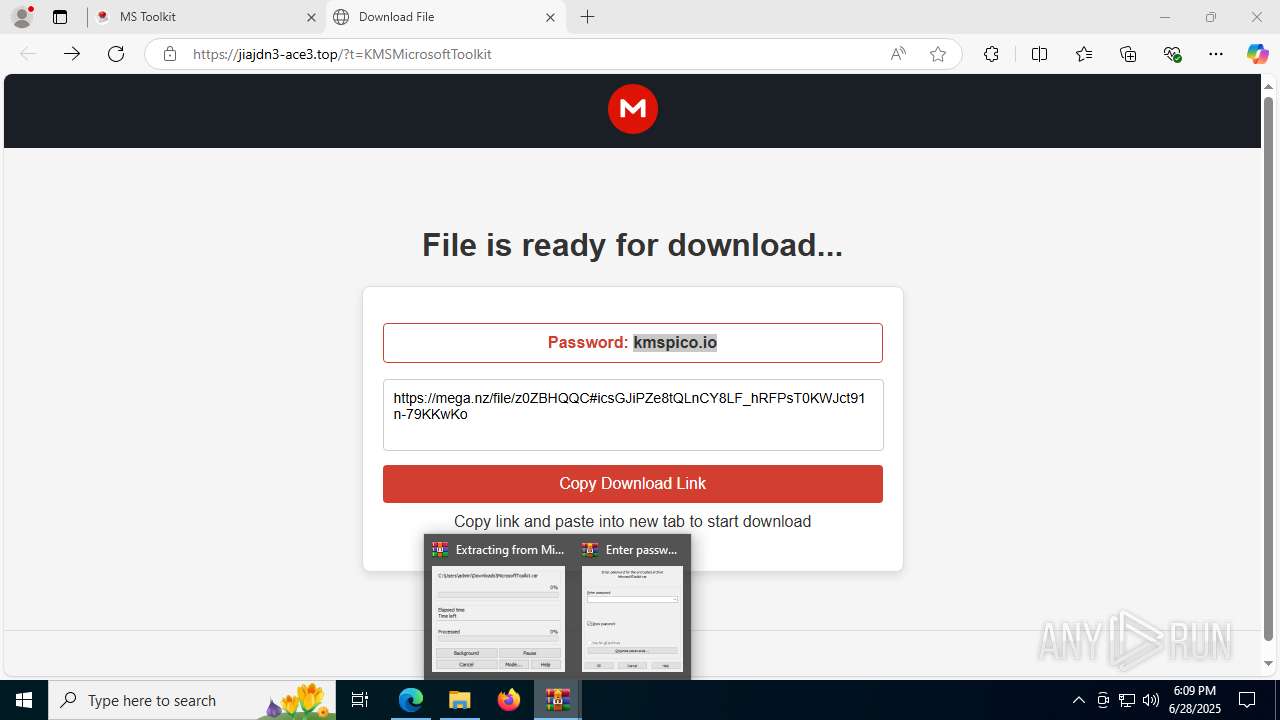
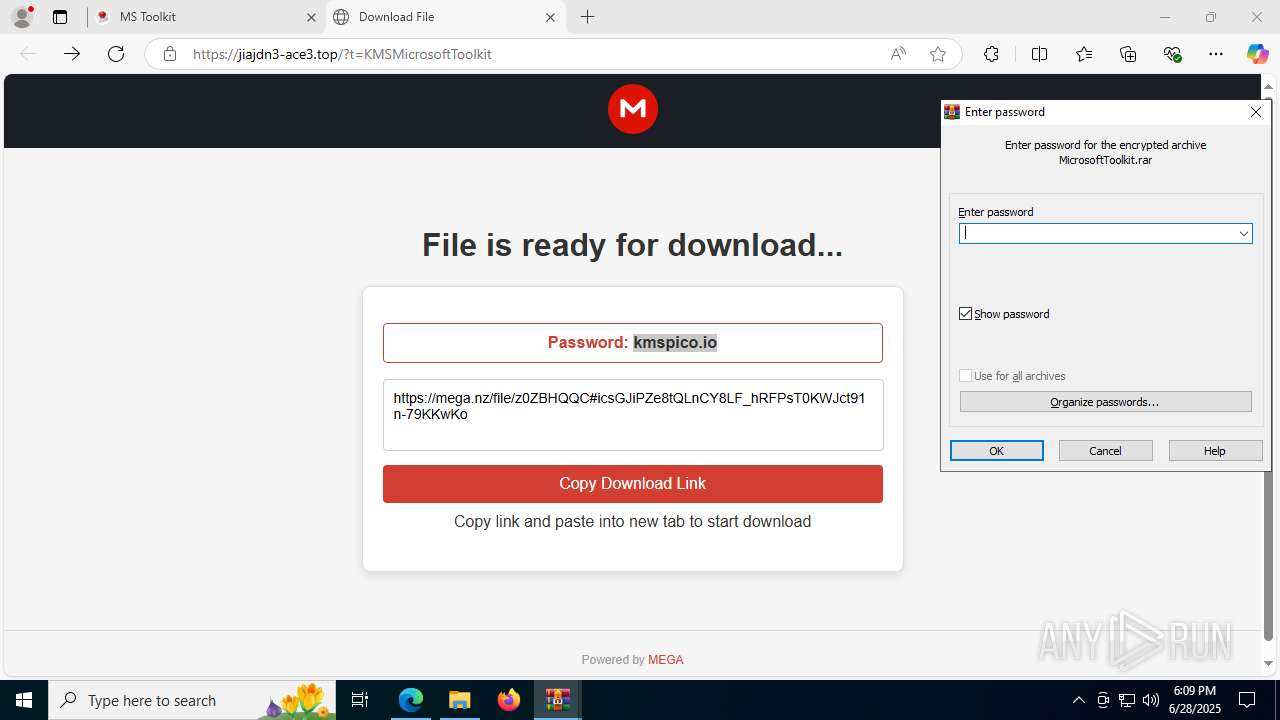
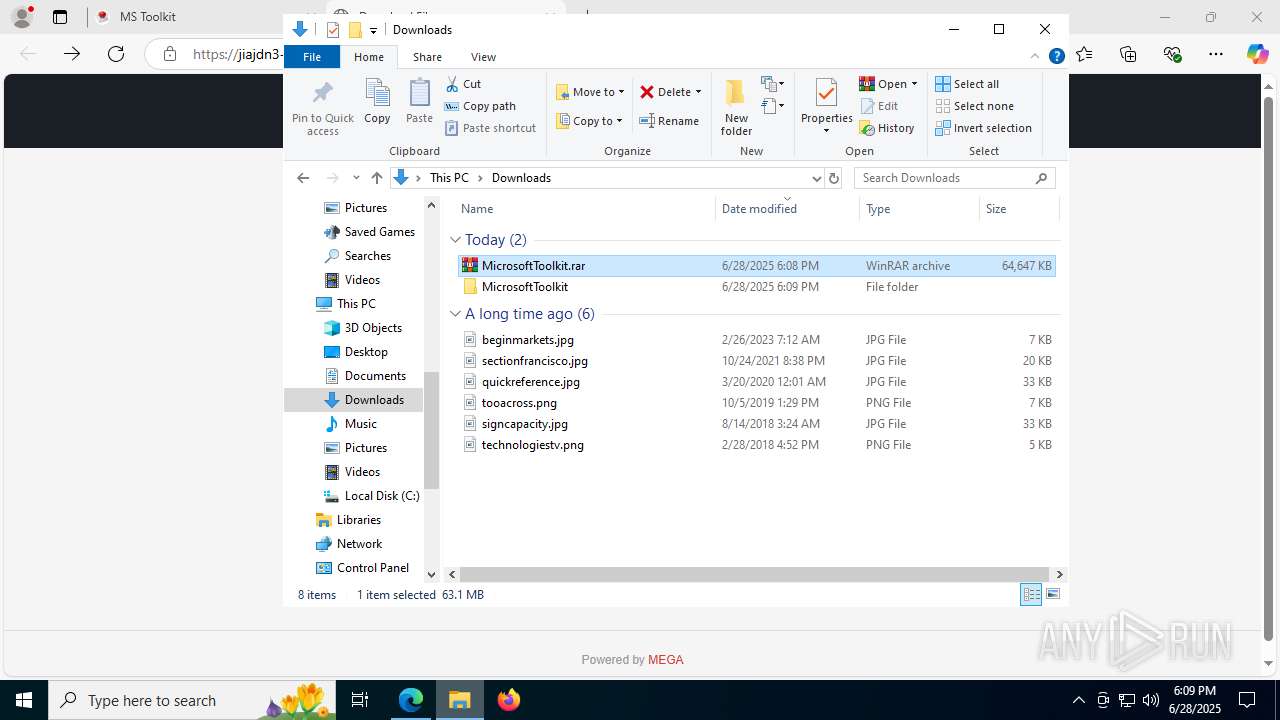
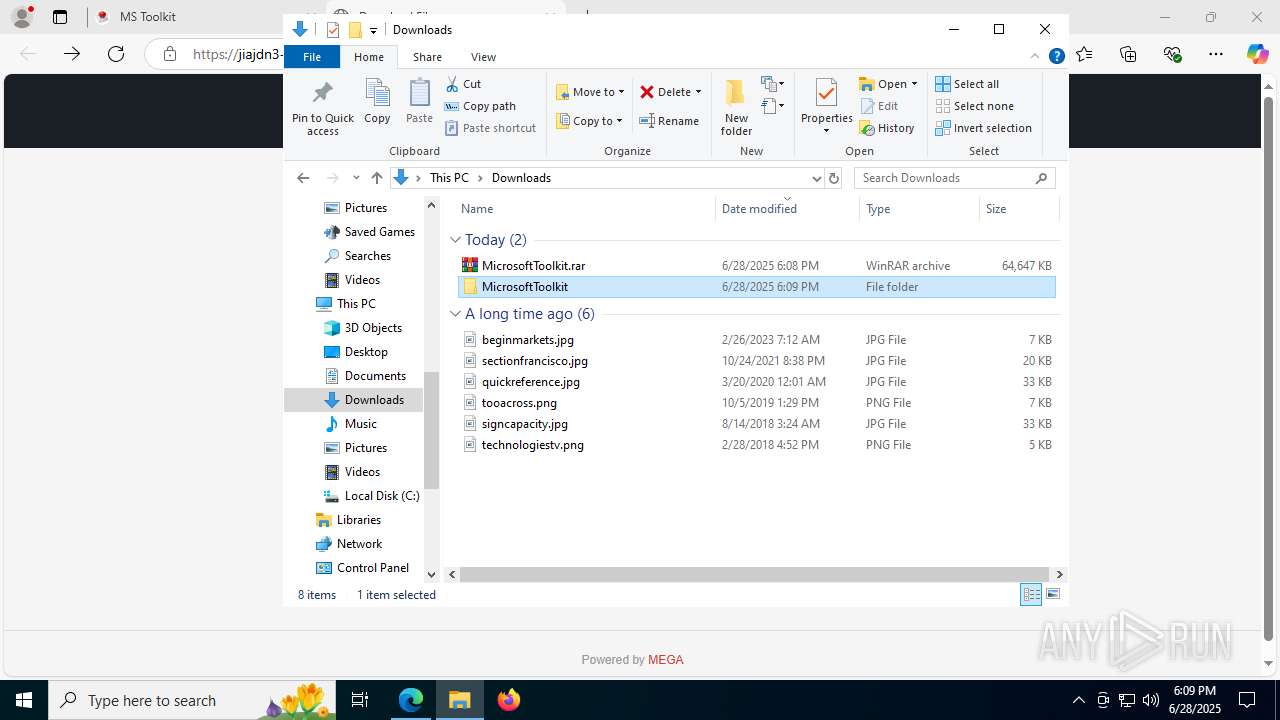
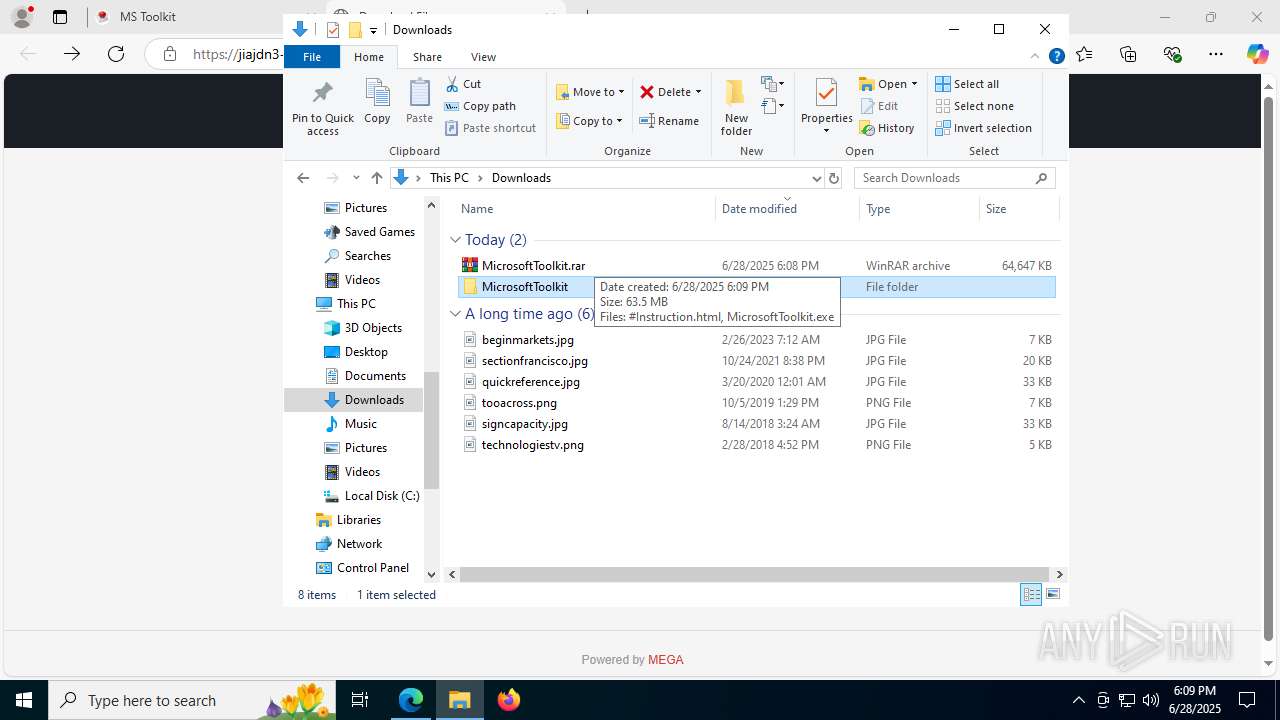
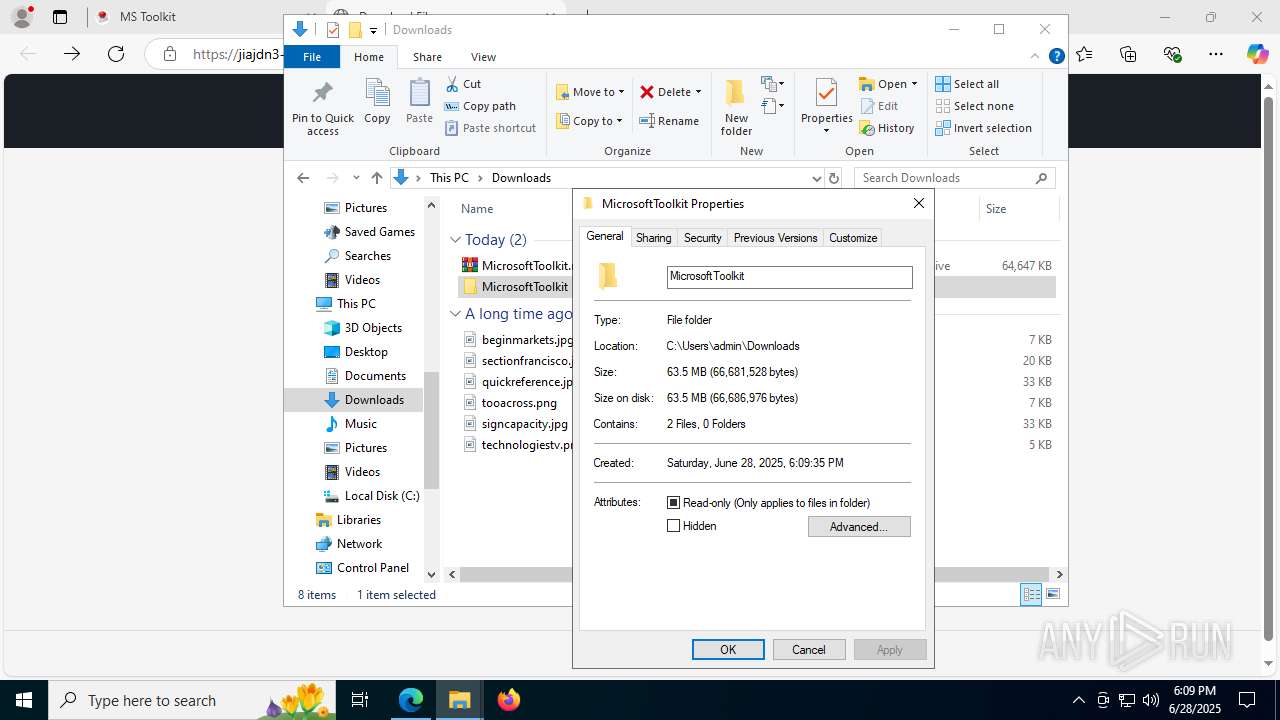
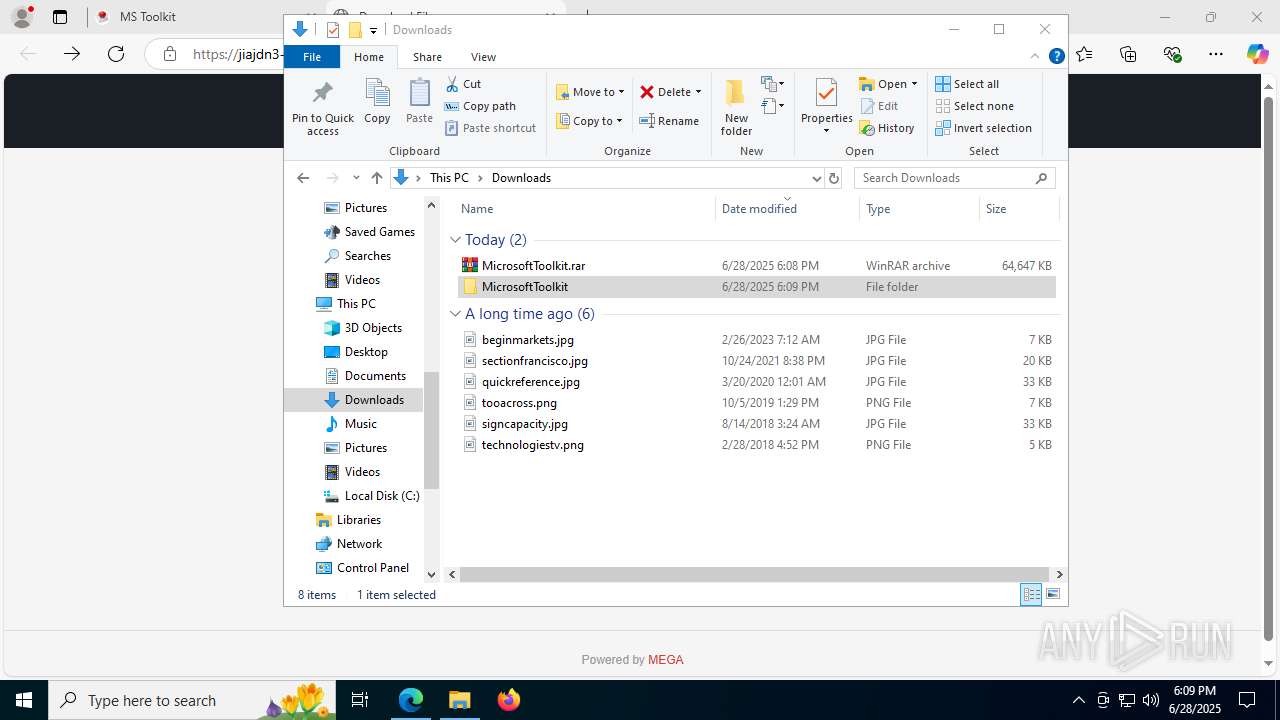
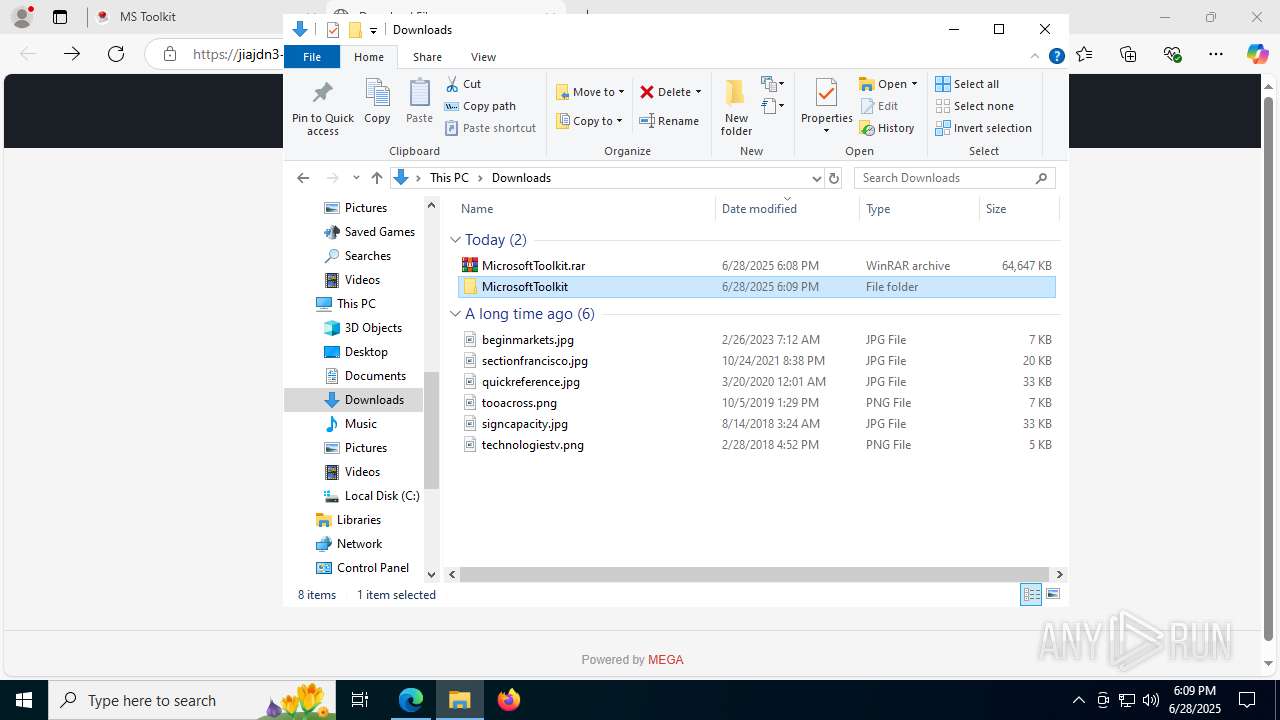
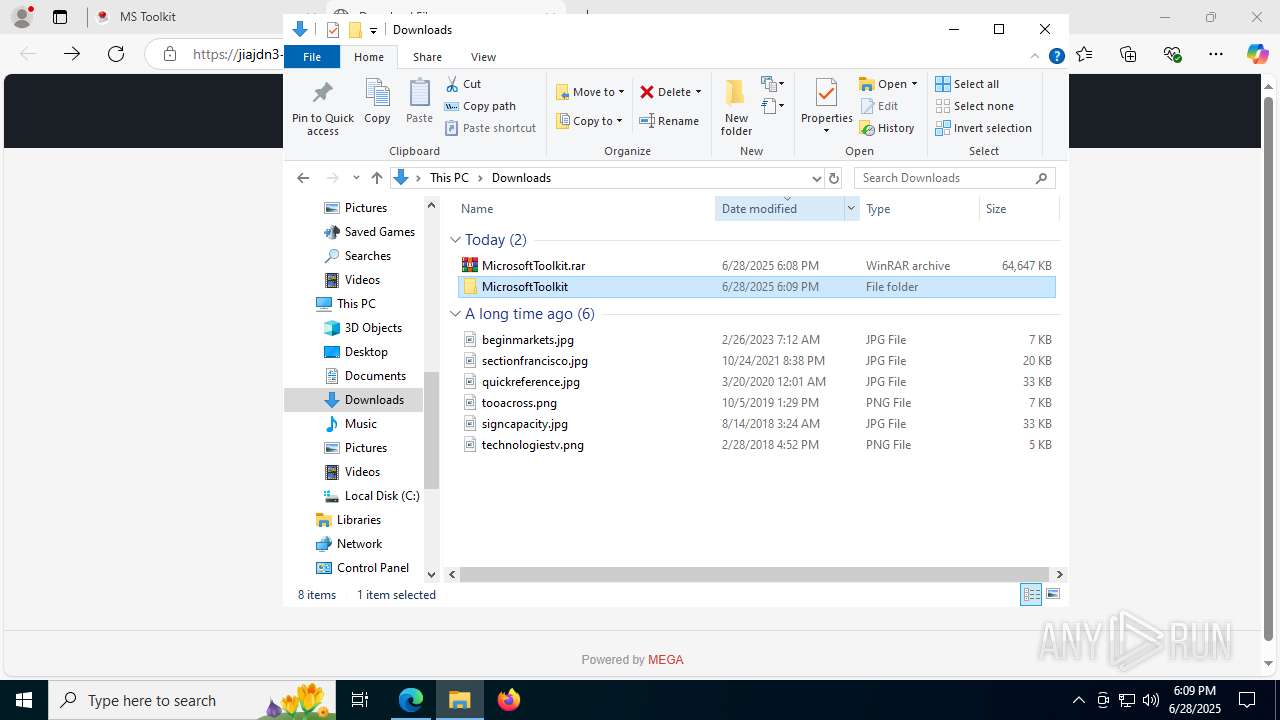
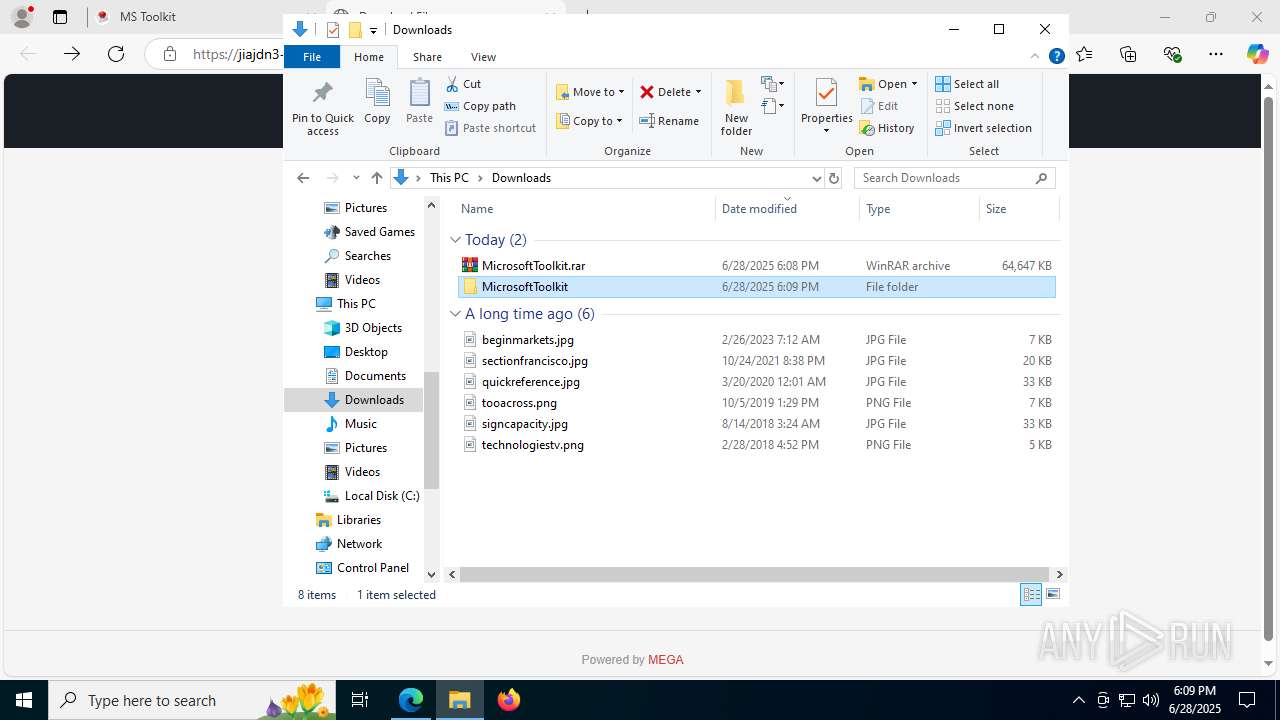
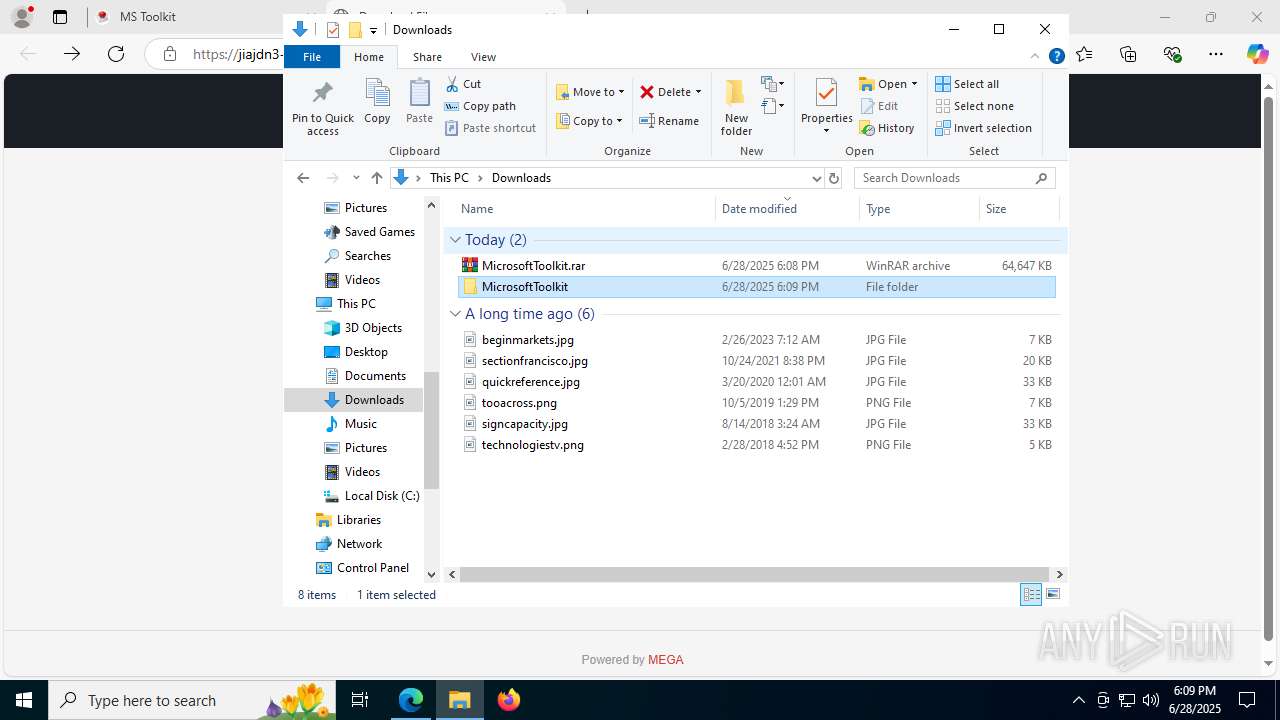
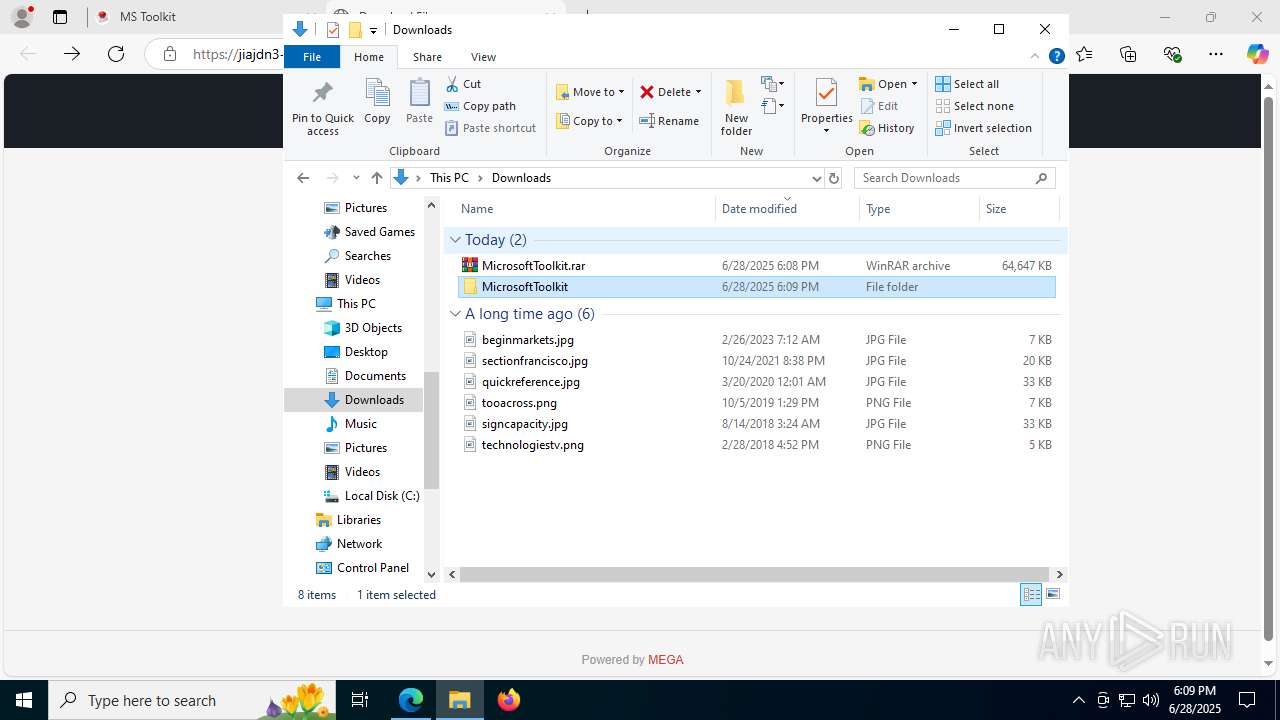
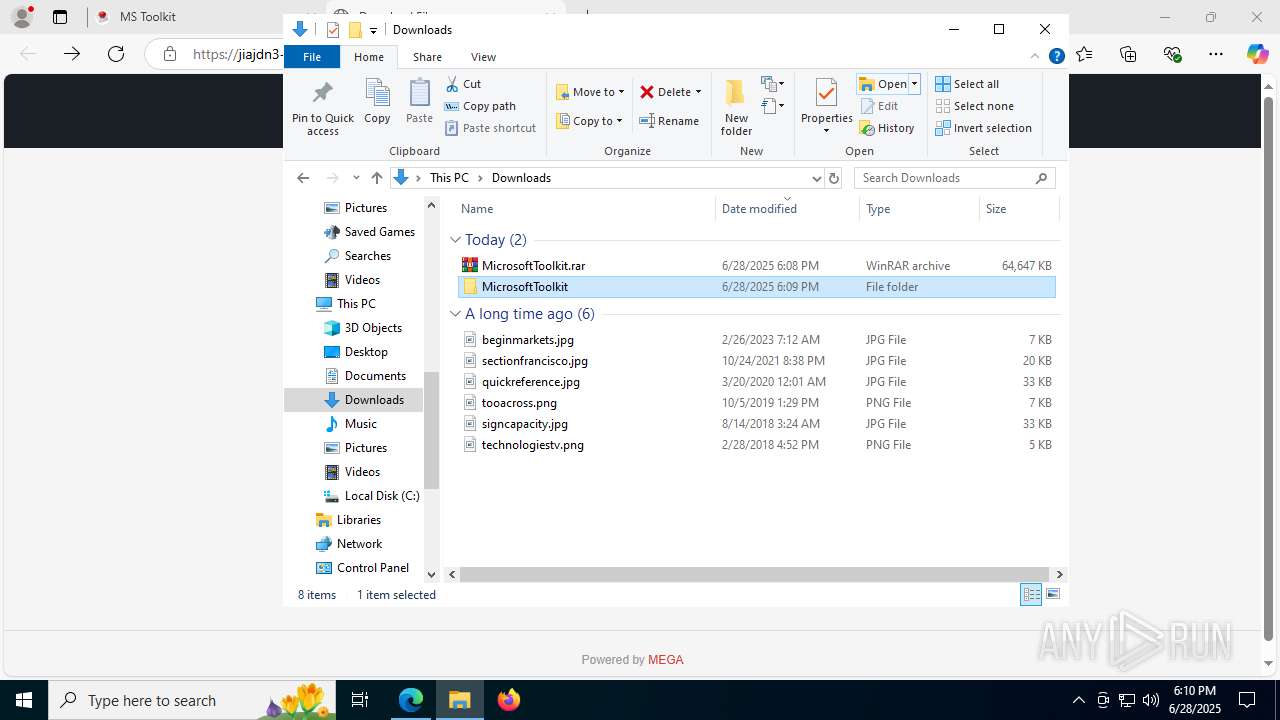
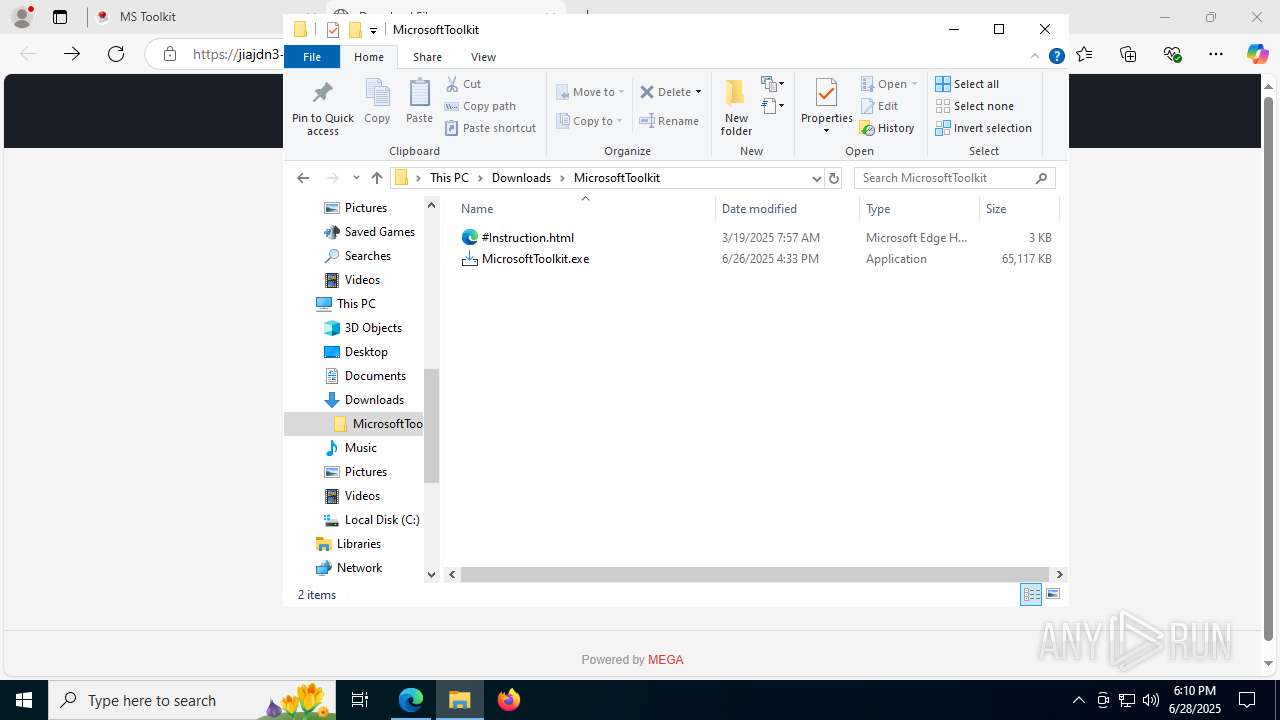
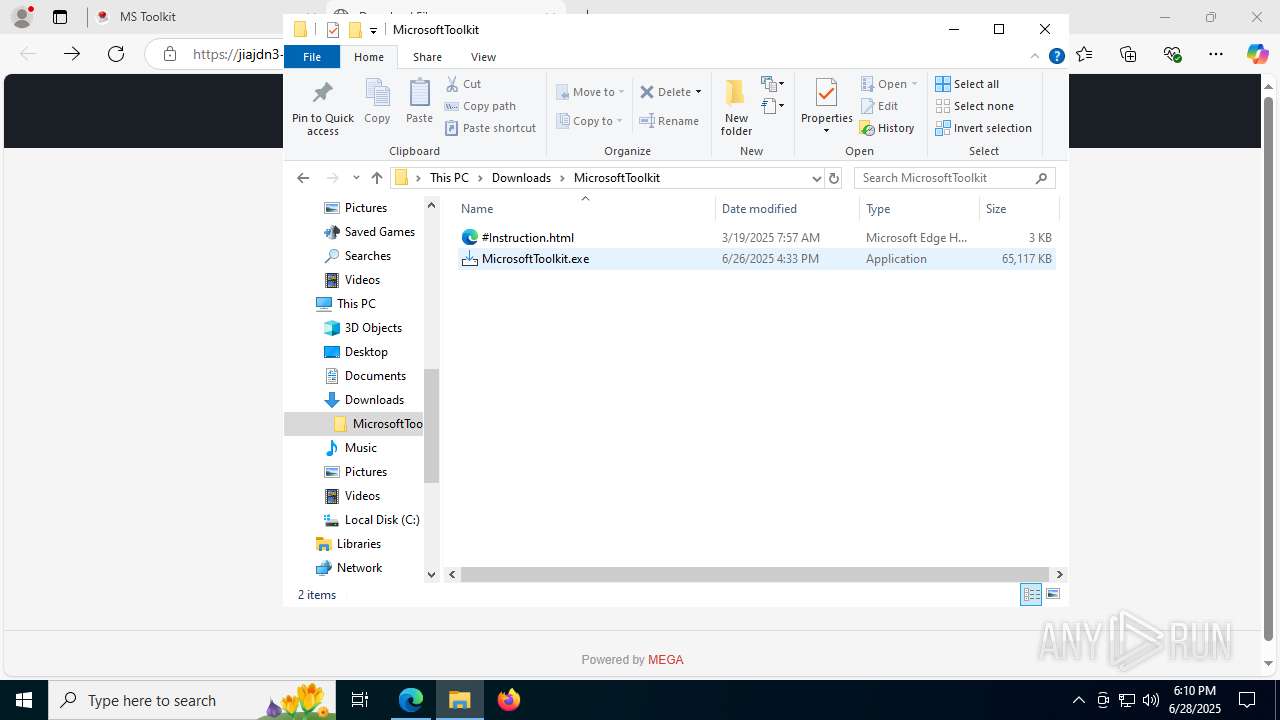
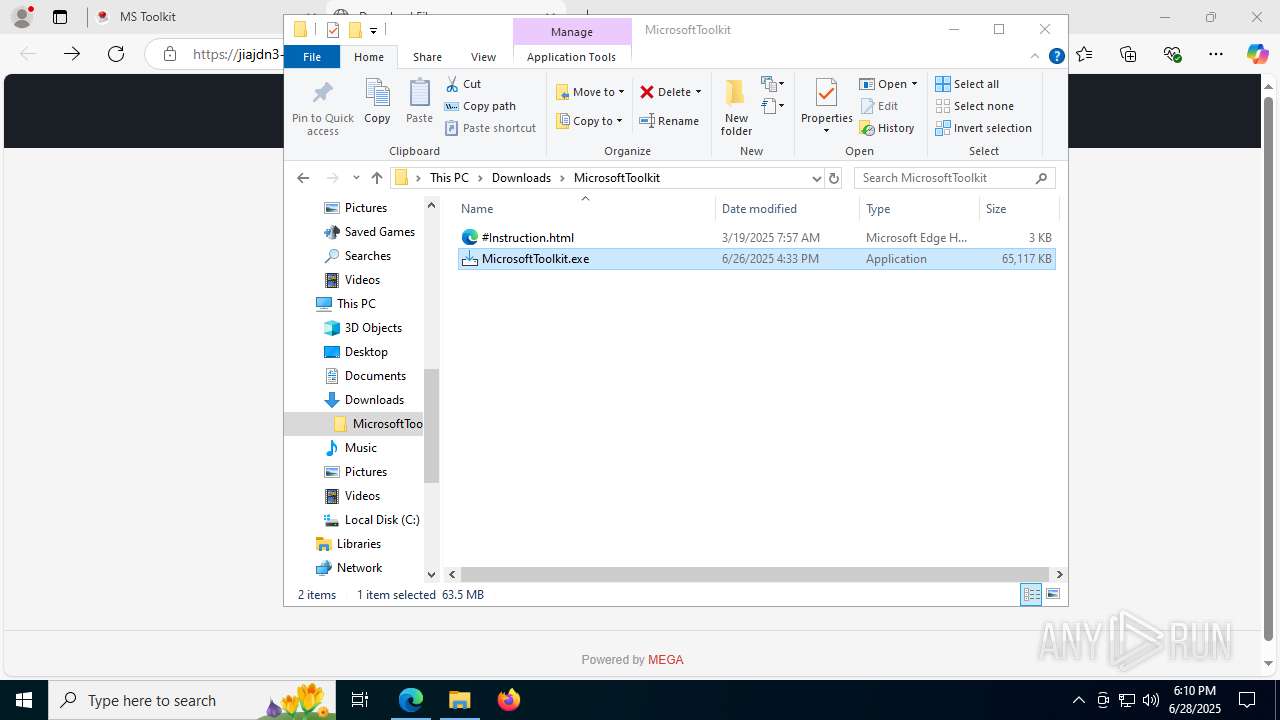
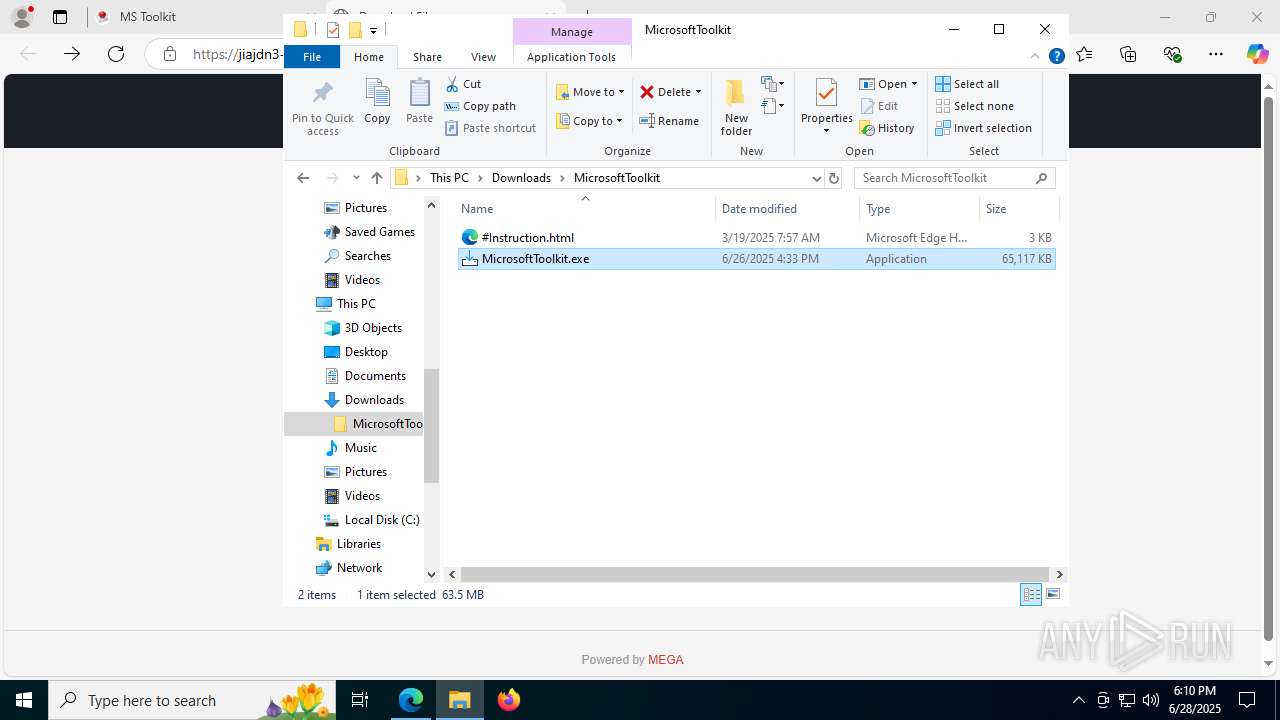
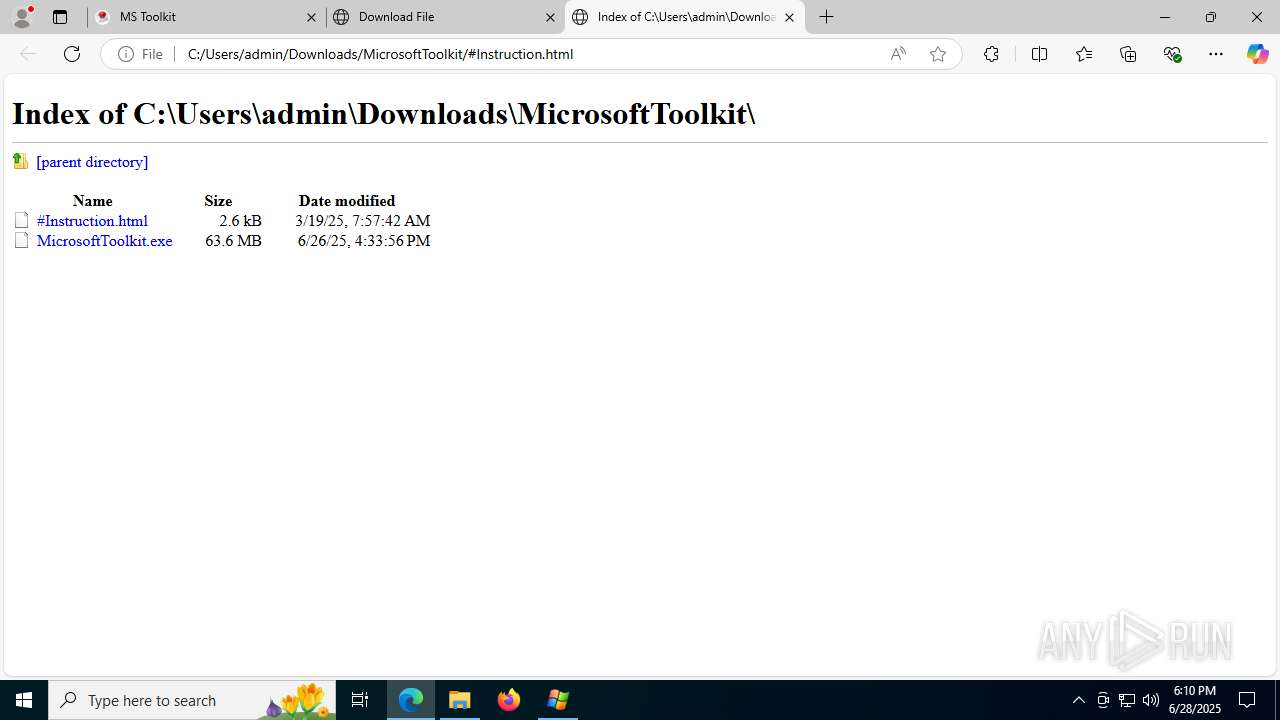
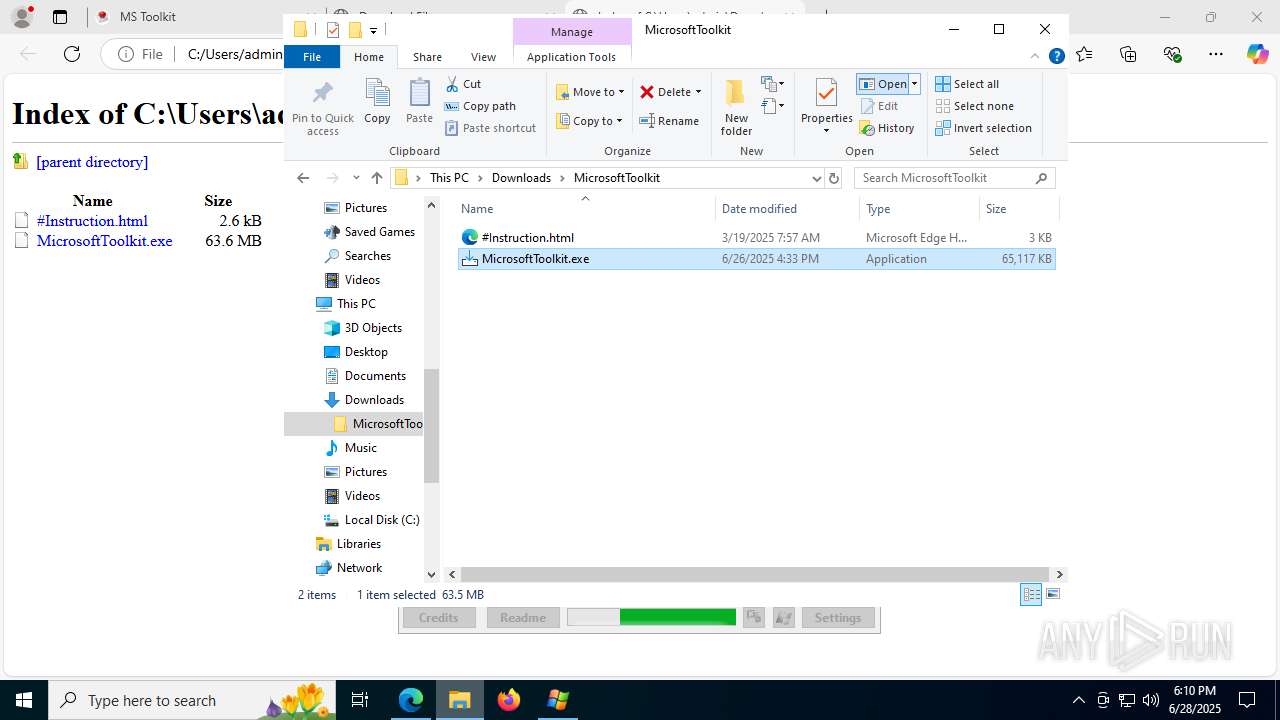
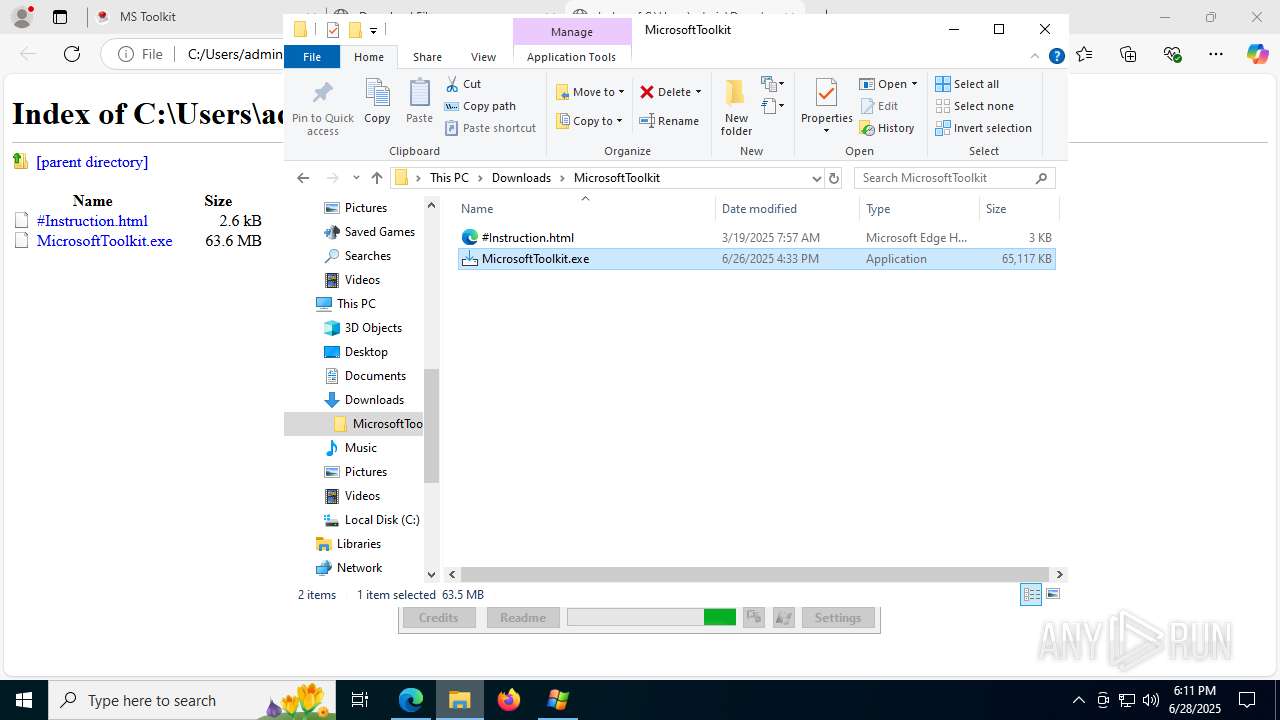
Manual execution by a user
- WinRAR.exe (PID: 8104)
- MicrosoftToolkit.exe (PID: 6812)
- iexplore.exe (PID: 7844)
- MicrosoftToolkit.exe (PID: 4804)
- MicrosoftToolkit.exe (PID: 4032)
Reads the software policy settings
- slui.exe (PID: 5444)
- core.exe (PID: 4236)
Create files in a temporary directory
- MicrosoftToolkit.tmp (PID: 7456)
- MicrosoftToolkit.exe (PID: 6812)
- MicrosoftToolkit.exe (PID: 6828)
- MicrosoftToolkit.exe (PID: 4804)
- MicrosoftToolkit.tmp (PID: 6812)
- MicrosoftToolkit.exe (PID: 4032)
- MicrosoftToolkit.tmp (PID: 7520)
Checks proxy server information
- slui.exe (PID: 5444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
217
Monitored processes
70
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 880 | C:\WINDOWS\system32\svchost.exe -k DcomLaunch -p | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 952 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6832,i,4908566101864608427,2224824862558775807,262144 --variations-seed-version --mojo-platform-channel-handle=1516 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7268,i,4908566101864608427,2224824862558775807,262144 --variations-seed-version --mojo-platform-channel-handle=7992 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=2764,i,4908566101864608427,2224824862558775807,262144 --variations-seed-version --mojo-platform-channel-handle=3664 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1288 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "kmspico.io" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4300,i,4908566101864608427,2224824862558775807,262144 --variations-seed-version --mojo-platform-channel-handle=4308 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=5496,i,4908566101864608427,2224824862558775807,262144 --variations-seed-version --mojo-platform-channel-handle=4936 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2760,i,4908566101864608427,2224824862558775807,262144 --variations-seed-version --mojo-platform-channel-handle=2776 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
15 476
Read events
15 352
Write events
106
Delete events
18
Modification events
| (PID) Process: | (2128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2128) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BD2DC9F43B972F00 | |||
| (PID) Process: | (2128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (880) svchost.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001_Classes\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppModel\SystemAppData\Microsoft.AAD.BrokerPlugin_cw5n1h2txyewy\HAM\AUI\App\V1\LU |
| Operation: | write | Name: | PCT |
Value: EAE92E9057E8DB01 | |||
| (PID) Process: | (2128) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262924 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E584A98C-2FF3-4E2A-8D77-D213375F6CB9} | |||
| (PID) Process: | (880) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\TermReason\5848 |
| Operation: | write | Name: | Terminator |
Value: HAM | |||
| (PID) Process: | (880) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\TermReason\5848 |
| Operation: | write | Name: | Reason |
Value: 4 | |||
| (PID) Process: | (880) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\TermReason\5848 |
| Operation: | write | Name: | CreationTime |
Value: A5CF4B9057E8DB01 | |||
Executable files
22
Suspicious files
235
Text files
148
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF175eaa.TMP | — | |
MD5:— | SHA256:— | |||
| 2128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF175eaa.TMP | — | |
MD5:— | SHA256:— | |||
| 2128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF175eba.TMP | — | |
MD5:— | SHA256:— | |||
| 2128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF175ed9.TMP | — | |
MD5:— | SHA256:— | |||
| 2128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF175f08.TMP | — | |
MD5:— | SHA256:— | |||
| 2128 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
159
TCP/UDP connections
163
DNS requests
141
Threats
56
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2716 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:ejkvYwXWNVDpcTyqWnK25HQU4p9b8-dXeSULOFDky0I&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2716 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/ | unknown | — | — | malicious |
2716 | msedge.exe | GET | 404 | 45.12.1.24:80 | http://kmspico.io/favicon.ico | unknown | — | — | malicious |
2716 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/ | unknown | — | — | malicious |
2716 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/siteground-optimizer-assets/siteground-optimizer-combined-css-62662e05aff056c88166fa7d7ece4742.css | unknown | — | — | malicious |
2716 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/themes/acabado/css/defer-style-min-width768.min.css?ver=1.4.0 | unknown | — | — | malicious |
1268 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2716 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/themes/acabado/css/defer-style-min-width960.min.css?ver=1.4.0 | unknown | — | — | malicious |
2716 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/themes/acabado/css/defer-style-min-width1200.min.css?ver=1.4.0 | unknown | — | — | malicious |
2716 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/2022/05/KMSPico-Download-The-Official-KMS-Activator-Website.png | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5504 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2716 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2716 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2716 | msedge.exe | 45.12.1.24:80 | kmspico.io | Virtual Systems LLC | UA | malicious |
2716 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2716 | msedge.exe | 45.12.1.24:443 | kmspico.io | Virtual Systems LLC | UA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
kmspico.io |
| malicious |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2716 | msedge.exe | Misc Attack | ET Threatview.io High Confidence Cobalt Strike C2 IP group 12 |
2716 | msedge.exe | Misc Attack | ET Threatview.io High Confidence Cobalt Strike C2 IP group 13 |
2716 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2716 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2716 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2716 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2716 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2716 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
2716 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
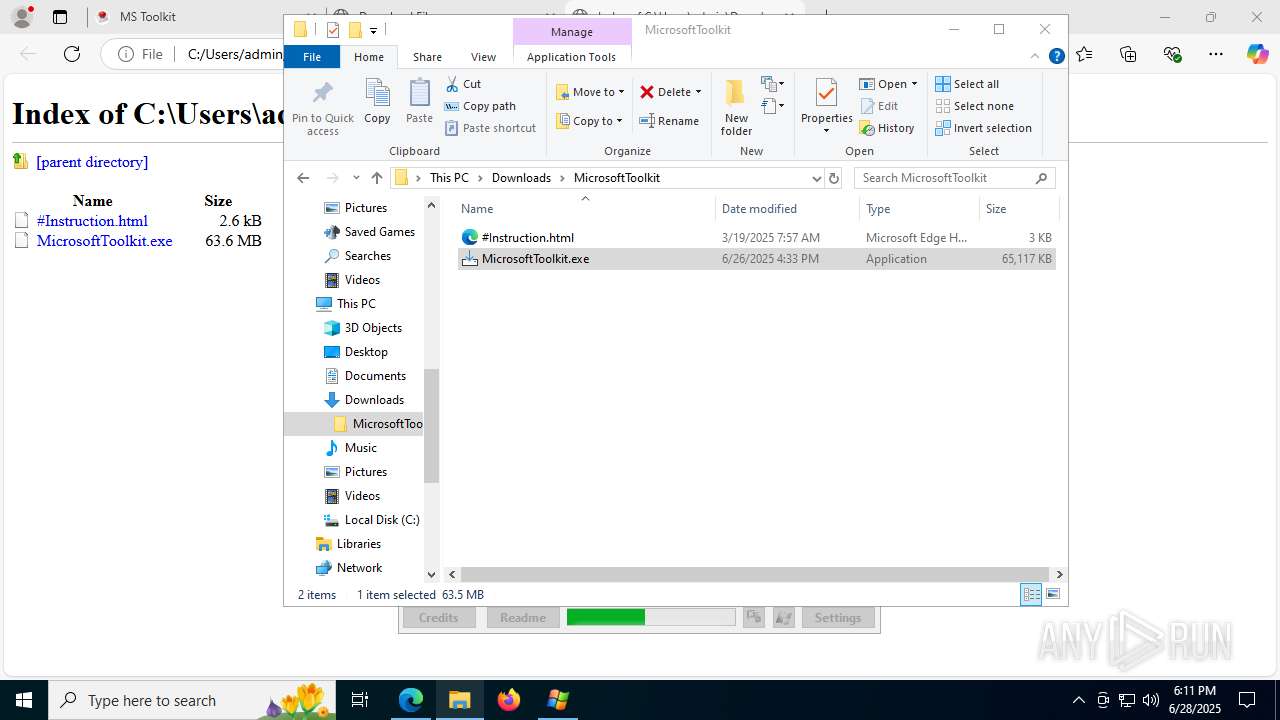
Process | Message |
|---|---|
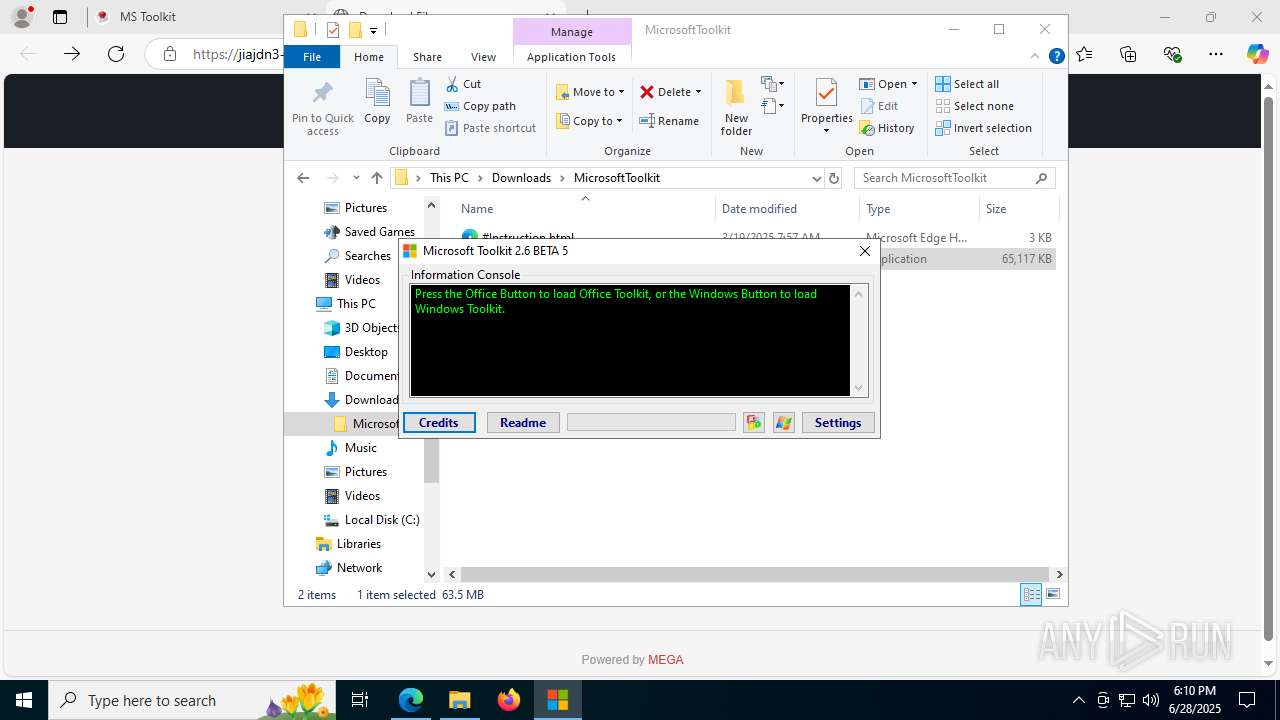
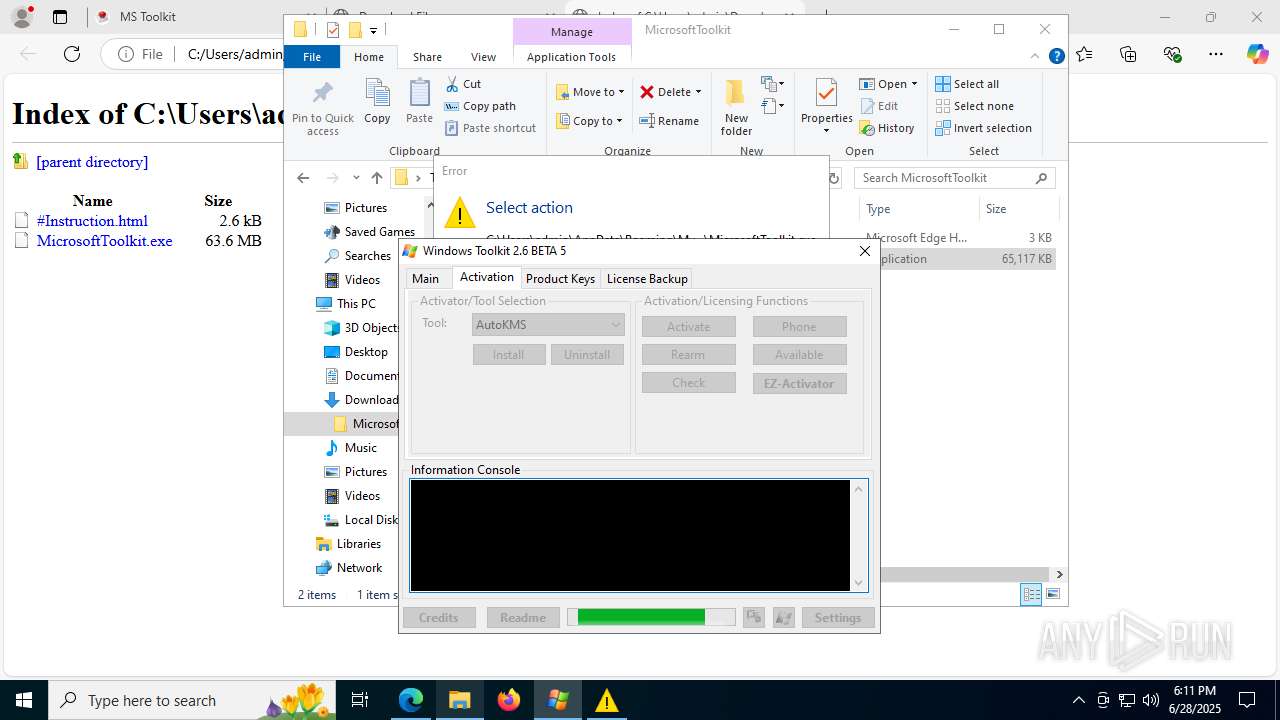
svchost.exe | [SppExtComObj Hook] v2.2 Microsoft Toolkit Edition | CODYQX4 & CyNecx | MDL |
svchost.exe | [SppExtComObj Hook B] Detected spawning process ... |
svchost.exe | [SppExtComObj Hook B] Loading Hook ... |
svchost.exe | [SppExtComObj Hook B] Hooking Success ... |
svchost.exe | [SppExtComObj Hook B] Dll Injection Success ... |
svchost.exe | [SppExtComObj Hook B] Resume process ... done... |
svchost.exe | [SppExtComObj Hook B] Suspeded process, injecting dll ... |
svchost.exe | [SppExtComObj Hook B] Detected process creation ... |
SppExtComObj.Exe | [SppExtComObj Hook A] Hooking Success ... |
SppExtComObj.Exe | [SppExtComObj Hook] v2.2 Microsoft Toolkit Edition | CODYQX4 & CyNecx | MDL |