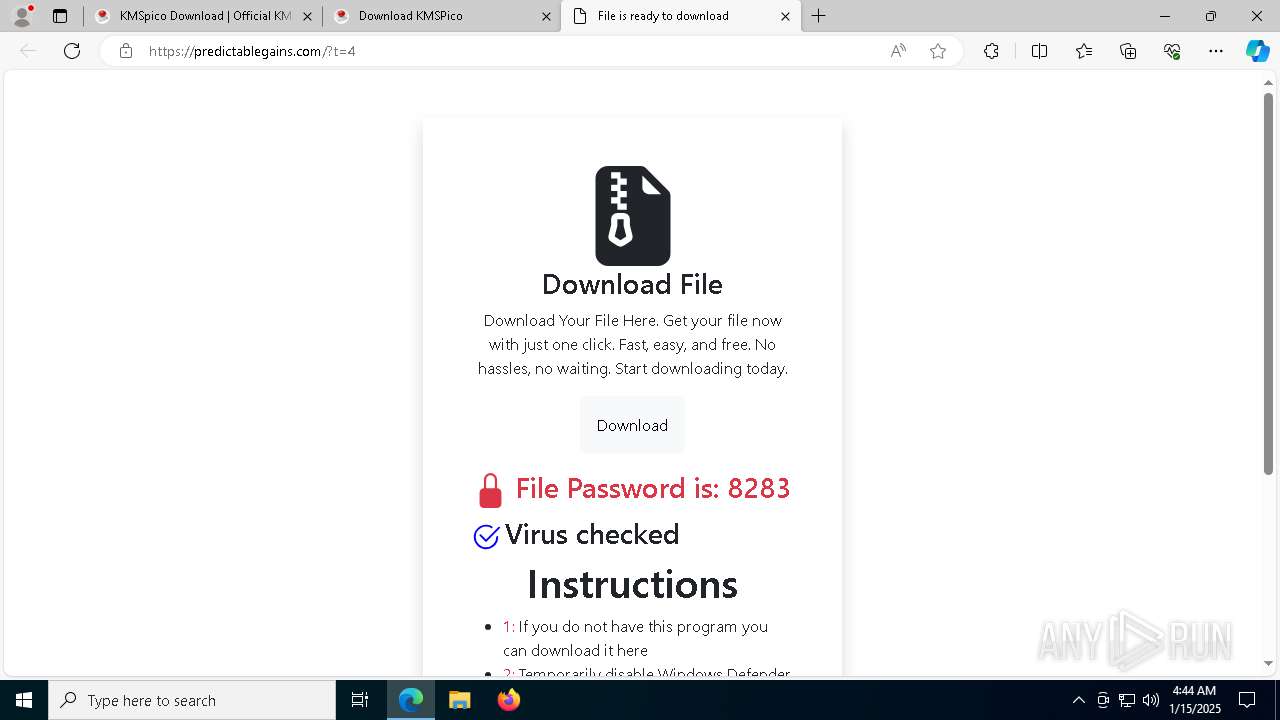
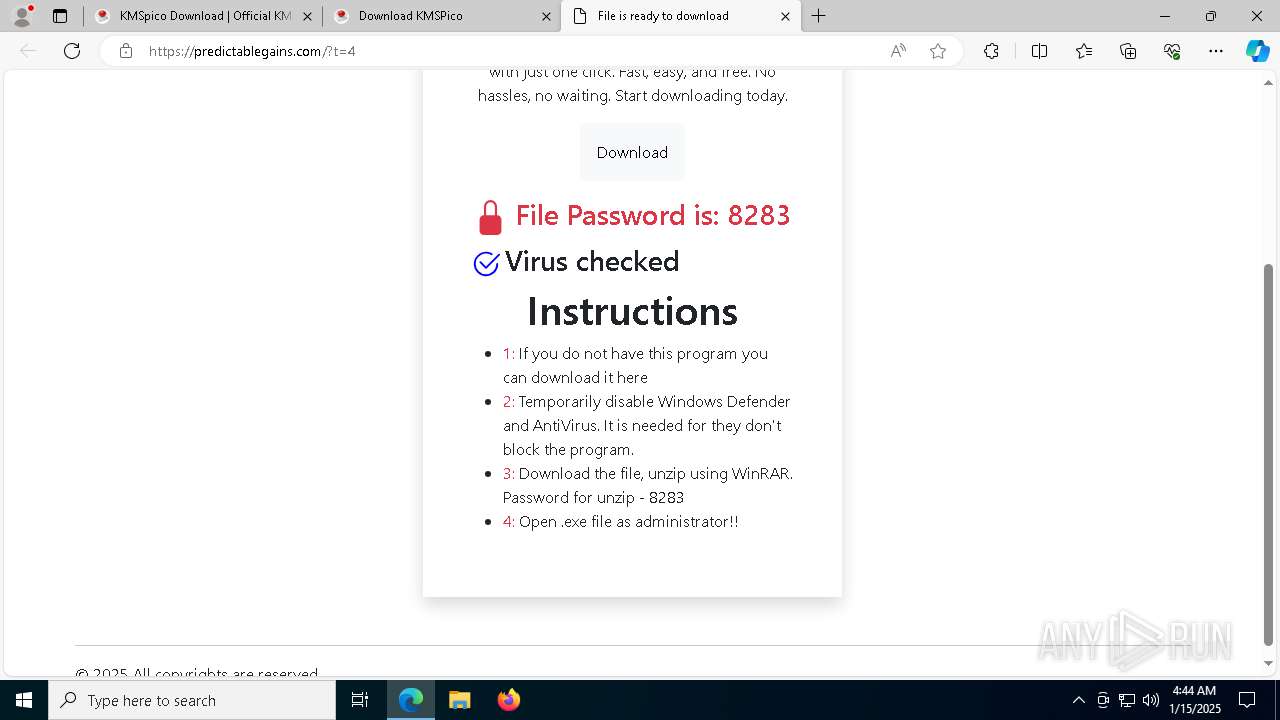
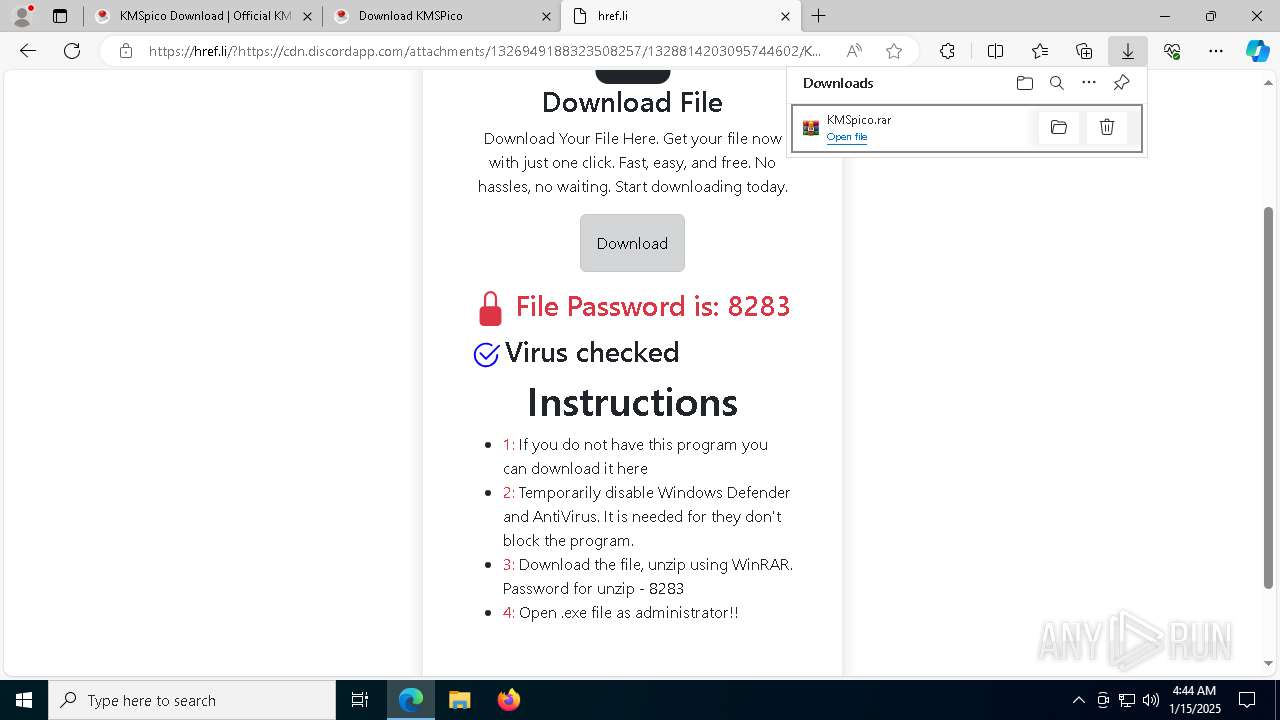
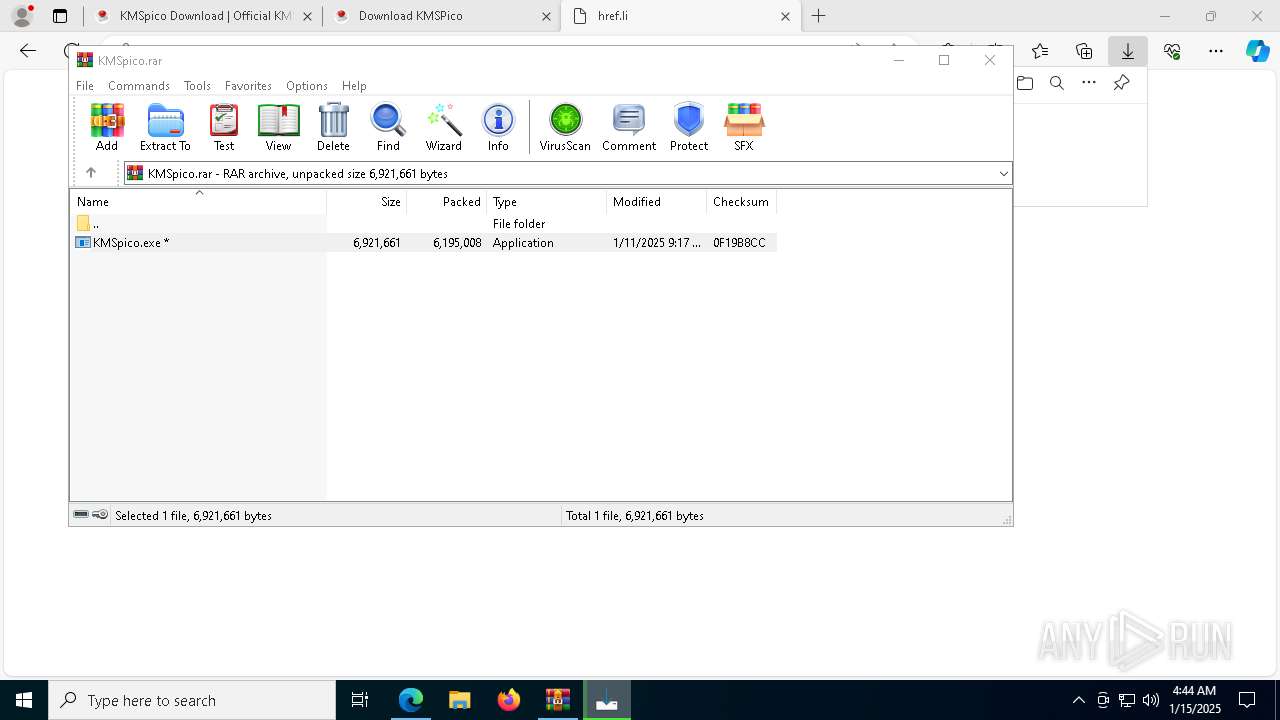
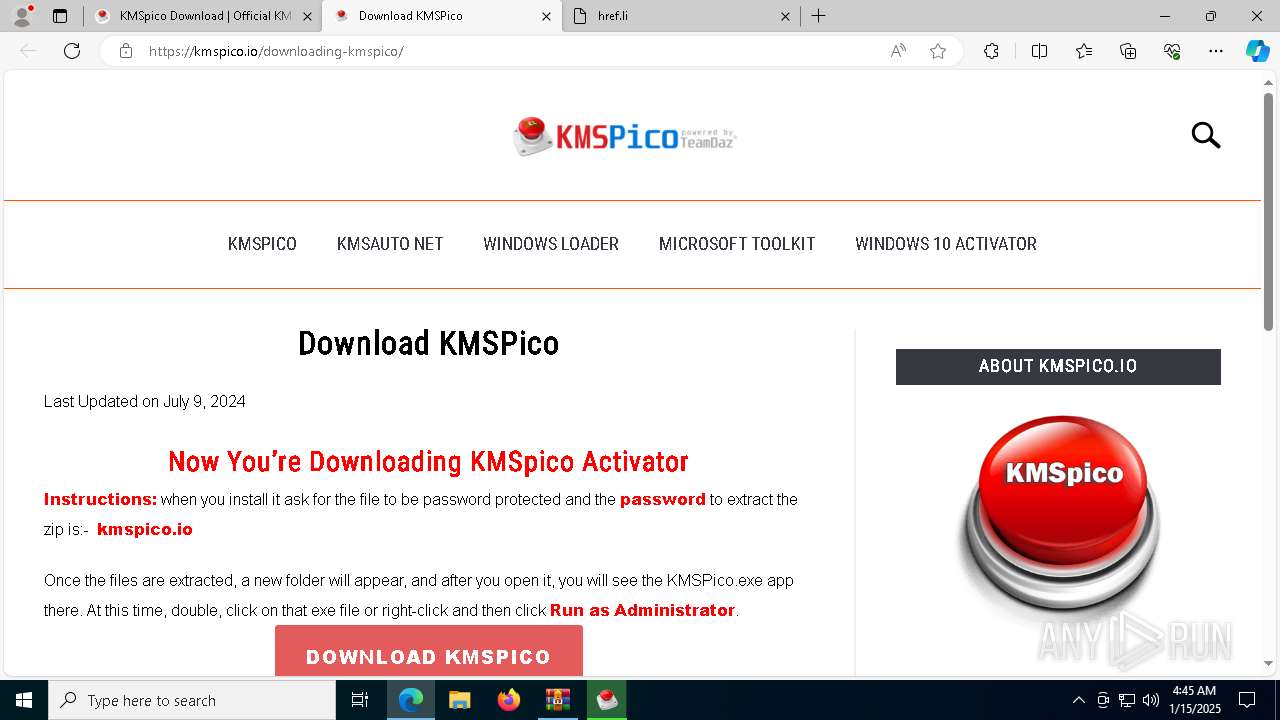
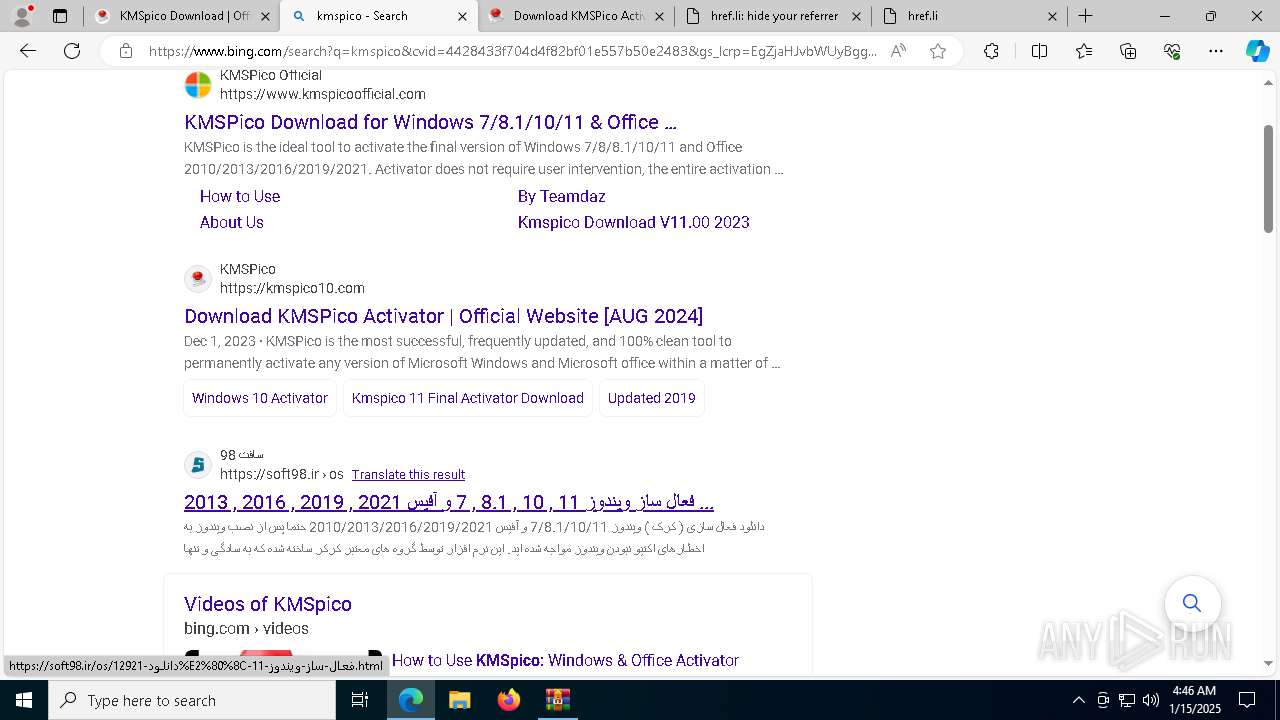
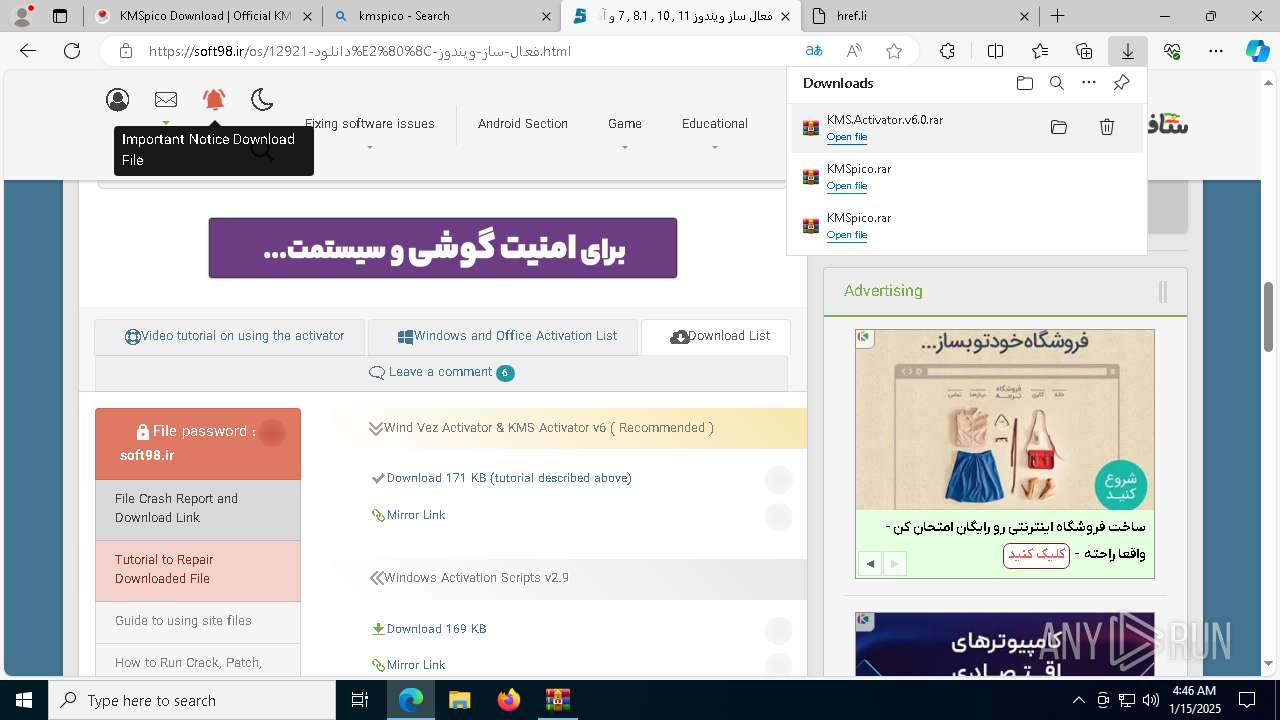
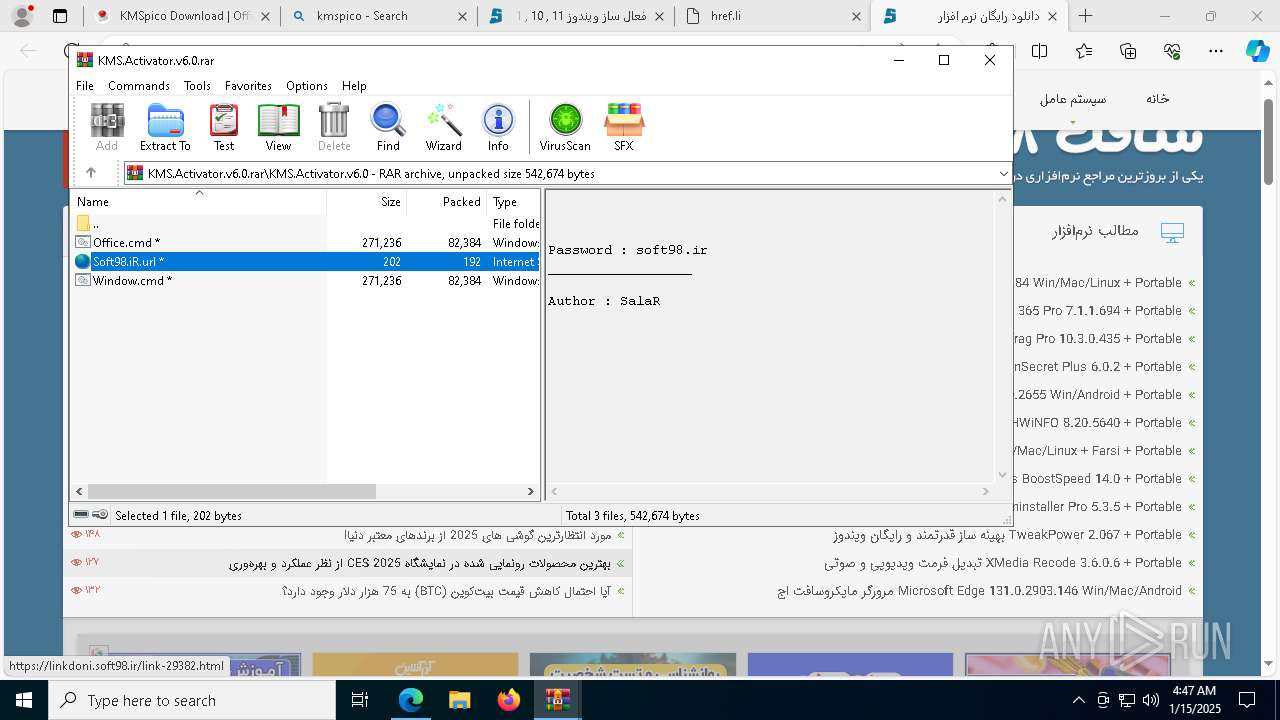
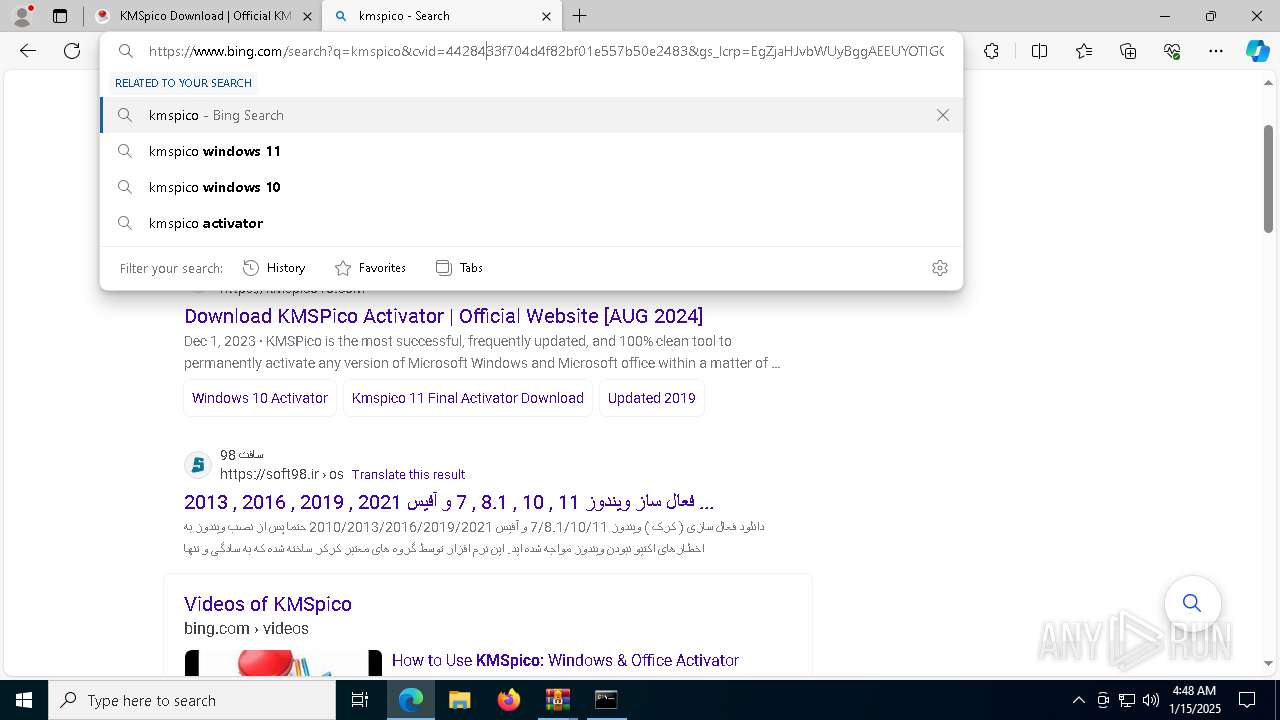
| URL: | kmspico.io |
| Full analysis: | https://app.any.run/tasks/20fec74e-f052-4347-98ab-839f367863f7 |
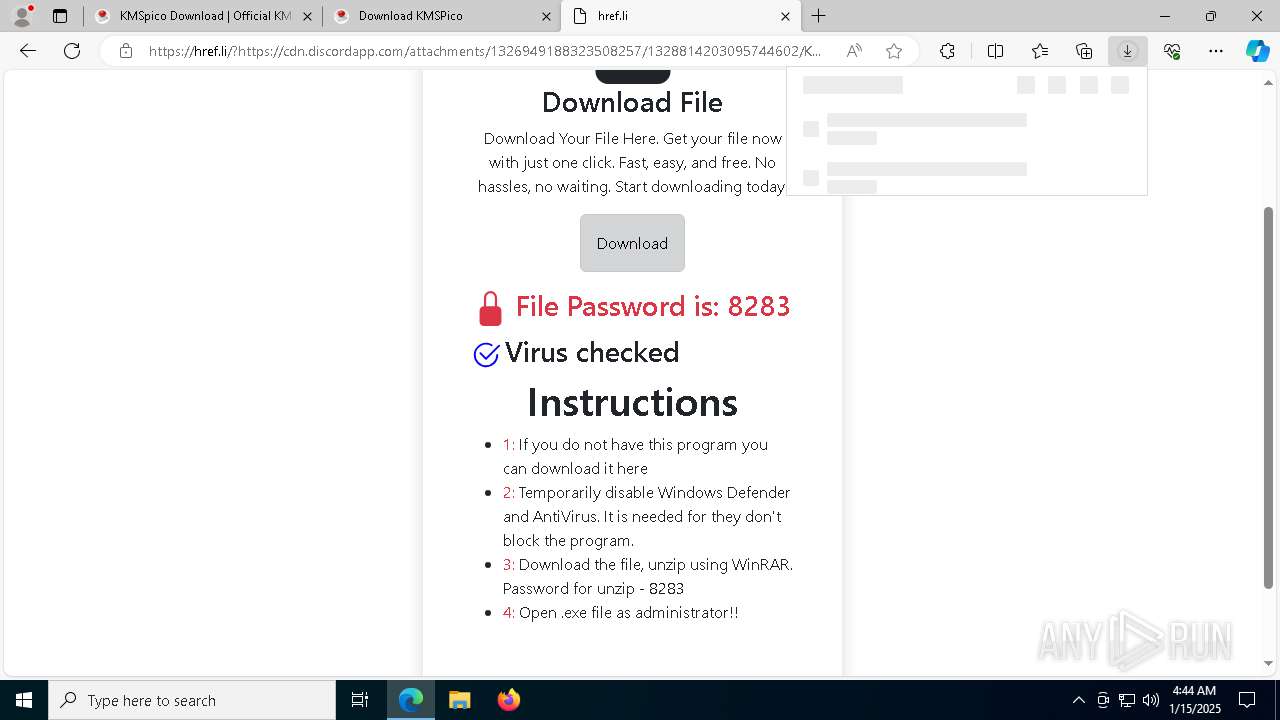
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | January 15, 2025, 04:44:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
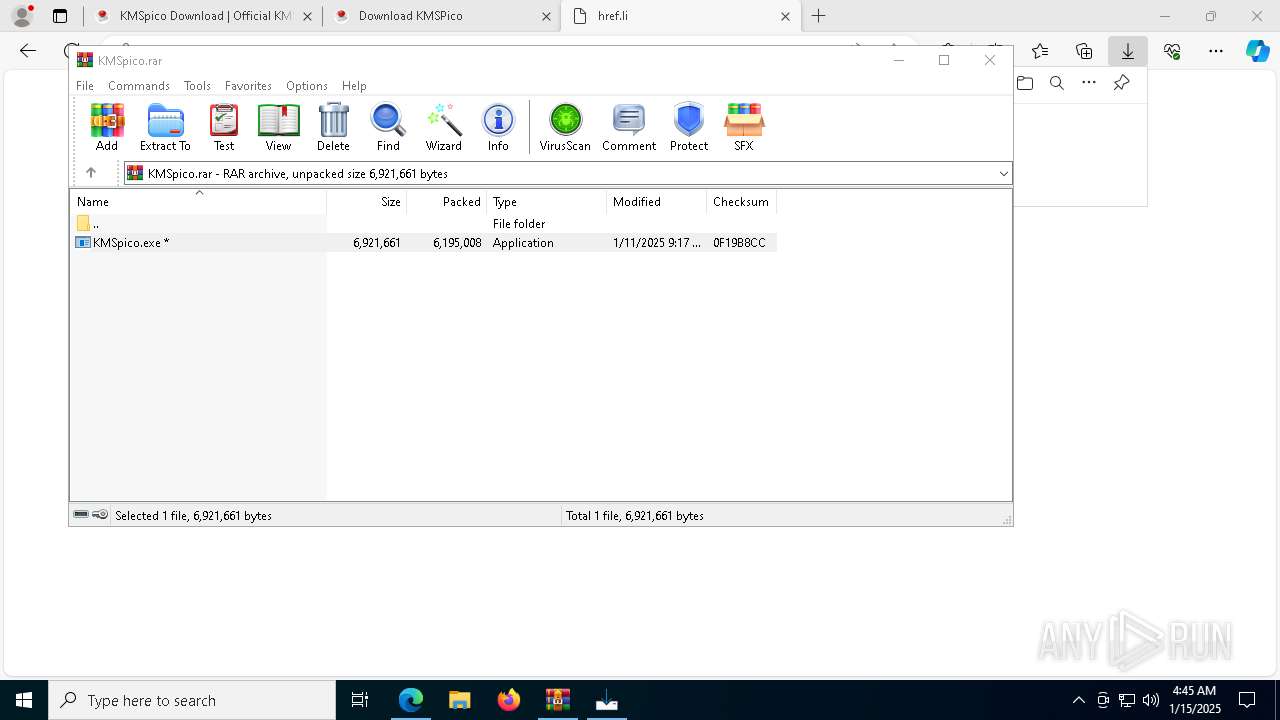
| MD5: | CDFA9B3709EE060A4BECE6FCCC5A9F66 |
| SHA1: | AD8ECBEB0C58236D94E85BE6FA7644647D2A87BD |
| SHA256: | AA0CFEA953F3EE084C0F287C2D06EF13DA9AC1CDF98A6F3493319852D95376DC |
| SSDEEP: | 3:/G0n:x |
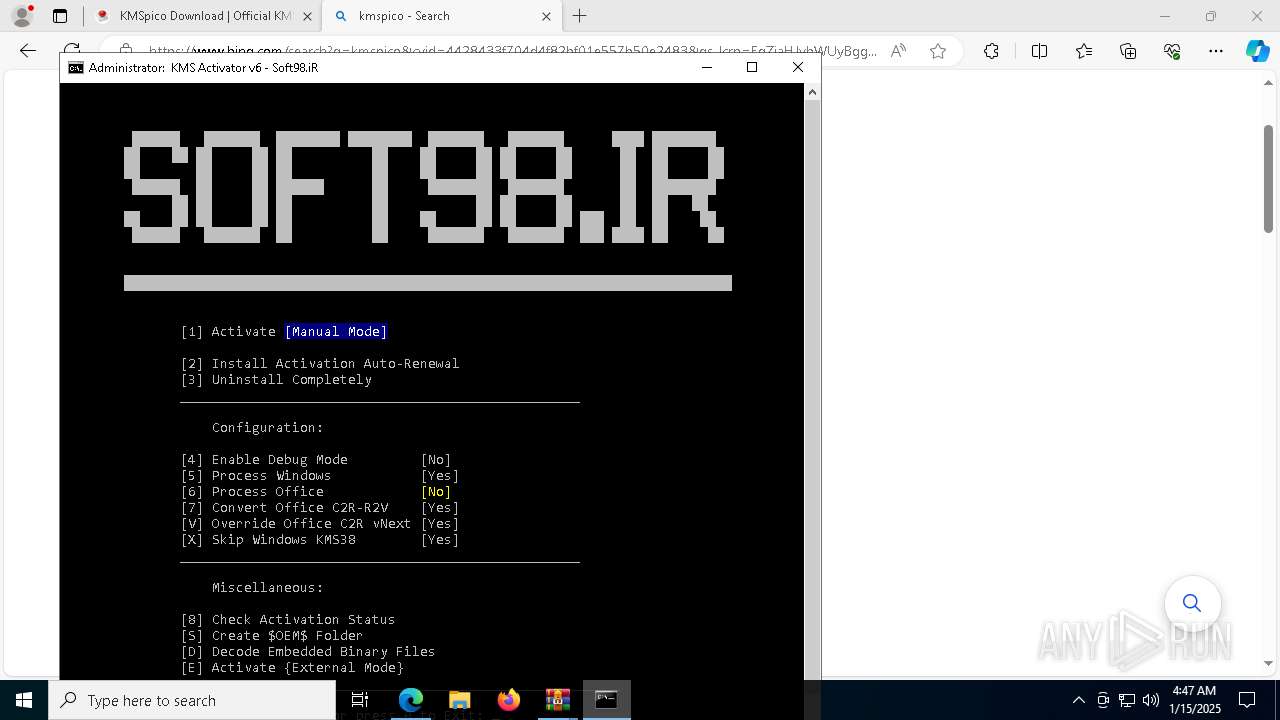
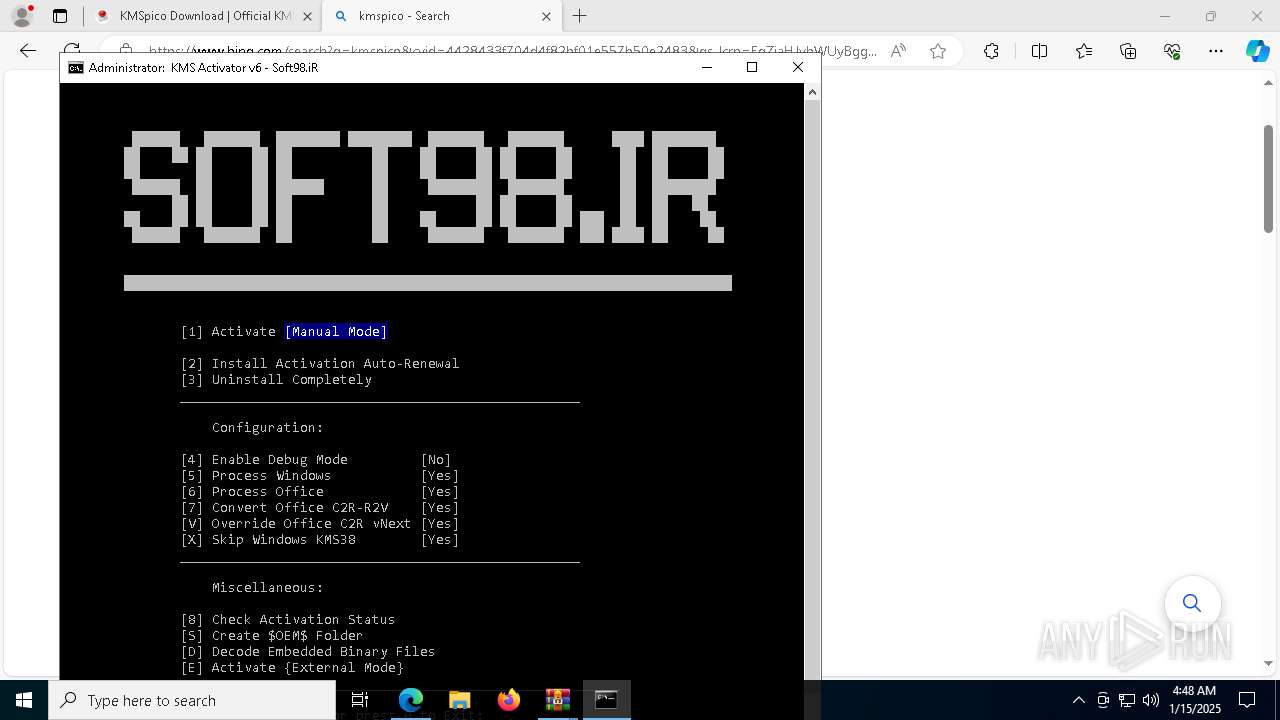
MALICIOUS
Connects to the CnC server
- msedge.exe (PID: 6608)
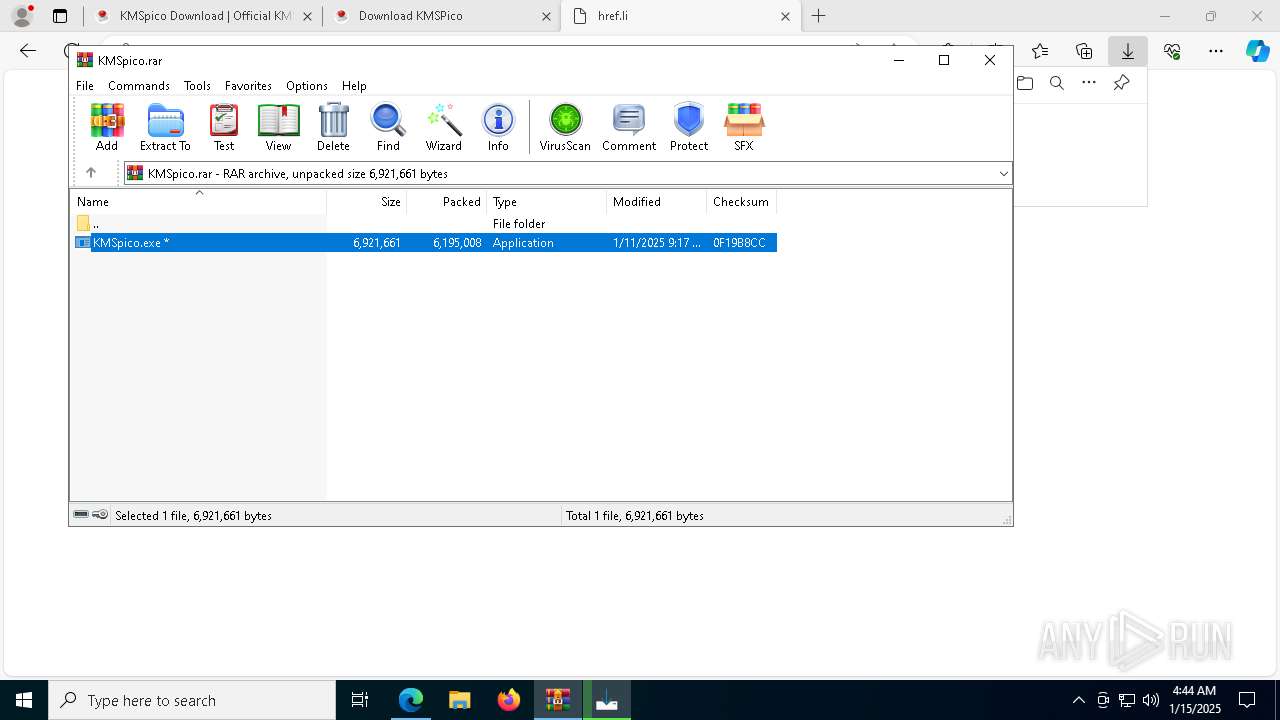
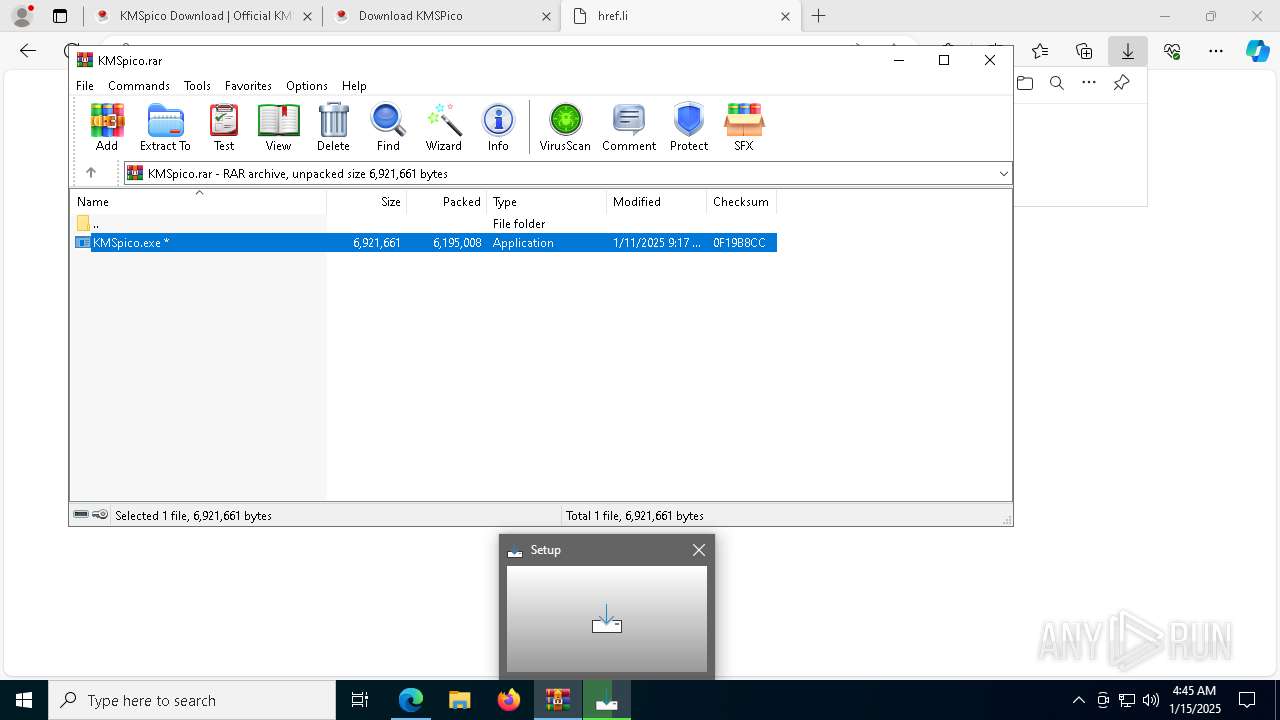
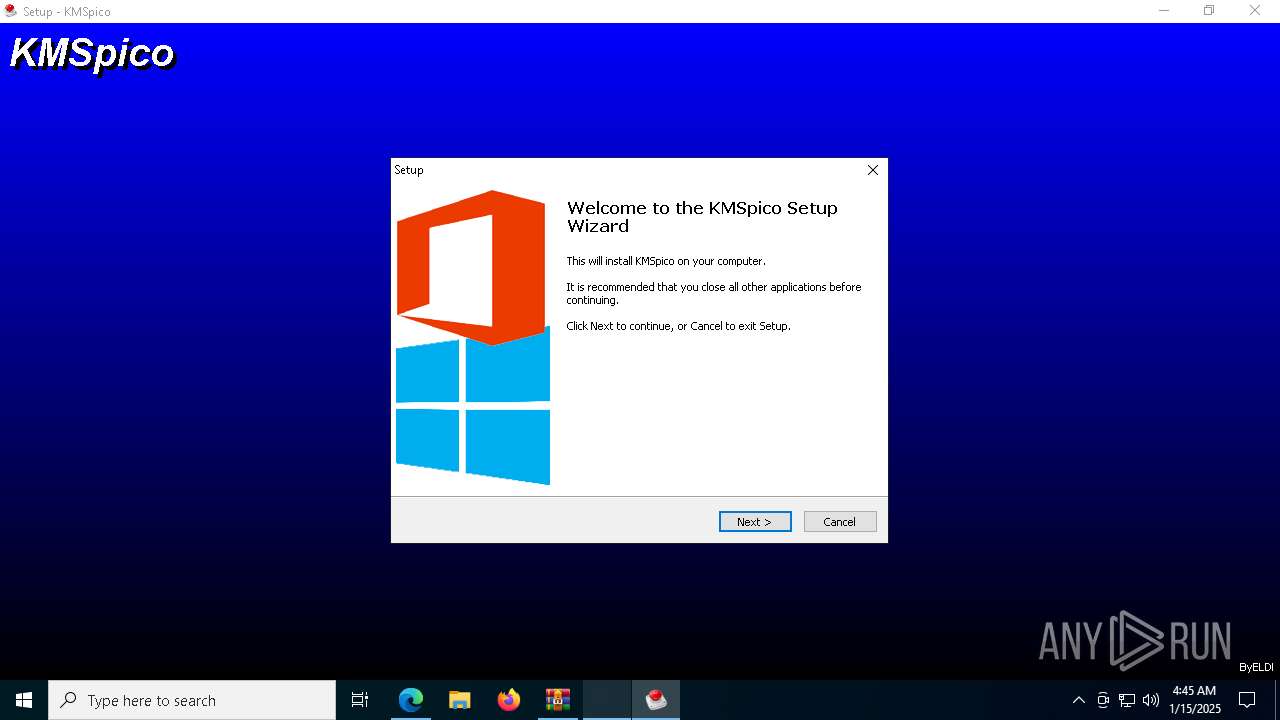
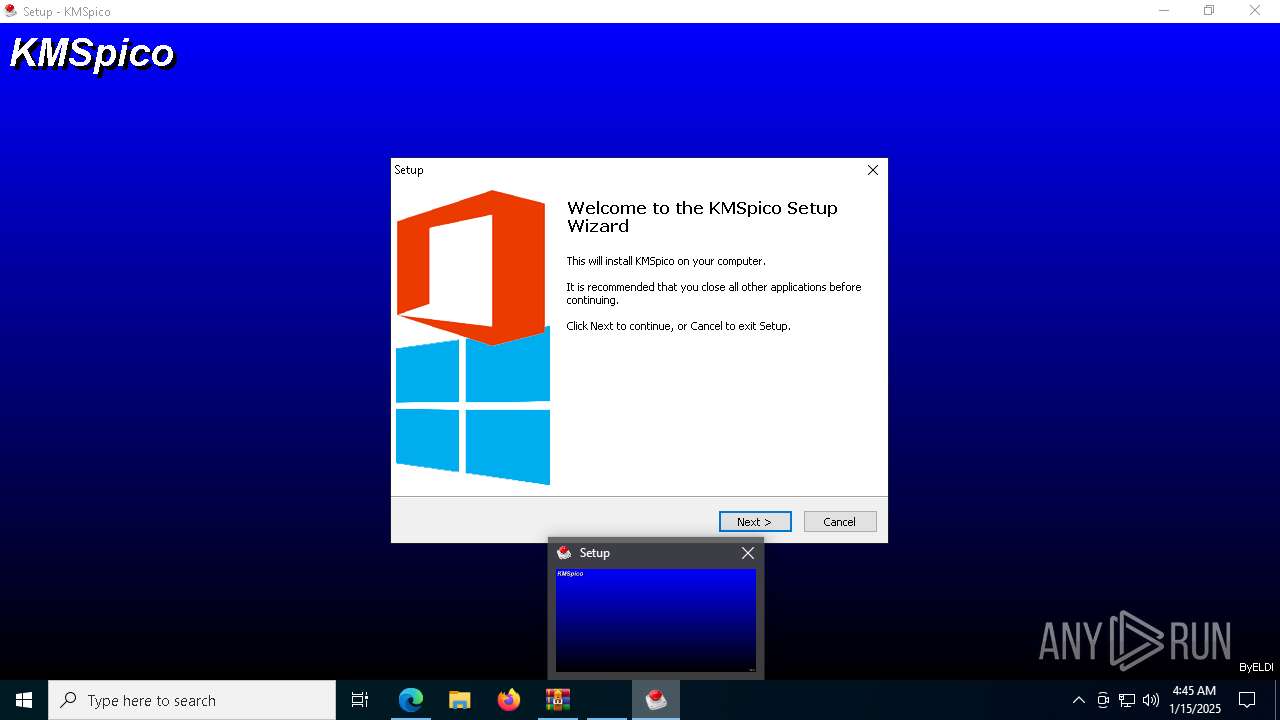
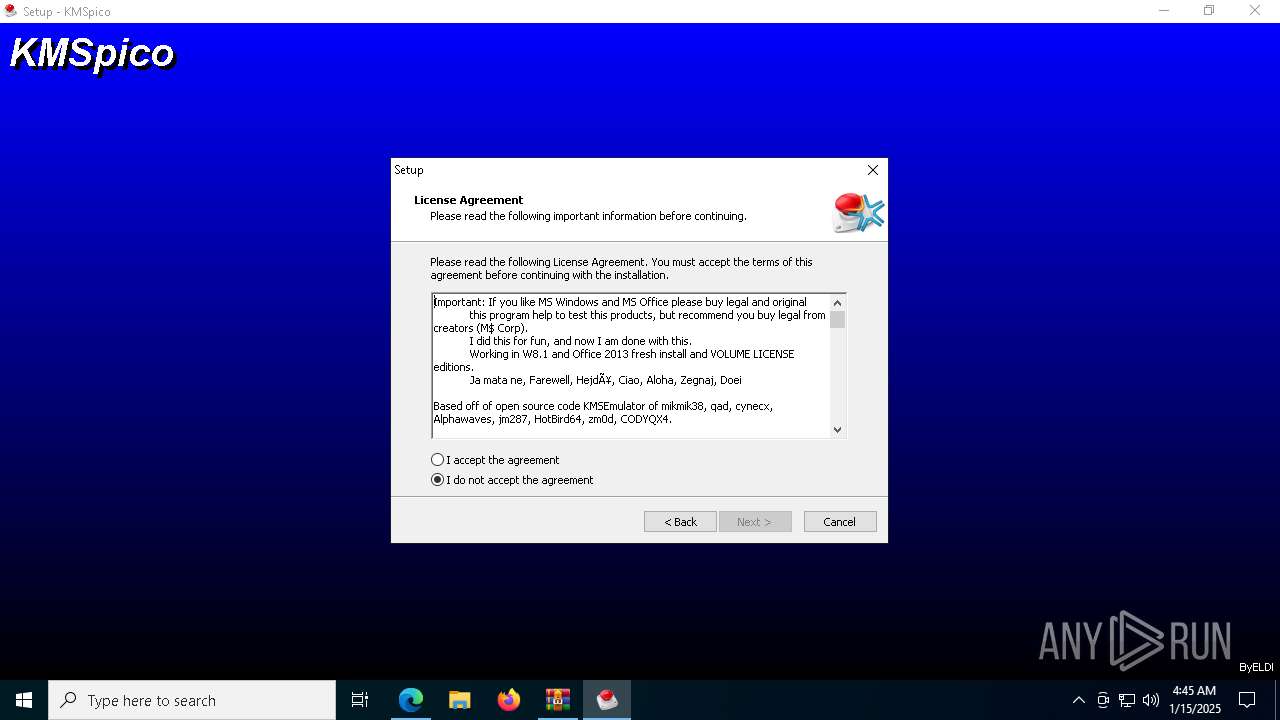
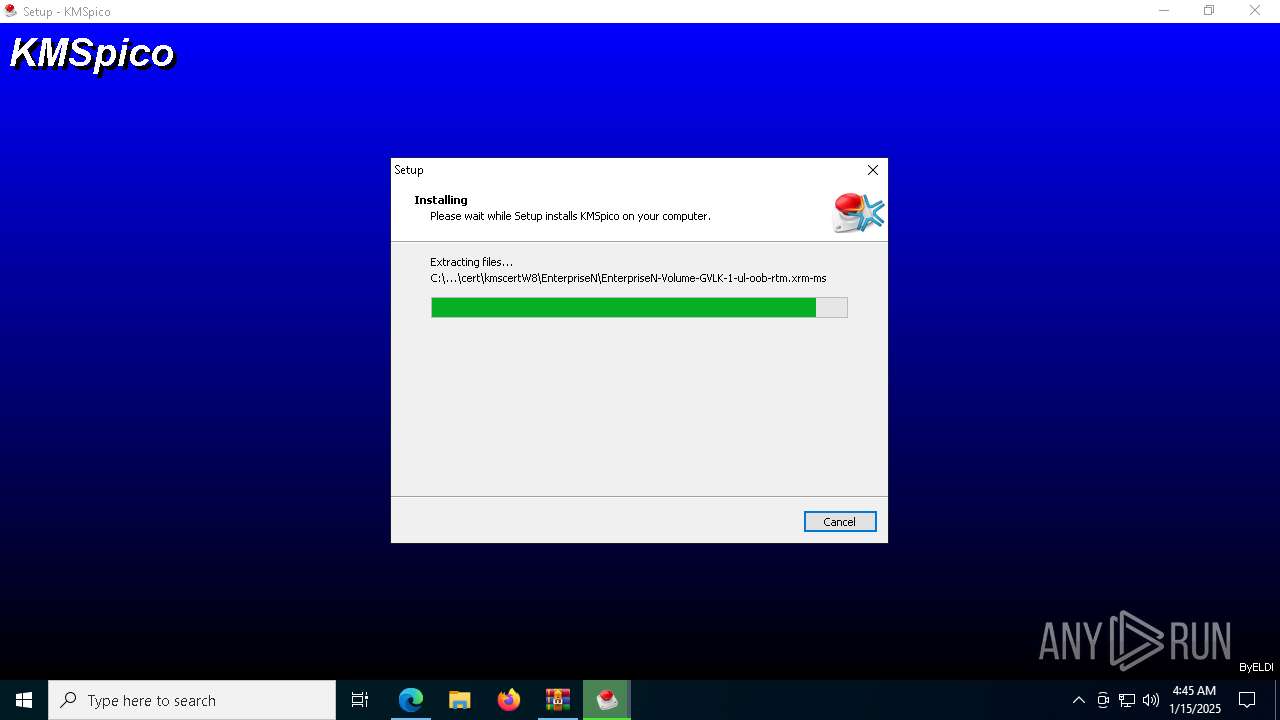
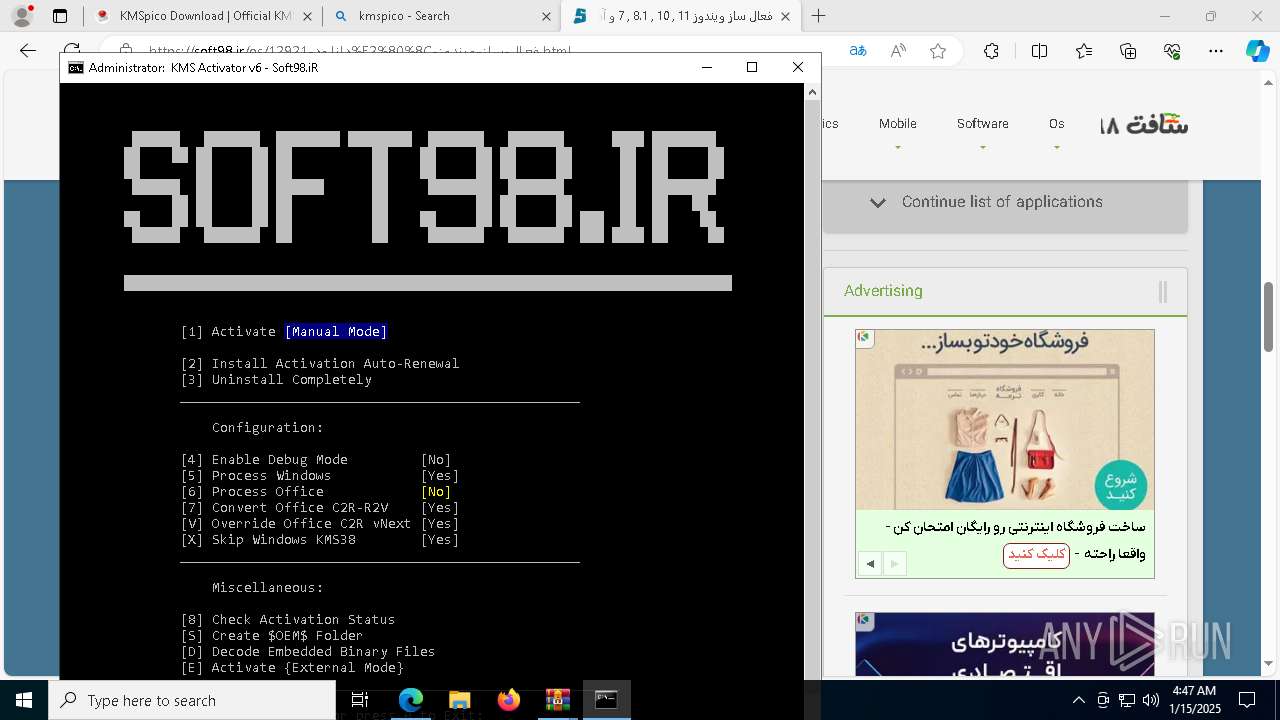
Executing a file with an untrusted certificate
- KMSpico.exe (PID: 936)
- core.exe (PID: 7956)
- KMSELDI.exe (PID: 3188)
- AutoPico.exe (PID: 8180)
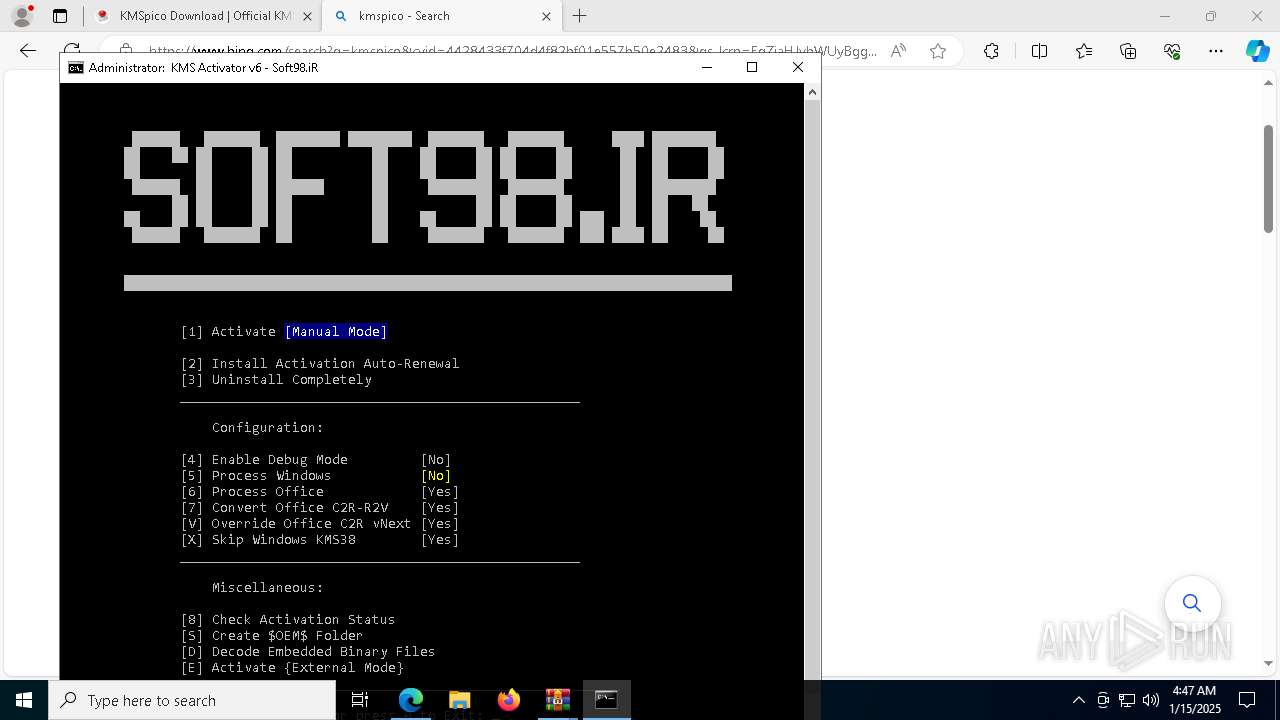
Changes powershell execution policy (Bypass)
- core.exe (PID: 7956)
LUMMA mutex has been found
- core.exe (PID: 7956)
Actions looks like stealing of personal data
- core.exe (PID: 7956)
Steals credentials from Web Browsers
- core.exe (PID: 7956)
Bypass execution policy to execute commands
- powershell.exe (PID: 7360)
Changes image file execution options
- KMSELDI.exe (PID: 3188)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3608)
Uses WMIC.EXE to add exclusions to the Windows Defender
- cmd.exe (PID: 3840)
Starts NET.EXE for service management
- net.exe (PID: 7796)
- cmd.exe (PID: 3840)
- net.exe (PID: 3888)
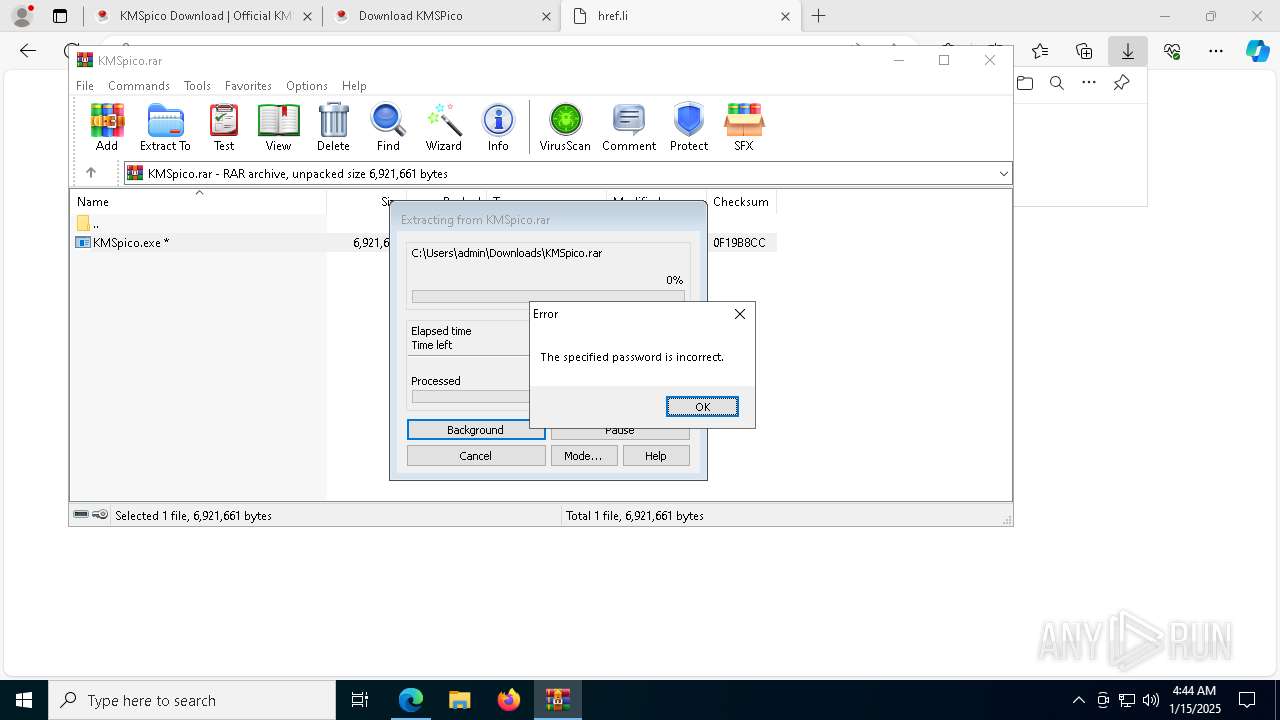
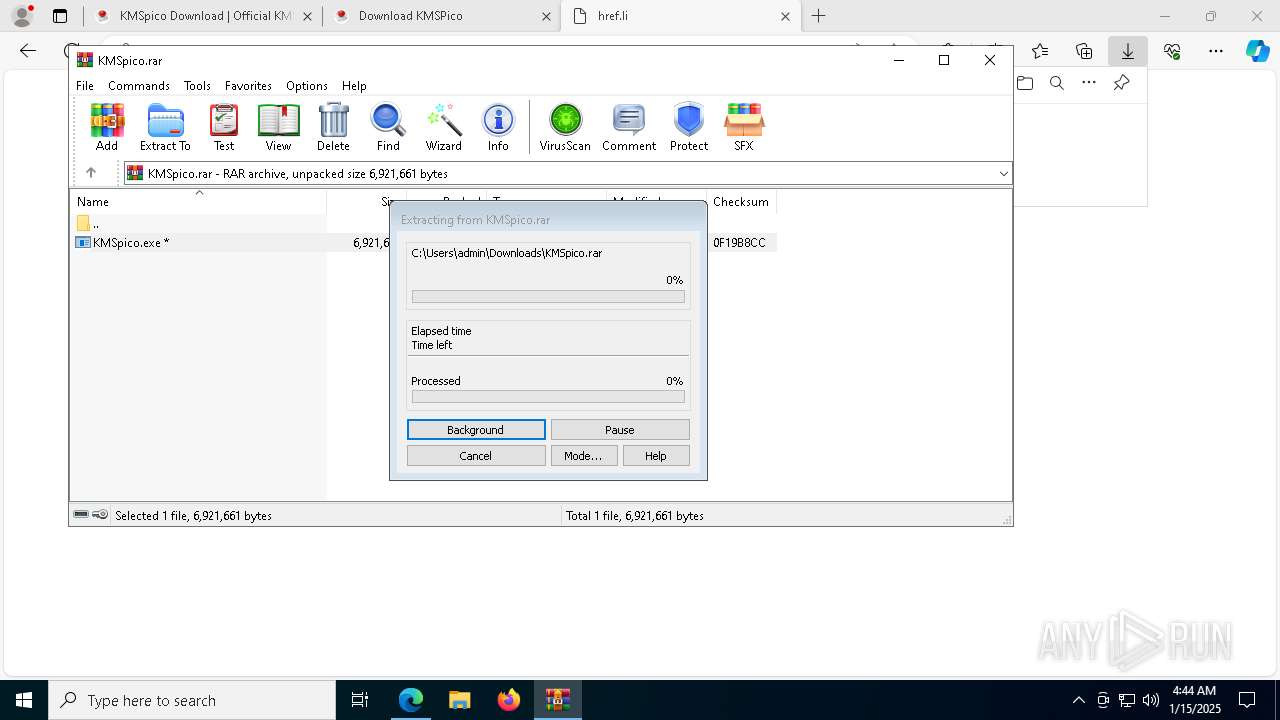
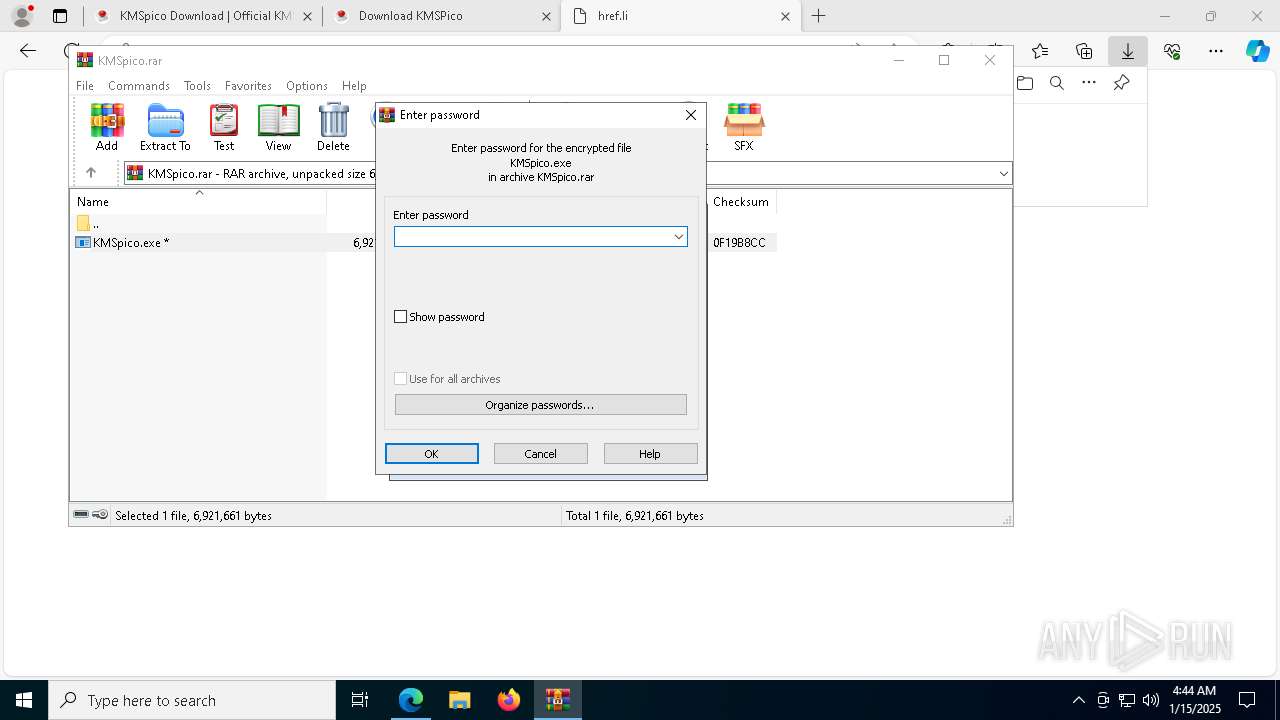
SUSPICIOUS
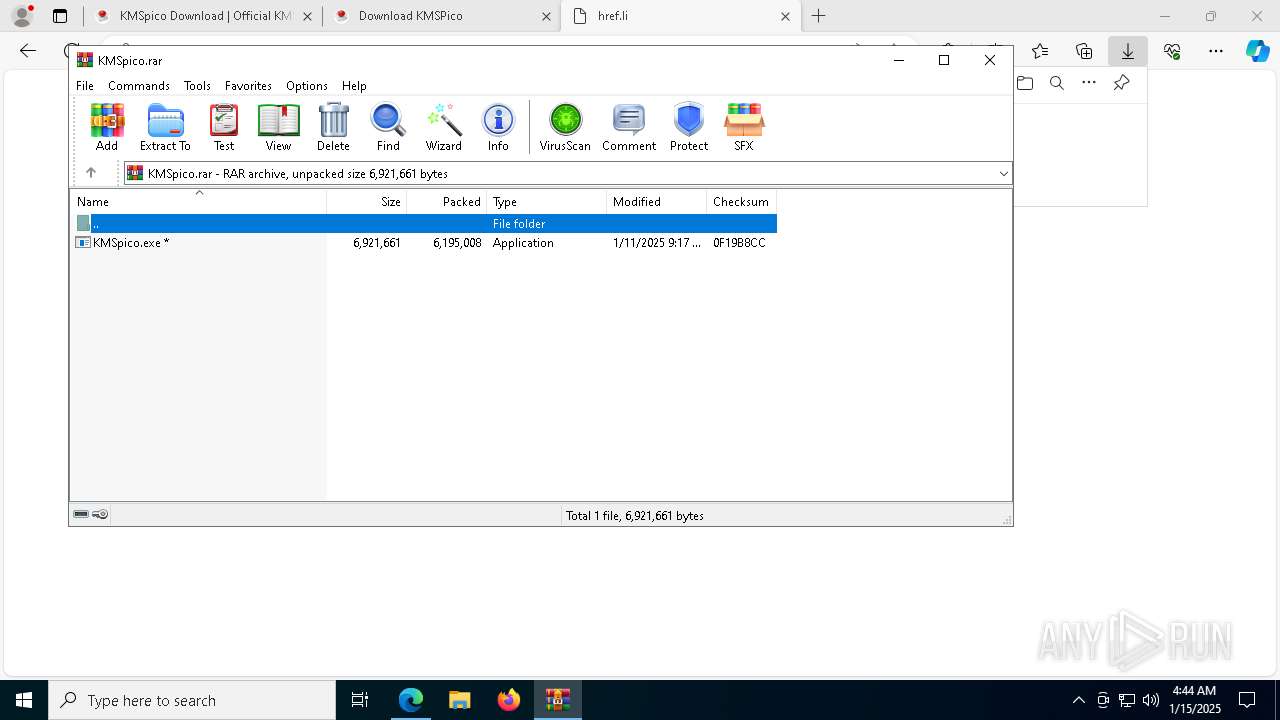
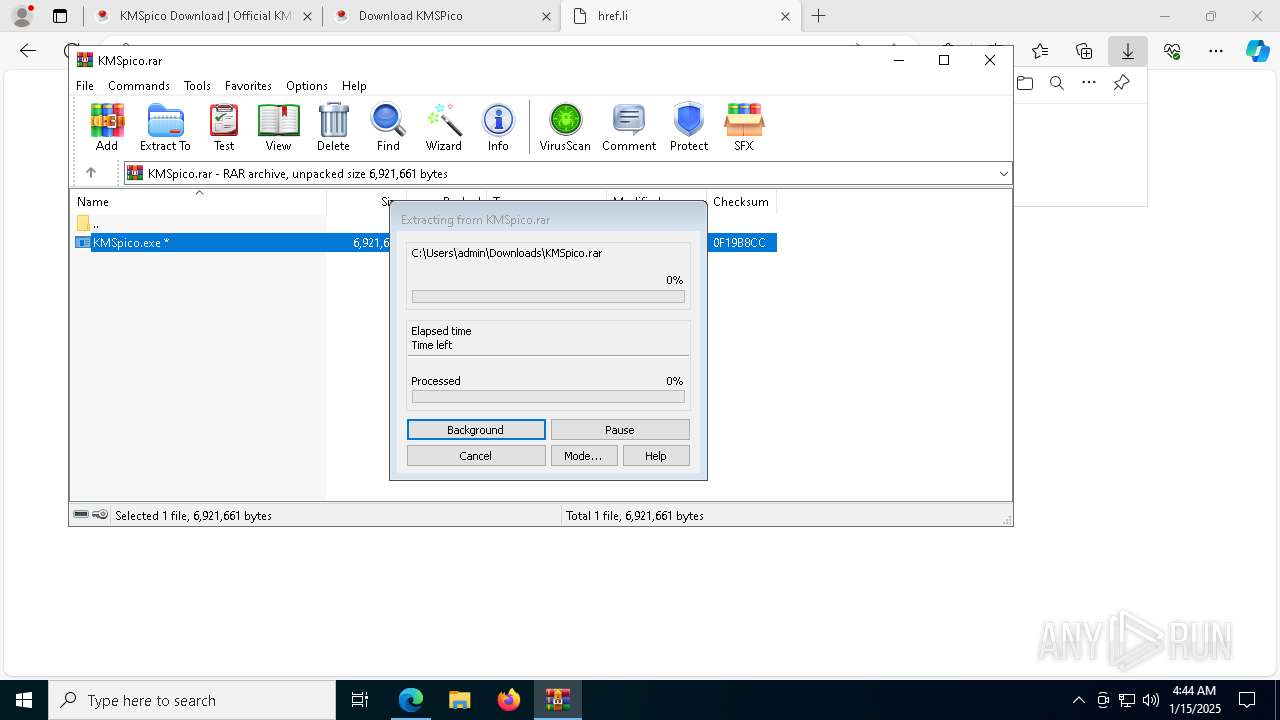
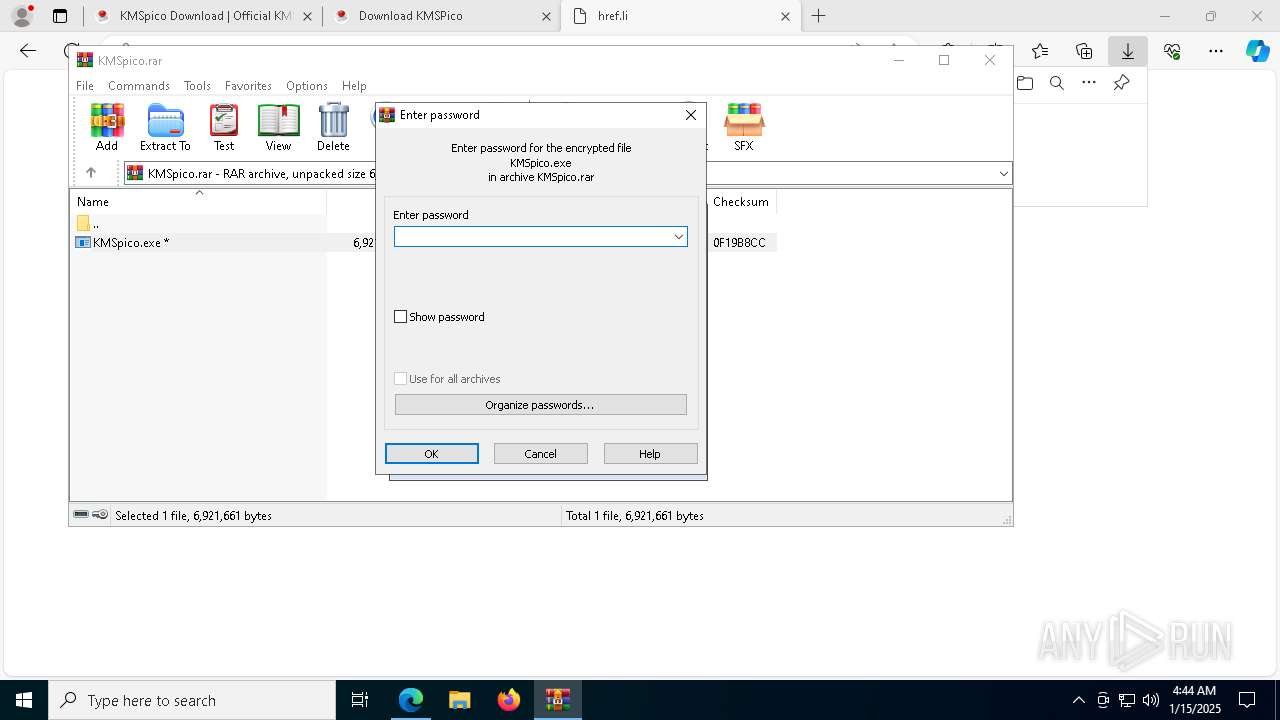
Reads security settings of Internet Explorer
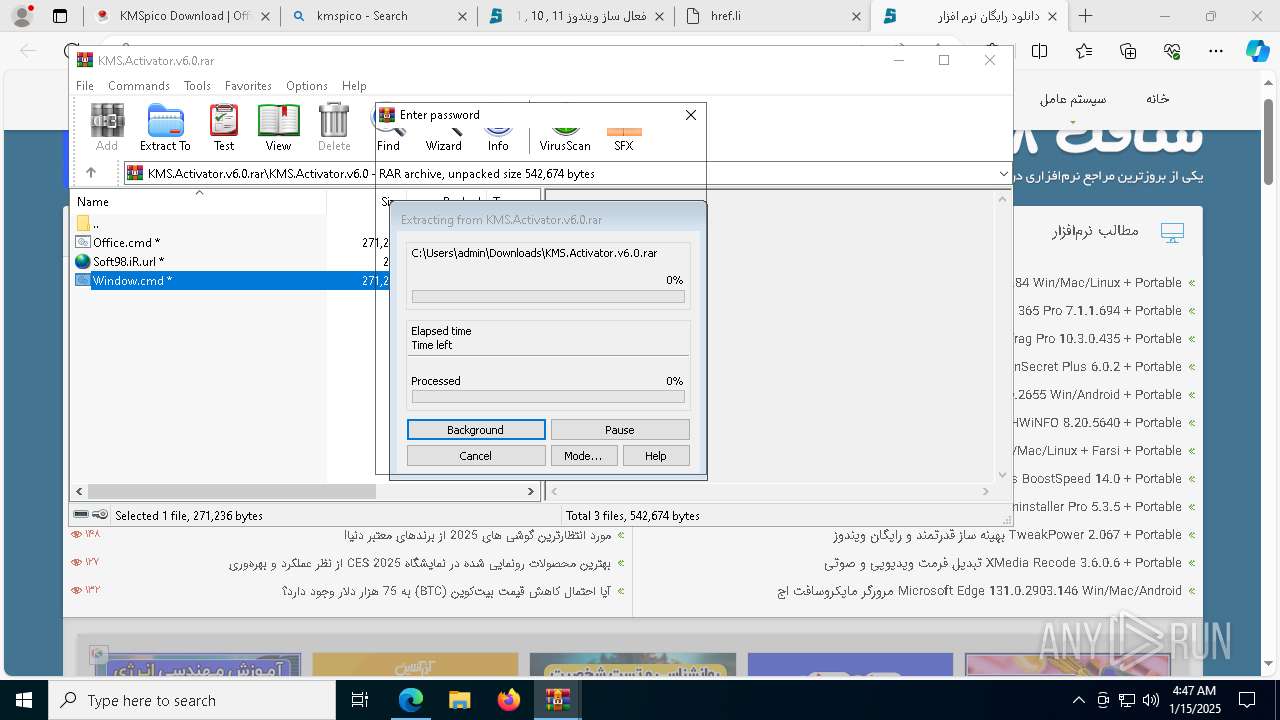
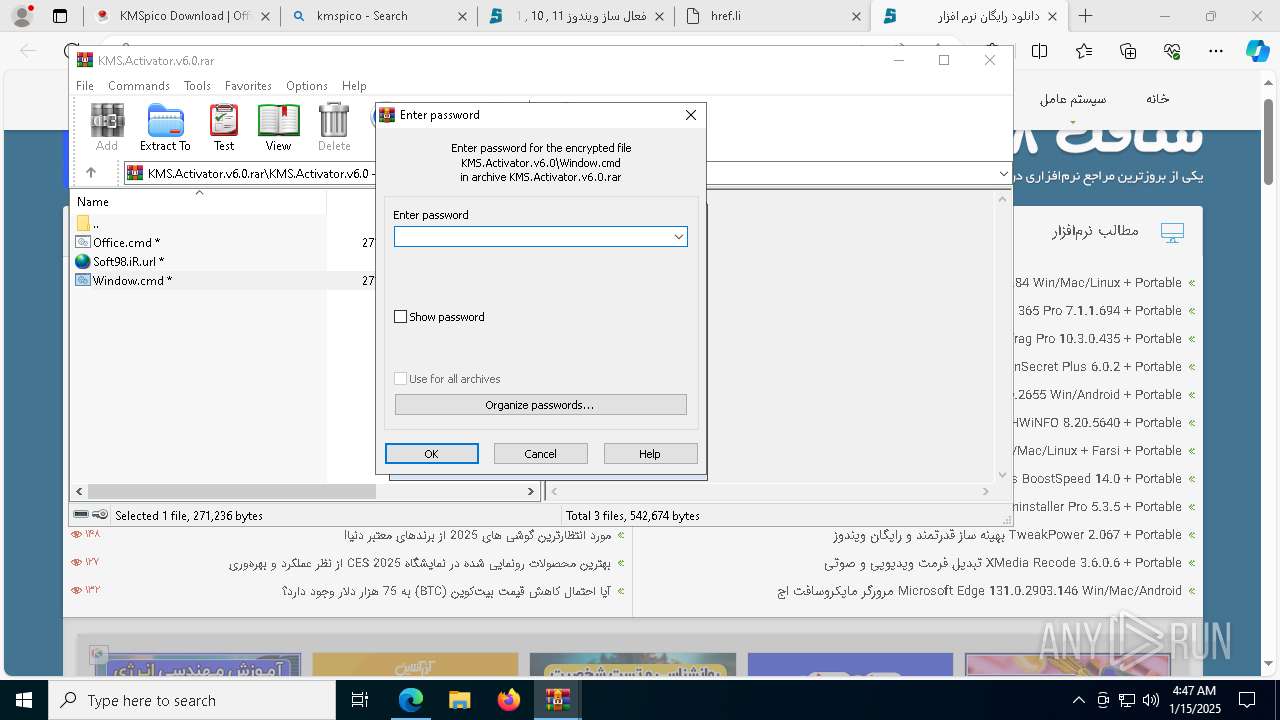
- WinRAR.exe (PID: 848)
- KMSpico.tmp (PID: 7980)
- KMSpico.tmp (PID: 5392)
- WinRAR.exe (PID: 1868)
Reads the Windows owner or organization settings
- KMSpico.tmp (PID: 7980)
- KMSpico.tmp (PID: 2672)
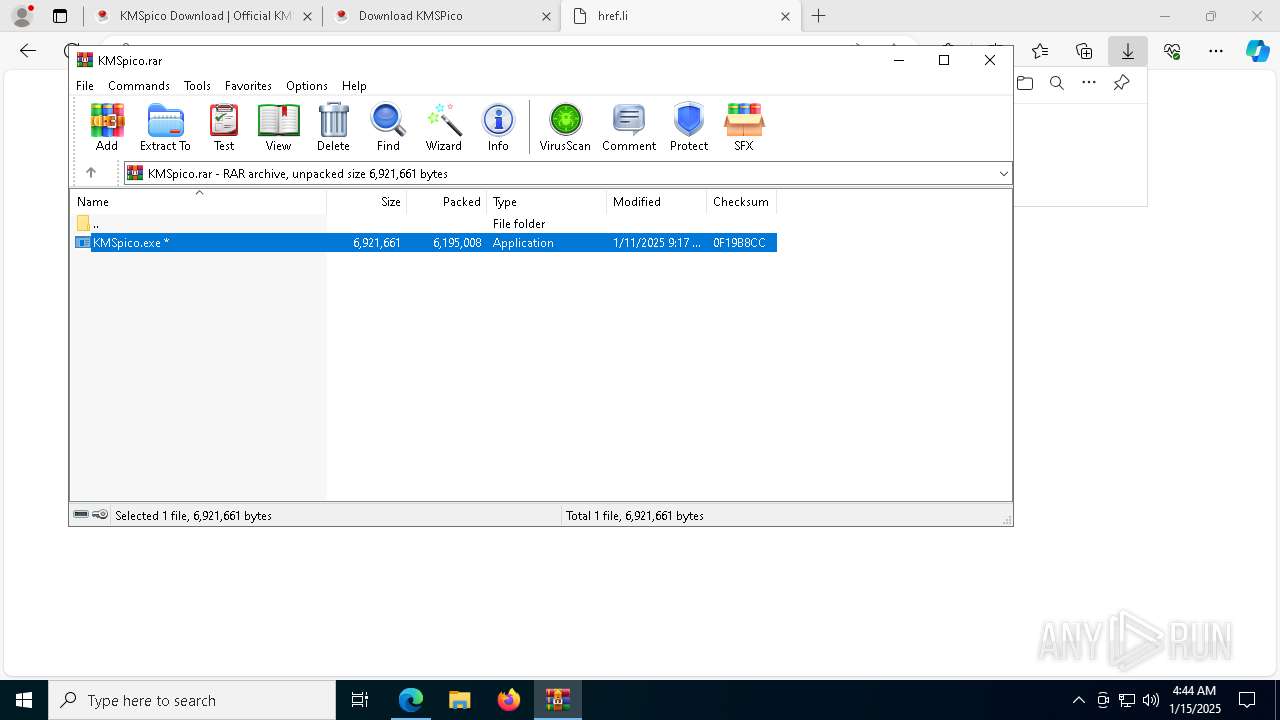
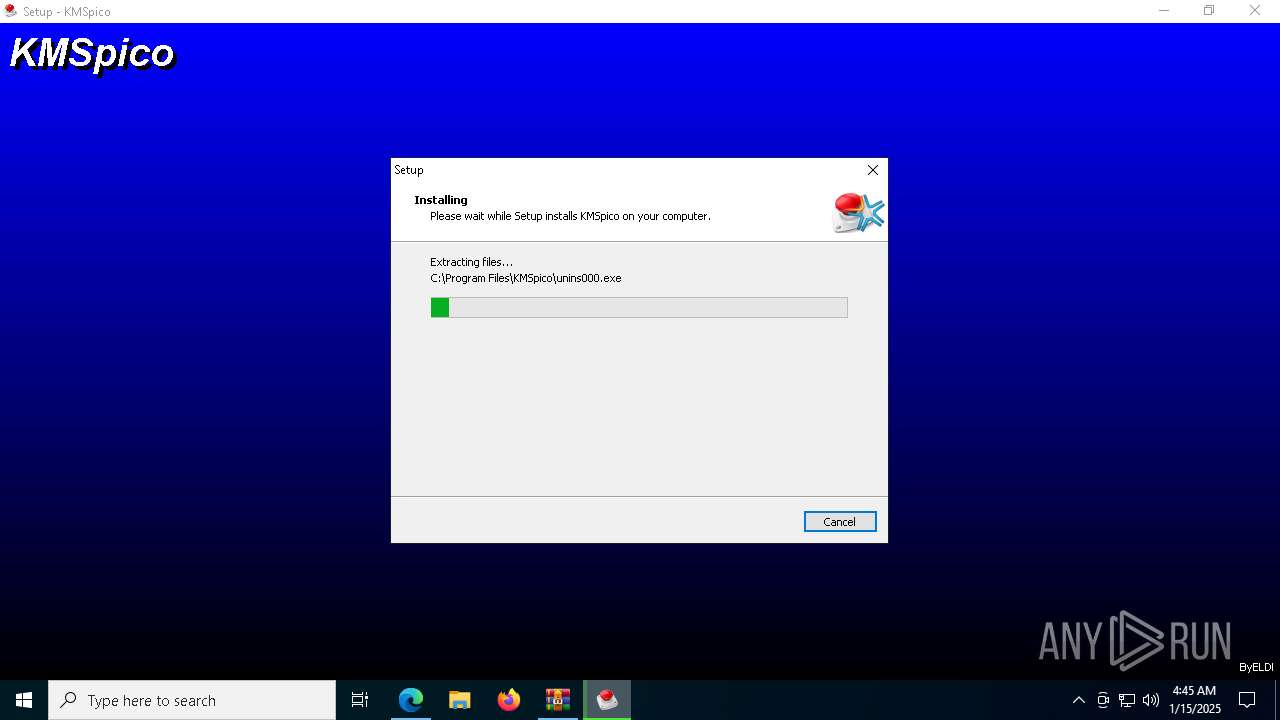
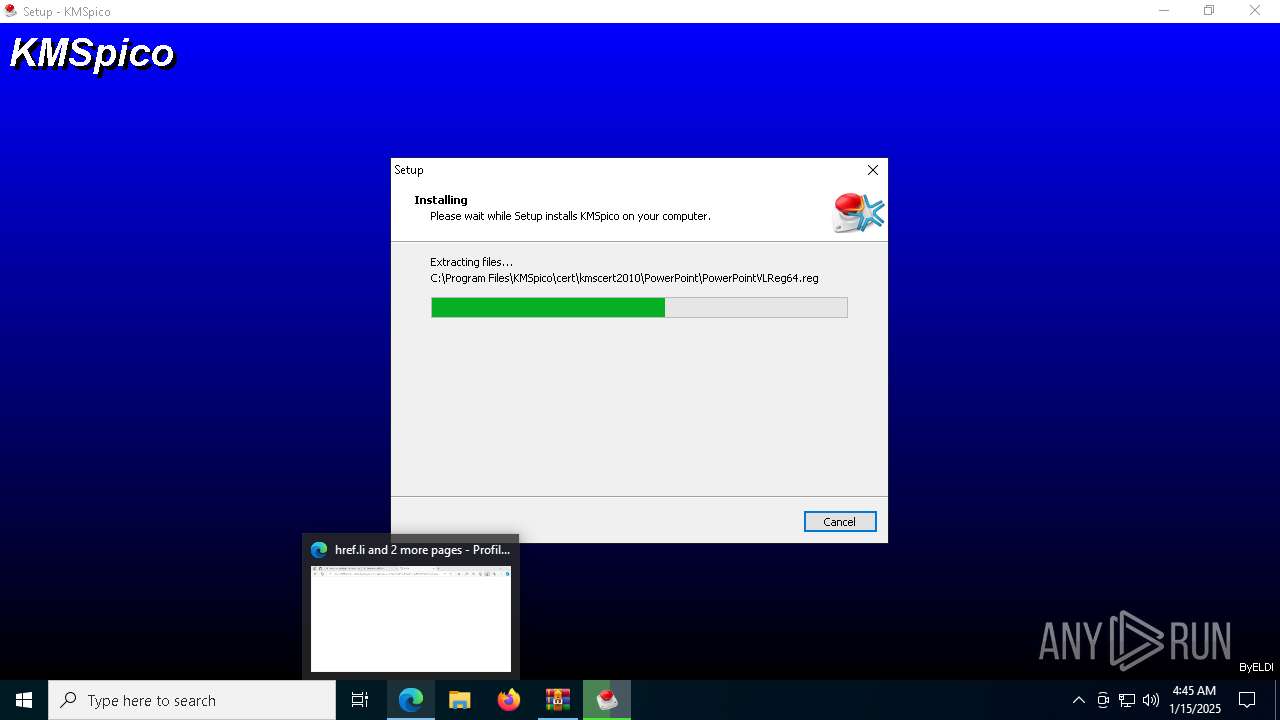
Executable content was dropped or overwritten
- KMSpico.exe (PID: 8068)
- KMSpico.tmp (PID: 7980)
- KMSpico.exe (PID: 936)
- KMSpico.exe (PID: 7920)
- KMSpico.tmp (PID: 2672)
- KMSELDI.exe (PID: 3188)
- powershell.exe (PID: 8004)
- csc.exe (PID: 4968)
Process drops legitimate windows executable
- KMSpico.tmp (PID: 2672)
Starts POWERSHELL.EXE for commands execution
- core.exe (PID: 7956)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 3840)
The process executes Powershell scripts
- core.exe (PID: 7956)
Modifies the phishing filter of IE
- KMSpico.tmp (PID: 2672)
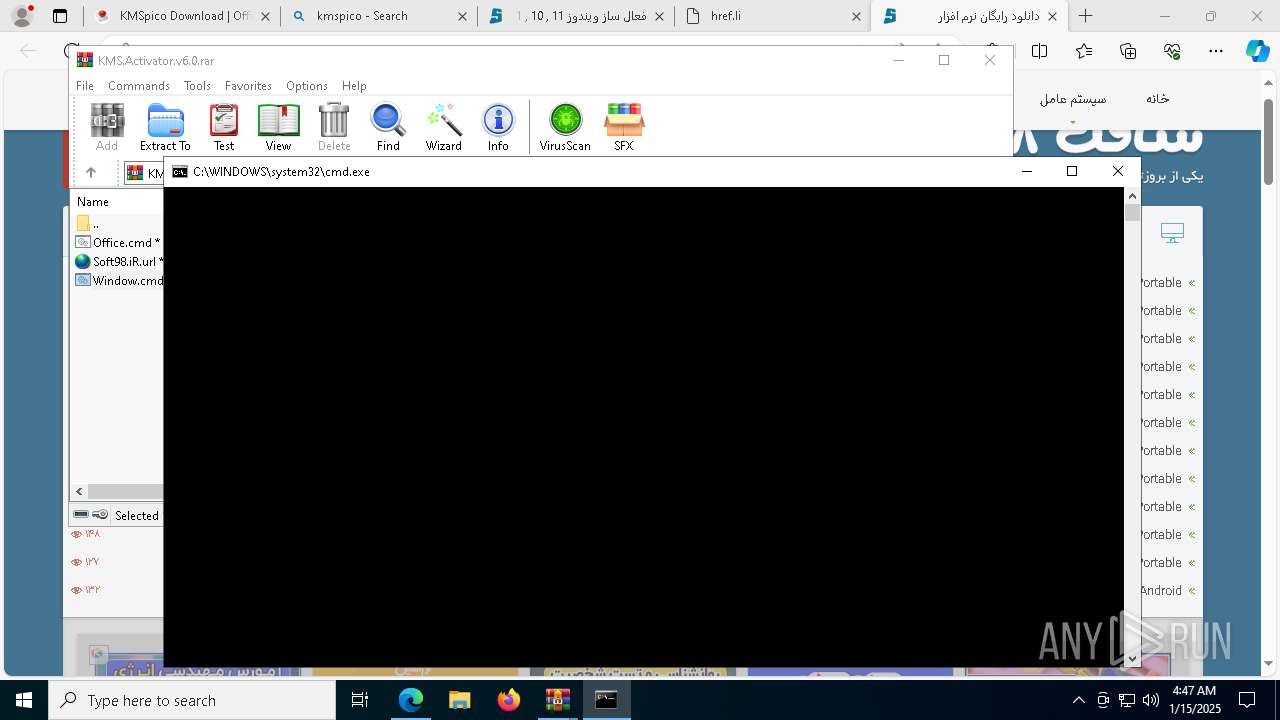
Starts CMD.EXE for commands execution
- KMSpico.tmp (PID: 2672)
- WinRAR.exe (PID: 1868)
- cmd.exe (PID: 7980)
- cscript.exe (PID: 4804)
- cmd.exe (PID: 3840)
Creates a new Windows service
- sc.exe (PID: 7204)
Starts SC.EXE for service management
- cmd.exe (PID: 7164)
- cmd.exe (PID: 3840)
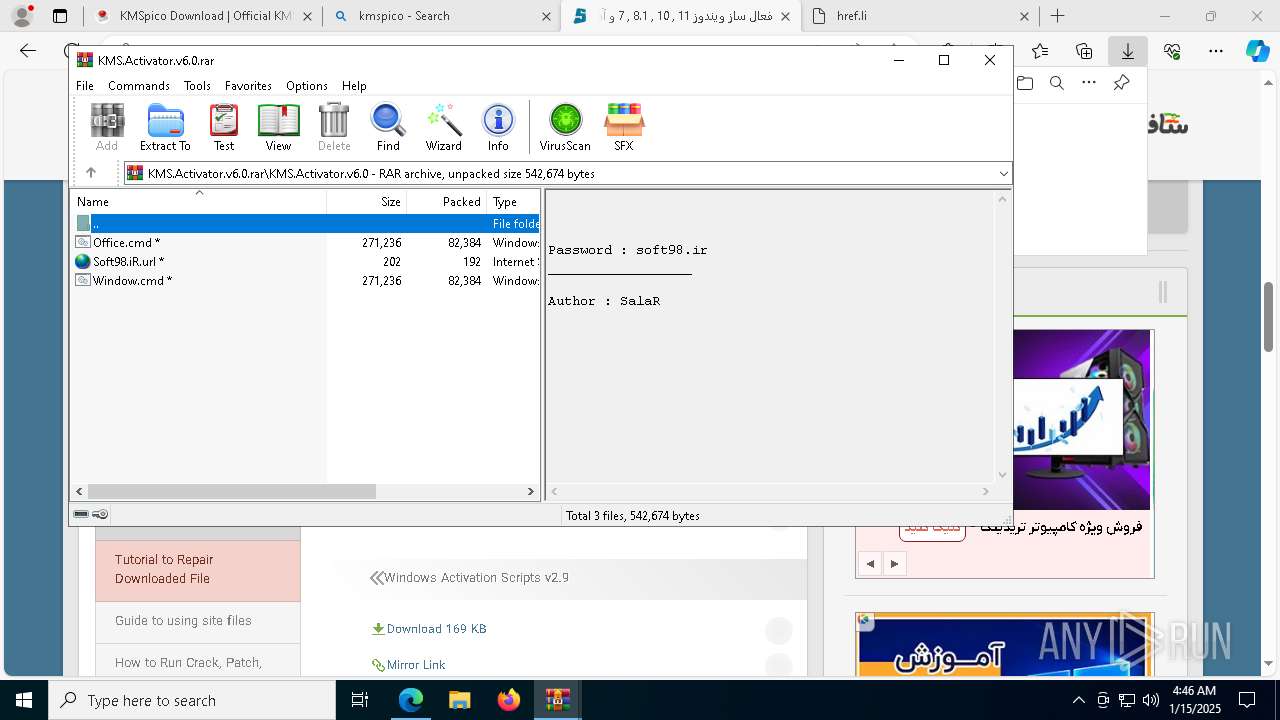
Executing commands from ".cmd" file
- KMSpico.tmp (PID: 2672)
- cscript.exe (PID: 4804)
- WinRAR.exe (PID: 1868)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7980)
- cmd.exe (PID: 3840)
- cmd.exe (PID: 7668)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 3724)
- cmd.exe (PID: 1796)
Executes script without checking the security policy
- powershell.exe (PID: 8140)
- powershell.exe (PID: 188)
- powershell.exe (PID: 540)
- powershell.exe (PID: 8004)
- powershell.exe (PID: 1684)
Runs shell command (SCRIPT)
- cscript.exe (PID: 4804)
Application launched itself
- cmd.exe (PID: 3840)
- cmd.exe (PID: 7980)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7980)
- cmd.exe (PID: 3840)
Hides command output
- cmd.exe (PID: 7532)
- cmd.exe (PID: 3724)
- cmd.exe (PID: 3820)
- cmd.exe (PID: 3420)
- cmd.exe (PID: 6068)
- cmd.exe (PID: 7760)
- cmd.exe (PID: 7176)
- cmd.exe (PID: 7324)
- cmd.exe (PID: 5616)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 6932)
- cmd.exe (PID: 7132)
- cmd.exe (PID: 7764)
Windows service management via SC.EXE
- sc.exe (PID: 4384)
- sc.exe (PID: 7632)
- sc.exe (PID: 3984)
- sc.exe (PID: 6512)
- sc.exe (PID: 7952)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3840)
Uses RUNDLL32.EXE to load library
- cscript.exe (PID: 4804)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 3840)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 3840)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 8004)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 8004)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8004)
CSC.EXE is used to compile C# code
- csc.exe (PID: 4968)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 3420)
- cmd.exe (PID: 4128)
- cmd.exe (PID: 5392)
- cmd.exe (PID: 3840)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 7088)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 2408)
- cmd.exe (PID: 3840)
Lists all scheduled tasks
- schtasks.exe (PID: 6368)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 6240)
- AutoPico.exe (PID: 8180)
- reg.exe (PID: 4020)
- reg.exe (PID: 7072)
- reg.exe (PID: 6196)
- reg.exe (PID: 8172)
- reg.exe (PID: 2976)
- reg.exe (PID: 8060)
- reg.exe (PID: 7332)
- reg.exe (PID: 6156)
- reg.exe (PID: 3824)
- reg.exe (PID: 3260)
- reg.exe (PID: 3584)
- reg.exe (PID: 4308)
- reg.exe (PID: 3744)
- reg.exe (PID: 5308)
- reg.exe (PID: 624)
- reg.exe (PID: 7844)
- reg.exe (PID: 7604)
- reg.exe (PID: 4392)
- reg.exe (PID: 7148)
- reg.exe (PID: 2260)
- reg.exe (PID: 8004)
- reg.exe (PID: 5564)
- reg.exe (PID: 7336)
- reg.exe (PID: 5876)
- reg.exe (PID: 6892)
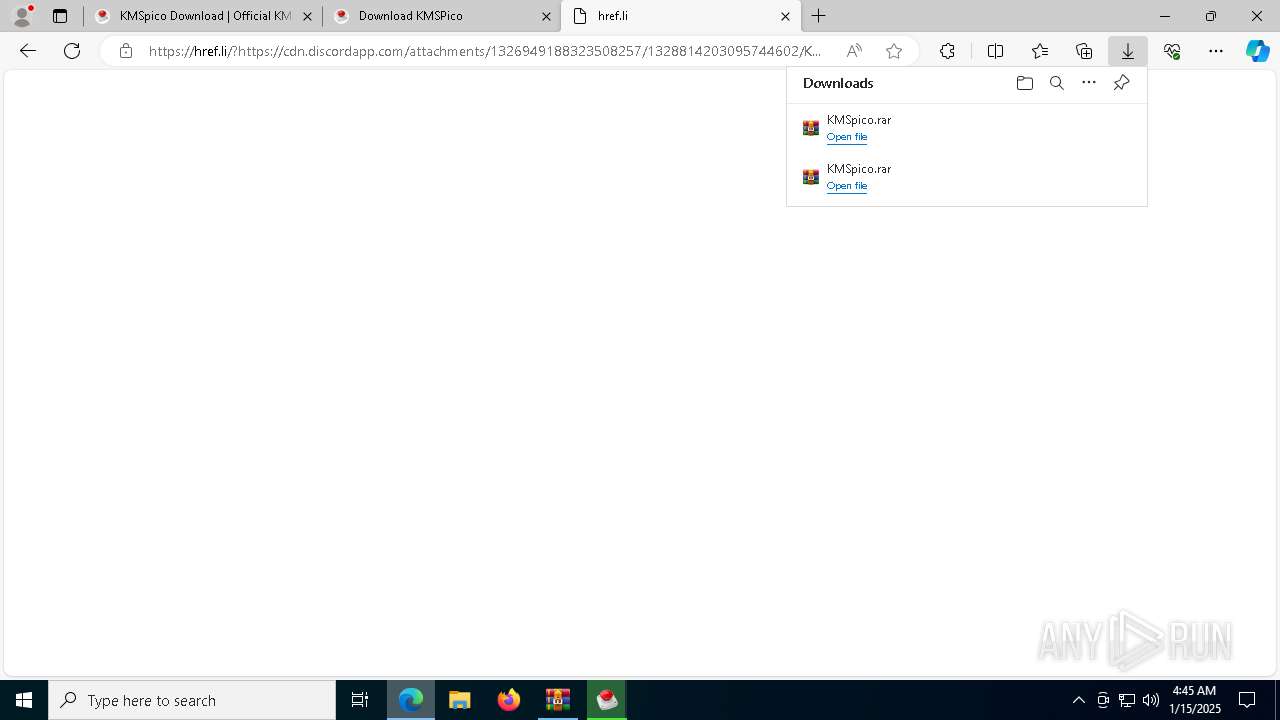
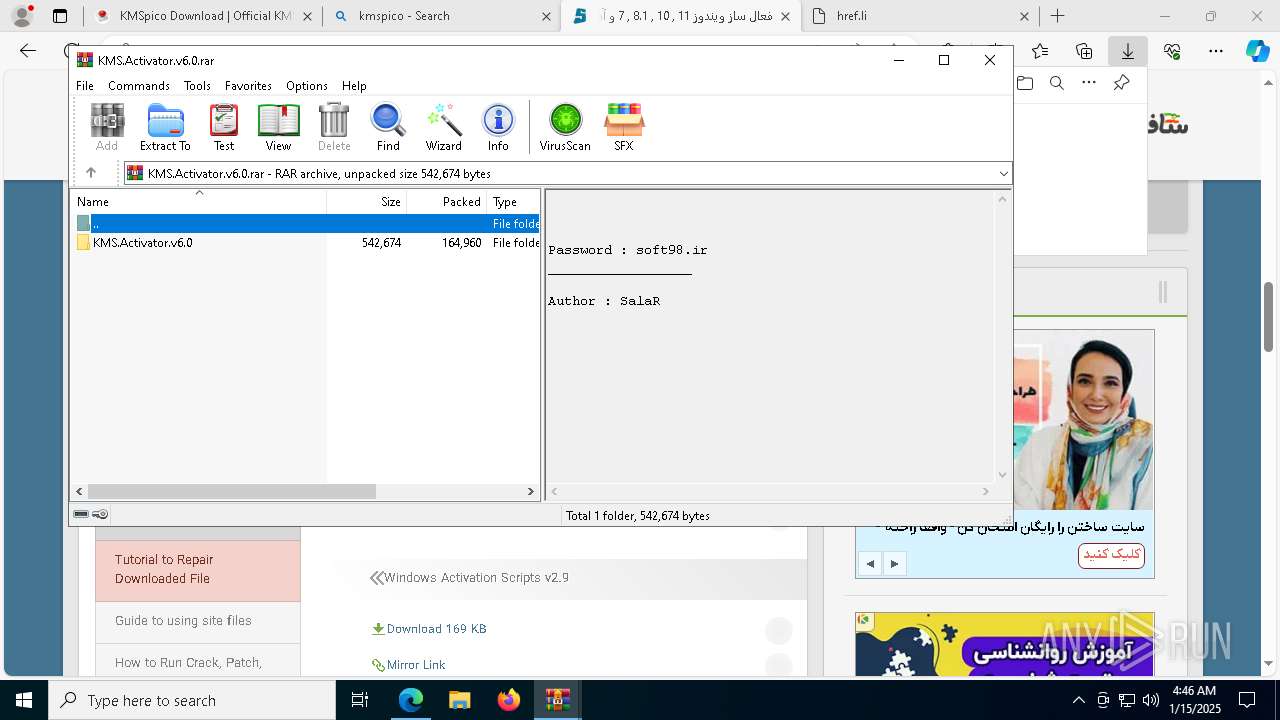
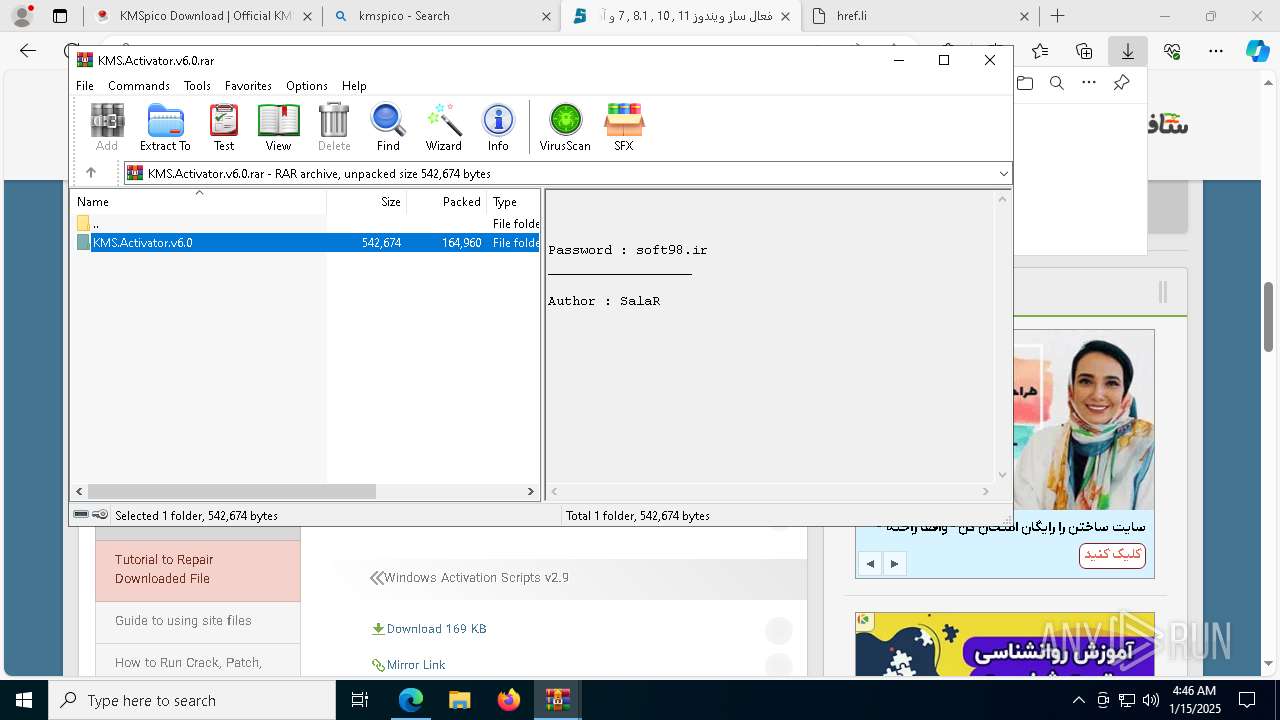
The process uses the downloaded file
- msedge.exe (PID: 6240)
- msedge.exe (PID: 3736)
- msedge.exe (PID: 7936)
- WinRAR.exe (PID: 848)
- KMSpico.tmp (PID: 7980)
- msedge.exe (PID: 2736)
- WinRAR.exe (PID: 1868)
Reads Environment values
- identity_helper.exe (PID: 7992)
- KMSELDI.exe (PID: 3188)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 848)
- msedge.exe (PID: 7184)
Create files in a temporary directory
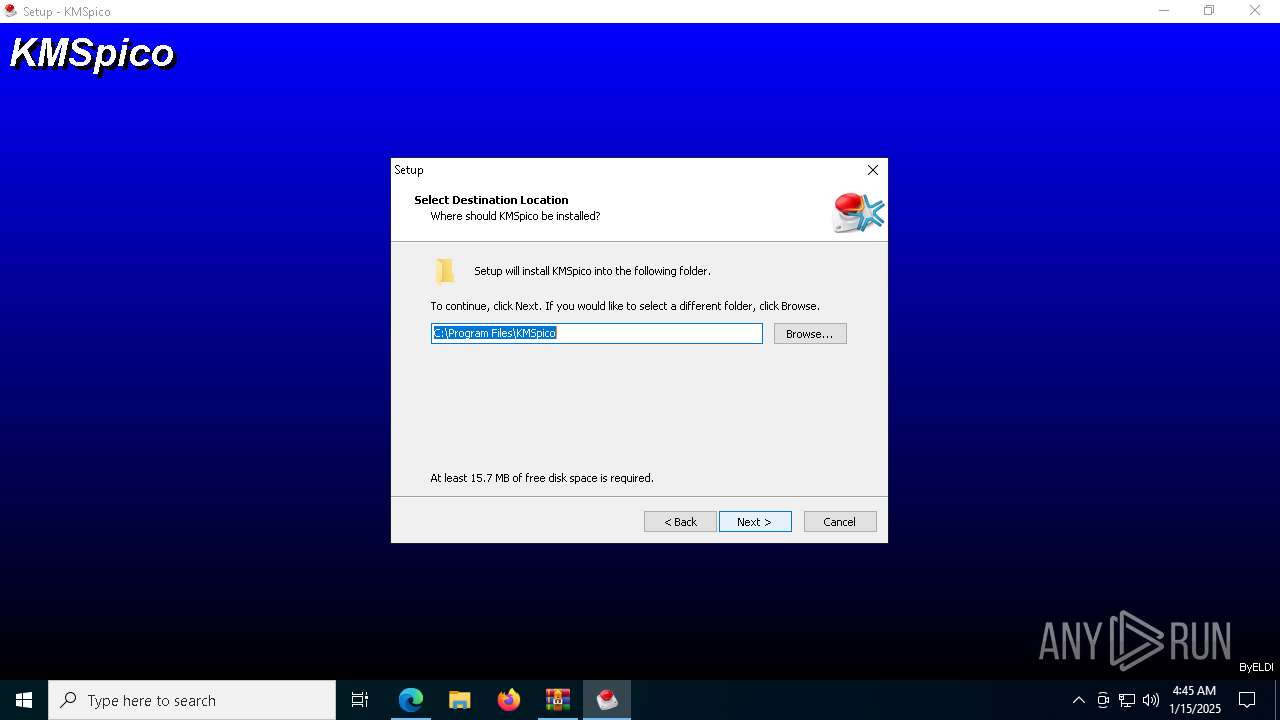
- KMSpico.exe (PID: 8068)
- KMSpico.tmp (PID: 7980)
- KMSpico.exe (PID: 936)
- KMSpico.exe (PID: 7920)
- KMSpico.tmp (PID: 2672)
- core.exe (PID: 7956)
Checks supported languages
- KMSpico.exe (PID: 8068)
- KMSpico.tmp (PID: 7980)
- identity_helper.exe (PID: 7992)
- KMSpico.tmp (PID: 5392)
- KMSpico.tmp (PID: 2672)
- KMSpico.exe (PID: 936)
- KMSpico.exe (PID: 7920)
- core.exe (PID: 7956)
- UninsHs.exe (PID: 3260)
- KMSELDI.exe (PID: 3188)
- AutoPico.exe (PID: 8180)
- SECOH-QAD.exe (PID: 7900)
- mode.com (PID: 7380)
- mode.com (PID: 5872)
- csc.exe (PID: 4968)
- mode.com (PID: 7920)
Reads the computer name
- identity_helper.exe (PID: 7992)
- KMSpico.tmp (PID: 7980)
- KMSpico.tmp (PID: 5392)
- KMSpico.tmp (PID: 2672)
- core.exe (PID: 7956)
- KMSELDI.exe (PID: 3188)
- AutoPico.exe (PID: 8180)
Application launched itself
- msedge.exe (PID: 6240)
Process checks computer location settings
- KMSpico.tmp (PID: 7980)
- KMSpico.tmp (PID: 5392)
Creates a software uninstall entry
- KMSpico.tmp (PID: 7980)
- KMSpico.tmp (PID: 2672)
Creates files or folders in the user directory
- KMSpico.tmp (PID: 7980)
The sample compiled with english language support
- KMSpico.tmp (PID: 2672)
- msedge.exe (PID: 7184)
Reads the software policy settings
- core.exe (PID: 7956)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7360)
Creates files in the program directory
- KMSpico.tmp (PID: 2672)
- KMSELDI.exe (PID: 3188)
Reads product name
- KMSELDI.exe (PID: 3188)
Reads the machine GUID from the registry
- KMSELDI.exe (PID: 3188)
- csc.exe (PID: 4968)
Local mutex for internet shortcut management
- WinRAR.exe (PID: 1868)
Checks proxy server information
- WinRAR.exe (PID: 1868)
Reads security settings of Internet Explorer
- cscript.exe (PID: 4804)
- WMIC.exe (PID: 5580)
- WMIC.exe (PID: 4520)
- WMIC.exe (PID: 5308)
- WMIC.exe (PID: 5592)
- WMIC.exe (PID: 3080)
- WMIC.exe (PID: 2392)
- WMIC.exe (PID: 540)
- WMIC.exe (PID: 7724)
- WMIC.exe (PID: 1348)
- WMIC.exe (PID: 7496)
- WMIC.exe (PID: 3124)
- WMIC.exe (PID: 5872)
- WMIC.exe (PID: 3656)
- WMIC.exe (PID: 1804)
- WMIC.exe (PID: 6904)
- WMIC.exe (PID: 2796)
- WMIC.exe (PID: 1296)
- WMIC.exe (PID: 6728)
- WMIC.exe (PID: 1220)
- WMIC.exe (PID: 7380)
- WMIC.exe (PID: 6360)
- WMIC.exe (PID: 5880)
- WMIC.exe (PID: 4576)
- WMIC.exe (PID: 7348)
- WMIC.exe (PID: 7832)
- WMIC.exe (PID: 6152)
- WMIC.exe (PID: 5916)
- WMIC.exe (PID: 6748)
- WMIC.exe (PID: 6744)
- WMIC.exe (PID: 5740)
- WMIC.exe (PID: 1476)
Checks operating system version
- cmd.exe (PID: 3840)
Starts MODE.COM to configure console settings
- mode.com (PID: 7920)
- mode.com (PID: 7380)
- mode.com (PID: 5872)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8004)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 8004)
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 4576)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 8004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
665
Monitored processes
524
Malicious processes
15
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | powershell -nop -c $ExecutionContext.SessionState.LanguageMode | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 436 | findstr /I /C:"MondoVolume" "C:\WINDOWS\Temp\c2rchk.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 488 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe" /f /v KMS_ActivationInterval /t REG_DWORD /d 43200 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 524 | reg query HKLM\SYSTEM\CurrentControlSet\Services\WinMgmt /v Start | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 524 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\0ff1ce15-a989-479d-af46-f275c6370663" /f /v KeyManagementServicePort /t REG_SZ /d "1688" /reg:32 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 524 | find /i "STOPPED" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | powershell -nop -c "&{$W=$Host.UI.RawUI.WindowSize;$B=$Host.UI.RawUI.BufferSize;$W.Height=31;$B.Height=300;$Host.UI.RawUI.WindowSize=$W;$Host.UI.RawUI.BufferSize=$B;}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | wmic path SoftwareLicensingProduct where "ApplicationID='55c92734-d682-4d71-983e-d6ec3f16059f' and Description like '%KMSCLIENT%' and PartialProductKey is not NULL" get Name /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | reg query HKCU\SOFTWARE\Microsoft\Office\16.0\Common\Licensing\LicensingNext | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | findstr /I /C:"VisioStdXVolume" "C:\WINDOWS\Temp\c2rchk.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
55 692
Read events
55 467
Write events
202
Delete events
23
Modification events
| (PID) Process: | (6240) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6240) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6240) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6240) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6240) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D353719C4D8A2F00 | |||
| (PID) Process: | (6240) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 74567E9C4D8A2F00 | |||
| (PID) Process: | (6240) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {34A590F2-C393-4801-8F4F-17E01FF4A8D6} | |||
| (PID) Process: | (6240) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {55C97141-51B2-4544-A3ED-8C6EC5F8D275} | |||
| (PID) Process: | (6240) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328474 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6E8ECC38-CF57-4143-8CD0-564E5ECD9258} | |||
| (PID) Process: | (6240) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5F0AC59C4D8A2F00 | |||
Executable files
57
Suspicious files
741
Text files
906
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6240 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1353a1.TMP | — | |
MD5:— | SHA256:— | |||
| 6240 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6240 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1353b1.TMP | — | |
MD5:— | SHA256:— | |||
| 6240 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6240 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1353b1.TMP | — | |
MD5:— | SHA256:— | |||
| 6240 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6240 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1353b1.TMP | — | |
MD5:— | SHA256:— | |||
| 6240 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6240 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1353c1.TMP | — | |
MD5:— | SHA256:— | |||
| 6240 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
63
TCP/UDP connections
237
DNS requests
227
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6608 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/2020/10/kmspico-software-1024x553.png | unknown | — | — | malicious |
6608 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/2020/10/download-kmspico.png | unknown | — | — | malicious |
6608 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/2020/10/kmspico-activator-1024x703.png | unknown | — | — | malicious |
— | — | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6608 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/2020/10/how-to-install-kmspico-1024x590.png | unknown | — | — | malicious |
6608 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/2020/10/kmspico-official-download-1024x574.png | unknown | — | — | malicious |
6608 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/2020/10/kmspico-windows-10-1024x576.png | unknown | — | — | malicious |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6608 | msedge.exe | GET | 200 | 45.12.1.24:80 | http://kmspico.io/wp-content/uploads/2020/10/windows-10-kmspico-1024x506.png | unknown | — | — | malicious |
7852 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5004 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.218.209.163:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.179:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
6608 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6240 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
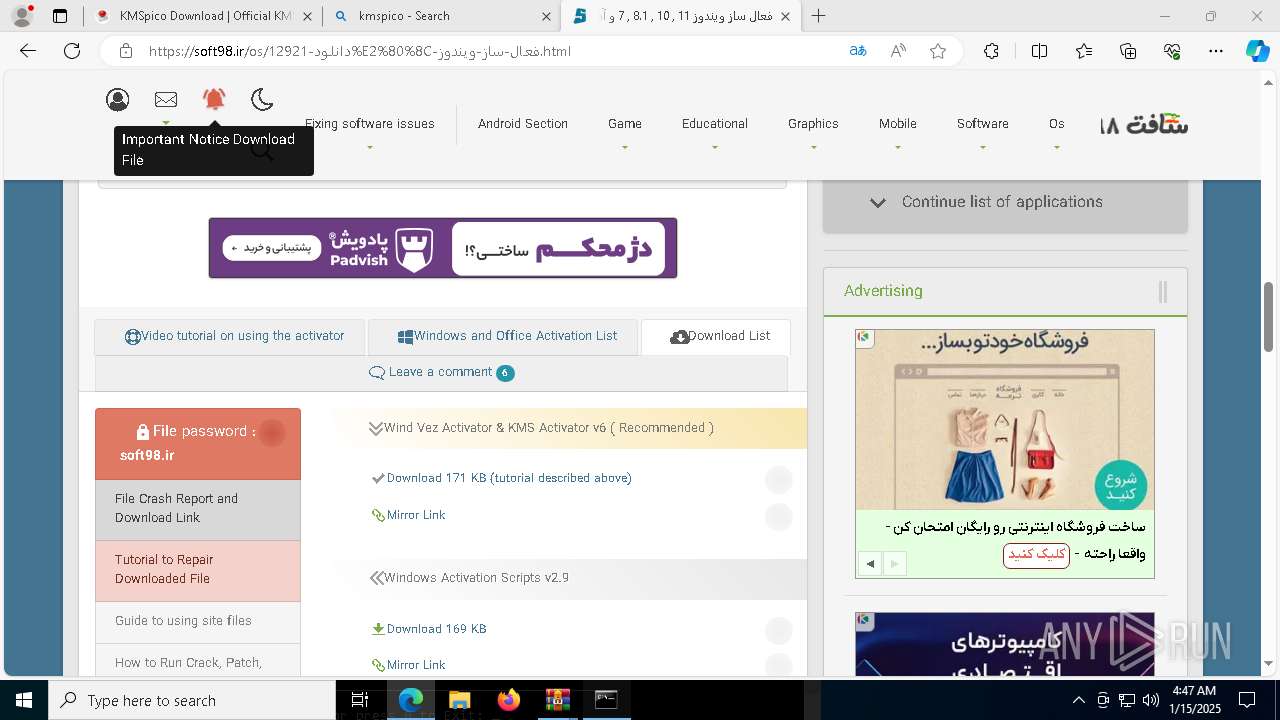
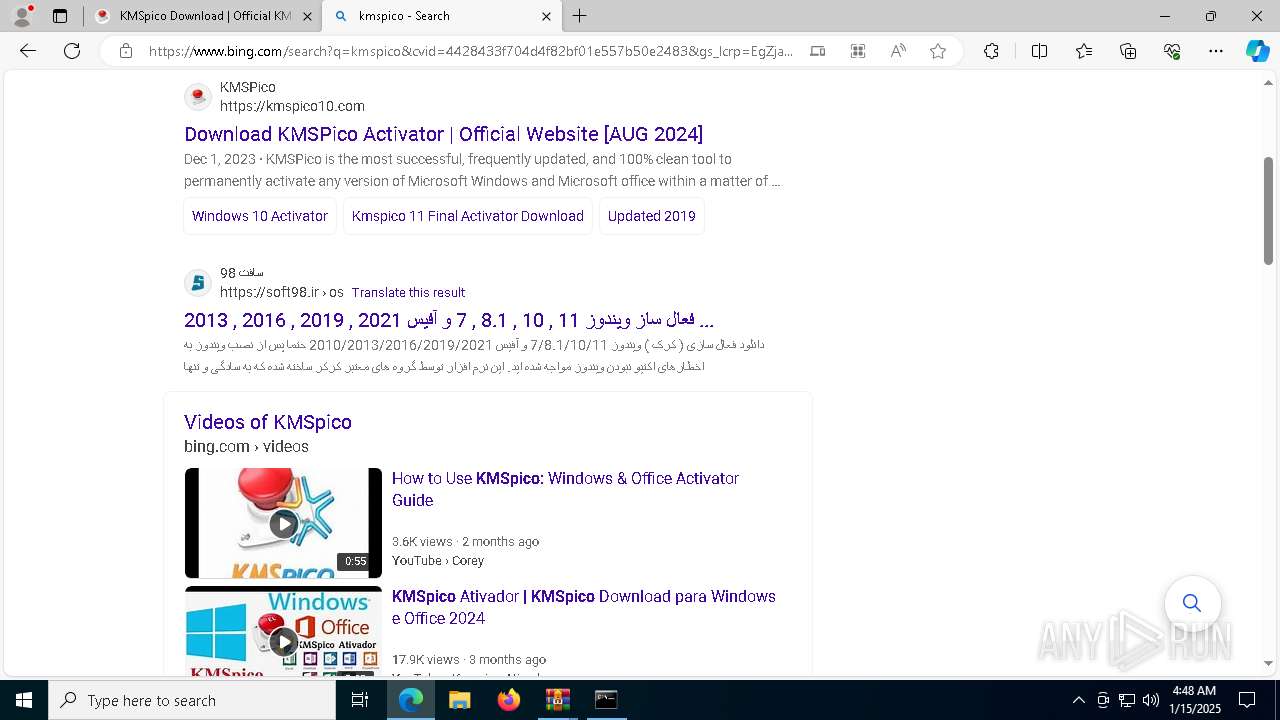
kmspico.io |
| malicious |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6608 | msedge.exe | Misc Attack | ET Threatview.io High Confidence Cobalt Strike C2 IP group 13 |
6608 | msedge.exe | Misc Attack | ET Threatview.io High Confidence Cobalt Strike C2 IP group 12 |
6608 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6608 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6608 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6608 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6608 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6608 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6608 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
6608 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
3 ETPRO signatures available at the full report