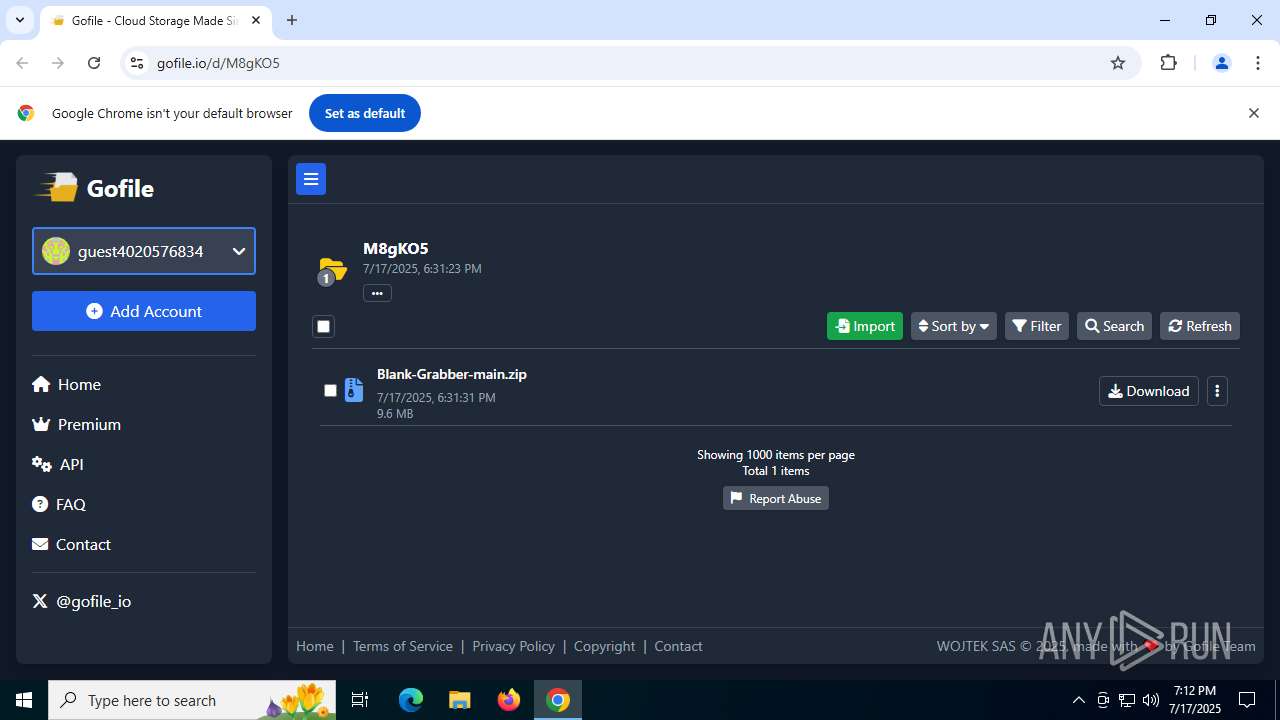
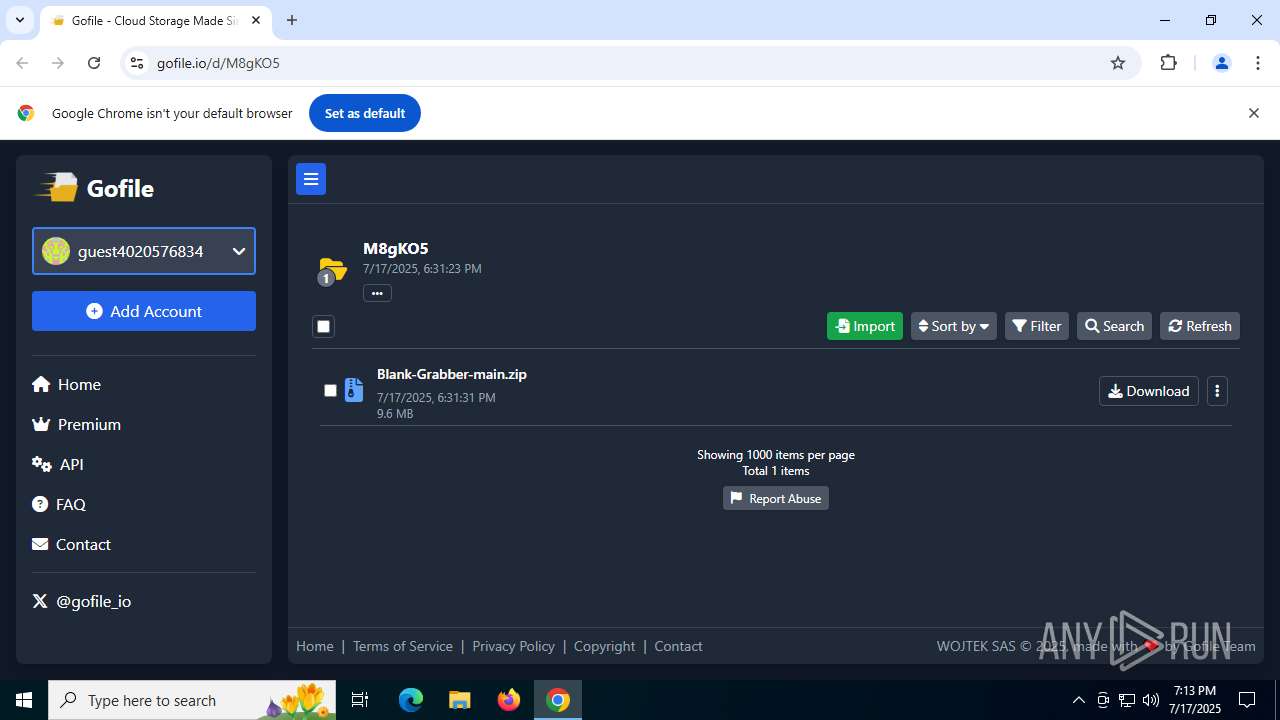
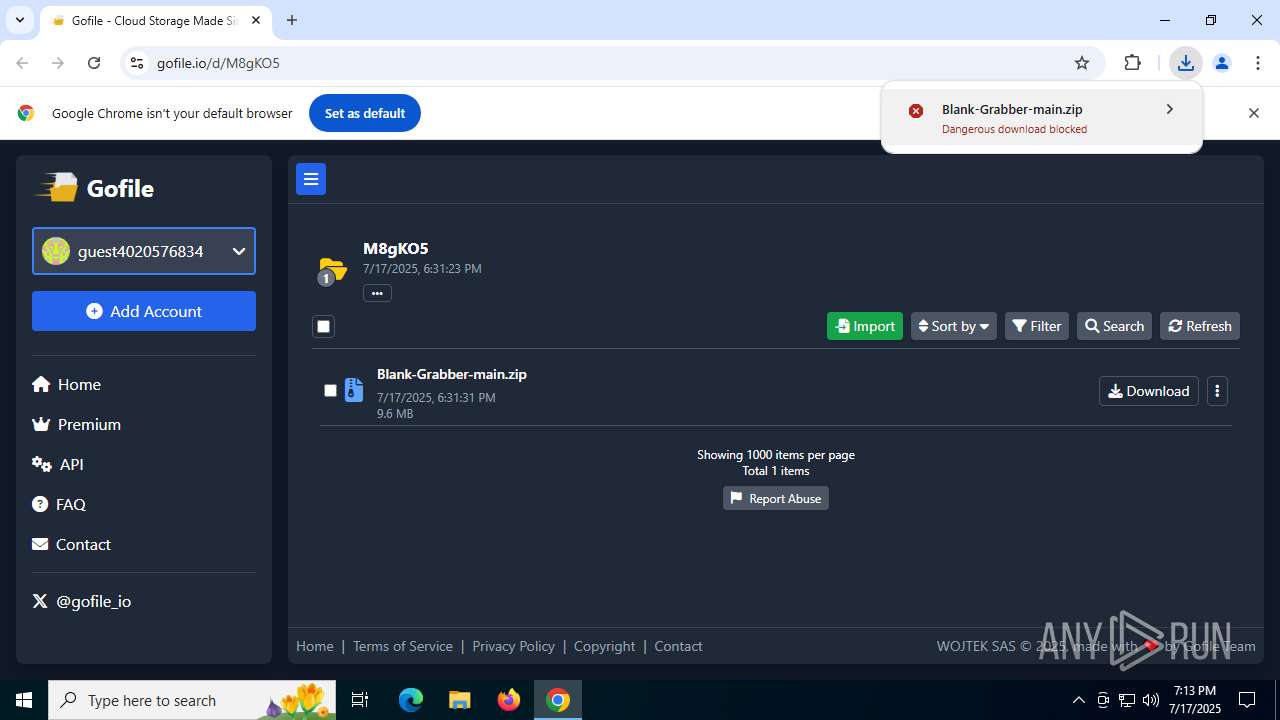
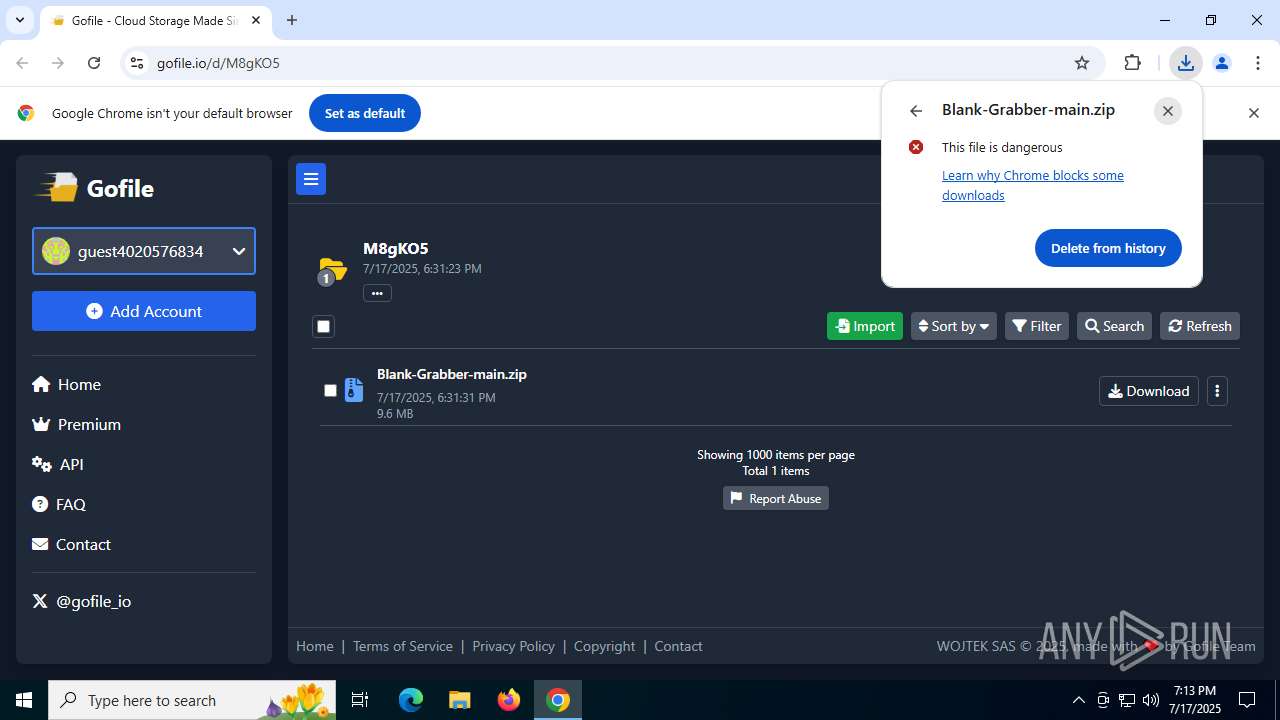
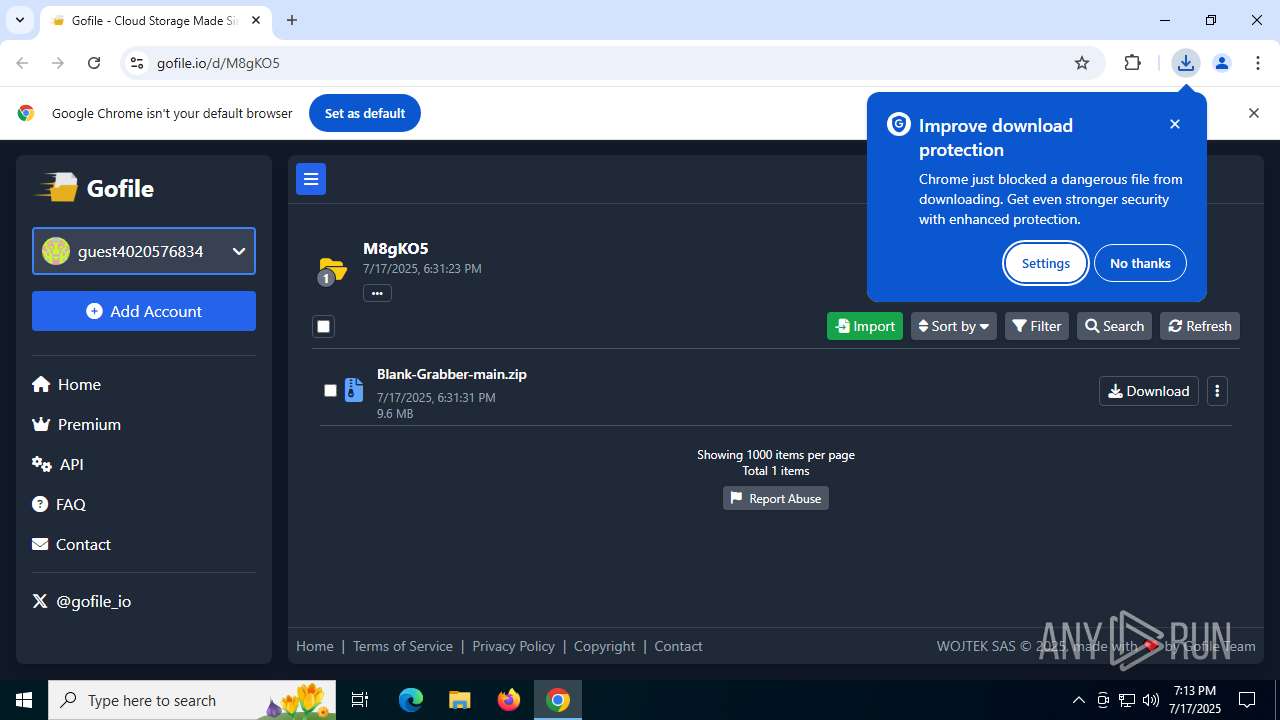
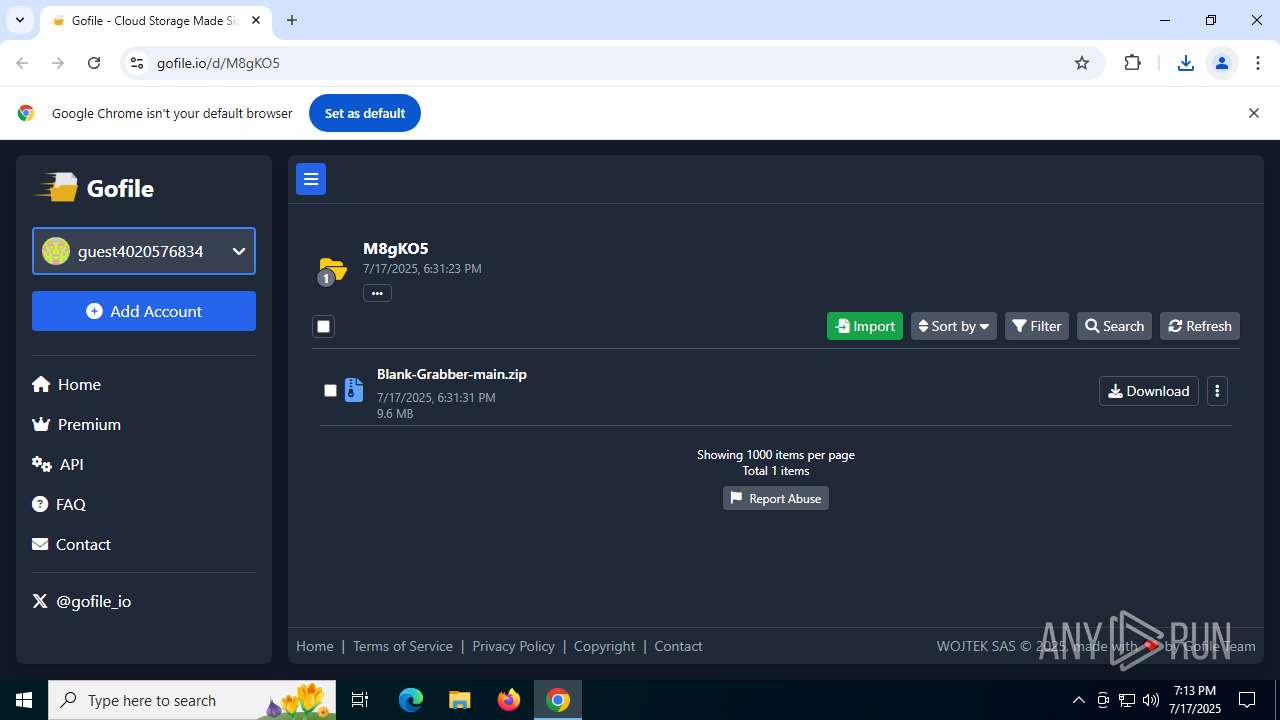
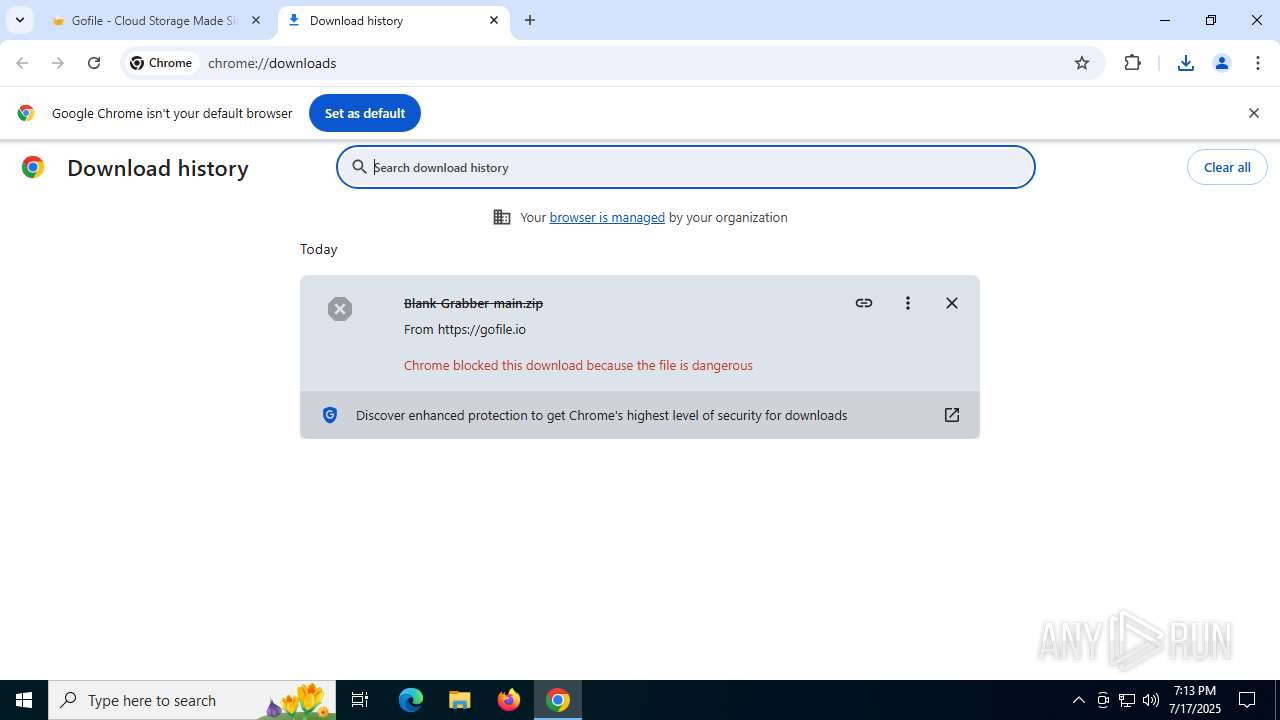
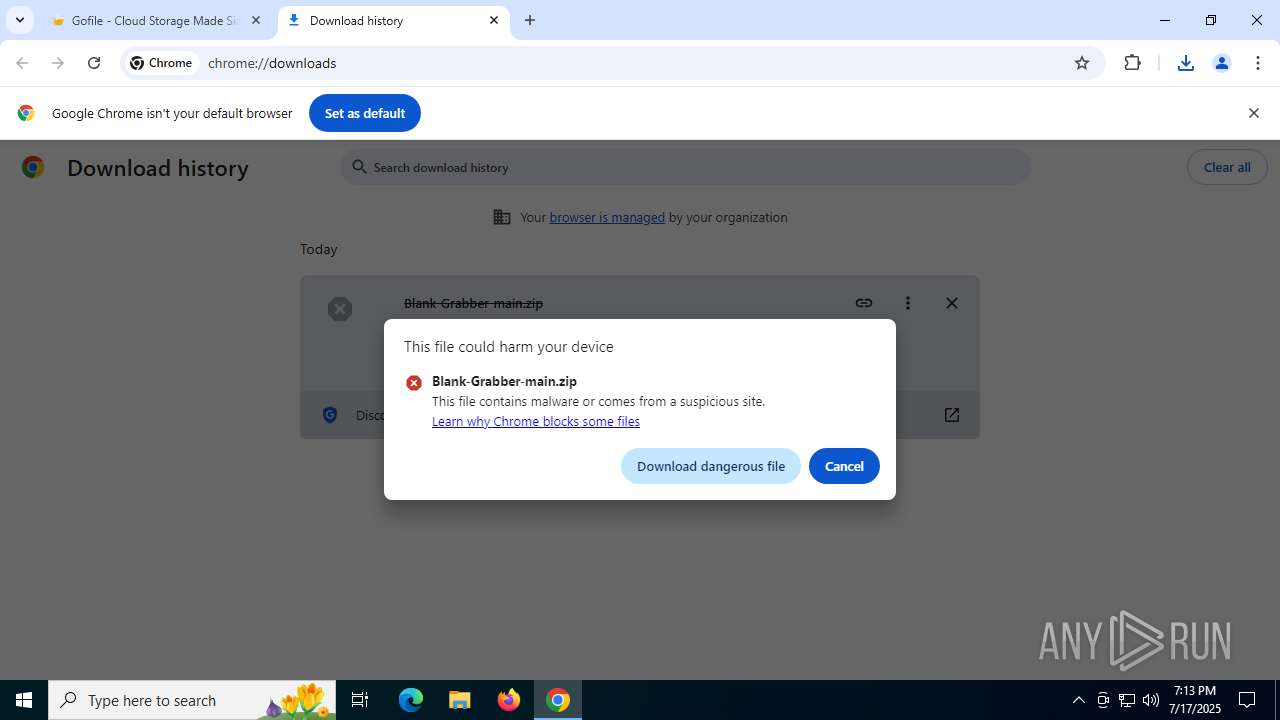
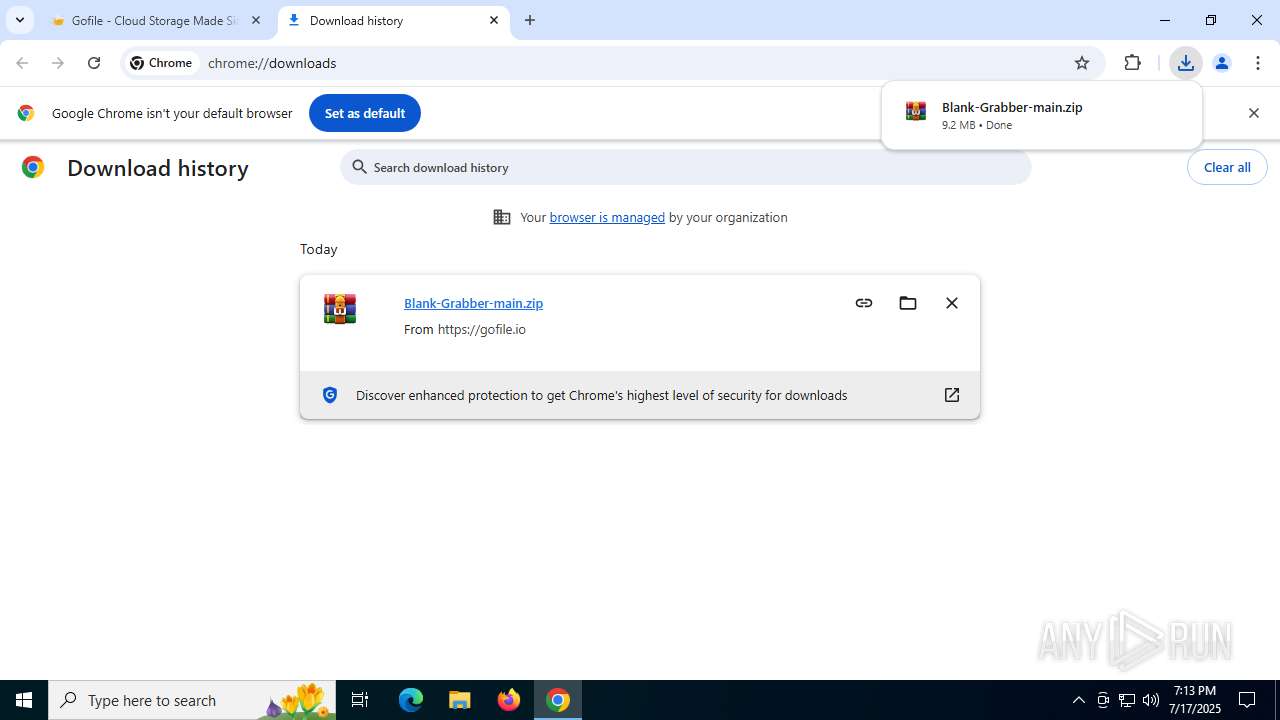
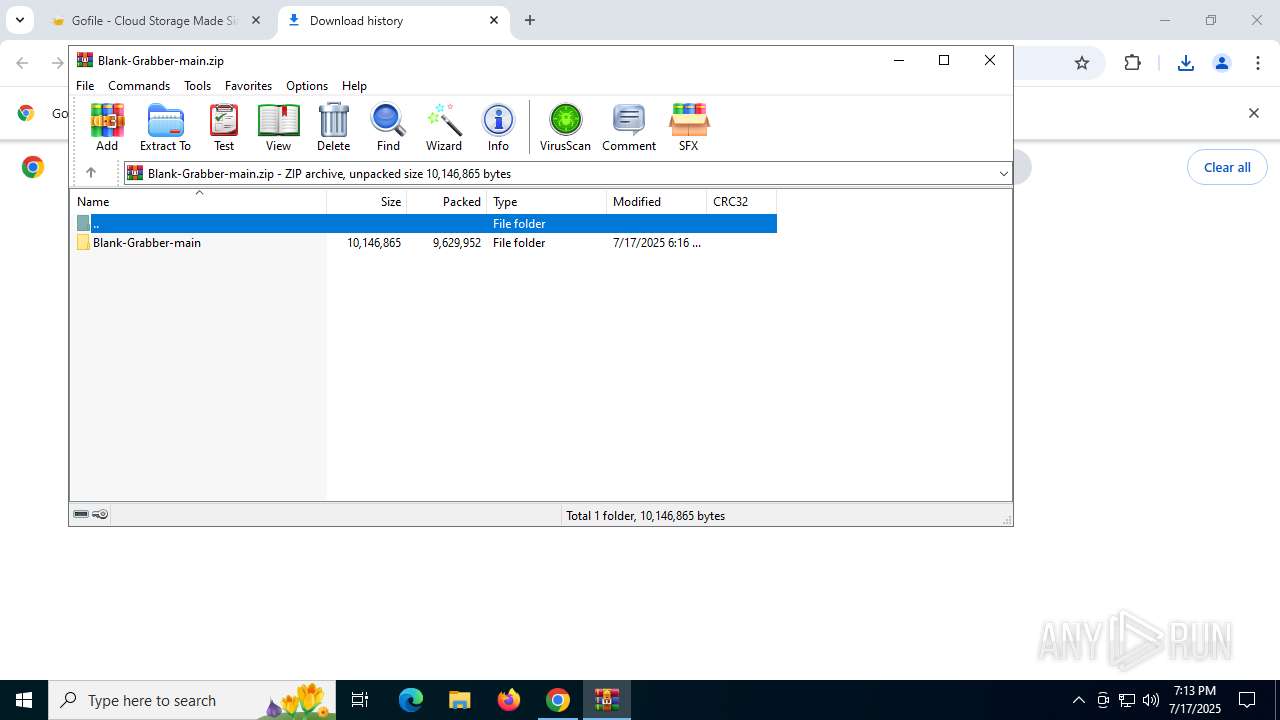
| URL: | https://gofile.io/d/M8gKO5 |
| Full analysis: | https://app.any.run/tasks/00155f5c-a61c-4c9f-a081-a0049108722b |
| Verdict: | Malicious activity |
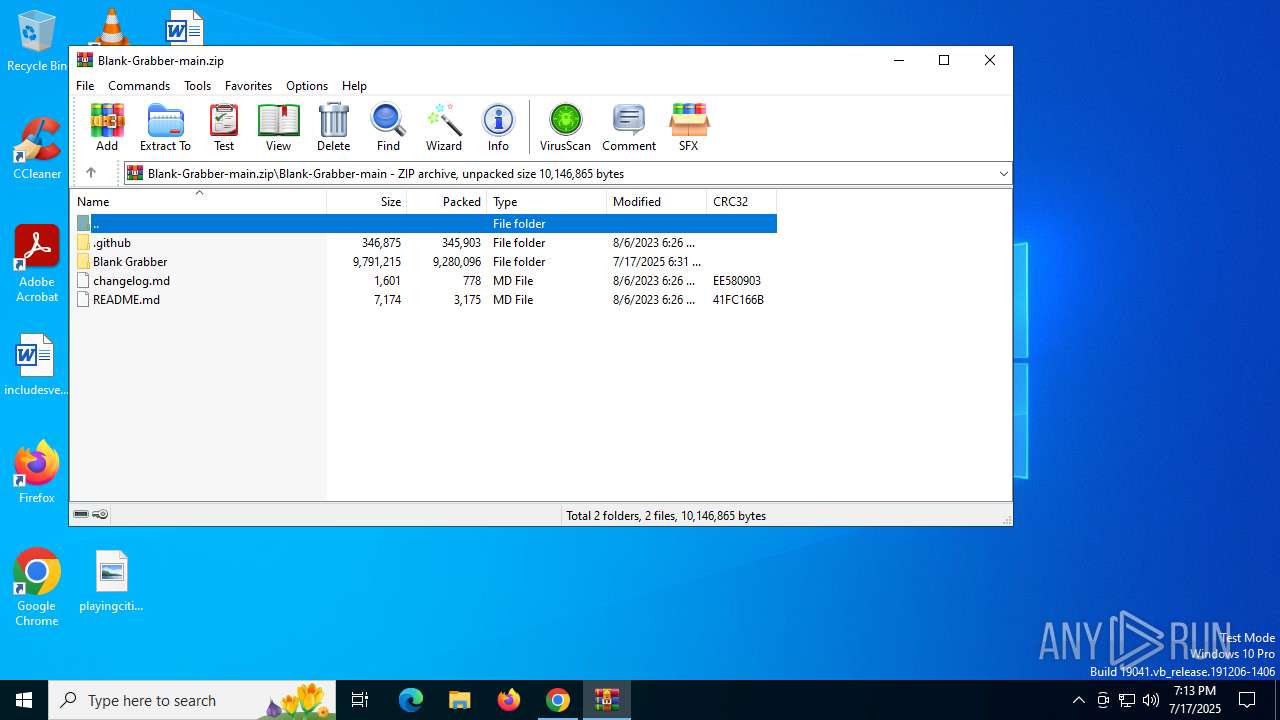
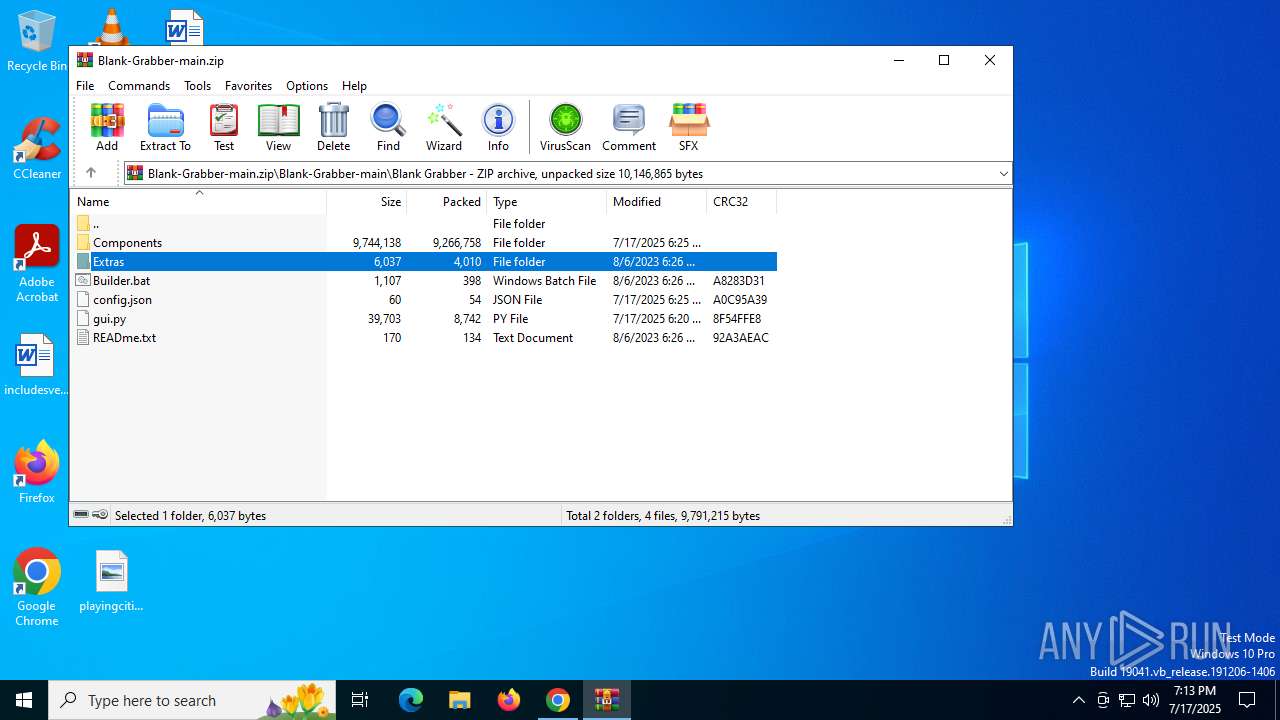
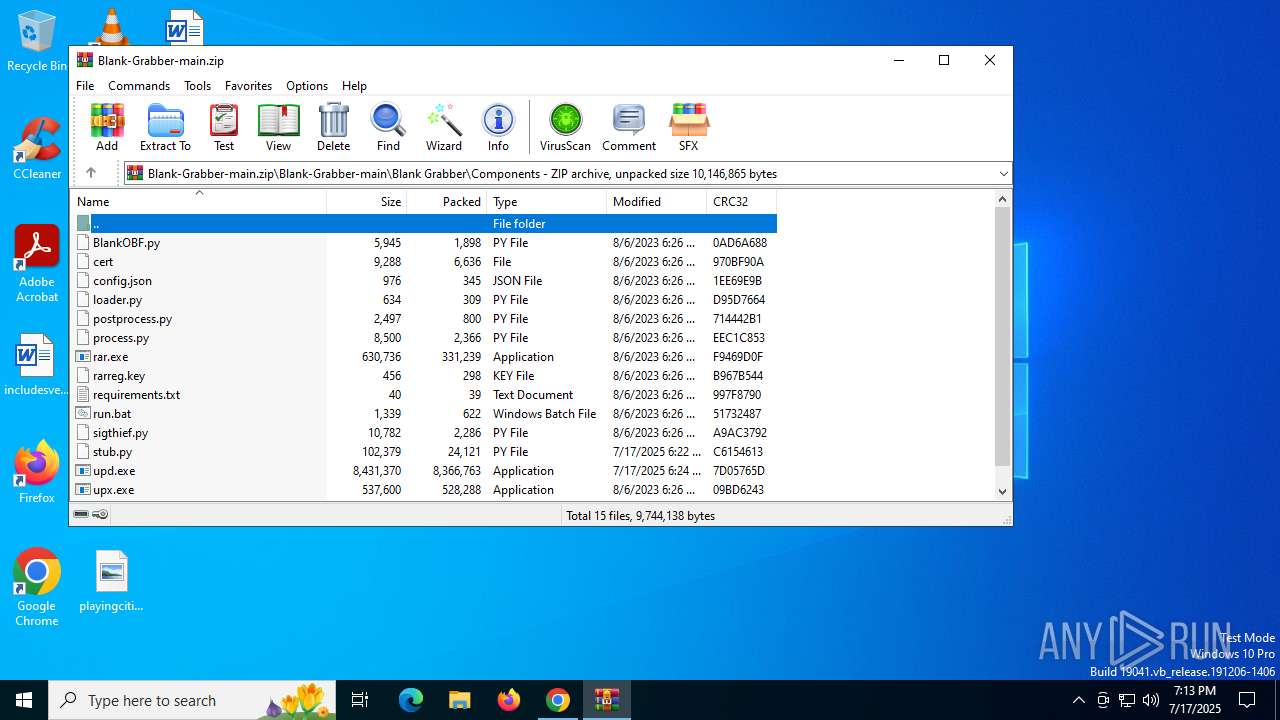
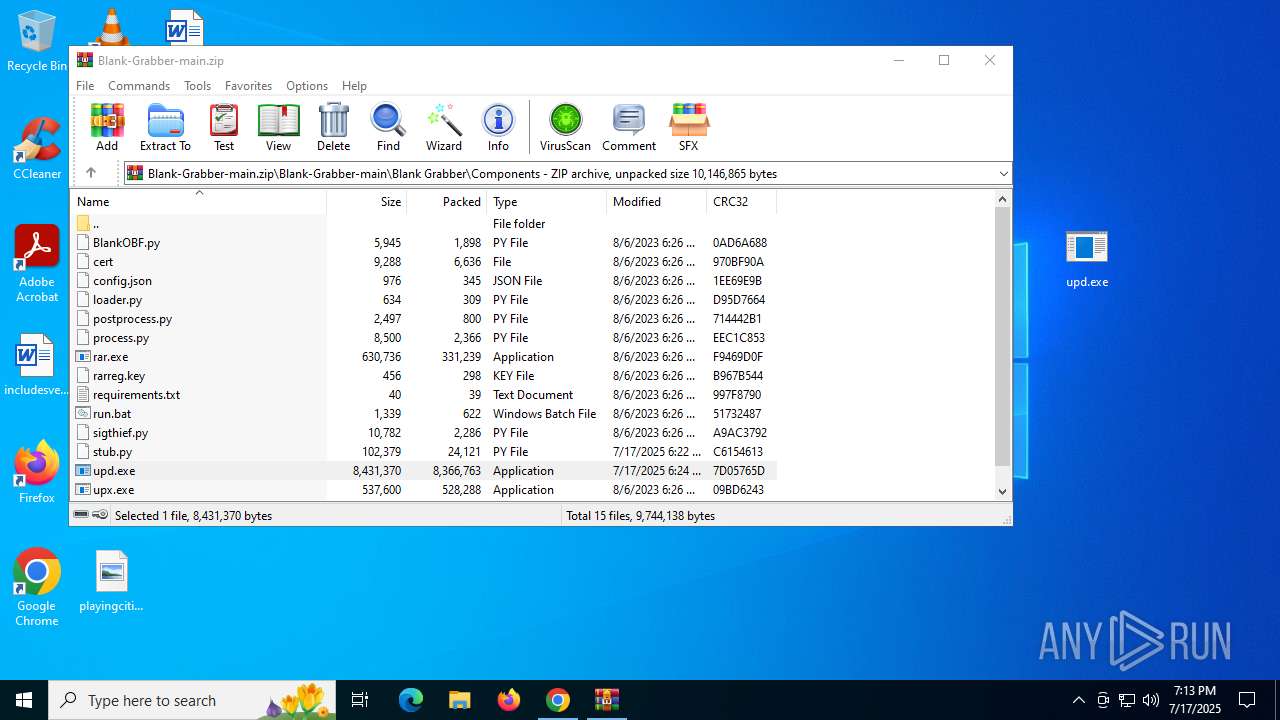
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | July 17, 2025, 19:12:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C33BC7F68957CA1188BDFAE24ABA1857 |
| SHA1: | 2F62DE6B16B3A2546568FC07C6267563C99682E5 |
| SHA256: | AA05754282A9AEDF2A31D201B5F3B86D4031872E0467116F5E86227525D8422A |
| SSDEEP: | 3:N8rxL1K:2ZE |
MALICIOUS
Executing a file with an untrusted certificate
- upd.exe (PID: 7232)
- upd.exe (PID: 7264)
- upd.exe (PID: 5988)
- upd.exe (PID: 7424)
- upd.exe (PID: 4884)
- upd.exe (PID: 8000)
- upd.exe (PID: 5368)
- upd.exe (PID: 3876)
- upd.exe (PID: 5188)
- upd.exe (PID: 7736)
BlankGrabber has been detected
- upd.exe (PID: 7232)
- upd.exe (PID: 5988)
- upd.exe (PID: 4884)
- upd.exe (PID: 5368)
- upd.exe (PID: 5188)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 6584)
- upd.exe (PID: 7424)
- cmd.exe (PID: 7872)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 2428)
Changes Windows Defender settings
- cmd.exe (PID: 6584)
- cmd.exe (PID: 2428)
- cmd.exe (PID: 7872)
Changes Controlled Folder Access settings
- powershell.exe (PID: 7496)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 7496)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 7496)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 7496)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 7496)
Changes settings for real-time protection
- powershell.exe (PID: 7496)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 7496)
Actions looks like stealing of personal data
- upd.exe (PID: 7424)
Steals credentials from Web Browsers
- upd.exe (PID: 7424)
Create files in the Startup directory
- upd.exe (PID: 7424)
Bypass execution policy to execute commands
- powershell.exe (PID: 2388)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 5184)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 8000)
BLANKGRABBER has been detected (SURICATA)
- upd.exe (PID: 7424)
SUSPICIOUS
Starts a Microsoft application from unusual location
- upd.exe (PID: 7232)
- upd.exe (PID: 7264)
- upd.exe (PID: 5988)
- upd.exe (PID: 7424)
- upd.exe (PID: 4884)
- upd.exe (PID: 8000)
- upd.exe (PID: 5368)
- upd.exe (PID: 3876)
- upd.exe (PID: 5188)
- upd.exe (PID: 7736)
Process drops legitimate windows executable
- chrome.exe (PID: 1932)
- WinRAR.exe (PID: 8060)
- upd.exe (PID: 7232)
- upd.exe (PID: 5988)
- upd.exe (PID: 7424)
- upd.exe (PID: 4884)
- upd.exe (PID: 5368)
- upd.exe (PID: 5188)
Executable content was dropped or overwritten
- upd.exe (PID: 7232)
- upd.exe (PID: 5988)
- upd.exe (PID: 7424)
- csc.exe (PID: 7436)
- upd.exe (PID: 4884)
- upd.exe (PID: 5368)
- upd.exe (PID: 5188)
Process drops python dynamic module
- upd.exe (PID: 7232)
- upd.exe (PID: 5988)
- upd.exe (PID: 4884)
- upd.exe (PID: 5368)
- upd.exe (PID: 5188)
The process drops C-runtime libraries
- upd.exe (PID: 7232)
- upd.exe (PID: 5988)
- upd.exe (PID: 4884)
- upd.exe (PID: 5368)
- upd.exe (PID: 5188)
Application launched itself
- upd.exe (PID: 7232)
- upd.exe (PID: 7264)
- upd.exe (PID: 5988)
- upd.exe (PID: 4884)
- upd.exe (PID: 5368)
- upd.exe (PID: 8000)
- upd.exe (PID: 5188)
Reads security settings of Internet Explorer
- upd.exe (PID: 7264)
- upd.exe (PID: 8000)
Reads the date of Windows installation
- upd.exe (PID: 7264)
- upd.exe (PID: 8000)
Found strings related to reading or modifying Windows Defender settings
- upd.exe (PID: 7424)
Get information on the list of running processes
- upd.exe (PID: 7424)
- cmd.exe (PID: 7528)
- cmd.exe (PID: 7280)
- cmd.exe (PID: 3460)
- cmd.exe (PID: 5400)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6584)
- cmd.exe (PID: 2428)
- cmd.exe (PID: 7872)
- cmd.exe (PID: 8052)
- cmd.exe (PID: 5184)
- cmd.exe (PID: 7724)
- cmd.exe (PID: 7632)
- cmd.exe (PID: 3576)
- cmd.exe (PID: 8020)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6584)
- cmd.exe (PID: 7872)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 2428)
Script disables Windows Defender's IPS
- cmd.exe (PID: 2428)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 7408)
- cmd.exe (PID: 7996)
- cmd.exe (PID: 4124)
Starts CMD.EXE for commands execution
- upd.exe (PID: 7424)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 7484)
- WMIC.exe (PID: 2348)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 2120)
- cmd.exe (PID: 7940)
Checks for external IP
- upd.exe (PID: 7424)
- svchost.exe (PID: 2200)
Starts application with an unusual extension
- cmd.exe (PID: 7588)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 6140)
- cmd.exe (PID: 3688)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 6304)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 4400)
- WMIC.exe (PID: 4224)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 3736)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 7316)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 5184)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 5184)
Base64-obfuscated command line is found
- cmd.exe (PID: 5184)
Accesses antivirus product name via WMI (SCRIPT)
- WMIC.exe (PID: 7596)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7936)
- cmd.exe (PID: 7680)
- cmd.exe (PID: 8012)
- cmd.exe (PID: 3876)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 3740)
- cmd.exe (PID: 7584)
- cmd.exe (PID: 6796)
CSC.EXE is used to compile C# code
- csc.exe (PID: 7436)
Captures screenshot (POWERSHELL)
- powershell.exe (PID: 2388)
The executable file from the user directory is run by the CMD process
- rar.exe (PID: 6352)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 2032)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 6736)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 8032)
INFO
Reads the computer name
- upd.exe (PID: 7232)
- upd.exe (PID: 7264)
- upd.exe (PID: 5988)
- upd.exe (PID: 7424)
- MpCmdRun.exe (PID: 8000)
- upd.exe (PID: 4884)
- upd.exe (PID: 8000)
- upd.exe (PID: 5368)
- upd.exe (PID: 5188)
The sample compiled with english language support
- upd.exe (PID: 7232)
- chrome.exe (PID: 1932)
- WinRAR.exe (PID: 8060)
- upd.exe (PID: 5988)
- upd.exe (PID: 7424)
- upd.exe (PID: 4884)
- upd.exe (PID: 5368)
- upd.exe (PID: 5188)
Create files in a temporary directory
- upd.exe (PID: 7232)
- upd.exe (PID: 7264)
- upd.exe (PID: 7424)
- upd.exe (PID: 5988)
- csc.exe (PID: 7436)
- cvtres.exe (PID: 6332)
- upd.exe (PID: 4884)
- MpCmdRun.exe (PID: 8000)
- upd.exe (PID: 8000)
- upd.exe (PID: 5368)
- rar.exe (PID: 6352)
- upd.exe (PID: 3876)
- upd.exe (PID: 5188)
- upd.exe (PID: 7736)
Checks supported languages
- upd.exe (PID: 7232)
- upd.exe (PID: 7264)
- upd.exe (PID: 5988)
- upd.exe (PID: 7424)
- tree.com (PID: 7616)
- tree.com (PID: 7380)
- tree.com (PID: 7596)
- tree.com (PID: 7296)
- tree.com (PID: 4512)
- tree.com (PID: 7360)
- cvtres.exe (PID: 6332)
- csc.exe (PID: 7436)
- upd.exe (PID: 4884)
- MpCmdRun.exe (PID: 8000)
- upd.exe (PID: 8000)
- upd.exe (PID: 5368)
- upd.exe (PID: 3876)
- rar.exe (PID: 6352)
- upd.exe (PID: 5188)
- upd.exe (PID: 7736)
Manual execution by a user
- upd.exe (PID: 7232)
- upd.exe (PID: 4884)
- upd.exe (PID: 5188)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8060)
Reads Microsoft Office registry keys
- chrome.exe (PID: 1932)
Application launched itself
- chrome.exe (PID: 1932)
Process checks computer location settings
- upd.exe (PID: 7264)
- upd.exe (PID: 8000)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7484)
- WMIC.exe (PID: 4400)
- WMIC.exe (PID: 7596)
- WMIC.exe (PID: 6736)
- WMIC.exe (PID: 3624)
- WMIC.exe (PID: 2348)
- WMIC.exe (PID: 4224)
Checks the directory tree
- tree.com (PID: 7616)
- tree.com (PID: 7380)
- tree.com (PID: 7596)
- tree.com (PID: 7296)
- tree.com (PID: 4512)
- tree.com (PID: 7360)
Launching a file from the Startup directory
- upd.exe (PID: 7424)
Creates files in the program directory
- upd.exe (PID: 7424)
The Powershell gets current clipboard
- powershell.exe (PID: 7576)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7412)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 7756)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7412)
- powershell.exe (PID: 7252)
- powershell.exe (PID: 5236)
Reads the machine GUID from the registry
- csc.exe (PID: 7436)
- rar.exe (PID: 6352)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 4916)
Checks proxy server information
- slui.exe (PID: 8132)
Reads the software policy settings
- slui.exe (PID: 8132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
295
Monitored processes
152
Malicious processes
13
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1028 | taskkill /F /PID 5468 | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3036,i,581537414602444483,6955015443231798739,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1816 | C:\WINDOWS\system32\cmd.exe /c "REG QUERY HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class\{4D36E968-E325-11CE-BFC1-08002BE10318}\0000\ProviderName 2" | C:\Windows\System32\cmd.exe | — | upd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://gofile.io/d/M8gKO5" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 1 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x21c,0x220,0x224,0x1fc,0x228,0x7ffc4392fff8,0x7ffc43930004,0x7ffc43930010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 1 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2028 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2032 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
67 798
Read events
67 781
Write events
17
Delete events
0
Modification events
| (PID) Process: | (1932) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1932) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1932) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1932) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1932) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1932) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
| (PID) Process: | (8060) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8060) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8060) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8060) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
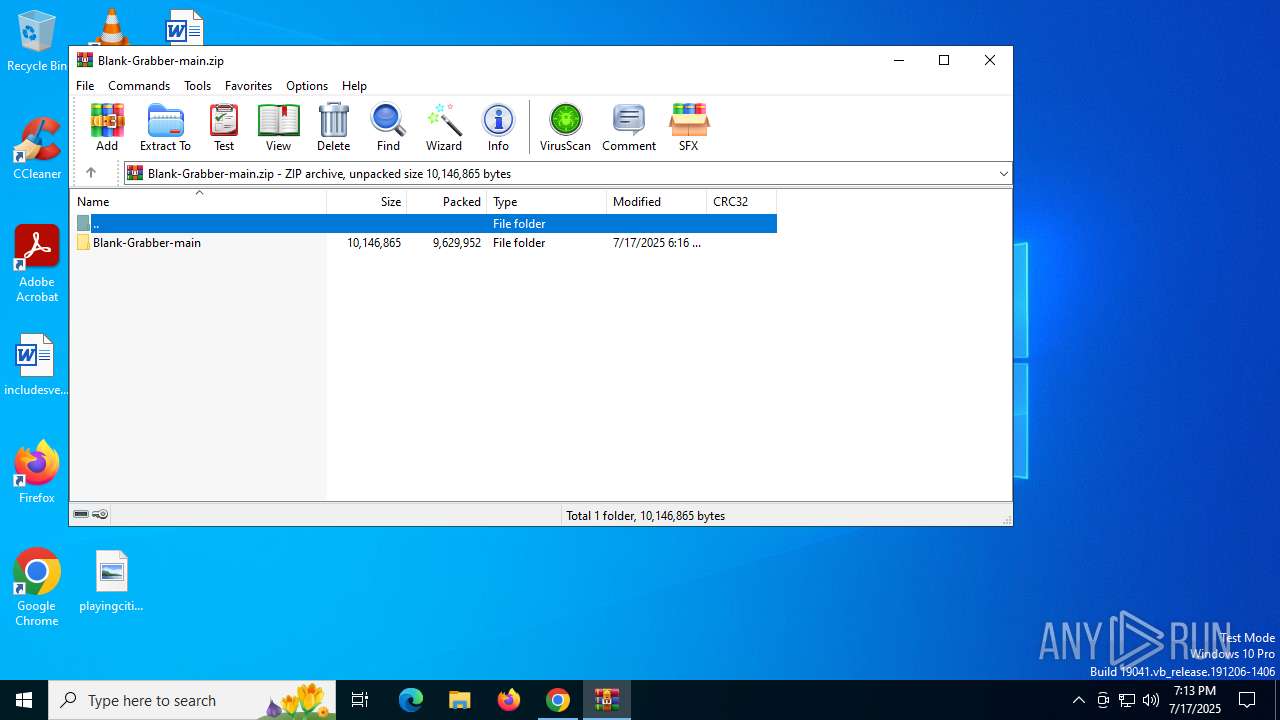
Value: C:\Users\admin\Downloads\Blank-Grabber-main.zip | |||
Executable files
293
Suspicious files
63
Text files
89
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF18ccd0.TMP | — | |
MD5:— | SHA256:— | |||
| 1932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF18cce0.TMP | — | |
MD5:— | SHA256:— | |||
| 1932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF18ccf0.TMP | — | |
MD5:— | SHA256:— | |||
| 1932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old~RF18ccf0.TMP | — | |
MD5:— | SHA256:— | |||
| 1932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF18ccff.TMP | — | |
MD5:— | SHA256:— | |||
| 1932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF18ccff.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
51
DNS requests
50
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5468 | chrome.exe | GET | 200 | 142.250.184.206:80 | http://clients2.google.com/time/1/current?cup2key=8:PfFcHO8bsBnzg13bcXOJ8MxUgQD85RHudQVQsDFUmTI&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
3396 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7720 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8188 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6bqrogtrdeb2aualzvp3izob2a_3/hajigopbbjhghbfimgkfmpenfkclmohk_3_all_acvntnsfjuuxi3fmeykewq3kivfq.crx3 | unknown | — | — | whitelisted |
7720 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8188 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6bqrogtrdeb2aualzvp3izob2a_3/hajigopbbjhghbfimgkfmpenfkclmohk_3_all_acvntnsfjuuxi3fmeykewq3kivfq.crx3 | unknown | — | — | whitelisted |
8188 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6bqrogtrdeb2aualzvp3izob2a_3/hajigopbbjhghbfimgkfmpenfkclmohk_3_all_acvntnsfjuuxi3fmeykewq3kivfq.crx3 | unknown | — | — | whitelisted |
8188 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad6bqrogtrdeb2aualzvp3izob2a_3/hajigopbbjhghbfimgkfmpenfkclmohk_3_all_acvntnsfjuuxi3fmeykewq3kivfq.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5968 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5468 | chrome.exe | 216.58.206.74:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
5468 | chrome.exe | 142.250.184.206:80 | clients2.google.com | GOOGLE | US | whitelisted |
5468 | chrome.exe | 51.75.242.210:443 | gofile.io | OVH SAS | FR | whitelisted |
5468 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5468 | chrome.exe | 51.159.98.203:443 | s.gofile.io | Online S.a.s. | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
gofile.io |
| whitelisted |
accounts.google.com |
| whitelisted |
s.gofile.io |
| whitelisted |
api.gofile.io |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5468 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
5468 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
5468 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
5468 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
5468 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
5468 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
5468 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
5468 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
5468 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
5468 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |