| File name: | SOA & UNPAID INVOICES.pdf.exe |
| Full analysis: | https://app.any.run/tasks/5f1f34bd-3808-4699-9d0e-007d13815dbe |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | May 21, 2022, 06:24:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | B6E3EA3CA41FADF4B2D8E8C4547BBB3B |
| SHA1: | DBD634B213E1DBA07B9D3CB4B880D2DB158818F7 |
| SHA256: | A9E823696E9C25DDA75EAE39878E430238E78B379BB51A0658D8FD93BD2C604D |
| SSDEEP: | 12288:9JKJFITiv73meT+jnSX7Lmgnb0WWmvVeAgy2+uKjSE:9JN+vSe6n4mgnbCmvEAz2+Jj |
MALICIOUS
Uses Task Scheduler to run other applications
- SOA & UNPAID INVOICES.pdf.exe (PID: 3968)
- SOA & UNPAID INVOICES.pdf.exe (PID: 1532)
Drops executable file immediately after starts
- SOA & UNPAID INVOICES.pdf.exe (PID: 3968)
- DllHost.exe (PID: 4028)
- cmd.exe (PID: 3424)
- SOA & UNPAID INVOICES.pdf.exe (PID: 1980)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3912)
- schtasks.exe (PID: 2072)
AVEMARIA was detected
- SOA & UNPAID INVOICES.pdf.exe (PID: 3020)
- SOA & UNPAID INVOICES.pdf.exe (PID: 1980)
Connects to CnC server
- SOA & UNPAID INVOICES.pdf.exe (PID: 3020)
- SOA & UNPAID INVOICES.pdf.exe (PID: 1980)
Runs app for hidden code execution
- SOA & UNPAID INVOICES.pdf.exe (PID: 3020)
Loads dropped or rewritten executable
- dism.exe (PID: 2896)
Creates or modifies windows services
- SOA & UNPAID INVOICES.pdf.exe (PID: 1980)
SUSPICIOUS
Drops a file with a compile date too recent
- SOA & UNPAID INVOICES.pdf.exe (PID: 3968)
- cmd.exe (PID: 3424)
- DllHost.exe (PID: 4028)
- SOA & UNPAID INVOICES.pdf.exe (PID: 1980)
Executable content was dropped or overwritten
- SOA & UNPAID INVOICES.pdf.exe (PID: 3968)
- cmd.exe (PID: 3424)
- DllHost.exe (PID: 4028)
- SOA & UNPAID INVOICES.pdf.exe (PID: 1980)
Creates files in the user directory
- SOA & UNPAID INVOICES.pdf.exe (PID: 3968)
Reads the computer name
- SOA & UNPAID INVOICES.pdf.exe (PID: 3020)
- SOA & UNPAID INVOICES.pdf.exe (PID: 3968)
- cmd.exe (PID: 3424)
- SOA & UNPAID INVOICES.pdf.exe (PID: 1532)
- SOA & UNPAID INVOICES.pdf.exe (PID: 1980)
- powershell.exe (PID: 1392)
- powershell.exe (PID: 1720)
Checks supported languages
- SOA & UNPAID INVOICES.pdf.exe (PID: 3968)
- SOA & UNPAID INVOICES.pdf.exe (PID: 3020)
- cmd.exe (PID: 3424)
- SOA & UNPAID INVOICES.pdf.exe (PID: 1532)
- SOA & UNPAID INVOICES.pdf.exe (PID: 1980)
- powershell.exe (PID: 1720)
- powershell.exe (PID: 1392)
Application launched itself
- SOA & UNPAID INVOICES.pdf.exe (PID: 3968)
- SOA & UNPAID INVOICES.pdf.exe (PID: 1532)
Starts CMD.EXE for commands execution
- SOA & UNPAID INVOICES.pdf.exe (PID: 3020)
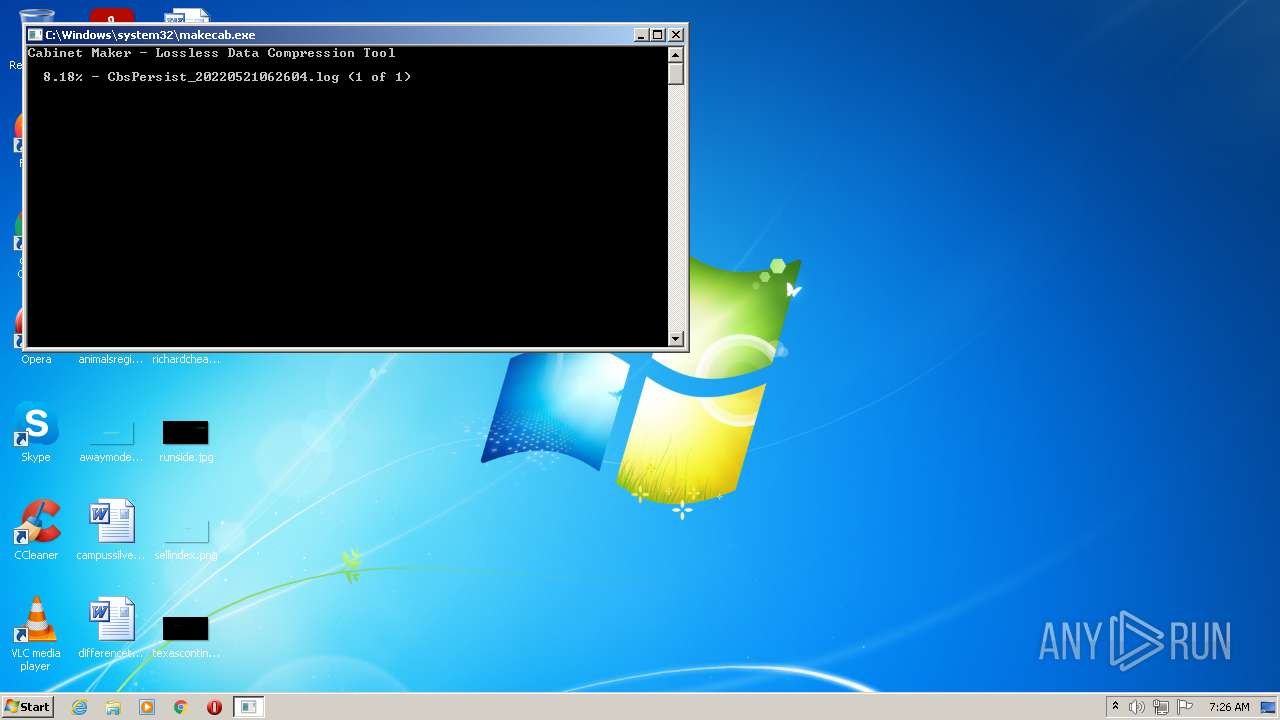
Creates files in the Windows directory
- pkgmgr.exe (PID: 2908)
- makecab.exe (PID: 2968)
- SOA & UNPAID INVOICES.pdf.exe (PID: 1980)
Executed via COM
- DllHost.exe (PID: 4028)
Creates a directory in Program Files
- SOA & UNPAID INVOICES.pdf.exe (PID: 1980)
Executes PowerShell scripts
- SOA & UNPAID INVOICES.pdf.exe (PID: 1980)
- SOA & UNPAID INVOICES.pdf.exe (PID: 1532)
Creates files in the program directory
- SOA & UNPAID INVOICES.pdf.exe (PID: 1980)
INFO
Reads the computer name
- schtasks.exe (PID: 3912)
- DllHost.exe (PID: 4028)
- dism.exe (PID: 2896)
- schtasks.exe (PID: 2072)
Checks supported languages
- schtasks.exe (PID: 3912)
- DllHost.exe (PID: 4028)
- dism.exe (PID: 2896)
- makecab.exe (PID: 2968)
- pkgmgr.exe (PID: 2908)
- schtasks.exe (PID: 2072)
Reads settings of System Certificates
- powershell.exe (PID: 1720)
- powershell.exe (PID: 1392)
Checks Windows Trust Settings
- powershell.exe (PID: 1720)
- powershell.exe (PID: 1392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | CIS153FinalProject |
| OriginalFileName: | HostExecutionContextMana.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © 2021 |
| InternalName: | HostExecutionContextMana.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | CIS153FinalProject |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0xa8b82 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 2560 |
| CodeSize: | 683008 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| TimeStamp: | 2060:02:22 06:13:59+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jan-1924 22:45:43 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | CIS153FinalProject |
| FileVersion: | 1.0.0.0 |
| InternalName: | HostExecutionContextMana.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFilename: | HostExecutionContextMana.exe |
| ProductName: | CIS153FinalProject |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 16-Jan-1924 22:45:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000A6B88 | 0x000A6C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.46455 |
.rsrc | 0x000AA000 | 0x00000614 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.45327 |
.reloc | 0x000AC000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
58
Monitored processes
14
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1392 | powershell Add-MpPreference -ExclusionPath C:\ | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | SOA & UNPAID INVOICES.pdf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1532 | "C:\Users\admin\AppData\Local\Temp\SOA & UNPAID INVOICES.pdf.exe" | C:\Users\admin\AppData\Local\Temp\SOA & UNPAID INVOICES.pdf.exe | — | dism.exe | |||||||||||
User: admin Integrity Level: HIGH Description: CIS153FinalProject Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1720 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath "C:\Users\admin\AppData\Roaming\TsWISurTqG.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | SOA & UNPAID INVOICES.pdf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1980 | "C:\Users\admin\AppData\Local\Temp\SOA & UNPAID INVOICES.pdf.exe" | C:\Users\admin\AppData\Local\Temp\SOA & UNPAID INVOICES.pdf.exe | SOA & UNPAID INVOICES.pdf.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: CIS153FinalProject Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2072 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\TsWISurTqG" /XML "C:\Users\admin\AppData\Local\Temp\tmpD2CE.tmp" | C:\Windows\System32\schtasks.exe | — | SOA & UNPAID INVOICES.pdf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2896 | "C:\Windows\system32\dism.exe" /online /norestart /apply-unattend:"C:\Users\admin\AppData\Local\Temp\ellocnak.xml" | C:\Windows\system32\dism.exe | — | pkgmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2908 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Package Manager Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2968 | "C:\Windows\system32\makecab.exe" C:\Windows\Logs\CBS\CbsPersist_20220521062604.log C:\Windows\Logs\CBS\CbsPersist_20220521062604.cab | C:\Windows\system32\makecab.exe | — | pkgmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3020 | "C:\Users\admin\AppData\Local\Temp\SOA & UNPAID INVOICES.pdf.exe" | C:\Users\admin\AppData\Local\Temp\SOA & UNPAID INVOICES.pdf.exe | SOA & UNPAID INVOICES.pdf.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: CIS153FinalProject Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3424 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | SOA & UNPAID INVOICES.pdf.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
9 046
Read events
8 965
Write events
81
Delete events
0
Modification events
| (PID) Process: | (3968) SOA & UNPAID INVOICES.pdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3968) SOA & UNPAID INVOICES.pdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3968) SOA & UNPAID INVOICES.pdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3968) SOA & UNPAID INVOICES.pdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3020) SOA & UNPAID INVOICES.pdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (3020) SOA & UNPAID INVOICES.pdf.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
| (PID) Process: | (3020) SOA & UNPAID INVOICES.pdf.exe | Key: | HKEY_CURRENT_USER\Software\_rptls |
| Operation: | write | Name: | Install |
Value: C:\Users\admin\AppData\Local\Temp\SOA & UNPAID INVOICES.pdf.exe | |||
| (PID) Process: | (3424) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3424) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3424) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
4
Suspicious files
11
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2908 | pkgmgr.exe | C:\Windows\Logs\CBS\CbsPersist_20220521062604.log | — | |
MD5:— | SHA256:— | |||
| 1980 | SOA & UNPAID INVOICES.pdf.exe | C:\Windows\System32\rfxvmt.dll | — | |
MD5:— | SHA256:— | |||
| 3968 | SOA & UNPAID INVOICES.pdf.exe | C:\Users\admin\AppData\Roaming\TsWISurTqG.exe | executable | |
MD5:— | SHA256:— | |||
| 3968 | SOA & UNPAID INVOICES.pdf.exe | C:\Users\admin\AppData\Local\Temp\tmpEEF6.tmp | xml | |
MD5:— | SHA256:— | |||
| 2968 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_2968_3 | binary | |
MD5:— | SHA256:— | |||
| 2908 | pkgmgr.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:— | SHA256:— | |||
| 2968 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_2968_5 | binary | |
MD5:— | SHA256:— | |||
| 2968 | makecab.exe | C:\Windows\Logs\CBS\CbsPersist_20220521062604.cab | compressed | |
MD5:— | SHA256:— | |||
| 1532 | SOA & UNPAID INVOICES.pdf.exe | C:\Users\admin\AppData\Local\Temp\tmpD2CE.tmp | xml | |
MD5:— | SHA256:— | |||
| 1980 | SOA & UNPAID INVOICES.pdf.exe | C:\Program Files\Microsoft DN1\rdpwrap.ini | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3020 | SOA & UNPAID INVOICES.pdf.exe | 76.8.53.133:1198 | — | Quonix Networks Inc. | US | malicious |
1980 | SOA & UNPAID INVOICES.pdf.exe | 76.8.53.133:1198 | — | Quonix Networks Inc. | US | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3020 | SOA & UNPAID INVOICES.pdf.exe | A Network Trojan was detected | AV TROJAN Ave Maria RAT CnC Response |
1980 | SOA & UNPAID INVOICES.pdf.exe | A Network Trojan was detected | AV TROJAN Ave Maria RAT CnC Response |
3 ETPRO signatures available at the full report