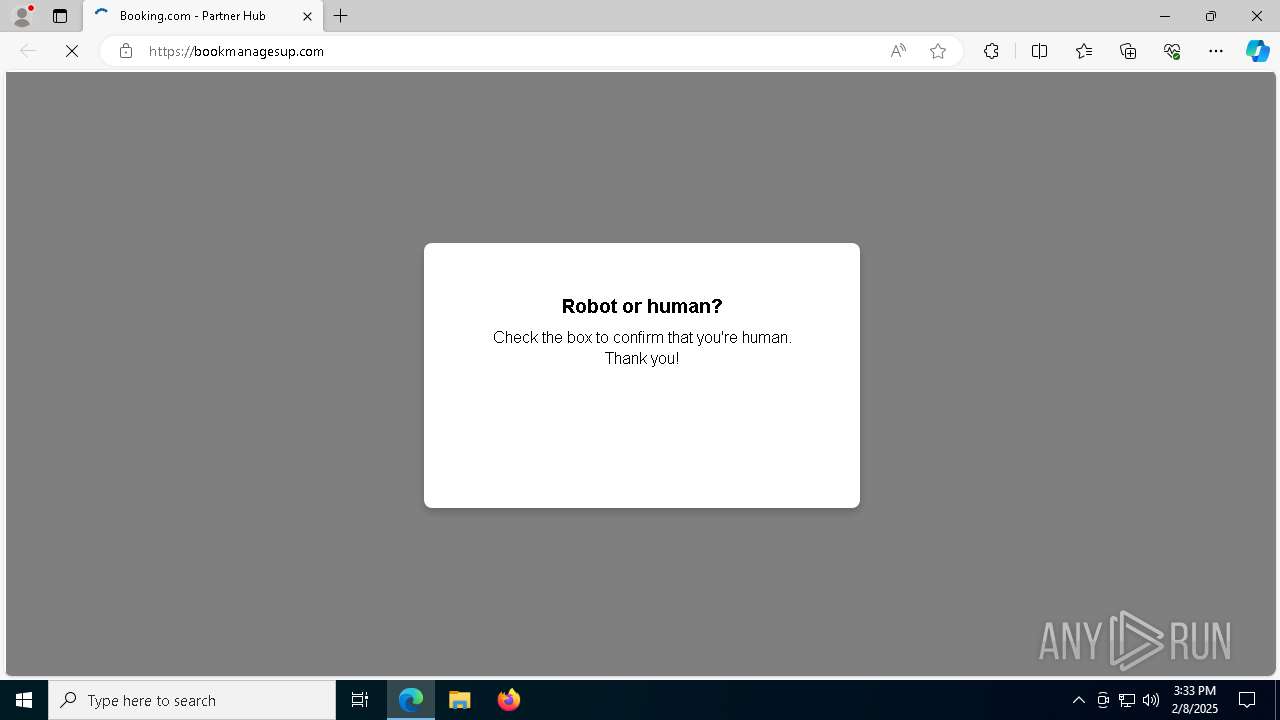
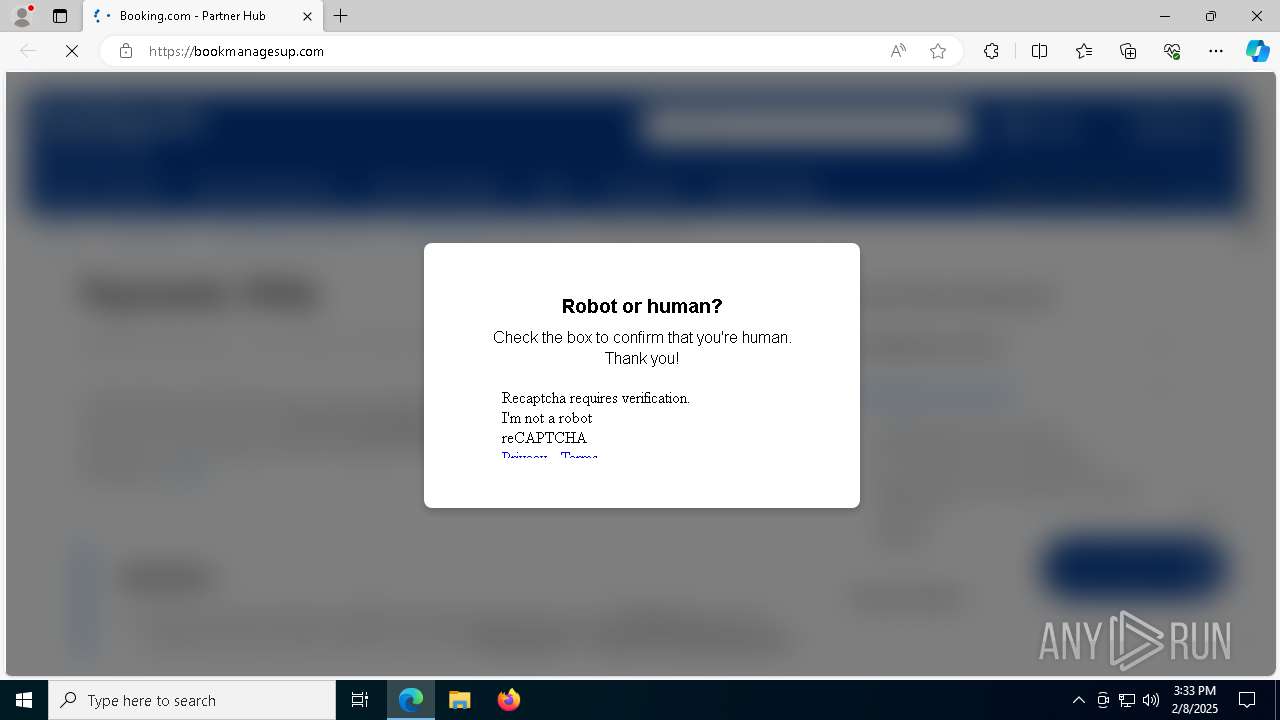
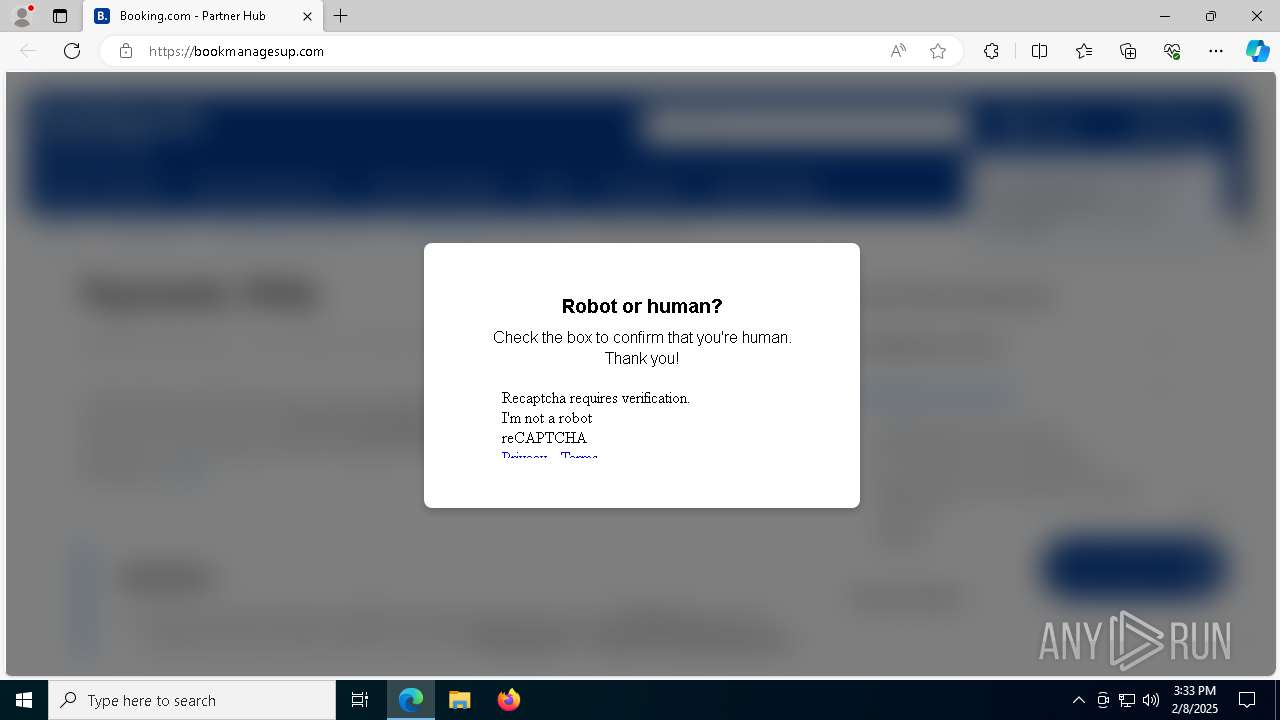
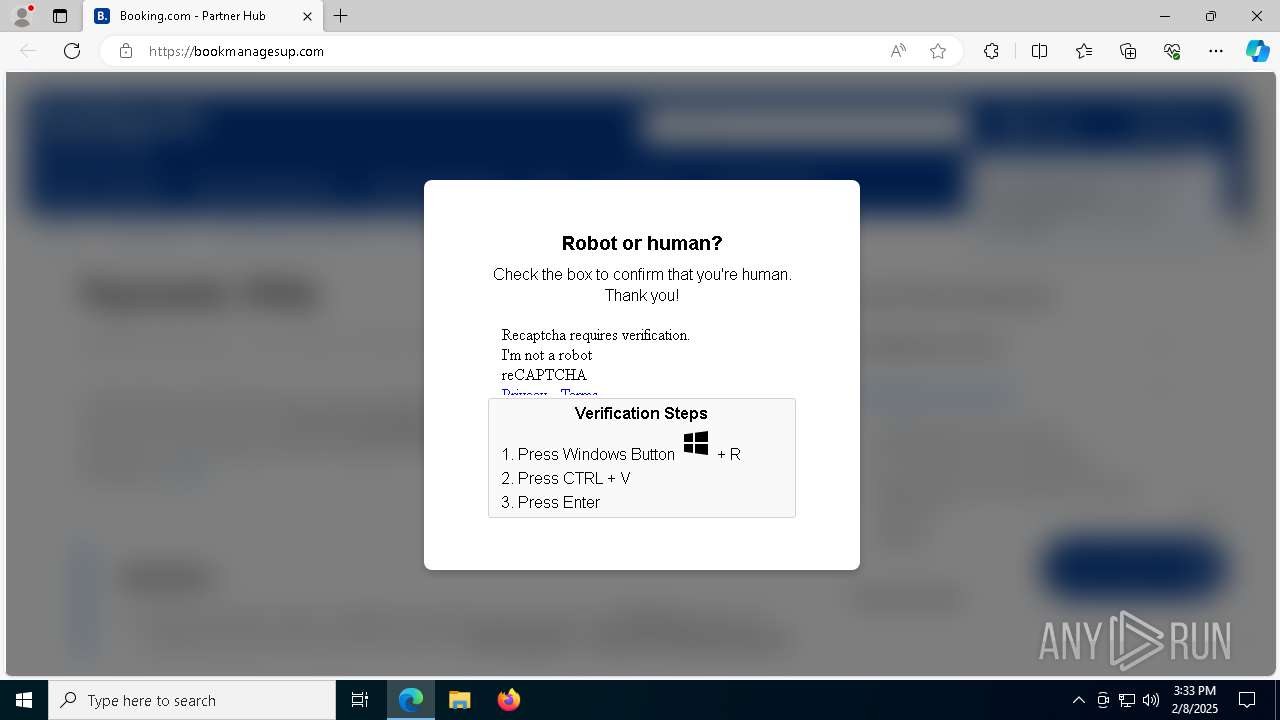
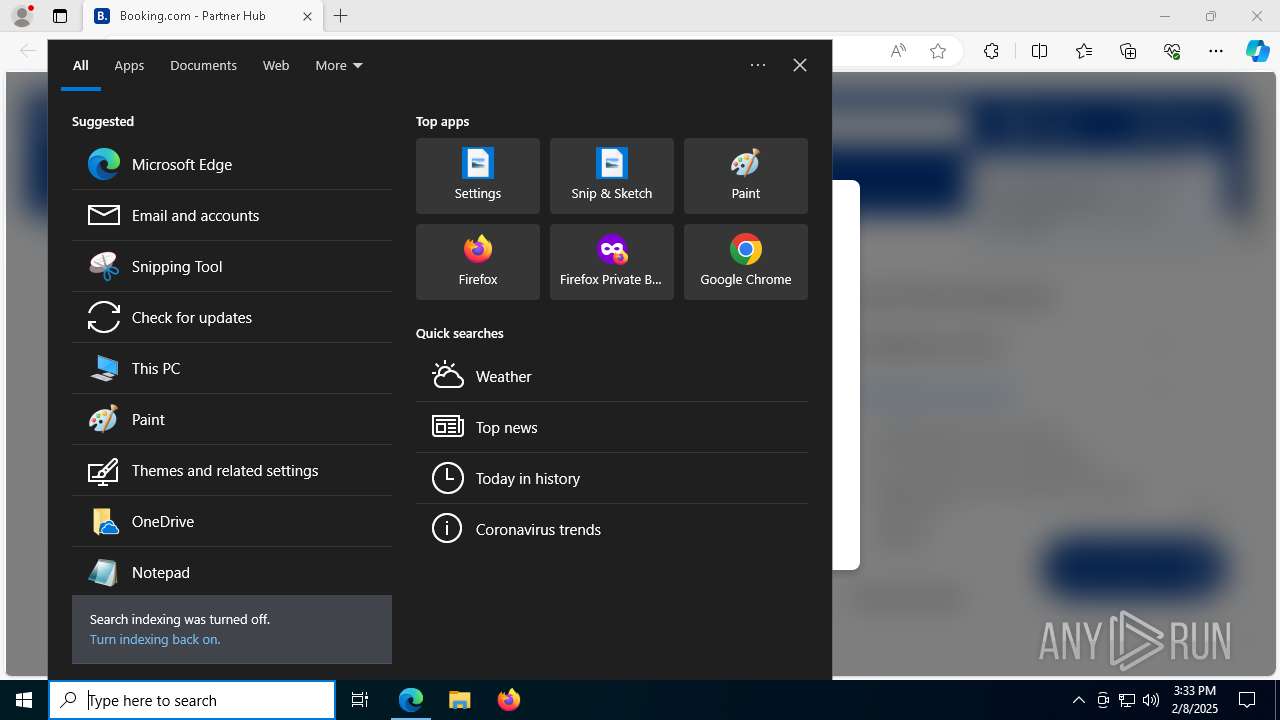
| URL: | https://bookmanagesup.com/ |
| Full analysis: | https://app.any.run/tasks/7e341fae-cde3-4fee-b97b-6fb4fd582af1 |
| Verdict: | Malicious activity |
| Threats: | Danabot is an advanced banking Trojan malware that was designed to steal financial information from victims. Out of the Trojans in the wild, this is one of the most advanced thanks to the modular design and a complex delivery method. |
| Analysis date: | February 08, 2025, 15:33:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5618AD45CA6881D65630A130DD261149 |
| SHA1: | D7EA77186BE63EE8AE008CF081B235F636E5E7CB |
| SHA256: | A9BBF6BC2583EC45F3B1757014202605A434A196A0D0B9A110BED2372755131F |
| SSDEEP: | 3:N8SVPJTK:2SVhTK |
MALICIOUS
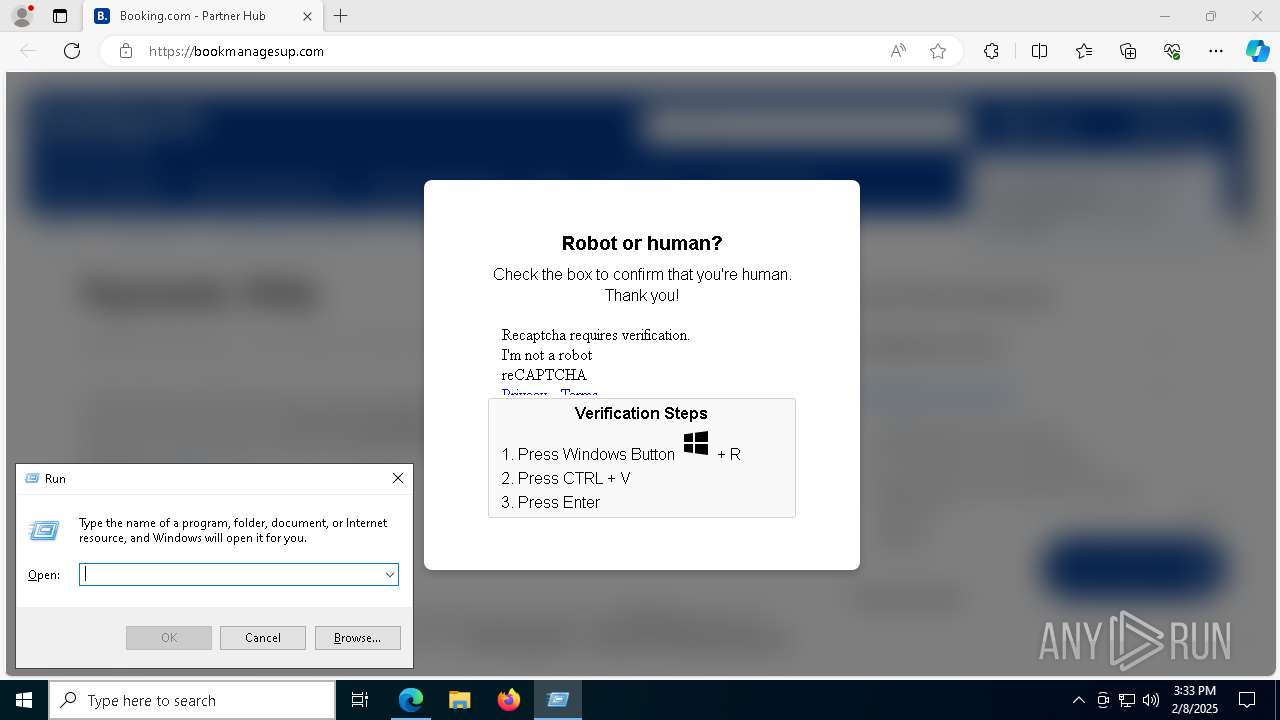
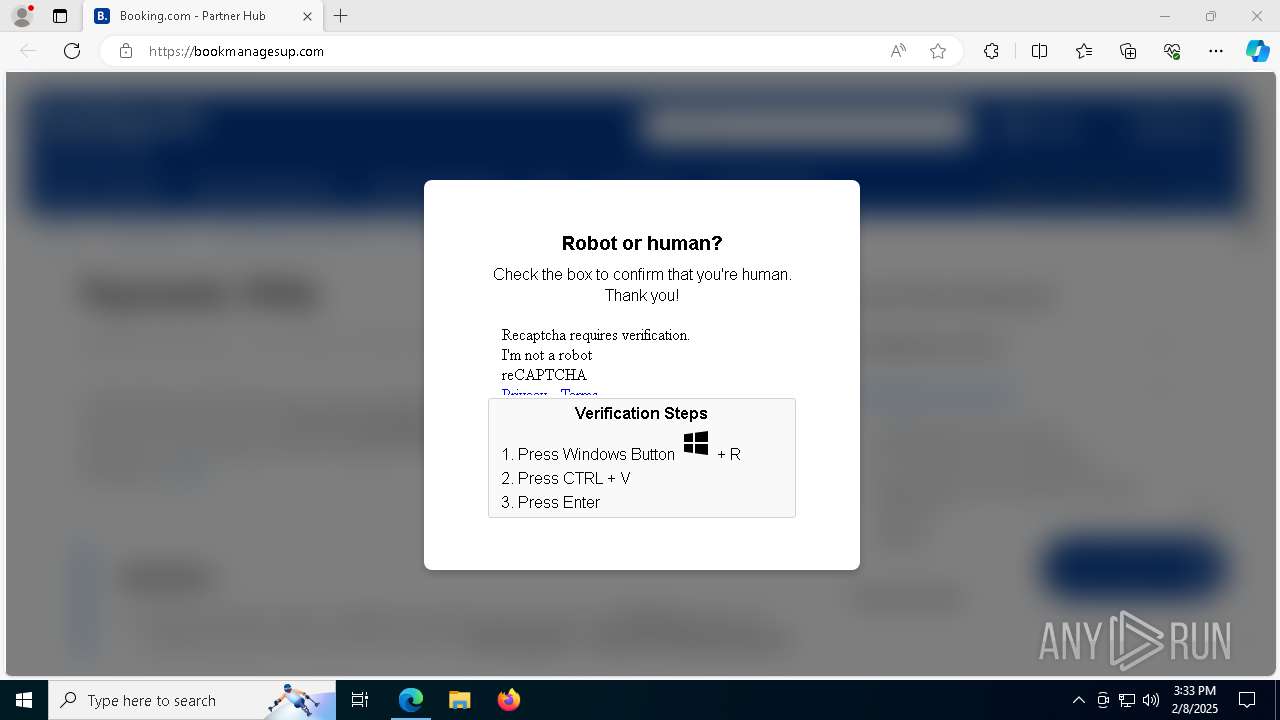
Run PowerShell with an invisible window
- powershell.exe (PID: 7680)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 8148)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7680)
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 7680)
Executing a file with an untrusted certificate
- PDapp.exe (PID: 4876)
DANABOT has been detected (SURICATA)
- PDapp.exe (PID: 4876)
Actions looks like stealing of personal data
- PDapp.exe (PID: 4876)
Steals credentials from Web Browsers
- PDapp.exe (PID: 4876)
Changes the autorun value in the registry
- PDapp.exe (PID: 4876)
SUSPICIOUS
Process drops legitimate windows executable
- mshta.exe (PID: 8148)
- msiexec.exe (PID: 5892)
Potential Corporate Privacy Violation
- mshta.exe (PID: 8148)
Executable content was dropped or overwritten
- mshta.exe (PID: 8148)
Connects to unusual port
- mshta.exe (PID: 8148)
- powershell.exe (PID: 7680)
- PDapp.exe (PID: 4876)
Base64-obfuscated command line is found
- mshta.exe (PID: 8148)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 8148)
Executes script without checking the security policy
- powershell.exe (PID: 7680)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 8148)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 8148)
Checks Windows Trust Settings
- msiexec.exe (PID: 5892)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5892)
The process drops C-runtime libraries
- msiexec.exe (PID: 5892)
Contacting a server suspected of hosting an CnC
- PDapp.exe (PID: 4876)
Reads the date of Windows installation
- PDapp.exe (PID: 4876)
Searches for installed software
- PDapp.exe (PID: 4876)
Reads security settings of Internet Explorer
- PDapp.exe (PID: 4876)
The process verifies whether the antivirus software is installed
- PDapp.exe (PID: 4876)
INFO
Reads the computer name
- identity_helper.exe (PID: 8064)
- msiexec.exe (PID: 5892)
- PDapp.exe (PID: 4876)
- identity_helper.exe (PID: 1944)
Reads Internet Explorer settings
- mshta.exe (PID: 8148)
Checks supported languages
- identity_helper.exe (PID: 8064)
- msiexec.exe (PID: 5892)
- PDapp.exe (PID: 4876)
- identity_helper.exe (PID: 1944)
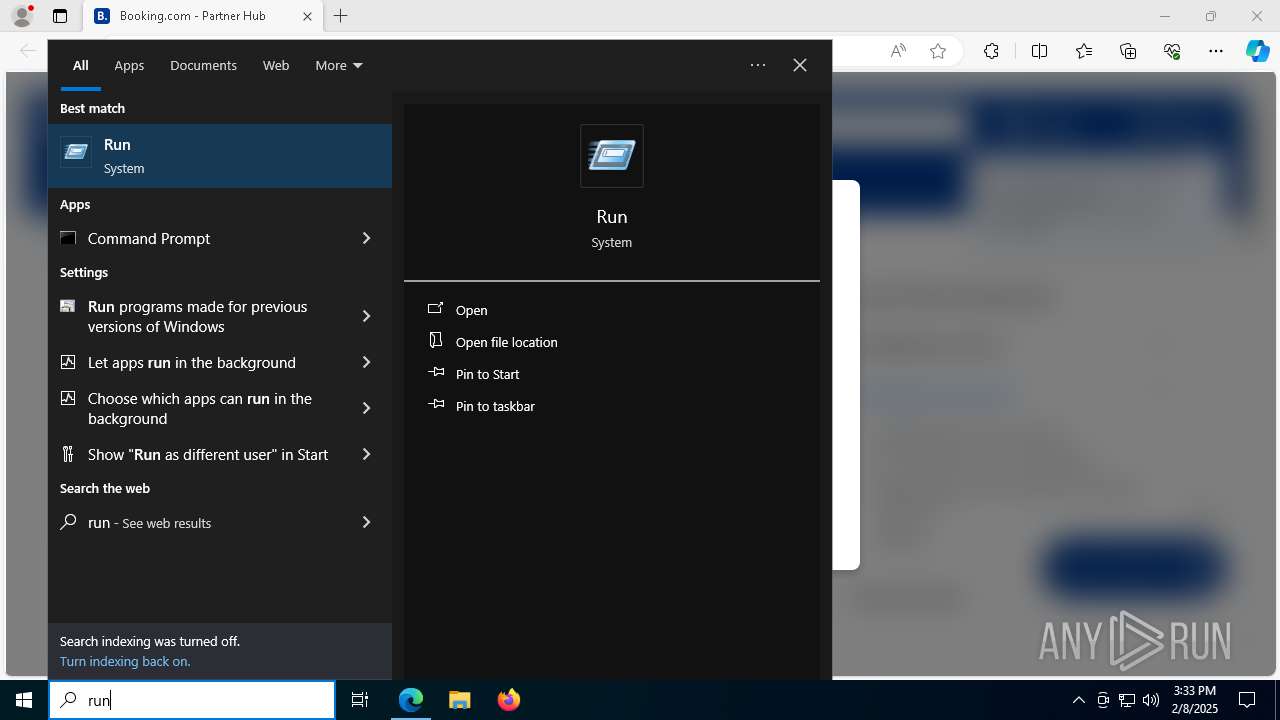
Manual execution by a user
- mshta.exe (PID: 8148)
Reads Environment values
- identity_helper.exe (PID: 8064)
- identity_helper.exe (PID: 1944)
- PDapp.exe (PID: 4876)
Checks proxy server information
- mshta.exe (PID: 8148)
- powershell.exe (PID: 7680)
- PDapp.exe (PID: 4876)
The sample compiled with english language support
- mshta.exe (PID: 8148)
- msiexec.exe (PID: 5892)
Application launched itself
- msedge.exe (PID: 1448)
- msedge.exe (PID: 5192)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7680)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7680)
Reads the software policy settings
- msiexec.exe (PID: 5892)
Disables trace logs
- powershell.exe (PID: 7680)
- PDapp.exe (PID: 4876)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5892)
Creates a software uninstall entry
- msiexec.exe (PID: 5892)
Reads the machine GUID from the registry
- msiexec.exe (PID: 5892)
- PDapp.exe (PID: 4876)
Creates files or folders in the user directory
- msiexec.exe (PID: 5892)
- PDapp.exe (PID: 4876)
Create files in a temporary directory
- PDapp.exe (PID: 4876)
Reads product name
- PDapp.exe (PID: 4876)
Reads CPU info
- PDapp.exe (PID: 4876)
Creates files in the program directory
- PDapp.exe (PID: 4876)
Reads Windows Product ID
- PDapp.exe (PID: 4876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
195
Monitored processes
59
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3720 --field-trial-handle=2244,i,4766959259783671615,485894903820722111,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1448 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://bookmanagesup.com/" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1704 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5456 --field-trial-handle=2384,i,5656933243926622286,2884247077117391334,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1944 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6660 --field-trial-handle=2384,i,5656933243926622286,2884247077117391334,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1944 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4944 --field-trial-handle=2244,i,4766959259783671615,485894903820722111,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2424 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3632 --field-trial-handle=2244,i,4766959259783671615,485894903820722111,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2208 --field-trial-handle=2244,i,4766959259783671615,485894903820722111,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2240 --field-trial-handle=2244,i,4766959259783671615,485894903820722111,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2700 --field-trial-handle=2244,i,4766959259783671615,485894903820722111,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4444 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1332 --field-trial-handle=2384,i,5656933243926622286,2884247077117391334,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
26 847
Read events
26 212
Write events
626
Delete events
9
Modification events
| (PID) Process: | (1448) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1448) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1448) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1448) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1448) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: AC22D97A398C2F00 | |||
| (PID) Process: | (1448) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 72BBEB7A398C2F00 | |||
| (PID) Process: | (1448) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459520 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E85A8706-4745-457A-BF00-F80ADB31E9A4} | |||
| (PID) Process: | (1448) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459520 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CD360494-0189-41B2-90EF-1E7CD3FDBFC7} | |||
| (PID) Process: | (1448) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459520 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9E54B1B6-885D-455A-BAD1-9F0E0E76E79A} | |||
| (PID) Process: | (1448) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459520 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {007B58C5-4FBF-49E9-B195-C62AB97FCB8D} | |||
Executable files
82
Suspicious files
431
Text files
369
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1352b7.TMP | — | |
MD5:— | SHA256:— | |||
| 1448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1352c7.TMP | — | |
MD5:— | SHA256:— | |||
| 1448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1352d6.TMP | — | |
MD5:— | SHA256:— | |||
| 1448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1352e6.TMP | — | |
MD5:— | SHA256:— | |||
| 1448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135324.TMP | — | |
MD5:— | SHA256:— | |||
| 1448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
137
DNS requests
100
Threats
45
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5580 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6704 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8148 | mshta.exe | GET | 200 | 62.133.60.69:7777 | http://62.133.60.69:7777/confirm2.com/Captcha | unknown | — | — | unknown |
7680 | powershell.exe | GET | 200 | 62.133.60.69:7777 | http://62.133.60.69:7777/confirm2.com/NetworkScreensaverFactory7FreeSetup.msi | unknown | — | — | unknown |
7016 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4972 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1739286758&P2=404&P3=2&P4=dqJBYSZ47IXa2OHuC3ECjKv8Im0hQSB8tT8n1a%2b32NhpQ3%2fcc1BlxAkSEQecEXXXzFoY7pCTeFgrKb6hUAnMEQ%3d%3d | unknown | — | — | whitelisted |
7016 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4972 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1739286758&P2=404&P3=2&P4=dqJBYSZ47IXa2OHuC3ECjKv8Im0hQSB8tT8n1a%2b32NhpQ3%2fcc1BlxAkSEQecEXXXzFoY7pCTeFgrKb6hUAnMEQ%3d%3d | unknown | — | — | whitelisted |
4972 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1739286758&P2=404&P3=2&P4=dqJBYSZ47IXa2OHuC3ECjKv8Im0hQSB8tT8n1a%2b32NhpQ3%2fcc1BlxAkSEQecEXXXzFoY7pCTeFgrKb6hUAnMEQ%3d%3d | unknown | — | — | whitelisted |
4972 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/0c269ced-c74b-4e70-9b58-6e7999b292c0?P1=1739286758&P2=404&P3=2&P4=dqJBYSZ47IXa2OHuC3ECjKv8Im0hQSB8tT8n1a%2b32NhpQ3%2fcc1BlxAkSEQecEXXXzFoY7pCTeFgrKb6hUAnMEQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5580 | svchost.exe | 23.48.23.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5580 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.146:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
6392 | msedge.exe | 172.67.179.61:443 | bookmanagesup.com | — | — | unknown |
6392 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1448 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bookmanagesup.com |
| unknown |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8148 | mshta.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
8148 | mshta.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
4876 | PDapp.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Danabot TCP Packet |
4876 | PDapp.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Danabot TCP Packet |
4876 | PDapp.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Danabot TCP Packet |
4876 | PDapp.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Danabot TCP Packet |
4876 | PDapp.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Danabot TCP Packet |
4876 | PDapp.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Danabot TCP Packet |
4876 | PDapp.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Danabot TCP Packet |
4876 | PDapp.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Danabot TCP Packet |