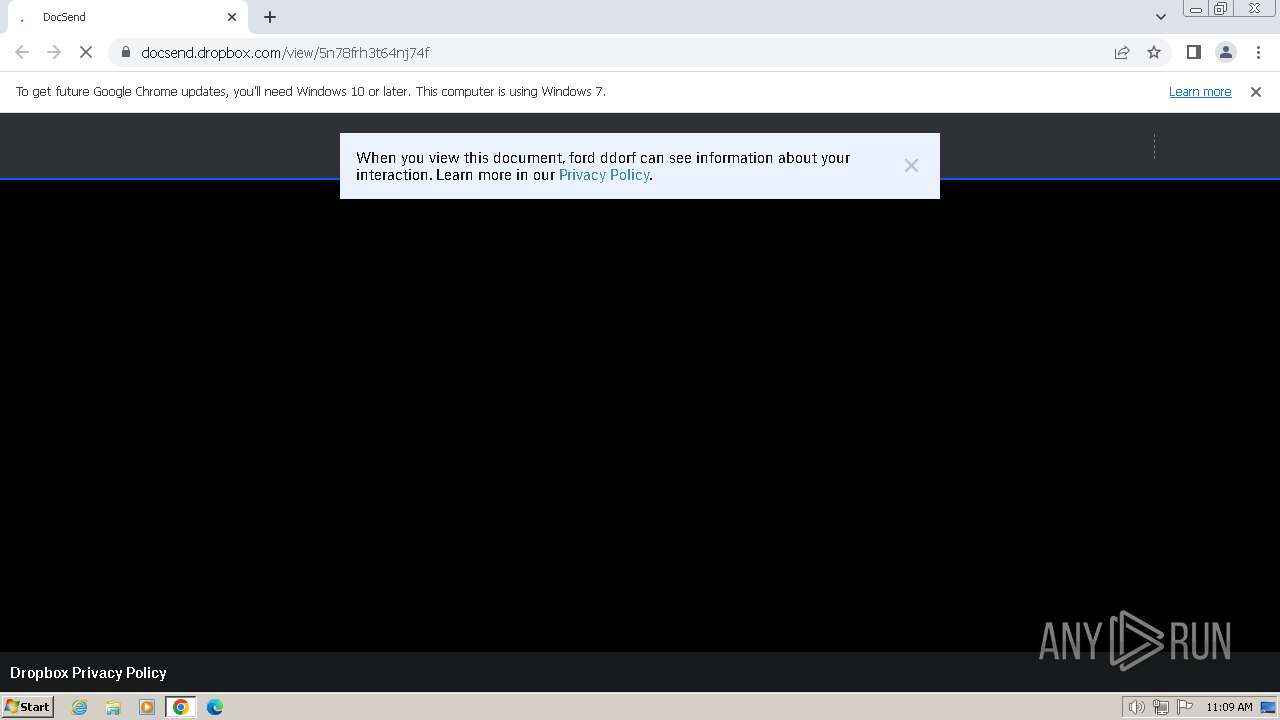
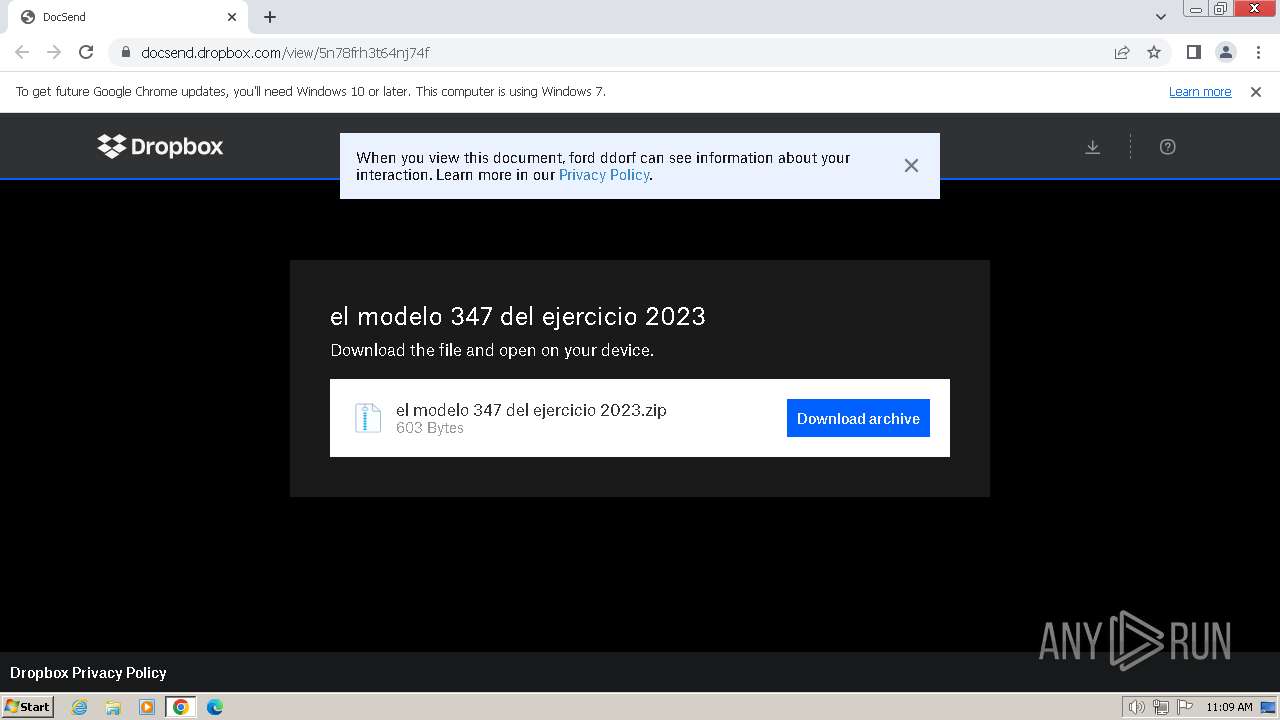
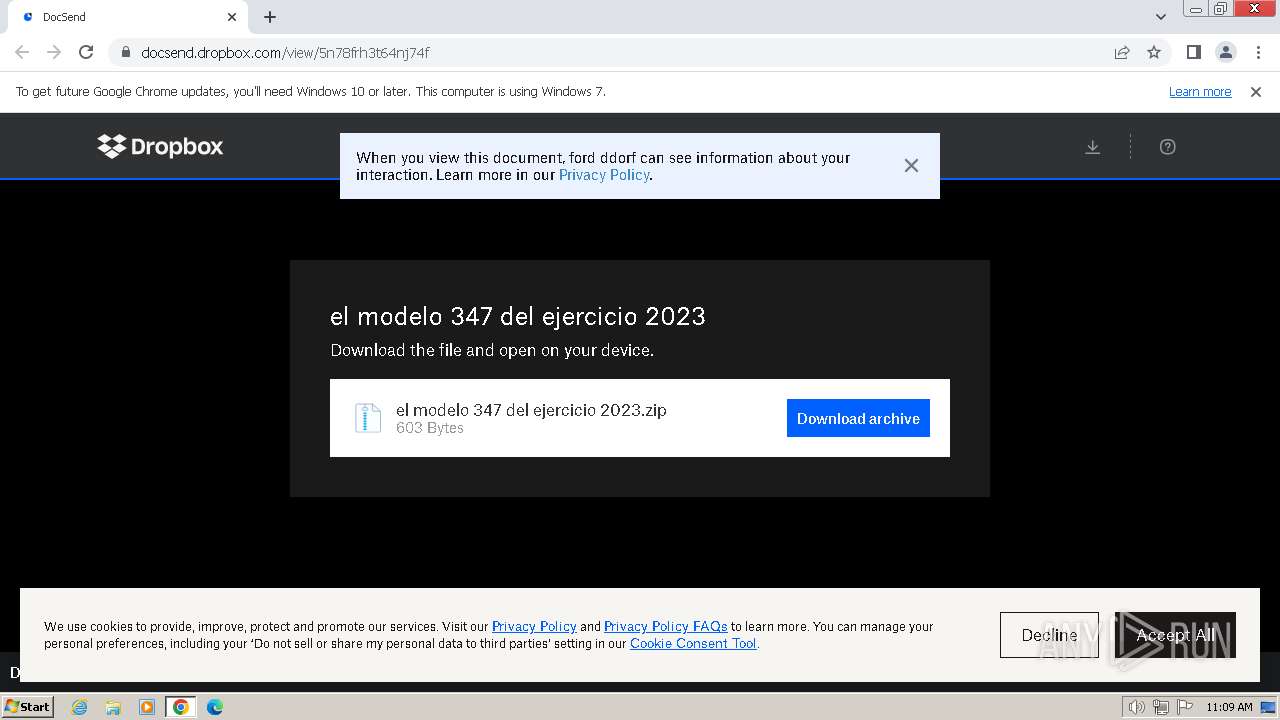
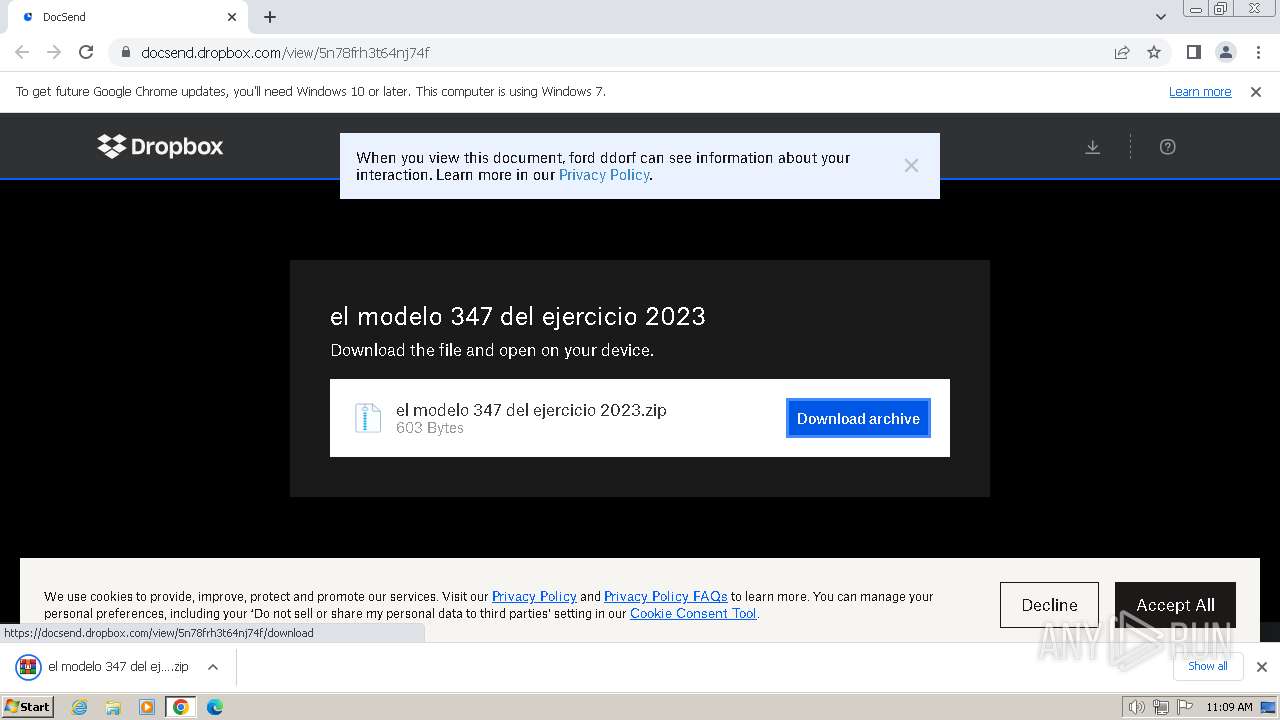
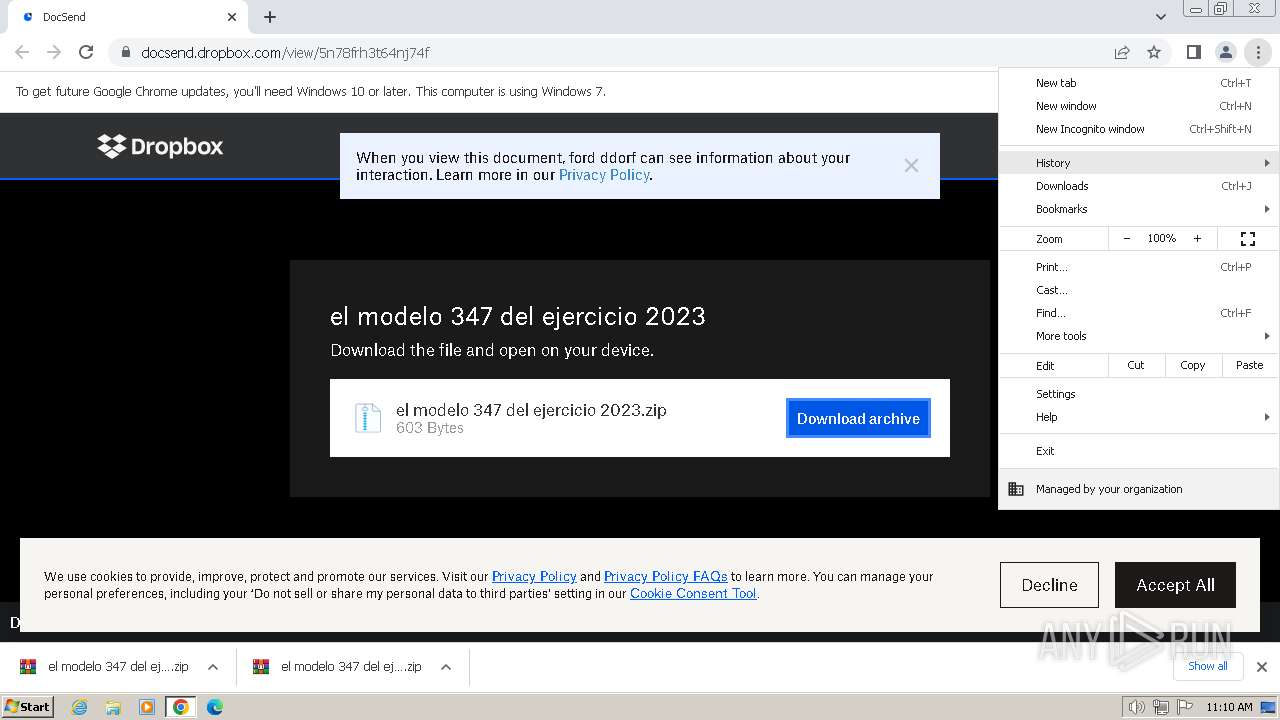
| URL: | https://docsend.dropbox.com/view/5n78frh3t64nj74f |
| Full analysis: | https://app.any.run/tasks/8a148f87-d297-4065-b5dc-5534249614d2 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | March 08, 2024, 11:09:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 01848501D021B6F2F2E73A40527E9989 |
| SHA1: | 5E34B954492A01F376770803CC07357EDFCA3453 |
| SHA256: | A9AB783393C95AEBEB16719A70BEBB1224F8E698C16315CA0D418506AC5ABE21 |
| SSDEEP: | 3:N8S2KVHGhMmBUbE:2SnVmymBeE |
MALICIOUS
Create files in the Startup directory
- cmd.exe (PID: 2980)
Antivirus name has been found in the command line (generic signature)
- tasklist.exe (PID: 3636)
- find.exe (PID: 3740)
Run PowerShell with an invisible window
- powershell.exe (PID: 2788)
- powershell.exe (PID: 568)
ASYNCRAT has been detected (SURICATA)
- powershell.exe (PID: 2812)
Bypass execution policy to execute commands
- powershell.exe (PID: 1840)
- powershell.exe (PID: 1840)
- powershell.exe (PID: 4008)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2980)
XWORM has been detected (YARA)
- powershell.exe (PID: 3032)
Connects to the CnC server
- powershell.exe (PID: 3032)
XWORM has been detected (SURICATA)
- powershell.exe (PID: 3032)
ASYNCRAT has been detected (YARA)
- powershell.exe (PID: 2812)
SUSPICIOUS
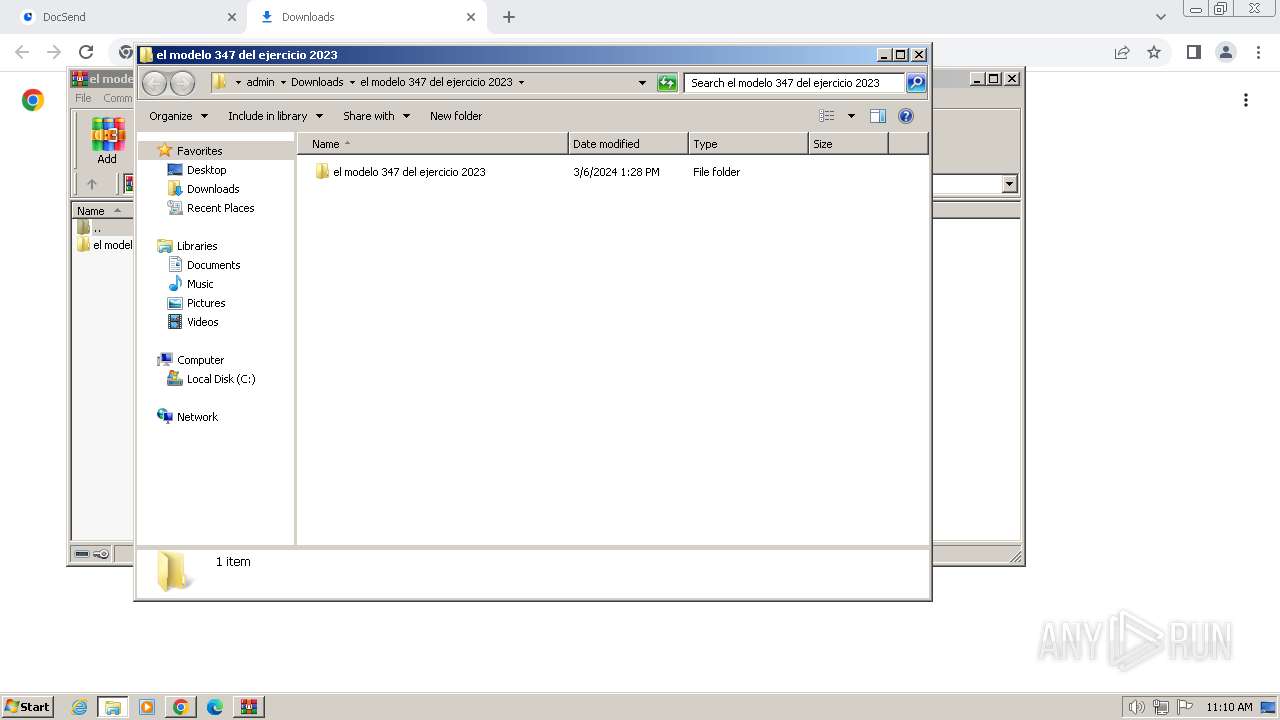
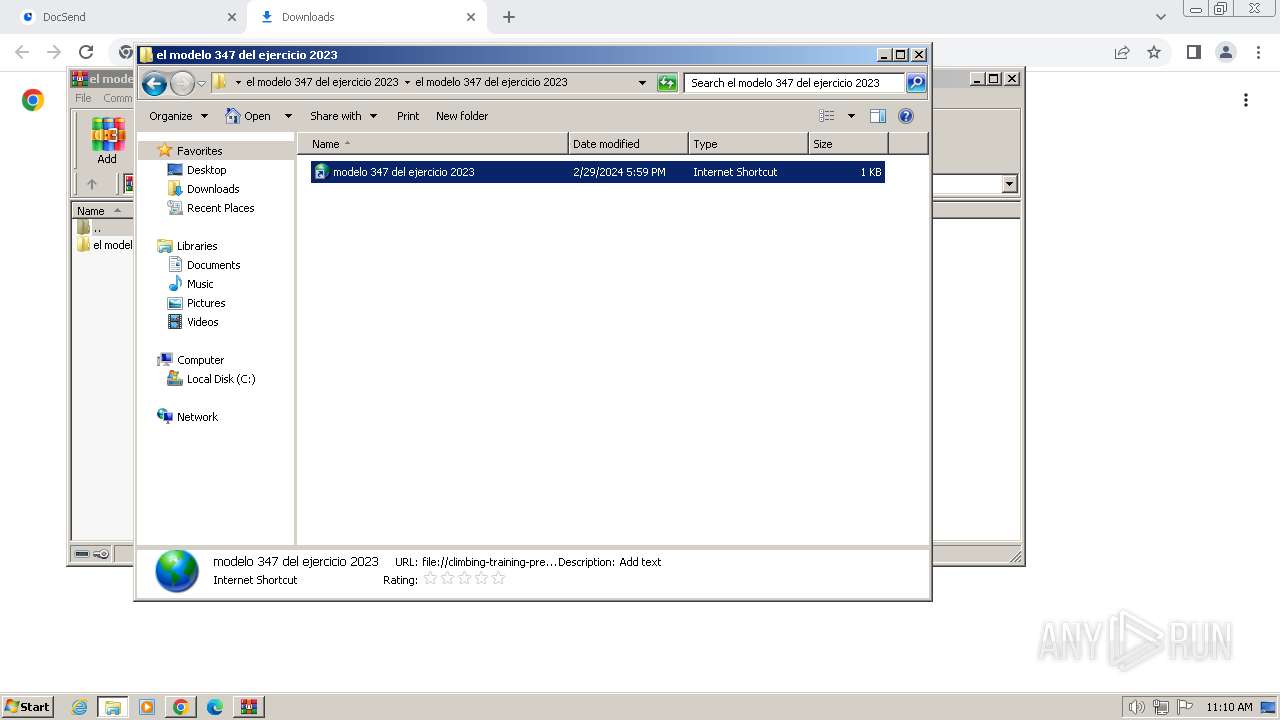
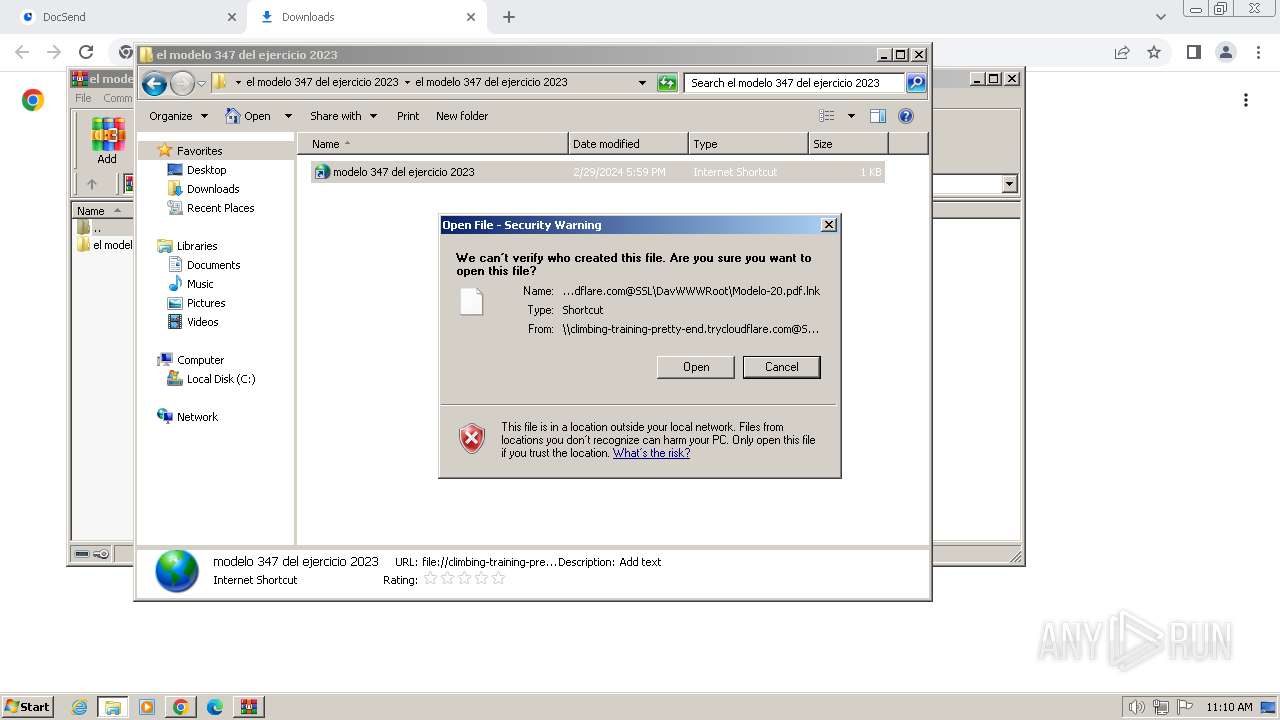
SMB connection has been detected (probably for file transfer)
- explorer.exe (PID: 1164)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2980)
- explorer.exe (PID: 1164)
- cmd.exe (PID: 3496)
- cmd.exe (PID: 2668)
- cmd.exe (PID: 2528)
- cmd.exe (PID: 268)
Application launched itself
- cmd.exe (PID: 2980)
- cmd.exe (PID: 3496)
- cmd.exe (PID: 2668)
- cmd.exe (PID: 2528)
- cmd.exe (PID: 268)
- powershell.exe (PID: 2812)
- powershell.exe (PID: 3032)
Reads the Internet Settings
- cmd.exe (PID: 2980)
- powershell.exe (PID: 2812)
- powershell.exe (PID: 1840)
- powershell.exe (PID: 4008)
Executing commands from a ".bat" file
- explorer.exe (PID: 1164)
Executing commands from ".cmd" file
- cmd.exe (PID: 2980)
- cmd.exe (PID: 3496)
- cmd.exe (PID: 2668)
- cmd.exe (PID: 2528)
- cmd.exe (PID: 268)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2528)
- cmd.exe (PID: 268)
- powershell.exe (PID: 2812)
- powershell.exe (PID: 3032)
- cmd.exe (PID: 2980)
Process starts base64 encoded powershell command
- cmd.exe (PID: 2528)
- cmd.exe (PID: 268)
Get information on the list of running processes
- cmd.exe (PID: 2980)
Connects to unusual port
- powershell.exe (PID: 2812)
- powershell.exe (PID: 3032)
The Powershell connects to the Internet
- powershell.exe (PID: 2812)
- powershell.exe (PID: 3032)
Unusual connection from system programs
- powershell.exe (PID: 2812)
- powershell.exe (PID: 3032)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 1840)
- powershell.exe (PID: 4008)
The process executes Powershell scripts
- cmd.exe (PID: 2980)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2980)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 1164)
Application launched itself
- chrome.exe (PID: 3652)
- msedge.exe (PID: 984)
Reads settings of System Certificates
- explorer.exe (PID: 1164)
Checks proxy server information
- explorer.exe (PID: 1164)
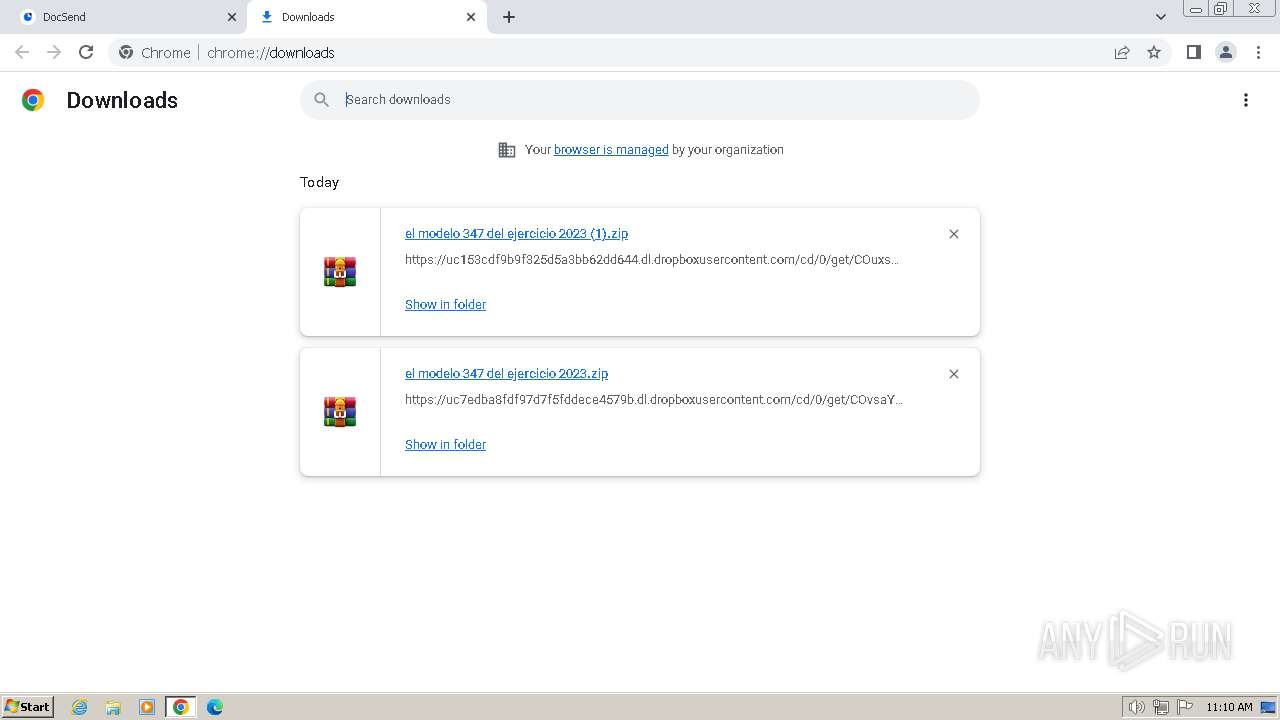
Drops the executable file immediately after the start
- chrome.exe (PID: 3388)
Executable content was dropped or overwritten
- chrome.exe (PID: 3388)
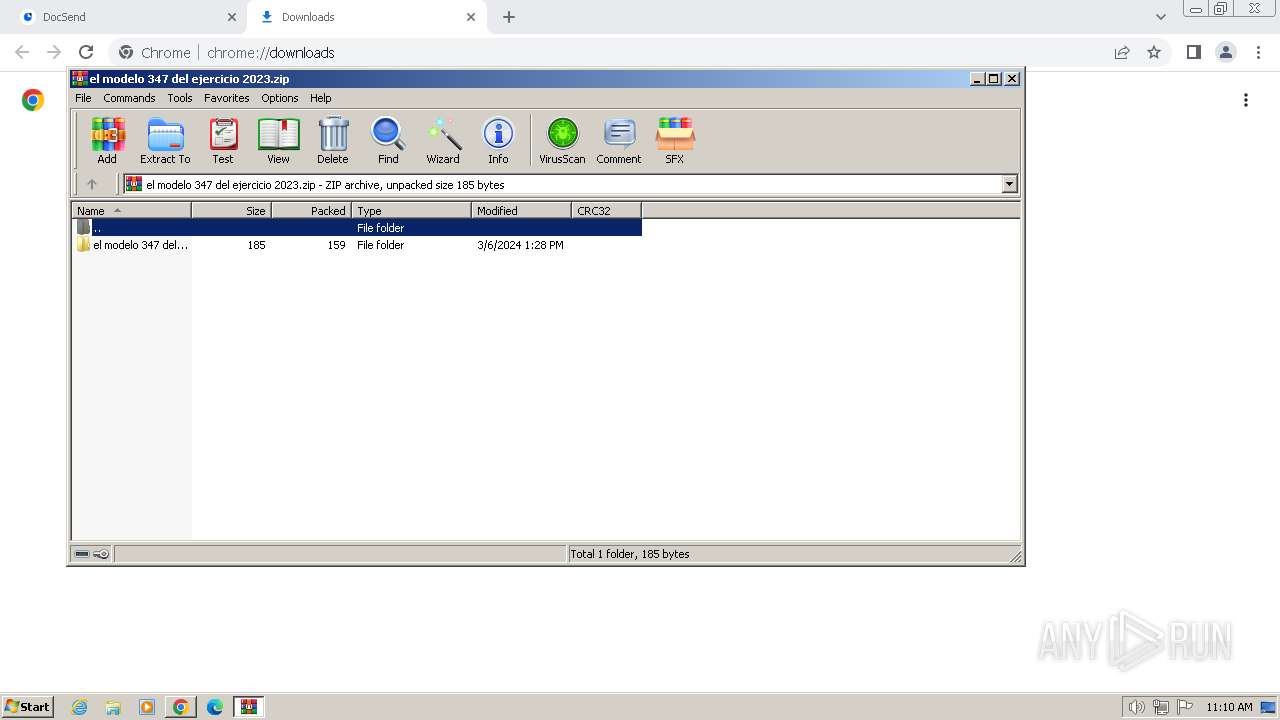
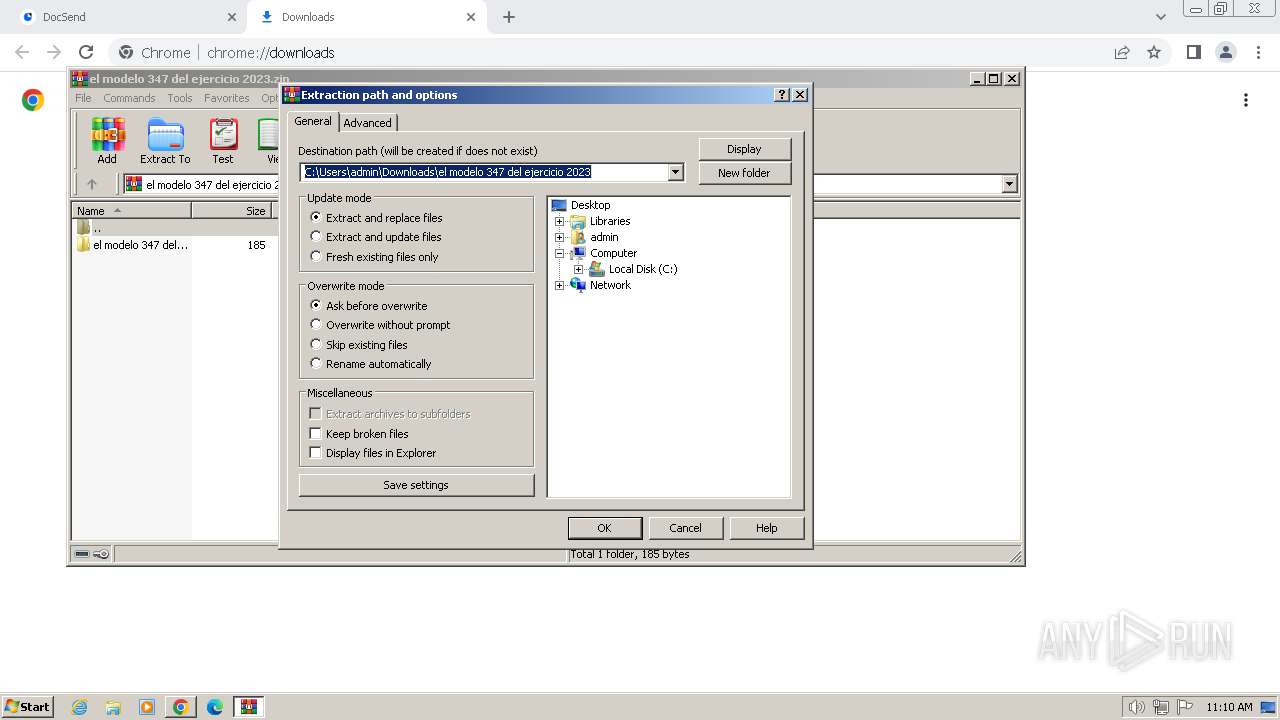
The process uses the downloaded file
- chrome.exe (PID: 2096)
- chrome.exe (PID: 1780)
- WinRAR.exe (PID: 3172)
Reads the Internet Settings
- explorer.exe (PID: 1164)
Reads the software policy settings
- explorer.exe (PID: 1164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
XWorm
(PID) Process(3032) powershell.exe
C291.134.150.150:7000
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameXWorm V5.2
MutexzF2pXWj2jnO4fKEV
AsyncRat
(PID) Process(2812) powershell.exe
C2 (1)91.134.150.150
Ports (1)3232
BotnetDefault
Options
AutoRunfalse
Mutexω5KץzU斯gωa3Q7bkC诶B
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIICKTCCAZKgAwIBAgIVAMqrQ7YVwxaDuhS0IjiRKIEbZNClMA0GCSqGSIb3DQEBDQUAMF0xDjAMBgNVBAMMBUVCT0xBMRMwEQYDVQQLDApxd3FkYW5jaHVuMRwwGgYDVQQKDBNEY1JhdCBCeSBxd3FkYW5jaHVuMQswCQYDVQQHDAJTSDELMAkGA1UEBhMCQ04wHhcNMjMwNTEwMDcyNDE2WhcNMzQwMjE2MDcyNDE2WjAQMQ4wDAYDVQQDDAVEY1JhdDCBnzANBgkqhkiG9w0BAQEFAAOBjQAwgYkCgYEA...
Server_SignatureBDV1HF41x/oBvAG+9mIwmZ3RfI7LJU/6qr93f8CicAZBV1gscp/LoAHsecRvNoBiclnz/x5F6T2qdYn17DktwLjZGS+vS5Gegs0R54A33zcKdJqKg86MRoUj/nRPMqPaRpr7yb4XGq68Hr1OJYMCcZQ9l6e103lVjzNiRo7BIrU=
Keys
AES8fe9e0624bcf4de148ca1170bd52e7ee84d1258195b89389682269bcd3b4bdbd
SaltDcRatByqwqdanchun
Total processes
131
Monitored processes
68
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=3644 --field-trial-handle=1160,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 268 | C:\Windows\system32\cmd.exe /K C:\Users\admin\Pictures\update.cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 568 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w hidden | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1032 --field-trial-handle=1160,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 712 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4084 --field-trial-handle=1412,i,4091416865120920642,1291031777135613424,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 764 | tasklist /FI "IMAGENAME eq fresh.exe" | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 880 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1536 --field-trial-handle=1412,i,4091416865120920642,1291031777135613424,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
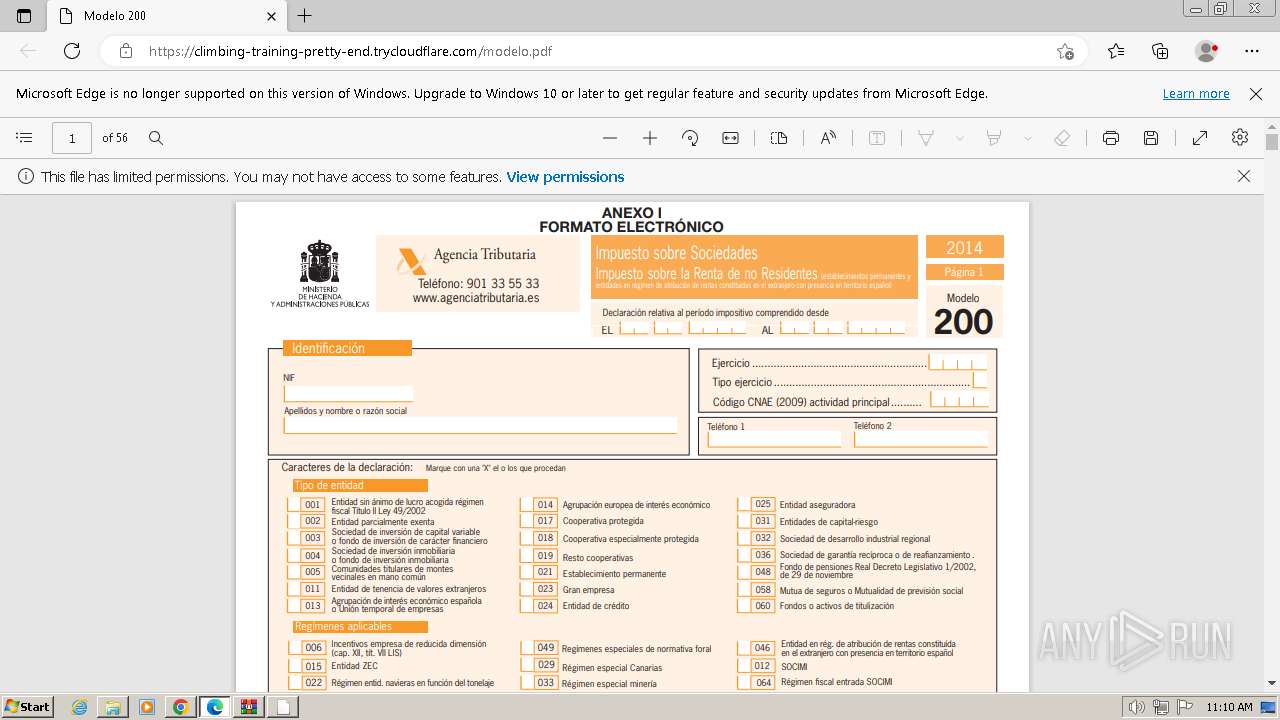
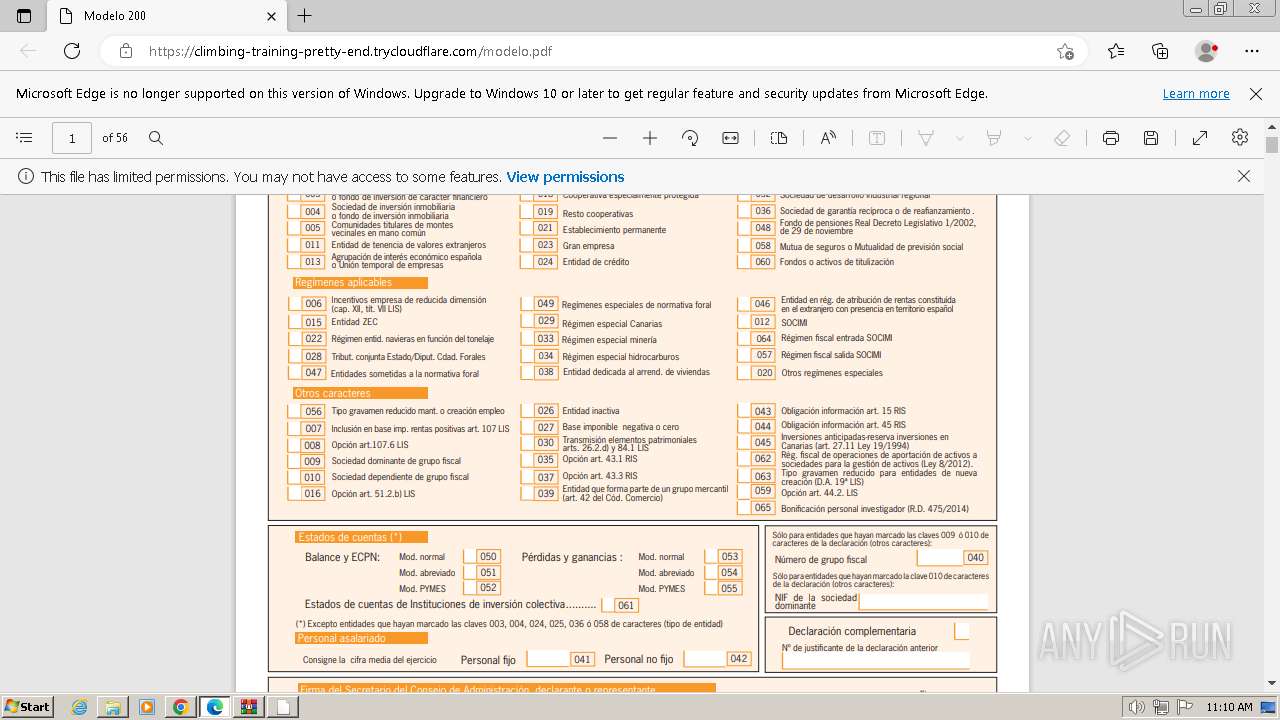
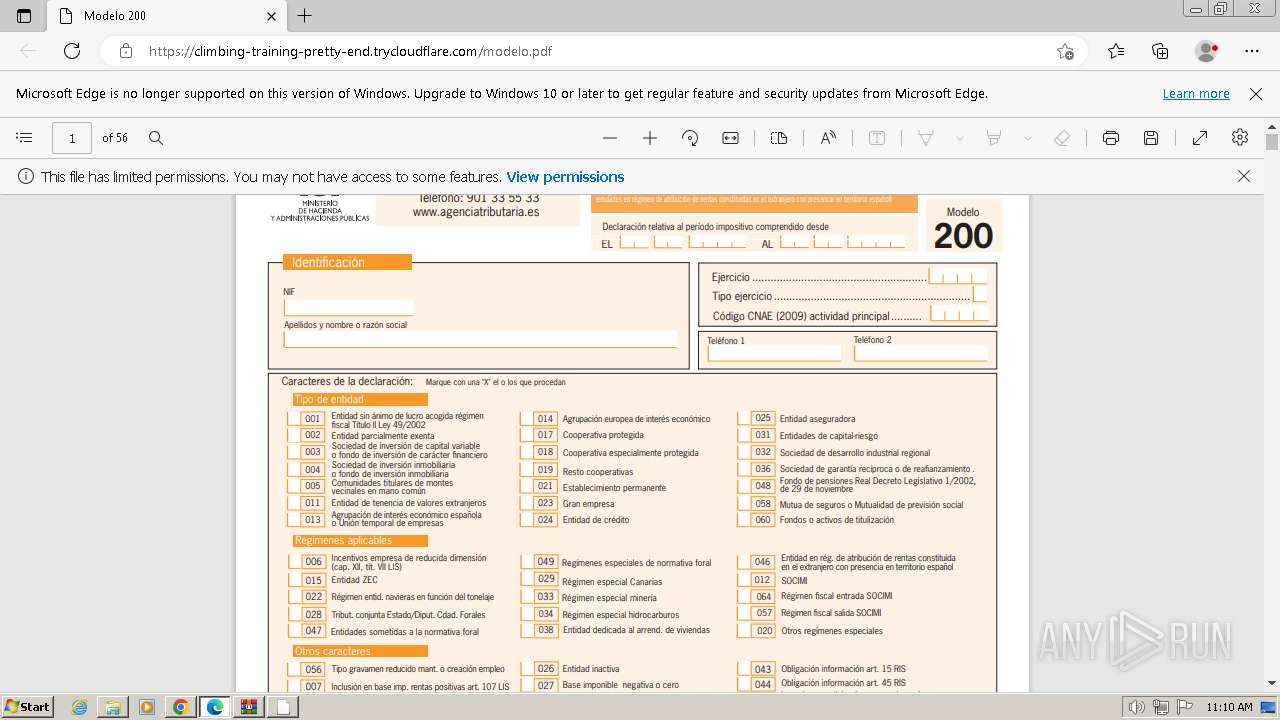
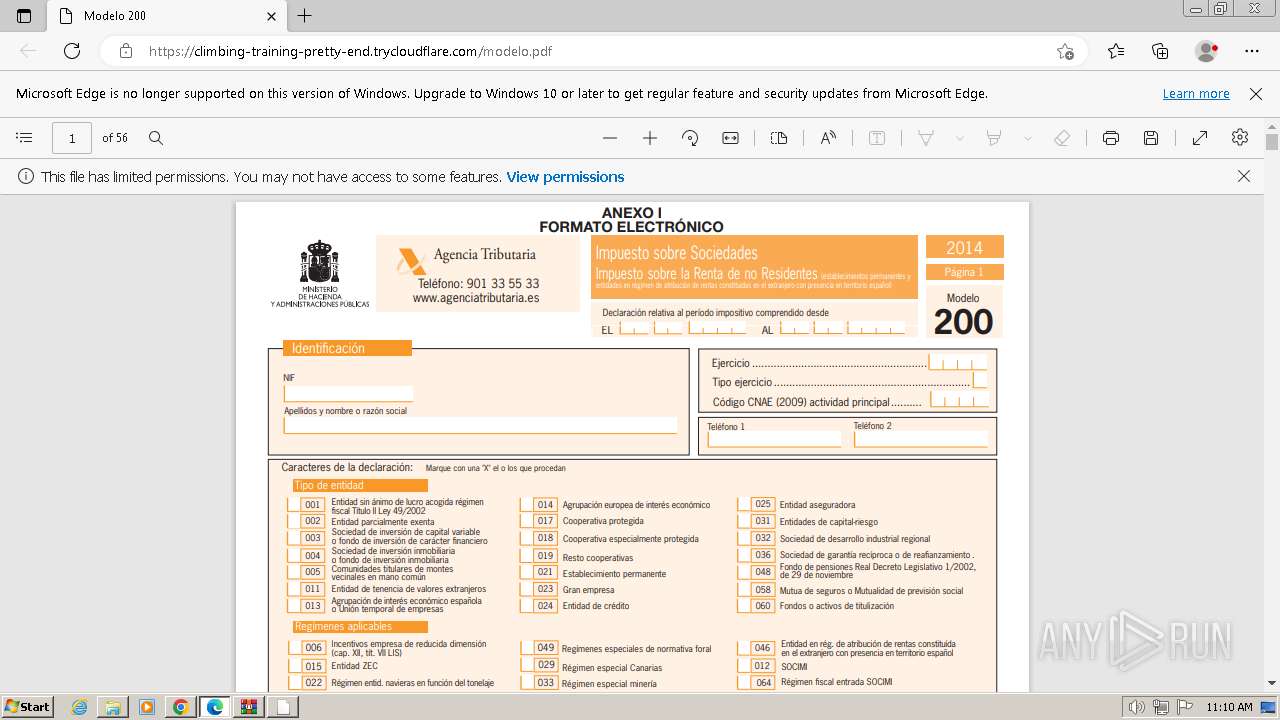
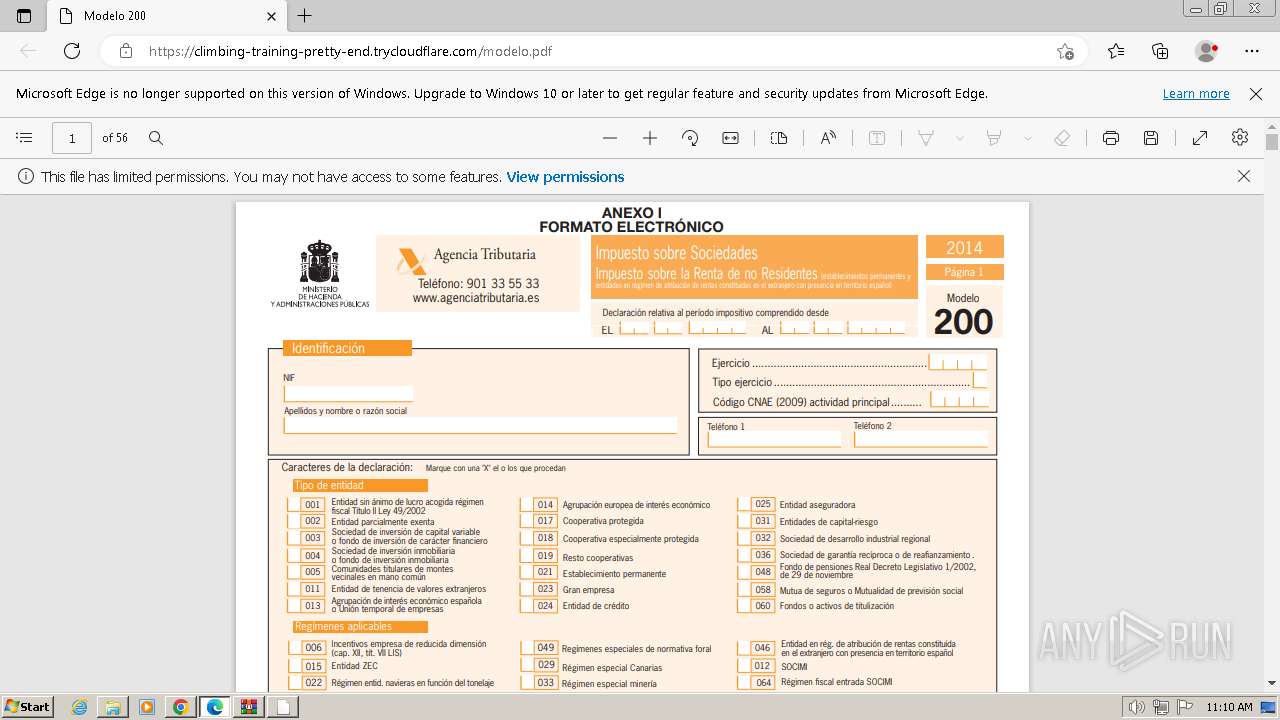
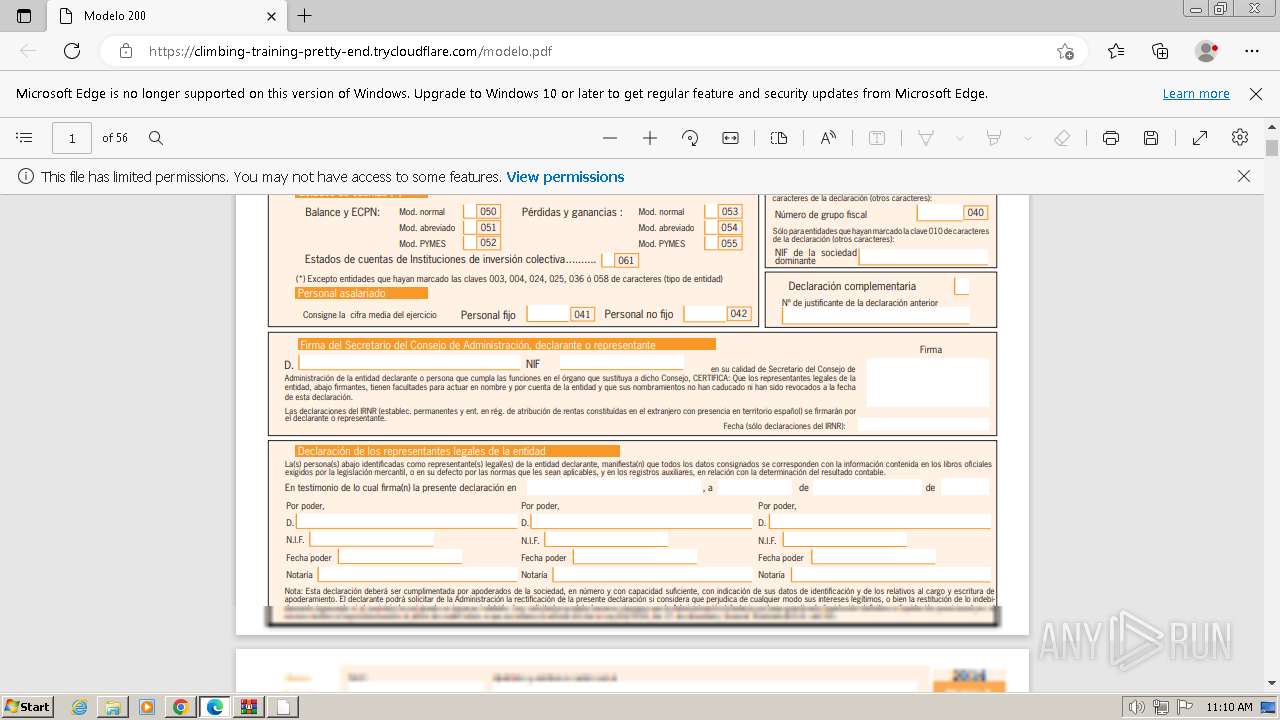
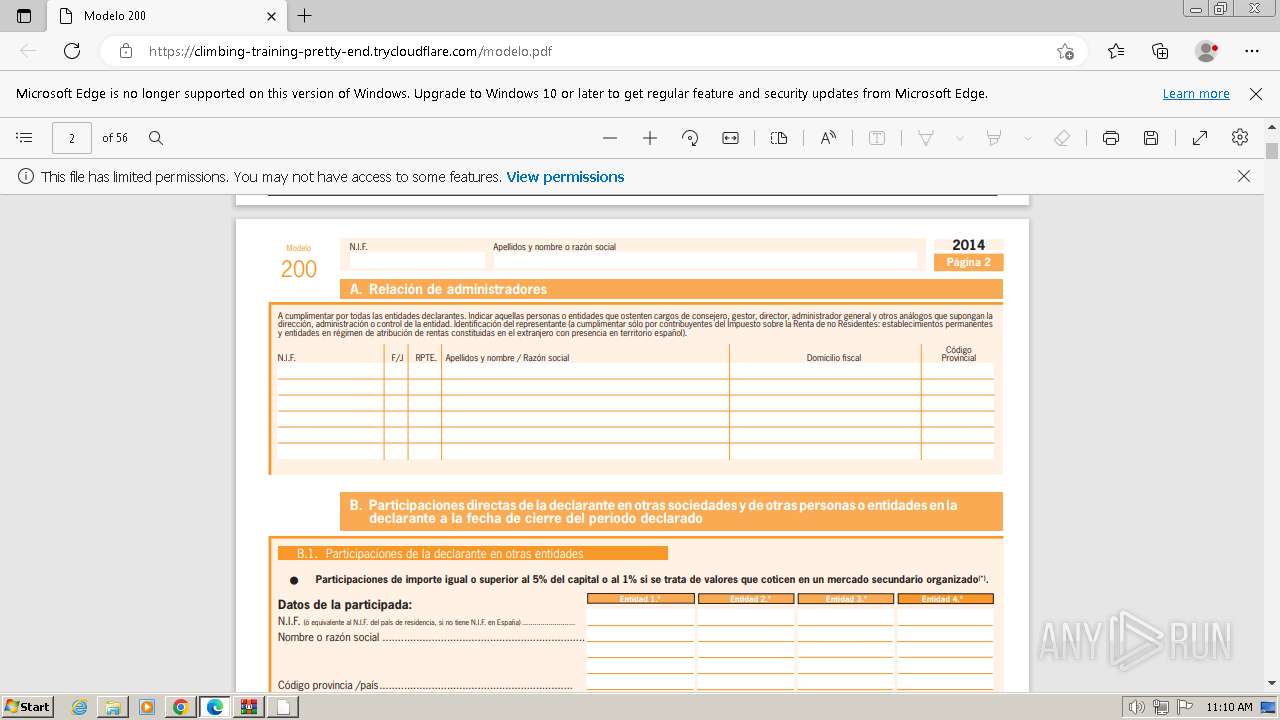
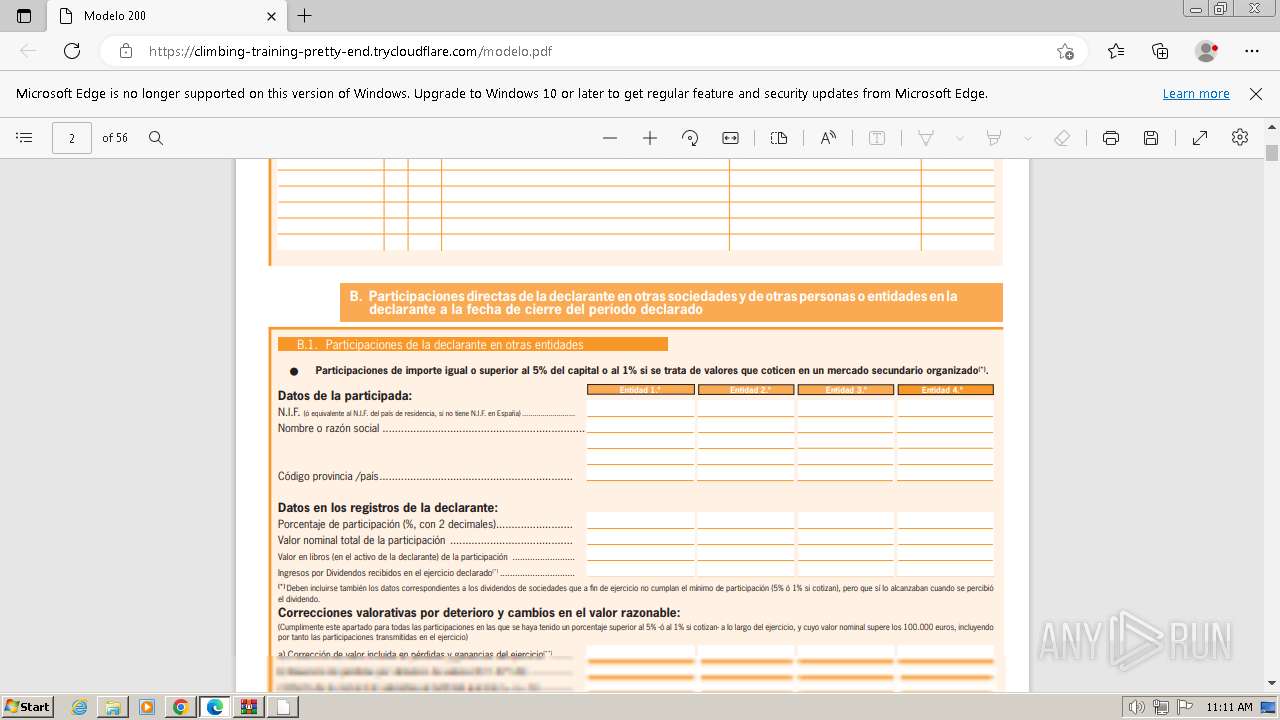
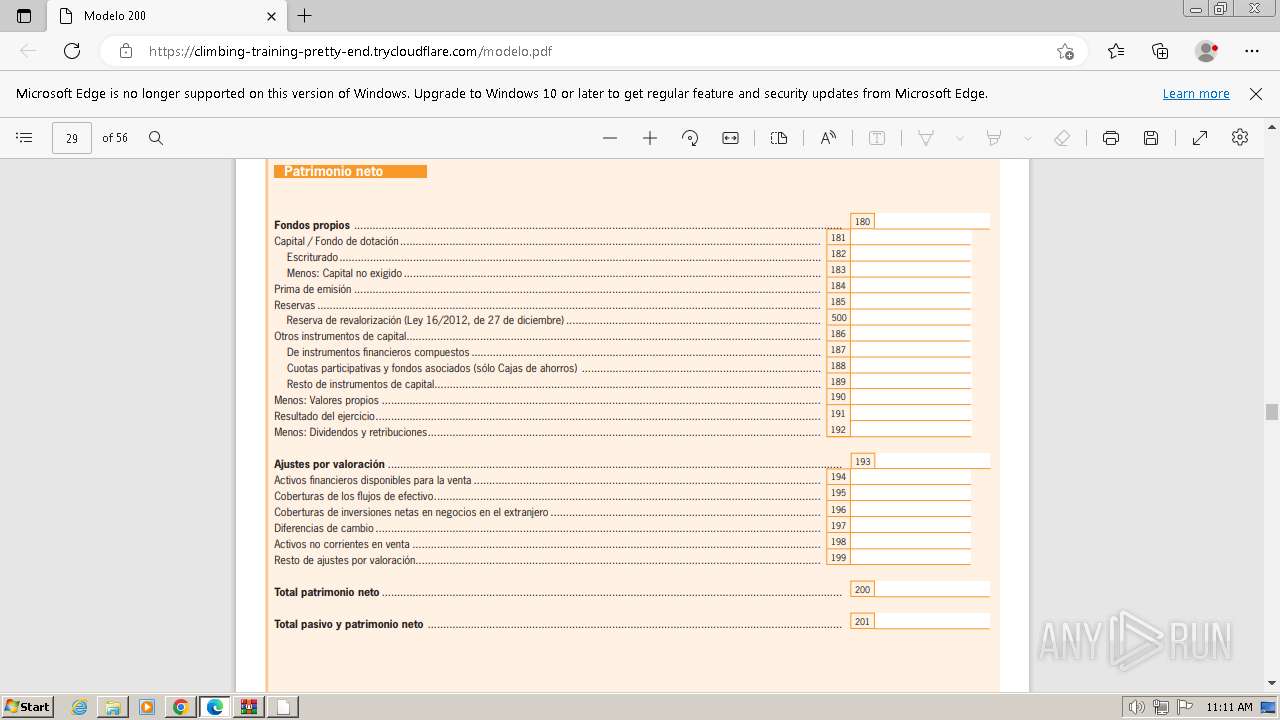
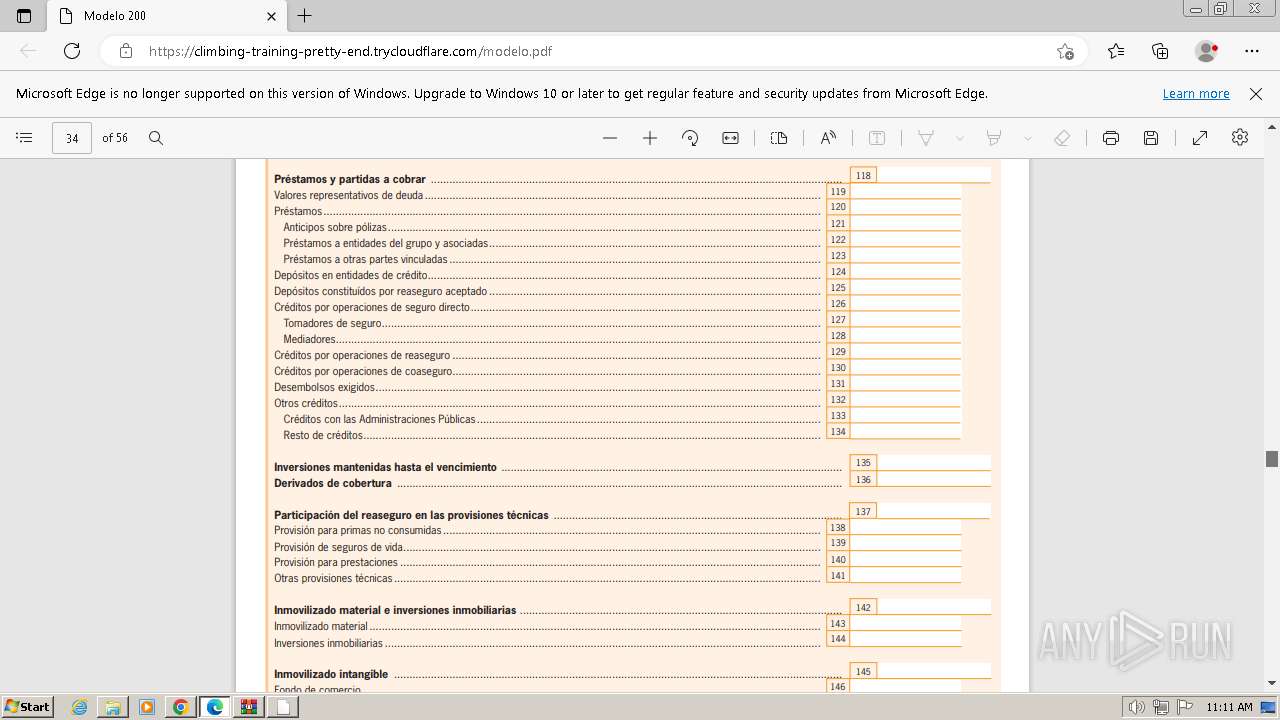
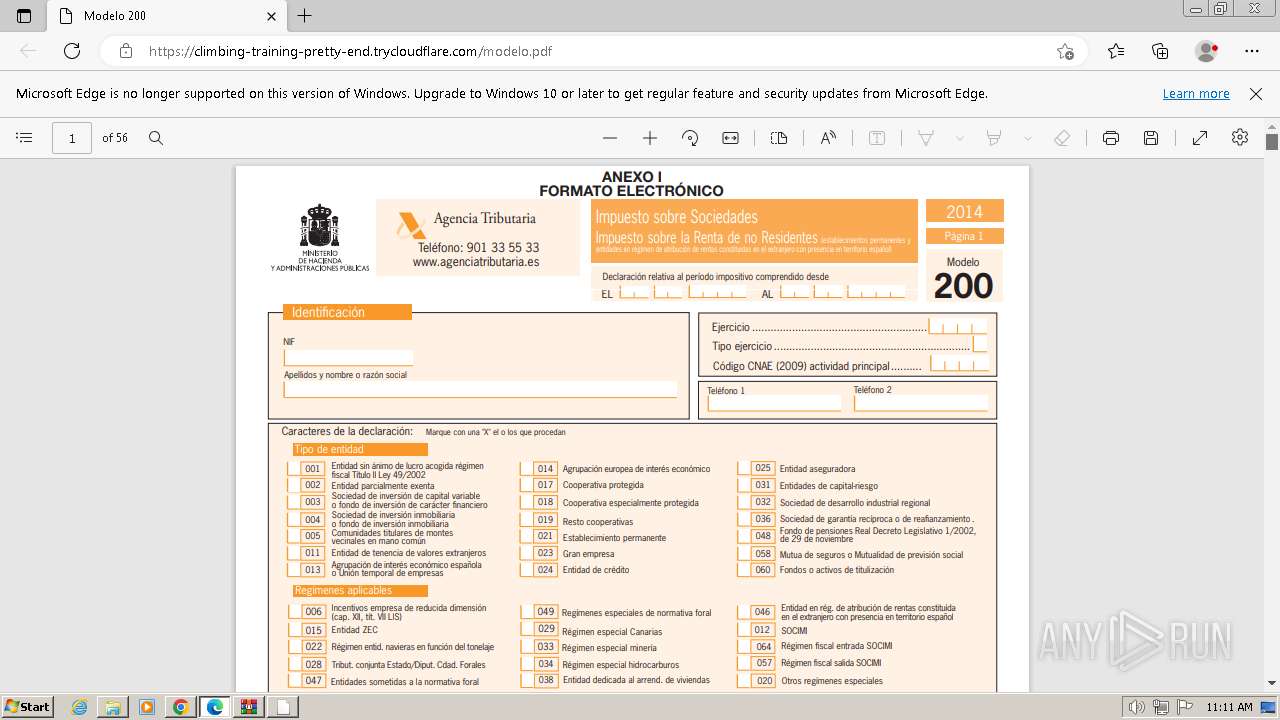
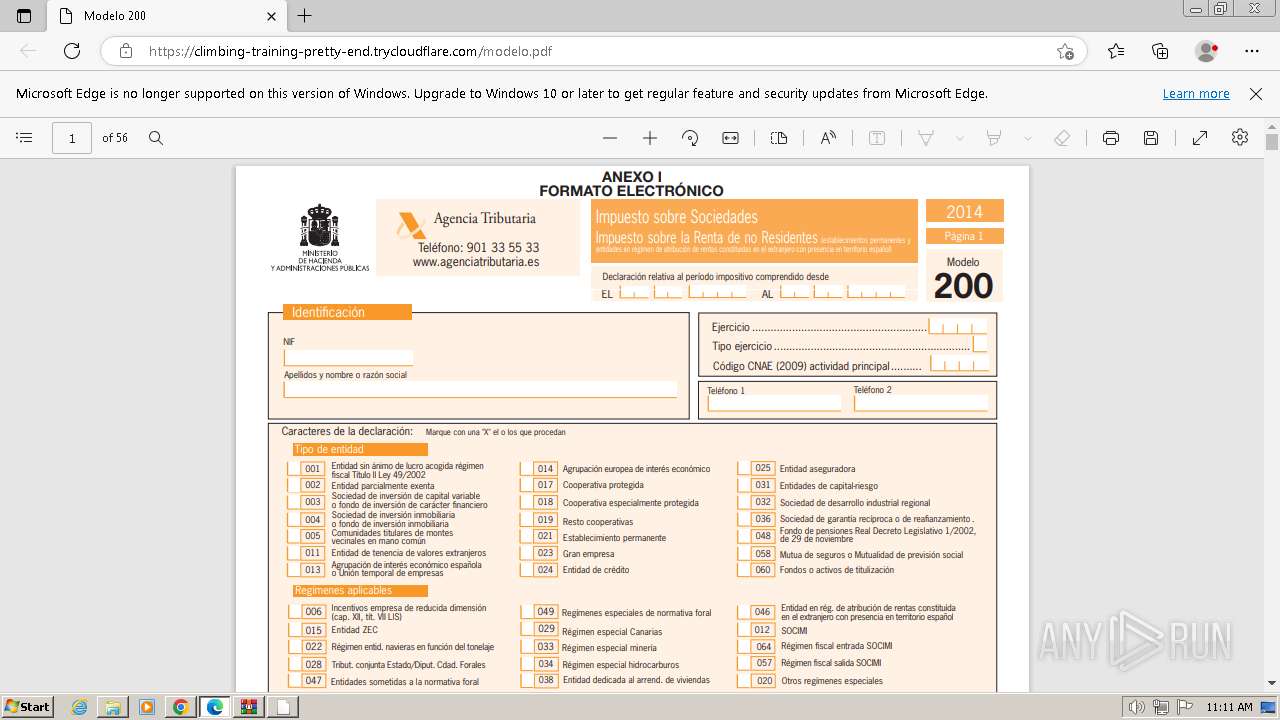
| 984 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --single-argument https://climbing-training-pretty-end.trycloudflare.com/modelo.pdf | C:\Program Files\Microsoft\Edge\Application\msedge.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1512 --field-trial-handle=1160,i,16333170535993396045,14541901396367095458,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3784 --field-trial-handle=1412,i,4091416865120920642,1291031777135613424,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
49 926
Read events
49 599
Write events
298
Delete events
29
Modification events
| (PID) Process: | (1164) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000DBDD10622BD67741A42163F361389C470000000002000000000010660000000100002000000091C40B09018A30DD0D9B469D7B66A7DC0B490AEE281A52AAE3BCD5166F2752BA000000000E80000000020000200000004EEC60C6A703F000E54A2B26B7327A97945FF7F7AAECB88B70829ADCA580819930000000DA0CEA889B27C051906C5006C14B49D2269D5D1A2FD1964A5A079EE1A680B1F823C0B43A1BC3B23A9F1390E5403BCD1640000000DEB6E6A4AC79DB6C662D0A96F86E811463CDE85916FCB2EC73CD2EDBAF04B1D77647E815766B35062D8267BFA15D7C8B4FAA654B46588C44CE6A623CD711C285 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
72
Text files
115
Unknown types
76
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f8b8.TMP | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF17f8c7.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1802f9.TMP | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
86
DNS requests
68
Threats
76
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
828 | svchost.exe | OPTIONS | 200 | 198.37.119.150:80 | http://diatruiest.com/sniptool/work/a.ico | unknown | — | — | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
828 | svchost.exe | PROPFIND | 404 | 198.37.119.150:80 | http://diatruiest.com/sniptool/work/a.ico | unknown | xml | 1.16 Kb | unknown |
828 | svchost.exe | PROPFIND | 404 | 198.37.119.150:80 | http://diatruiest.com/sniptool/work | unknown | xml | 1.16 Kb | unknown |
828 | svchost.exe | PROPFIND | 404 | 198.37.119.150:80 | http://diatruiest.com/sniptool/work/a.ico.DLL | unknown | xml | 1.16 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | binary | 6.31 Kb | unknown |
828 | svchost.exe | PROPFIND | 404 | 198.37.119.150:80 | http://diatruiest.com/sniptool/work | unknown | xml | 1.16 Kb | unknown |
828 | svchost.exe | PROPFIND | 404 | 198.37.119.150:80 | http://diatruiest.com/sniptool/work/a.ico | unknown | xml | 1.16 Kb | unknown |
828 | svchost.exe | PROPFIND | 404 | 198.37.119.150:80 | http://diatruiest.com/sniptool/work/a.ico | unknown | xml | 1.16 Kb | unknown |
828 | svchost.exe | PROPFIND | 404 | 198.37.119.150:80 | http://diatruiest.com/sniptool/work | unknown | xml | 1.16 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3460 | chrome.exe | 66.102.1.84:443 | accounts.google.com | GOOGLE | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3652 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3460 | chrome.exe | 108.156.60.105:443 | docsend.dropbox.com | AMAZON-02 | US | unknown |
3460 | chrome.exe | 143.204.215.39:443 | assets.docsend.com | AMAZON-02 | US | unknown |
3460 | chrome.exe | 142.250.185.234:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3460 | chrome.exe | 162.125.66.18:443 | www.dropbox.com | DROPBOX | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
docsend.dropbox.com |
| unknown |
assets.docsend.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
www.dropbox.com |
| shared |
assets.ducksend.com |
| unknown |
cfl.dropboxstatic.com |
| shared |
d.dropbox.com |
| unknown |
widget.intercom.io |
| shared |
consent.dropbox.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3460 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
3460 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
3460 | chrome.exe | Misc activity | ET INFO DropBox User Content Download Access over SSL M2 |
1080 | svchost.exe | Potentially Bad Traffic | ET POLICY Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
1164 | explorer.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Cloudflare Domain Abuse for Phishing Purposes (RGDA) |
828 | svchost.exe | Malware Command and Control Activity Detected | ET MALWARE Suspected REDCURL CnC Activity M1 |
828 | svchost.exe | Malware Command and Control Activity Detected | ET MALWARE Suspected REDCURL CnC Activity M1 |
3284 | msedge.exe | Potentially Bad Traffic | ET POLICY Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
3284 | msedge.exe | Potentially Bad Traffic | ET POLICY Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
3284 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Cloudflare Domain Abuse for Phishing Purposes (RGDA) |
61 ETPRO signatures available at the full report