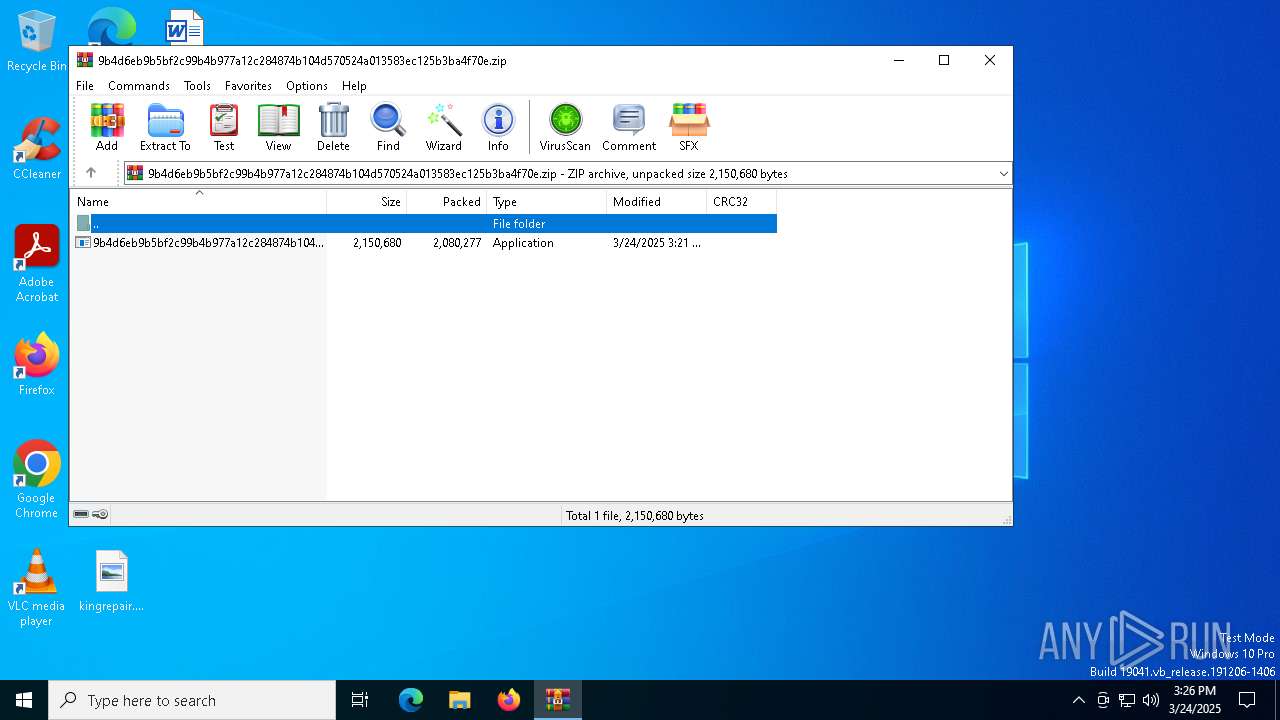
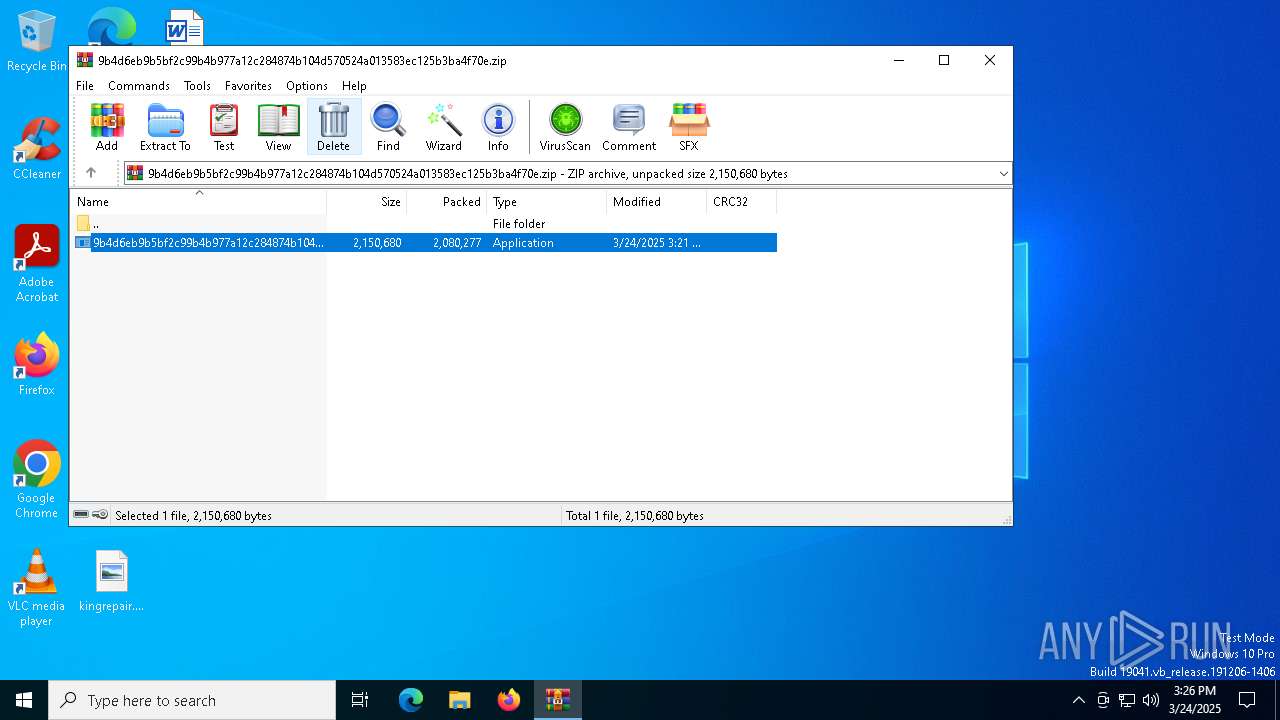
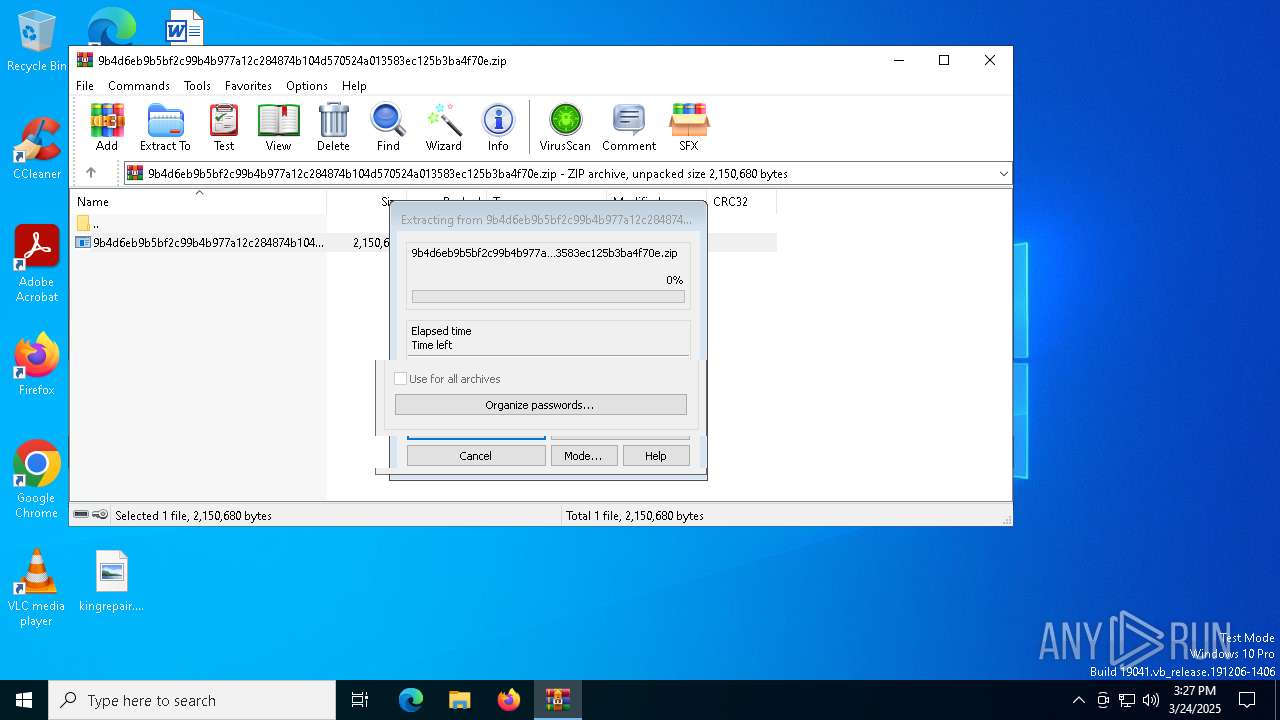
| File name: | 9b4d6eb9b5bf2c99b4b977a12c284874b104d570524a013583ec125b3ba4f70e.zip |
| Full analysis: | https://app.any.run/tasks/e6666a45-8678-4dc6-a4f1-15ce180b122d |
| Verdict: | Malicious activity |
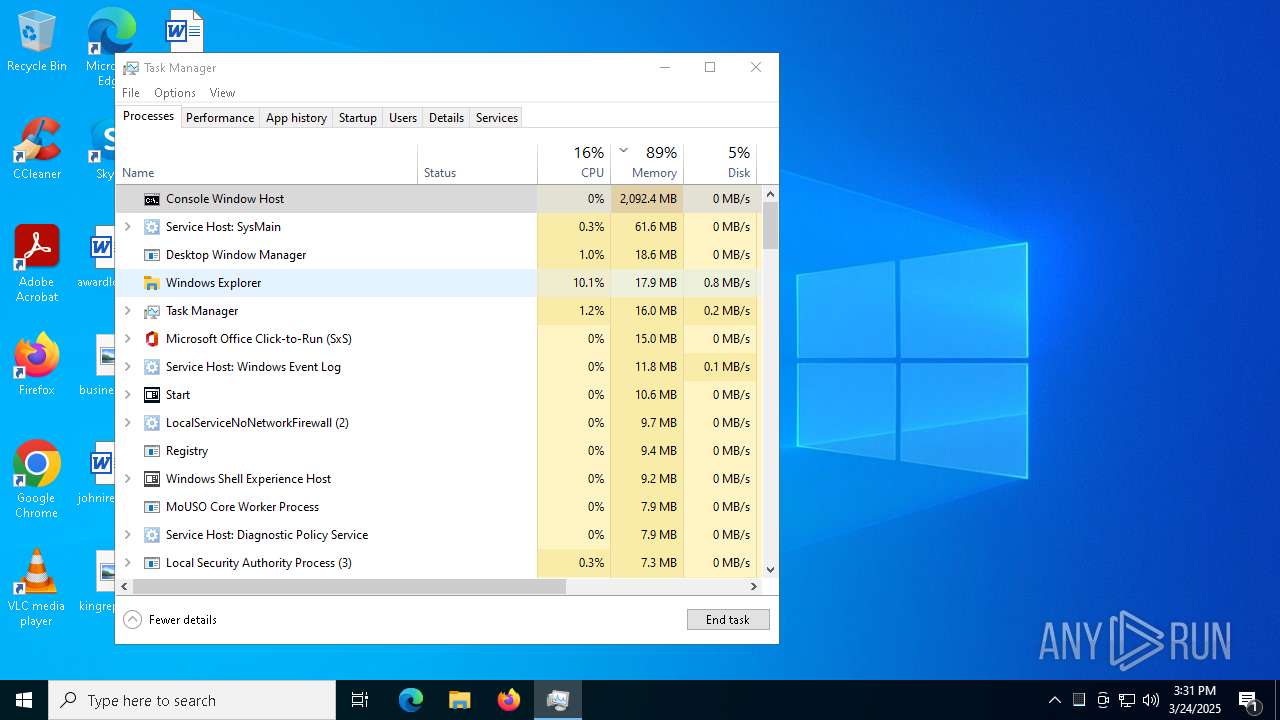
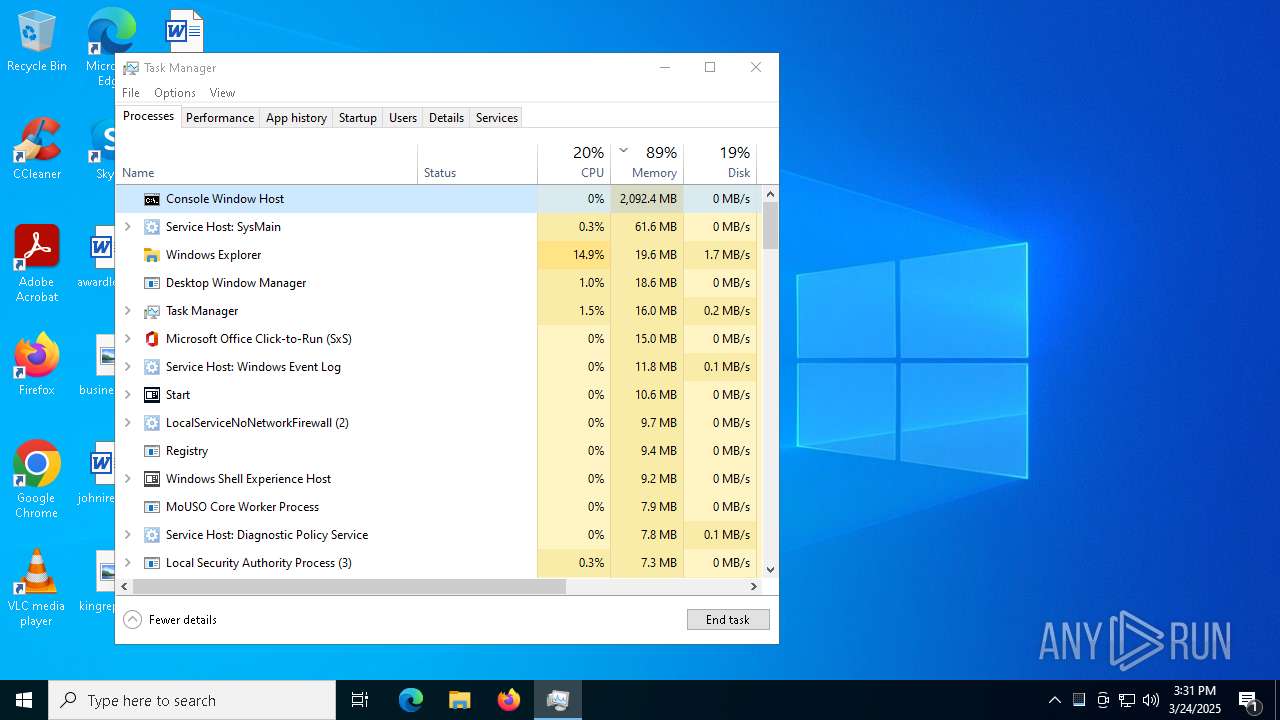
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | March 24, 2025, 15:26:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
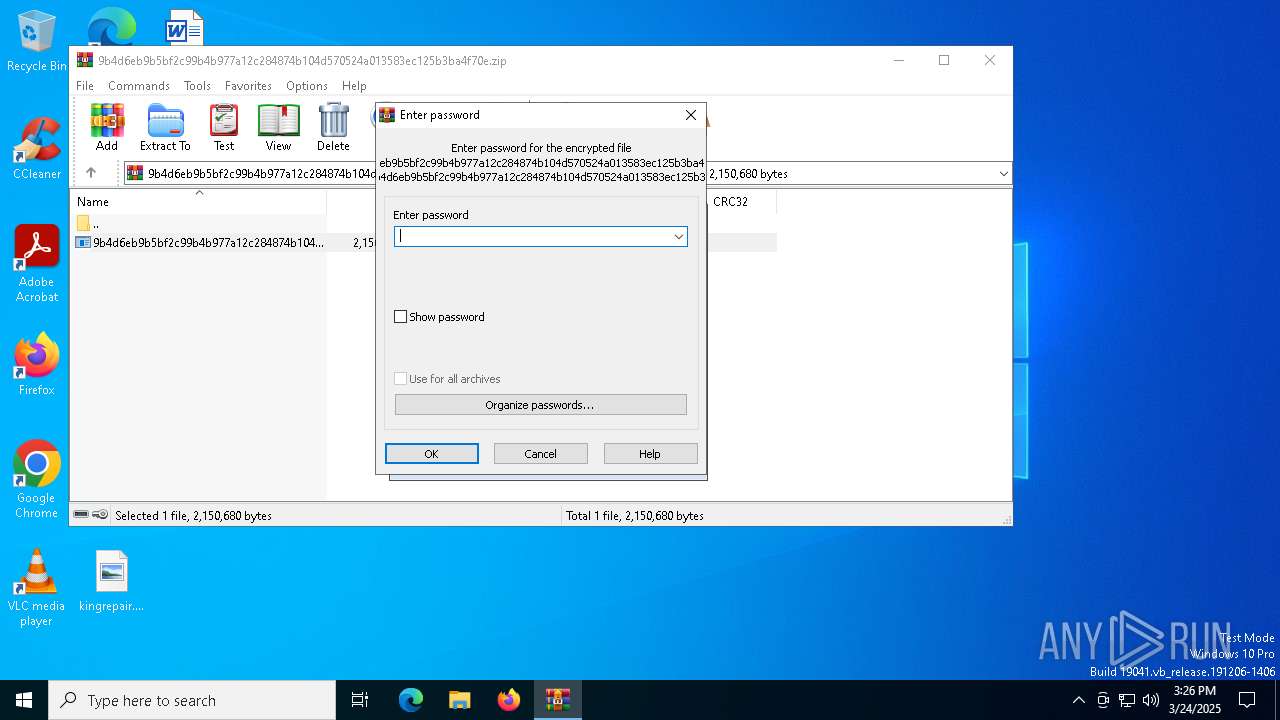
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 2F9B12947C8854A3F040AE1CADD15C73 |
| SHA1: | B8FEBCD0228592F26A0B442E9A6F899D085C1E6F |
| SHA256: | A90C22F60C0BEA09BBBA772BD97995503659B19207348DB2BA05C23DA92B316E |
| SSDEEP: | 98304:uUbkO4XspkSB2jpN8JTN7uE3OpdLLdfG3LgUD+IY+A+0wqhezScskB2c4NlUIb41:nf6o |
MALICIOUS
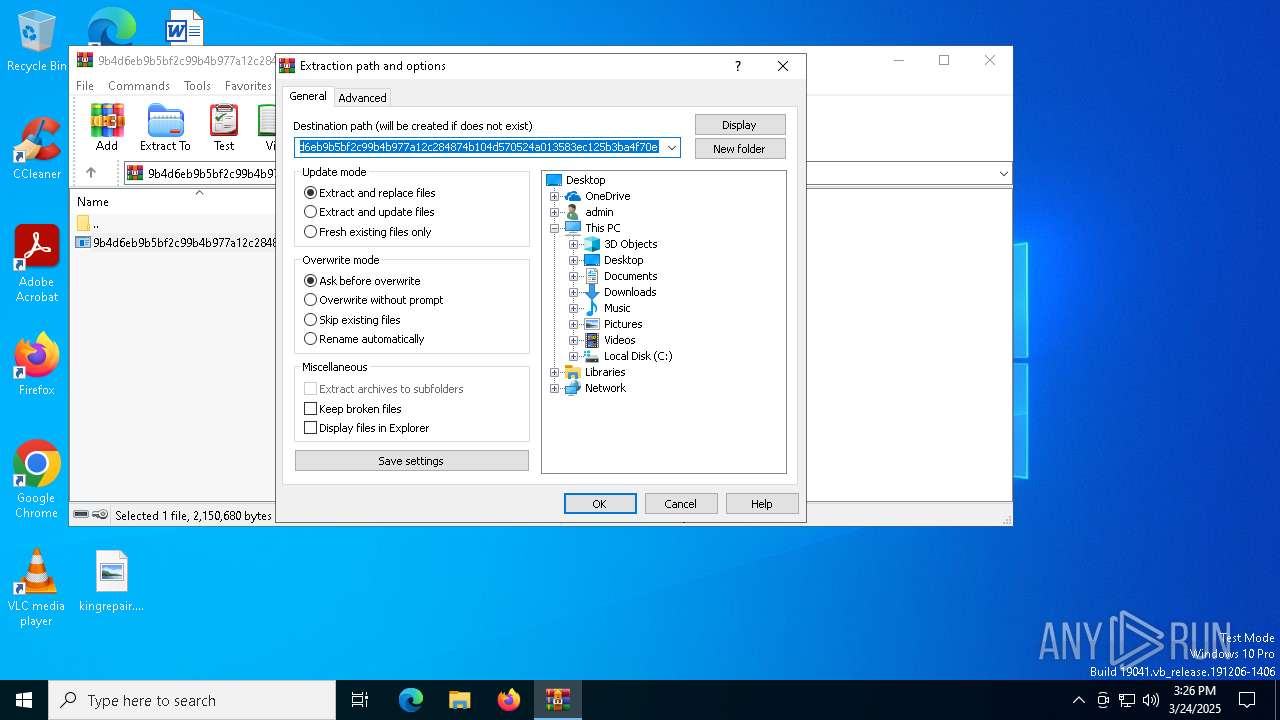
Generic archive extractor
- WinRAR.exe (PID: 4448)
Executing a file with an untrusted certificate
- 9b4d6eb9b5bf2c99b4b977a12c284874b104d570524a013583ec125b3ba4f70e.exe (PID: 8024)
- 9b4d6eb9b5bf2c99b4b977a12c284874b104d570524a013583ec125b3ba4f70e.exe (PID: 8072)
- updater.exe (PID: 7260)
Vulnerable driver has been detected
- updater.exe (PID: 7260)
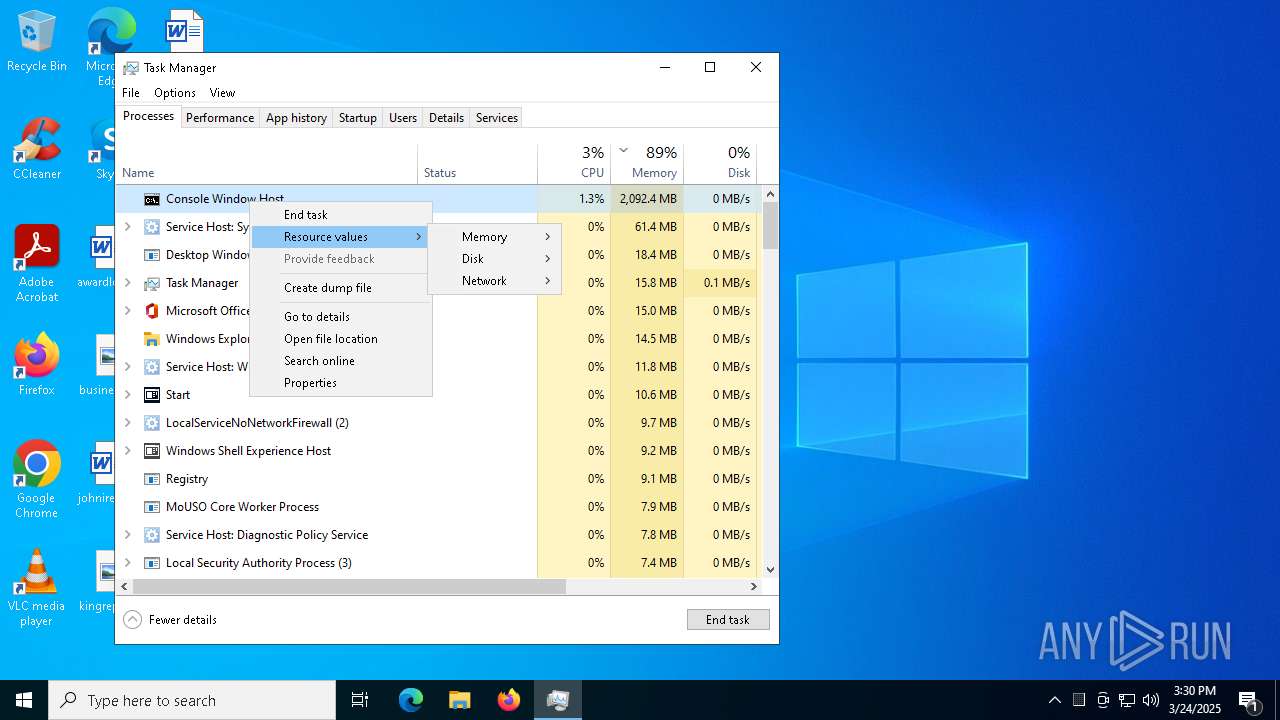
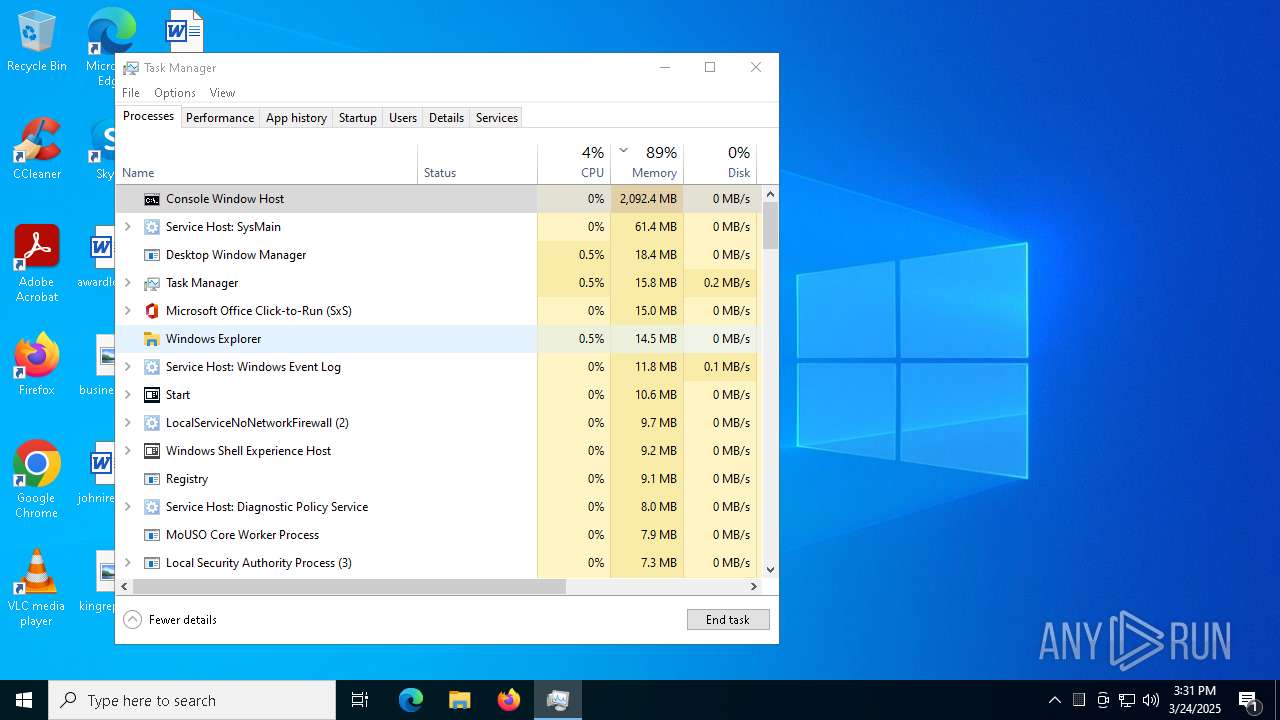
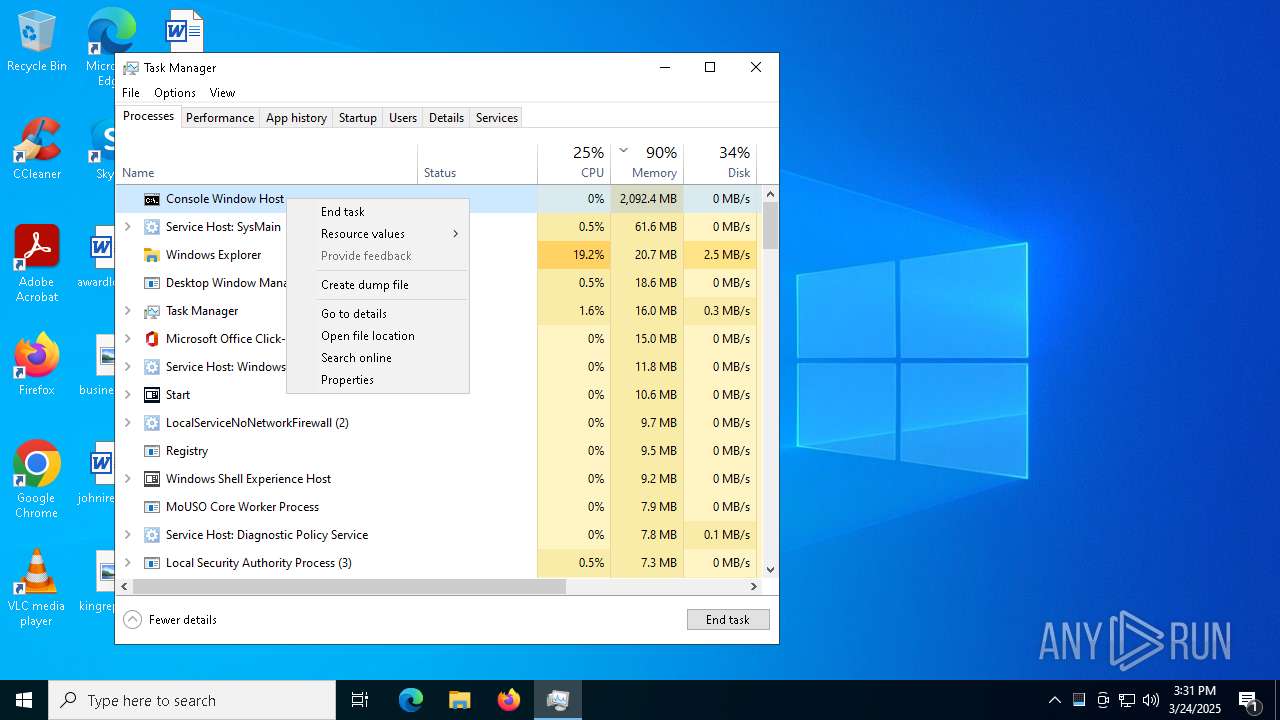
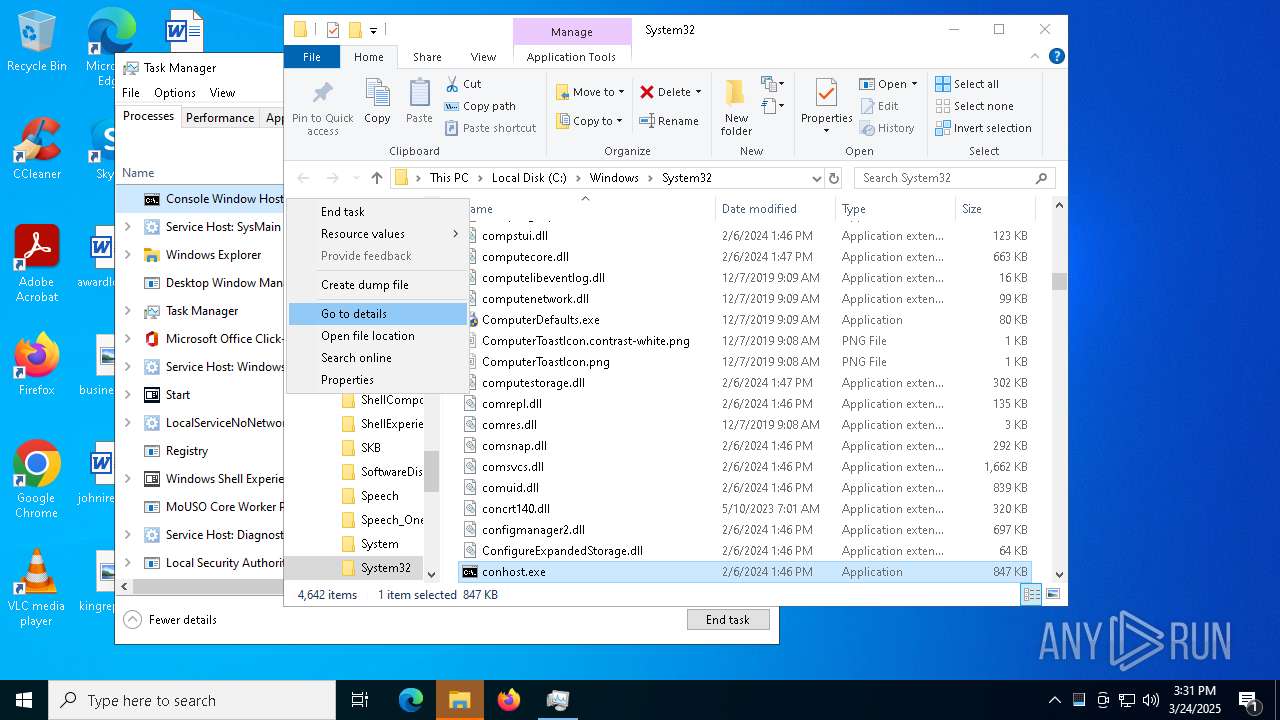
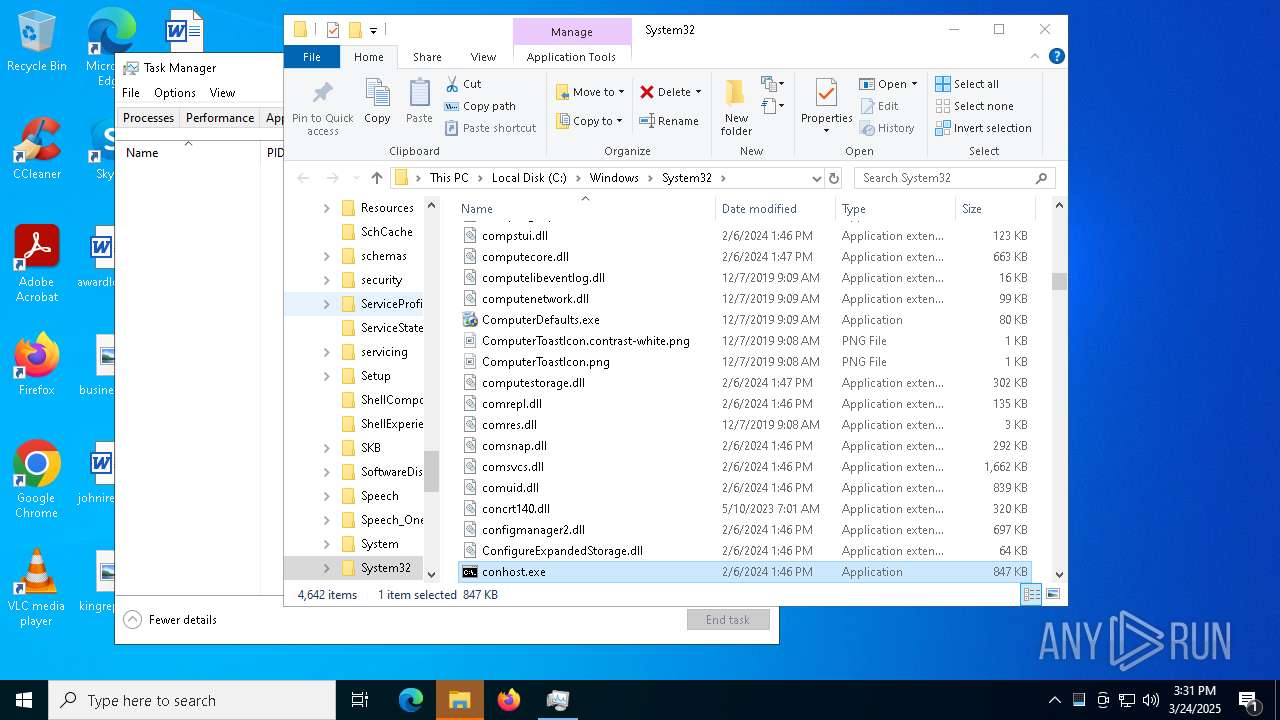
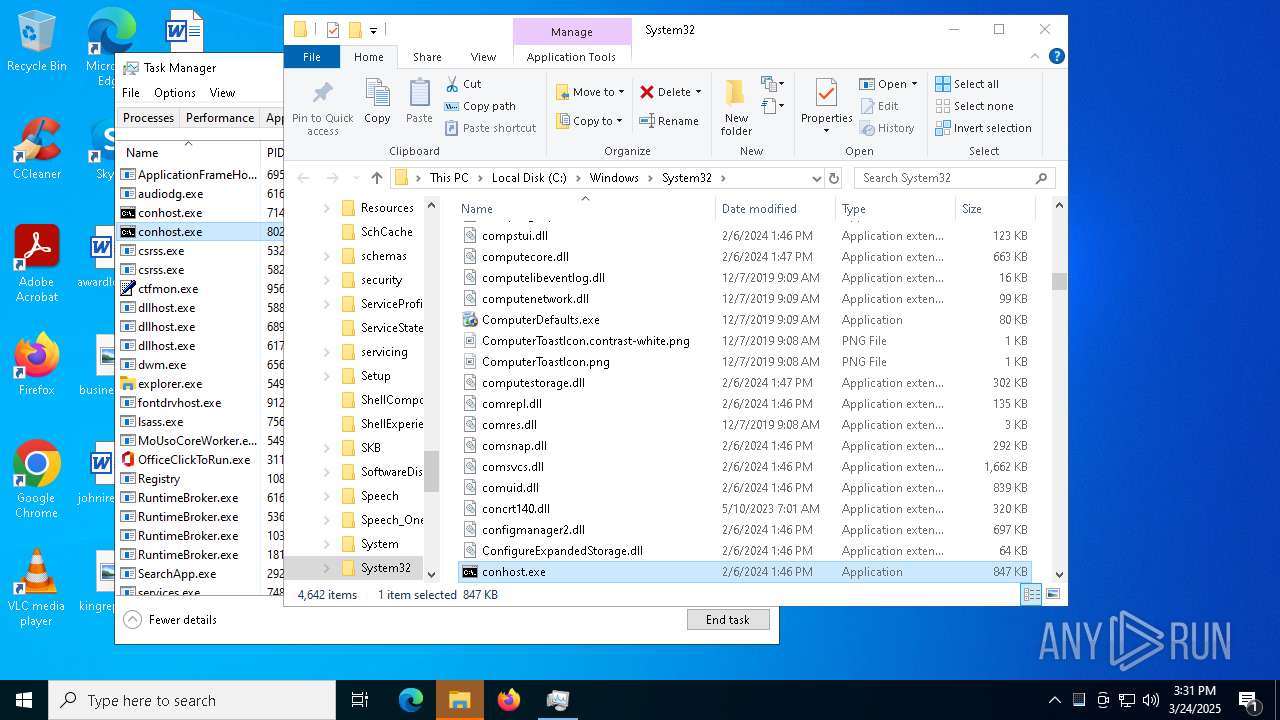
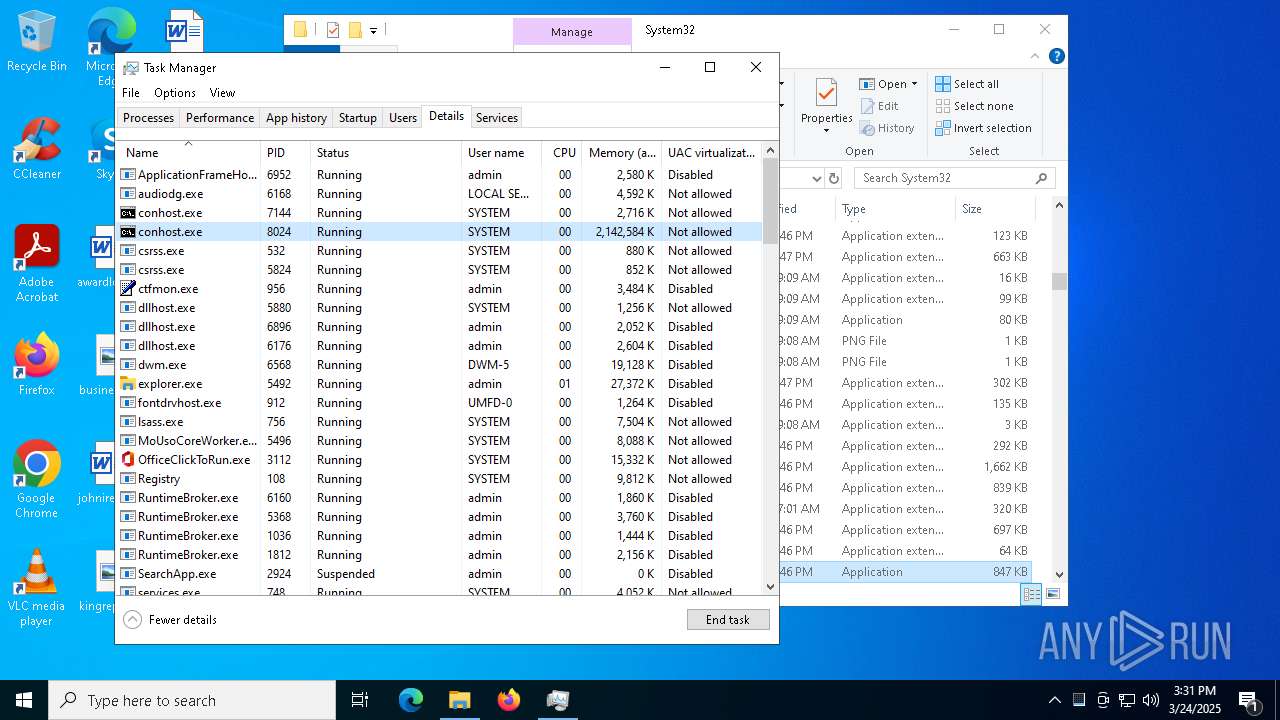
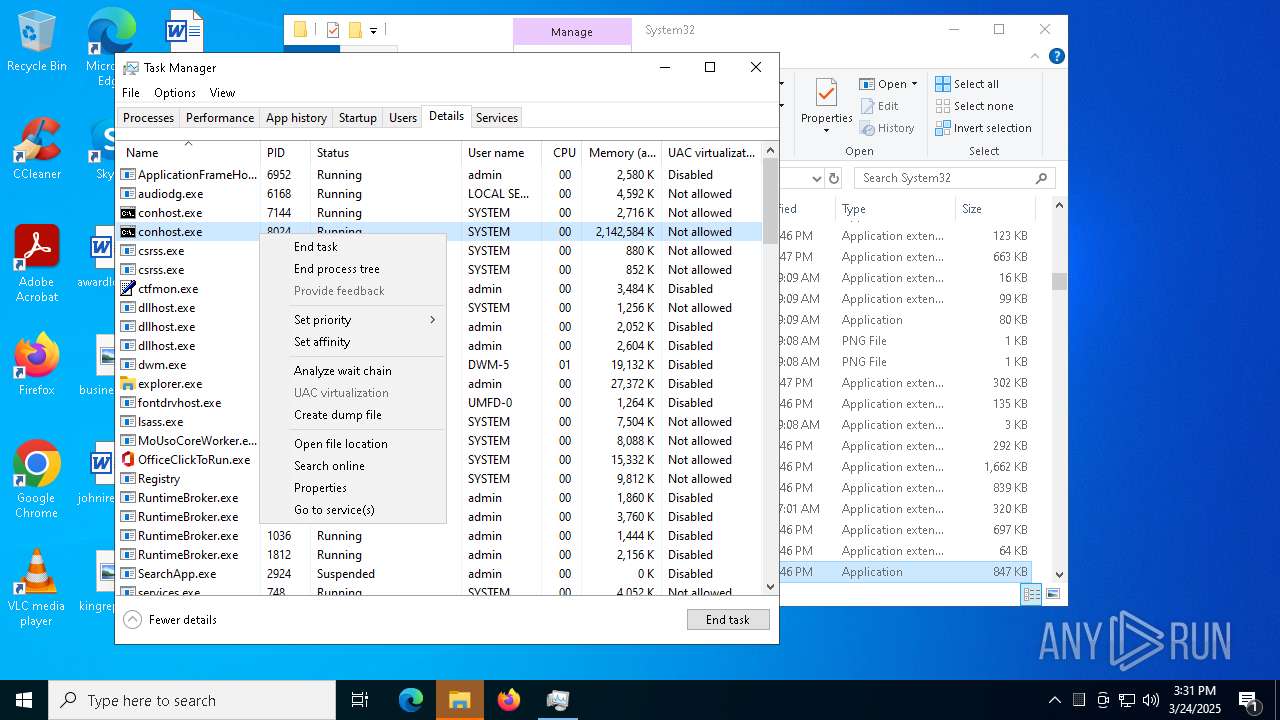
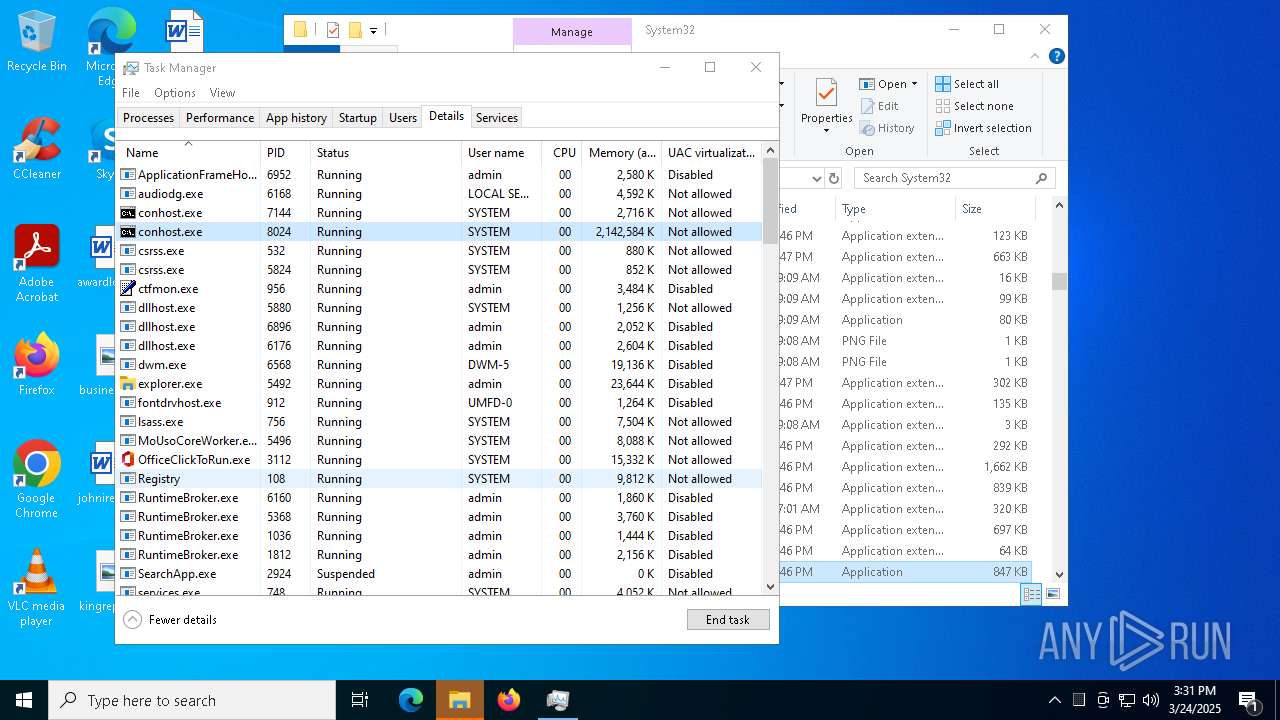
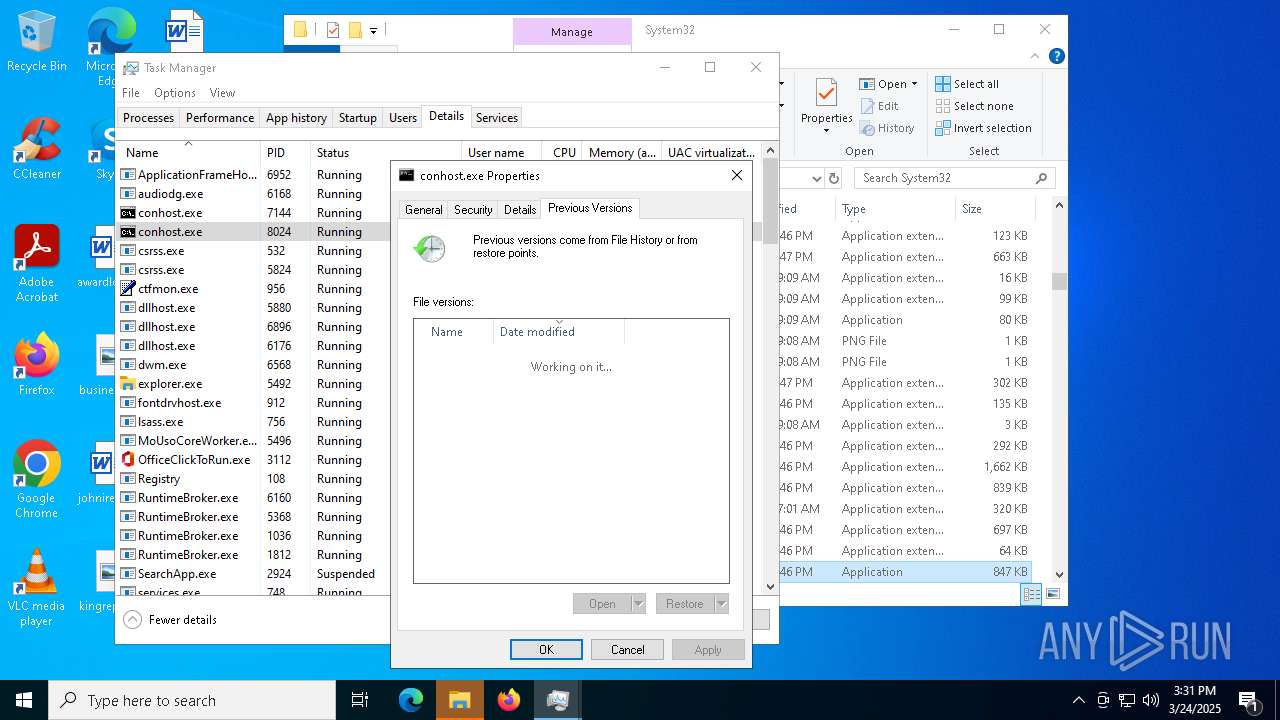
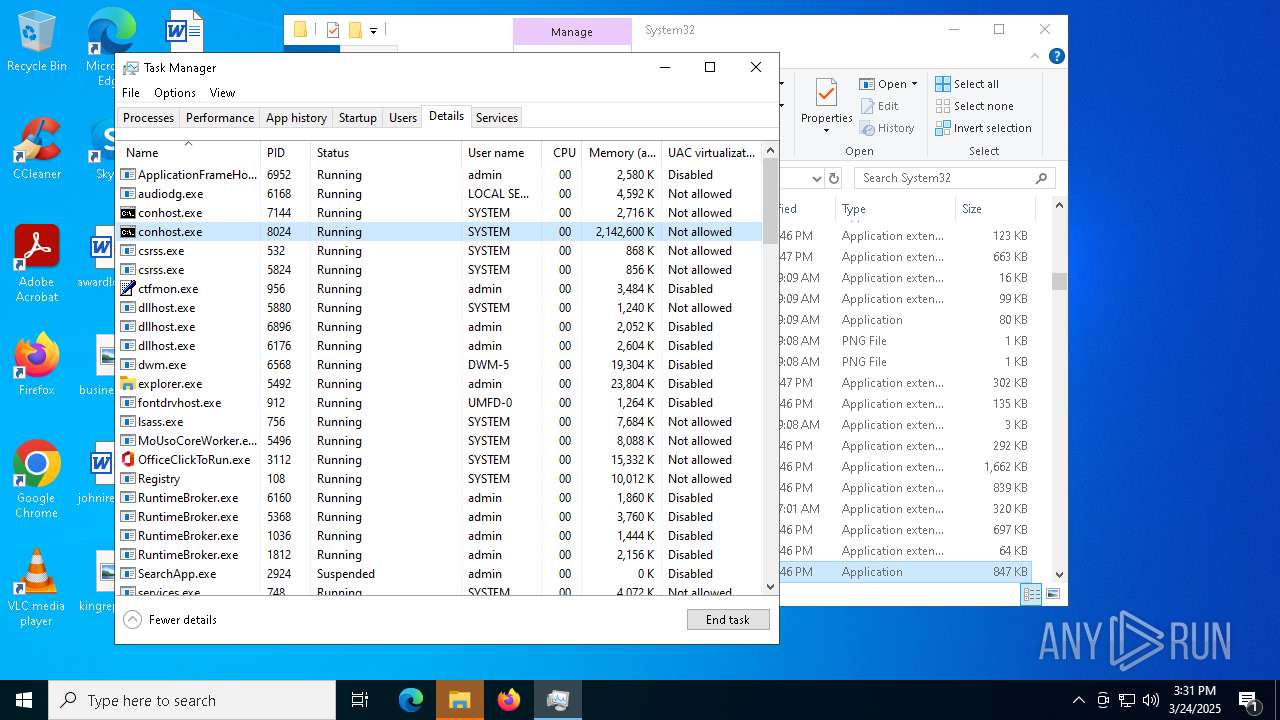
Execute application with conhost.exe as parent process
- cmd.exe (PID: 7152)
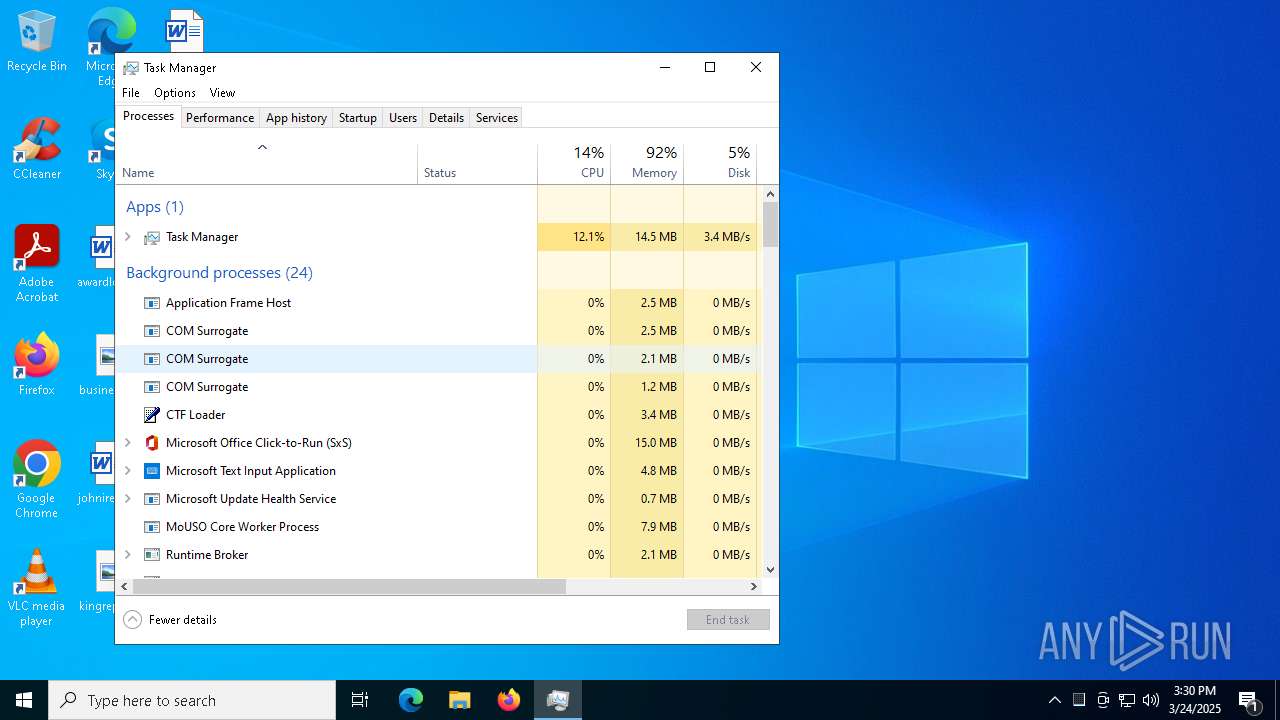
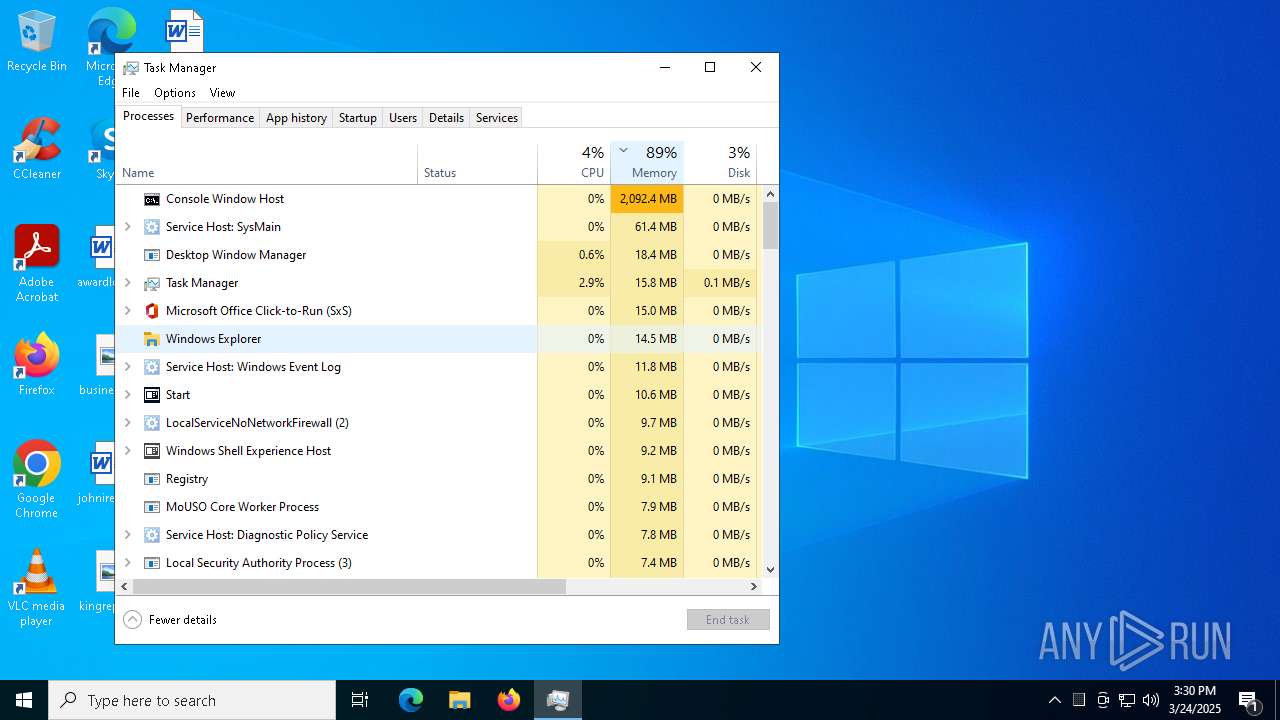
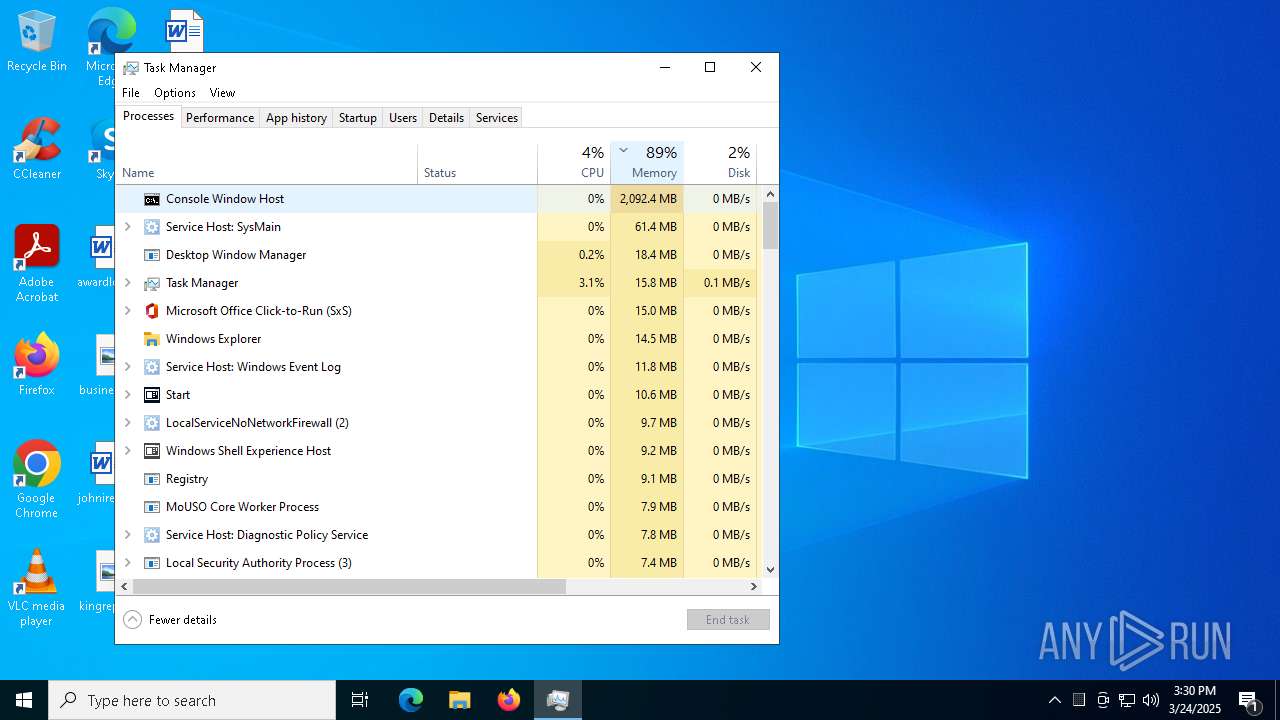
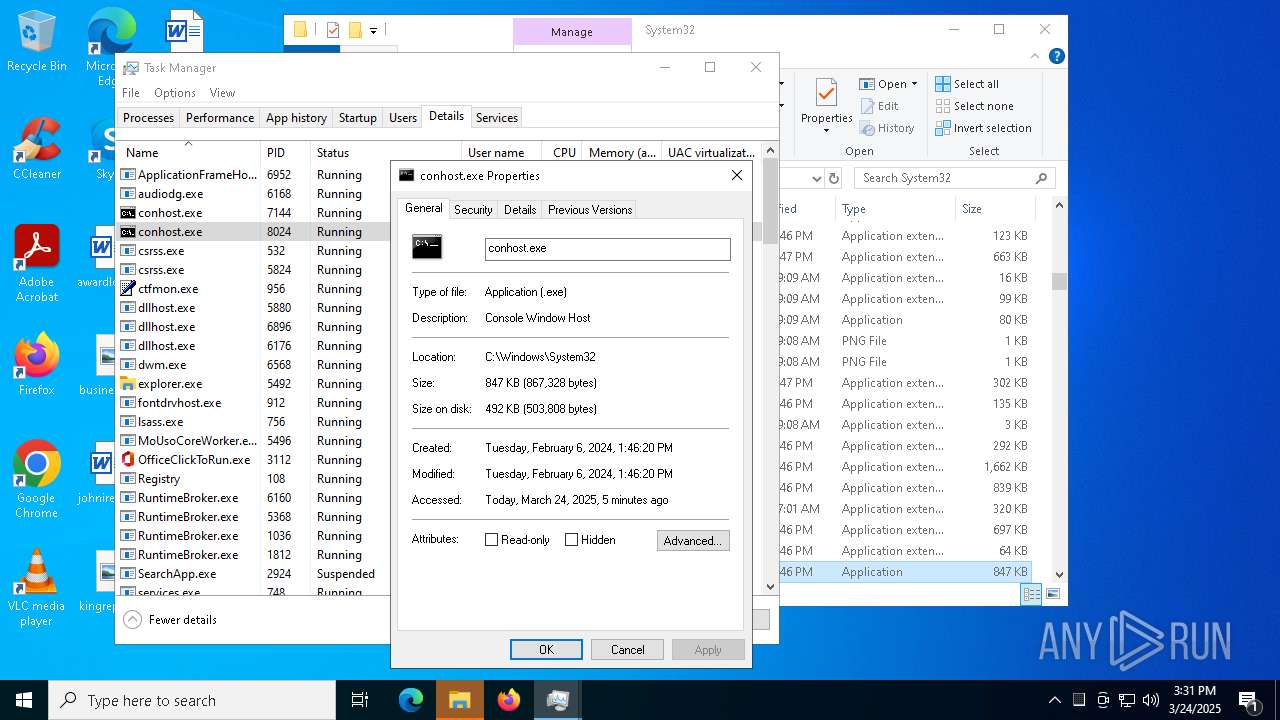
MINER has been detected (SURICATA)
- conhost.exe (PID: 8024)
- svchost.exe (PID: 2196)
Connects to the CnC server
- conhost.exe (PID: 8024)
XORed URL has been found (YARA)
- conhost.exe (PID: 8024)
XMRIG has been detected (YARA)
- conhost.exe (PID: 8024)
SUSPICIOUS
Manipulates environment variables
- powershell.exe (PID: 8092)
- powershell.exe (PID: 7256)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 7712)
- cmd.exe (PID: 7420)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 7900)
- powershell.exe (PID: 3888)
- powershell.exe (PID: 7432)
Executable content was dropped or overwritten
- 9b4d6eb9b5bf2c99b4b977a12c284874b104d570524a013583ec125b3ba4f70e.exe (PID: 8072)
- updater.exe (PID: 7260)
The process executes via Task Scheduler
- updater.exe (PID: 7260)
Drops a system driver (possible attempt to evade defenses)
- updater.exe (PID: 7260)
Starts CMD.EXE for commands execution
- conhost.exe (PID: 7144)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 1388)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 5776)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2196)
- conhost.exe (PID: 8024)
Connects to unusual port
- conhost.exe (PID: 8024)
Uses pipe srvsvc via SMB (transferring data)
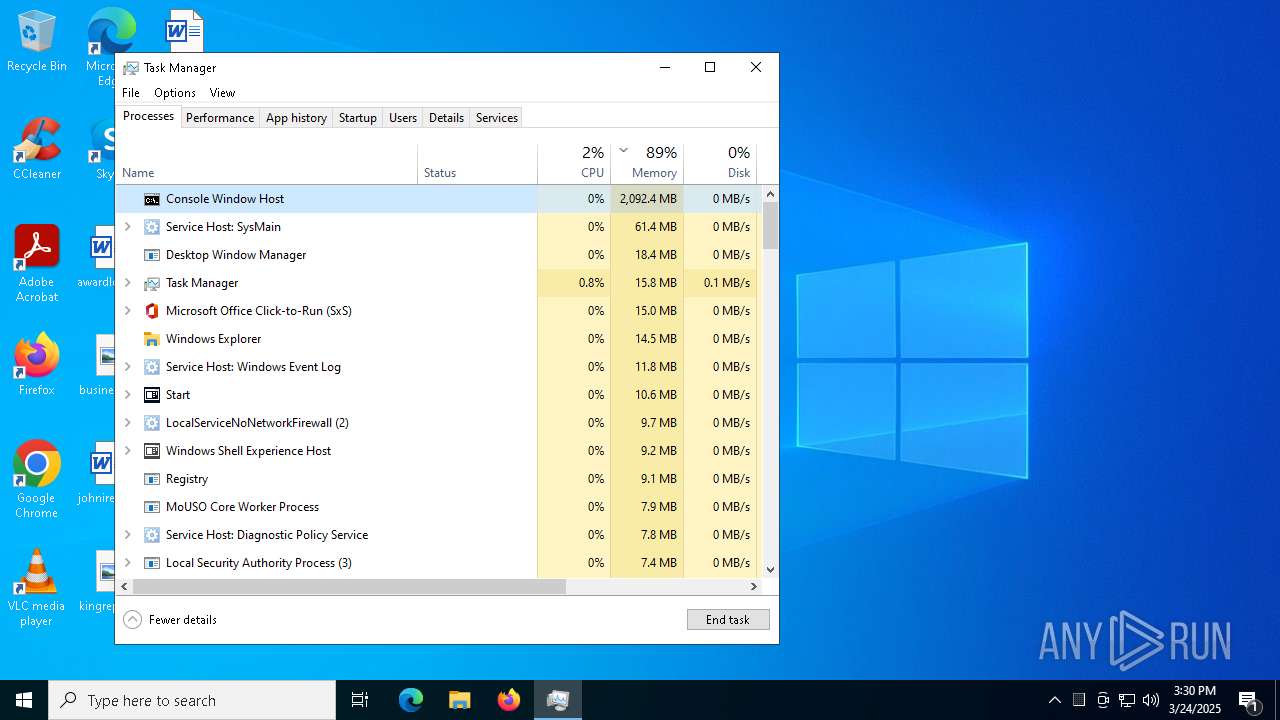
- Taskmgr.exe (PID: 7588)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7928)
- BackgroundTransferHost.exe (PID: 2904)
- BackgroundTransferHost.exe (PID: 8152)
- BackgroundTransferHost.exe (PID: 5868)
- BackgroundTransferHost.exe (PID: 7520)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 8152)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 8152)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 8152)
Manual execution by a user
- 9b4d6eb9b5bf2c99b4b977a12c284874b104d570524a013583ec125b3ba4f70e.exe (PID: 8024)
- 9b4d6eb9b5bf2c99b4b977a12c284874b104d570524a013583ec125b3ba4f70e.exe (PID: 8072)
- powershell.exe (PID: 8092)
- cmd.exe (PID: 7712)
- powershell.exe (PID: 7900)
- cmd.exe (PID: 1672)
- powershell.exe (PID: 3888)
- powershell.exe (PID: 7432)
- powershell.exe (PID: 7256)
- cmd.exe (PID: 7420)
- cmd.exe (PID: 5776)
- conhost.exe (PID: 7144)
- conhost.exe (PID: 8024)
- Taskmgr.exe (PID: 776)
- Taskmgr.exe (PID: 7588)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4448)
The sample compiled with english language support
- WinRAR.exe (PID: 4448)
- 9b4d6eb9b5bf2c99b4b977a12c284874b104d570524a013583ec125b3ba4f70e.exe (PID: 8072)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8092)
- powershell.exe (PID: 7256)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8092)
- powershell.exe (PID: 7256)
- powershell.exe (PID: 7900)
- powershell.exe (PID: 7432)
Creates files in the program directory
- 9b4d6eb9b5bf2c99b4b977a12c284874b104d570524a013583ec125b3ba4f70e.exe (PID: 8072)
- updater.exe (PID: 7260)
The sample compiled with japanese language support
- updater.exe (PID: 7260)
Reads the computer name
- ShellExperienceHost.exe (PID: 6872)
UPX packer has been detected
- conhost.exe (PID: 8024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:03:24 15:21:08 |
| ZipCRC: | 0x7afe84a7 |
| ZipCompressedSize: | 2080277 |
| ZipUncompressedSize: | 2150680 |
| ZipFileName: | 9b4d6eb9b5bf2c99b4b977a12c284874b104d570524a013583ec125b3ba4f70e.exe |
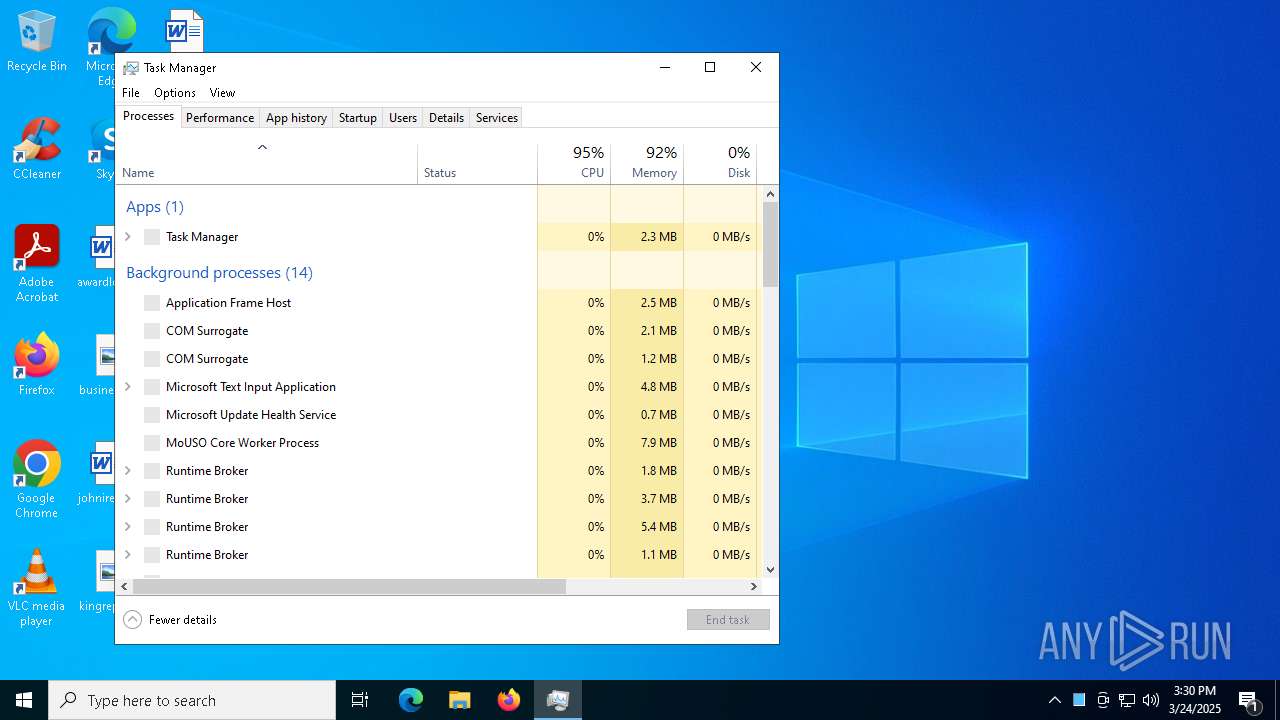
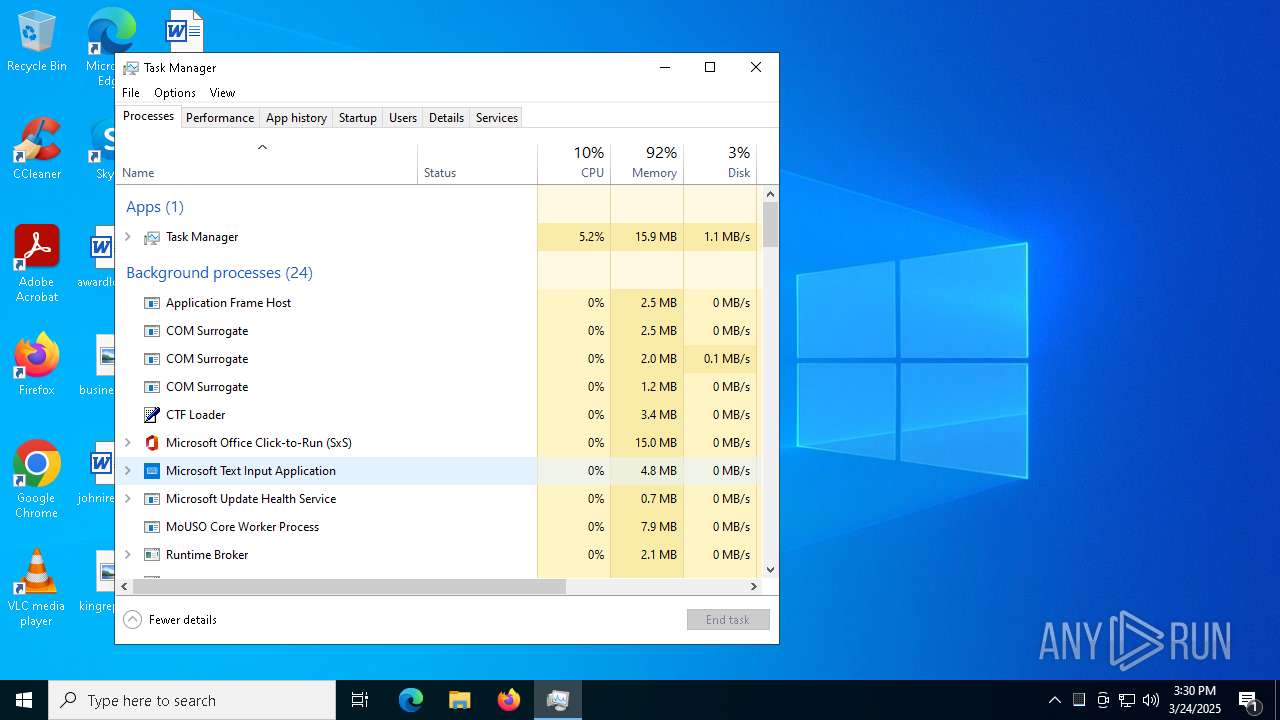
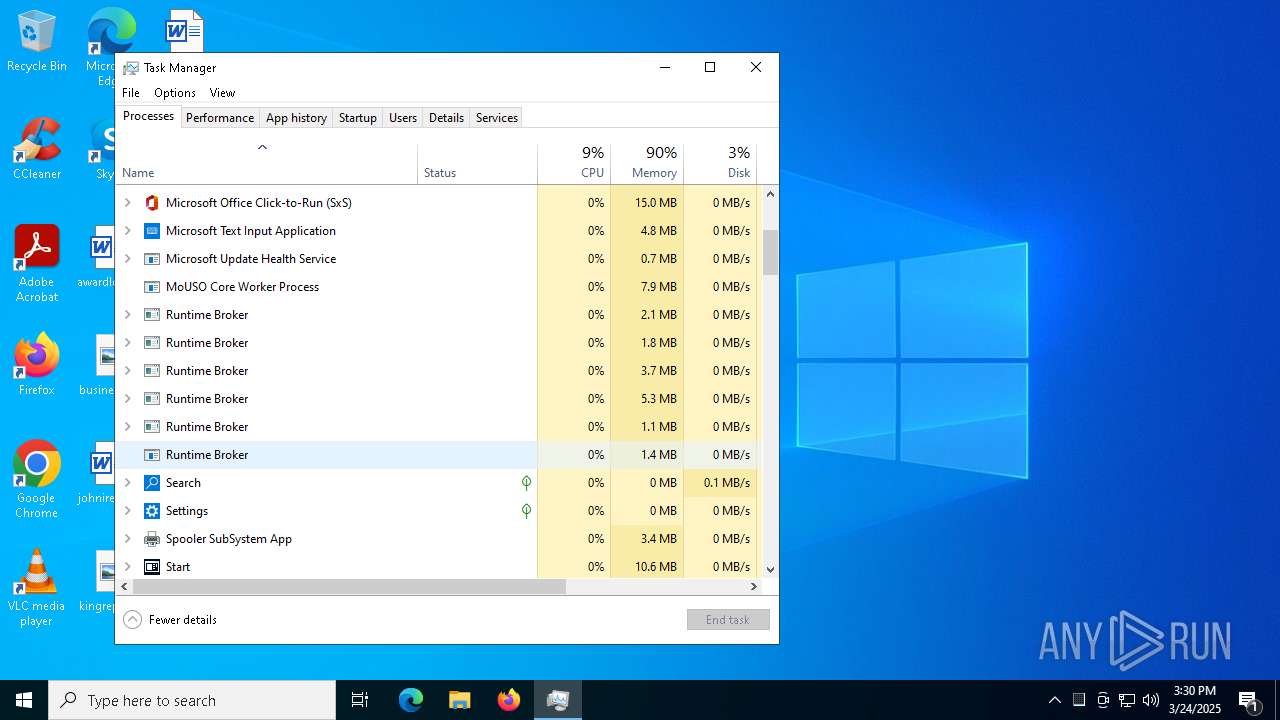
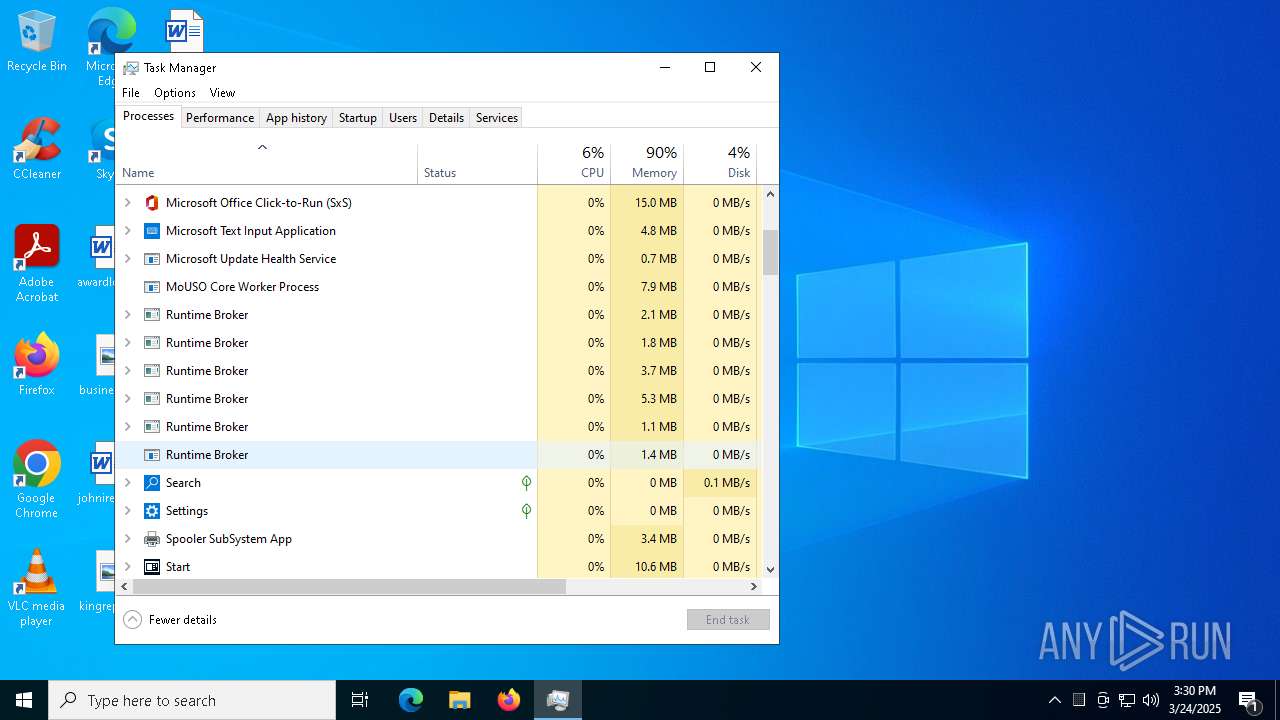
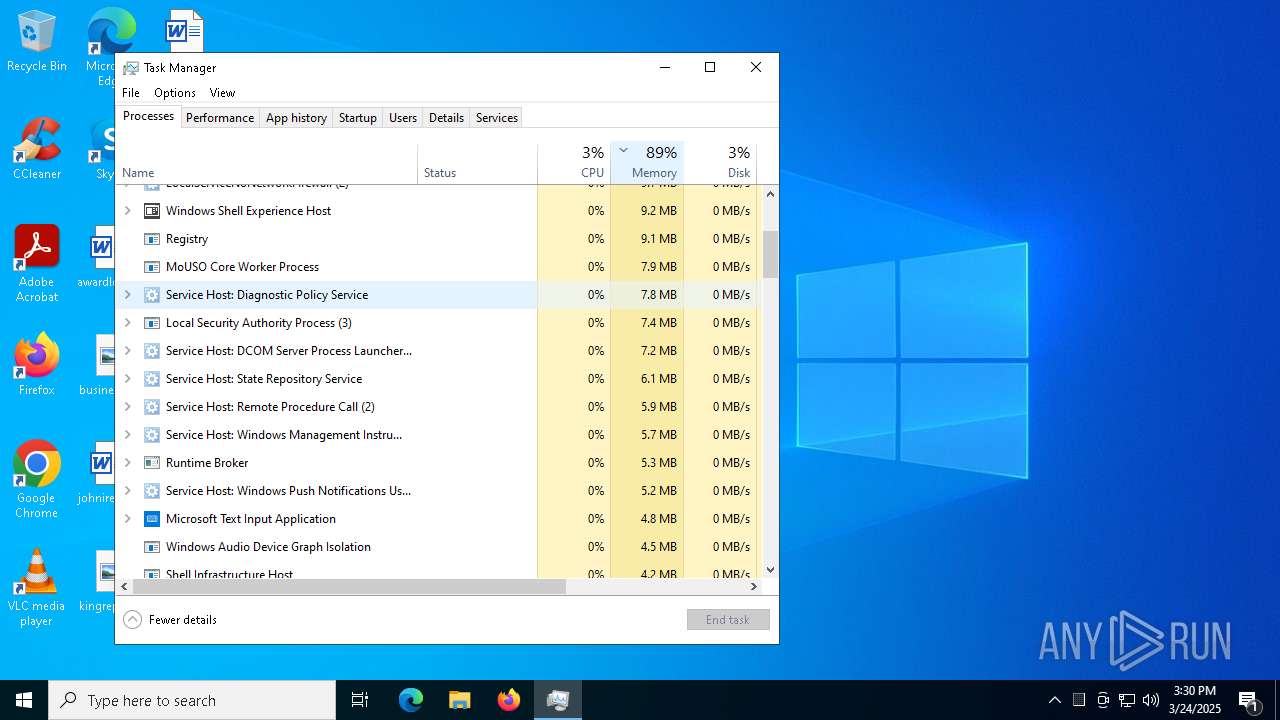
Total processes
195
Monitored processes
50
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | powercfg /x -hibernate-timeout-dc 0 | C:\Windows\System32\powercfg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | "C:\WINDOWS\system32\taskmgr.exe" /0 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | wmic PATH Win32_VideoController GET Name, VideoProcessor | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1672 | C:\WINDOWS\System32\cmd.exe /c choice /C Y /N /D Y /T 3 & Del "C:\Users\admin\Desktop\9b4d6eb9b5bf2c99b4b977a12c284874b104d570524a013583ec125b3ba4f70e.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2904 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe <#cbgyjptmk#> IF((New-Object Security.Principal.WindowsPrincipal([Security.Principal.WindowsIdentity]::GetCurrent())).IsInRole([Security.Principal.WindowsBuiltInRole]::Administrator)) { schtasks /run /tn "GoogleUpdateTaskMachineQC" } Else { "C:\Program Files\Google\Chrome\updater.exe" } | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4408 | powercfg /x -standby-timeout-dc 0 | C:\Windows\System32\powercfg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
39 895
Read events
39 840
Write events
41
Delete events
14
Modification events
| (PID) Process: | (4448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\9b4d6eb9b5bf2c99b4b977a12c284874b104d570524a013583ec125b3ba4f70e.zip | |||
| (PID) Process: | (4448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4448) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7928) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7928) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
5
Suspicious files
7
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8152 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\b963ee45-00ce-436e-a62a-3c64871e5a4d.down_data | — | |
MD5:— | SHA256:— | |||
| 8152 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\b963ee45-00ce-436e-a62a-3c64871e5a4d.79a00931-7560-4ce6-982f-9dd0ee8d9a6d.down_meta | binary | |
MD5:79A734360B91512F8A20B67C0D5F183D | SHA256:15E99300D89F13303F6B3185420DDAD85FE13E7ADE0B7520431705FD9B617458 | |||
| 8152 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:4872BABAF39AA62B8D32695EBB7E9173 | SHA256:2EE85DF86EE29BBEB3DCA81AA29B6DE204F605A2769B84C728A329178A2D0999 | |||
| 7900 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_a4psogvq.jxr.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7256 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_0cq1sl2u.k05.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7432 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_5wmxflq4.tlo.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7256 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_fg0el3vf.wln.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3888 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_x4vlblmt.mfy.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7256 | powershell.exe | C:\Windows\System32\config\systemprofile\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:7E202197B0658D8E4F0A8A000C52F81F | SHA256:E69F69276D95CEE19482D68606DC9D4396F409A76033EE24060ACED08D83585F | |||
| 7588 | Taskmgr.exe | \Device\Mup:\localhost\PIPE\srvsvc | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
32
DNS requests
22
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7344 | backgroundTaskHost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6512 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8152 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6512 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
4164 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.63.118.230:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO Observed DNS Query to Coin Mining Domain (nanopool .org) |
8024 | conhost.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
8024 | conhost.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |