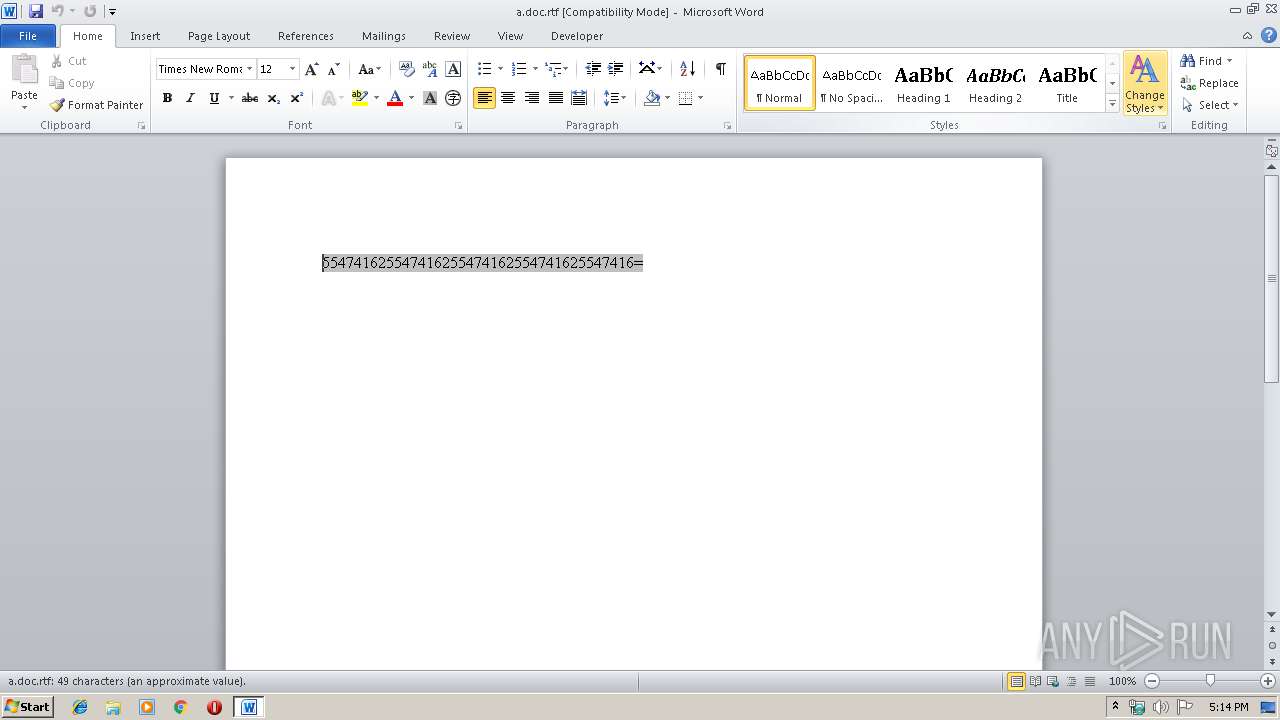
| File name: | a.doc |
| Full analysis: | https://app.any.run/tasks/509e5047-3552-4dea-86ce-308715b7efa9 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | October 14, 2019, 16:14:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, unknown version |
| MD5: | 874C64DD0FDAD641AB85FD78636E3714 |
| SHA1: | 7AE611FBB77DAFE73321C3CDF257702346845FD7 |
| SHA256: | A8D83B286651CEF3BF8E96A3727D96F246675CC604A7CF78B294233A703885B9 |
| SSDEEP: | 96:rurMOqFA44XI+XoxYWgM82Z1wcf4YXCaeP:lRFA44YioxGMccfLXuP |
MALICIOUS
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 3892)
Application was dropped or rewritten from another process
- qwertyuhgfdsadfghgf.exe (PID: 656)
- qwertyuhgfdsadfghgf.exe (PID: 3232)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3892)
AGENTTESLA was detected
- qwertyuhgfdsadfghgf.exe (PID: 3232)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2232)
Uses Task Scheduler to run other applications
- qwertyuhgfdsadfghgf.exe (PID: 656)
Actions looks like stealing of personal data
- qwertyuhgfdsadfghgf.exe (PID: 3232)
SUSPICIOUS
Executed via COM
- EQNEDT32.EXE (PID: 3892)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 3892)
- qwertyuhgfdsadfghgf.exe (PID: 656)
Creates files in the user directory
- EQNEDT32.EXE (PID: 3892)
- qwertyuhgfdsadfghgf.exe (PID: 3232)
- qwertyuhgfdsadfghgf.exe (PID: 656)
Reads the cookies of Mozilla Firefox
- qwertyuhgfdsadfghgf.exe (PID: 3232)
Reads the cookies of Google Chrome
- qwertyuhgfdsadfghgf.exe (PID: 3232)
Reads Internet Cache Settings
- qwertyuhgfdsadfghgf.exe (PID: 3232)
Application launched itself
- qwertyuhgfdsadfghgf.exe (PID: 656)
Checks for external IP
- qwertyuhgfdsadfghgf.exe (PID: 3232)
Connects to SMTP port
- qwertyuhgfdsadfghgf.exe (PID: 3232)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2396)
Creates files in the user directory
- WINWORD.EXE (PID: 2396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
41
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 656 | "C:\Users\admin\AppData\Roaming\qwertyuhgfdsadfghgf.exe" | C:\Users\admin\AppData\Roaming\qwertyuhgfdsadfghgf.exe | EQNEDT32.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Pig Dice Game Exit code: 0 Version: 1.8.8.8 Modules
| |||||||||||||||
| 2232 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\bHPiviWSjdH" /XML "C:\Users\admin\AppData\Local\Temp\tmp9214.tmp" | C:\Windows\System32\schtasks.exe | — | qwertyuhgfdsadfghgf.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\a.doc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3232 | "C:\Users\admin\AppData\Roaming\qwertyuhgfdsadfghgf.exe" | C:\Users\admin\AppData\Roaming\qwertyuhgfdsadfghgf.exe | qwertyuhgfdsadfghgf.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Pig Dice Game Exit code: 0 Version: 1.8.8.8 Modules
| |||||||||||||||
| 3892 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
Total events
1 734
Read events
1 009
Write events
598
Delete events
127
Modification events
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 60c |
Value: 363063005C090000010000000000000000000000 | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2396) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2396 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA4B6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 656 | qwertyuhgfdsadfghgf.exe | C:\Users\admin\AppData\Local\Temp\tmp9214.tmp | — | |
MD5:— | SHA256:— | |||
| 3232 | qwertyuhgfdsadfghgf.exe | C:\Users\admin\AppData\Roaming\o5f3cvvw.fnh\Chrome\Default\Cookies | — | |
MD5:— | SHA256:— | |||
| 3232 | qwertyuhgfdsadfghgf.exe | C:\Users\admin\AppData\Roaming\o5f3cvvw.fnh\Firefox\Profiles\qldyz51w.default\cookies.sqlite | — | |
MD5:— | SHA256:— | |||
| 3892 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\qwertyuhgfdsadfghgf.exe | executable | |
MD5:— | SHA256:— | |||
| 2396 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 656 | qwertyuhgfdsadfghgf.exe | C:\Users\admin\AppData\Roaming\bHPiviWSjdH.exe | executable | |
MD5:— | SHA256:— | |||
| 3232 | qwertyuhgfdsadfghgf.exe | C:\Users\admin\AppData\Roaming\o5f3cvvw.fnh.zip | compressed | |
MD5:— | SHA256:— | |||
| 2396 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$a.doc.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3232 | qwertyuhgfdsadfghgf.exe | C:\Users\admin\AppData\Local\Temp\637066701377218750_e7fae880-0056-42ee-a477-d2b81e5193e2.db | sqlite | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
3
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3232 | qwertyuhgfdsadfghgf.exe | GET | 200 | 18.214.132.216:80 | http://checkip.amazonaws.com/ | US | text | 13 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3892 | EQNEDT32.EXE | 112.213.89.40:443 | tfvn.com.vn | SUPERDATA | VN | malicious |
3232 | qwertyuhgfdsadfghgf.exe | 18.214.132.216:80 | checkip.amazonaws.com | — | US | shared |
3232 | qwertyuhgfdsadfghgf.exe | 198.54.122.60:587 | mail.privateemail.com | Namecheap, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tfvn.com.vn |
| unknown |
checkip.amazonaws.com |
| malicious |
mail.privateemail.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3232 | qwertyuhgfdsadfghgf.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
3 ETPRO signatures available at the full report