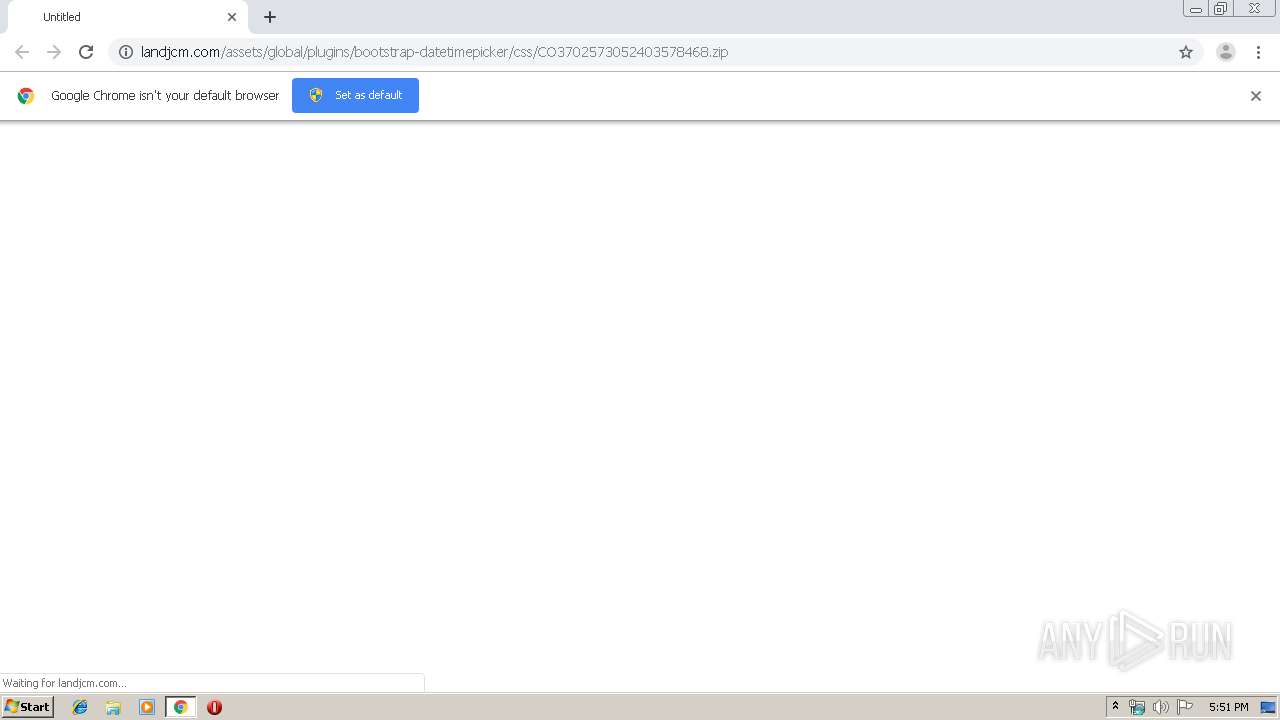
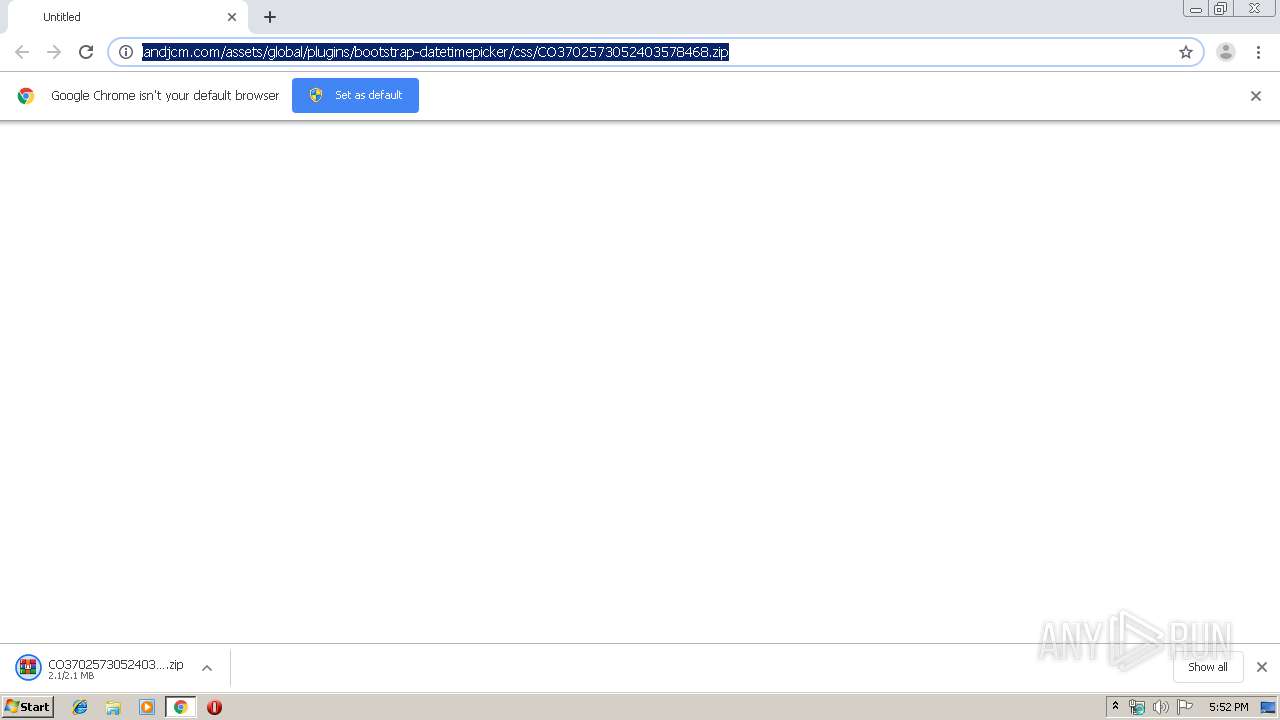
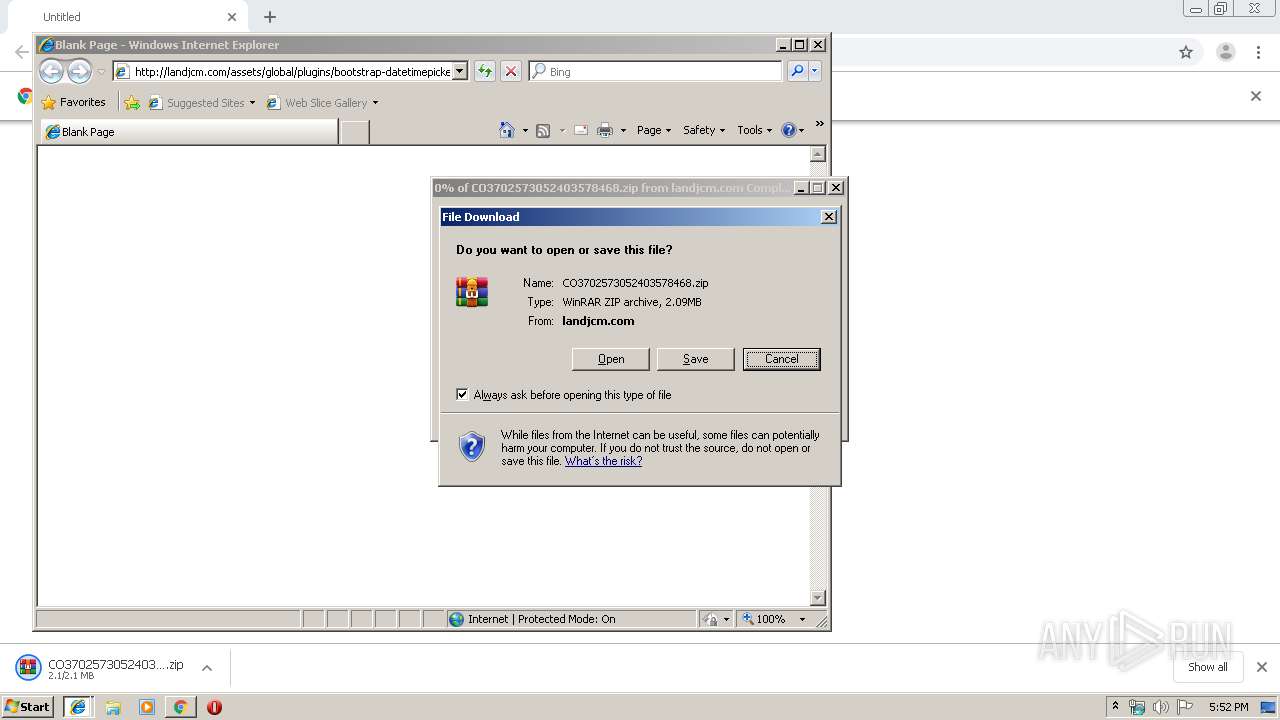
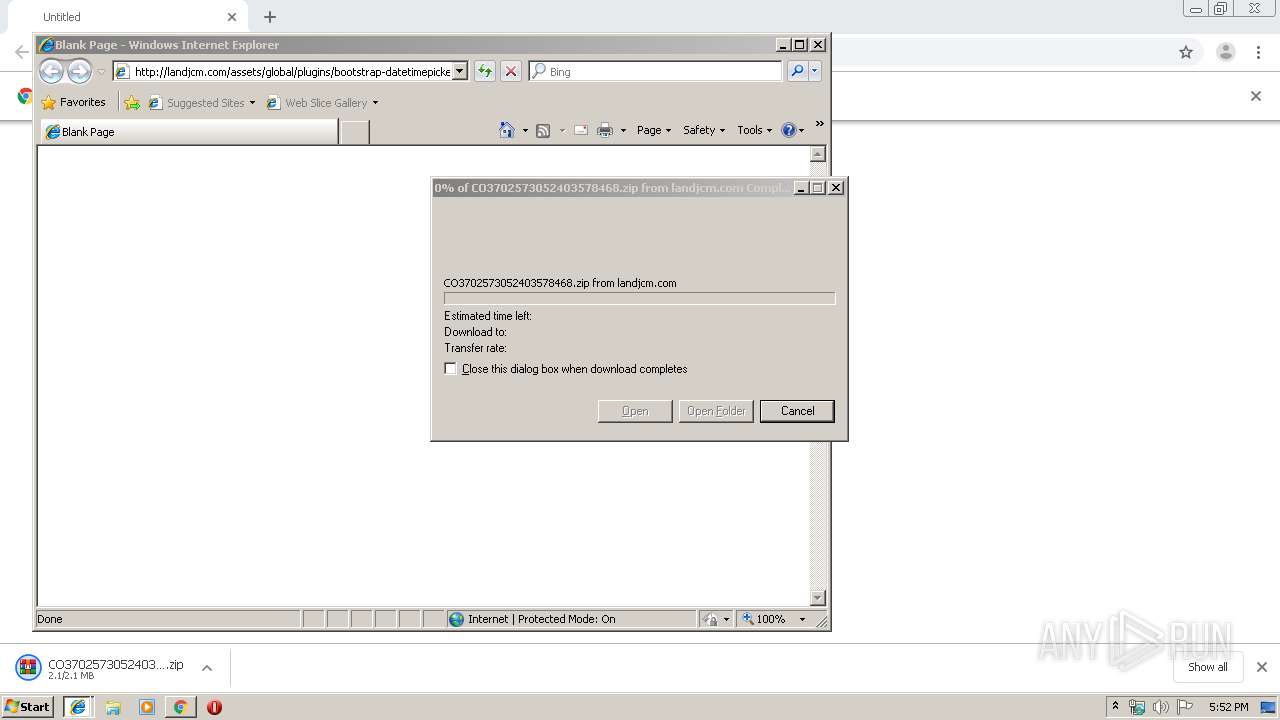
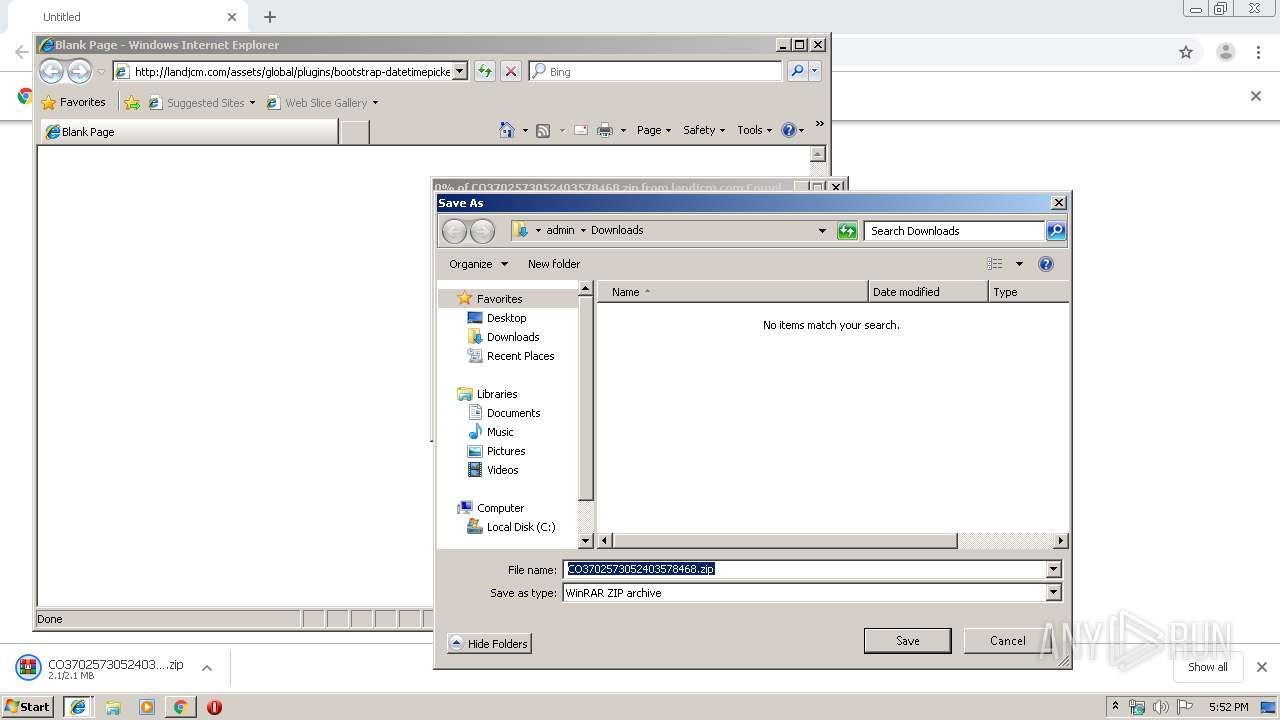
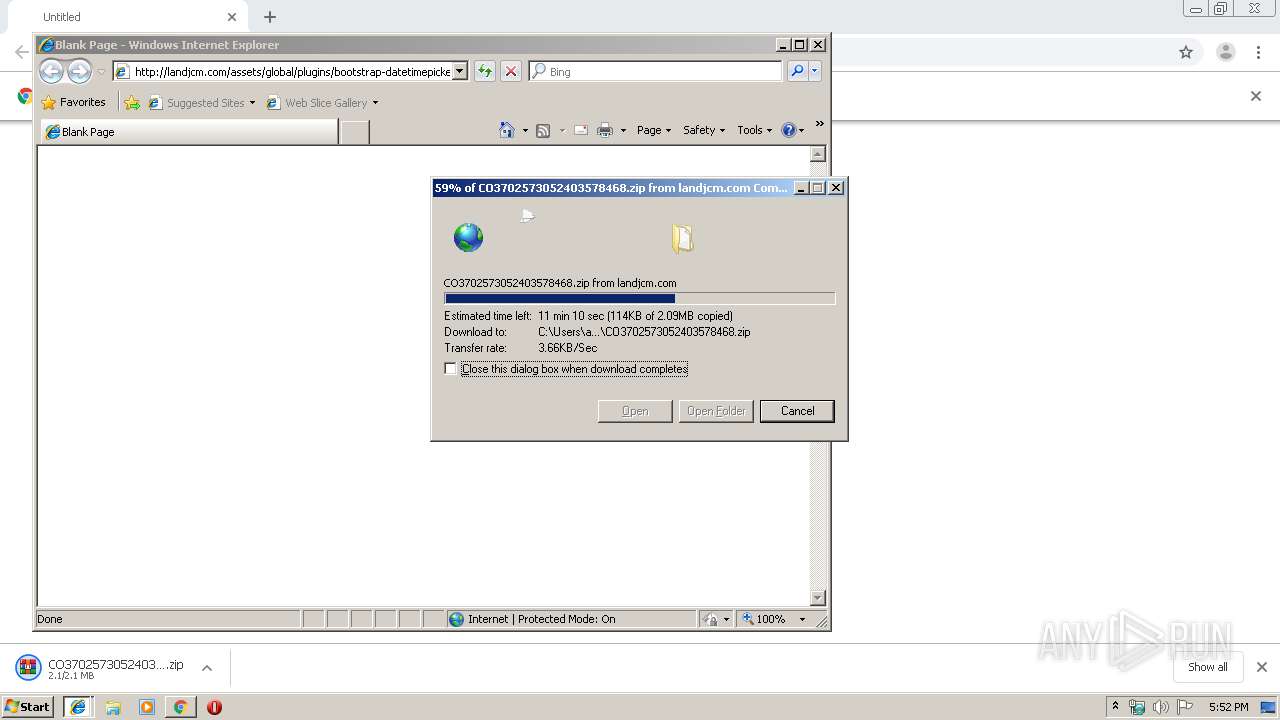
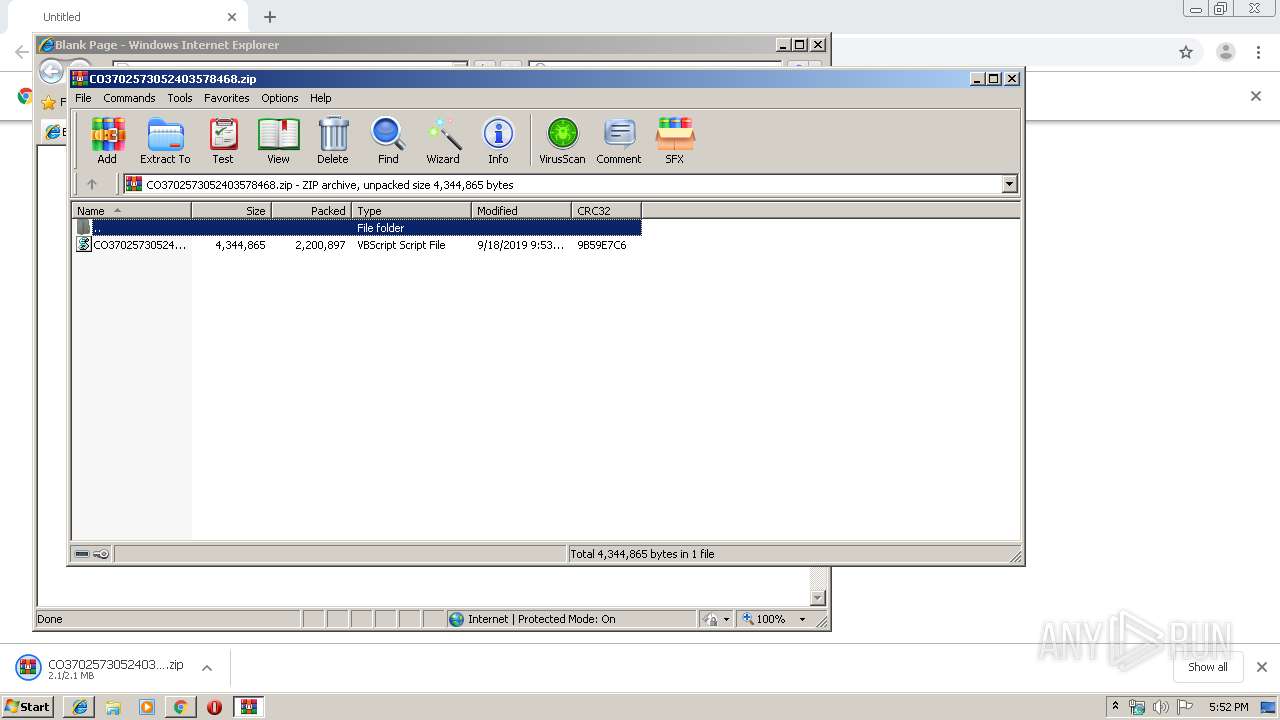
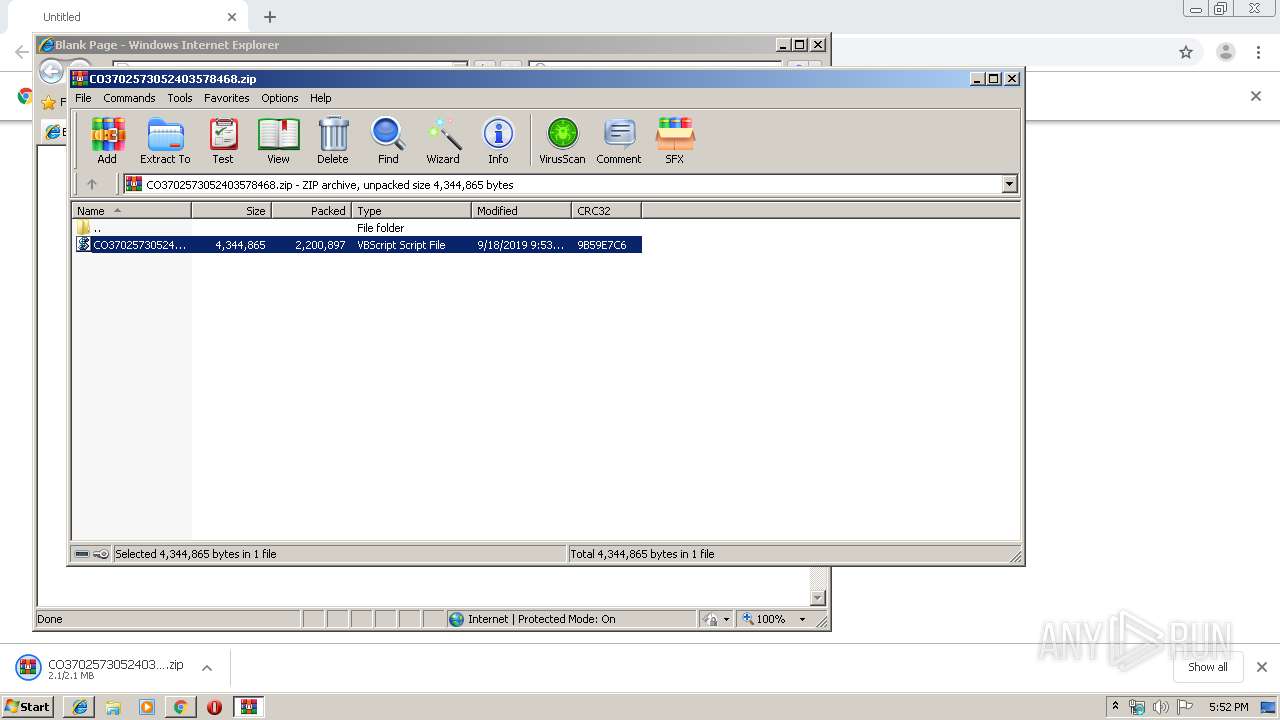
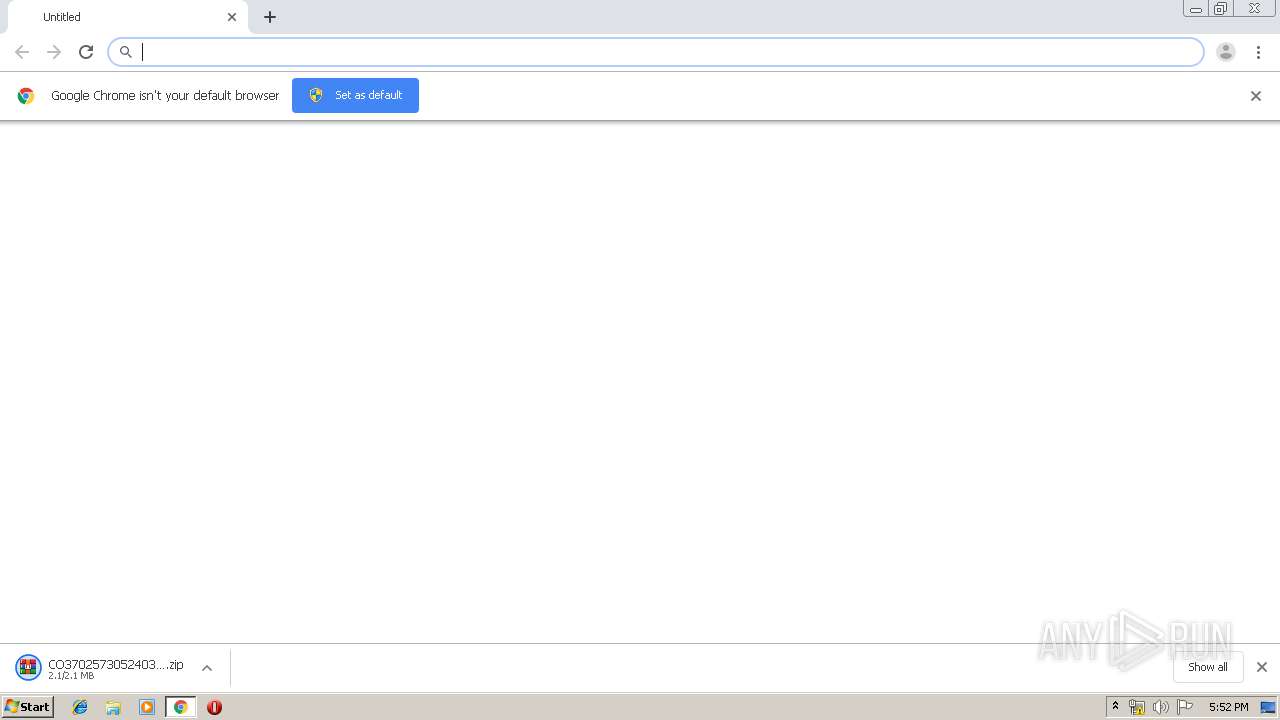
| URL: | http://landjcm.com/assets/global/plugins/bootstrap-datetimepicker/css/CO3702573052403578468.zip |
| Full analysis: | https://app.any.run/tasks/9f53d0ee-735b-42ab-acaf-18e6076d5af5 |
| Verdict: | Malicious activity |
| Threats: | Qbot is a banking Trojan — a malware designed to collect banking information from victims. Qbot targets organizations mostly in the US. It is equipped with various sophisticated evasion and info-stealing functions and worm-like functionality, and a strong persistence mechanism. |
| Analysis date: | September 18, 2019, 16:51:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DDDA5F41399ECCF4AF313ADEAA489DCA |
| SHA1: | 4EEFF6EBAA062F66973356410DACB31DB0B06AAE |
| SHA256: | A890730CCBD402A2D9B371DC93AF388B2B4DBC38C472CF05794E02D69F5A8A43 |
| SSDEEP: | 3:N1KSE13yKIJ3GKcXEiWM+ETNVPn:CSi3ZIJ3uEjcJdn |
MALICIOUS
Application was dropped or rewritten from another process
- atGFXtSZZ.exe (PID: 2500)
- ytfovlym.exe (PID: 1372)
- atGFXtSZZ.exe (PID: 3572)
- ytfovlym.exe (PID: 3616)
QBOT was detected
- atGFXtSZZ.exe (PID: 3572)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3552)
Changes the autorun value in the registry
- explorer.exe (PID: 2428)
SUSPICIOUS
Application launched itself
- atGFXtSZZ.exe (PID: 3572)
- ytfovlym.exe (PID: 1372)
Executes scripts
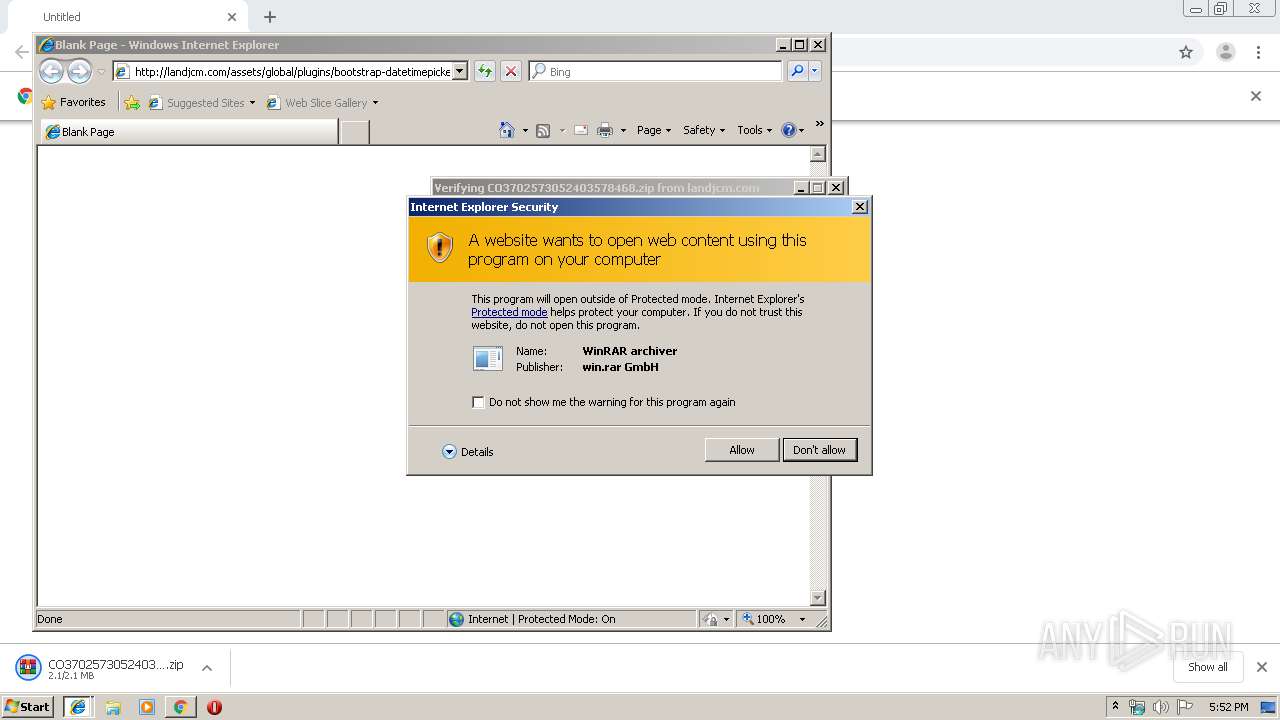
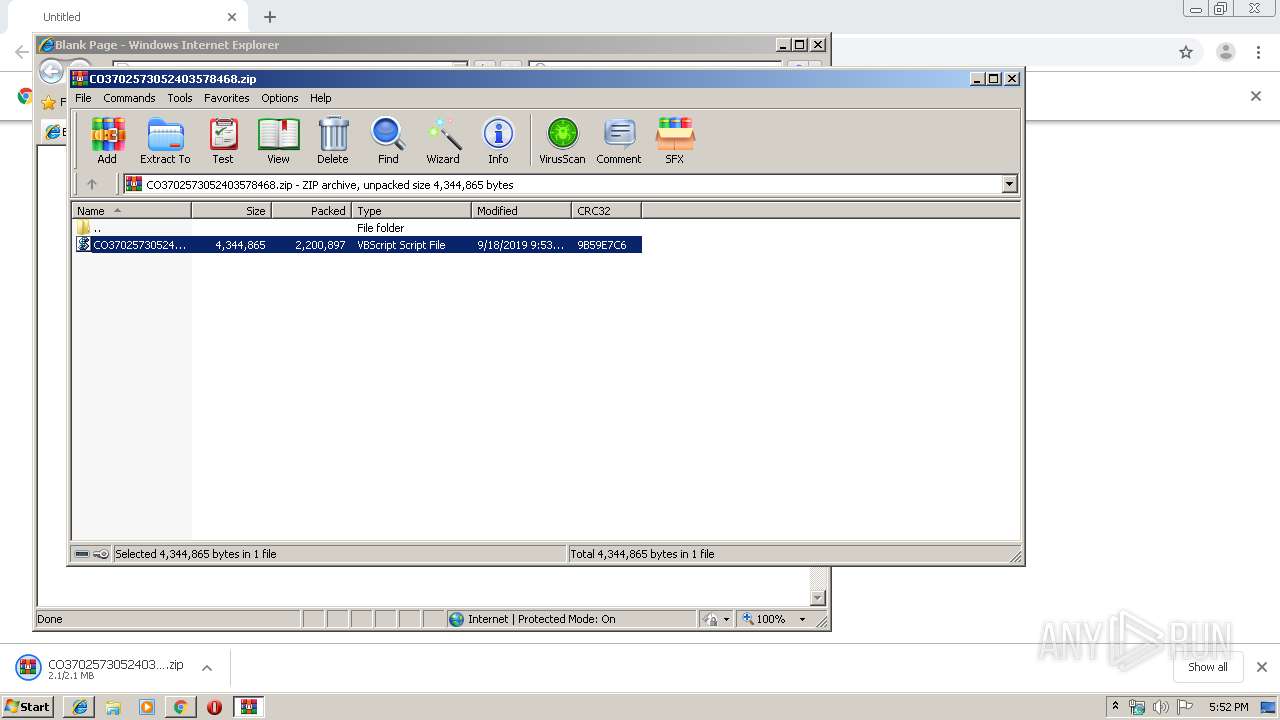
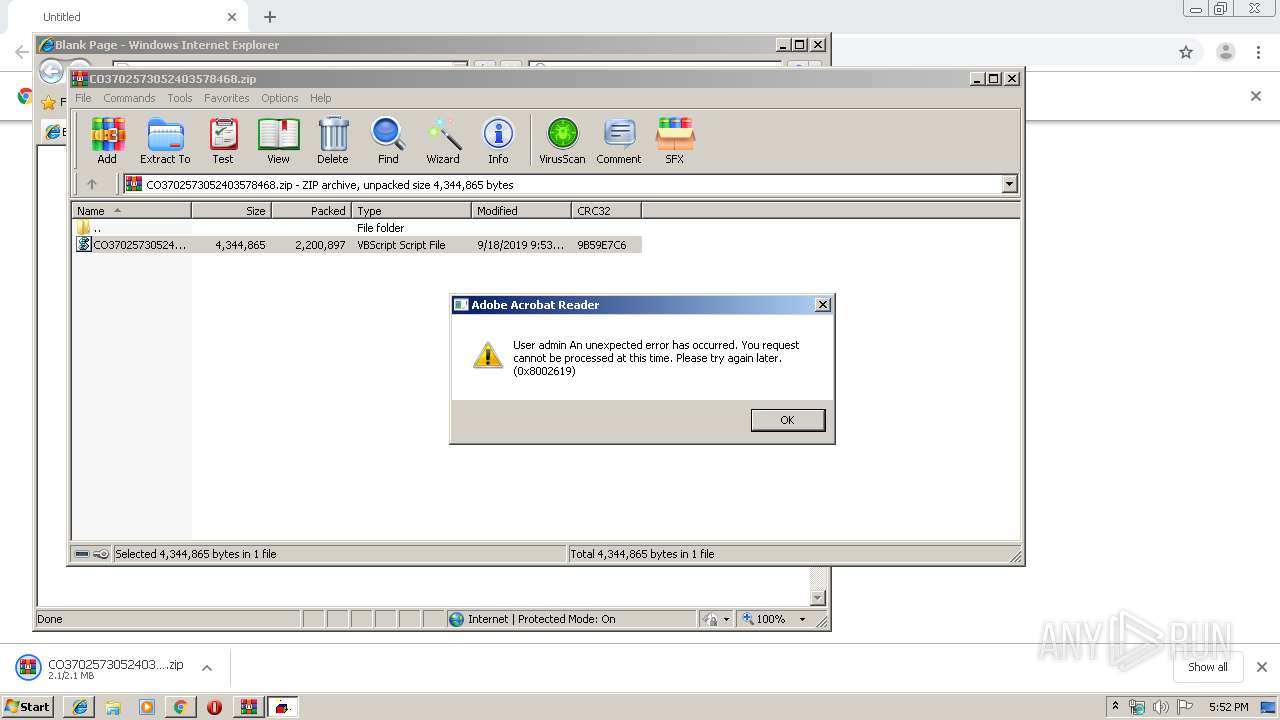
- WinRAR.exe (PID: 3664)
Executable content was dropped or overwritten
- atGFXtSZZ.exe (PID: 3572)
- cmd.exe (PID: 3552)
- WScript.exe (PID: 4020)
Executed via WMI
- atGFXtSZZ.exe (PID: 3572)
Creates files in the user directory
- atGFXtSZZ.exe (PID: 3572)
Starts itself from another location
- atGFXtSZZ.exe (PID: 3572)
Starts CMD.EXE for commands execution
- atGFXtSZZ.exe (PID: 3572)
INFO
Reads the hosts file
- chrome.exe (PID: 2332)
- chrome.exe (PID: 2788)
Application launched itself
- chrome.exe (PID: 2788)
- iexplore.exe (PID: 2104)
Manual execution by user
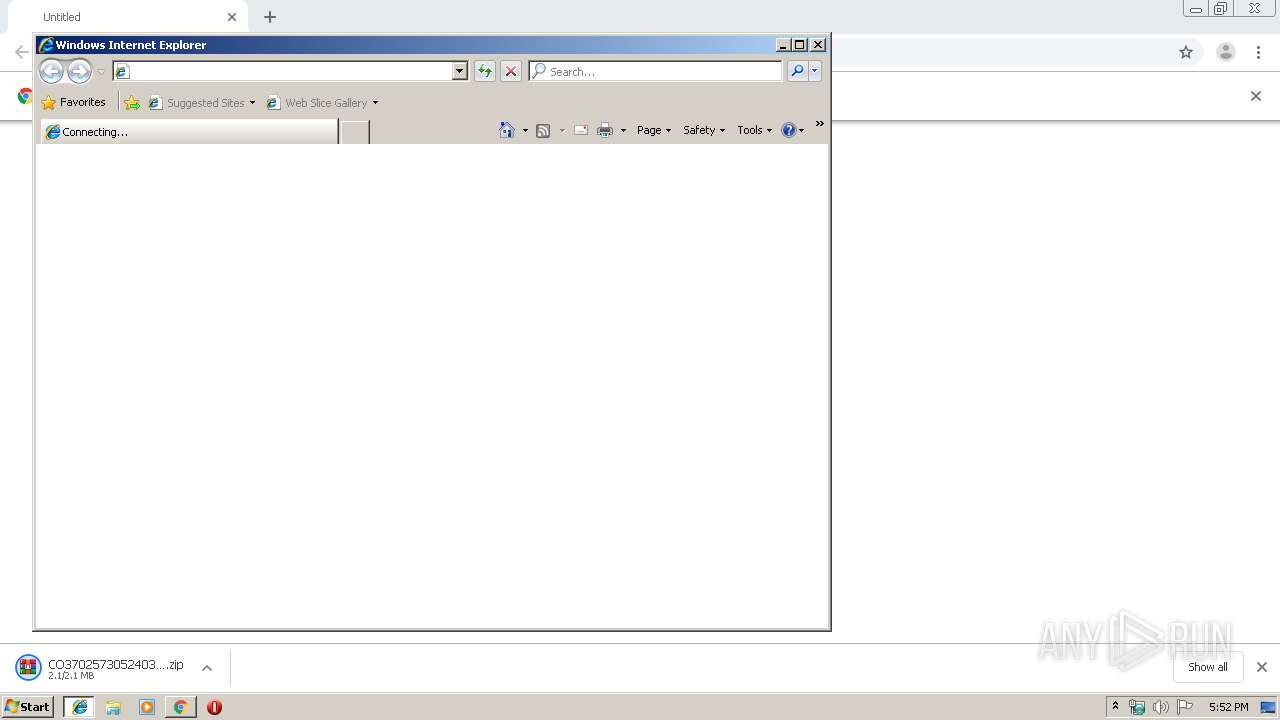
- iexplore.exe (PID: 2104)
Reads internet explorer settings
- iexplore.exe (PID: 2956)
Creates files in the user directory
- iexplore.exe (PID: 2104)
Reads Internet Cache Settings
- iexplore.exe (PID: 2104)
- iexplore.exe (PID: 2956)
Reads settings of System Certificates
- iexplore.exe (PID: 2104)
Dropped object may contain Bitcoin addresses
- cmd.exe (PID: 3552)
Changes internet zones settings
- iexplore.exe (PID: 2104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
21
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1372 | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | — | atGFXtSZZ.exe | |||||||||||
User: admin Company: Allowdone Fishbowl Inventory Integrity Level: MEDIUM Description: PlanGrass Exit code: 0 Version: 12.1.25.40 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,9780183322754742833,8464065576179346307,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13772133699621992432 --mojo-platform-channel-handle=1036 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9780183322754742833,8464065576179346307,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9774541987244639704 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,9780183322754742833,8464065576179346307,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=1047765453982124186 --mojo-platform-channel-handle=1524 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2428 | C:\Windows\explorer.exe | C:\Windows\explorer.exe | ytfovlym.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2500 | C:\Users\admin\AppData\Local\Temp\atGFXtSZZ.exe /C | C:\Users\admin\AppData\Local\Temp\atGFXtSZZ.exe | — | atGFXtSZZ.exe | |||||||||||
User: admin Company: Allowdone Fishbowl Inventory Integrity Level: MEDIUM Description: PlanGrass Exit code: 0 Version: 12.1.25.40 Modules
| |||||||||||||||
| 2684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,9780183322754742833,8464065576179346307,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=7421999620941585534 --mojo-platform-channel-handle=908 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://landjcm.com/assets/global/plugins/bootstrap-datetimepicker/css/CO3702573052403578468.zip" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,9780183322754742833,8464065576179346307,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7167151758074346518 --mojo-platform-channel-handle=3324 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 734
Read events
2 544
Write events
183
Delete events
7
Modification events
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2788-13213299111268625 |
Value: 259 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
3
Suspicious files
33
Text files
93
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\31932d21-17b5-4989-a305-e55c19975ac7.tmp | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF169d3e.TMP | text | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169d2f.TMP | text | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169d3e.TMP | text | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
14
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2332 | chrome.exe | GET | 200 | 70.35.199.191:80 | http://landjcm.com/assets/global/plugins/bootstrap-datetimepicker/css/CO3702573052403578468.zip | US | compressed | 2.10 Mb | unknown |
2956 | iexplore.exe | GET | 200 | 70.35.199.191:80 | http://landjcm.com/assets/global/plugins/bootstrap-datetimepicker/css/CO3702573052403578468.zip | US | compressed | 2.10 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2332 | chrome.exe | 70.35.199.191:80 | landjcm.com | 1&1 Internet SE | US | unknown |
2332 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2332 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2332 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
2332 | chrome.exe | 172.217.16.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2332 | chrome.exe | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2104 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2332 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2956 | iexplore.exe | 70.35.199.191:80 | landjcm.com | 1&1 Internet SE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
landjcm.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
www.google.com.ua |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google.lt |
| whitelisted |
www.gstatic.com |
| whitelisted |