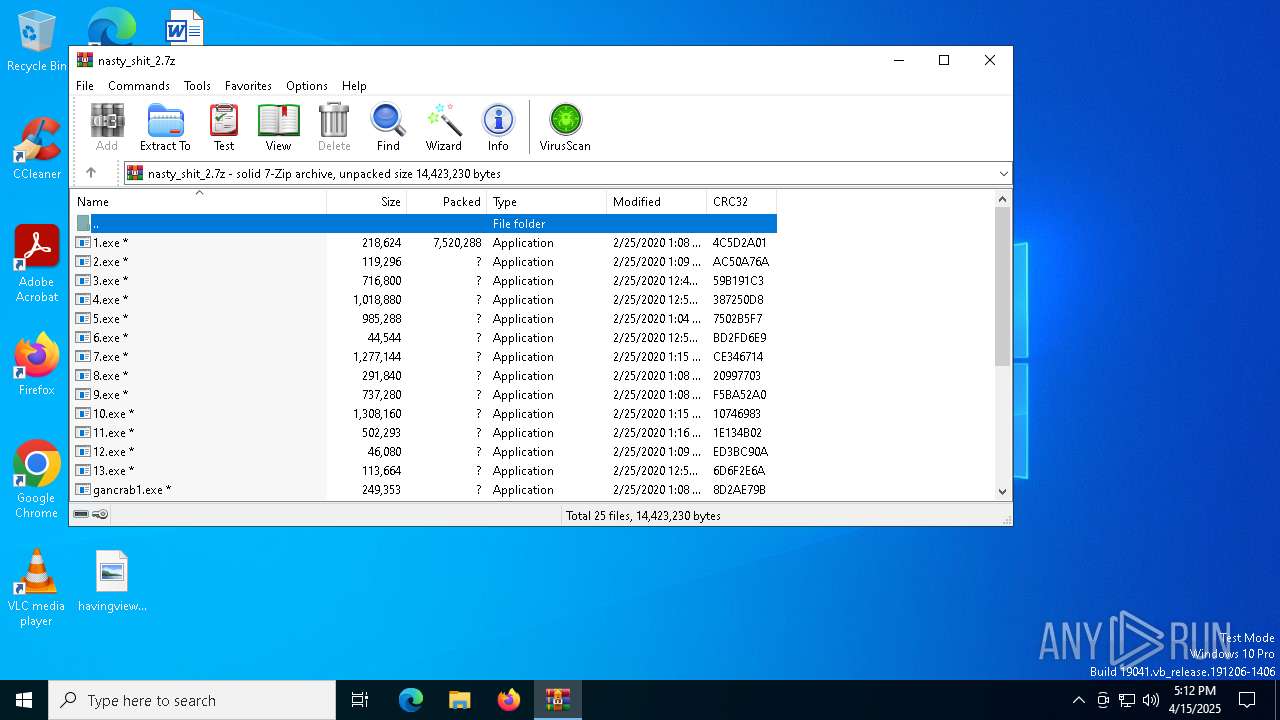
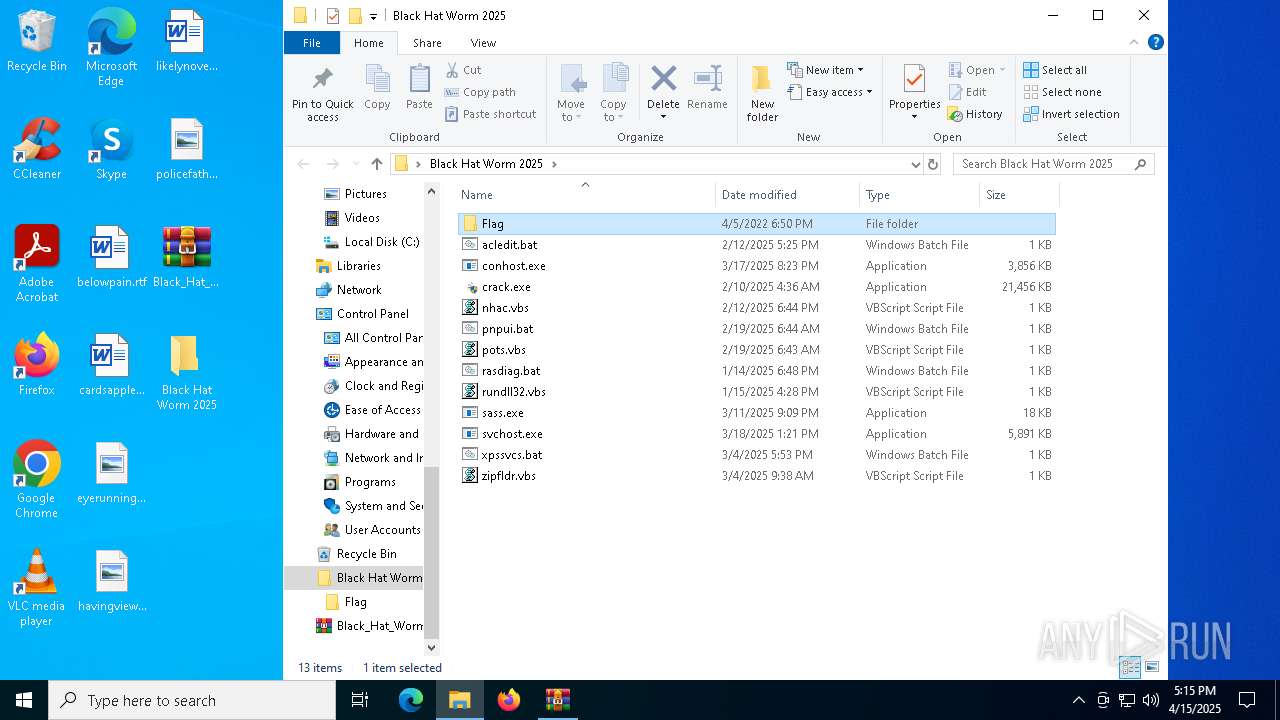
| File name: | nasty_shit_2.7z |
| Full analysis: | https://app.any.run/tasks/2c37581d-17c7-4b7b-987e-efd26c39c309 |
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | April 15, 2025, 17:12:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | E44D25E590037C894FA9872FD7FA0299 |
| SHA1: | 2BDBA16FD29D3A44E2D789A4CCBF572C02729DCF |
| SHA256: | A8836A0BD7365780264C0E25590769F9A48A55AF22E0694B0E2C42C18C73418C |
| SSDEEP: | 98304:VIwijDsZVfTotRn9tzAiE/ZTPR6olCDEABjv7oxvauUXkObZXoFkSQMq1cObAFzK:Jptb2x/zmZL37ncrL+E |
MALICIOUS
Create files in the Startup directory
- sass.exe (PID: 5024)
- conhost.exe (PID: 5136)
- Built.exe (PID: 7208)
Executing a file with an untrusted certificate
- Built.exe (PID: 3760)
- Built.exe (PID: 7208)
XMRig has been detected
- OmegaEngine.exe (PID: 2616)
BlankGrabber has been detected
- Built.exe (PID: 3760)
Connects to the CnC server
- OmegaEngine.exe (PID: 2616)
MINER has been detected (SURICATA)
- OmegaEngine.exe (PID: 2616)
- svchost.exe (PID: 2196)
Adds path to the Windows Defender exclusion list
- Built.exe (PID: 7208)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7544)
Changes Windows Defender settings
- cmd.exe (PID: 7400)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7544)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 7500)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 7500)
Changes Controlled Folder Access settings
- powershell.exe (PID: 7500)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 7400)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 7500)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 7500)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 7500)
Changes settings for real-time protection
- powershell.exe (PID: 7500)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 8084)
Changes the autorun value in the registry
- conhost.exe (PID: 8172)
Vulnerable driver has been detected
- svchost.exe (PID: 728)
SUSPICIOUS
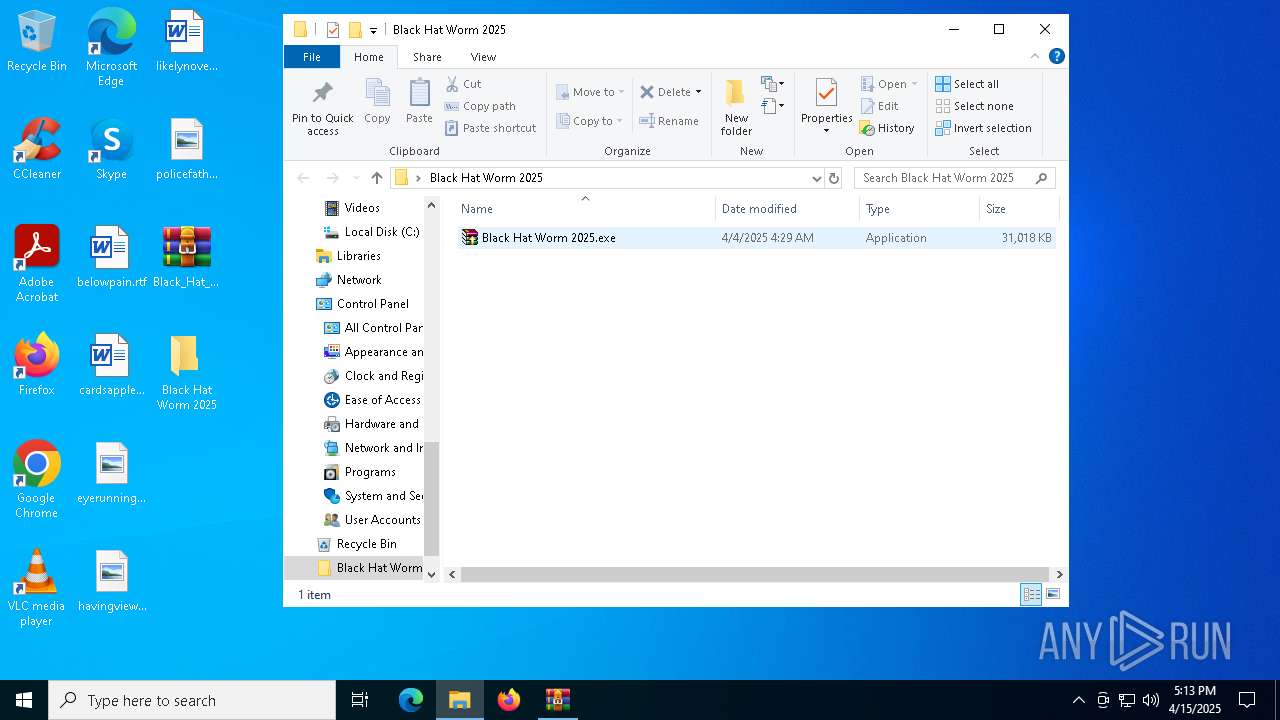
Reads Microsoft Outlook installation path
- Black Hat Worm 2025.exe (PID: 5400)
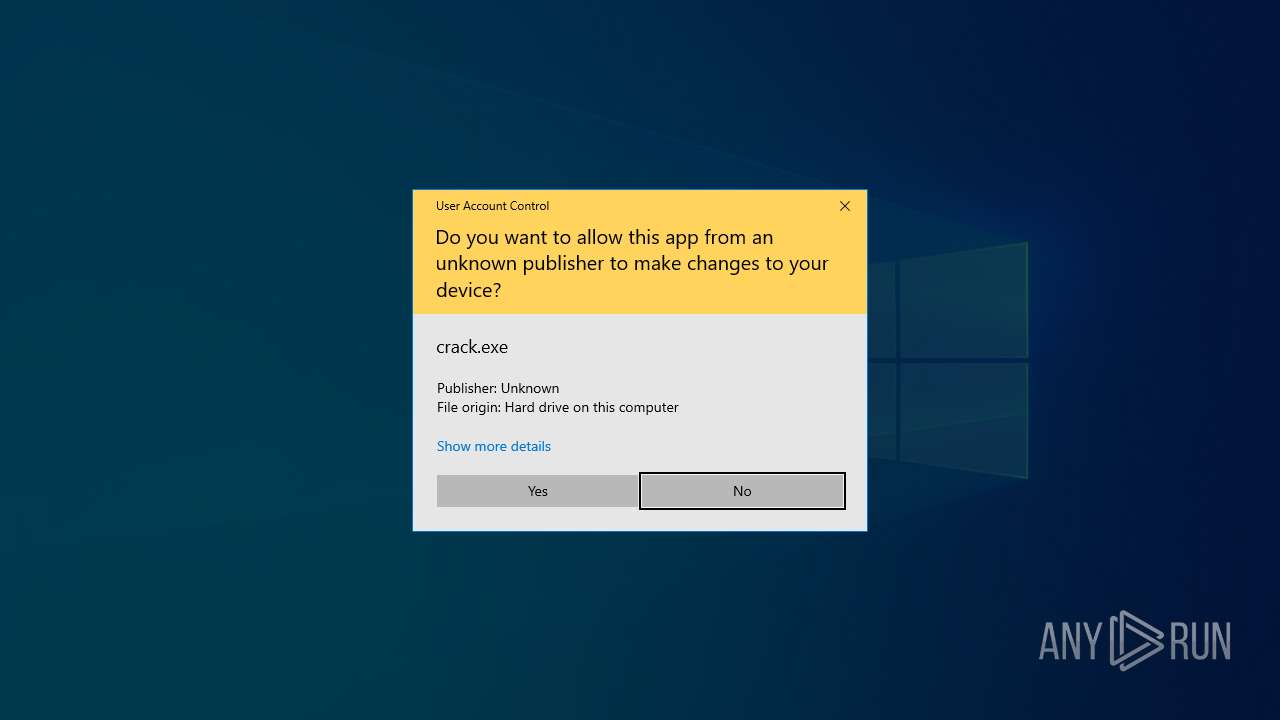
Reads security settings of Internet Explorer
- Black Hat Worm 2025.exe (PID: 5400)
- crack.exe (PID: 4784)
- svchost.exe (PID: 728)
- svchost.exe (PID: 4112)
Reads Internet Explorer settings
- Black Hat Worm 2025.exe (PID: 5400)
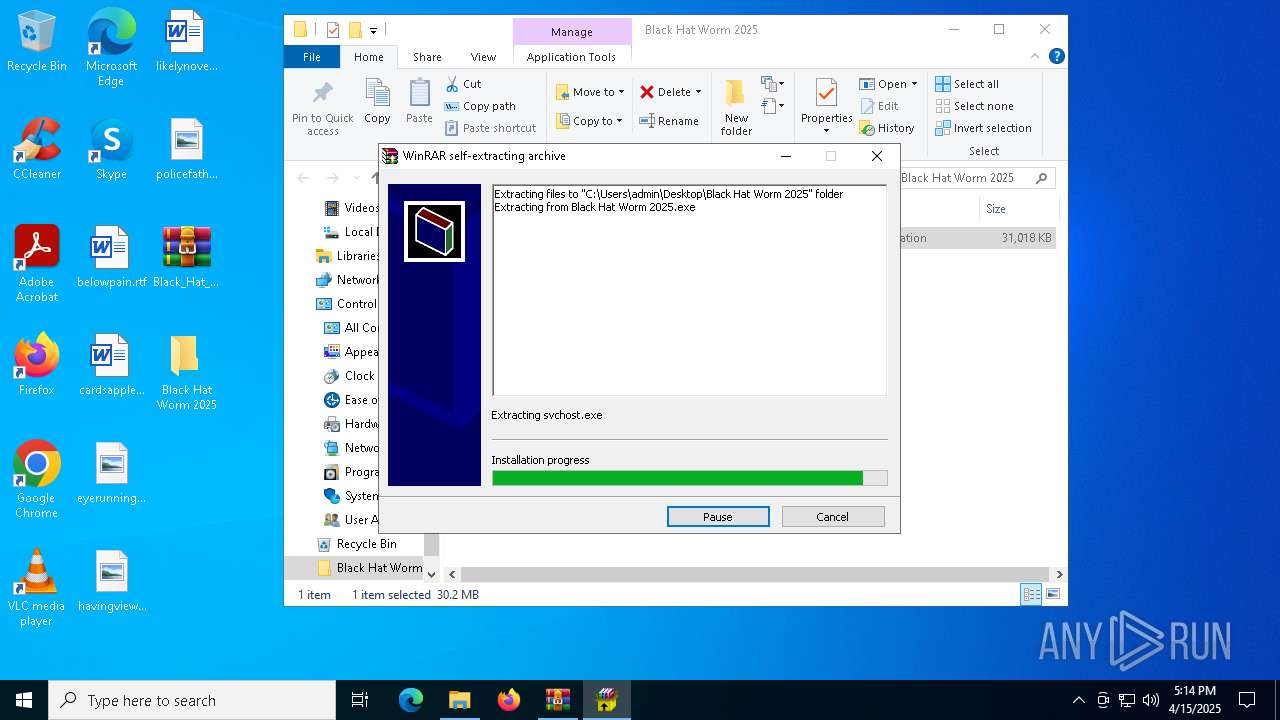
Executable content was dropped or overwritten
- Black Hat Worm 2025.exe (PID: 5400)
- sass.exe (PID: 5024)
- svchost.exe (PID: 4112)
- conhost.exe (PID: 5136)
- crack.exe (PID: 4784)
- Built.exe (PID: 3760)
- conhost.exe (PID: 856)
- svchost.exe (PID: 728)
- Built.exe (PID: 7208)
- conhost.exe (PID: 8172)
The process executes VB scripts
- Black Hat Worm 2025.exe (PID: 5400)
The process creates files with name similar to system file names
- Black Hat Worm 2025.exe (PID: 5400)
- crack.exe (PID: 4784)
- conhost.exe (PID: 5136)
- svchost.exe (PID: 728)
- WerFault.exe (PID: 7440)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 5344)
- wscript.exe (PID: 2616)
- wscript.exe (PID: 5376)
- wscript.exe (PID: 1168)
- Built.exe (PID: 7208)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5344)
- wscript.exe (PID: 2616)
- wscript.exe (PID: 5376)
- wscript.exe (PID: 1168)
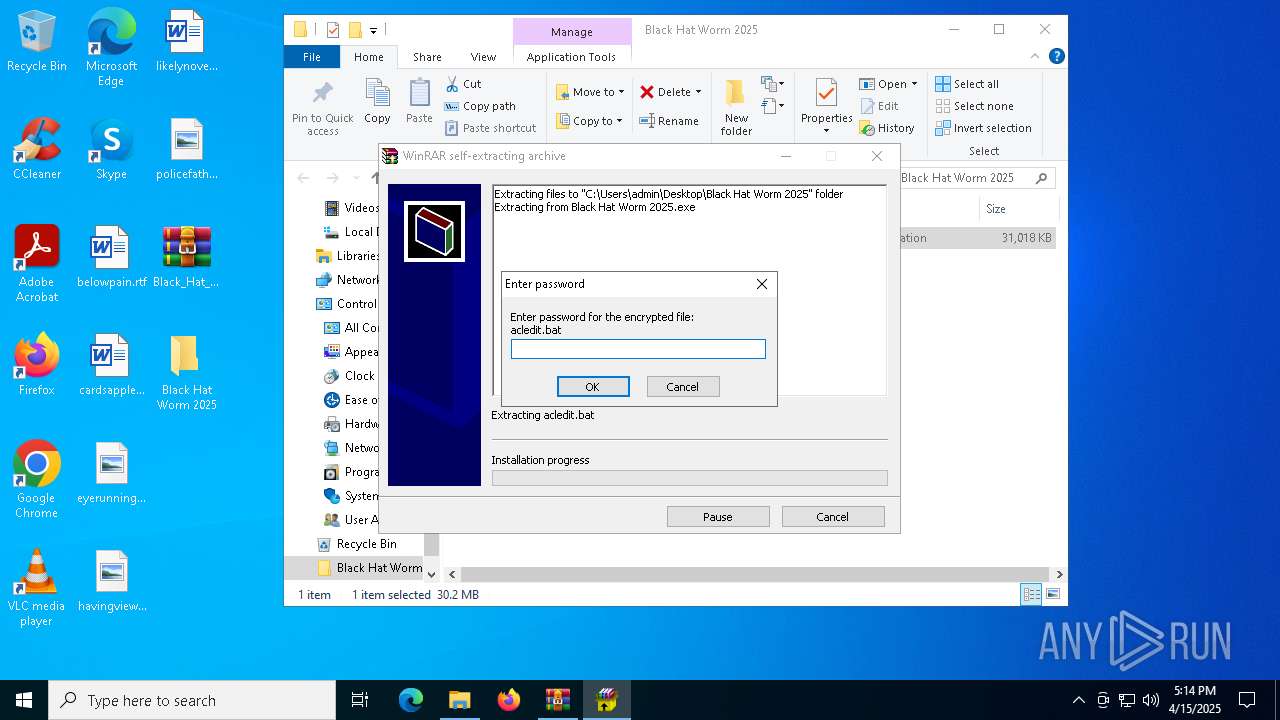
Executing commands from a ".bat" file
- wscript.exe (PID: 5376)
- wscript.exe (PID: 1168)
- wscript.exe (PID: 5344)
- wscript.exe (PID: 2616)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2284)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 3124)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7544)
Malware-specific behavior: drops SQLite library (may be used to steal credentials)
- svchost.exe (PID: 4112)
Downloads file from URI via Powershell
- powershell.exe (PID: 6392)
- powershell.exe (PID: 4284)
- powershell.exe (PID: 5036)
- powershell.exe (PID: 4920)
Process drops legitimate windows executable
- crack.exe (PID: 4784)
- conhost.exe (PID: 856)
- Built.exe (PID: 3760)
- Built.exe (PID: 7208)
Checks for external IP
- svchost.exe (PID: 2196)
- svchost.exe (PID: 4112)
- Update.exe (PID: 7352)
- conhost.exe (PID: 8172)
Starts a Microsoft application from unusual location
- Built.exe (PID: 3760)
- Built.exe (PID: 7208)
The process drops C-runtime libraries
- Built.exe (PID: 3760)
- conhost.exe (PID: 856)
Process drops python dynamic module
- Built.exe (PID: 3760)
- conhost.exe (PID: 856)
Reads the date of Windows installation
- svchost.exe (PID: 728)
- svchost.exe (PID: 4112)
Drops a system driver (possible attempt to evade defenses)
- svchost.exe (PID: 728)
Executes application which crashes
- InstallUtil.exe (PID: 5756)
- svchost.exe (PID: 7280)
Potential Corporate Privacy Violation
- OmegaEngine.exe (PID: 2616)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2196)
Application launched itself
- Built.exe (PID: 3760)
- conhost.exe (PID: 856)
The executable file from the user directory is run by the CMD process
- svchost.exe (PID: 7280)
Starts itself from another location
- svchost.exe (PID: 4112)
Found strings related to reading or modifying Windows Defender settings
- Built.exe (PID: 7208)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 7400)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7544)
Script disables Windows Defender's IPS
- cmd.exe (PID: 7400)
Found regular expressions for crypto-addresses (YARA)
- sass.exe (PID: 5024)
Loads Python modules
- conhost.exe (PID: 8172)
INFO
Reads the software policy settings
- slui.exe (PID: 1324)
- svchost.exe (PID: 4112)
- Update.exe (PID: 7352)
- slui.exe (PID: 4724)
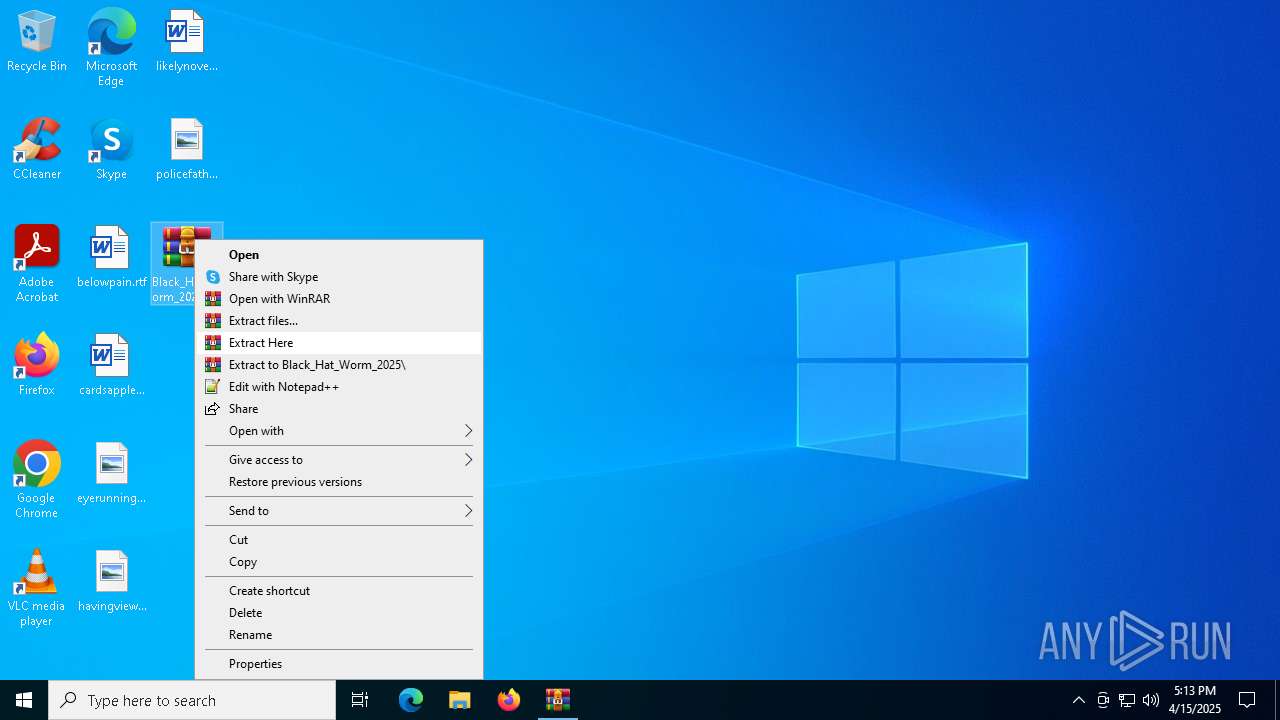
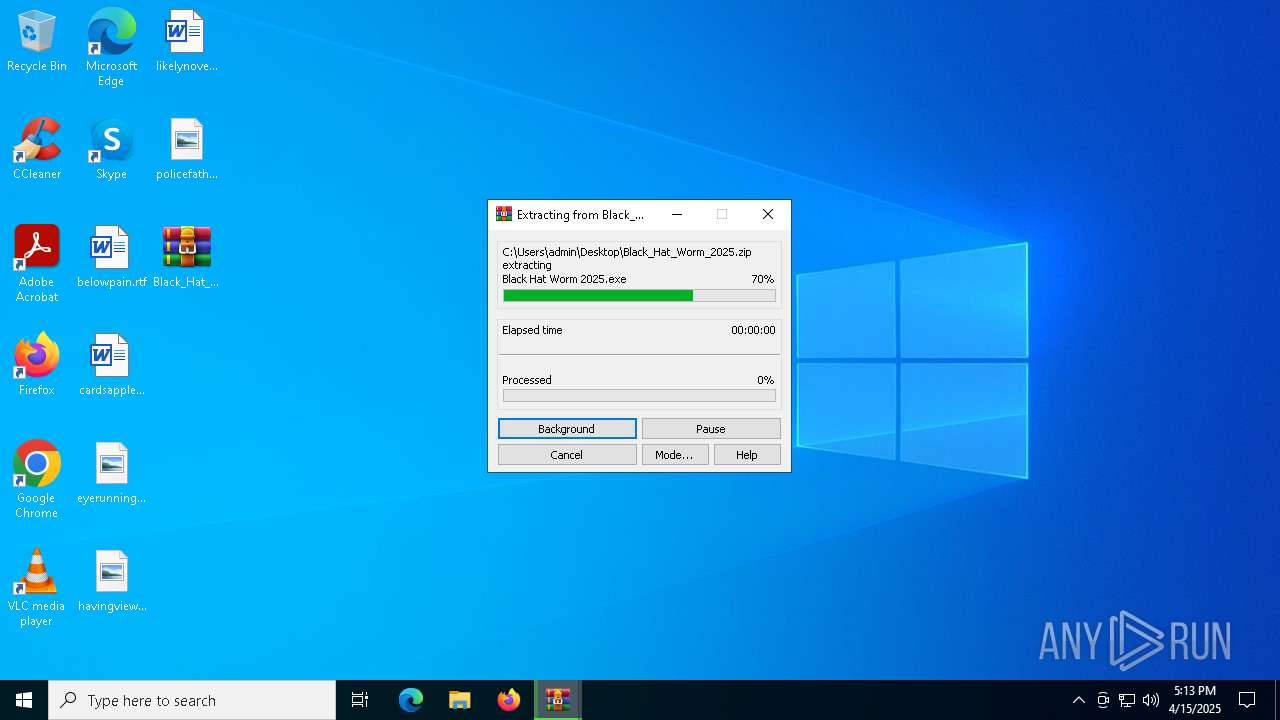
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6132)
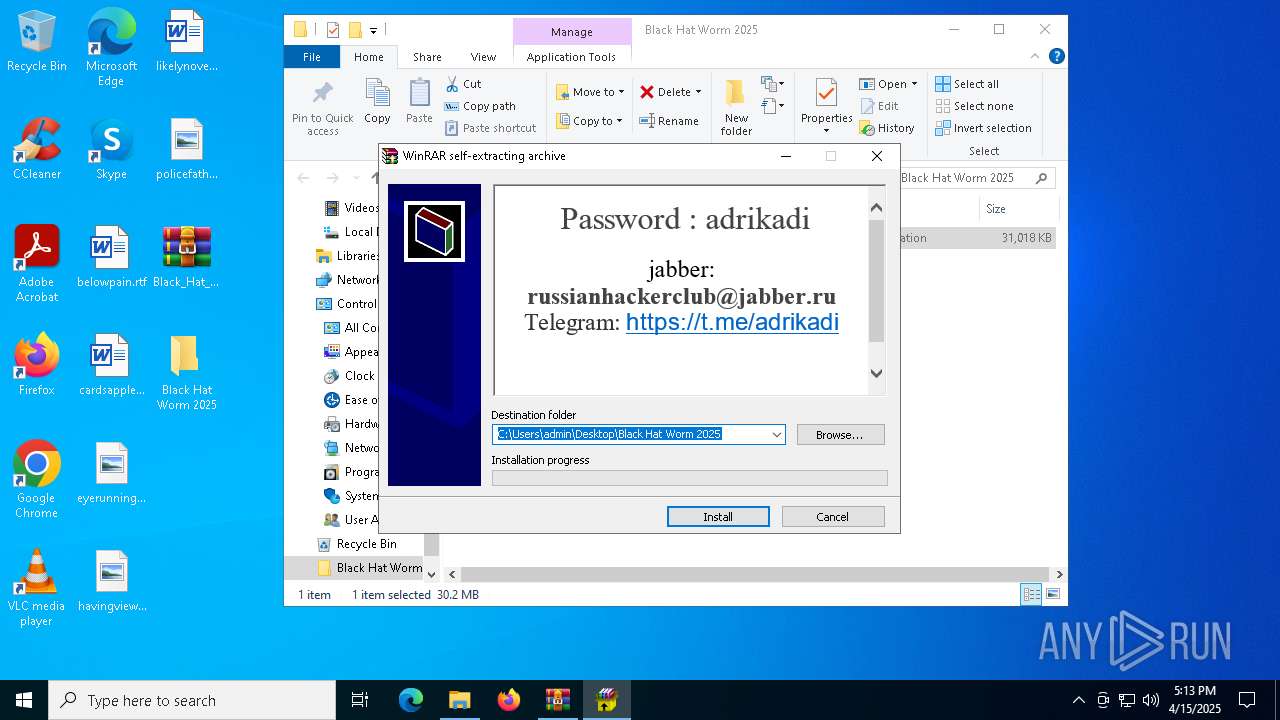
Manual execution by a user
- Black Hat Worm 2025.exe (PID: 5400)
- WinRAR.exe (PID: 6132)
- InstallUtil.exe (PID: 5756)
Checks supported languages
- Black Hat Worm 2025.exe (PID: 5400)
- sass.exe (PID: 5024)
- svchost.exe (PID: 4112)
- conhost.exe (PID: 5136)
- crack.exe (PID: 4784)
- conhost.exe (PID: 856)
- svchost.exe (PID: 728)
- InstallUtil.exe (PID: 5756)
- OmegaEngine.exe (PID: 2616)
- Built.exe (PID: 7208)
- svchost.exe (PID: 7280)
- Update.exe (PID: 7352)
- MpCmdRun.exe (PID: 8084)
- conhost.exe (PID: 8172)
Reads the computer name
- Black Hat Worm 2025.exe (PID: 5400)
- sass.exe (PID: 5024)
- svchost.exe (PID: 4112)
- conhost.exe (PID: 5136)
- crack.exe (PID: 4784)
- conhost.exe (PID: 856)
- svchost.exe (PID: 728)
- InstallUtil.exe (PID: 5756)
- OmegaEngine.exe (PID: 2616)
- svchost.exe (PID: 7280)
- Update.exe (PID: 7352)
- Built.exe (PID: 7208)
- MpCmdRun.exe (PID: 8084)
- conhost.exe (PID: 8172)
Checks proxy server information
- Black Hat Worm 2025.exe (PID: 5400)
- svchost.exe (PID: 4112)
- powershell.exe (PID: 4920)
- powershell.exe (PID: 4284)
- powershell.exe (PID: 6392)
- powershell.exe (PID: 5036)
- Update.exe (PID: 7352)
Process checks computer location settings
- Black Hat Worm 2025.exe (PID: 5400)
- crack.exe (PID: 4784)
- svchost.exe (PID: 728)
- svchost.exe (PID: 4112)
Creates files or folders in the user directory
- sass.exe (PID: 5024)
- conhost.exe (PID: 5136)
- svchost.exe (PID: 728)
- svchost.exe (PID: 4112)
- WerFault.exe (PID: 7188)
- WerFault.exe (PID: 7440)
- conhost.exe (PID: 8172)
Reads the machine GUID from the registry
- sass.exe (PID: 5024)
- conhost.exe (PID: 5136)
- svchost.exe (PID: 4112)
- Update.exe (PID: 7352)
Create files in a temporary directory
- svchost.exe (PID: 4112)
- crack.exe (PID: 4784)
- conhost.exe (PID: 856)
- Built.exe (PID: 3760)
- Built.exe (PID: 7208)
- MpCmdRun.exe (PID: 8084)
The sample compiled with english language support
- svchost.exe (PID: 4112)
- conhost.exe (PID: 856)
- Built.exe (PID: 3760)
Disables trace logs
- svchost.exe (PID: 4112)
- powershell.exe (PID: 4284)
- powershell.exe (PID: 5036)
- powershell.exe (PID: 6392)
- Update.exe (PID: 7352)
Reads Environment values
- svchost.exe (PID: 4112)
- Update.exe (PID: 7352)
The sample compiled with japanese language support
- svchost.exe (PID: 728)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6392)
- powershell.exe (PID: 4920)
- powershell.exe (PID: 4284)
- powershell.exe (PID: 5036)
- powershell.exe (PID: 7500)
- powershell.exe (PID: 7536)
- powershell.exe (PID: 7616)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 5036)
- powershell.exe (PID: 4920)
- powershell.exe (PID: 4284)
- powershell.exe (PID: 6392)
Creates files in the program directory
- Built.exe (PID: 7208)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 7536)
- powershell.exe (PID: 7500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2020:02:25 01:08:56+00:00 |
| ArchivedFileName: | 1.exe |
Total processes
183
Monitored processes
51
Malicious processes
15
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\Users\admin\AppData\Local\Temp\svchost.exe" | C:\Users\admin\AppData\Local\Temp\svchost.exe | crack.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Er minator Version: 1.0.0.0 Modules
| |||||||||||||||
| 856 | "C:\Users\admin\AppData\Local\Temp\conhost.exe" | C:\Users\admin\AppData\Local\Temp\conhost.exe | crack.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1168 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Desktop\Black Hat Worm 2025\rundll32.vbs" | C:\Windows\SysWOW64\wscript.exe | — | Black Hat Worm 2025.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | "C:\Windows\System32\cmd.exe" /c xpssvcs.bat | C:\Windows\SysWOW64\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2332 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Desktop\Black Hat Worm 2025\zipfldr.vbs" | C:\Windows\SysWOW64\wscript.exe | — | Black Hat Worm 2025.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
97 894
Read events
97 823
Write events
69
Delete events
2
Modification events
| (PID) Process: | (4212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\nasty_shit_2.7z | |||
| (PID) Process: | (4212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6132) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
134
Suspicious files
10
Text files
1 201
Unknown types
0
Dropped files
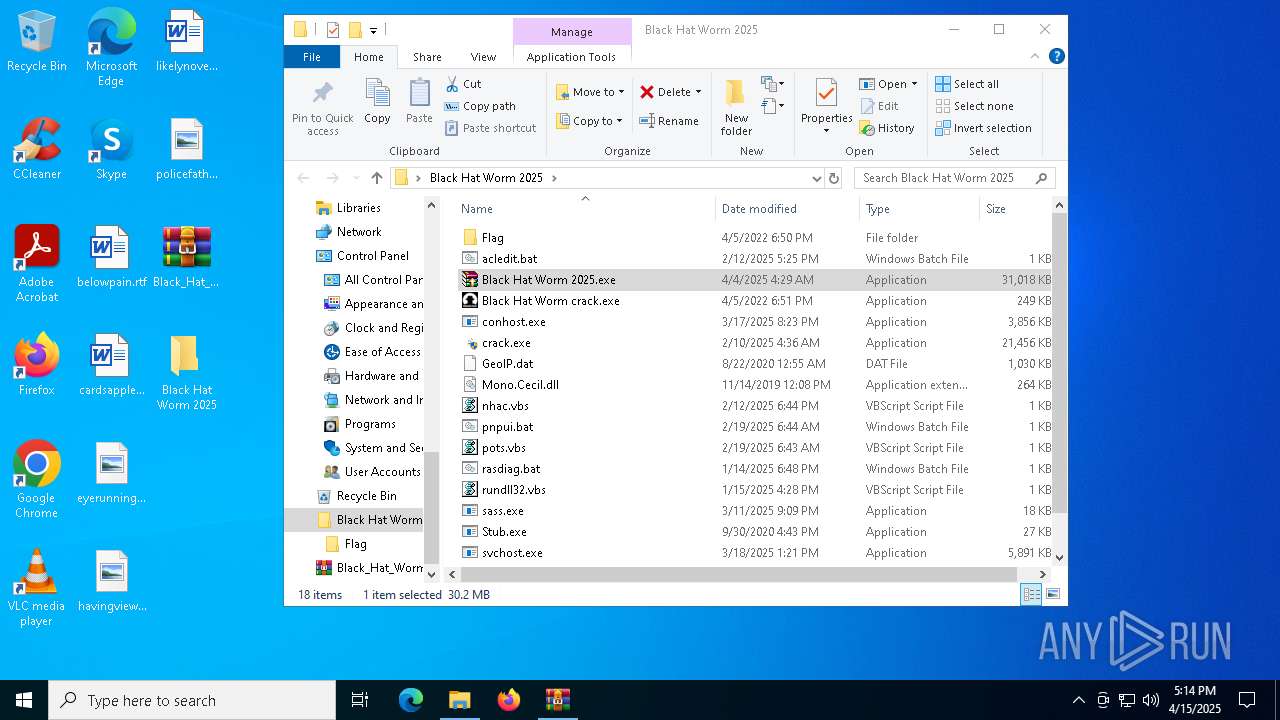
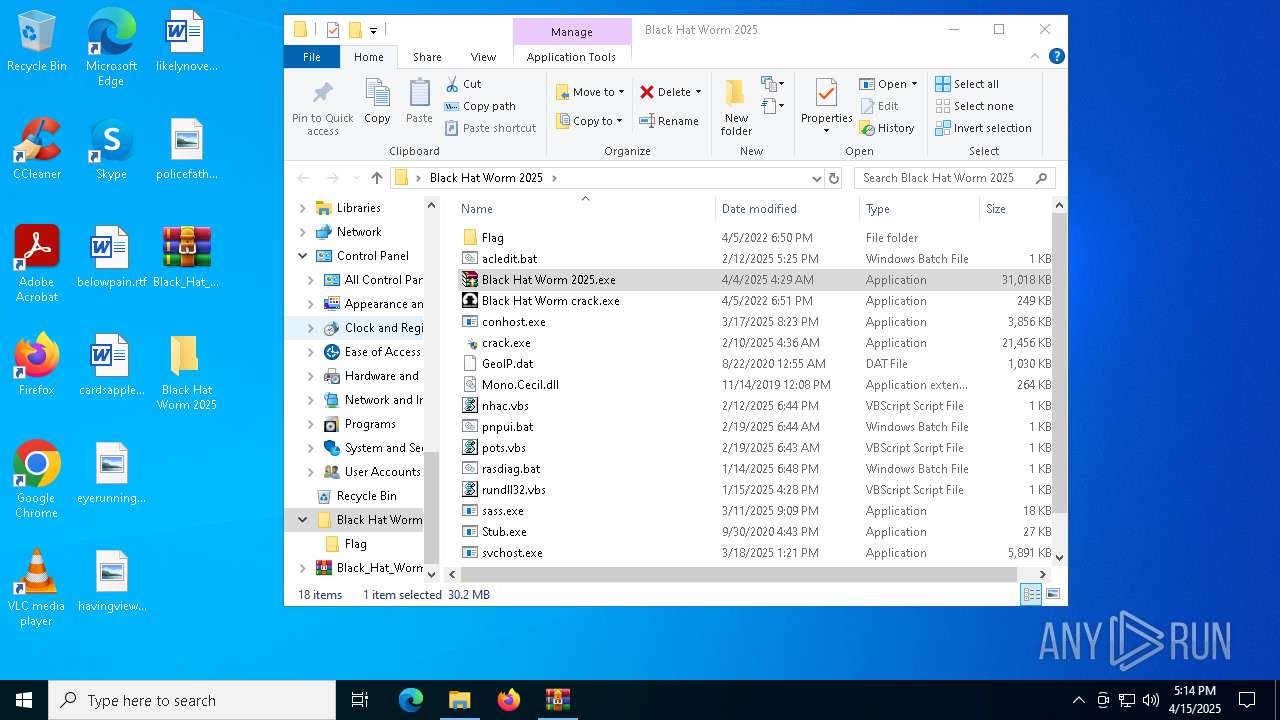
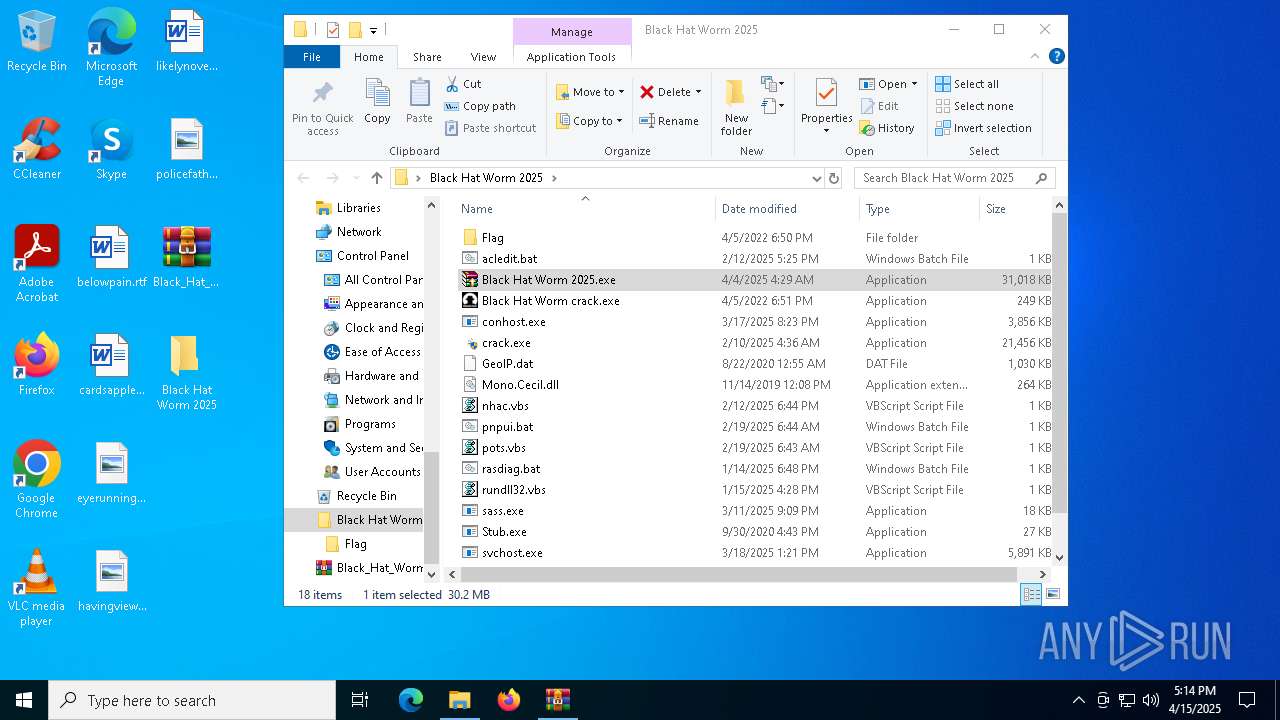
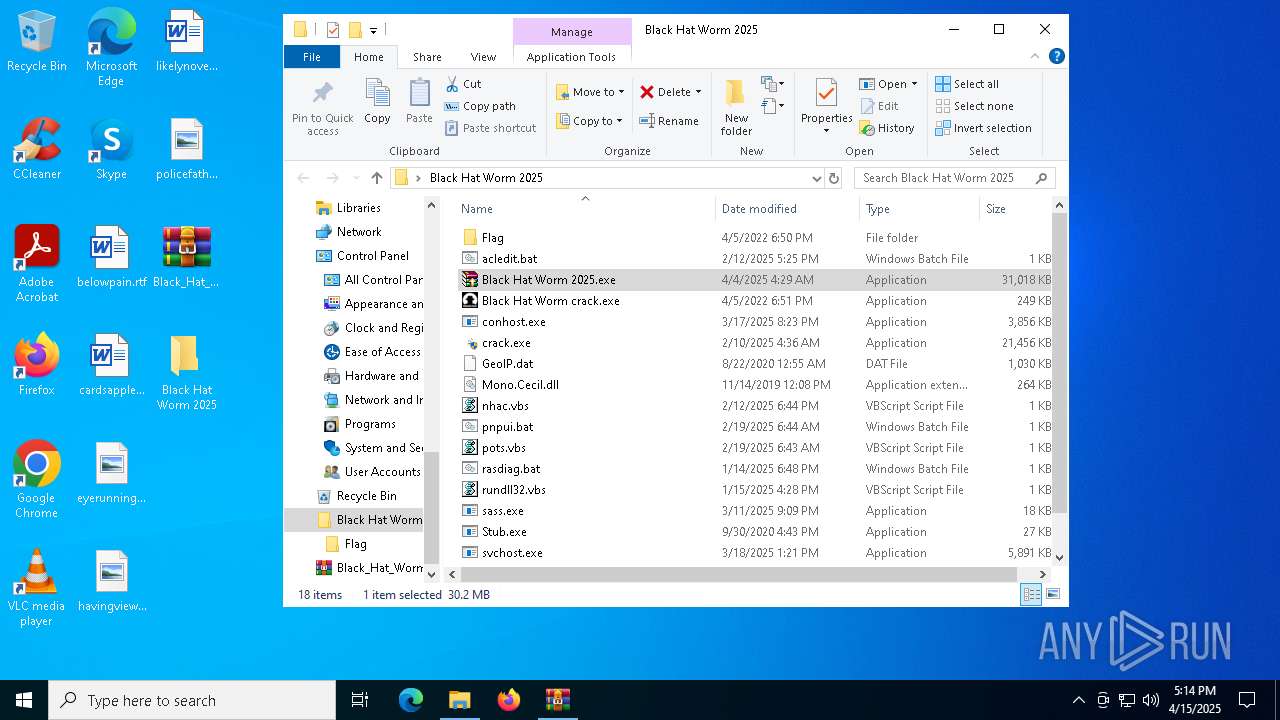
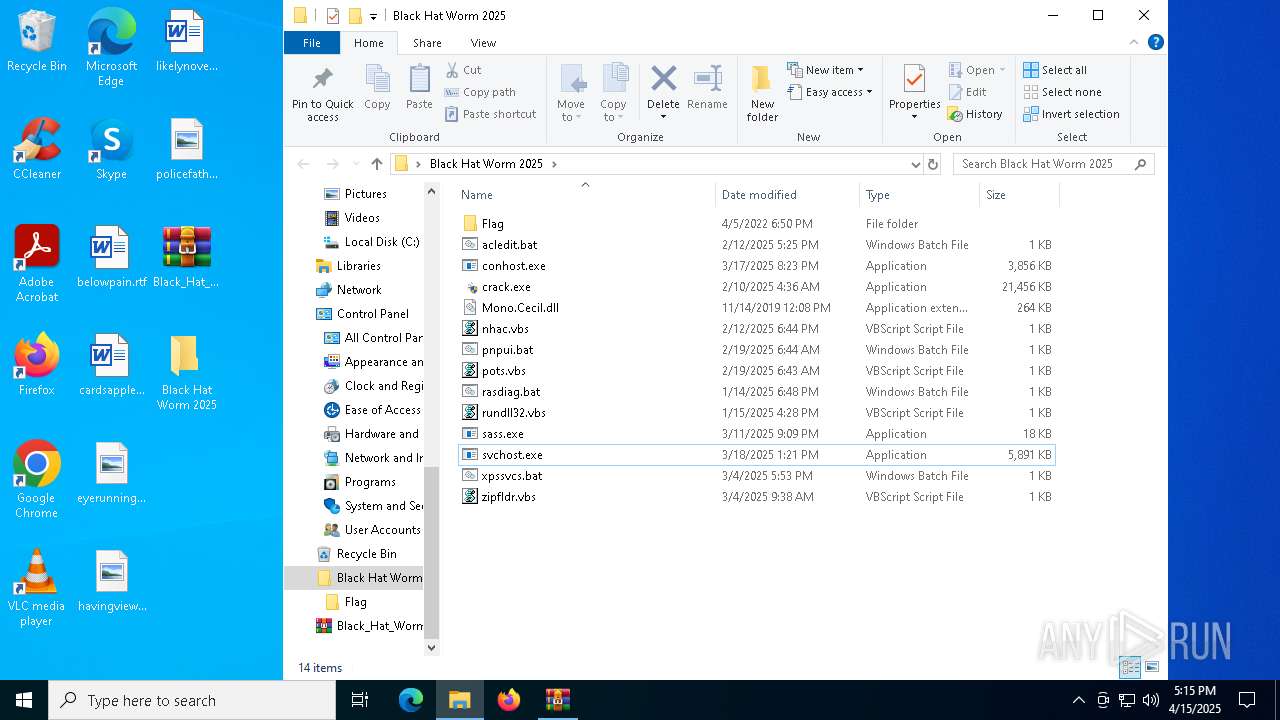
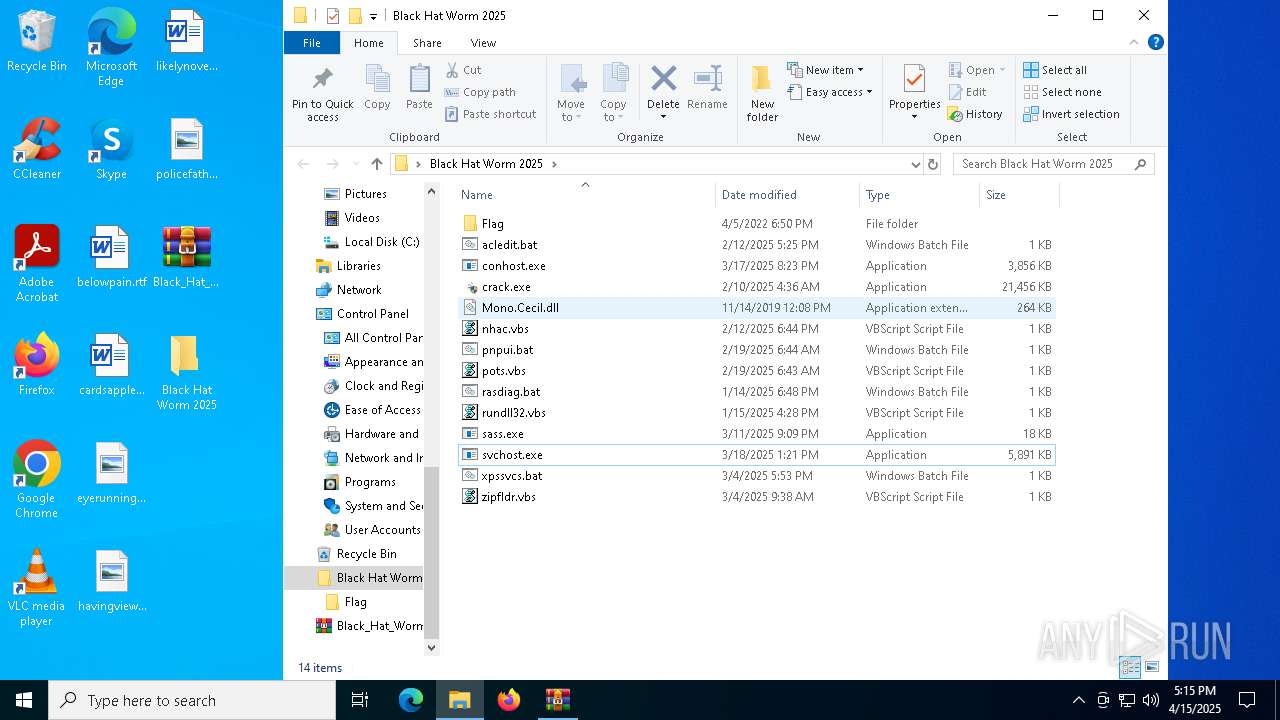
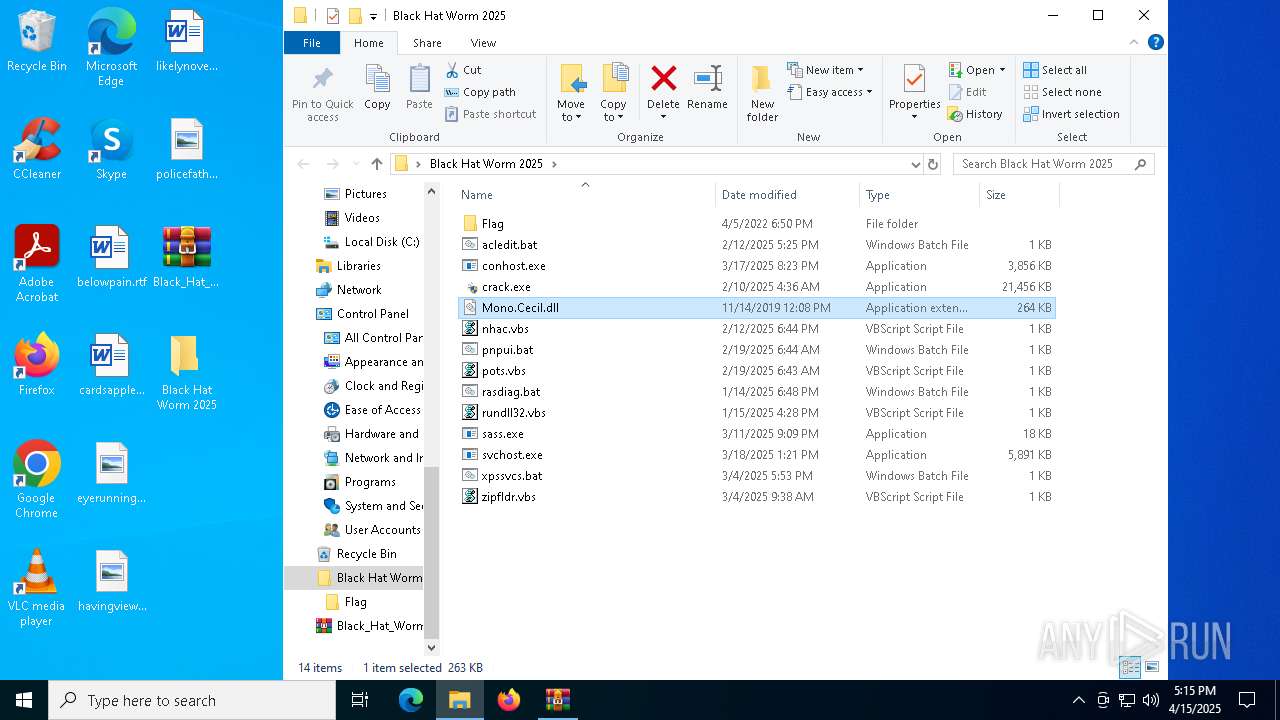
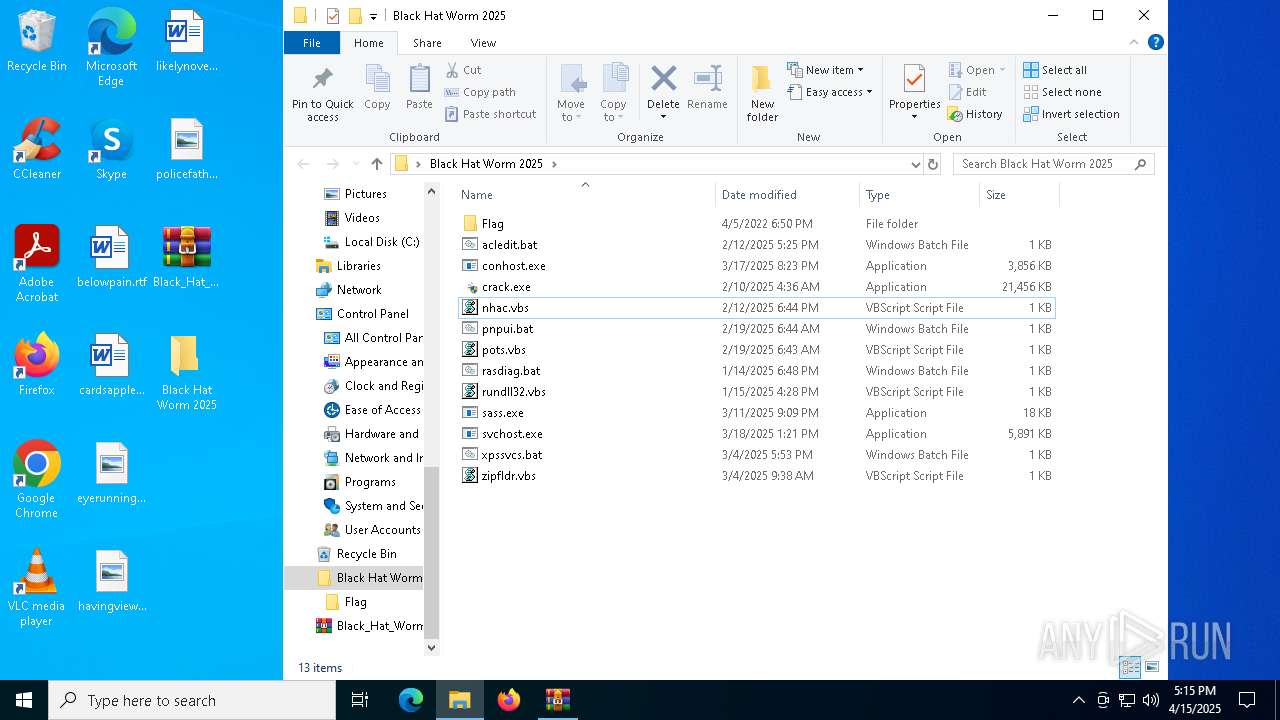
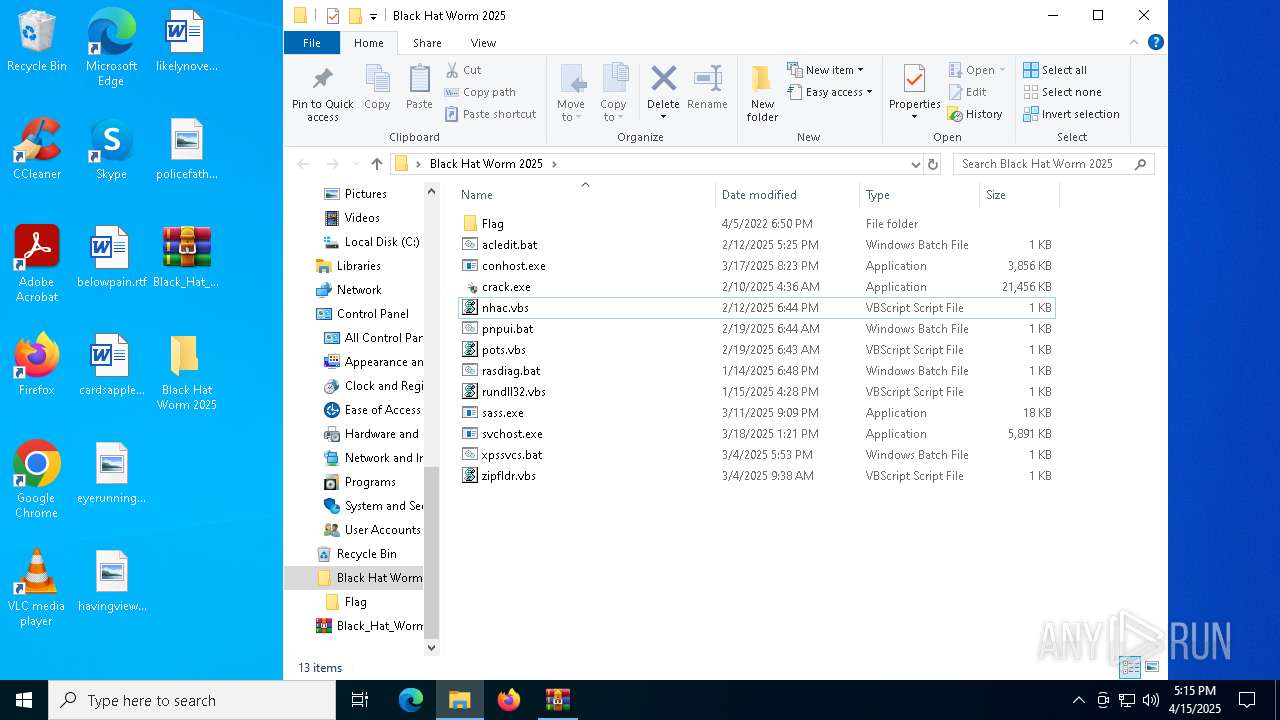
PID | Process | Filename | Type | |
|---|---|---|---|---|
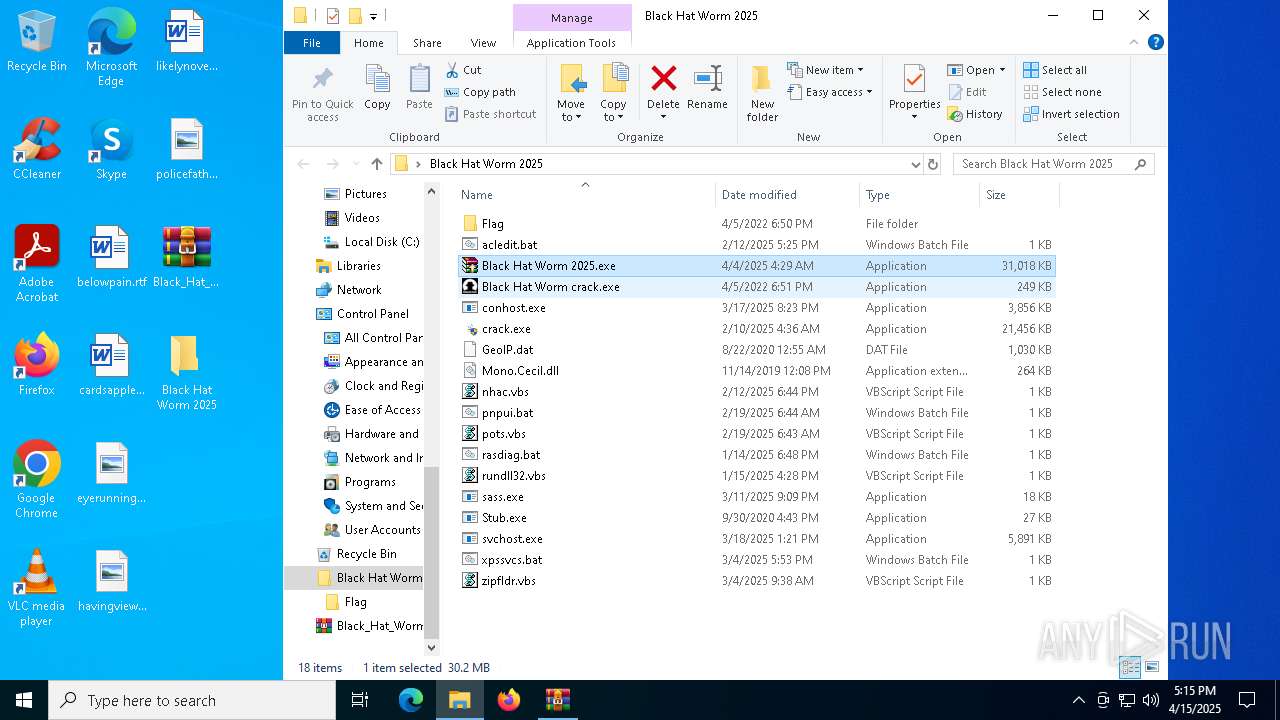
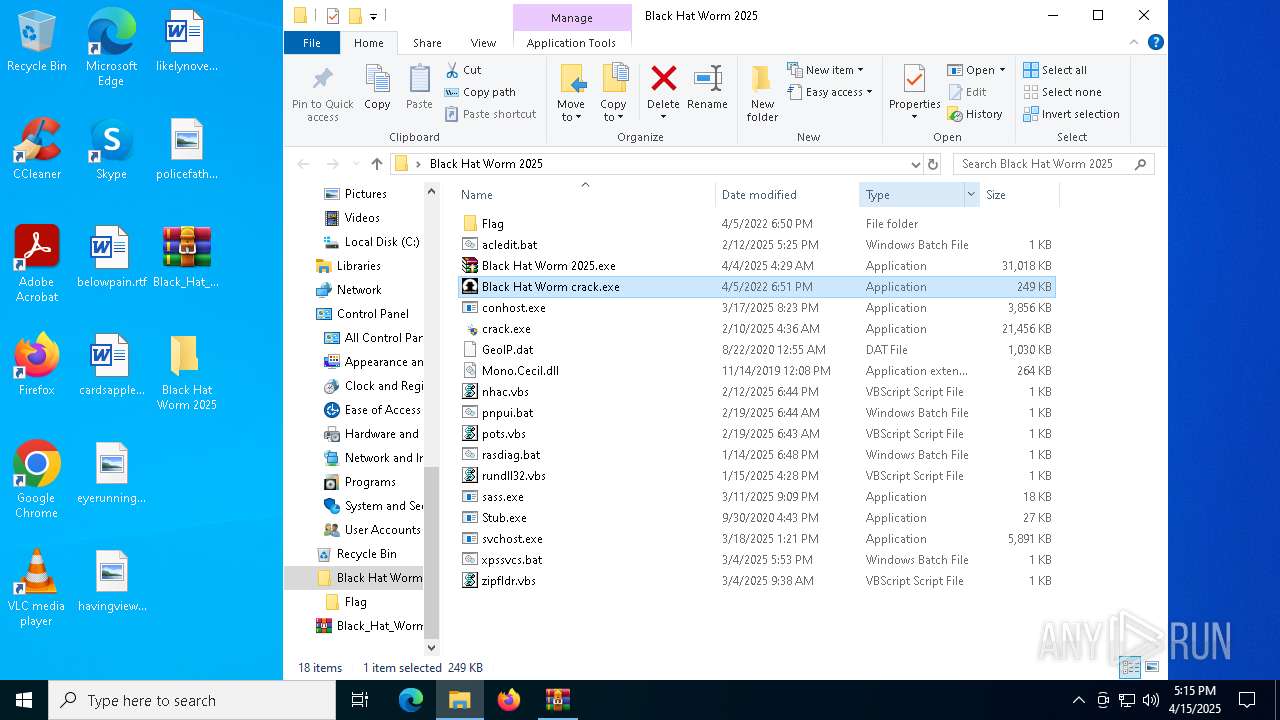
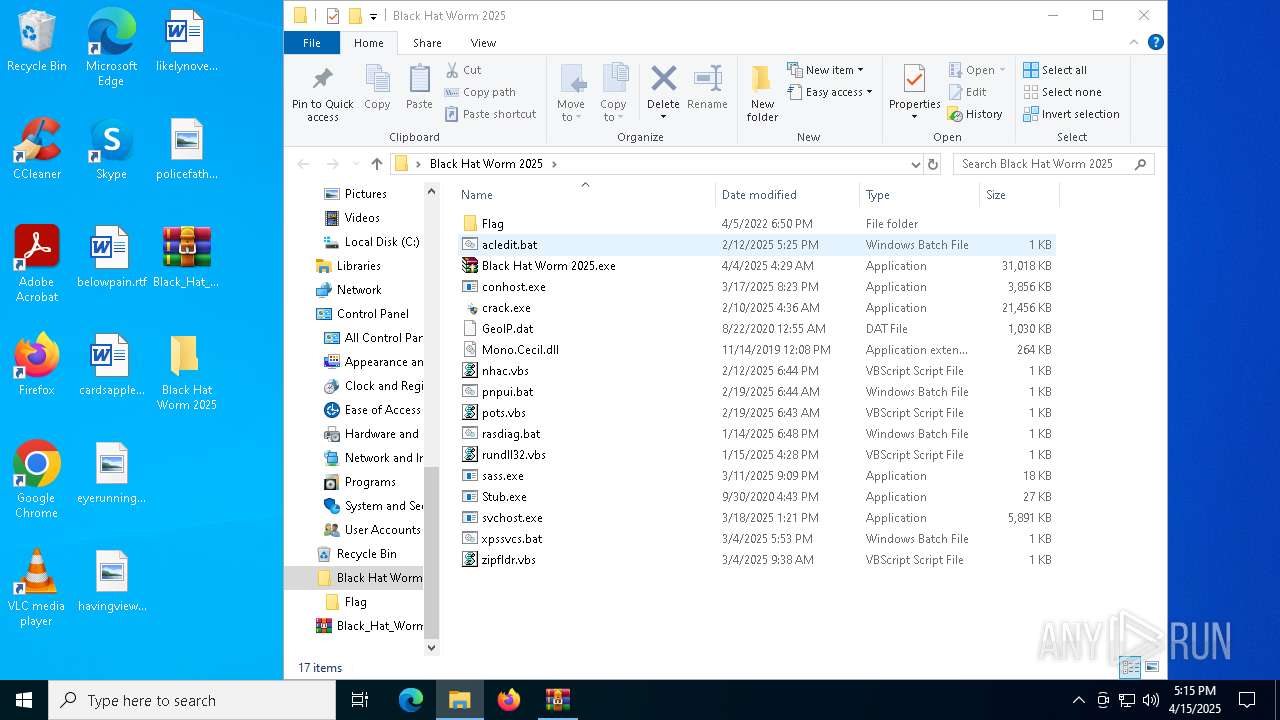
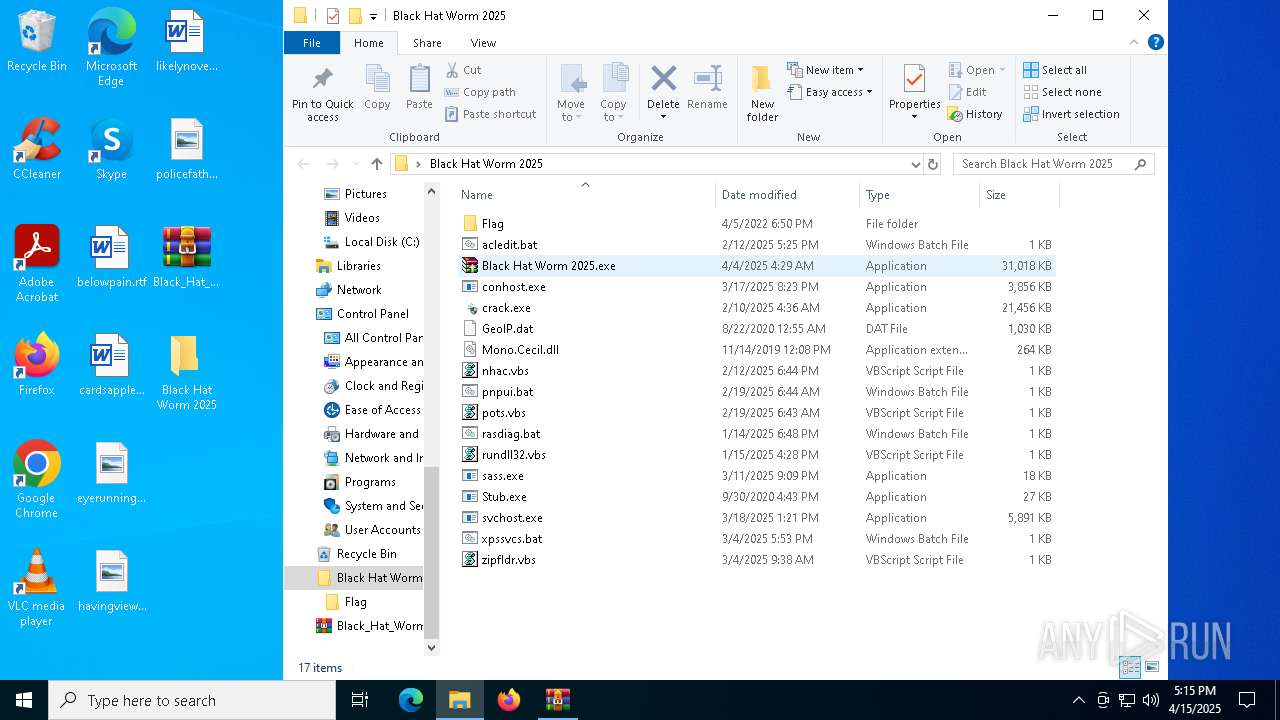
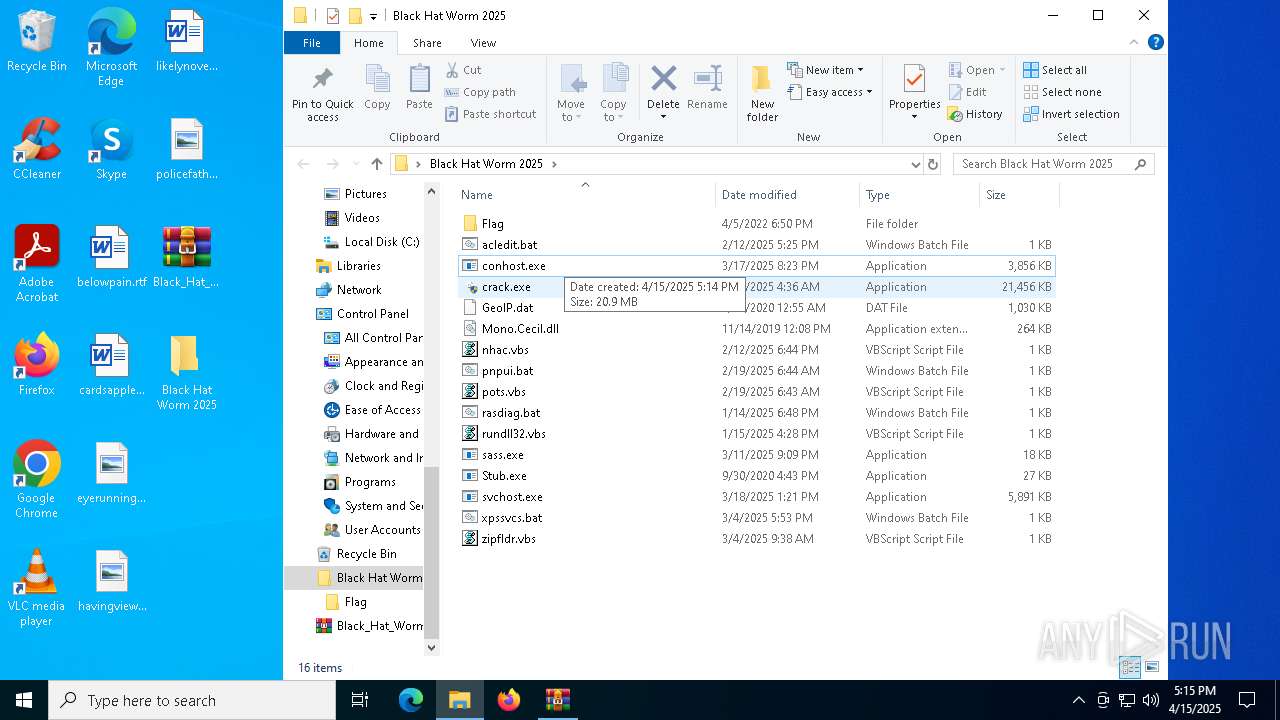
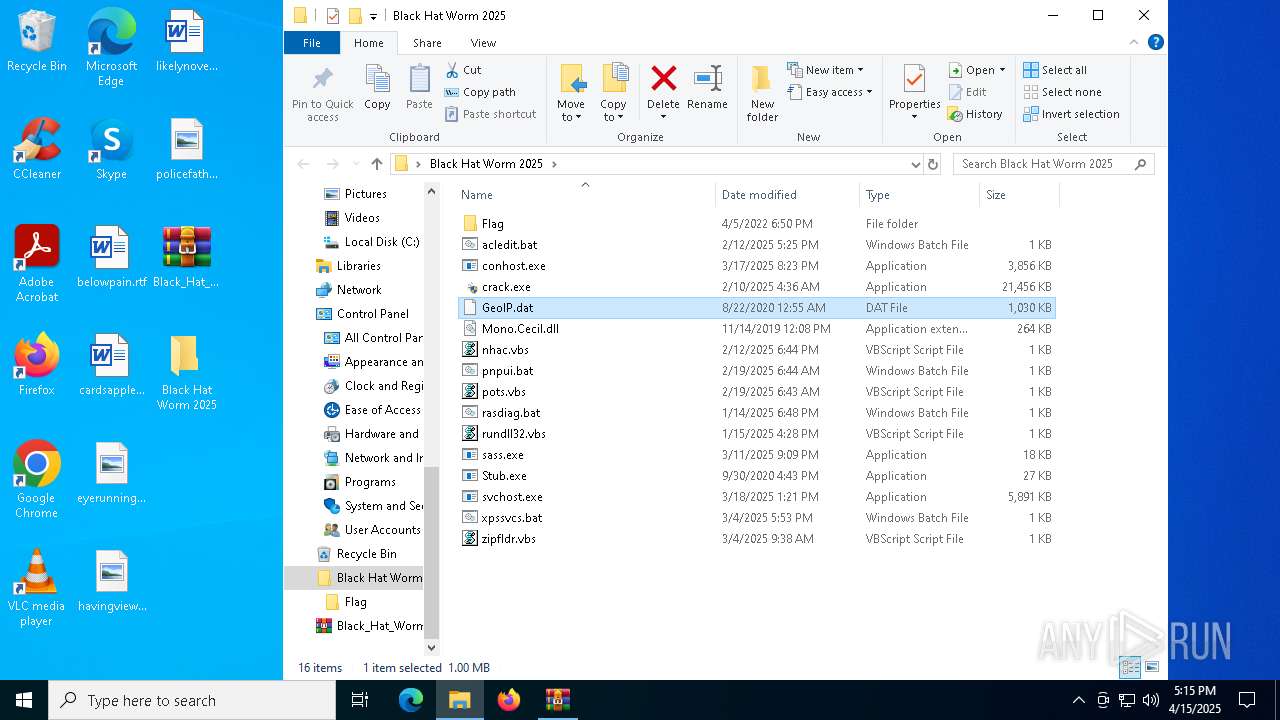
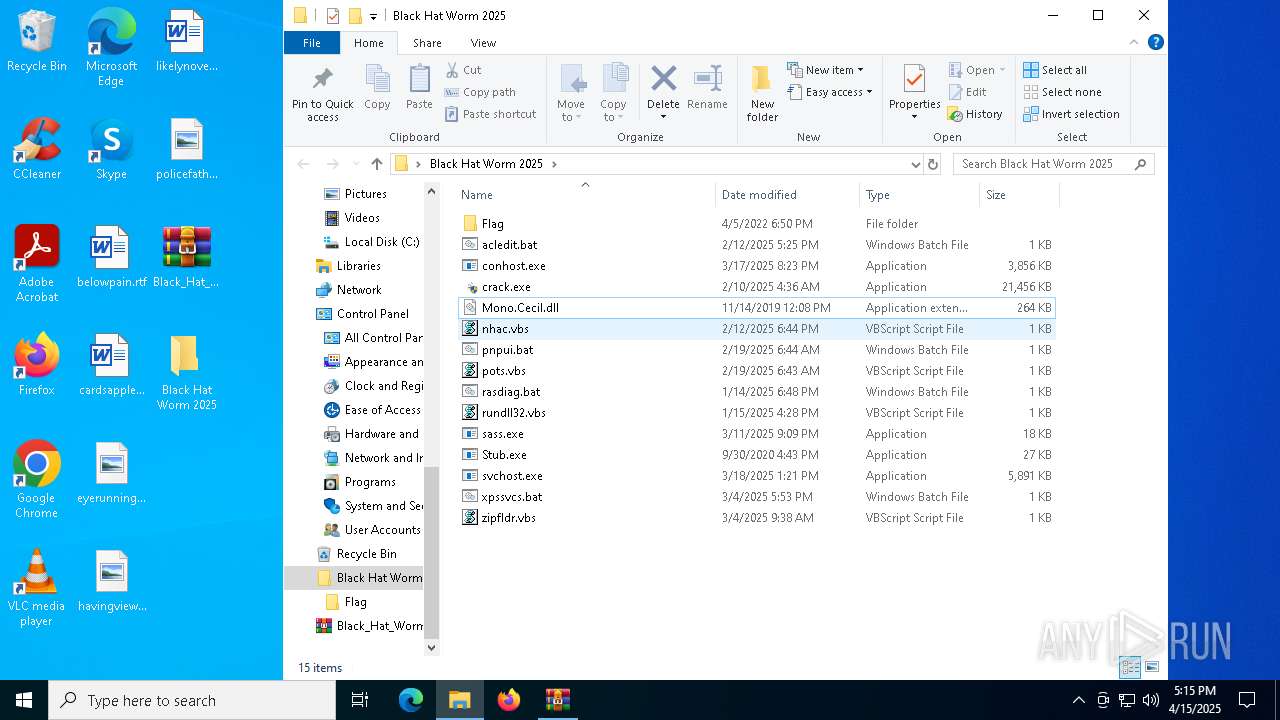
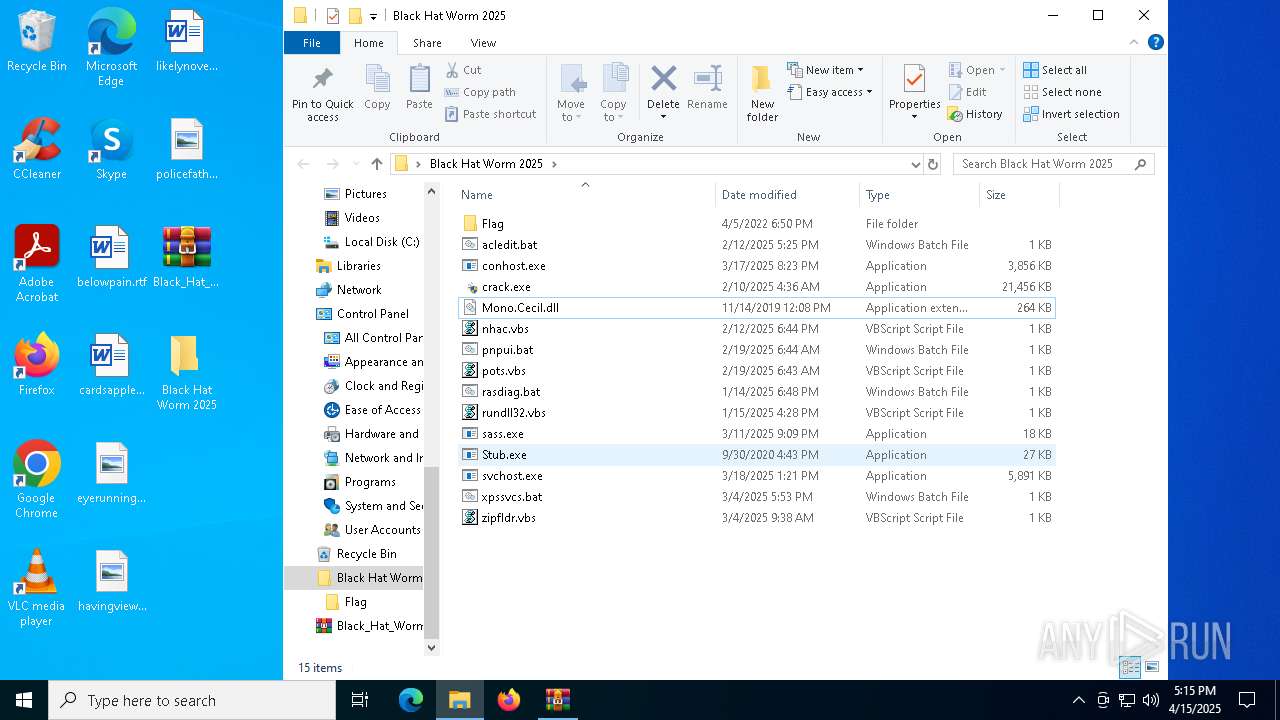
| 5400 | Black Hat Worm 2025.exe | C:\Users\admin\Desktop\Black Hat Worm 2025\rasdiag.bat | text | |
MD5:B791442311C4FFBE2471DF0EB834BAC1 | SHA256:62FA167C45C5535D931711A3572716FC029534F5CDF90D77A23947C6A534A499 | |||
| 6132 | WinRAR.exe | C:\Users\admin\Desktop\Black Hat Worm 2025\Black Hat Worm 2025.exe | executable | |
MD5:00DB1FEA110CC050F058E5E57EDE6C71 | SHA256:AE6A3F7DEAD9E3CB4398DB0F6883CB63028E4055B9BCAFC0E918FE226F61952A | |||
| 5400 | Black Hat Worm 2025.exe | C:\Users\admin\Desktop\Black Hat Worm 2025\xpssvcs.bat | text | |
MD5:6217EEF145710F57A87B30326D90F7C1 | SHA256:33C0C361BDE270E7F5F4376D4DBA3EA217169021D4611A4D7AEE804CC5D0FD10 | |||
| 5400 | Black Hat Worm 2025.exe | C:\Users\admin\Desktop\Black Hat Worm 2025\pnpui.bat | text | |
MD5:9EA1BB4FF775243C97272F9FC14F7658 | SHA256:FC711EC126E0A47BCF178AFFD6A72A0A65785A608D7EDB85A682150583FC7273 | |||
| 5400 | Black Hat Worm 2025.exe | C:\Users\admin\Desktop\Black Hat Worm 2025\acledit.bat | text | |
MD5:3B33446A78CFF74B5FB4E9A19599D174 | SHA256:85CB802D09069E128067E809F25AC0850EC356DE280E67F1DC44469025ECF621 | |||
| 5400 | Black Hat Worm 2025.exe | C:\Users\admin\Desktop\Black Hat Worm 2025\conhost.exe | executable | |
MD5:4964C1751F6DB917B5C285338EFC4687 | SHA256:6353B1218561A746BB3E009B611A1945BC2367B4D3FFEF7849D4AF4D369F184C | |||
| 5400 | Black Hat Worm 2025.exe | C:\Users\admin\Desktop\Black Hat Worm 2025\sass.exe | executable | |
MD5:0E14E70C14597160AAAEABA06536191D | SHA256:269DD8A318E57E8445D23E76DB7C692B4C670840064168BBD1A221B363B9EE6F | |||
| 5400 | Black Hat Worm 2025.exe | C:\Users\admin\Desktop\Black Hat Worm 2025\rundll32.vbs | text | |
MD5:6A18E846C6BE9B68DA2448EC4D6F9CC4 | SHA256:CFB13E7F03514BC8C1558A8D7819037185C530F2DA645897ADBE22CD30D56C2A | |||
| 5400 | Black Hat Worm 2025.exe | C:\Users\admin\Desktop\Black Hat Worm 2025\pots.vbs | text | |
MD5:9C21C8D0CEB71D1E29552153D26E2B99 | SHA256:E64DA7B7D57B7F02677A384D0737D5F95C57A0FD49F07F53E3108DC633035900 | |||
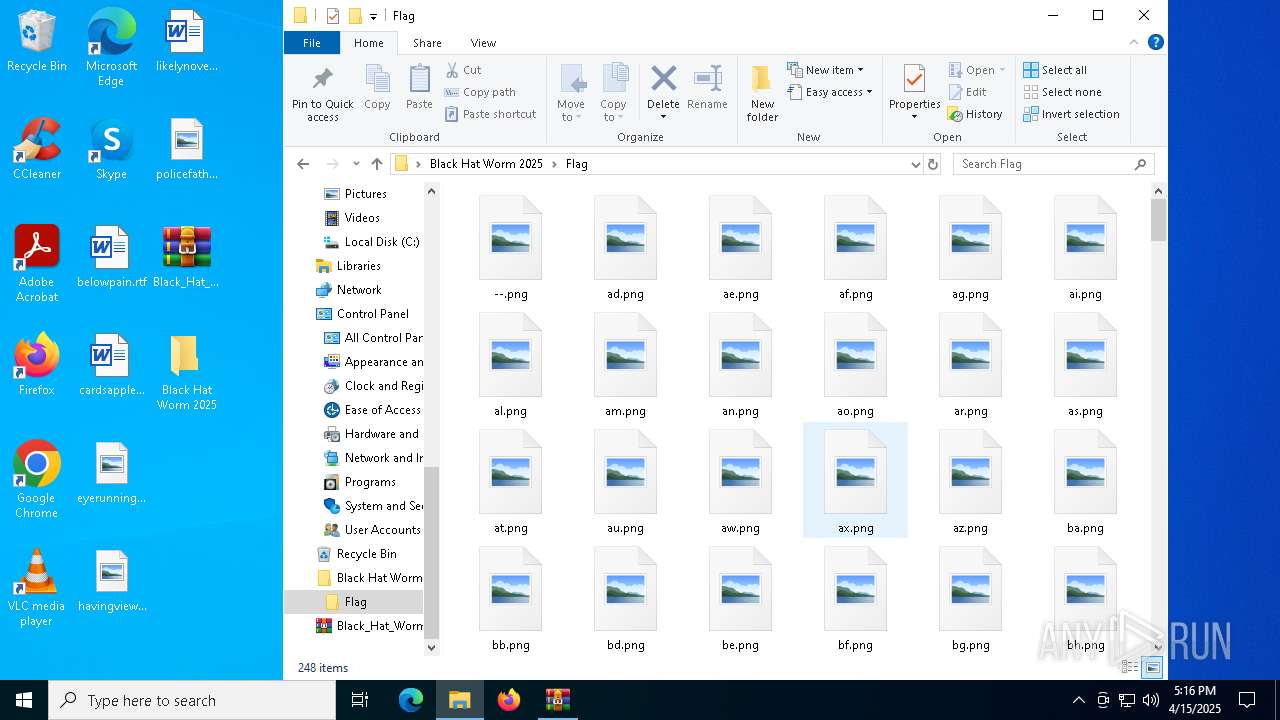
| 5400 | Black Hat Worm 2025.exe | C:\Users\admin\Desktop\Black Hat Worm 2025\Flag\--.png | image | |
MD5:2949D7765354B2F1C2B686A21BA63CE3 | SHA256:BA79A5CF5A4338572B1FBCD75D7B49BB8FC00D49608103C48579EF87EE42F985 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
67
DNS requests
22
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4112 | svchost.exe | GET | 404 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | — | — | whitelisted |
7352 | Update.exe | GET | 404 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5392 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5392 | SIHClient.exe | 20.242.39.171:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
171.39.242.20.in-addr.arpa |
| unknown |
d.3.0.0.0.0.0.0.0.0.0.0.0.0.0.0.7.0.0.0.8.0.4.0.0.3.0.1.3.0.6.2.ip6.arpa |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
4112 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Crypto Currency Mining Activity Detected | ET COINMINER CoinMiner Domain in DNS Lookup (pool .hashvault .pro) |
2616 | OmegaEngine.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
2616 | OmegaEngine.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |
7352 | Update.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
8172 | conhost.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |