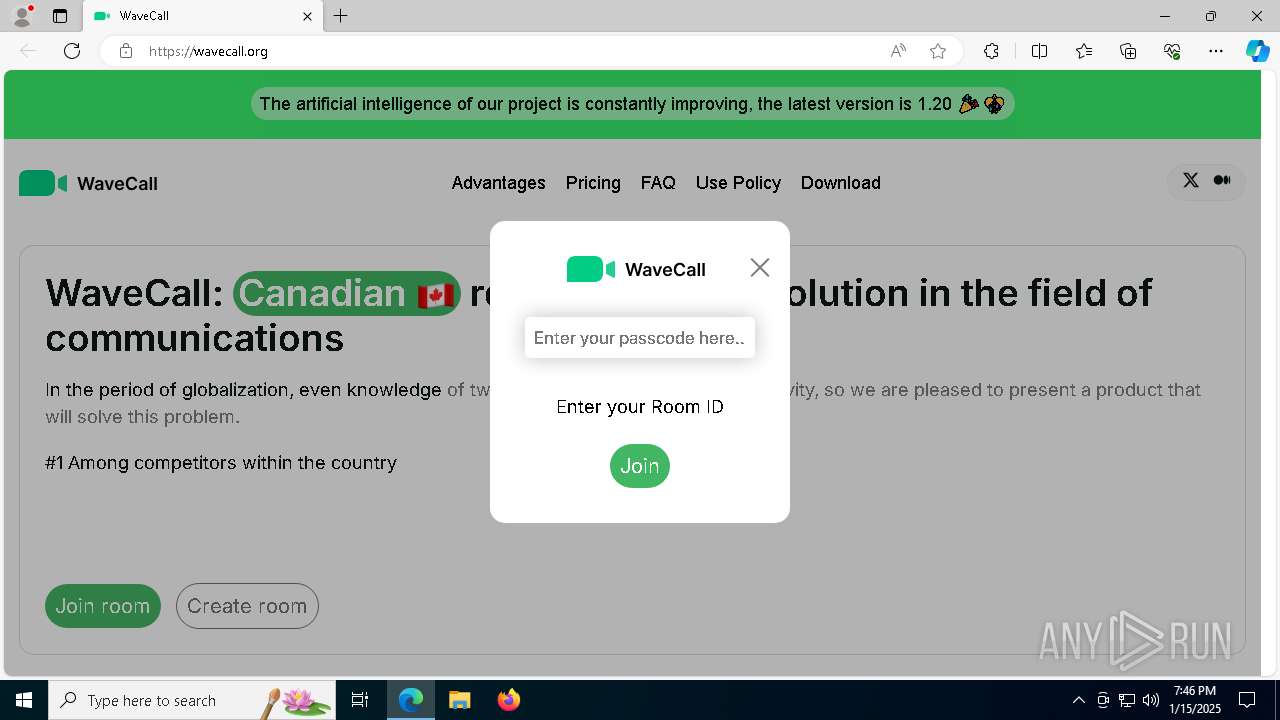
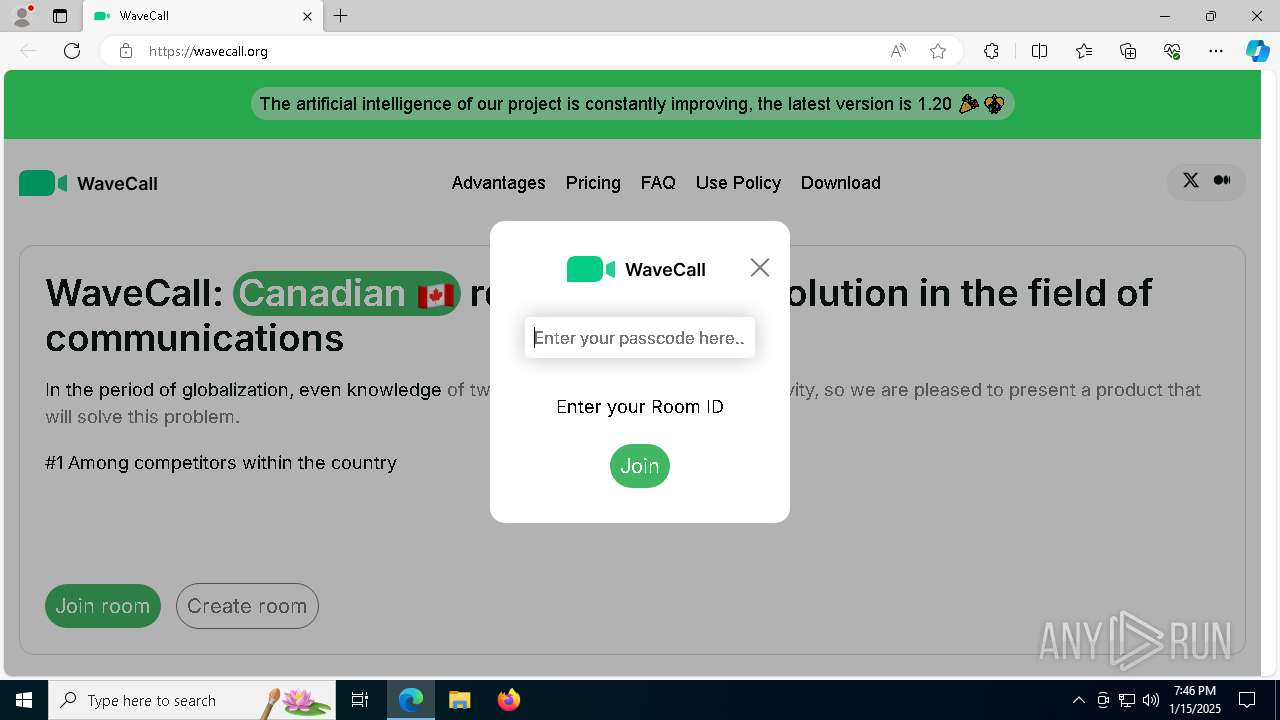
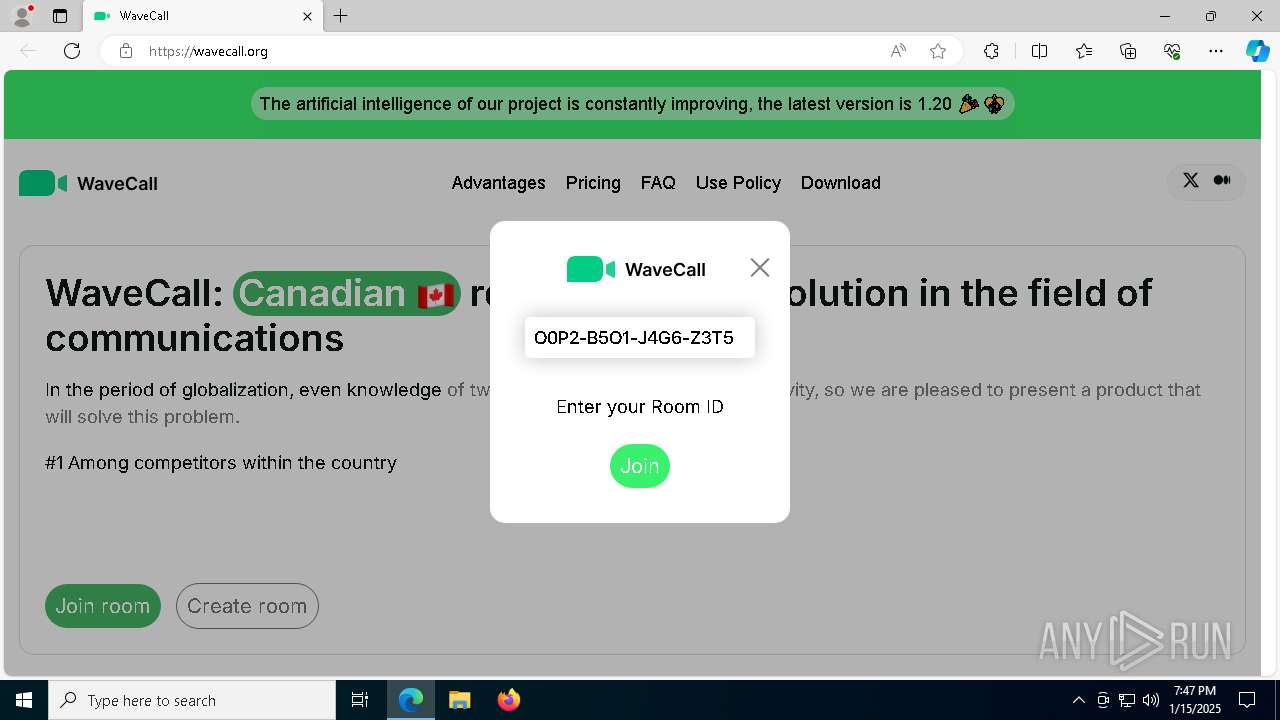
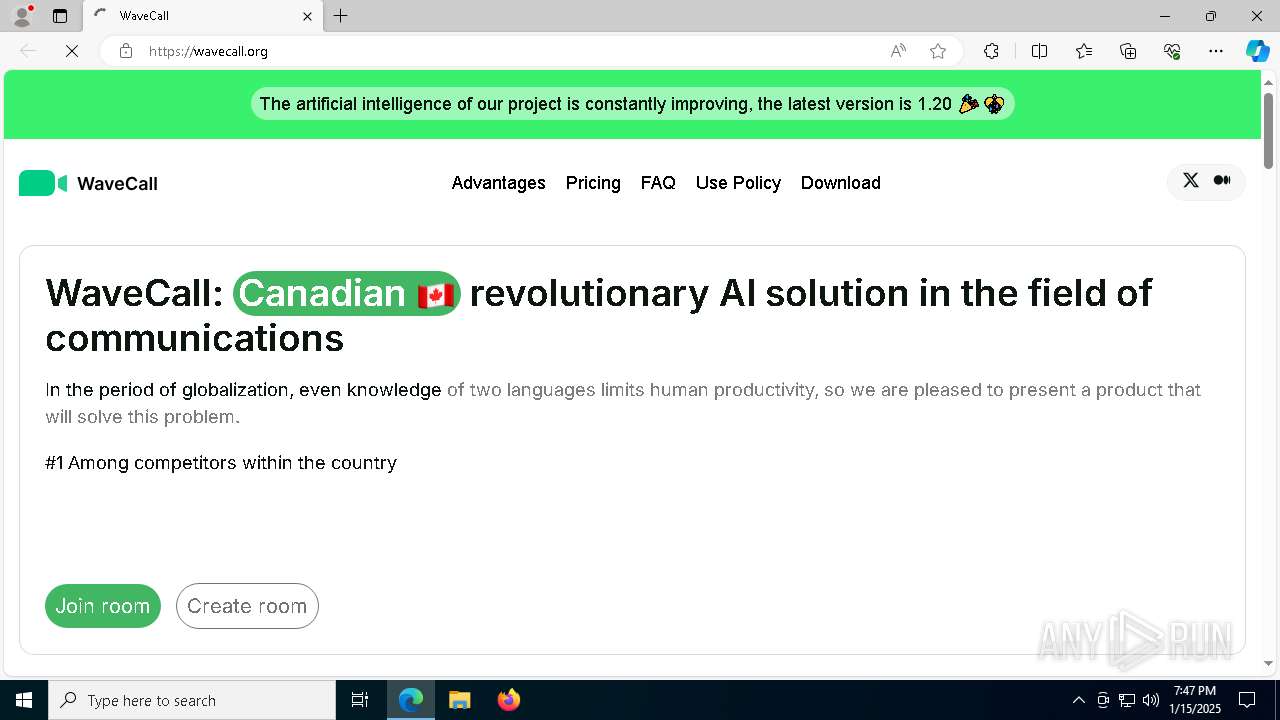
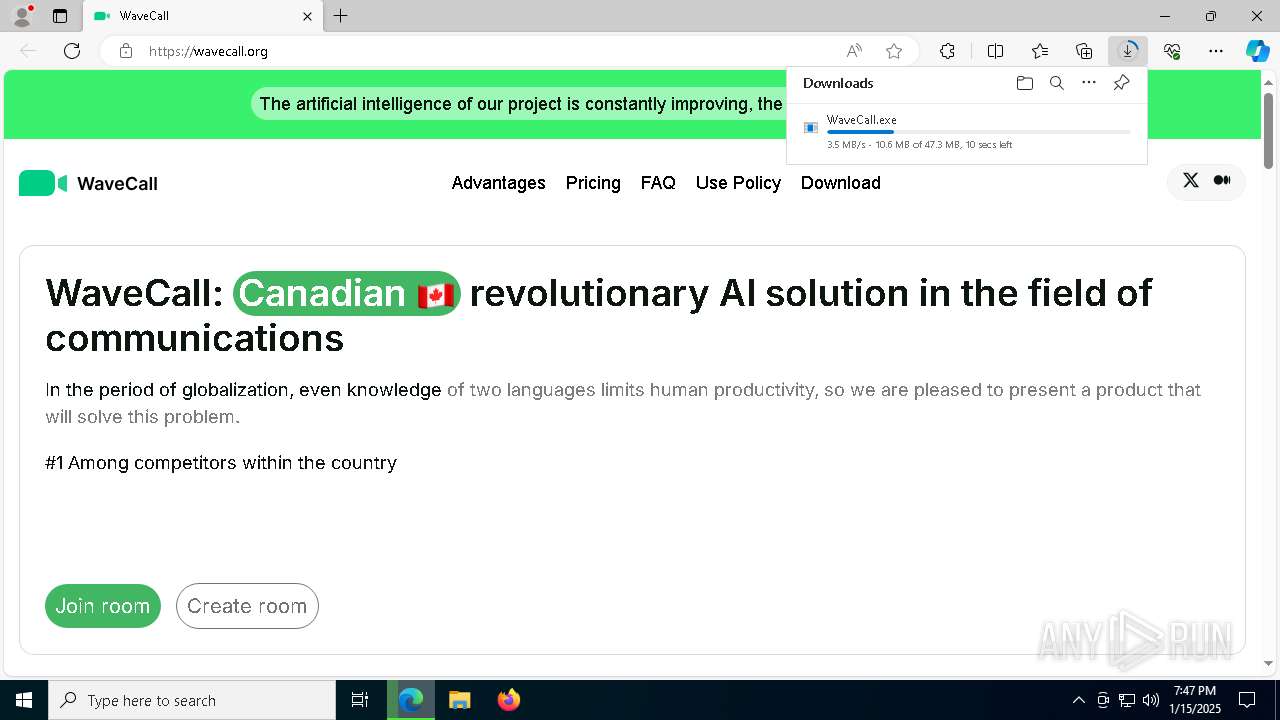
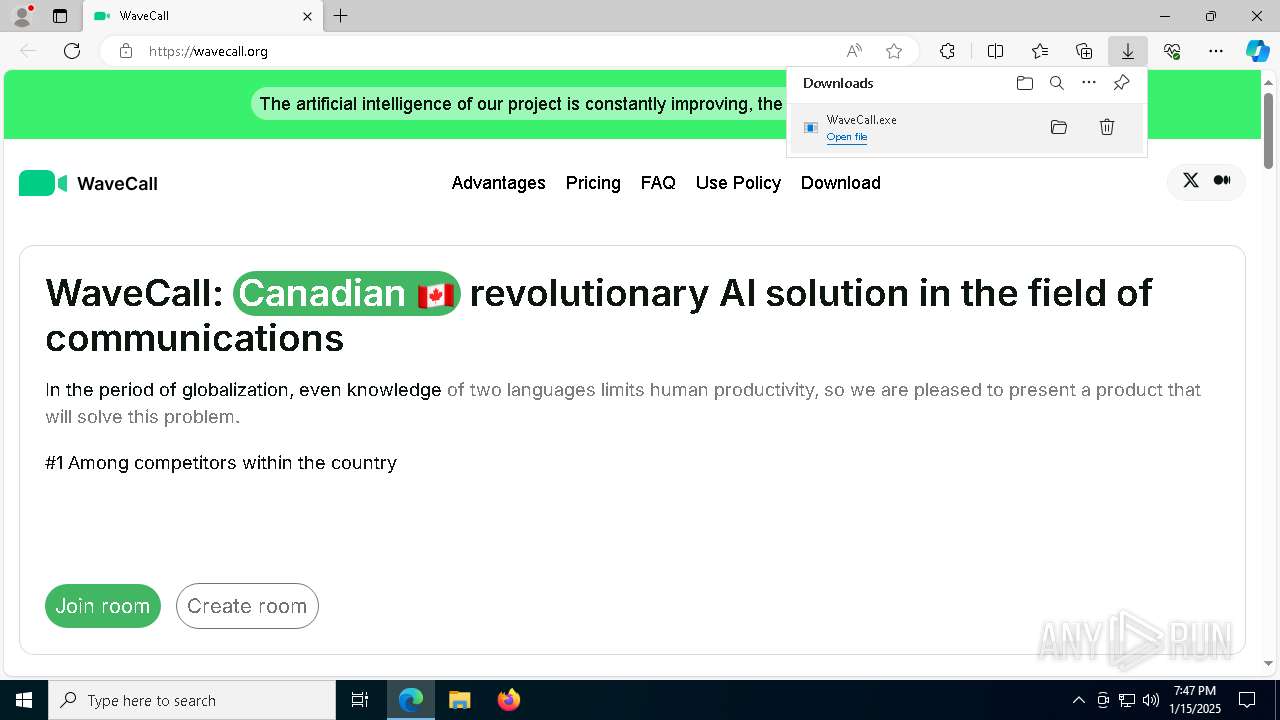
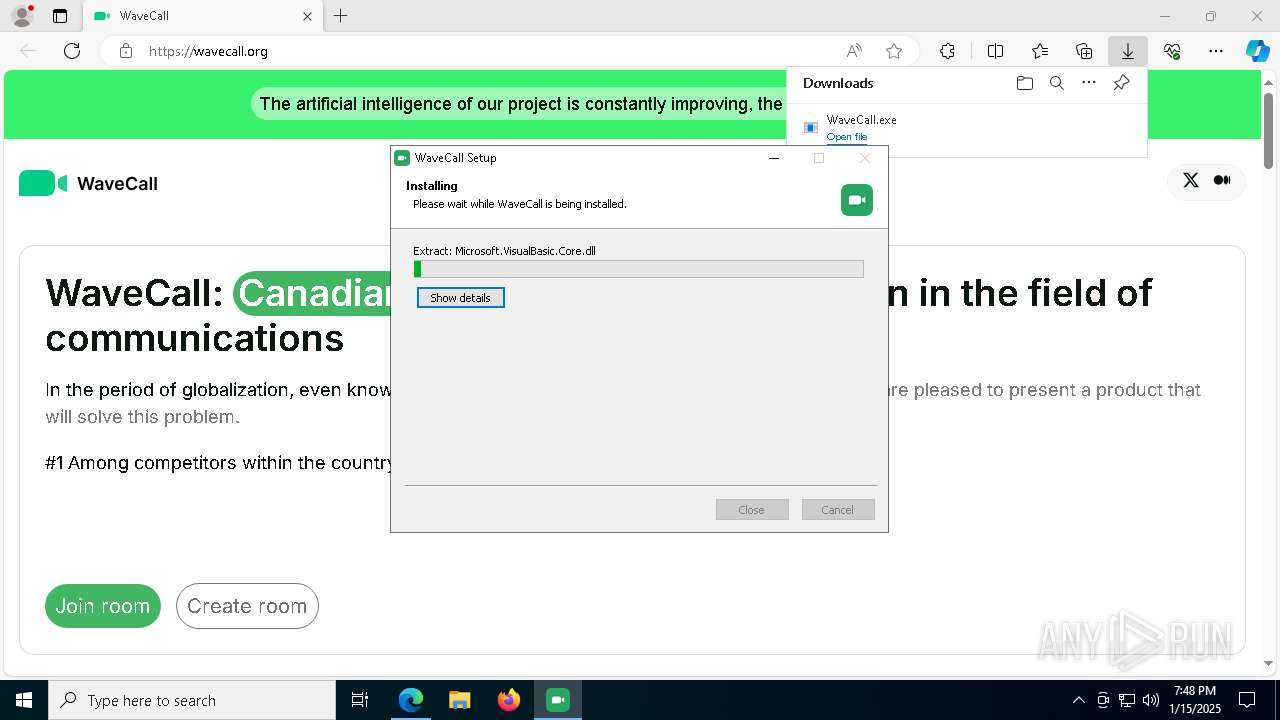
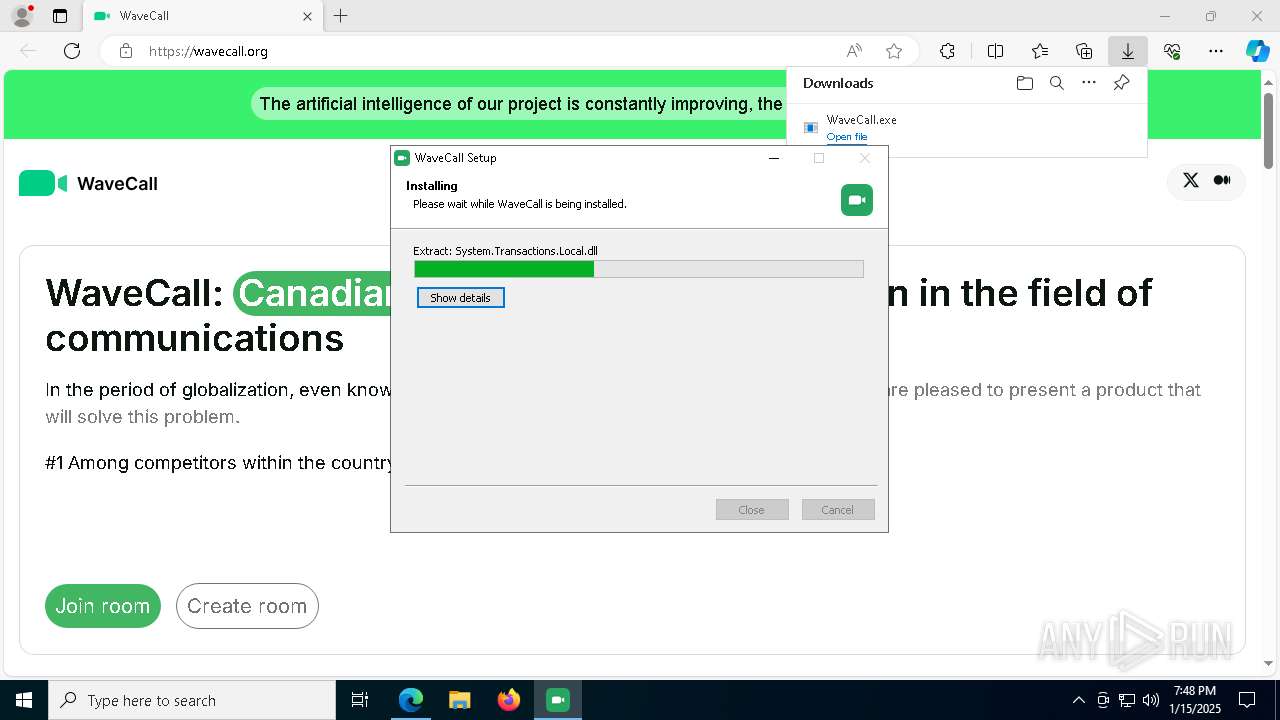
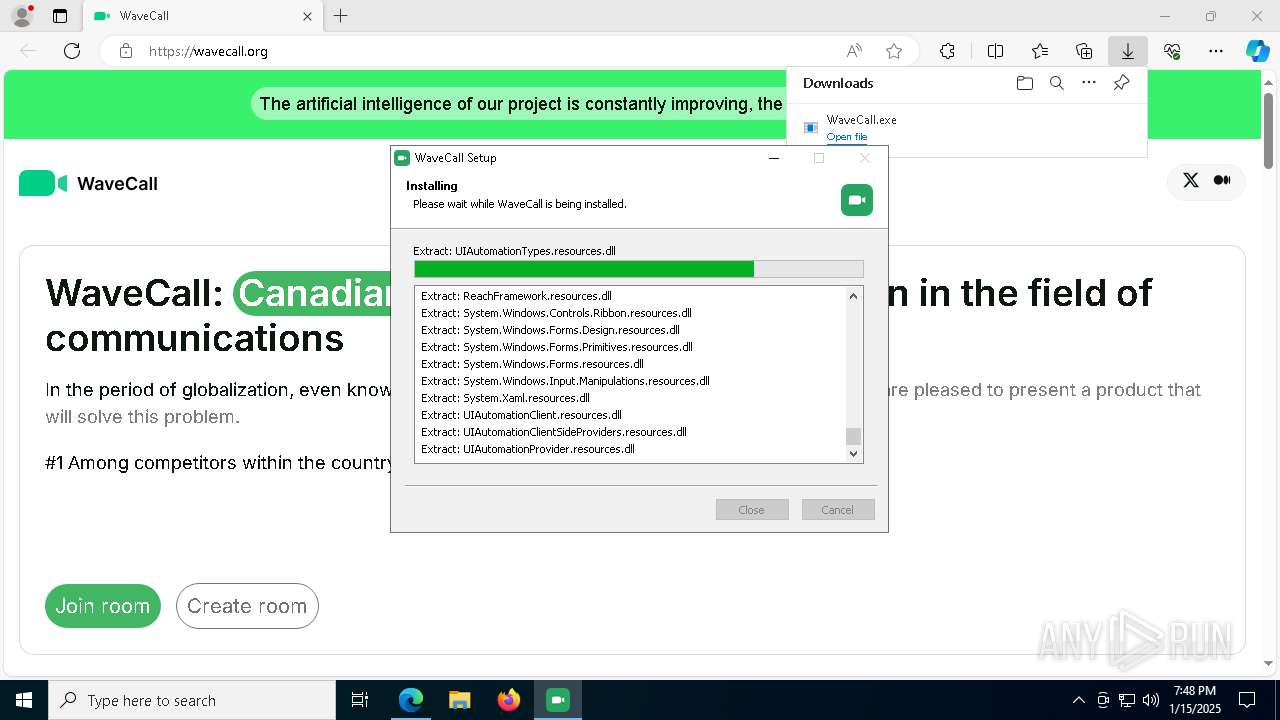
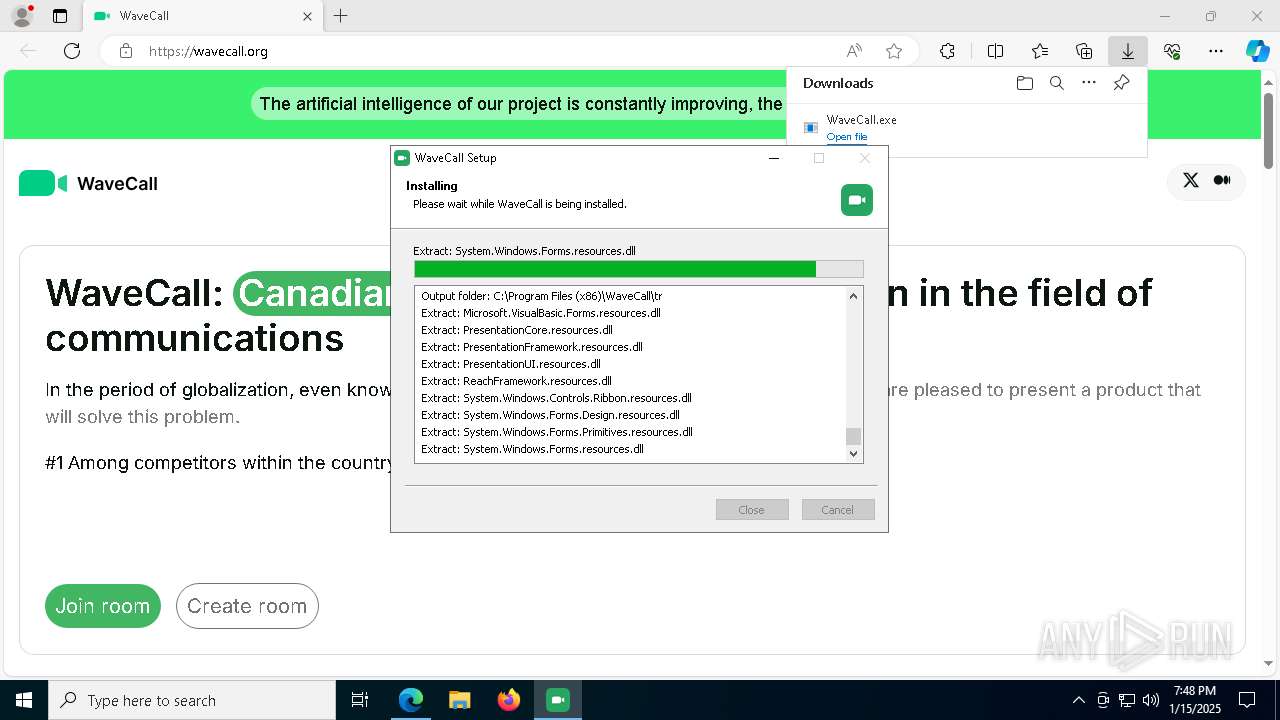
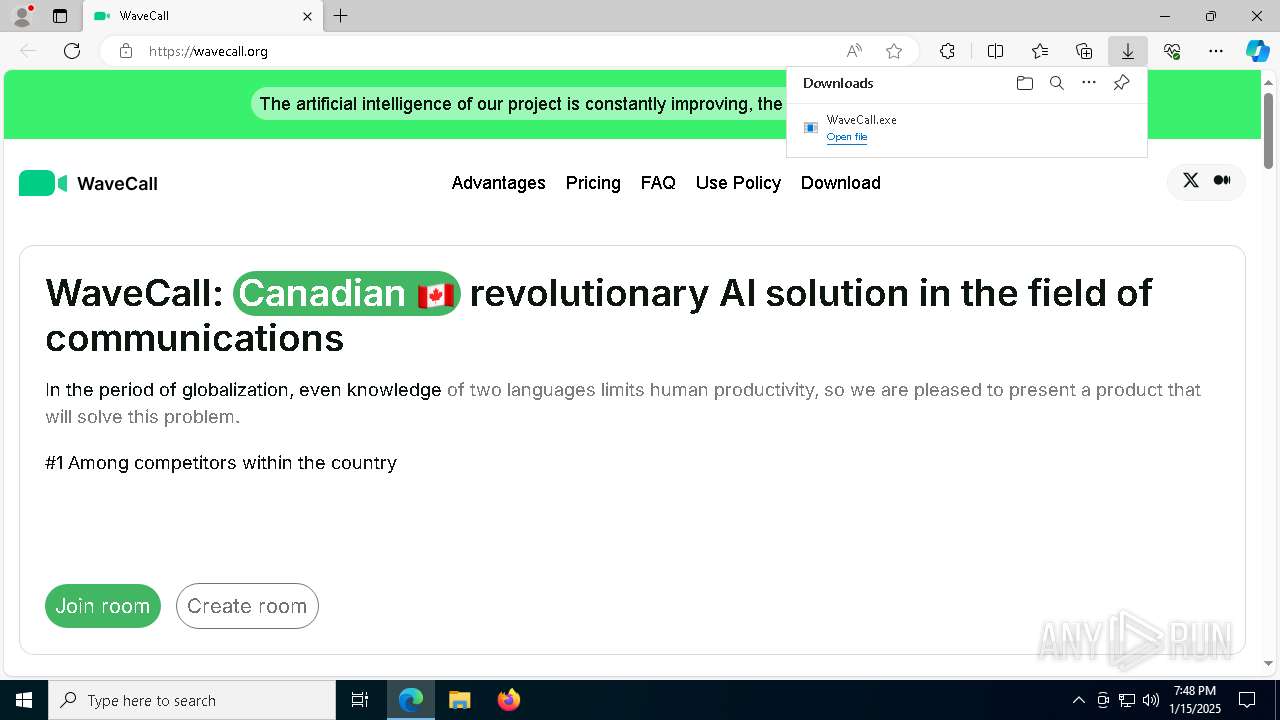
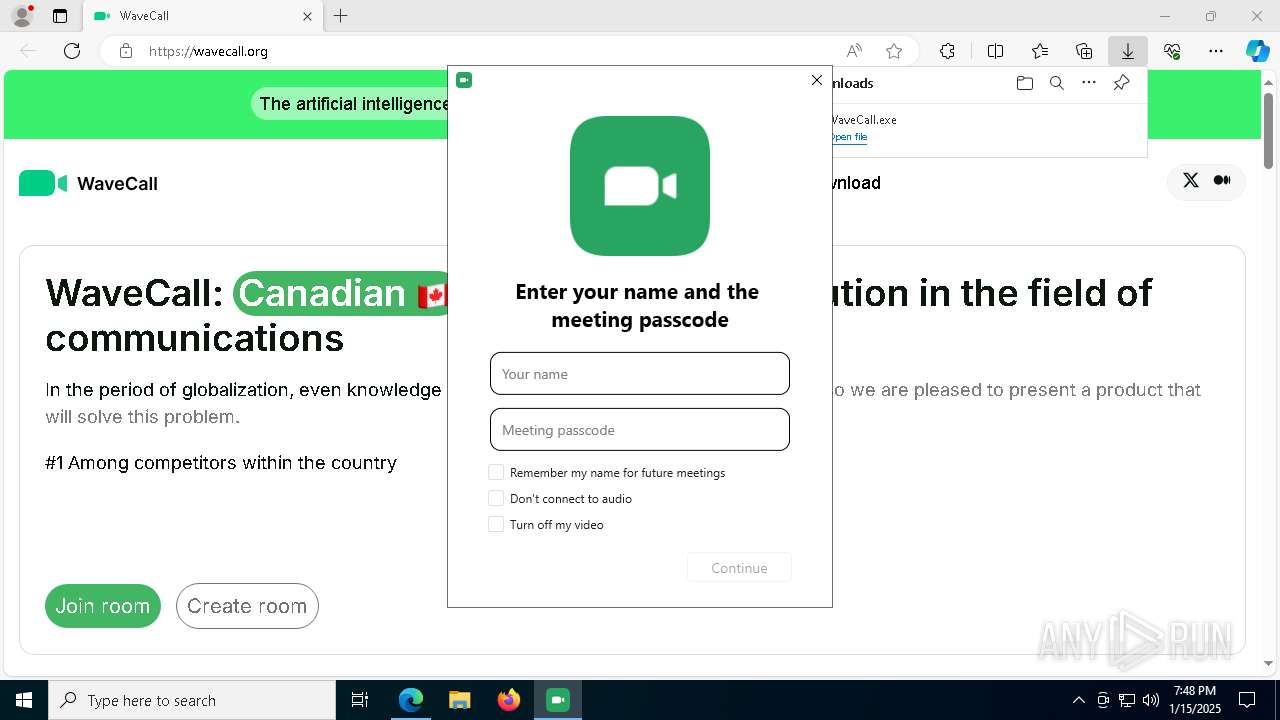
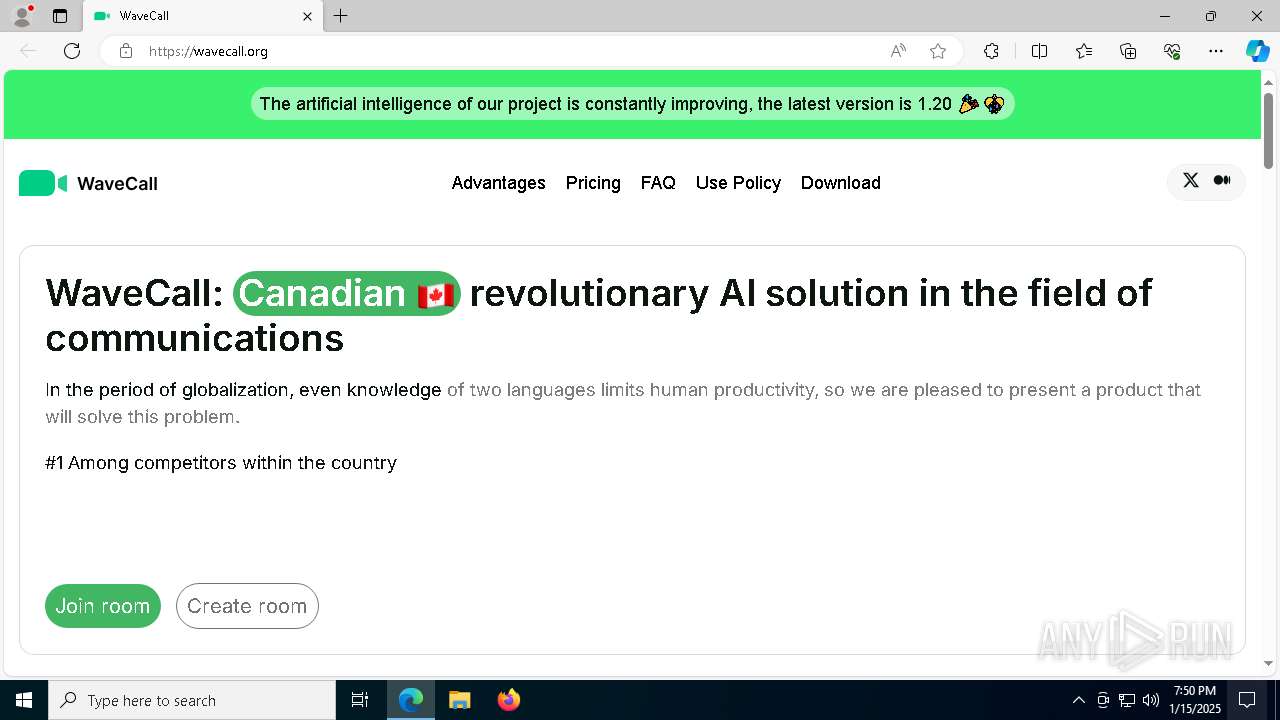
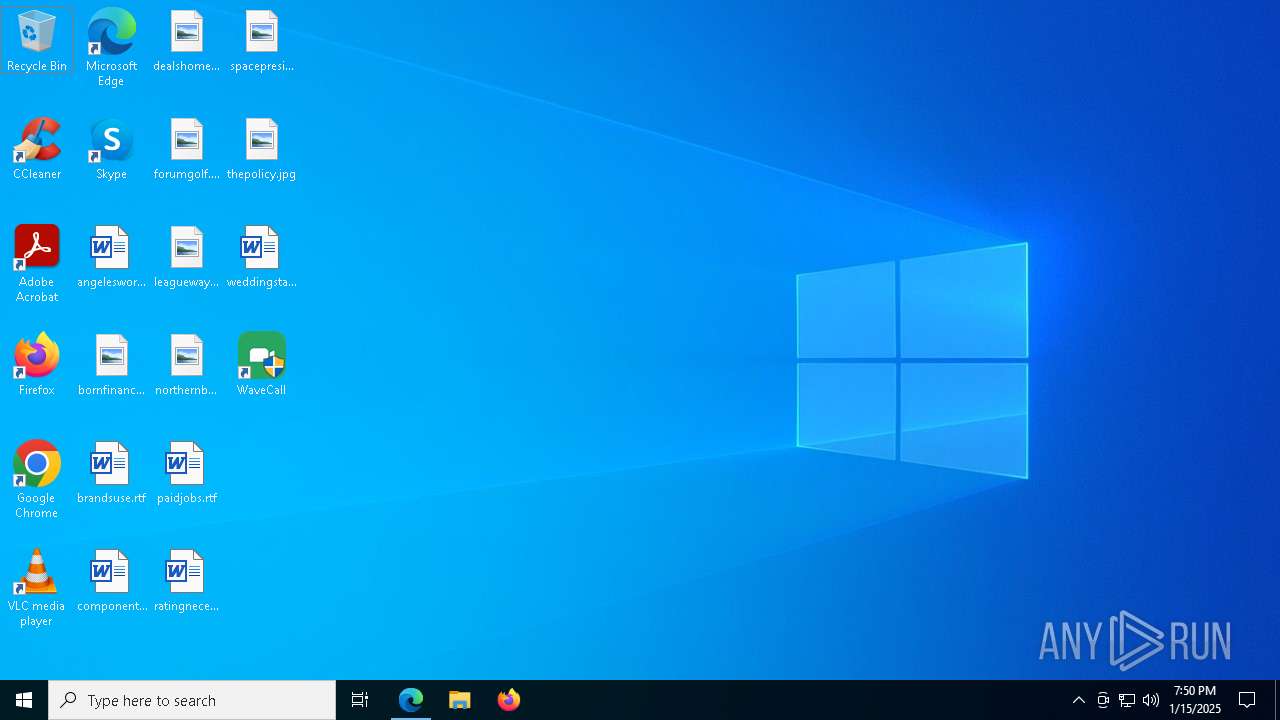
| URL: | wavecall.org |
| Full analysis: | https://app.any.run/tasks/f148a598-2d99-48cd-8efc-e0a107d460d5 |
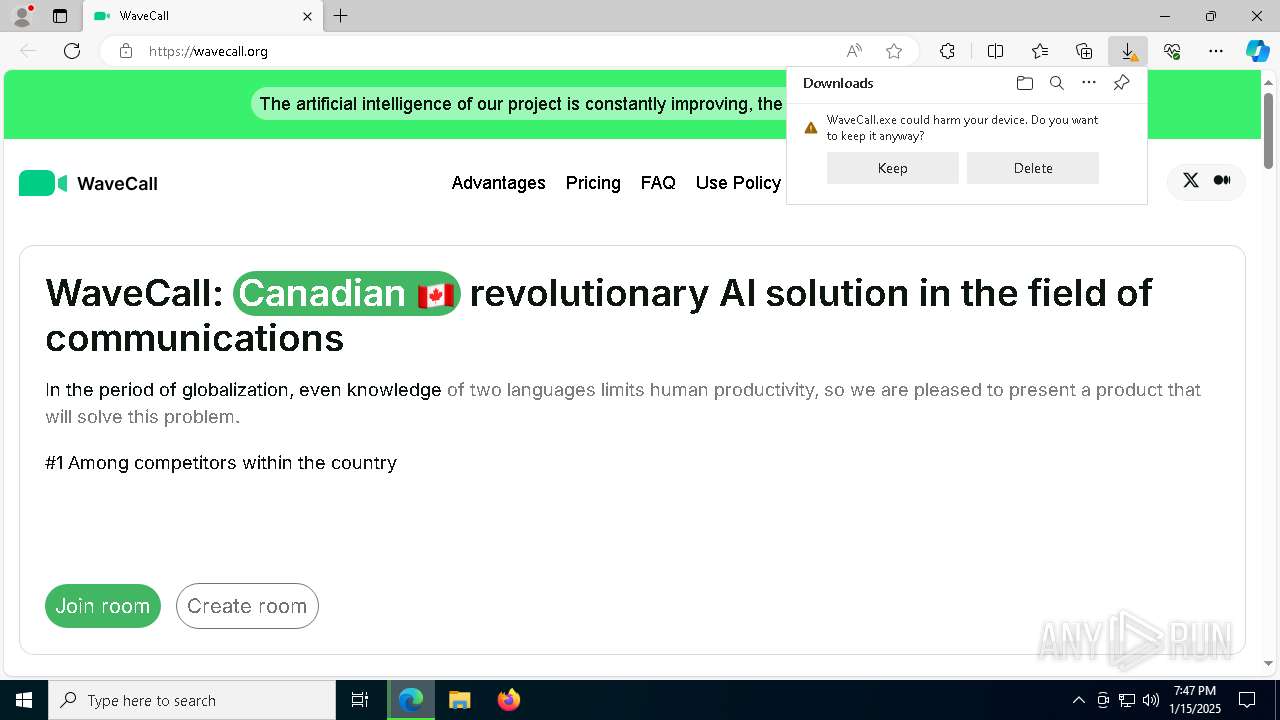
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | January 15, 2025, 19:46:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3AEC26948ACBD67422D59FBAE892E507 |
| SHA1: | 585B9E135E1A9EFA2502DA0E23891040ECAB7B75 |
| SHA256: | A83F9F738AC54A3486406E461D08E7CBFEE90BCE4D87CF5B5953FC172DE4E81D |
| SSDEEP: | 3:8zf:cf |
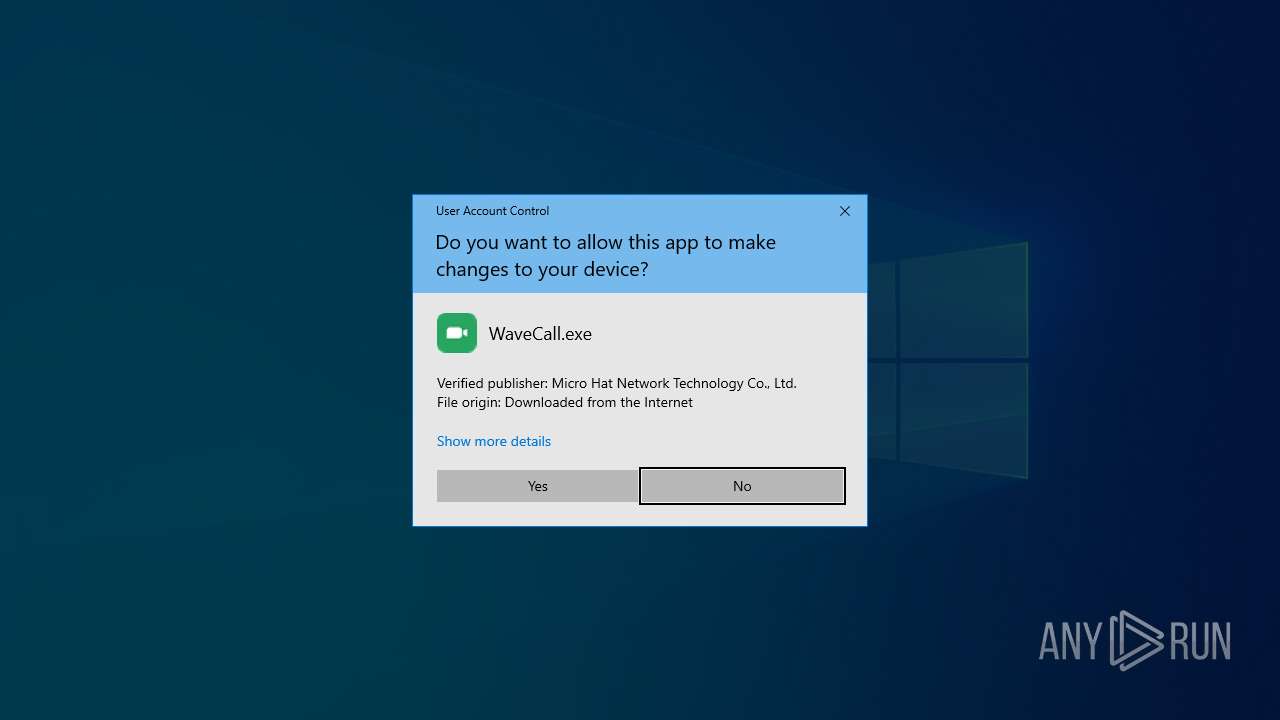
MALICIOUS
Adds path to the Windows Defender exclusion list
- WaveCall.exe (PID: 6252)
RHADAMANTHYS has been detected (SURICATA)
- fontdrvhost.exe (PID: 3732)
- fontdrvhost.exe (PID: 6136)
- OpenWith.exe (PID: 6248)
- OOBE-Maintenance.exe (PID: 2728)
Actions looks like stealing of personal data
- fontdrvhost.exe (PID: 6136)
- chrome.exe (PID: 2828)
- OOBE-Maintenance.exe (PID: 2728)
SUSPICIOUS
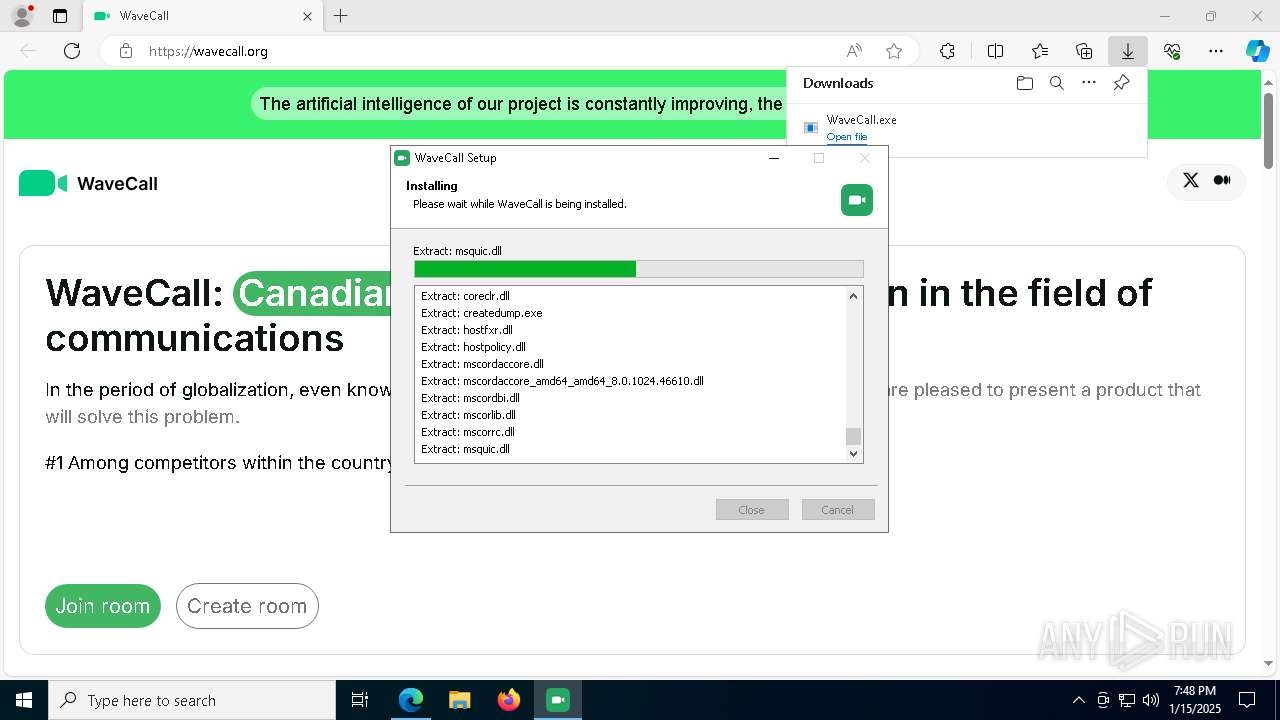
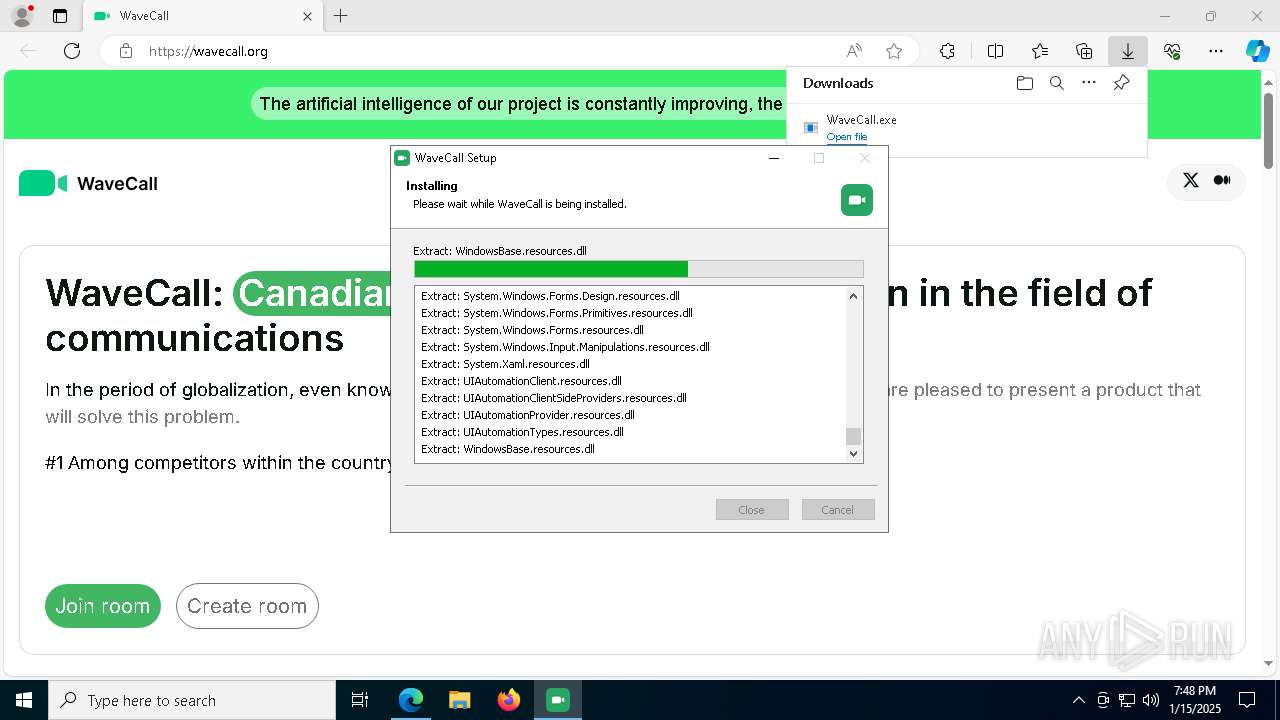
Executable content was dropped or overwritten
- WaveCall.exe (PID: 6576)
- WaveCall.exe (PID: 6252)
Process drops legitimate windows executable
- WaveCall.exe (PID: 6576)
The process drops C-runtime libraries
- WaveCall.exe (PID: 6576)
Reads security settings of Internet Explorer
- WaveCall.exe (PID: 6576)
- WaveCall.exe (PID: 6252)
- ShellExperienceHost.exe (PID: 1572)
The process creates files with name similar to system file names
- WaveCall.exe (PID: 6576)
Starts POWERSHELL.EXE for commands execution
- WaveCall.exe (PID: 6252)
Script adds exclusion path to Windows Defender
- WaveCall.exe (PID: 6252)
Executes application which crashes
- csrss1.exe (PID: 3836)
- csrss2.exe (PID: 5792)
Connects to unusual port
- fontdrvhost.exe (PID: 3732)
- fontdrvhost.exe (PID: 6136)
- OpenWith.exe (PID: 6248)
- OOBE-Maintenance.exe (PID: 2728)
Contacting a server suspected of hosting an CnC
- fontdrvhost.exe (PID: 3732)
- fontdrvhost.exe (PID: 6136)
- OOBE-Maintenance.exe (PID: 2728)
- OpenWith.exe (PID: 6248)
Application launched itself
- chrome.exe (PID: 2828)
- msedge.exe (PID: 3732)
Loads DLL from Mozilla Firefox
- fontdrvhost.exe (PID: 6136)
- OOBE-Maintenance.exe (PID: 2728)
Searches for installed software
- OOBE-Maintenance.exe (PID: 2728)
Checks for external IP
- svchost.exe (PID: 2192)
INFO
Application launched itself
- msedge.exe (PID: 6164)
Reads Environment values
- identity_helper.exe (PID: 6776)
- chrome.exe (PID: 2828)
- msedge.exe (PID: 3732)
Reads the computer name
- identity_helper.exe (PID: 6776)
- ShellExperienceHost.exe (PID: 1572)
- WaveCall.exe (PID: 6576)
The sample compiled with english language support
- WaveCall.exe (PID: 6576)
- WaveCall.exe (PID: 6252)
- msedge.exe (PID: 5240)
Creates files in the program directory
- WaveCall.exe (PID: 6576)
Reads the machine GUID from the registry
- WaveCall.exe (PID: 6252)
The process uses the downloaded file
- WaveCall.exe (PID: 6576)
- msedge.exe (PID: 6164)
- msedge.exe (PID: 308)
Checks supported languages
- WaveCall.exe (PID: 6252)
- csrss1.exe (PID: 3836)
- chrome.exe (PID: 2828)
- ShellExperienceHost.exe (PID: 1572)
- msedge.exe (PID: 3732)
- csrss2.exe (PID: 5792)
- WaveCall.exe (PID: 6576)
- identity_helper.exe (PID: 6776)
Creates files or folders in the user directory
- WaveCall.exe (PID: 6576)
Process checks computer location settings
- WaveCall.exe (PID: 6576)
- chrome.exe (PID: 2828)
- msedge.exe (PID: 3732)
Checks proxy server information
- WaveCall.exe (PID: 6252)
- chrome.exe (PID: 2828)
- msedge.exe (PID: 3732)
.NET Reactor protector has been detected
- WaveCall.exe (PID: 6252)
Reads the software policy settings
- WaveCall.exe (PID: 6252)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4668)
- powershell.exe (PID: 6968)
- powershell.exe (PID: 3900)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6968)
- powershell.exe (PID: 4668)
- powershell.exe (PID: 3900)
Create files in a temporary directory
- WaveCall.exe (PID: 6252)
- chrome.exe (PID: 2828)
- msedge.exe (PID: 3732)
- WaveCall.exe (PID: 6576)
Drops encrypted VBS script (Microsoft Script Encoder)
- fontdrvhost.exe (PID: 6136)
Executable content was dropped or overwritten
- msedge.exe (PID: 5240)
Sends debugging messages
- chrome.exe (PID: 2828)
- msedge.exe (PID: 3732)
- fontdrvhost.exe (PID: 6136)
- ShellExperienceHost.exe (PID: 1572)
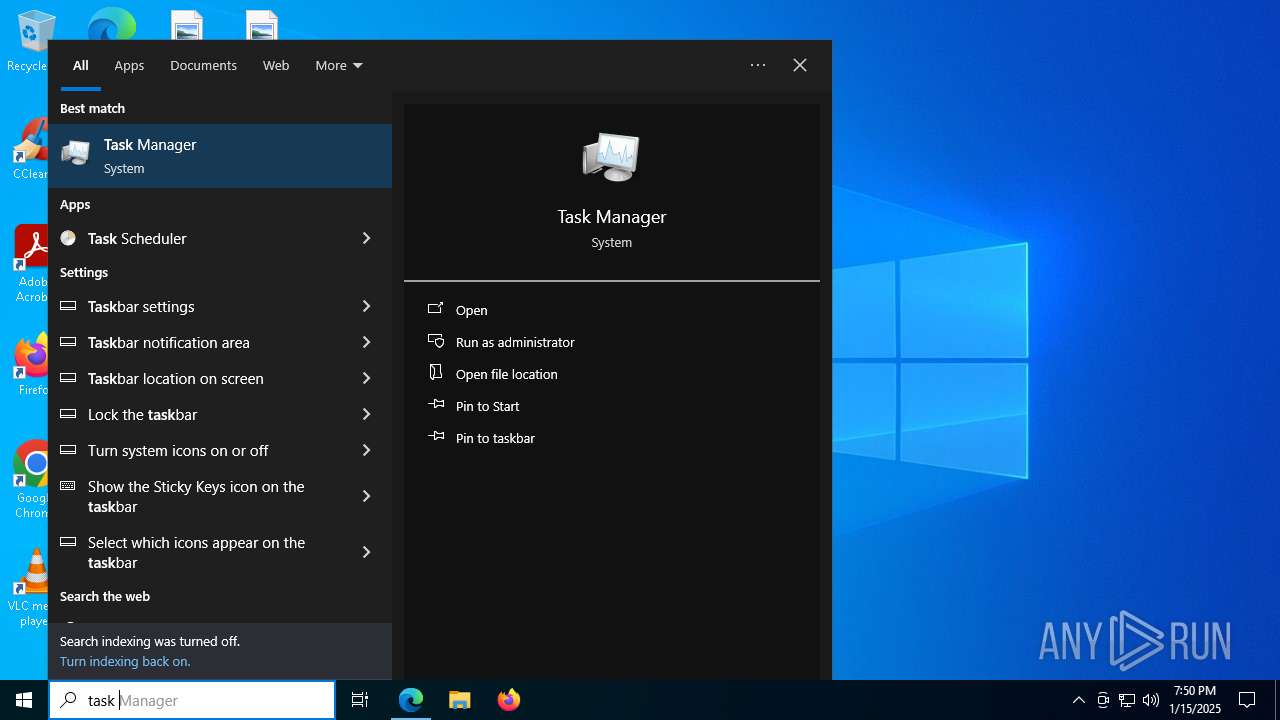
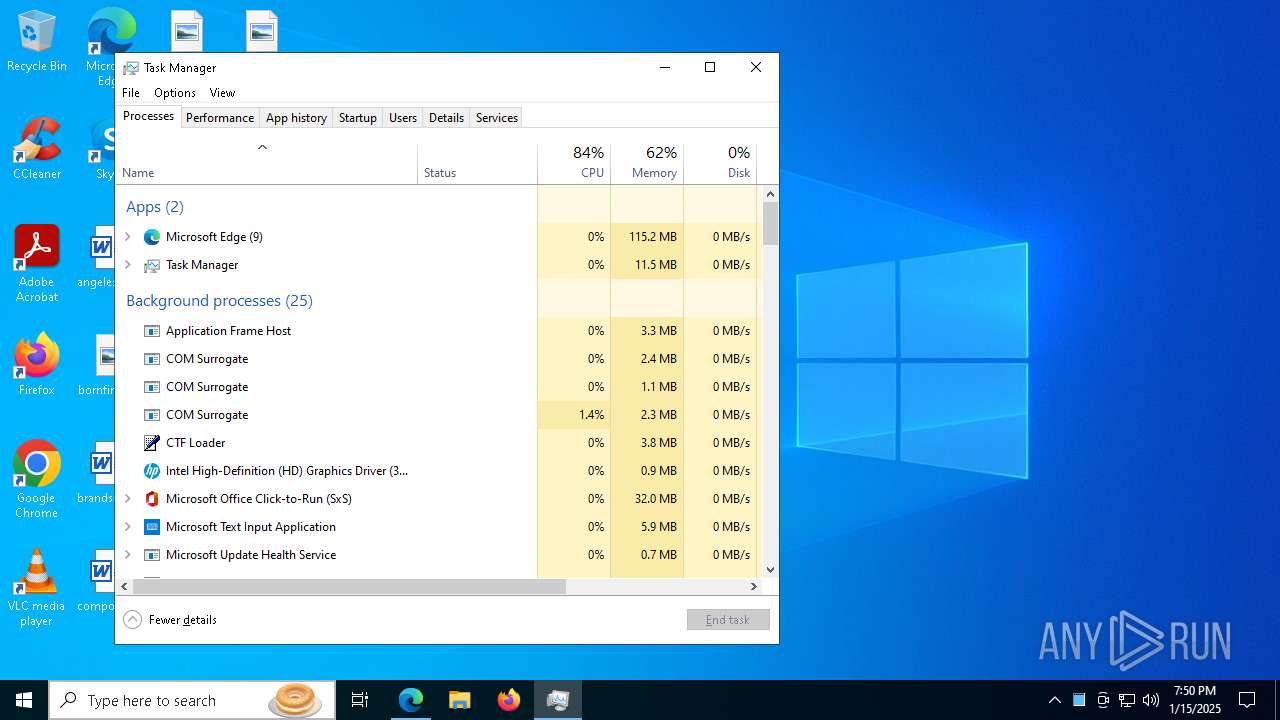
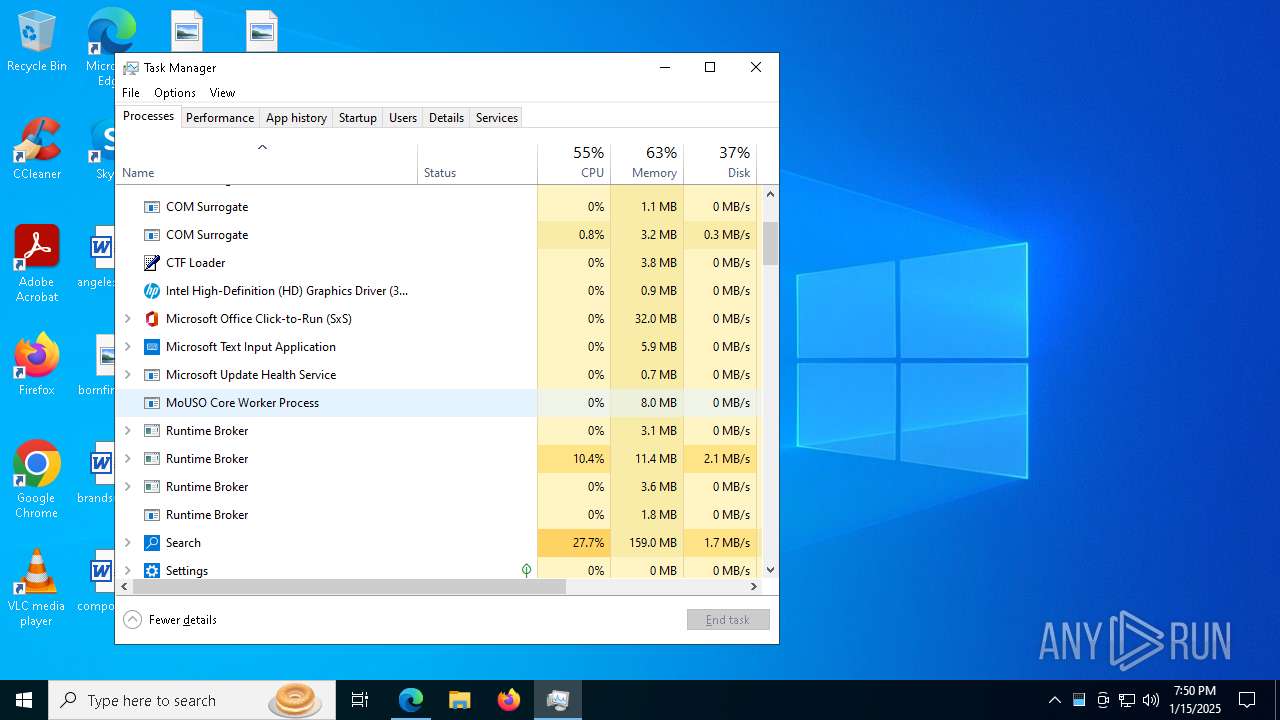
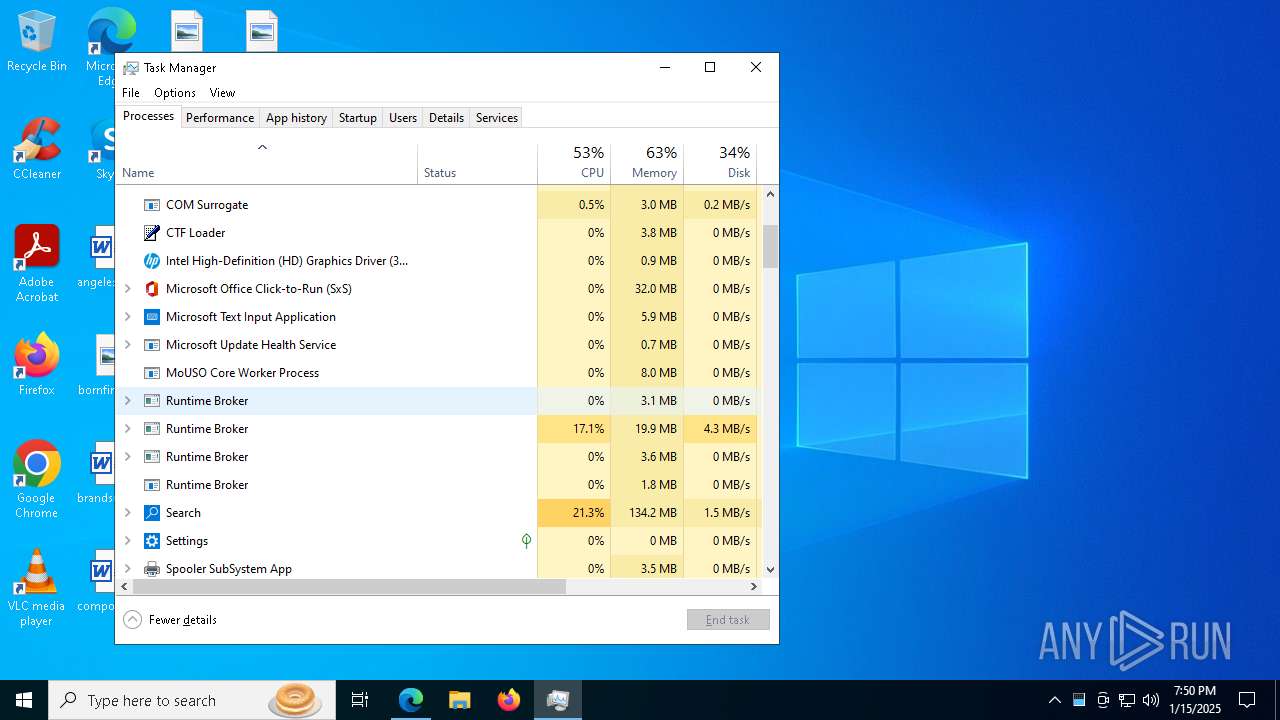
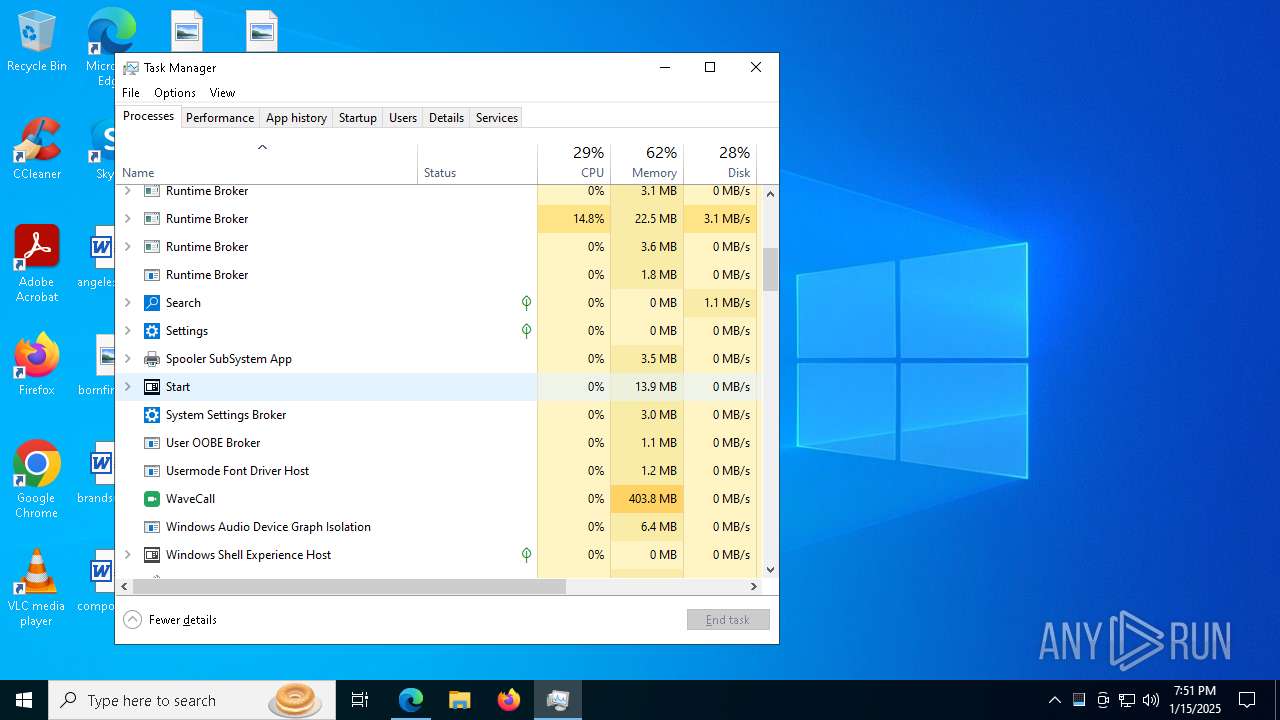
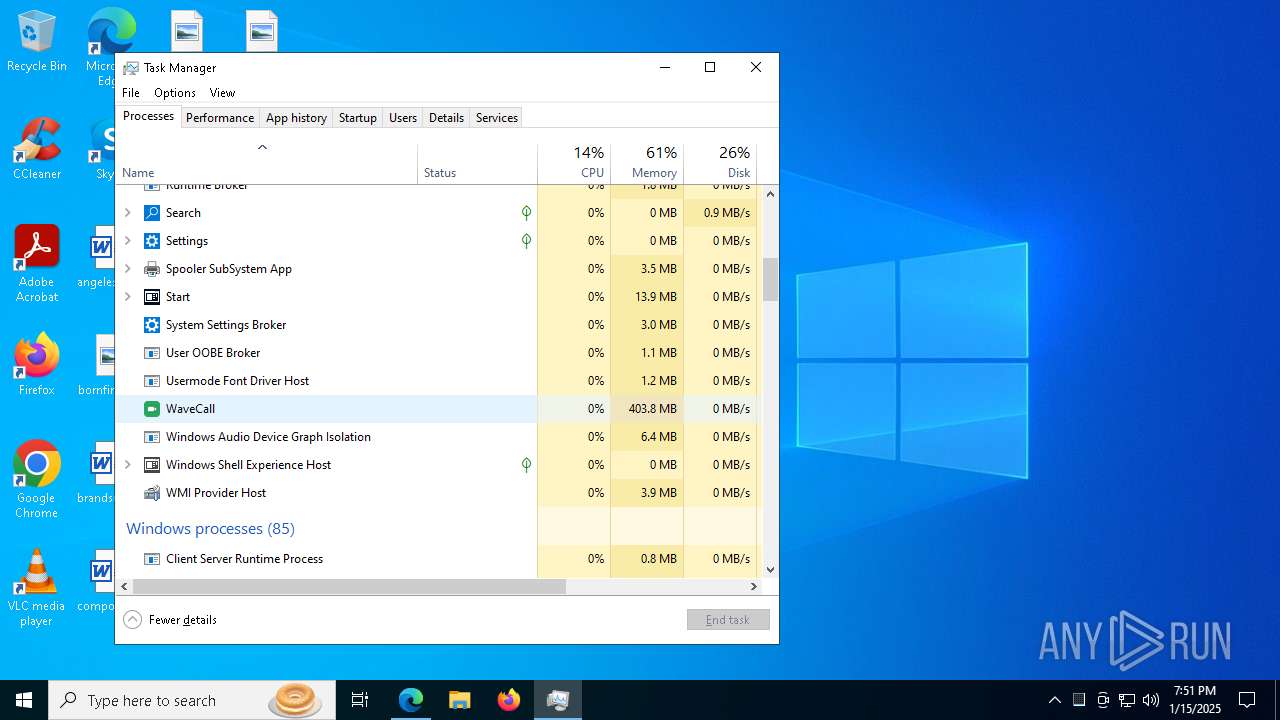
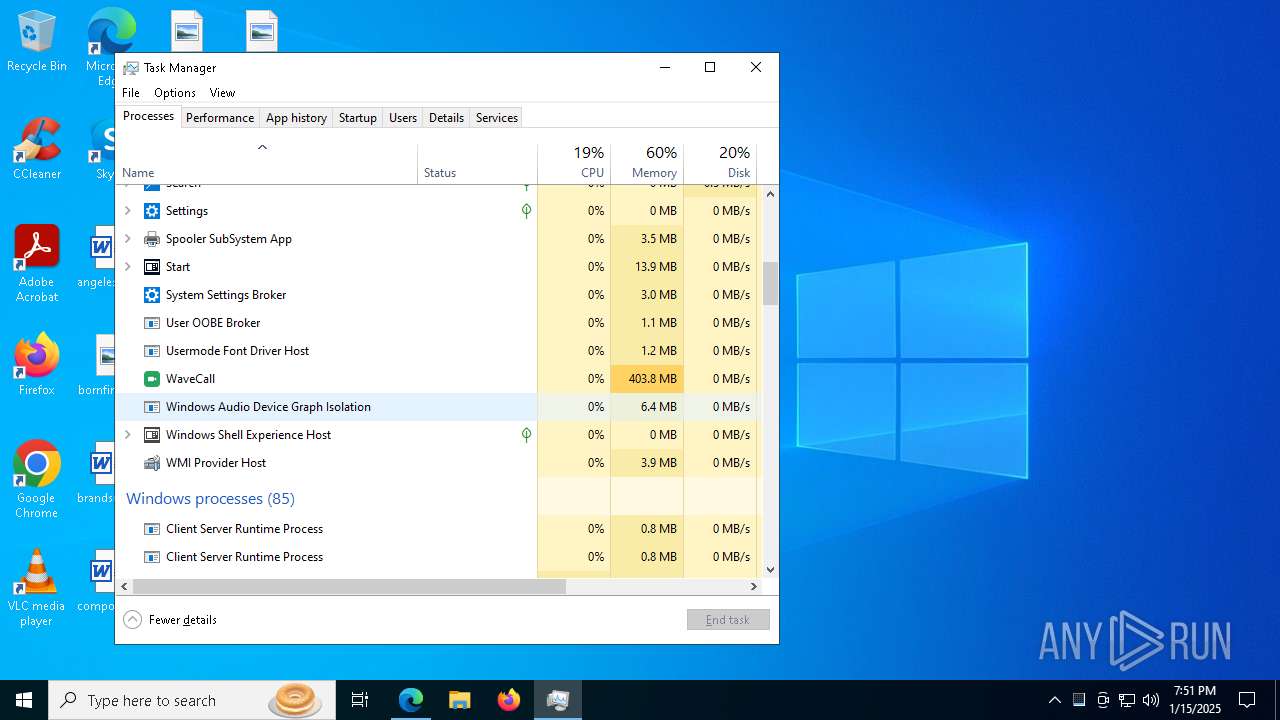
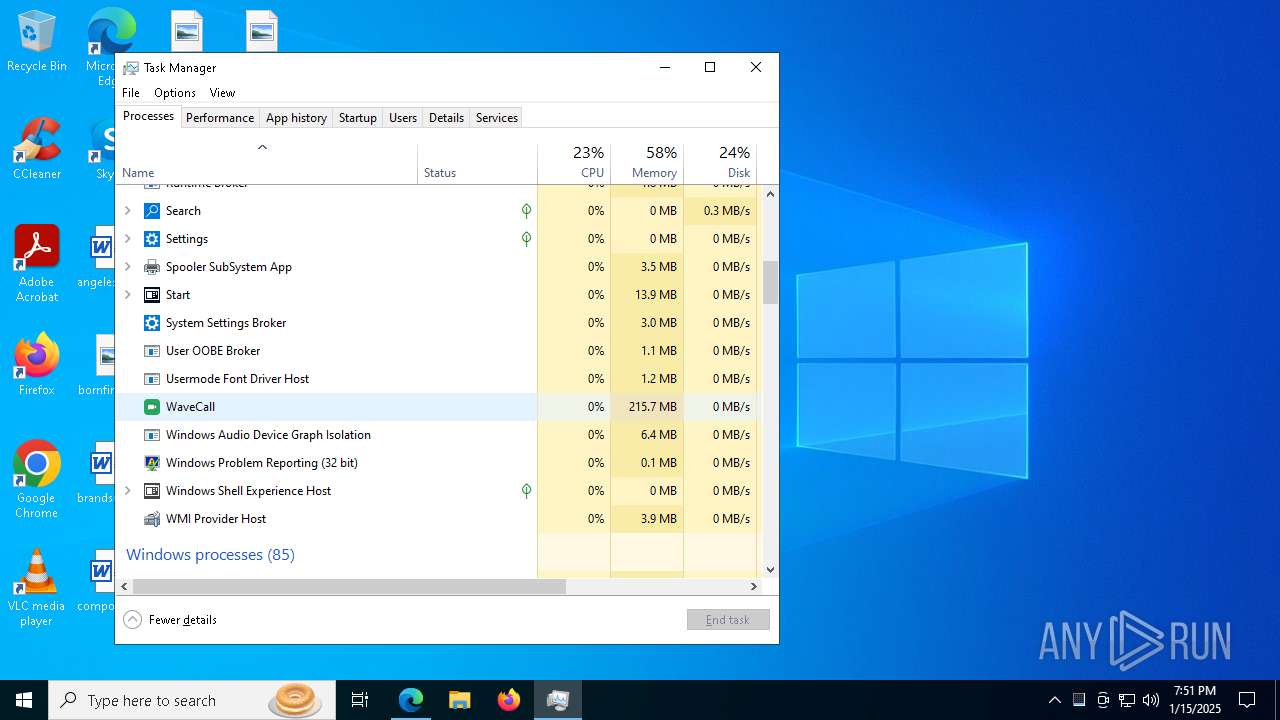
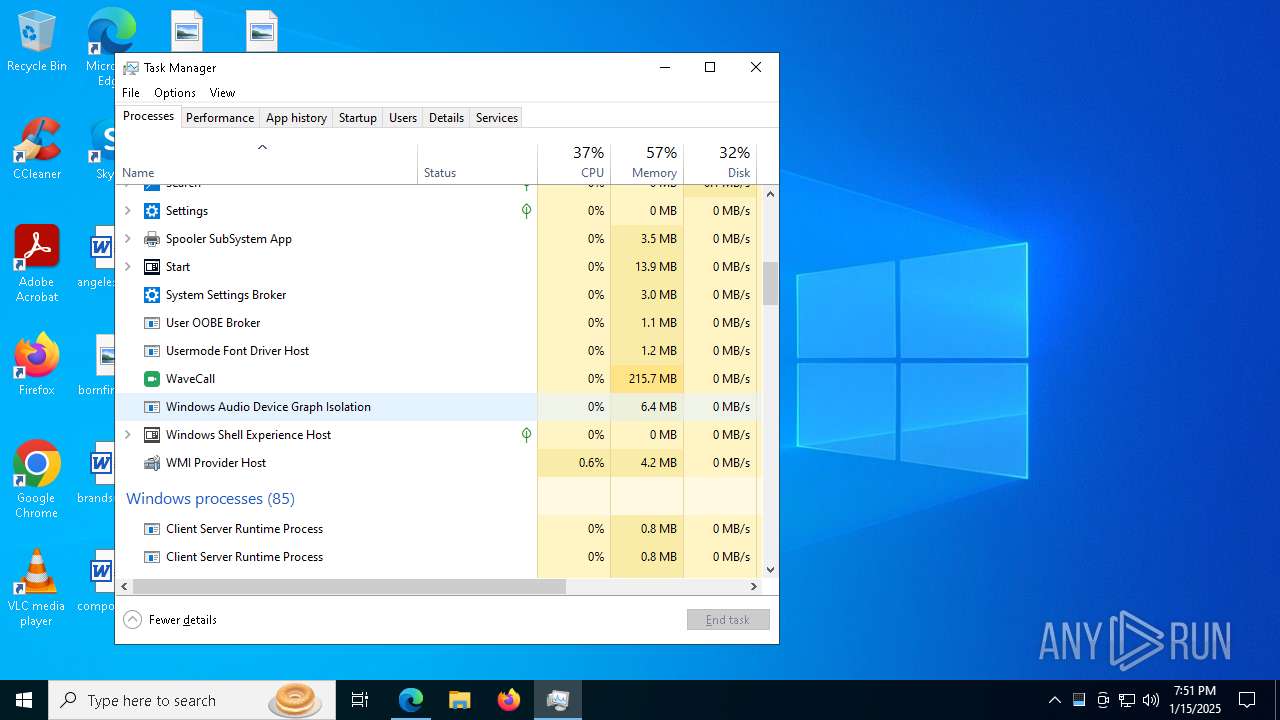
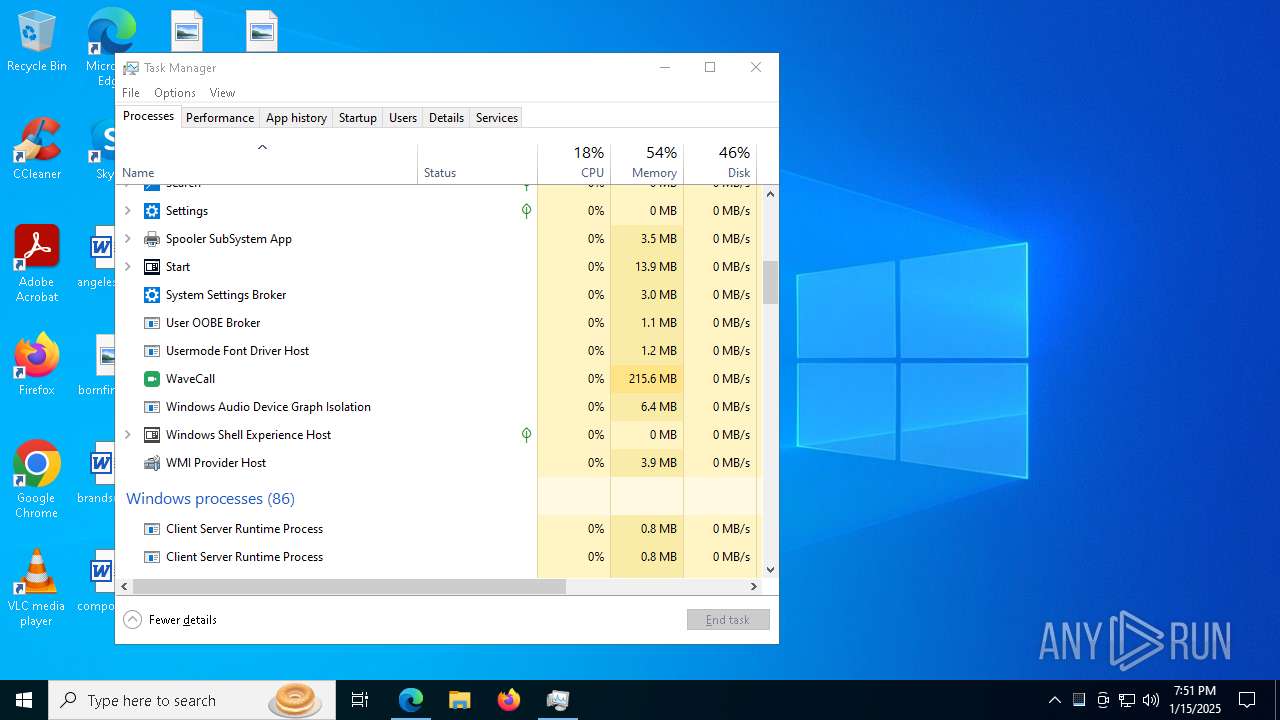
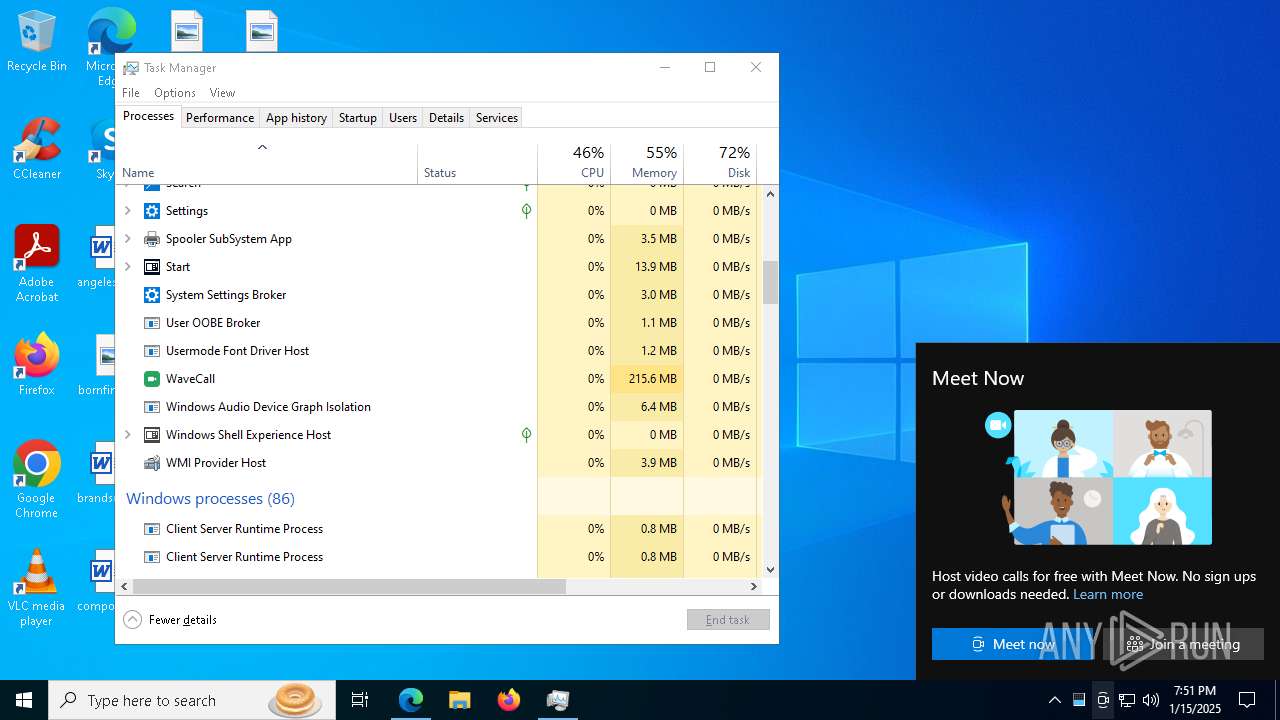
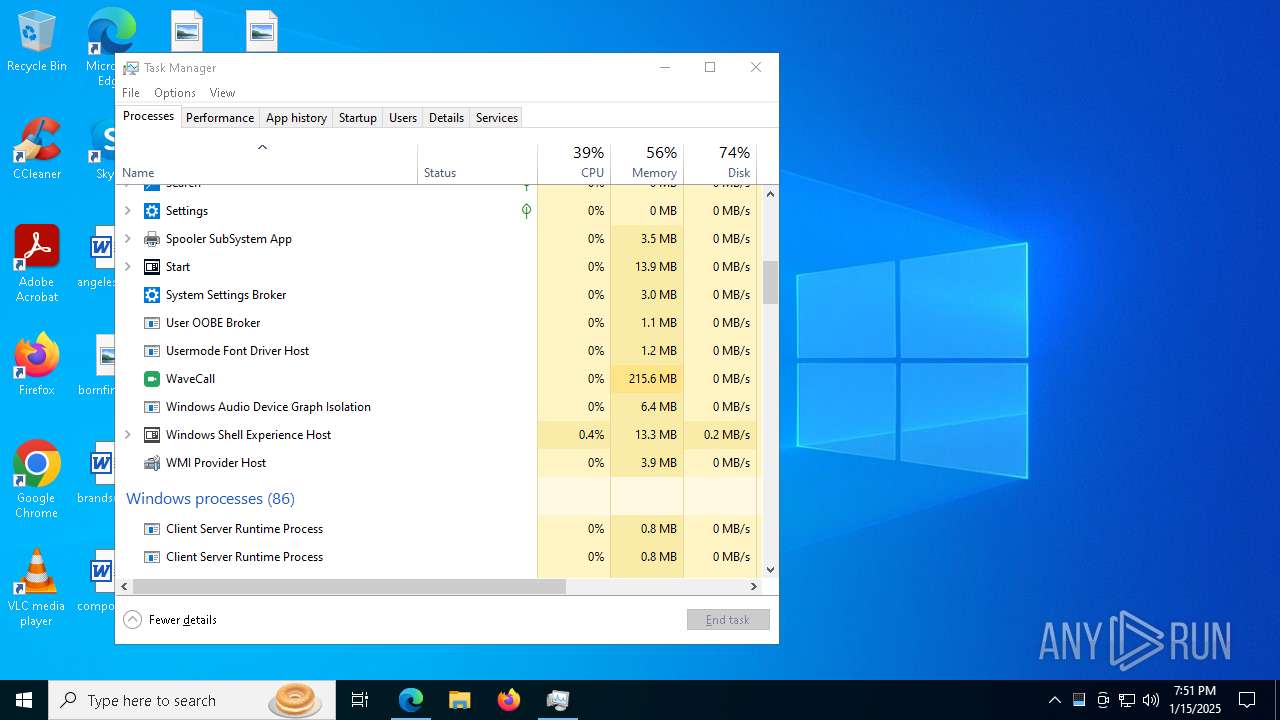
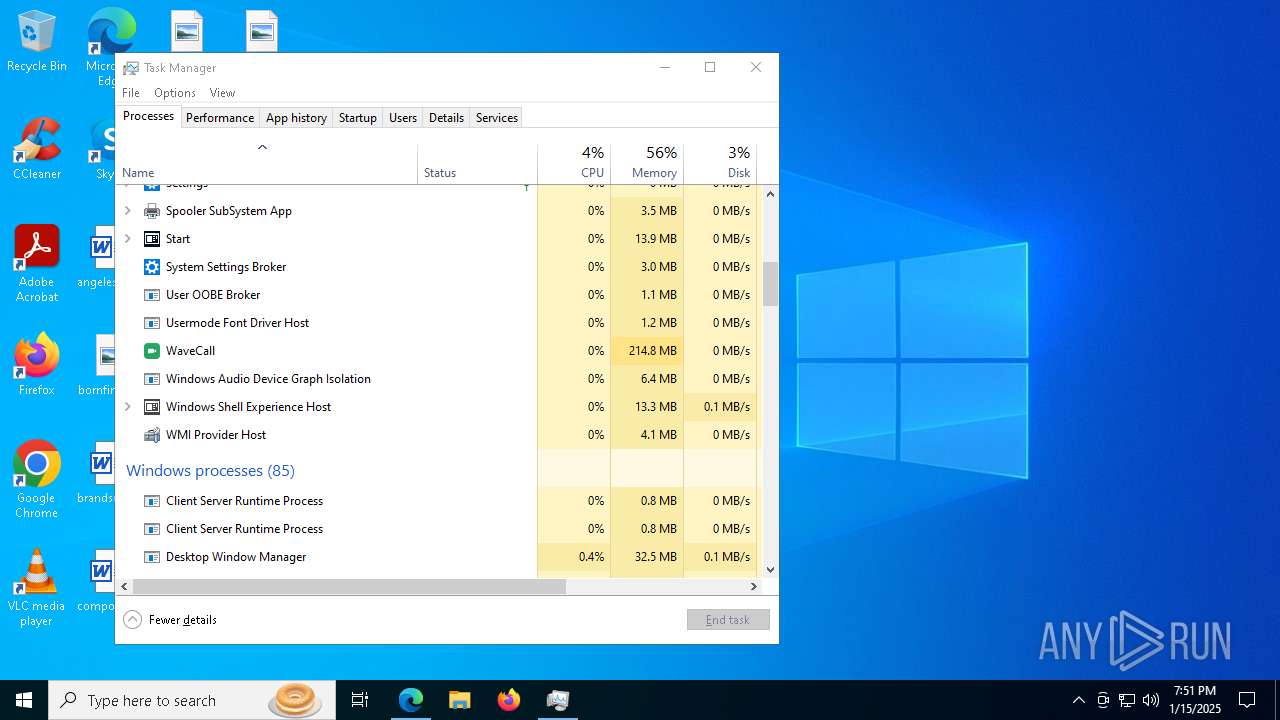
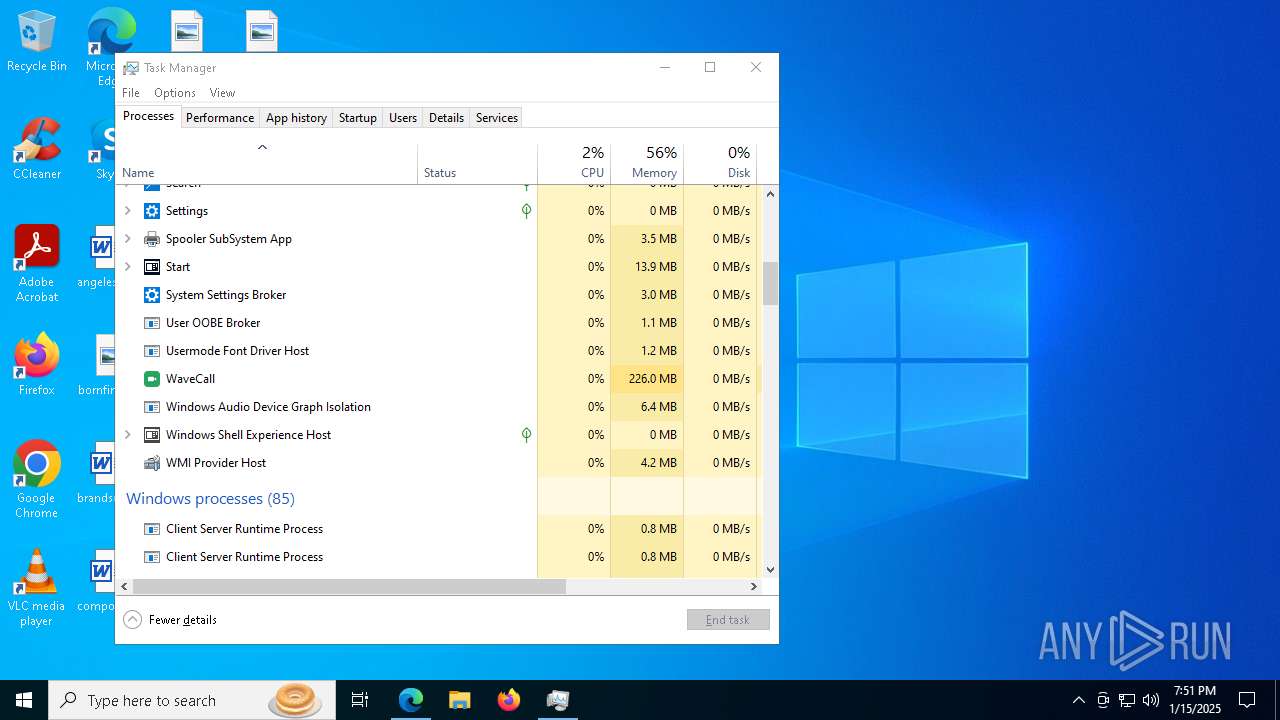
Manual execution by a user
- msedge.exe (PID: 6288)
- Taskmgr.exe (PID: 5776)
- Taskmgr.exe (PID: 7092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
245
Monitored processes
103
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 308 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6620 --field-trial-handle=2228,i,16711913267276954070,17243384243017082073,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 640 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6816 --field-trial-handle=2228,i,16711913267276954070,17243384243017082073,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 772 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7260 --field-trial-handle=2228,i,16711913267276954070,17243384243017082073,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=3640 --field-trial-handle=1980,i,2845704463255404696,8997488562470294339,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1344 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=2300 --field-trial-handle=2324,i,15054190425648176118,11289056648781076469,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2256 --field-trial-handle=1980,i,2845704463255404696,8997488562470294339,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1572 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1580 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6764 --field-trial-handle=2228,i,16711913267276954070,17243384243017082073,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Local\Temp\chrA389.tmp /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\Temp\chrA389.tmp\Crashpad --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x288,0x28c,0x290,0x280,0x298,0x7ff818625fd8,0x7ff818625fe4,0x7ff818625ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
33 388
Read events
33 321
Write events
47
Delete events
20
Modification events
| (PID) Process: | (6164) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328426 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CC740F76-F6AB-4507-B6CE-7DE5C370A9C4} | |||
| (PID) Process: | (6164) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328426 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {ABB6C922-8EDA-47DF-AC55-9108B08ECAB4} | |||
| (PID) Process: | (6164) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6164) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6164) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6164) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6164) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: FF5078385A8A2F00 | |||
| (PID) Process: | (6164) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 816A80385A8A2F00 | |||
| (PID) Process: | (6164) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328426 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F89BA090-15A1-4A63-902E-458122EE5684} | |||
| (PID) Process: | (6164) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C0C0B2385A8A2F00 | |||
Executable files
482
Suspicious files
607
Text files
136
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6164 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1367b6.TMP | — | |
MD5:— | SHA256:— | |||
| 6164 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6164 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1367b6.TMP | — | |
MD5:— | SHA256:— | |||
| 6164 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1367b6.TMP | — | |
MD5:— | SHA256:— | |||
| 6164 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1367b6.TMP | — | |
MD5:— | SHA256:— | |||
| 6164 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6164 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6164 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6164 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1367c6.TMP | — | |
MD5:— | SHA256:— | |||
| 6164 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
113
DNS requests
118
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5732 | svchost.exe | GET | 200 | 184.24.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5732 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4624 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4624 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2424 | svchost.exe | HEAD | 200 | 84.201.210.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1737475195&P2=404&P3=2&P4=eEtHkxwbh8T%2bFNBtditC9mmunJsE3dogGzRoRFEnzEVEi0B9T4TpZsbi1y0dzP9c8arjJad2Mam%2fhNoxQ7%2fA8A%3d%3d | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5732 | svchost.exe | 184.24.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.24.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5732 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.139:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6164 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6484 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
wavecall.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6484 | msedge.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup Domain (ipapi .co in DNS lookup) |
6484 | msedge.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup Domain (ipapi .co in DNS lookup) |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
6136 | fontdrvhost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
2728 | OOBE-Maintenance.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
2192 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
6 ETPRO signatures available at the full report
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr955F.tmp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chrA389.tmp directory exists )
|
fontdrvhost.exe | [thresholding] image = 00000242361D9640 , (0 , 1341) (0 , 670)
|
fontdrvhost.exe | [thresholding] image = 000002423761D040 , (0 , 1713) (0 , 856)
|
fontdrvhost.exe | [thresholding] image = 00000242361D9640 , (0 , 1315) (0 , 658)
|
fontdrvhost.exe | [thresholding] image = 00000242375F6040 , (0 , 1692) (0 , 846)
|
fontdrvhost.exe | [thresholding] image = 0000024237508040 , (0 , 1538) (0 , 769)
|
OOBE-Maintenance.exe | [thresholding] image = 000001375F7065E0 , (0 , 1341) (0 , 670)
|
OOBE-Maintenance.exe | [thresholding] image = 0000013760A5D040 , (0 , 1713) (0 , 856)
|
OOBE-Maintenance.exe | [thresholding] image = 000001375F7065E0 , (0 , 1315) (0 , 658)
|