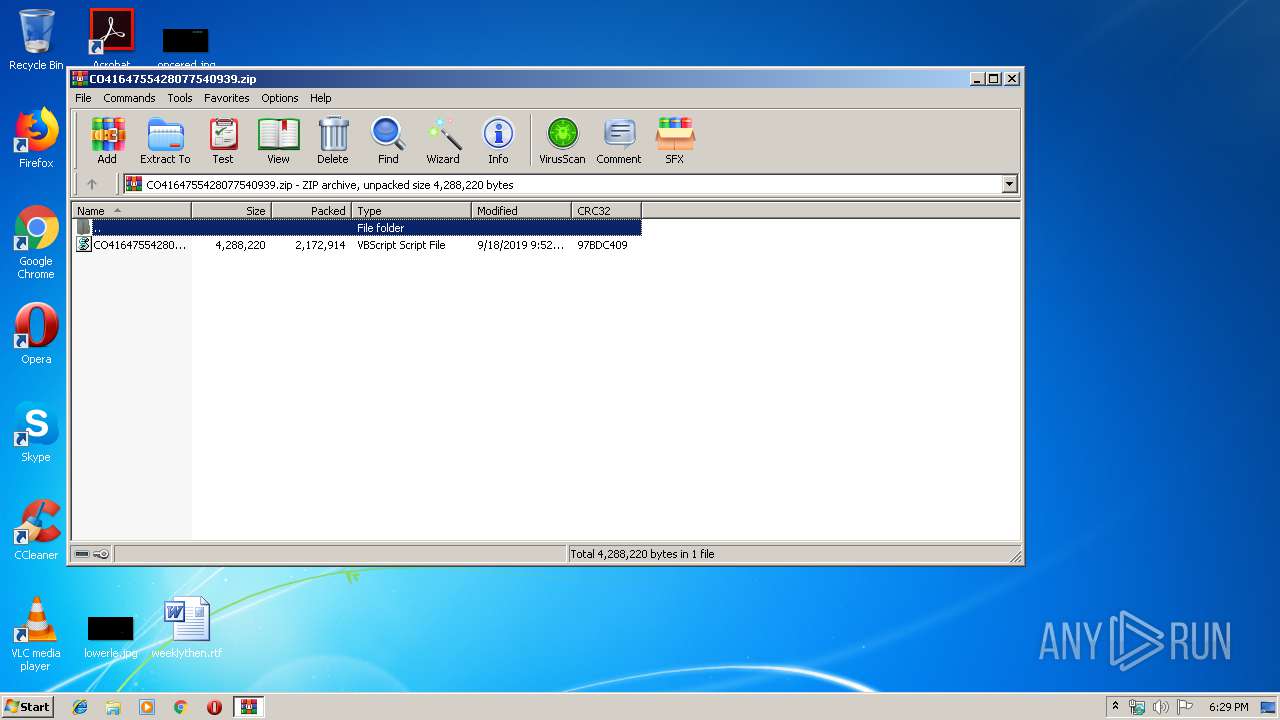
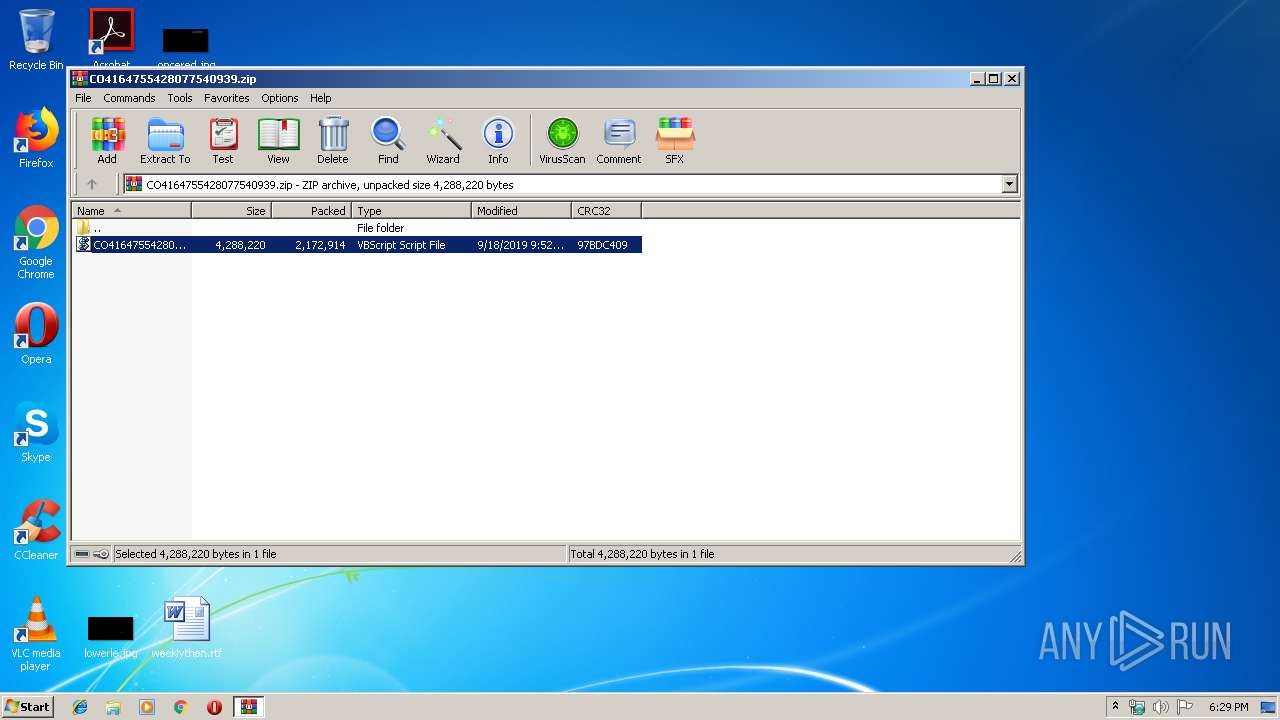
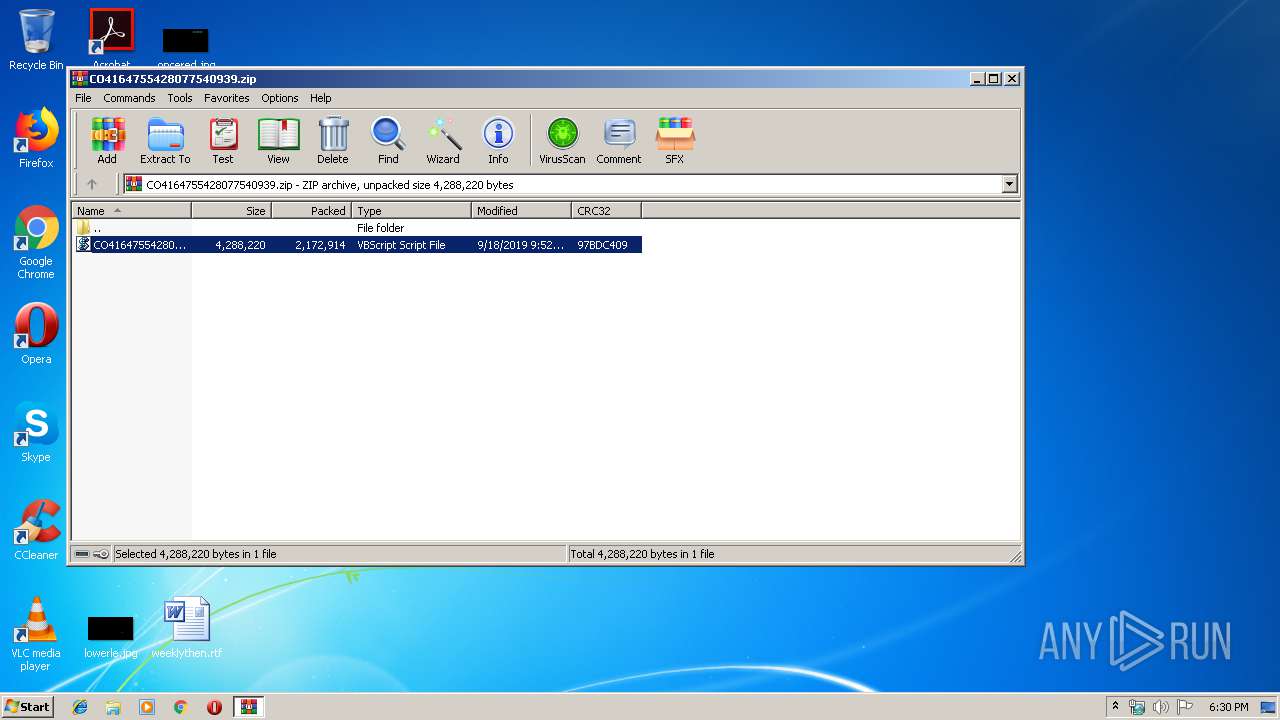
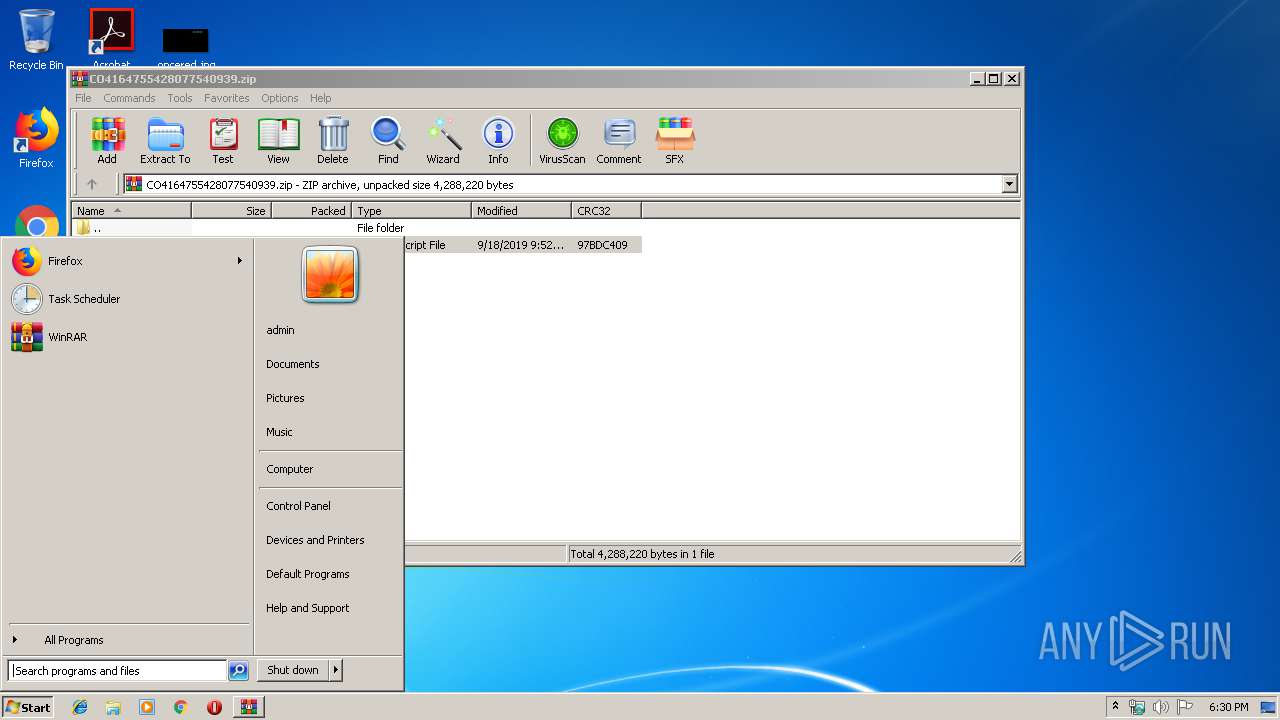
| download: | CO4164755428077540939.zip |
| Full analysis: | https://app.any.run/tasks/ca29d2bc-274a-4d42-a22b-7ddf97a4ef2d |
| Verdict: | Malicious activity |
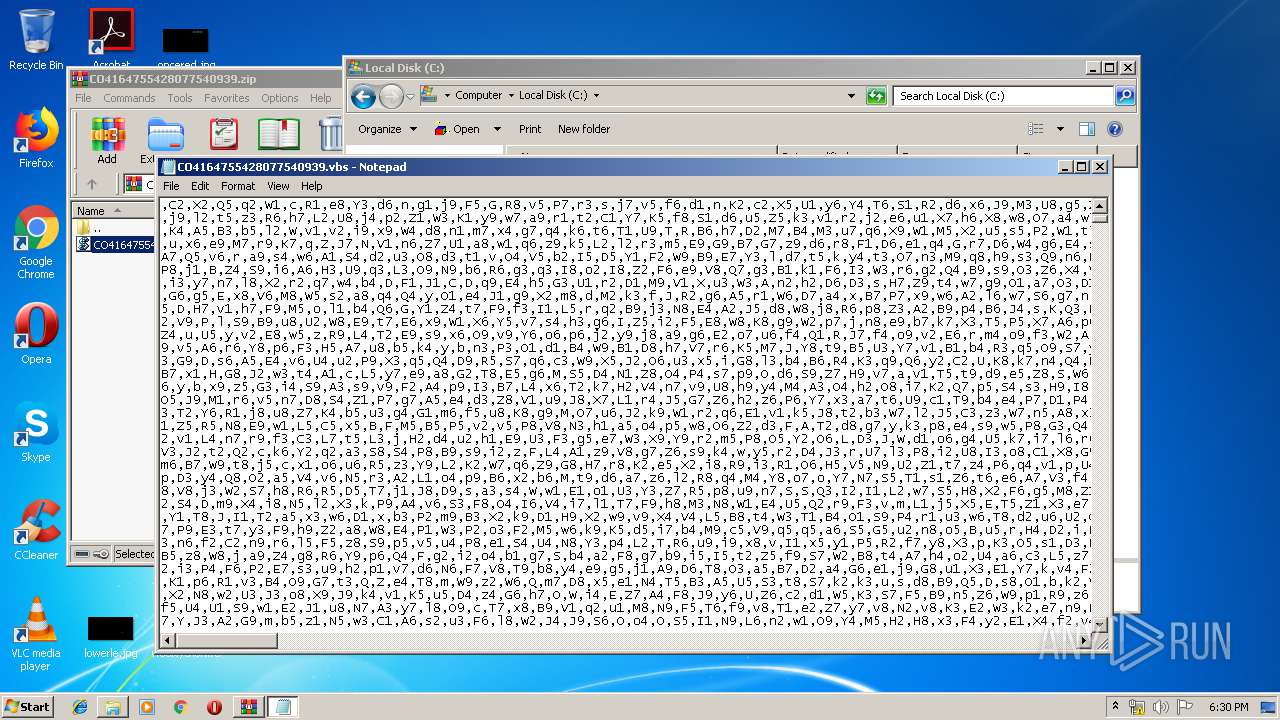
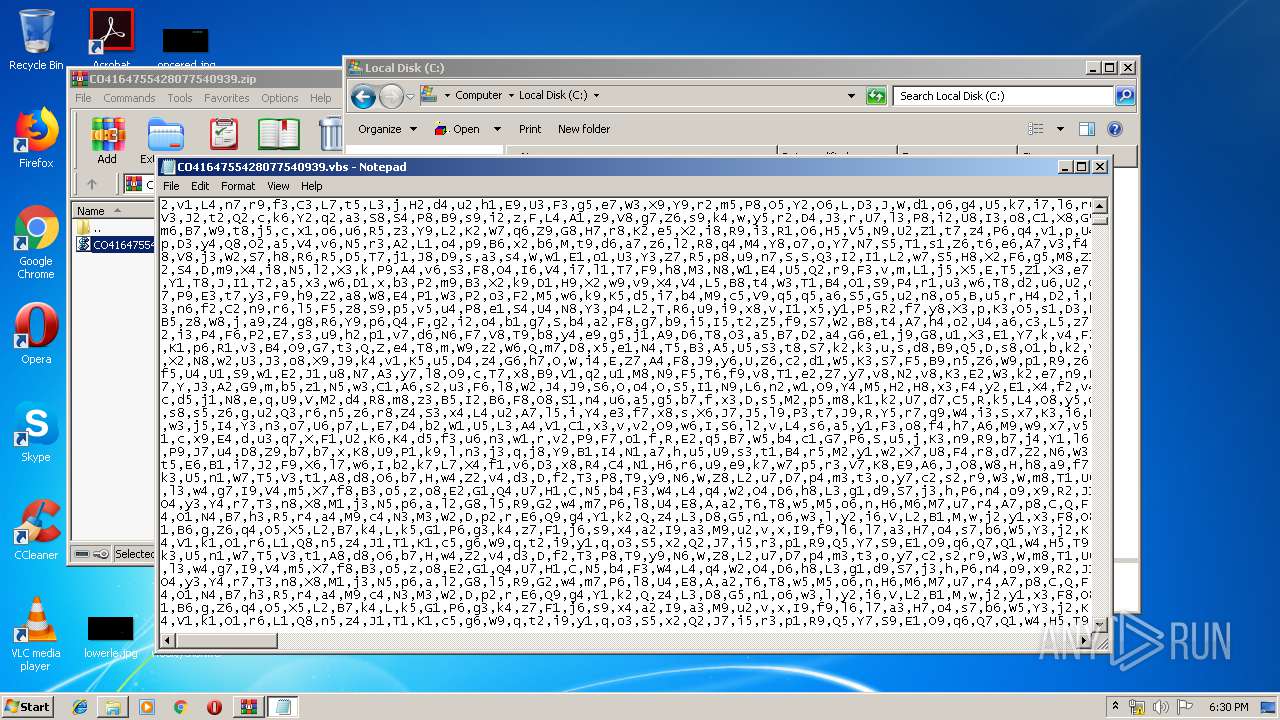
| Threats: | Qbot is a banking Trojan — a malware designed to collect banking information from victims. Qbot targets organizations mostly in the US. It is equipped with various sophisticated evasion and info-stealing functions and worm-like functionality, and a strong persistence mechanism. |
| Analysis date: | September 18, 2019, 17:29:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 2F3B8594EBD4ADBF31649619A2C402B7 |
| SHA1: | 4620C8A1D791318DEA600BD3B264E4B94C08EB9F |
| SHA256: | A825D47643CBBCFDC28388FC05E63F32BFE6F390D2EB99FA6D47A44E2764D248 |
| SSDEEP: | 49152:aKe//ZVuyr4xwUEeKRivzGmoxyTRnQ92PuFm/wEtPTV:a7zN0xw4K86meEnLGUwcV |
MALICIOUS
Application was dropped or rewritten from another process
- ACOQsTn.exe (PID: 3752)
- ACOQsTn.exe (PID: 3664)
- ytfovlym.exe (PID: 1816)
- ytfovlym.exe (PID: 2440)
QBOT was detected
- ACOQsTn.exe (PID: 3752)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2924)
SUSPICIOUS
Executable content was dropped or overwritten
- WScript.exe (PID: 2736)
- ACOQsTn.exe (PID: 3752)
- cmd.exe (PID: 2924)
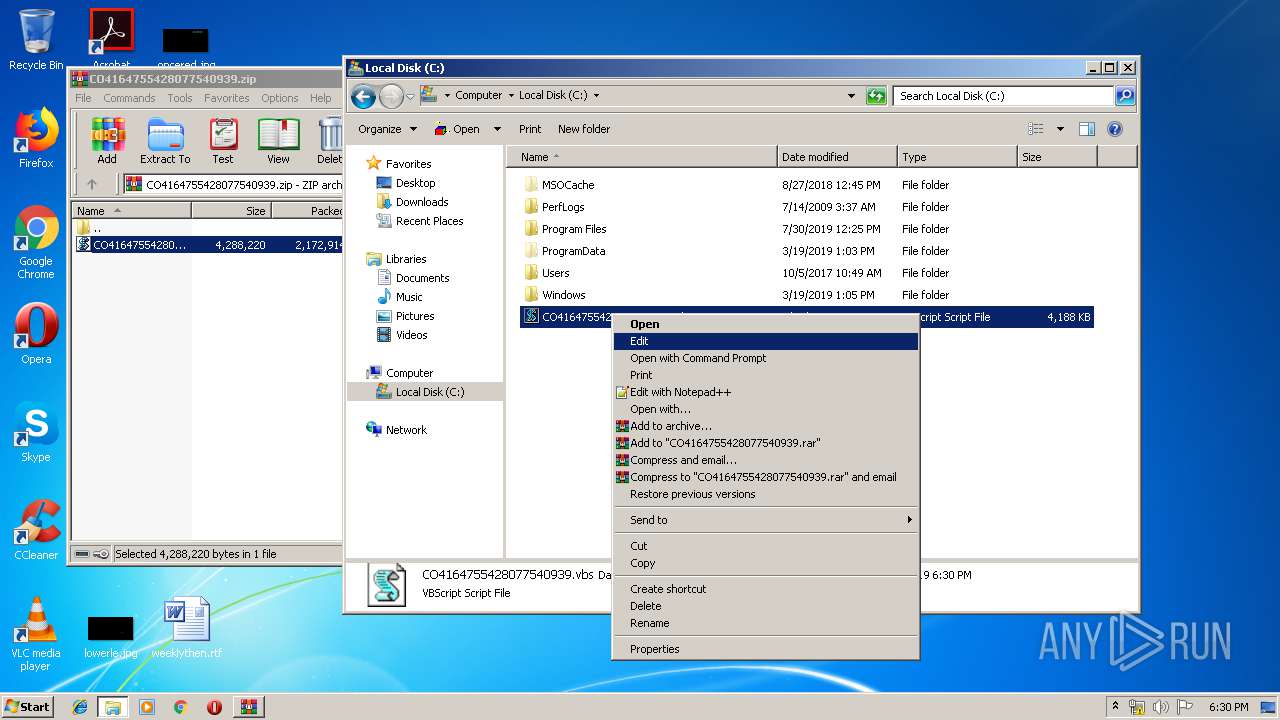
Executes scripts
- WinRAR.exe (PID: 2888)
Executed via WMI
- ACOQsTn.exe (PID: 3752)
Application launched itself
- WinRAR.exe (PID: 2888)
- ACOQsTn.exe (PID: 3752)
- ytfovlym.exe (PID: 1816)
Creates files in the user directory
- ACOQsTn.exe (PID: 3752)
Starts itself from another location
- ACOQsTn.exe (PID: 3752)
Starts CMD.EXE for commands execution
- ACOQsTn.exe (PID: 3752)
INFO
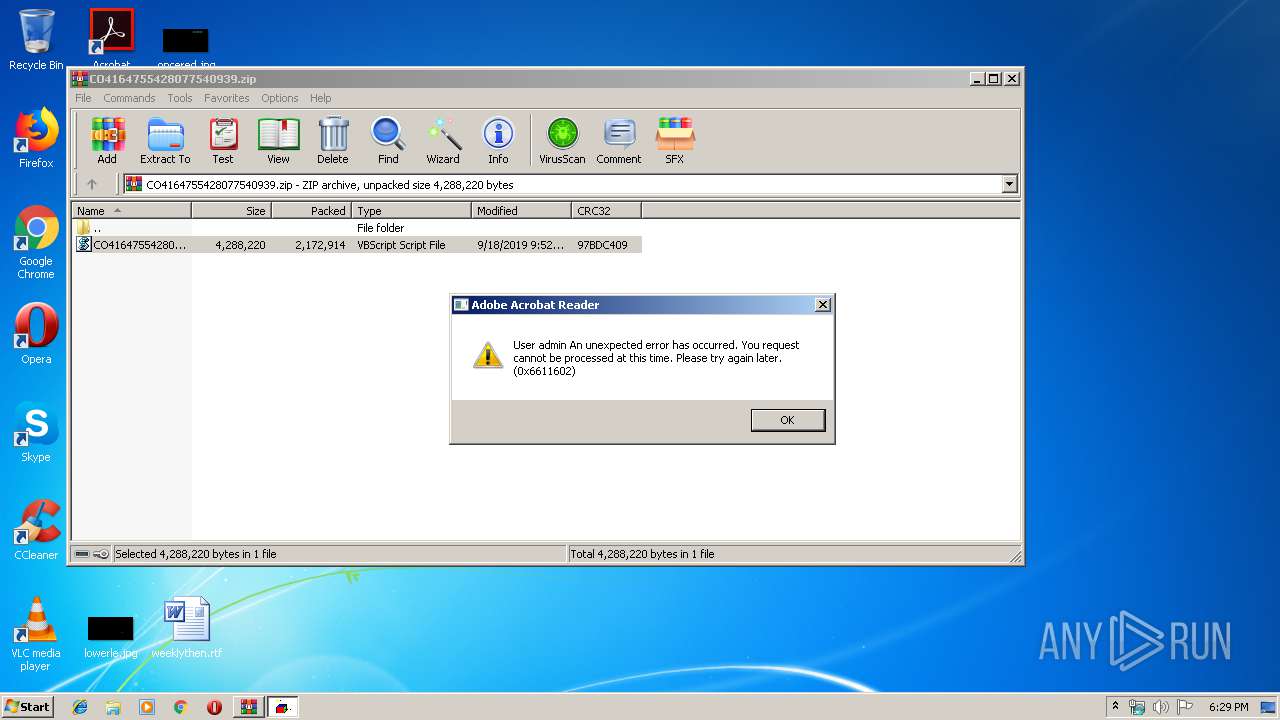
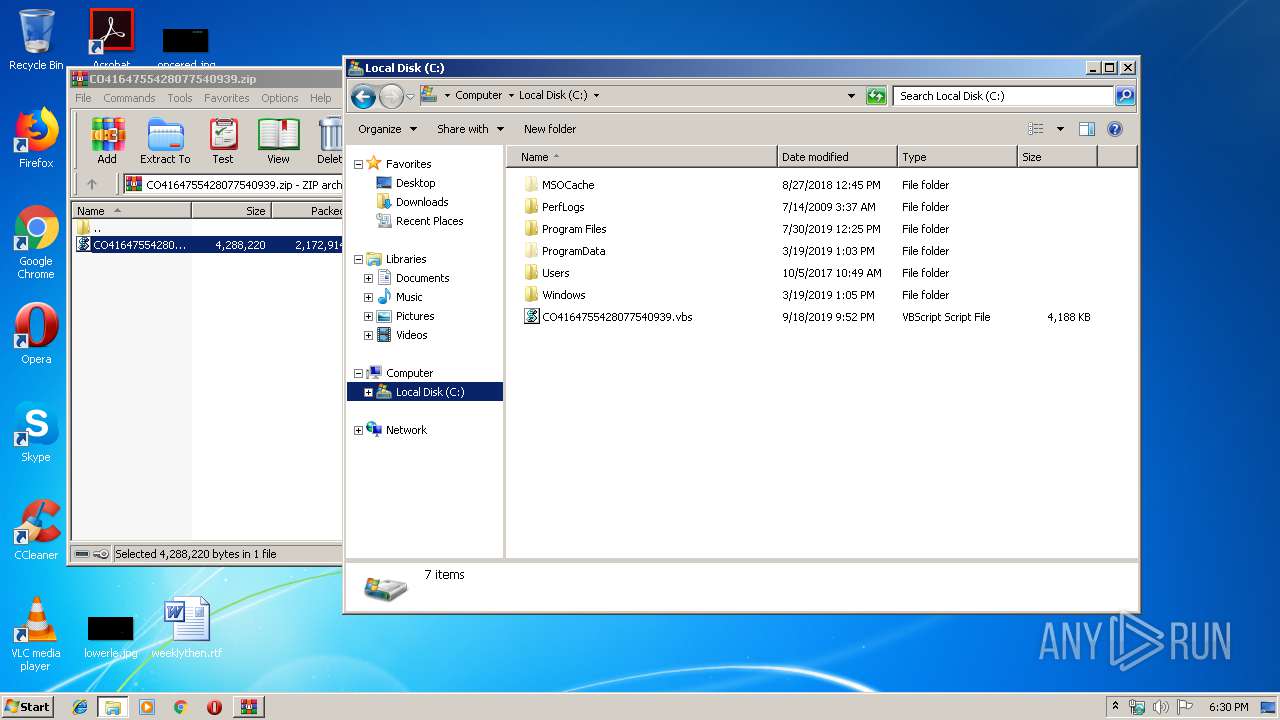
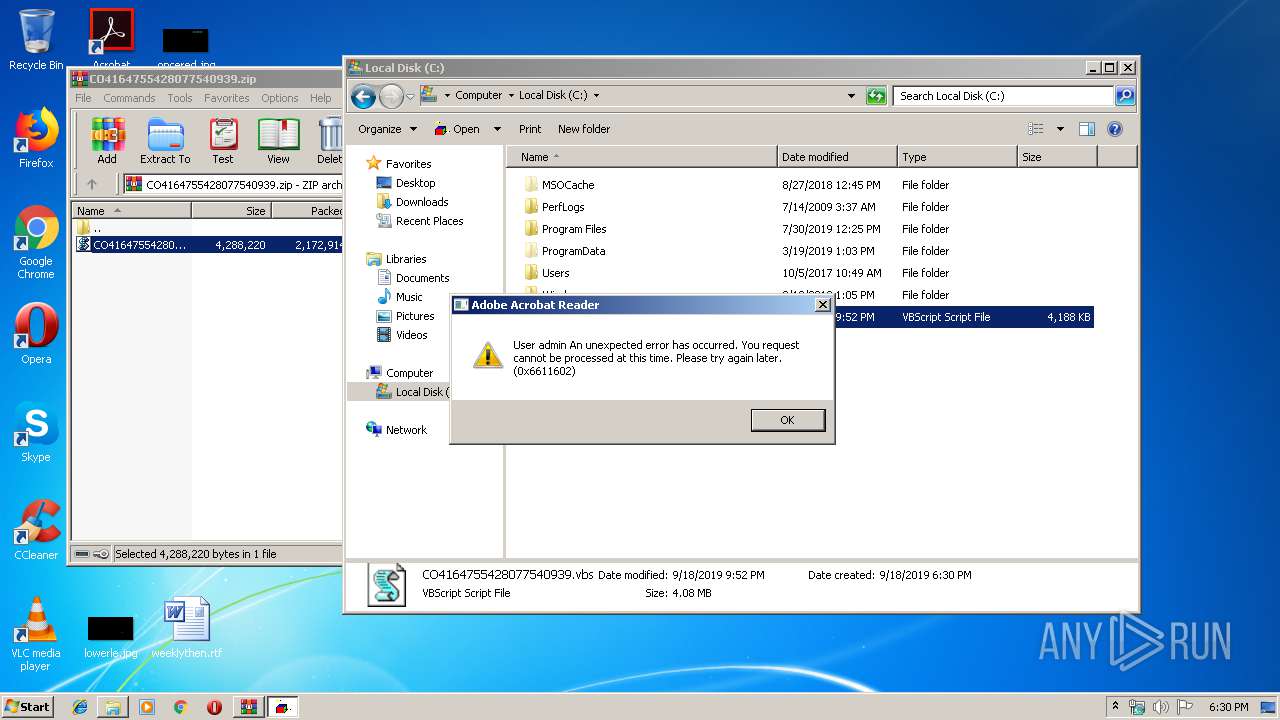
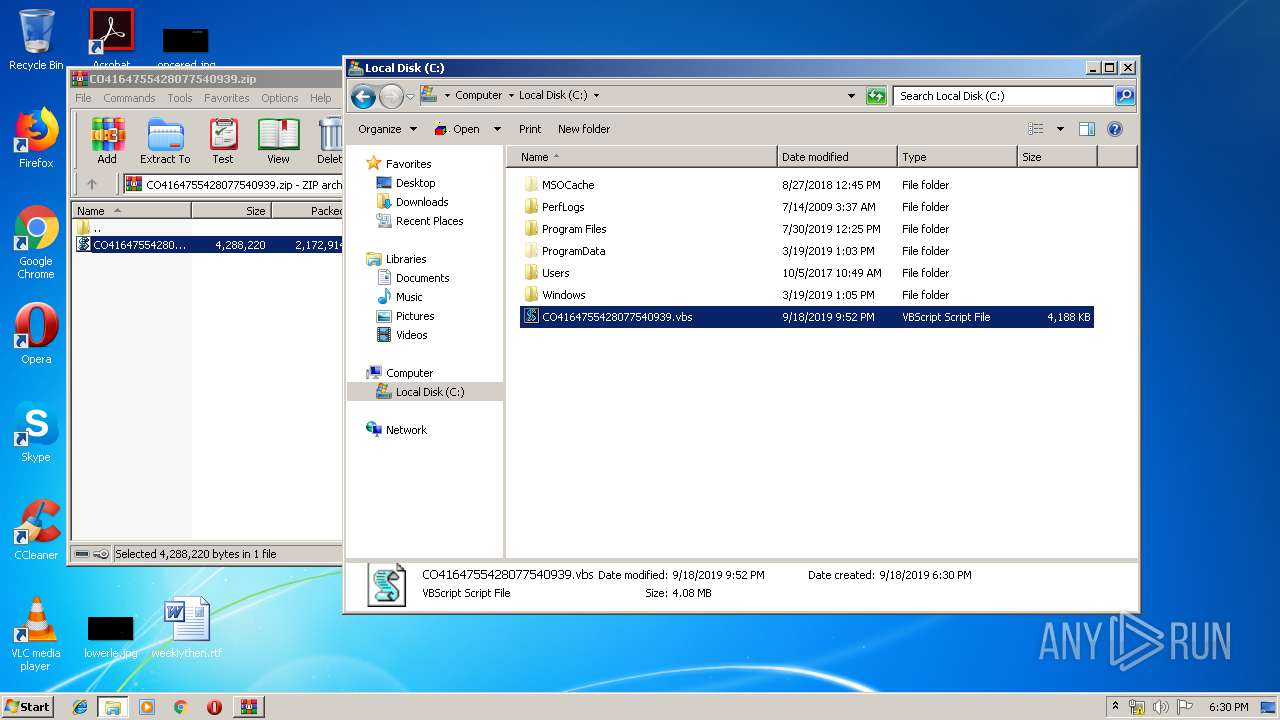
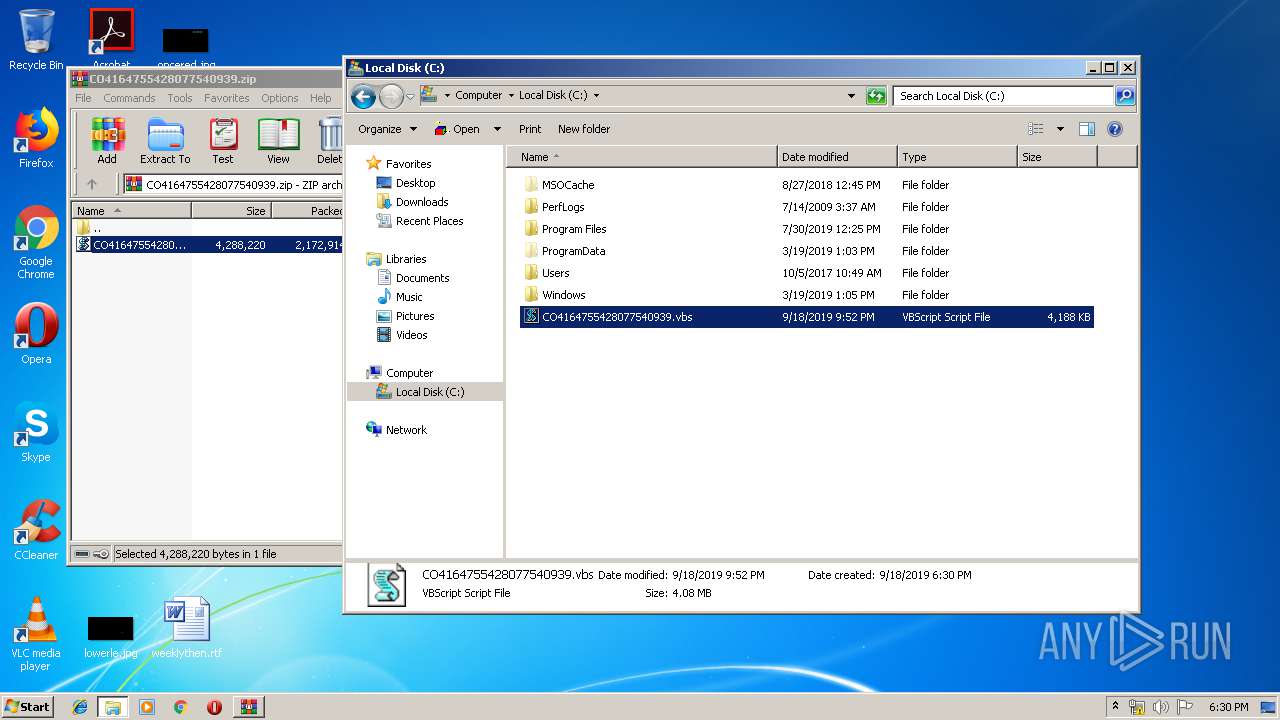
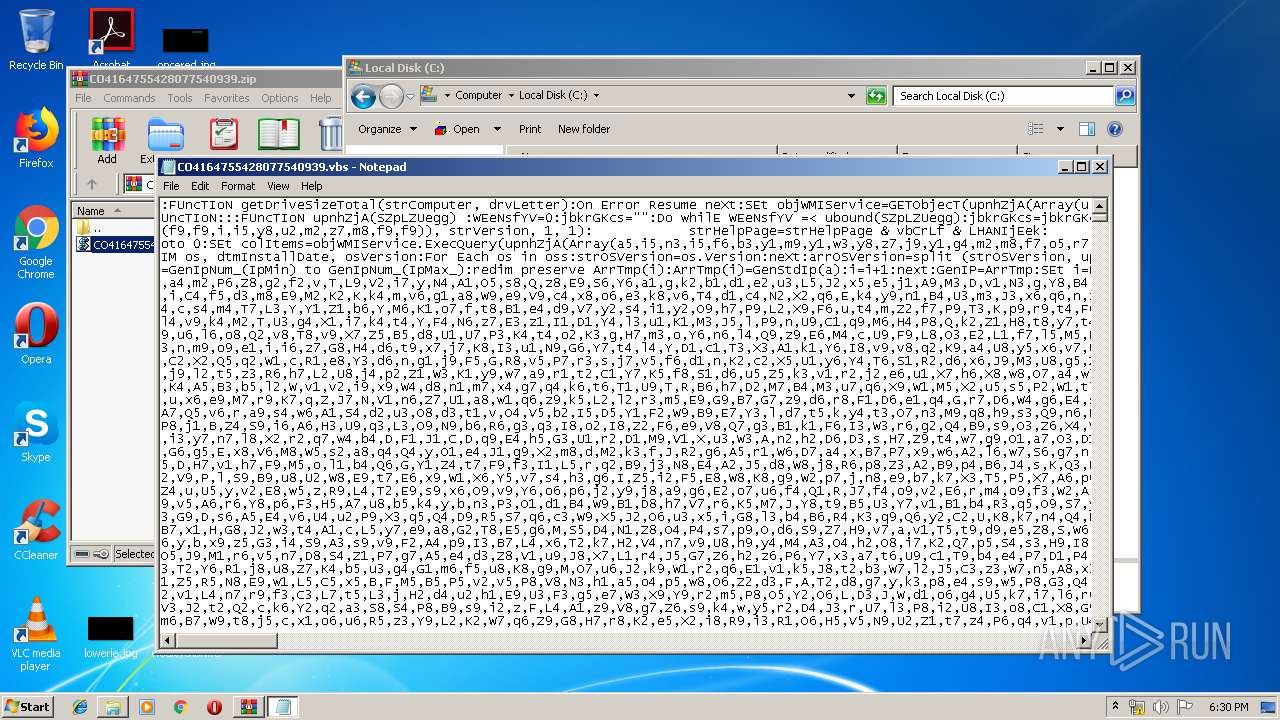
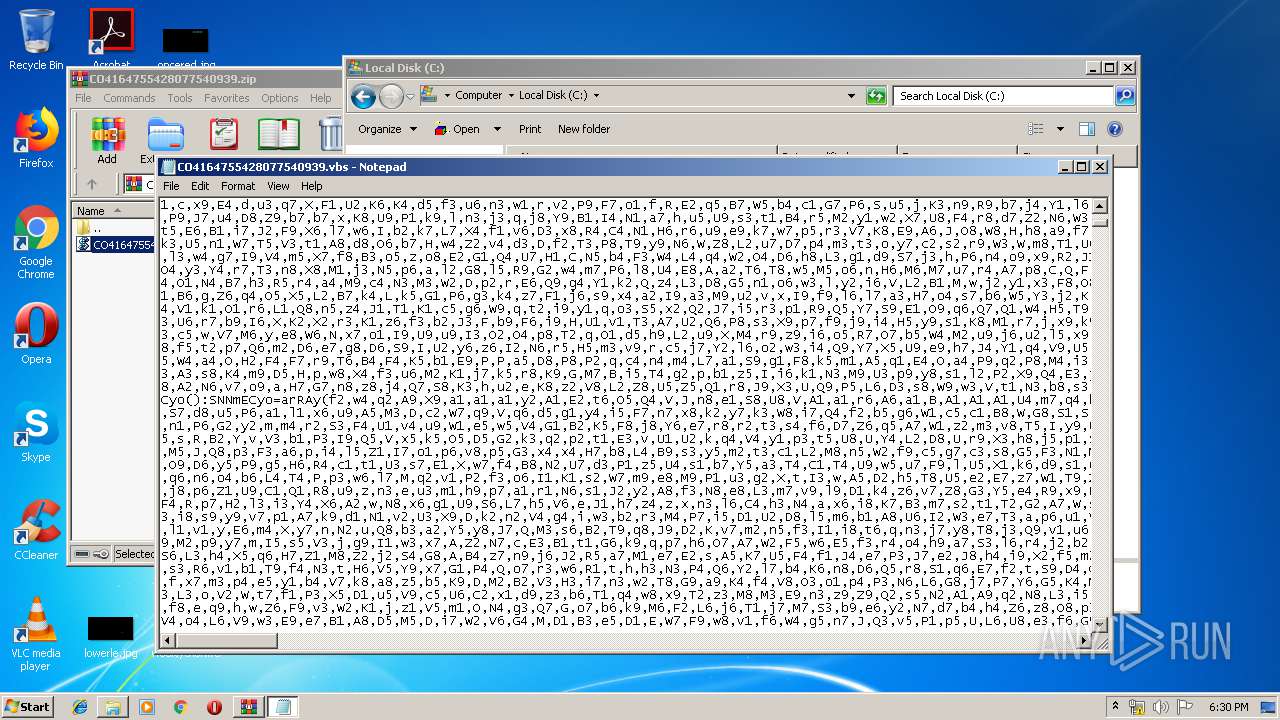
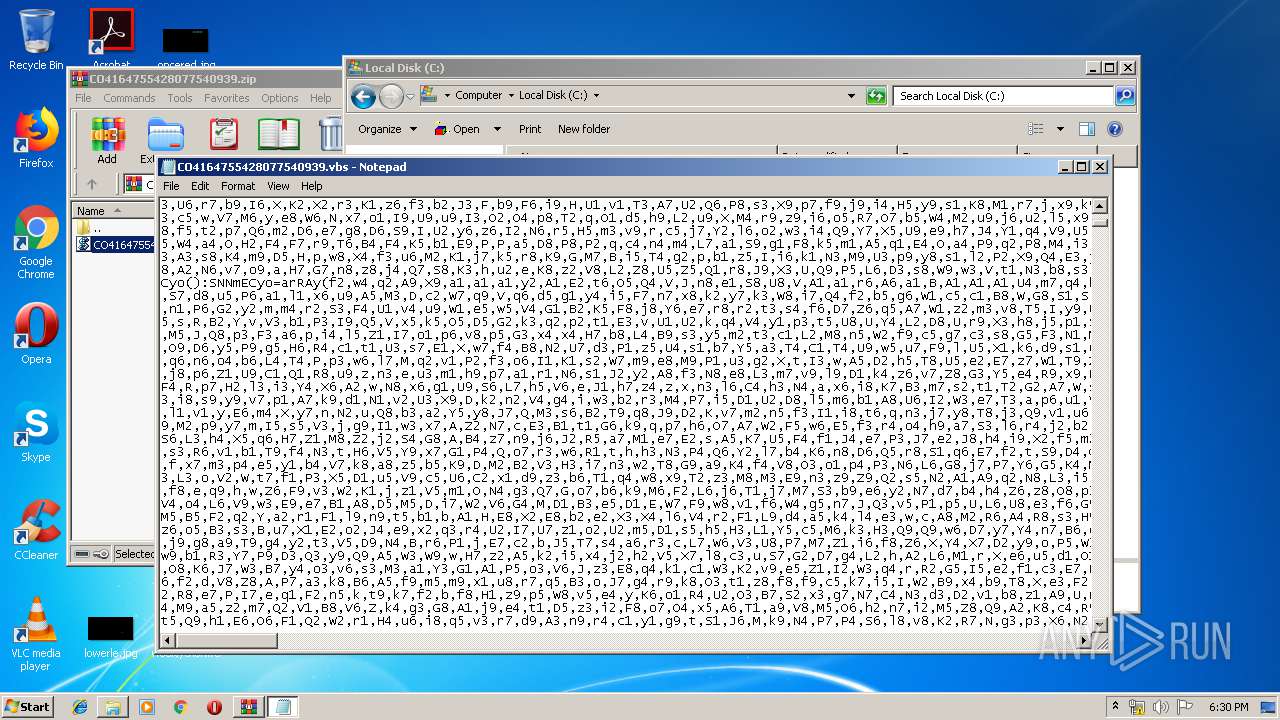
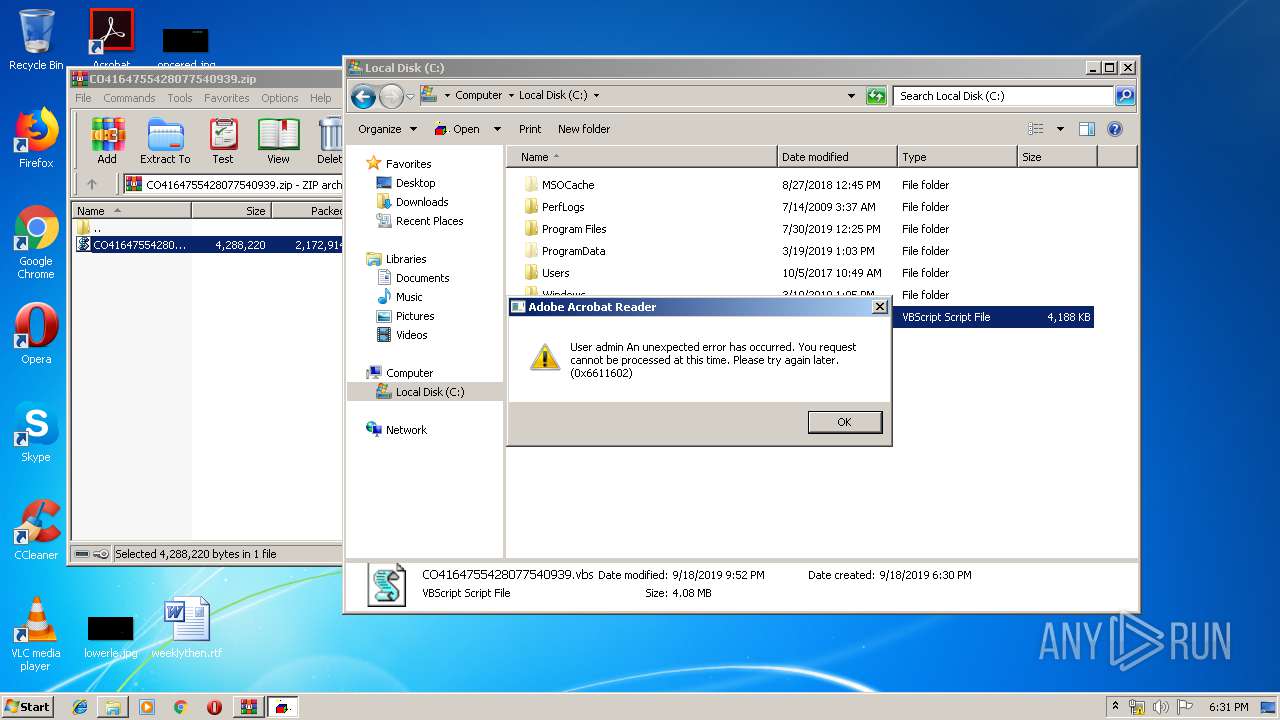
Manual execution by user
- explorer.exe (PID: 3860)
- WScript.exe (PID: 356)
- Notepad.exe (PID: 3168)
- WScript.exe (PID: 3832)
Dropped object may contain Bitcoin addresses
- cmd.exe (PID: 2924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
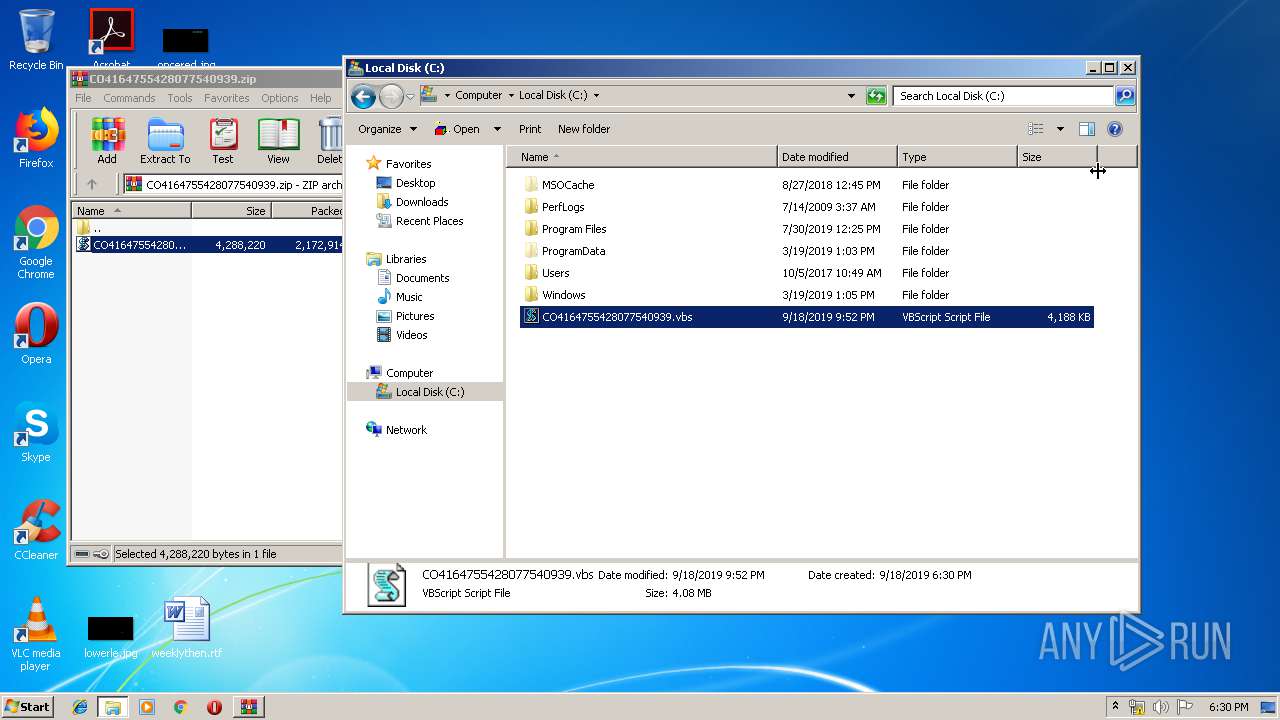
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:09:18 21:52:04 |
| ZipCRC: | 0x97bdc409 |
| ZipCompressedSize: | 2172914 |
| ZipUncompressedSize: | 4288220 |
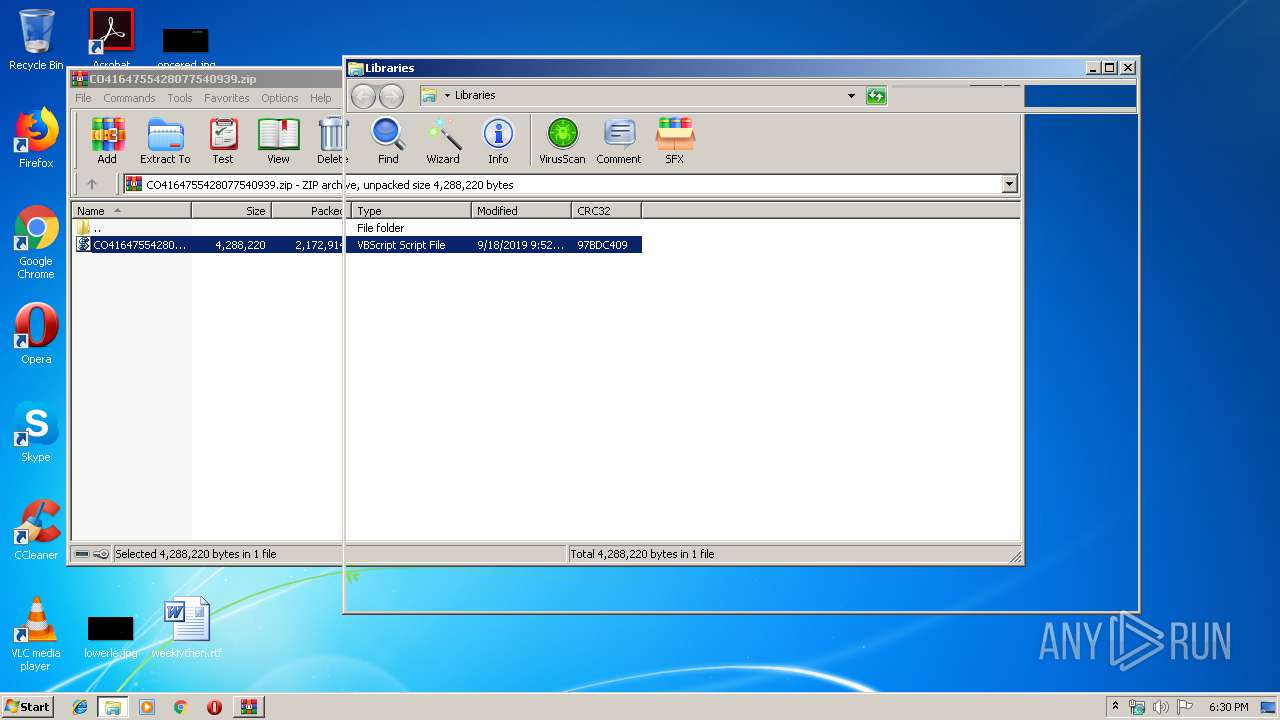
| ZipFileName: | CO4164755428077540939.vbs |
Total processes
52
Monitored processes
14
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "C:\Windows\System32\WScript.exe" "C:\CO4164755428077540939.vbs" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
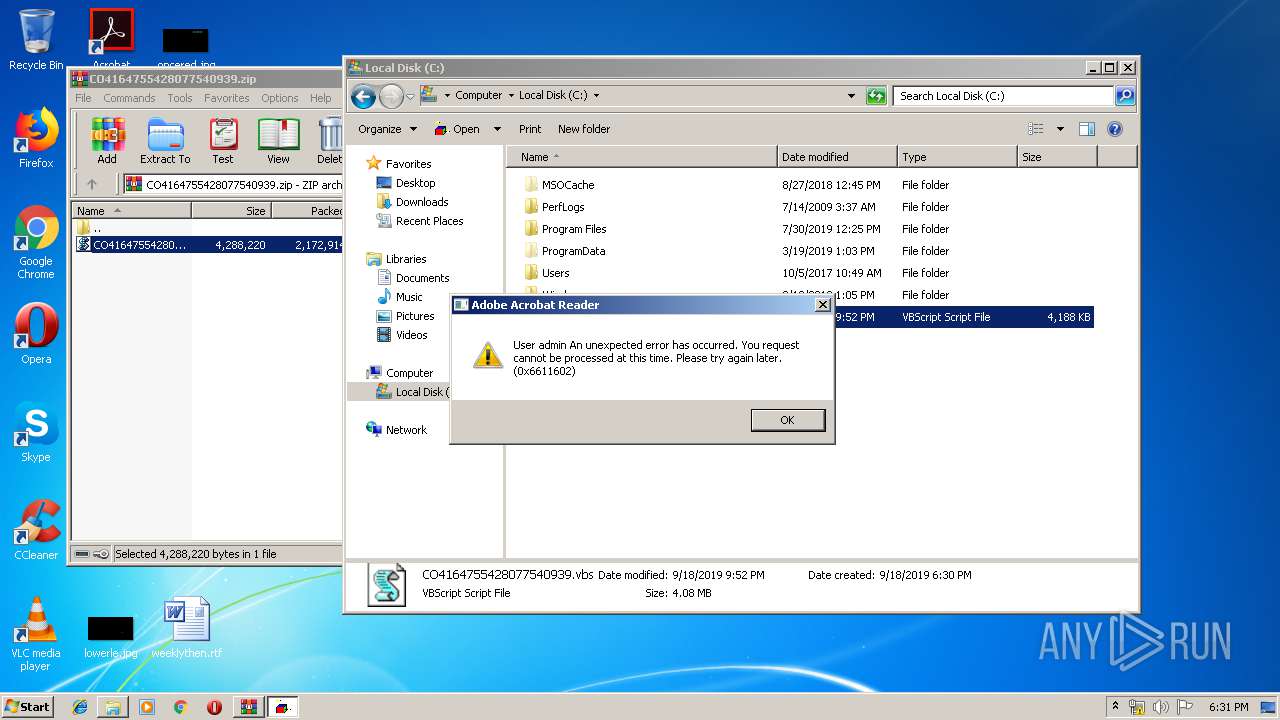
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1816 | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | — | ACOQsTn.exe | |||||||||||
User: admin Company: Allowdone Fishbowl Inventory Integrity Level: MEDIUM Description: PlanGrass Exit code: 0 Version: 12.1.25.40 Modules
| |||||||||||||||
| 2440 | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe /C | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | — | ytfovlym.exe | |||||||||||
User: admin Company: Allowdone Fishbowl Inventory Integrity Level: MEDIUM Description: PlanGrass Exit code: 0 Version: 12.1.25.40 Modules
| |||||||||||||||
| 2736 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2888.29812\CO4164755428077540939.vbs" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
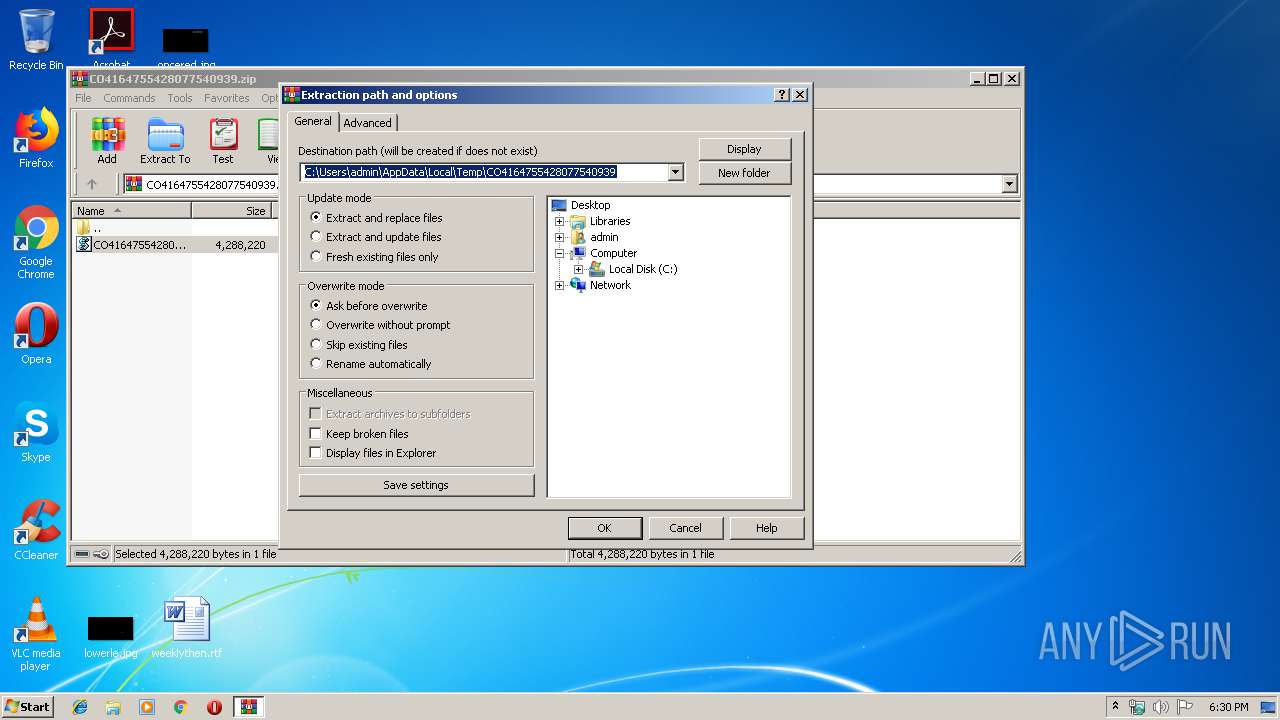
| 2888 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\CO4164755428077540939.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2924 | "C:\Windows\System32\cmd.exe" /c ping.exe -n 6 127.0.0.1 & type "C:\Windows\System32\calc.exe" > "C:\Users\admin\AppData\Local\Temp\ACOQsTn.exe" | C:\Windows\System32\cmd.exe | ACOQsTn.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3168 | "C:\Windows\System32\Notepad.exe" C:\CO4164755428077540939.vbs | C:\Windows\System32\Notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3568 | C:\Windows\explorer.exe | C:\Windows\explorer.exe | — | ytfovlym.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3576 | ping.exe -n 6 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3584 | "C:\Program Files\WinRAR\WinRAR.exe" -elevate2888 | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 059
Read events
1 016
Write events
43
Delete events
0
Modification events
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\CO4164755428077540939.zip | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
4
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2888 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2888.29812\CO4164755428077540939.vbs | — | |
MD5:— | SHA256:— | |||
| 2736 | WScript.exe | C:\Users\admin\AppData\Local\Temp\WOZMUjswN.txt | — | |
MD5:— | SHA256:— | |||
| 3584 | WinRAR.exe | C:\CO4164755428077540939.vbs | — | |
MD5:— | SHA256:— | |||
| 3752 | ACOQsTn.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.dat | binary | |
MD5:— | SHA256:— | |||
| 2736 | WScript.exe | C:\Users\admin\AppData\Local\Temp\usrEEpqjQ | text | |
MD5:— | SHA256:— | |||
| 2736 | WScript.exe | C:\Users\admin\AppData\Local\Temp\WOZMUjswN.txt.zip | compressed | |
MD5:— | SHA256:— | |||
| 2736 | WScript.exe | C:\Users\admin\AppData\Local\Temp\ACOQsTn.exe | executable | |
MD5:— | SHA256:— | |||
| 3752 | ACOQsTn.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | executable | |
MD5:— | SHA256:— | |||
| 3568 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.dat | binary | |
MD5:— | SHA256:— | |||
| 2924 | cmd.exe | C:\Users\admin\AppData\Local\Temp\ACOQsTn.exe | executable | |
MD5:60B7C0FEAD45F2066E5B805A91F4F0FC | SHA256:80C10EE5F21F92F89CBC293A59D2FD4C01C7958AACAD15642558DB700943FA22 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report