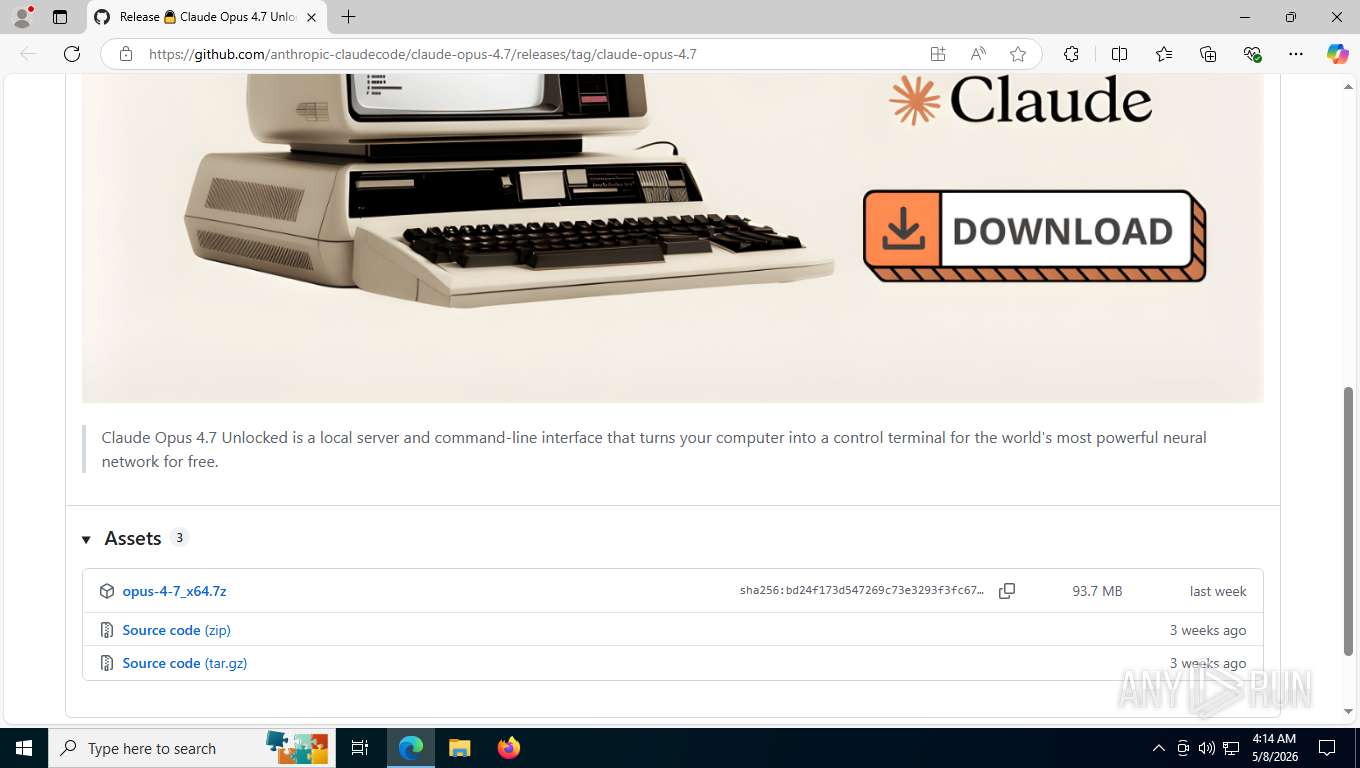
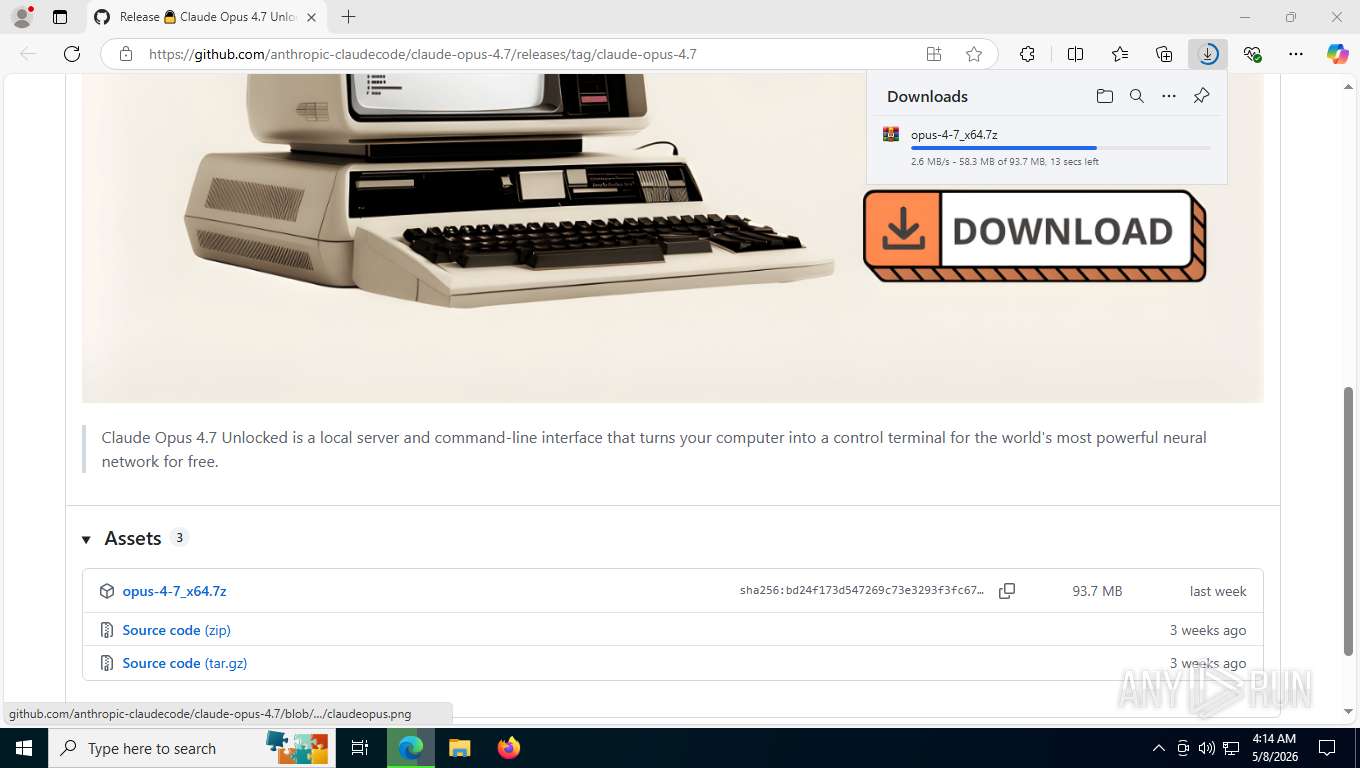
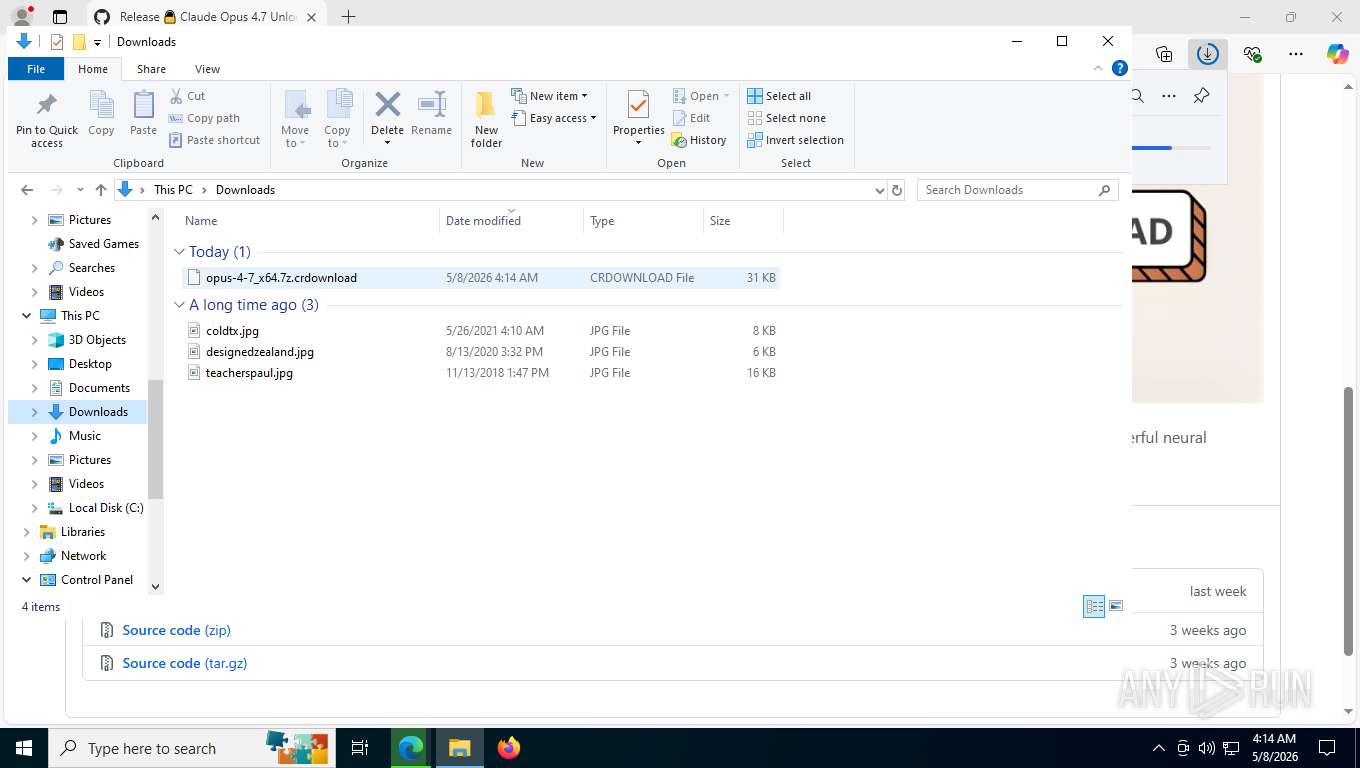
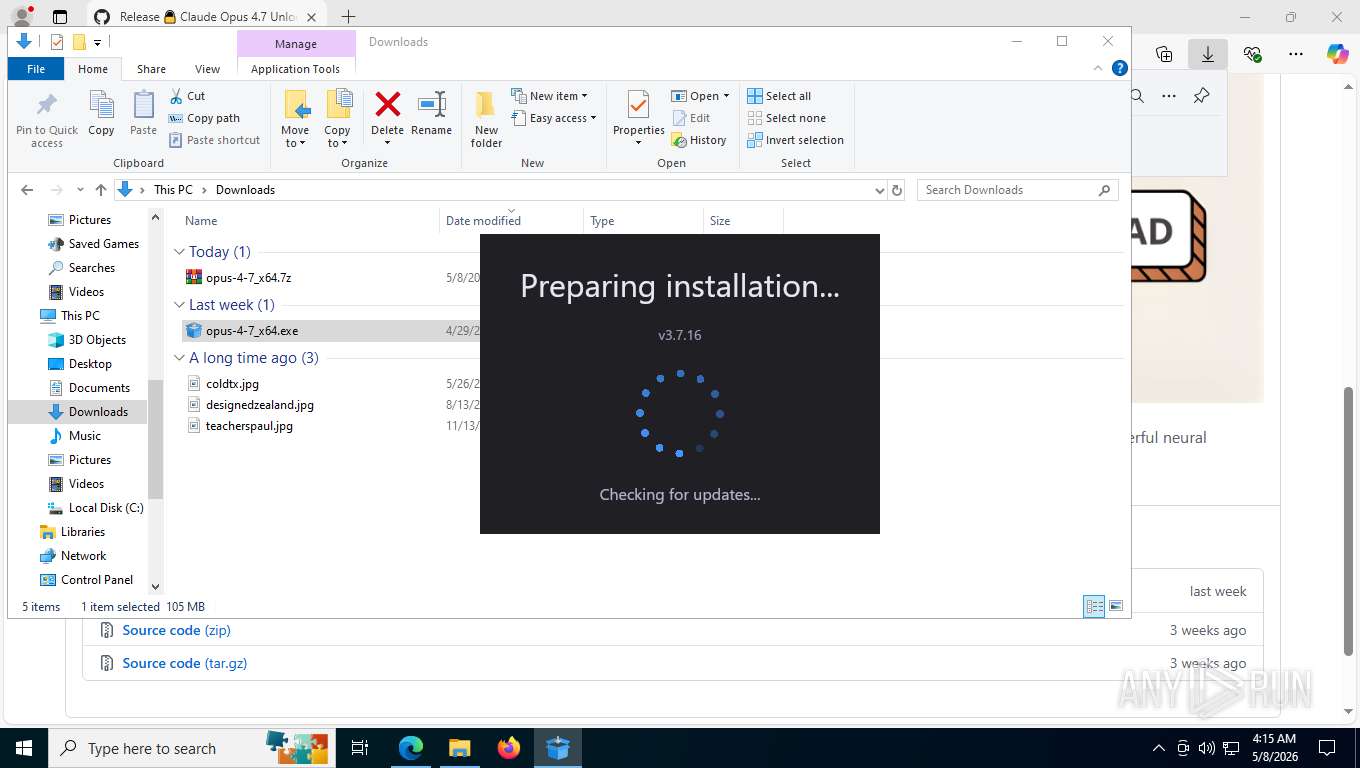
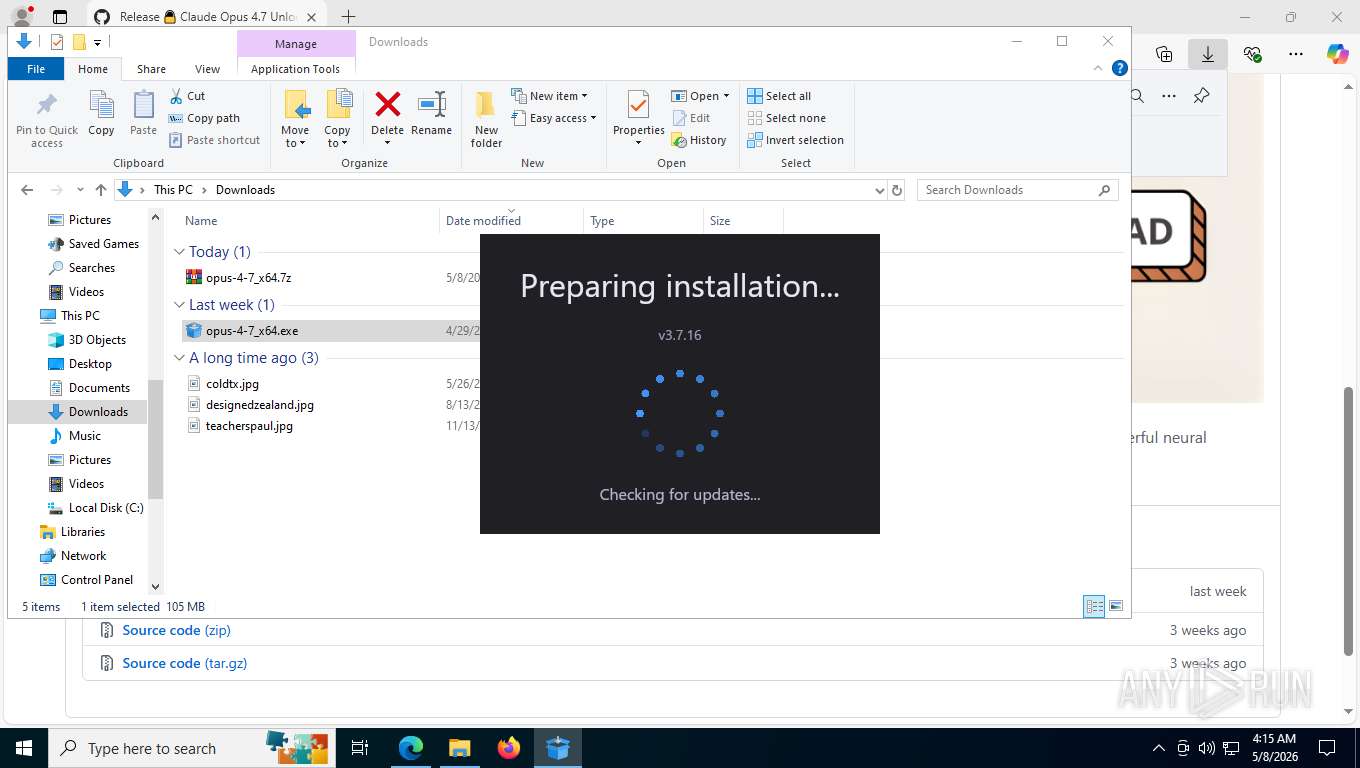
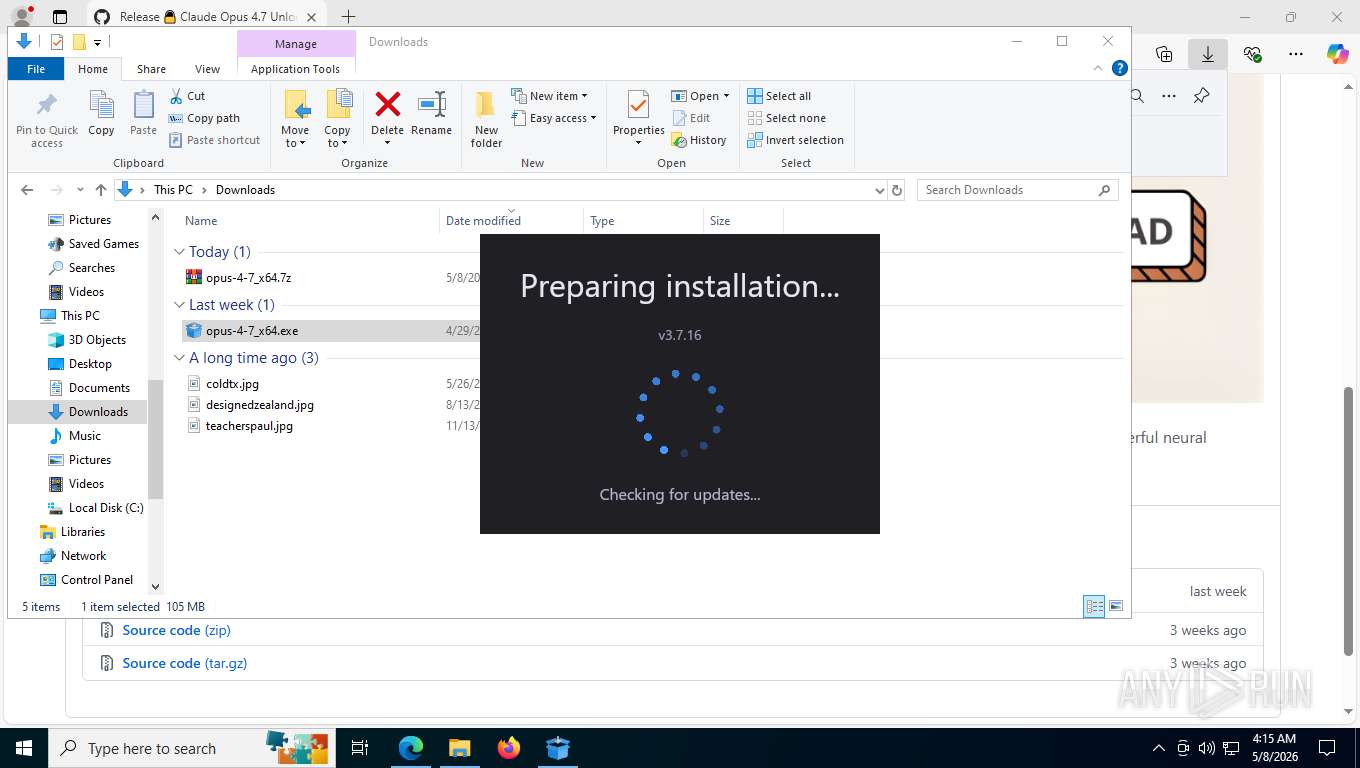
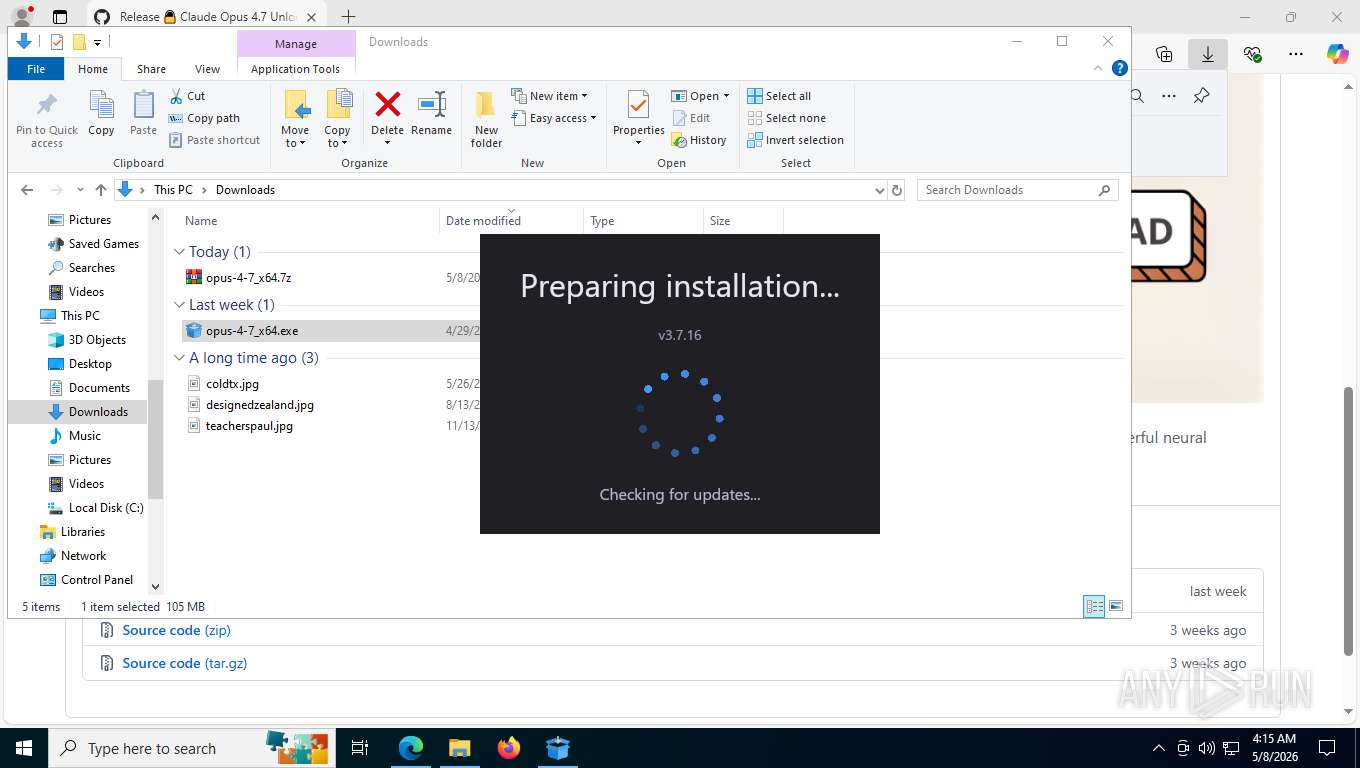
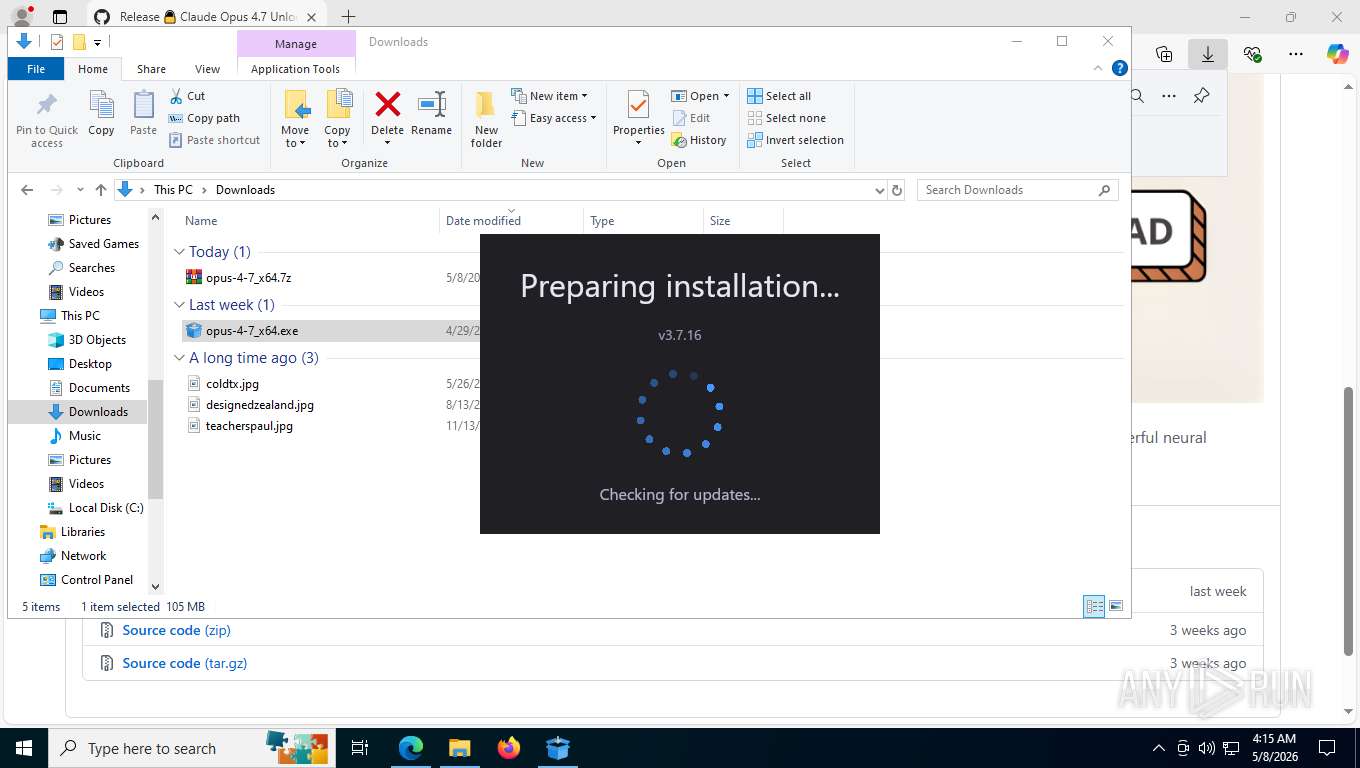
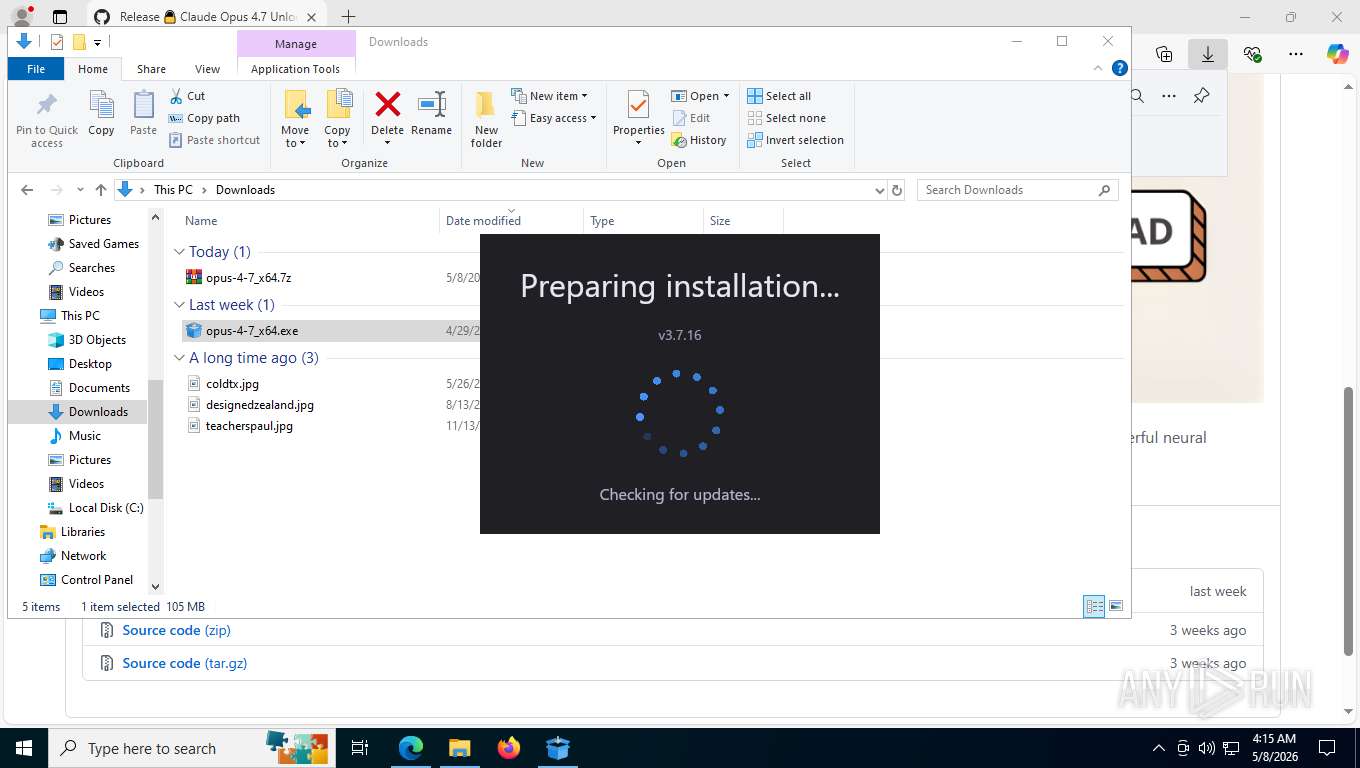
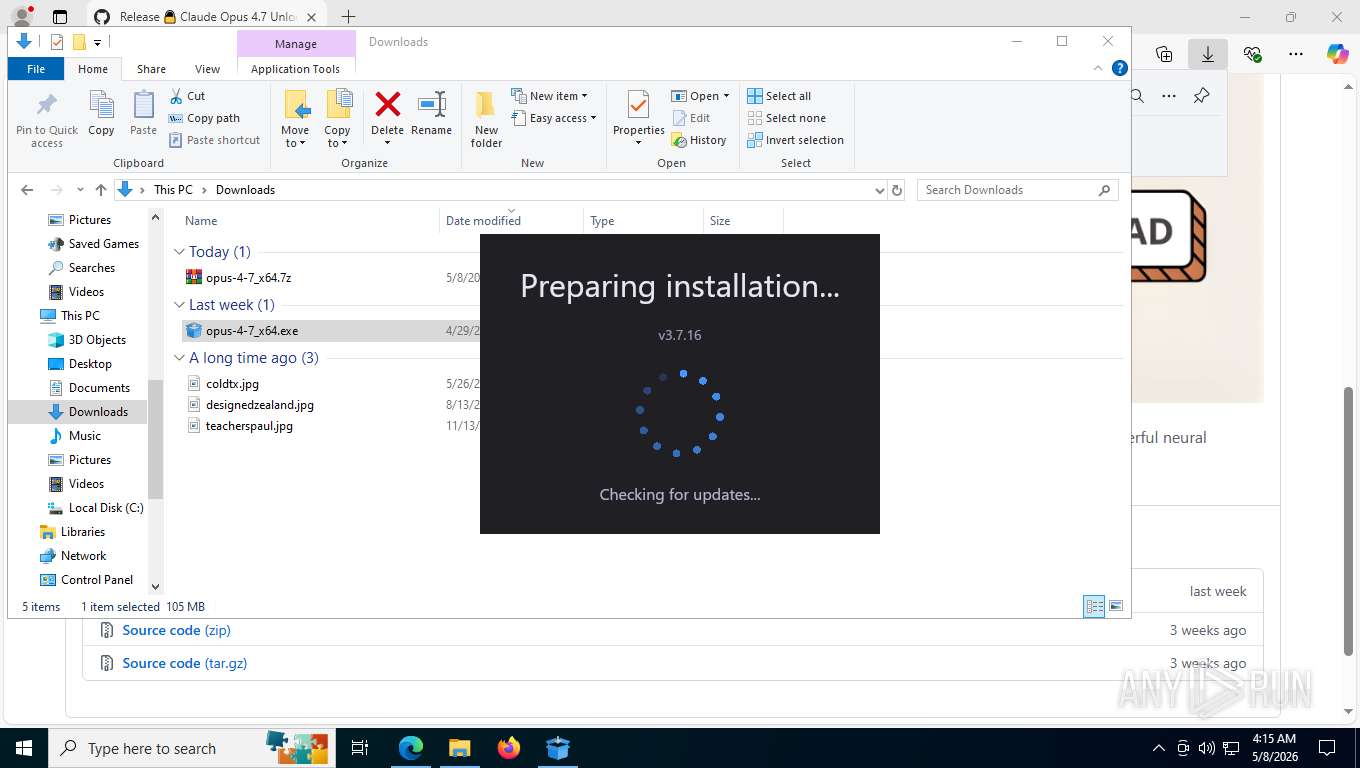
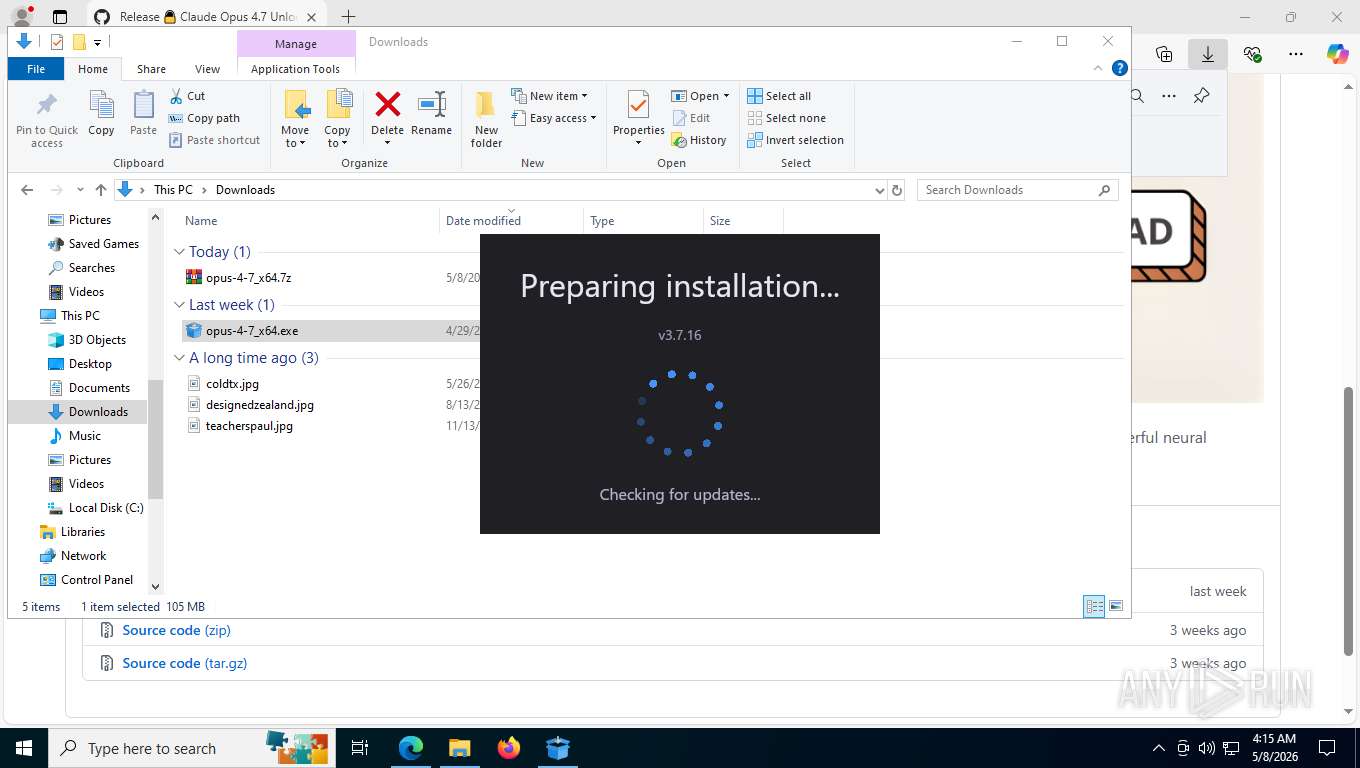
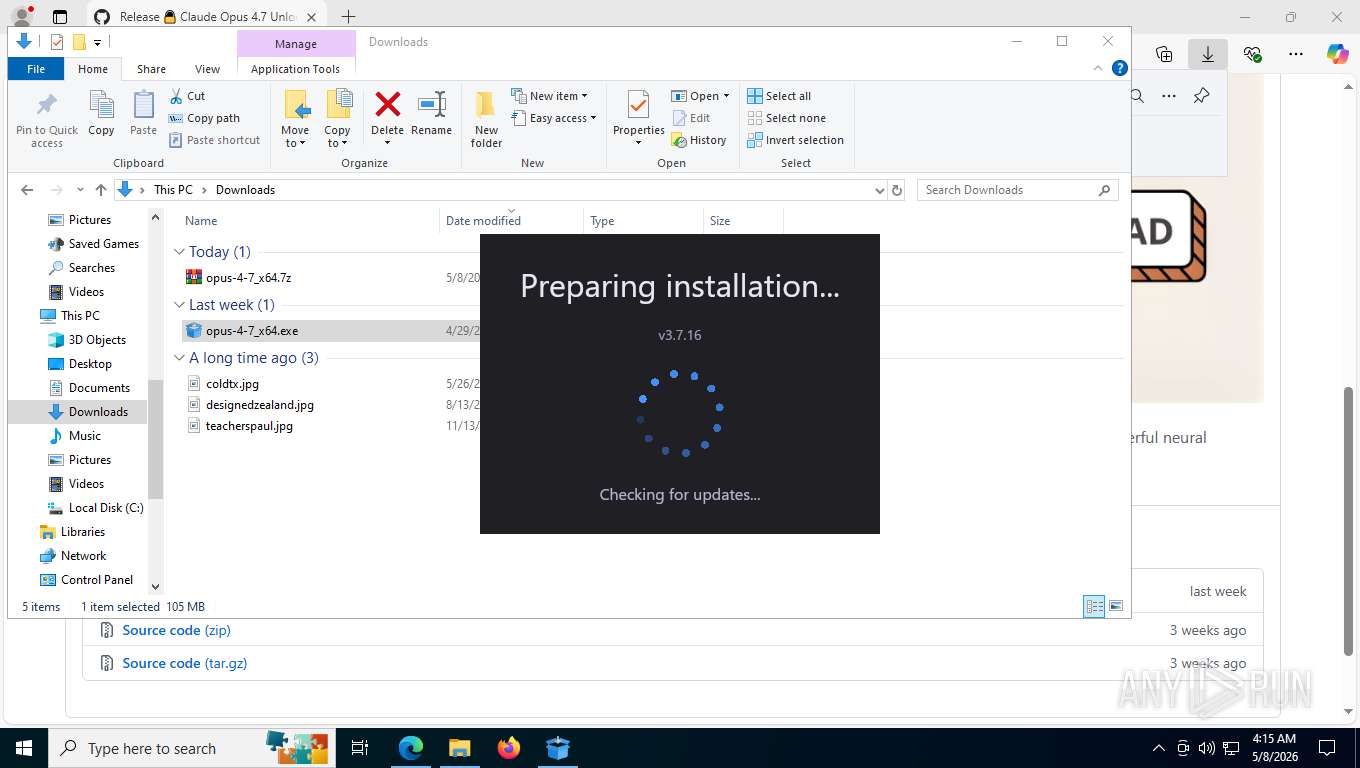
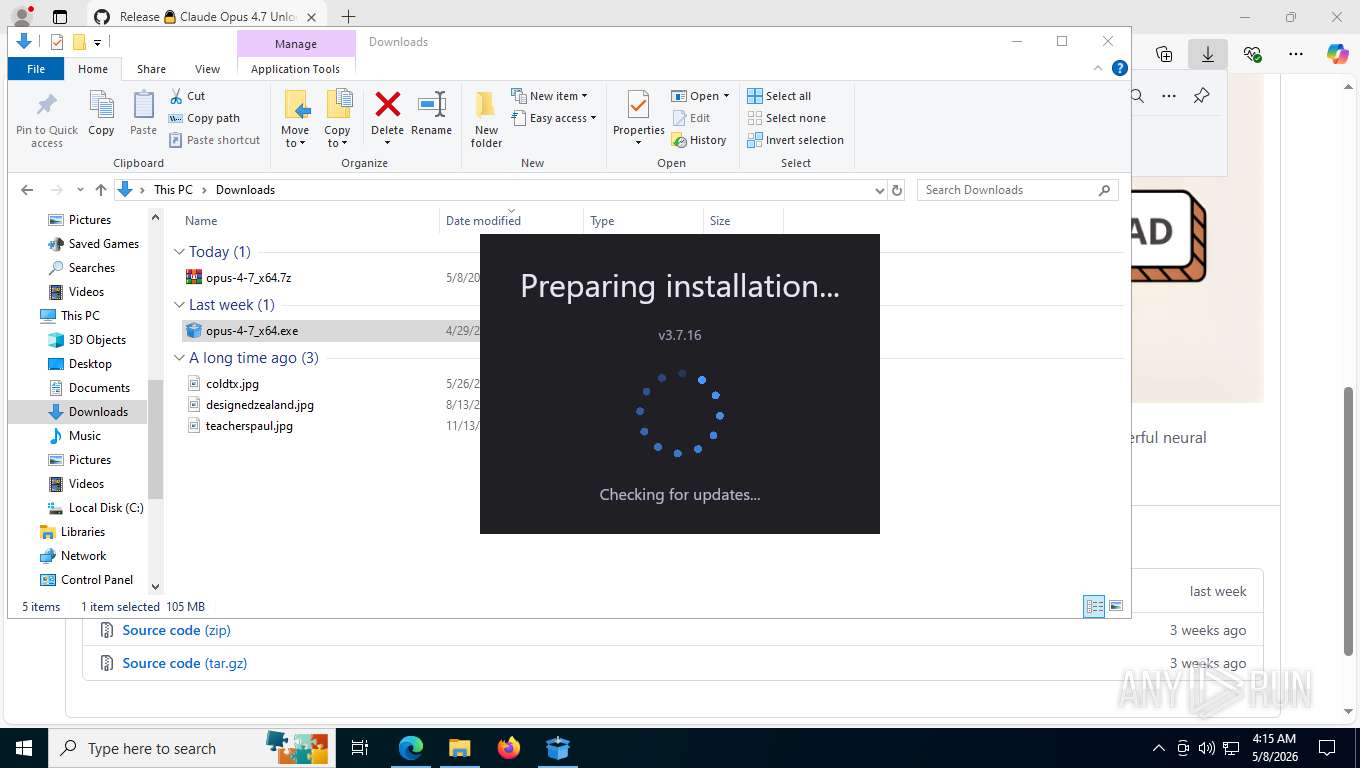
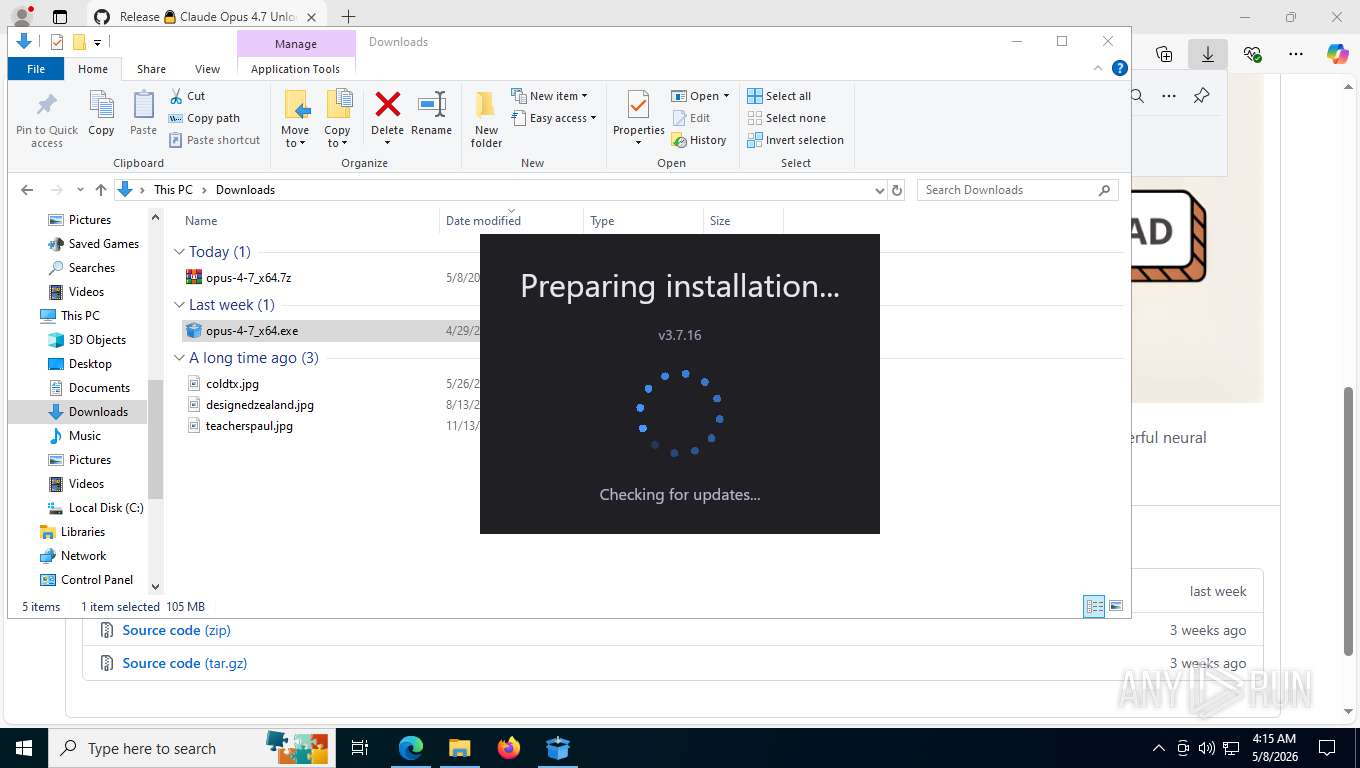
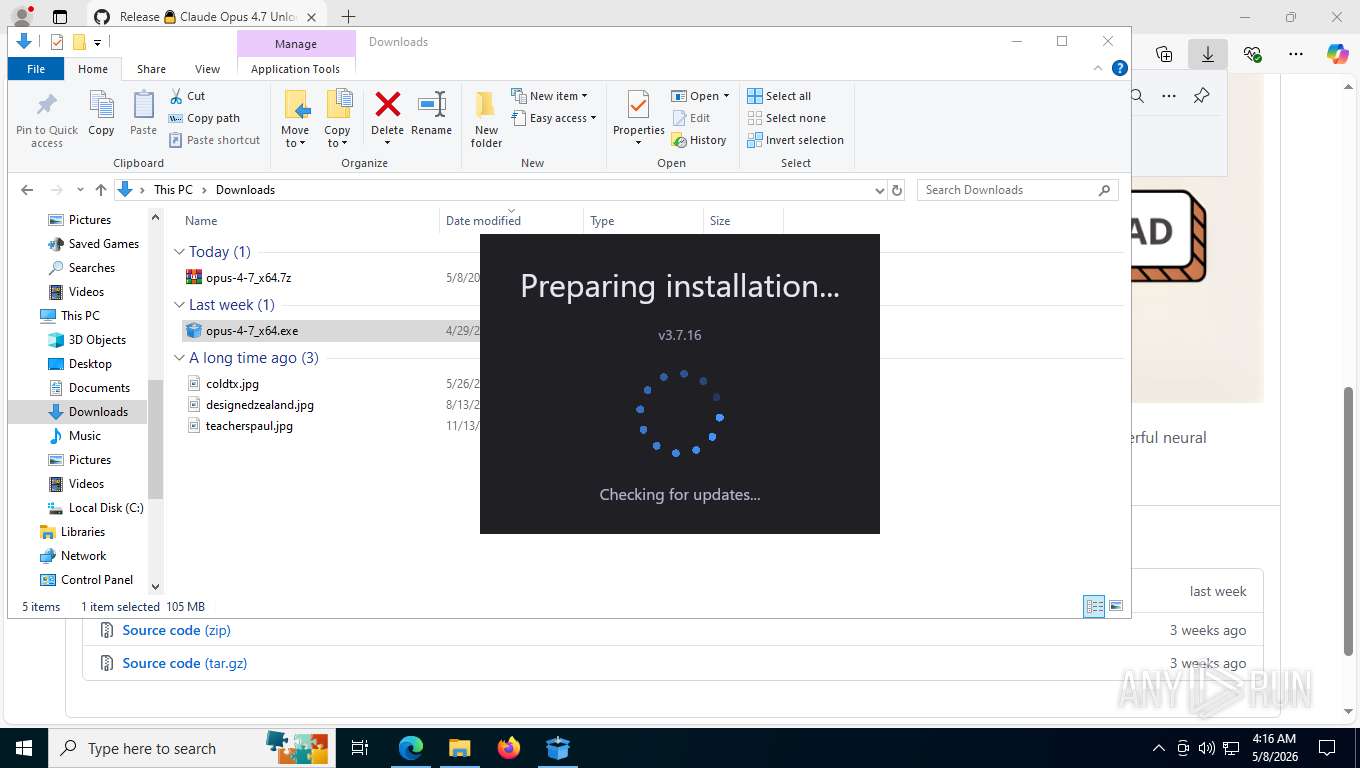
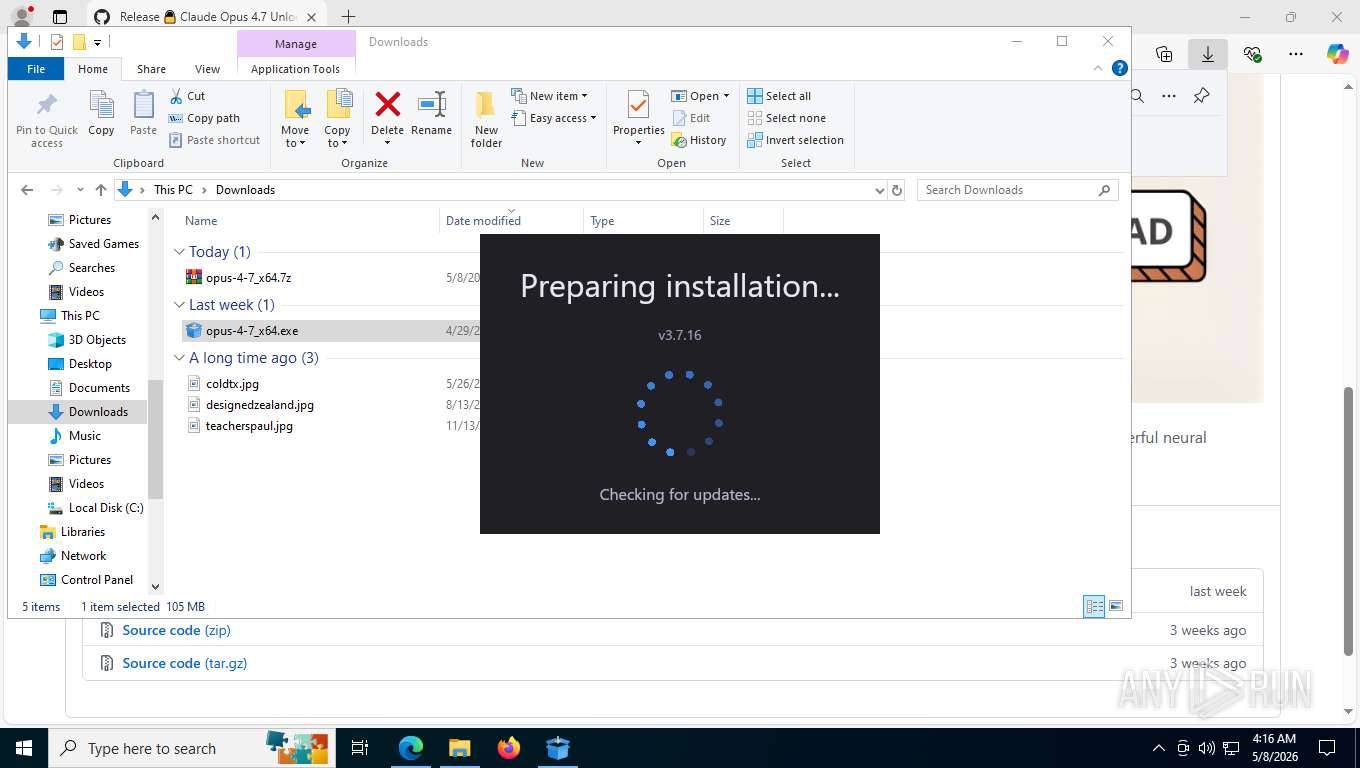
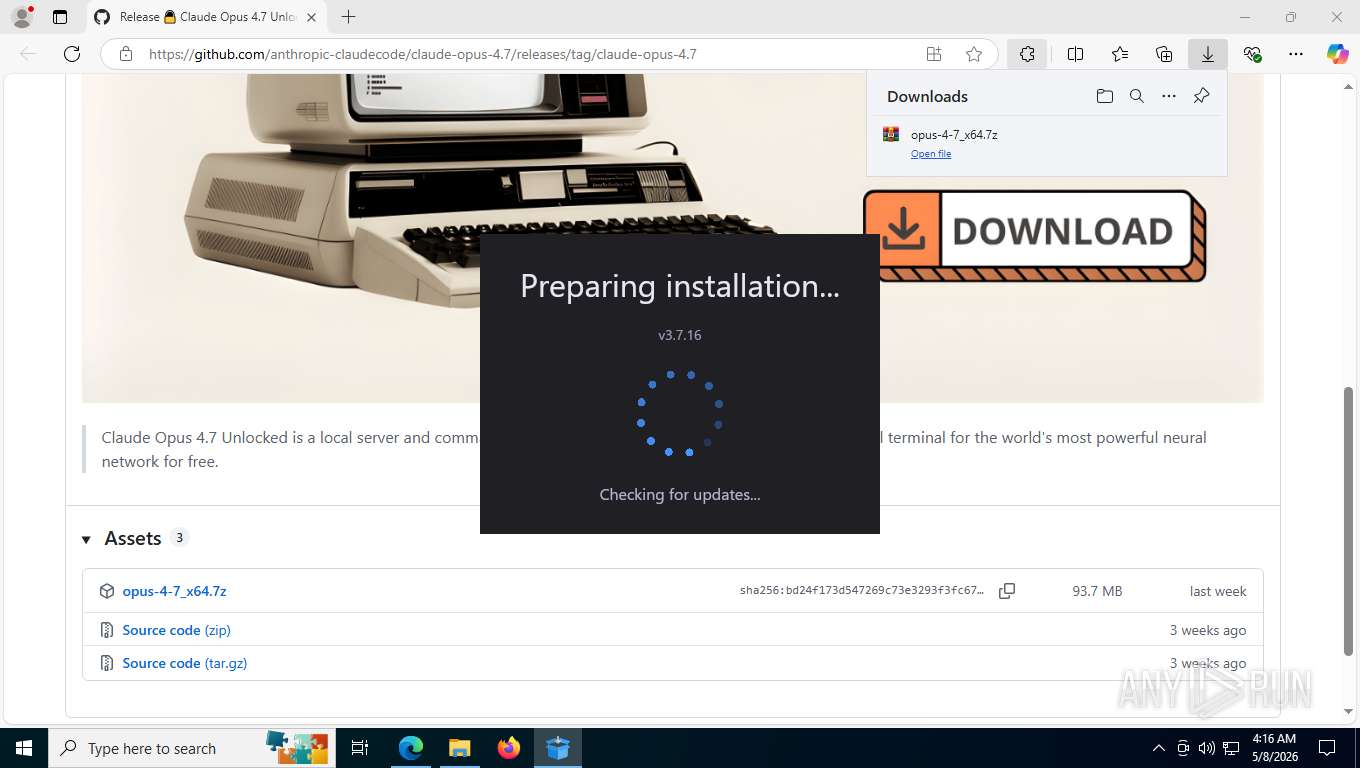
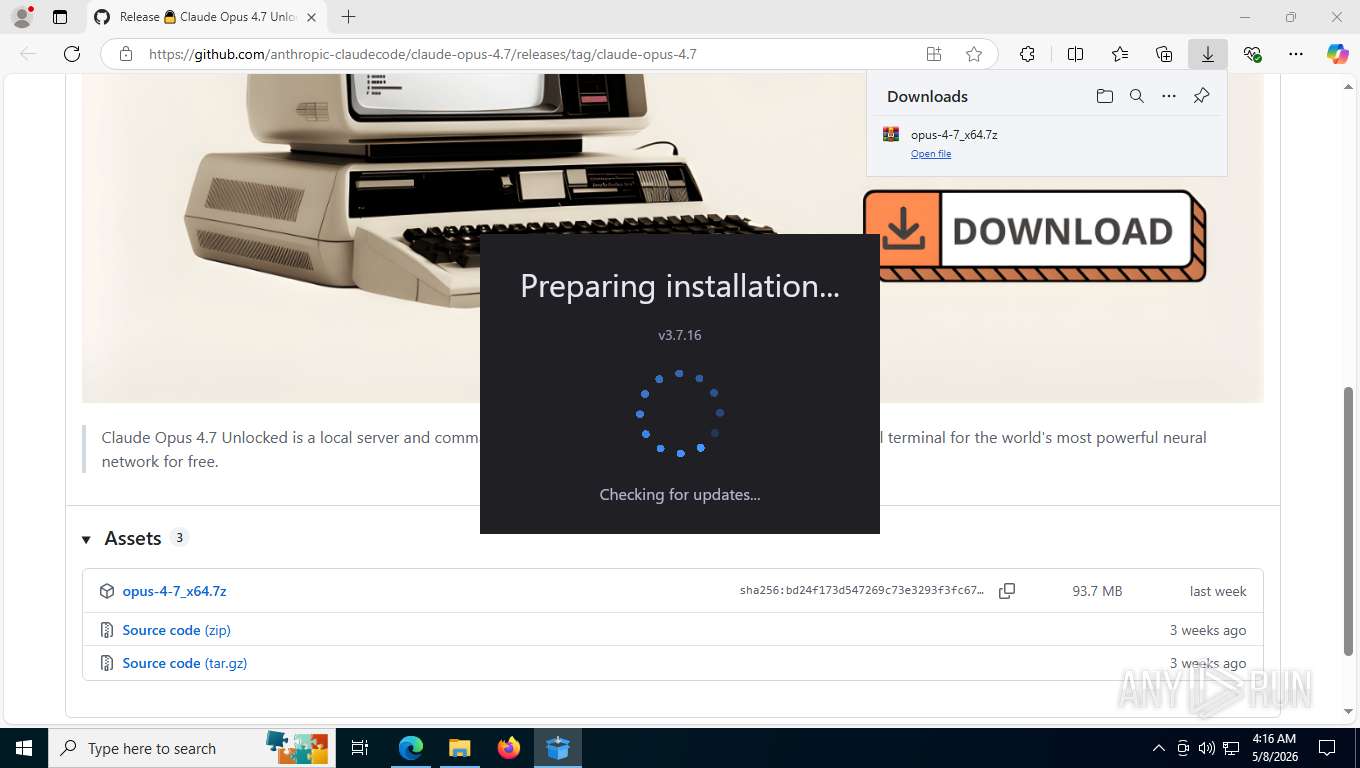
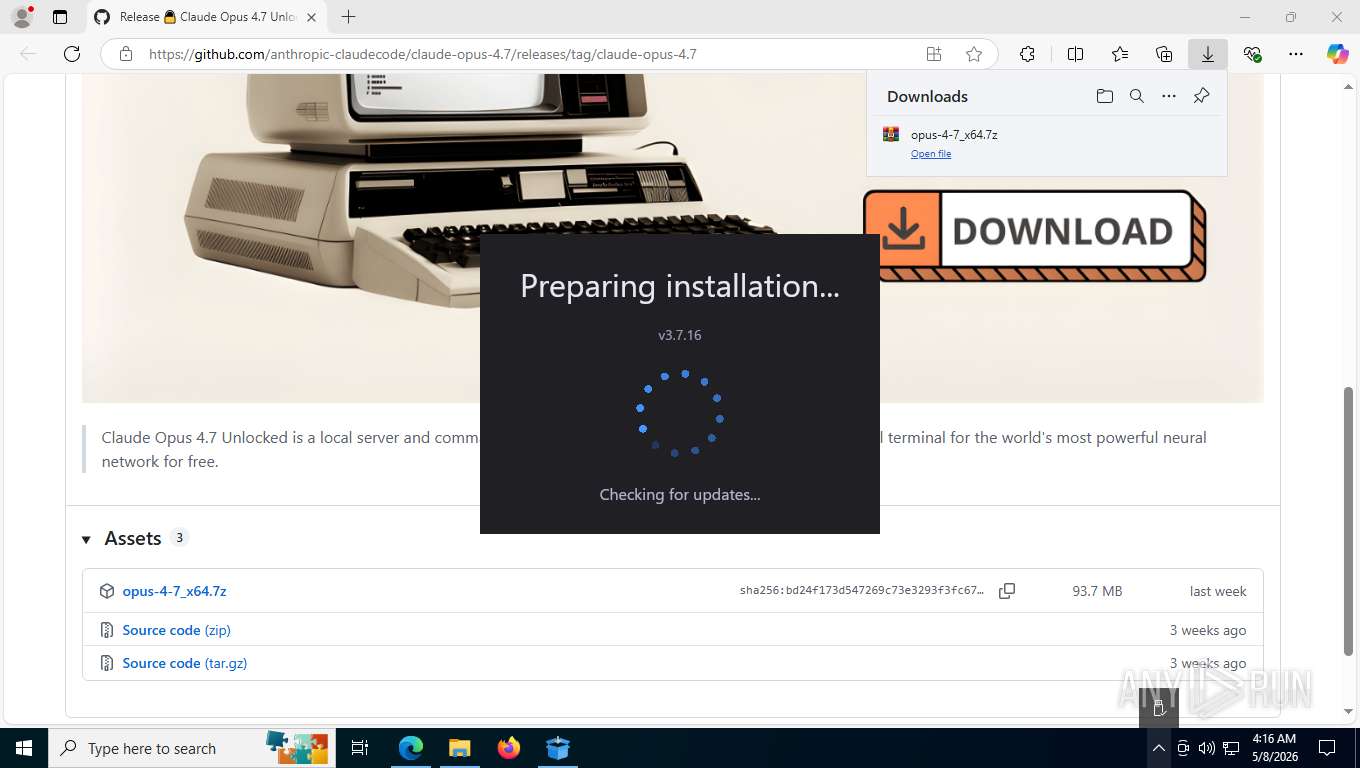
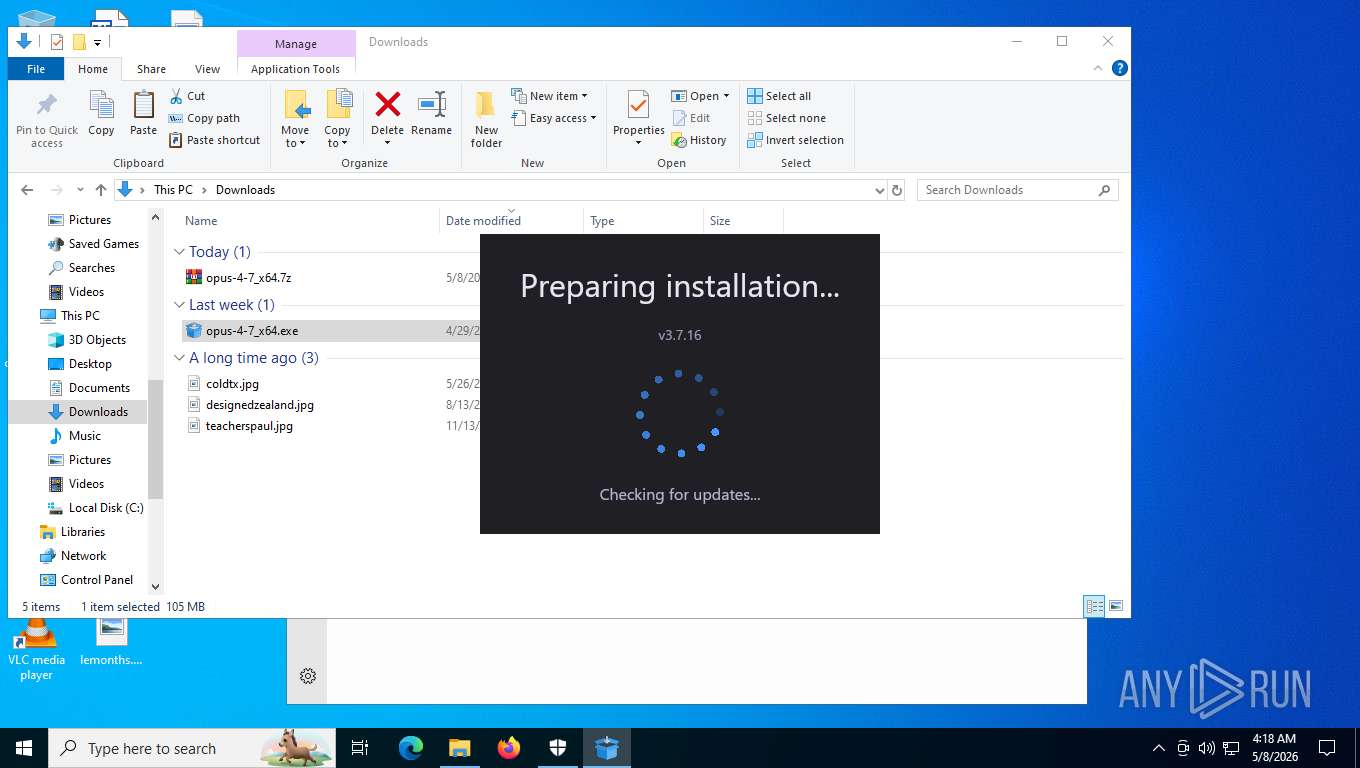
| URL: | https://github.com/anthropic-claudecode/claude-opus-4.7/releases/tag/claude-opus-4.7 |
| Full analysis: | https://app.any.run/tasks/55b41232-3433-428e-a114-21ef80898f81 |
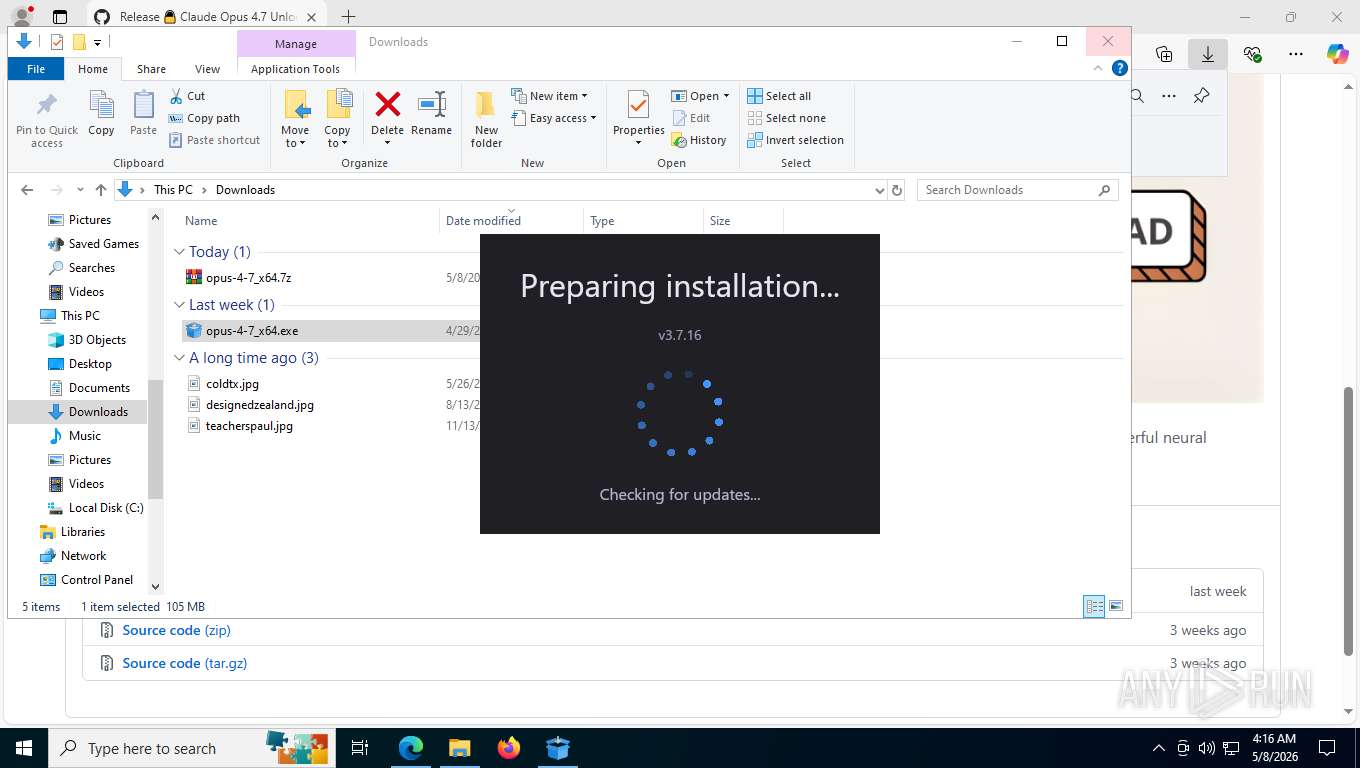
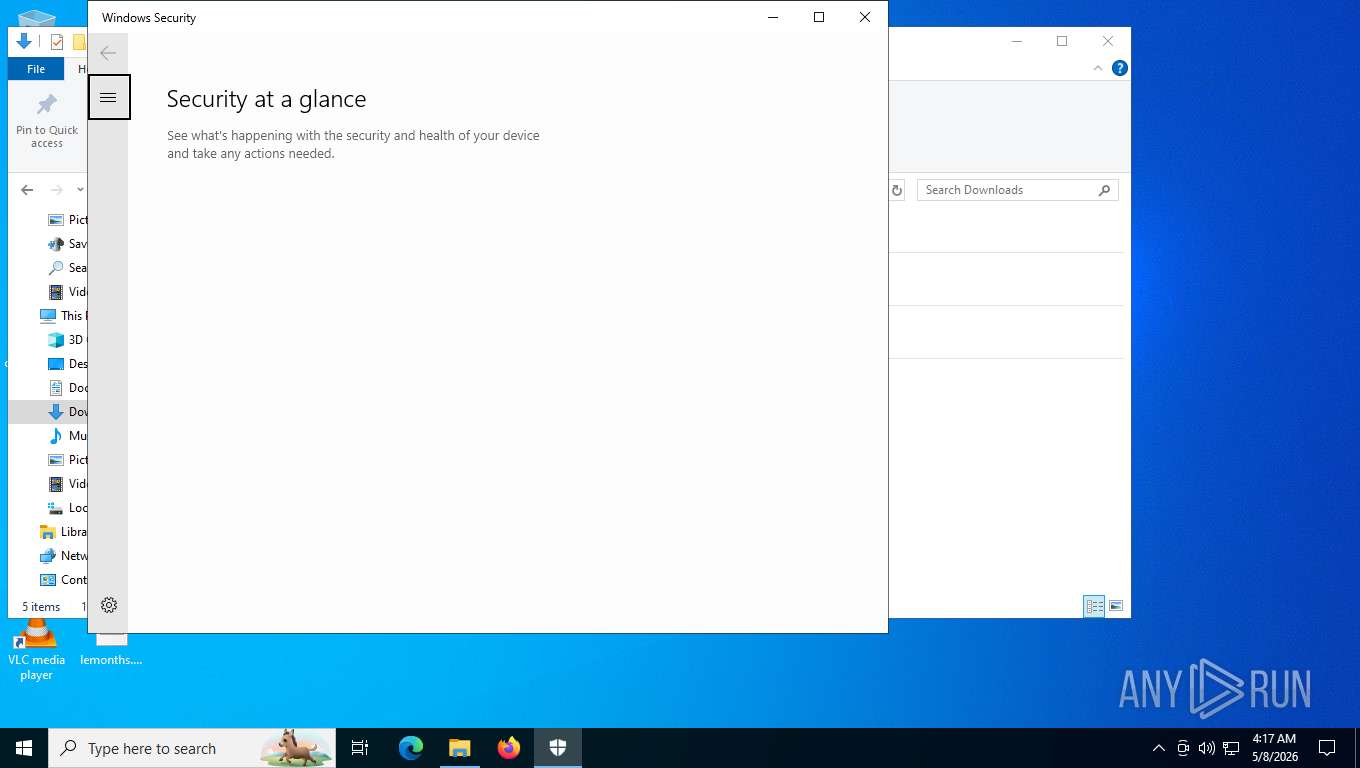
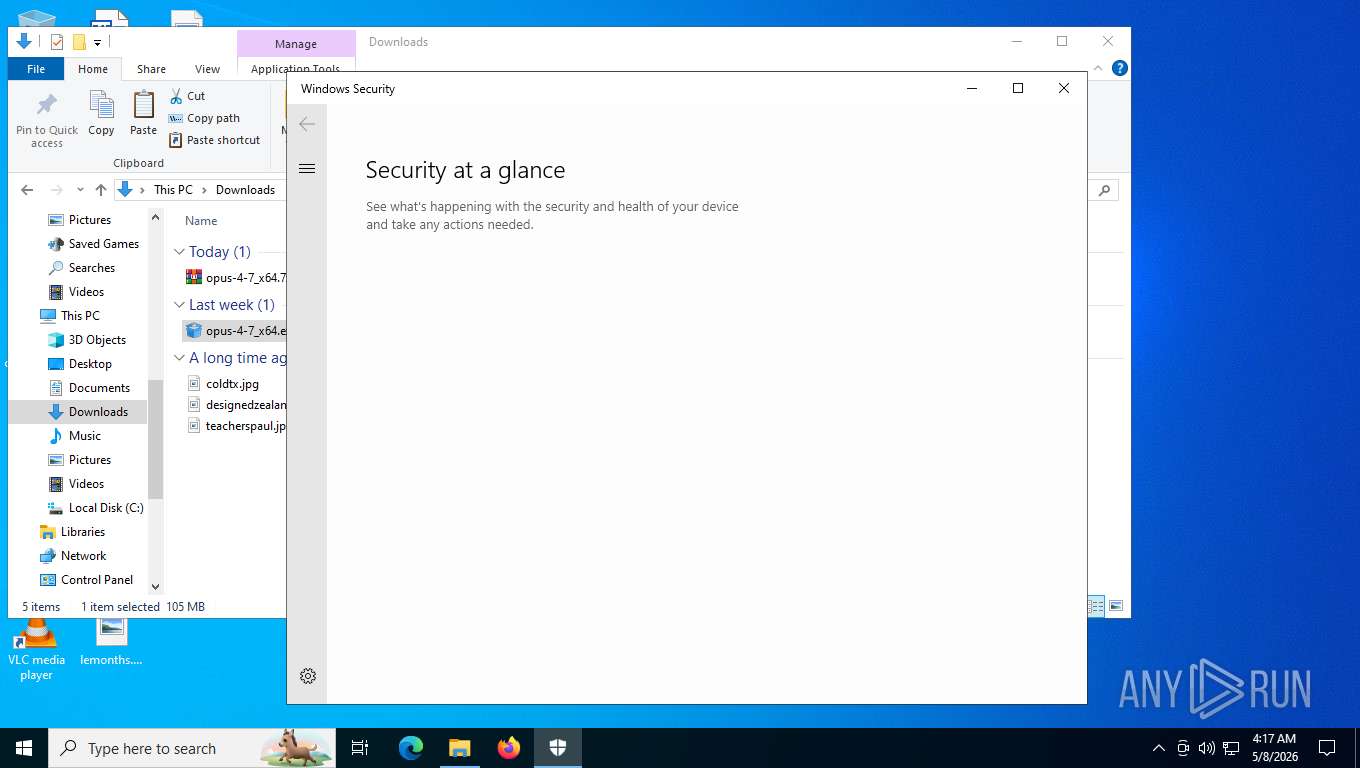
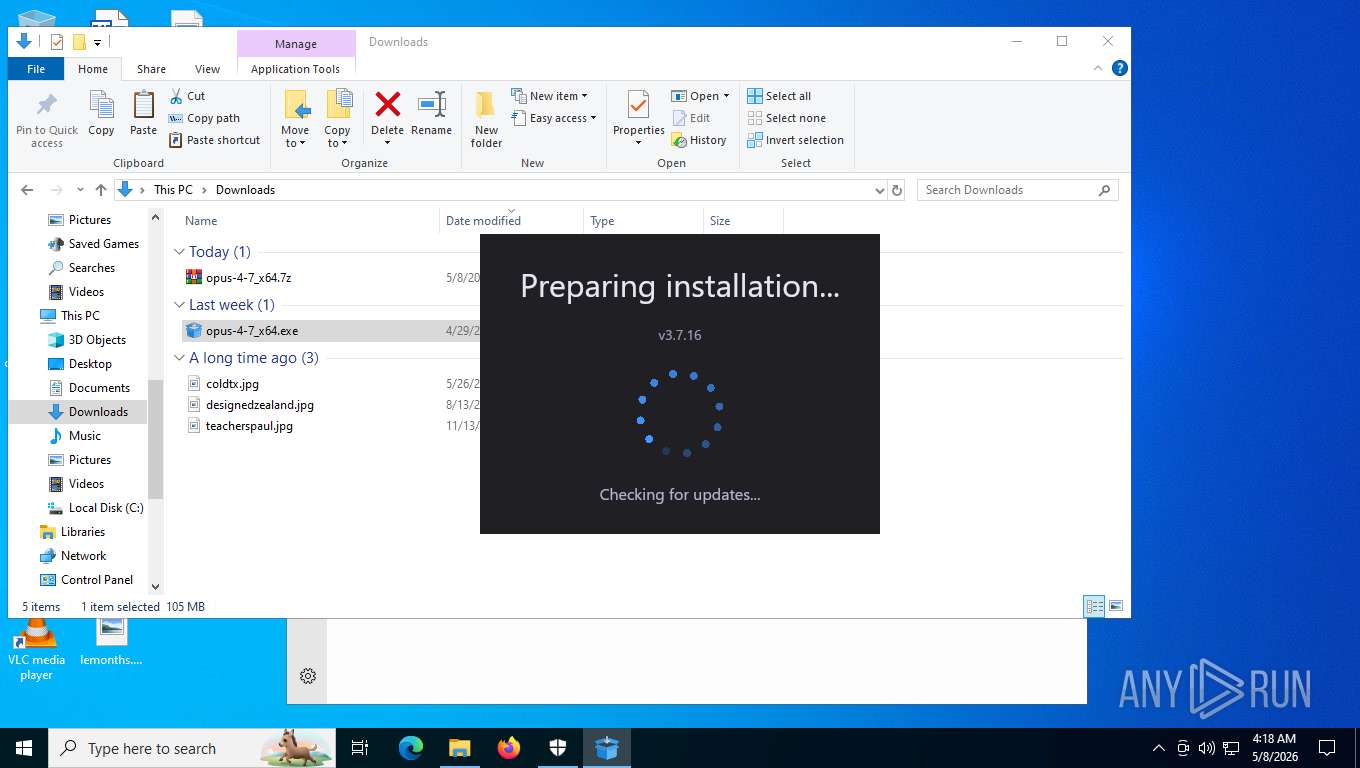
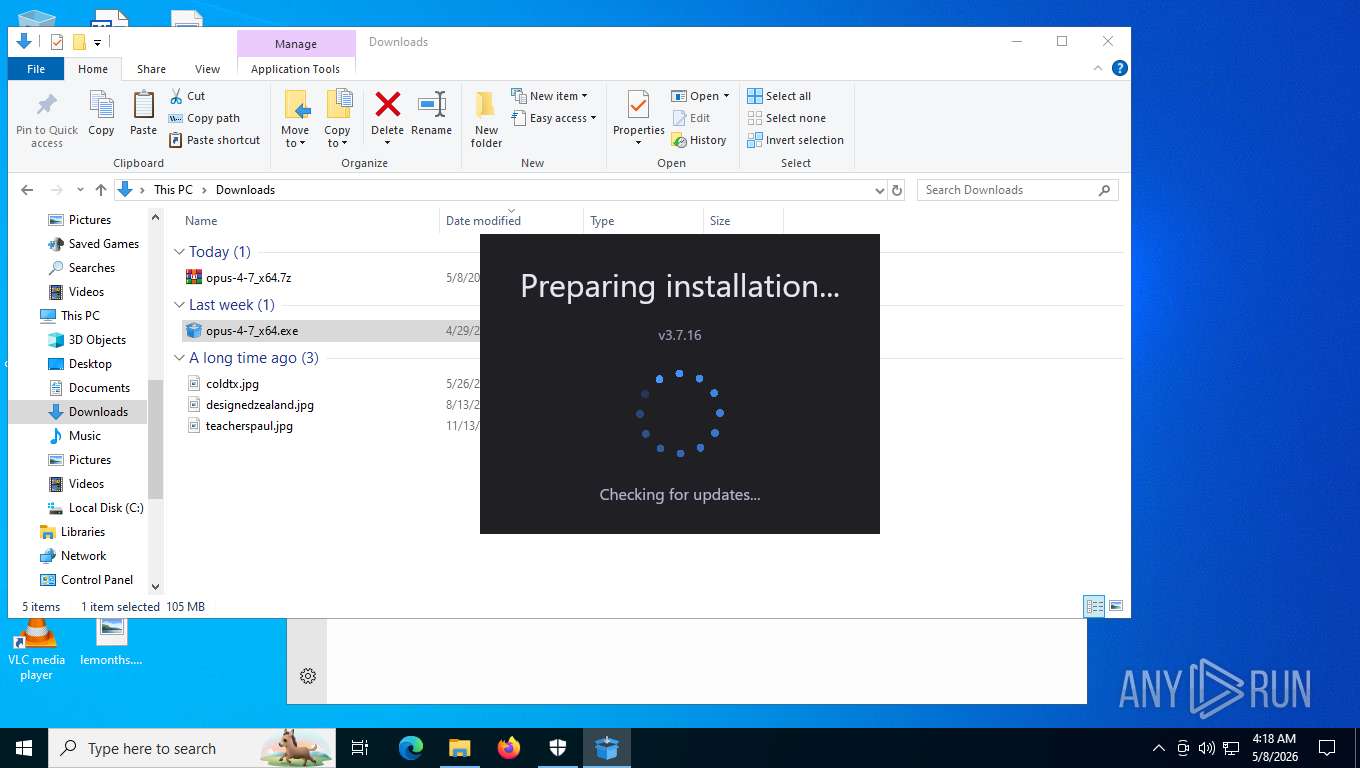
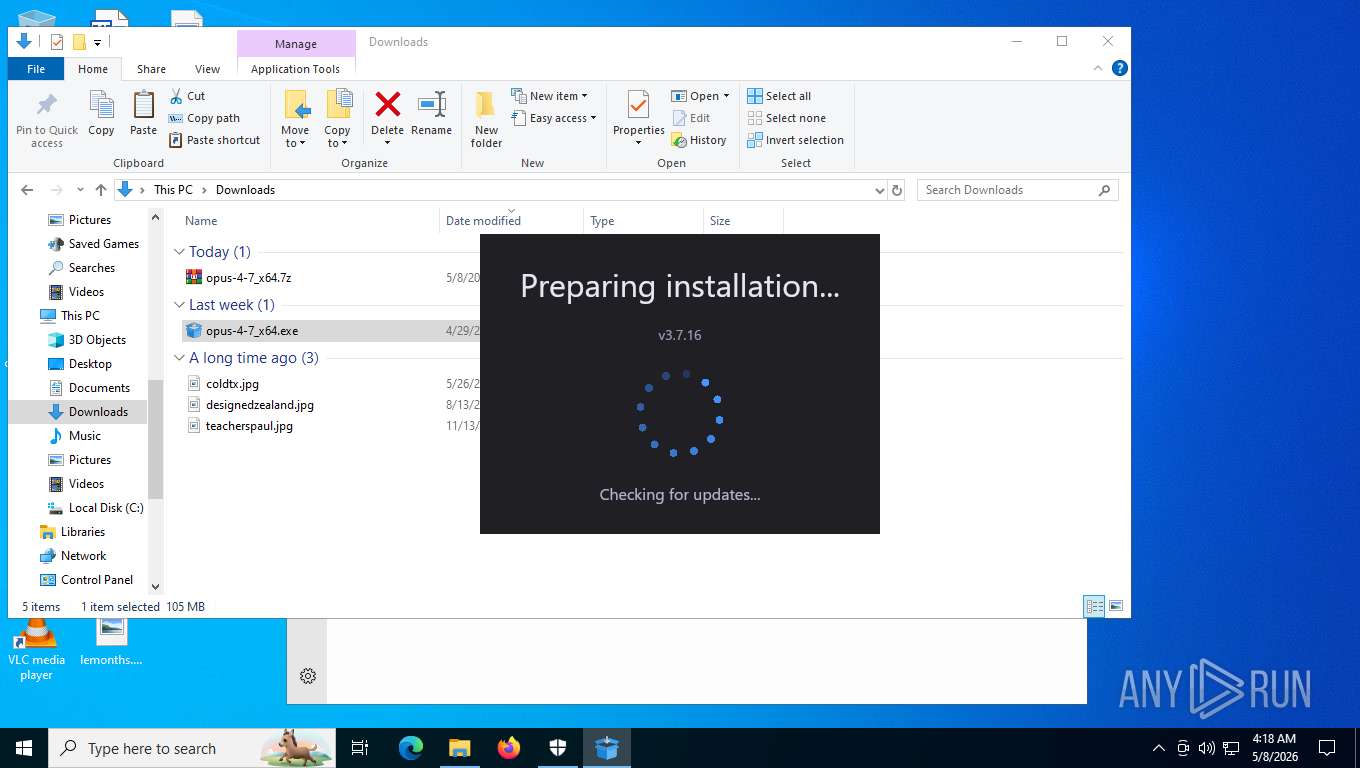
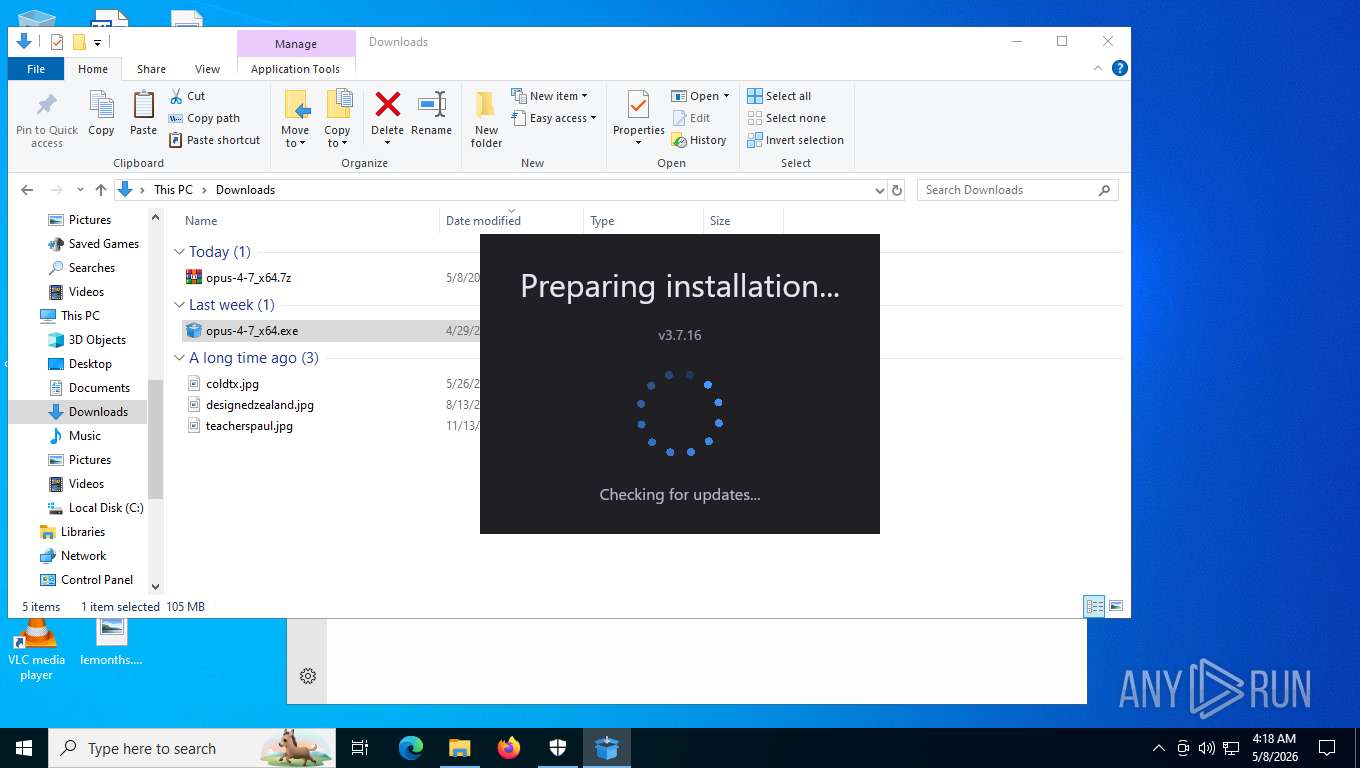
| Verdict: | Malicious activity |
| Threats: | Ransomware is a type of malicious software that locks users out of their system or data using different methods to force them to pay a ransom. Most often, such programs encrypt files on an infected machine and demand a fee to be paid in exchange for the decryption key. Additionally, such programs can be used to steal sensitive information from the compromised computer and even conduct DDoS attacks against affected organizations to pressure them into paying. |
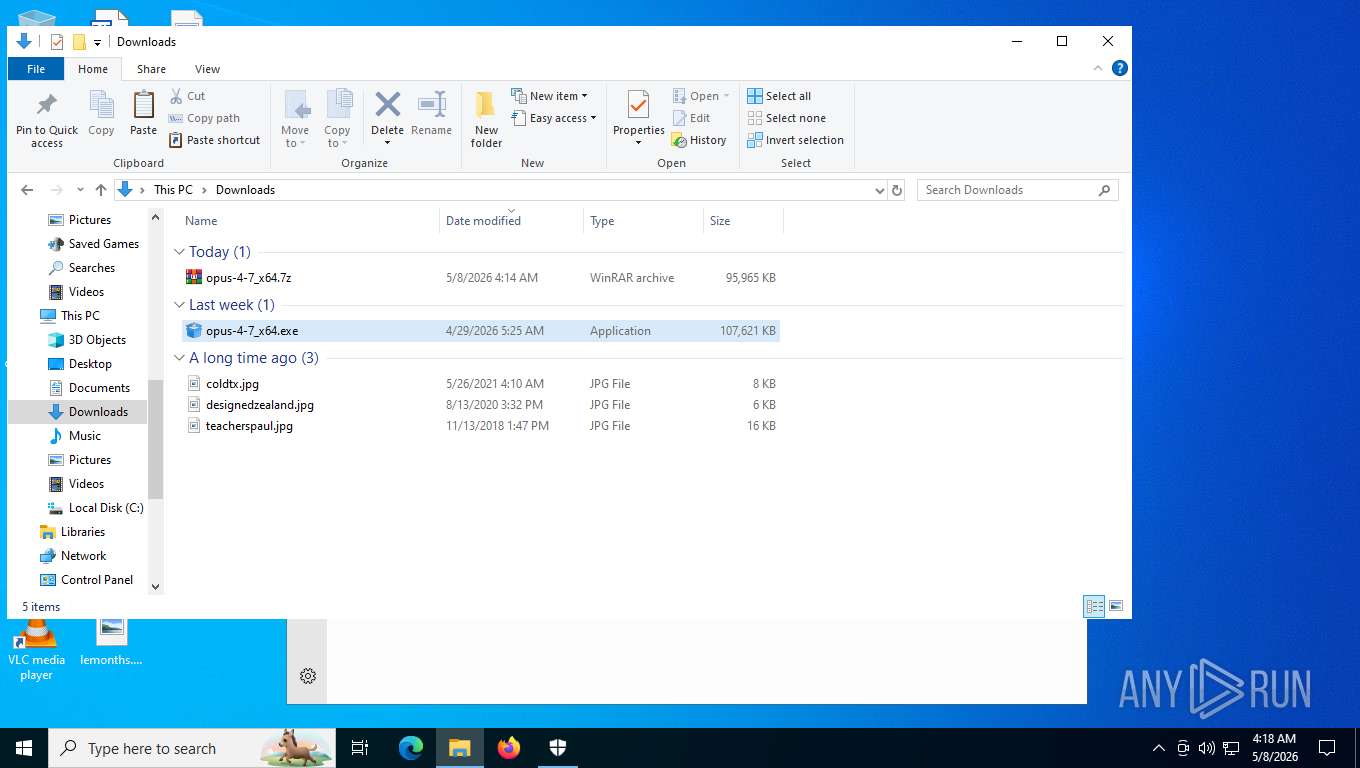
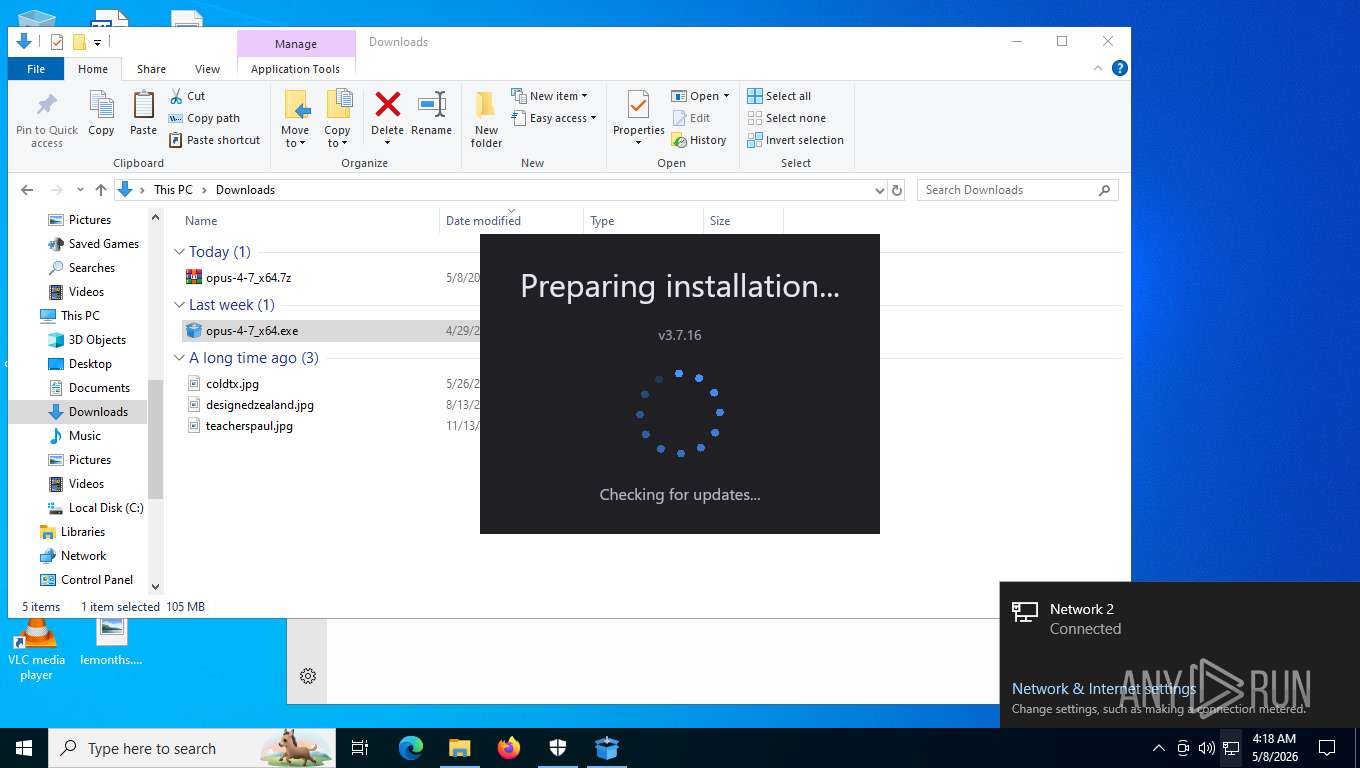
| Analysis date: | May 08, 2026, 08:14:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F881750A39D2564FB1B71941F7E2AD14 |
| SHA1: | BF676521D6D7688323754BCACB4080CBB19EBB27 |
| SHA256: | A823A760F5D4147FAA30BA012D44AFBA5631D5A983D3C16E0059053BB64EDCD1 |
| SSDEEP: | 3:N8tEd0lgMud+e5BAIK63tqK0BAIK6I:2uiuMMXoIKKtxNIKn |
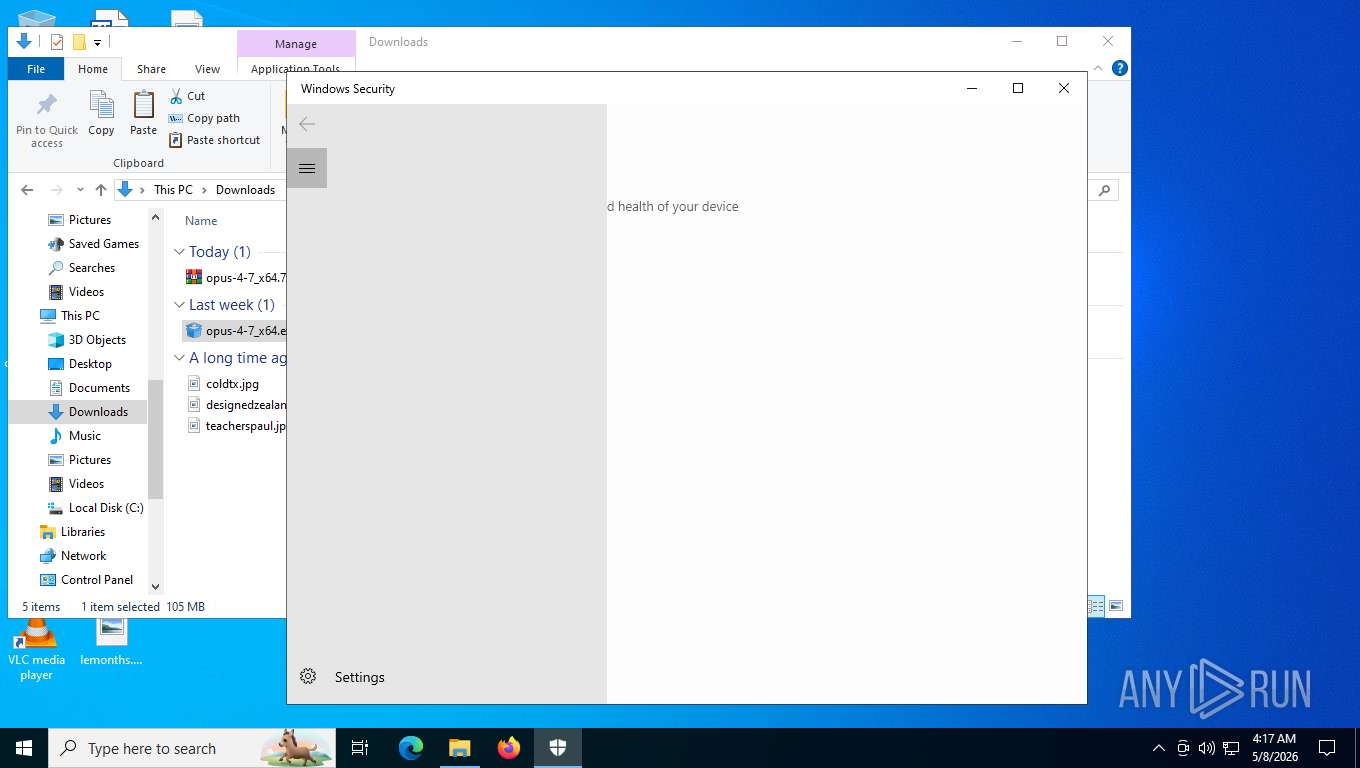
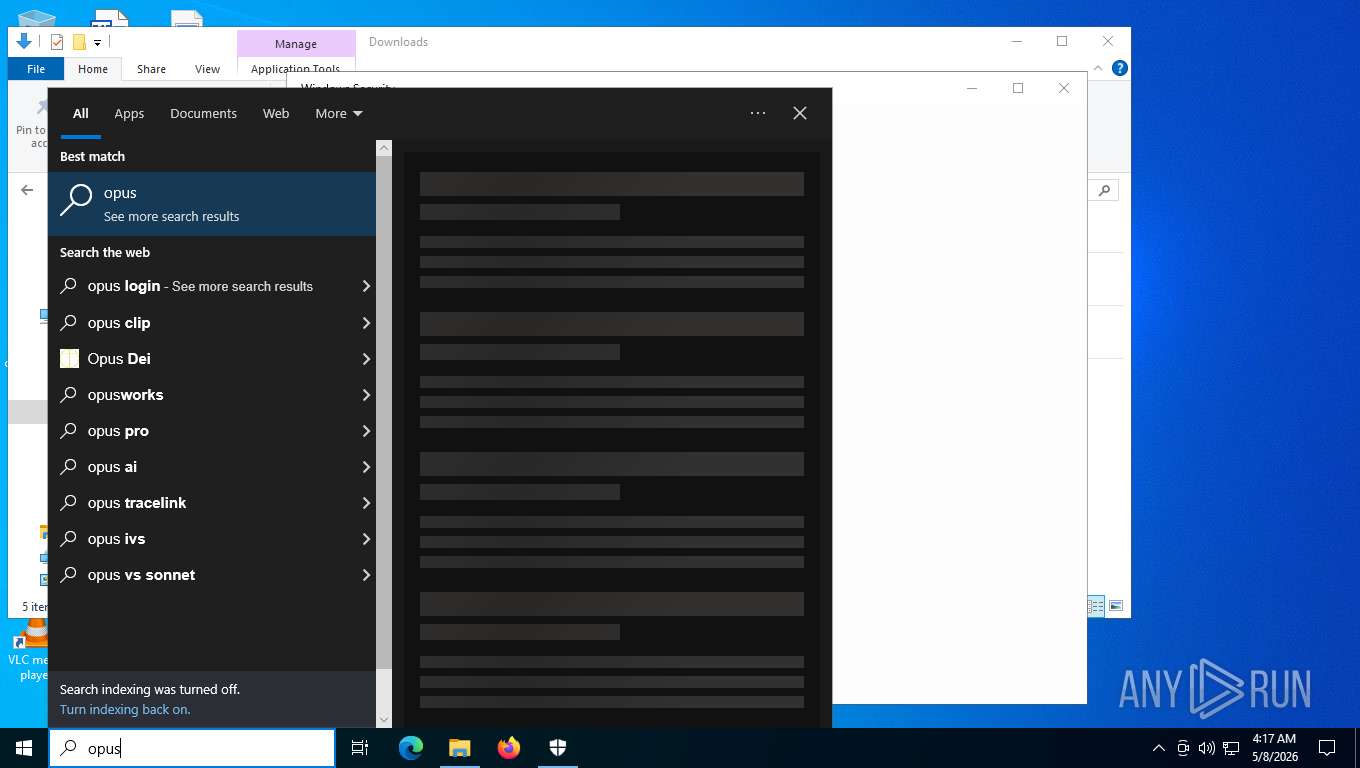
MALICIOUS
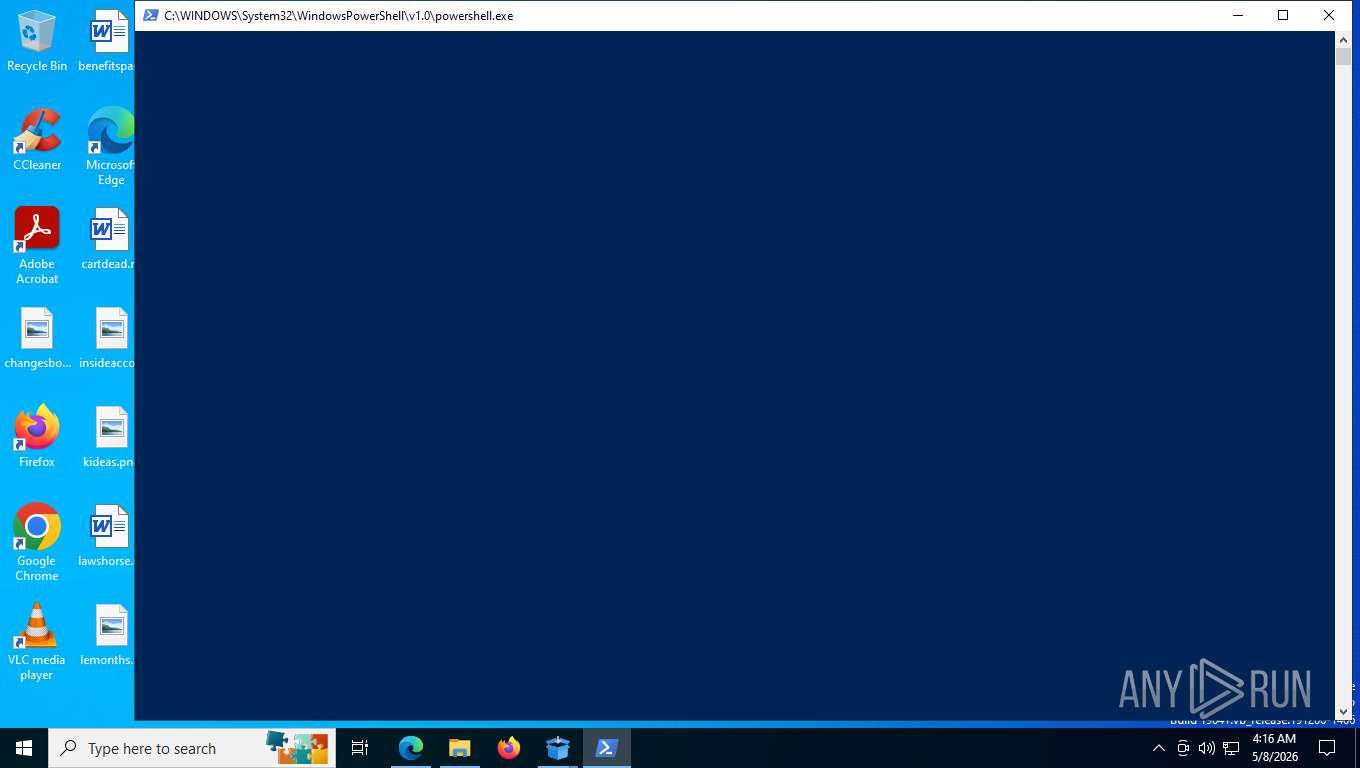
Run PowerShell with an invisible window
- powershell.exe (PID: 8728)
- powershell.exe (PID: 9724)
Changes powershell execution policy (Bypass)
- opus-4-7_x64.exe (PID: 8452)
- opus-4-7_x64.exe (PID: 7724)
Changes the autorun value in the registry
- onedrive_sync.exe (PID: 8732)
- OneSync.exe (PID: 8460)
- WinHealhCare.exe (PID: 1684)
Actions looks like stealing of personal data
- vicloud.exe (PID: 7404)
- svc_service.exe (PID: 7792)
- autodate.exe (PID: 8592)
VIDAR has been detected (YARA)
- vicloud.exe (PID: 7404)
Steals credentials from Web Browsers
- autodate.exe (PID: 8592)
- vicloud.exe (PID: 7404)
Uses Task Scheduler to run other applications
- OneSync.exe (PID: 8460)
Create files in the Startup directory
- powershell.exe (PID: 664)
AURA has been detected (SURICATA)
- autodate.exe (PID: 8592)
STEALC has been detected (SURICATA)
- vicloud.exe (PID: 7404)
VIDAR has been detected (SURICATA)
- vicloud.exe (PID: 7404)
Changes the login/logoff helper path in the registry
- svc_service.exe (PID: 7792)
Uses Task Scheduler to autorun other applications
- svc_service.exe (PID: 7792)
SUSPICIOUS
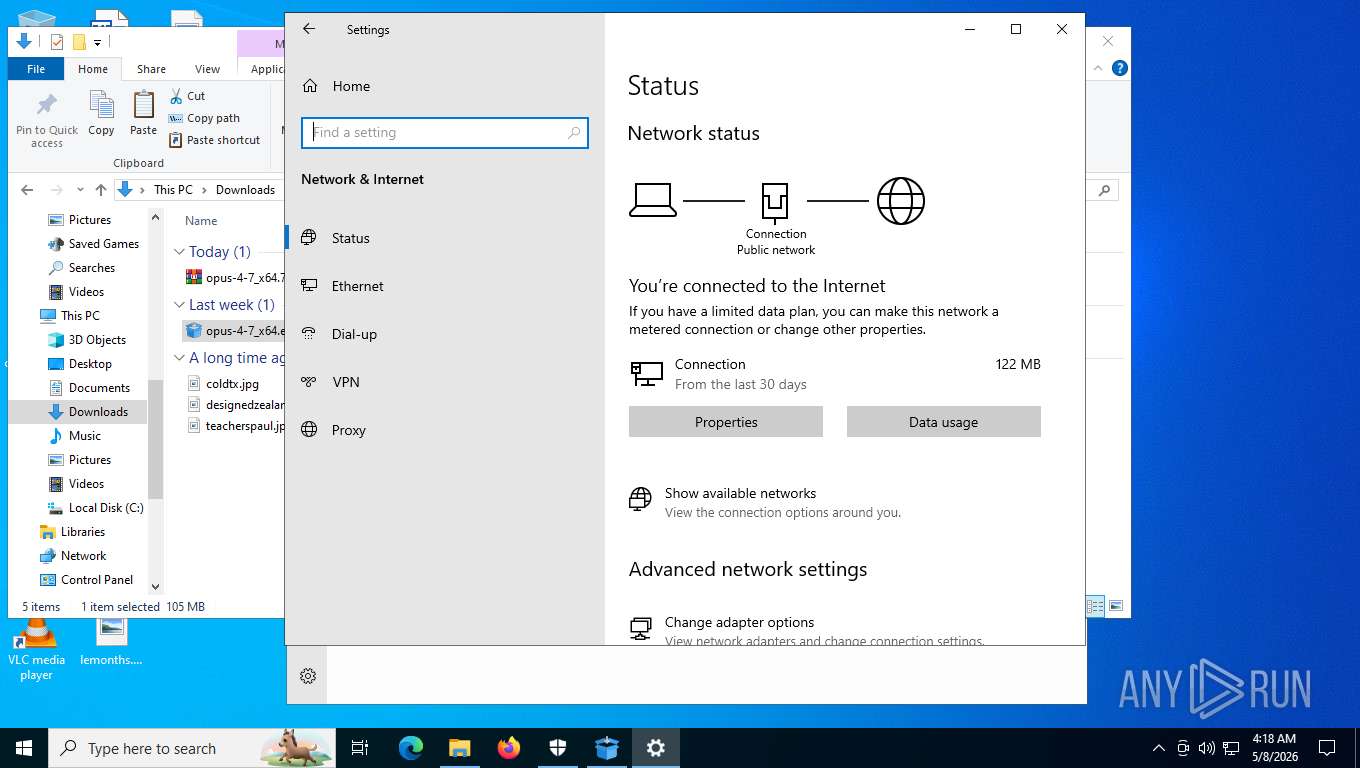
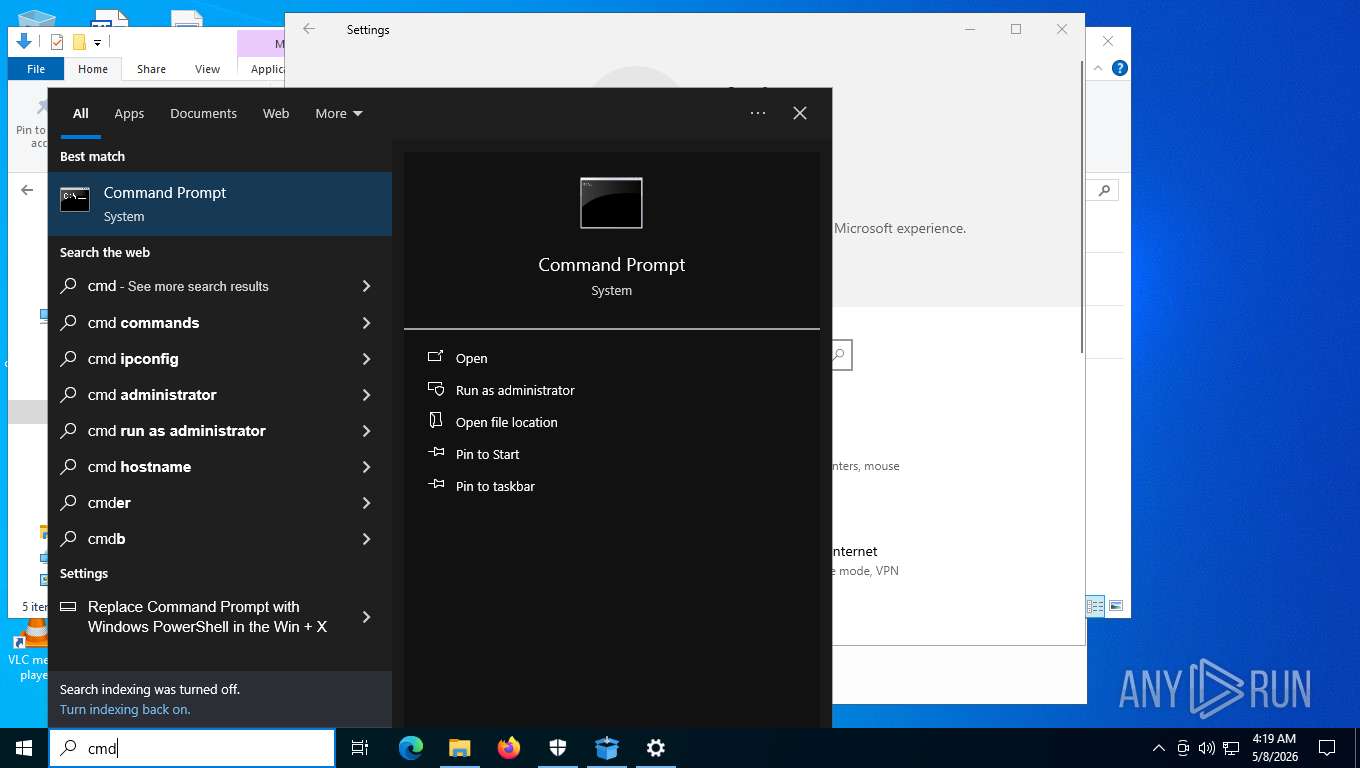
Process uses IPCONFIG to get network configuration information
- opus-4-7_x64.exe (PID: 9132)
- opus-4-7_x64.exe (PID: 8452)
- OneSync.exe (PID: 8460)
- WinHealhCare.exe (PID: 1684)
- opus-4-7_x64.exe (PID: 10152)
- opus-4-7_x64.exe (PID: 7724)
Reads the BIOS version
- opus-4-7_x64.exe (PID: 9132)
- opus-4-7_x64.exe (PID: 8452)
- opus-4-7_x64.exe (PID: 10152)
- opus-4-7_x64.exe (PID: 7724)
The process checks if it is being run in the virtual environment
- opus-4-7_x64.exe (PID: 9132)
- opus-4-7_x64.exe (PID: 8452)
- OneSync.exe (PID: 8460)
- WinHealhCare.exe (PID: 1684)
- opus-4-7_x64.exe (PID: 10152)
- opus-4-7_x64.exe (PID: 7724)
Checks for external IP
- svchost.exe (PID: 2232)
- opus-4-7_x64.exe (PID: 9132)
- opus-4-7_x64.exe (PID: 8452)
- opus-4-7_x64.exe (PID: 10152)
Reads the date of Windows installation
- opus-4-7_x64.exe (PID: 9132)
- autodate.exe (PID: 8592)
- opus-4-7_x64.exe (PID: 10152)
Application launched itself
- opus-4-7_x64.exe (PID: 9132)
- opus-4-7_x64.exe (PID: 10152)
The process bypasses the loading of PowerShell profile settings
- opus-4-7_x64.exe (PID: 8452)
- OneSync.exe (PID: 8460)
- opus-4-7_x64.exe (PID: 7724)
Starts POWERSHELL.EXE for commands execution
- opus-4-7_x64.exe (PID: 8452)
- OneSync.exe (PID: 8460)
- opus-4-7_x64.exe (PID: 7724)
Bypass execution policy to execute commands
- powershell.exe (PID: 8728)
- powershell.exe (PID: 9724)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8728)
- powershell.exe (PID: 9724)
Likely accesses (executes) a file from the Public directory
- OneSync.exe (PID: 8460)
- vicloud.exe (PID: 7404)
- svc_service.exe (PID: 7792)
- WinHealhCare.exe (PID: 1684)
- autodate.exe (PID: 8592)
- onedrive_sync.exe (PID: 8732)
- powershell.exe (PID: 664)
- schtasks.exe (PID: 3684)
The process creates files with name similar to system file names
- svc_service.exe (PID: 7792)
- OneSync.exe (PID: 8460)
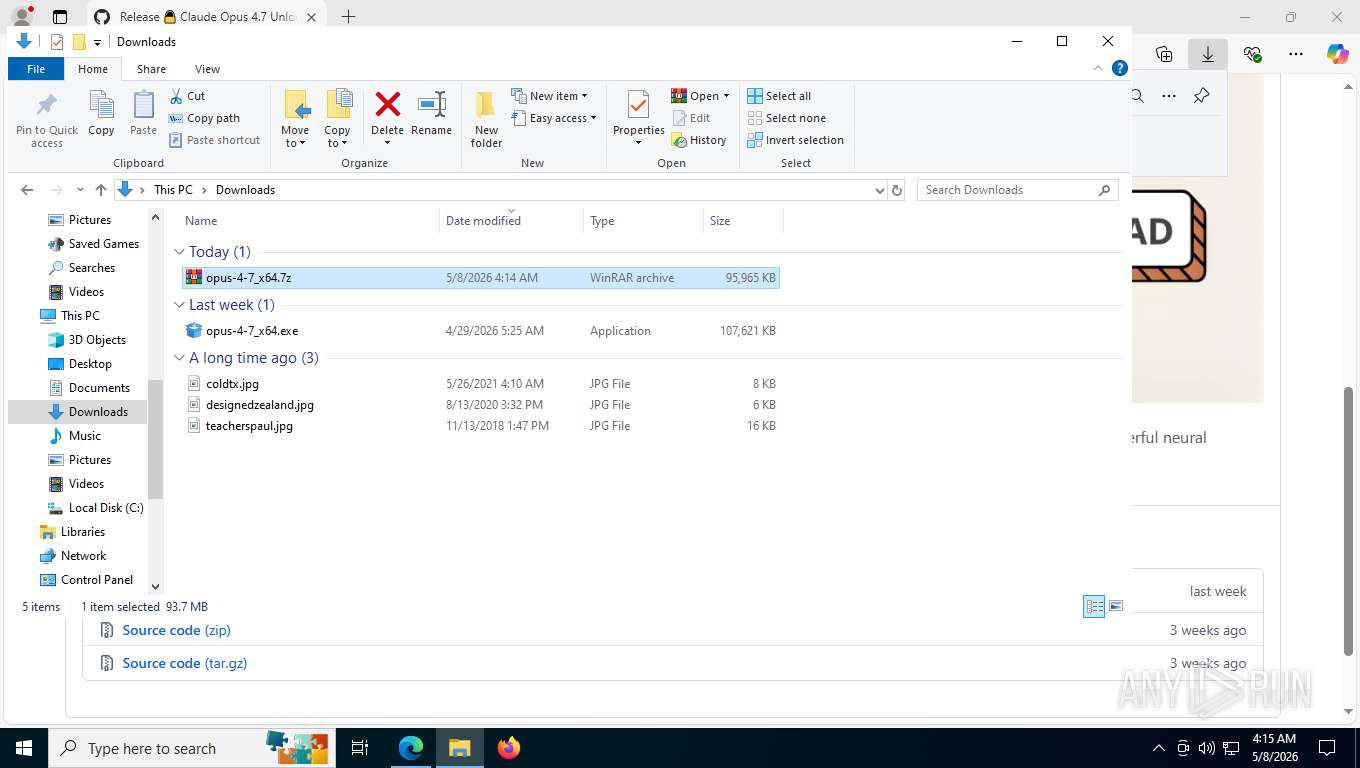
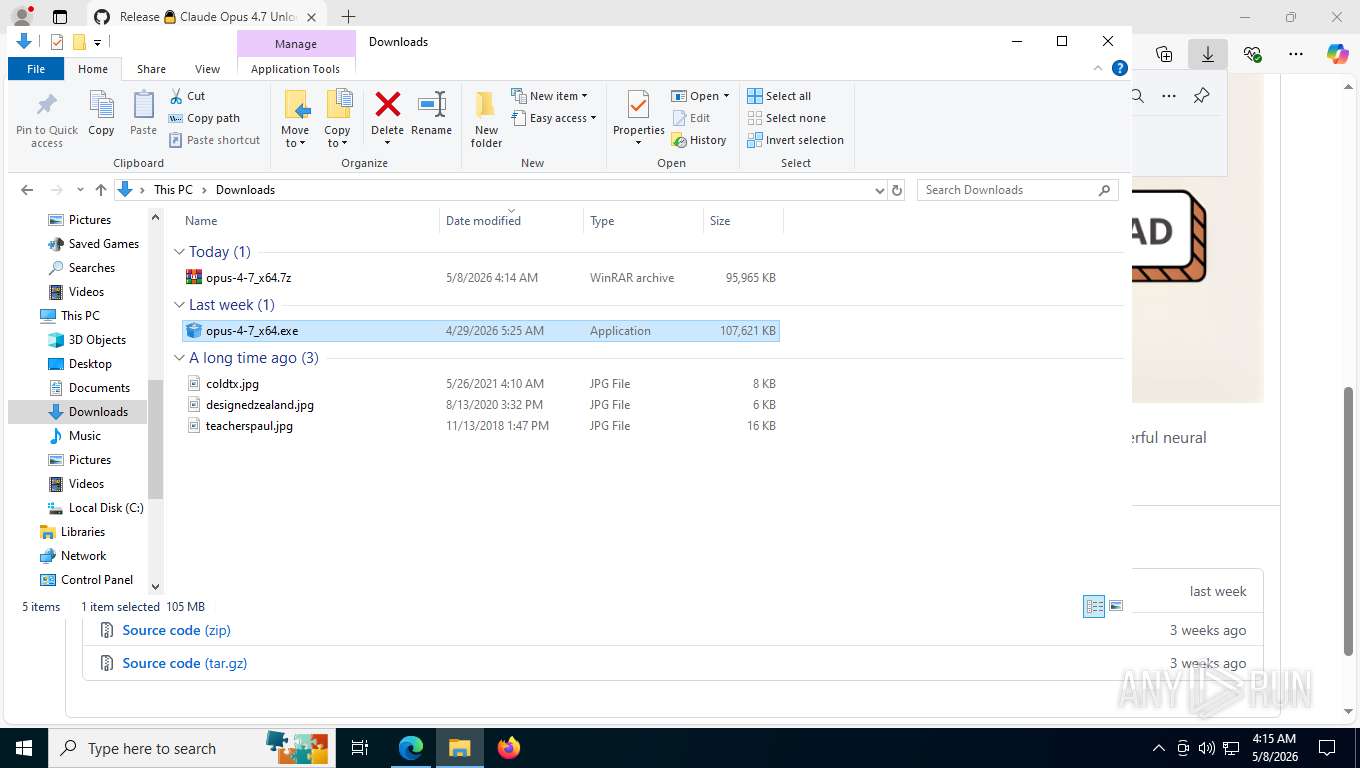
Executable content was dropped or overwritten
- svc_service.exe (PID: 7792)
- opus-4-7_x64.exe (PID: 8452)
- onedrive_sync.exe (PID: 8732)
- OneSync.exe (PID: 8460)
The process hide an interactive prompt from the user
- opus-4-7_x64.exe (PID: 8452)
- opus-4-7_x64.exe (PID: 7724)
Uses NETSH.EXE to add a firewall rule or allowed programs
- svc_service.exe (PID: 7792)
Possible stealing from crypto wallets
- opus-4-7_x64.exe (PID: 8452)
- vicloud.exe (PID: 7404)
- svc_service.exe (PID: 7792)
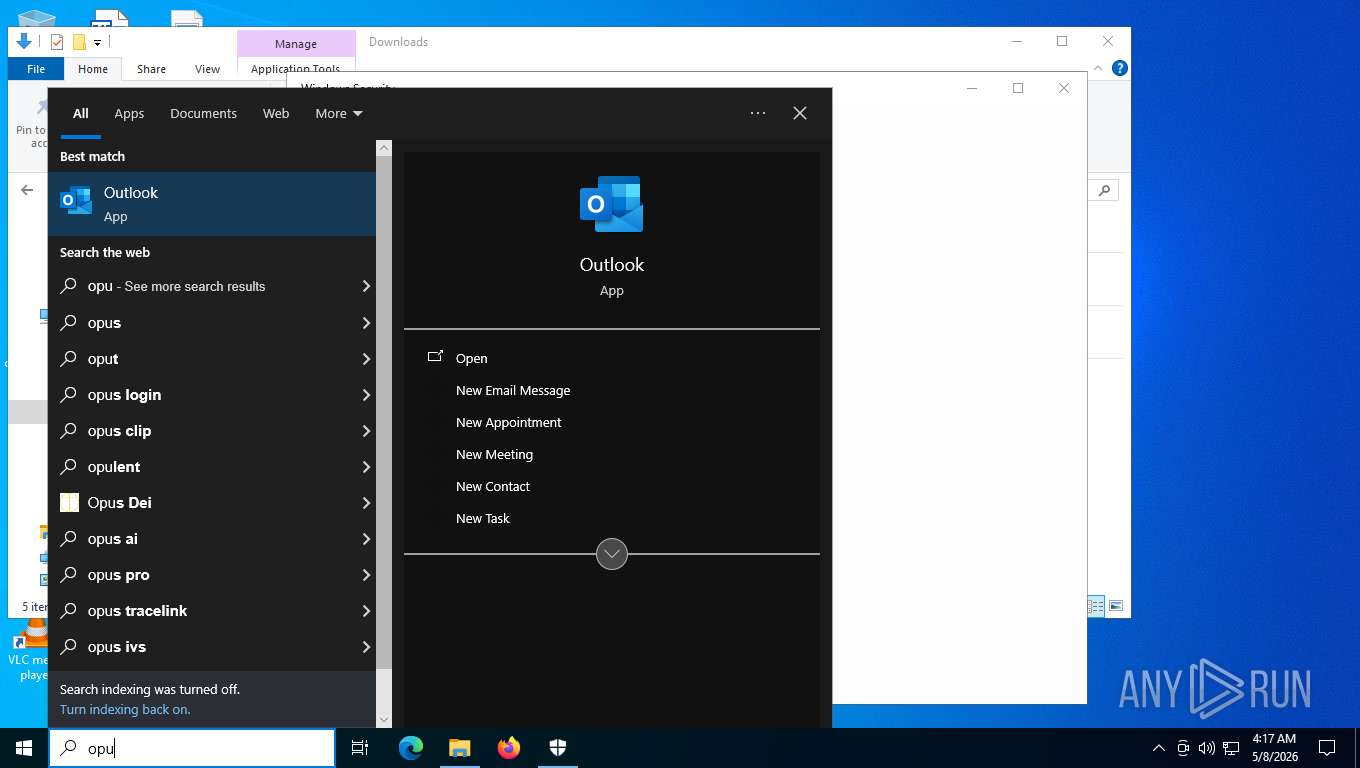
Searches for installed software
- vicloud.exe (PID: 7404)
- autodate.exe (PID: 8592)
There is functionality for capture public ip (YARA)
- OneSync.exe (PID: 8460)
- WinHealhCare.exe (PID: 1684)
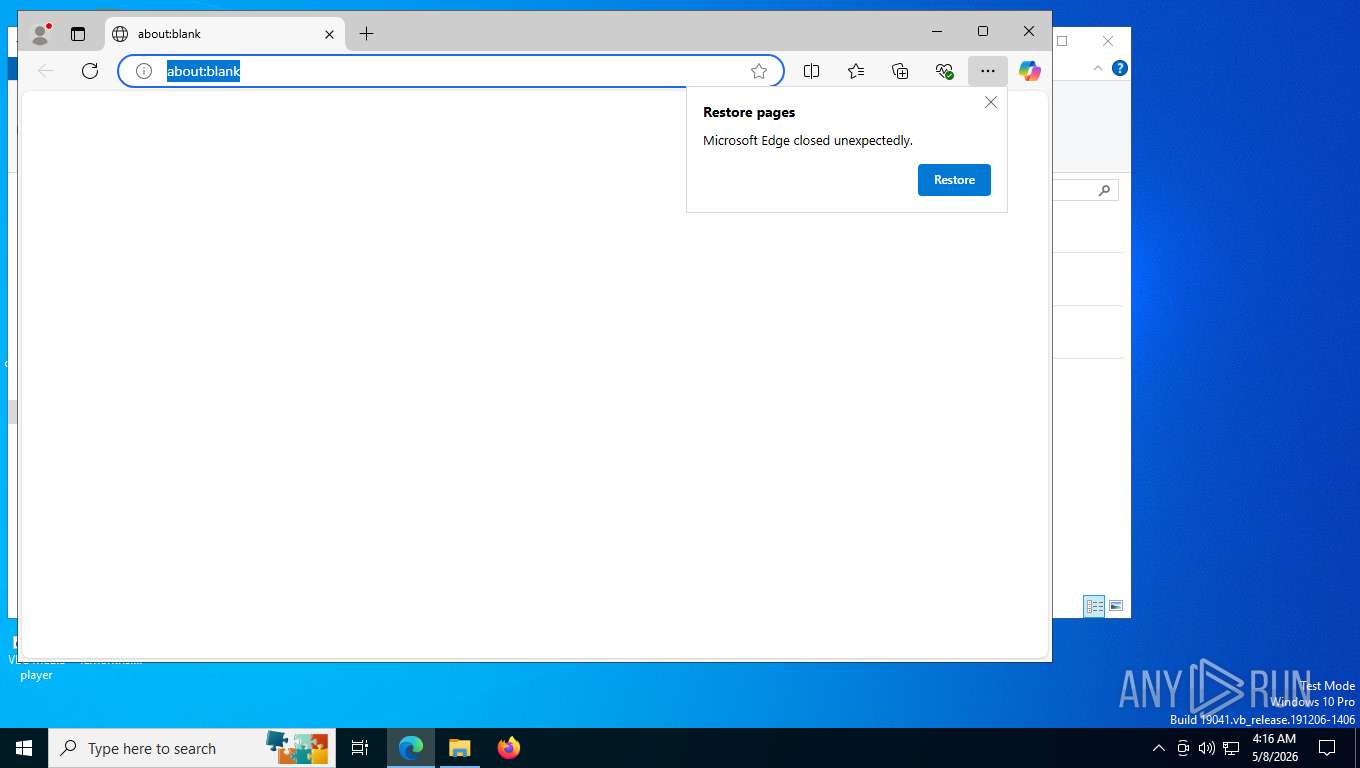
Browser headless start
- msedge.exe (PID: 1860)
- chrome.exe (PID: 7240)
- msedge.exe (PID: 8712)
- chrome.exe (PID: 8760)
- firefox.exe (PID: 8784)
- msedge.exe (PID: 9888)
- firefox.exe (PID: 8300)
- msedge.exe (PID: 2680)
- chrome.exe (PID: 7196)
- msedge.exe (PID: 9084)
- msedge.exe (PID: 9528)
- msedge.exe (PID: 9860)
There is functionality for VM detection VirtualBox (YARA)
- OneSync.exe (PID: 8460)
- WinHealhCare.exe (PID: 1684)
There is functionality for VM detection antiVM strings (YARA)
- OneSync.exe (PID: 8460)
- WinHealhCare.exe (PID: 1684)
There is functionality for VM detection VMWare (YARA)
- OneSync.exe (PID: 8460)
- WinHealhCare.exe (PID: 1684)
Multiple wallet extension IDs have been found
- vicloud.exe (PID: 7404)
- svc_service.exe (PID: 7792)
Possible stealing of email data
- vicloud.exe (PID: 7404)
- autodate.exe (PID: 8592)
Lists all scheduled tasks
- schtasks.exe (PID: 8816)
- schtasks.exe (PID: 8372)
- schtasks.exe (PID: 4916)
Creates scheduled task with highest privileges
- schtasks.exe (PID: 5648)
- schtasks.exe (PID: 8012)
- schtasks.exe (PID: 4776)
- schtasks.exe (PID: 3684)
Browser launch with unusual user-data-dir
- msedge.exe (PID: 9888)
- chrome.exe (PID: 8760)
- msedge.exe (PID: 9084)
Possible stealing from browsers
- vicloud.exe (PID: 7404)
The process verifies whether the antivirus software is installed
- vicloud.exe (PID: 7404)
Possible stealing from password managers
- vicloud.exe (PID: 7404)
Possible stealing of FTP data
- vicloud.exe (PID: 7404)
Possible stealing of cloud data
- vicloud.exe (PID: 7404)
Contacting a server suspected of hosting an CnC
- autodate.exe (PID: 8592)
- vicloud.exe (PID: 7404)
Creates scheduled task with ONLOGON parameter
- svc_service.exe (PID: 7792)
Uses REG/REGEDIT.EXE to modify or delete registry entries
- svc_service.exe (PID: 7792)
INFO
Application launched itself
- msedge.exe (PID: 7804)
- chrome.exe (PID: 2160)
- chrome.exe (PID: 9312)
- chrome.exe (PID: 10068)
- msedge.exe (PID: 3152)
- chrome.exe (PID: 9664)
- msedge.exe (PID: 7356)
- msedge.exe (PID: 9684)
- msedge.exe (PID: 1140)
- msedge.exe (PID: 9436)
- msedge.exe (PID: 2452)
- msedge.exe (PID: 7512)
- msedge.exe (PID: 10088)
- msedge.exe (PID: 9904)
- msedge.exe (PID: 8712)
- chrome.exe (PID: 8760)
- firefox.exe (PID: 8784)
- msedge.exe (PID: 9888)
- msedge.exe (PID: 9084)
- firefox.exe (PID: 8300)
Checks supported languages
- identity_helper.exe (PID: 5764)
- opus-4-7_x64.exe (PID: 9132)
- opus-4-7_x64.exe (PID: 8452)
- vicloud.exe (PID: 7404)
- OneSync.exe (PID: 8460)
- svc_service.exe (PID: 7792)
- WinHealhCare.exe (PID: 1684)
- autodate.exe (PID: 8592)
- onedrive_sync.exe (PID: 8732)
- SecHealthUI.exe (PID: 7116)
- identity_helper.exe (PID: 9324)
- opus-4-7_x64.exe (PID: 10152)
- opus-4-7_x64.exe (PID: 7724)
Reads the computer name
- identity_helper.exe (PID: 5764)
- opus-4-7_x64.exe (PID: 9132)
- opus-4-7_x64.exe (PID: 8452)
- svc_service.exe (PID: 7792)
- autodate.exe (PID: 8592)
- vicloud.exe (PID: 7404)
- WinHealhCare.exe (PID: 1684)
- OneSync.exe (PID: 8460)
- identity_helper.exe (PID: 9324)
- SecHealthUI.exe (PID: 7116)
- opus-4-7_x64.exe (PID: 10152)
- opus-4-7_x64.exe (PID: 7724)
Reads Environment values
- identity_helper.exe (PID: 5764)
- vicloud.exe (PID: 7404)
- svc_service.exe (PID: 7792)
- autodate.exe (PID: 8592)
- identity_helper.exe (PID: 9324)
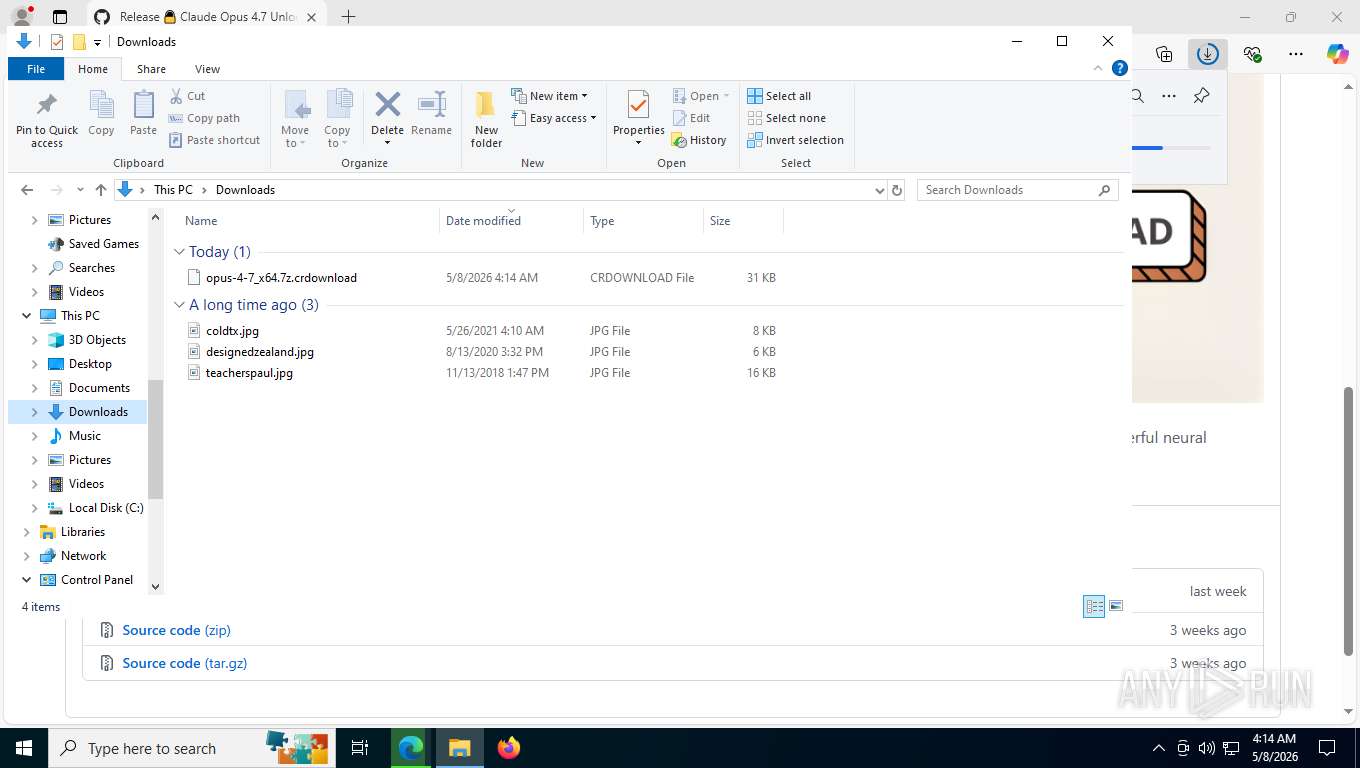
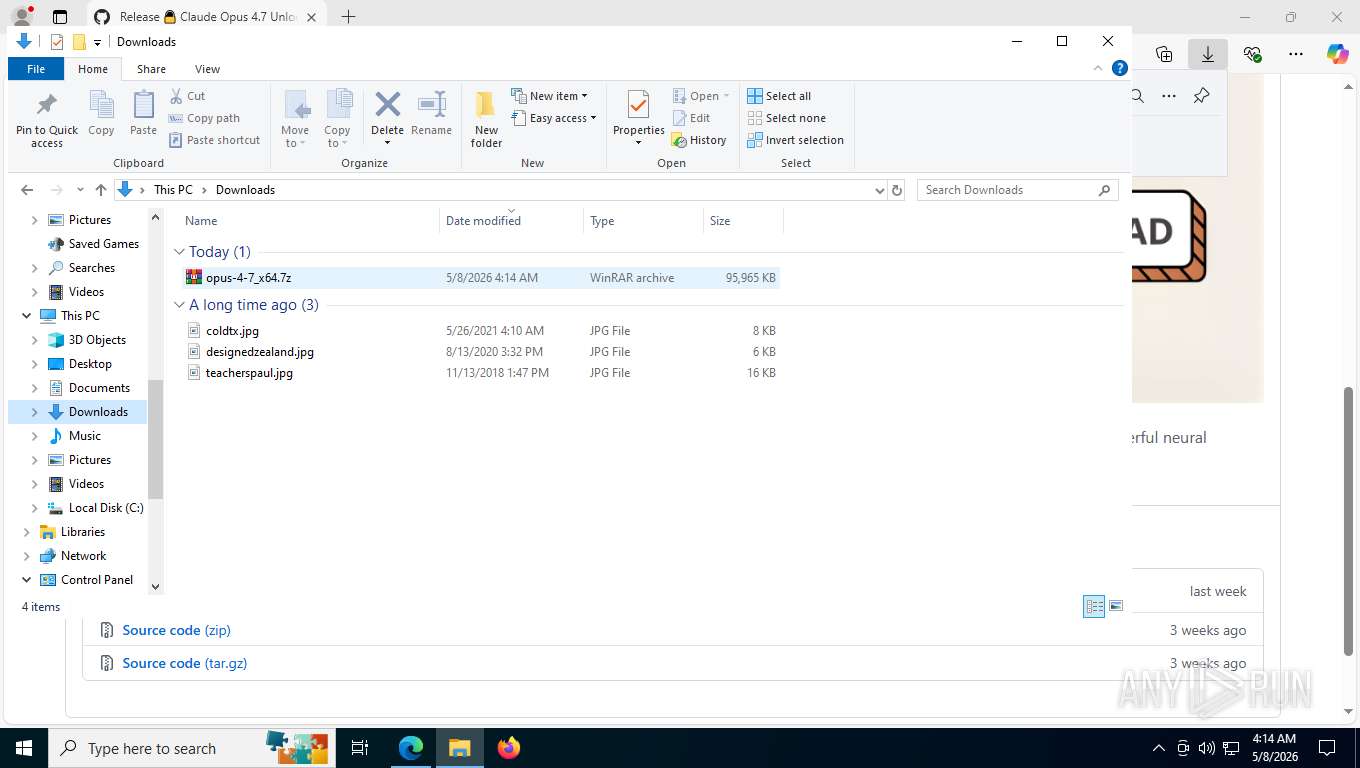
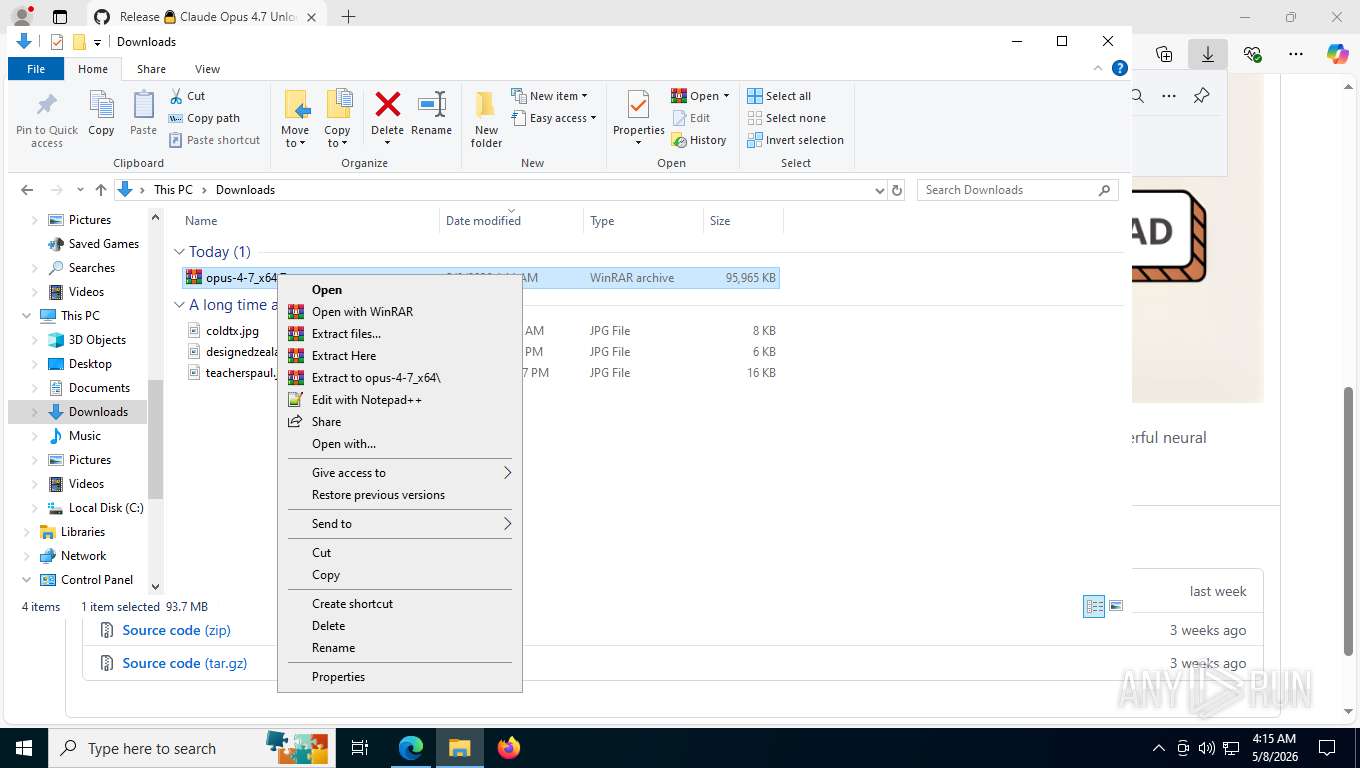
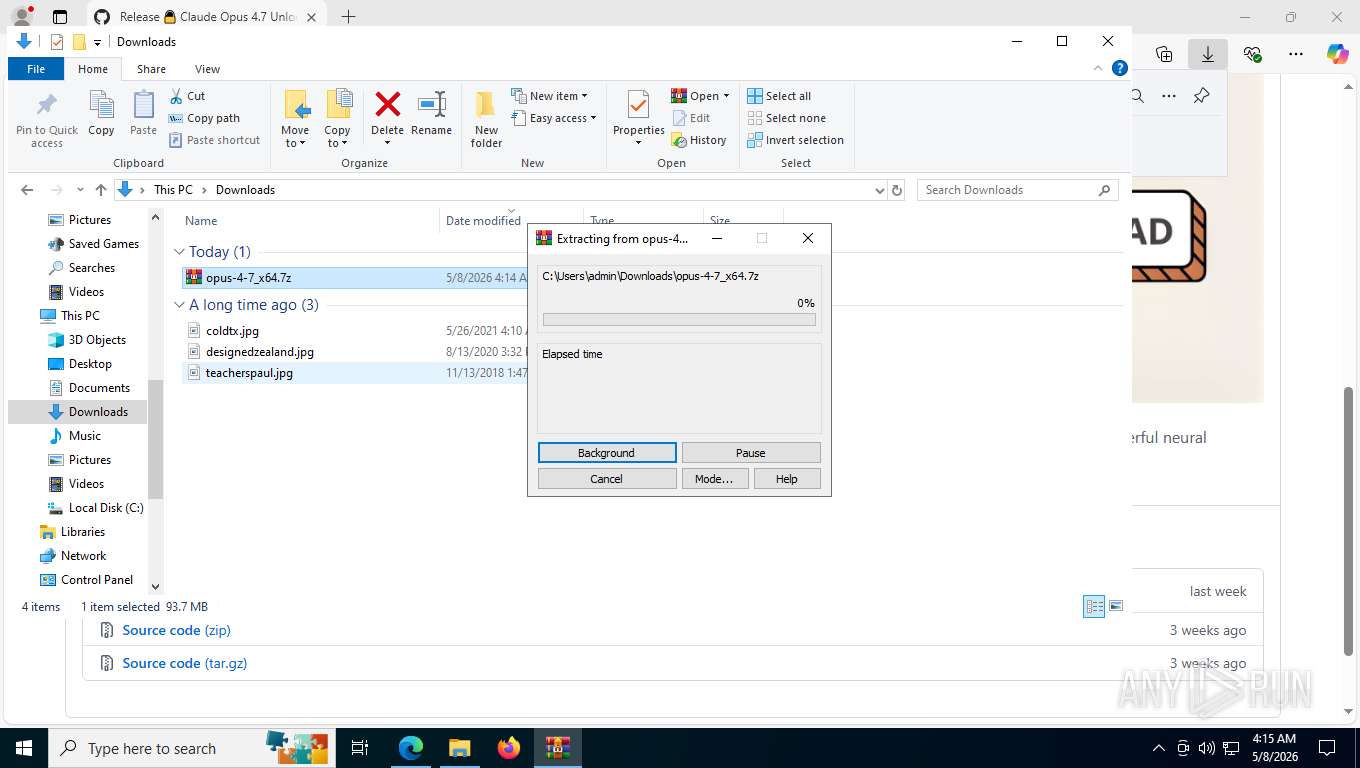
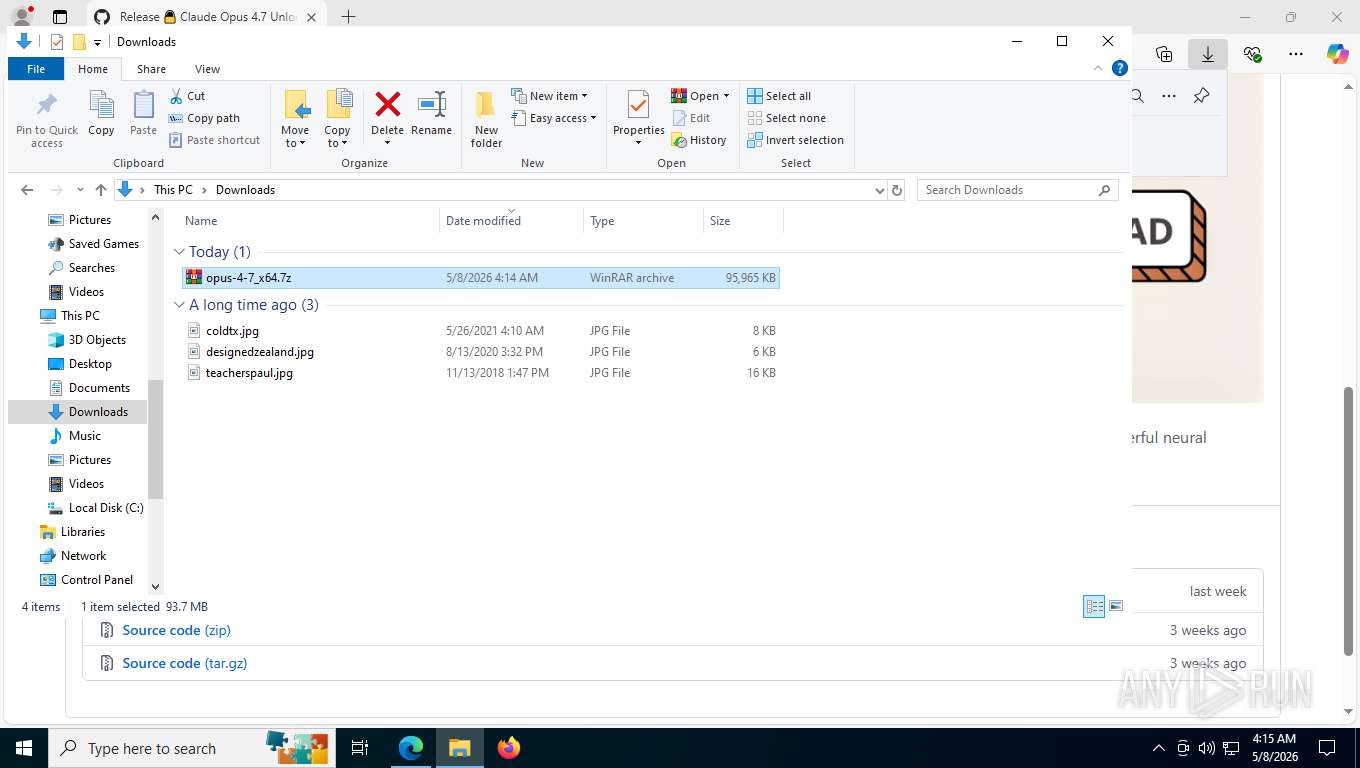
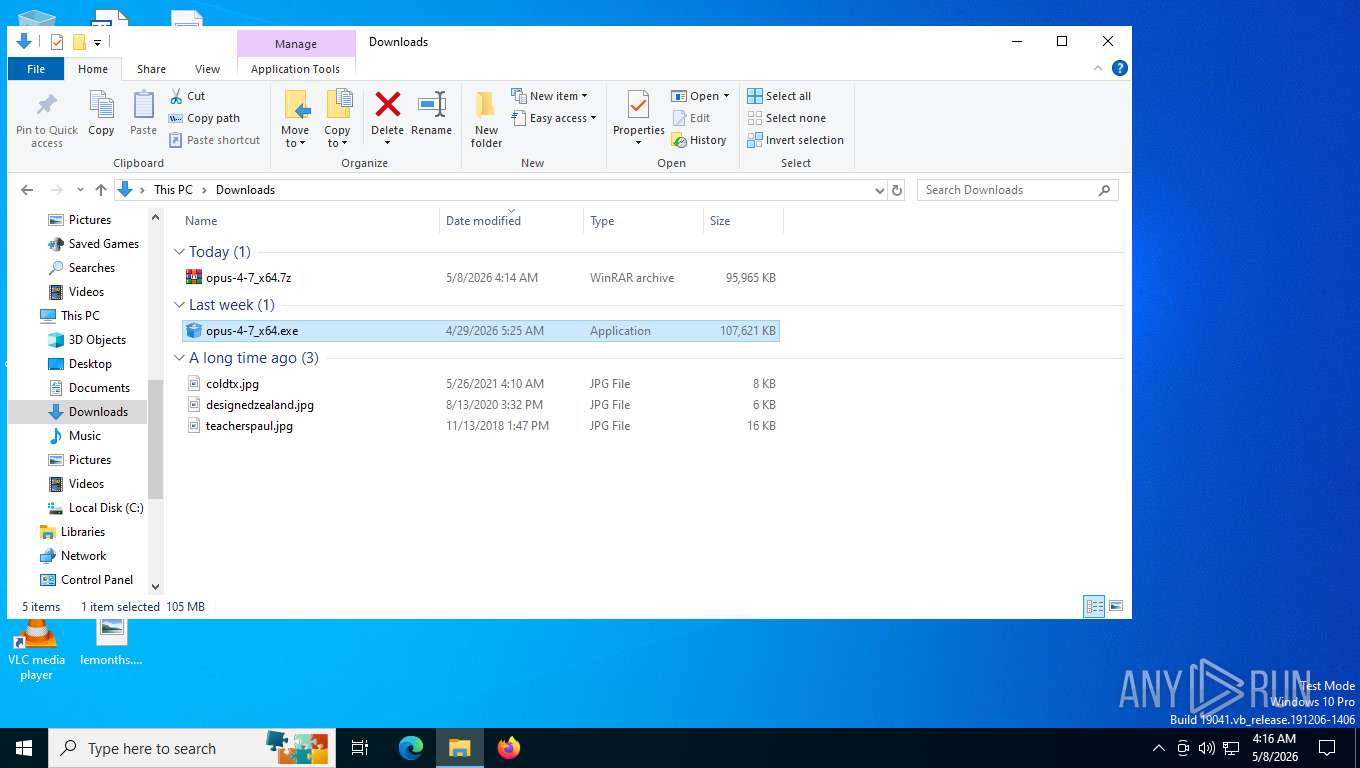
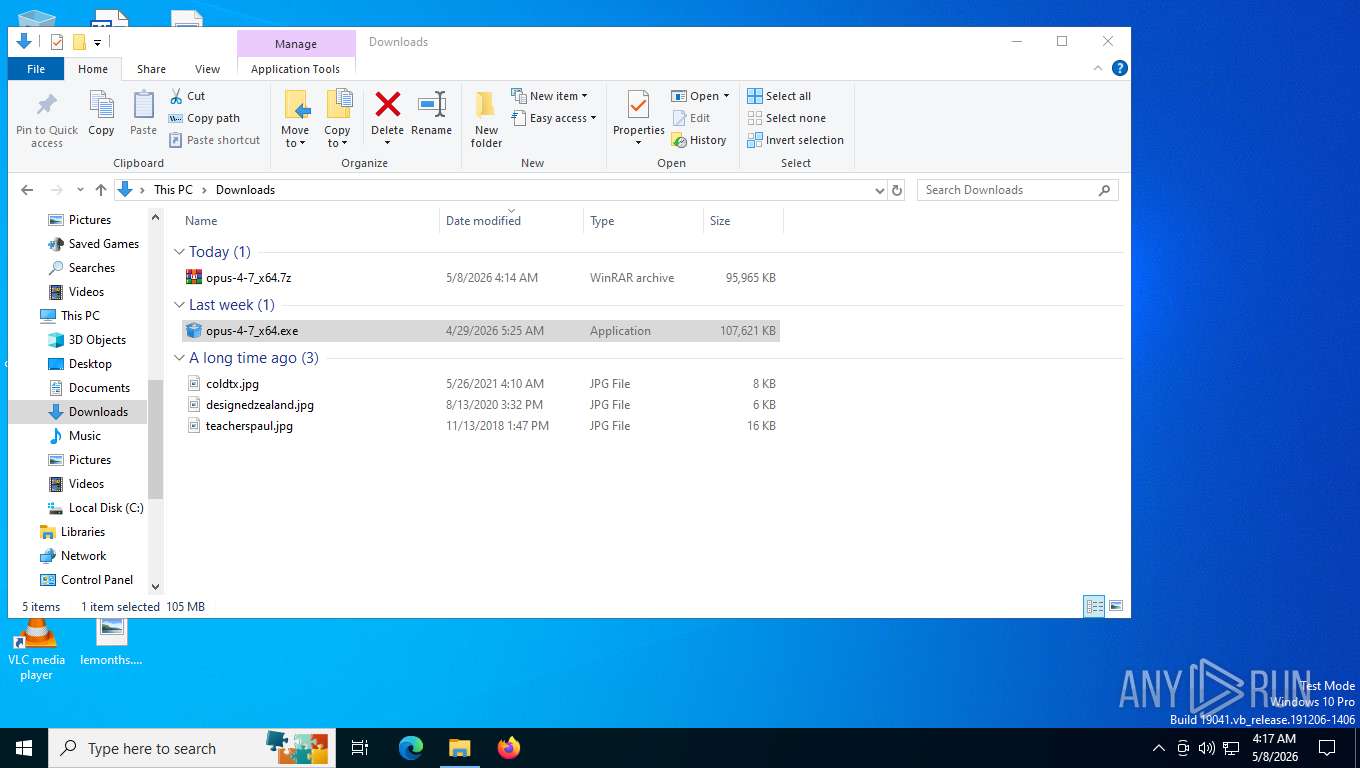
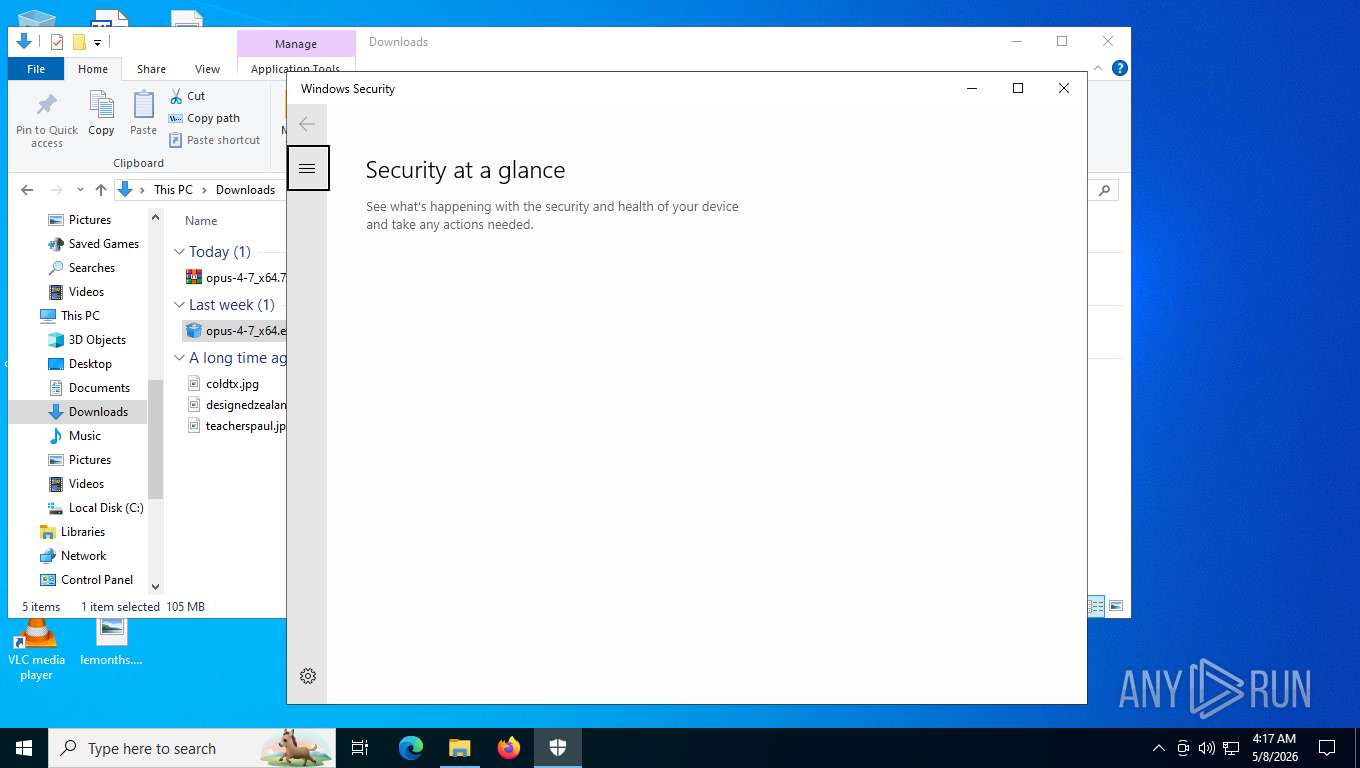
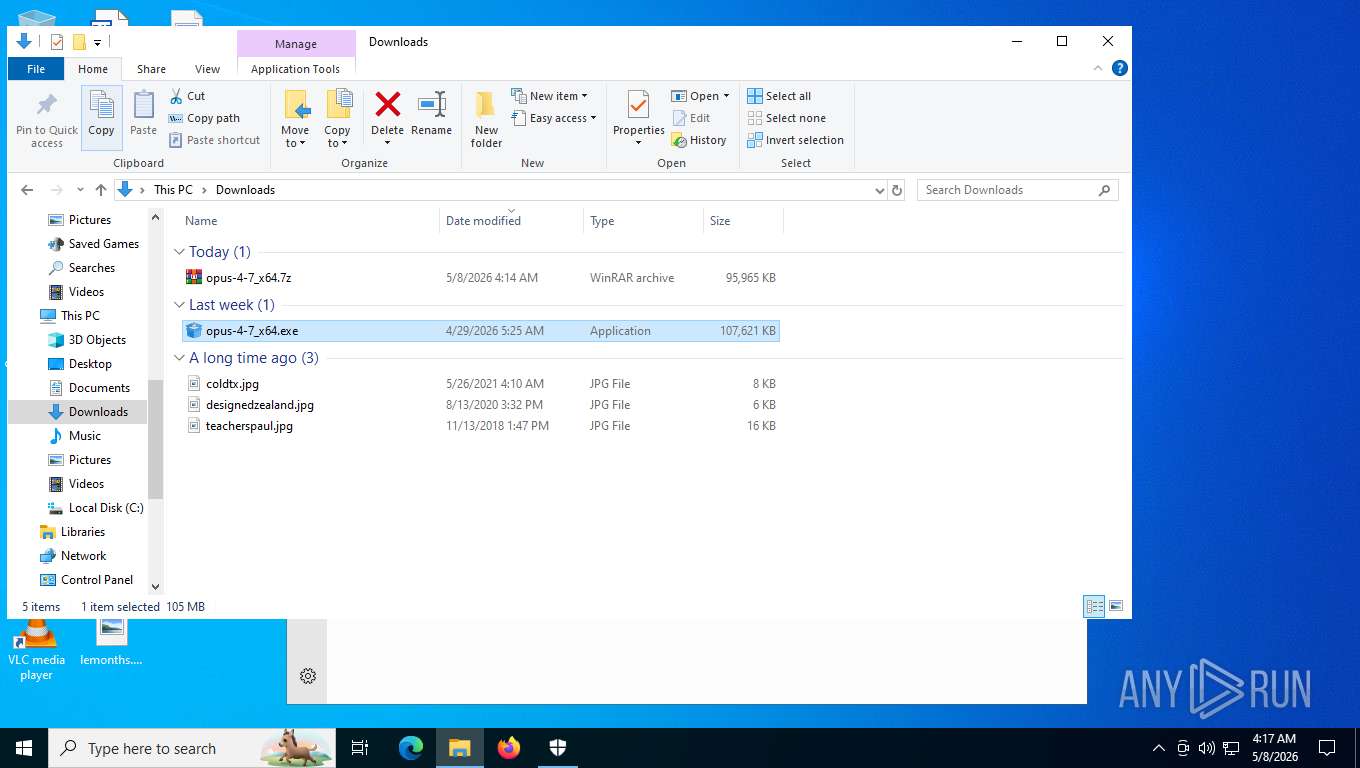
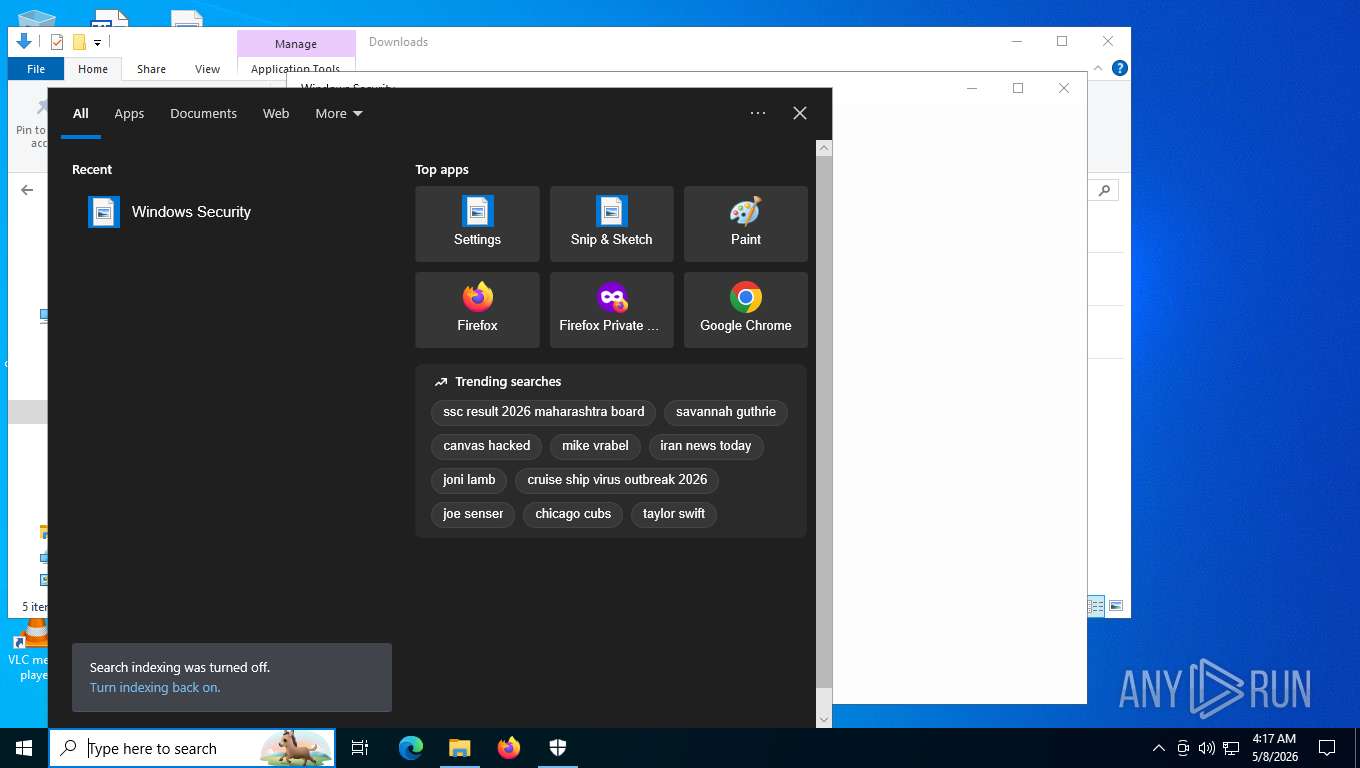
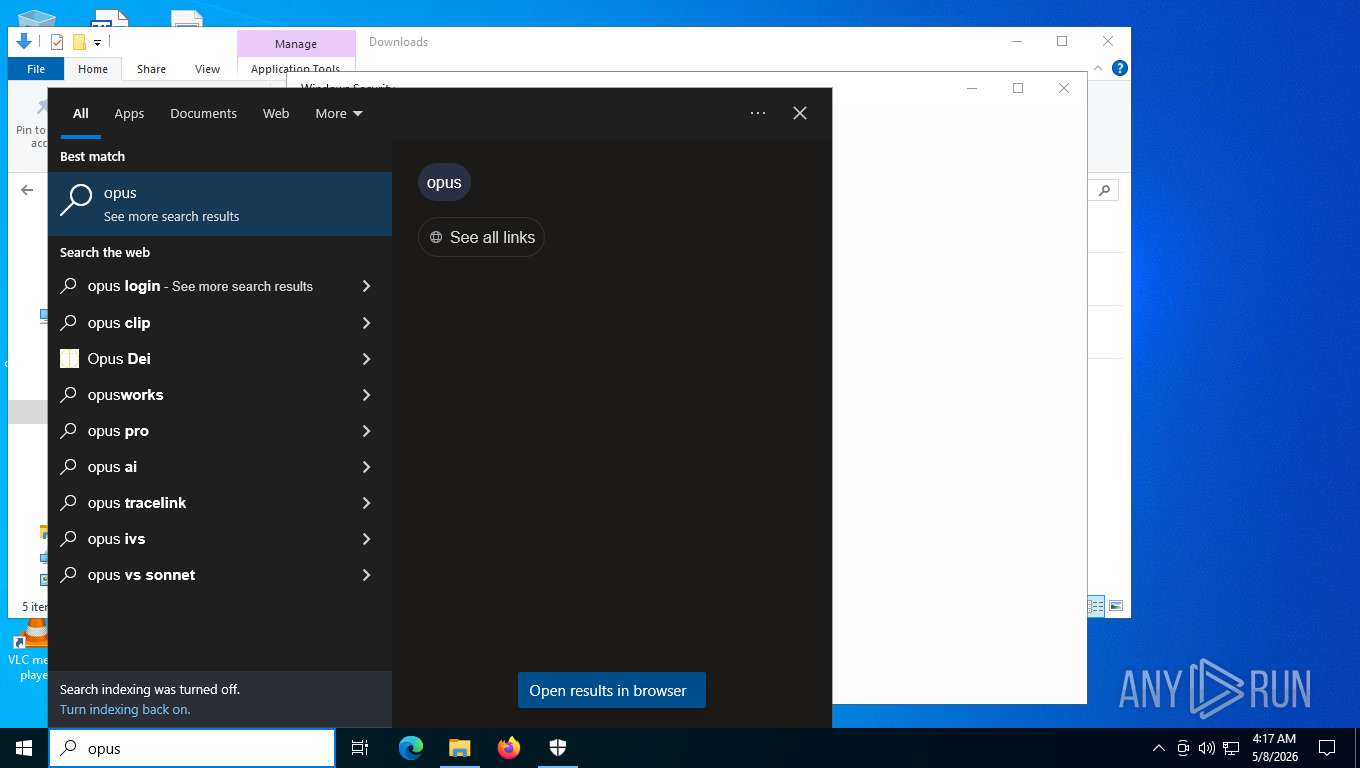
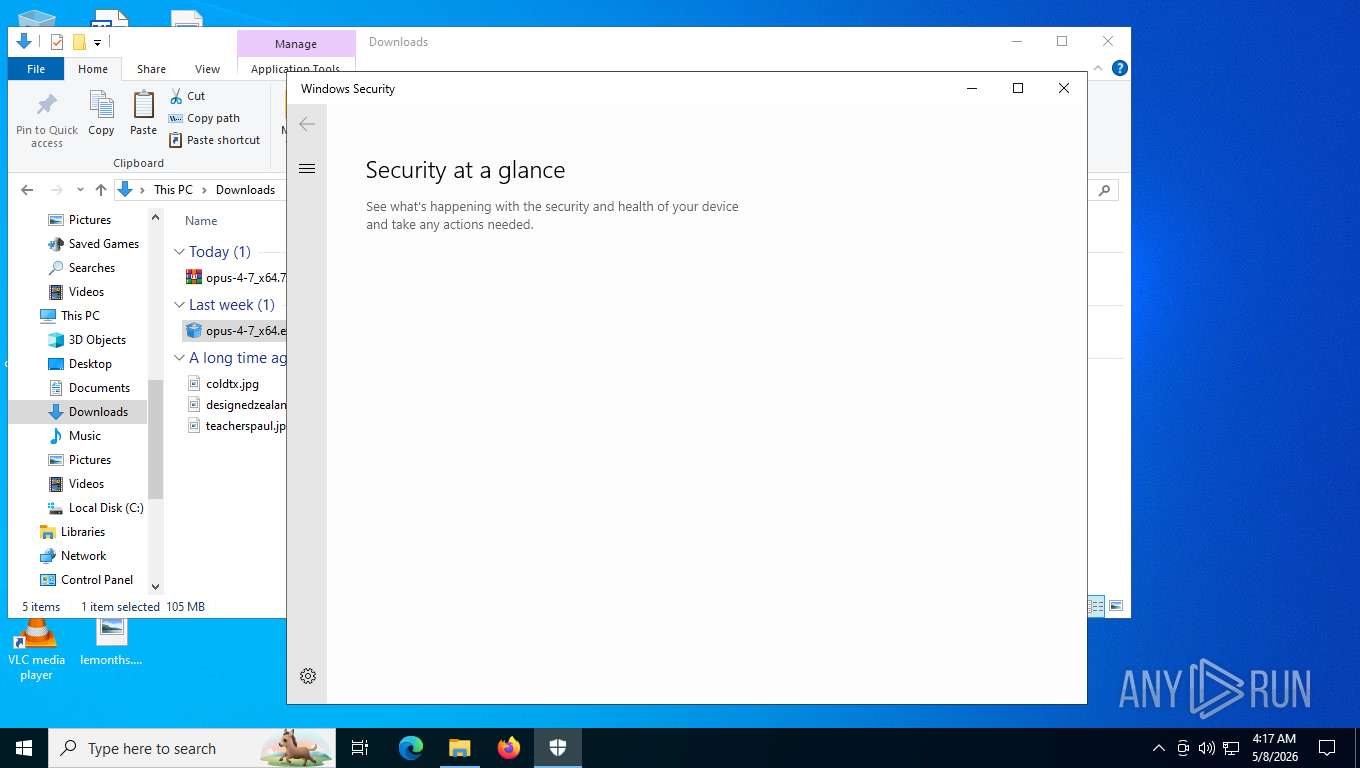
Manual execution by a user
- WinRAR.exe (PID: 9024)
- opus-4-7_x64.exe (PID: 9132)
- msedge.exe (PID: 1140)
- msedge.exe (PID: 3152)
- msedge.exe (PID: 9904)
- msedge.exe (PID: 9084)
- opus-4-7_x64.exe (PID: 10152)
- cmd.exe (PID: 1116)
Reads the machine GUID from the registry
- opus-4-7_x64.exe (PID: 9132)
- opus-4-7_x64.exe (PID: 8452)
- svc_service.exe (PID: 7792)
- autodate.exe (PID: 8592)
- opus-4-7_x64.exe (PID: 10152)
- opus-4-7_x64.exe (PID: 7724)
Creates files or folders in the user directory
- opus-4-7_x64.exe (PID: 9132)
- svc_service.exe (PID: 7792)
- onedrive_sync.exe (PID: 8732)
- WinHealhCare.exe (PID: 1684)
- OneSync.exe (PID: 8460)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 7132)
- getmac.exe (PID: 7976)
- getmac.exe (PID: 8260)
- getmac.exe (PID: 8404)
- getmac.exe (PID: 9960)
- getmac.exe (PID: 9516)
Reads CPU info
- opus-4-7_x64.exe (PID: 9132)
- opus-4-7_x64.exe (PID: 8452)
- vicloud.exe (PID: 7404)
- autodate.exe (PID: 8592)
- opus-4-7_x64.exe (PID: 10152)
- opus-4-7_x64.exe (PID: 7724)
Create files in a temporary directory
- opus-4-7_x64.exe (PID: 9132)
- powershell.exe (PID: 8728)
- svc_service.exe (PID: 7792)
- autodate.exe (PID: 8592)
- OneSync.exe (PID: 8460)
- opus-4-7_x64.exe (PID: 10152)
- powershell.exe (PID: 9724)
Reads security settings of Internet Explorer
- opus-4-7_x64.exe (PID: 9132)
- powershell.exe (PID: 8728)
- SecHealthUI.exe (PID: 7116)
- opus-4-7_x64.exe (PID: 10152)
- powershell.exe (PID: 9724)
Process checks computer location settings
- opus-4-7_x64.exe (PID: 9132)
- autodate.exe (PID: 8592)
- opus-4-7_x64.exe (PID: 10152)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8728)
- powershell.exe (PID: 9724)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8728)
- powershell.exe (PID: 9724)
The sample compiled with english language support
- opus-4-7_x64.exe (PID: 8452)
- OneSync.exe (PID: 8460)
Launching a file from a Registry key
- onedrive_sync.exe (PID: 8732)
- OneSync.exe (PID: 8460)
- WinHealhCare.exe (PID: 1684)
Reads product name
- vicloud.exe (PID: 7404)
- autodate.exe (PID: 8592)
Application based on Rust
- OneSync.exe (PID: 8460)
- vicloud.exe (PID: 7404)
- svc_service.exe (PID: 7792)
- onedrive_sync.exe (PID: 8732)
- WinHealhCare.exe (PID: 1684)
Reads Windows Product ID
- autodate.exe (PID: 8592)
Launching a file from Task Scheduler
- OneSync.exe (PID: 8460)
.NET Reactor protector has been detected
- svc_service.exe (PID: 7792)
Launching a file from the Startup directory
- powershell.exe (PID: 664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Vidar
(PID) Process(7404) vicloud.exe
C2 (2)https://pvp.hidayahnetwork.com/
https://web.telegram.org
BrowserExtensionsID (38)fiedbfgcleddlbcmgdigjgdfcggjcion
fmhmiaejopepamlcjkncpgpdjichnecm
oboonakemofpalcgghocfoadofidjkkk
blgcbajigpdfohpgcmbbfnphcgifjopc
bmhejbnmpamgfnomlahkonpanlkcfabg
bmikpgodpkclnkgmnpphehdgcimmided
bnfdmghkeppfadphbnkjcicejfepnbfe
bnfooenhhgcnhdkdjelgmmkpaemlnoek
caljgklbbfbcjjanaijlacgncafpegll
cnlhokffphohmfcddnibpohmkdfafdli
dbfoemgnkgieejfkaddieamagdfepnff
didegimhafipceonhjepacocaffmoppf
eajafomhmkipbjmfmhebemolkcicgfmd
eljmjmgjkbmpmfljlmklcfineebidmlo
fdfemjpbhpcjeadhbblfifdldedefnhe
fdjamakpfbbddfjaooikfcpapjohcfmg
fooolghllnmhmmndgjiamiiodkpenpbb
ghmbeldphafepmbegfdlkpapadhbakde
gmohoglkppnemohbcgjakmgengkeaphi
hfdkpbblioghdghhkdppipefbchgpohn
hifafgmccdpekplomjjkcfgodnhcellj
hldllnfgjbablcfcdcjldbbfopmohnda
hpcbfphmanablmeomioemmamedfffmpd
ibpjepoimpcdofeoalokgpjafnjonkpc
igkpcodhieompeloncfnbekccinhapdb
kfmlopbepahlcjbkfnnklglgibbopkbk
khhapgacijodhjokkcjmleaempmchlem
kmcfomidfpdkfieipokbalgegidffkal
lgbjhdkjmpgjgcbcdlhkokkckpjmedgc
mfgccjchihfkkindfppnaooecgfneiii
mfhbebgoclkghebffdldpobeajmbecfk
mlhdnjepakdfdaabohjgegnomlgeejep
mmhlniccooihdimnnjhamobppdhaolme
naepdomgkenhinolocfifgehidddafch
nhhldecdfagpbfggphklkaeiocfnaafm
njimencmbpfibibelblbbabiffimoajp
pnbabdldpneocemigmicebglmmfcjccm
oeljdldpnmdbchonielidgobddffflal
Total processes
392
Monitored processes
230
Malicious processes
11
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 416 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --string-annotations --noerrdialogs --always-read-main-dll --field-trial-handle=4544,i,17073541629081353428,11578234316569461194,262144 --disable-features=PaintHolding --variations-seed-version --disable-logging --log-level=3 --mojo-platform-channel-handle=4960 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 488 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --noerrdialogs --extension-process --renderer-sub-type=extension --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=20 --always-read-main-dll --field-trial-handle=4620,i,17073541629081353428,11578234316569461194,262144 --disable-features=PaintHolding --variations-seed-version --disable-logging --log-level=3 --mojo-platform-channel-handle=4616 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 664 | "powershell" -NoProfile -Command "$WshShell = New-Object -comObject WScript.Shell; $Shortcut = $WshShell.CreateShortcut('C:\ProgramData\Microsoft\Windows\Start Menu\Programs\StartUp\OneDriveSync.lnk'); $Shortcut.TargetPath = 'C:\Users\Public\OneDriveSync.exe'; $Shortcut.Save()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | OneSync.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6684,i,4753444727721145657,9611880739961301960,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6588 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 996 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3596,i,903194781072185168,14527032184858116909,262144 --variations-seed-version --disable-logging --log-level=3 --mojo-platform-channel-handle=3632 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 996 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ipconfig.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-first-run --disable-extensions --disable-background-networking --disable-sync --disable-logging --log-level=3 --disable-gpu --flag-switches-begin --disable-quic --flag-switches-end --do-not-de-elevate about:blank | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Temp\HeadlessChrome87601082640" --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=12 --field-trial-handle=4072,i,1325789536060985665,2213652972561814997,262144 --disable-features=PaintHolding --variations-seed-version --disable-logging --log-level=3 --mojo-platform-channel-handle=3748 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x214,0x218,0x21c,0x1fc,0x220,0x7ffe08e0fff8,0x7ffe08e10004,0x7ffe08e10010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
47 617
Read events
47 606
Write events
11
Delete events
0
Modification events
| (PID) Process: | (9024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (9024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (9024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (9024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8732) onedrive_sync.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | {NetworkManager} |
Value: C:\Users\admin\AppData\Roaming\Roaming\Data\Config\manager.exe | |||
| (PID) Process: | (7404) vicloud.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | TS_26b799fa |
Value: F2A08D2 | |||
| (PID) Process: | (8460) OneSync.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftAgent |
Value: C:\Users\Public\Documents\IntelProcess\DisplaySupport\OneSync.exe | |||
| (PID) Process: | (1684) WinHealhCare.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | USBDriver |
Value: C:\Users\Public\Pictures\DisplayMonitor\DriverModule\WinHealhCare.exe | |||
| (PID) Process: | (8460) OneSync.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | WindowsSystemUpdate |
Value: C:\ProgramData\Microsoft\EdgeUpdateSvc.exe | |||
| (PID) Process: | (10152) SecurityHealthHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @%systemroot%\system32\SecurityHealthAgent.dll,-12001 |
Value: Windows Security | |||
Executable files
16
Suspicious files
478
Text files
862
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFdf954.TMP | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFdf964.TMP | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFdf964.TMP | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFdf974.TMP | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFdf993.TMP | — | |
MD5:— | SHA256:— | |||
| 7804 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
616
TCP/UDP connections
238
DNS requests
212
Threats
89
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 924 b | whitelisted |
4312 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 132 b | whitelisted |
4312 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:ML9XZKeF5nIUT0k50isk7yY7garHMiEWPTGUNhSNwUw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 99 b | whitelisted |
4312 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
4312 | msedge.exe | GET | 200 | 140.82.121.4:443 | https://github.com/anthropic-claudecode/claude-opus-4.7/releases/tag/claude-opus-4.7 | US | html | 206 Kb | whitelisted |
4312 | msedge.exe | GET | 200 | 52.123.243.202:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1778228061&lafgdate=0 | US | text | 4.14 Kb | whitelisted |
4312 | msedge.exe | GET | 302 | 140.82.121.4:443 | https://github.com/anthropic-claudecode/claude-opus-4.7/raw/claude-opus-4.7/assets/claudeopus.png | US | — | — | whitelisted |
4312 | msedge.exe | GET | 200 | 150.171.109.193:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
4312 | msedge.exe | GET | 200 | 92.123.104.38:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | NL | text | 665 Kb | whitelisted |
4312 | msedge.exe | GET | 200 | 185.199.109.215:443 | https://github.githubassets.com/assets/light-2ff56e1b36116ee2.css | US | text | 74.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8000 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | SearchApp.exe | 92.123.104.38:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
5532 | SearchApp.exe | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4312 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
4312 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4312 | msedge.exe | 52.123.243.202:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
4312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
4312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
4312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
4312 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
8000 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2232 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (checkip .amazonaws .com) |
9132 | opus-4-7_x64.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |
9132 | opus-4-7_x64.exe | Device Retrieving External IP Address Detected | ET INFO External IP Check (checkip .amazonaws .com) |
2232 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessChrome87601082640 directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessEdge98881082718 directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\HeadlessEdge90841083187 directory exists )
|