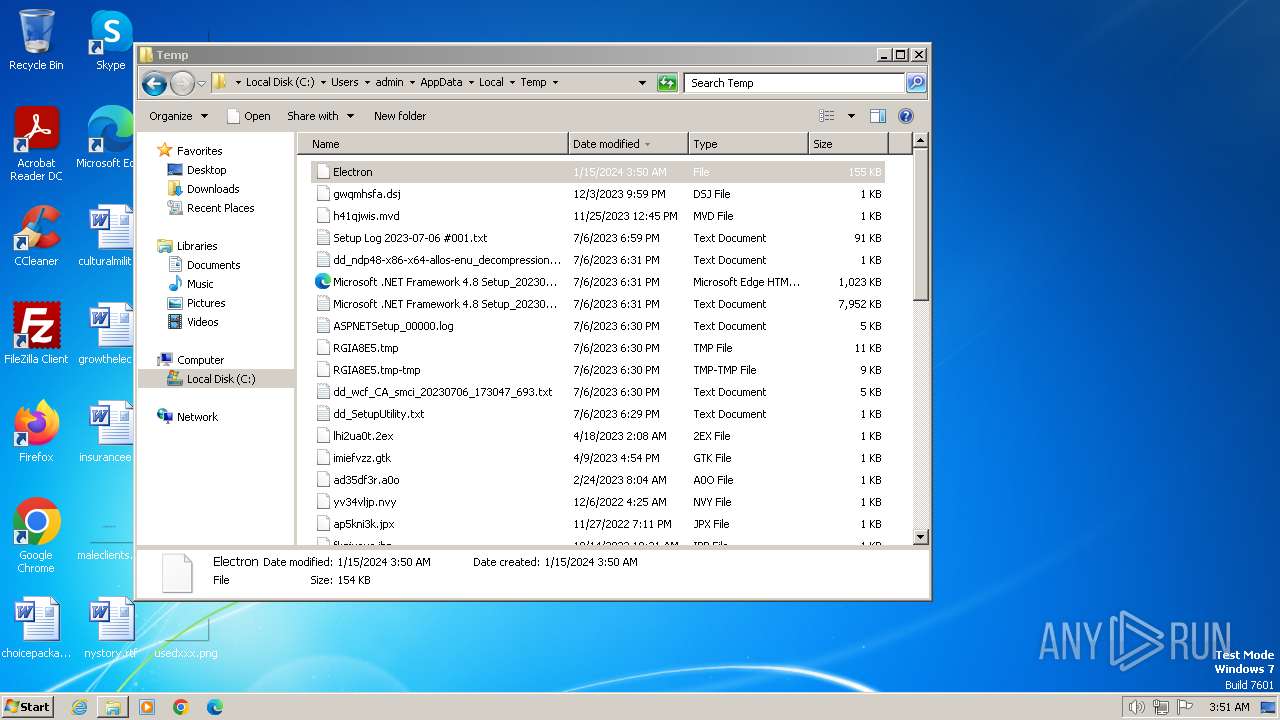
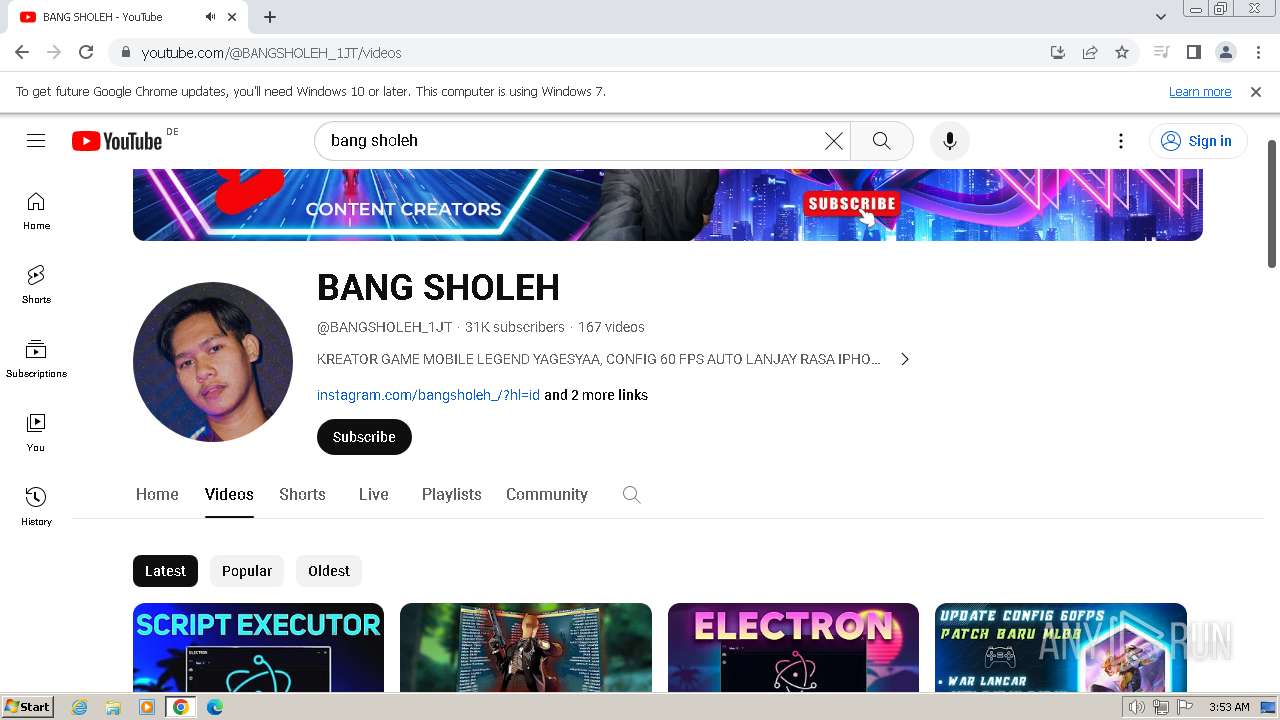
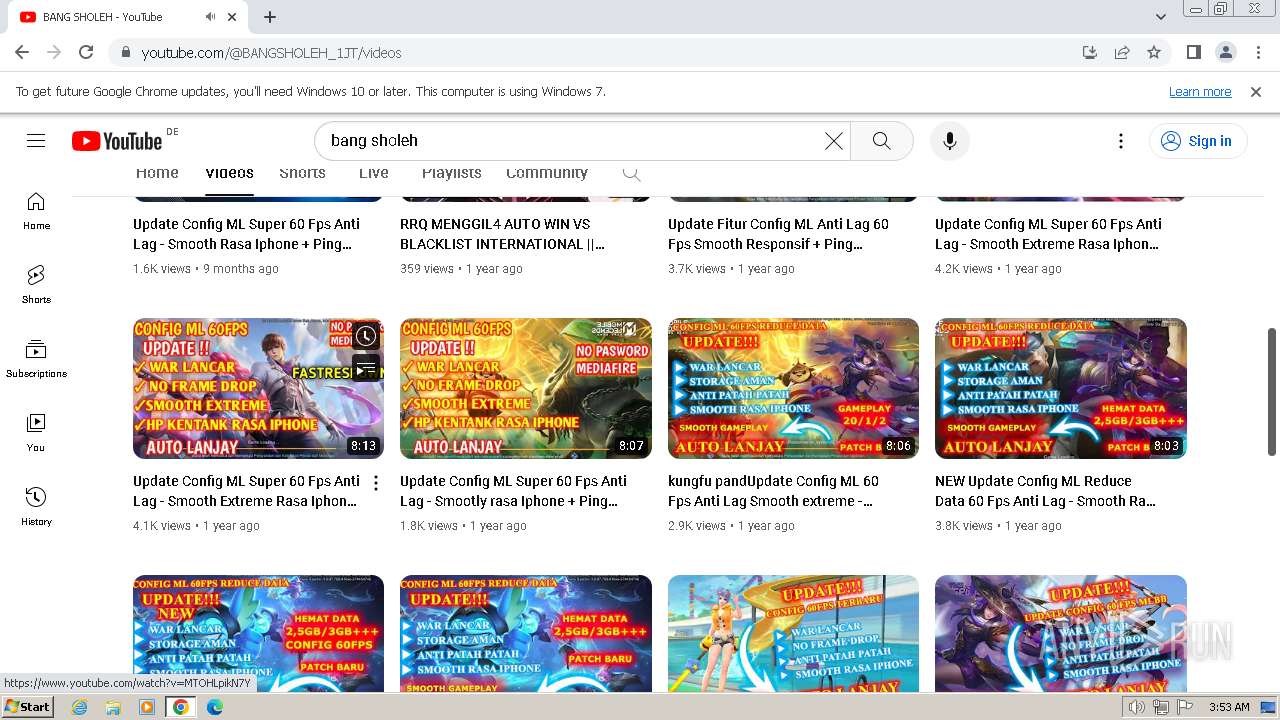
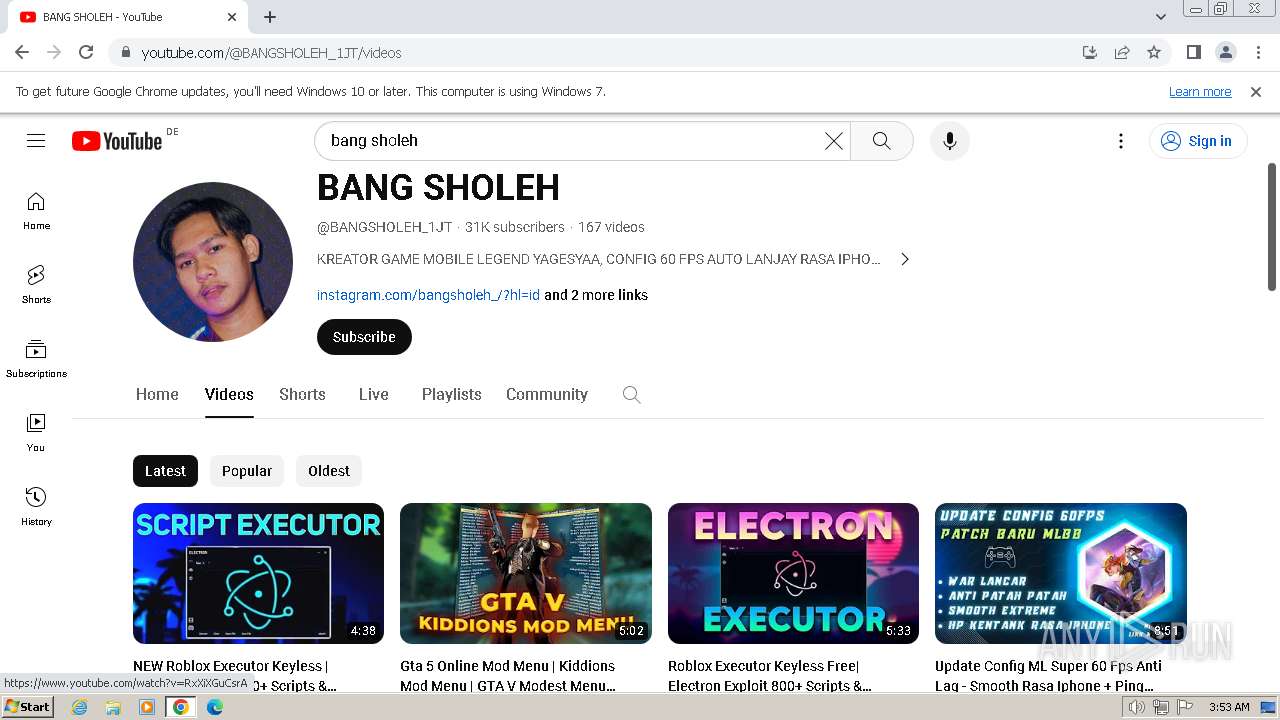
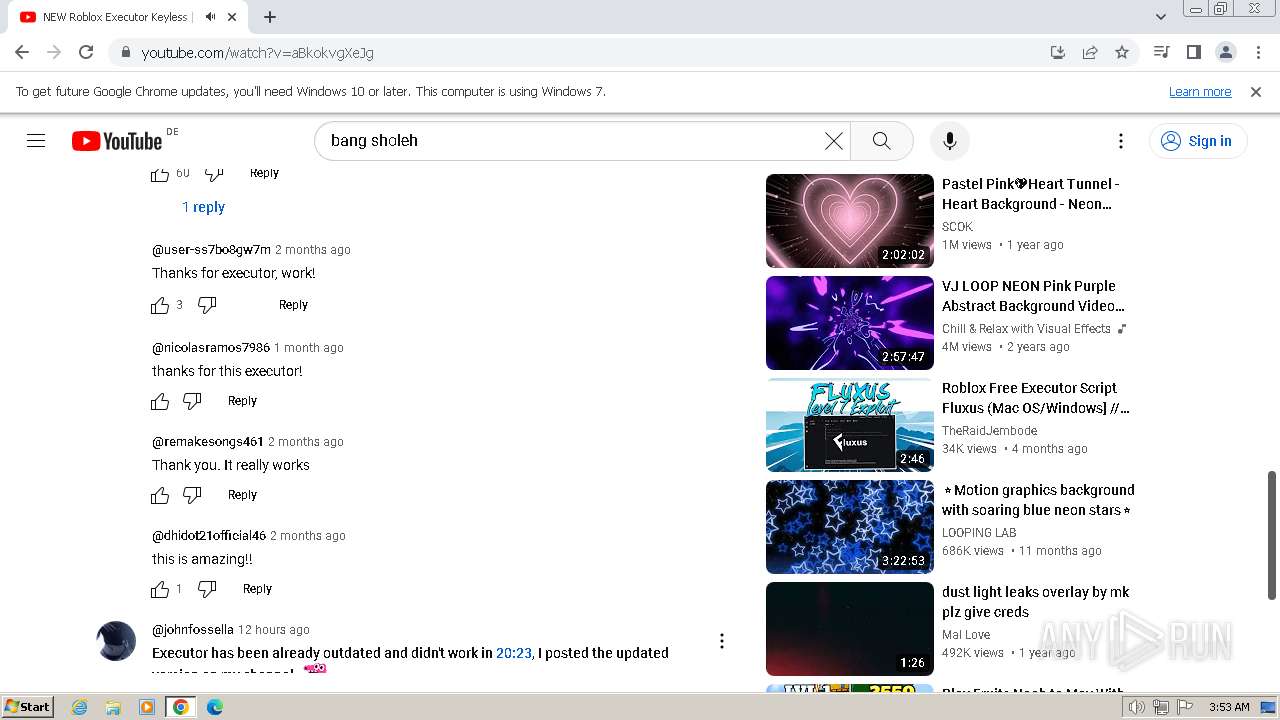
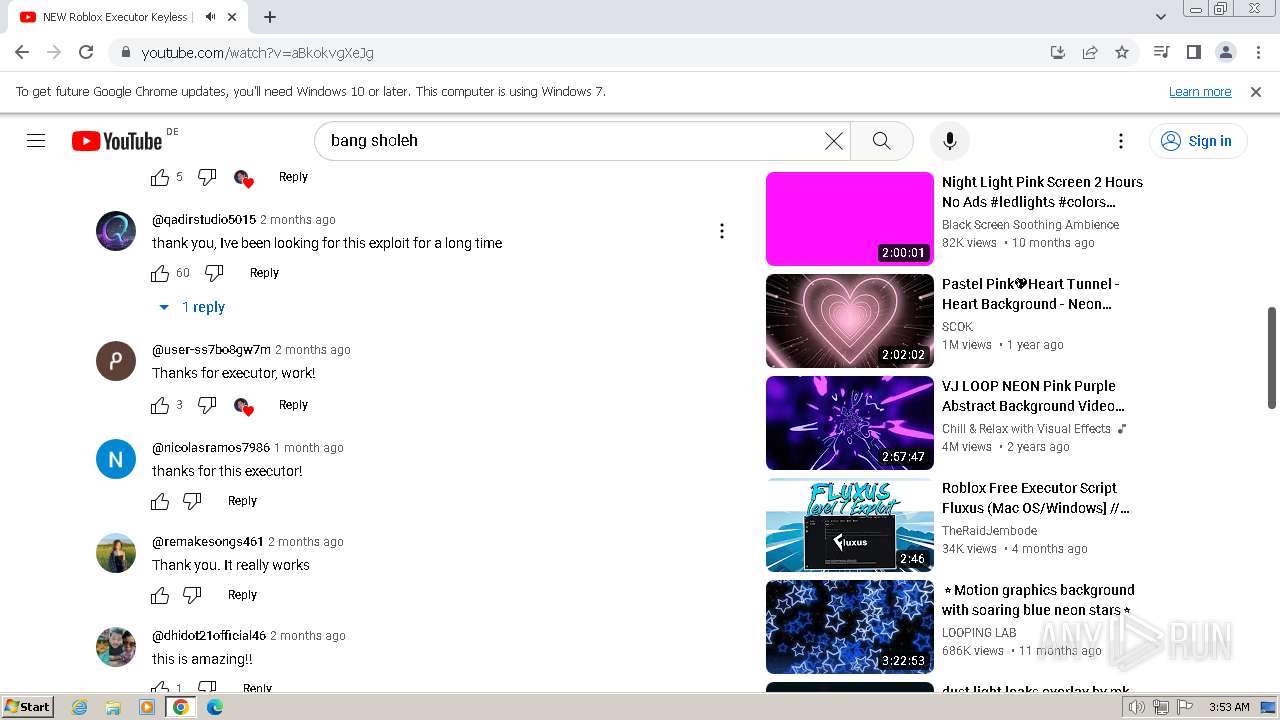
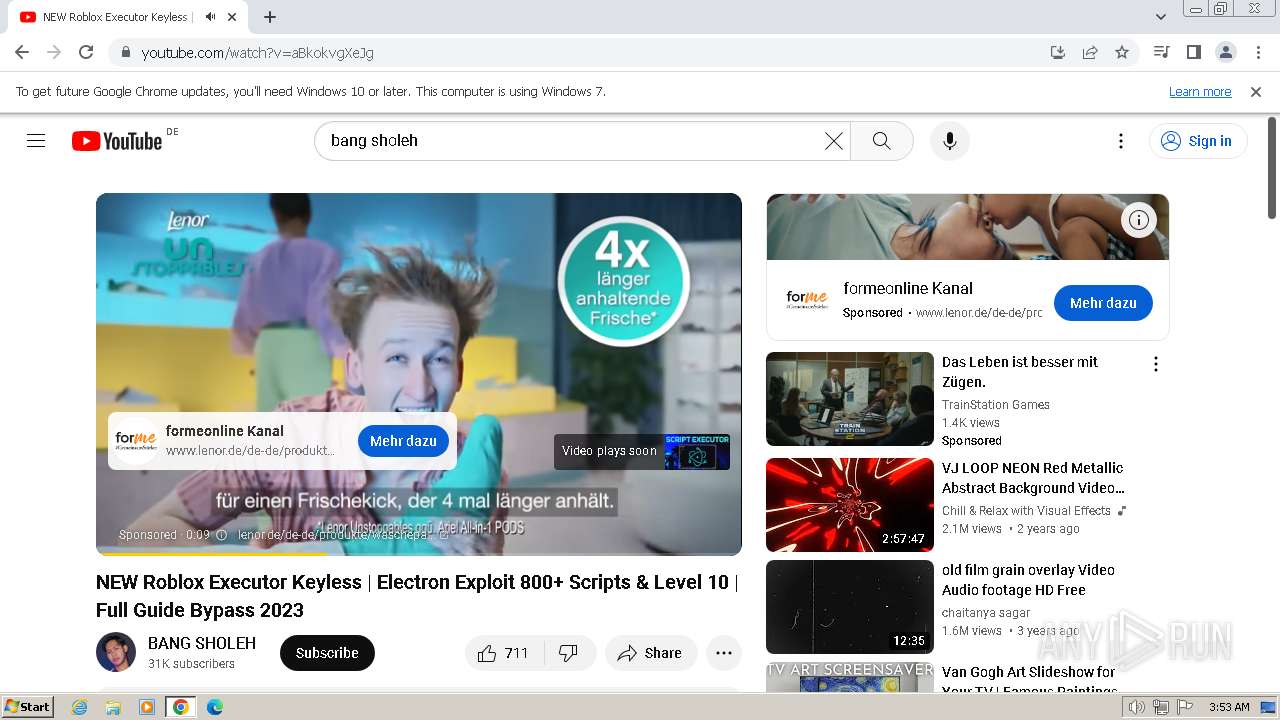
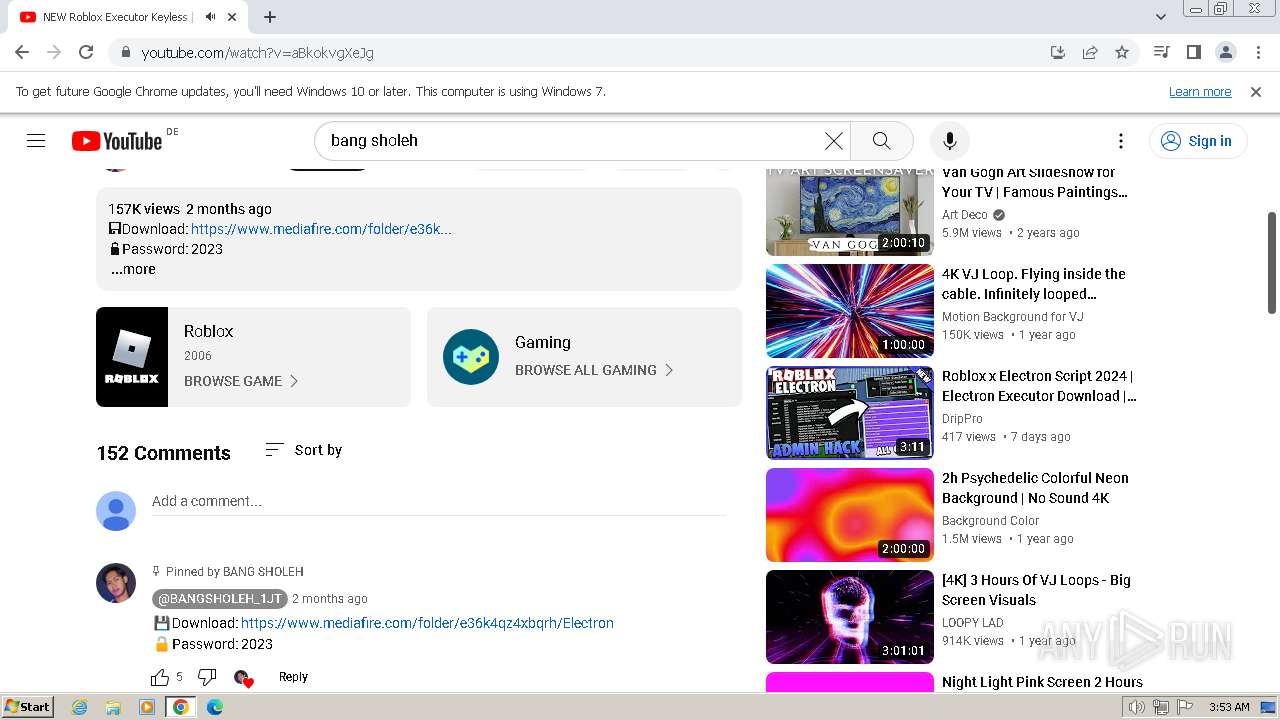
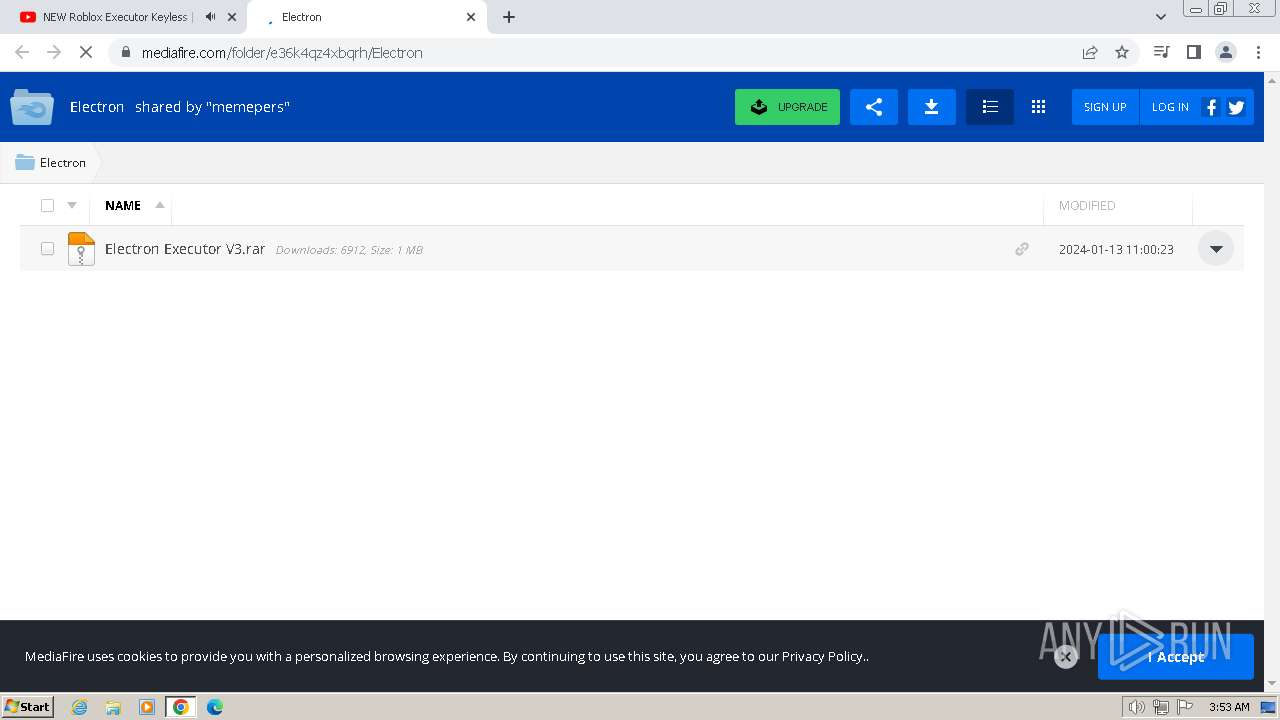
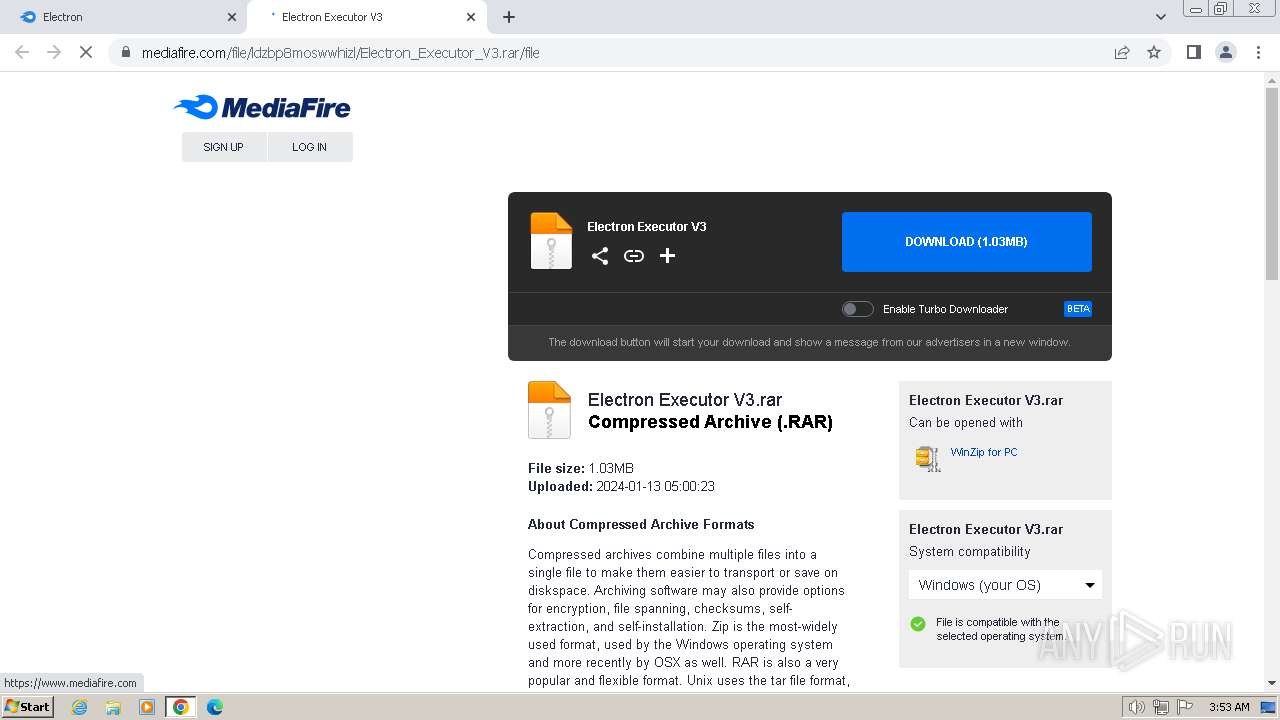
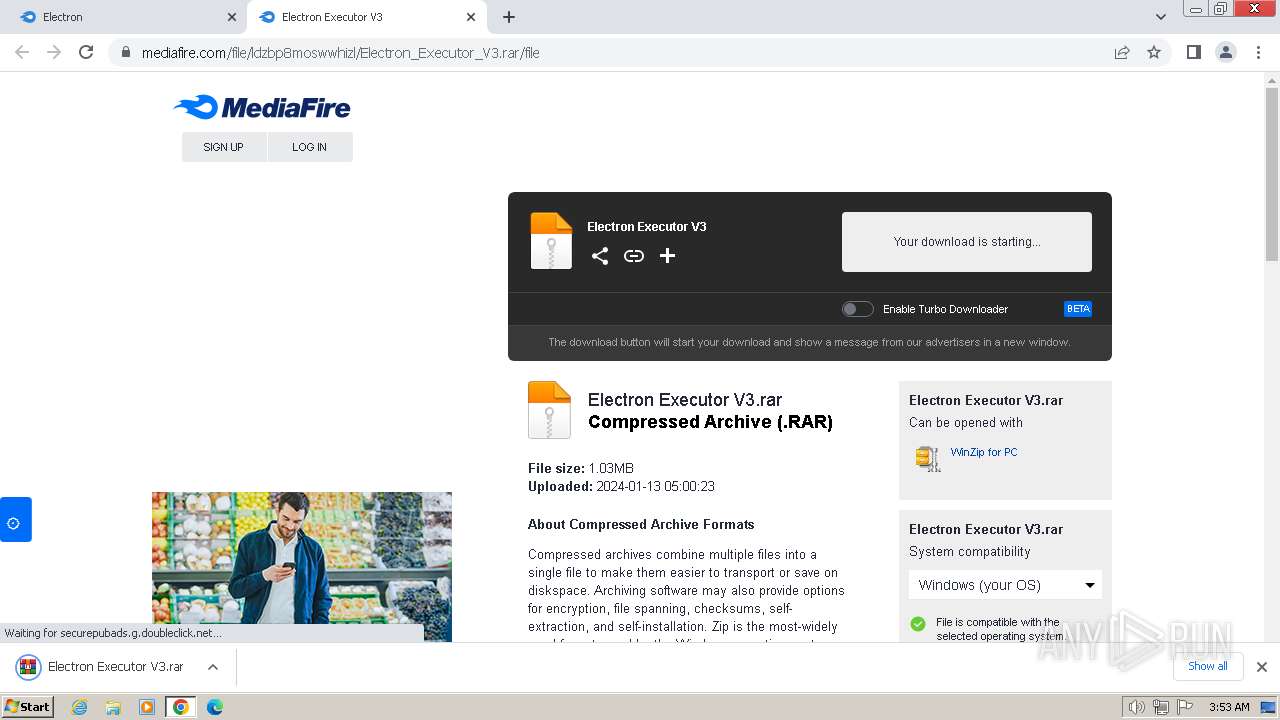
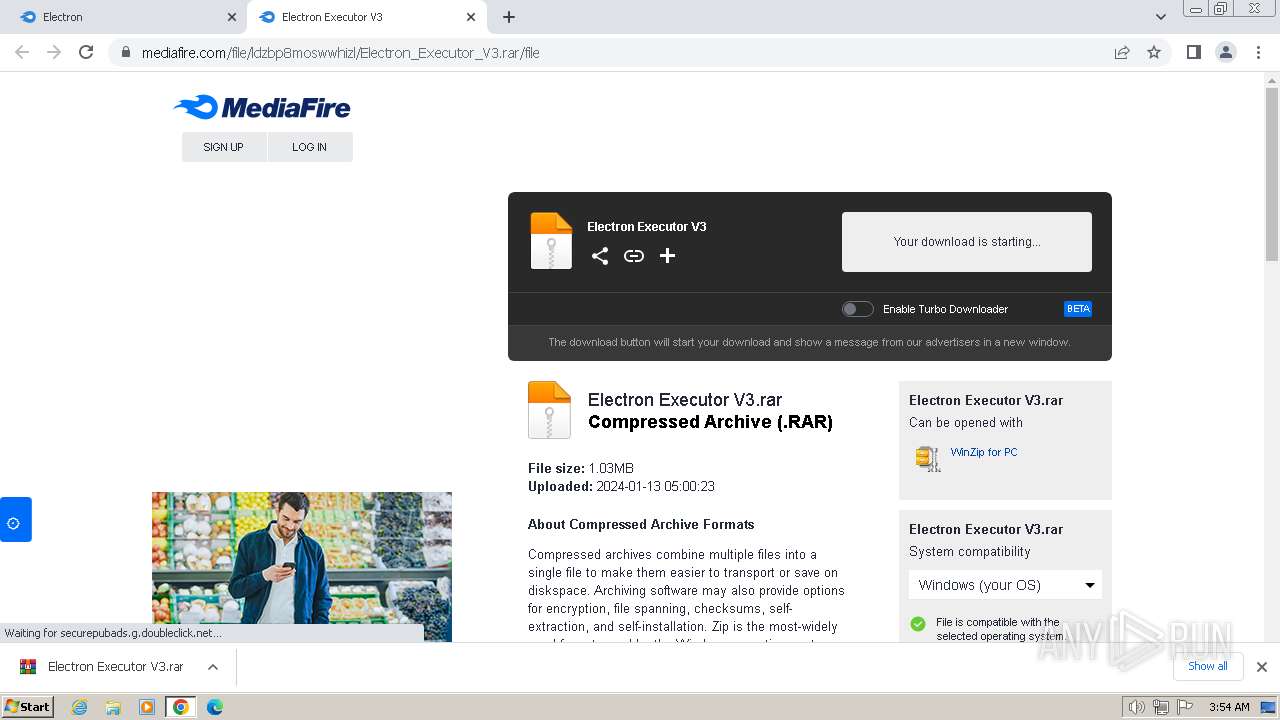
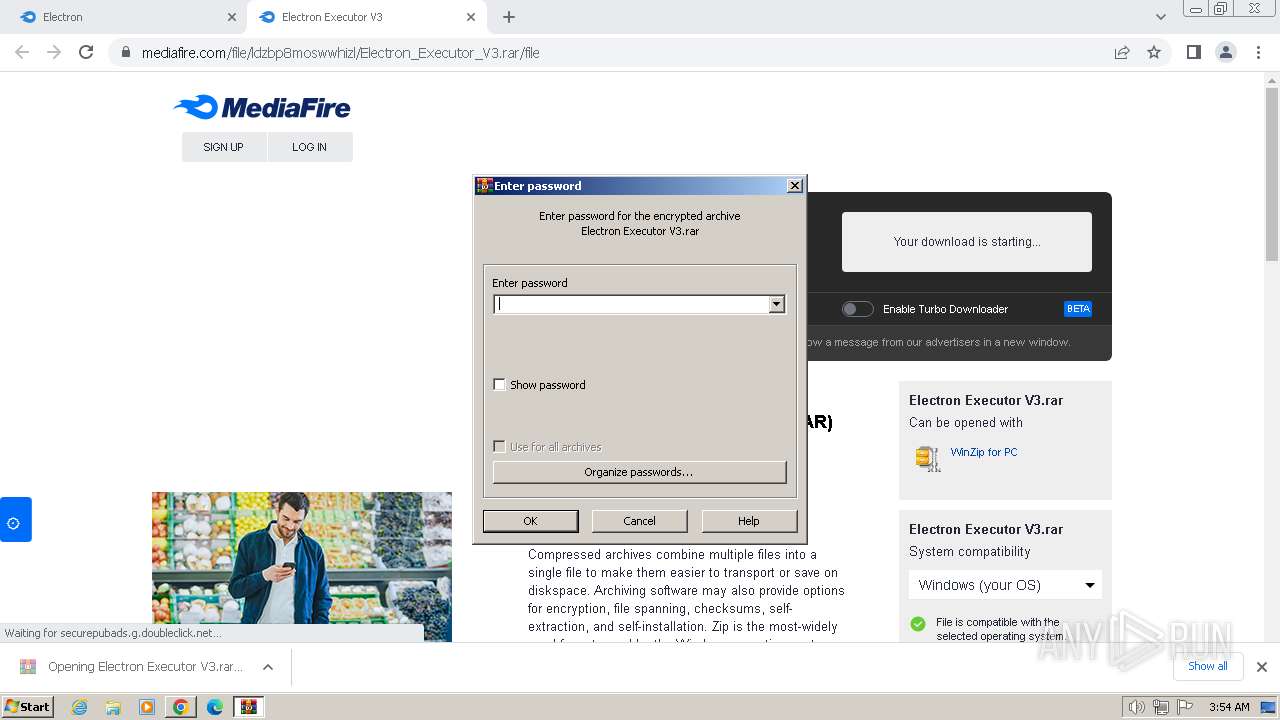
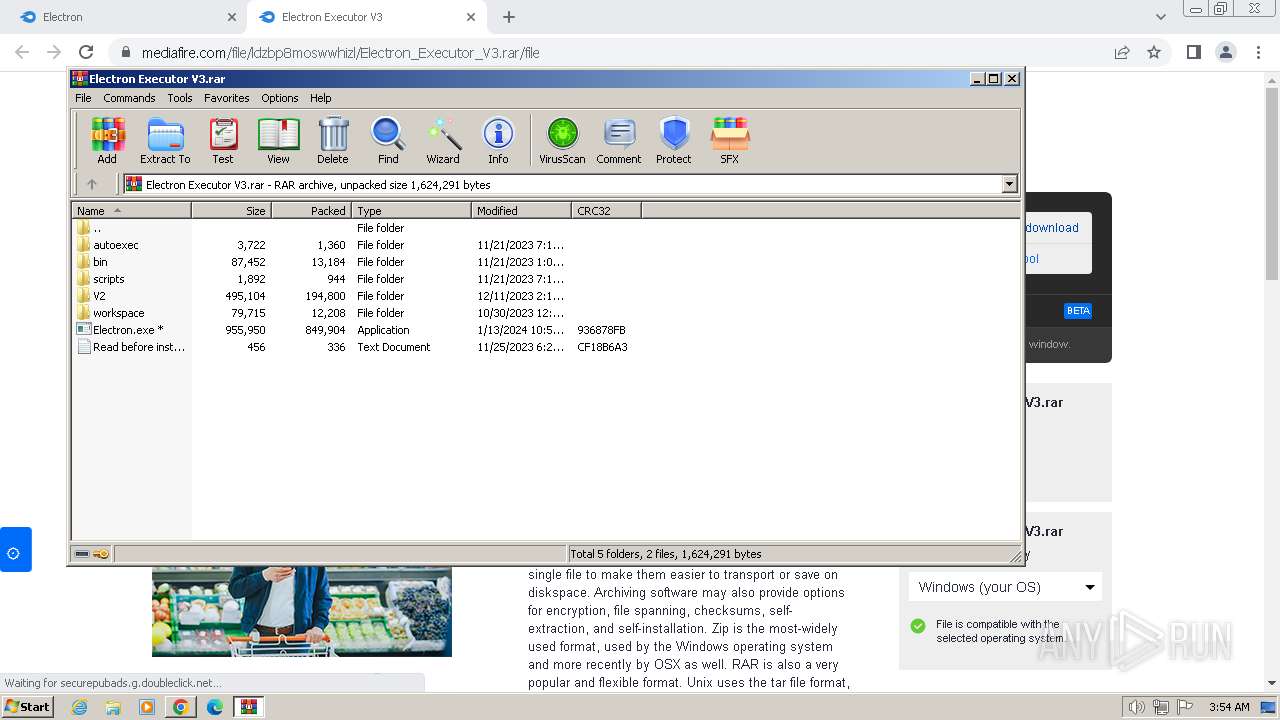
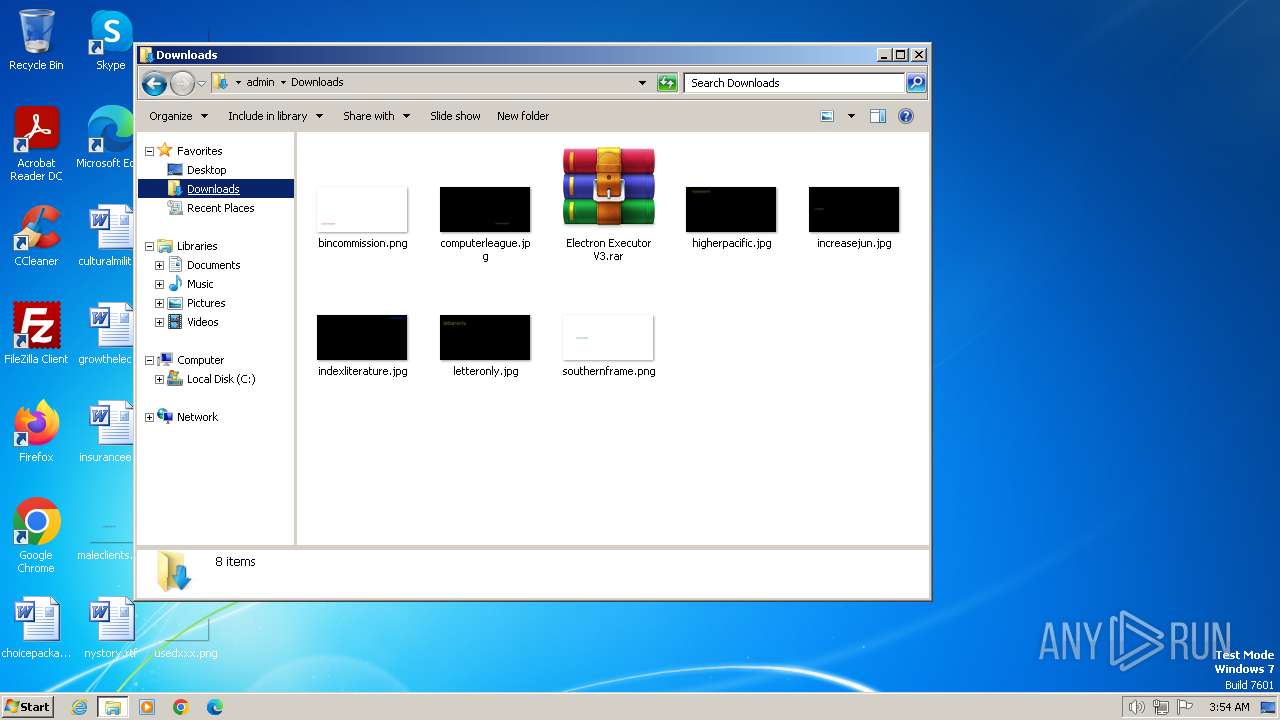
| download: | /folder/e36k4qz4xbqrh/Electron |
| Full analysis: | https://app.any.run/tasks/8e3f3150-f8b9-4171-a7ef-643c2da1b8e1 |
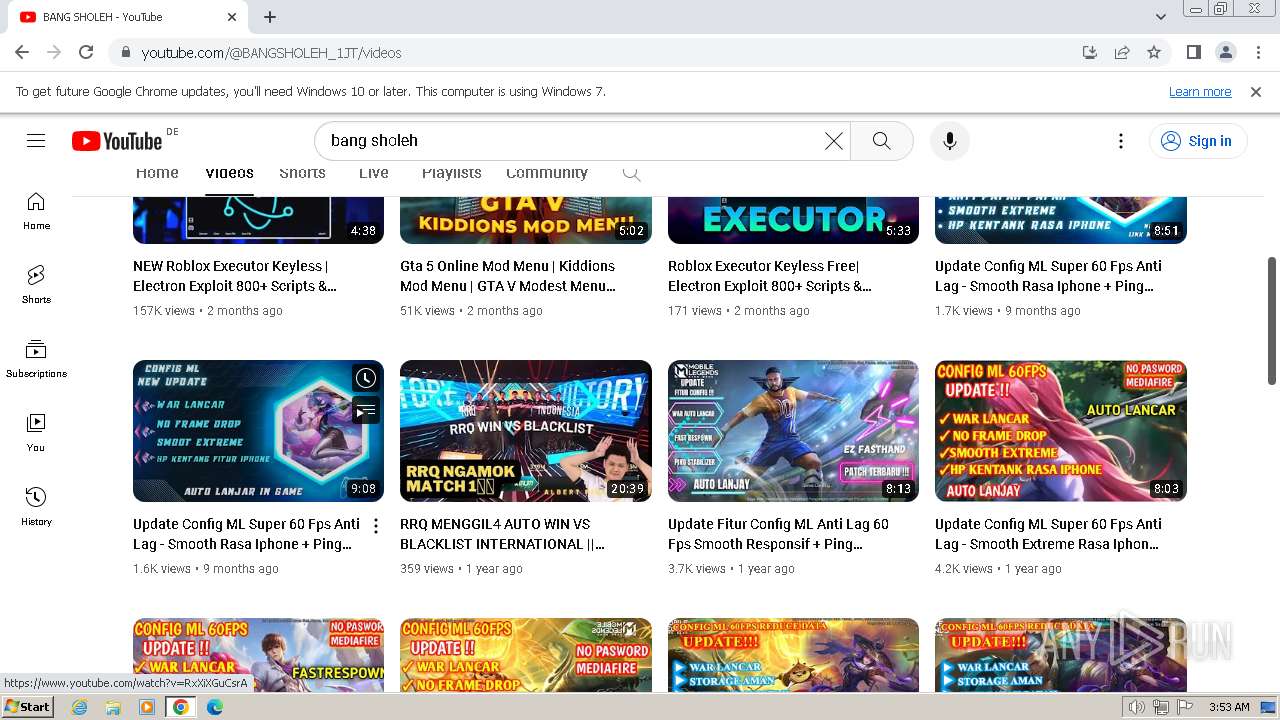
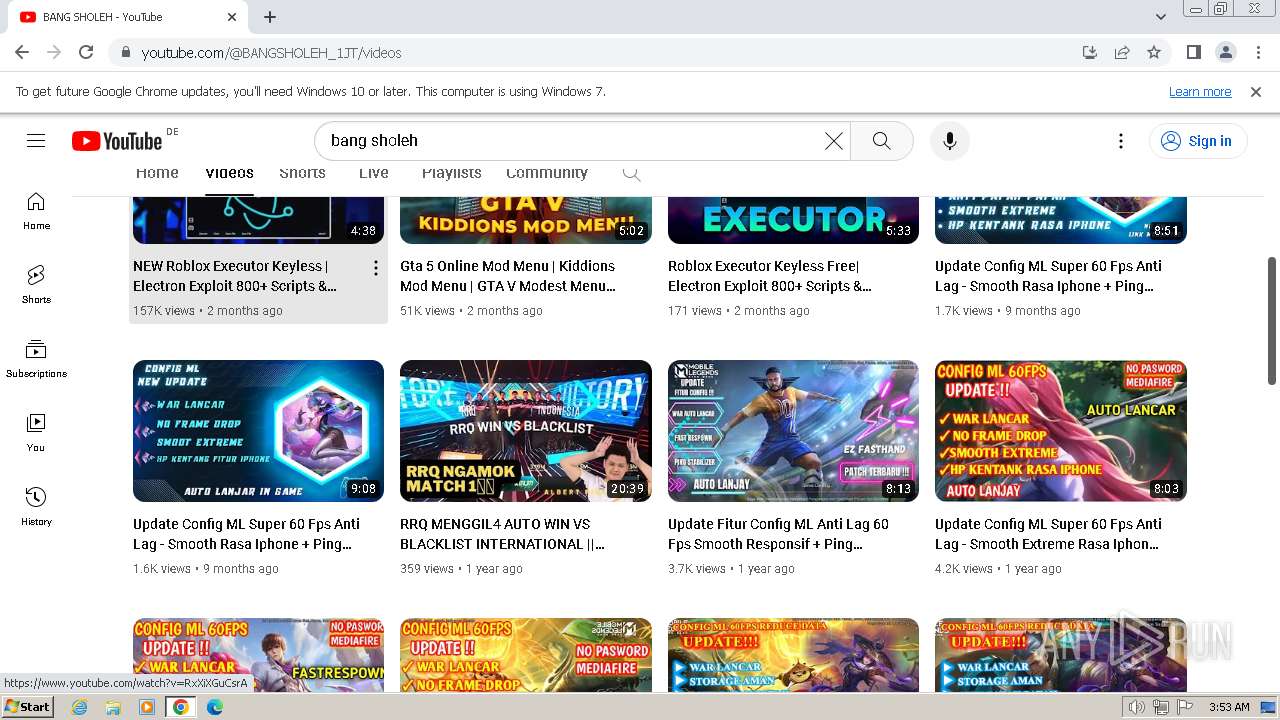
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
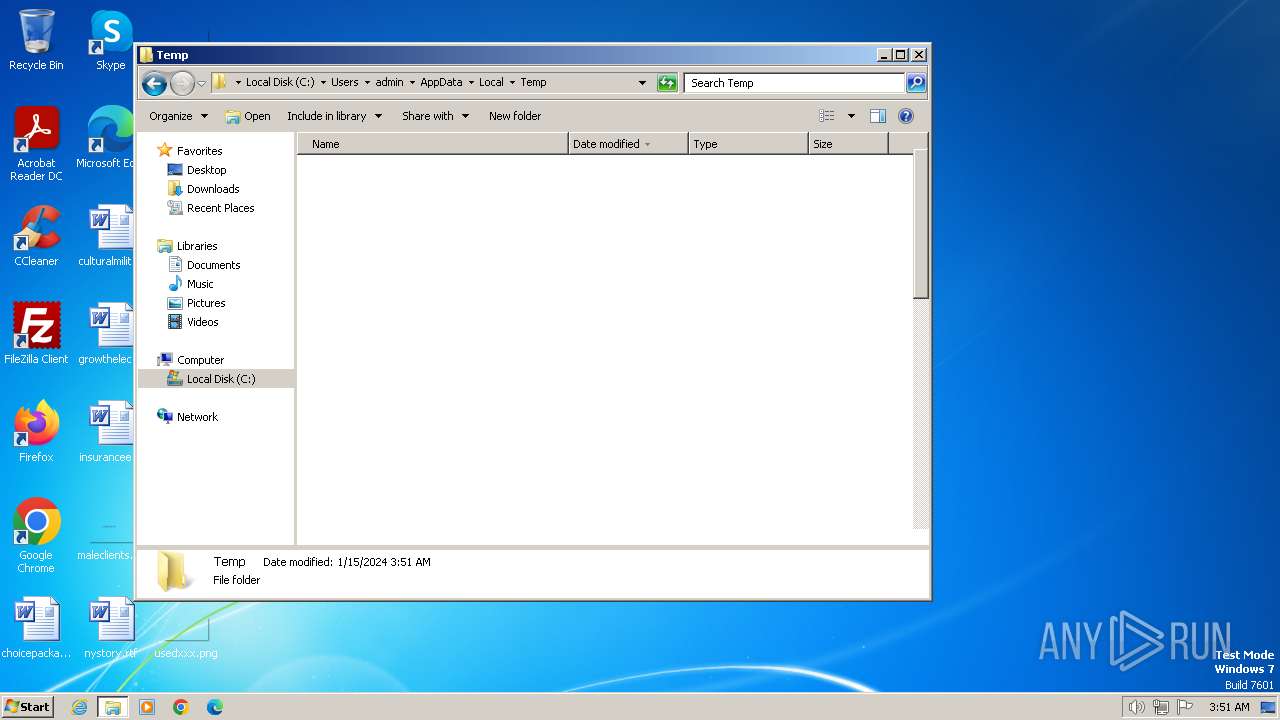
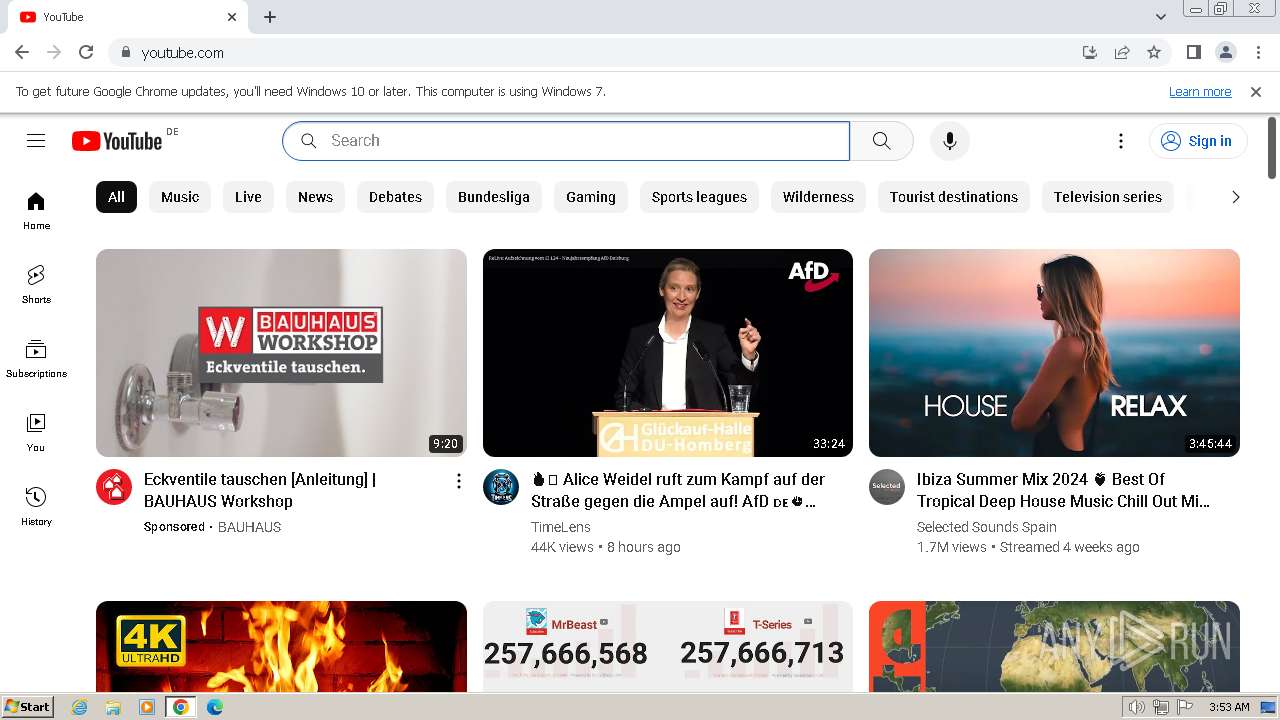
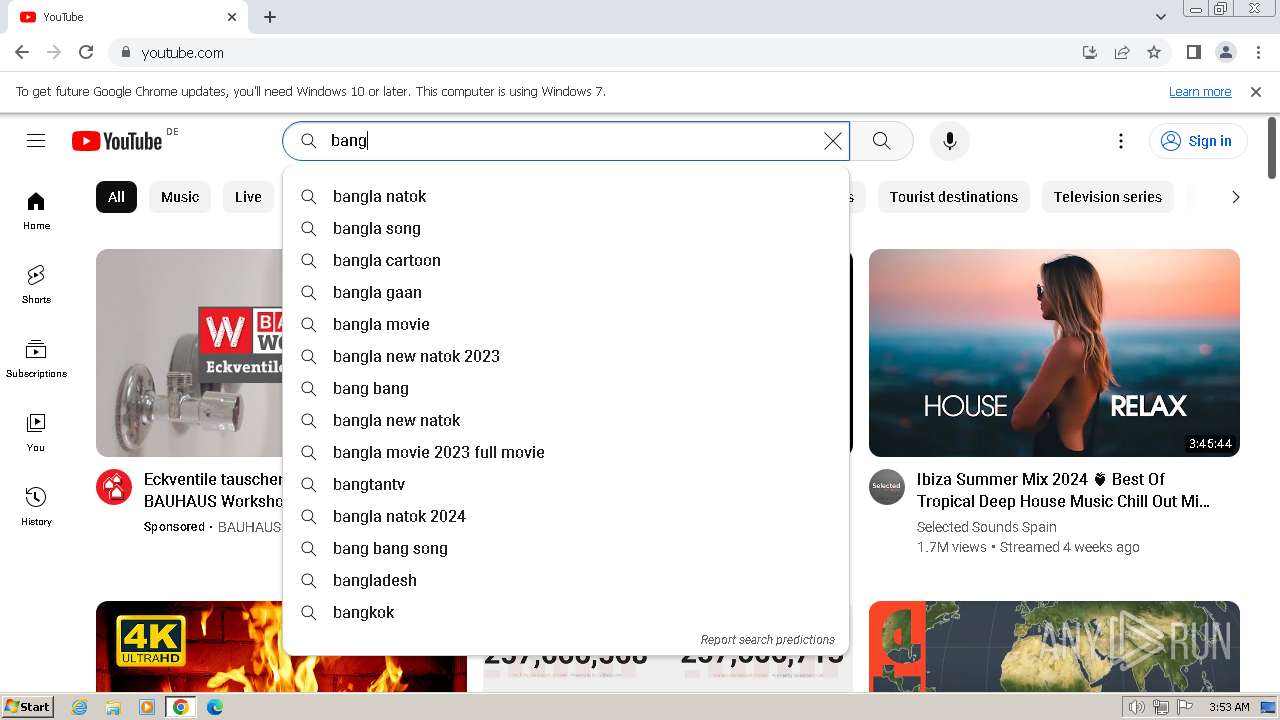
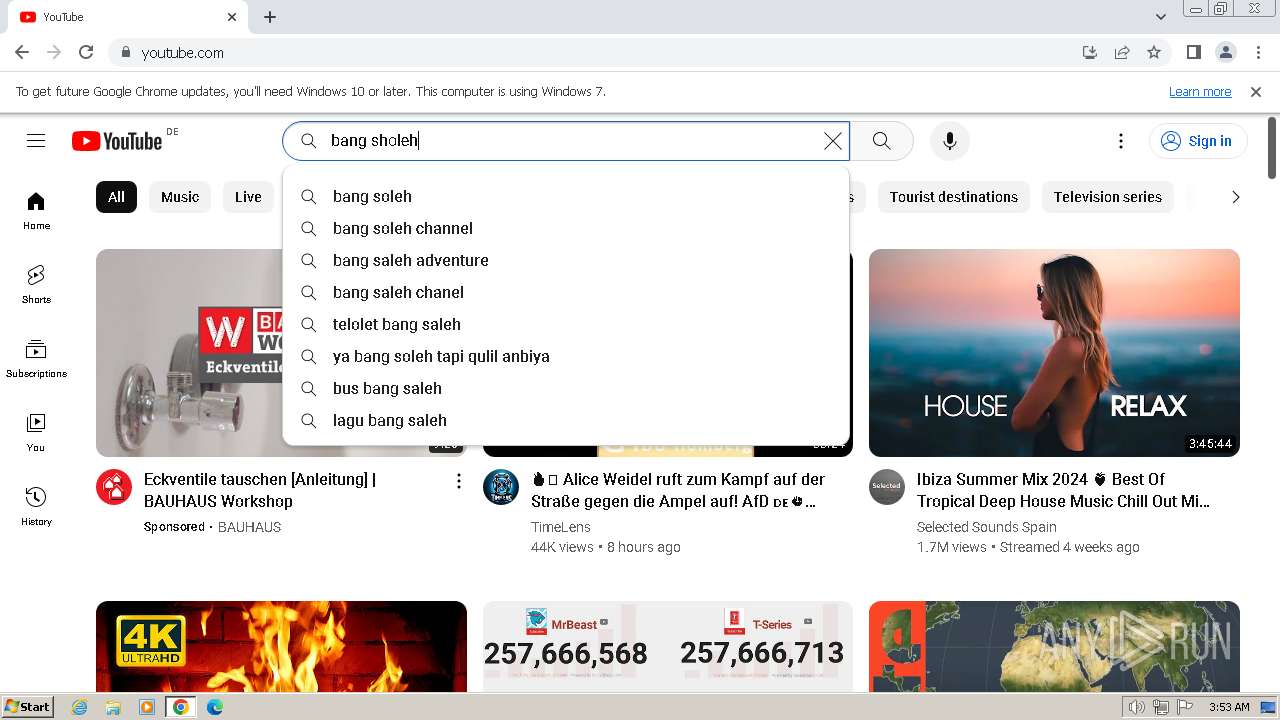
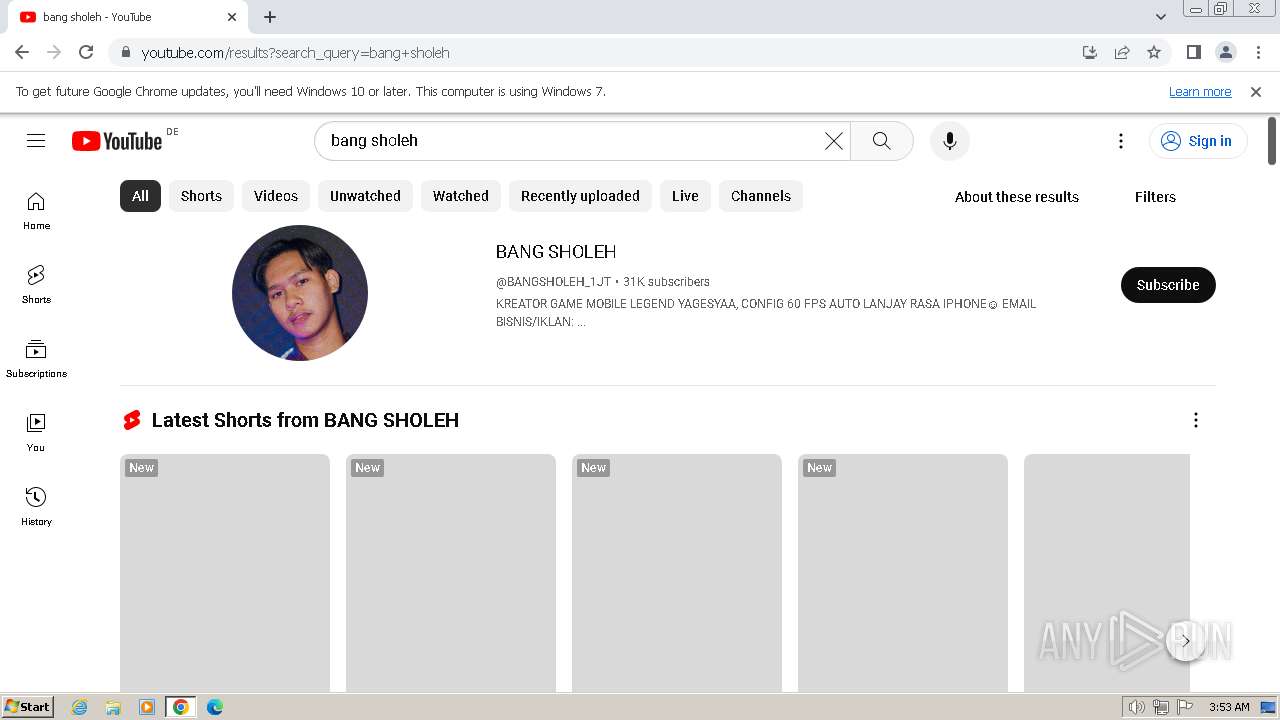
| Analysis date: | January 15, 2024, 03:50:42 |
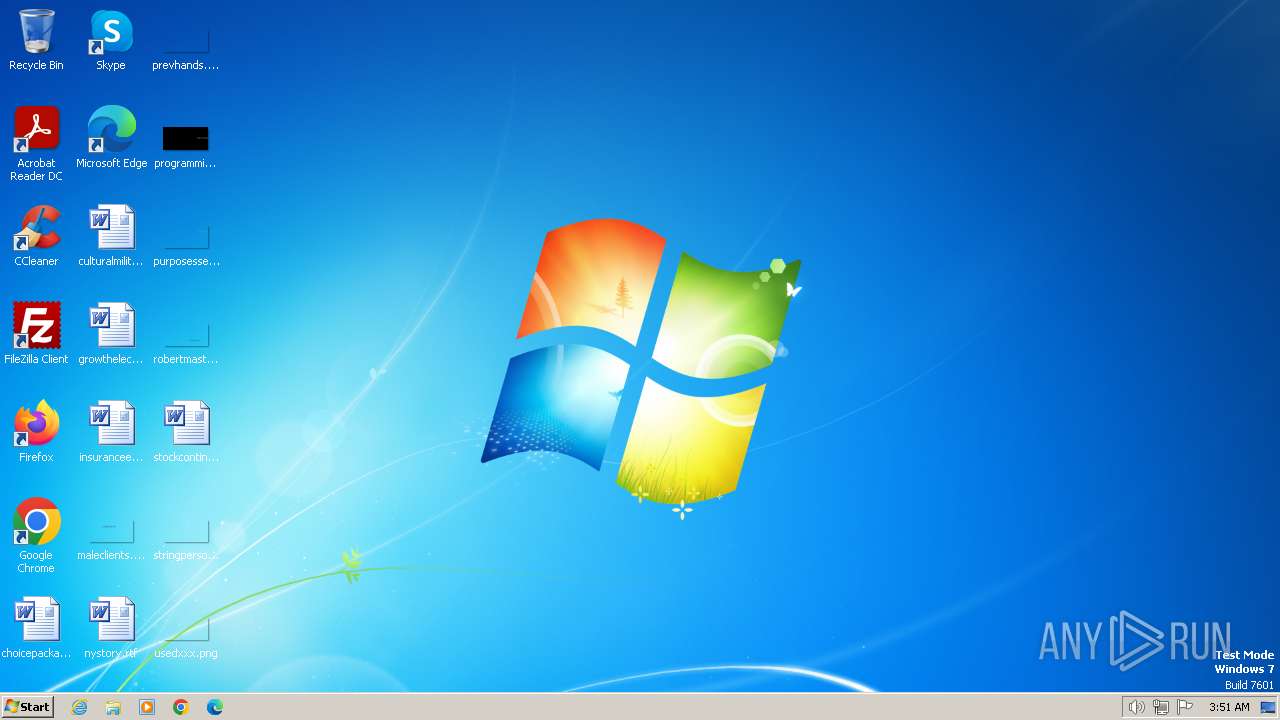
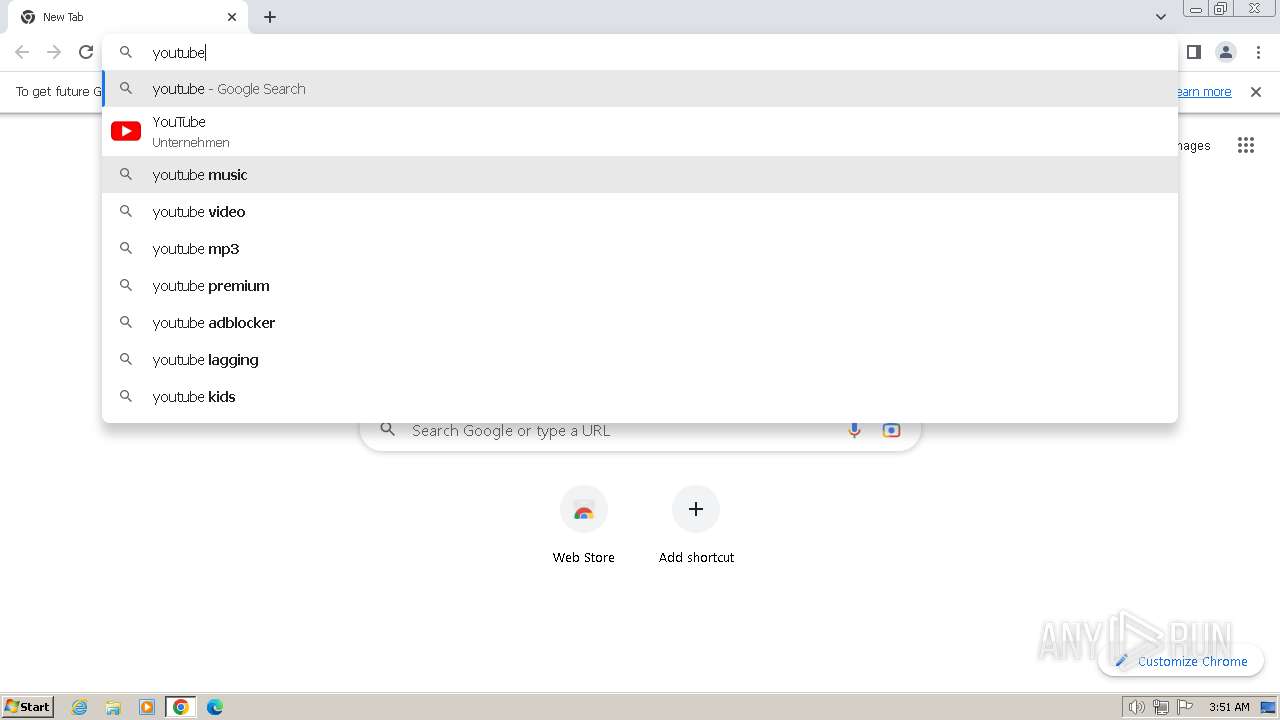
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines |
| MD5: | D91B02866E4EB4DECD179571F37F4B59 |
| SHA1: | 04532FA4E54EF78EA6676D51BE89A1FA466C8B71 |
| SHA256: | A75A129CB09DA3F10559C91D27C2CDED4F4B1C954B0DAAEA1A663627D9C82E08 |
| SSDEEP: | 3072:EIHm8HIrTBcKV7uzoR7qqHn0F5NRs3MXK6Pg3X1+gitcNnpk:oKcR0F5NRs8XK6Pg3X1+gitcNpk |
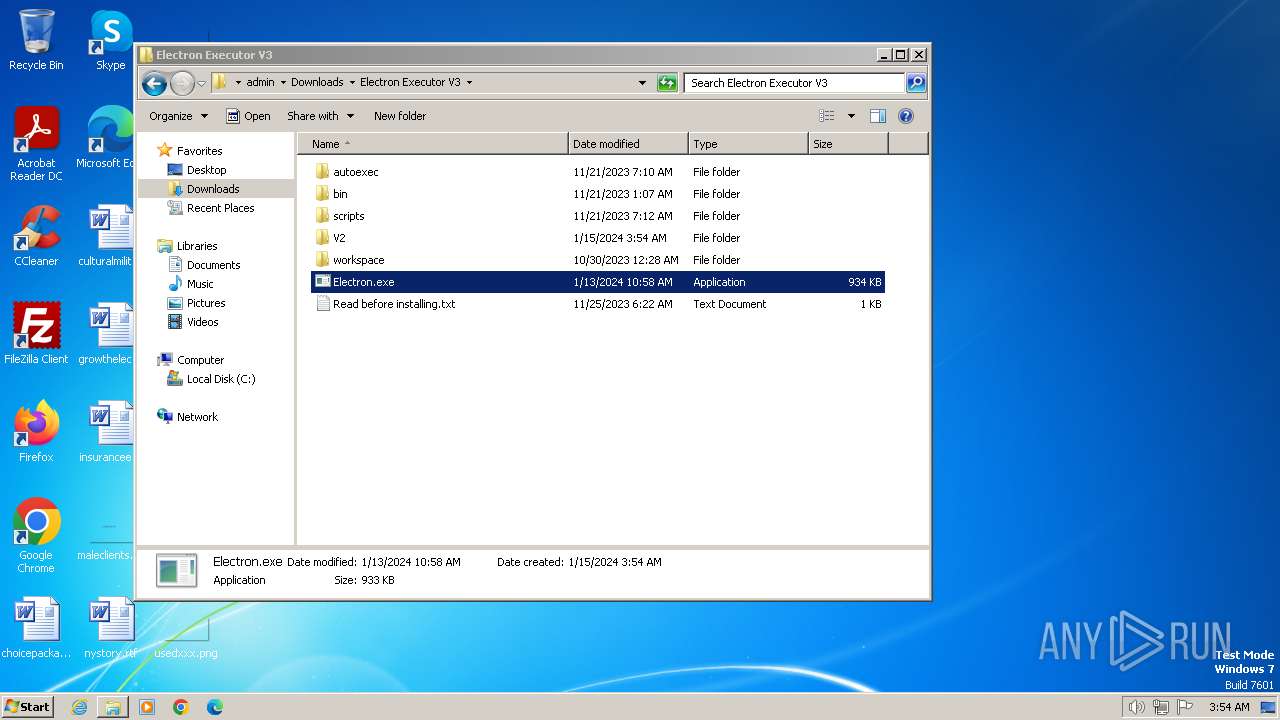
MALICIOUS
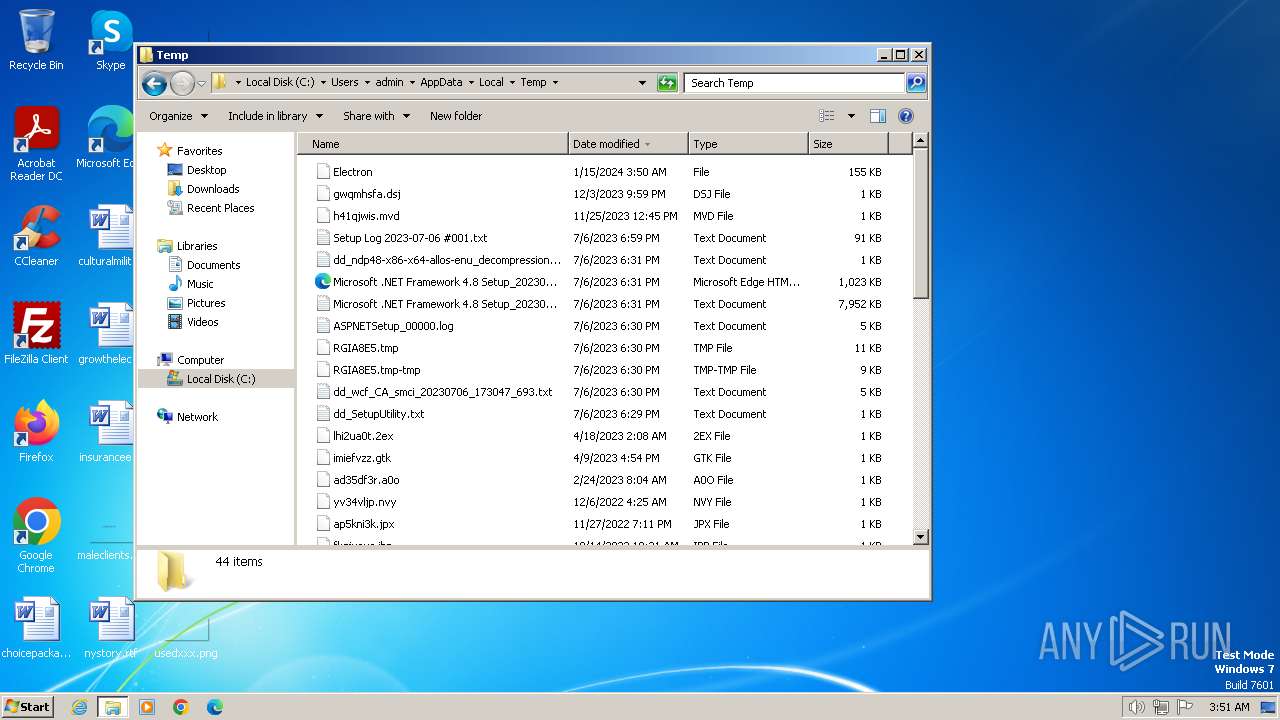
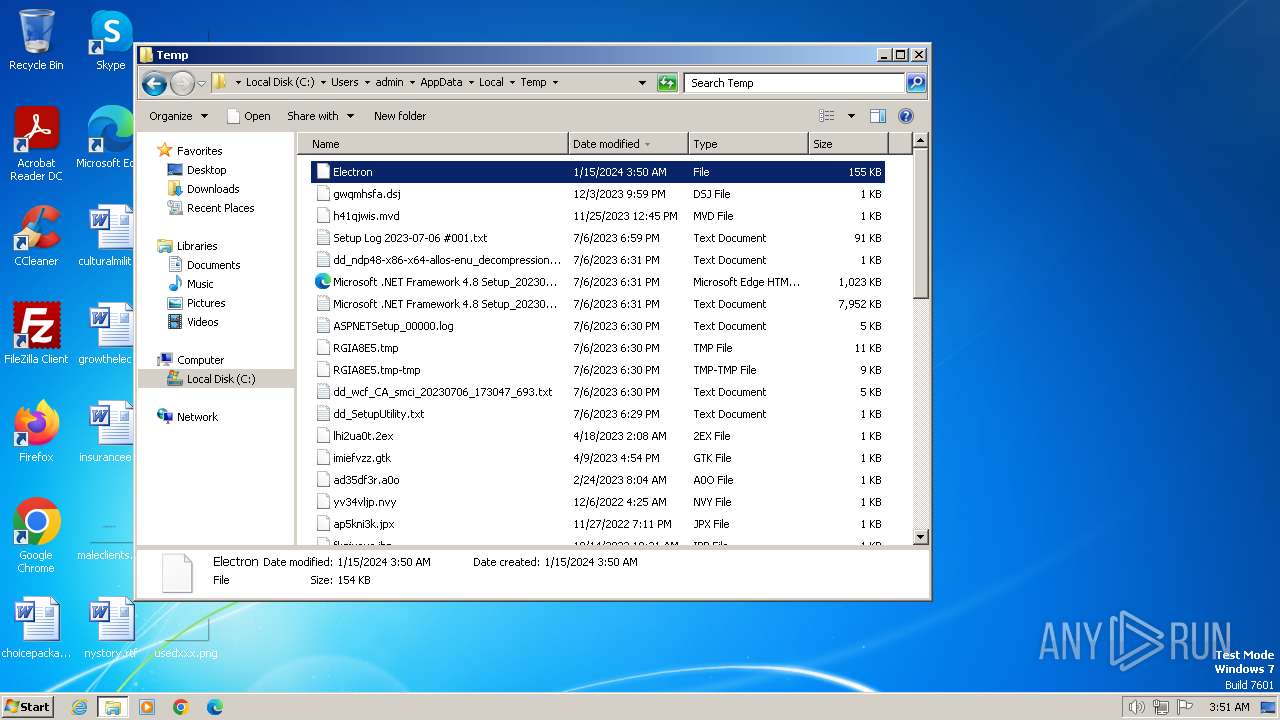
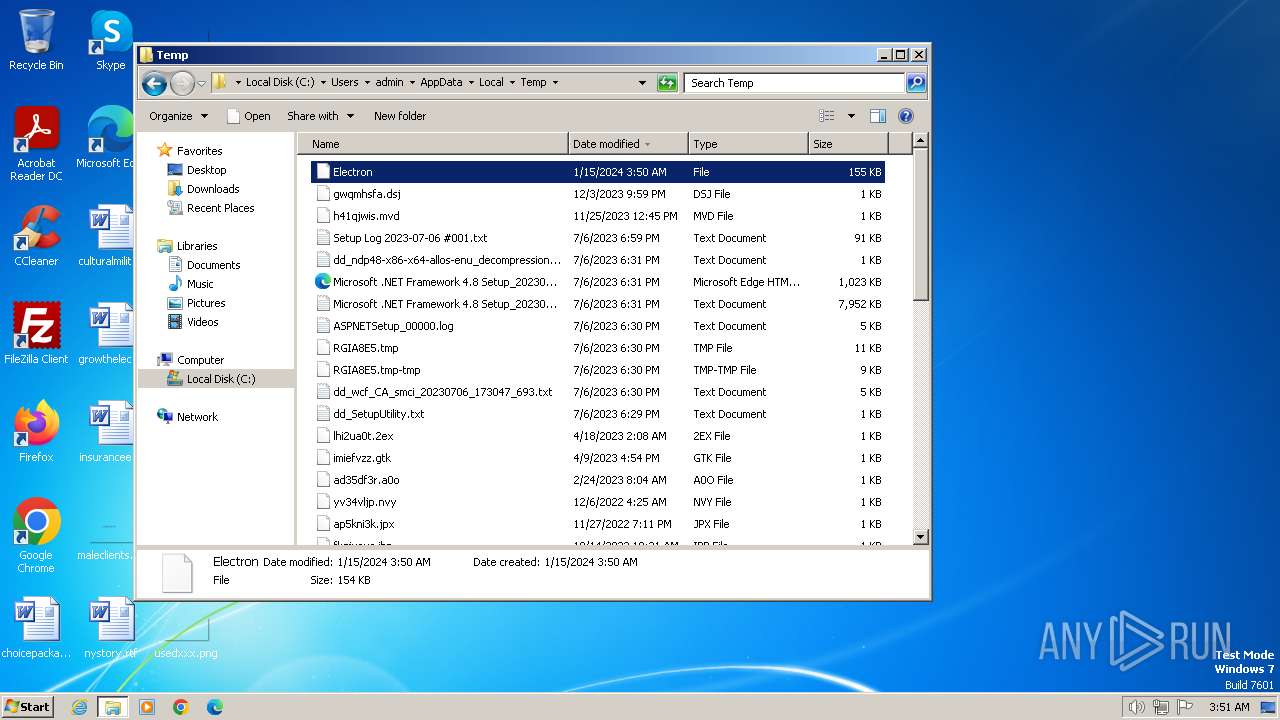
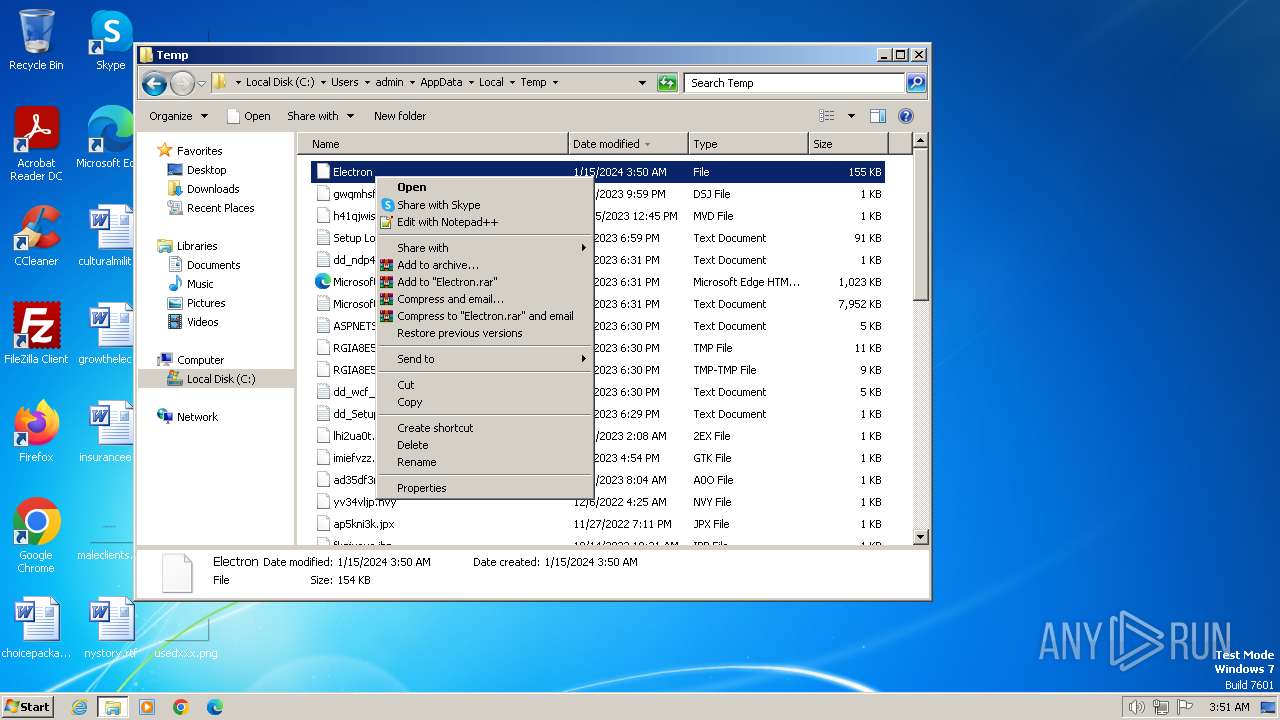
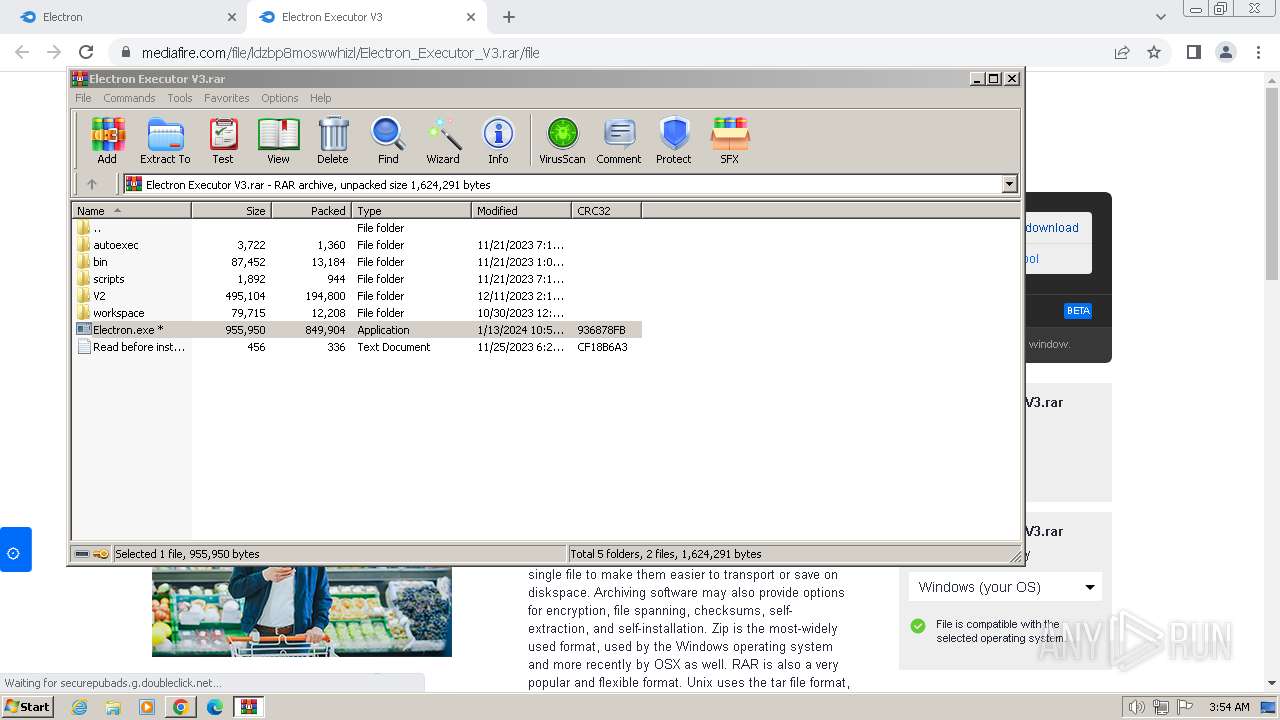
Drops the executable file immediately after the start
- Electron.exe (PID: 5408)
- cmd.exe (PID: 5640)
- Issn.pif (PID: 5664)
- jsc.exe (PID: 6140)
- Electron.exe (PID: 4128)
- Issn.pif (PID: 3048)
- cmd.exe (PID: 3524)
Steals credentials from Web Browsers
- jsc.exe (PID: 6140)
- jsc.exe (PID: 4680)
Actions looks like stealing of personal data
- jsc.exe (PID: 6140)
- jsc.exe (PID: 4680)
Create files in the Startup directory
- jsc.exe (PID: 6140)
REDLINE has been detected (SURICATA)
- jsc.exe (PID: 4680)
- jsc.exe (PID: 6140)
SUSPICIOUS
Reads the Internet Settings
- rundll32.exe (PID: 120)
- jsc.exe (PID: 6140)
- Electron.exe (PID: 4128)
- Electron.exe (PID: 5408)
Starts CMD.EXE for commands execution
- Electron.exe (PID: 5408)
- cmd.exe (PID: 5480)
- Electron.exe (PID: 4128)
- cmd.exe (PID: 4004)
- cmd.exe (PID: 3872)
- cmd.exe (PID: 5456)
Application launched itself
- cmd.exe (PID: 5456)
- cmd.exe (PID: 5480)
- cmd.exe (PID: 4004)
- cmd.exe (PID: 3872)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5480)
- cmd.exe (PID: 3872)
Starts application with an unusual extension
- cmd.exe (PID: 5480)
- cmd.exe (PID: 3872)
The executable file from the user directory is run by the CMD process
- Issn.pif (PID: 5664)
- Issn.pif (PID: 3048)
Executable content was dropped or overwritten
- cmd.exe (PID: 5640)
- Issn.pif (PID: 5664)
- jsc.exe (PID: 6140)
- Electron.exe (PID: 4128)
- cmd.exe (PID: 3524)
- Electron.exe (PID: 5408)
- Issn.pif (PID: 3048)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 5480)
- cmd.exe (PID: 3872)
Get information on the list of running processes
- cmd.exe (PID: 5480)
- cmd.exe (PID: 3872)
Process drops legitimate windows executable
- Issn.pif (PID: 5664)
- Issn.pif (PID: 3048)
Connects to unusual port
- jsc.exe (PID: 6140)
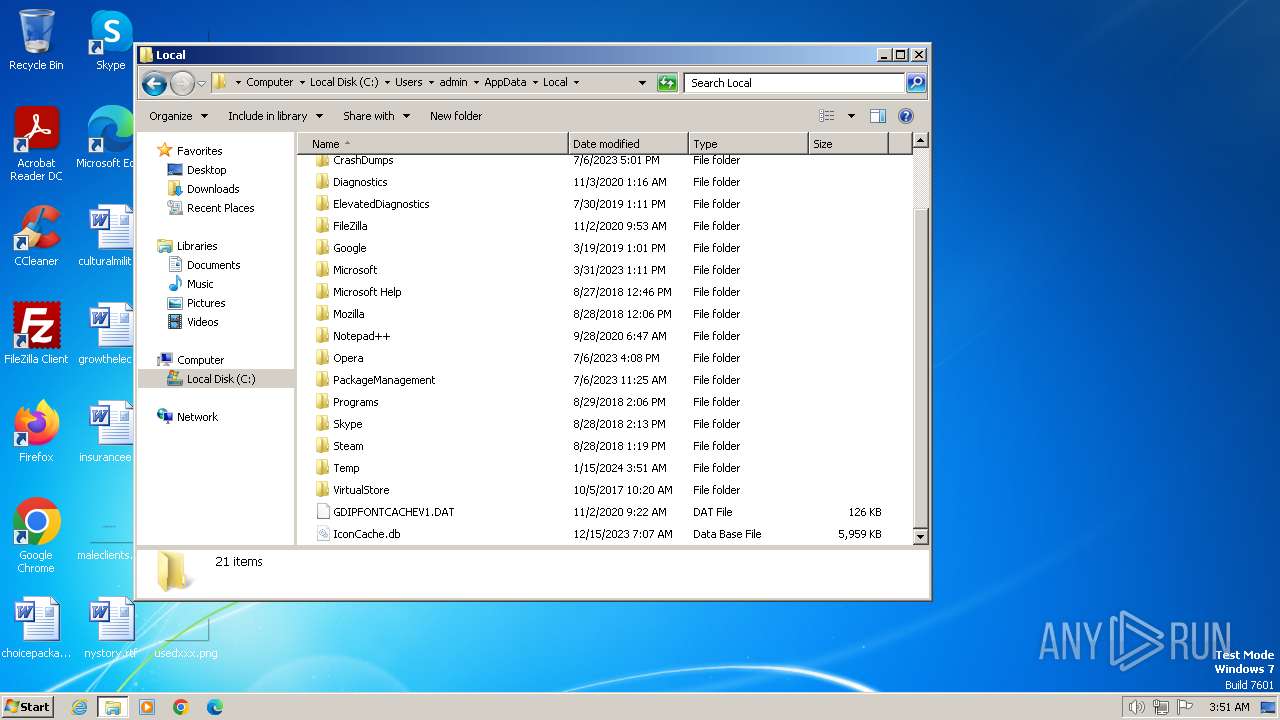
Reads browser cookies
- jsc.exe (PID: 6140)
- jsc.exe (PID: 4680)
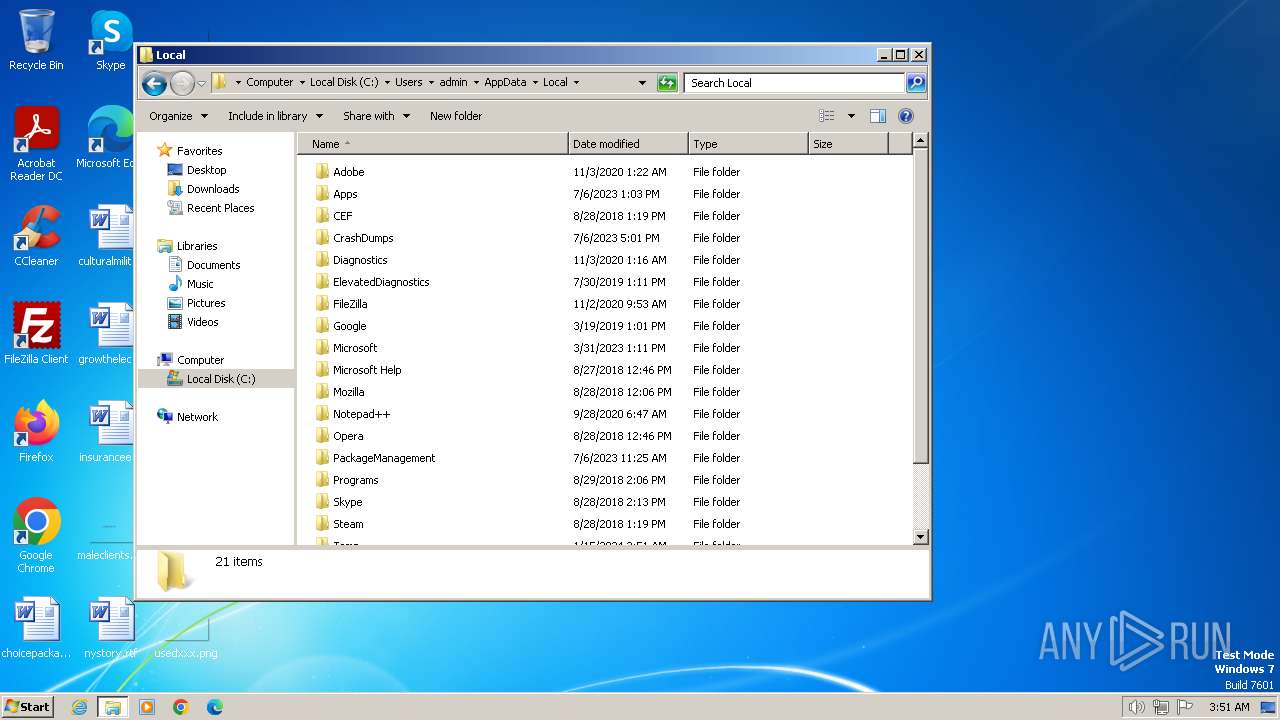
Searches for installed software
- jsc.exe (PID: 6140)
- jsc.exe (PID: 4680)
INFO
Application launched itself
- firefox.exe (PID: 2036)
- firefox.exe (PID: 1404)
- chrome.exe (PID: 1776)
Reads the computer name
- Electron.exe (PID: 5408)
- Issn.pif (PID: 5664)
- qemu-ga.exe (PID: 4248)
- Electron.exe (PID: 4128)
- Issn.pif (PID: 3048)
- jsc.exe (PID: 4680)
- jsc.exe (PID: 6140)
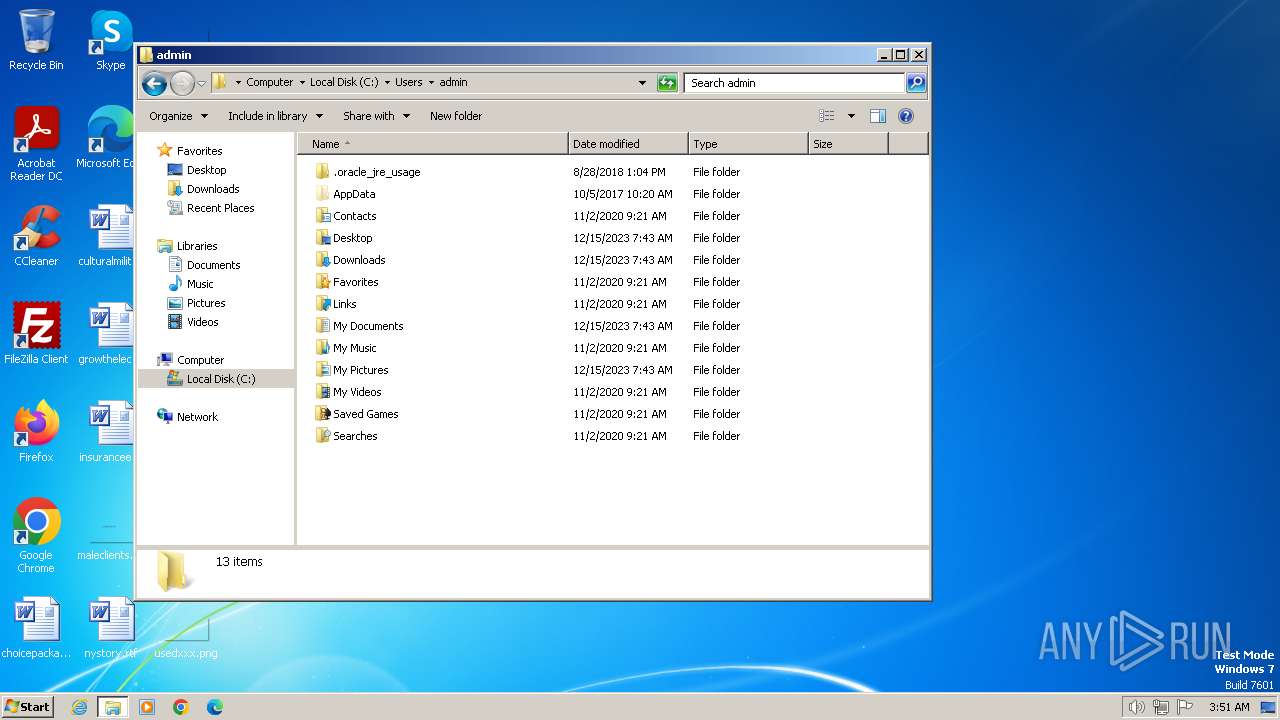
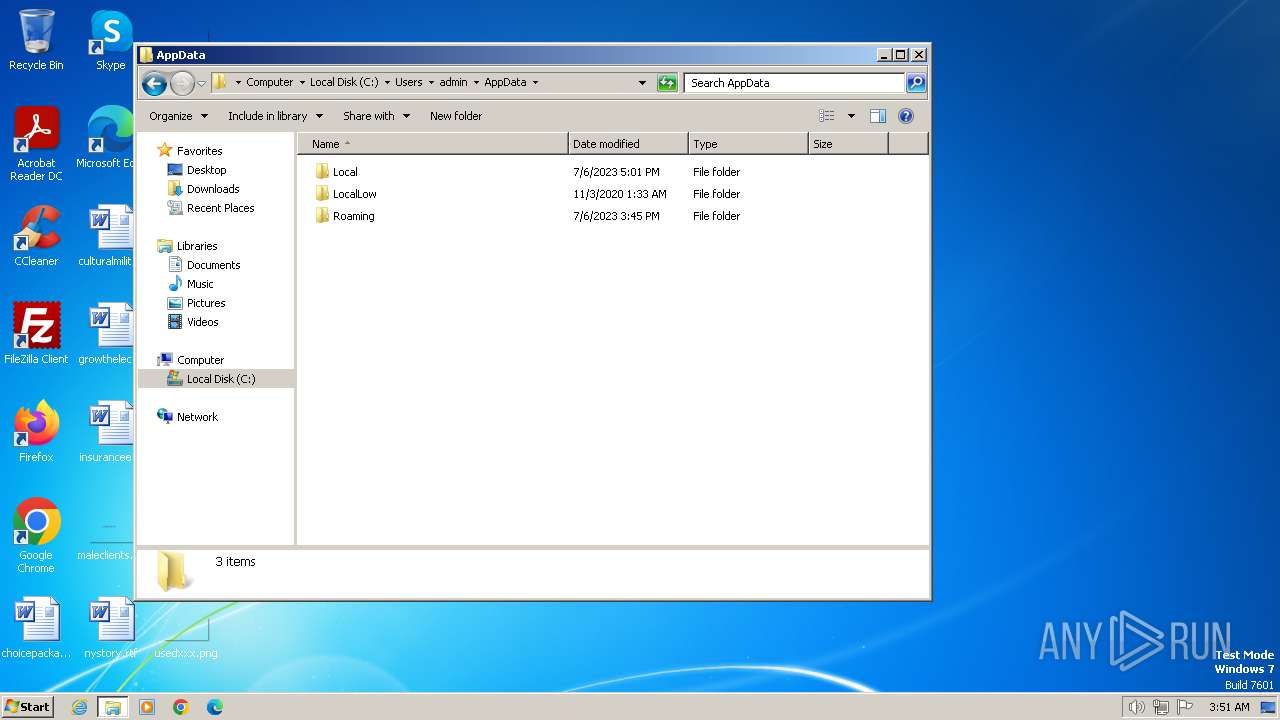
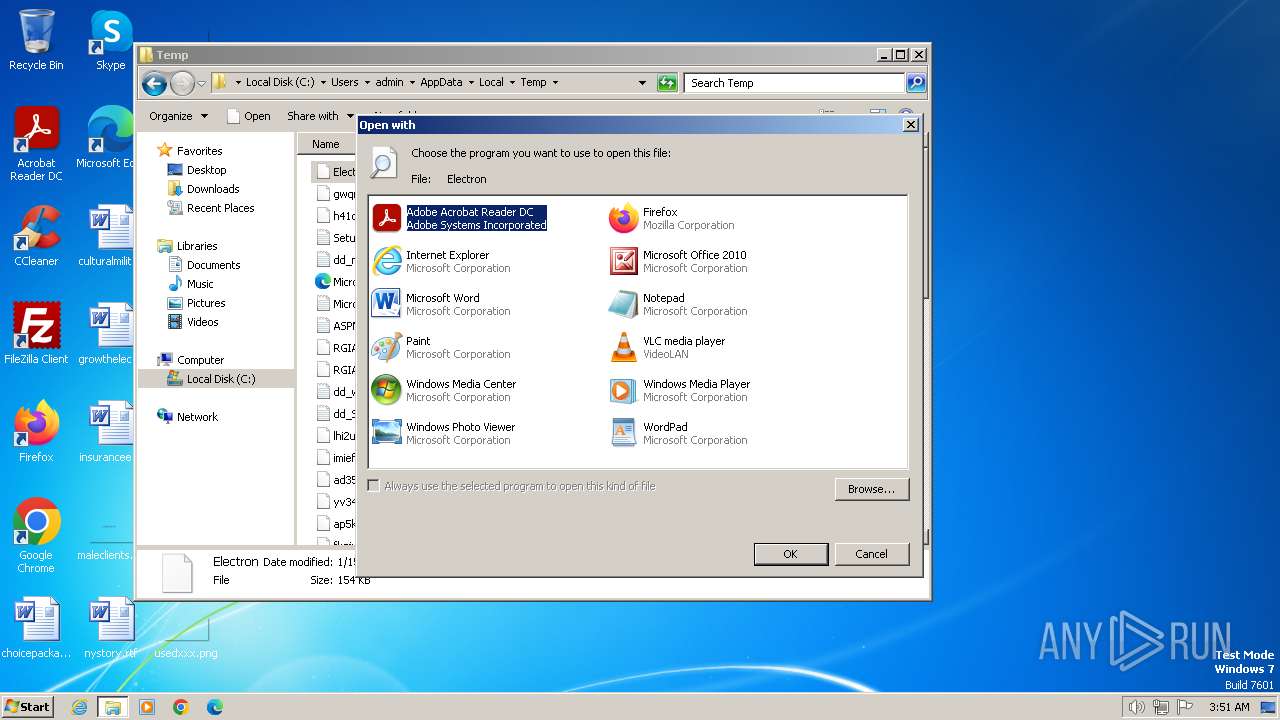
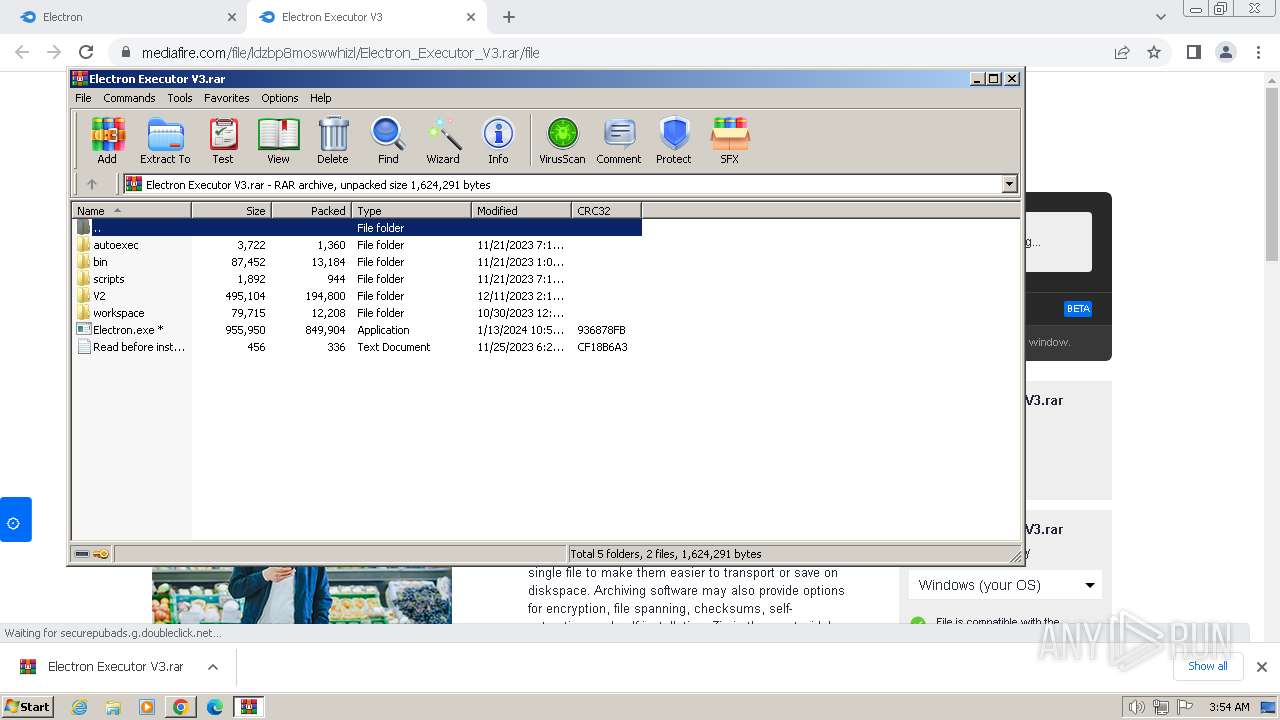
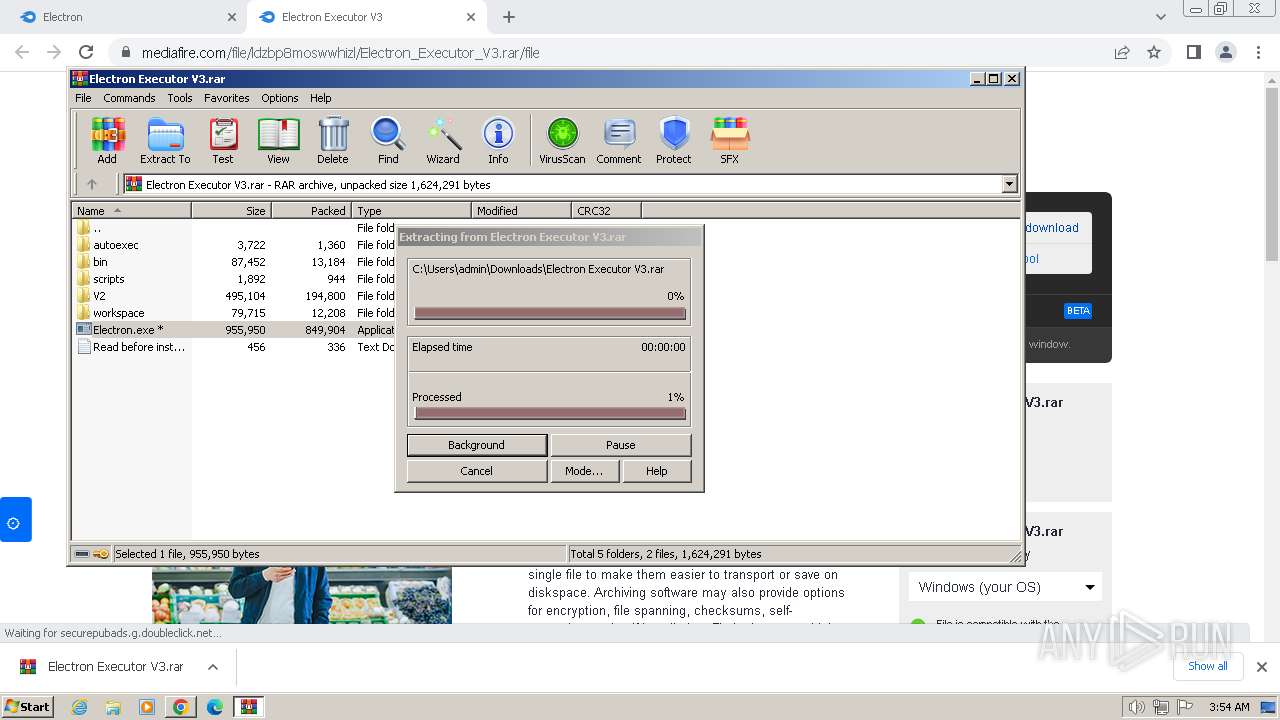
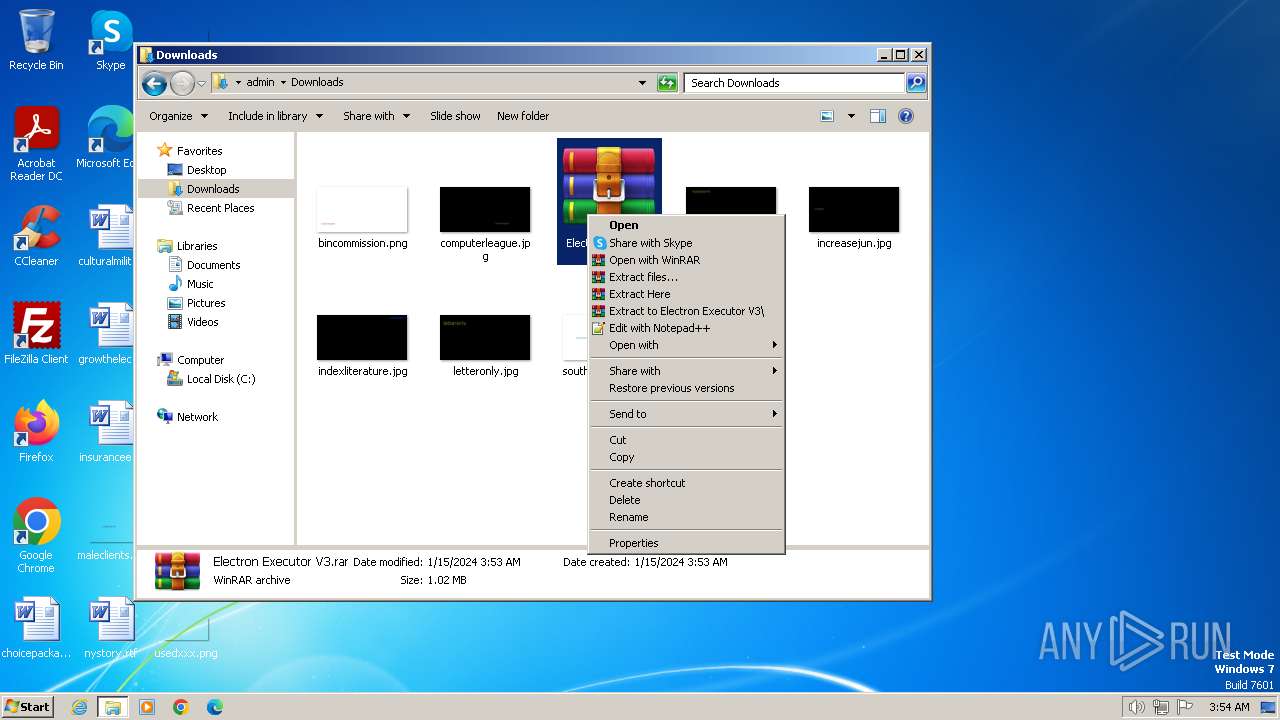
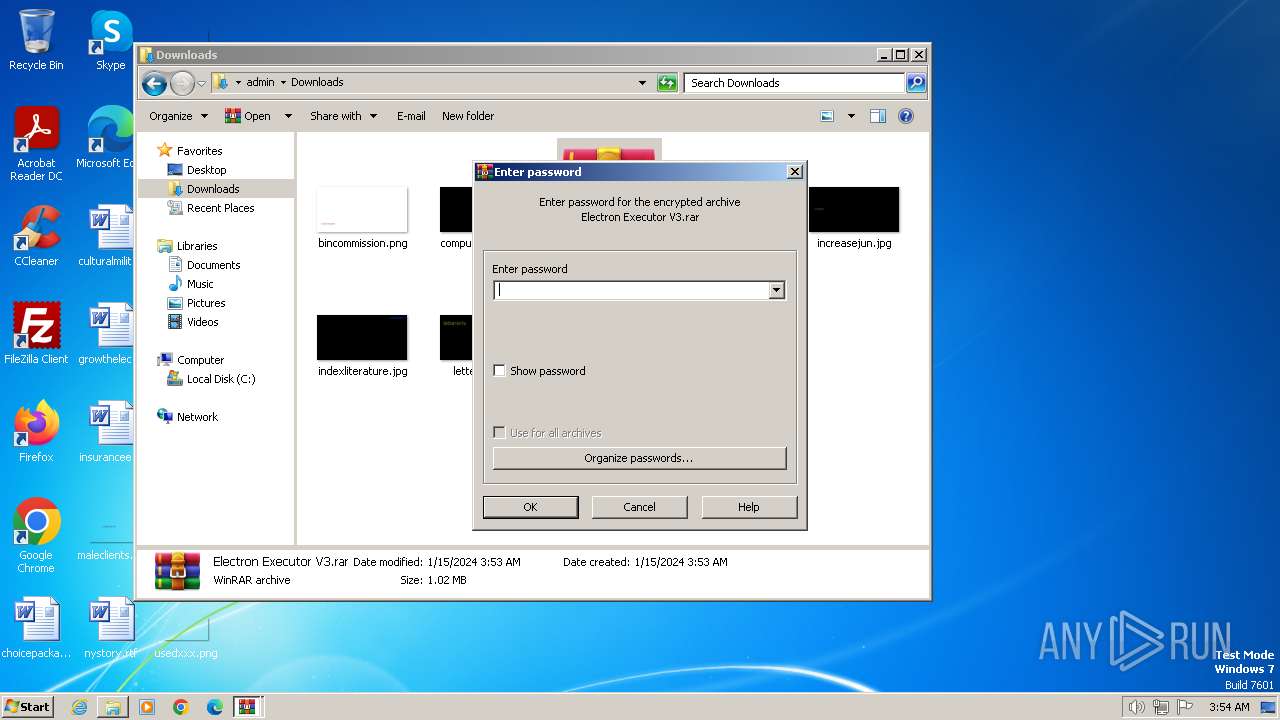
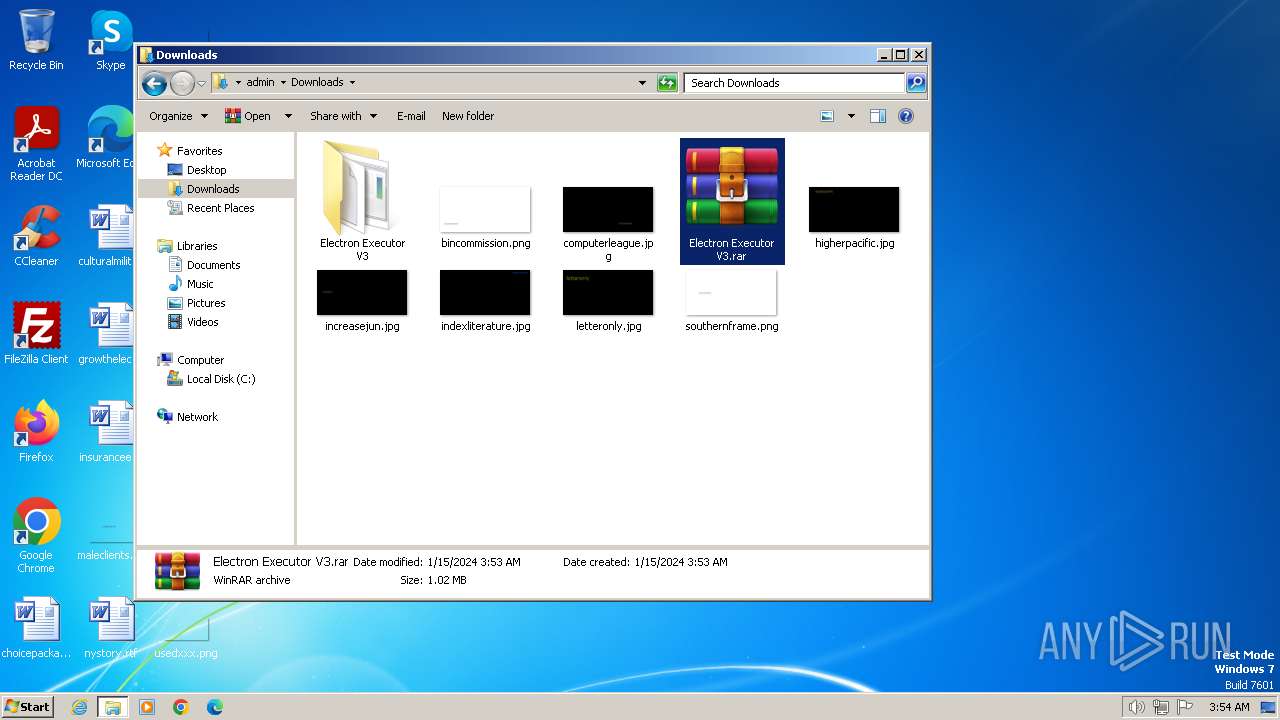
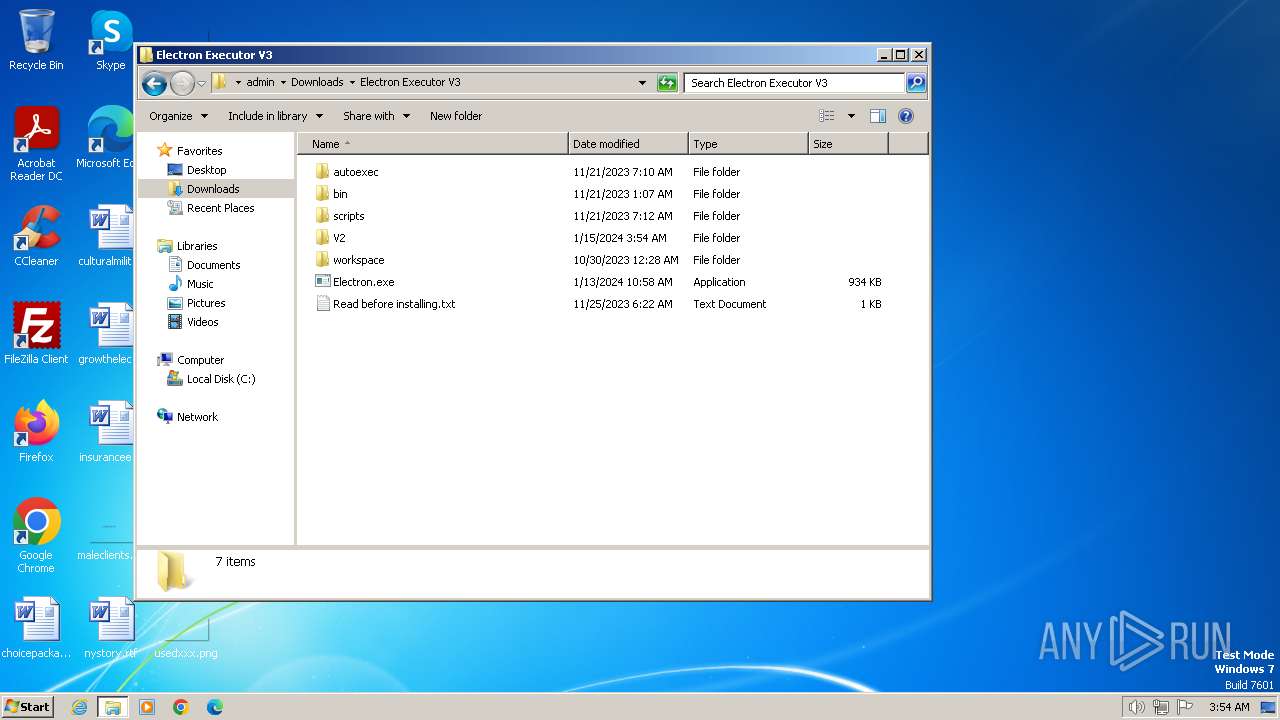
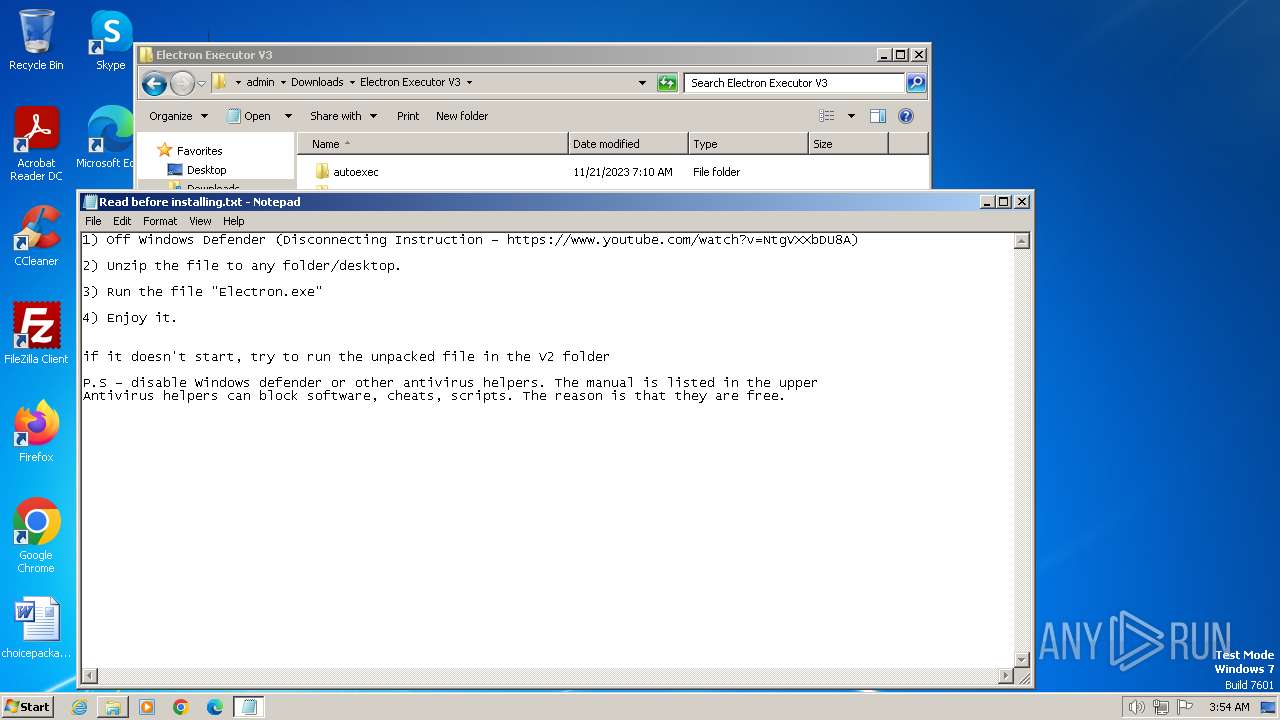
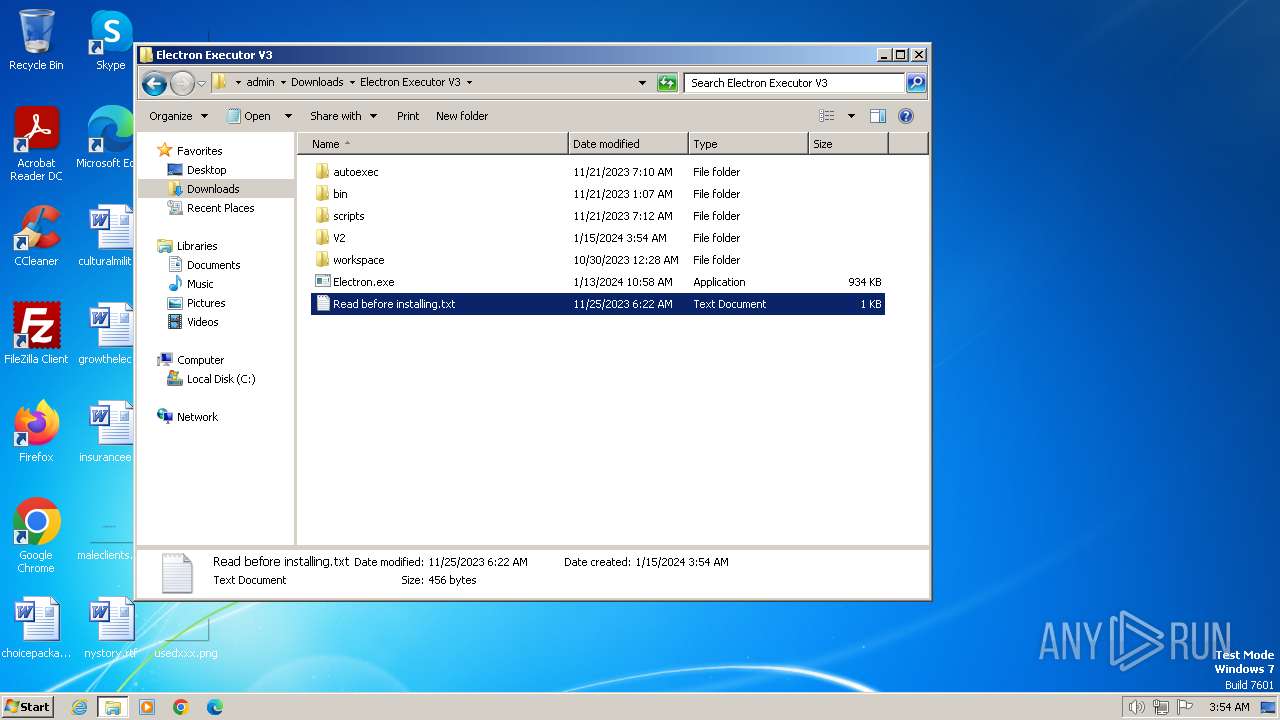
Manual execution by a user
- chrome.exe (PID: 1776)
- rundll32.exe (PID: 2124)
- explorer.exe (PID: 2868)
- jsc.exe (PID: 6140)
- explorer.exe (PID: 5928)
- WinRAR.exe (PID: 6120)
- notepad.exe (PID: 4572)
- Electron.exe (PID: 4128)
- jsc.exe (PID: 4680)
Drops the executable file immediately after the start
- chrome.exe (PID: 1776)
- WinRAR.exe (PID: 6120)
- WinRAR.exe (PID: 5264)
The process uses the downloaded file
- chrome.exe (PID: 2096)
- WinRAR.exe (PID: 5264)
- WinRAR.exe (PID: 6120)
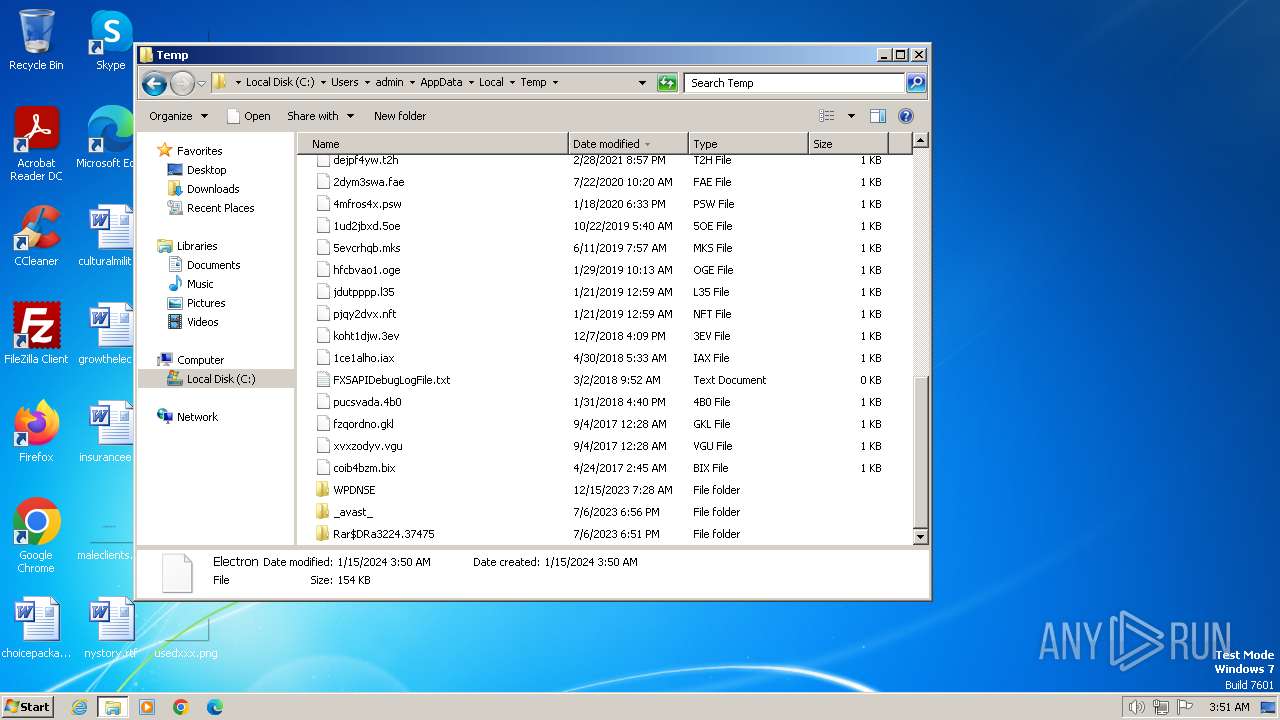
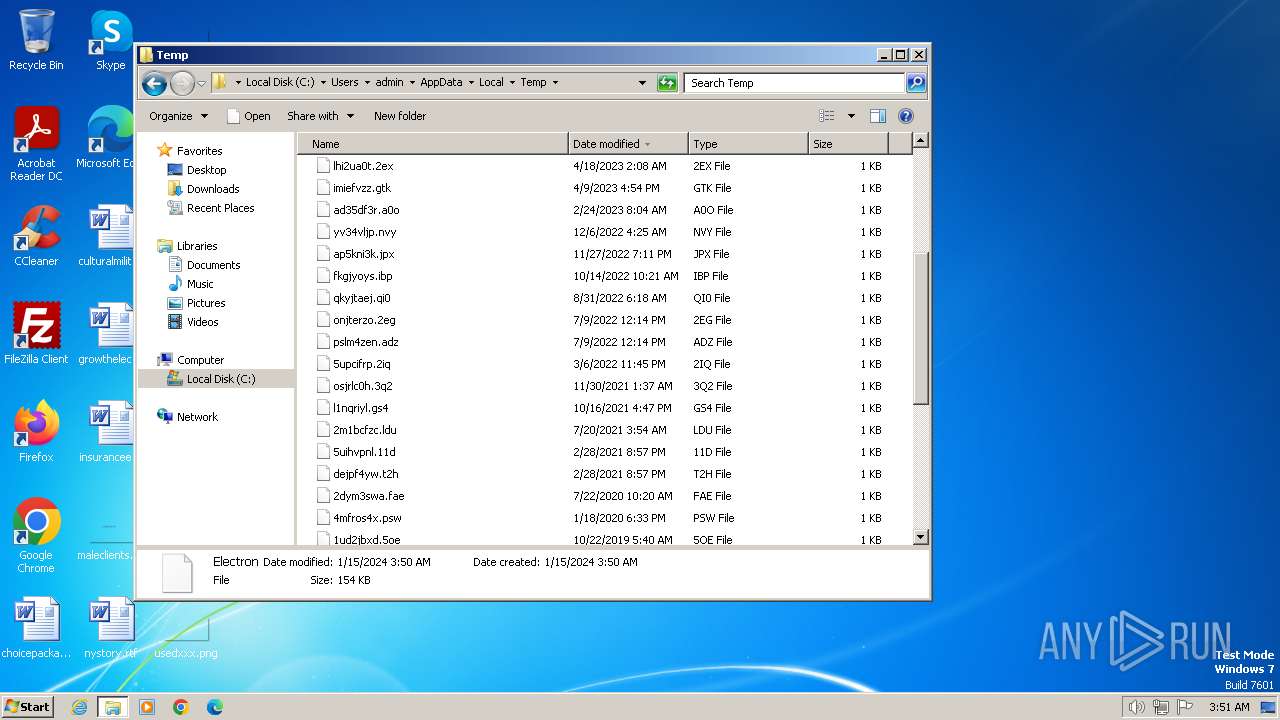
Create files in a temporary directory
- Electron.exe (PID: 5408)
- Issn.pif (PID: 5664)
- Electron.exe (PID: 4128)
- Issn.pif (PID: 3048)
Checks supported languages
- Issn.pif (PID: 5664)
- qemu-ga.exe (PID: 4248)
- Electron.exe (PID: 4128)
- Issn.pif (PID: 3048)
- Electron.exe (PID: 5408)
- jsc.exe (PID: 4680)
- jsc.exe (PID: 6140)
Reads mouse settings
- Issn.pif (PID: 5664)
- Issn.pif (PID: 3048)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6120)
- WinRAR.exe (PID: 5264)
Reads product name
- jsc.exe (PID: 6140)
- jsc.exe (PID: 4680)
Reads Environment values
- jsc.exe (PID: 6140)
- jsc.exe (PID: 4680)
Creates files or folders in the user directory
- jsc.exe (PID: 6140)
Reads the machine GUID from the registry
- jsc.exe (PID: 6140)
- jsc.exe (PID: 4680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
| ContentType: | text/html; charset=iso-8859-1 |
|---|---|
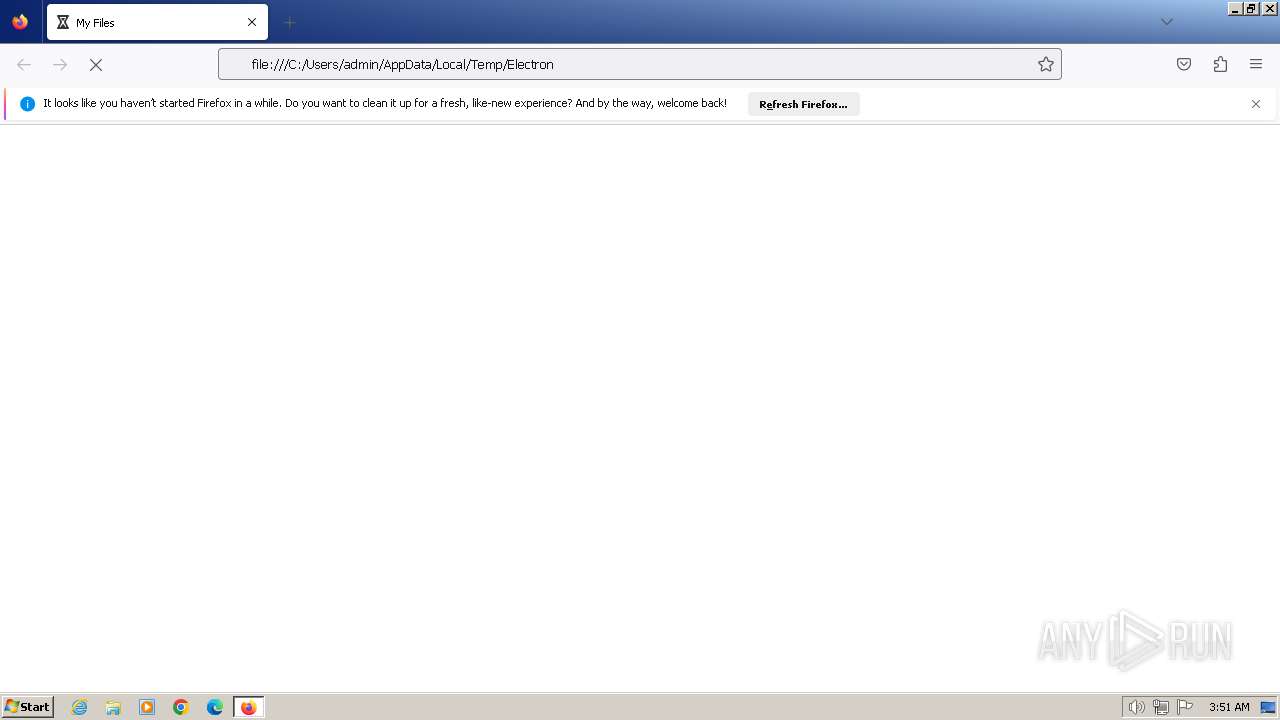
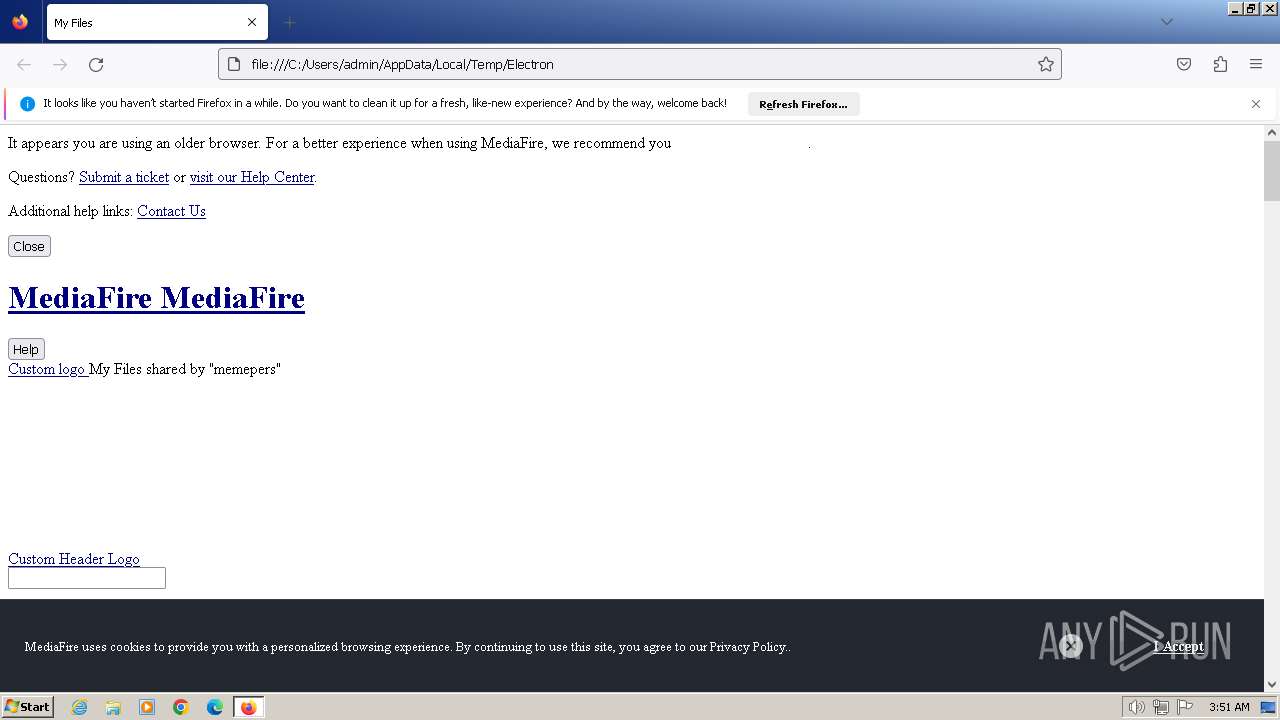
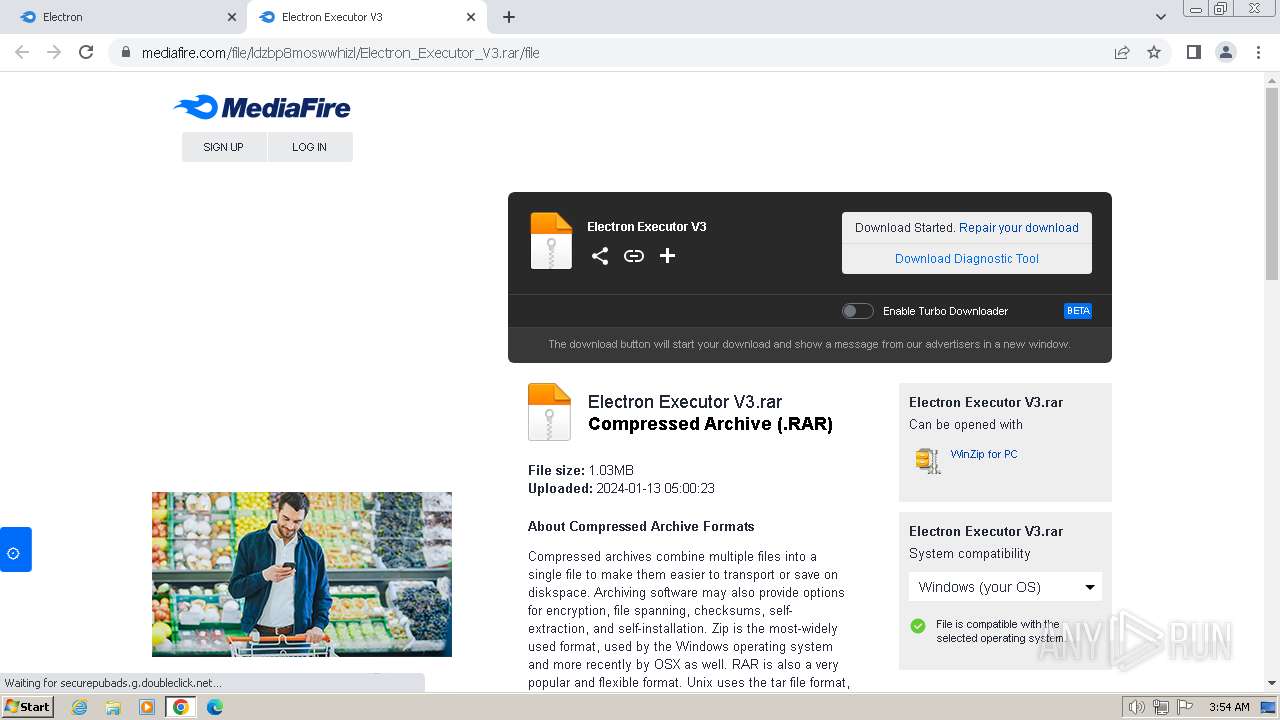
| Title: | My Files |
| Keywords: | online storage, free storage, cloud Storage, collaboration, backup file Sharing, share Files, photo backup, photo sharing, ftp replacement, cross platform, remote access, mobile access, send large files, recover files, file versioning, undelete, Windows, PC, Mac, OS X, Linux, iPhone, iPad, Android |
| Description: | MediaFire is a simple to use free service that lets you put all your photos, documents, music, and video in a single place so you can access them anywhere and share them everywhere. |
| Robots: | NOINDEX,FOLLOW |
| GoogleBot: | NOINDEX,FOLLOW |
| SLURP: | NOINDEX,FOLLOW |
| GoogleTranslateCustomization: | 5587c1b0a958bf07-62a8e309de686e87-gc92f61279a2c8524-11 |
| CacheControl: | no-store, no-cache, must-revalidate, post-check=0, pre-check=0 |
| Pragma: | no-cache |
| Expires: | - |
| HTTPEquivXUACompatible: | IE=edge,chrome=1 |
| AppleItunesApp: | app-id=555646196 |
| Viewport: | width=device-width, initial-scale=1.0 |
| MsapplicationTileImage: | favicon.png |
| MsapplicationTileColor: | #0077ff |
| ThemeColor: | #0077ff |
Total processes
166
Monitored processes
119
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
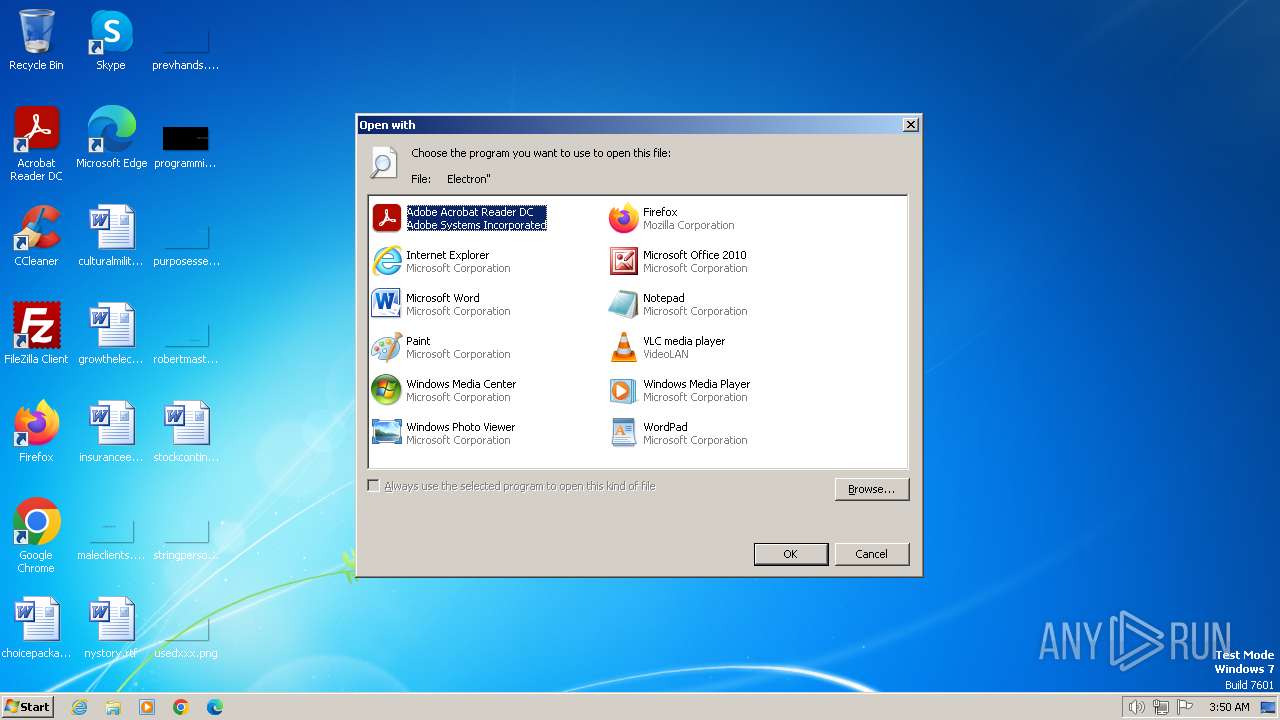
| 120 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL "C:\Users\admin\AppData\Local\Temp\Electron" | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 240 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1404.4.44699532\1067057344" -childID 3 -isForBrowser -prefsHandle 3896 -prefMapHandle 3848 -prefsLen 29209 -prefMapSize 244195 -jsInitHandle 936 -jsInitLen 240908 -parentBuildID 20230710165010 -appDir "C:\Program Files\Mozilla Firefox\browser" - {97f62cfb-bae5-4669-86aa-920935d393f8} 1404 "\\.\pipe\gecko-crash-server-pipe.1404" 3900 19174c90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=4004 --field-trial-handle=1204,i,10275649721007520653,14942437311478506038,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1404.0.78731527\967713355" -parentBuildID 20230710165010 -prefsHandle 1124 -prefMapHandle 1116 -prefsLen 28523 -prefMapSize 244195 -appDir "C:\Program Files\Mozilla Firefox\browser" - {b0549517-a44a-47f3-a359-49feeed1d807} 1404 "\\.\pipe\gecko-crash-server-pipe.1404" 1196 dba7a10 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 1 Version: 115.0.2 Modules
| |||||||||||||||
| 696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=4444 --field-trial-handle=1204,i,10275649721007520653,14942437311478506038,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3764 --field-trial-handle=1204,i,10275649721007520653,14942437311478506038,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=4232 --field-trial-handle=1204,i,10275649721007520653,14942437311478506038,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=46 --mojo-platform-channel-handle=6740 --field-trial-handle=1204,i,10275649721007520653,14942437311478506038,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=664 --field-trial-handle=1204,i,10275649721007520653,14942437311478506038,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=3140 --field-trial-handle=1204,i,10275649721007520653,14942437311478506038,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
25 084
Read events
24 824
Write events
259
Delete events
1
Modification events
| (PID) Process: | (120) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (120) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (120) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (120) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (120) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2036) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 2166C0A101000000 | |||
| (PID) Process: | (1404) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 044CC1A101000000 | |||
| (PID) Process: | (1404) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (1404) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (1404) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Theme |
Value: 1 | |||
Executable files
19
Suspicious files
689
Text files
147
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1404 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:B7A3C61D0C144CC5E166B1E769CA8F8C | SHA256:7FADCB77FFACA6B9E9F15C6F1CD3AAD4C20DCD90FA92429A627A3A7110CA2644 | |||
| 1404 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 1404 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:60E0DE9E05EC76C749D80F0D15A81B21 | SHA256:08252FA62CCCCD316474E20CC7317A6B5C932B2C972234318E8CCDA39EC2EF48 | |||
| 1404 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1404 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1404 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:60E0DE9E05EC76C749D80F0D15A81B21 | SHA256:08252FA62CCCCD316474E20CC7317A6B5C932B2C972234318E8CCDA39EC2EF48 | |||
| 1404 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 1404 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1404 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\places.sqlite-wal | binary | |
MD5:D0C85BBB9A32D4D5FF29CAE9D04F4B49 | SHA256:49609C4A932B80B888AE0E99E162C21C5A86426483C9509826AE06E69AB6C780 | |||
| 1404 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
380
DNS requests
627
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1404 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | text | 90 b | unknown |
1404 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | text | 8 b | unknown |
1404 | firefox.exe | POST | 200 | 23.53.40.154:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
1404 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3 | unknown | binary | 472 b | unknown |
1404 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3 | unknown | binary | 471 b | unknown |
1404 | firefox.exe | POST | 200 | 23.53.40.154:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
1404 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3 | unknown | binary | 472 b | unknown |
1404 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3 | unknown | binary | 472 b | unknown |
1404 | firefox.exe | POST | 200 | 23.53.40.154:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
1404 | firefox.exe | POST | — | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1404 | firefox.exe | 142.250.184.202:443 | ajax.googleapis.com | — | — | whitelisted |
1404 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
1404 | firefox.exe | 34.117.237.239:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
1404 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | GOOGLE | US | unknown |
1404 | firefox.exe | 142.250.184.232:443 | www.googletagmanager.com | — | — | unknown |
1404 | firefox.exe | 142.250.184.234:443 | safebrowsing.googleapis.com | — | — | whitelisted |
1404 | firefox.exe | 142.250.186.132:443 | www.google.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
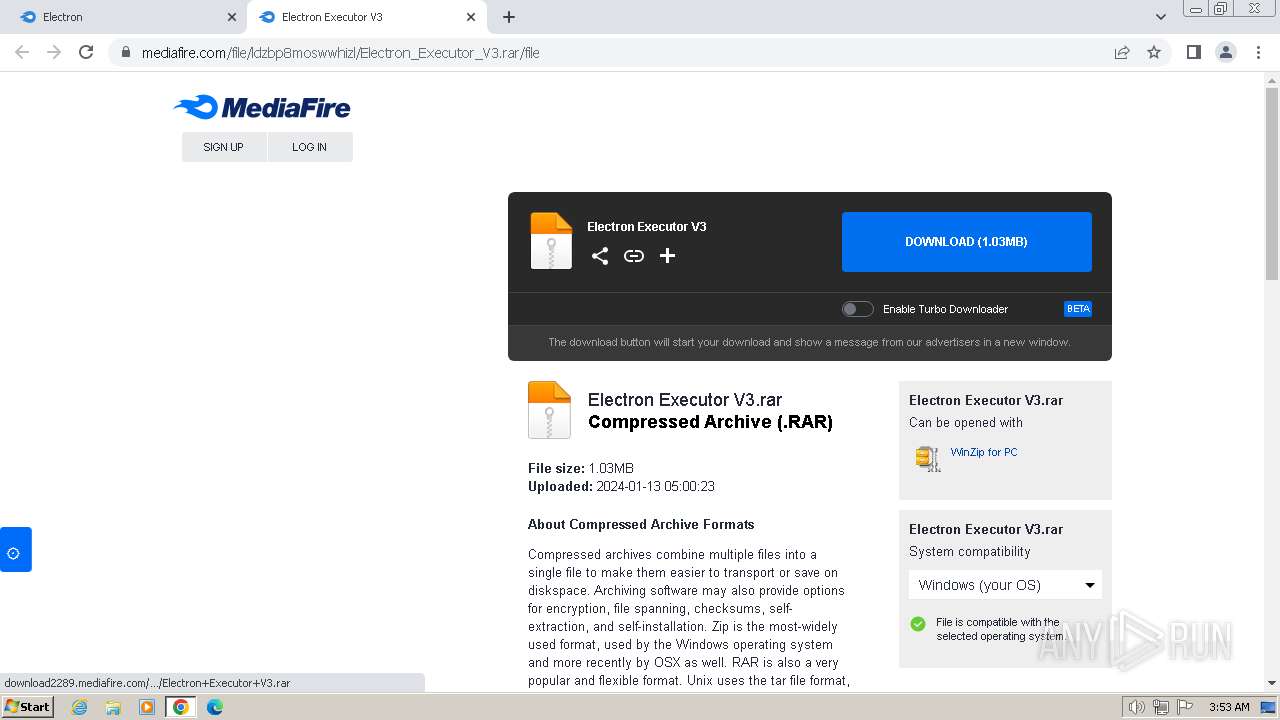
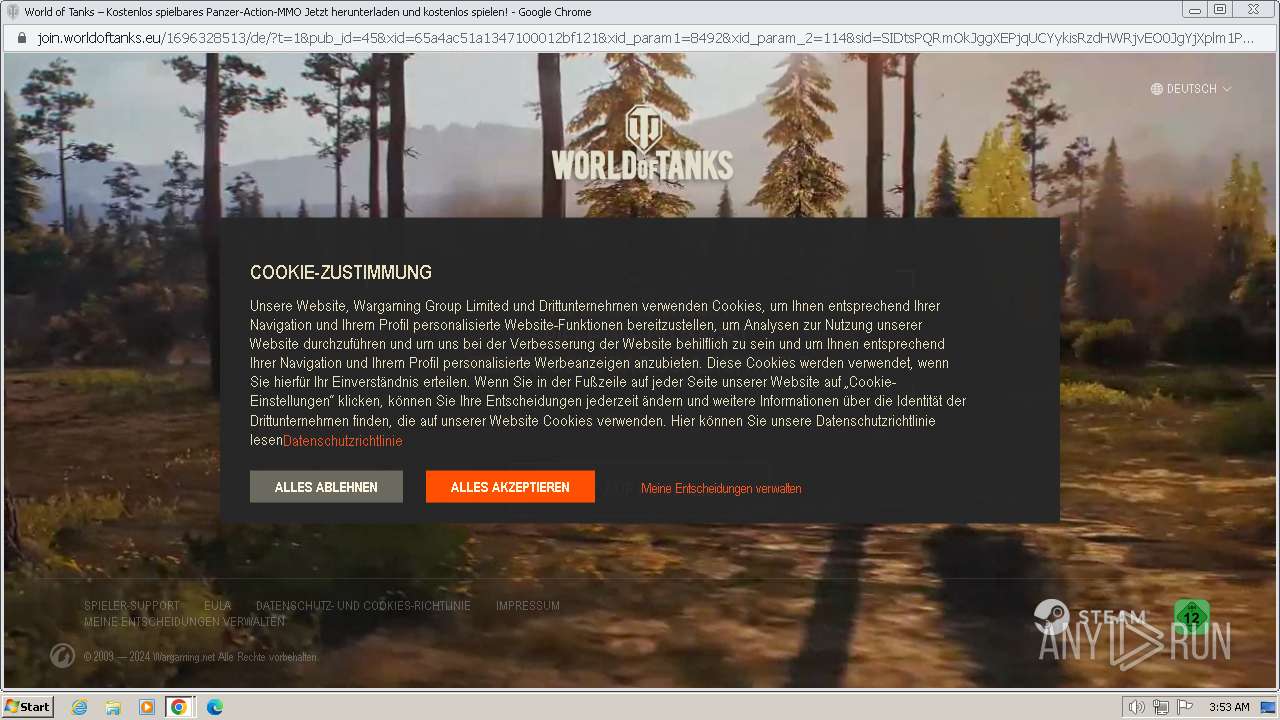
1080 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
1080 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
1080 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
1080 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
1080 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2632 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2632 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2632 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
2632 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
2632 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |