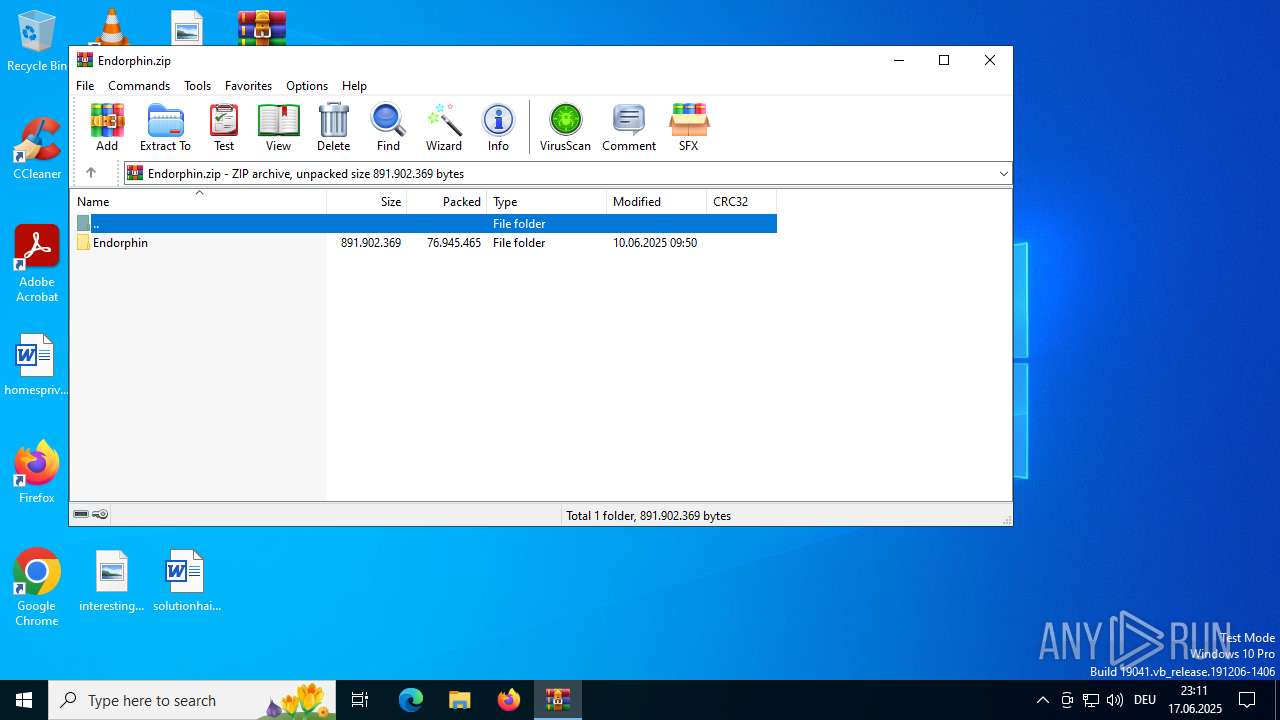
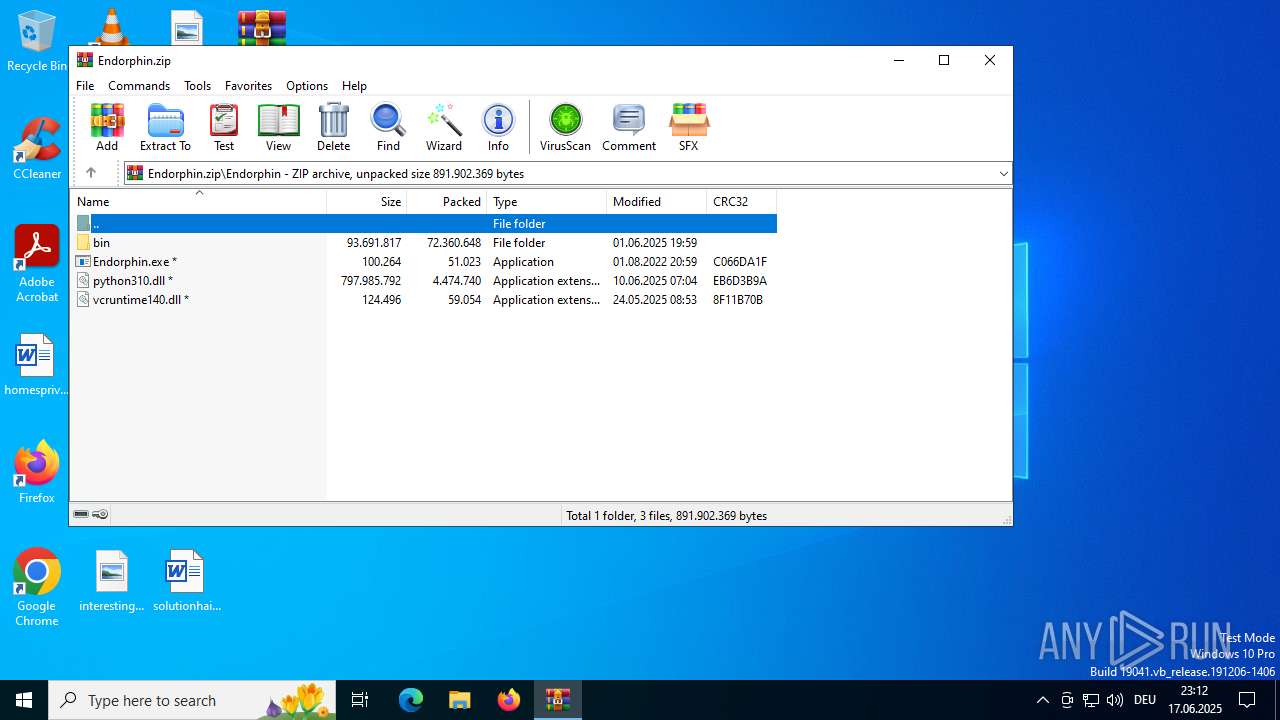
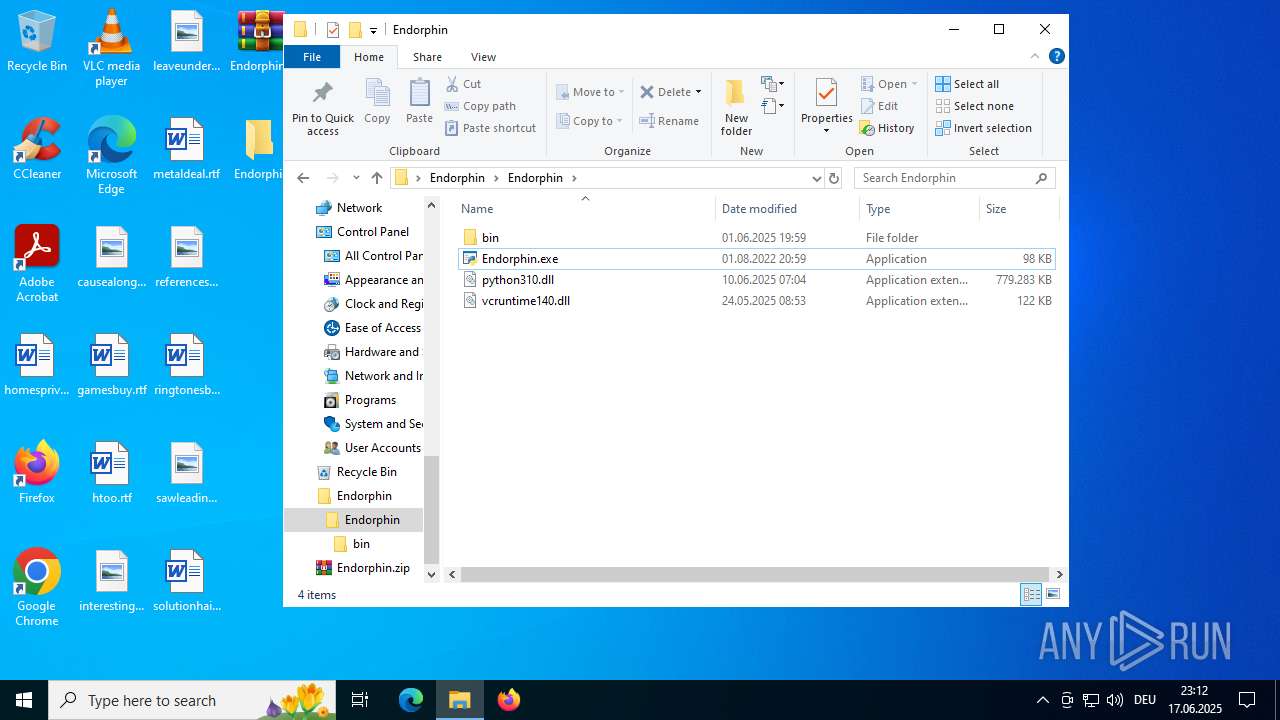
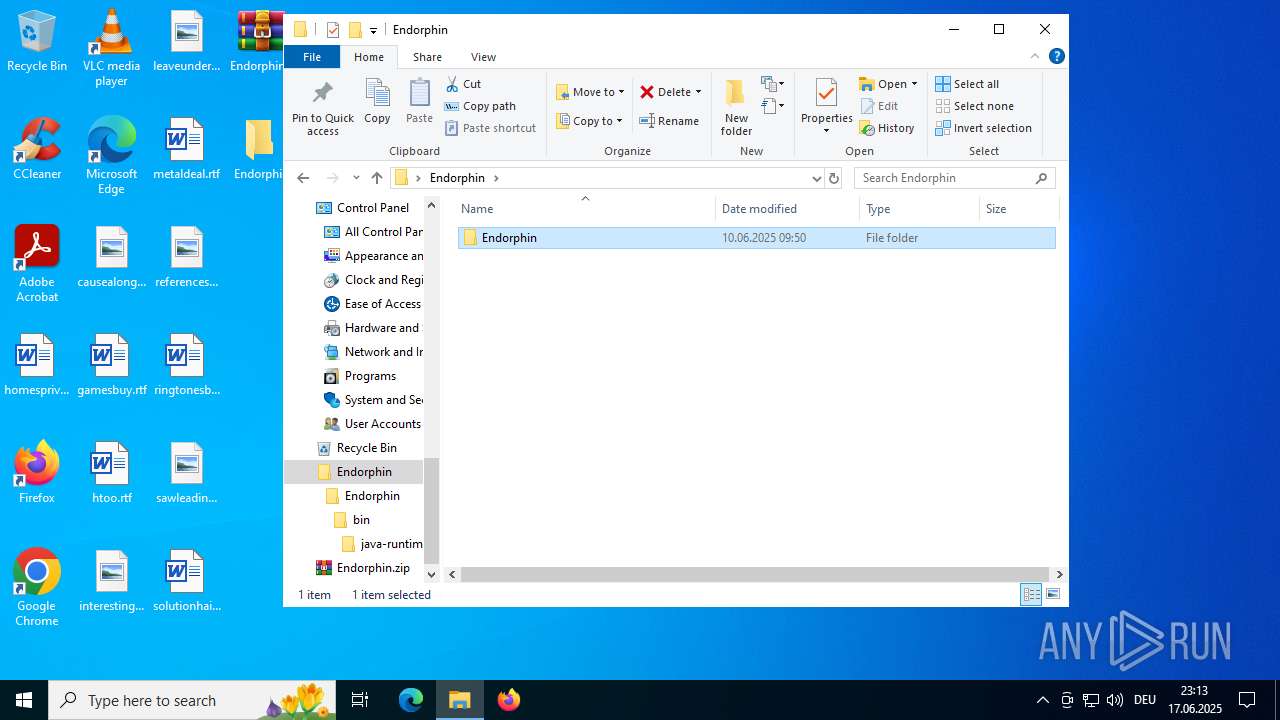
| File name: | Endorphin.zip |
| Full analysis: | https://app.any.run/tasks/2fe03de7-35c1-4e3e-8d5f-12871574f4b4 |
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | June 17, 2025, 21:11:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
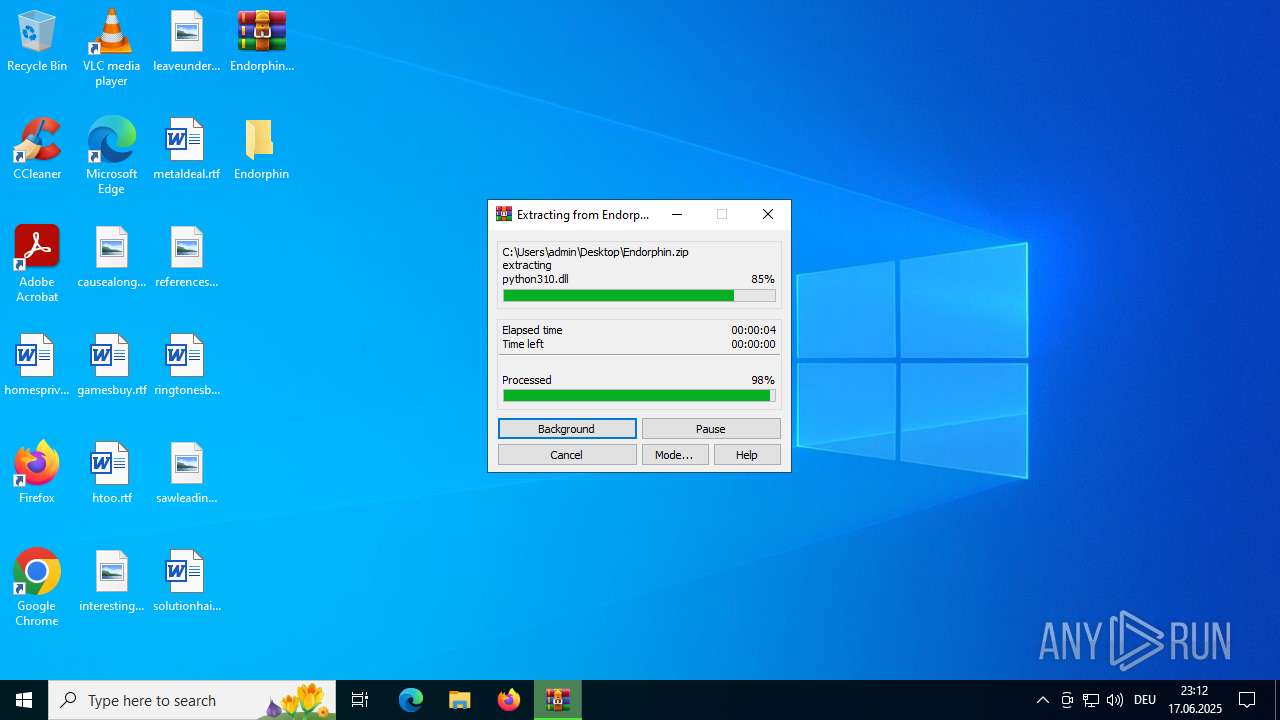
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 92606E564C2EFA3805843855E30217FC |
| SHA1: | B6F6F72AFF3222F7F1EE4E4C6AF1EDE717E4D17E |
| SHA256: | A744316908F454D16387DA45B8711DB2E2BC5D853242261226540C20FE13D6C5 |
| SSDEEP: | 786432:KroH38c9N+vVn6G3zUIbGcHQ5IQI9LaeV:KroX8c9AvlZjFC0QWQI9Lak |
MALICIOUS
RHADAMANTHYS has been detected (YARA)
- OOBE-Maintenance.exe (PID: 7060)
Actions looks like stealing of personal data
- OOBE-Maintenance.exe (PID: 7060)
SUSPICIOUS
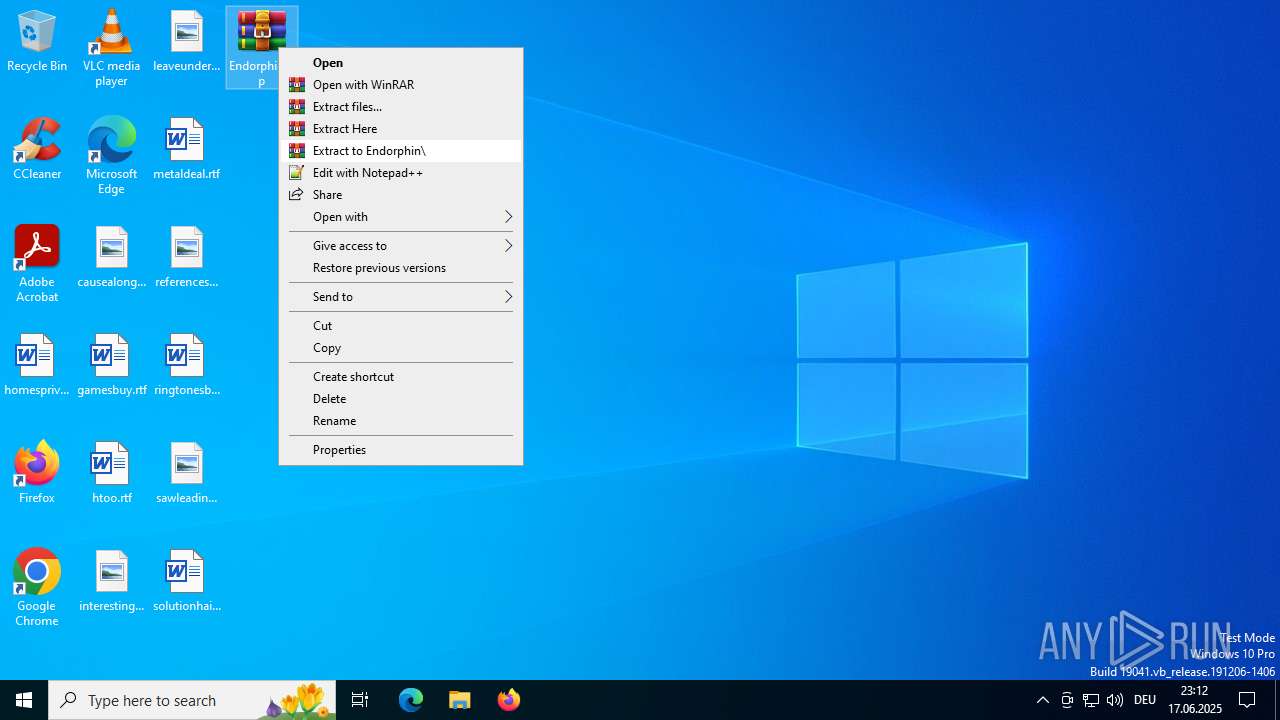
Process drops legitimate windows executable
- WinRAR.exe (PID: 6896)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 6896)
The process checks if it is being run in the virtual environment
- OpenWith.exe (PID: 3584)
Executes application which crashes
- winhlp32.exe (PID: 4084)
Reads security settings of Internet Explorer
- msedge.exe (PID: 2668)
Reads Mozilla Firefox installation path
- msedge.exe (PID: 2668)
Loads DLL from Mozilla Firefox
- OOBE-Maintenance.exe (PID: 7060)
Searches for installed software
- OOBE-Maintenance.exe (PID: 7060)
INFO
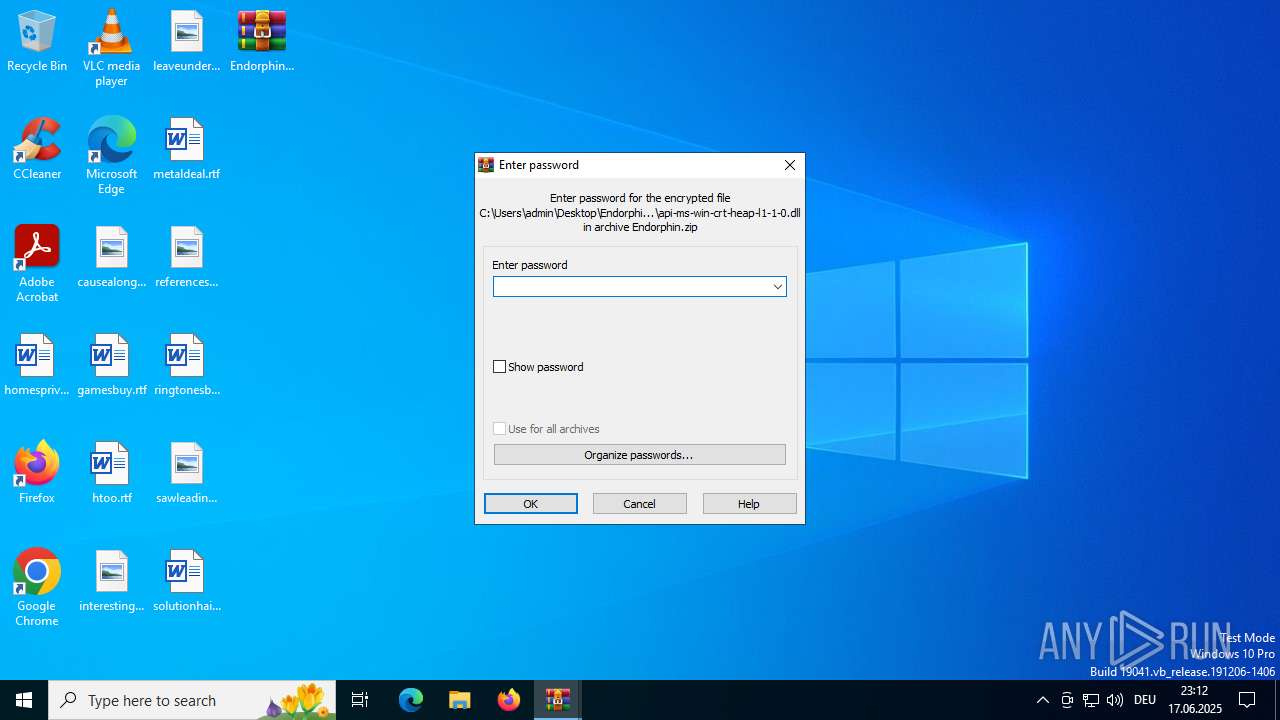
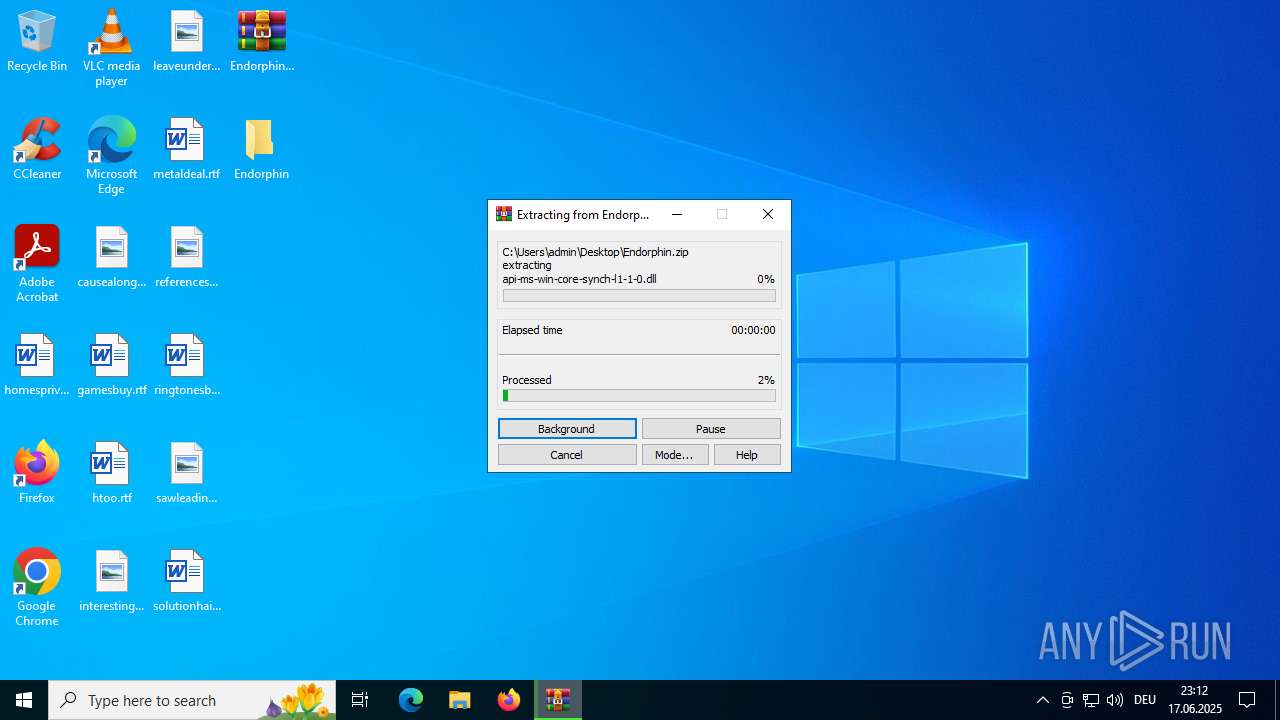
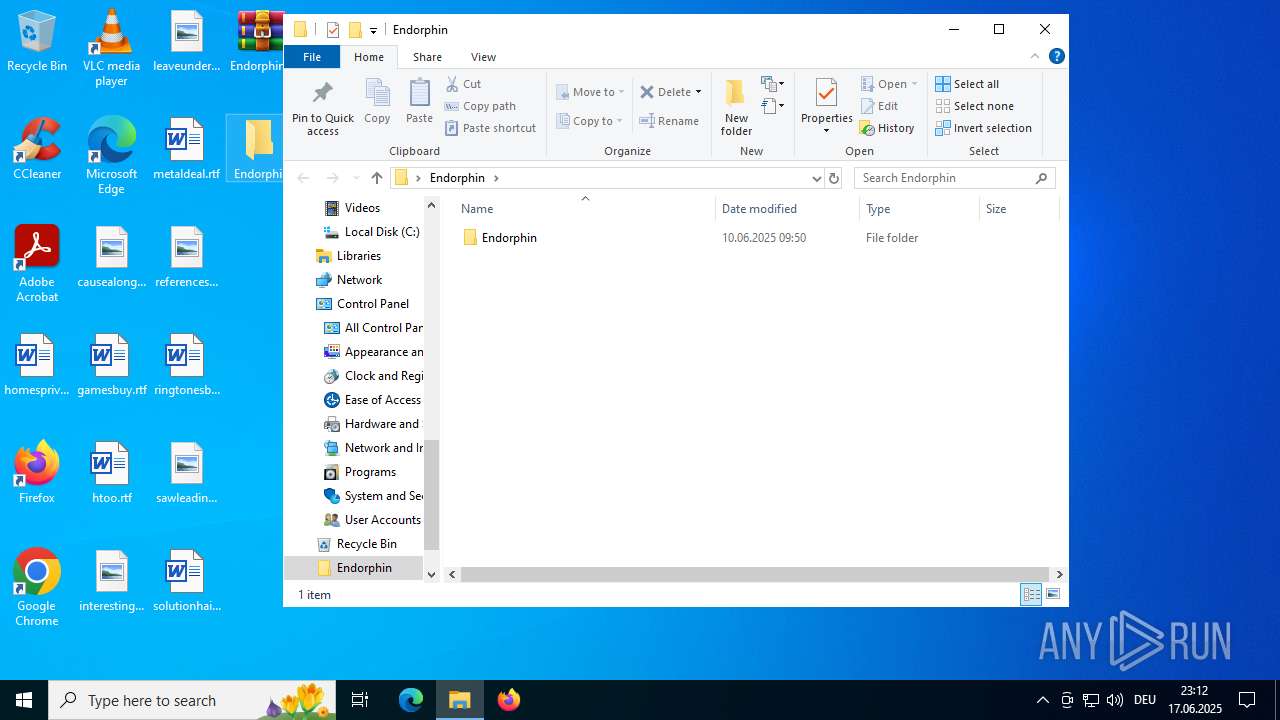
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6896)
The sample compiled with english language support
- WinRAR.exe (PID: 6896)
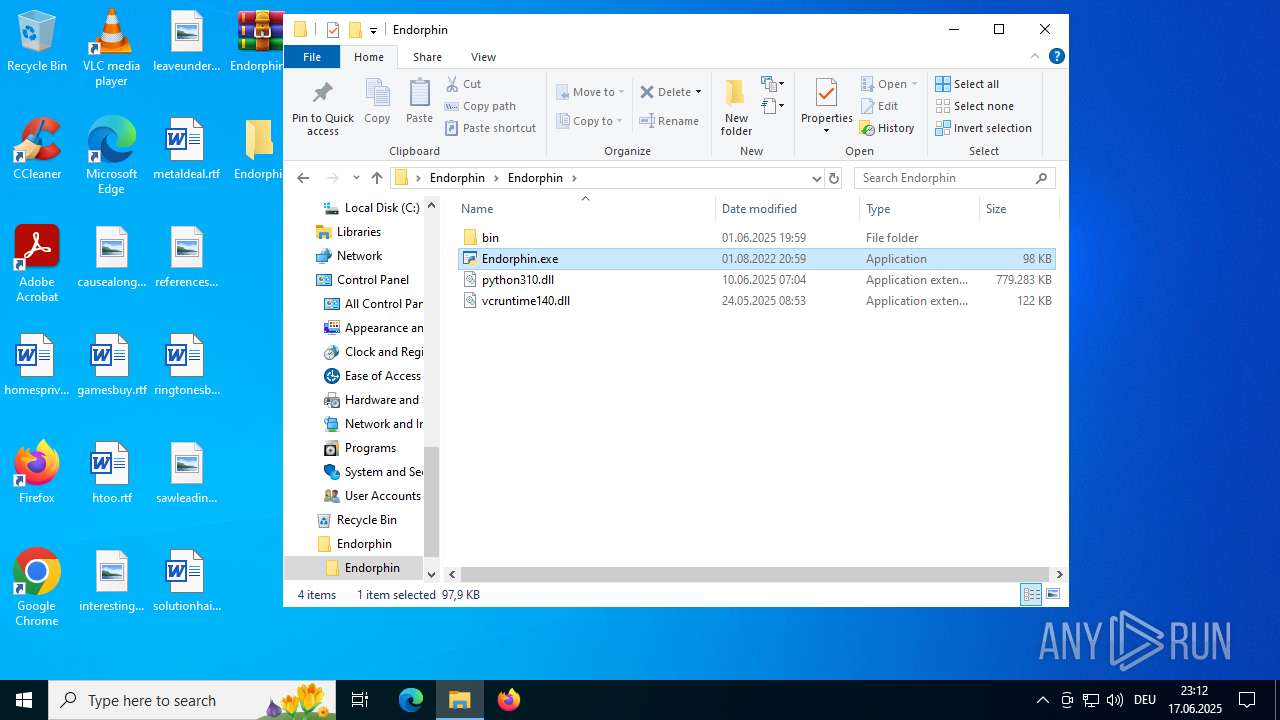
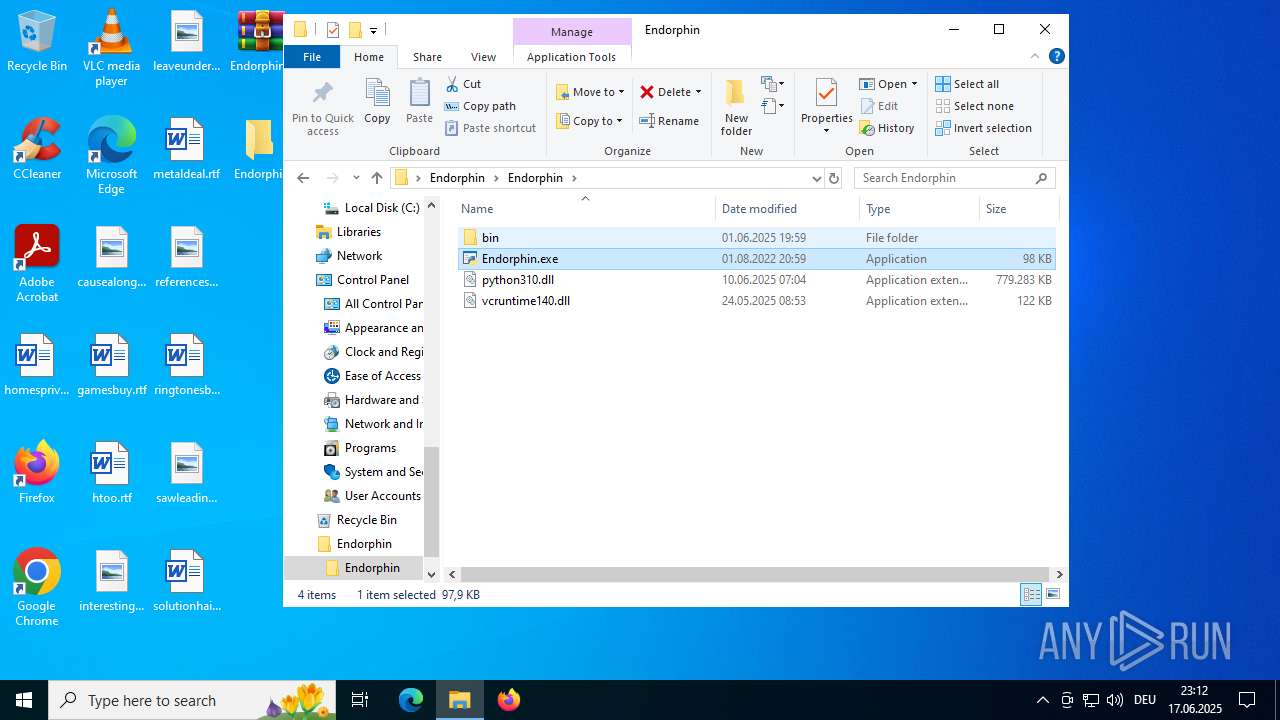
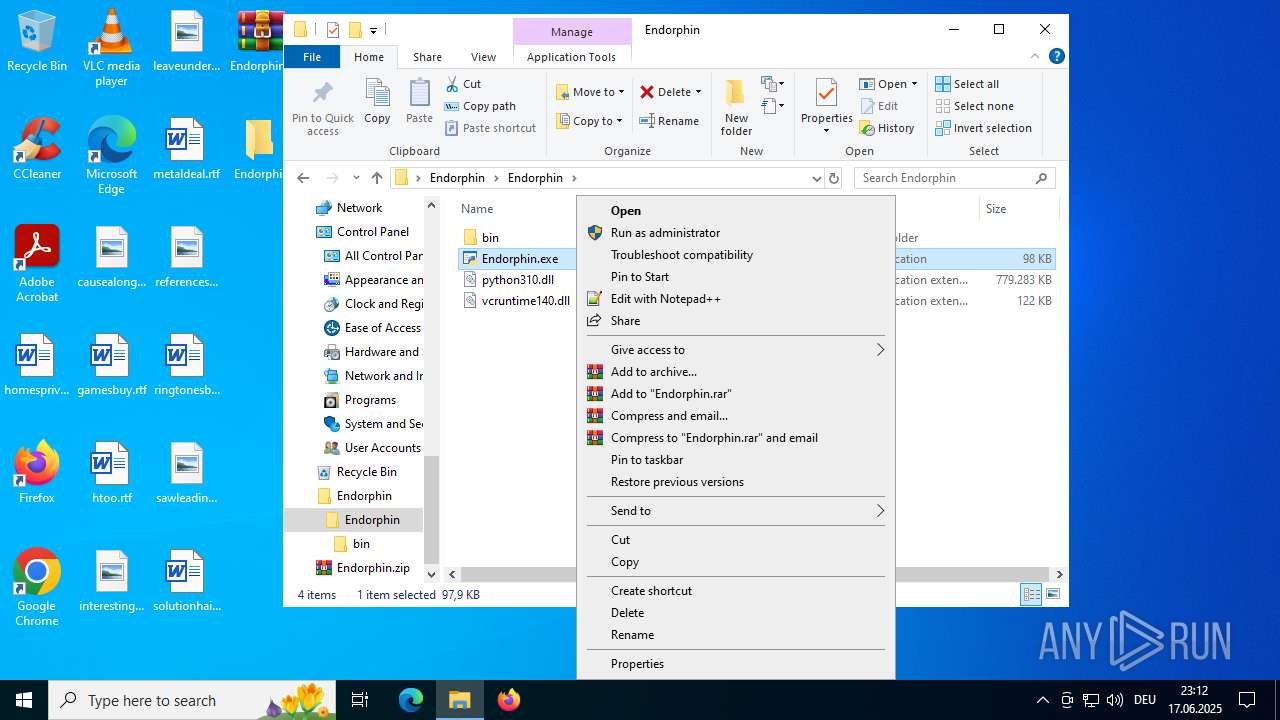
Manual execution by a user
- WinRAR.exe (PID: 6896)
- Endorphin.exe (PID: 6980)
- OpenWith.exe (PID: 3584)
- OOBE-Maintenance.exe (PID: 7060)
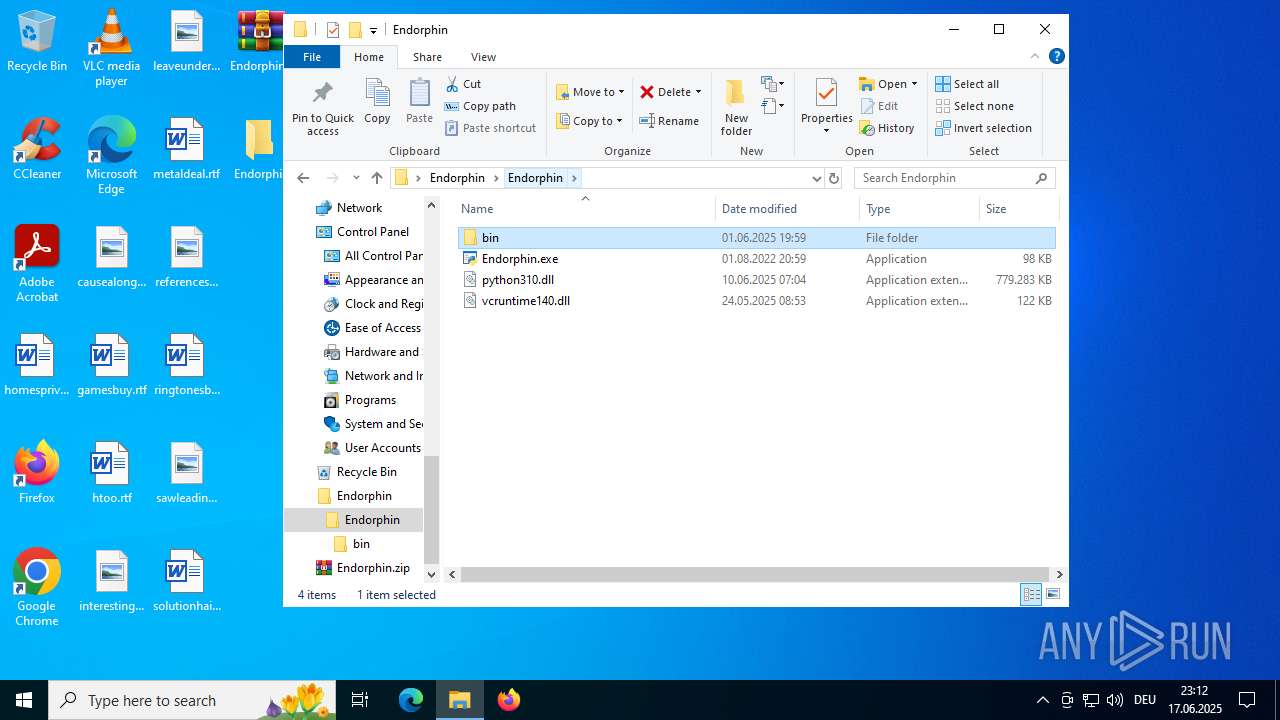
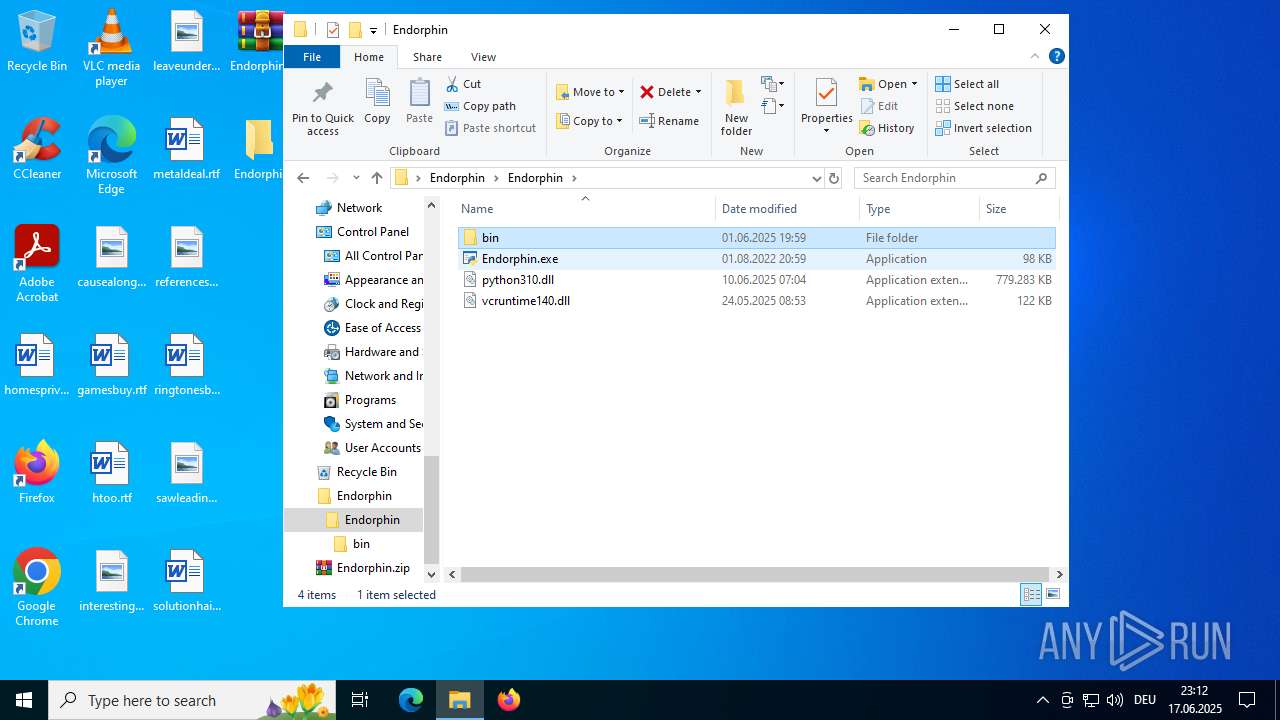
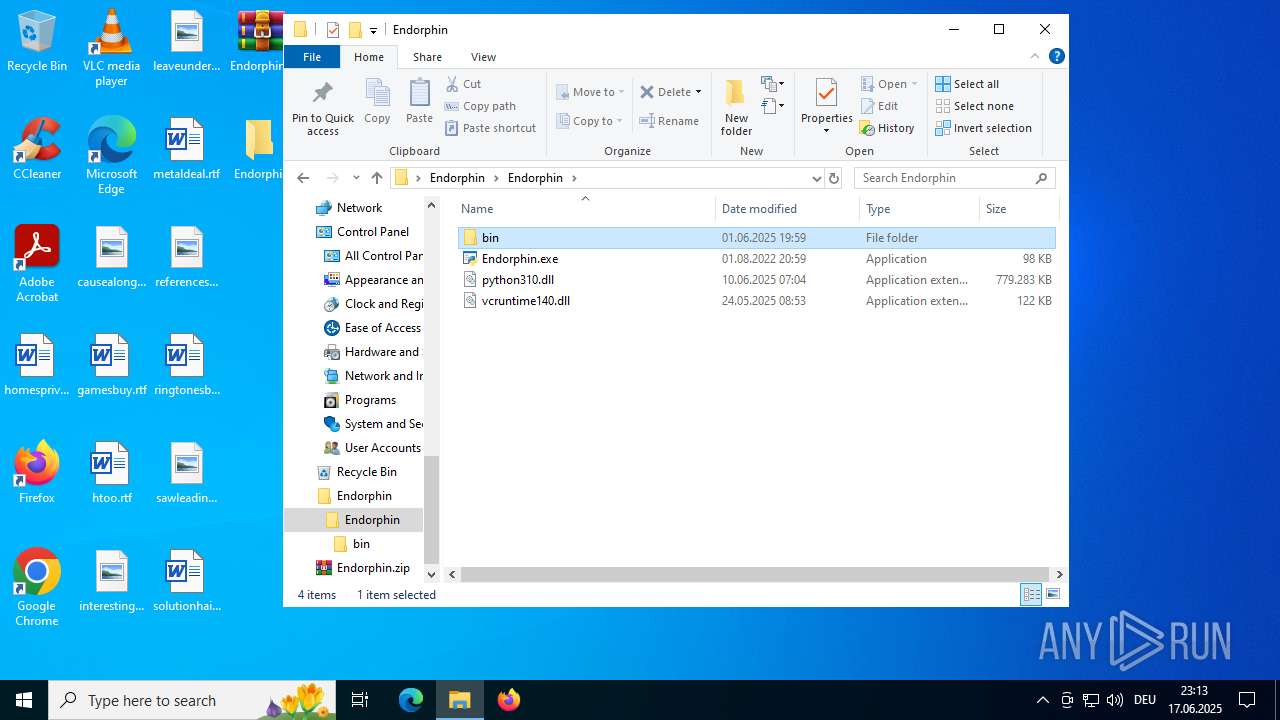
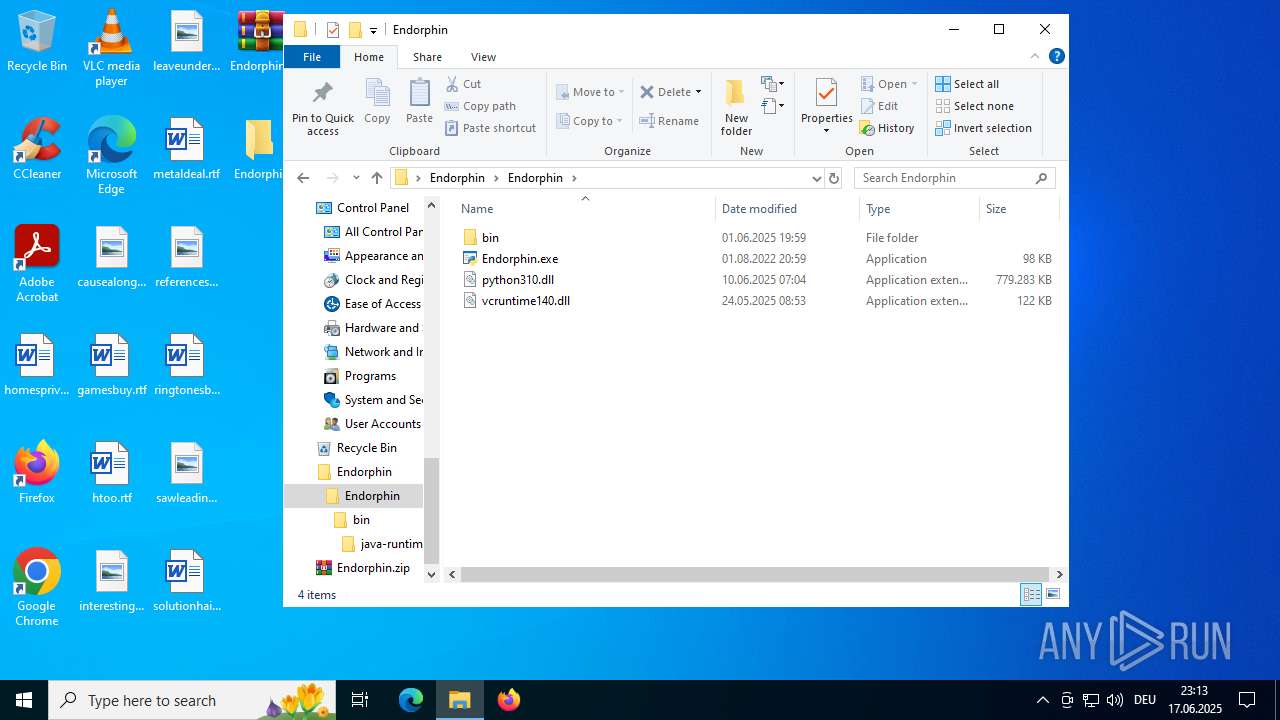
Python executable
- Endorphin.exe (PID: 6980)
Checks supported languages
- Endorphin.exe (PID: 6980)
- chrome.exe (PID: 3620)
- msedge.exe (PID: 2668)
- wmpshare.exe (PID: 7448)
Reads the computer name
- chrome.exe (PID: 3620)
- msedge.exe (PID: 2668)
Reads the software policy settings
- slui.exe (PID: 3720)
Checks proxy server information
- slui.exe (PID: 3720)
- chrome.exe (PID: 3620)
- msedge.exe (PID: 2668)
Reads Environment values
- chrome.exe (PID: 3620)
- msedge.exe (PID: 2668)
Create files in a temporary directory
- chrome.exe (PID: 3620)
- OOBE-Maintenance.exe (PID: 7060)
- msedge.exe (PID: 2668)
Reads the machine GUID from the registry
- chrome.exe (PID: 3620)
- msedge.exe (PID: 2668)
- wmpshare.exe (PID: 7448)
Process checks computer location settings
- chrome.exe (PID: 3620)
- msedge.exe (PID: 2668)
Application launched itself
- msedge.exe (PID: 2668)
- chrome.exe (PID: 3620)
Process checks whether UAC notifications are on
- msedge.exe (PID: 2668)
Creates files or folders in the user directory
- msedge.exe (PID: 2668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:06:10 10:50:22 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Endorphin/ |
Total processes
170
Monitored processes
48
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --string-annotations --always-read-main-dll --field-trial-handle=2376,i,2087694476849849867,8339928900191012228,262144 --variations-seed-version --mojo-platform-channel-handle=2500 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAAAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --use-gl=angle --use-angle=swiftshader-webgl --field-trial-handle=2208,i,6046303951996133614,15320936523752858475,262144 --variations-seed-version --mojo-platform-channel-handle=2200 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 892 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=4776,i,2087694476849849867,8339928900191012228,262144 --variations-seed-version --mojo-platform-channel-handle=4796 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1080 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --always-read-main-dll --field-trial-handle=5240,i,2087694476849849867,8339928900191012228,262144 --variations-seed-version --mojo-platform-channel-handle=5188 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --string-annotations --always-read-main-dll --field-trial-handle=2824,i,2087694476849849867,8339928900191012228,262144 --variations-seed-version --mojo-platform-channel-handle=2992 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1296 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --always-read-main-dll --field-trial-handle=4876,i,2087694476849849867,8339928900191012228,262144 --variations-seed-version --mojo-platform-channel-handle=5156 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --string-annotations --field-trial-handle=2304,i,6046303951996133614,15320936523752858475,262144 --variations-seed-version --mojo-platform-channel-handle=2352 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1752 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --always-read-main-dll --field-trial-handle=4800,i,2087694476849849867,8339928900191012228,262144 --variations-seed-version --mojo-platform-channel-handle=4872 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | OOBE-Maintenance.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 27768 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --field-trial-handle=3652,i,6046303951996133614,15320936523752858475,262144 --variations-seed-version --mojo-platform-channel-handle=3988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
14 020
Read events
13 976
Write events
41
Delete events
3
Modification events
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Endorphin.zip | |||
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
134
Suspicious files
133
Text files
346
Unknown types
110
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
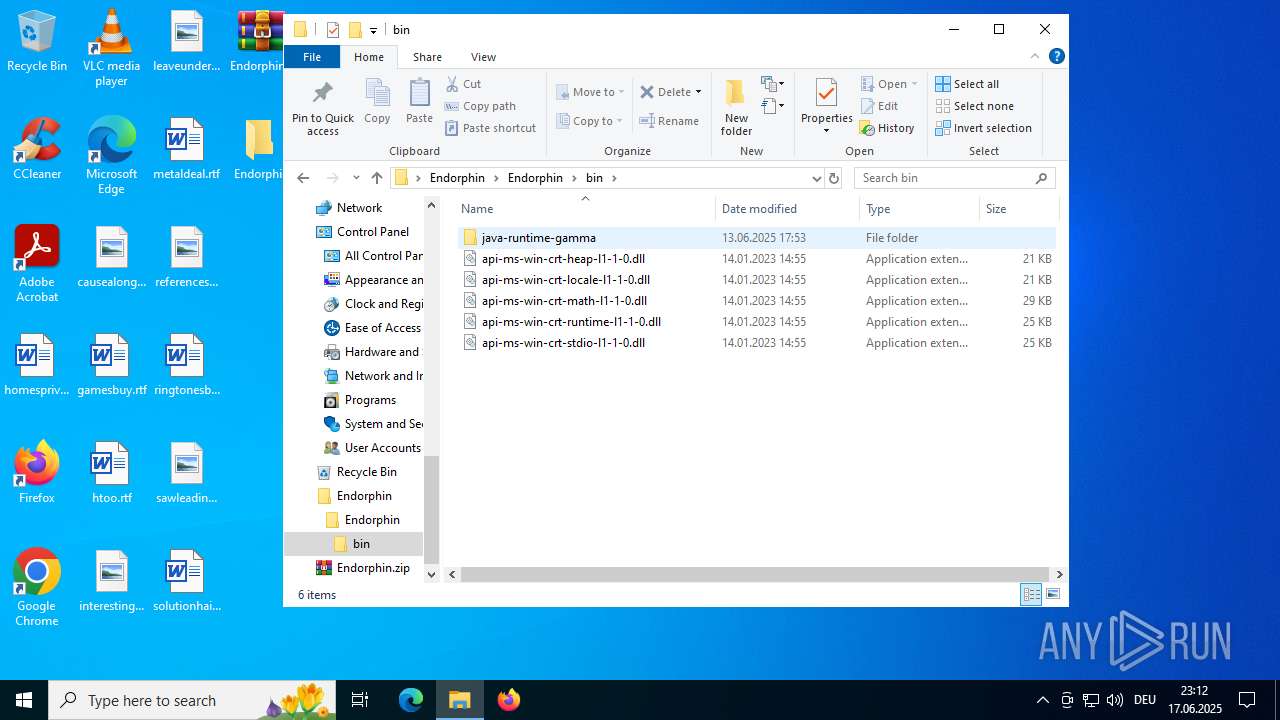
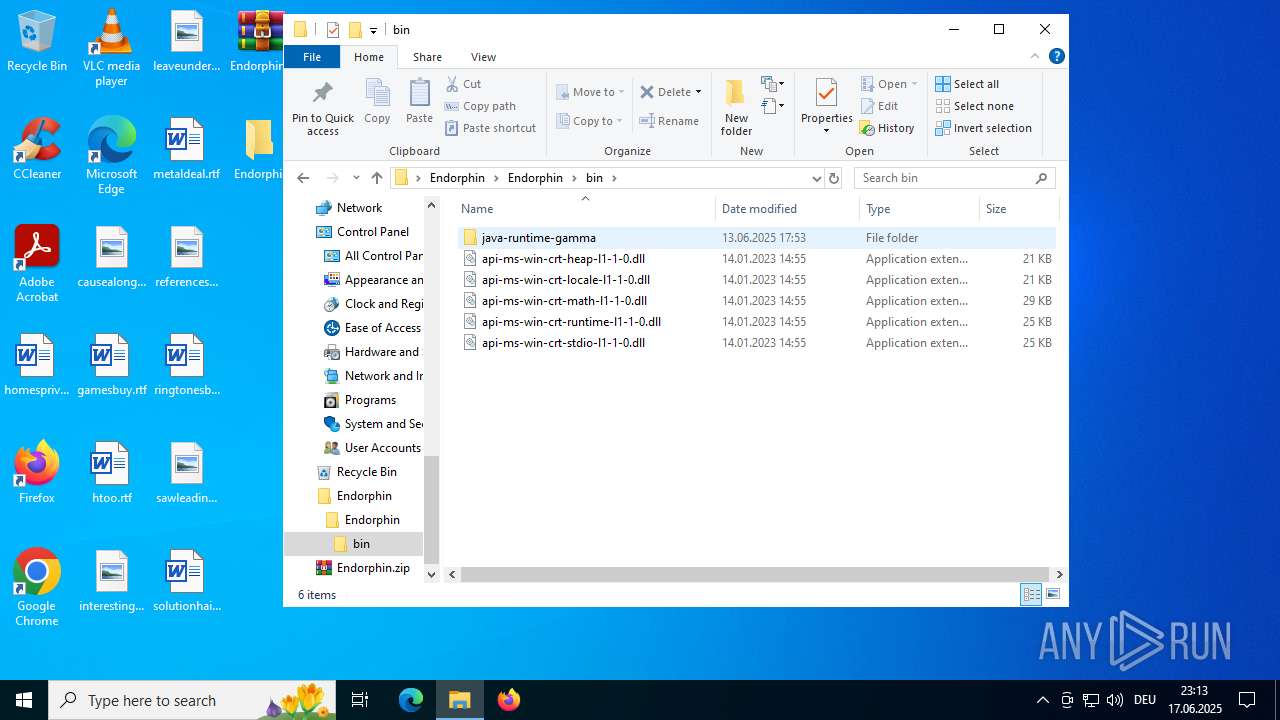
| 6896 | WinRAR.exe | C:\Users\admin\Desktop\Endorphin\Endorphin\bin\api-ms-win-crt-math-l1-1-0.dll | executable | |
MD5:7A235962DBAB1E807C6EC7609FC76077 | SHA256:F7C5D7394643C95FE14C07773A8A206E74A28DB125F9B3976F9E1C8C599F2AF1 | |||
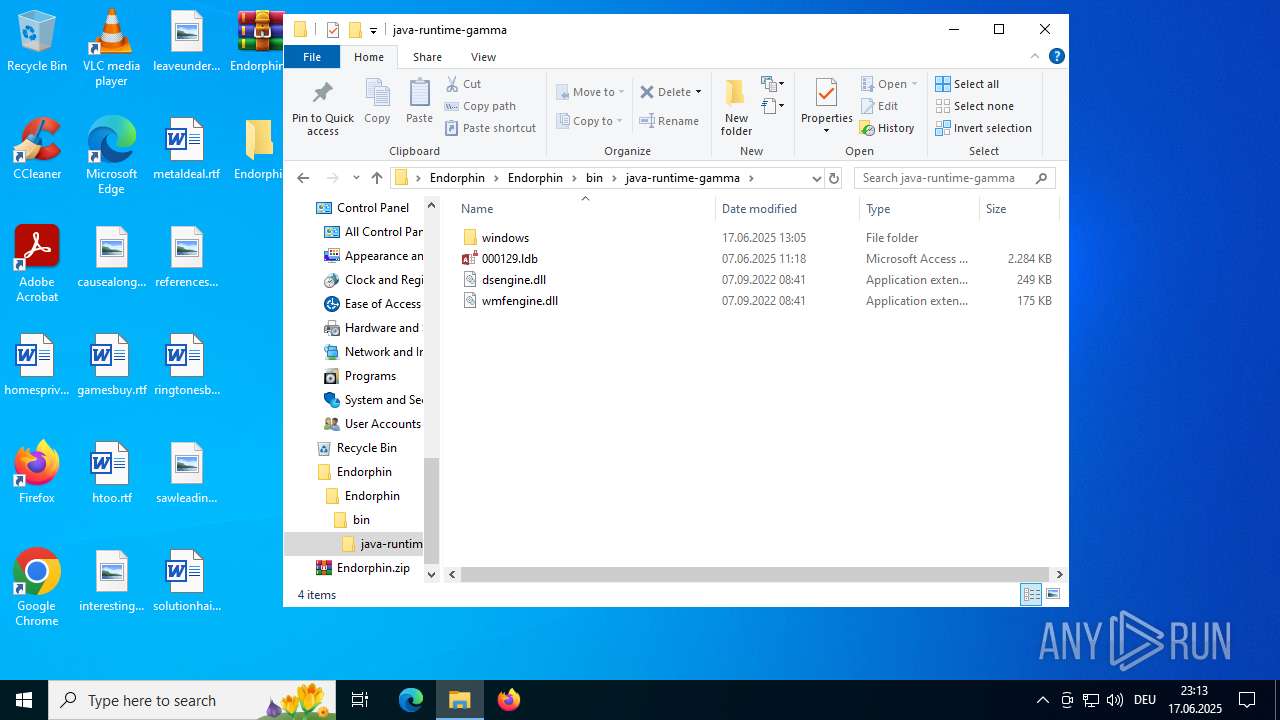
| 6896 | WinRAR.exe | C:\Users\admin\Desktop\Endorphin\Endorphin\bin\java-runtime-gamma\000129.ldb | binary | |
MD5:A5AC95FD722C2B84322F3CB51716A95F | SHA256:F916A657CDB5ABEF575E399E50BE48D14737B23970F9AEBCA5A356E6A45CE1A1 | |||
| 6896 | WinRAR.exe | C:\Users\admin\Desktop\Endorphin\Endorphin\bin\java-runtime-gamma\windows\java-runtime-gamma\bin\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:ECDD006AAE56427C3555740F1ABFA8D6 | SHA256:13BC8B3F90DA149030897B8F9F08D71E5D1561E3AE604472A82F58DAB2B103F9 | |||
| 6896 | WinRAR.exe | C:\Users\admin\Desktop\Endorphin\Endorphin\bin\java-runtime-gamma\windows\java-runtime-gamma\bin\api-ms-win-core-handle-l1-1-0.dll | executable | |
MD5:3039A2F694D26E754F77AECFFDA9ACE4 | SHA256:625667EA50B2BD0BAE1D6EB3C7E732E9E3A0DEA21B2F9EAC3A94C71C5E57F537 | |||
| 6896 | WinRAR.exe | C:\Users\admin\Desktop\Endorphin\Endorphin\bin\java-runtime-gamma\windows\java-runtime-gamma\bin\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:681C84FB102B5761477D8DA2D68CD834 | SHA256:F0F7CB2A9FFCCB43400DB88D6BF99F2FCC3161DE1AC96C48501D4D522C48C2CA | |||
| 6896 | WinRAR.exe | C:\Users\admin\Desktop\Endorphin\Endorphin\bin\java-runtime-gamma\windows\java-runtime-gamma\bin\api-ms-win-core-console-l1-2-0.dll | executable | |
MD5:039D612693E56CCF32AE81C99443EA77 | SHA256:4E978EE035B72032D0B7693E09EED6E112DCED6965780BC3E6B8E024EA2366AB | |||
| 6896 | WinRAR.exe | C:\Users\admin\Desktop\Endorphin\Endorphin\bin\java-runtime-gamma\windows\java-runtime-gamma\bin\api-ms-win-core-fibers-l1-1-0.dll | executable | |
MD5:EB065ED1B5CABDBB90E2403B8564778F | SHA256:BB2D740333AFAEA2A73A163F95FA102D018CCD68DEF28B6815A2BE0696AB57DB | |||
| 6896 | WinRAR.exe | C:\Users\admin\Desktop\Endorphin\Endorphin\bin\java-runtime-gamma\windows\java-runtime-gamma\bin\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:720DB2235C4193151FF8987F8A729135 | SHA256:092B72832C47F9C4EDCDE61F1A111C20EB73452984E0A6109482DE74EB03C34D | |||
| 6896 | WinRAR.exe | C:\Users\admin\Desktop\Endorphin\Endorphin\bin\java-runtime-gamma\windows\java-runtime-gamma\bin\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:D92E6A007FC22A1E218552EBFB65DA93 | SHA256:03BD3217EAE0EF68521B39556E7491292DB540F615DA873DD8DA538693B81862 | |||
| 6896 | WinRAR.exe | C:\Users\admin\Desktop\Endorphin\Endorphin\bin\java-runtime-gamma\windows\java-runtime-gamma\bin\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:36277B52C64CC66216751AAD135528F9 | SHA256:F353B6C2DF7AADB457263A02BCE59C44BBAB55F98AE6509674CFBC3751F761B9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
53
DNS requests
50
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 178.236.254.91:443 | https://polototupo.shop/gaDERGEteway/x9qucgk3.xpfus | unknown | image | 1.91 Mb | unknown |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
1336 | chrome.exe | GET | 200 | 142.250.184.206:80 | http://clients2.google.com/time/1/current?cup2key=8:IKPDaVKQWotbgOsHmUhiImRl5GpEbqI-qEUMdlaJ72Y&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
1268 | svchost.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5944 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
cloudflare-dns.com |
| whitelisted |
polototupo.shop |
| unknown |
x.ns.gin.ntt.net |
| whitelisted |
pool.ntp.org |
| whitelisted |
ntp.time.nl |
| unknown |
Threats
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr18CE.tmp directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\chr2D7F.tmp directory exists )
|