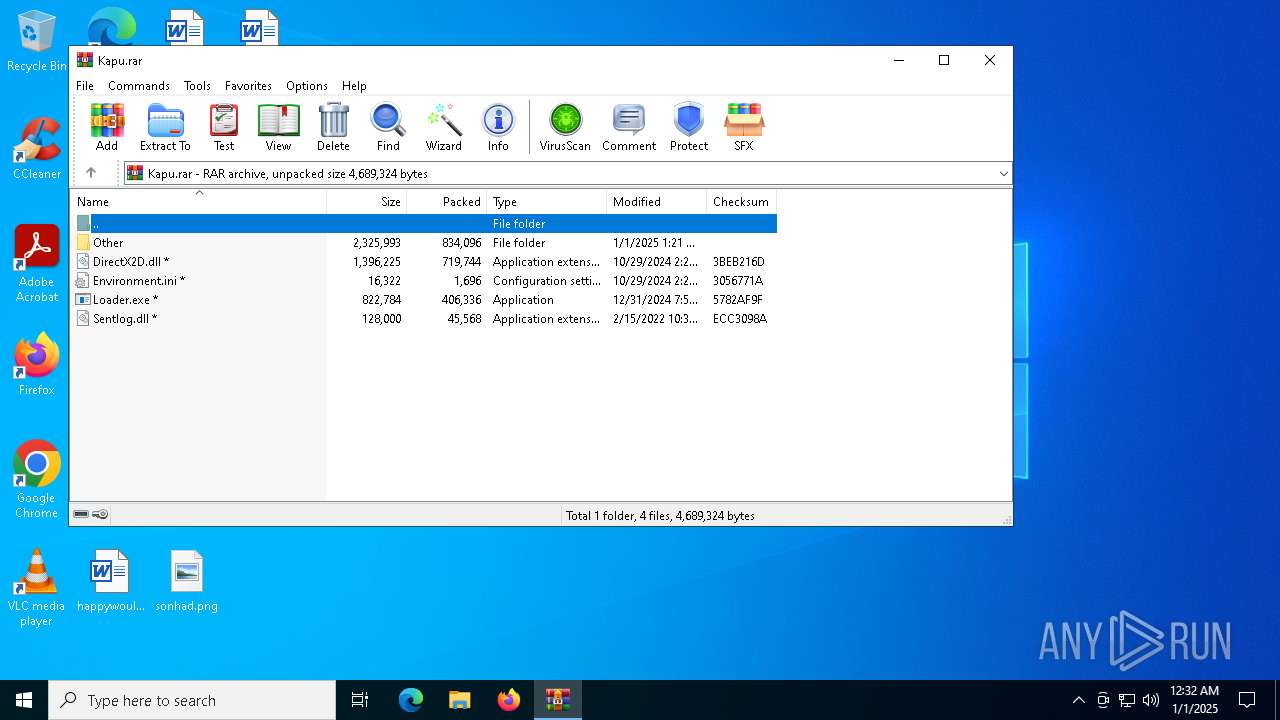
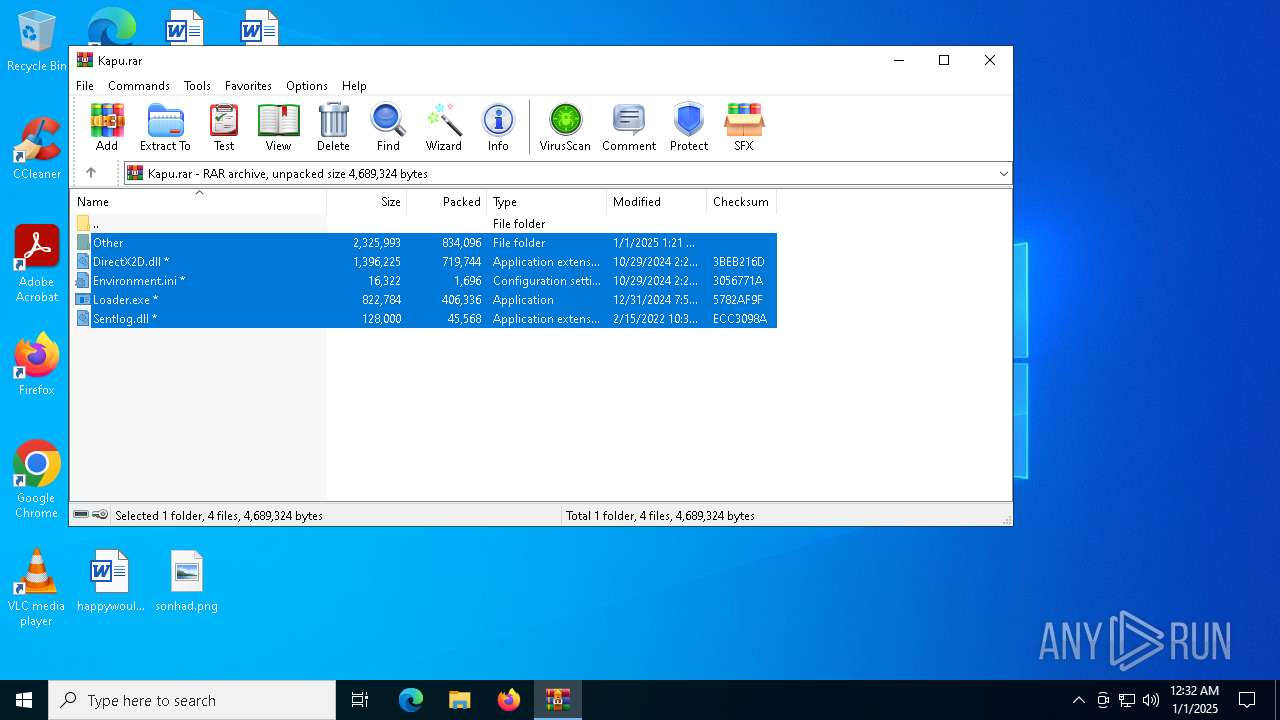
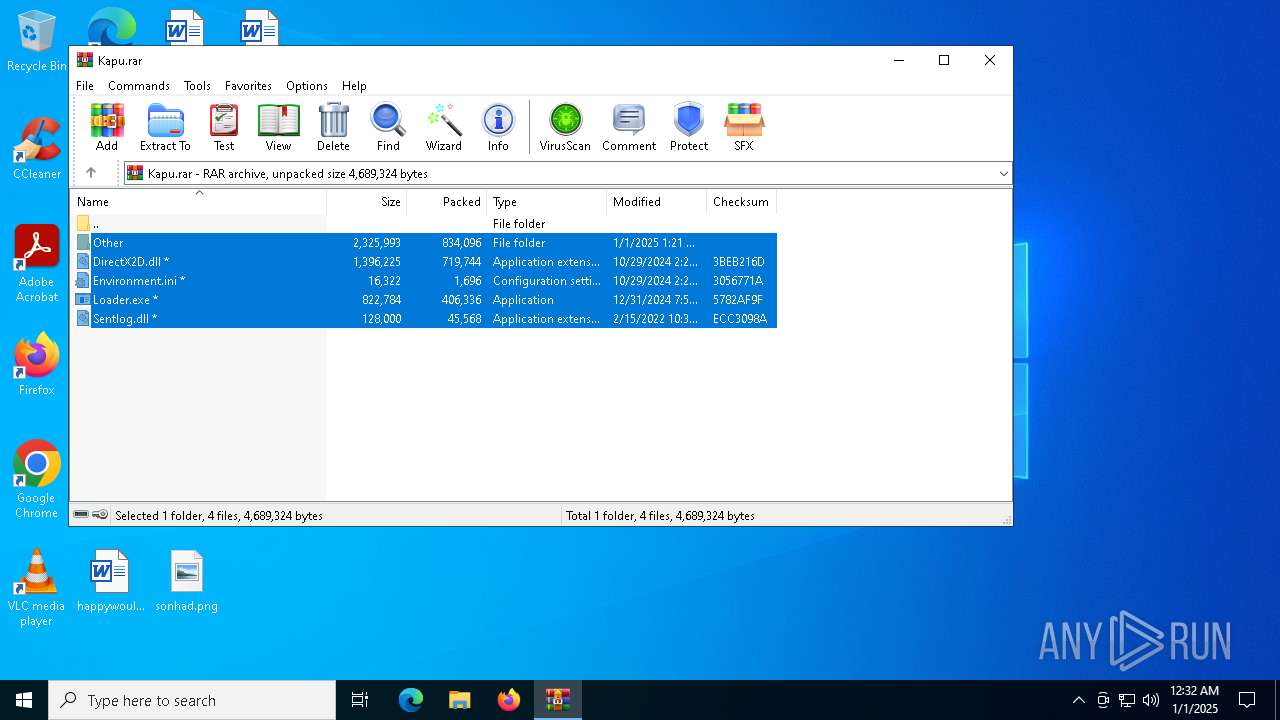
| File name: | Kapu.rar |
| Full analysis: | https://app.any.run/tasks/7751fe9a-ef92-4dd6-88ef-a24bbd684faf |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | January 01, 2025, 00:32:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 3E7D92344E8DB20BF412D2AF642DEE8E |
| SHA1: | F09A3909386DD8E487F6A762F5C6DCCEAF69C012 |
| SHA256: | A73669D3144B8CD37D13543E8188E41701A142D0EC953118C0CD921575ABFF88 |
| SSDEEP: | 98304:UUy4P5nWdUeEuVkaa6/70OiFlbFkH8HxO59WKShUg0AFyDa+IjsB7NeSRuCcacaZ:67R |
MALICIOUS
Connects to the CnC server
- svchost.exe (PID: 2192)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
- Loader.exe (PID: 7128)
LUMMA mutex has been found
- Loader.exe (PID: 7128)
Actions looks like stealing of personal data
- Loader.exe (PID: 7128)
Steals credentials from Web Browsers
- Loader.exe (PID: 7128)
LUMMA has been detected (YARA)
- Loader.exe (PID: 7128)
SUSPICIOUS
Application launched itself
- Loader.exe (PID: 7060)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2192)
- Loader.exe (PID: 7128)
INFO
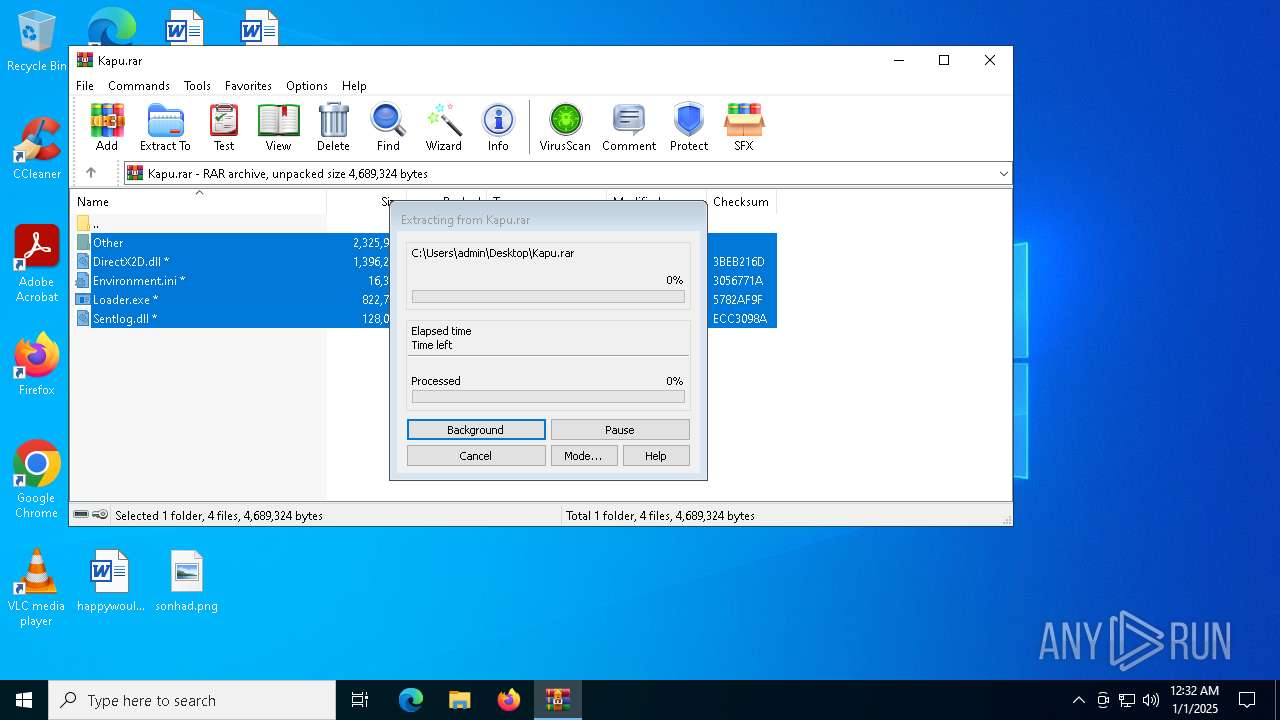
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6716)
The process uses the downloaded file
- WinRAR.exe (PID: 6716)
Checks supported languages
- Loader.exe (PID: 7060)
- Loader.exe (PID: 7128)
Manual execution by a user
- Loader.exe (PID: 7060)
Reads the computer name
- Loader.exe (PID: 7128)
Reads the software policy settings
- Loader.exe (PID: 7128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 95168 |
| UncompressedSize: | 252928 |
| OperatingSystem: | Win32 |
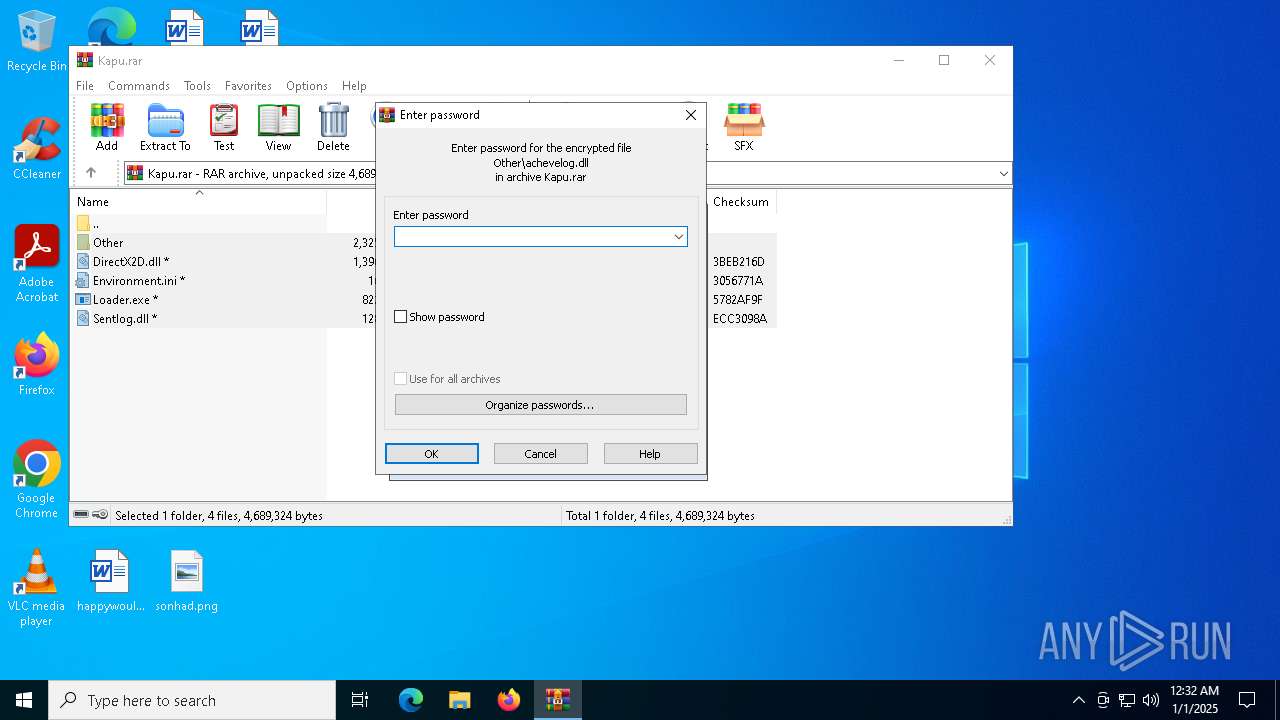
| ArchivedFileName: | Other/achevelog.dll |
Total processes
122
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6716 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Kapu.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7060 | "C:\Users\admin\Desktop\Loader.exe" | C:\Users\admin\Desktop\Loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7068 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7128 | "C:\Users\admin\Desktop\Loader.exe" | C:\Users\admin\Desktop\Loader.exe | Loader.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
1 839
Read events
1 830
Write events
9
Delete events
0
Modification events
| (PID) Process: | (6716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Kapu.rar | |||
| (PID) Process: | (6716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6716) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
Executable files
9
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6716 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6716.35476\Other\jascriptfortpatch.pdb | executable | |
MD5:916D32B899F1BC23B209648D007B99FD | SHA256:72CF291D4BAB0EDD08A9B07C6173E1E7AD1ABB7AB727FD7044BF6305D7515661 | |||
| 6716 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6716.35476\Other\Sentlog.dll | executable | |
MD5:181F3E3D0C509566283156816EB317CA | SHA256:DB0A4C4A21A1BA0937D1C22095C2B0702422EFD4C7A41AAA577608288A2E69FC | |||
| 6716 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6716.35476\Other\d2patch.dll | executable | |
MD5:9ED0CC60FAA1CA995F75DC8B4BF407C4 | SHA256:ACFDE5B1463C95832DD7757A0407D7B81584D1F2AA5175095CA88A47535B2557 | |||
| 6716 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6716.35476\Other\achevelog.dll | executable | |
MD5:319226C18DBC02D2AC4C0DD9DC116D53 | SHA256:EB9B84A3DF6AE51759544BA04224A4F91454B8A81D54B37C846A4216BC72C15E | |||
| 6716 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6716.35476\DirectX2D.dll | executable | |
MD5:00B3E7DFC26FD3547082EB20F4EEC53B | SHA256:494D98A99AB8FCE6D615BB48D4D014640DA2E208002BA647E226F09B8678AFA3 | |||
| 6716 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6716.35476\Sentlog.dll | executable | |
MD5:181F3E3D0C509566283156816EB317CA | SHA256:DB0A4C4A21A1BA0937D1C22095C2B0702422EFD4C7A41AAA577608288A2E69FC | |||
| 6716 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6716.35476\Other\Environment.ini | xml | |
MD5:E7DD4E065AF3CD26FED13BA93F37C015 | SHA256:000628E5C2BD0E1BAA6DA1827E506BC7359CA68B18BD6D50B0ABD5D84000ED5B | |||
| 6716 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6716.35476\Other\patch.dll | executable | |
MD5:3169B48A9A2086E53C4493C03579902C | SHA256:E63EDE4EBD7E64493EAD8E91F475238FF7DEC17EB403798E4BA27D592A9757A8 | |||
| 6716 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6716.35476\Environment.ini | xml | |
MD5:0521921D1B973D325896A215F059E864 | SHA256:E41FDF321EC9B1287521481E8A277EB6768C639C6C142880970B5ECCA2A1FF00 | |||
| 6716 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6716.35476\Loader.exe | executable | |
MD5:0792FCE4557CAE0687A02E5E41BE587A | SHA256:6E7B661FB3B6610BC026DD050824E7FAAF3BD3B5FA0B168D941858FC694BA871 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
37
DNS requests
19
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2136 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6408 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2136 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5732 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 104.126.37.176:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
fancywaxxers.shop |
| malicious |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (fancywaxxers .shop) |
7128 | Loader.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (fancywaxxers .shop in TLS SNI) |
7128 | Loader.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
7128 | Loader.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (fancywaxxers .shop in TLS SNI) |
7128 | Loader.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (fancywaxxers .shop in TLS SNI) |
7128 | Loader.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (fancywaxxers .shop in TLS SNI) |
7128 | Loader.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (fancywaxxers .shop in TLS SNI) |
7128 | Loader.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (fancywaxxers .shop in TLS SNI) |