| File name: | RuntimeBroker.exe |
| Full analysis: | https://app.any.run/tasks/2b32b256-e400-40b0-a763-f4e8e7a1c151 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | March 13, 2025, 18:59:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | FC12A2E6F37C028C1B3E8A4EDF24CA99 |
| SHA1: | E13E7C83047EED30602F5EE2D29C8360090C4C23 |
| SHA256: | A6EB97732429A680D777C44C010B851064D89500764DFB50AF2CEAB258B4CB18 |
| SSDEEP: | 1536:dmf4cHdp3b2ryAgwCBewIfyhRPo9aGsY982ro7IGk:dmf4cHLb2ryAgwCBbXMaGsY9WI |
MALICIOUS
ASYNCRAT has been detected (YARA)
- RuntimeBroker.exe (PID: 2108)
- $77Runtime Broker.exe (PID: 6228)
Uses Task Scheduler to run other applications
- $77Runtime Broker.exe (PID: 3884)
- $77Runtime Broker.exe (PID: 6228)
Changes the autorun value in the registry
- RuntimeBroker.exe (PID: 2108)
Adds extension to the Windows Defender exclusion list
- $77Runtime Broker.exe (PID: 6228)
SUSPICIOUS
Reads the date of Windows installation
- RuntimeBroker.exe (PID: 2108)
- $77Runtime Broker.exe (PID: 3884)
- $77Runtime Broker.exe (PID: 6228)
Reads security settings of Internet Explorer
- RuntimeBroker.exe (PID: 2108)
- $77Runtime Broker.exe (PID: 3884)
- $77Runtime Broker.exe (PID: 6228)
Executable content was dropped or overwritten
- RuntimeBroker.exe (PID: 2108)
Uses ATTRIB.EXE to modify file attributes
- RuntimeBroker.exe (PID: 2108)
Lists all scheduled tasks
- schtasks.exe (PID: 6712)
- schtasks.exe (PID: 5260)
- schtasks.exe (PID: 4380)
Starts CMD.EXE for commands execution
- RuntimeBroker.exe (PID: 2108)
- $77Runtime Broker.exe (PID: 3884)
Executing commands from a ".bat" file
- RuntimeBroker.exe (PID: 2108)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 4300)
The executable file from the user directory is run by the CMD process
- $77Runtime Broker.exe (PID: 3884)
- $77Runtime Broker.exe (PID: 6228)
Executes as Windows Service
- VSSVC.exe (PID: 4692)
Starts POWERSHELL.EXE for commands execution
- $77Runtime Broker.exe (PID: 6228)
Script adds exclusion extension to Windows Defender
- $77Runtime Broker.exe (PID: 6228)
Connects to unusual port
- $77Runtime Broker.exe (PID: 6228)
INFO
Reads the machine GUID from the registry
- RuntimeBroker.exe (PID: 2108)
- $77Runtime Broker.exe (PID: 3884)
- $77Runtime Broker.exe (PID: 6228)
Reads the computer name
- RuntimeBroker.exe (PID: 2108)
- $77Runtime Broker.exe (PID: 3884)
- $77Runtime Broker.exe (PID: 6228)
Creates files or folders in the user directory
- RuntimeBroker.exe (PID: 2108)
Checks proxy server information
- RuntimeBroker.exe (PID: 2108)
- $77Runtime Broker.exe (PID: 3884)
- $77Runtime Broker.exe (PID: 6228)
- slui.exe (PID: 348)
Checks supported languages
- RuntimeBroker.exe (PID: 2108)
- $77Runtime Broker.exe (PID: 3884)
- $77Runtime Broker.exe (PID: 6228)
Process checks computer location settings
- RuntimeBroker.exe (PID: 2108)
- $77Runtime Broker.exe (PID: 3884)
- $77Runtime Broker.exe (PID: 6228)
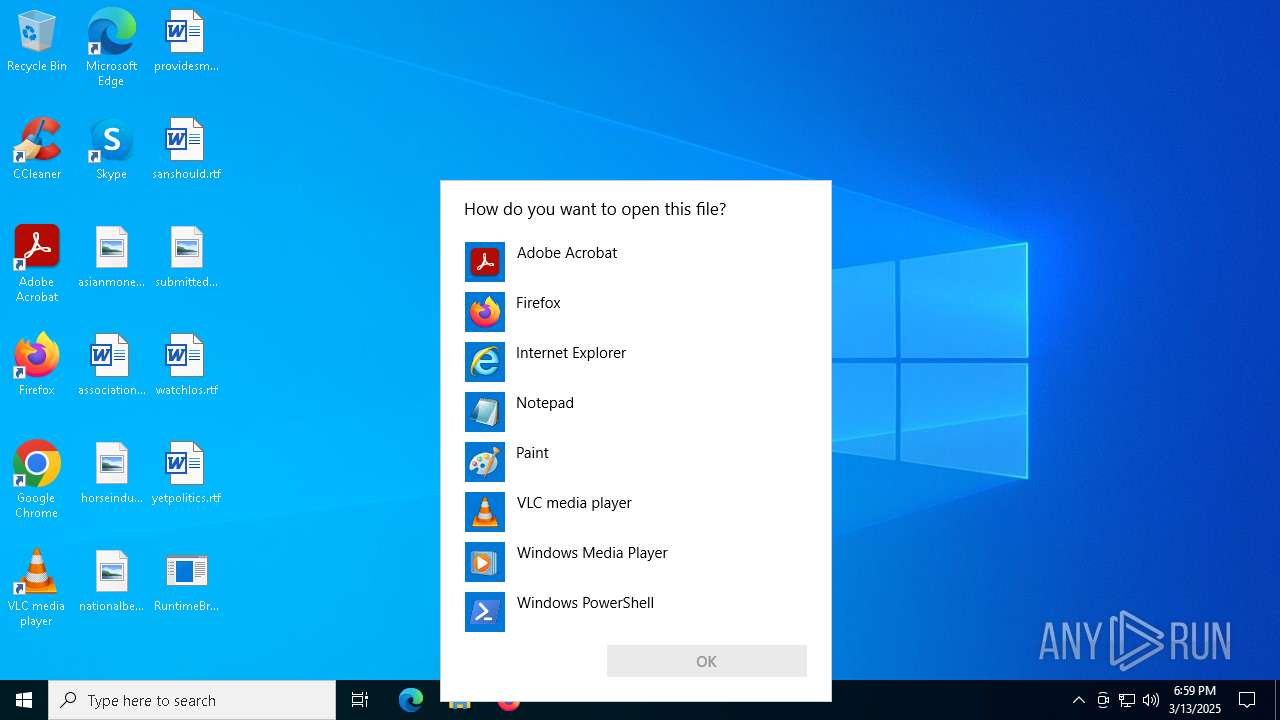
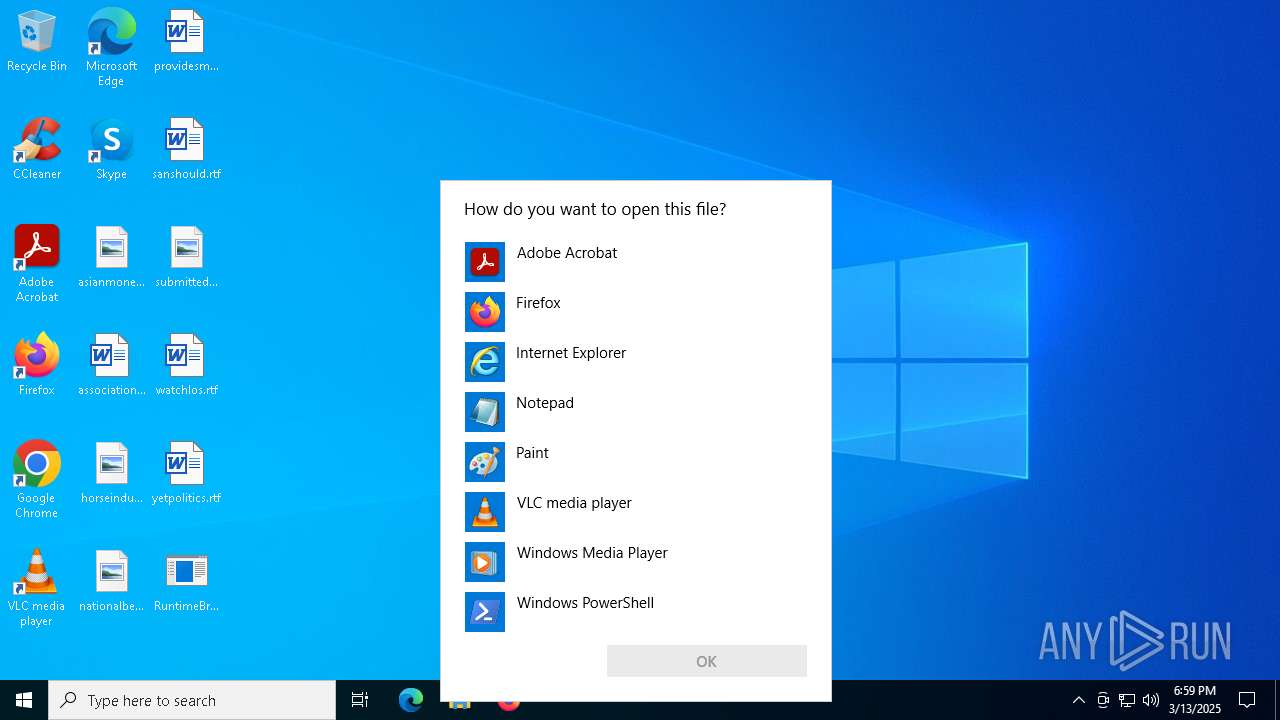
Manual execution by a user
- OpenWith.exe (PID: 4268)
- OpenWith.exe (PID: 2568)
- OpenWith.exe (PID: 5156)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 4268)
- OpenWith.exe (PID: 2568)
- OpenWith.exe (PID: 5156)
Autorun file from Task Scheduler
- $77Runtime Broker.exe (PID: 3884)
- $77Runtime Broker.exe (PID: 6228)
Create files in a temporary directory
- RuntimeBroker.exe (PID: 2108)
Autorun file from Registry key
- RuntimeBroker.exe (PID: 2108)
Reads Environment values
- $77Runtime Broker.exe (PID: 6228)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6032)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6032)
Reads the software policy settings
- slui.exe (PID: 348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:02:27 18:06:37+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 11 |
| CodeSize: | 42496 |
| InitializedDataSize: | 1536 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | RuntimeBroker.exe |
| LegalCopyright: | |
| OriginalFileName: | RuntimeBroker.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
155
Monitored processes
33
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1240 | "C:\Windows\System32\schtasks.exe" /create /sc hourly /mo 1 /tn "Runtime Broker_Task-HOURLY-01" /tr "%MyFile%" /st 00:00 | C:\Windows\System32\schtasks.exe | — | $77Runtime Broker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "schtasks.exe" /Create /SC ONCE /TN "$77Runtime Broker.exe" /TR "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\SysTemp64\$77Runtime Broker.exe \"\$77Runtime Broker.exe\" /AsAdmin" /ST 00:01 /IT /F /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | $77Runtime Broker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | "C:\Users\admin\Desktop\RuntimeBroker.exe" | C:\Users\admin\Desktop\RuntimeBroker.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2568 | "C:\WINDOWS\System32\OpenWith.exe" ""C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\SysTemp64\$77Runtime Broker.exe \"" | C:\Windows\System32\OpenWith.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 2147943623 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | "C:\Windows\System32\attrib.exe" +s +h "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\SysTemp64" | C:\Windows\System32\attrib.exe | — | RuntimeBroker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2984 | "C:\Windows\System32\cmd.exe" /k START "" "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\SysTemp64\$77Runtime Broker.exe" & EXIT | C:\Windows\System32\cmd.exe | $77Runtime Broker.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3100 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | attrib.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 094
Read events
14 049
Write events
45
Delete events
0
Modification events
| (PID) Process: | (2108) RuntimeBroker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | (default) |
Value: "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\SysTemp64\$77Runtime Broker.exe" | |||
| (PID) Process: | (5256) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000068A3FD194A94DB018814000000120000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5256) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000034B9421A4A94DB018814000000120000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5256) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000034B9421A4A94DB018814000000120000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5256) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000221D451A4A94DB018814000000120000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6228) $77Runtime Broker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000CBE3491A4A94DB01541800002C080000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6228) $77Runtime Broker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000065474C1A4A94DB01541800002C080000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6228) $77Runtime Broker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000065474C1A4A94DB01541800002C080000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6228) $77Runtime Broker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000001EAB4E1A4A94DB01541800002C080000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6228) $77Runtime Broker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000BDACE91A4A94DB01541800002C080000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
1
Suspicious files
1
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6032 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_v1amrjxo.l1u.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6032 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_adaq4idf.swi.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2108 | RuntimeBroker.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\SysTemp64\$77Runtime Broker.exe | executable | |
MD5:FC12A2E6F37C028C1B3E8A4EDF24CA99 | SHA256:A6EB97732429A680D777C44C010B851064D89500764DFB50AF2CEAB258B4CB18 | |||
| 6032 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:14B23A95F0C712031D494D522771414C | SHA256:74CD3BE7BDB551039591FB641221C5E7AF5ED31A957BD44C3B76FEED9D575E3E | |||
| 2108 | RuntimeBroker.exe | C:\Users\admin\AppData\Local\Temp\tmp18F4.tmp.bat | text | |
MD5:460DEA9A75222F5C4BB2A9C69D1AF1D3 | SHA256:49039F110C2BD25663CC0DCBDAB30A6E8F33496601F0ABAE6587B2BE2AE915CD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
158
DNS requests
4
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6228 | $77Runtime Broker.exe | 147.185.221.25:17094 | if-eventually.gl.at.ply.gg | PLAYIT-GG | US | malicious |
4652 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
348 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
if-eventually.gl.at.ply.gg |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |