| File name: | file |
| Full analysis: | https://app.any.run/tasks/9a7bb6fb-6d3b-447b-9531-e2de083a63b1 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | December 03, 2023, 16:41:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2A1B6A27FF3D806C85140A9266CB1F23 |
| SHA1: | 495228F84617BF2C8BA2BC241B65FD70CB3F1D6A |
| SHA256: | A6DFEDDD45D8B0DB976AE4053860BB2AEECBE5F61188D6FAF3214A41B1875784 |
| SSDEEP: | 98304:zzshzF7IFPBoaHnyhLbchZkDYaEYalYaqYaLYa9YaTYaTYaTYaTYaWCAc6Xq4JAF:i0V67tDDDD5foB |
MALICIOUS
LUMMA has been detected (YARA)
- file.exe (PID: 2208)
- MSBuild.exe (PID: 2844)
LUMMA has been detected (SURICATA)
- MSBuild.exe (PID: 2844)
Connects to the CnC server
- MSBuild.exe (PID: 2844)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 2844)
SUSPICIOUS
Reads the Internet Settings
- file.exe (PID: 2208)
Reads browser cookies
- MSBuild.exe (PID: 2844)
Searches for installed software
- MSBuild.exe (PID: 2844)
INFO
Reads the machine GUID from the registry
- file.exe (PID: 2208)
Checks supported languages
- file.exe (PID: 2208)
- MSBuild.exe (PID: 2844)
Reads the computer name
- file.exe (PID: 2208)
- MSBuild.exe (PID: 2844)
Checks proxy server information
- file.exe (PID: 2208)
Reads Environment values
- file.exe (PID: 2208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2099:09:03 15:44:07+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 5848064 |
| InitializedDataSize: | 5850112 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x595ba2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.5.1 |
| ProductVersionNumber: | 2.1.5.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
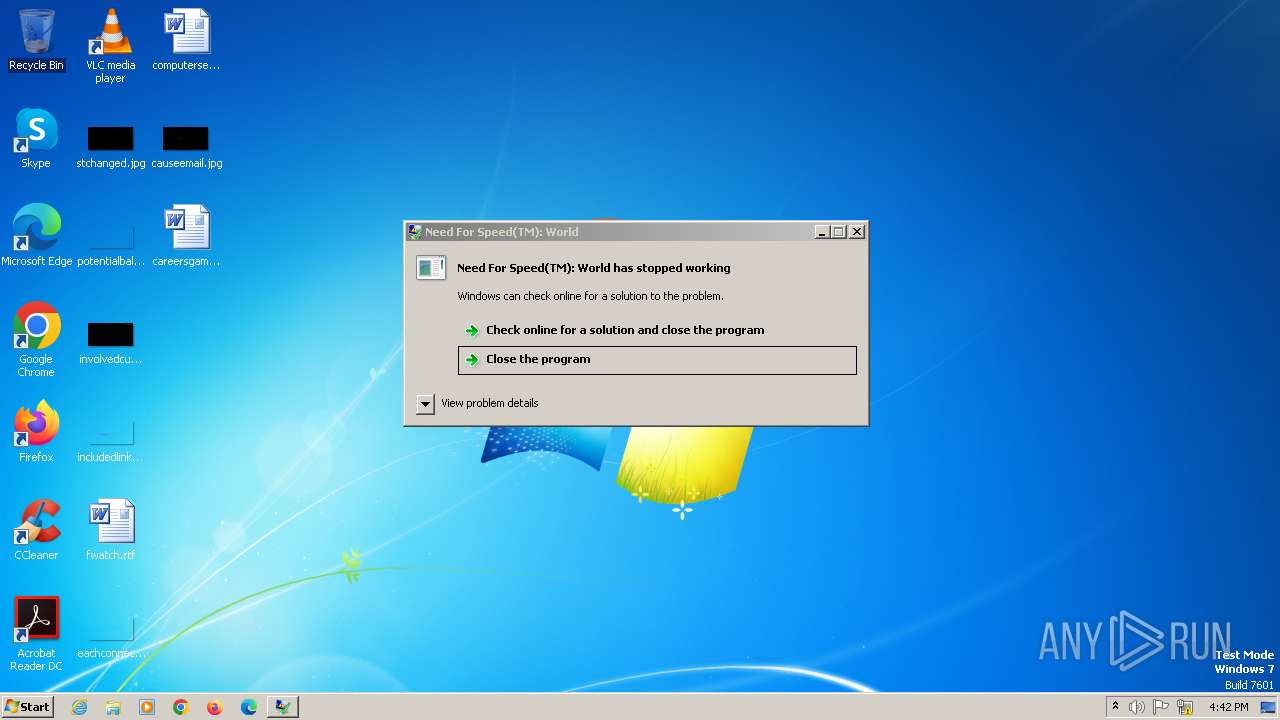
| Comments: | Need For Speed(TM): World |
| CompanyName: | Need For Speed(TM): World |
| FileDescription: | Need For Speed(TM): World |
| FileVersion: | 2.1.5.0001 |
| InternalName: | WolrCfuhsd.exe |
| LegalCopyright: | © Need For Speed(TM): World |
| LegalTrademarks: | - |
| OriginalFileName: | WolrCfuhsd.exe |
| ProductName: | SBRW Launcher |
| ProductVersion: | 2.1.5.0001 |
| AssemblyVersion: | 2.1.5.1 |
Total processes
40
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2208 | "C:\Users\admin\AppData\Local\Temp\file.exe" | C:\Users\admin\AppData\Local\Temp\file.exe | explorer.exe | ||||||||||||
User: admin Company: Need For Speed(TM): World Integrity Level: MEDIUM Description: Need For Speed(TM): World Exit code: 0 Version: 2.1.5.0001 Modules
| |||||||||||||||
| 2844 | title | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | file.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
Total events
2 101
Read events
2 101
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
43
DNS requests
1
Threats
47
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2844 | MSBuild.exe | POST | 200 | 104.21.14.160:80 | http://payfrecklematurei.pw/api | unknown | text | 16.5 Kb | unknown |
2844 | MSBuild.exe | POST | 200 | 104.21.14.160:80 | http://payfrecklematurei.pw/api | unknown | text | 2 b | unknown |
2844 | MSBuild.exe | POST | 200 | 104.21.14.160:80 | http://payfrecklematurei.pw/api | unknown | text | 21 b | unknown |
2844 | MSBuild.exe | POST | 200 | 104.21.14.160:80 | http://payfrecklematurei.pw/api | unknown | text | 21 b | unknown |
2844 | MSBuild.exe | POST | 200 | 104.21.14.160:80 | http://payfrecklematurei.pw/api | unknown | text | 21 b | unknown |
2844 | MSBuild.exe | POST | 200 | 104.21.14.160:80 | http://payfrecklematurei.pw/api | unknown | text | 21 b | unknown |
2844 | MSBuild.exe | POST | 200 | 104.21.14.160:80 | http://payfrecklematurei.pw/api | unknown | text | 21 b | unknown |
2844 | MSBuild.exe | POST | 200 | 104.21.14.160:80 | http://payfrecklematurei.pw/api | unknown | text | 21 b | unknown |
2844 | MSBuild.exe | POST | 200 | 104.21.14.160:80 | http://payfrecklematurei.pw/api | unknown | text | 21 b | unknown |
2844 | MSBuild.exe | POST | 200 | 104.21.14.160:80 | http://payfrecklematurei.pw/api | unknown | text | 21 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2844 | MSBuild.exe | 104.21.14.160:80 | payfrecklematurei.pw | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
payfrecklematurei.pw |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
324 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
2844 | MSBuild.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
2844 | MSBuild.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
2844 | MSBuild.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Check-In |
2844 | MSBuild.exe | Malware Command and Control Activity Detected | ET MALWARE [ANY.RUN] Win32/Lumma Stealer Check-In |
2844 | MSBuild.exe | Malware Command and Control Activity Detected | ET MALWARE [ANY.RUN] Win32/Lumma Stealer Exfiltration |
2844 | MSBuild.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
2844 | MSBuild.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Exfiltration |
2844 | MSBuild.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
2844 | MSBuild.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
2 ETPRO signatures available at the full report