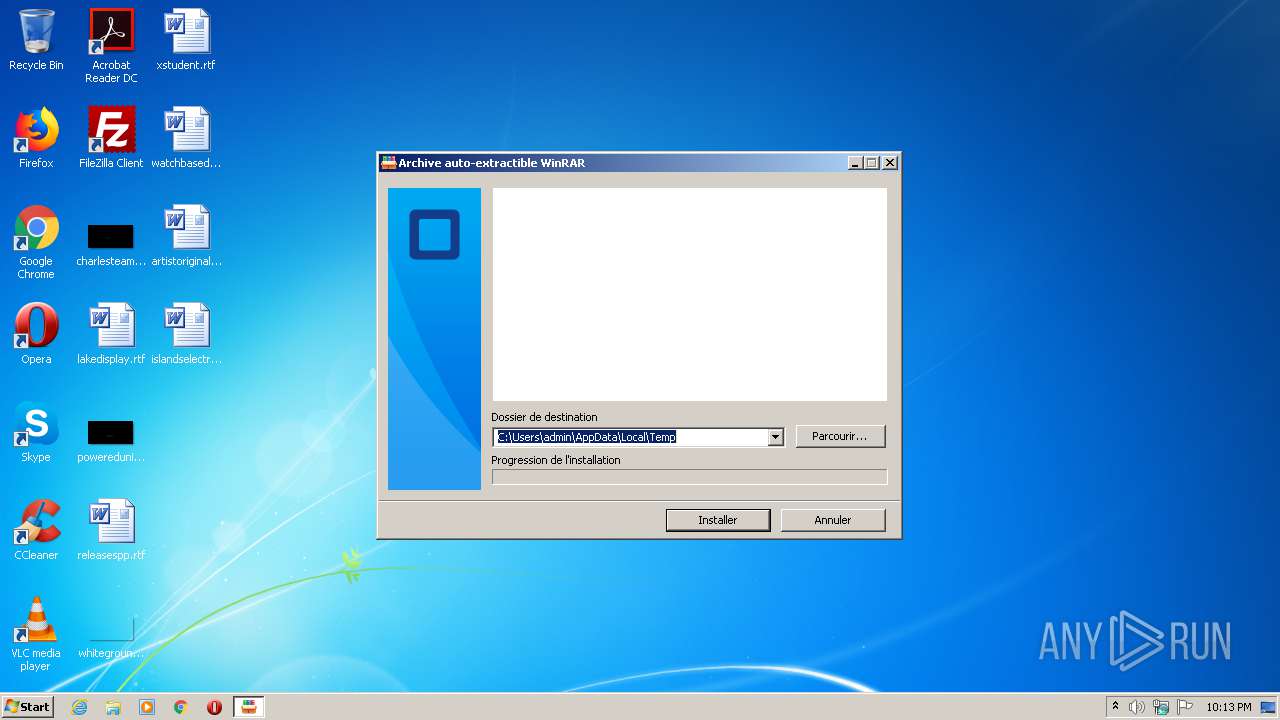
| File name: | OTC_ADDON.sfx.exe |
| Full analysis: | https://app.any.run/tasks/79e2c73c-0140-486f-bc5c-9106a7141e34 |
| Verdict: | Malicious activity |
| Threats: | DarkComet RAT is a malicious program designed to remotely control or administer a victim's computer, steal private data and spy on the victim. |
| Analysis date: | August 08, 2020, 21:12:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CE48DF20FB74C7B4D2AAC280E7595498 |
| SHA1: | 696217B71807D96FB371CFF9B6E462CA8E8CD36C |
| SHA256: | A6DDDECBE61E707C1843342D25EE8B8AF3A5634A7792AC94D13811B94487D63D |
| SSDEEP: | 12288:5hqxSLo5C1Ps4XhitX+t498Ws2veW7j6zy0YfPv95:5HLmCiIhiXRsseW7/Hz |
MALICIOUS
Changes the autorun value in the registry
- OTC_ADDON.exe (PID: 2152)
Changes the login/logoff helper path in the registry
- OTC_ADDON.exe (PID: 2152)
Application was dropped or rewritten from another process
- OTC_ADDON.exe (PID: 2152)
- msdcsc.exe (PID: 2728)
DARKCOMET was detected
- msdcsc.exe (PID: 2728)
SUSPICIOUS
Reads internet explorer settings
- OTC_ADDON.sfx.exe (PID: 1912)
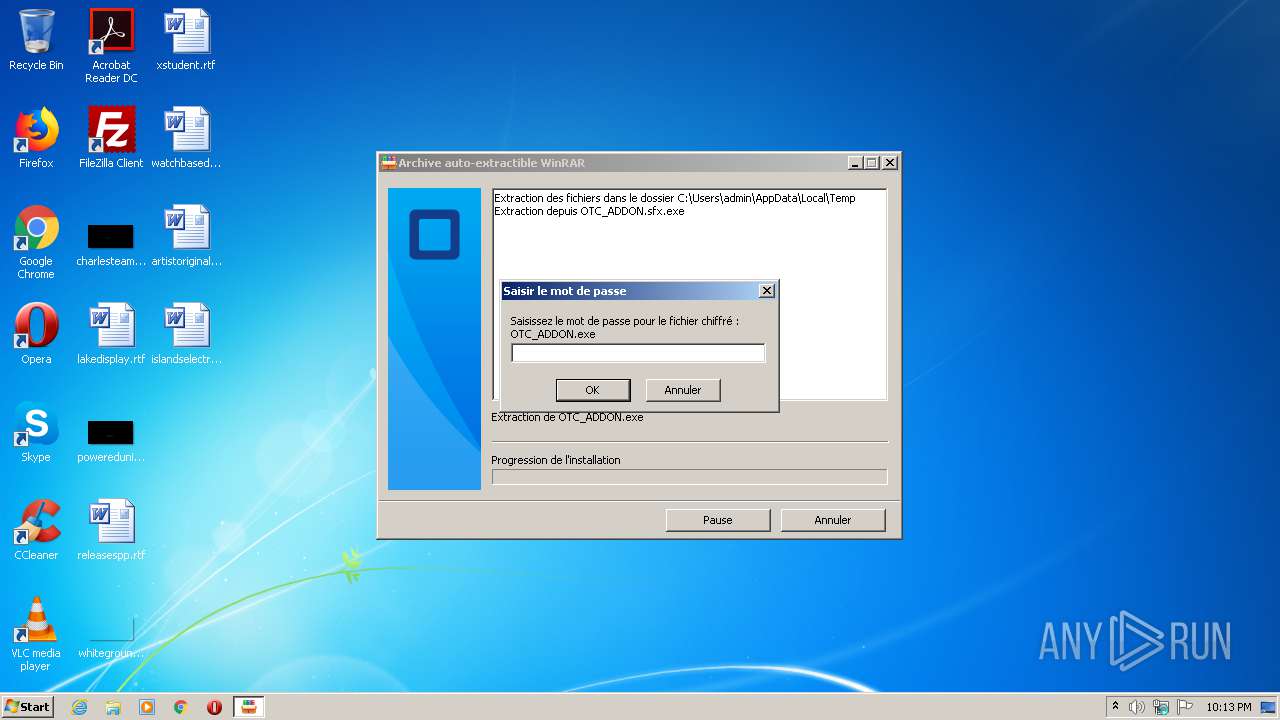
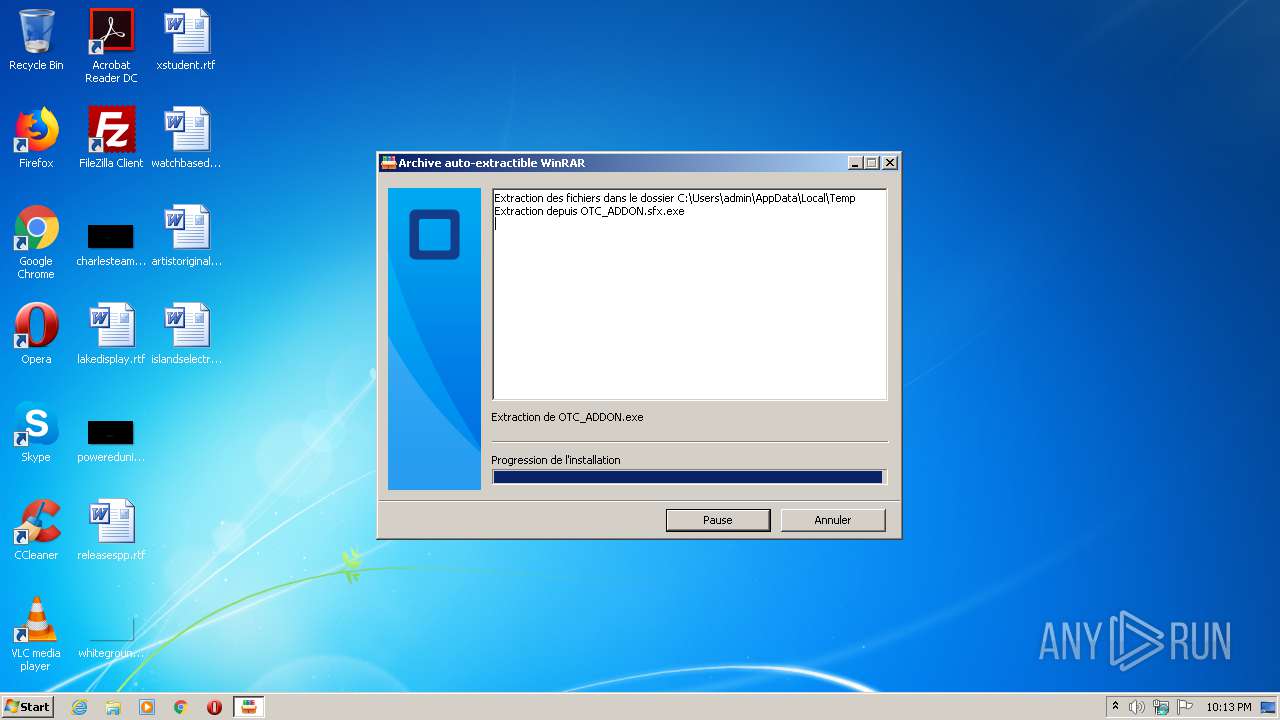
Executable content was dropped or overwritten
- OTC_ADDON.sfx.exe (PID: 1912)
- OTC_ADDON.exe (PID: 2152)
Starts CMD.EXE for commands execution
- OTC_ADDON.exe (PID: 2152)
Reads Internet Cache Settings
- OTC_ADDON.sfx.exe (PID: 1912)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 1672)
Starts itself from another location
- OTC_ADDON.exe (PID: 2152)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:06:25 12:38:24+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 200704 |
| InitializedDataSize: | 254976 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ea80 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jun-2020 10:38:24 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 25-Jun-2020 10:38:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00030F2A | 0x00031000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70442 |
.rdata | 0x00032000 | 0x0000A5F2 | 0x0000A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.2593 |
.data | 0x0003D000 | 0x00023720 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.70568 |
.didat | 0x00061000 | 0x00000188 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29951 |
.rsrc | 0x00062000 | 0x0000DFD0 | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.63693 |
.reloc | 0x00070000 | 0x00002264 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55675 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.10026 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 5.25868 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.02609 | 1128 | UNKNOWN | English - United States | RT_ICON |
5 | 5.18109 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.04307 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.11236 | 440 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
43
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1672 | "C:\Windows\System32\cmd.exe" /k attrib "C:\Users\admin\AppData\Local\Temp" +s +h | C:\Windows\System32\cmd.exe | — | OTC_ADDON.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1912 | "C:\Users\admin\AppData\Local\Temp\OTC_ADDON.sfx.exe" | C:\Users\admin\AppData\Local\Temp\OTC_ADDON.sfx.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2152 | "C:\Users\admin\AppData\Local\Temp\OTC_ADDON.exe" | C:\Users\admin\AppData\Local\Temp\OTC_ADDON.exe | OTC_ADDON.sfx.exe | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Remote Service Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2188 | notepad | C:\Windows\system32\notepad.exe | — | msdcsc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2504 | attrib "C:\Users\admin\AppData\Local\Temp" +s +h | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
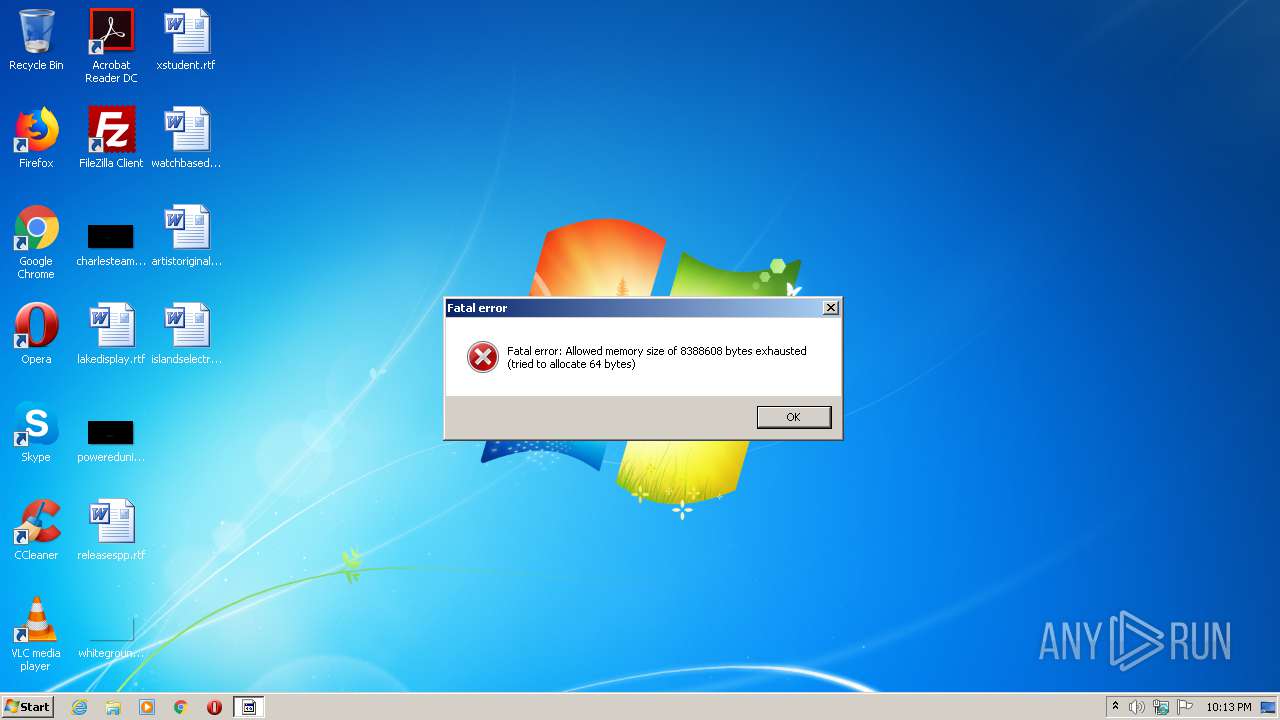
| 2728 | "C:\Users\admin\Documents\MSDCSC\msdcsc.exe" | C:\Users\admin\Documents\MSDCSC\msdcsc.exe | OTC_ADDON.exe | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: MEDIUM Description: Remote Service Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
1 000
Read events
930
Write events
70
Delete events
0
Modification events
| (PID) Process: | (1912) OTC_ADDON.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1912) OTC_ADDON.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1912) OTC_ADDON.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1912) OTC_ADDON.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1912) OTC_ADDON.sfx.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2152) OTC_ADDON.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicroUpdate |
Value: C:\Users\admin\Documents\MSDCSC\msdcsc.exe | |||
| (PID) Process: | (2152) OTC_ADDON.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | UserInit |
Value: C:\Windows\system32\userinit.exe,C:\Users\admin\Documents\MSDCSC\msdcsc.exe | |||
| (PID) Process: | (2152) OTC_ADDON.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2152) OTC_ADDON.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2152) OTC_ADDON.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1912 | OTC_ADDON.sfx.exe | C:\Users\admin\AppData\Local\Temp\OTC_ADDON.exe | executable | |
MD5:— | SHA256:— | |||
| 2152 | OTC_ADDON.exe | C:\Users\admin\Documents\MSDCSC\msdcsc.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
27
DNS requests
5
Threats
78
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2728 | msdcsc.exe | 90.66.196.28:1604 | xaurap.ddns.net | Orange | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xaurap.ddns.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
2728 | msdcsc.exe | A Network Trojan was detected | MALWARE [PTsecurity] DarkComet-RAT Inbound connection |
2728 | msdcsc.exe | A Network Trojan was detected | MALWARE [PTsecurity] DarkComet-RAT Inbound connection |
2728 | msdcsc.exe | A Network Trojan was detected | MALWARE [PTsecurity] DarkComet-RAT Inbound connection |
2728 | msdcsc.exe | A Network Trojan was detected | MALWARE [PTsecurity] DarkComet-RAT Inbound connection |
2728 | msdcsc.exe | A Network Trojan was detected | MALWARE [PTsecurity] DarkComet-RAT Inbound connection |
2728 | msdcsc.exe | A Network Trojan was detected | MALWARE [PTsecurity] DarkComet-RAT Inbound connection |
2728 | msdcsc.exe | A Network Trojan was detected | MALWARE [PTsecurity] DarkComet-RAT Inbound connection |
1048 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
2728 | msdcsc.exe | A Network Trojan was detected | MALWARE [PTsecurity] DarkComet-RAT Inbound connection |
37 ETPRO signatures available at the full report