| File name: | Binder 2.0.exe |
| Full analysis: | https://app.any.run/tasks/90fad68c-fe7e-4a61-afa8-d4dba4c8bc65 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | August 19, 2024, 17:01:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | E61597F913AFCD1BE8147ADD84B63131 |
| SHA1: | F59C1D2712CC35992DAA010B70CDF9803D548298 |
| SHA256: | A6C08DFACF4CA09C66184AD3E609AC60C9758F78416731267E57918043099498 |
| SSDEEP: | 98304:rzuNxKB7goIS3AbcksWvMYVc0G8MztJaLBjPF243G/wdjJ+WrMK2+ZbRjwNwnlMC:56Io+hgwsn2ErOKrT8mz |
MALICIOUS
NjRAT is detected
- Microsoft Defender.exe (PID: 3464)
- Windows Updatet.exe (PID: 3280)
- Server.exe (PID: 2948)
ASYNCRAT has been detected (MUTEX)
- Microseft.exe (PID: 1600)
- Realtek HD Audio Uiversal Service.exe (PID: 3120)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 3756)
REVENGERAT has been detected (YARA)
- Google Chrome.exe (PID: 3460)
Changes the autorun value in the registry
- Windows Updatet.exe (PID: 3280)
Create files in the Startup directory
- Windows Updatet.exe (PID: 3280)
Uses Task Scheduler to run other applications
- Windows Updatet.exe (PID: 3280)
SUSPICIOUS
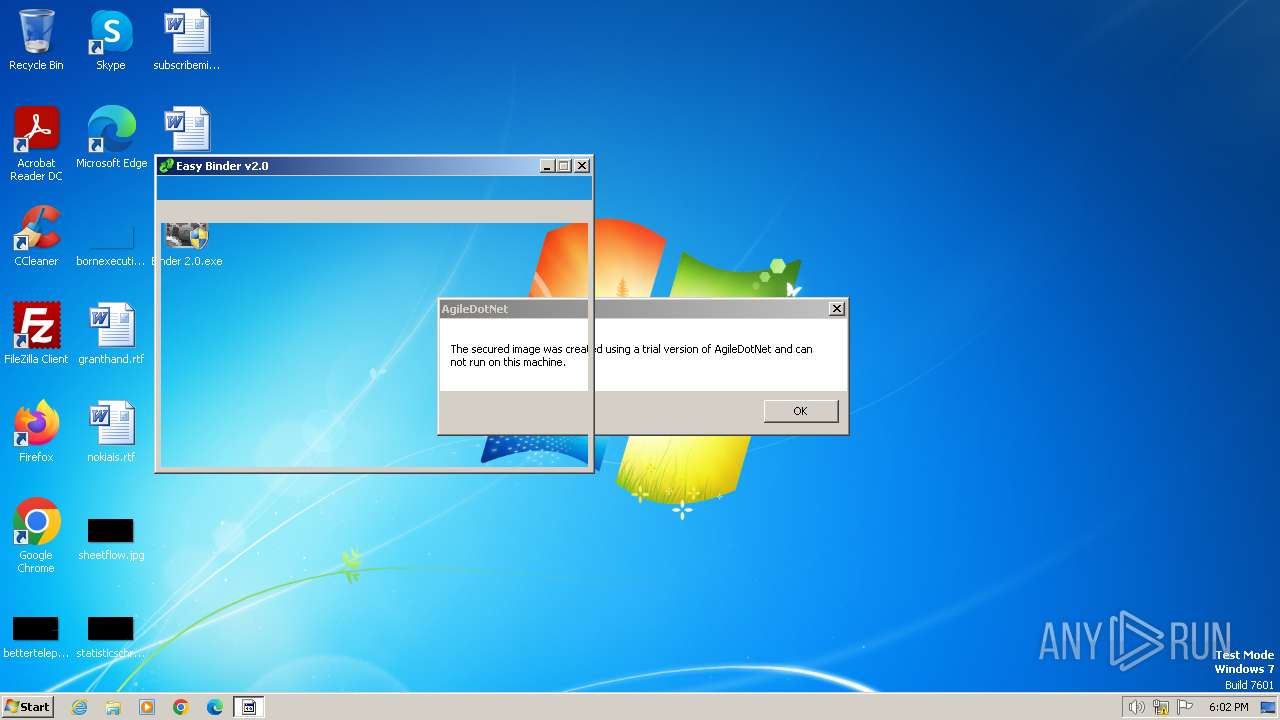
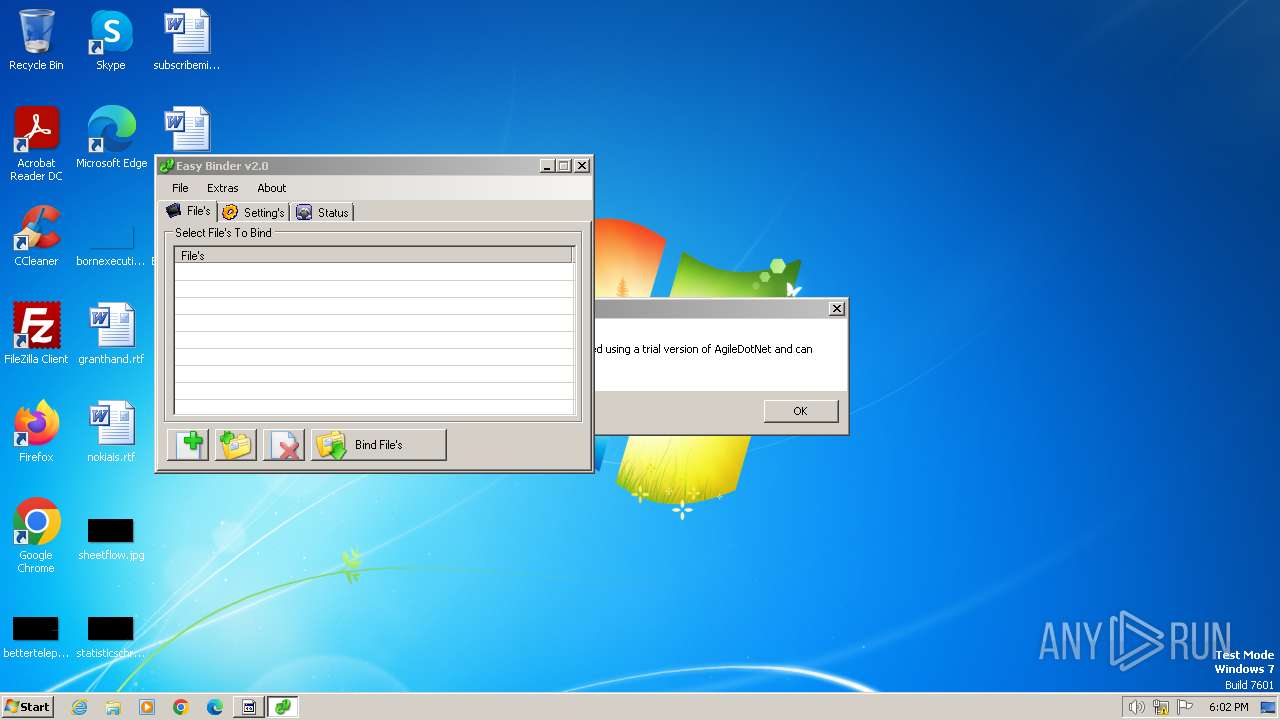
Executable content was dropped or overwritten
- Binder 2.0.exe (PID: 3644)
- Microsoft.exe (PID: 2560)
- Easy Binder.exe (PID: 3376)
- temp.exe (PID: 3932)
- Microseft.exe (PID: 1600)
- Microsoft Defender.exe (PID: 3464)
- Windows Updatet.exe (PID: 3280)
- Google Chrome.exe (PID: 3460)
Starts a Microsoft application from unusual location
- Microseft.exe (PID: 1600)
- Microsoft.exe (PID: 2560)
Process drops legitimate windows executable
- Binder 2.0.exe (PID: 3644)
- Microseft.exe (PID: 1600)
Reads security settings of Internet Explorer
- Binder 2.0.exe (PID: 3644)
- Microsoft.exe (PID: 2560)
- Easy Binder.exe (PID: 3376)
- Microseft.exe (PID: 1600)
- Microsoft Defender.exe (PID: 3464)
- Google Chrome.exe (PID: 3460)
Drops the executable file immediately after the start
- Binder 2.0.exe (PID: 3644)
- Microsoft.exe (PID: 2560)
- Easy Binder.exe (PID: 3376)
- temp.exe (PID: 3932)
- Microseft.exe (PID: 1600)
- Microsoft Defender.exe (PID: 3464)
- Windows Updatet.exe (PID: 3280)
- Google Chrome.exe (PID: 3460)
Reads the Internet Settings
- Binder 2.0.exe (PID: 3644)
- Easy Binder.exe (PID: 3376)
- Microseft.exe (PID: 1600)
- Microsoft Defender.exe (PID: 3464)
- Google Chrome.exe (PID: 3460)
Reads the BIOS version
- Microsoft.exe (PID: 2560)
Checks Windows Trust Settings
- Microsoft.exe (PID: 2560)
Reads settings of System Certificates
- Microsoft.exe (PID: 2560)
The process creates files with name similar to system file names
- temp.exe (PID: 3932)
Starts CMD.EXE for commands execution
- Microseft.exe (PID: 1600)
Executing commands from a ".bat" file
- Microseft.exe (PID: 1600)
Probably fake Windows Update file has been dropped
- Microsoft Defender.exe (PID: 3464)
- Windows Updatet.exe (PID: 3280)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1964)
Probably fake Windows Update
- Windows Updatet.exe (PID: 3280)
The executable file from the user directory is run by the CMD process
- Realtek HD Audio Uiversal Service.exe (PID: 3120)
Starts itself from another location
- Microsoft Defender.exe (PID: 3464)
- Google Chrome.exe (PID: 3460)
The process executes via Task Scheduler
- Server.exe (PID: 2948)
INFO
Create files in a temporary directory
- Microseft.exe (PID: 1600)
- Microsoft Defender.exe (PID: 3464)
- Binder 2.0.exe (PID: 3644)
- Google Chrome.exe (PID: 3460)
- Microsoft.exe (PID: 2560)
- Easy Binder.exe (PID: 3376)
- Realtek HD Audio Uiversal Service.exe (PID: 3120)
- Windows Updatet.exe (PID: 3280)
- Google Chrome.exe (PID: 3164)
- Server.exe (PID: 2948)
Checks supported languages
- Binder 2.0.exe (PID: 3644)
- Google Chrome.exe (PID: 3460)
- Easy Binder.exe (PID: 3376)
- Microsoft Defender.exe (PID: 3464)
- Microsoft.exe (PID: 2560)
- Microseft.exe (PID: 1600)
- temp.exe (PID: 3932)
- Windows Updatet.exe (PID: 3280)
- Realtek HD Audio Uiversal Service.exe (PID: 3120)
- wmpnscfg.exe (PID: 3212)
- Google Chrome.exe (PID: 3164)
- Server.exe (PID: 2948)
Reads the computer name
- Microsoft.exe (PID: 2560)
- Binder 2.0.exe (PID: 3644)
- Microseft.exe (PID: 1600)
- Easy Binder.exe (PID: 3376)
- Google Chrome.exe (PID: 3460)
- Microsoft Defender.exe (PID: 3464)
- Realtek HD Audio Uiversal Service.exe (PID: 3120)
- Windows Updatet.exe (PID: 3280)
- wmpnscfg.exe (PID: 3212)
- Google Chrome.exe (PID: 3164)
- Server.exe (PID: 2948)
Process checks whether UAC notifications are on
- Microsoft.exe (PID: 2560)
Reads the machine GUID from the registry
- Easy Binder.exe (PID: 3376)
- Microsoft.exe (PID: 2560)
- Google Chrome.exe (PID: 3460)
- Microseft.exe (PID: 1600)
- Microsoft Defender.exe (PID: 3464)
- Realtek HD Audio Uiversal Service.exe (PID: 3120)
- Windows Updatet.exe (PID: 3280)
- Google Chrome.exe (PID: 3164)
- Server.exe (PID: 2948)
Reads Environment values
- Easy Binder.exe (PID: 3376)
- Google Chrome.exe (PID: 3460)
- Windows Updatet.exe (PID: 3280)
- Google Chrome.exe (PID: 3164)
Reads the software policy settings
- Microsoft.exe (PID: 2560)
Creates files or folders in the user directory
- Microseft.exe (PID: 1600)
- Windows Updatet.exe (PID: 3280)
- Google Chrome.exe (PID: 3460)
Manual execution by a user
- wmpnscfg.exe (PID: 3212)
Themida protector has been detected
- Microsoft.exe (PID: 2560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:03:31 15:09:55+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 165376 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x315d |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
60
Monitored processes
19
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Users\admin\Desktop\Binder 2.0.exe" | C:\Users\admin\Desktop\Binder 2.0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1060 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1600 | "C:\Users\admin\AppData\Local\Temp\Microseft.exe" | C:\Users\admin\AppData\Local\Temp\Microseft.exe | Binder 2.0.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual Studio Ultimate 2012 Exit code: 0 Version: 11.0.50727.26 Modules
| |||||||||||||||
| 1964 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmp55AB.tmp.bat"" | C:\Windows\System32\cmd.exe | — | Microseft.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2560 | "C:\Users\admin\AppData\Local\Temp\Microsoft.exe" | C:\Users\admin\AppData\Local\Temp\Microsoft.exe | Binder 2.0.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual Studio Ultimate 2012 Version: 11.0.50727.26 Modules
| |||||||||||||||
| 2948 | C:\Users\admin\AppData\Local\Temp/Server.exe | C:\Users\admin\AppData\Local\Temp\Server.exe | taskeng.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3120 | "C:\Users\admin\AppData\Roaming\Realtek HD Audio Uiversal Service.exe" | C:\Users\admin\AppData\Roaming\Realtek HD Audio Uiversal Service.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual Studio Ultimate 2012 Version: 11.0.50727.26 Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\AppData\Roaming\Google Chrome.exe" | C:\Users\admin\AppData\Roaming\Google Chrome.exe | — | Google Chrome.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 3212 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3220 | schtasks /create /sc minute /mo 1 /tn Server /tr C:\Users\admin\AppData\Local\Temp/Server.exe | C:\Windows\System32\schtasks.exe | — | Windows Updatet.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
16 382
Read events
16 220
Write events
162
Delete events
0
Modification events
| (PID) Process: | (3644) Binder 2.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3644) Binder 2.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3644) Binder 2.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3644) Binder 2.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3464) Microsoft Defender.exe | Key: | HKEY_CURRENT_USER |
| Operation: | write | Name: | di |
Value: ! | |||
| (PID) Process: | (2560) Microsoft.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3376) Easy Binder.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3376) Easy Binder.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3376) Easy Binder.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3376) Easy Binder.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
45
Suspicious files
4
Text files
75
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3644 | Binder 2.0.exe | C:\Users\admin\AppData\Local\Temp\Microsoft.exe | executable | |
MD5:9A80533265D74CD0E5E181F4C3CC191E | SHA256:9BBBE2F31E73FA03794D2FF9AB3220BEE545EEFE10C21ABC26194F17EACA949D | |||
| 3644 | Binder 2.0.exe | C:\Users\admin\AppData\Local\Temp\Microseft.exe | executable | |
MD5:80D14F6DED3CC82EA75E8F9C2A91971E | SHA256:C9ABE2EF8E277B393E22FF4AB838A67262F1B62A48DF97CB0AFA5E905080EF59 | |||
| 3932 | temp.exe | C:\Windows\EasyBind\Contrib\Language files\Bulgarian.nlf | text | |
MD5:9179B1FF3AA76719C234A8DF574FD3FA | SHA256:3D224763D6F210FFEC24604810BDB8613584D253F829C35F3701BC4B90B0FCC3 | |||
| 3376 | Easy Binder.exe | C:\Users\admin\AppData\Local\Temp\temp.exe | executable | |
MD5:DF21207322BB1E8511A824107E852E16 | SHA256:5EAB7CBC6741AEE4FE457138732E8F07751CE360ABA25F973E41CF96A6B880B5 | |||
| 3644 | Binder 2.0.exe | C:\Users\admin\AppData\Local\Temp\Easy Binder.exe | executable | |
MD5:EFBC9F49DD2F2E1088CDCEC3CF35A41B | SHA256:CF28DE8089BC70759C9D524CBBAC2C3D46C4AED10AC57F622086E71032226295 | |||
| 3644 | Binder 2.0.exe | C:\Users\admin\AppData\Local\Temp\Microsoft Defender.exe | executable | |
MD5:CDCD29EEC42A89E08D5C01E3124DF45E | SHA256:B69034691E65E6D8D98F77064D117E955E0CD04D862EACCF56C5D52229447FAC | |||
| 3932 | temp.exe | C:\Windows\EasyBind\Contrib\Language files\Basque.nlf | text | |
MD5:58818A07E83C360E46B142CC5B7CBCF1 | SHA256:7CD4C534482A093C0A09487E3941ABFA915F3E1E57FD929265D93B2A8FD48F90 | |||
| 3932 | temp.exe | C:\Windows\EasyBind\Contrib\Language files\Breton.nlf | text | |
MD5:E896187D248EE1357CC00AE6BF9B5BA3 | SHA256:C60767A1E9AF91FC1AFDDE71187E0CF62F70BA4C57666D3174775EB531938044 | |||
| 3932 | temp.exe | C:\Windows\EasyBind\Contrib\Language files\Bosnian.nlf | text | |
MD5:0F05012A476852635E4CA84EA9A63B31 | SHA256:6D9DF735BF635D10DEBA274B57ED43AC22A3289A76964DA488EFB712C987DF2F | |||
| 3932 | temp.exe | C:\Windows\EasyBind\Contrib\Language files\Croatian.nlf | text | |
MD5:20CB7DFACE30D36391A29F9CD0C28457 | SHA256:09312C43CA52326D0E9F2863B6BF4BE14472AD44FC12EA14EB1A6B4A4FA9A61E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
10
DNS requests
6
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | whitelisted |
1060 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?11acddbe1ebd82b3 | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1372 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1372 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1372 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1060 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
xixi.3utilities.com |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.3utilities .com |