| download: | index.html |
| Full analysis: | https://app.any.run/tasks/e3b5ae33-9ace-4a65-a004-182078b56ce2 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | September 30, 2020, 09:46:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | FC517F02B65A40F27F236F5293A8CC94 |
| SHA1: | 107FE1D8EE9D9459E48C7C8BE9888A6405CF33D7 |
| SHA256: | A6A0104B3248FCEA011B98D68F3B77E338A085BB82729EDD6FAD5CB0DE0CC007 |
| SSDEEP: | 768:iBOtP+hN7Jn9an+SjGr1ARnGKqchShNTvvqXRhpjp6MHMSXl:iSP+Pan+SjhMvW6MHMQl |
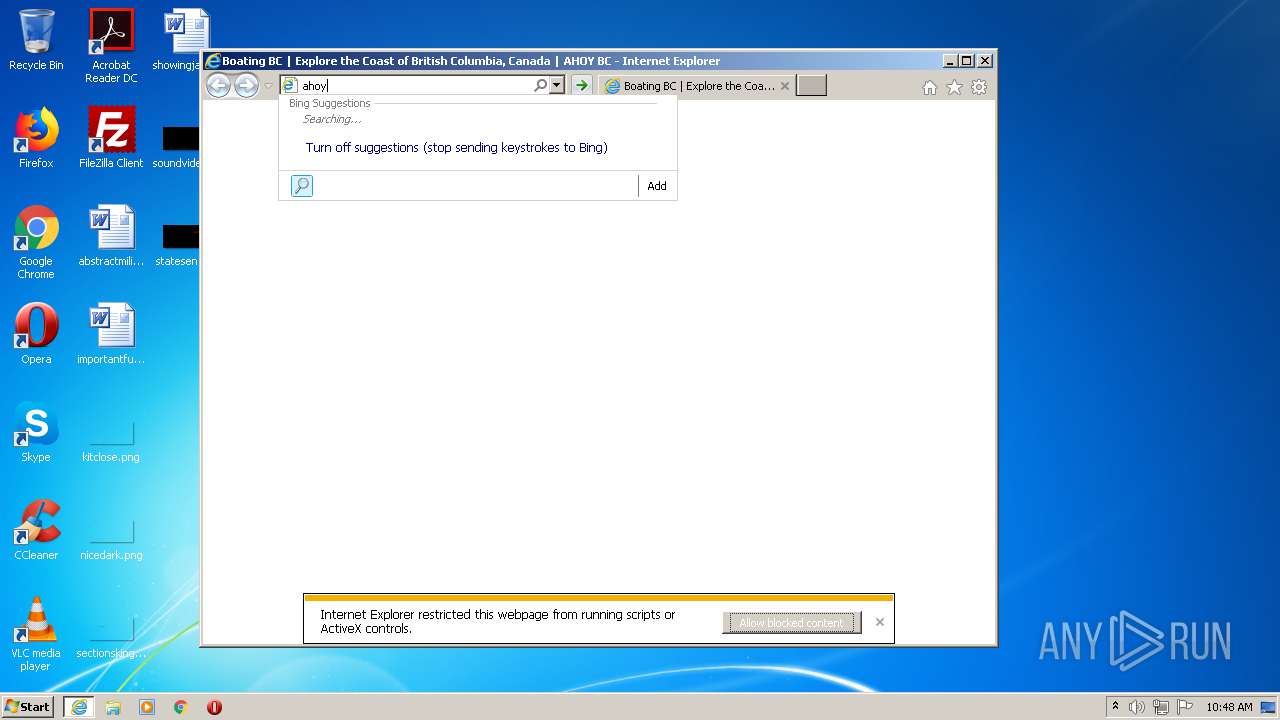
MALICIOUS
MINER was detected
- iexplore.exe (PID: 2276)
SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2124)
- iexplore.exe (PID: 2276)
Reads settings of System Certificates
- iexplore.exe (PID: 2616)
- iexplore.exe (PID: 2124)
- iexplore.exe (PID: 2276)
Application launched itself
- iexplore.exe (PID: 2124)
- iexplore.exe (PID: 2616)
Changes internet zones settings
- iexplore.exe (PID: 2124)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2616)
- iexplore.exe (PID: 2124)
Changes settings of System certificates
- iexplore.exe (PID: 2616)
- iexplore.exe (PID: 2124)
Creates files in the user directory
- iexplore.exe (PID: 2616)
- iexplore.exe (PID: 2124)
- iexplore.exe (PID: 2276)
Reads internet explorer settings
- iexplore.exe (PID: 2616)
- iexplore.exe (PID: 2276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| viewport: | width=device-width |
|---|---|
| Title: | Boating BC | Explore the Coast of British Columbia, Canada | AHOY BC |
| Description: | Explore the wild, hospitable coast of British Columbia. Find all your boating BC info here including marinas, communities, fishing & on-shore activities. |
| Robots: | index, follow, max-snippet:-1, max-image-preview:large, max-video-preview:-1 |
| twitterCard: | summary |
| msapplicationTileImage: | http: |
Total processes
38
Monitored processes
3
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2124 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2124 CREDAT:398593 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2124 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
2 803
Read events
2 615
Write events
183
Delete events
5
Modification events
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3222484110 | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30840590 | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
60
Text files
140
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\dd4e9.default.include.349cb1[1].css | text | |
MD5:— | SHA256:— | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\apbct-public.min[1].js | text | |
MD5:— | SHA256:— | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabB18.tmp | — | |
MD5:— | SHA256:— | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarB19.tmp | — | |
MD5:— | SHA256:— | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\venobox-init[1].js | text | |
MD5:— | SHA256:— | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\slide3[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\dd4e9.default.include-footer.b672d9[1].js | text | |
MD5:— | SHA256:— | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\slide2[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_592839A8569F831D0F2306AE4BB5C24B | binary | |
MD5:— | SHA256:— | |||
| 2616 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\slide1[1].jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
172
TCP/UDP connections
118
DNS requests
34
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2616 | iexplore.exe | GET | 200 | 159.203.27.31:80 | http://ahoybc.com/wp-content/cache/minify/dd4e9.default.include.349cb1.css | CA | text | 20.3 Kb | unknown |
2616 | iexplore.exe | GET | 200 | 159.203.27.31:80 | http://ahoybc.com/wp-content/plugins/venobox-lightbox/js/venobox-init.js?ver=2.0.3 | CA | text | 1.28 Kb | unknown |
2616 | iexplore.exe | GET | 200 | 159.203.27.31:80 | http://ahoybc.com/wp-content/plugins/cleantalk-spam-protect/js/apbct-public.min.js?ver=5.146 | CA | text | 1.69 Kb | unknown |
2616 | iexplore.exe | GET | 200 | 159.203.27.31:80 | http://ahoybc.com/wp-content/cache/minify/dd4e9.default.include-footer.b672d9.js | CA | text | 27.0 Kb | unknown |
2616 | iexplore.exe | GET | 200 | 159.203.27.31:80 | http://ahoybc.com/wp-content/uploads/2015/03/slide2.jpg | CA | image | 194 Kb | unknown |
2616 | iexplore.exe | GET | 200 | 159.203.27.31:80 | http://ahoybc.com/wp-content/uploads/2015/03/slide1.jpg | CA | image | 185 Kb | unknown |
2616 | iexplore.exe | GET | 200 | 159.203.27.31:80 | http://ahoybc.com/wp-content/uploads/2015/03/slide3.jpg | CA | image | 103 Kb | unknown |
2616 | iexplore.exe | GET | 200 | 159.203.27.31:80 | http://ahoybc.com/wp-content/uploads/2015/03/slide4.jpg | CA | image | 194 Kb | unknown |
2616 | iexplore.exe | GET | 200 | 159.203.27.31:80 | http://ahoybc.com/wp-content/uploads/2015/03/slide6.jpg | CA | image | 189 Kb | unknown |
2616 | iexplore.exe | GET | 200 | 159.203.27.31:80 | http://ahoybc.com/wp-content/plugins/ml-slider/assets/sliders/flexslider/flexslider.css?ver=0.1.0 | CA | text | 1.14 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2616 | iexplore.exe | 172.217.18.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2616 | iexplore.exe | 172.217.18.3:443 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2616 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2124 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4 | System | 209.197.3.15:445 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
2616 | iexplore.exe | 172.67.39.148:443 | static.addtoany.com | — | US | unknown |
2276 | iexplore.exe | 13.107.13.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
2276 | iexplore.exe | 159.203.27.31:80 | ahoybc.com | Digital Ocean, Inc. | CA | unknown |
2276 | iexplore.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ahoybc.com |
| unknown |
maxcdn.bootstrapcdn.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report