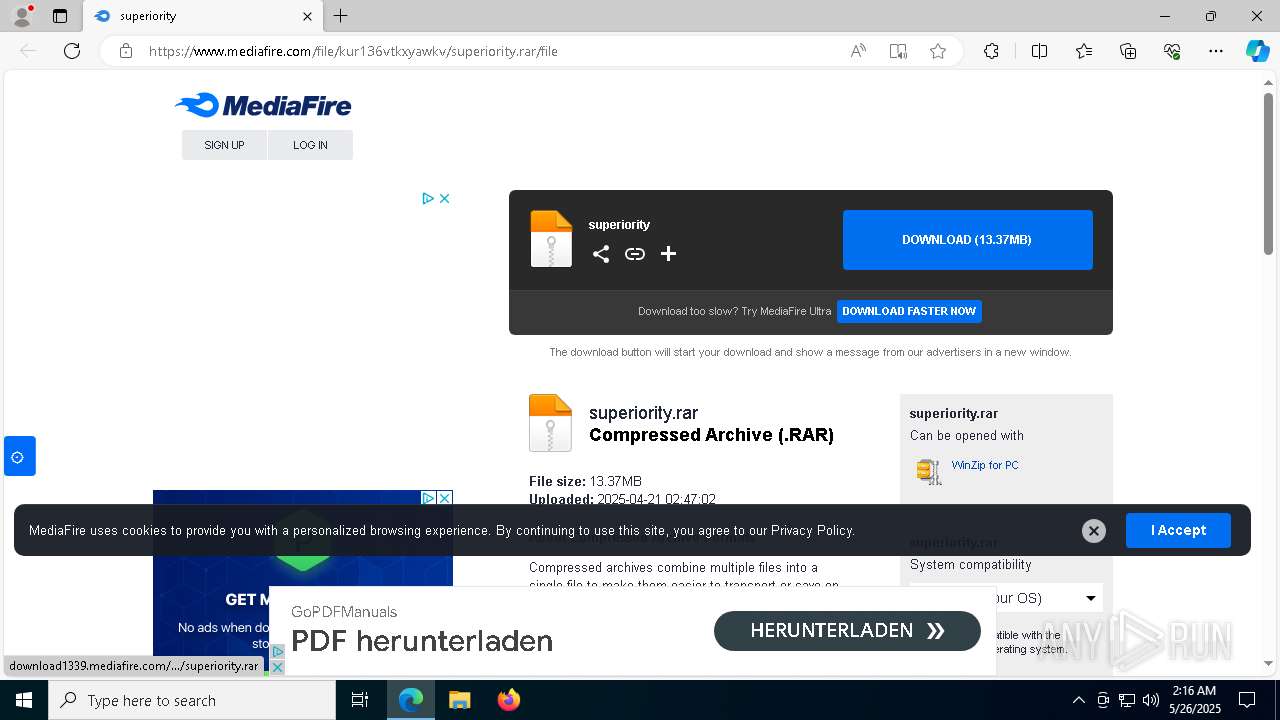
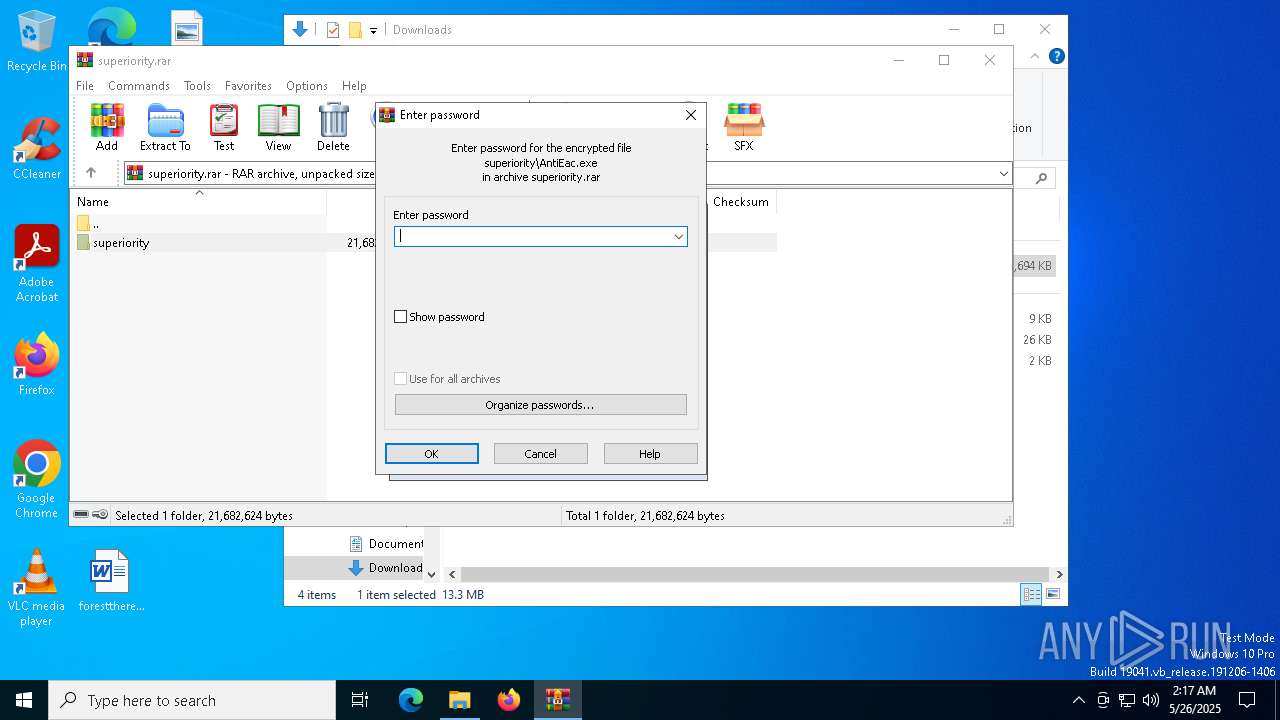
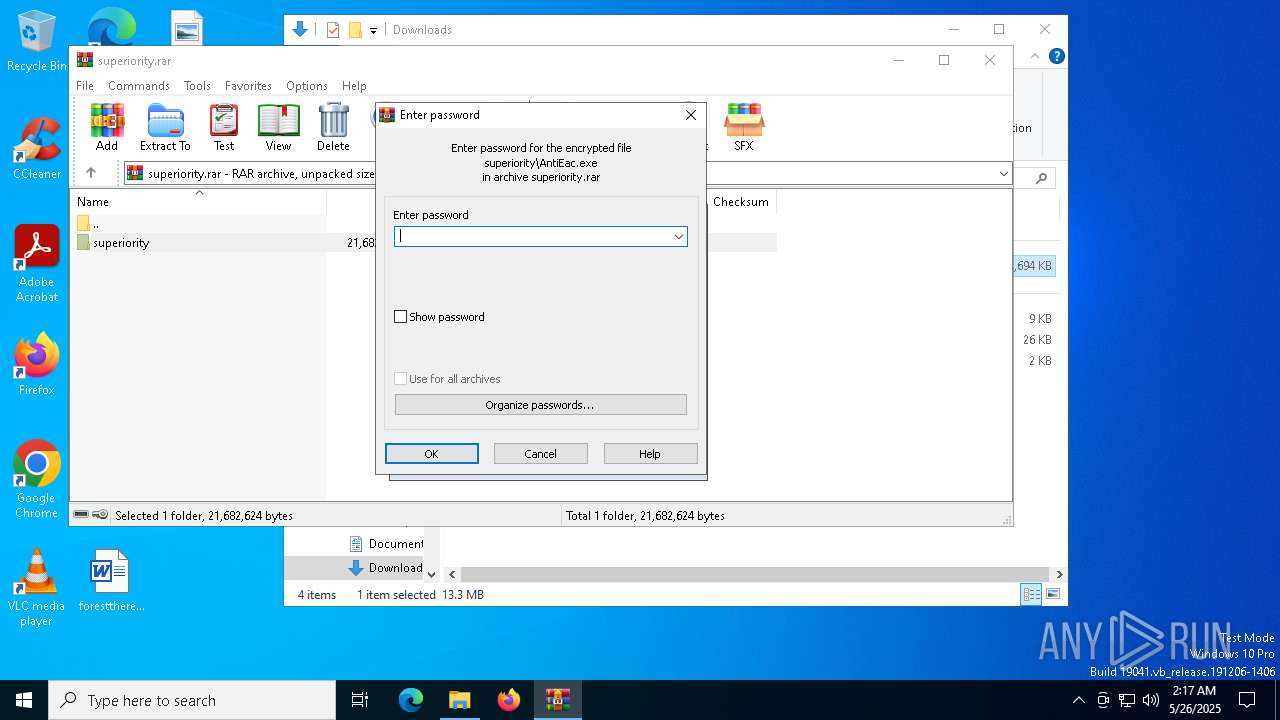
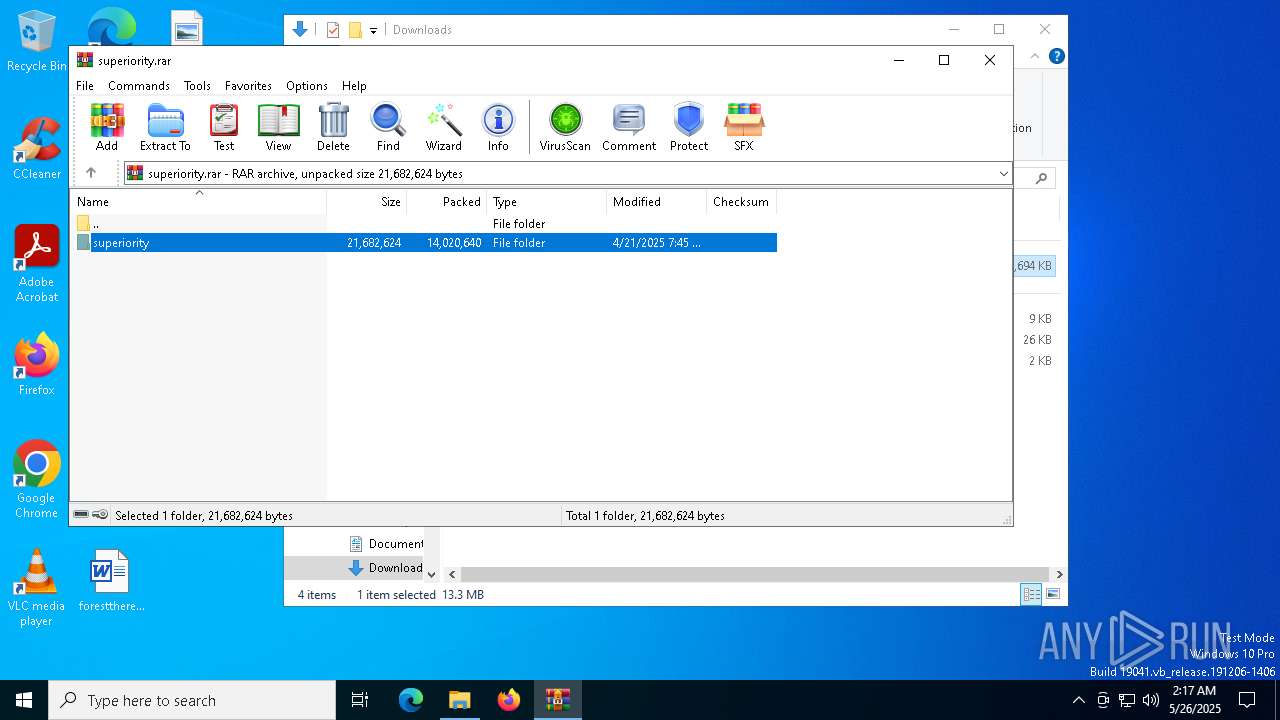
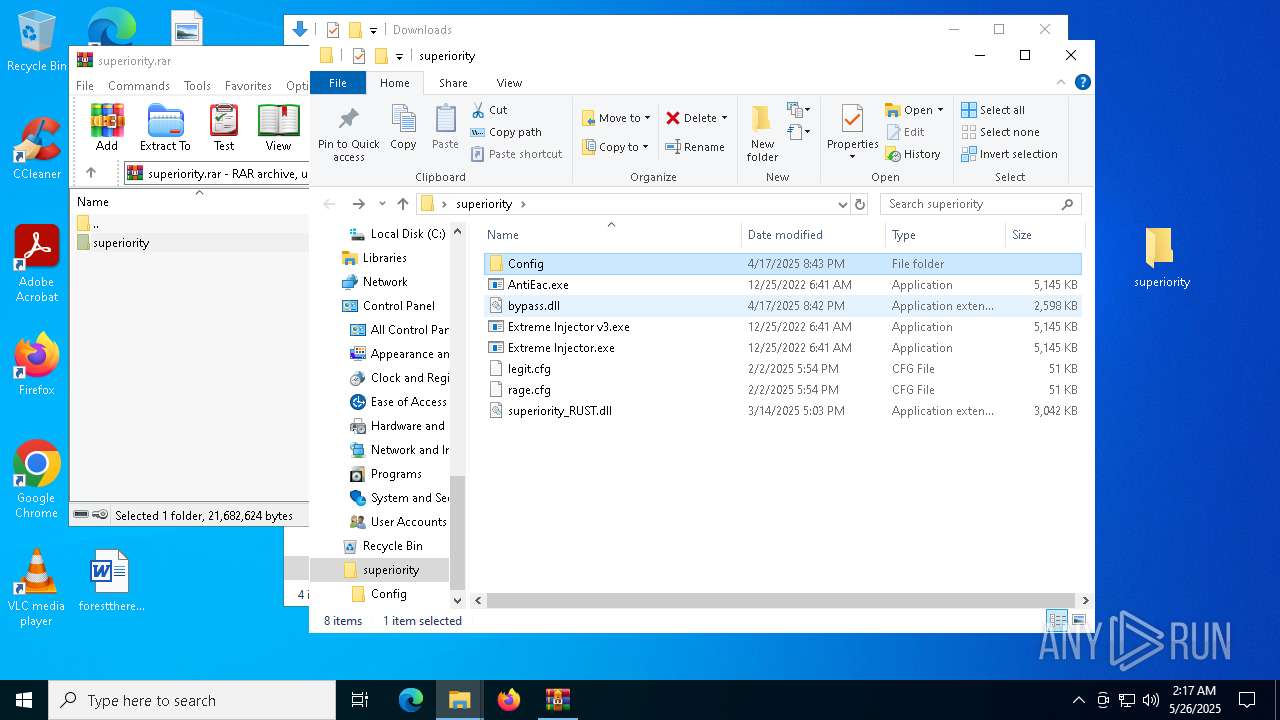
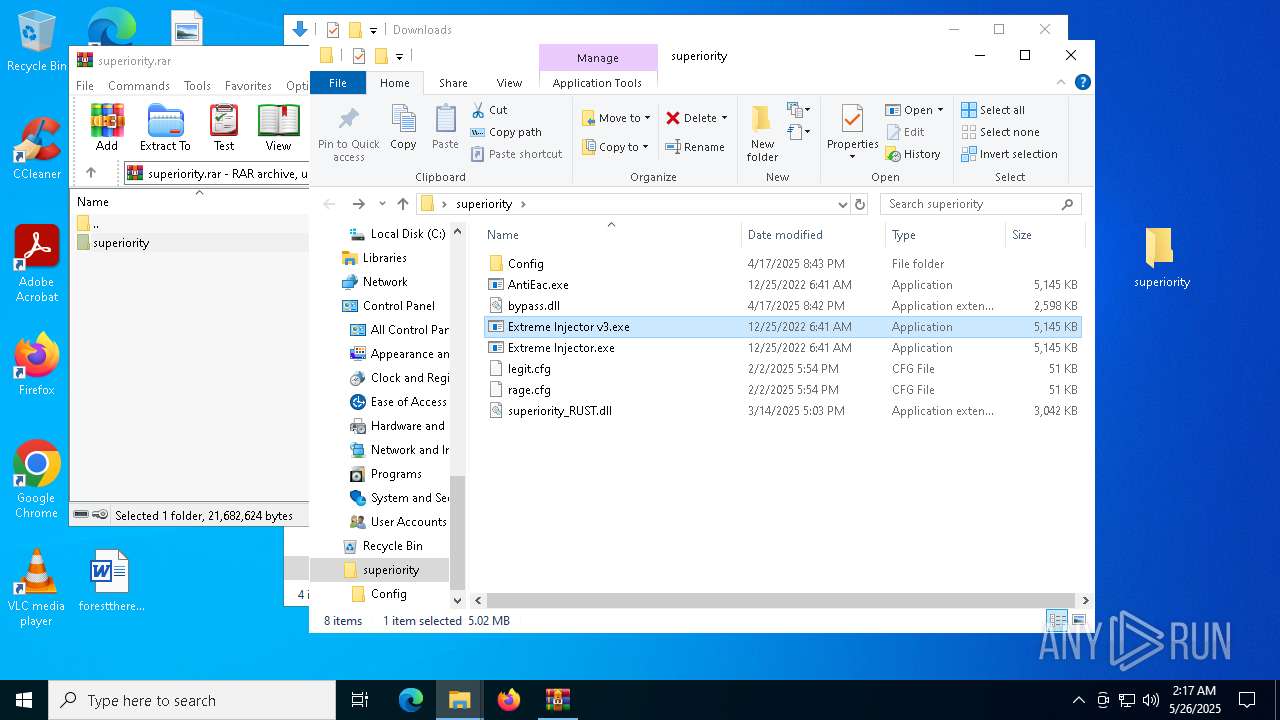
| URL: | www.mediafire.com/file/kur136vtkxyawkv/superiority.rar/file |
| Full analysis: | https://app.any.run/tasks/72d98703-b37b-4976-8cee-5241ab9a0c99 |
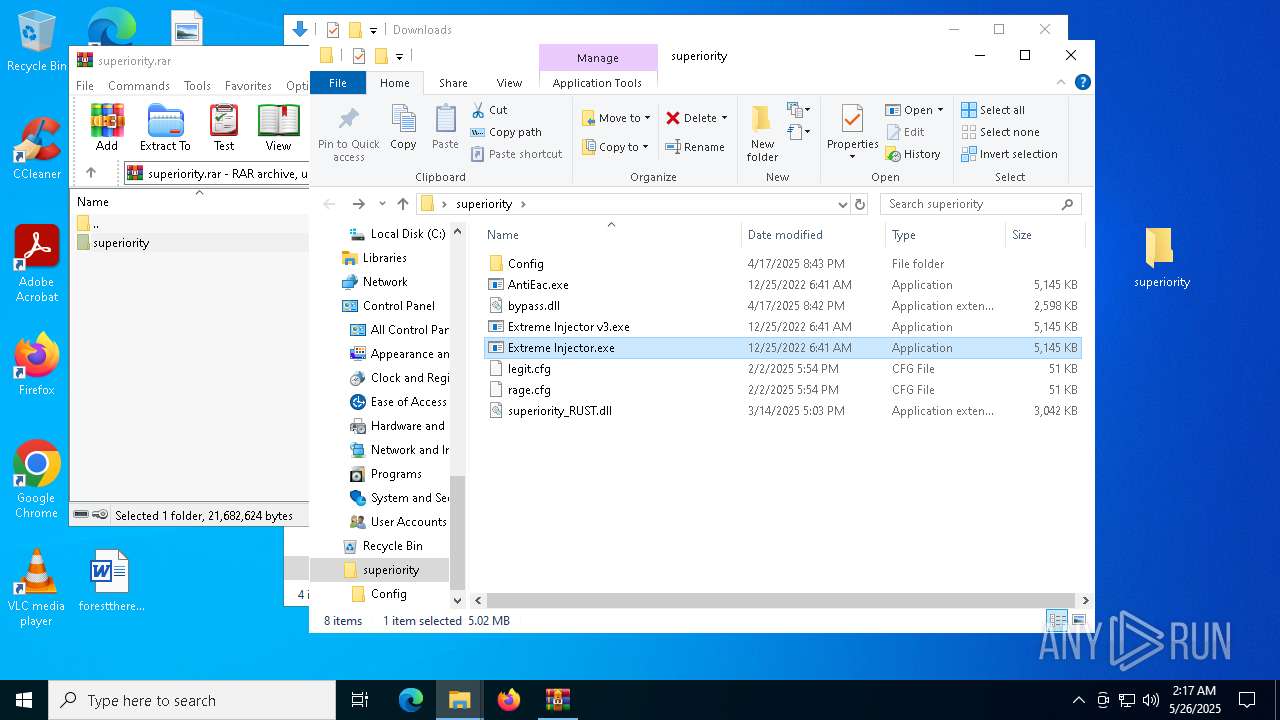
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
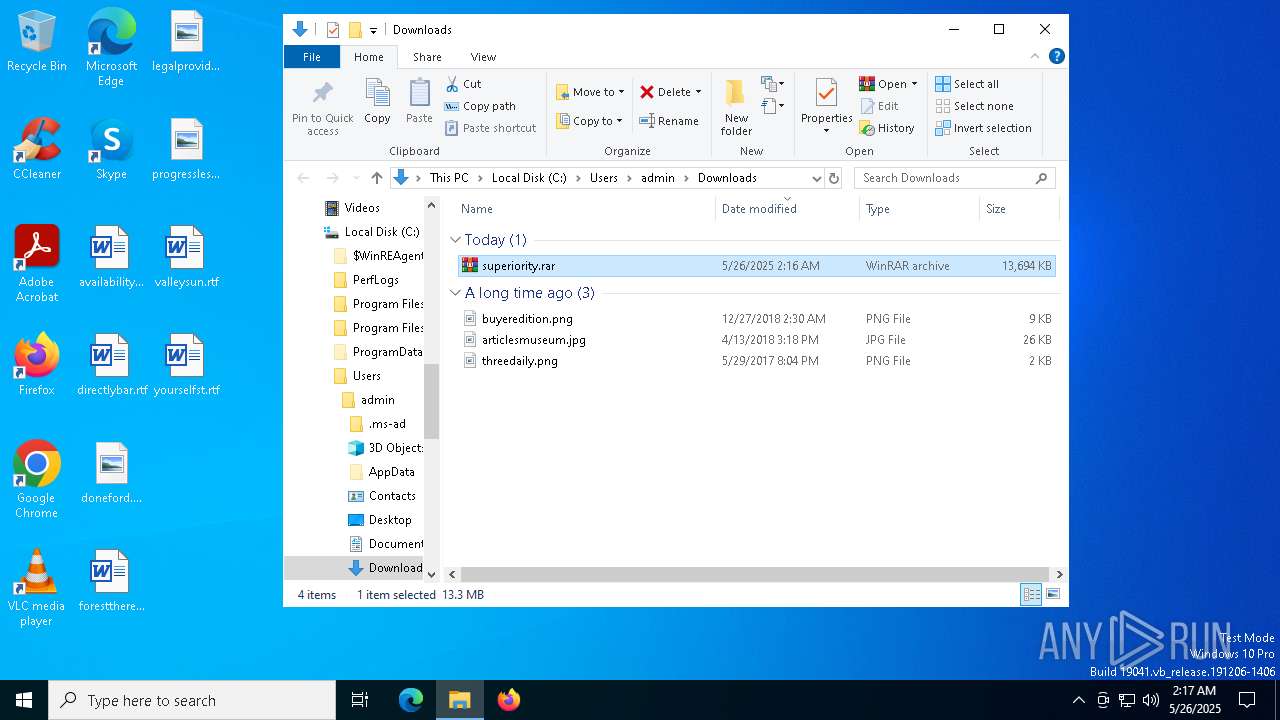
| Analysis date: | May 26, 2025, 02:16:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 135D9A8744A3373A4CA5F43B2A6E2B48 |
| SHA1: | B0878C07815EA32C49E24E1F862C8458074C1F1A |
| SHA256: | A668C79738BAA63C39F9D69DD91250EA5EEEECB769AEC39F717E3A2A51D89E13 |
| SSDEEP: | 3:ER63eGUo/ooIXJ4PA:h3eGBq2PA |
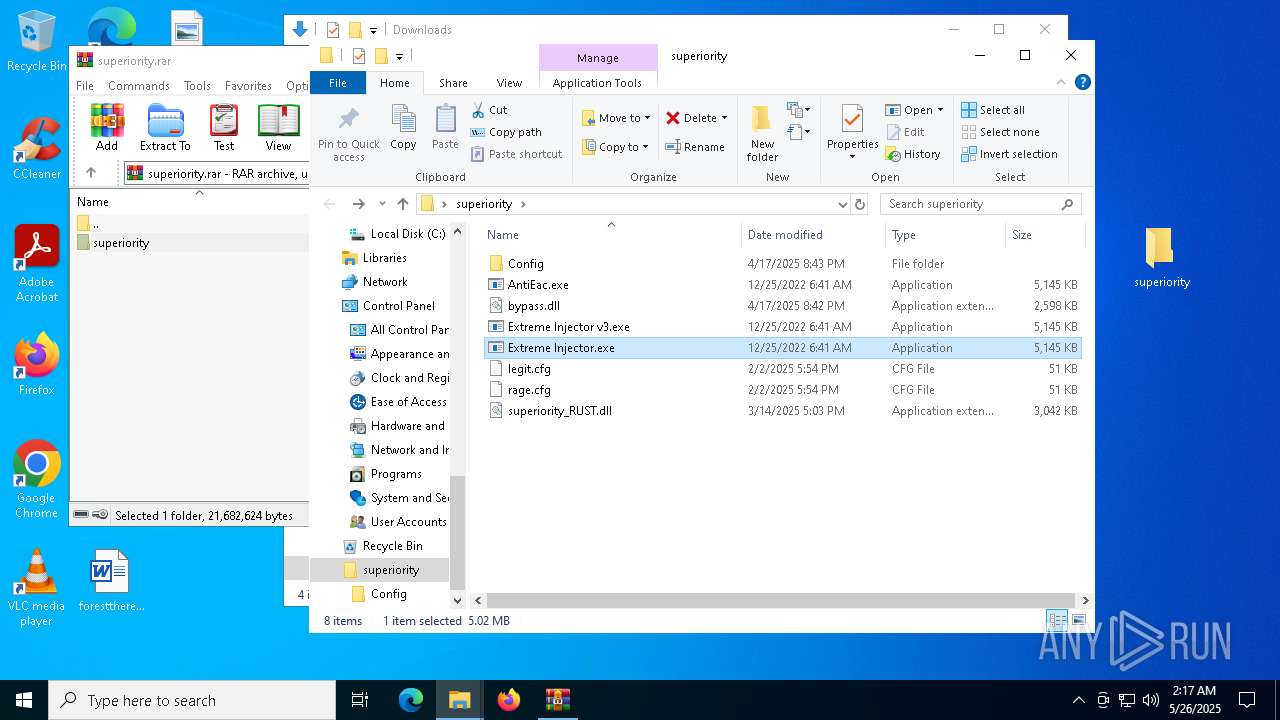
MALICIOUS
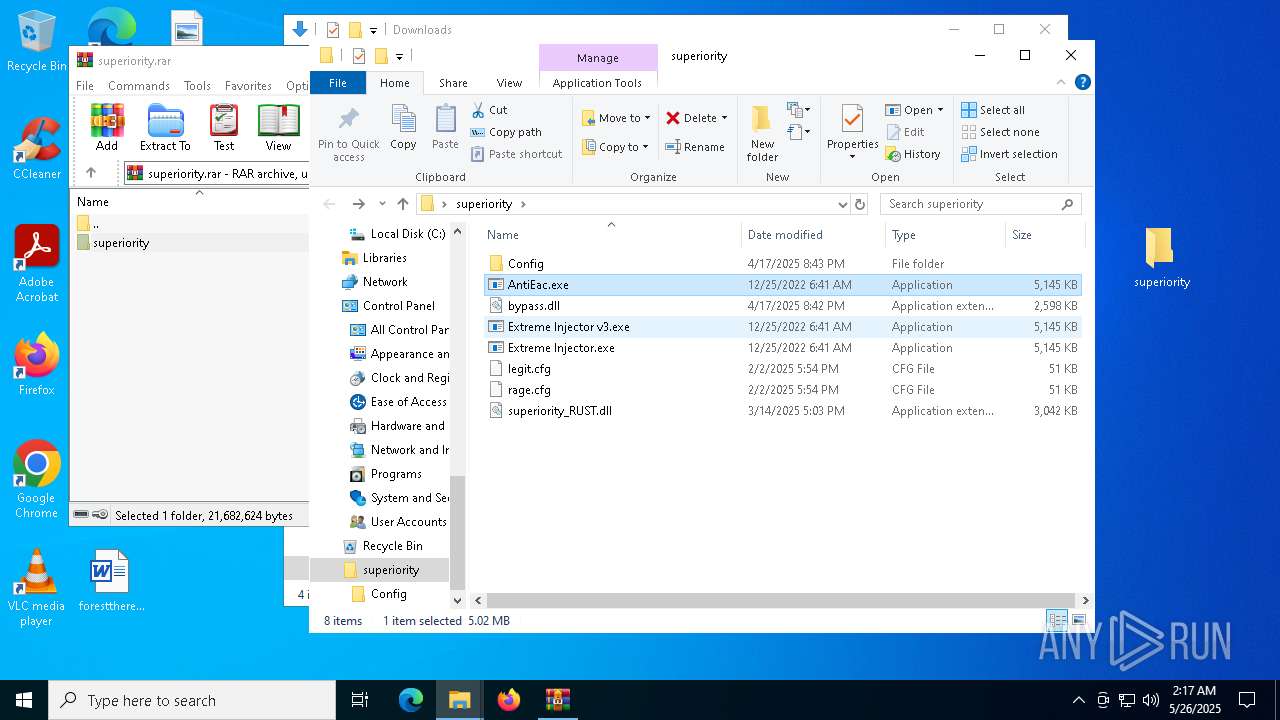
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 496)
Changes Windows Defender settings
- AntiEac.exe (PID: 8120)
- jnznthcwddeq.exe (PID: 2084)
Adds extension to the Windows Defender exclusion list
- AntiEac.exe (PID: 8120)
- jnznthcwddeq.exe (PID: 2084)
Vulnerable driver has been detected
- jnznthcwddeq.exe (PID: 2084)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2196)
XMRIG has been detected (YARA)
- conhost.exe (PID: 8272)
SUSPICIOUS
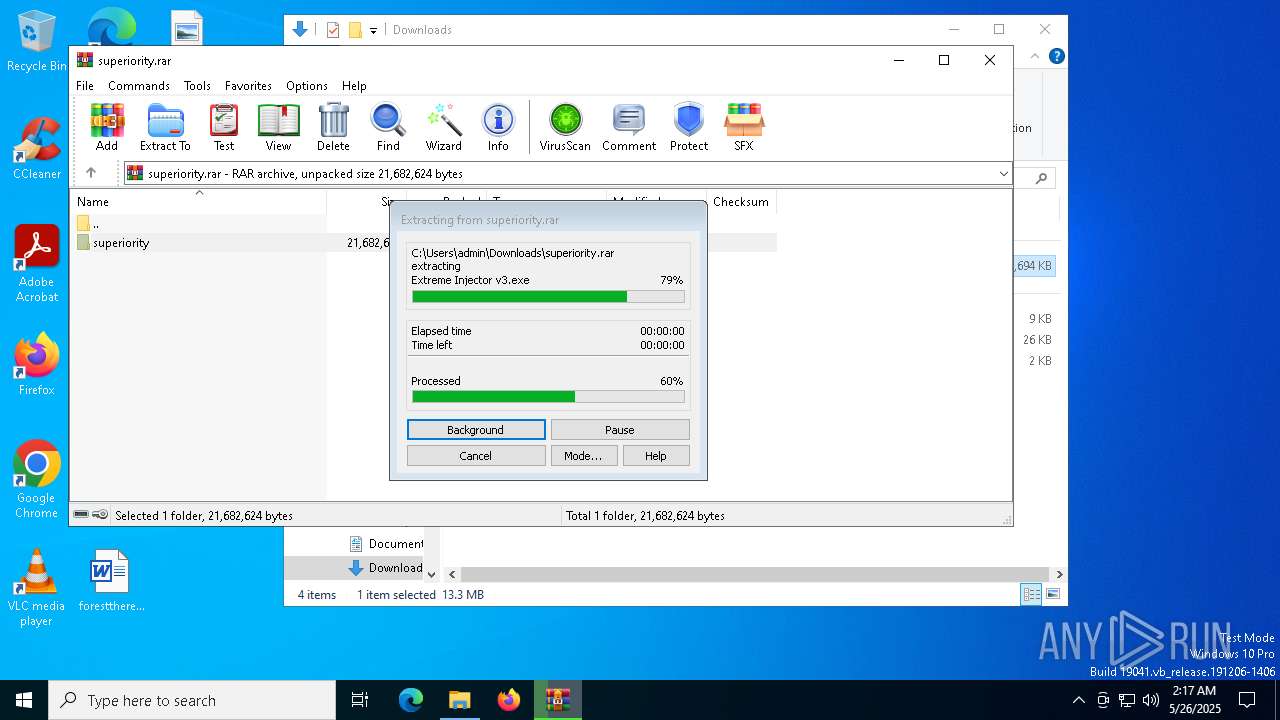
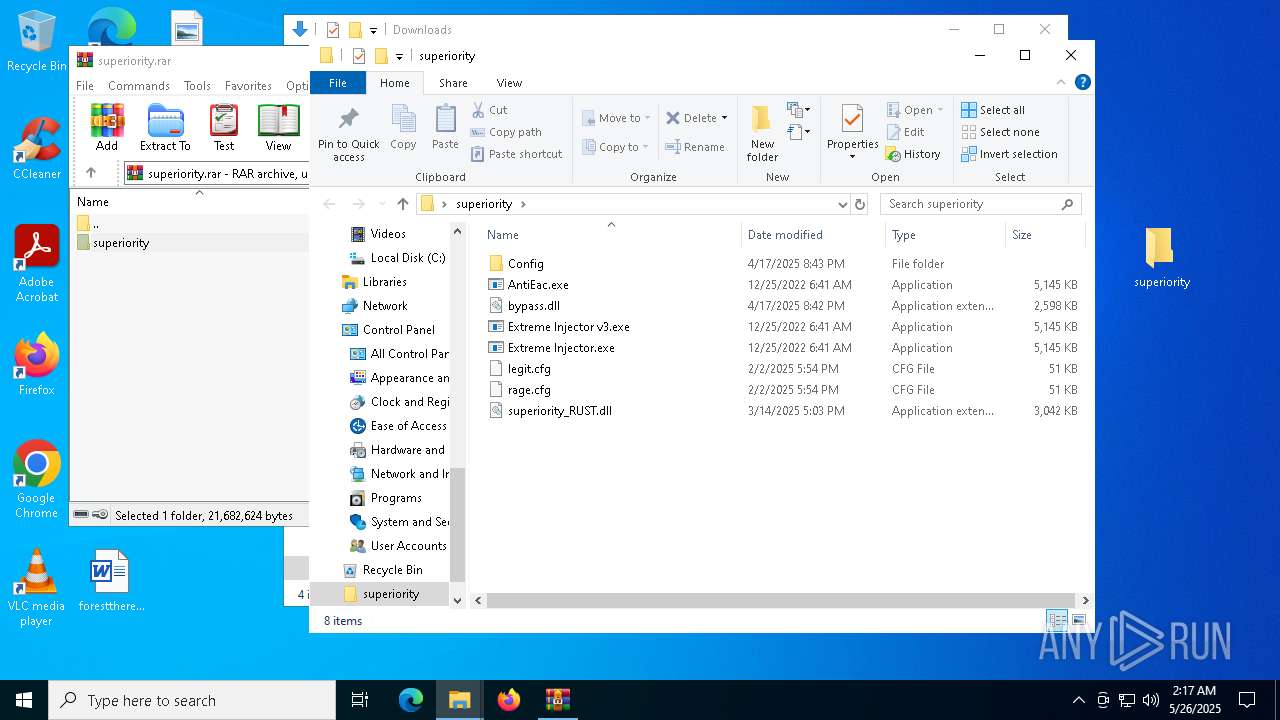
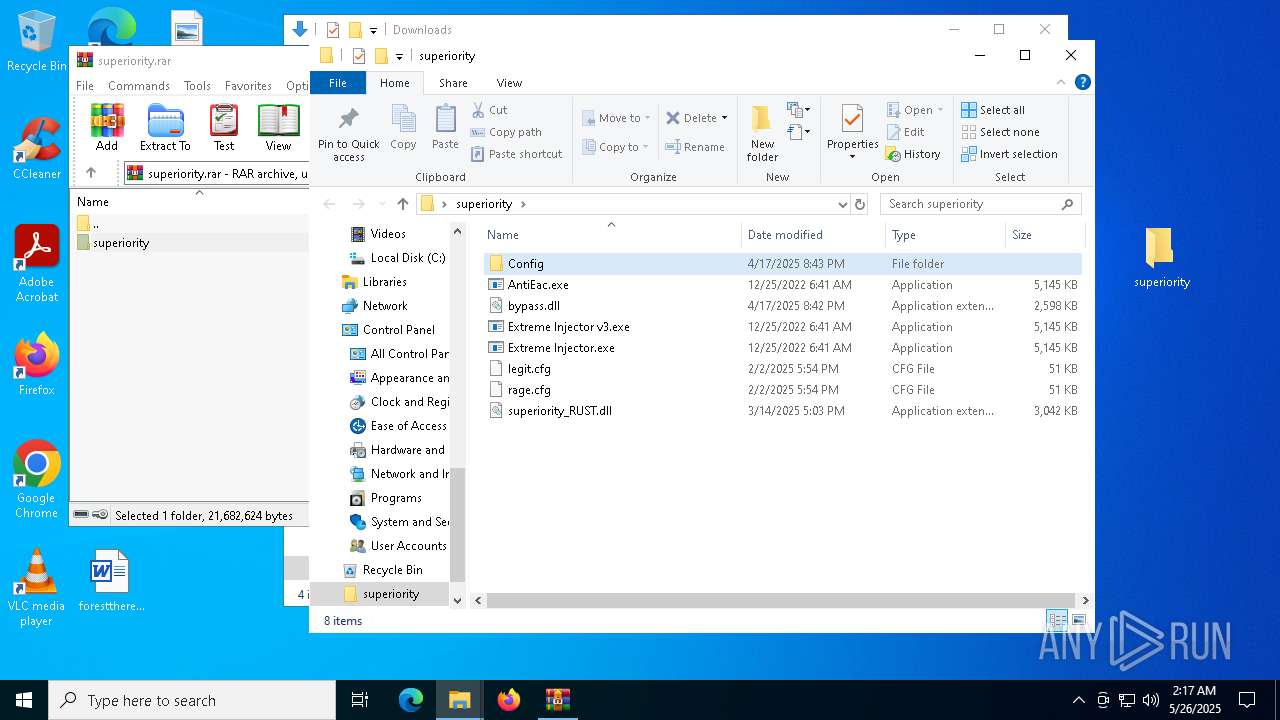
Starts POWERSHELL.EXE for commands execution
- Extreme Injector v3.exe (PID: 8140)
- AntiEac.exe (PID: 8340)
- Extreme Injector.exe (PID: 6872)
- Extreme Injector.exe (PID: 5984)
- AntiEac.exe (PID: 8120)
- jnznthcwddeq.exe (PID: 2084)
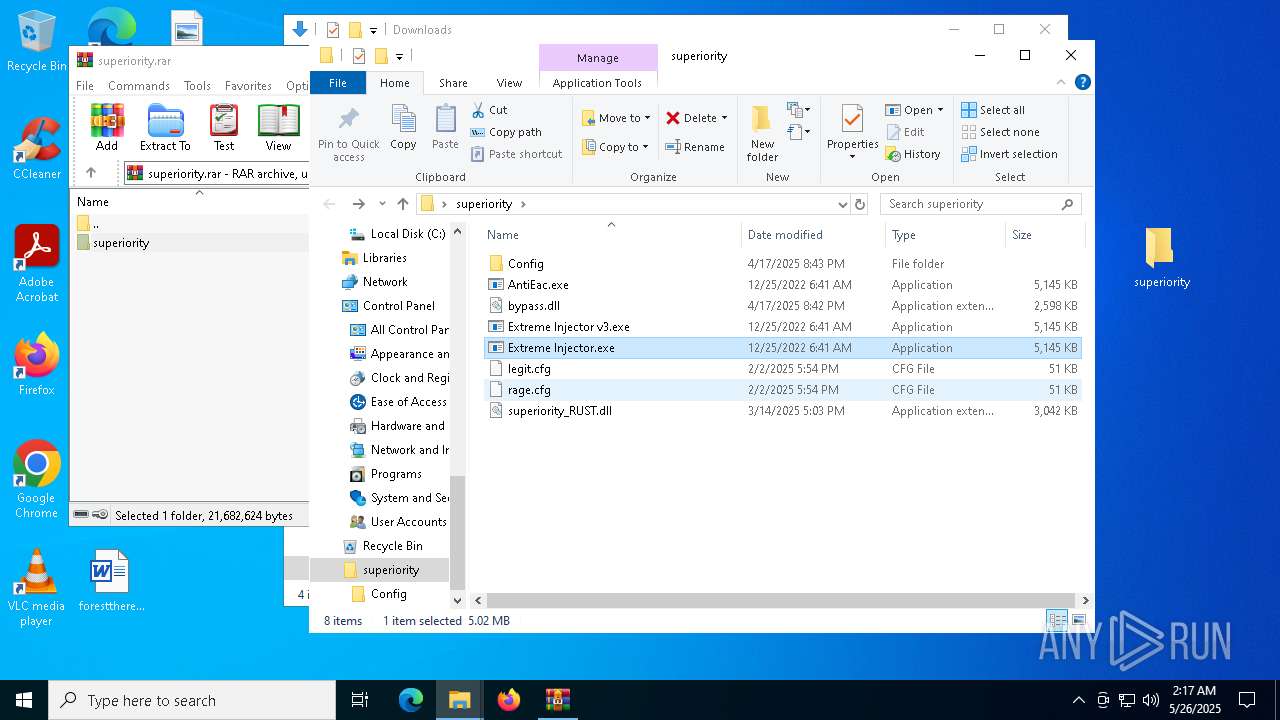
Starts process via Powershell
- powershell.exe (PID: 8392)
- powershell.exe (PID: 2108)
- powershell.exe (PID: 4920)
- powershell.exe (PID: 7888)
Script adds exclusion extension to Windows Defender
- AntiEac.exe (PID: 8120)
- jnznthcwddeq.exe (PID: 2084)
Script adds exclusion path to Windows Defender
- AntiEac.exe (PID: 8120)
- jnznthcwddeq.exe (PID: 2084)
Process uninstalls Windows update
- wusa.exe (PID: 7532)
- wusa.exe (PID: 5408)
Manipulates environment variables
- powershell.exe (PID: 7508)
- powershell.exe (PID: 9120)
Stops a currently running service
- sc.exe (PID: 8168)
- sc.exe (PID: 8416)
- sc.exe (PID: 8180)
- sc.exe (PID: 9136)
- sc.exe (PID: 8544)
- sc.exe (PID: 6252)
- sc.exe (PID: 6040)
- sc.exe (PID: 5024)
- sc.exe (PID: 9160)
- sc.exe (PID: 5352)
- sc.exe (PID: 8448)
Starts CMD.EXE for commands execution
- AntiEac.exe (PID: 8120)
- jnznthcwddeq.exe (PID: 2084)
Uses powercfg.exe to modify the power settings
- AntiEac.exe (PID: 8120)
- jnznthcwddeq.exe (PID: 2084)
Starts SC.EXE for service management
- AntiEac.exe (PID: 8120)
- jnznthcwddeq.exe (PID: 2084)
Windows service management via SC.EXE
- sc.exe (PID: 8488)
- sc.exe (PID: 7156)
Executable content was dropped or overwritten
- AntiEac.exe (PID: 8120)
- jnznthcwddeq.exe (PID: 2084)
Creates a new Windows service
- sc.exe (PID: 2192)
Executes as Windows Service
- jnznthcwddeq.exe (PID: 2084)
Drops a system driver (possible attempt to evade defenses)
- jnznthcwddeq.exe (PID: 2084)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2196)
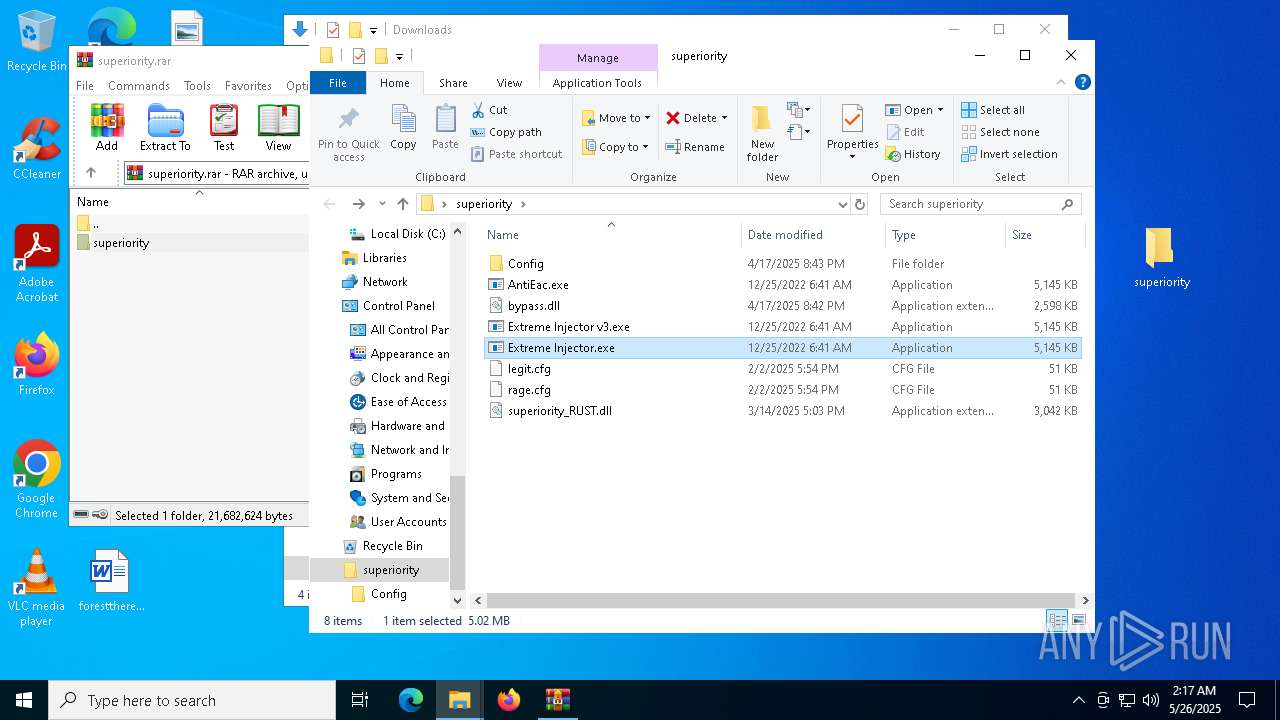
INFO
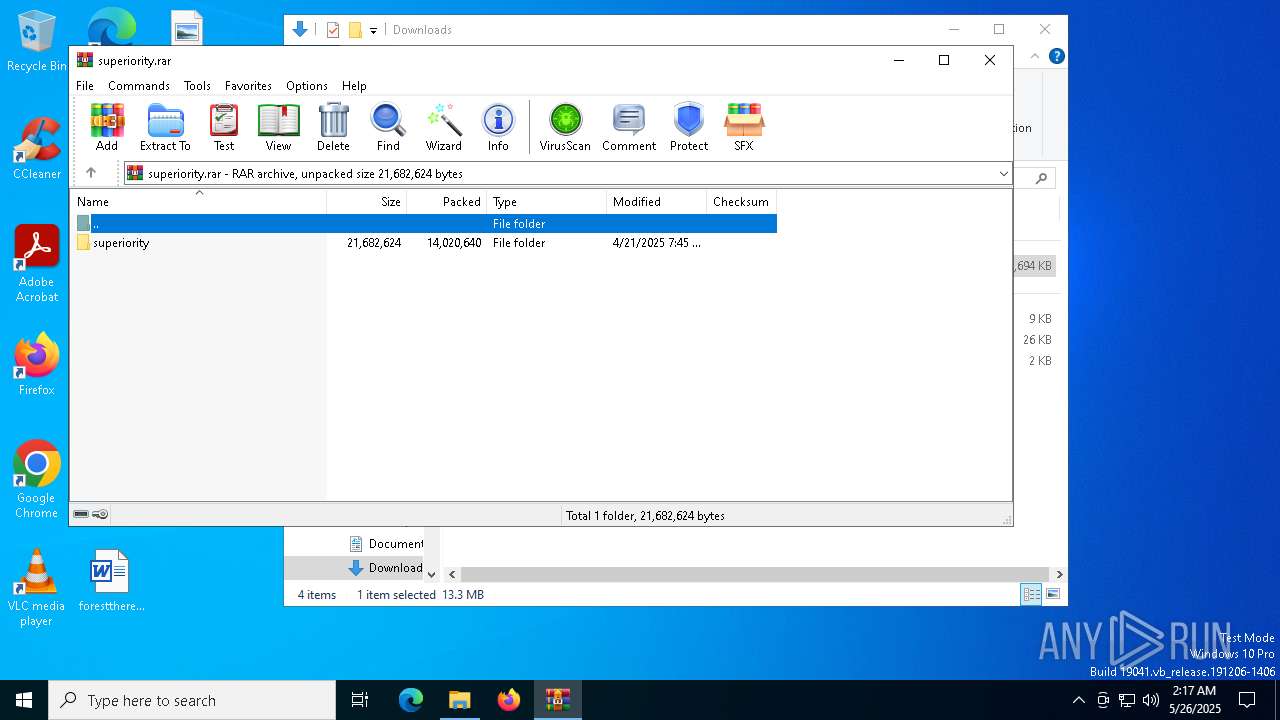
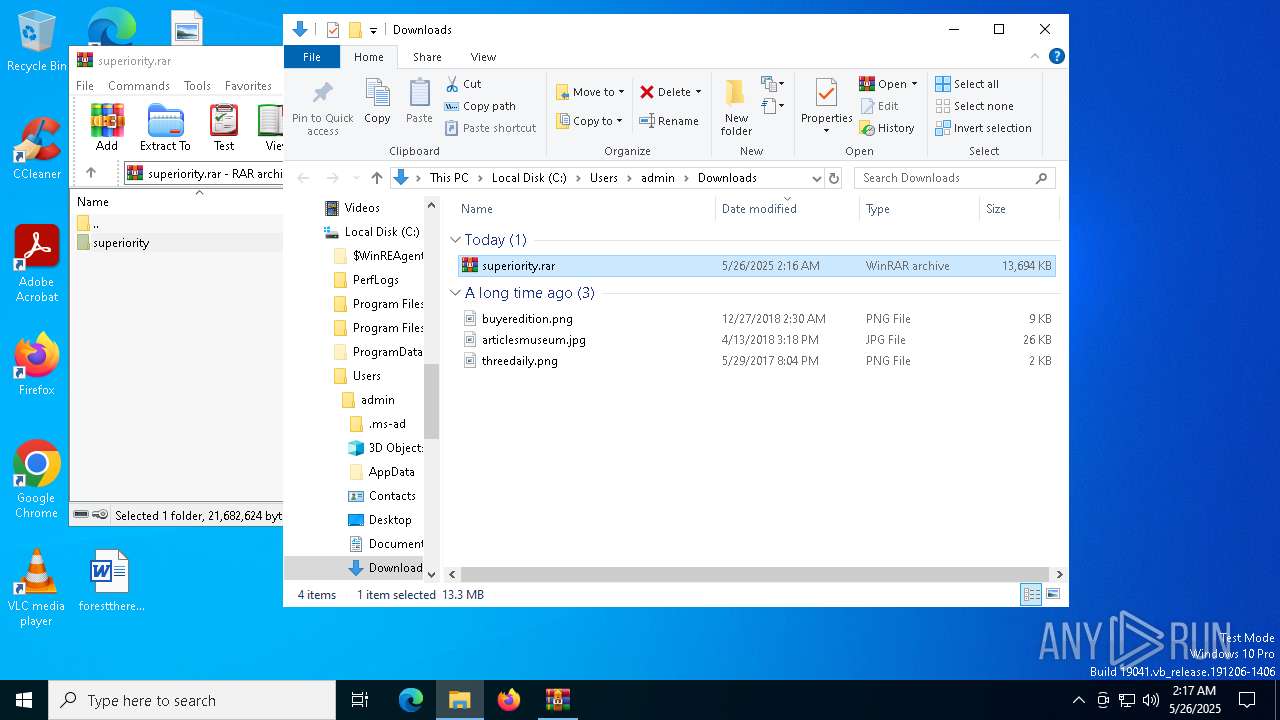
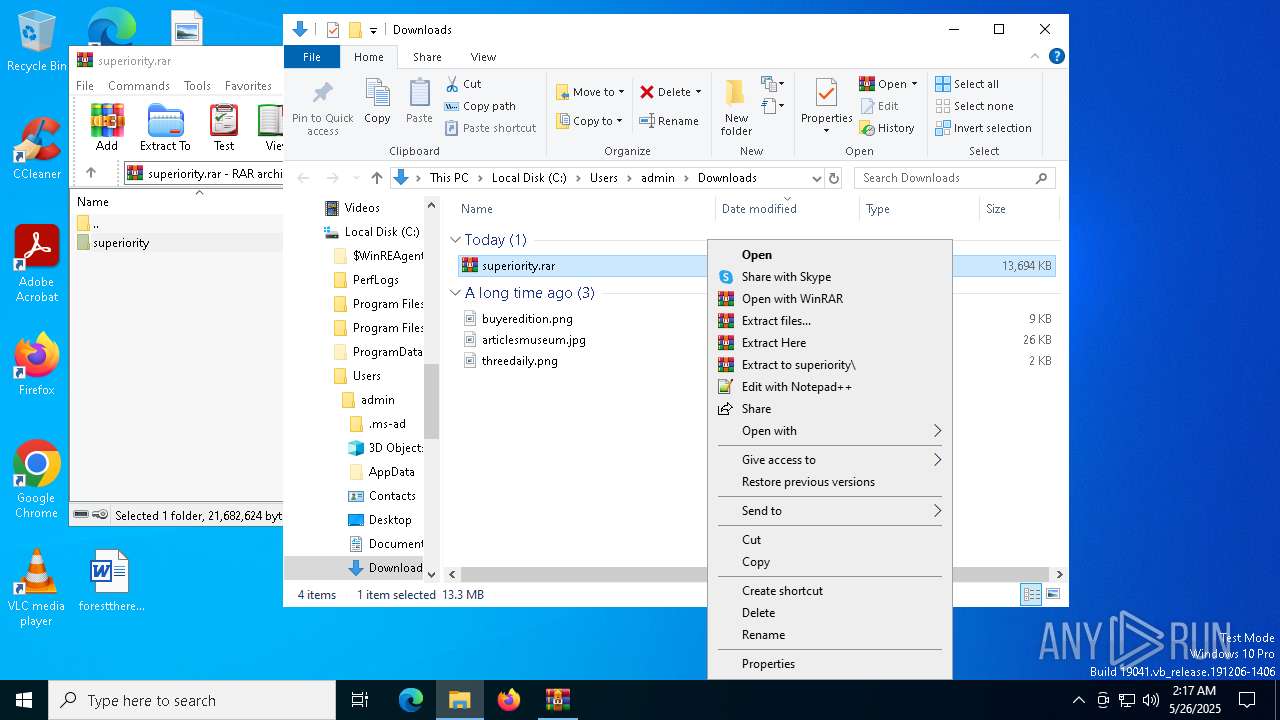
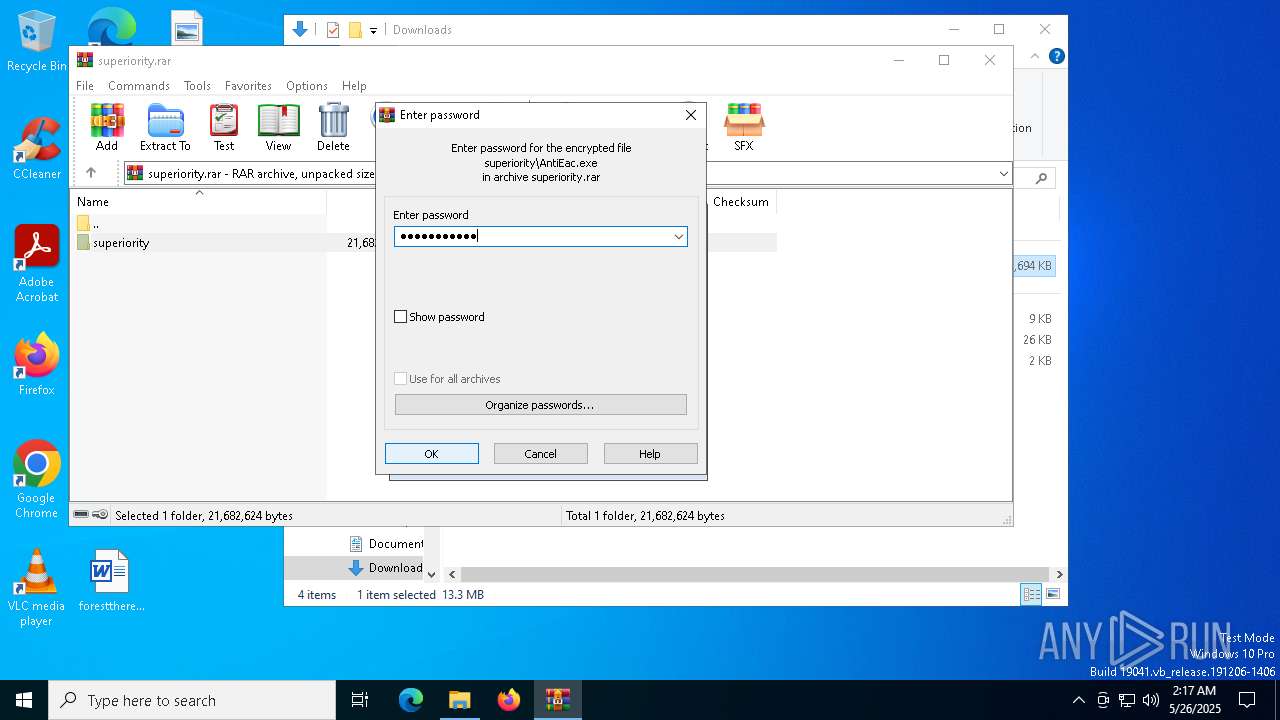
Manual execution by a user
- AntiEac.exe (PID: 8340)
- WinRAR.exe (PID: 9208)
- Extreme Injector v3.exe (PID: 8140)
- Extreme Injector.exe (PID: 5984)
- Extreme Injector.exe (PID: 6872)
Application launched itself
- msedge.exe (PID: 6676)
- msedge.exe (PID: 7316)
Reads the computer name
- identity_helper.exe (PID: 9120)
- identity_helper.exe (PID: 8488)
The sample compiled with english language support
- WinRAR.exe (PID: 9208)
- AntiEac.exe (PID: 8120)
- msedge.exe (PID: 8800)
Reads Environment values
- identity_helper.exe (PID: 9120)
- identity_helper.exe (PID: 8488)
Checks supported languages
- identity_helper.exe (PID: 9120)
- identity_helper.exe (PID: 8488)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 9208)
- msedge.exe (PID: 8800)
The sample compiled with japanese language support
- jnznthcwddeq.exe (PID: 2084)
UPX packer has been detected
- conhost.exe (PID: 8272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
288
Monitored processes
156
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | C:\WINDOWS\system32\cmd.exe /c wusa /uninstall /kb:890830 /quiet /norestart | C:\Windows\System32\cmd.exe | — | jnznthcwddeq.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 87 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --mojo-platform-channel-handle=6160 --field-trial-handle=2660,i,2981545748508940250,648948691833410955,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2084 | C:\ProgramData\gkgoyponfwum\jnznthcwddeq.exe | C:\ProgramData\gkgoyponfwum\jnznthcwddeq.exe | services.exe | ||||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: SYSTEM Description: Google Chrome Exit code: 0 Version: 70,0,3538,110 Modules
| |||||||||||||||
| 2108 | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe Start-Process "C:\Users\admin\Desktop\superiority\Extreme Injector.exe" -Verb runAs | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Extreme Injector.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\sc.exe create "QROERQFD" binpath= "C:\ProgramData\gkgoyponfwum\jnznthcwddeq.exe" start= "auto" | C:\Windows\System32\sc.exe | — | AntiEac.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5716 --field-trial-handle=2388,i,14248608531700084571,10173513187403933847,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=808 --field-trial-handle=2388,i,14248608531700084571,10173513187403933847,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2908 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --mojo-platform-channel-handle=6464 --field-trial-handle=2660,i,2981545748508940250,648948691833410955,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
43 885
Read events
43 837
Write events
48
Delete events
0
Modification events
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D3E4F2D196942F00 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 344DFFD196942F00 | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197228 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {84685800-C2F7-4173-BE10-3ED6956B46AF} | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197228 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A428B0A6-1E7F-42D4-886D-94EE9AD20B16} | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197228 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {16C8E5E9-4FB7-4877-A903-FF52818CF172} | |||
| (PID) Process: | (7316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197228 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2486337B-21D7-4E01-83AE-9AAC7D736E13} | |||
Executable files
32
Suspicious files
564
Text files
140
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b72c.TMP | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b72c.TMP | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b72c.TMP | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b72c.TMP | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b76b.TMP | — | |
MD5:— | SHA256:— | |||
| 7316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
318
DNS requests
305
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8480 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8480 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8836 | msedge.exe | GET | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3306b655-8319-4199-8014-458f0c48d21f?P1=1748405923&P2=404&P3=2&P4=IiMLz39nFqhQGZbk04DpWEj7k%2fFQuLfrq6k4f6cwoEpgCiyvuJGSFAIMFLj8tNcT0CaHsWiSsBbviboPxU1ARA%3d%3d | unknown | — | — | whitelisted |
8836 | msedge.exe | GET | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748297975&P2=404&P3=2&P4=Mt6JouheYdpBjrDQSqLJe4vTd5eW3CXeNsn5E8FGBP99r8iG7ja1eGdB8vl1xwG8oxaSWg2%2fAY83REgcx%2bff0g%3d%3d | unknown | — | — | whitelisted |
8836 | msedge.exe | GET | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1748297967&P2=404&P3=2&P4=IHPmnzi4UlAHJrfl9k3lLXq2gxbn7Da7oLBLUvuI6bShX4WQY4VRZB0PCeTglQTmvDlzDgs3kIDZjfS6l1AxUw%3d%3d | unknown | — | — | whitelisted |
8836 | msedge.exe | GET | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1748297968&P2=404&P3=2&P4=G7LfPPCuS91fsVF4yYFN2N%2fBiDEhP3n8Vdm%2b3G31X8jJ5bcXBjpdfP4xQiV5mCoh5lZgcfKYmYd3jlLFewe%2biQ%3d%3d | unknown | — | — | whitelisted |
8836 | msedge.exe | GET | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9530bc3d-28ec-4dca-8d8d-874a68b1b861?P1=1748297968&P2=404&P3=2&P4=nbWpASKmH57V596ctW%2bpLeaQ71Fc0HOXDzxBmhoCwuK4XF5ZlnEGY2egRxSHLdwpc2vGijwYcYCQMxzuzXO2WQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7316 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7656 | msedge.exe | 104.17.150.117:443 | www.mediafire.com | — | — | whitelisted |
7656 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7656 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.mediafire.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7656 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7656 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7656 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7656 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7656 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7656 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7656 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7656 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7656 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7656 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |