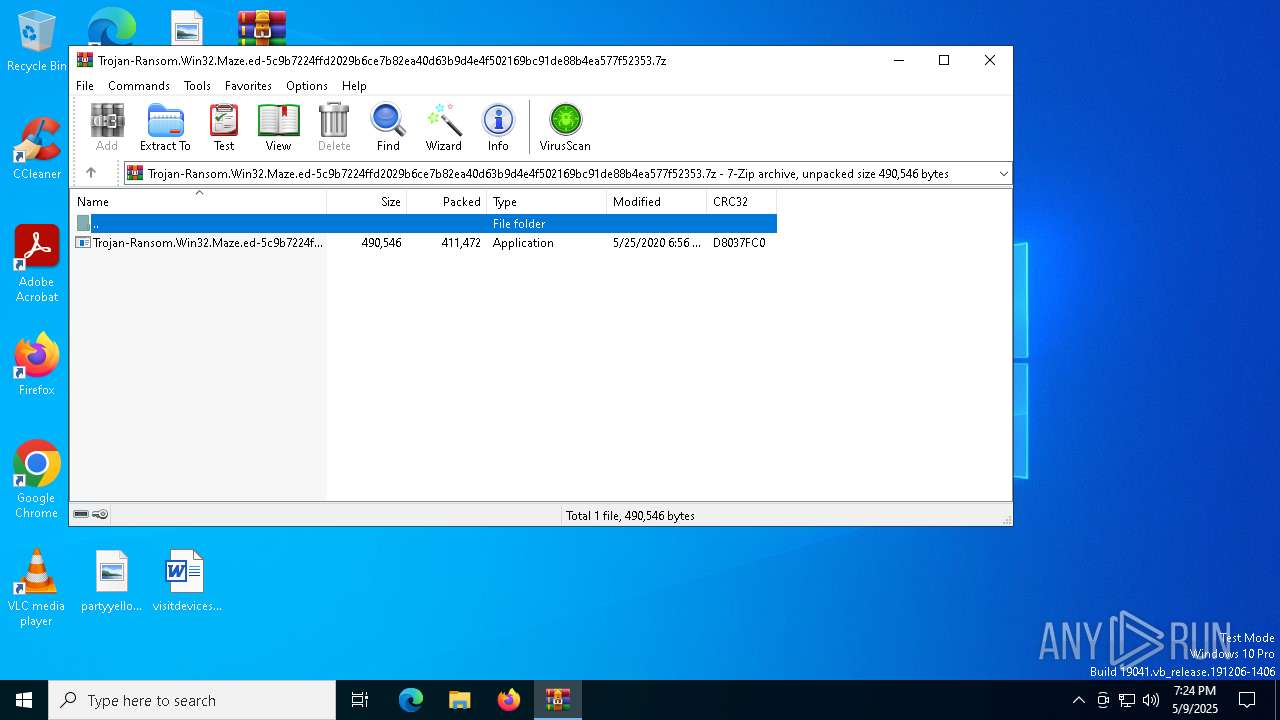
| File name: | Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.7z |
| Full analysis: | https://app.any.run/tasks/f42d1e52-ba85-47d6-af32-f77f0af2c7d3 |
| Verdict: | Malicious activity |
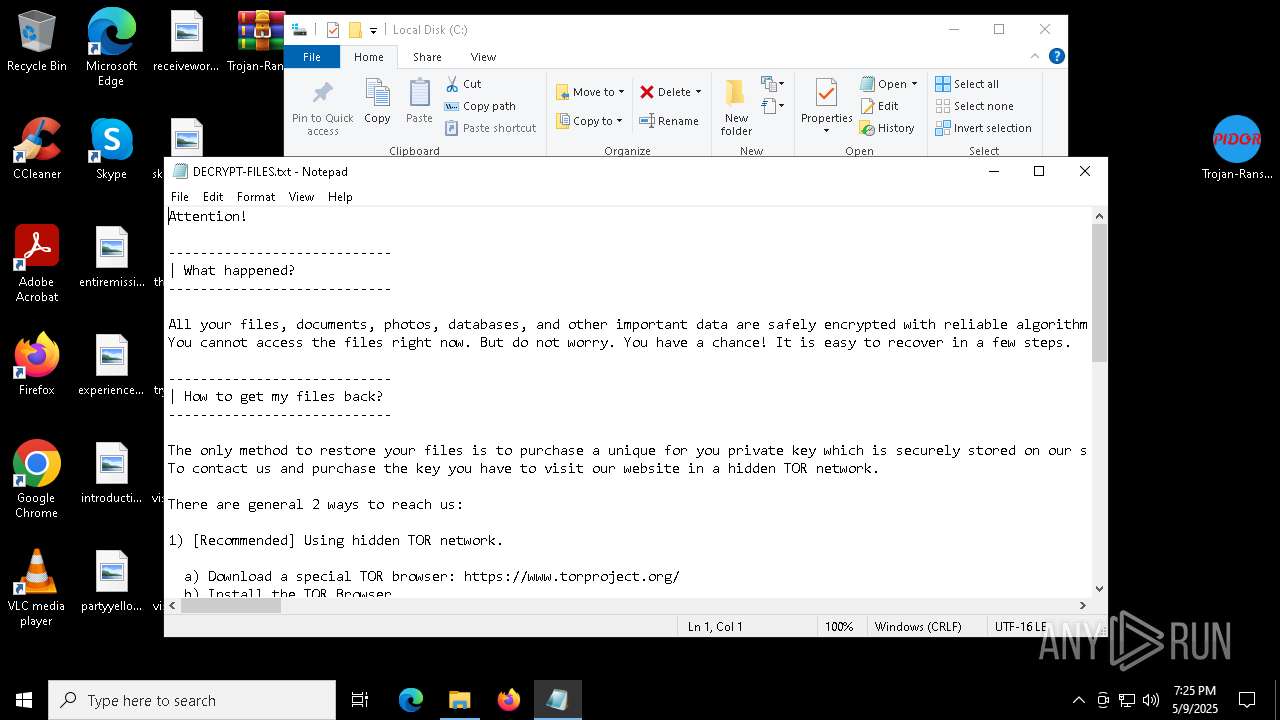
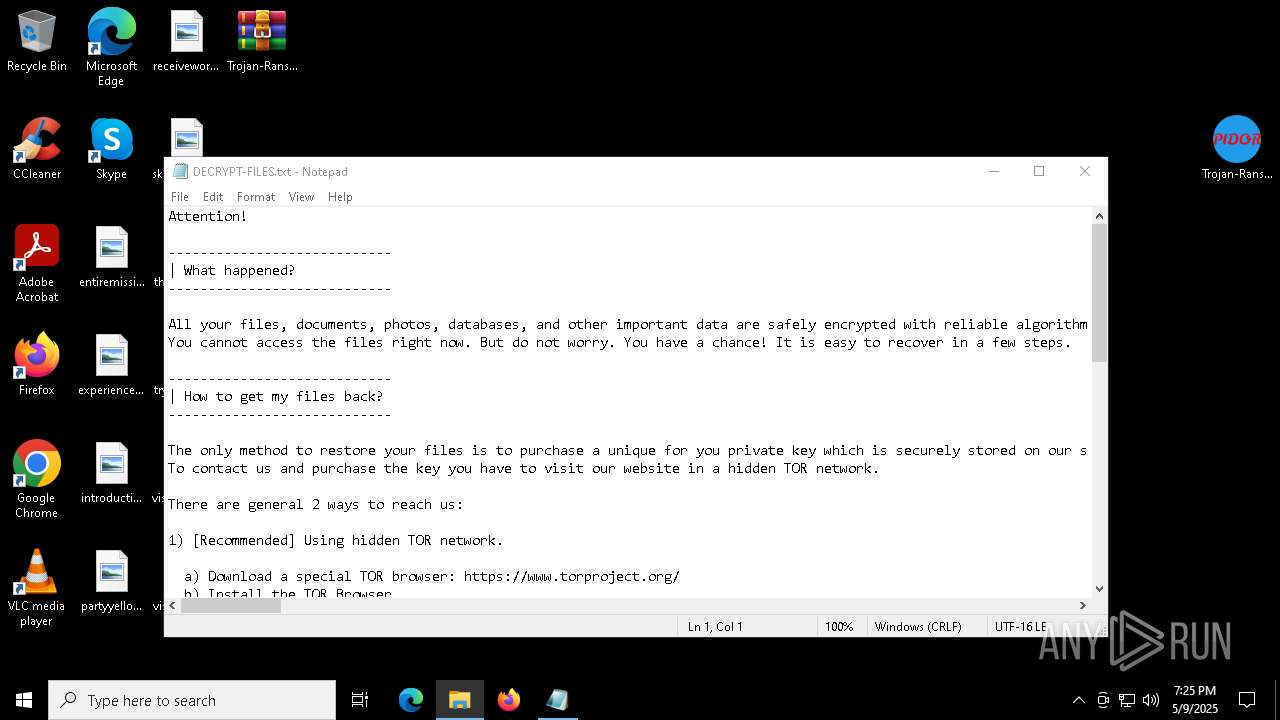
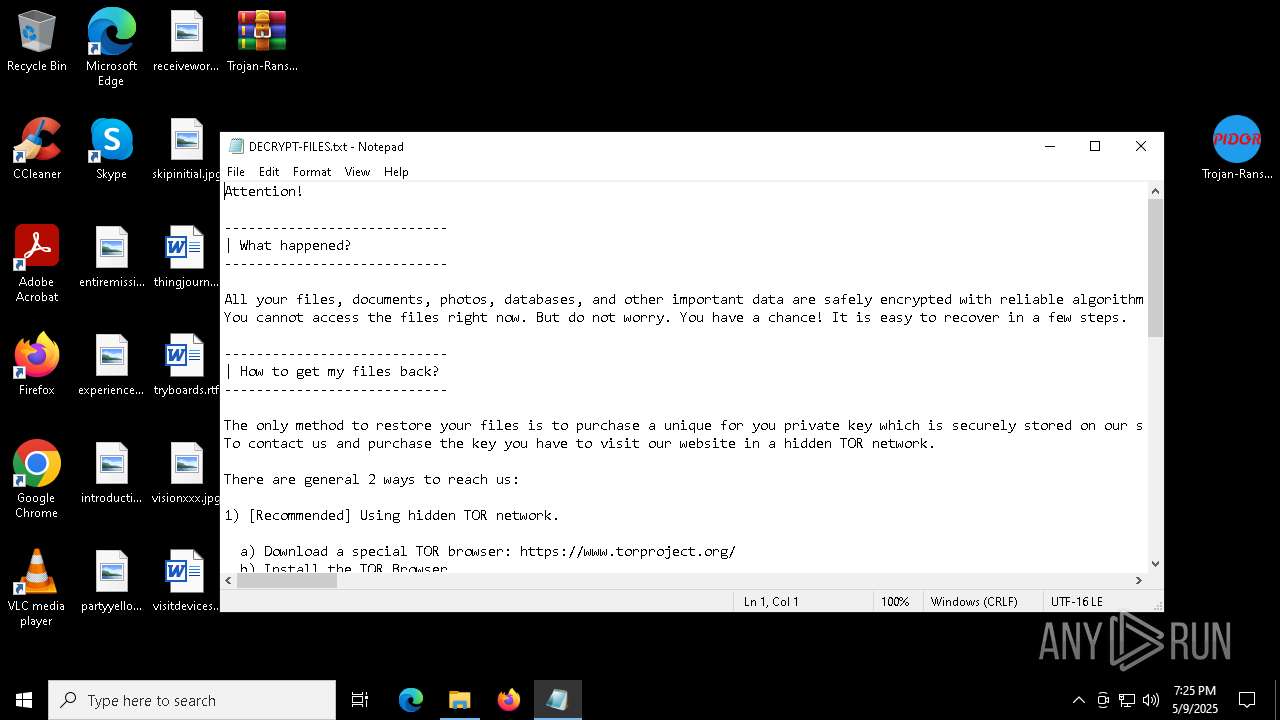
| Threats: | Maze is ransomware — a malware type that encrypts the victim’s files and restores the data in exchange for a ransom payment. One of the most distinguishable features of Maze is that it is one of the first malware of the kind to publicly release stolen data. |
| Analysis date: | May 09, 2025, 19:24:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 46D31B392CCEF626B0A9121C6A8A87BD |
| SHA1: | A92224A07D2C53AA6584C506B7FEF22D83A918A8 |
| SHA256: | A63341E3A6CDCBF77656AD9370B619A46DAE3B0FCF3AD5D868A36D4FEA9D5B1D |
| SSDEEP: | 12288:zNEUfA3B9nwU0A0ZlF9heTwfE1hBQSuWu1xe7x542dX:zN/fsnwnA0ZlvhecfE1hBQSuX1U7b42Z |
MALICIOUS
MAZE mutex has been found
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
Maze is detected
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
RANSOMWARE has been detected
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
Create files in the Startup directory
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
Writes a file to the Word startup folder
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
Renames files like ransomware
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
SUSPICIOUS
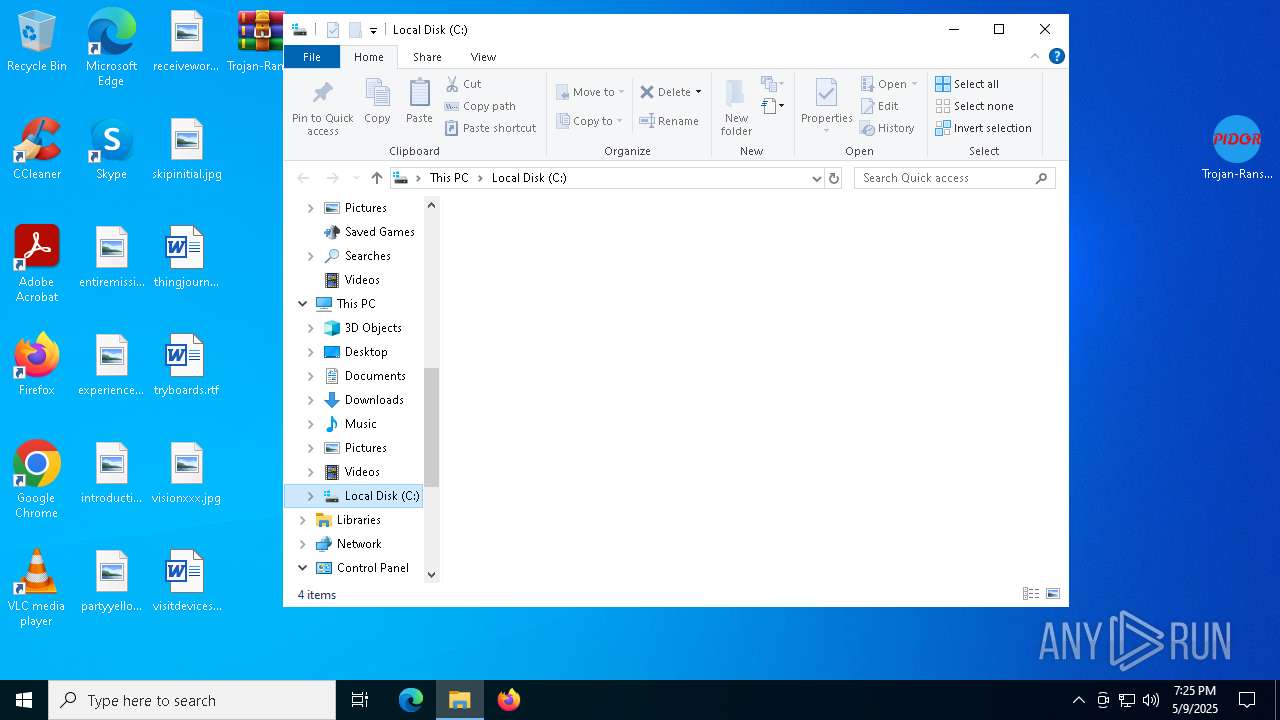
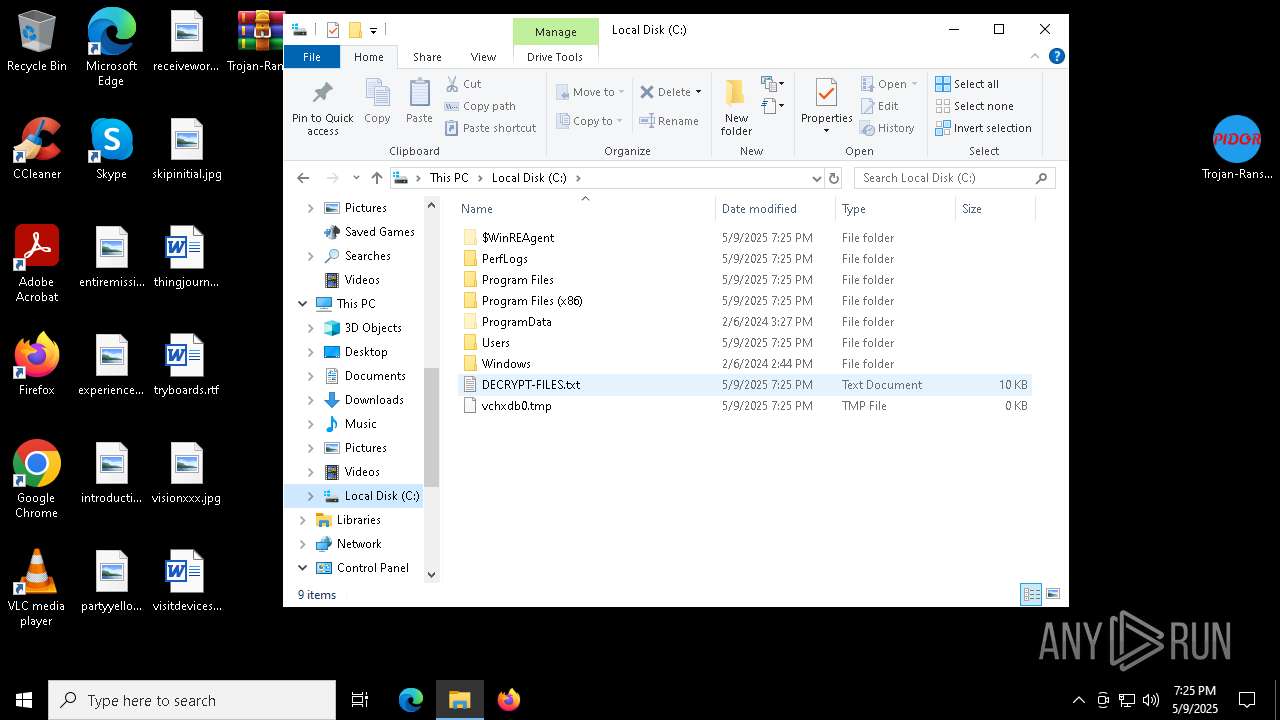
Creates file in the systems drive root
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
There is functionality for taking screenshot (YARA)
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
Reads security settings of Internet Explorer
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
INFO
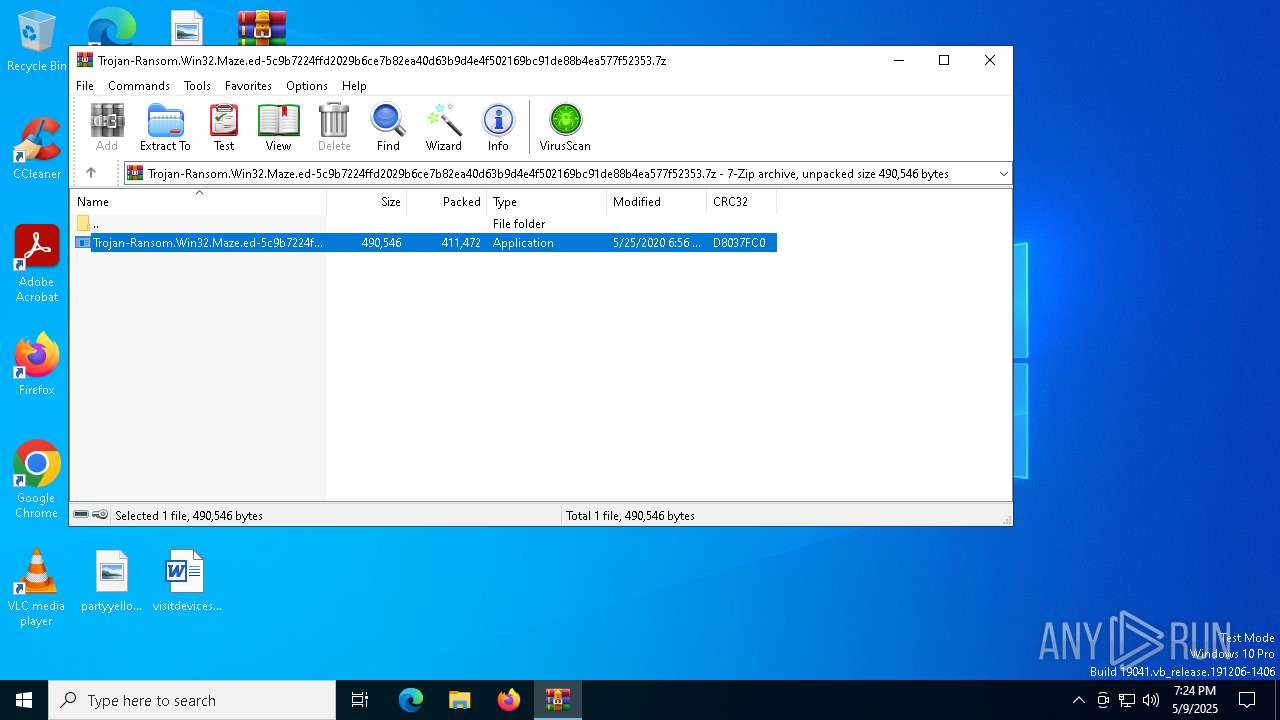
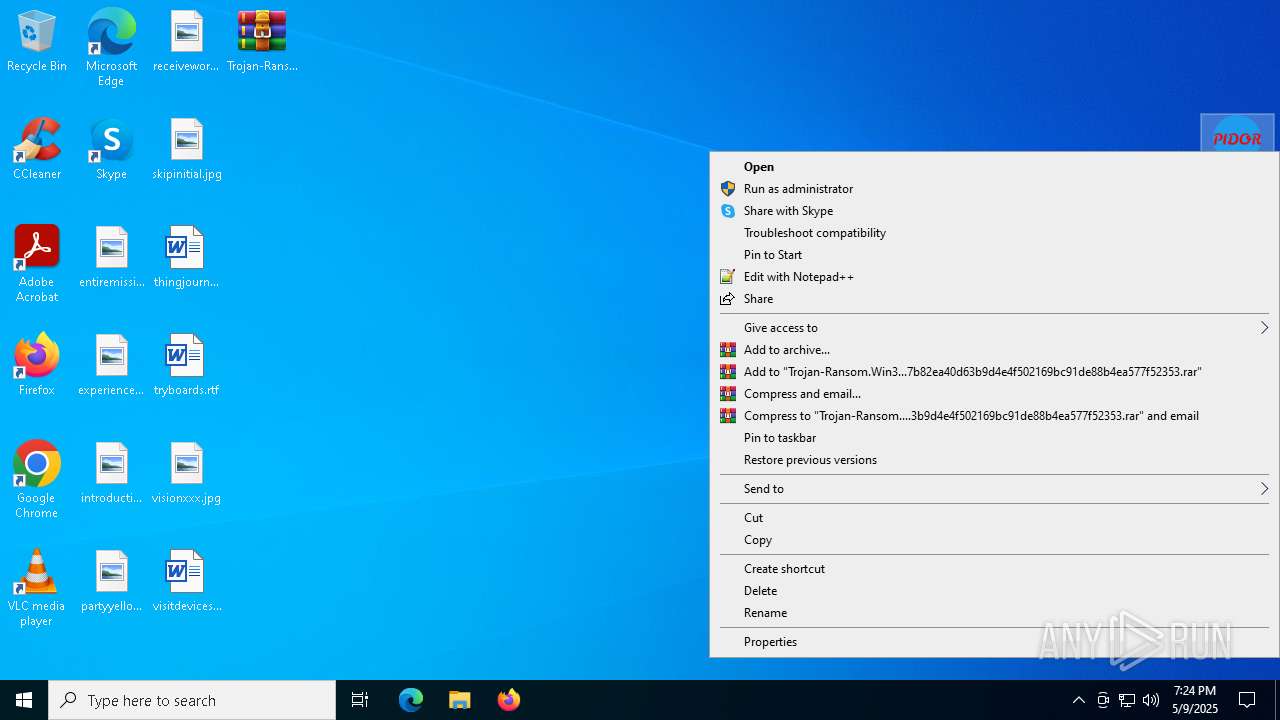
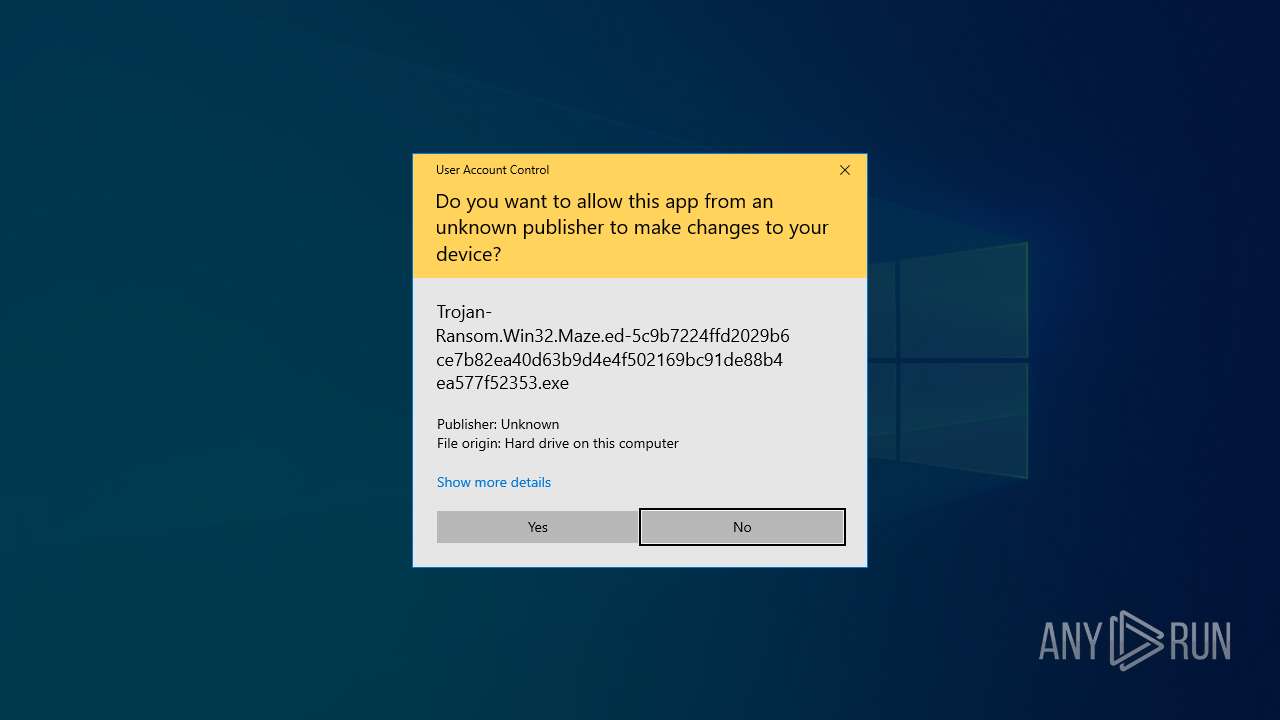
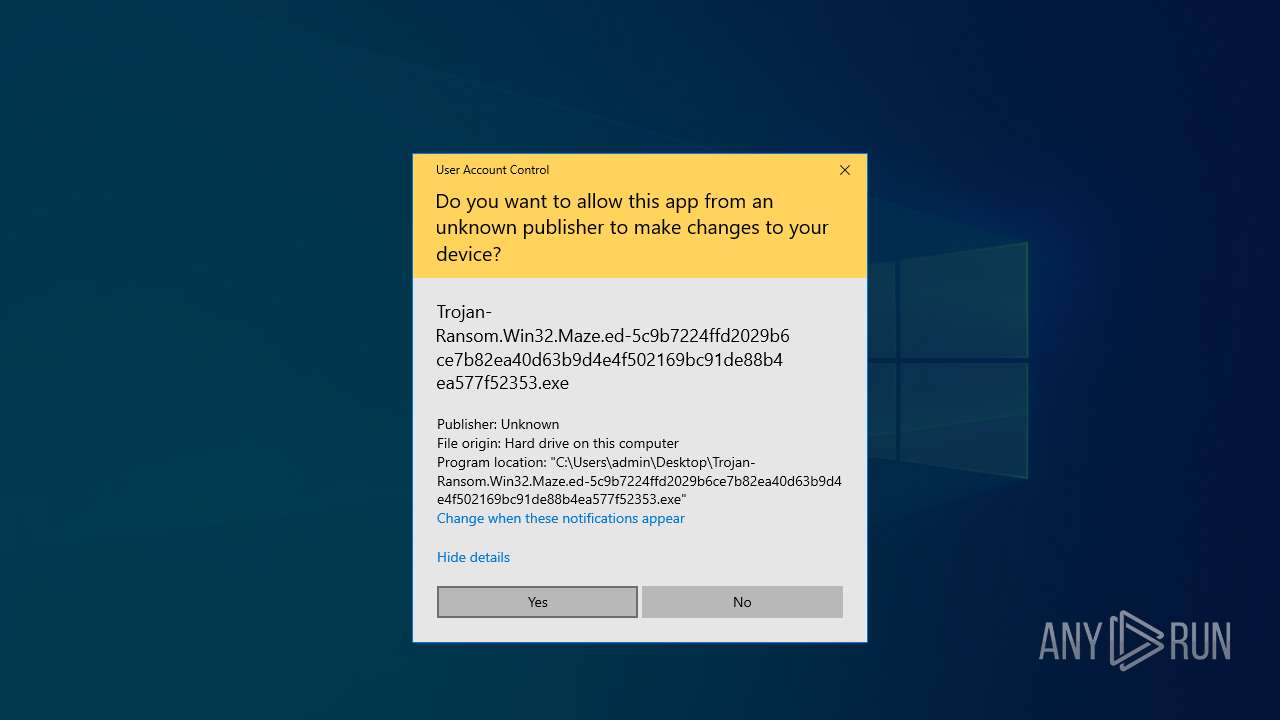
Manual execution by a user
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
- notepad.exe (PID: 5048)
Reads the machine GUID from the registry
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
Checks supported languages
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
Reads the computer name
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
Creates files in the program directory
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
Creates files or folders in the user directory
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
Checks proxy server information
- Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe (PID: 7872)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2616)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5048)
Reads the software policy settings
- slui.exe (PID: 7292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2020:05:25 06:56:58+00:00 |
| ArchivedFileName: | Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe |
Total processes
134
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
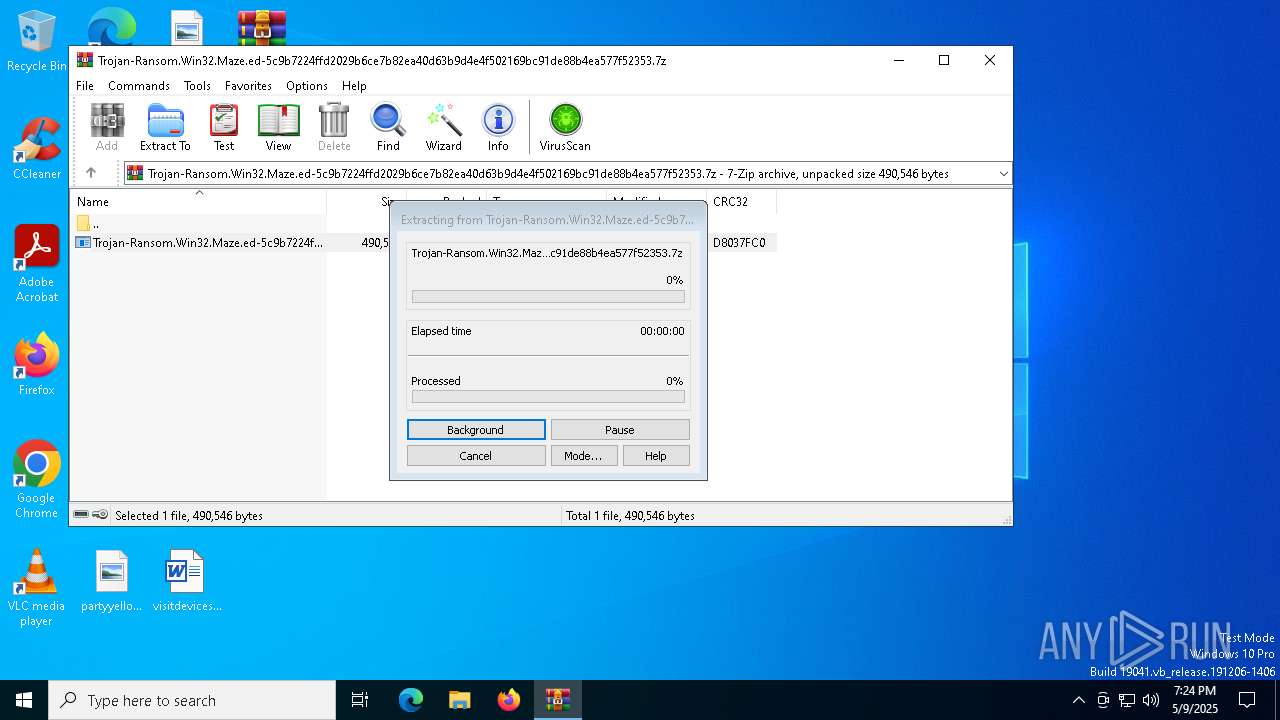
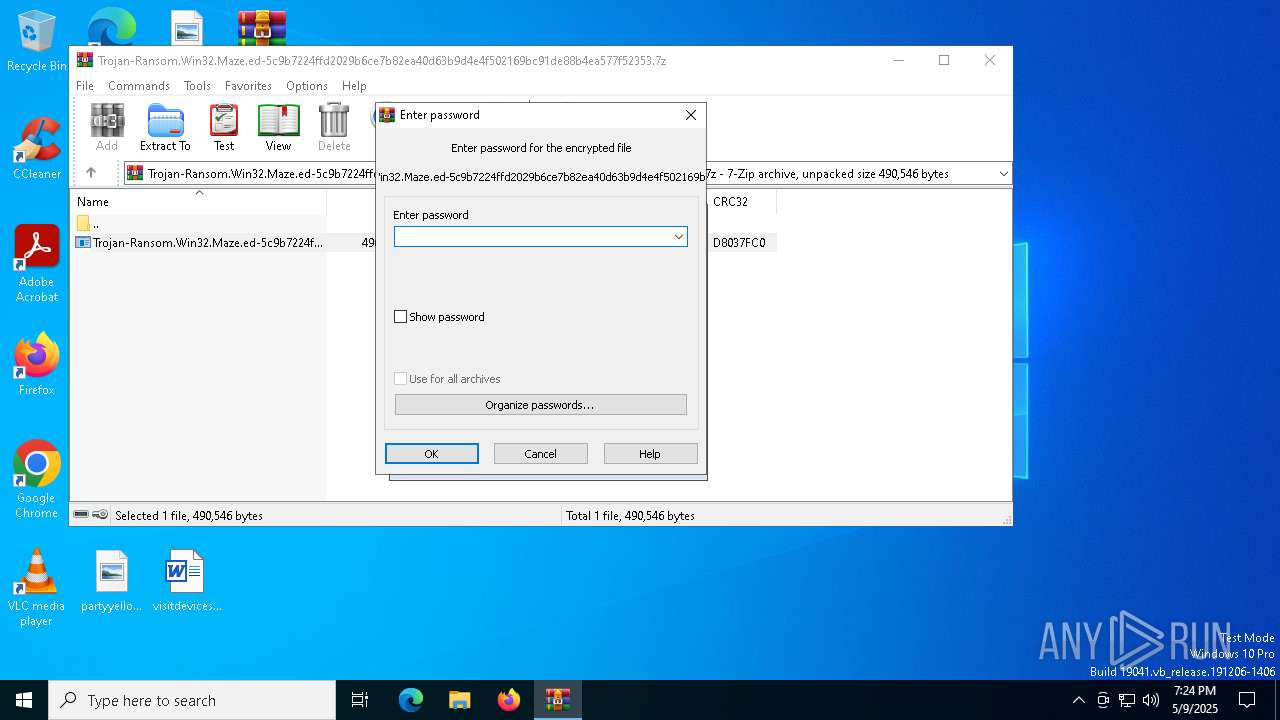
| 2616 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
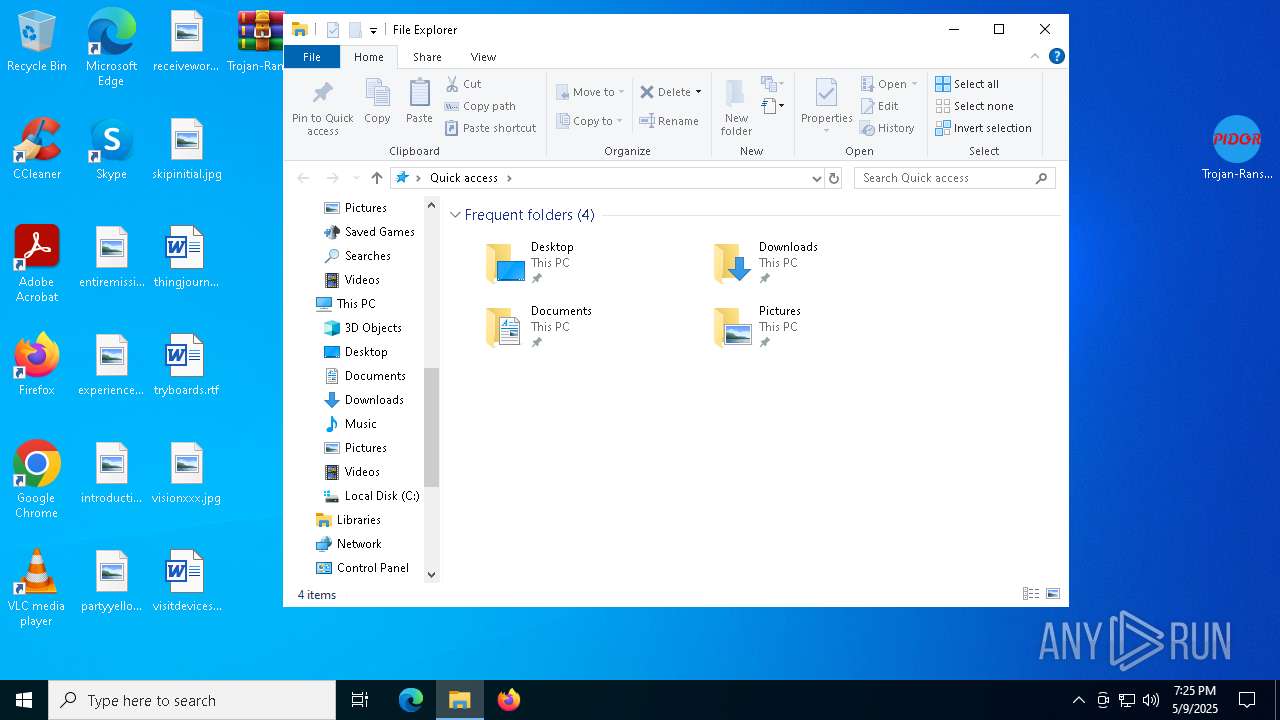
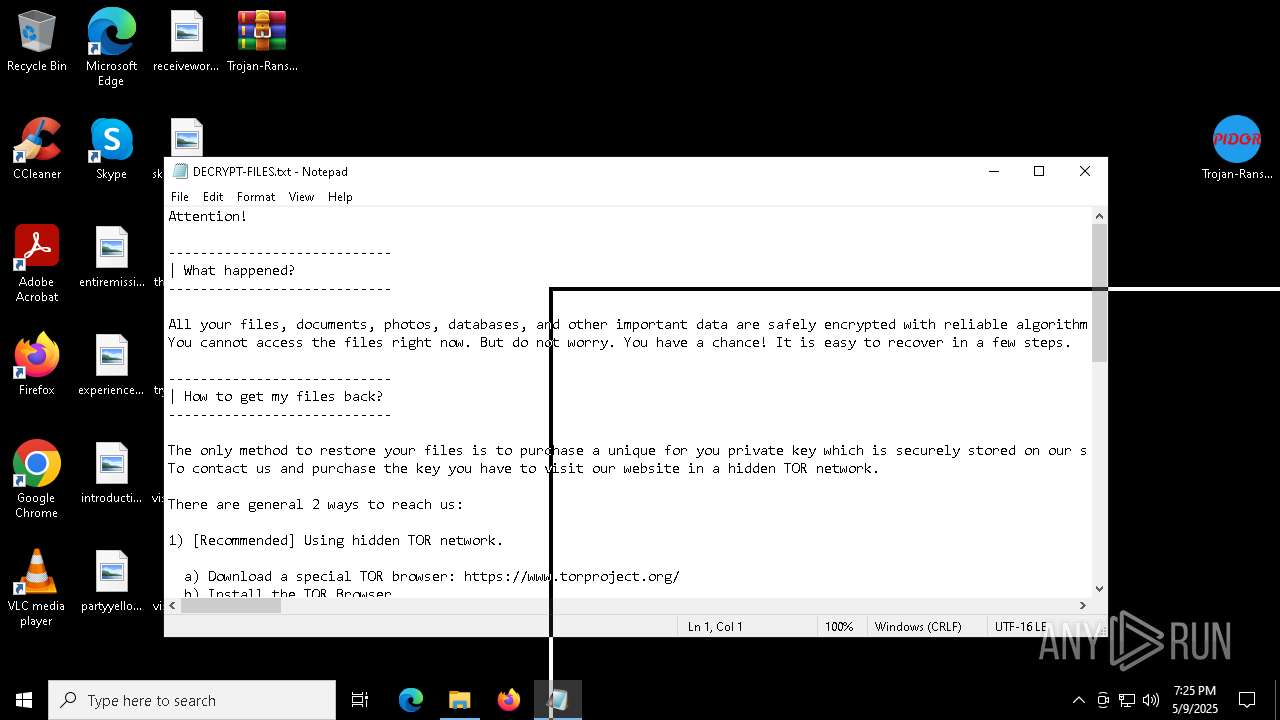
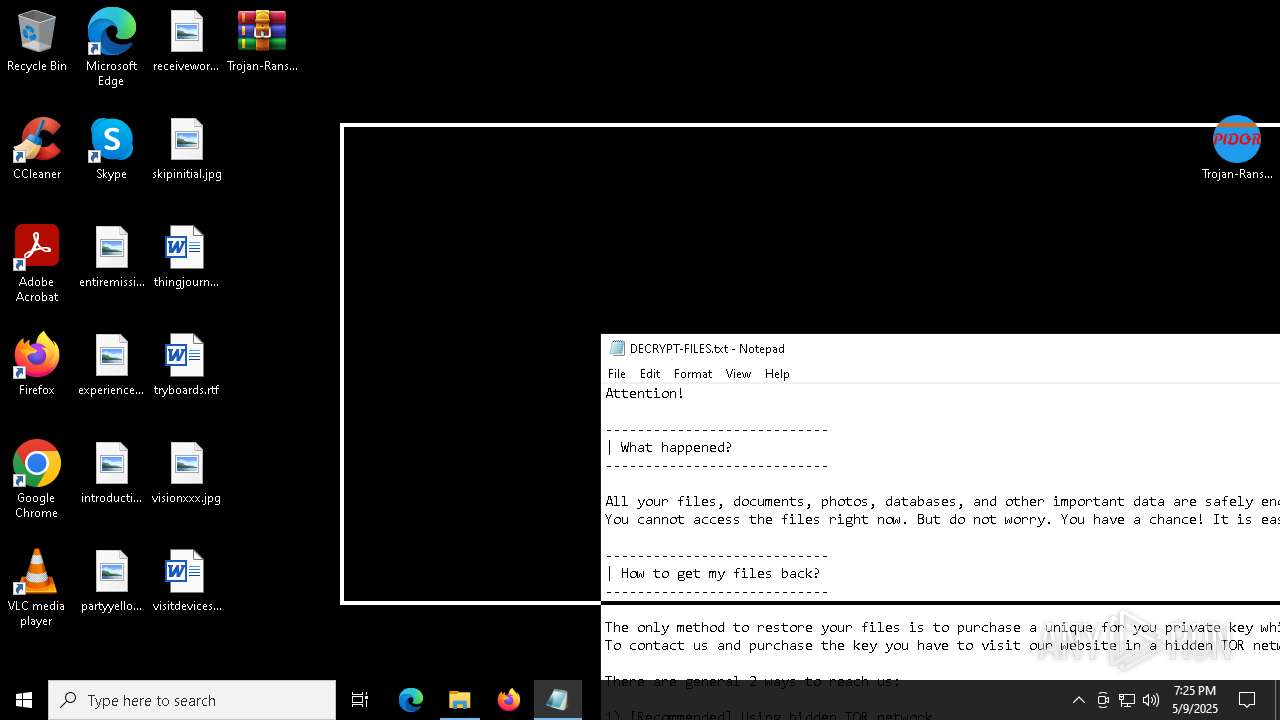
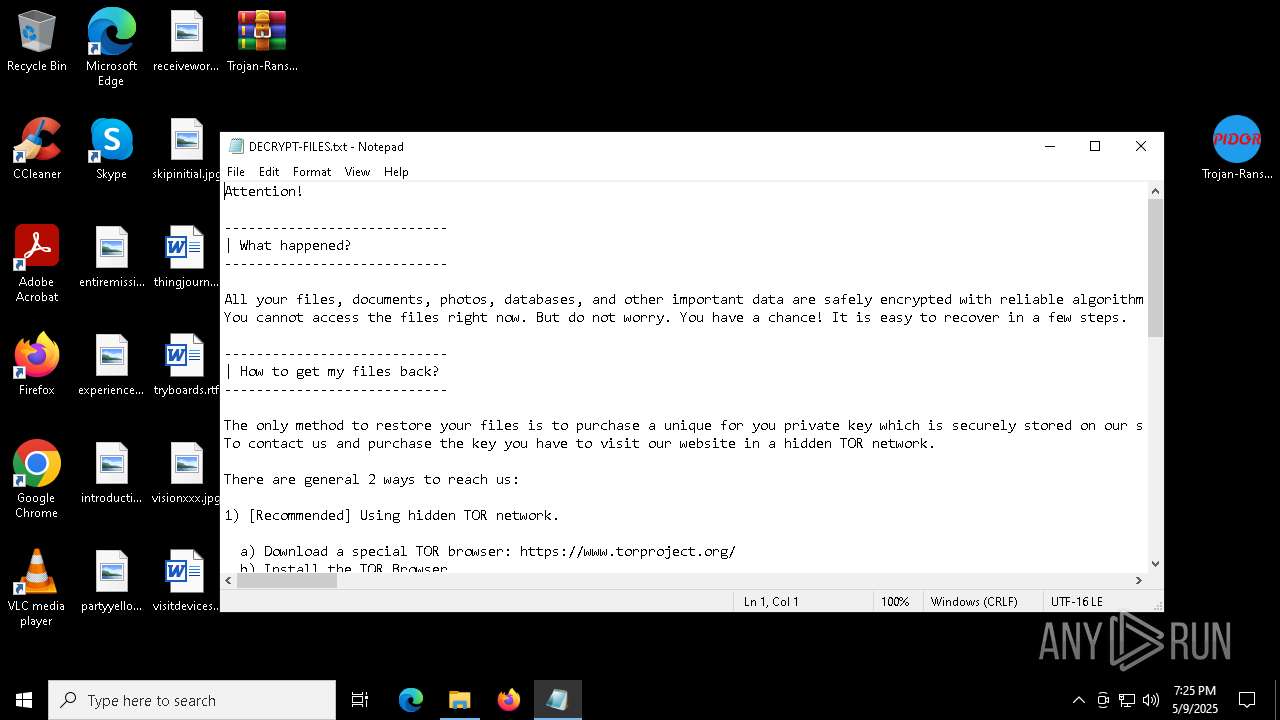
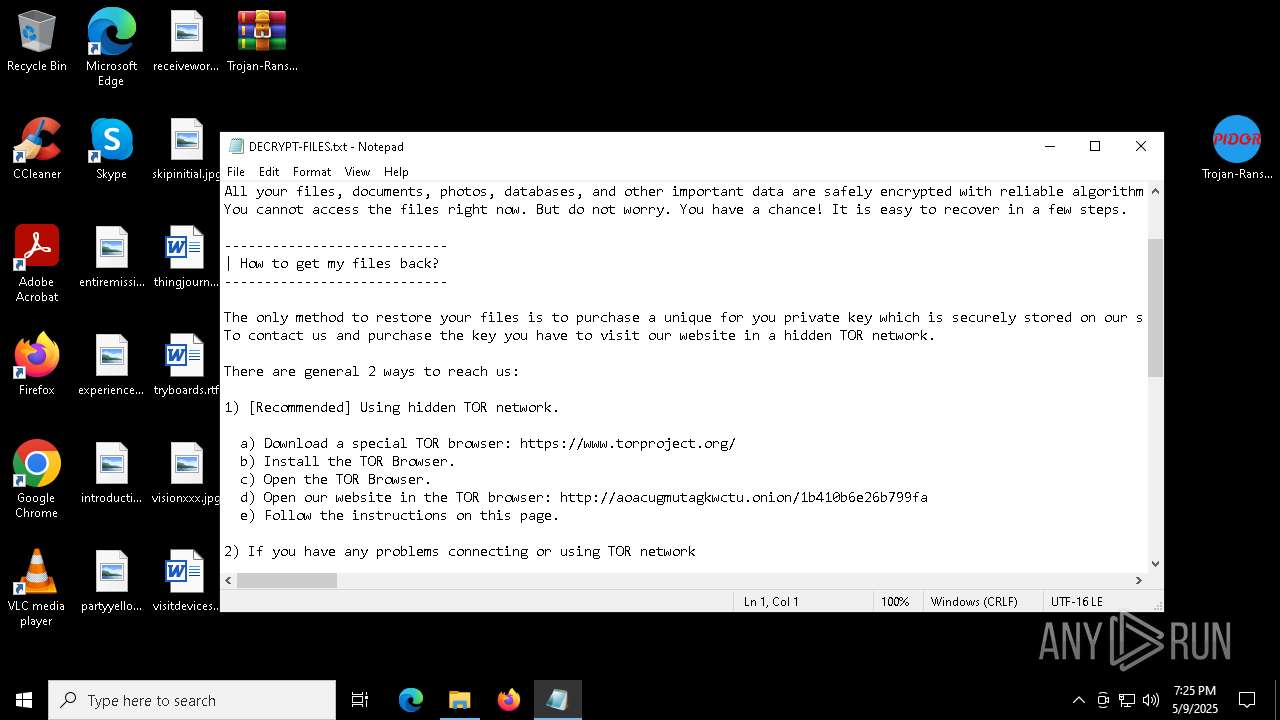
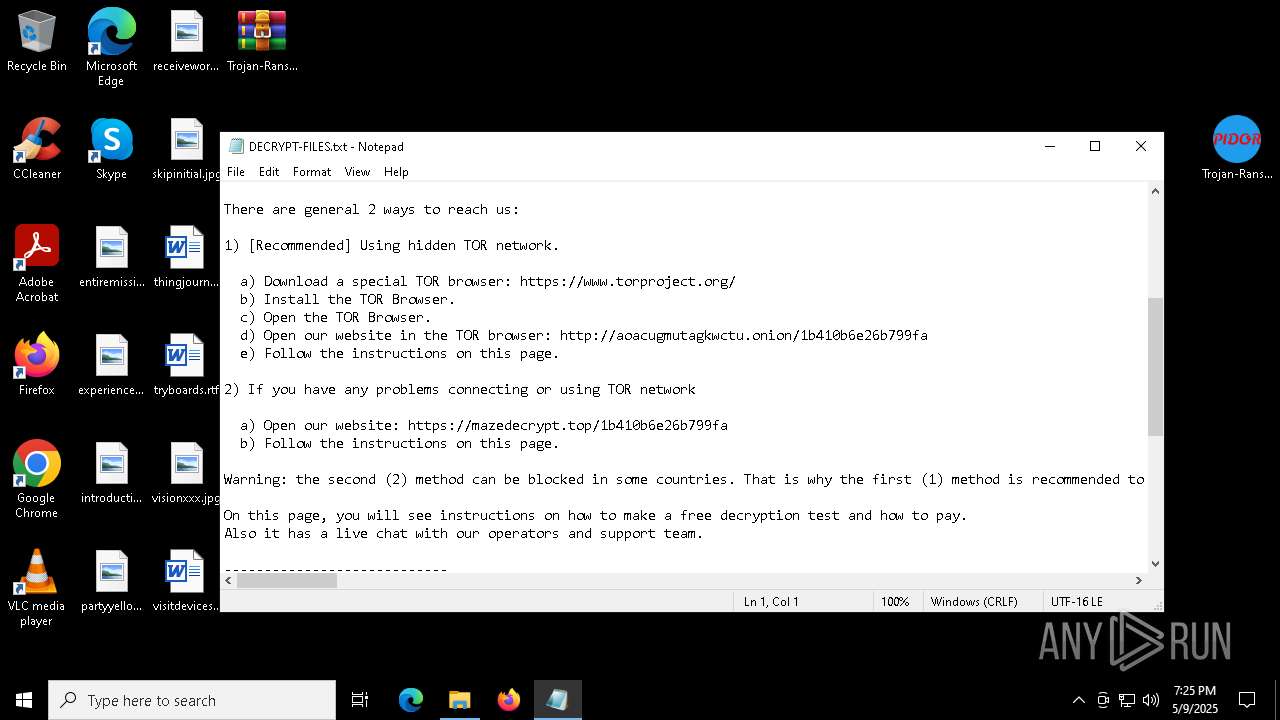
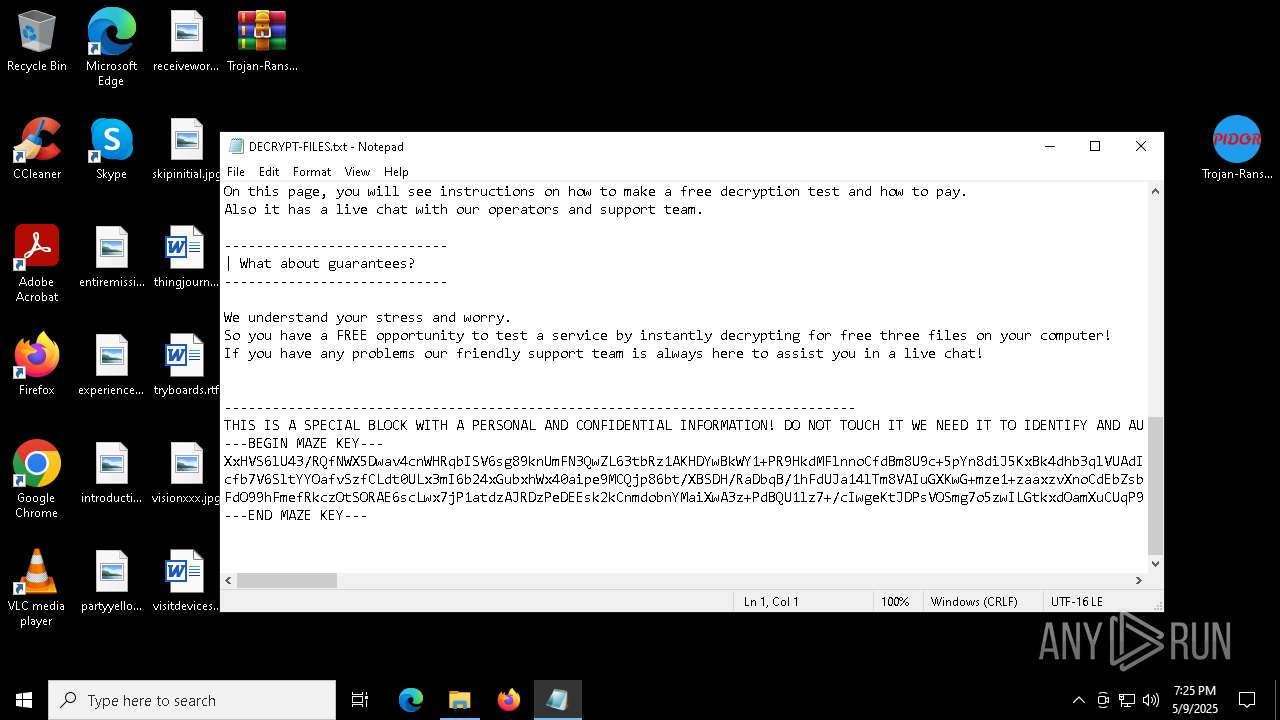
| 5048 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\DECRYPT-FILES.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5204 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7260 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7292 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7872 | "C:\Users\admin\Desktop\Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe" | C:\Users\admin\Desktop\Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
2 585
Read events
2 563
Write events
22
Delete events
0
Modification events
| (PID) Process: | (2616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.7z | |||
| (PID) Process: | (2616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2616) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
3
Suspicious files
1 050
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7872 | Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe | C:\$WinREAgent\Backup\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 7872 | Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe | C:\$WinREAgent\Backup\Winre.wim.w9XCfJi | — | |
MD5:— | SHA256:— | |||
| 7872 | Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe | C:\ProgramData\0x29A.db | binary | |
MD5:76F8F28BD51EFA03AB992FDB050C8382 | SHA256:5470F0644589685000154CB7D3F60280ACB16E39CA961CCE2C016078B303BC1B | |||
| 2616 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2616.49449\Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe | executable | |
MD5:FBA4CBB7167176990D5A8D24E9505F71 | SHA256:5C9B7224FFD2029B6CE7B82EA40D63B9D4E4F502169BC91DE88B4EA577F52353 | |||
| 7872 | Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-1000\DECRYPT-FILES.txt | binary | |
MD5:96A4C5BABB88FAB16B25AF1ACBC639A8 | SHA256:8CBC54CBCE3217A46A28084E819A8360211A4CD62F7DC5FD4A4052188F791C4B | |||
| 7872 | Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe | C:\$WinREAgent\Scratch\update.wim | — | |
MD5:— | SHA256:— | |||
| 7872 | Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe | C:\$WinREAgent\Scratch\update.wim.CSbo3R | — | |
MD5:— | SHA256:— | |||
| 7872 | Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe | C:\$Recycle.Bin\S-1-5-18\DECRYPT-FILES.txt | binary | |
MD5:96A4C5BABB88FAB16B25AF1ACBC639A8 | SHA256:8CBC54CBCE3217A46A28084E819A8360211A4CD62F7DC5FD4A4052188F791C4B | |||
| 7872 | Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-1001\DECRYPT-FILES.txt | binary | |
MD5:96A4C5BABB88FAB16B25AF1ACBC639A8 | SHA256:8CBC54CBCE3217A46A28084E819A8360211A4CD62F7DC5FD4A4052188F791C4B | |||
| 7872 | Trojan-Ransom.Win32.Maze.ed-5c9b7224ffd2029b6ce7b82ea40d63b9d4e4f502169bc91de88b4ea577f52353.exe | C:\$WinREAgent\Backup\DECRYPT-FILES.txt | binary | |
MD5:96A4C5BABB88FAB16B25AF1ACBC639A8 | SHA256:8CBC54CBCE3217A46A28084E819A8360211A4CD62F7DC5FD4A4052188F791C4B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8064 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8064 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
8064 | SIHClient.exe | 52.149.20.212:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |