| File name: | demo-sample.msg |
| Full analysis: | https://app.any.run/tasks/c60722ca-3848-42ce-90e3-828b2f79a56e |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | June 21, 2025, 06:41:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | A67B03F57933663D0779115B74A4B2E3 |
| SHA1: | 5C4D663A15E428F1367A42406D5C7B78524B48F9 |
| SHA256: | A6189266C815831C91E79464638DA6249C3D27D6EE06C524434A99FE9F7BB689 |
| SSDEEP: | 24576:MafQNcq5V8m16Yru0Oec7UYPJROYDU5m8XUBt4wZlGYCq1wSpdJkkN4+:MafQWq5V8m16Yru0OecAYPJROY+m8kBL |
MALICIOUS
LOKIBOT mutex has been found
- cvtres.exe (PID: 4544)
Steals credentials from Web Browsers
- cvtres.exe (PID: 4544)
Actions looks like stealing of personal data
- cvtres.exe (PID: 4544)
Scans artifacts that could help determine the target
- cvtres.exe (PID: 4544)
Lokibot is detected
- cvtres.exe (PID: 4544)
LOKIBOT has been detected (SURICATA)
- svchost.exe (PID: 2200)
Connects to the CnC server
- svchost.exe (PID: 2200)
LOKIBOT has been detected (YARA)
- cvtres.exe (PID: 4544)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4888)
- cvtres.exe (PID: 4544)
Executable content was dropped or overwritten
- cvtres.exe (PID: 4544)
Process drops legitimate windows executable
- cvtres.exe (PID: 4544)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2200)
INFO
Reads the software policy settings
- slui.exe (PID: 6948)
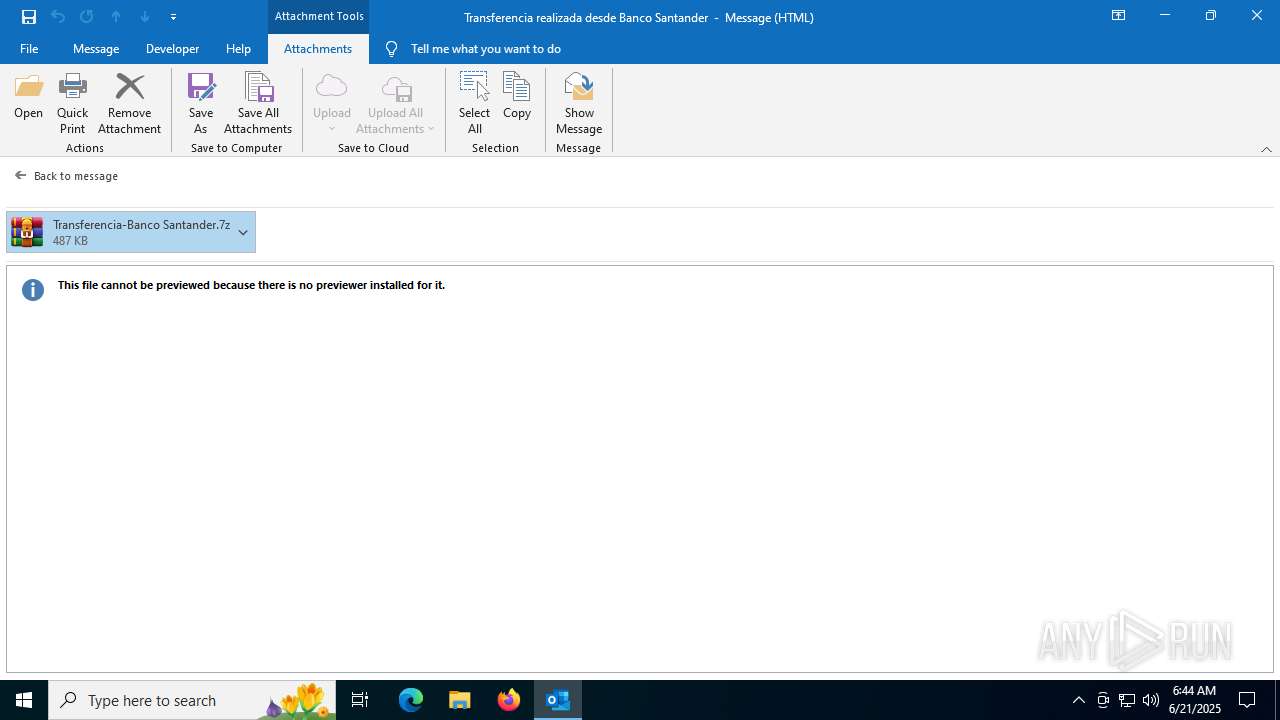
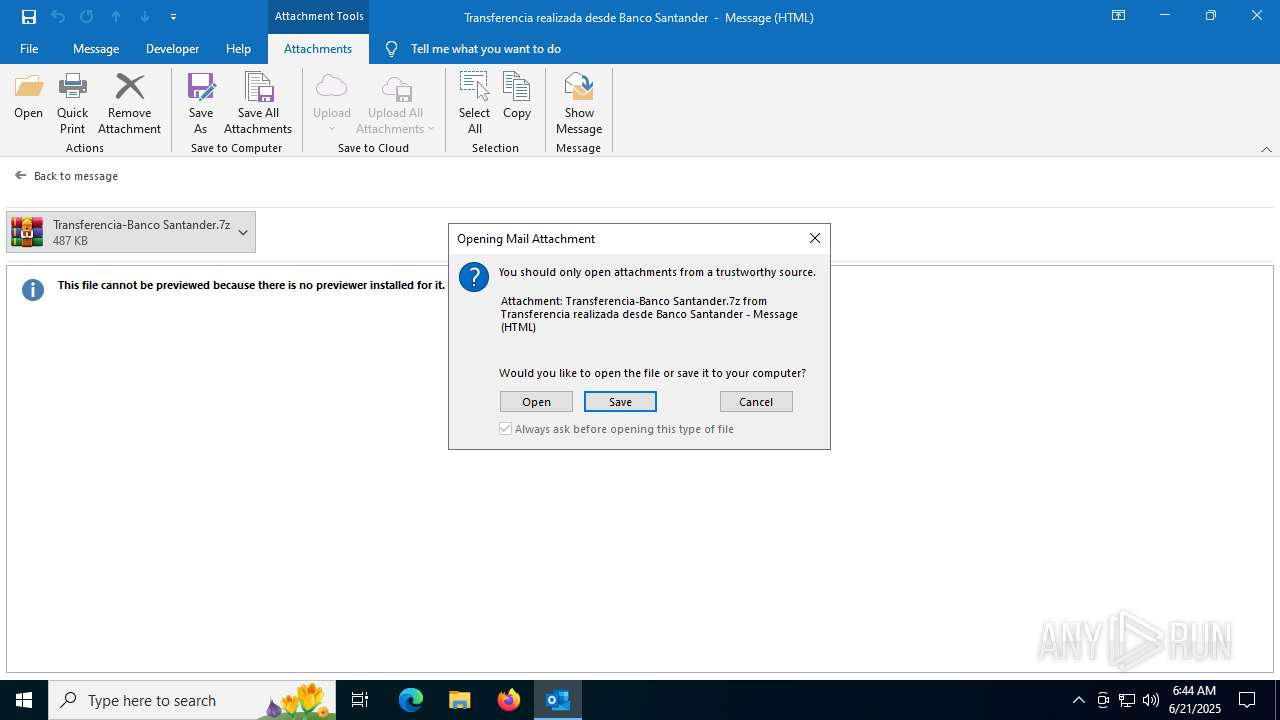
Email with attachments
- OUTLOOK.EXE (PID: 3656)
Checks proxy server information
- slui.exe (PID: 6948)
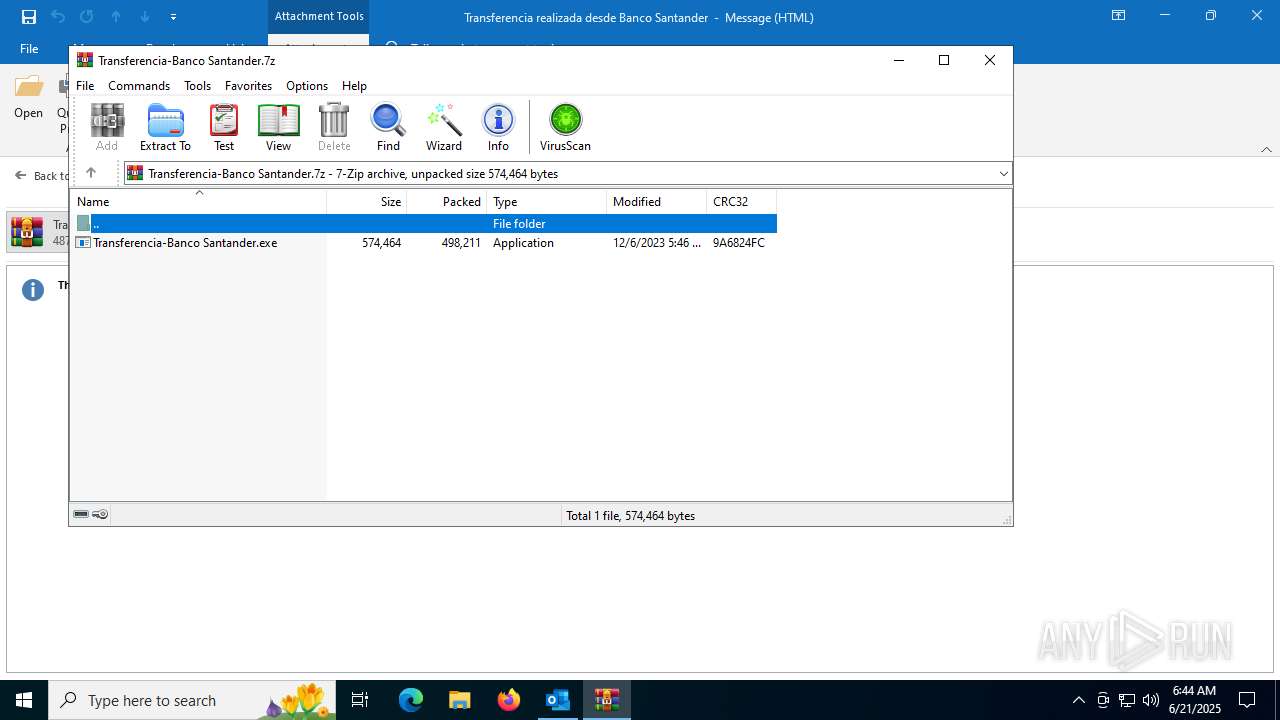
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4888)
Reads the machine GUID from the registry
- Transferencia-Banco Santander.exe (PID: 7092)
- cvtres.exe (PID: 4544)
Checks supported languages
- cvtres.exe (PID: 4544)
- Transferencia-Banco Santander.exe (PID: 7092)
Reads the computer name
- Transferencia-Banco Santander.exe (PID: 7092)
- cvtres.exe (PID: 4544)
Creates files or folders in the user directory
- cvtres.exe (PID: 4544)
Reads Microsoft Office registry keys
- cvtres.exe (PID: 4544)
The sample compiled with english language support
- cvtres.exe (PID: 4544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
LokiBot
(PID) Process(4544) cvtres.exe
C2http://dcqapz.shop/PWS/fre.php
Decoys (4)kbfvzoboss.bid/alien/fre.php
alphastand.trade/alien/fre.php
alphastand.win/alien/fre.php
alphastand.top/alien/fre.php
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
146
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1728 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "D76296F3-01A8-44C2-9991-EDD046EAE0D3" "810D241A-2C99-44DF-9CF7-CFF8196668C8" "3656" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3656 | "C:\Program Files\Microsoft Office\Root\Office16\OUTLOOK.EXE" /f C:\Users\admin\AppData\Local\Temp\demo-sample.msg | C:\Program Files\Microsoft Office\root\Office16\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 4544 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | Transferencia-Banco Santander.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Version: 14.32.31326.0 Modules
LokiBot(PID) Process(4544) cvtres.exe C2http://dcqapz.shop/PWS/fre.php Decoys (4)kbfvzoboss.bid/alien/fre.php alphastand.trade/alien/fre.php alphastand.win/alien/fre.php alphastand.top/alien/fre.php | |||||||||||||||
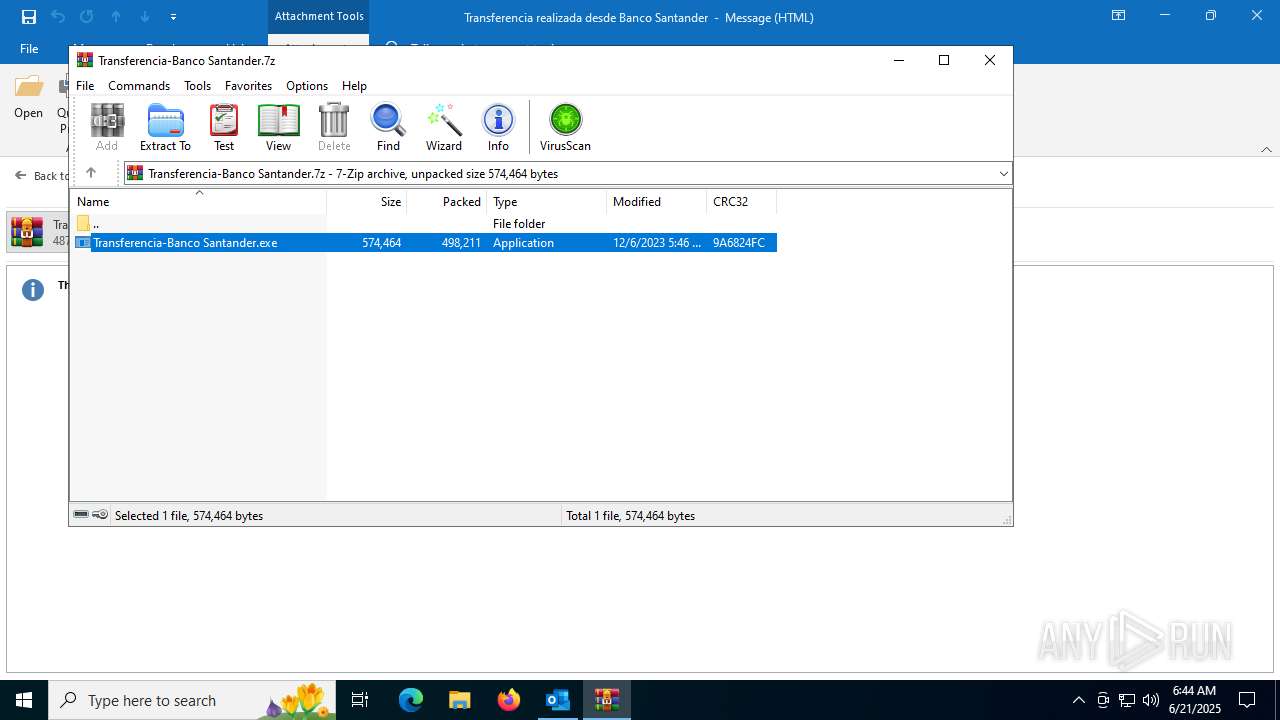
| 4888 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\M8Y5CRKZ\Transferencia-Banco Santander.7z" | C:\Program Files\WinRAR\WinRAR.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6948 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7092 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4888.9552\Transferencia-Banco Santander.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4888.9552\Transferencia-Banco Santander.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: MKiJ887777 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
15 044
Read events
13 810
Write events
1 085
Delete events
149
Modification events
| (PID) Process: | (3656) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 6 |
Value: 01941A000000001000B24E9A3E06000000000000000600000000000000 | |||
| (PID) Process: | (3656) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\OUTLOOK\3656 |
| Operation: | write | Name: | 0 |
Value: 0B0E1080F967DCD25CC34995F8827E5E03A00A230046ACDD9ED9F9CEF8ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511C81CD2120B6F00750074006C006F006F006B002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (3656) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootCommand |
Value: | |||
| (PID) Process: | (3656) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootFailureCount |
Value: | |||
| (PID) Process: | (3656) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3656) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | CantBootResolution |
Value: BootSuccess | |||
| (PID) Process: | (3656) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | ProfileBeingOpened |
Value: Outlook | |||
| (PID) Process: | (3656) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | SessionId |
Value: C3D8E96E-C1AF-4750-8D52-F4E28119C131 | |||
| (PID) Process: | (3656) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics\BootDiagnosticsDataPreviousSession |
| Operation: | write | Name: | BootDiagnosticsLogFile |
Value: C:\Users\admin\AppData\Local\Temp\Outlook Logging\OUTLOOK_16_0_16026_20146-20240718T1116060318-1644.etl | |||
| (PID) Process: | (3656) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | ProfileBeingOpened |
Value: | |||
Executable files
2
Suspicious files
10
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3656 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 3656 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.MSO\8BF403DE.dat | image | |
MD5:CA7322F8A70CD9D7D921E5D03C37F024 | SHA256:D519FF233BF51A9D82D98F4CEC7980F1138E249822D35E23C20030442CA3F7BD | |||
| 3656 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:CC2DAA9F68F0A3F1C009273E8A16EB31 | SHA256:F93F20E5B5FA6370BDE64B114517ECE028935251D11238BF7727E1EE19EA2F3E | |||
| 3656 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:C1AAE26D7E80B29DDF9717F215B4CDAE | SHA256:0D5FEA24678115FD518766556D0DE738A55C06FD1BC0E55D7E48EB11EA16318A | |||
| 3656 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TableViewPreviewPrefs_2_D1BAF8B61CF1A04391C283A2B4BD92ED.dat | xml | |
MD5:0E092DB99AEE99FDFF9B5B222C732CFD | SHA256:D1614AD99ADED9F6F5C1BE7FE7FFA5124BD04A526580DA3818EA8A954E852AA6 | |||
| 3656 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
| 3656 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntitiesUpdated.bin | text | |
MD5:BFBFBA2276C2148AE1BEC6B3C677D9A6 | SHA256:C57A13719D0D9F4B82449A6E63DD368416542A7B29BAA0055082FB9061555EA4 | |||
| 3656 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:6DEF8DCADD28C66981250D30A9C9088B | SHA256:401C6562667A7E9B076319927DA638BC9D6B921E162371078AC1181E9865CE46 | |||
| 3656 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:1EF7968BC740DB4958EE9EDCFE4F86E1 | SHA256:7E3ABDB84C5EE87B3083DEE9EB1FA0BD445C962A8B563C7D80671A7283308CF5 | |||
| 3656 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\M8Y5CRKZ\Transferencia-Banco Santander.7z:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
35
DNS requests
25
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7072 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3656 | OUTLOOK.EXE | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
1932 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1932 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4816 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3656 | OUTLOOK.EXE | 52.123.128.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3656 | OUTLOOK.EXE | 23.200.86.240:443 | omex.cdn.office.net | Akamai International B.V. | FR | whitelisted |
3656 | OUTLOOK.EXE | 52.111.231.8:443 | messaging.lifecycle.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7072 | svchost.exe | 20.190.160.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Domain Observed Used for C2 Detected | MALWARE [ANY.RUN] Lokibot CnC related domain (dcqapz .shop) |