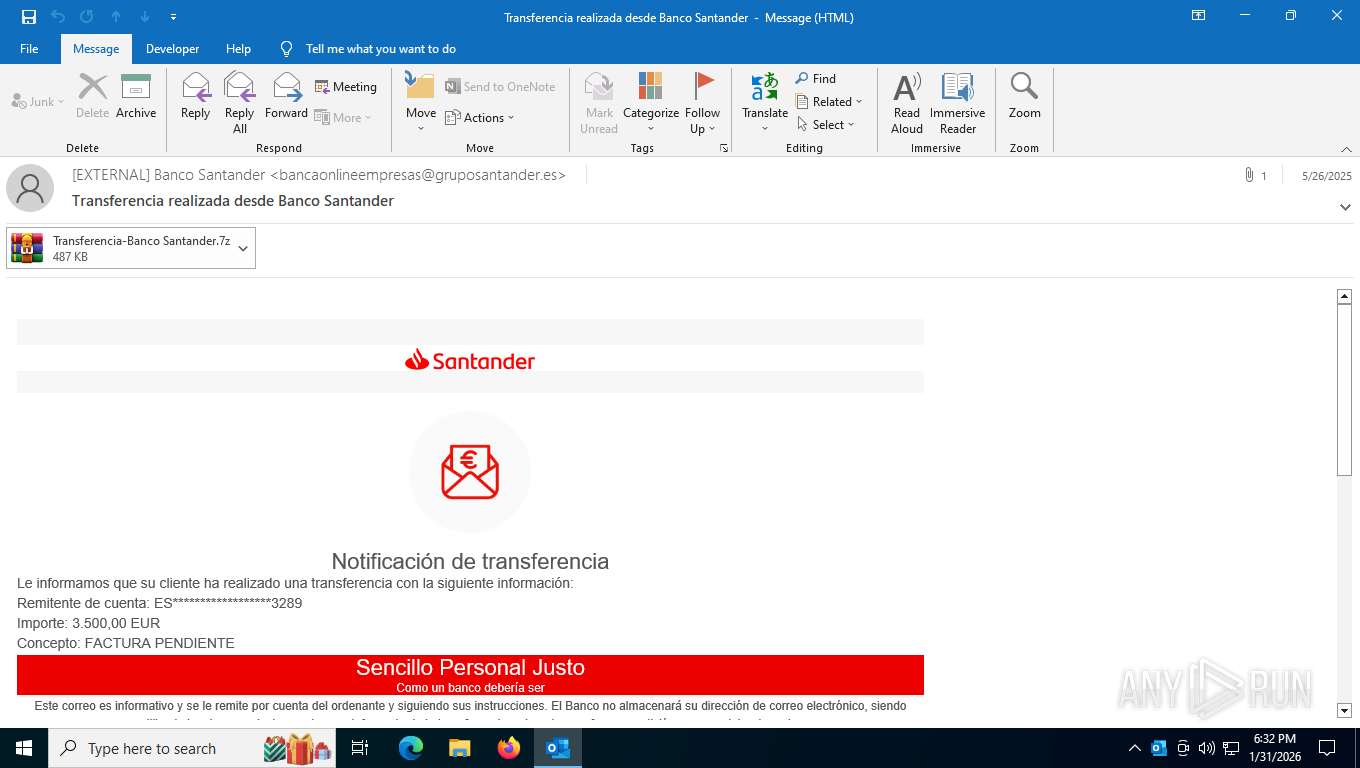
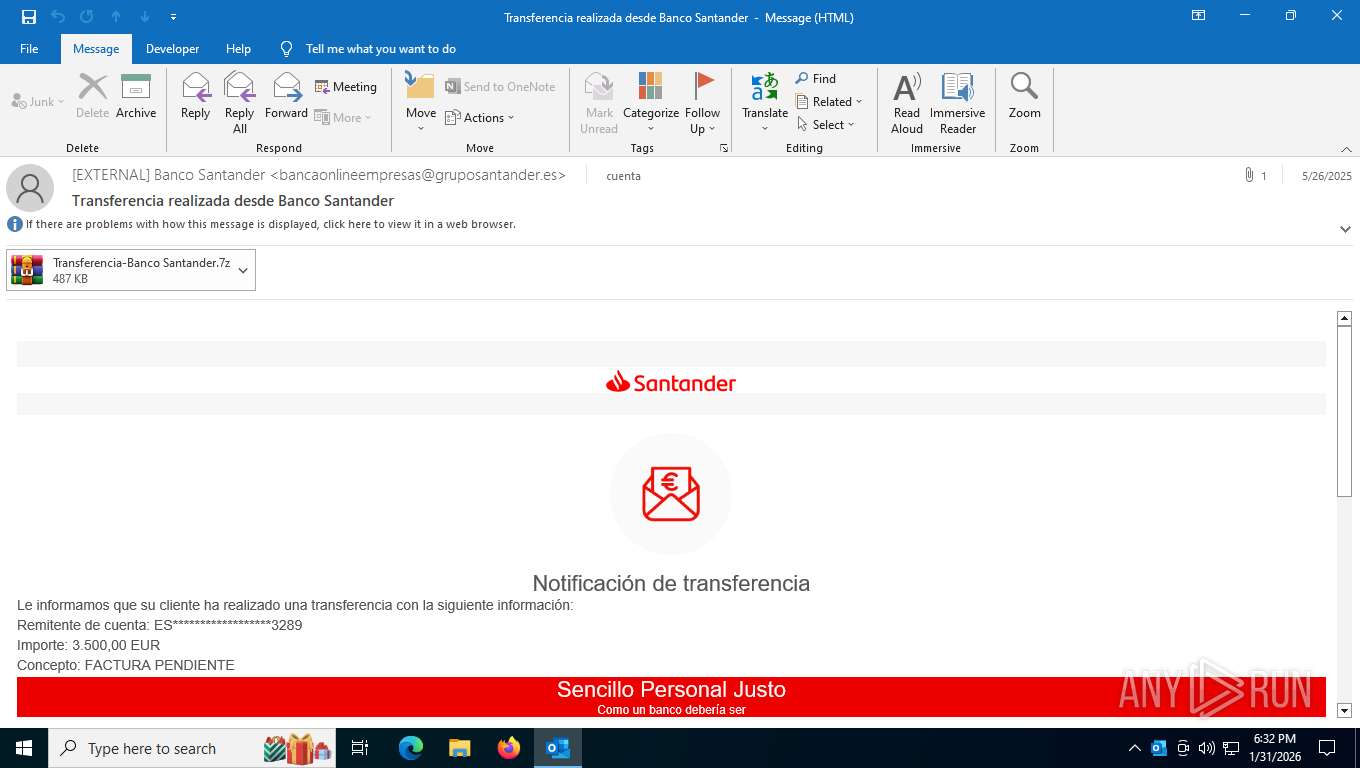
| File name: | demo-sample.msg |
| Full analysis: | https://app.any.run/tasks/ae9c12dc-7444-411a-8c78-2a24e3abbc90 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | January 31, 2026, 23:32:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
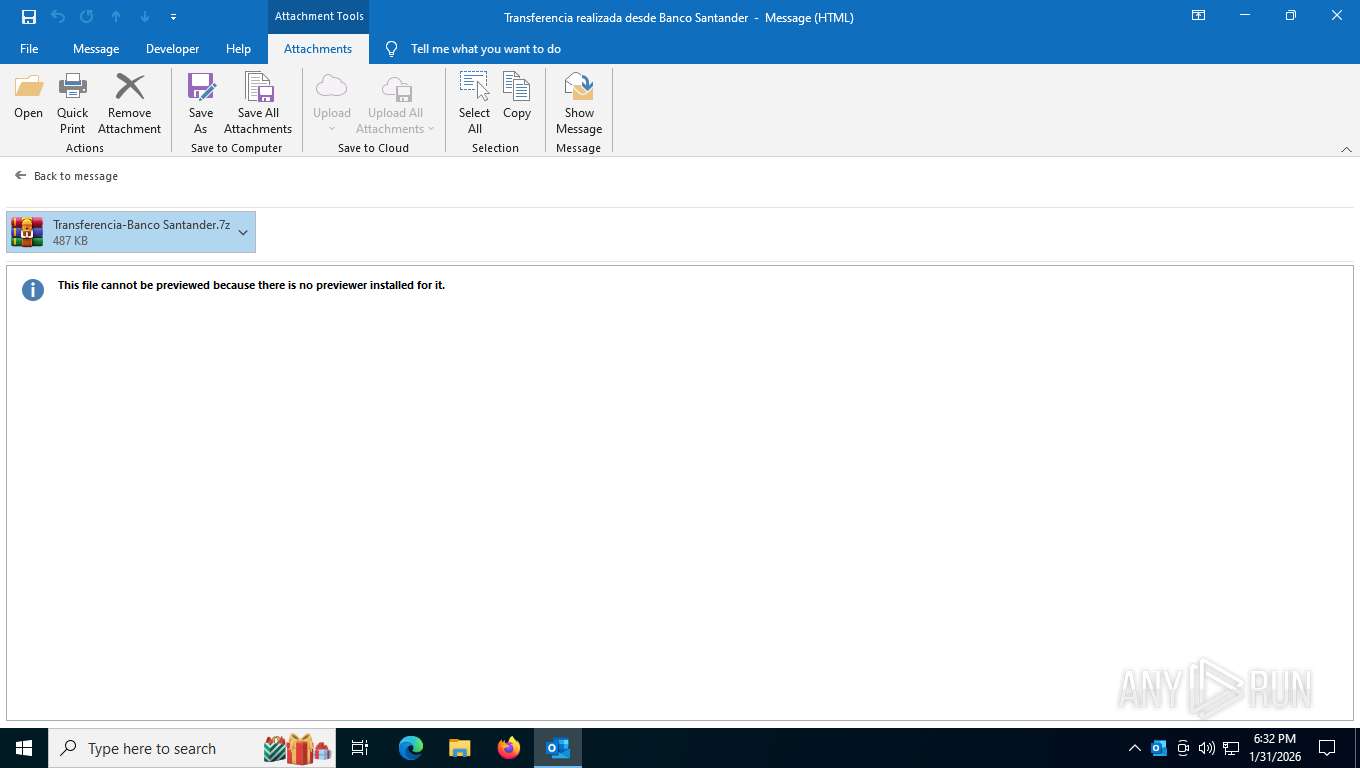
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | A67B03F57933663D0779115B74A4B2E3 |
| SHA1: | 5C4D663A15E428F1367A42406D5C7B78524B48F9 |
| SHA256: | A6189266C815831C91E79464638DA6249C3D27D6EE06C524434A99FE9F7BB689 |
| SSDEEP: | 24576:MafQNcq5V8m16Yru0Oec7UYPJROYDU5m8XUBt4wZlGYCq1wSpdJkkN4+:MafQWq5V8m16Yru0OecAYPJROY+m8kBL |
MALICIOUS
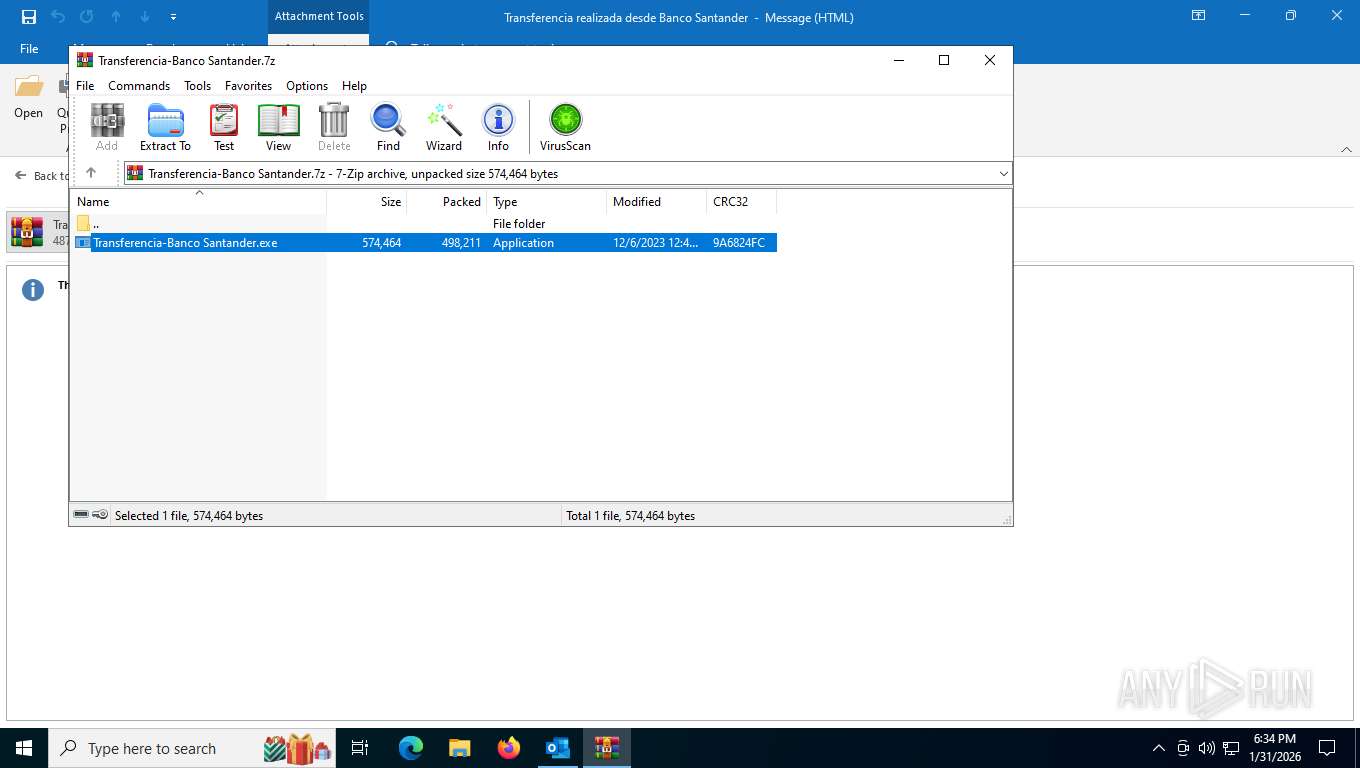
Generic archive extractor
- OUTLOOK.EXE (PID: 6928)
LOKIBOT mutex has been found
- cvtres.exe (PID: 7652)
- cvtres.exe (PID: 7920)
- cvtres.exe (PID: 5600)
Actions looks like stealing of personal data
- cvtres.exe (PID: 7652)
Steals credentials from Web Browsers
- cvtres.exe (PID: 7652)
Scans artifacts that could help determine the target
- cvtres.exe (PID: 7652)
Connects to the CnC server
- cvtres.exe (PID: 7652)
- svchost.exe (PID: 2292)
Lokibot is detected
- cvtres.exe (PID: 7652)
LOKIBOT has been detected (SURICATA)
- svchost.exe (PID: 2292)
- cvtres.exe (PID: 7652)
SUSPICIOUS
Possible stealing from browsers
- cvtres.exe (PID: 7652)
Possible stealing of FTP data
- cvtres.exe (PID: 7652)
Possible stealing of messenger data
- cvtres.exe (PID: 7652)
Possible stealing of email data
- cvtres.exe (PID: 7652)
Possible stealing from notes
- cvtres.exe (PID: 7652)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2292)
- cvtres.exe (PID: 7652)
Executable content was dropped or overwritten
- cvtres.exe (PID: 7652)
Process drops legitimate windows executable
- cvtres.exe (PID: 7652)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4544)
Reads the computer name
- Transferencia-Banco Santander.exe (PID: 5732)
- cvtres.exe (PID: 7652)
- Transferencia-Banco Santander.exe (PID: 8956)
- Transferencia-Banco Santander.exe (PID: 3332)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4544)
- cvtres.exe (PID: 7652)
Reads Microsoft Office registry keys
- cvtres.exe (PID: 7652)
Checks supported languages
- cvtres.exe (PID: 7652)
- Transferencia-Banco Santander.exe (PID: 5732)
- Transferencia-Banco Santander.exe (PID: 8956)
- cvtres.exe (PID: 7920)
- cvtres.exe (PID: 5600)
- Transferencia-Banco Santander.exe (PID: 3332)
Reads the machine GUID from the registry
- Transferencia-Banco Santander.exe (PID: 5732)
- cvtres.exe (PID: 7652)
- cvtres.exe (PID: 5600)
- Transferencia-Banco Santander.exe (PID: 3332)
- cvtres.exe (PID: 7920)
- Transferencia-Banco Santander.exe (PID: 8956)
The sample compiled with english language support
- cvtres.exe (PID: 7652)
Checks proxy server information
- slui.exe (PID: 9032)
Creates files or folders in the user directory
- cvtres.exe (PID: 7652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
163
Monitored processes
13
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1492 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | Transferencia-Banco Santander.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 4294967295 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
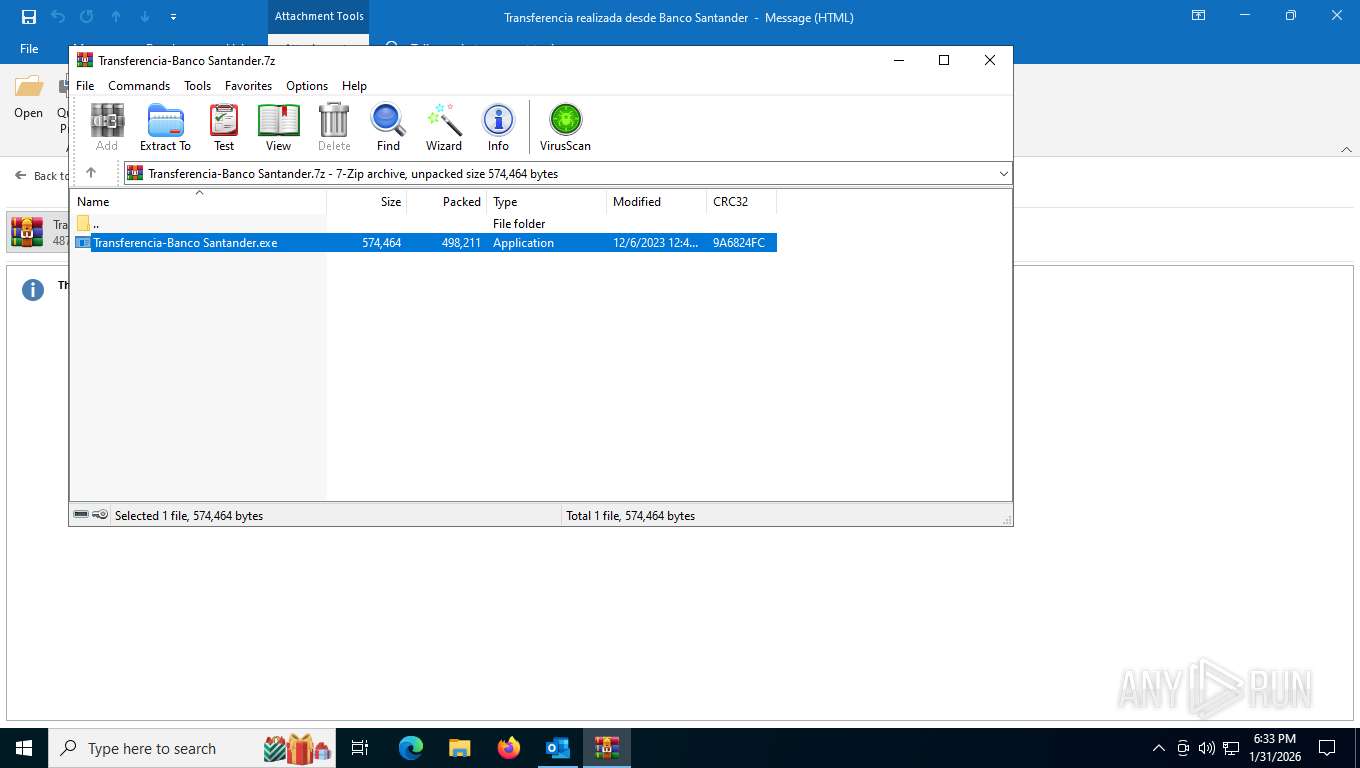
| 3332 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4544.10261\Transferencia-Banco Santander.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4544.10261\Transferencia-Banco Santander.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: MKiJ887777 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3536 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | Transferencia-Banco Santander.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 4294967295 Version: 14.32.31326.0 Modules
| |||||||||||||||
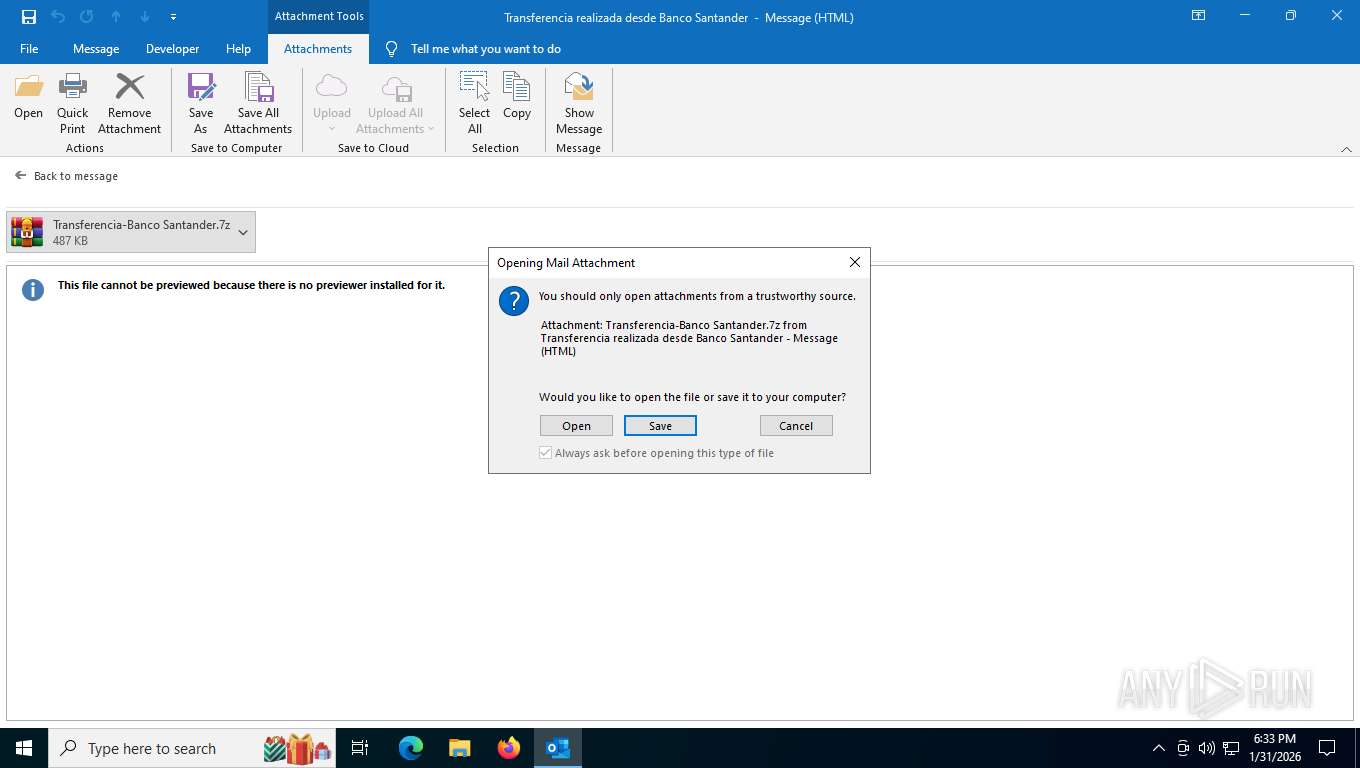
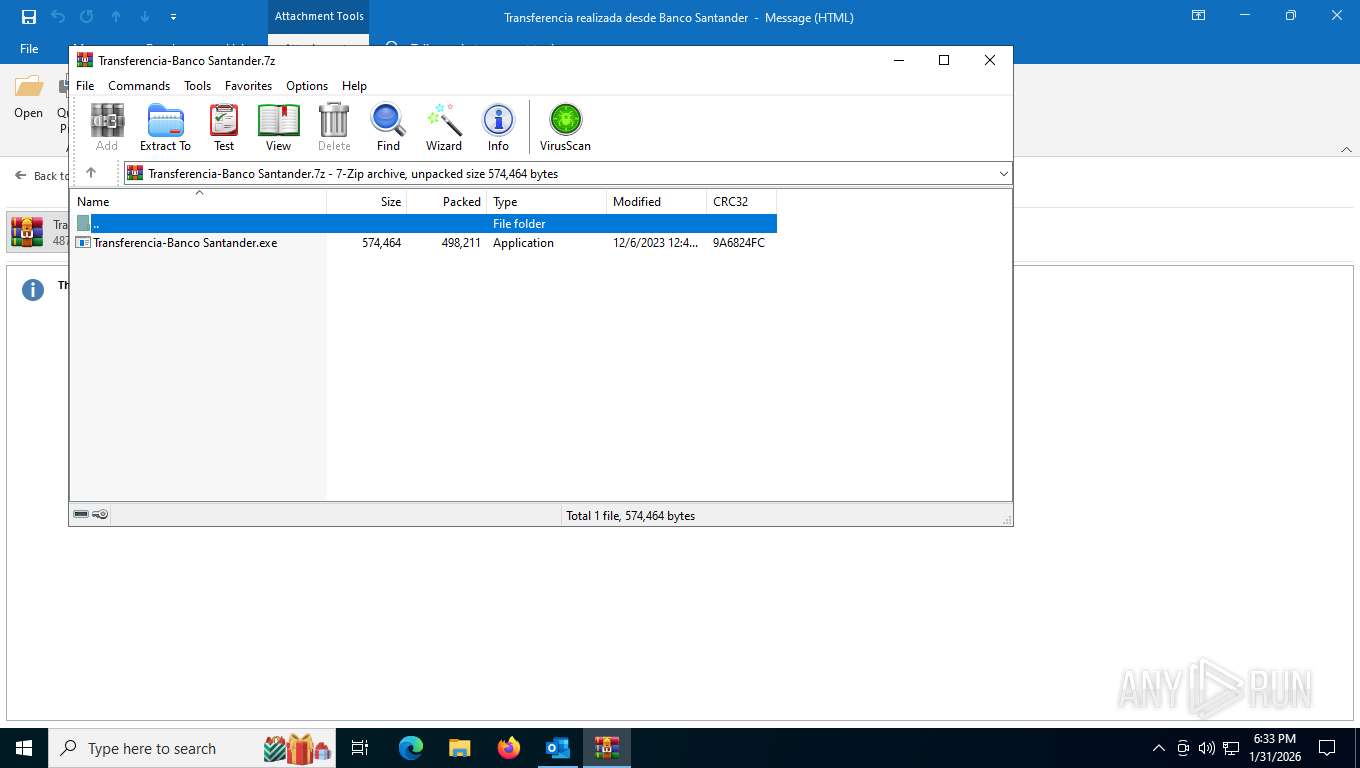
| 4544 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\4N6JHLSF\Transferencia-Banco Santander.7z" | C:\Program Files\WinRAR\WinRAR.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4700 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "29722A5C-C2F0-40F2-B1E9-81CE76FA1FF0" "A1A9BE21-304F-4B37-987D-269E9104D0D4" "6928" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 5600 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | Transferencia-Banco Santander.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 5732 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4544.7318\Transferencia-Banco Santander.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4544.7318\Transferencia-Banco Santander.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: MKiJ887777 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6928 | "C:\Program Files\Microsoft Office\Root\Office16\OUTLOOK.EXE" /f C:\Users\admin\AppData\Local\Temp\demo-sample.msg | C:\Program Files\Microsoft Office\root\Office16\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 7652 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | Transferencia-Banco Santander.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Version: 14.32.31326.0 Modules
| |||||||||||||||
Total events
19 570
Read events
18 363
Write events
1 067
Delete events
140
Modification events
| (PID) Process: | (6928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 6 |
Value: 01941A000000001000B24E9A3E06000000000000000600000000000000 | |||
| (PID) Process: | (6928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\OUTLOOK\6928 |
| Operation: | write | Name: | 0 |
Value: 0B0E10FC7C1D3CE75318408A6322174D06C921230046A3A590BC9DE1A4EE016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C5119036D2120B6F00750074006C006F006F006B002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (6928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Outlook\Diagnostics |
| Operation: | delete value | Name: | BootCommand |
Value: | |||
| (PID) Process: | (6928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 1 | |||
| (PID) Process: | (6928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 1 | |||
| (PID) Process: | (6928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 1 | |||
| (PID) Process: | (6928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 1 | |||
| (PID) Process: | (6928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 1 | |||
| (PID) Process: | (6928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 1 | |||
| (PID) Process: | (6928) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 1 | |||
Executable files
4
Suspicious files
14
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6928 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook1.pst | — | |
MD5:— | SHA256:— | |||
| 6928 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\5475cb191e478c39370a215b2da98a37e9dc813d.tbres | binary | |
MD5:001A2689BF9B403F1124AB4A30079D58 | SHA256:7FB28C6B82B0DEA5229FAEE09BE557BEF7FCAE07D3DA7C718688F93A7E52ABEC | |||
| 6928 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\27F2B97C-1F83-4640-B17E-052532C8C3FA | xml | |
MD5:8F6C9BDB9004D12AAC2D99958201BCC3 | SHA256:D3BED44F8C01B4A73A0AB4788A09B658F0A9C63595B3AD9E866C1170B56C7157 | |||
| 6928 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\4N6JHLSF\Transferencia-Banco Santander.7z:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 6928 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\4N6JHLSF\Transferencia-Banco Santander.7z | compressed | |
MD5:1A19E68F34BD318980D39B2CF0CD9918 | SHA256:DC5B31FCBB13B0FEA350BC82F98B74C9E9F7031720B9D6D0254B521607920C3B | |||
| 6928 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Outlook\4N6JHLSF\Transferencia-Banco Santander (002).7z | compressed | |
MD5:1A19E68F34BD318980D39B2CF0CD9918 | SHA256:DC5B31FCBB13B0FEA350BC82F98B74C9E9F7031720B9D6D0254B521607920C3B | |||
| 6928 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | binary | |
MD5:6802A62BE2EBC41601381BA3311C68CC | SHA256:E52742C377D9BEFD0A2F55AFDC50FD31C941605D8CDFD2C6DFE66339E7341A0E | |||
| 6928 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_CBDCCBFE4F7A916411C1E69BDD97BB04 | binary | |
MD5:DF5FC729EB7C29E4F175D73C1A4E13ED | SHA256:F320D122977AF47773C898EFE92AEB1215E1A39003C7A6560AD4E2C6AF006C23 | |||
| 6928 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\56a61aeb75d8f5be186c26607f4bb213abe7c5ec.tbres | binary | |
MD5:3BC5C8ED69C6370D575EF7BF1913BB0E | SHA256:3276DC7CBD880C01C76D0E714ABB5D84C8C6FBEC56F46B24DA53B11190B3744C | |||
| 6928 | OUTLOOK.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:1136AD32A7AD6538CEACDEAEEDD1F91D | SHA256:086498C17074E73D6E66E20FE75D00614585AA5C95CC844FEEDFC3FB66E71745 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
47
DNS requests
34
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
7428 | svchost.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WaaS/FeatureManagement?IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&CurrentBranch=vb_release&AccountFirstChar=&ActivationChannel=Retail&OEMModel=DELL&FlightRing=Retail&AttrDataVer=186&InstallLanguage=en-US&OSUILocale=en-US&WebExperience=1&FlightingBranchName=&ChassisTypeId=1&OSSkuId=48&App=CDM&InstallDate=1661339444&AppVer=&OSArchitecture=AMD64&DefaultUserRegion=244&TelemetryLevel=1&OSVersion=10.0.19045.4046&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
7480 | SIHClient.exe | GET | 304 | 20.165.94.63:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
6928 | OUTLOOK.EXE | GET | 200 | 52.123.128.14:443 | https://ecs.office.com/config/v2/Office/outlook/16.0.16026.20146/Production/CC?&Clientid=%7bD61AB268-C26A-439D-BB15-2A0DEDFCA6A3%7d&Application=outlook&Platform=win32&Version=16.0.16026.20146&MsoVersion=16.0.16026.20002&SDX=fa000000002.2.0.1907.31003&SDX=fa000000005.1.0.1909.30011&SDX=fa000000006.1.0.1909.13002&SDX=fa000000008.1.0.1908.16006&SDX=fa000000009.1.0.1908.6002&SDX=fa000000016.1.0.1810.13001&SDX=fa000000029.1.0.1906.25001&SDX=fa000000033.1.0.1908.24001&SDX=wa104381125.1.0.1810.9001&ProcessName=outlook.exe&Audience=Production&Build=ship&Architecture=x64&Language=en-US&SubscriptionLicense=false&PerpetualLicense=2019&LicenseCategory=6&LicenseSKU=Professional2019Retail&OsVersion=10.0&OsBuild=19045&Channel=CC&InstallType=C2R&SessionId=%7b3C1D7CFC-53E7-4018-8A63-22174D06C921%7d&LabMachine=false | unknown | text | 128 Kb | unknown |
7480 | SIHClient.exe | GET | 200 | 13.95.31.18:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
7480 | SIHClient.exe | GET | 200 | 20.165.94.63:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
7480 | SIHClient.exe | GET | 304 | 20.165.94.63:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
6928 | OUTLOOK.EXE | GET | 200 | 52.109.32.97:443 | https://officeclient.microsoft.com/config16/?lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3 | unknown | xml | 128 Kb | whitelisted |
6928 | OUTLOOK.EXE | POST | 200 | 52.110.17.62:443 | https://roaming.svc.cloud.microsoft/rs/RoamingSoapService.svc | unknown | text | 654 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7428 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4948 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6928 | OUTLOOK.EXE | 52.109.32.97:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6928 | OUTLOOK.EXE | 52.123.128.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6928 | OUTLOOK.EXE | 52.110.17.62:443 | roaming.svc.cloud.microsoft | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6928 | OUTLOOK.EXE | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
roaming.svc.cloud.microsoft |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
messaging.lifecycle.office.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2292 | svchost.exe | Domain Observed Used for C2 Detected | MALWARE [ANY.RUN] Lokibot CnC related domain (dcqapz .shop) |
7652 | cvtres.exe | A Network Trojan was detected | ET MALWARE LokiBot User-Agent (Charon/Inferno) |
7652 | cvtres.exe | Malware Command and Control Activity Detected | ET MALWARE LokiBot Checkin |
7652 | cvtres.exe | A Network Trojan was detected | ET MALWARE LokiBot User-Agent (Charon/Inferno) |
7652 | cvtres.exe | A Network Trojan was detected | ET MALWARE LokiBot Application/Credential Data Exfiltration Detected M1 |
7652 | cvtres.exe | Malware Command and Control Activity Detected | ET MALWARE LokiBot Checkin |
7652 | cvtres.exe | A Network Trojan was detected | ET MALWARE LokiBot User-Agent (Charon/Inferno) |
7652 | cvtres.exe | Malware Command and Control Activity Detected | ET MALWARE LokiBot Request for C2 Commands Detected M2 |
7652 | cvtres.exe | A Network Trojan was detected | ET MALWARE LokiBot Application/Credential Data Exfiltration Detected M1 |
7652 | cvtres.exe | Malware Command and Control Activity Detected | ET MALWARE LokiBot Checkin |