| File name: | GenP-3.4.14.1.exe |
| Full analysis: | https://app.any.run/tasks/3cd264e6-cc3c-4abf-b165-a400186a0cf6 |
| Verdict: | Malicious activity |
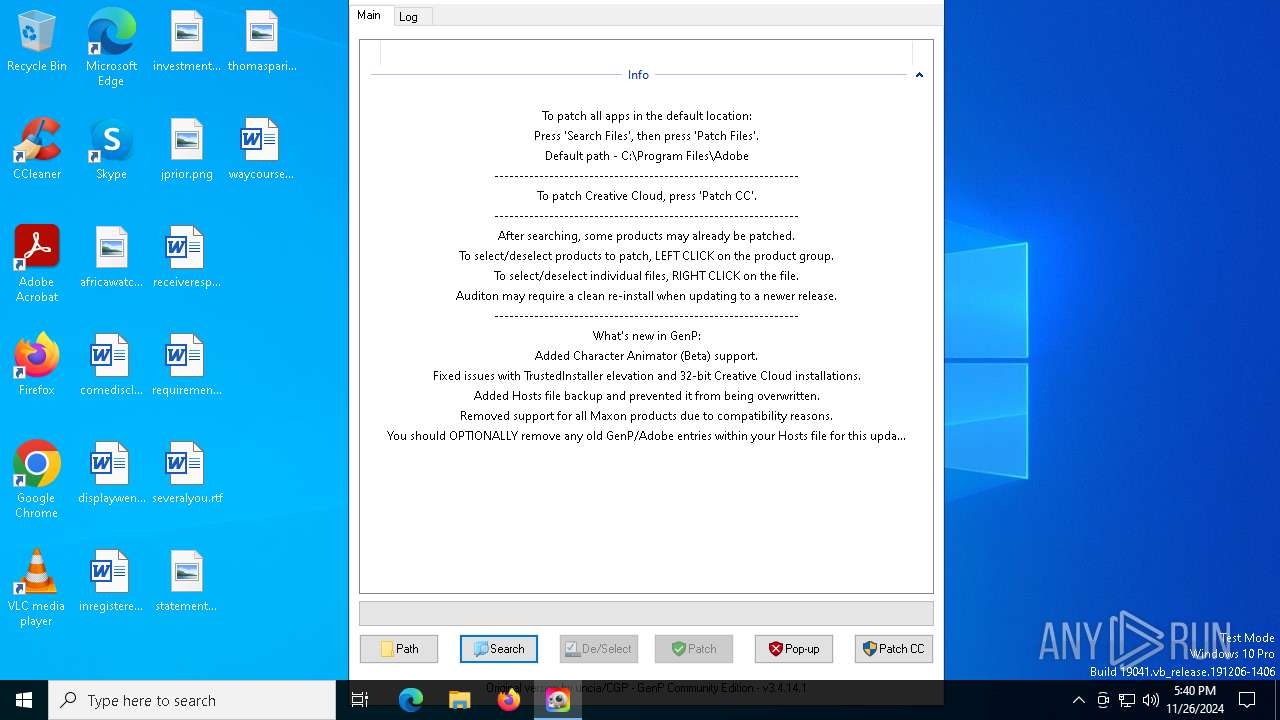
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | November 26, 2024, 17:40:22 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 18286DEB642A79BD9AF012A30DC872C7 |
| SHA1: | 8CD8AFA5D4DA303D1B1BE482DC077E0F9CBC7A45 |
| SHA256: | A5CE5FC1A69793F317E433CDC75DDC86FF19597E0355BE3E82114FCEABFEC2E6 |
| SSDEEP: | 98304:jJ30YsuDA5MsRUIm0BHFCgdfhFoILy83HdMtAafid/phC/1w9snJTueXrrR2HH5S:6kYykhMV00ZZiM |
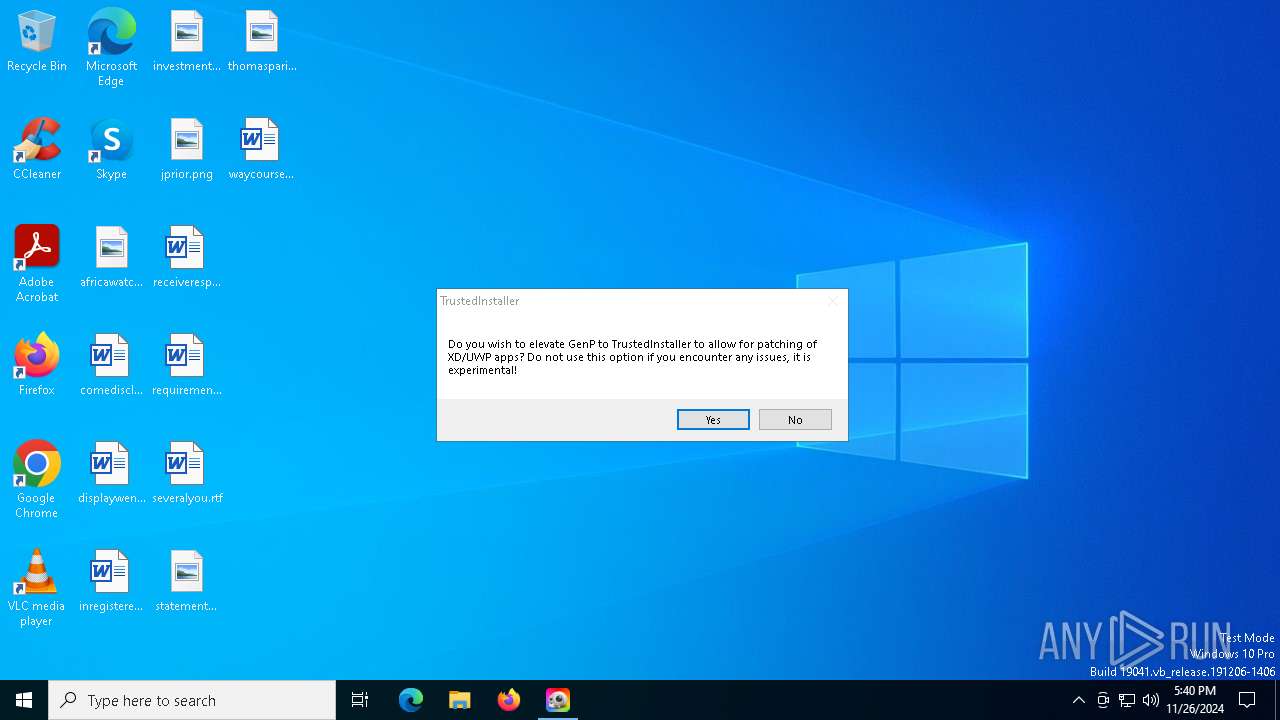
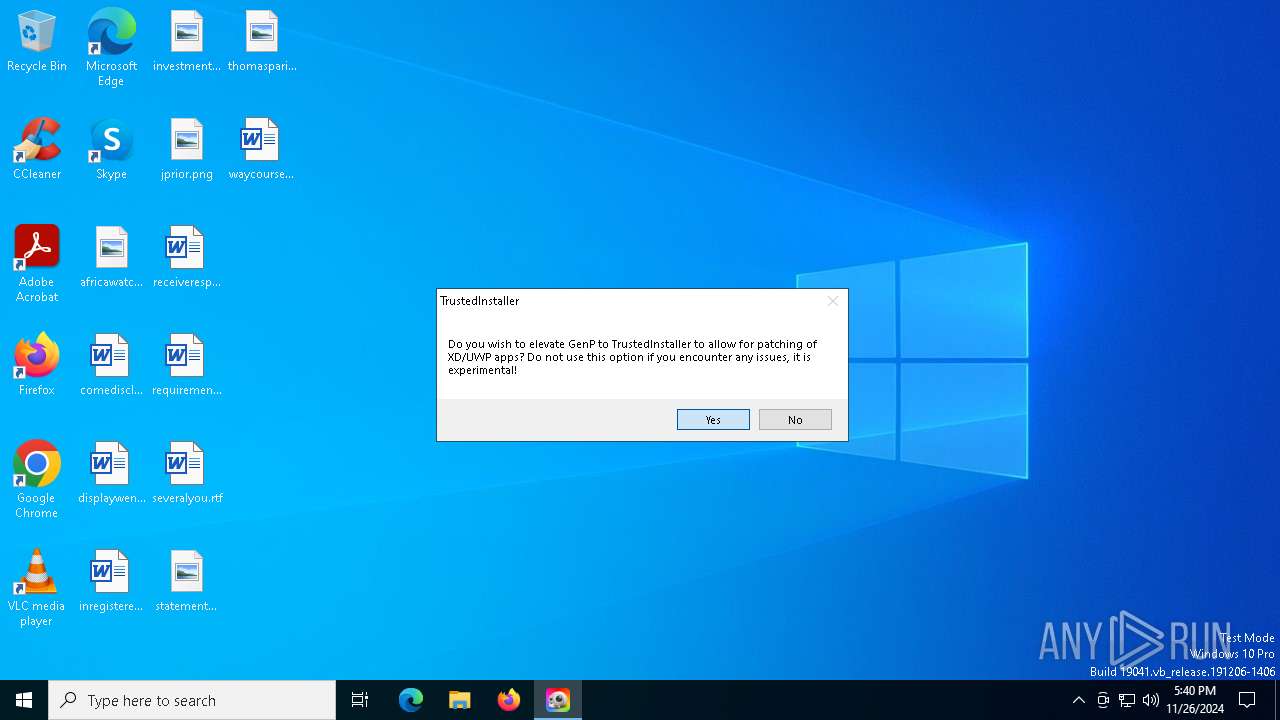
MALICIOUS
Executing a file with an untrusted certificate
- GenP-3.4.14.1.exe (PID: 6480)
- GenP-3.4.14.1.exe (PID: 6568)
Adds path to the Windows Defender exclusion list
- GenP-3.4.14.1.exe (PID: 6824)
Bypass execution policy to execute commands
- powershell.exe (PID: 7356)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7144)
BLANKGRABBER has been detected (SURICATA)
- GenP-3.4.14.1.exe (PID: 6824)
Stealers network behavior
- GenP-3.4.14.1.exe (PID: 6824)
SUSPICIOUS
The process drops C-runtime libraries
- GenP-3.4.14.1.exe (PID: 6480)
Process drops legitimate windows executable
- GenP-3.4.14.1.exe (PID: 6480)
- GenP-3.4.14.1.exe (PID: 6824)
Found strings related to reading or modifying Windows Defender settings
- GenP-3.4.14.1.exe (PID: 6824)
Get information on the list of running processes
- cmd.exe (PID: 3816)
- cmd.exe (PID: 1580)
- GenP-3.4.14.1.exe (PID: 6824)
- cmd.exe (PID: 4628)
Starts CMD.EXE for commands execution
- GenP-3.4.14.1.exe (PID: 6824)
Process drops python dynamic module
- GenP-3.4.14.1.exe (PID: 6480)
Starts a Microsoft application from unusual location
- GenP-3.4.14.1.exe (PID: 6480)
- GenP-3.4.14.1.exe (PID: 6568)
- GenP-3.4.14.1.exe (PID: 6788)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5096)
- cmd.exe (PID: 6308)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3772)
- cmd.exe (PID: 7144)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 7584)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 7252)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 6764)
Starts application with an unusual extension
- cmd.exe (PID: 3280)
- cmd.exe (PID: 7440)
- cmd.exe (PID: 7628)
- cmd.exe (PID: 7944)
- cmd.exe (PID: 8176)
- cmd.exe (PID: 6900)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 3992)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7144)
Base64-obfuscated command line is found
- cmd.exe (PID: 7144)
Executable content was dropped or overwritten
- bound.exe (PID: 7392)
- csc.exe (PID: 2324)
- GenP-3.4.14.1.exe (PID: 6480)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 7144)
CSC.EXE is used to compile C# code
- csc.exe (PID: 2324)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 7468)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 7028)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 6952)
Checks for external IP
- svchost.exe (PID: 2192)
- GenP-3.4.14.1.exe (PID: 6824)
The executable file from the user directory is run by the CMD process
- rar.exe (PID: 7040)
Application launched itself
- GenP-3.4.14.1.exe (PID: 6480)
- GenP-3.4.14.1.exe (PID: 6568)
INFO
The Powershell gets current clipboard
- powershell.exe (PID: 6936)
Checks the directory tree
- tree.com (PID: 7584)
- tree.com (PID: 7740)
- tree.com (PID: 8092)
- tree.com (PID: 7204)
- tree.com (PID: 3524)
- tree.com (PID: 6332)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 6880)
Attempting to use instant messaging service
- GenP-3.4.14.1.exe (PID: 6824)
- svchost.exe (PID: 2192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:11:23 12:16:27+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 172032 |
| InitializedDataSize: | 94208 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce20 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.0.19041.3636 |
| ProductVersionNumber: | 10.0.19041.3636 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Certificate Enrollment Control |
| FileVersion: | 10.0.19041.3636 (WinBuild.160101.0800) |
| InternalName: | EnrollComServer.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | EnrollComServer.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 10.0.19041.3636 |
Total processes
220
Monitored processes
84
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1580 | C:\WINDOWS\system32\cmd.exe /c "tasklist /FO LIST" | C:\Windows\System32\cmd.exe | — | GenP-3.4.14.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\v5gx1jhk\v5gx1jhk.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2972 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3280 | C:\WINDOWS\system32\cmd.exe /c "tree /A /F" | C:\Windows\System32\cmd.exe | — | GenP-3.4.14.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3524 | tree /A /F | C:\Windows\System32\tree.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Tree Walk Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
44 612
Read events
44 585
Write events
21
Delete events
6
Modification events
| (PID) Process: | (6824) GenP-3.4.14.1.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Multimedia\DrawDib |
| Operation: | write | Name: | 1280x720x32(BGR 0) |
Value: 31,31,31,31 | |||
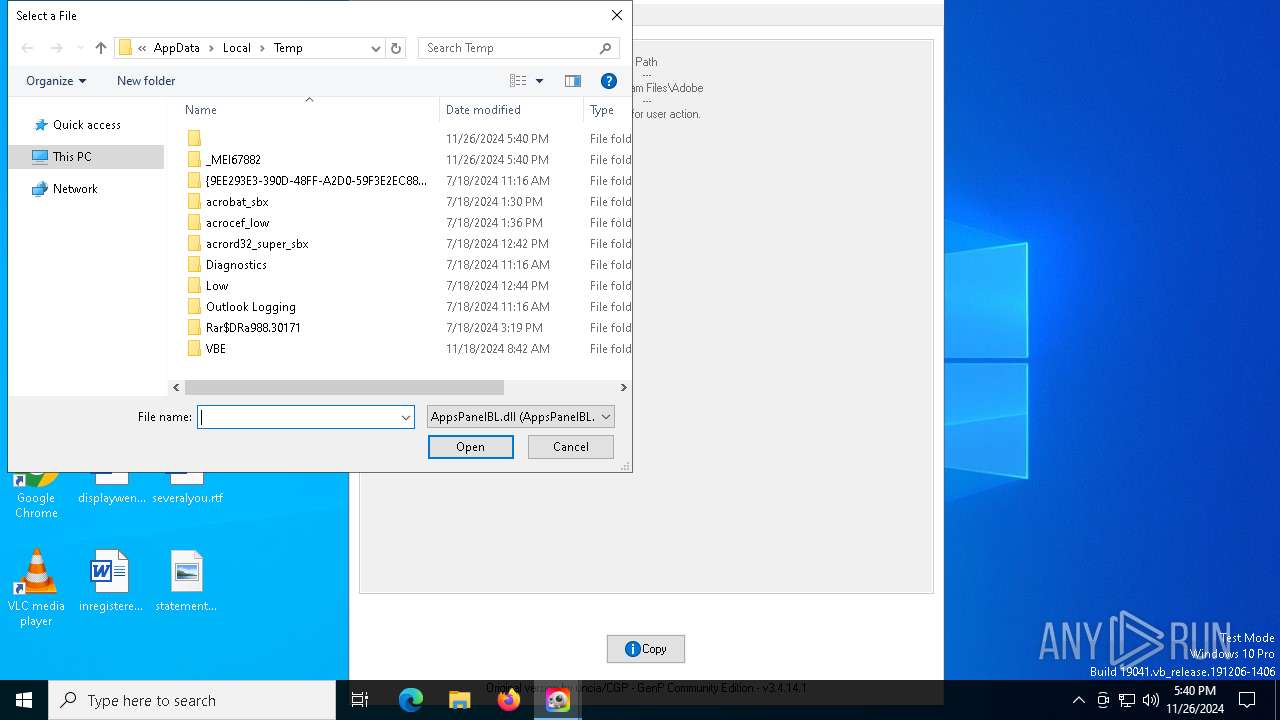
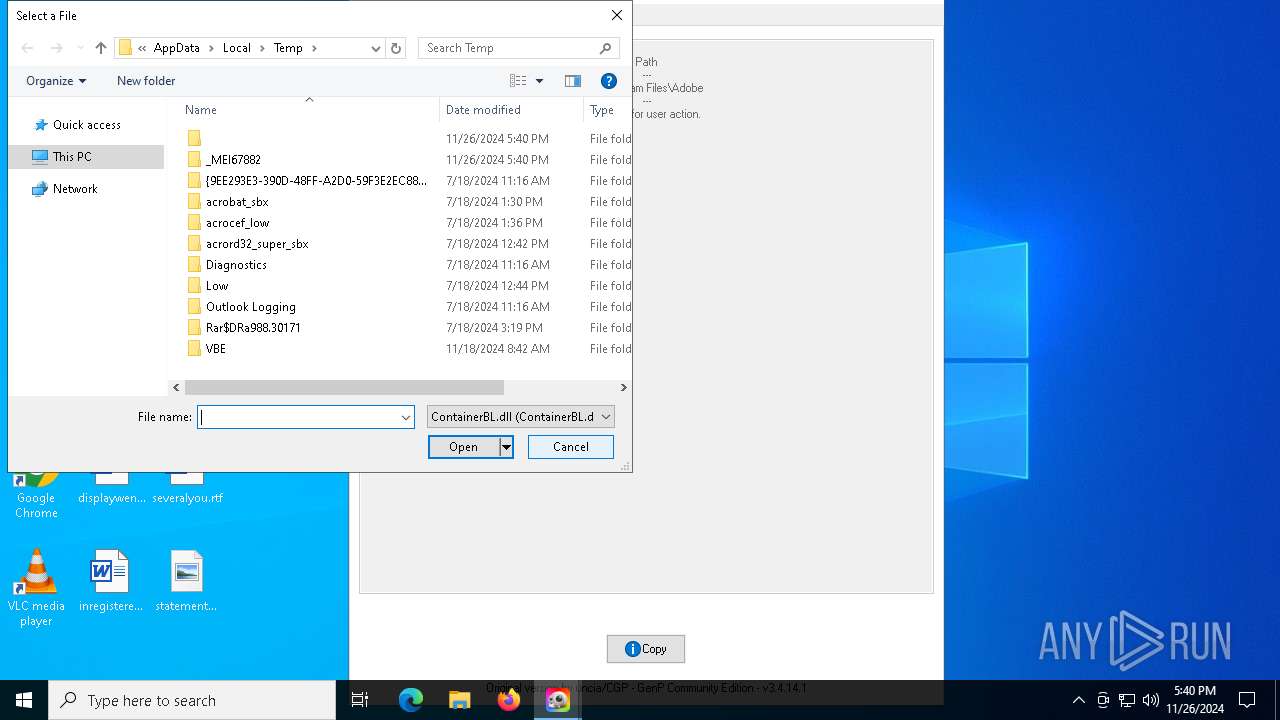
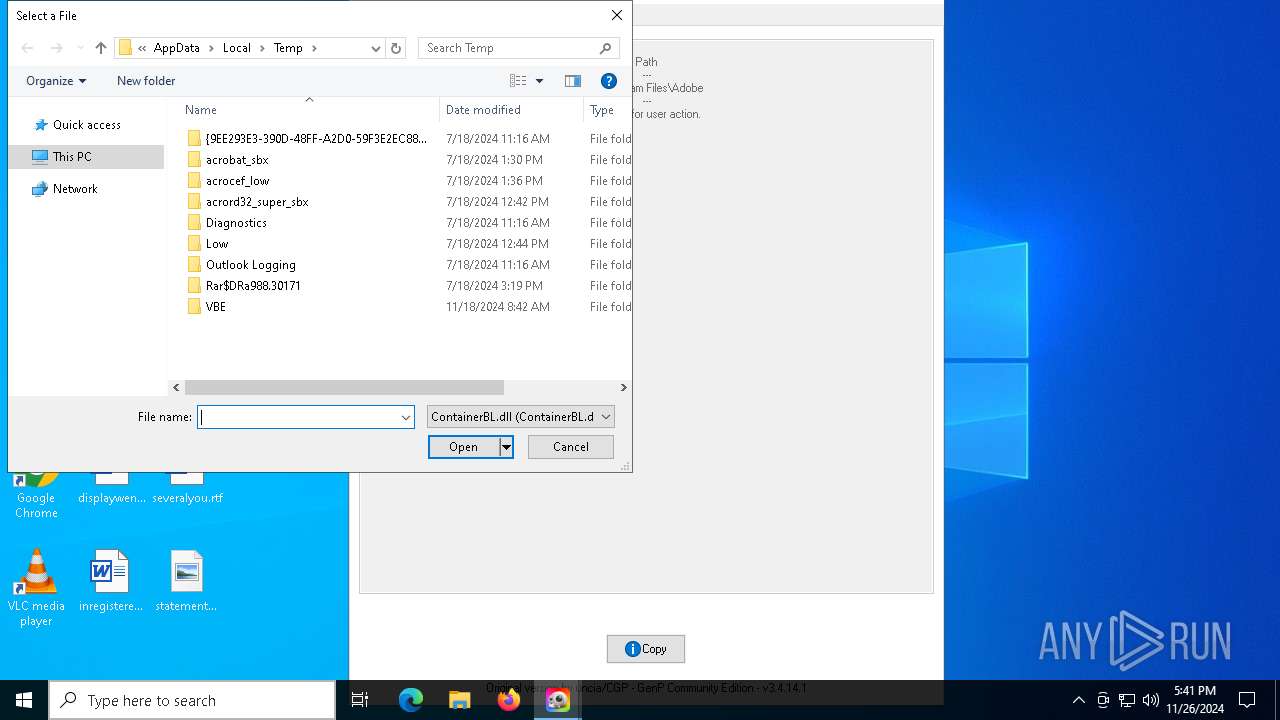
| (PID) Process: | (7392) bound.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (7392) bound.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0062006F0075006E0064002E00650078006500000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070000000 | |||
| (PID) Process: | (7392) bound.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (7392) bound.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (7392) bound.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
| (PID) Process: | (7392) bound.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (8028) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31146026 | |||
| (PID) Process: | (8028) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: | |||
| (PID) Process: | (7392) bound.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {F02C1A0D-BE21-4350-88B0-7367FC96EF3C} {000214E6-0000-0000-C000-000000000046} 0xFFFF |
Value: 0100000000000000D1F7B6502A40DB01 | |||
Executable files
22
Suspicious files
20
Text files
44
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6480 | GenP-3.4.14.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI64802\_bz2.pyd | executable | |
MD5:20A7ECFE1E59721E53AEBEB441A05932 | SHA256:7EBBE24DA78B652A1B6FE77B955507B1DAFF6AF7FF7E5C3FA5AC71190BDE3DA8 | |||
| 6480 | GenP-3.4.14.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI64802\_lzma.pyd | executable | |
MD5:F8B61629E42ADFE417CB39CDBDF832BB | SHA256:7A3973FEDD5D4F60887CF0665BCB7BD3C648AD40D3AE7A8E249D875395E5E320 | |||
| 6480 | GenP-3.4.14.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI64802\_sqlite3.pyd | executable | |
MD5:63618D0BC7B07AECC487A76EB3A94AF8 | SHA256:E74C9CA9007B6B43FF46783ECB393E6EC9EBBDF03F7C12A90C996D9331700A8B | |||
| 6480 | GenP-3.4.14.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI64802\_decimal.pyd | executable | |
MD5:D0231F126902DB68D7F6CA1652B222C0 | SHA256:69876F825678B717C51B7E7E480DE19499D972CB1E98BBFD307E53EE5BACE351 | |||
| 6480 | GenP-3.4.14.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI64802\_ssl.pyd | executable | |
MD5:E52DBAEBA8CD6CADF00FEA19DF63F0C1 | SHA256:EAF60A9E979C95669D8F209F751725DF385944F347142E0ECDCF2F794D005EAD | |||
| 6480 | GenP-3.4.14.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI64802\_hashlib.pyd | executable | |
MD5:A81E0DF35DED42E8909597F64865E2B3 | SHA256:5582F82F7656D4D92ED22F8E460BEBD722E04C8F993C3A6ADCC8437264981185 | |||
| 6480 | GenP-3.4.14.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI64802\base_library.zip | compressed | |
MD5:34A1E9C9033D4DBEC9AA8FCE5CF8403F | SHA256:4C21ADBCC2A8D8ADC1D4B693017C6276B03CB505BB810F46709D75AC3FB77668 | |||
| 6480 | GenP-3.4.14.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI64802\_socket.pyd | executable | |
MD5:C12BDED48873B3098C7A36EB06B34870 | SHA256:6C4860CB071BB6D0B899F7CA2A1DA796B06EA391BAC99A01F192E856725E88AA | |||
| 6480 | GenP-3.4.14.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI64802\_queue.pyd | executable | |
MD5:0DA22CCB73CD146FCDF3C61EF279B921 | SHA256:E8AE2C5D37A68BD34054678AE092E2878F73A0F41E6787210F1E9B9BB97F37A0 | |||
| 6480 | GenP-3.4.14.1.exe | C:\Users\admin\AppData\Local\Temp\_MEI64802\_ctypes.pyd | executable | |
MD5:5006B7EA33FCE9F7800FECC4EB837A41 | SHA256:8F7A5B0ABC319BA9BFD11581F002E533FCBE4CA96CEDD37656B579CD3942EF81 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
35
DNS requests
19
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.81:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.81:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5244 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5244 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6468 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6824 | GenP-3.4.14.1.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=225545 | unknown | — | — | shared |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.81:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.164.81:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.189:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
gstatic.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2192 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6824 | GenP-3.4.14.1.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6824 | GenP-3.4.14.1.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
6824 | GenP-3.4.14.1.exe | A Network Trojan was detected | STEALER [ANY.RUN] BlankGrabber (SkochGrabber) Generic External IP Check |