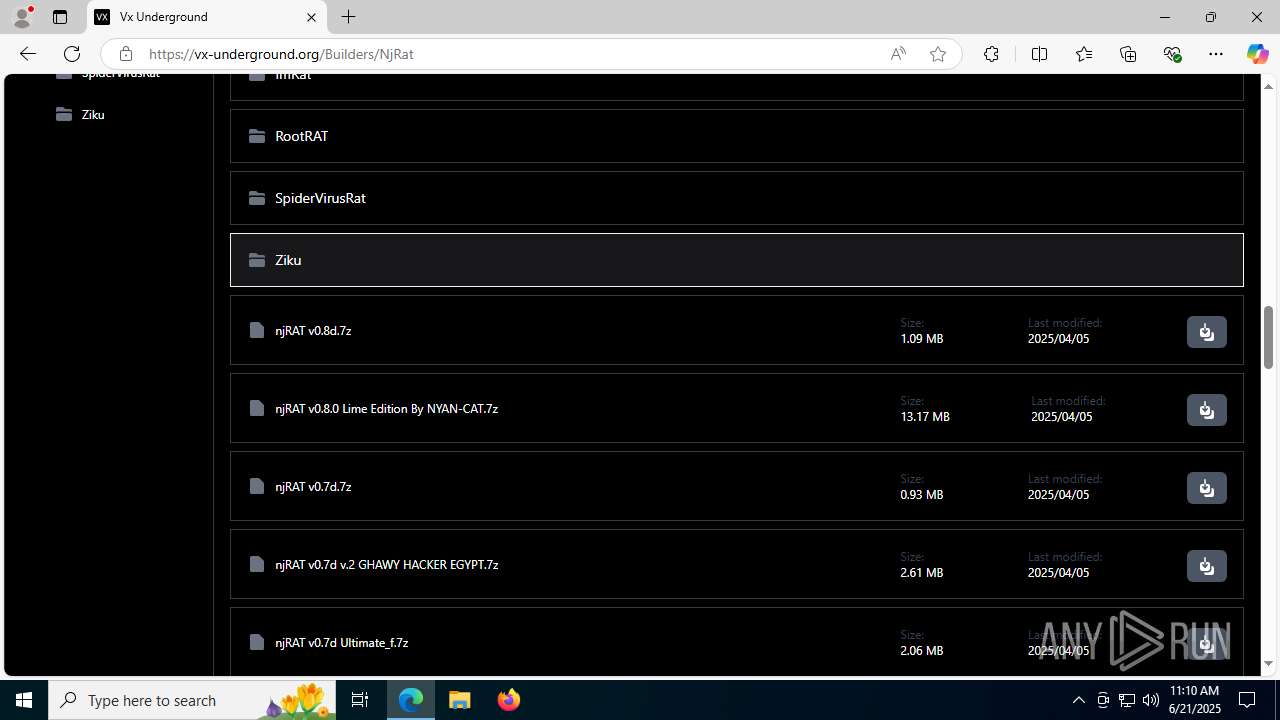
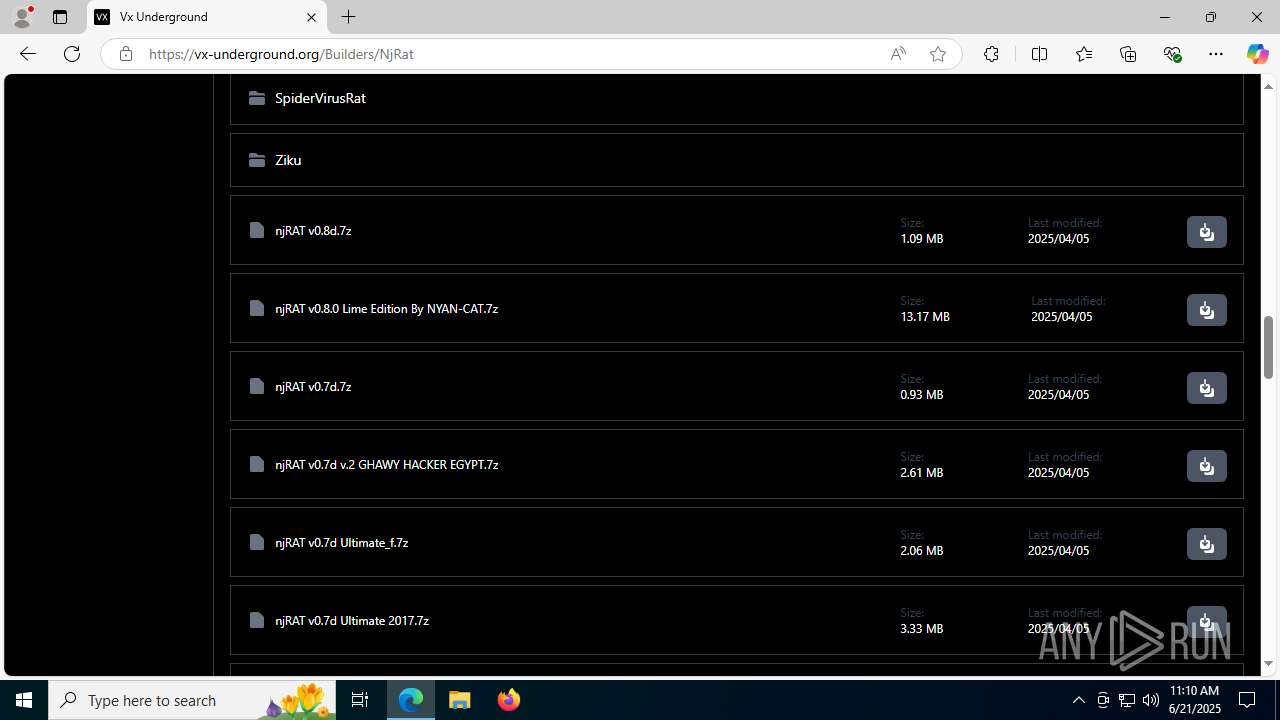
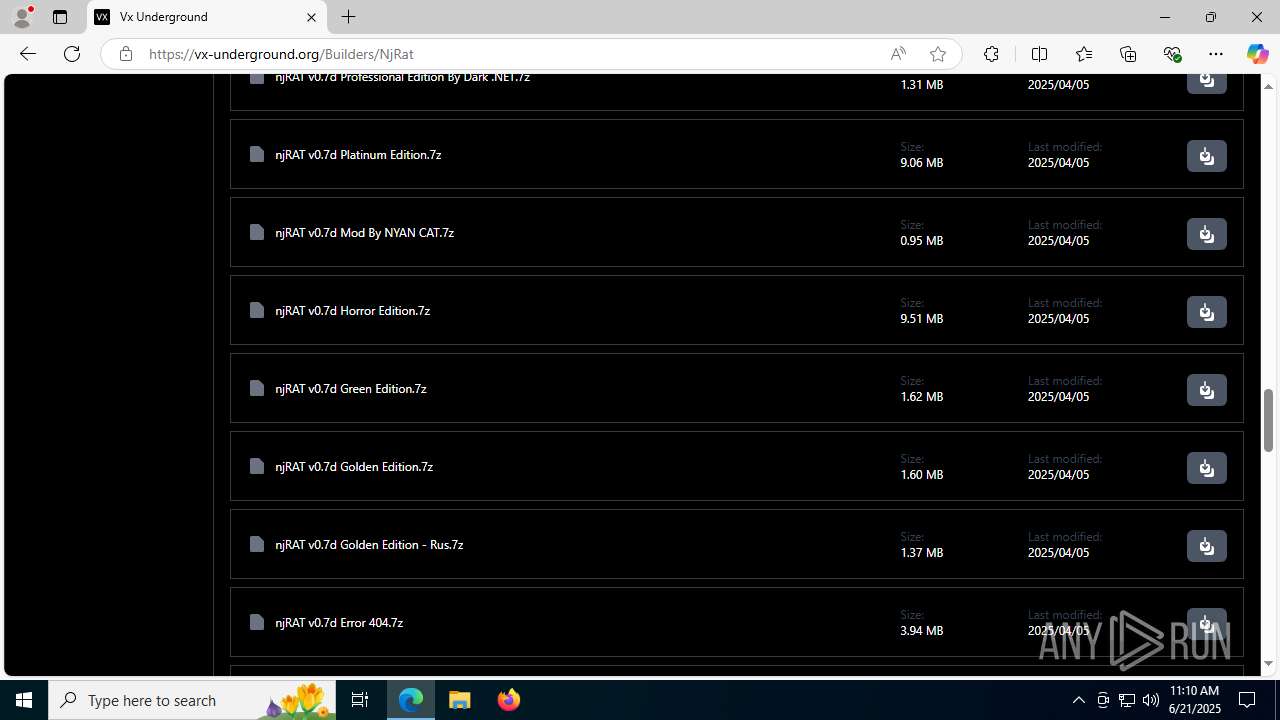
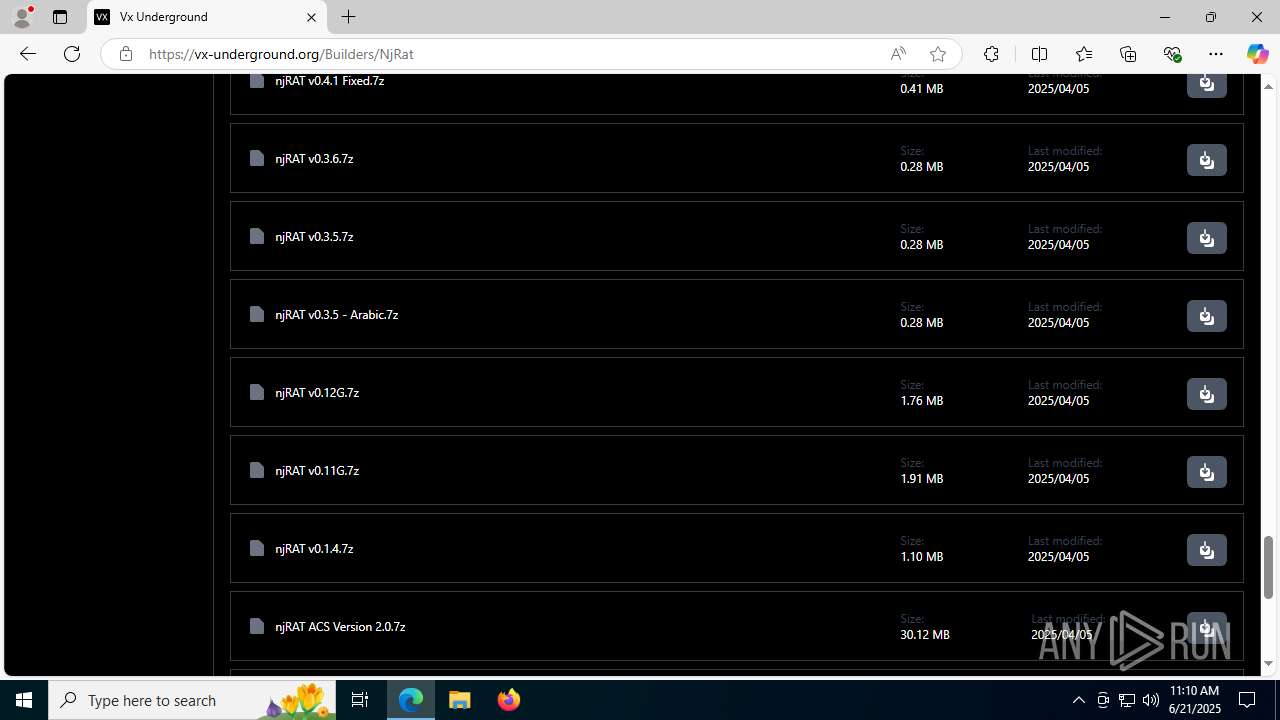
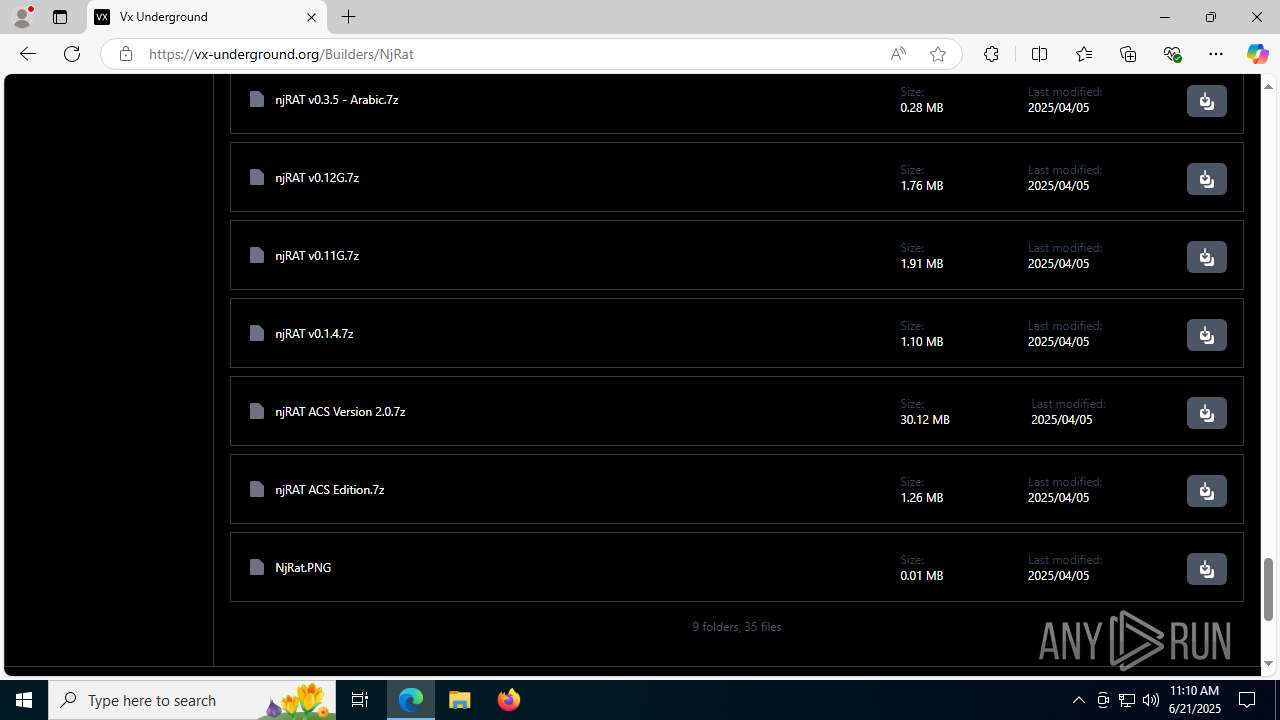
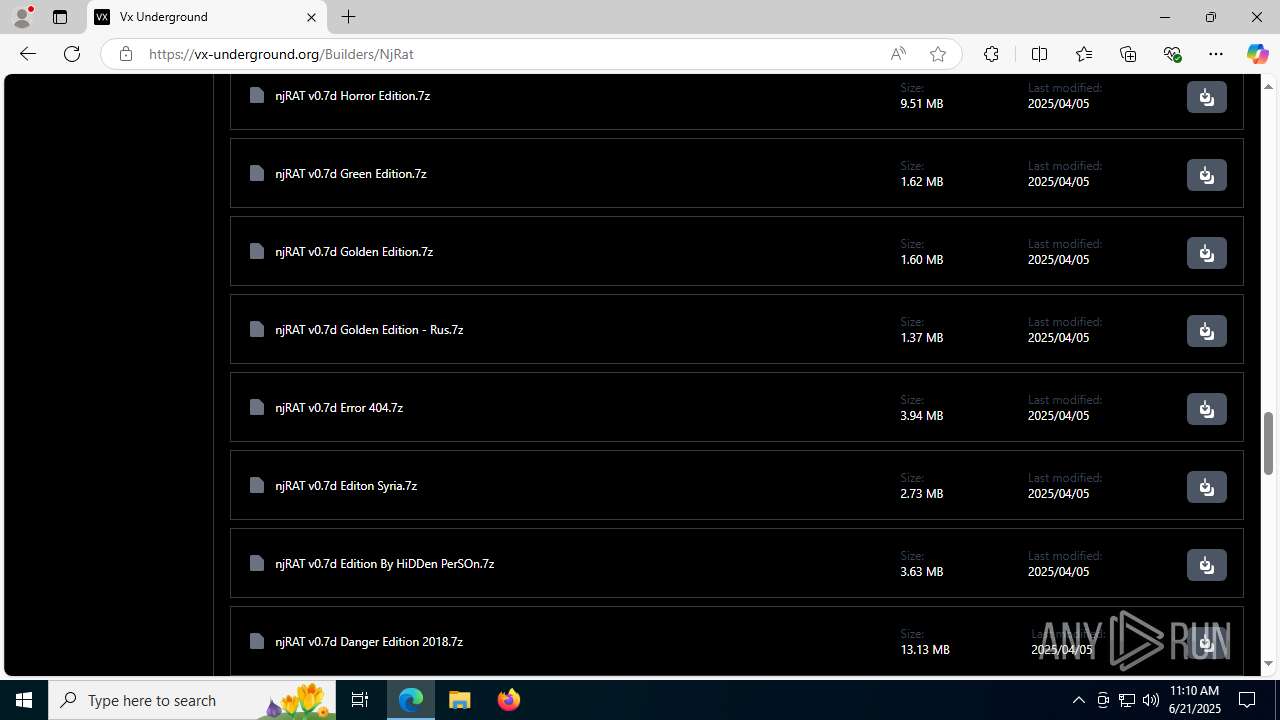
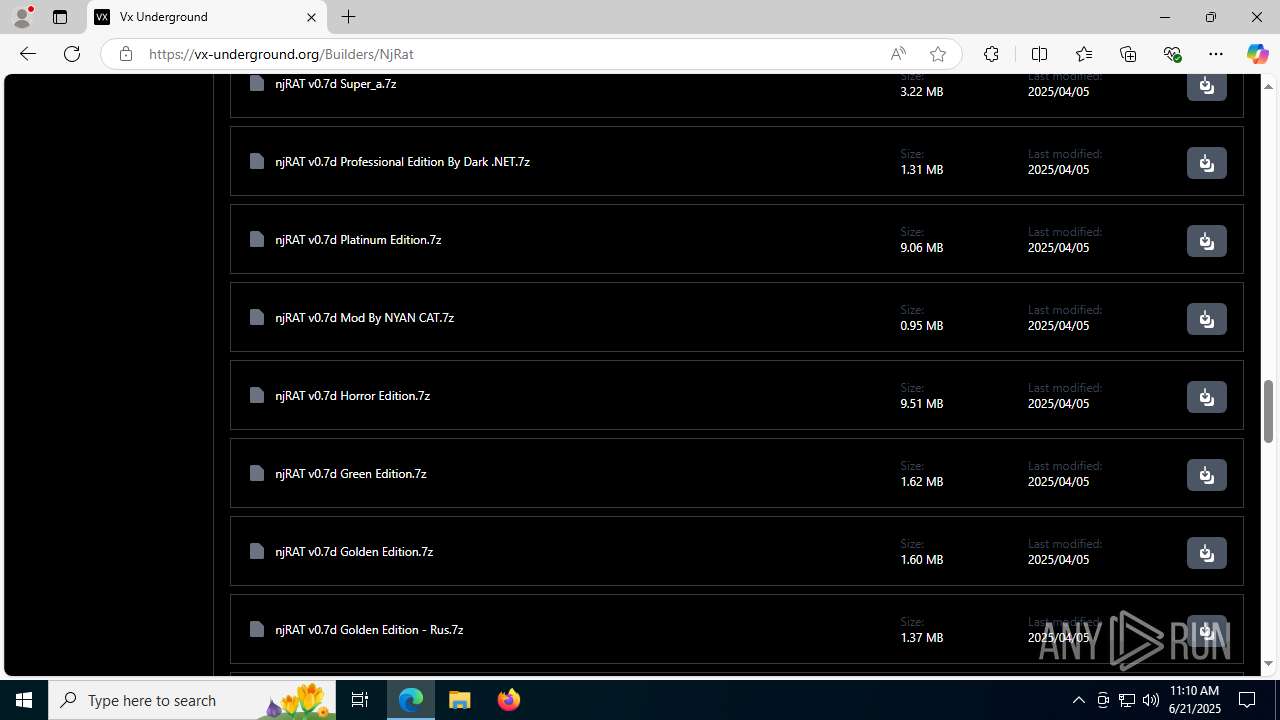
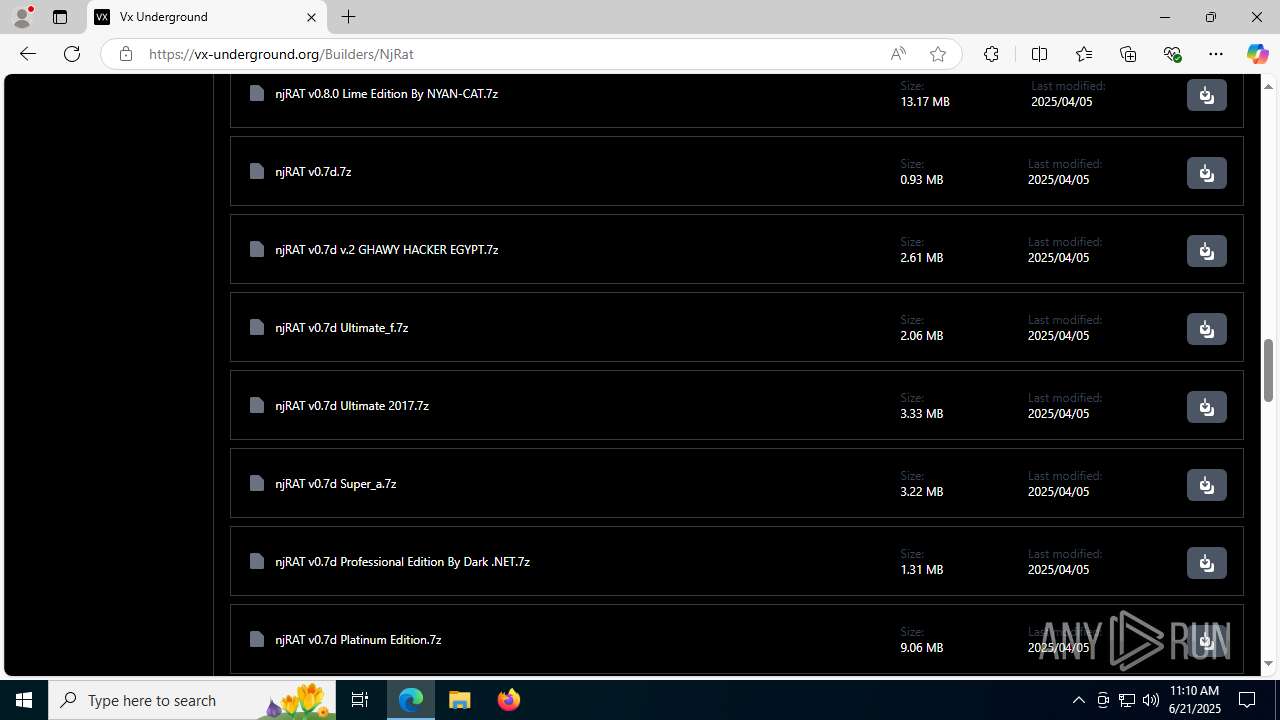
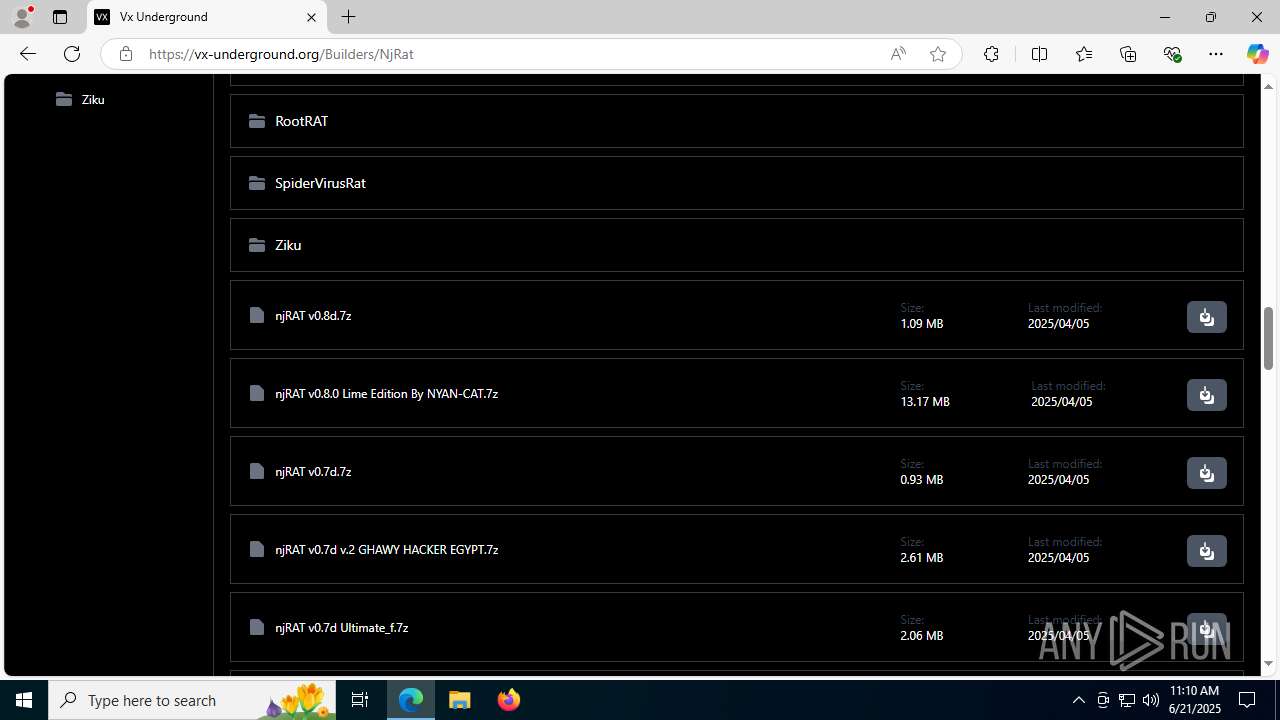
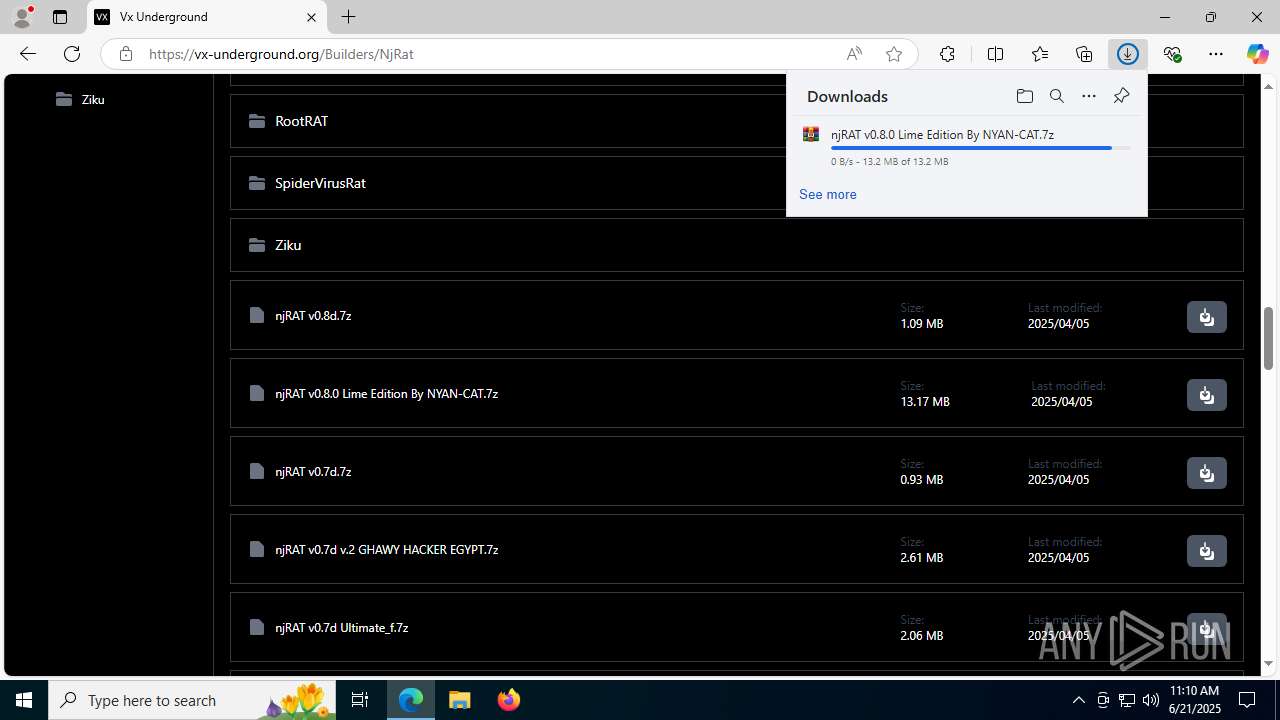
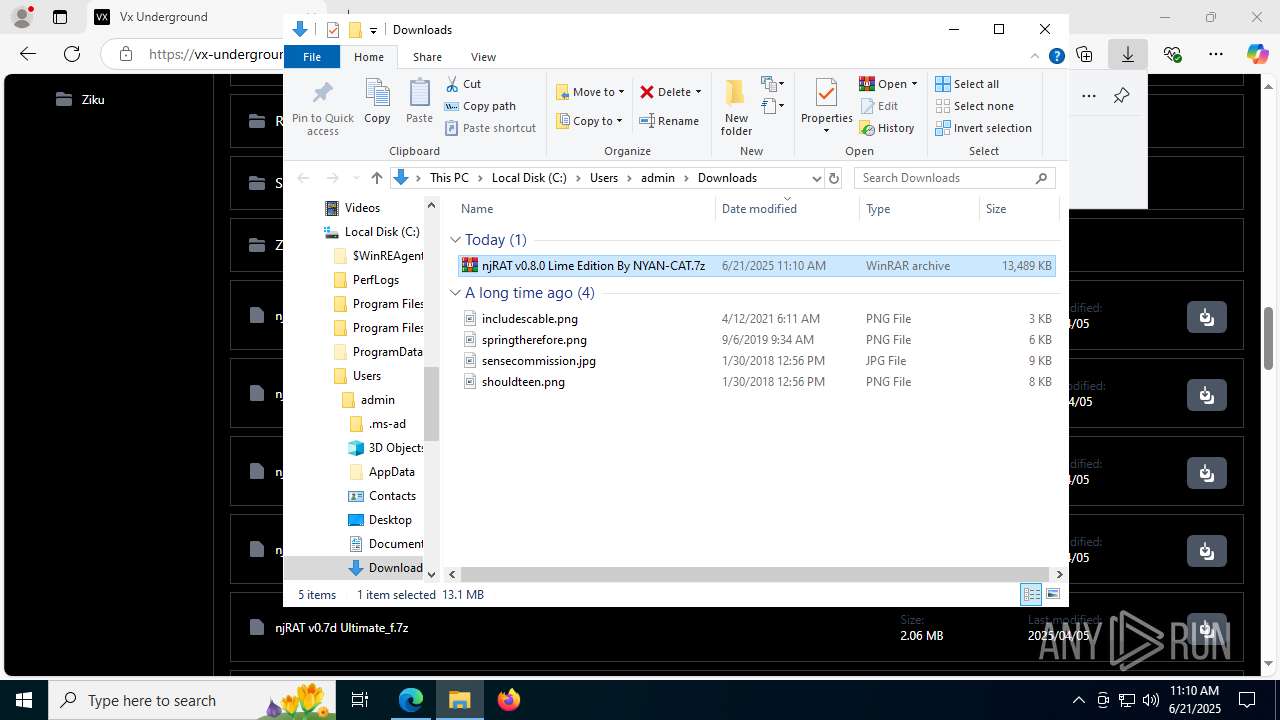
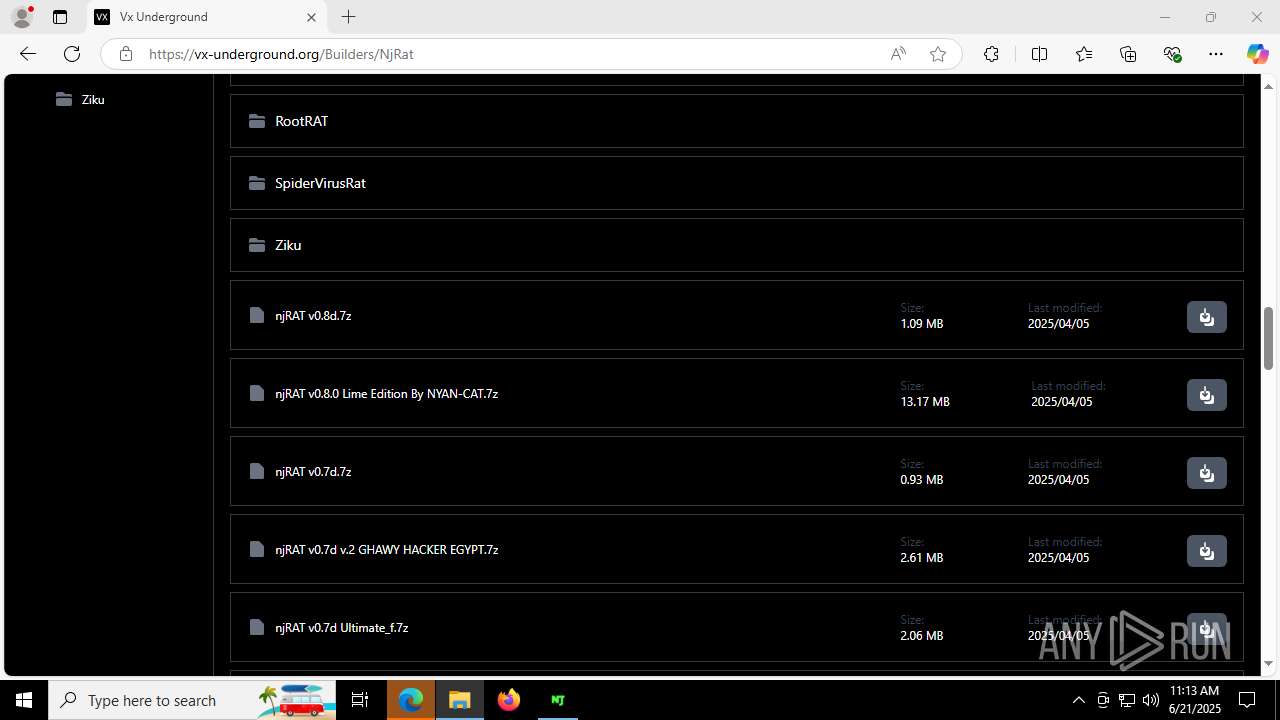
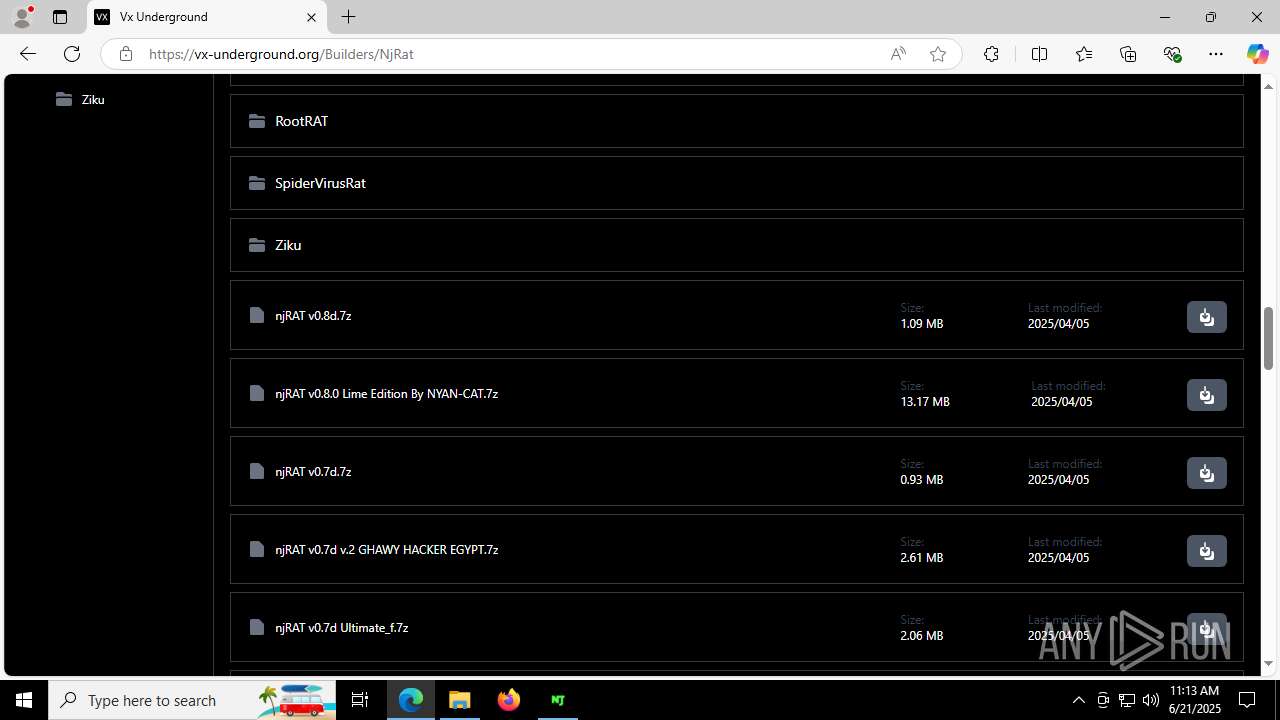
| URL: | https://vx-underground.org/Builders/NjRat |
| Full analysis: | https://app.any.run/tasks/a666c23f-b1dc-4efd-b928-7a74104c64a2 |
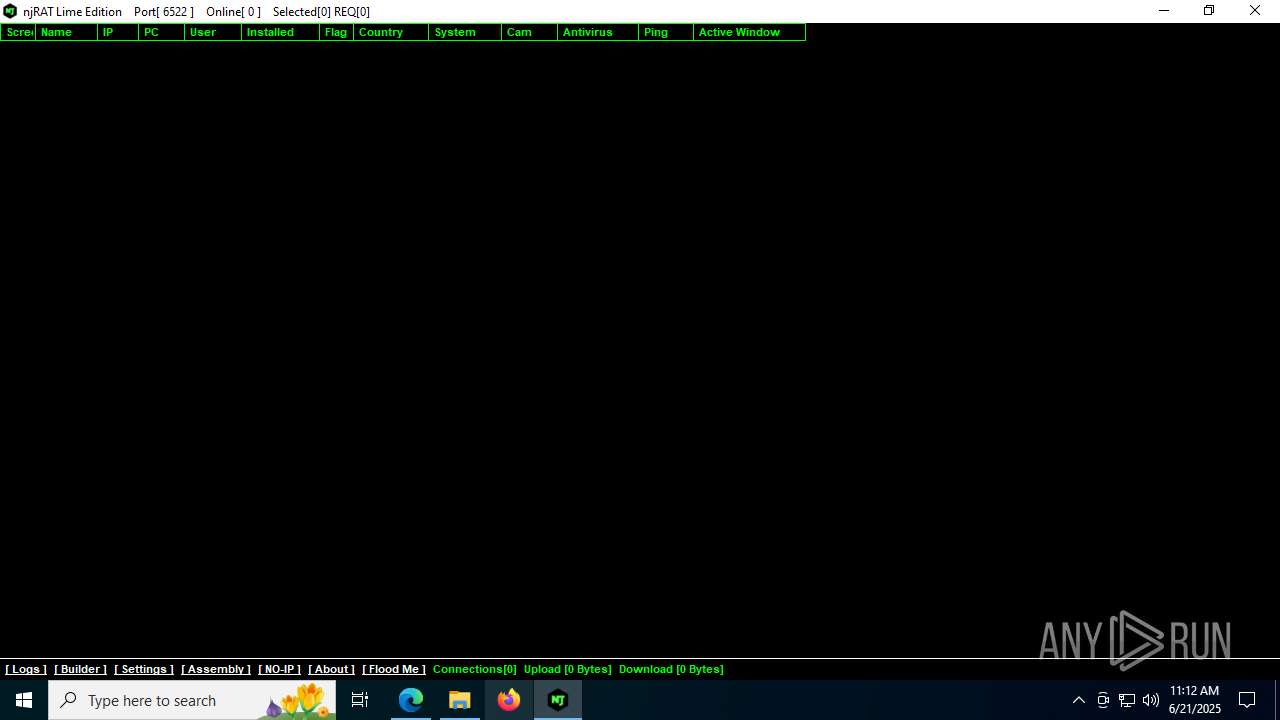
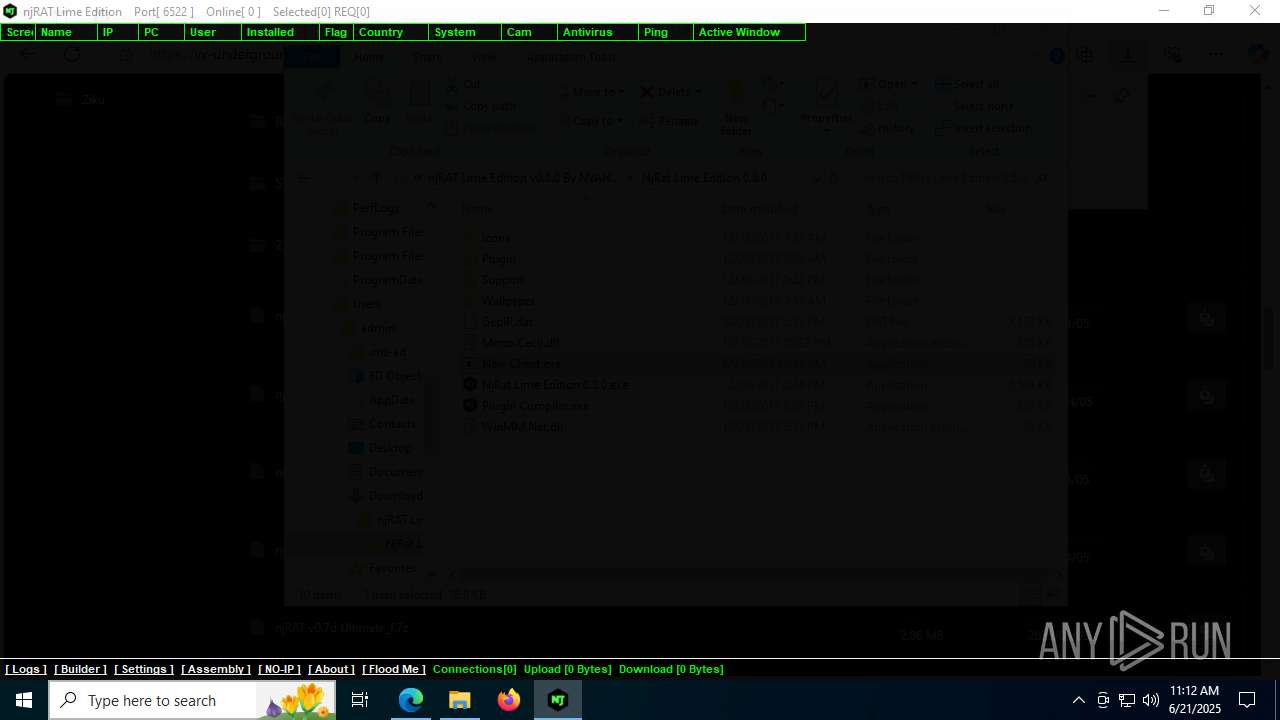
| Verdict: | Malicious activity |
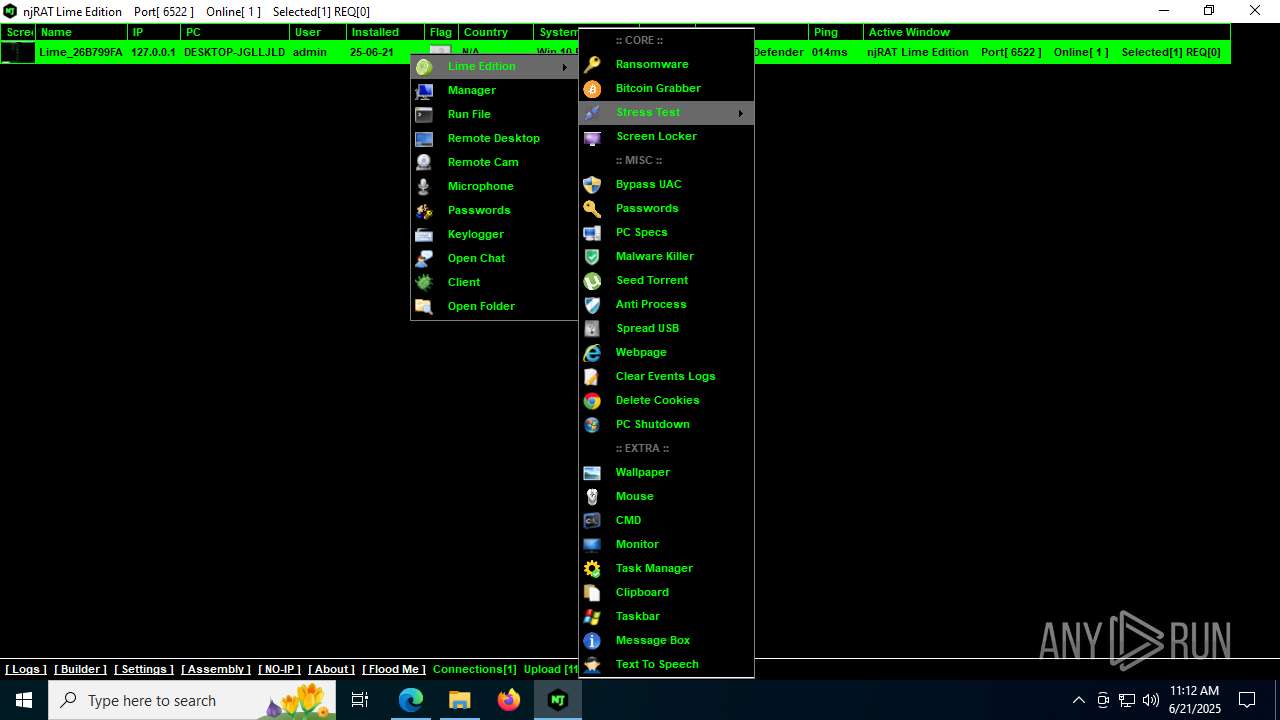
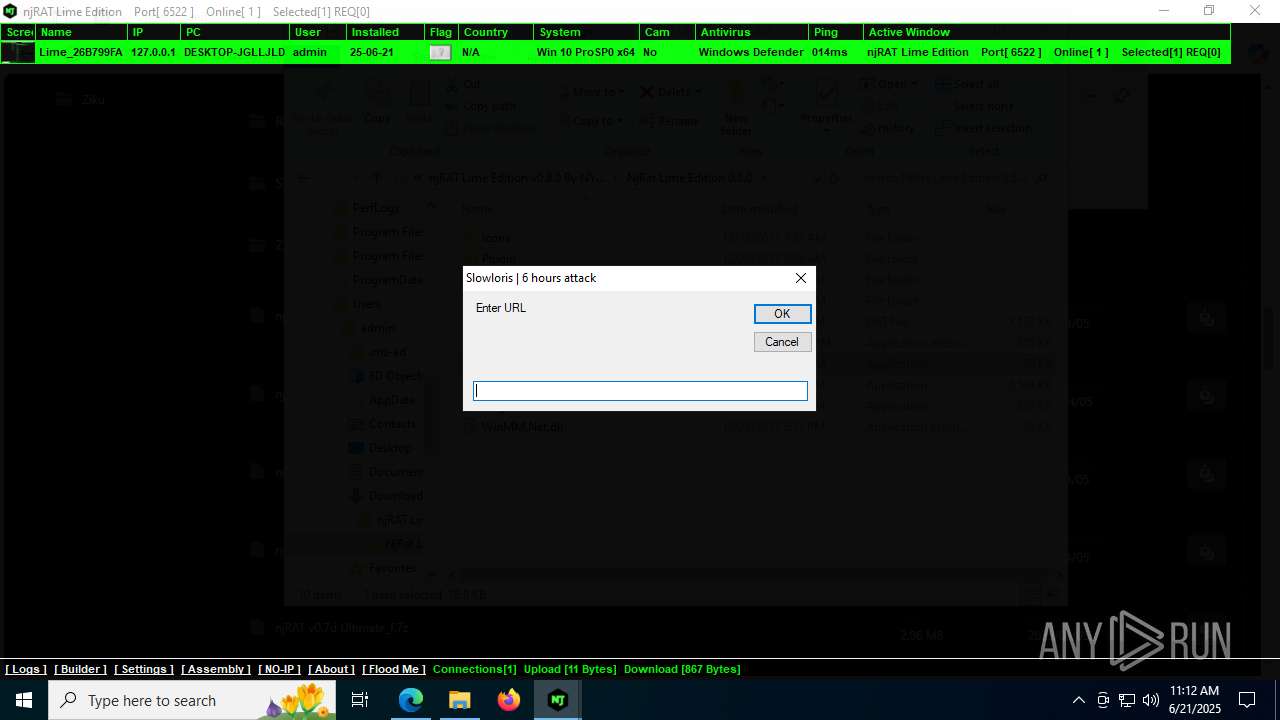
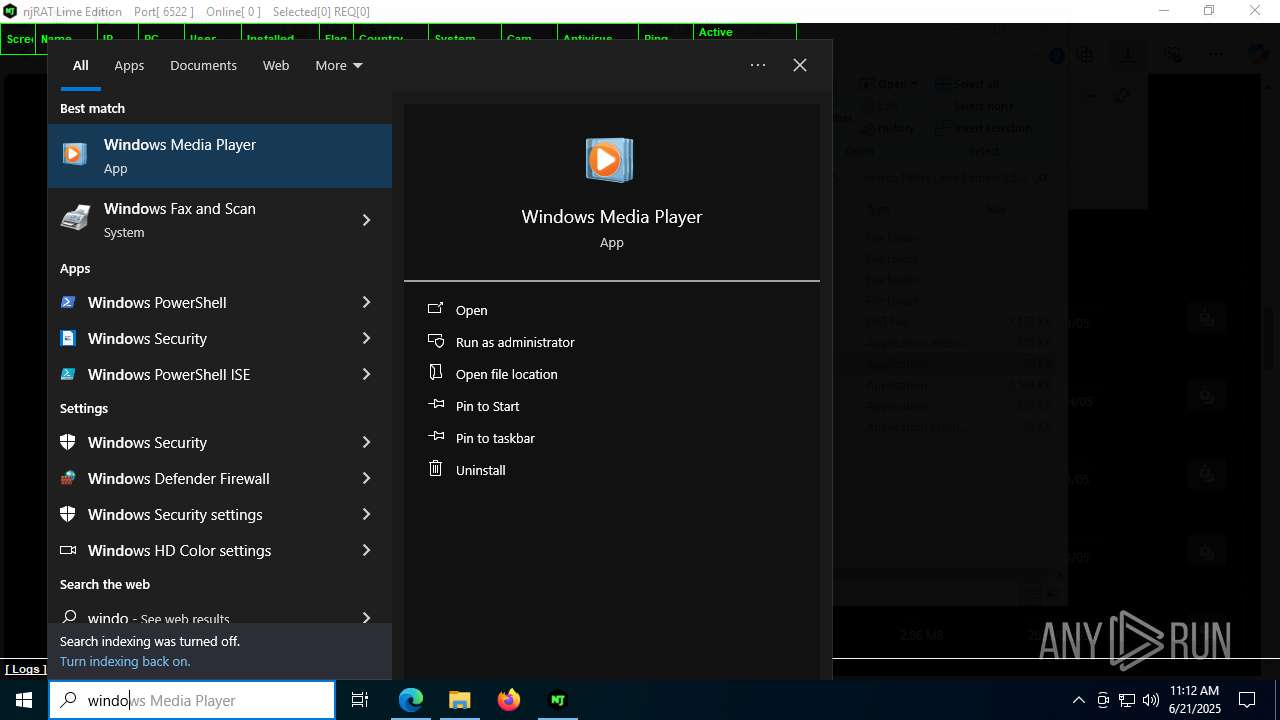
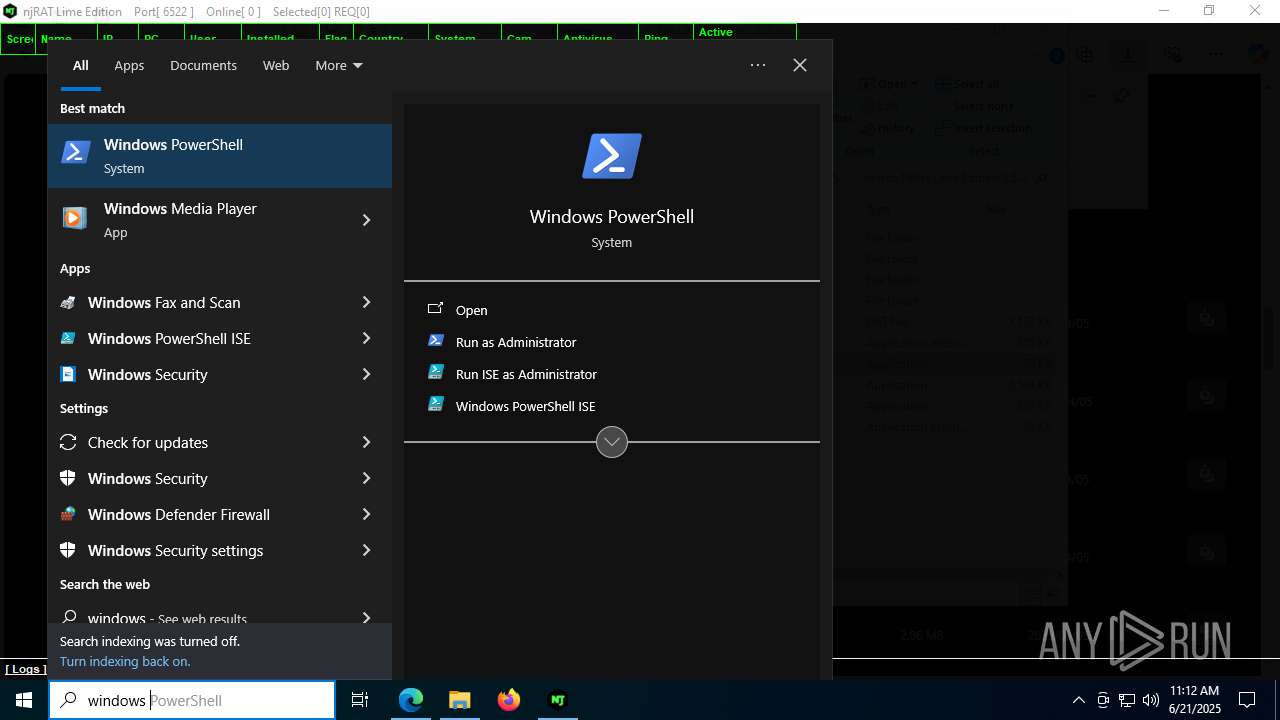
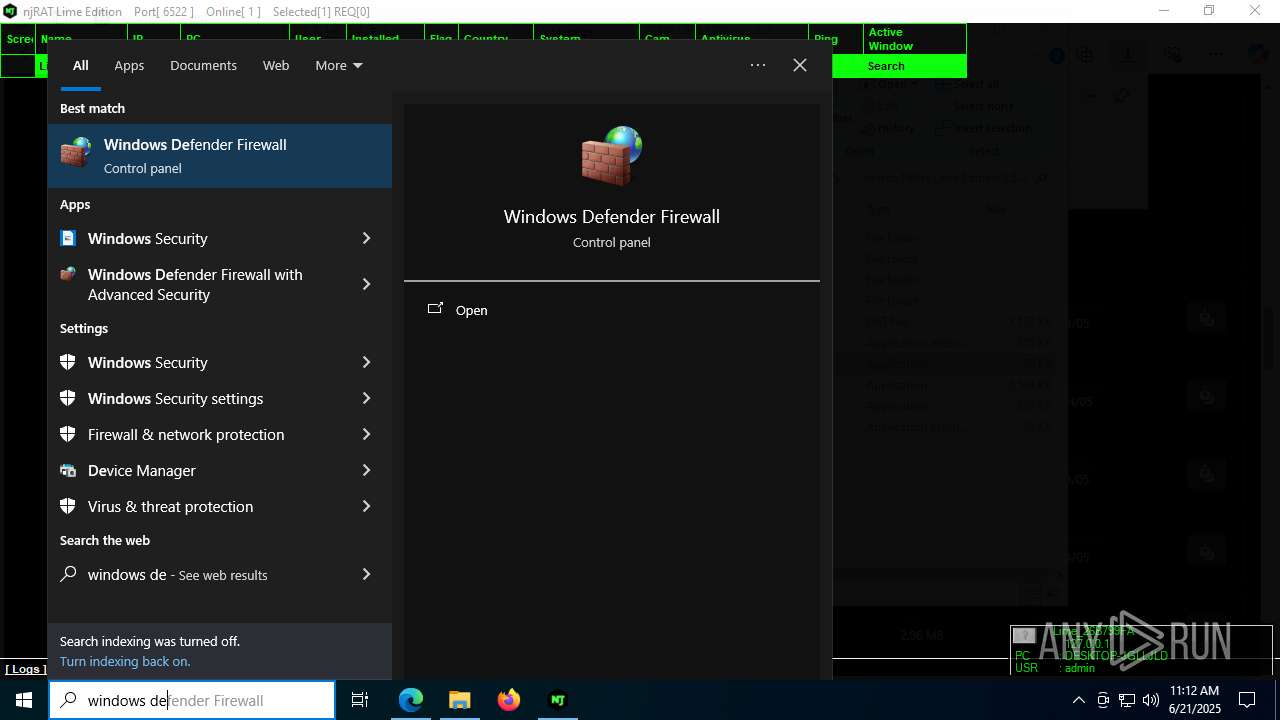
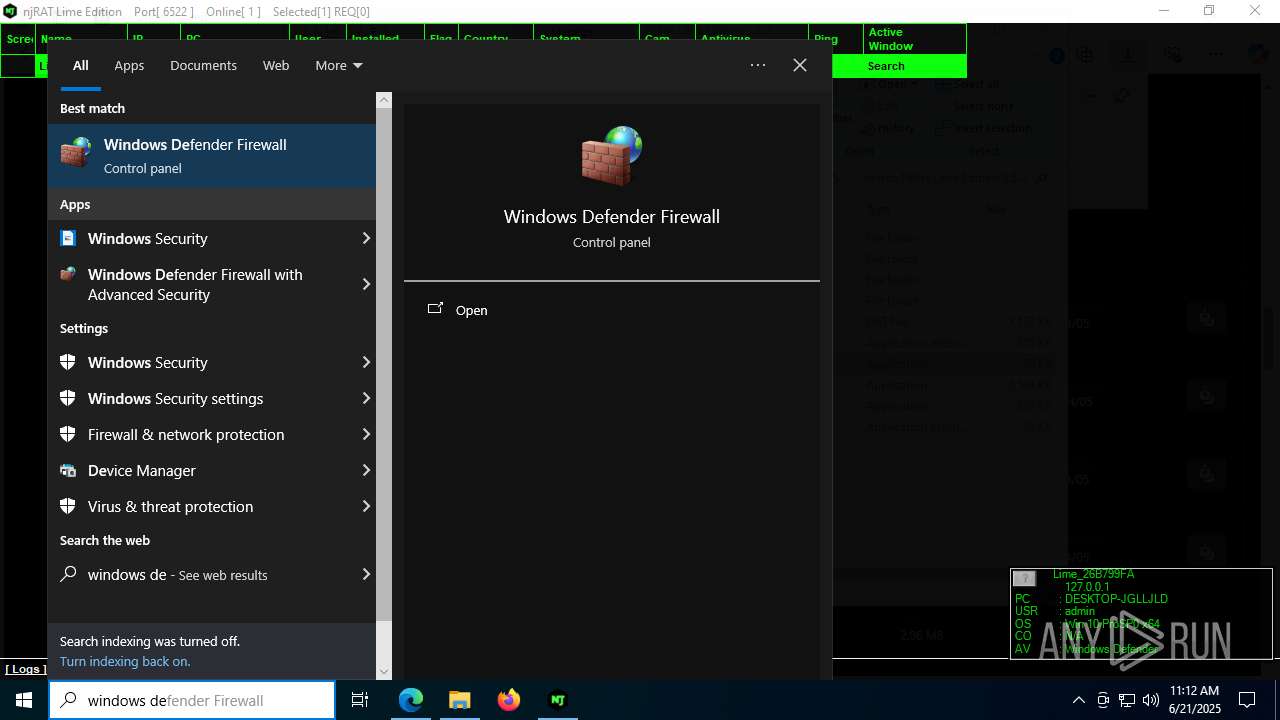
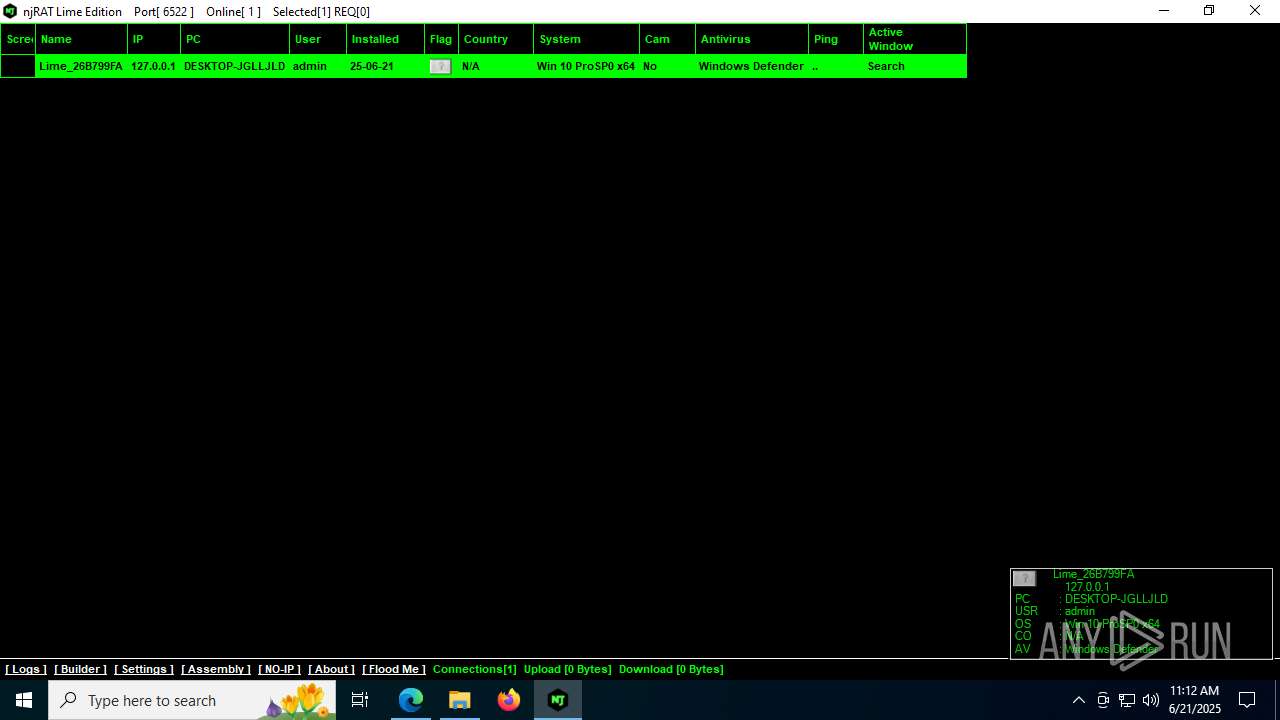
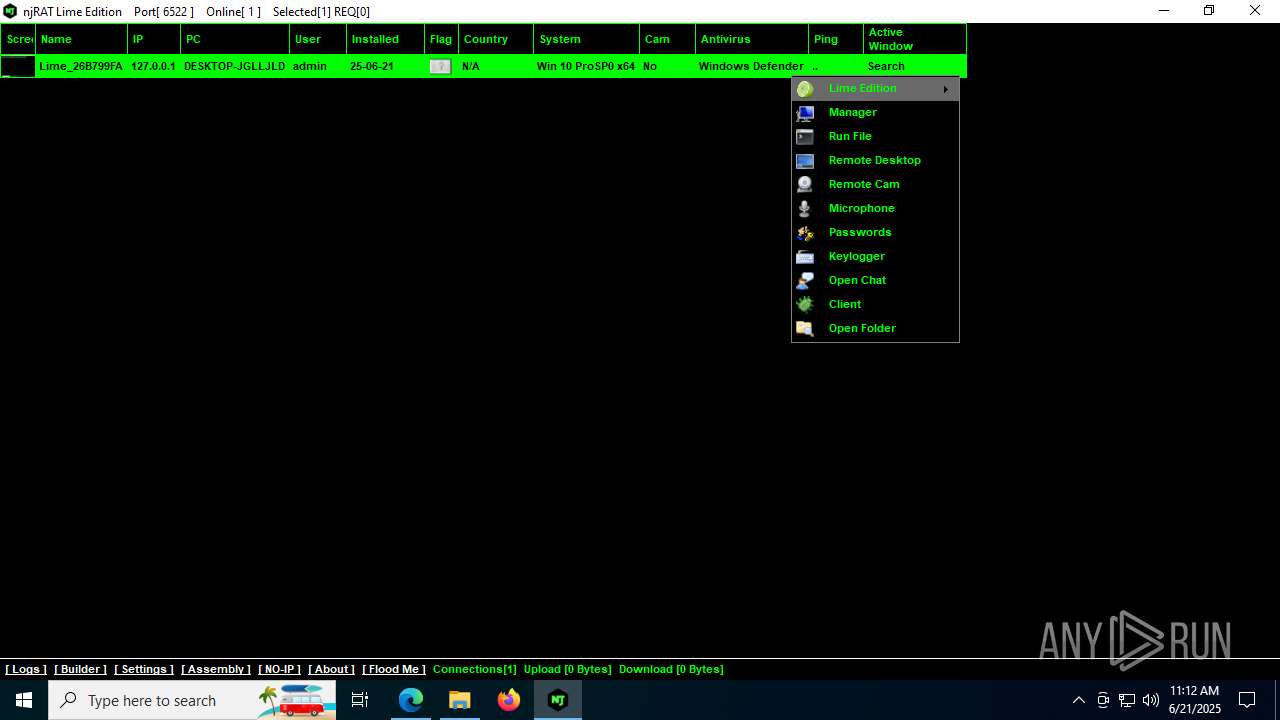
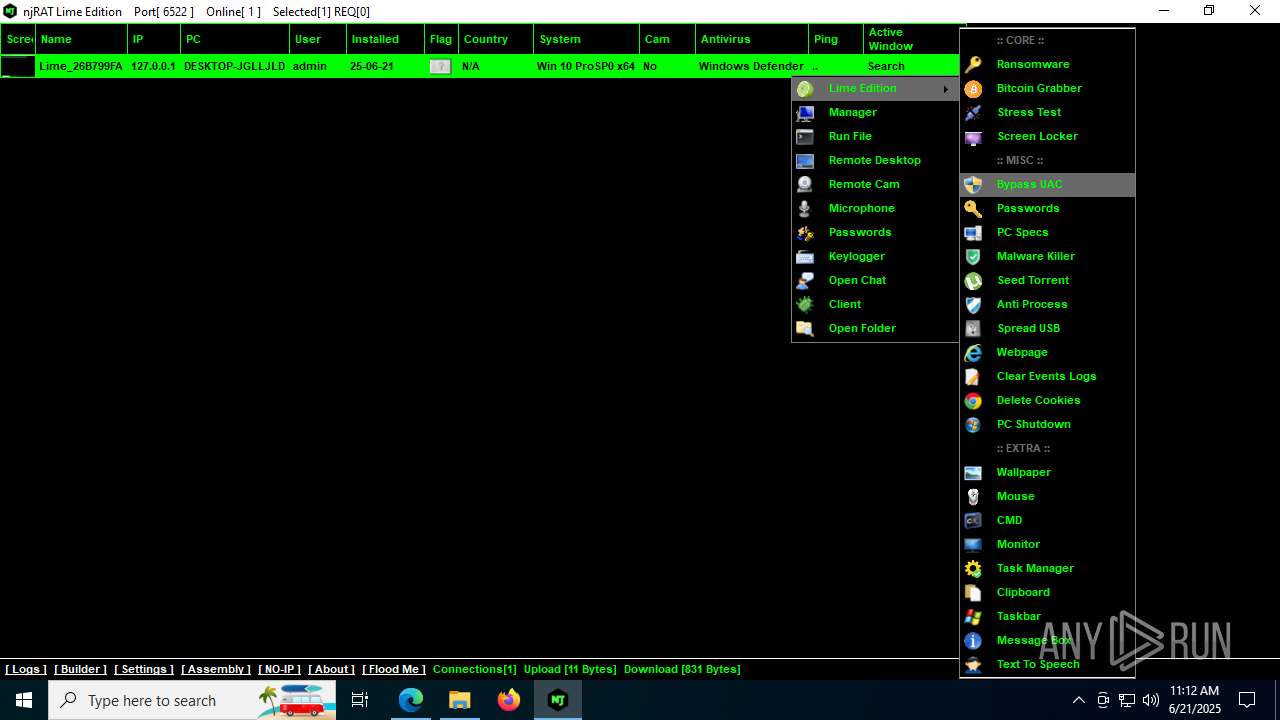
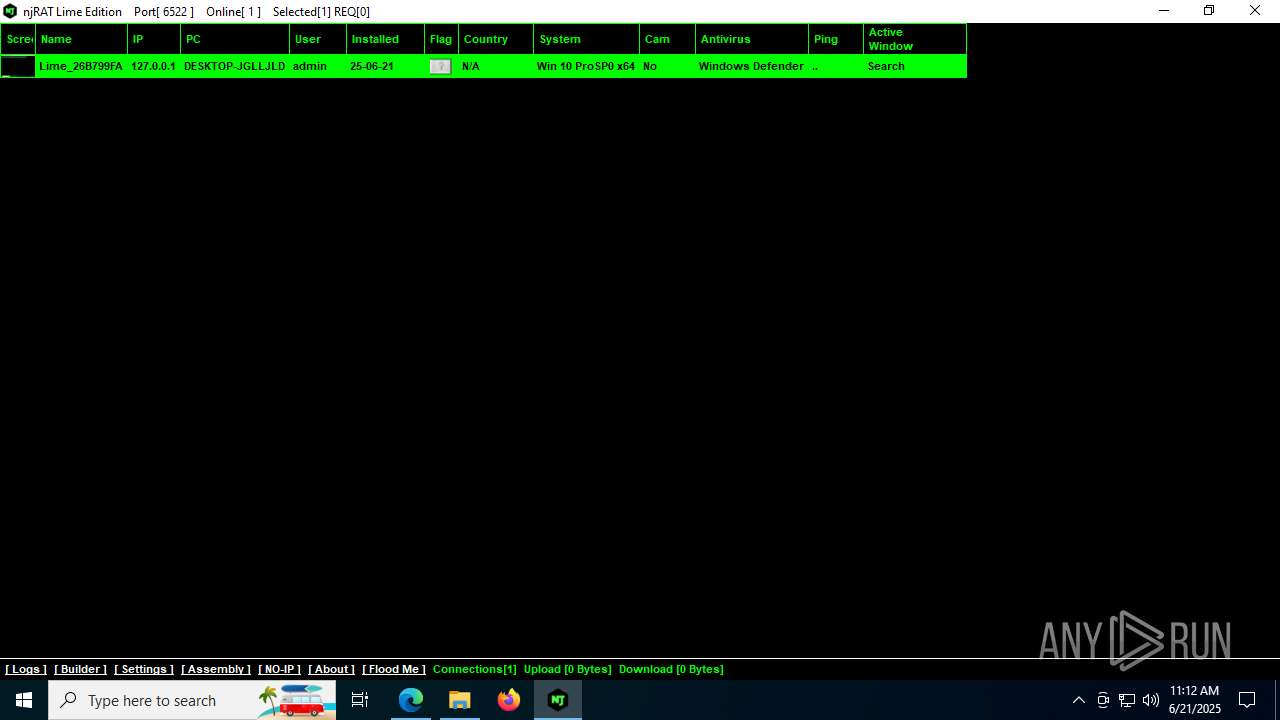
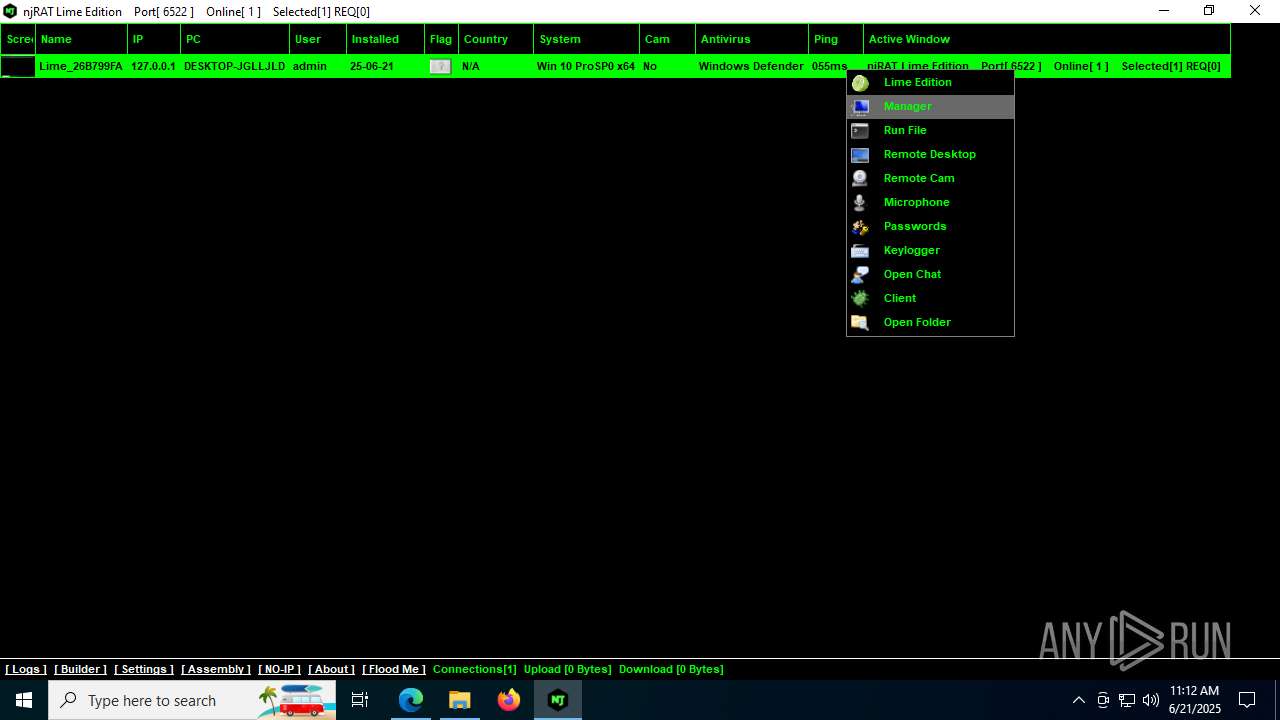
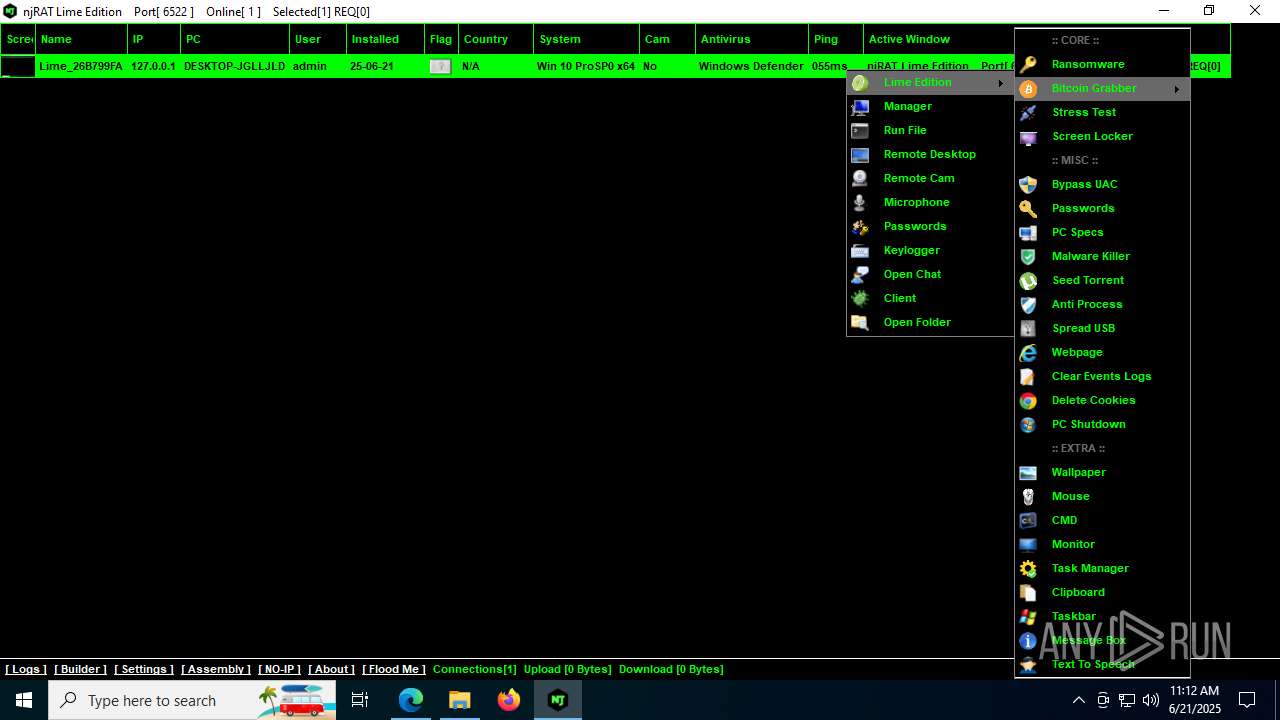
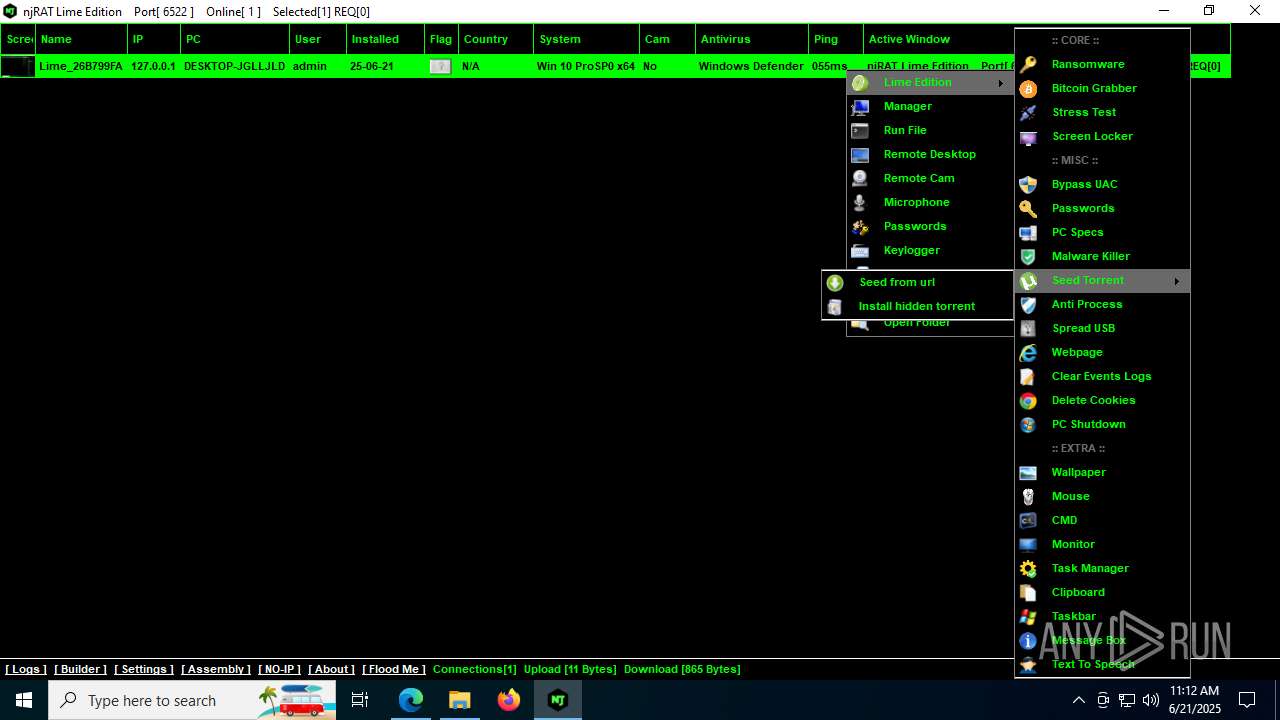
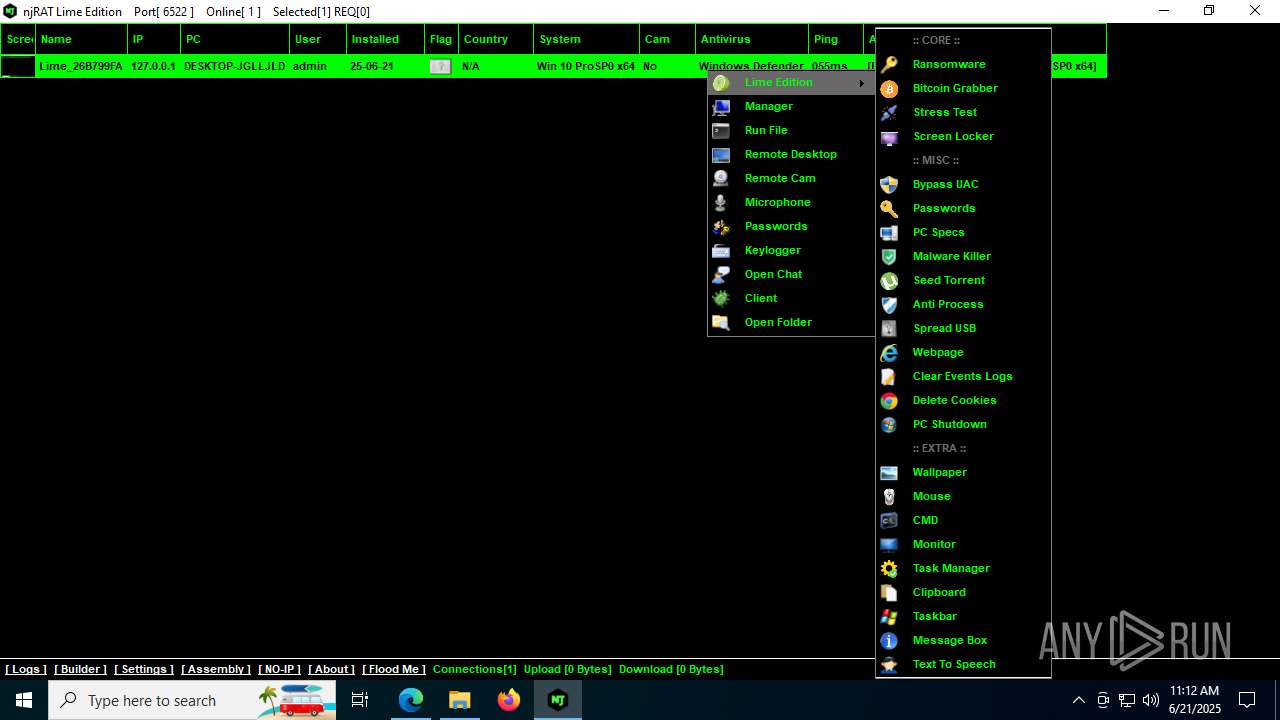
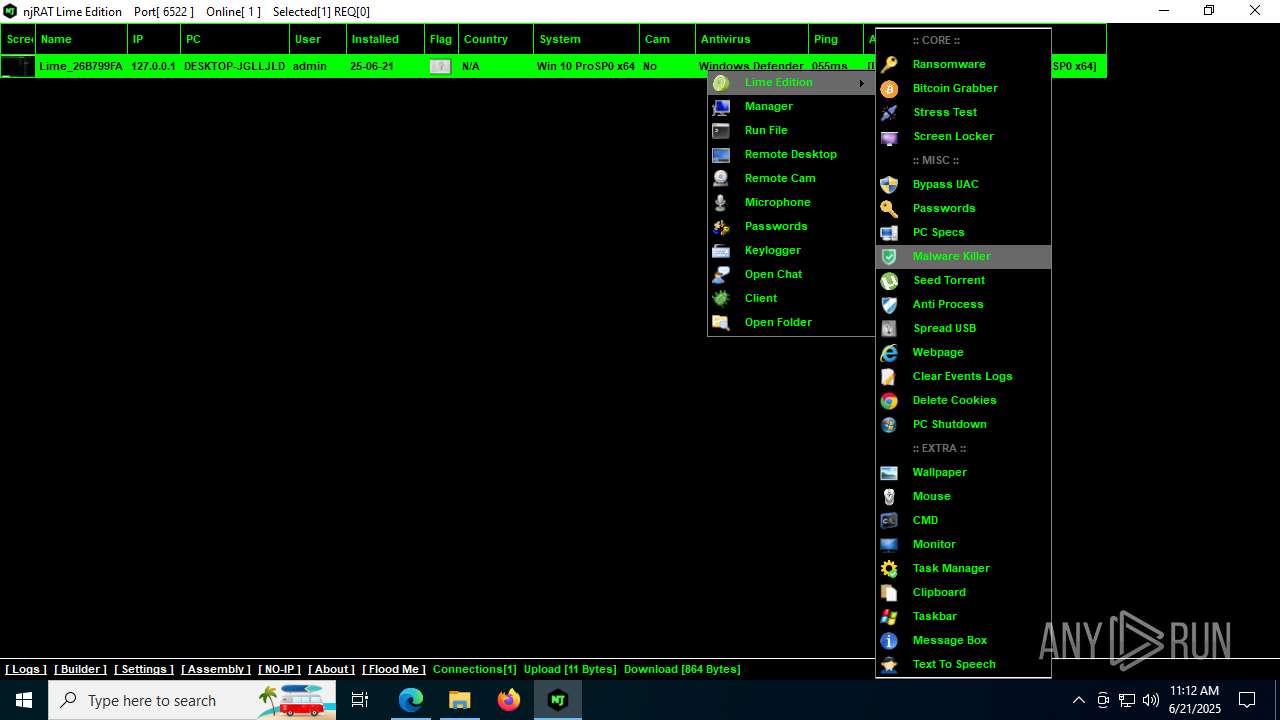
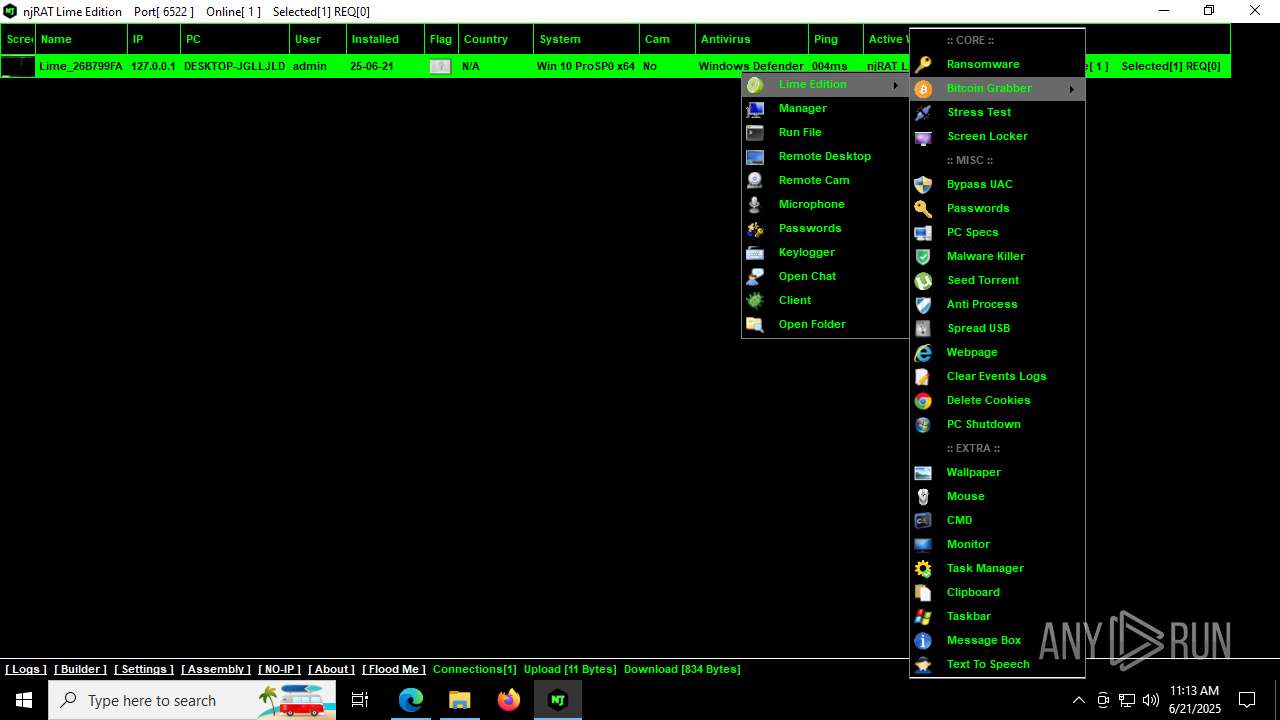
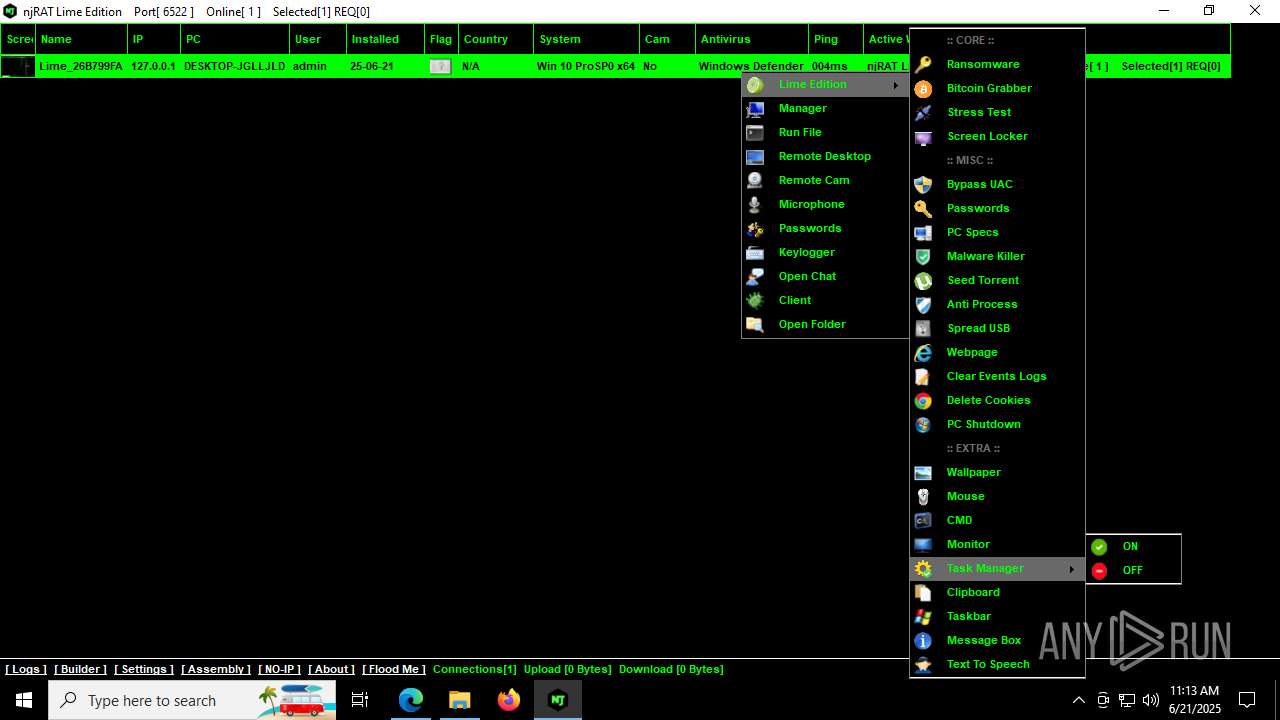
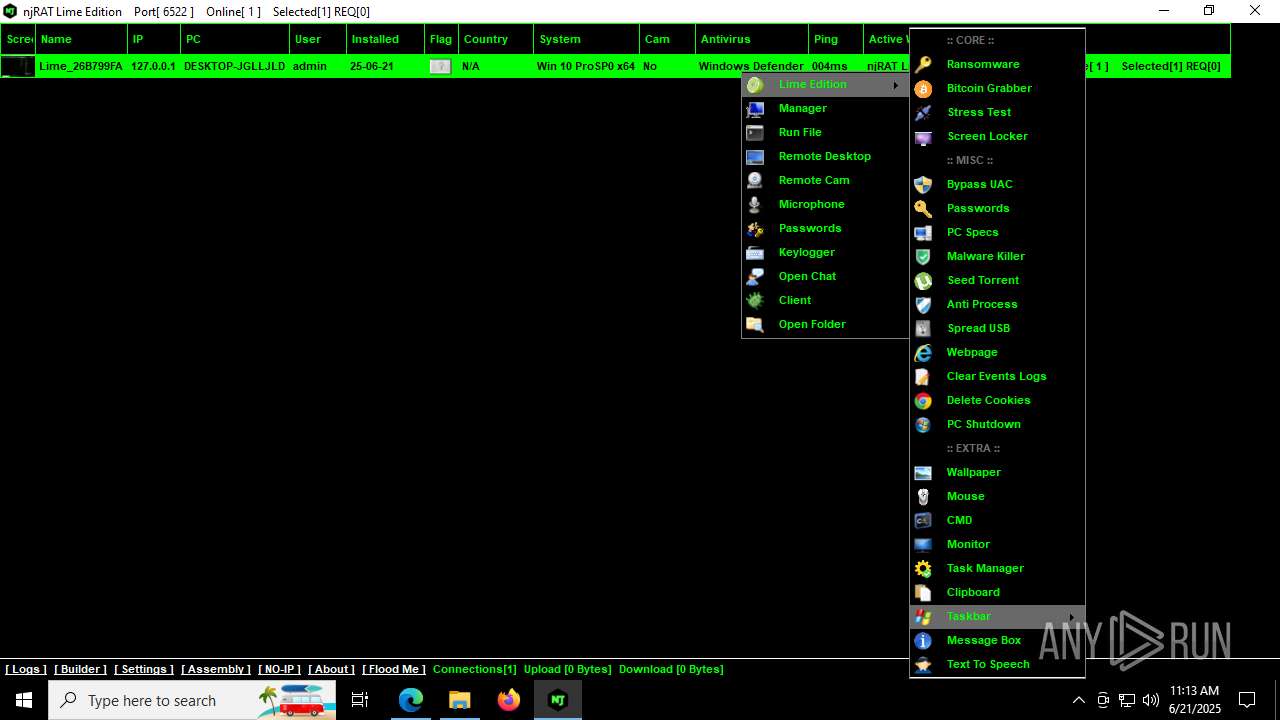
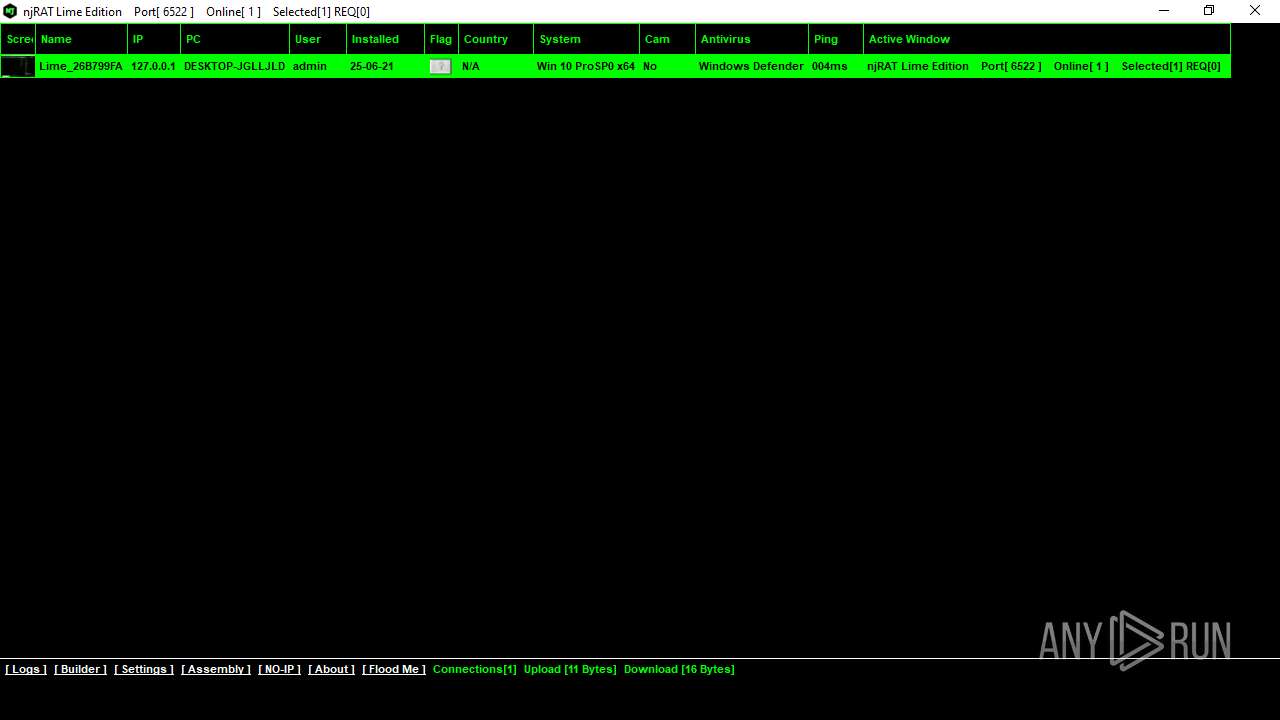
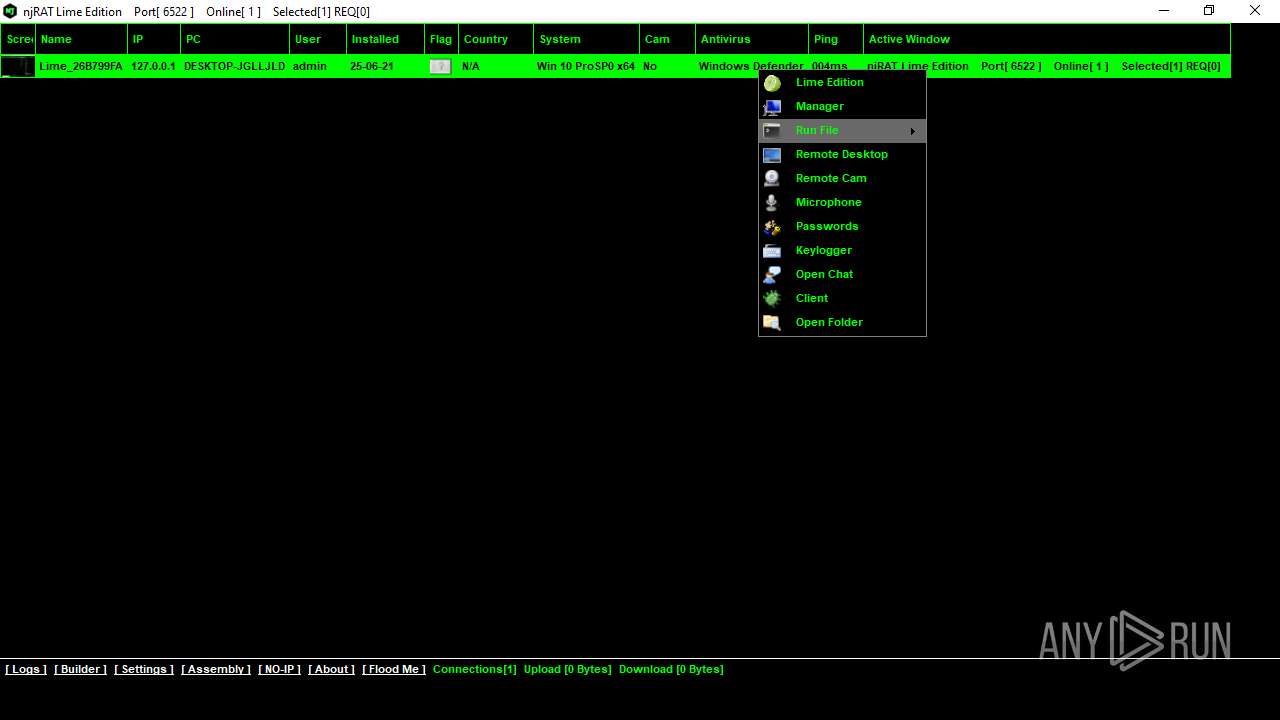
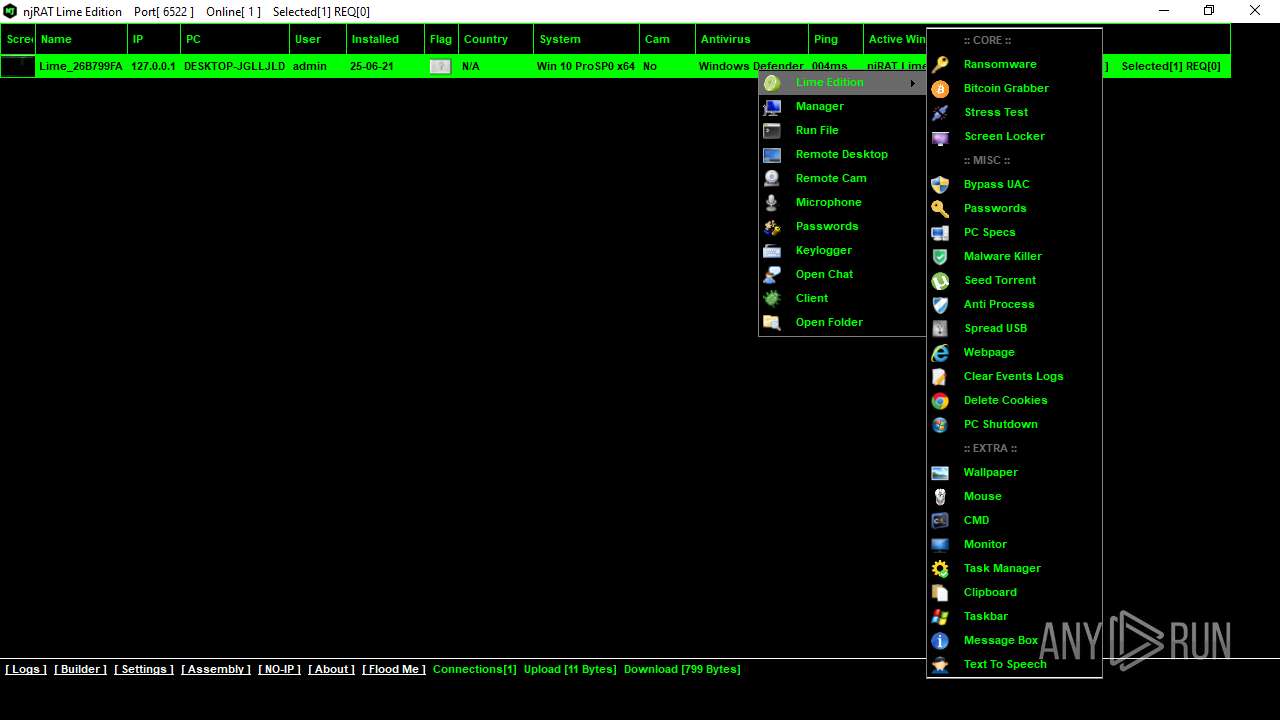
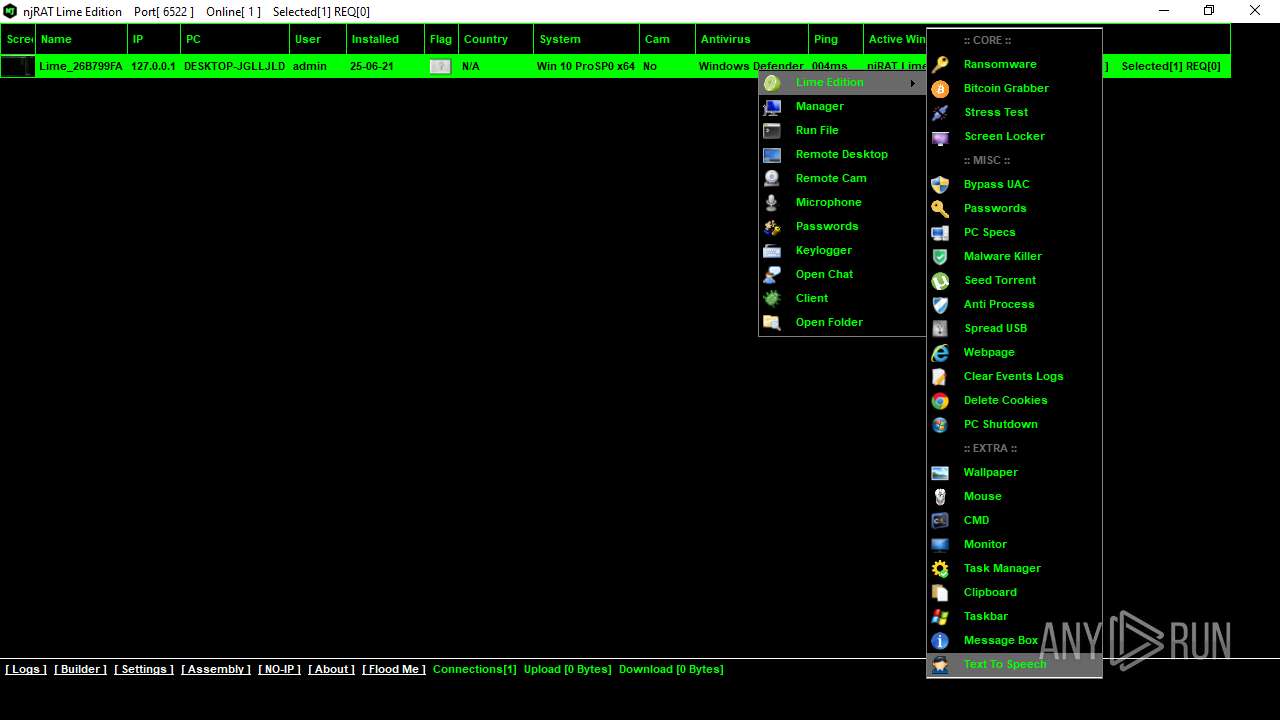
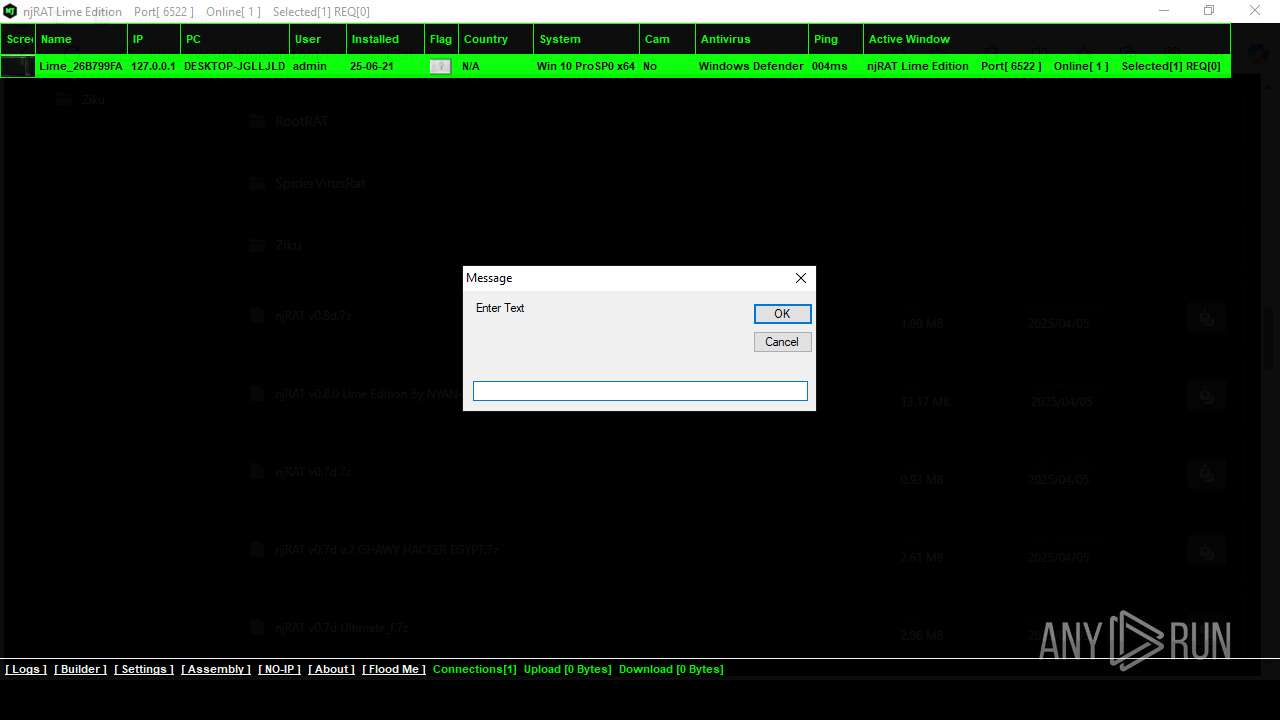
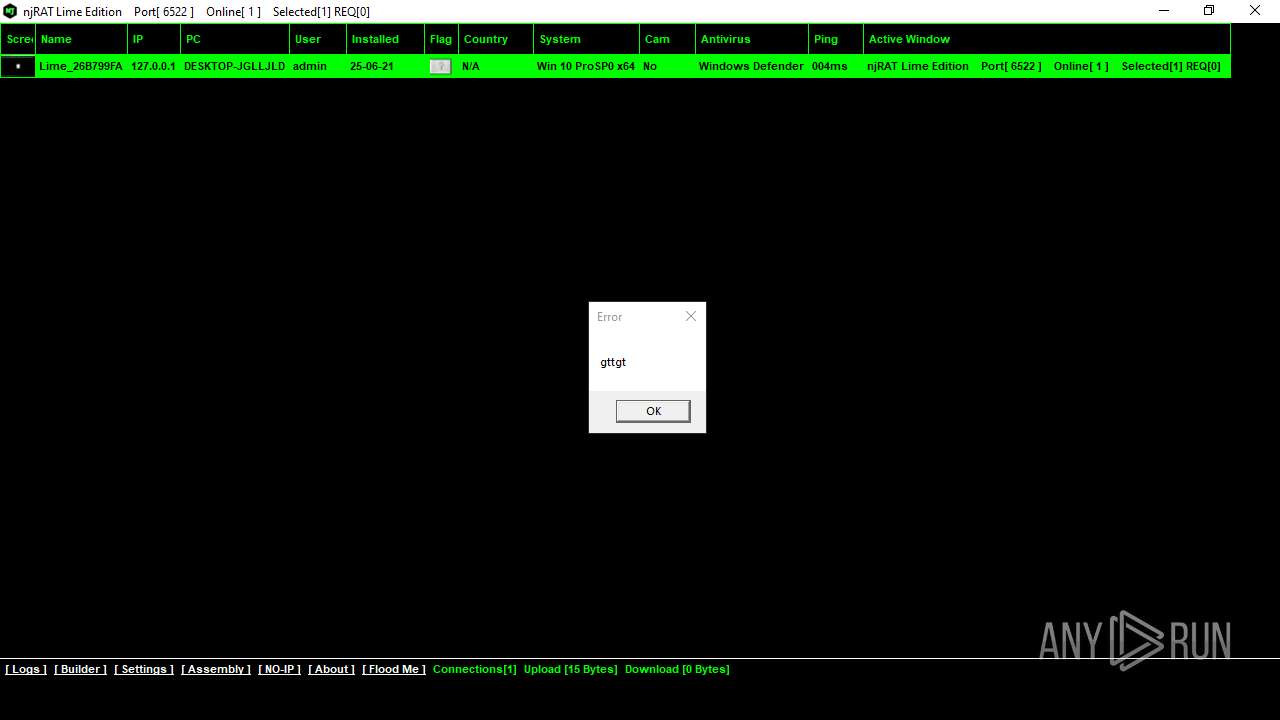
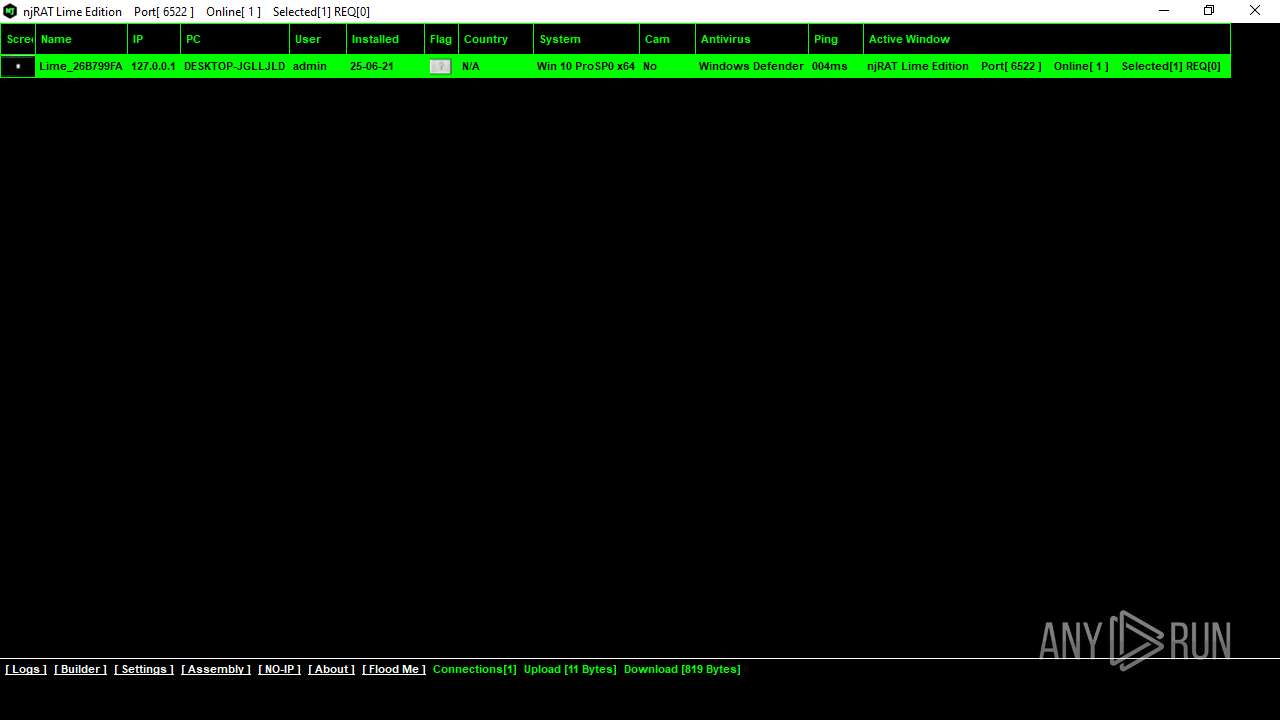
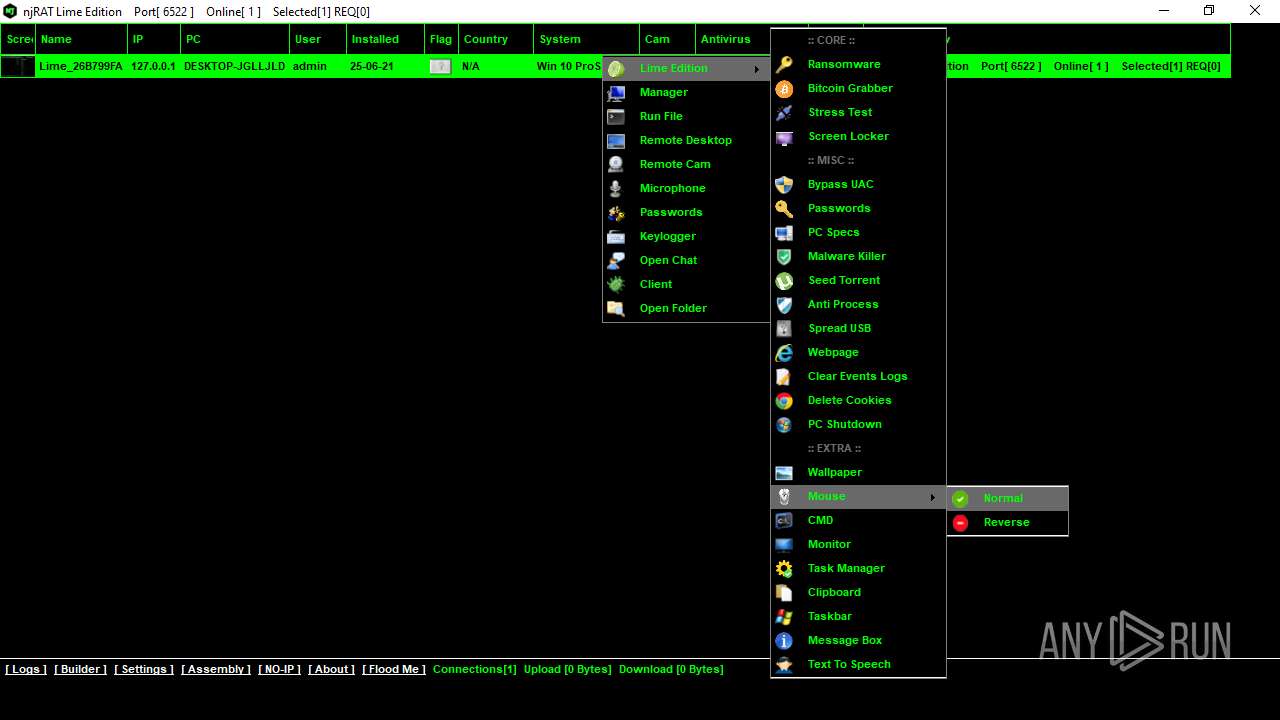
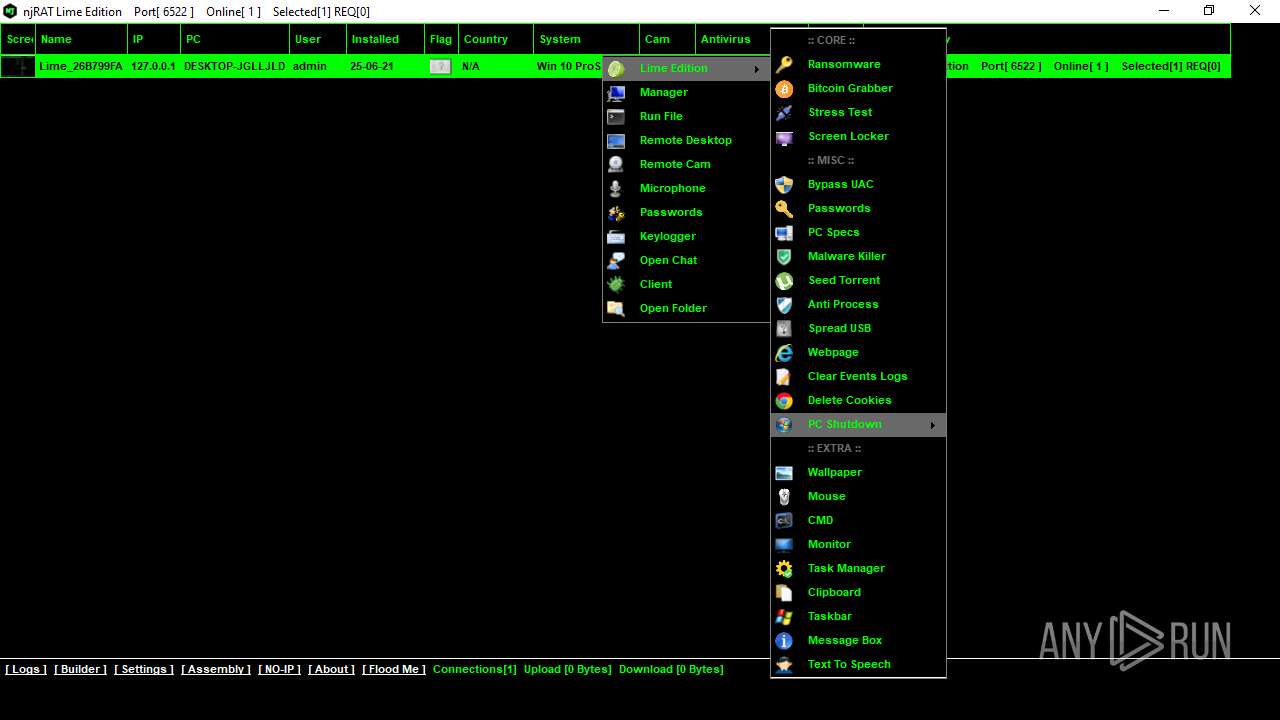
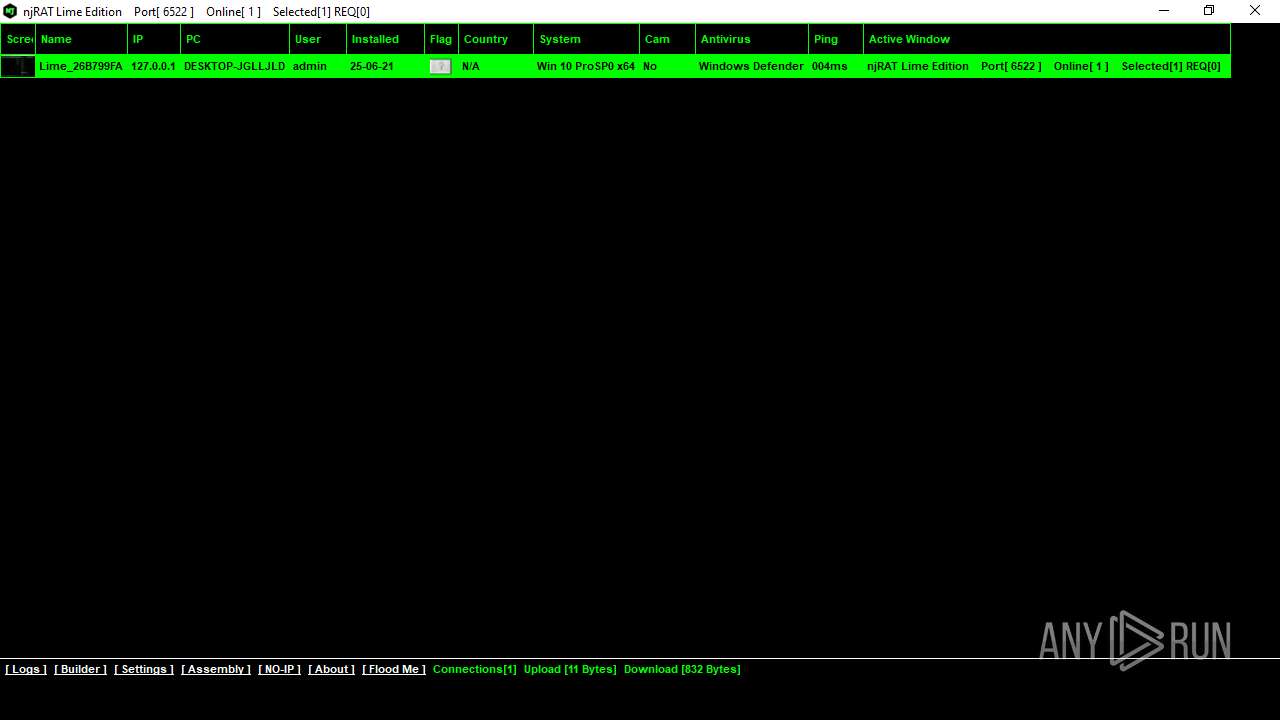
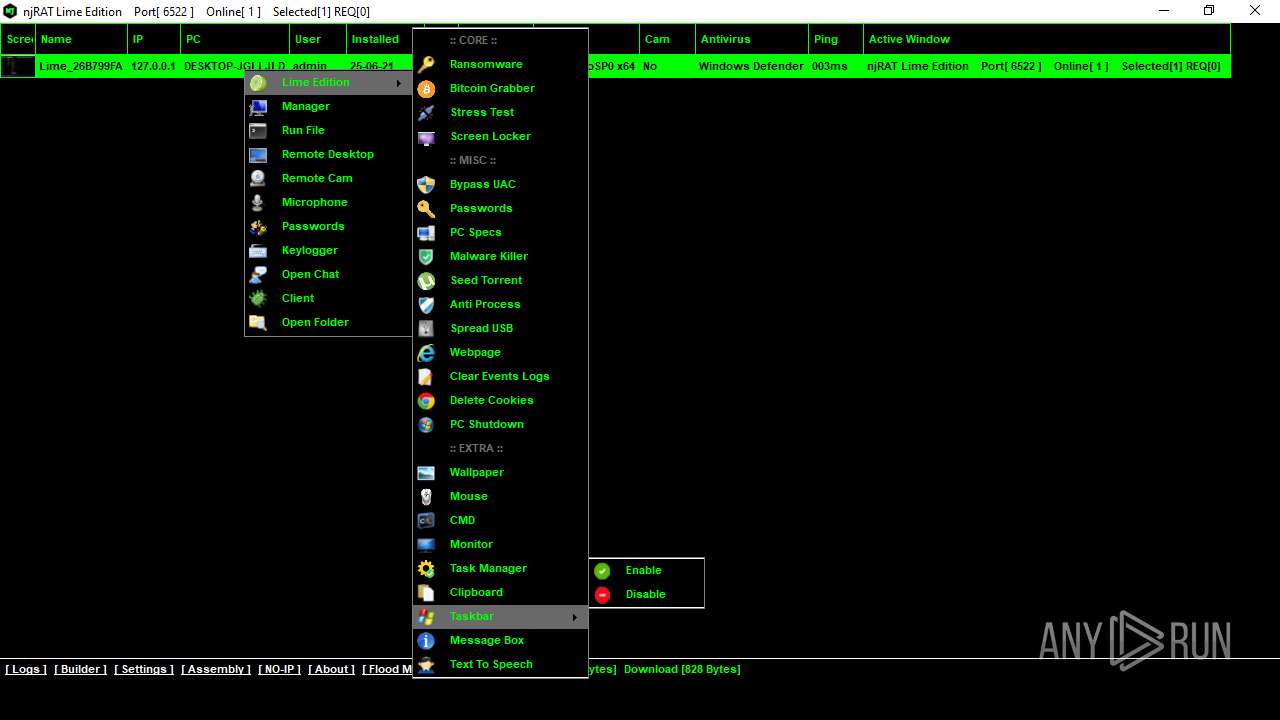
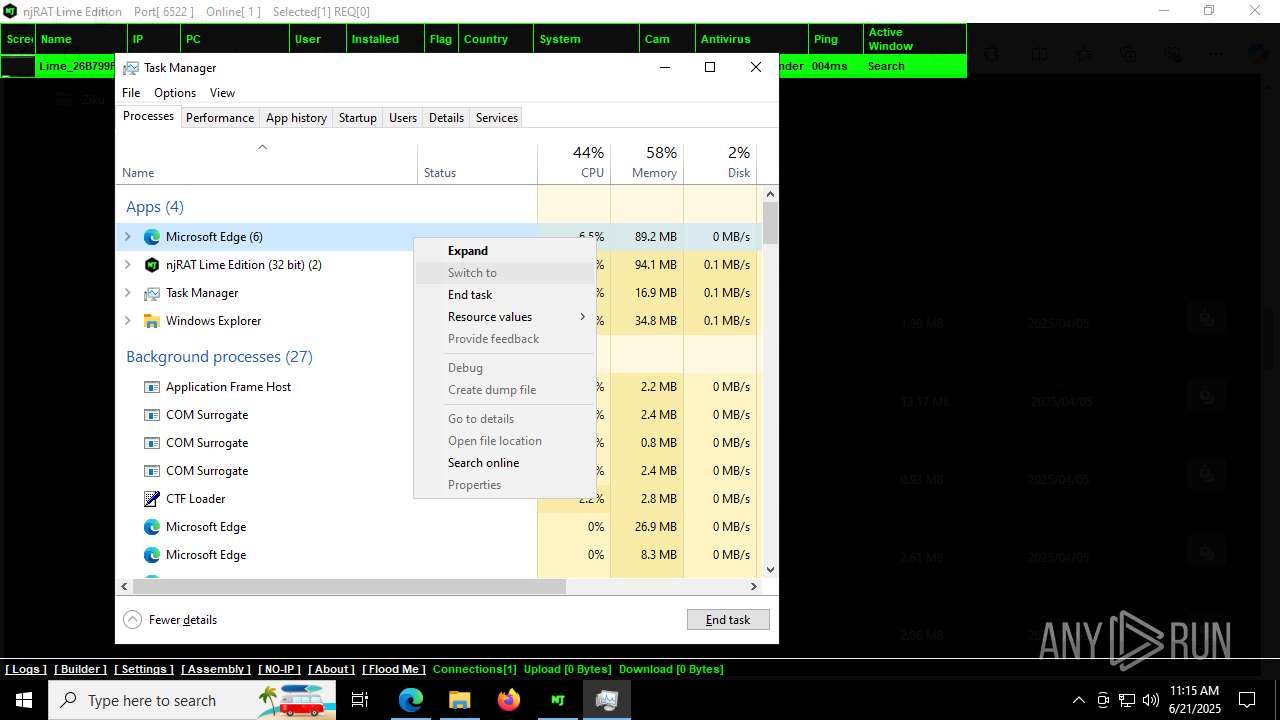
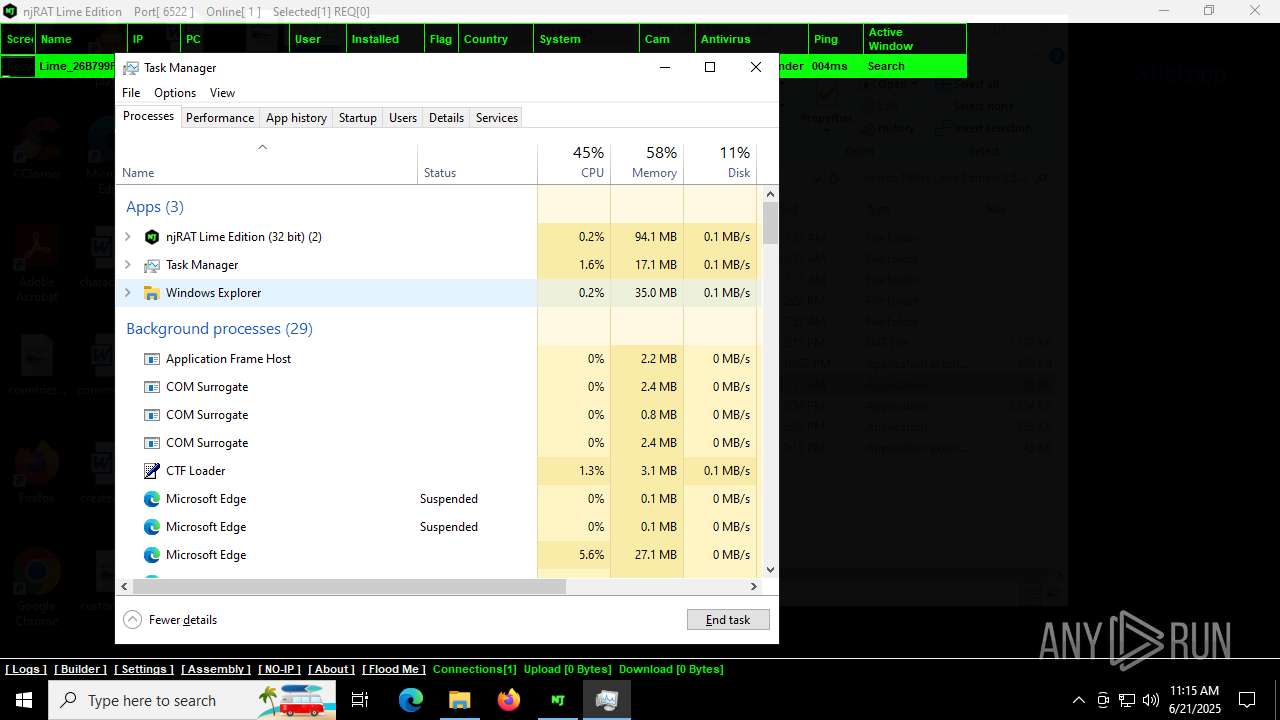
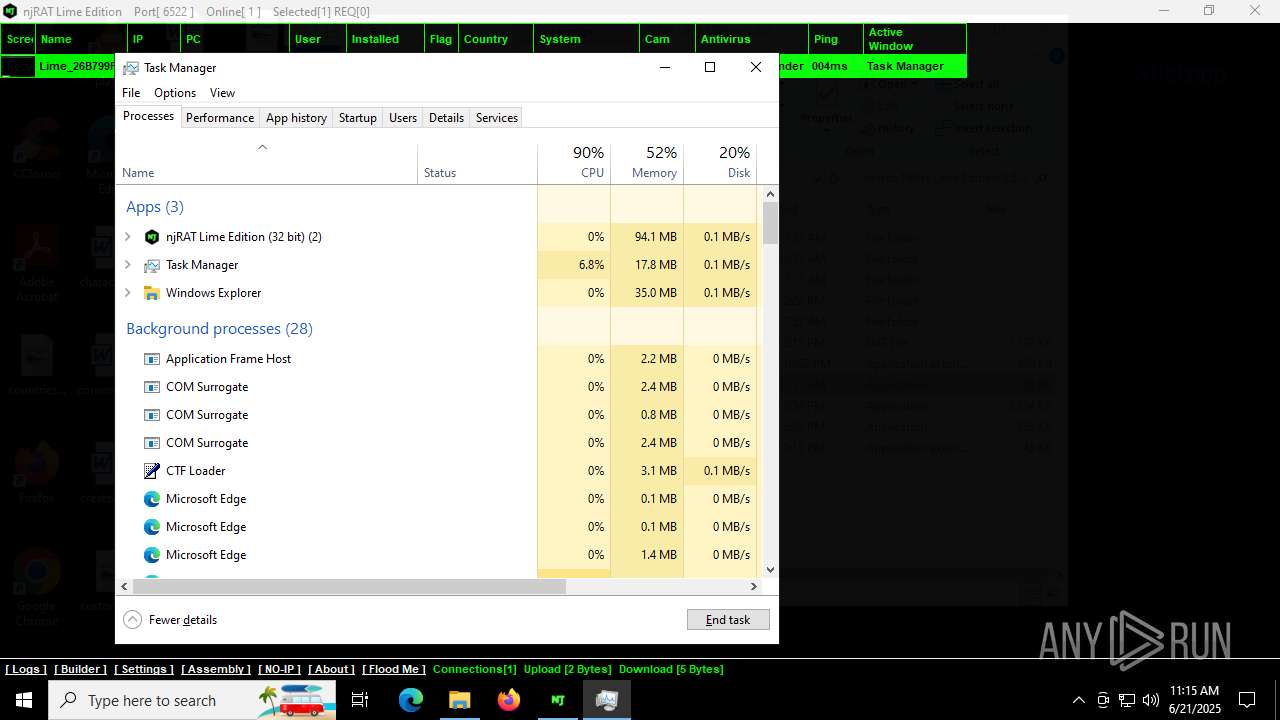
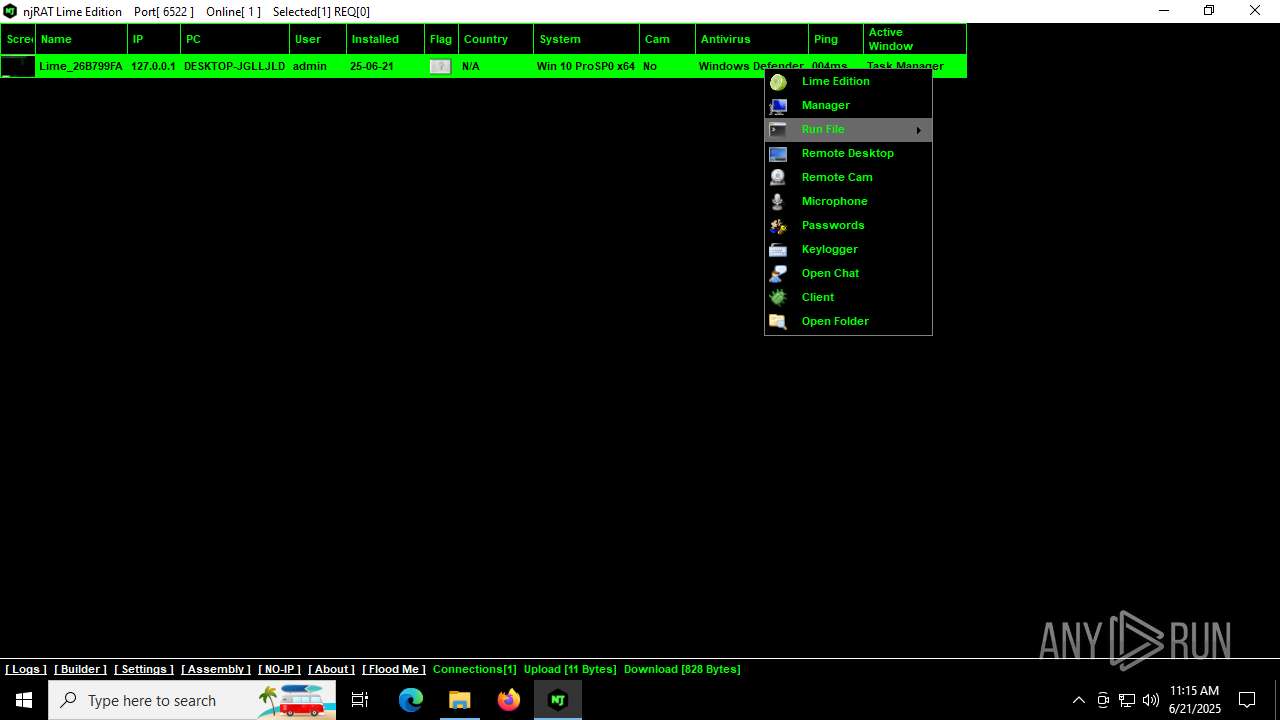
| Threats: | njRAT is a remote access trojan. It is one of the most widely accessible RATs on the market that features an abundance of educational information. Interested attackers can even find tutorials on YouTube. This allows it to become one of the most popular RATs in the world. |
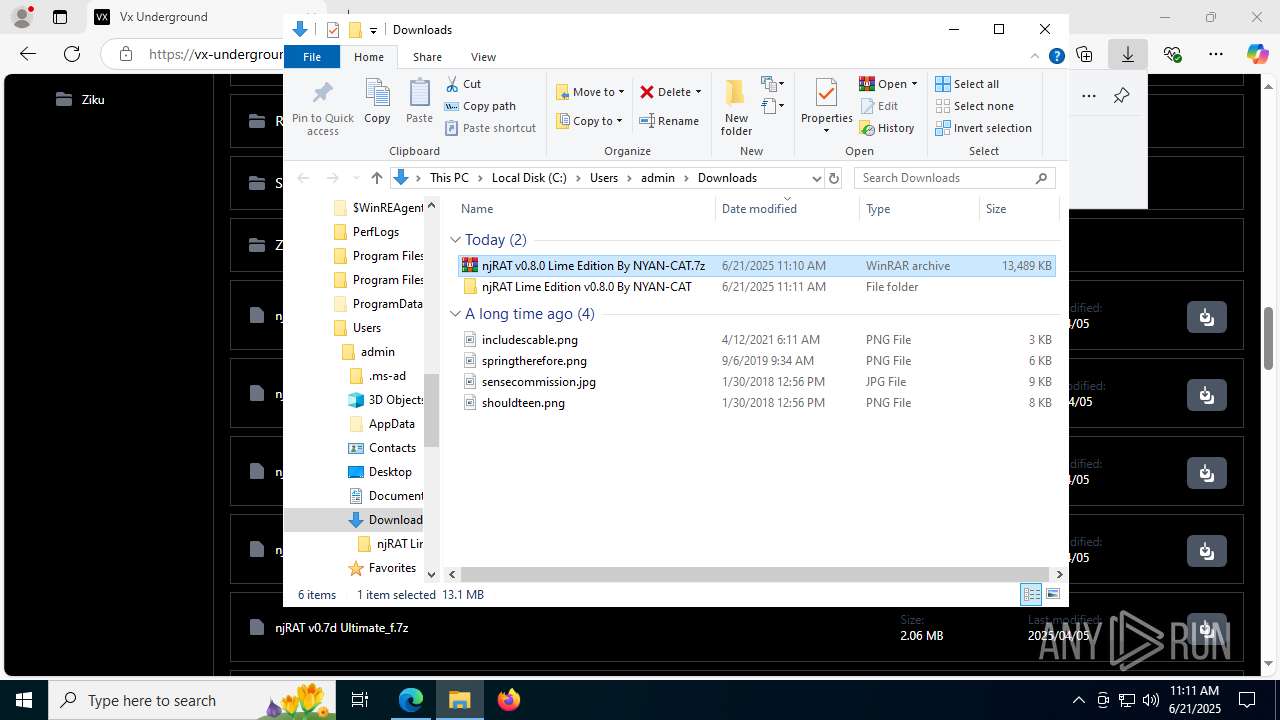
| Analysis date: | June 21, 2025, 11:10:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 45D0B9189C5A691F7C06B1D7F954FA5B |
| SHA1: | A90D34FD82FCEAFB27CB8AAF64BB4F4D654EF852 |
| SHA256: | A573A97A1C36D3CE94DAC97F1A095C12B11BBAD7807920031684E9E01BD74709 |
| SSDEEP: | 3:N83mWAn:23mWA |
MALICIOUS
NJRAT mutex has been found
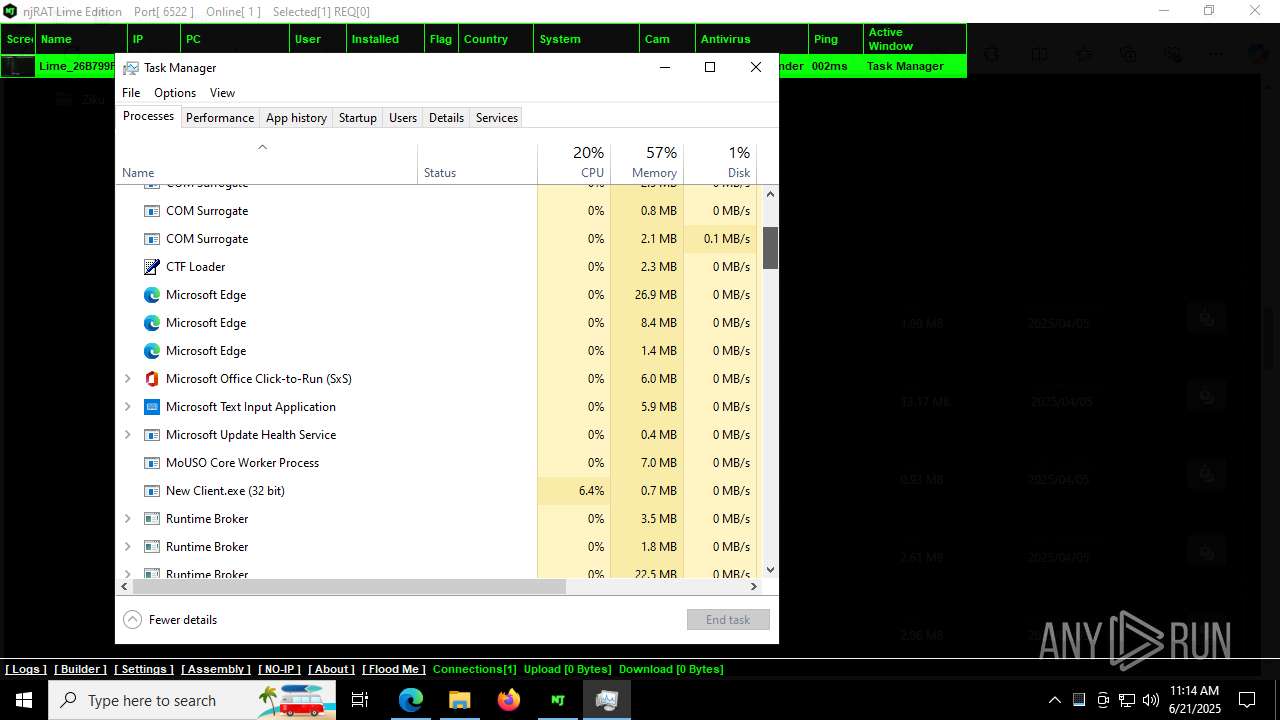
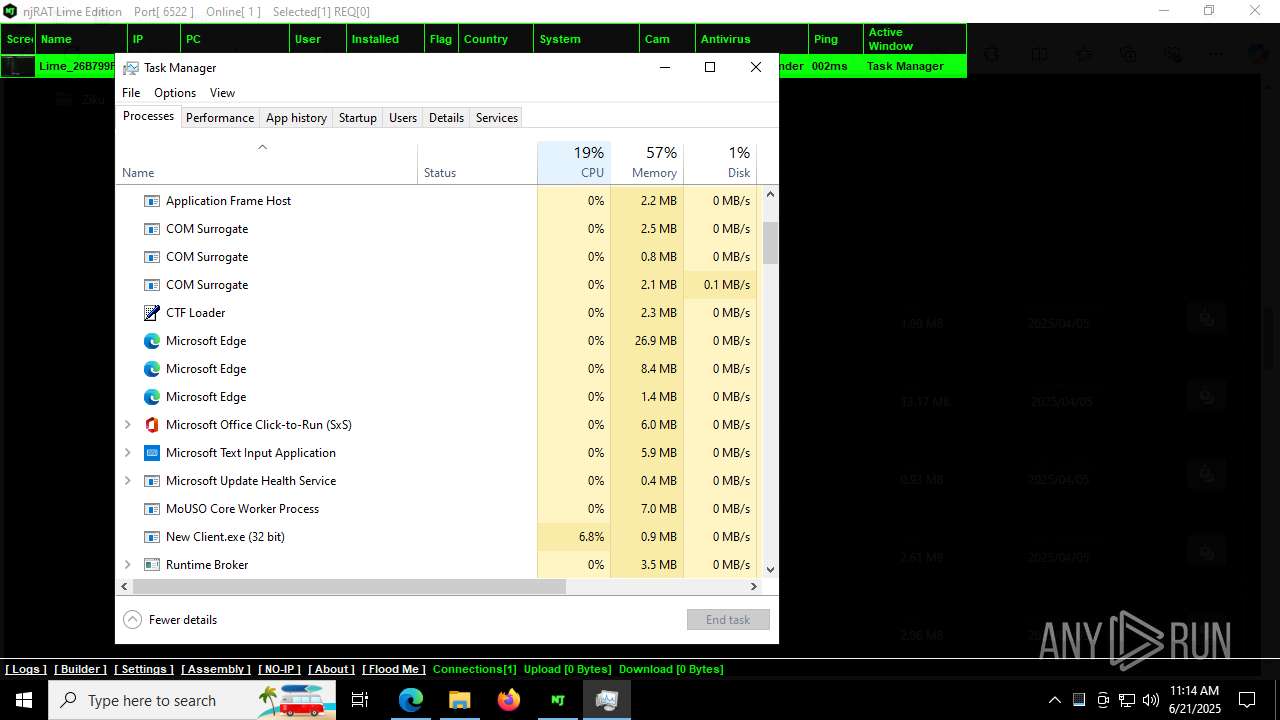
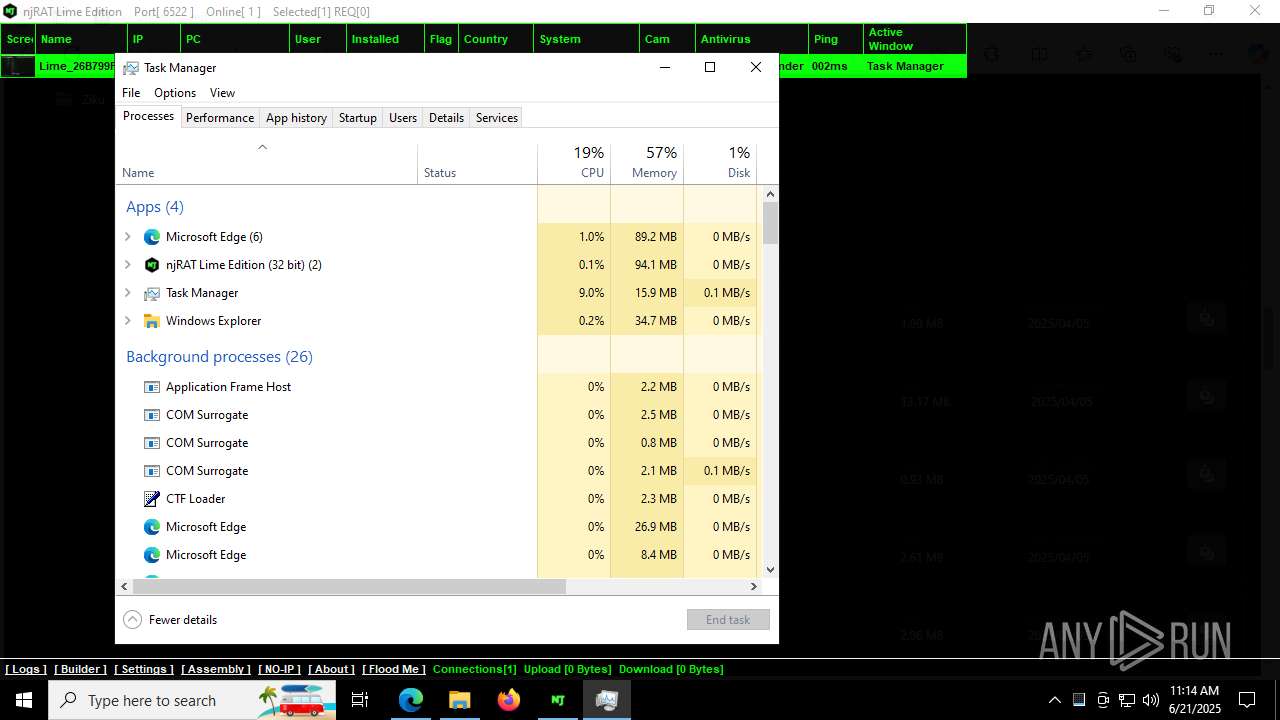
- New Client.exe (PID: 7420)
- New Client.exe (PID: 504)
NJRAT has been detected (YARA)
- New Client.exe (PID: 7420)
- New Client.exe (PID: 504)
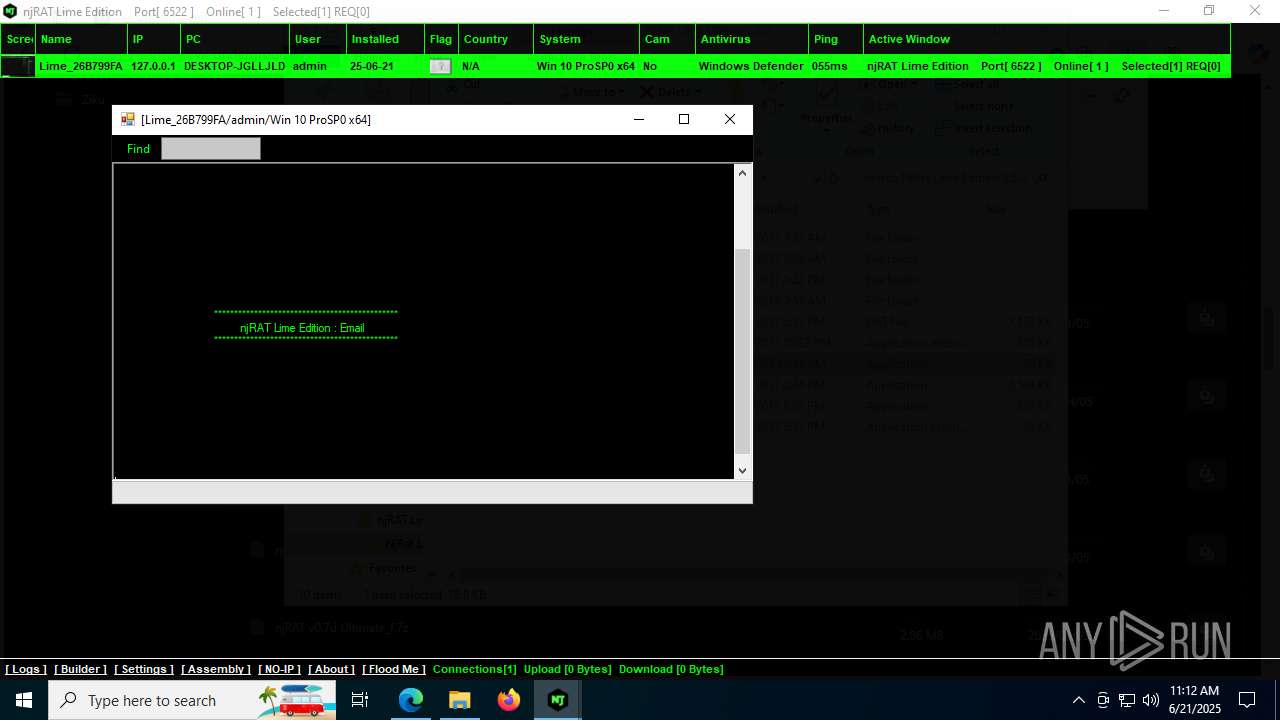
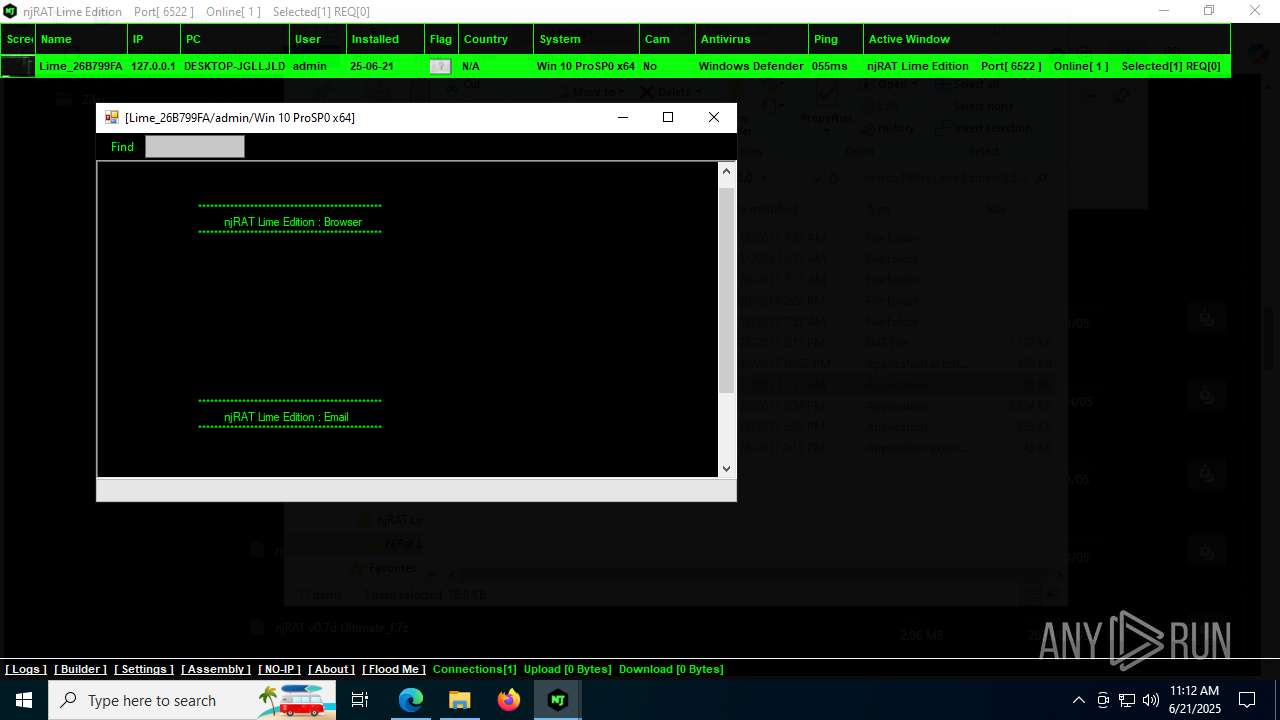
Actions looks like stealing of personal data
- email.exe (PID: 5564)
- browser.exe (PID: 1580)
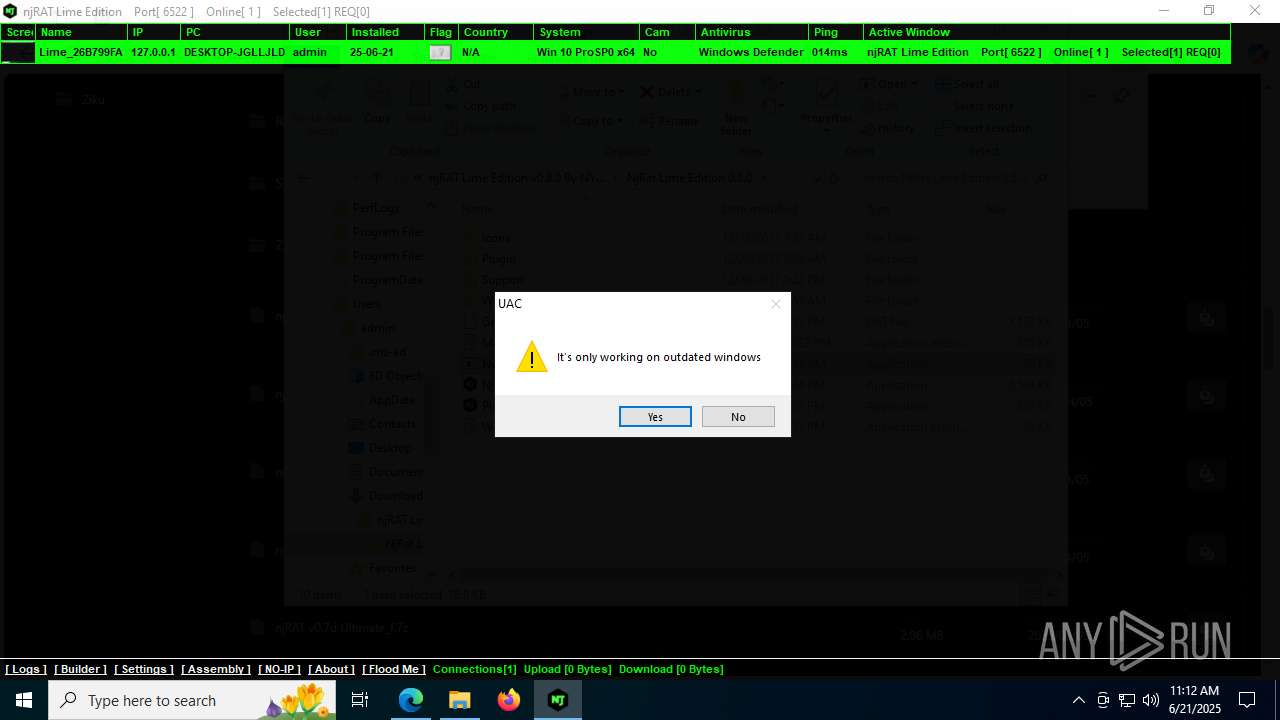
SUSPICIOUS
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 2864)
- NjRat Lime Edition 0.8.0.exe (PID: 7528)
- New Client.exe (PID: 7420)
- New Client.exe (PID: 504)
- browser.exe (PID: 1580)
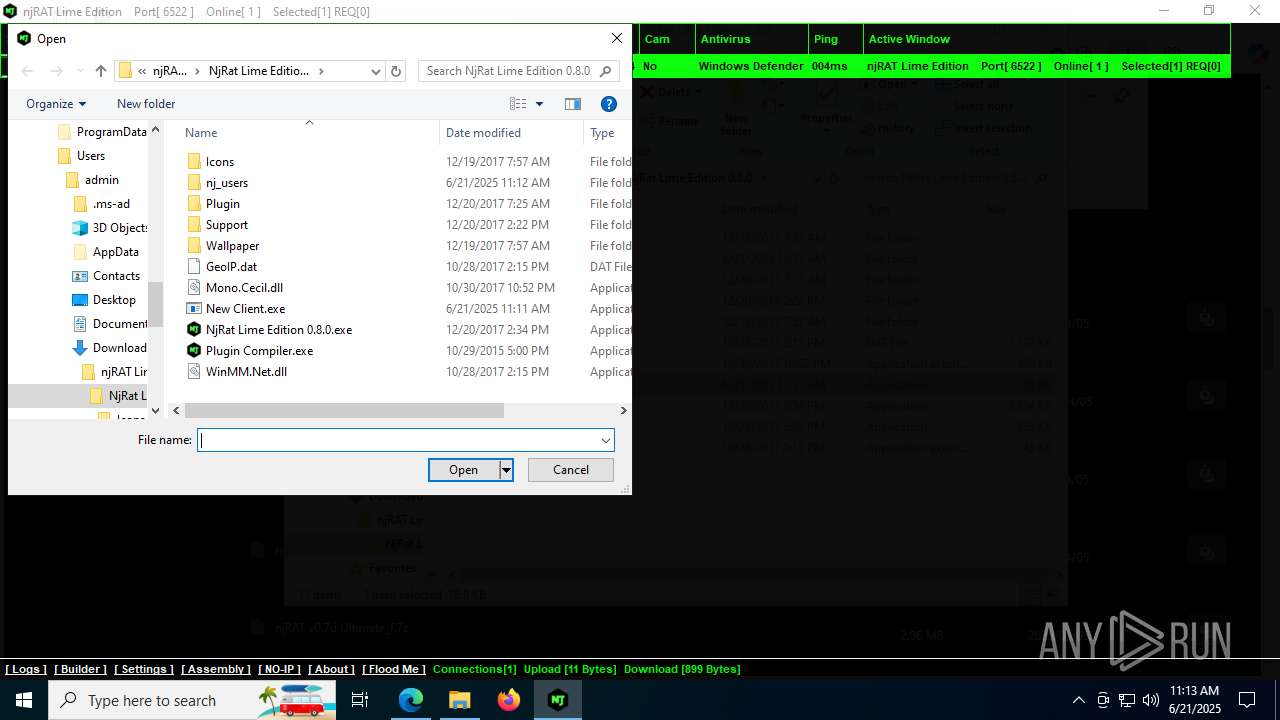
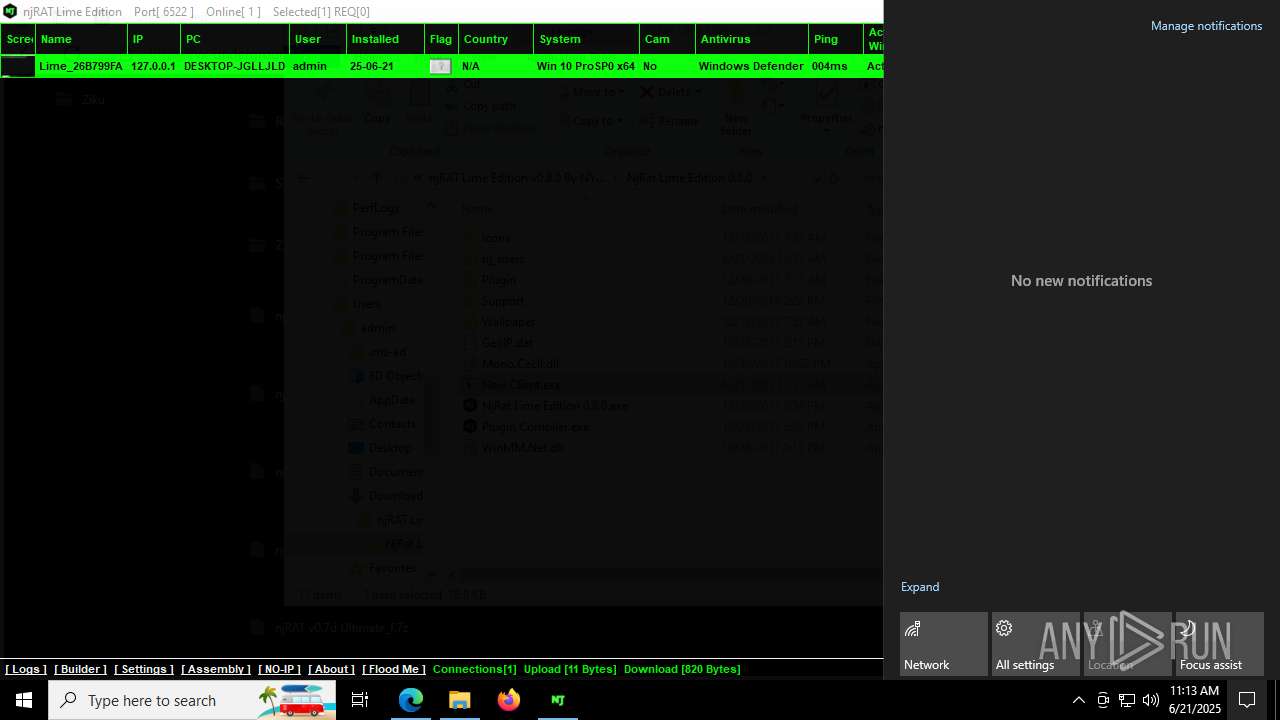
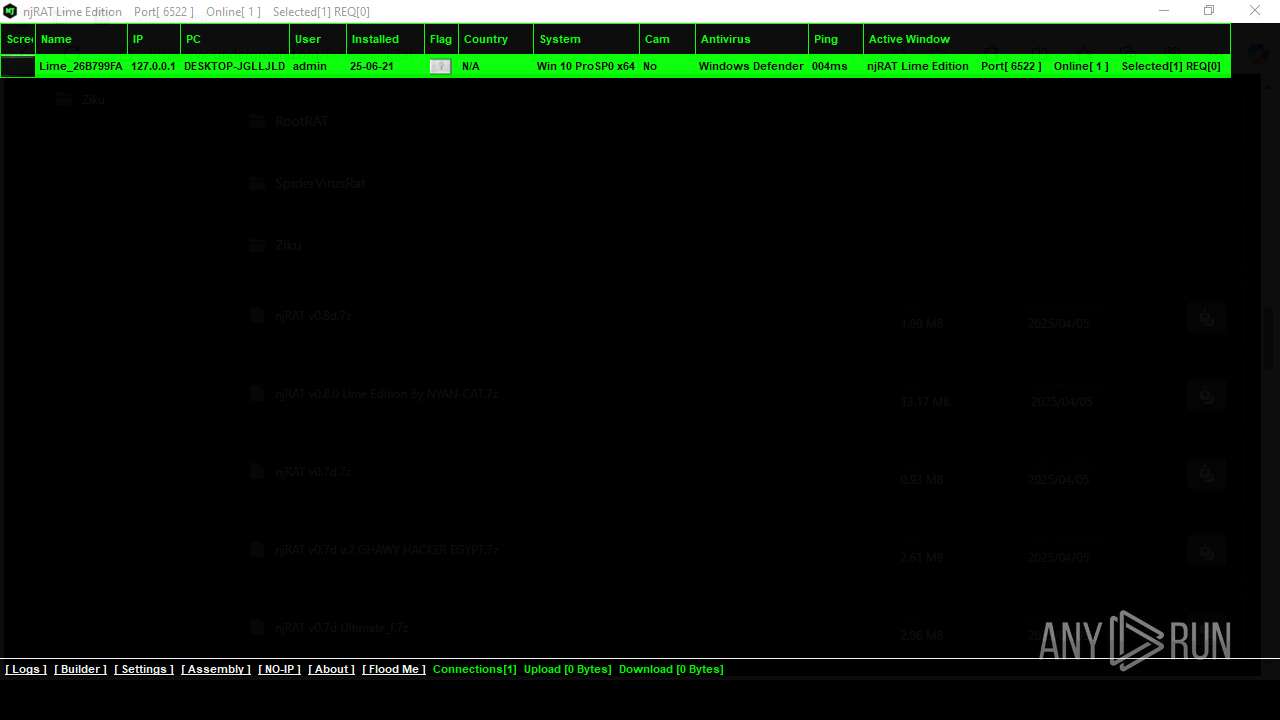
Creates file in the systems drive root
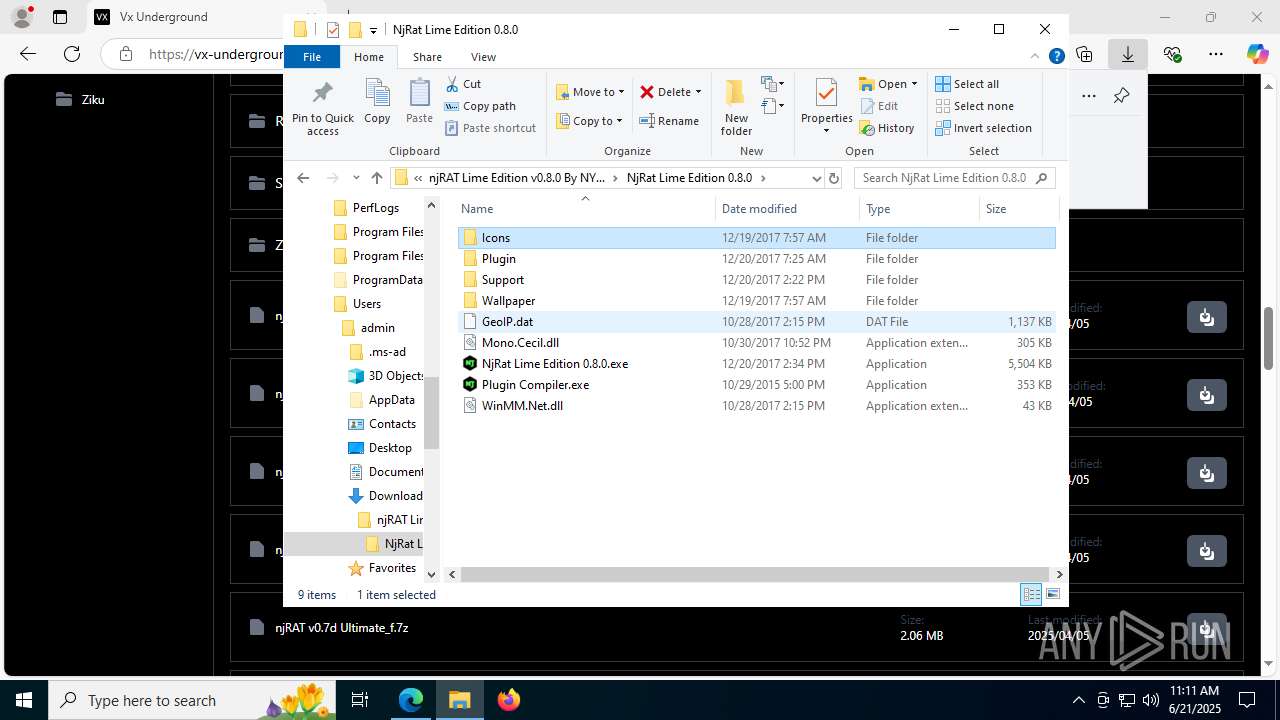
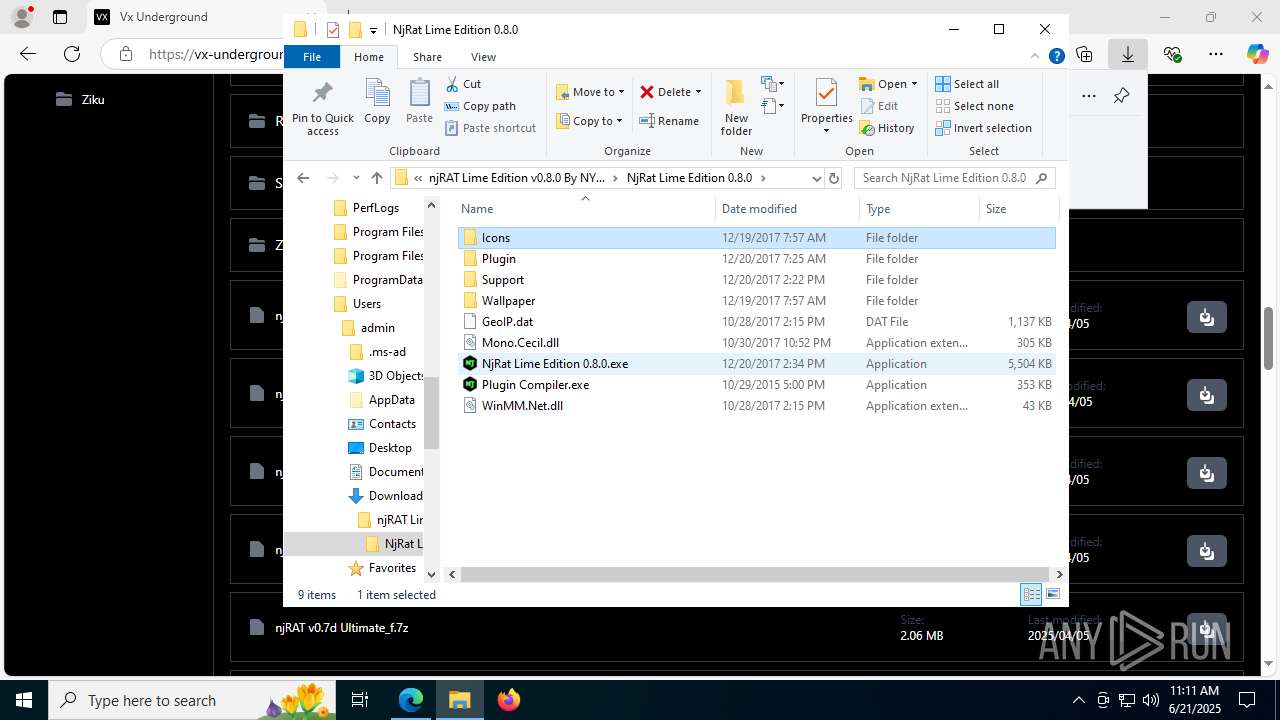
- NjRat Lime Edition 0.8.0.exe (PID: 7528)
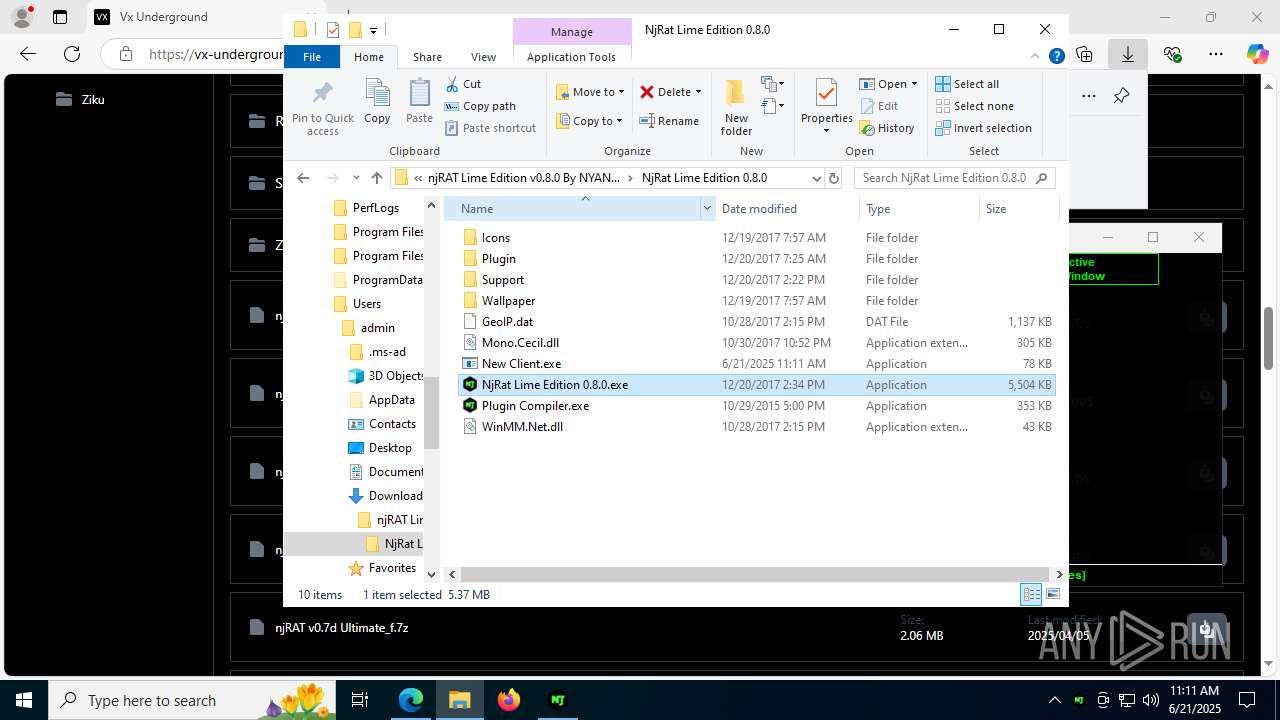
Executable content was dropped or overwritten
- NjRat Lime Edition 0.8.0.exe (PID: 7528)
- ilasm.exe (PID: 7712)
- New Client.exe (PID: 504)
- tmp8459.tmp.exe (PID: 7728)
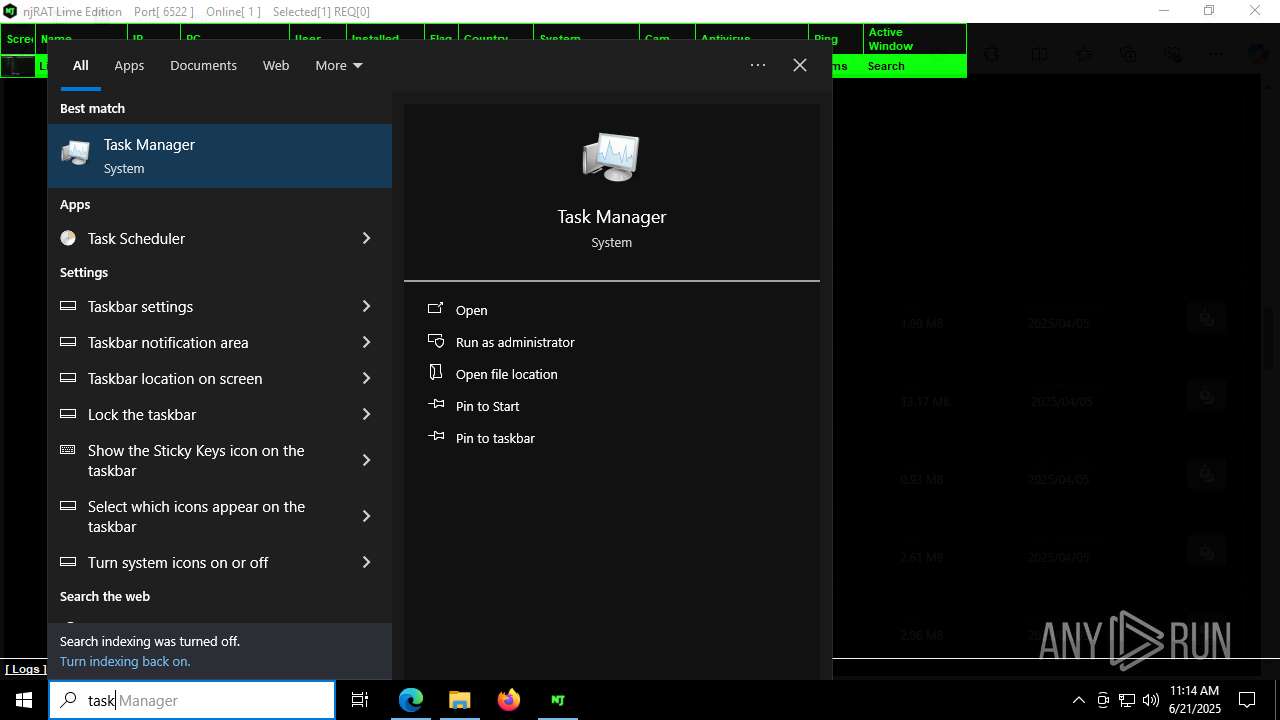
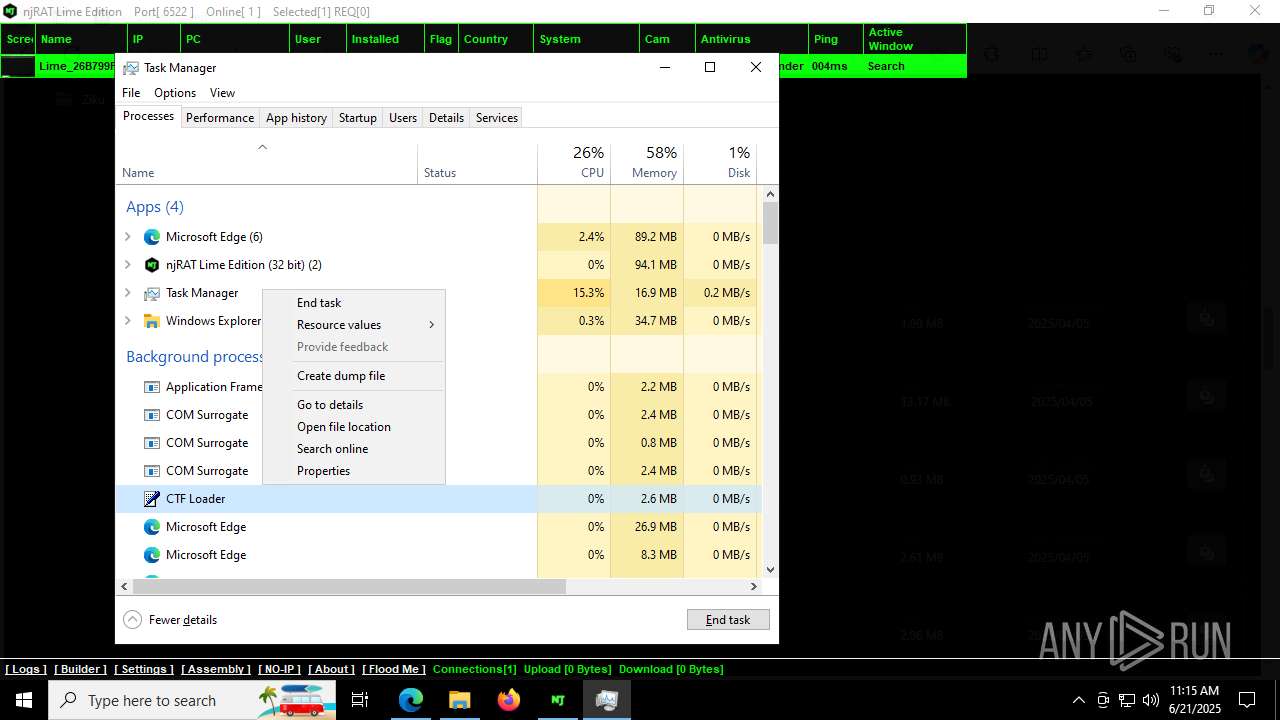
Uses TASKKILL.EXE to kill process
- New Client.exe (PID: 504)
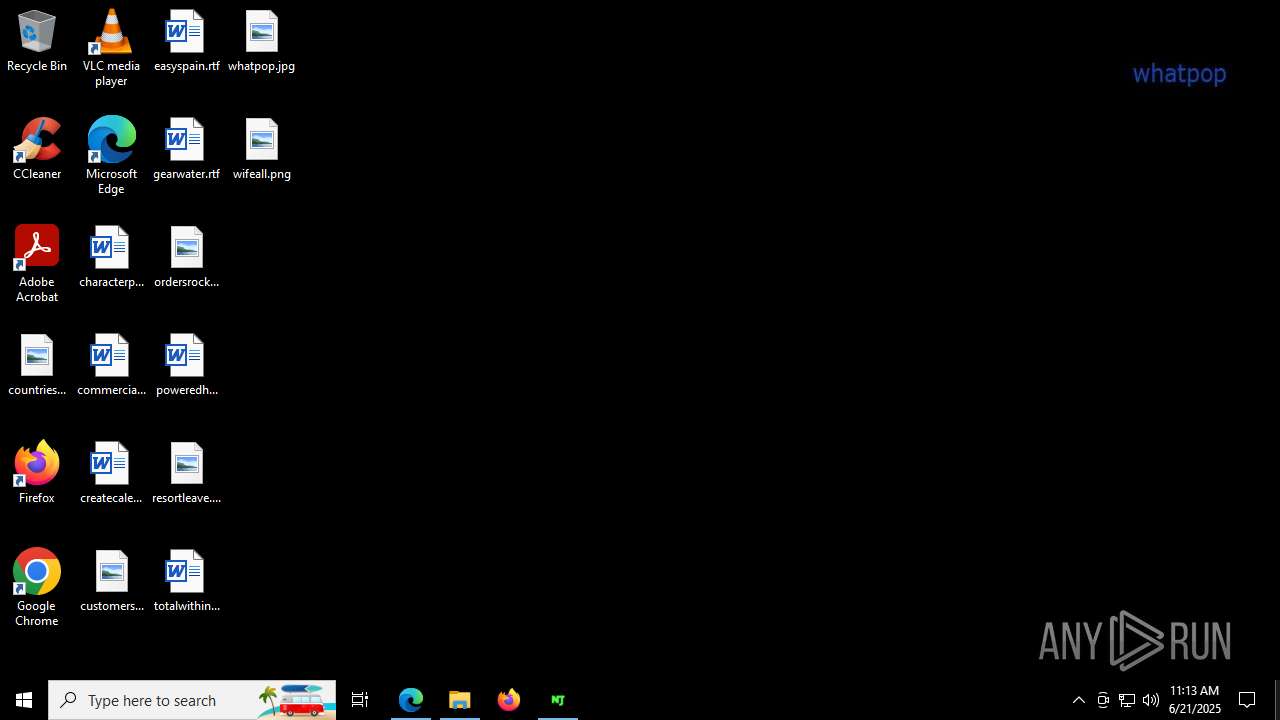
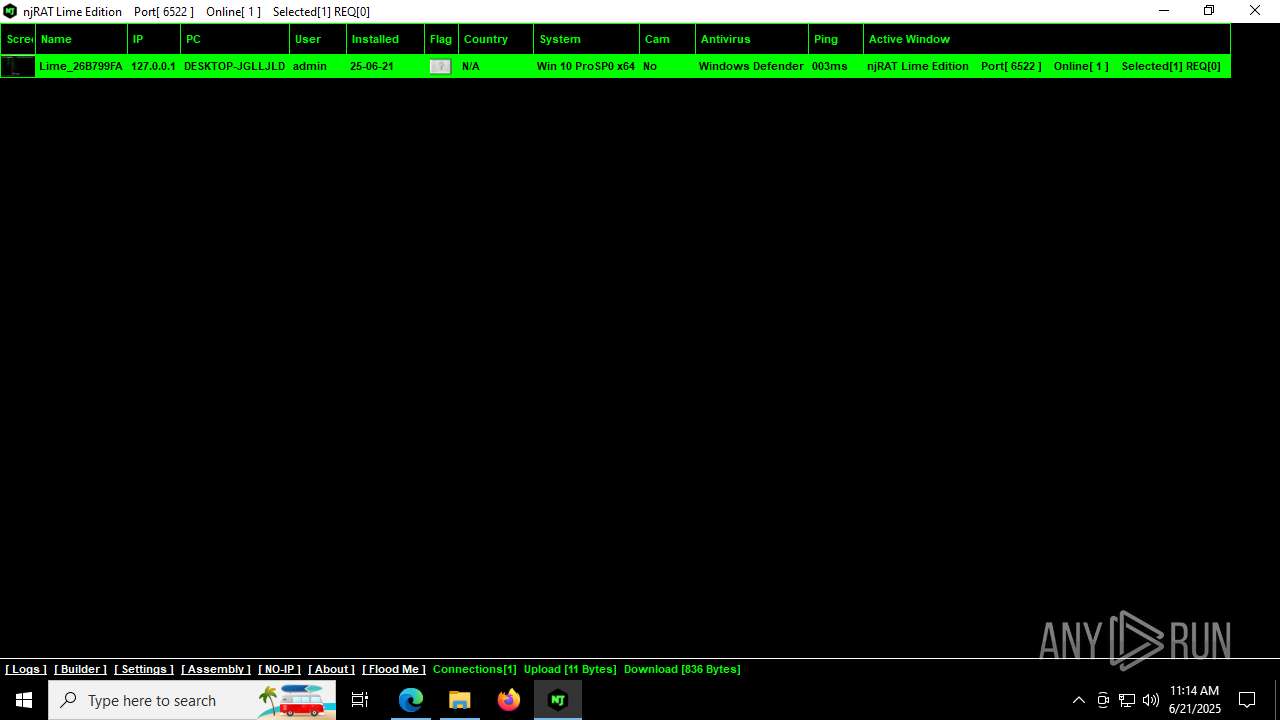
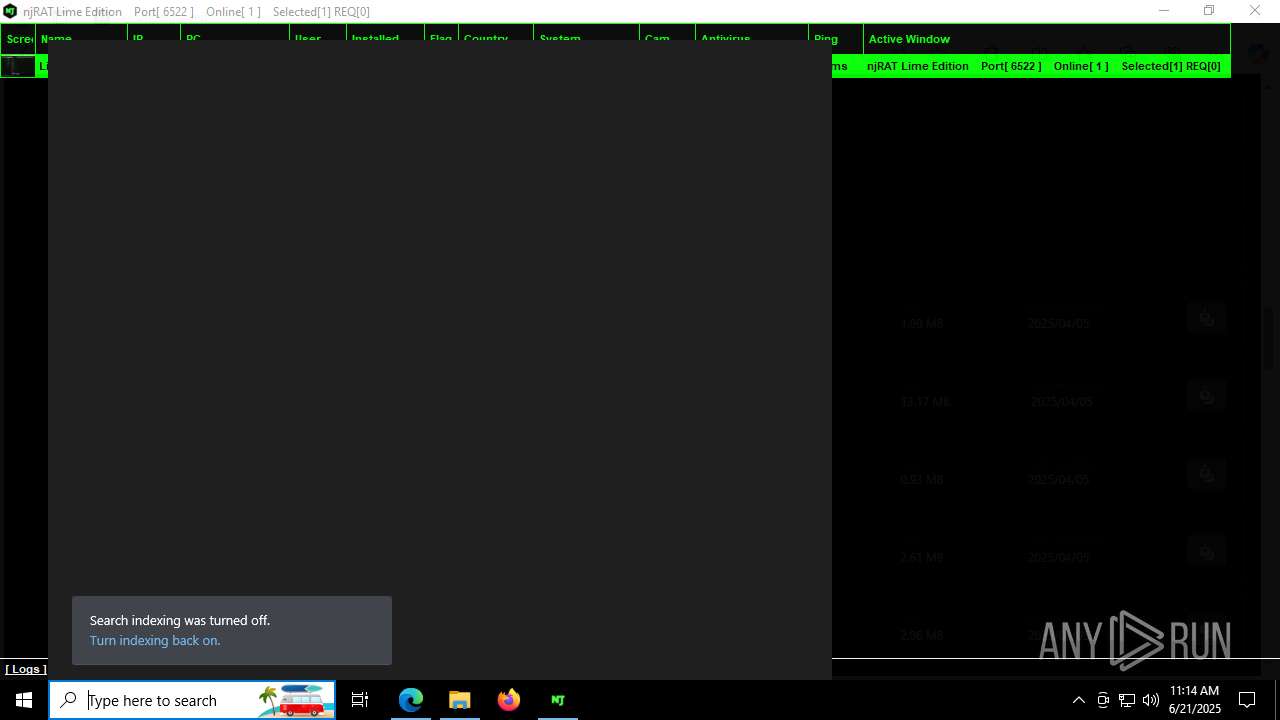
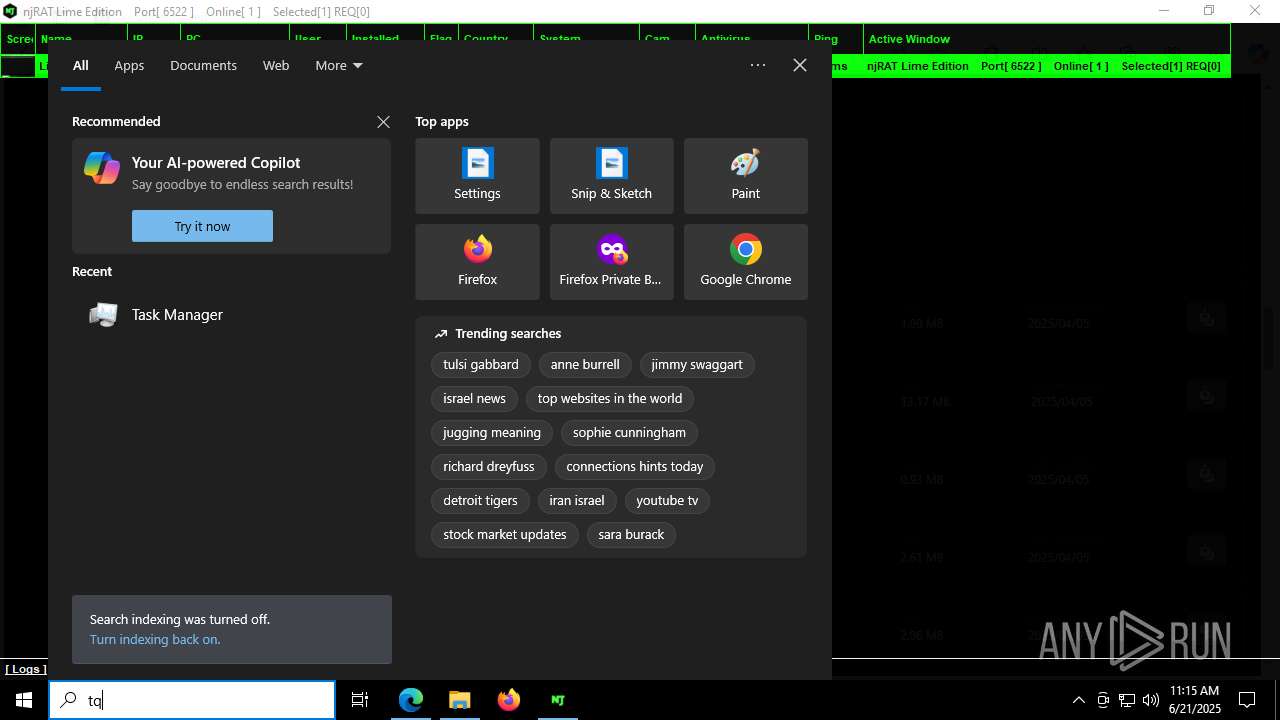
Changes the desktop background image
- New Client.exe (PID: 504)
INFO
Checks supported languages
- SearchApp.exe (PID: 5328)
- ShellExperienceHost.exe (PID: 2864)
- identity_helper.exe (PID: 7836)
- NjRat Lime Edition 0.8.0.exe (PID: 7528)
- ilasm.exe (PID: 7712)
- New Client.exe (PID: 7420)
- New Client.exe (PID: 504)
- tmp8459.tmp.exe (PID: 7728)
- email.exe (PID: 5564)
- browser.exe (PID: 1580)
- identity_helper.exe (PID: 236)
Reads the computer name
- ShellExperienceHost.exe (PID: 2864)
- identity_helper.exe (PID: 7836)
- NjRat Lime Edition 0.8.0.exe (PID: 7528)
- New Client.exe (PID: 7420)
- New Client.exe (PID: 504)
- browser.exe (PID: 1580)
- email.exe (PID: 5564)
- tmp8459.tmp.exe (PID: 7728)
- identity_helper.exe (PID: 236)
Application launched itself
- msedge.exe (PID: 2044)
- msedge.exe (PID: 7520)
Reads Environment values
- identity_helper.exe (PID: 7836)
- identity_helper.exe (PID: 236)
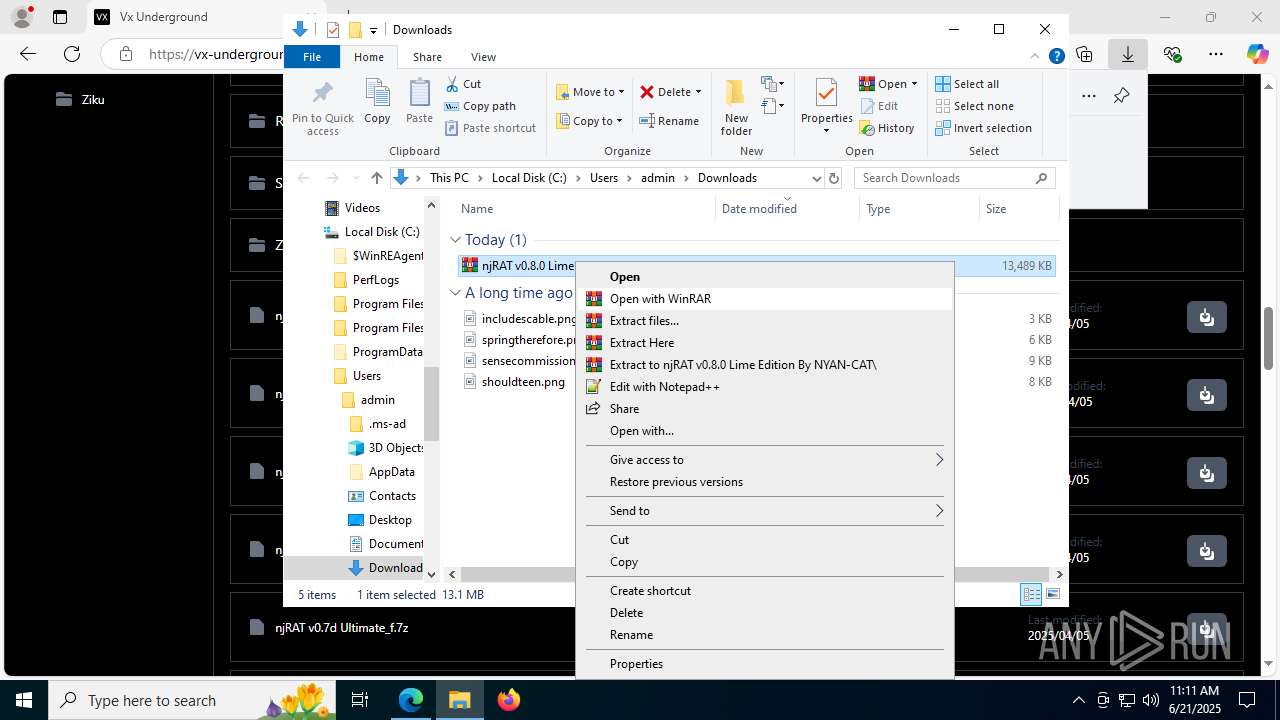
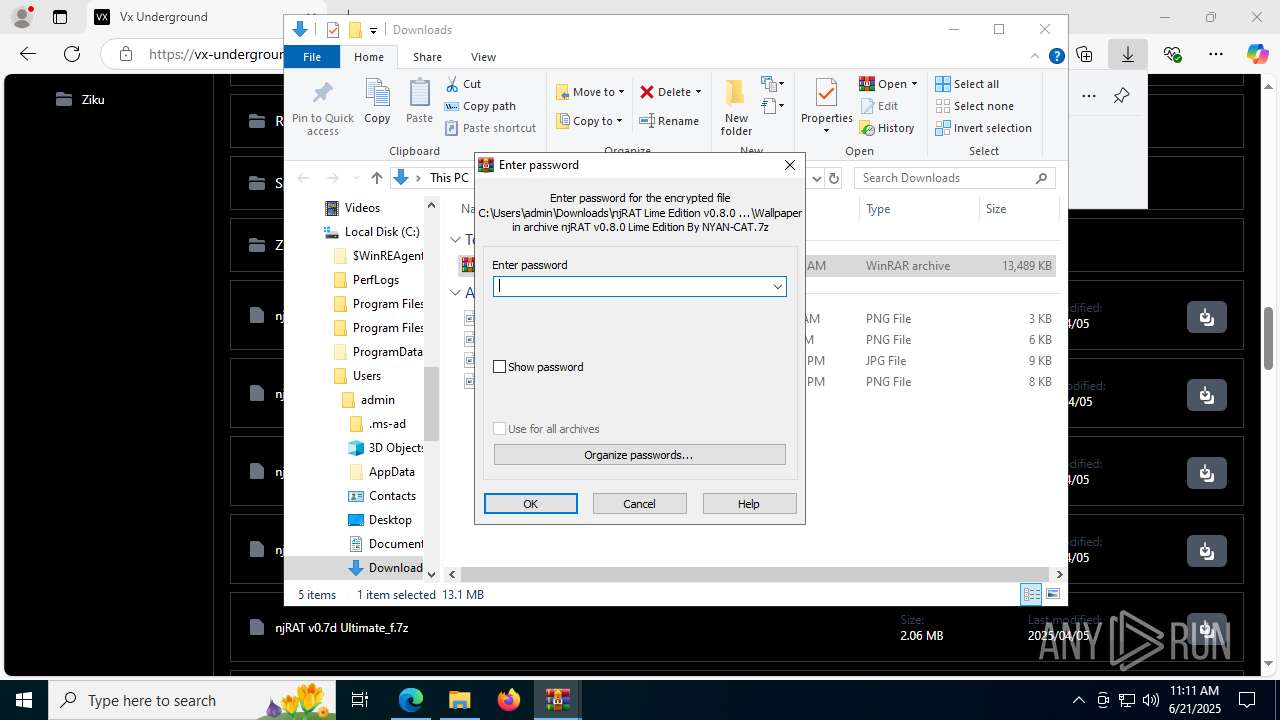
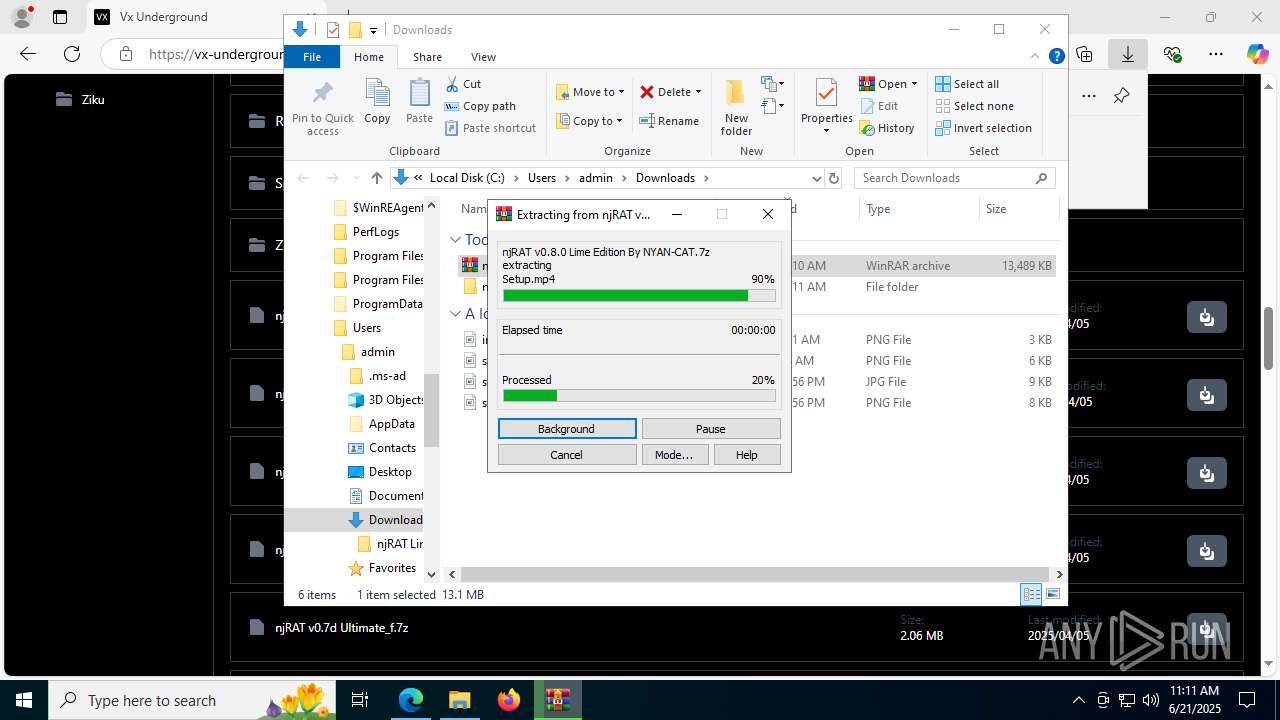
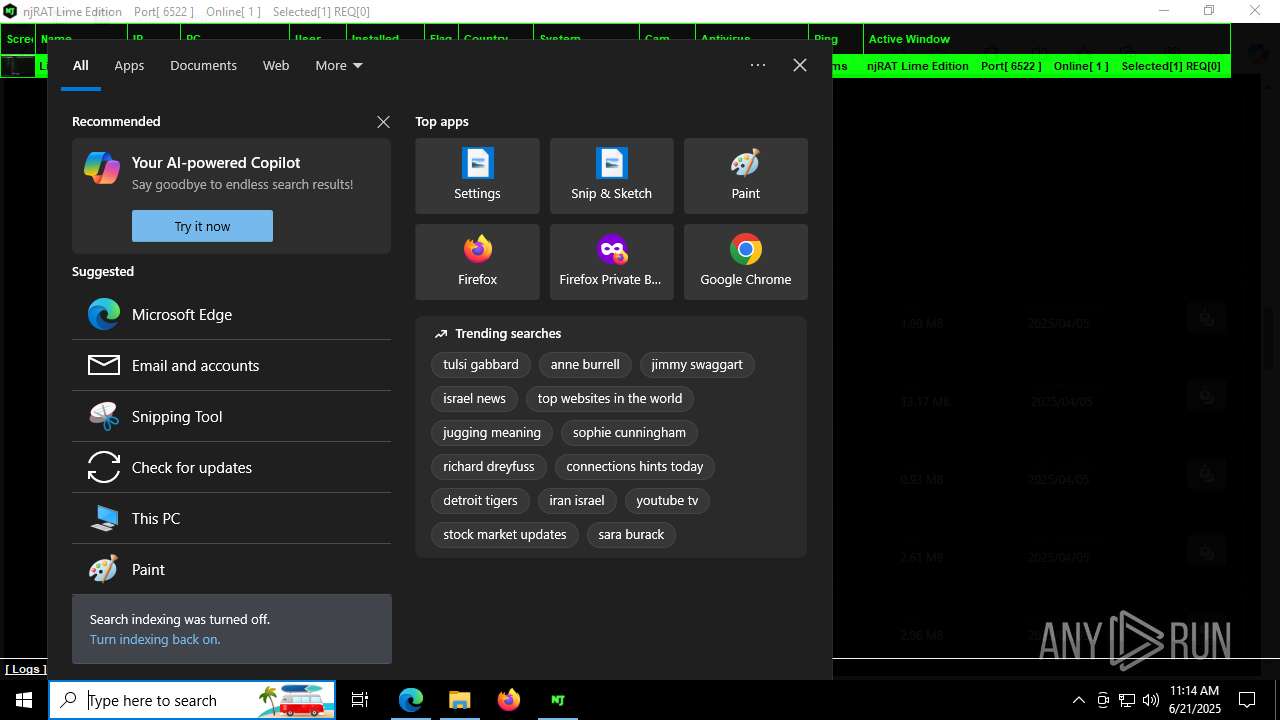
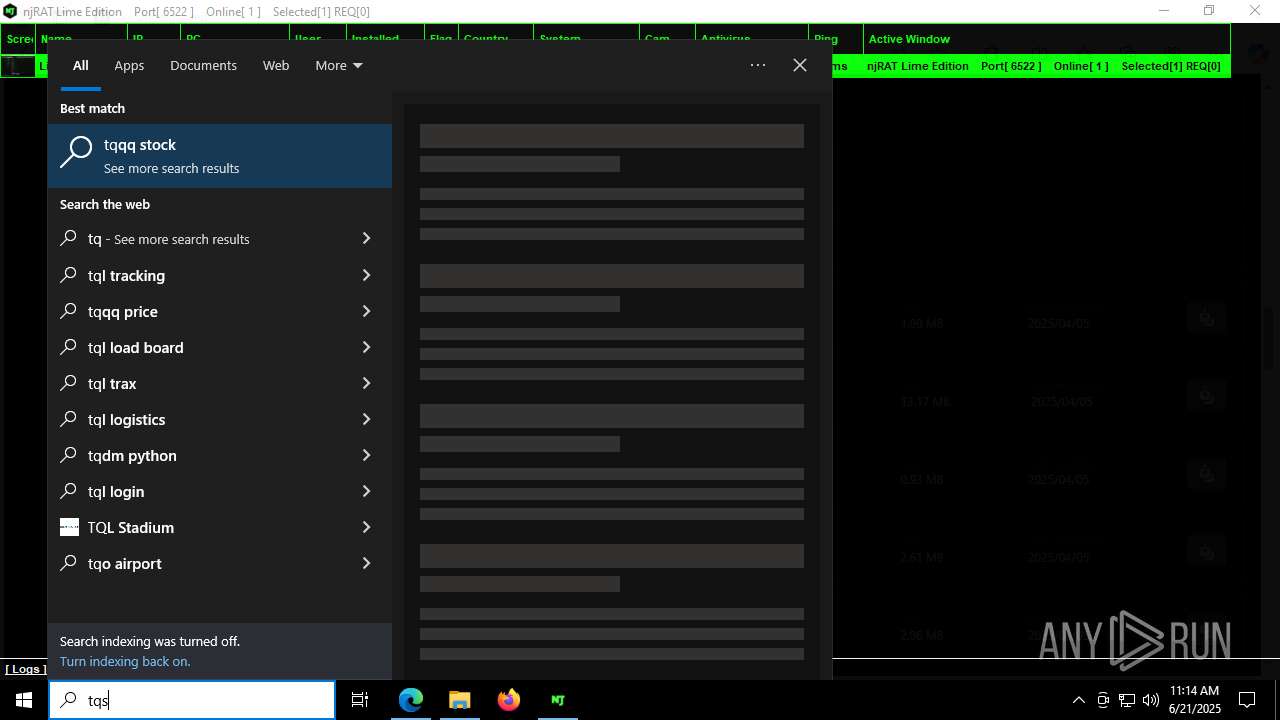
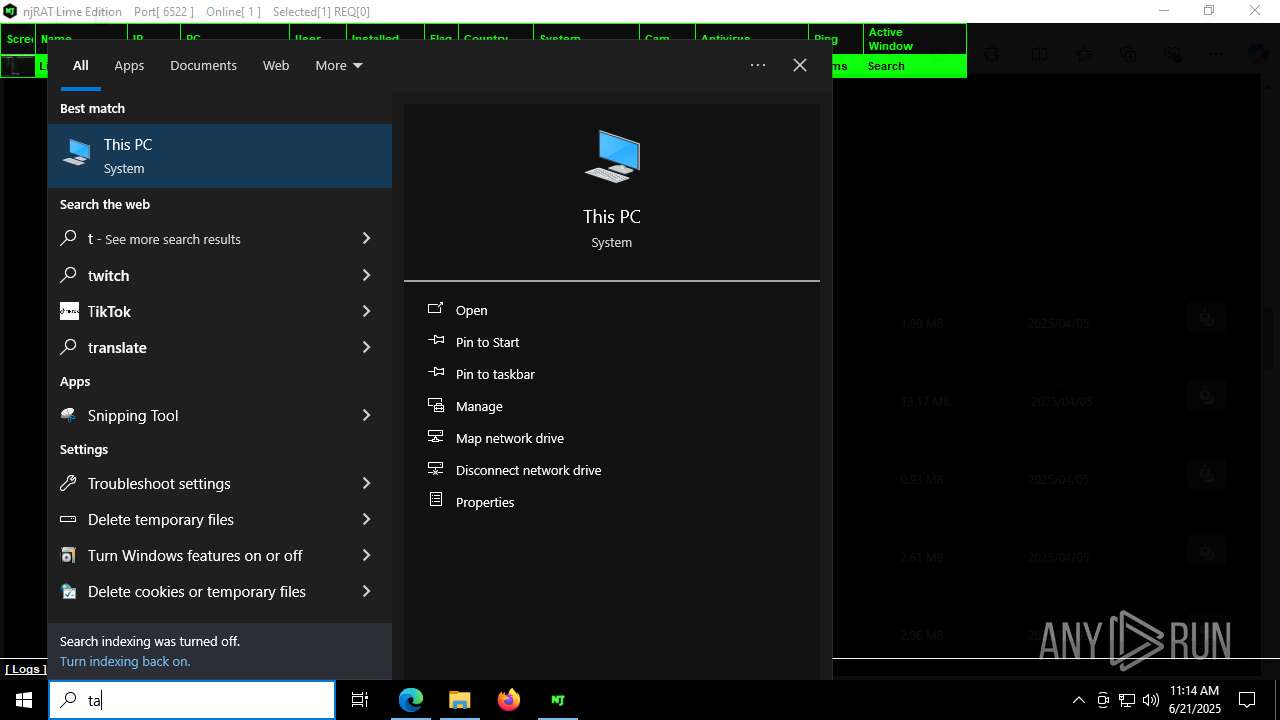
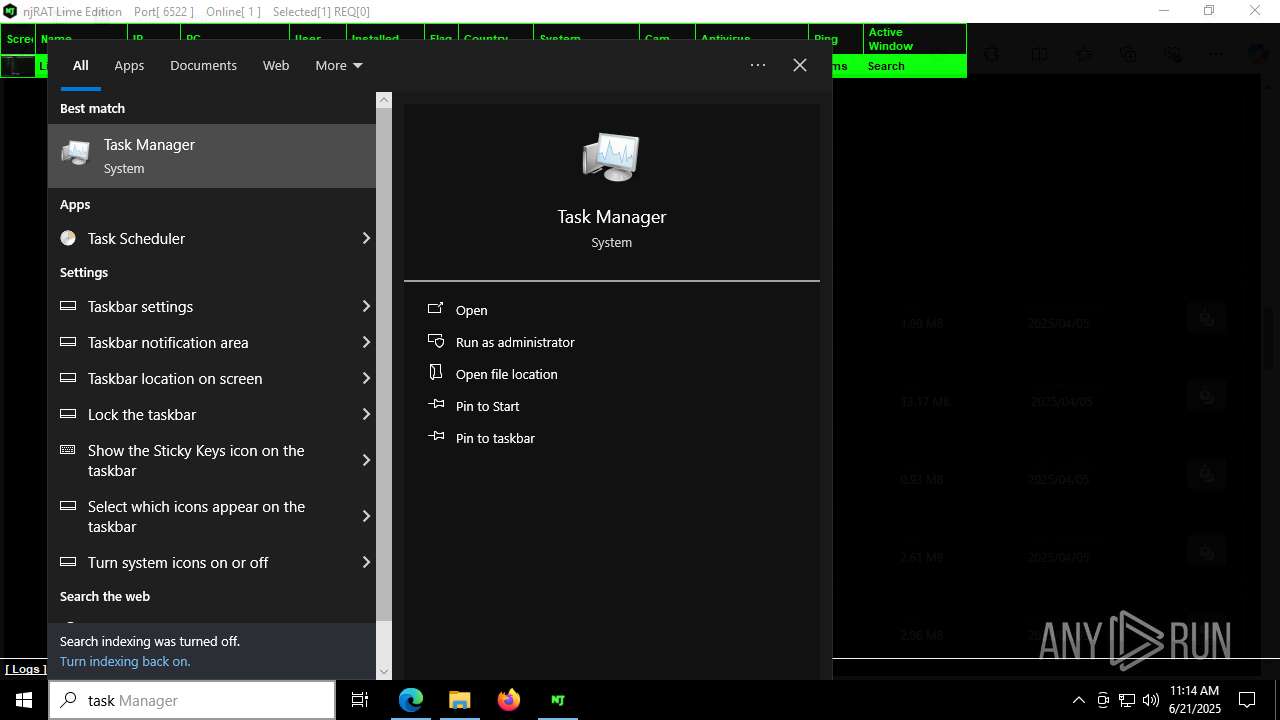
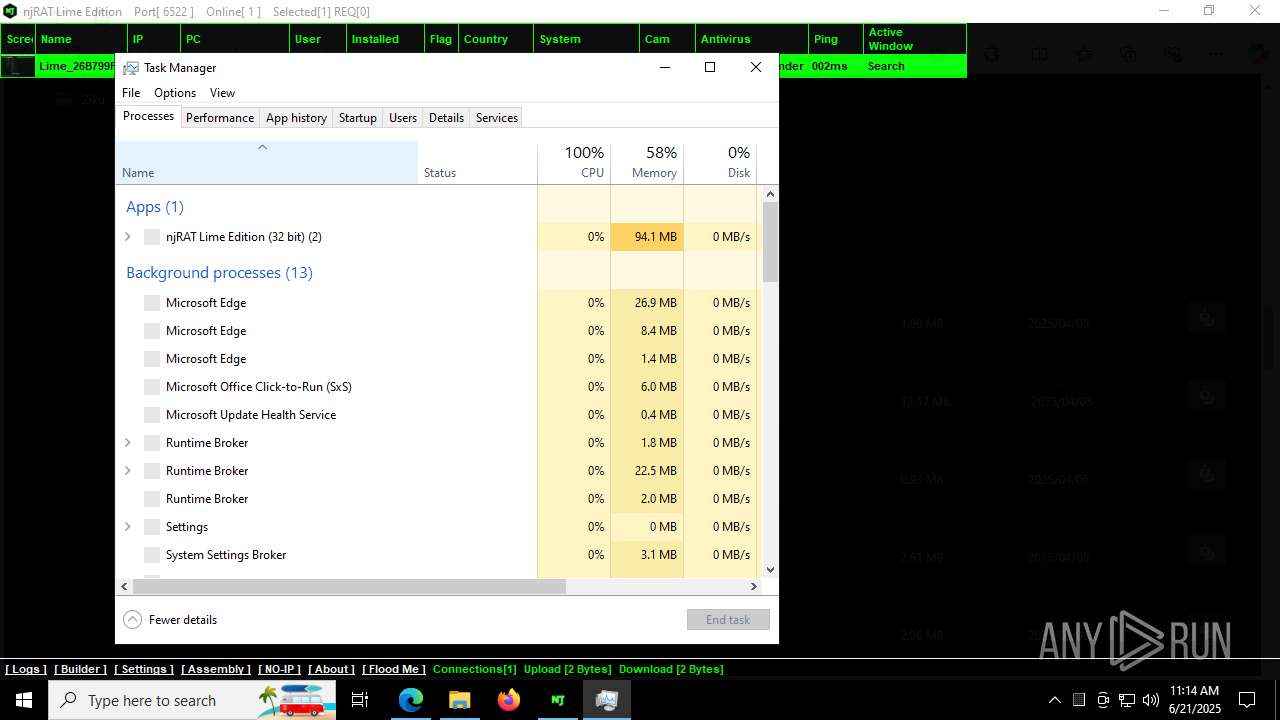
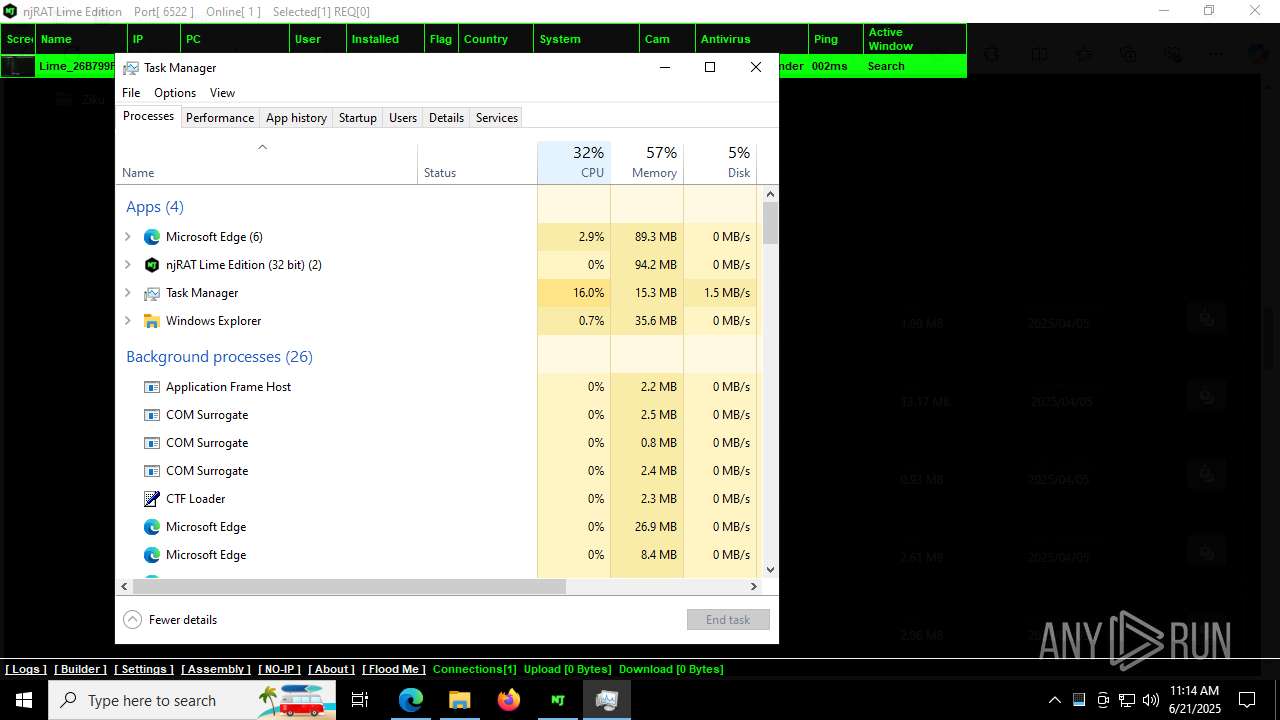
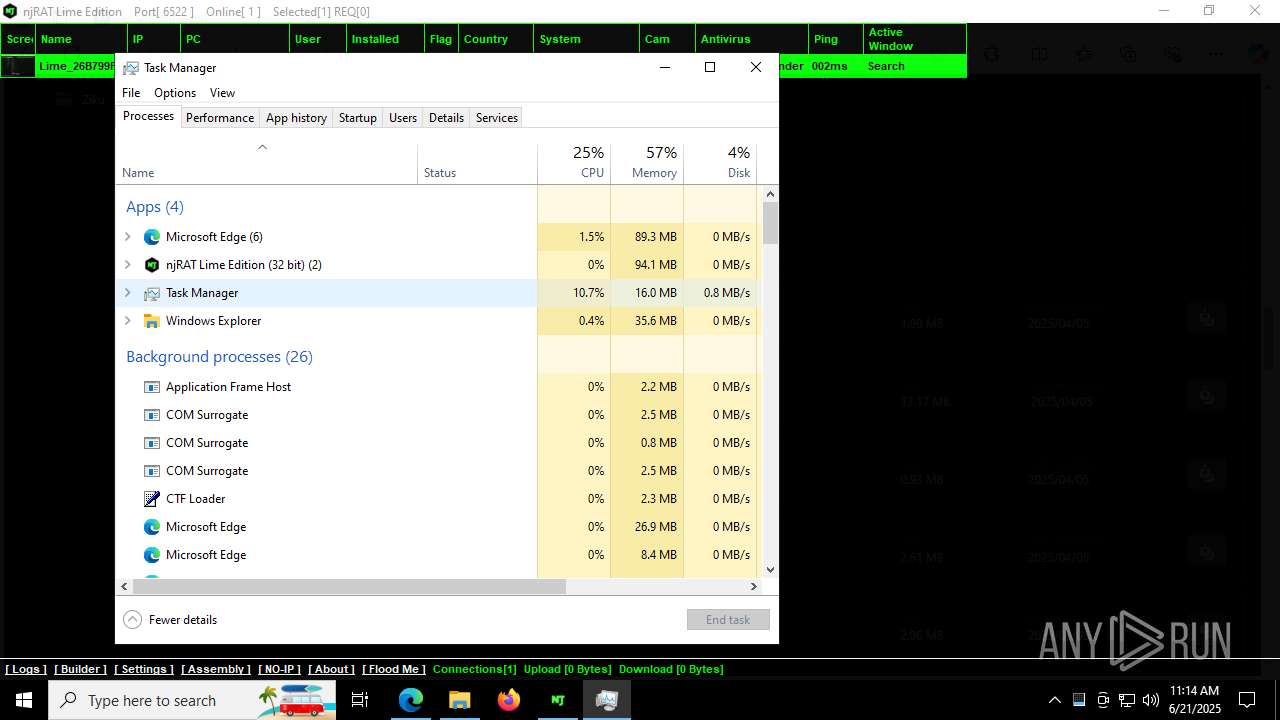
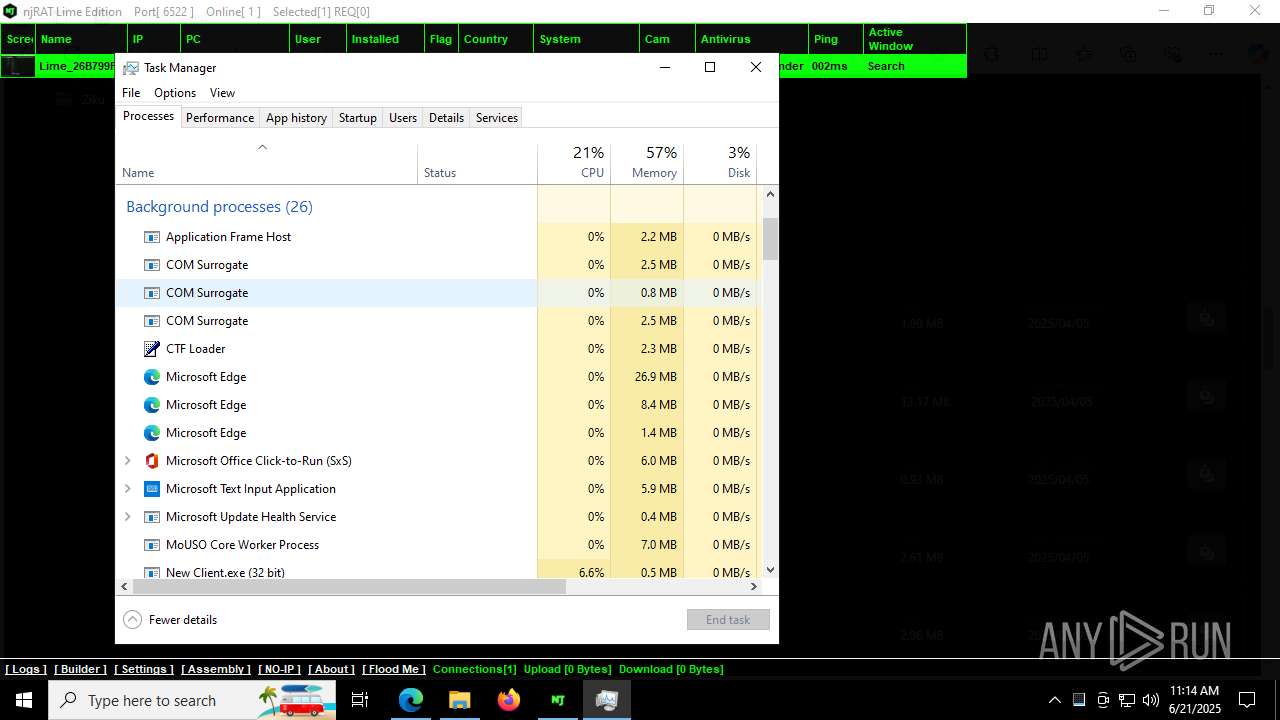
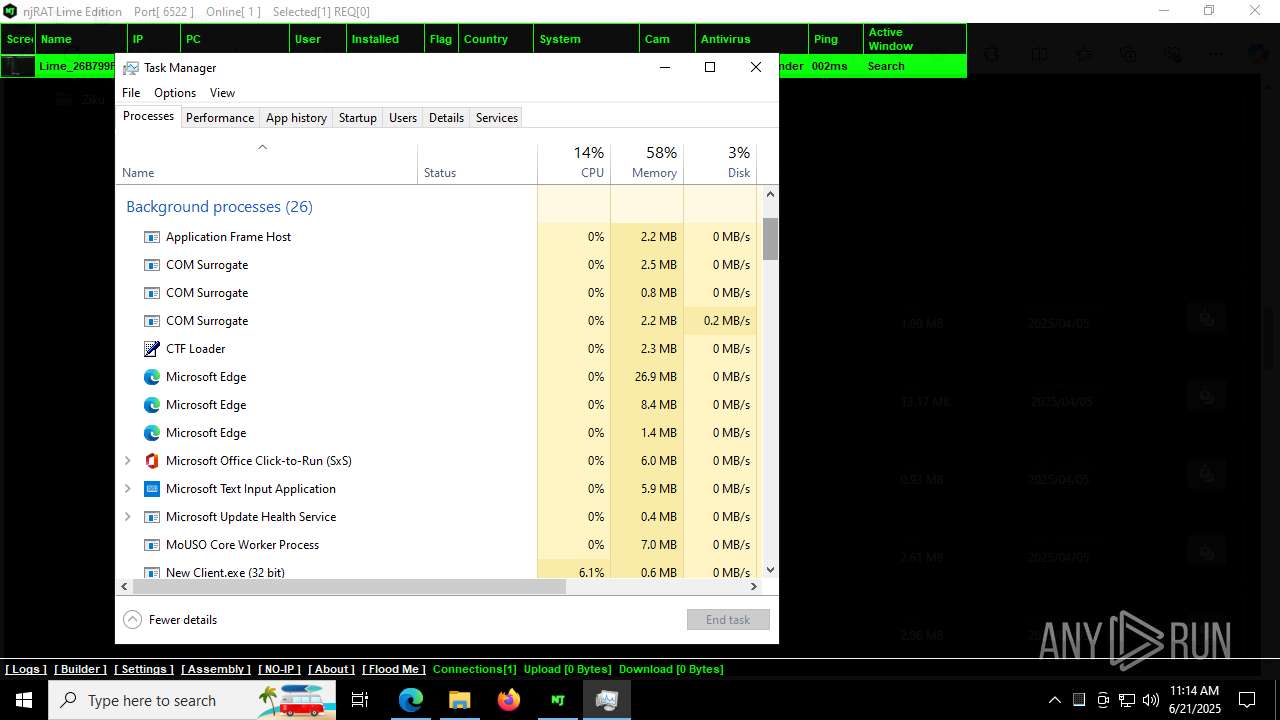
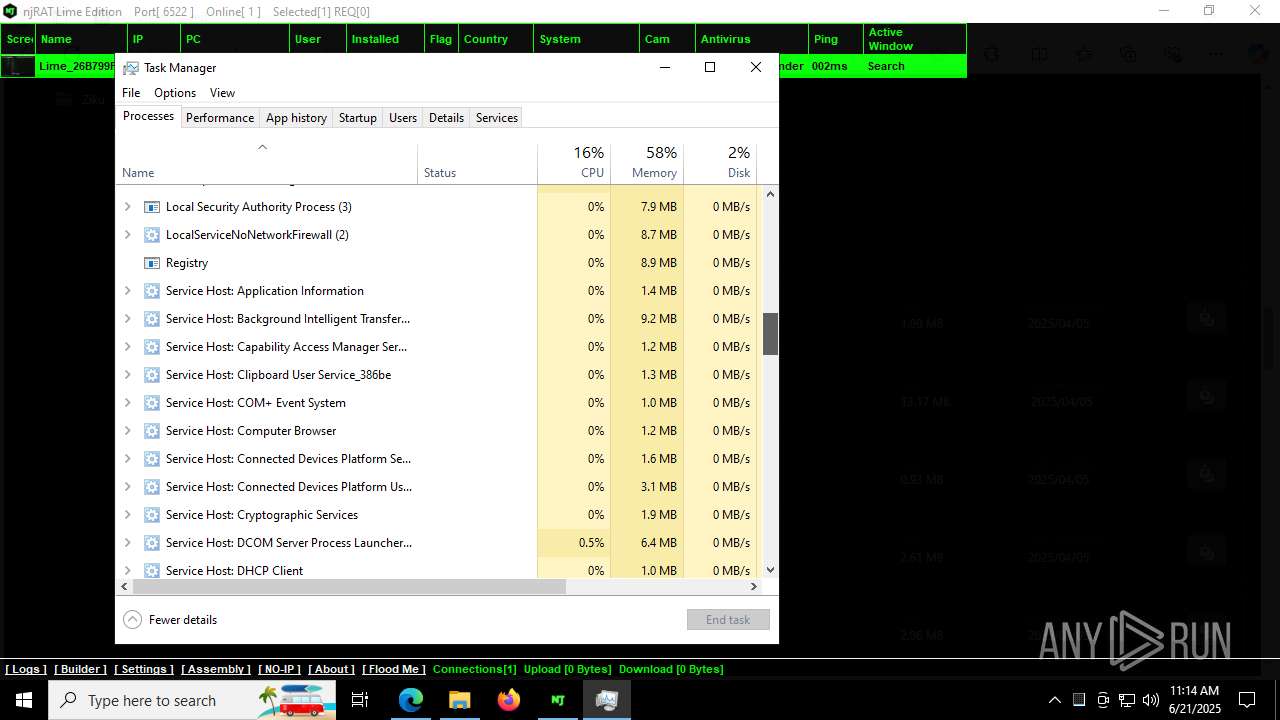
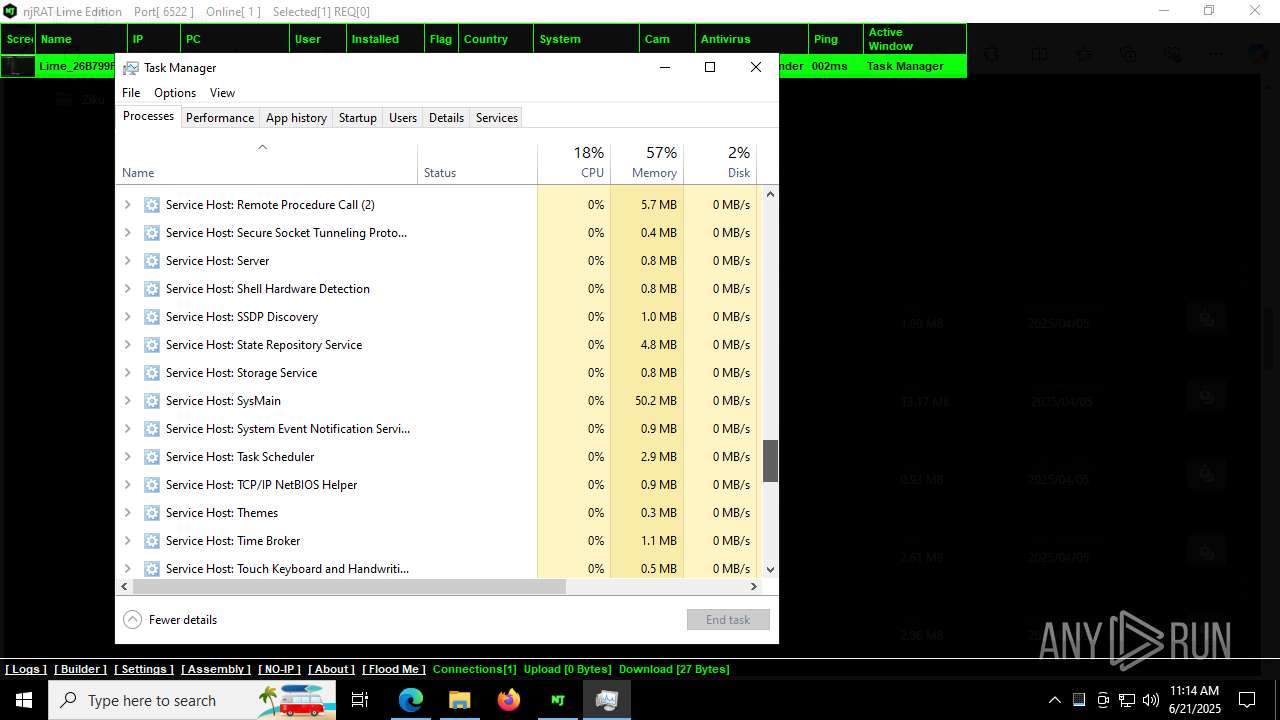
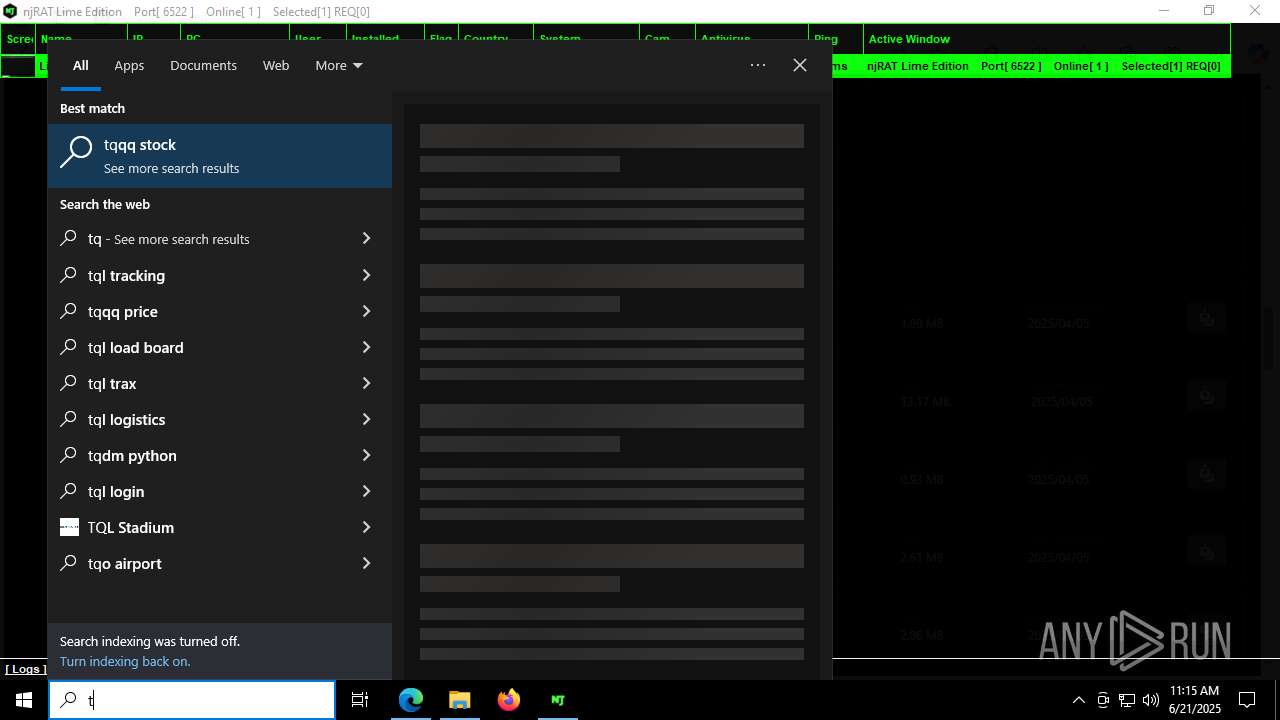
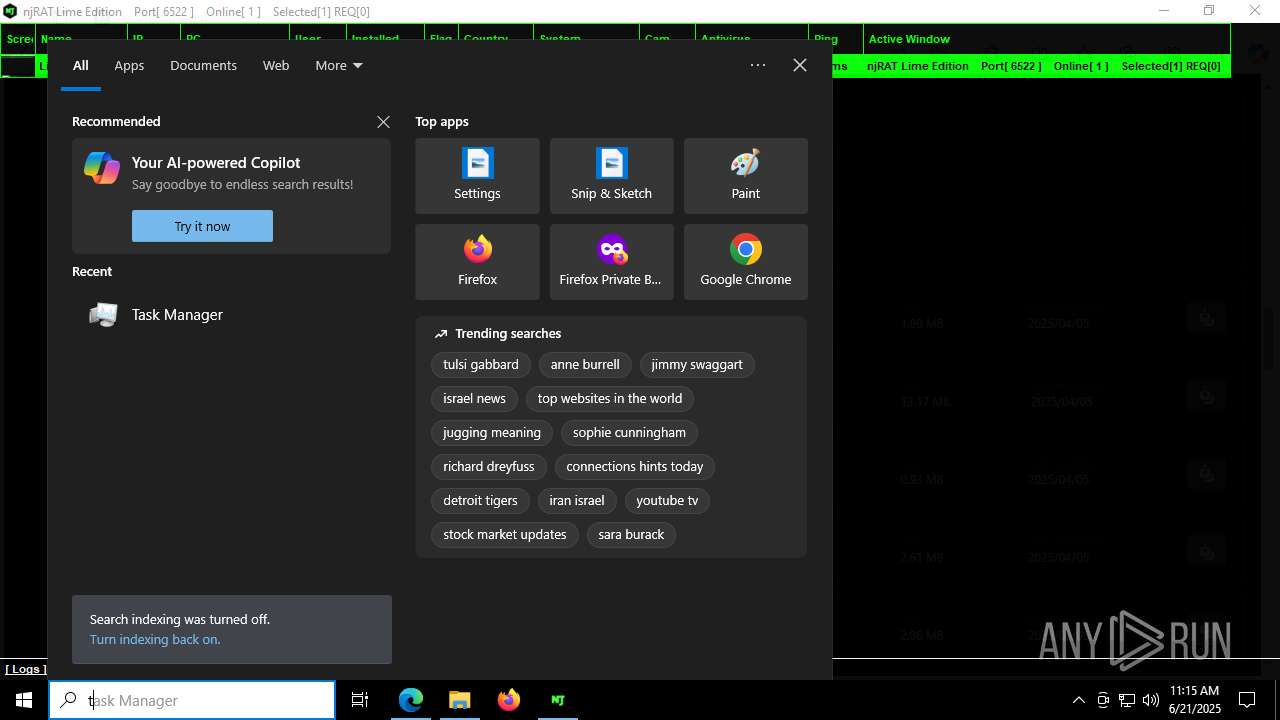
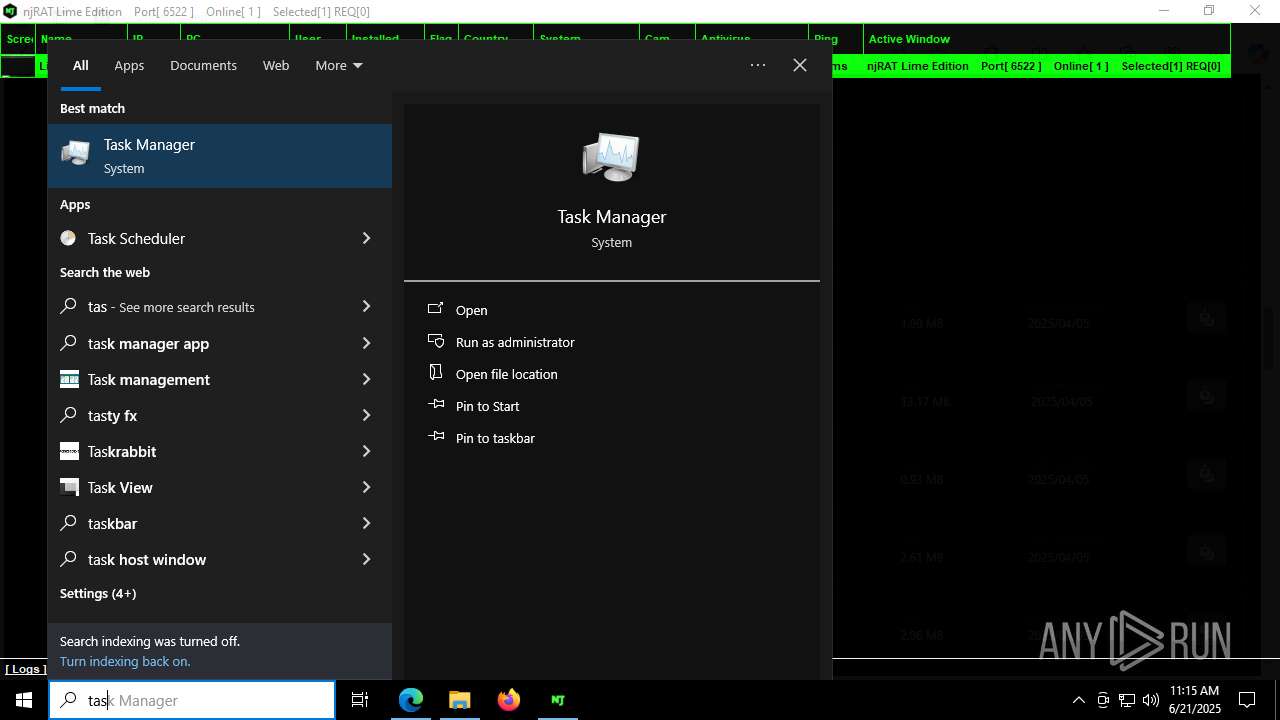
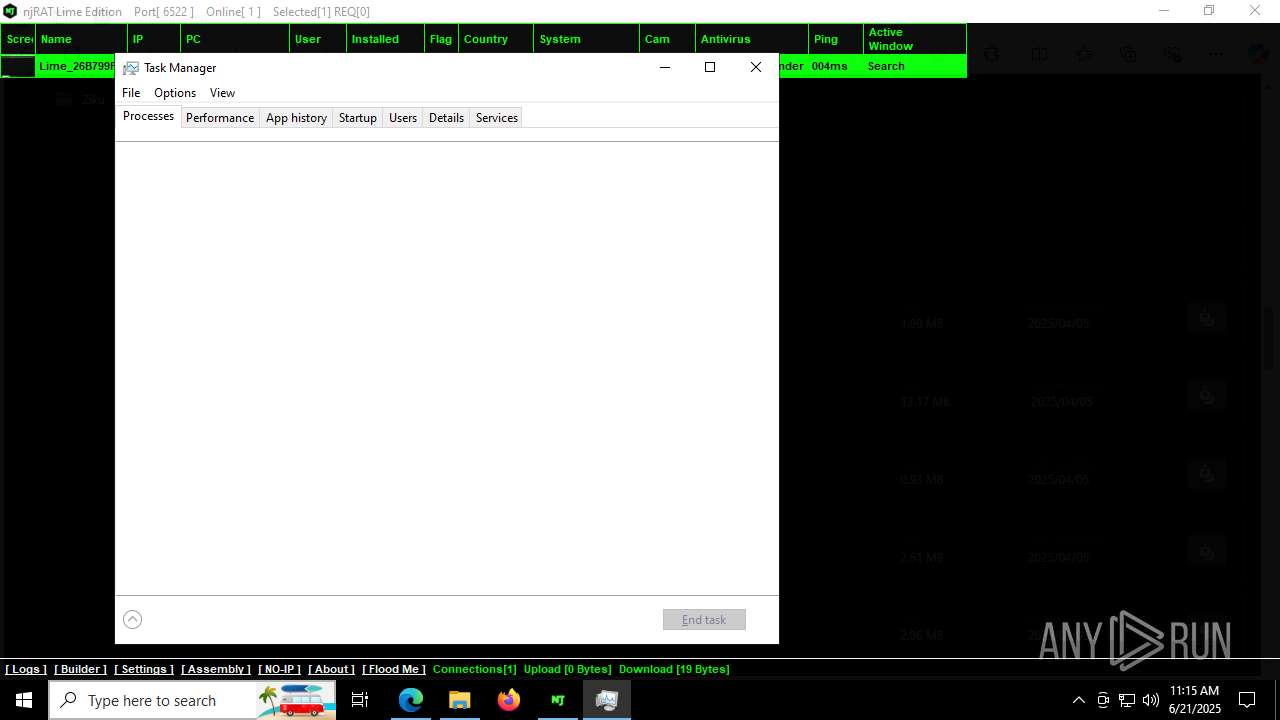
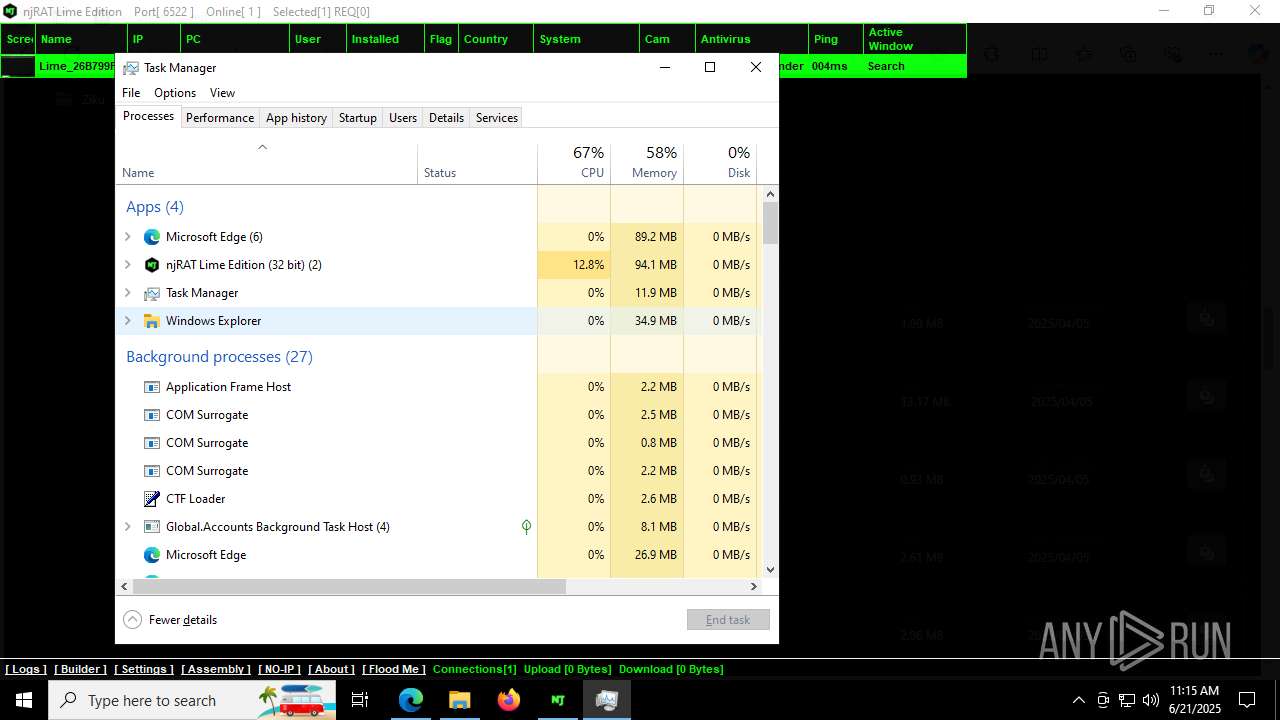
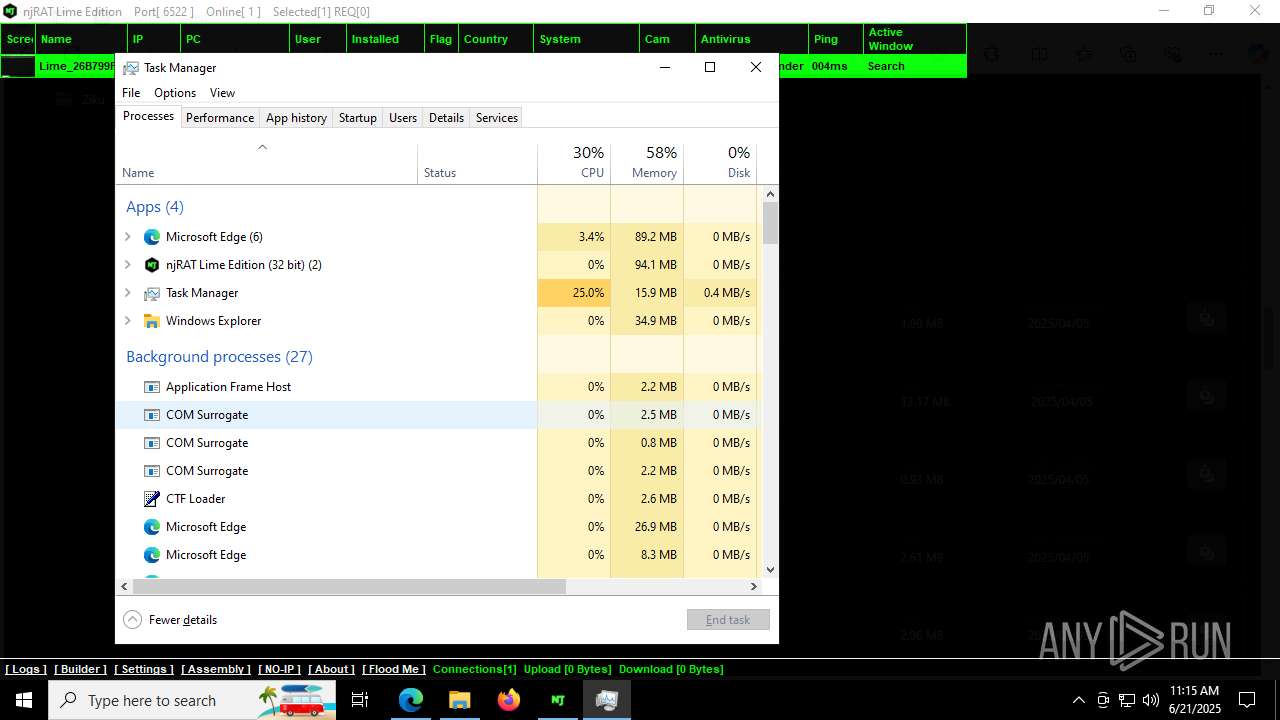
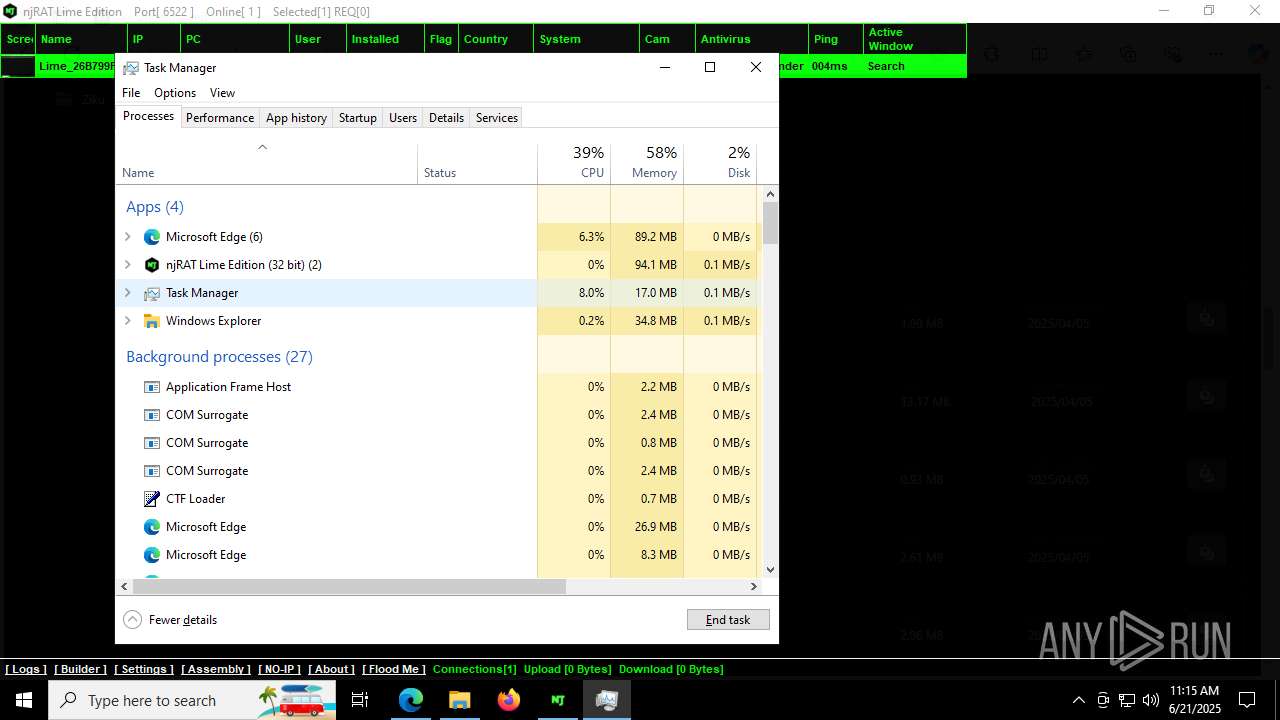
Manual execution by a user
- WinRAR.exe (PID: 6960)
- NjRat Lime Edition 0.8.0.exe (PID: 7528)
- New Client.exe (PID: 7420)
- New Client.exe (PID: 504)
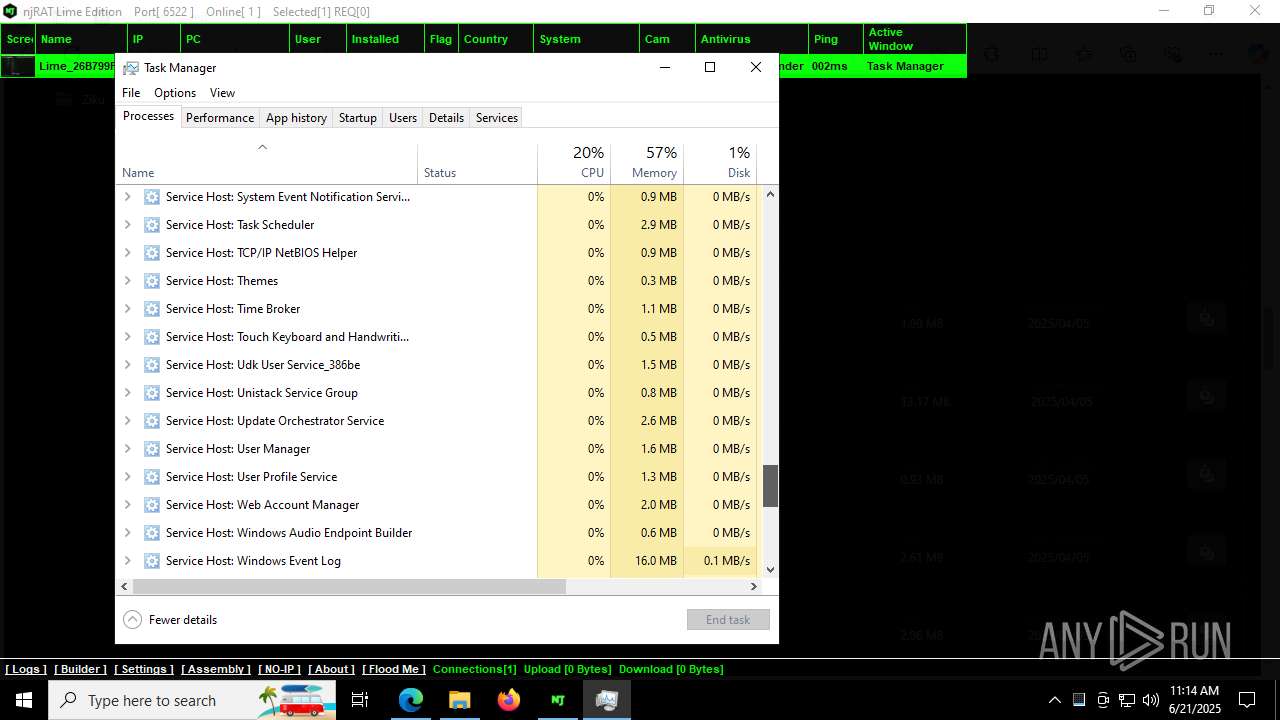
- Taskmgr.exe (PID: 5468)
- Taskmgr.exe (PID: 1068)
- Taskmgr.exe (PID: 7704)
- Taskmgr.exe (PID: 5564)
Creates files or folders in the user directory
- NjRat Lime Edition 0.8.0.exe (PID: 7528)
- mmc.exe (PID: 1808)
- New Client.exe (PID: 504)
Reads the machine GUID from the registry
- NjRat Lime Edition 0.8.0.exe (PID: 7528)
- New Client.exe (PID: 7420)
- SearchApp.exe (PID: 5328)
- New Client.exe (PID: 504)
- browser.exe (PID: 1580)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6960)
Confuser has been detected (YARA)
- NjRat Lime Edition 0.8.0.exe (PID: 7528)
.NET Reactor protector has been detected
- NjRat Lime Edition 0.8.0.exe (PID: 7528)
Compiled with Borland Delphi (YARA)
- NjRat Lime Edition 0.8.0.exe (PID: 7528)
Create files in a temporary directory
- NjRat Lime Edition 0.8.0.exe (PID: 7528)
- New Client.exe (PID: 504)
- browser.exe (PID: 1580)
- email.exe (PID: 5564)
- tmp8459.tmp.exe (PID: 7728)
Process checks computer location settings
- NjRat Lime Edition 0.8.0.exe (PID: 7528)
- SearchApp.exe (PID: 5328)
- New Client.exe (PID: 504)
- New Client.exe (PID: 7420)
Reads the software policy settings
- slui.exe (PID: 3632)
- SearchApp.exe (PID: 5328)
- New Client.exe (PID: 504)
Reads security settings of Internet Explorer
- mmc.exe (PID: 1808)
- mmc.exe (PID: 2128)
- Taskmgr.exe (PID: 5564)
- Taskmgr.exe (PID: 1068)
Creates files in the program directory
- mmc.exe (PID: 1808)
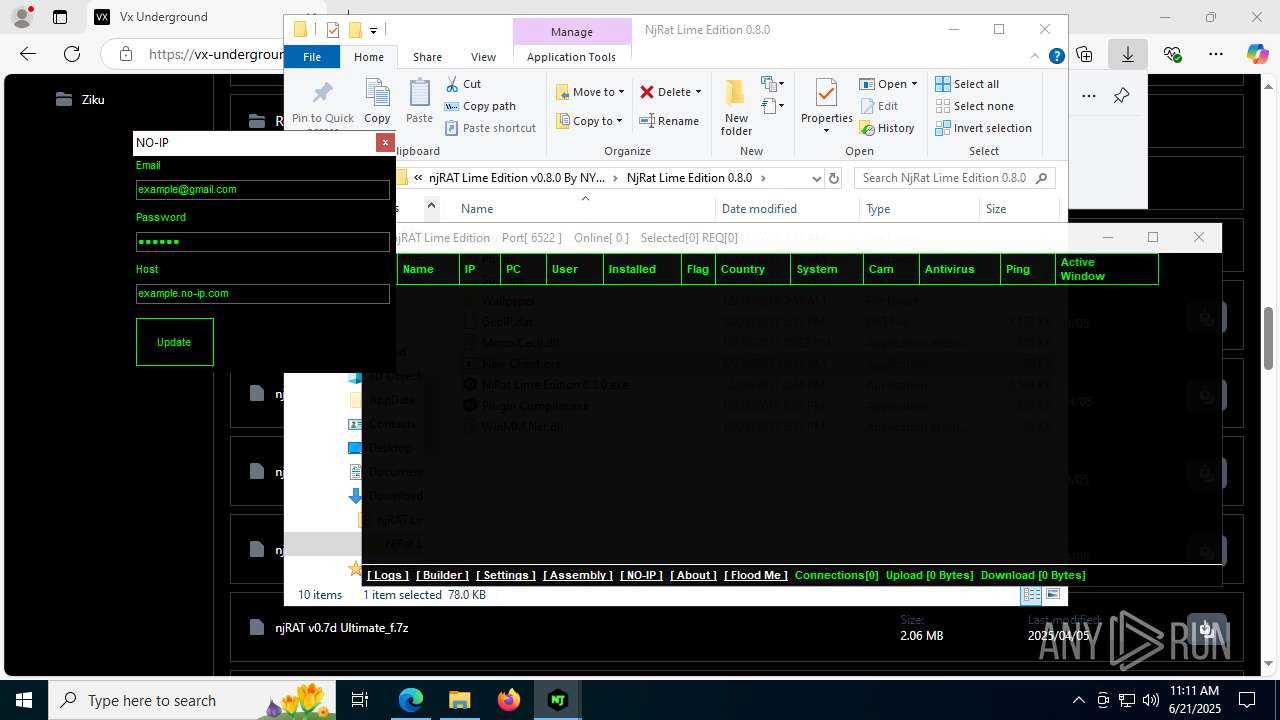
Checks proxy server information
- slui.exe (PID: 3632)
- New Client.exe (PID: 504)
The sample compiled with english language support
- tmp8459.tmp.exe (PID: 7728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
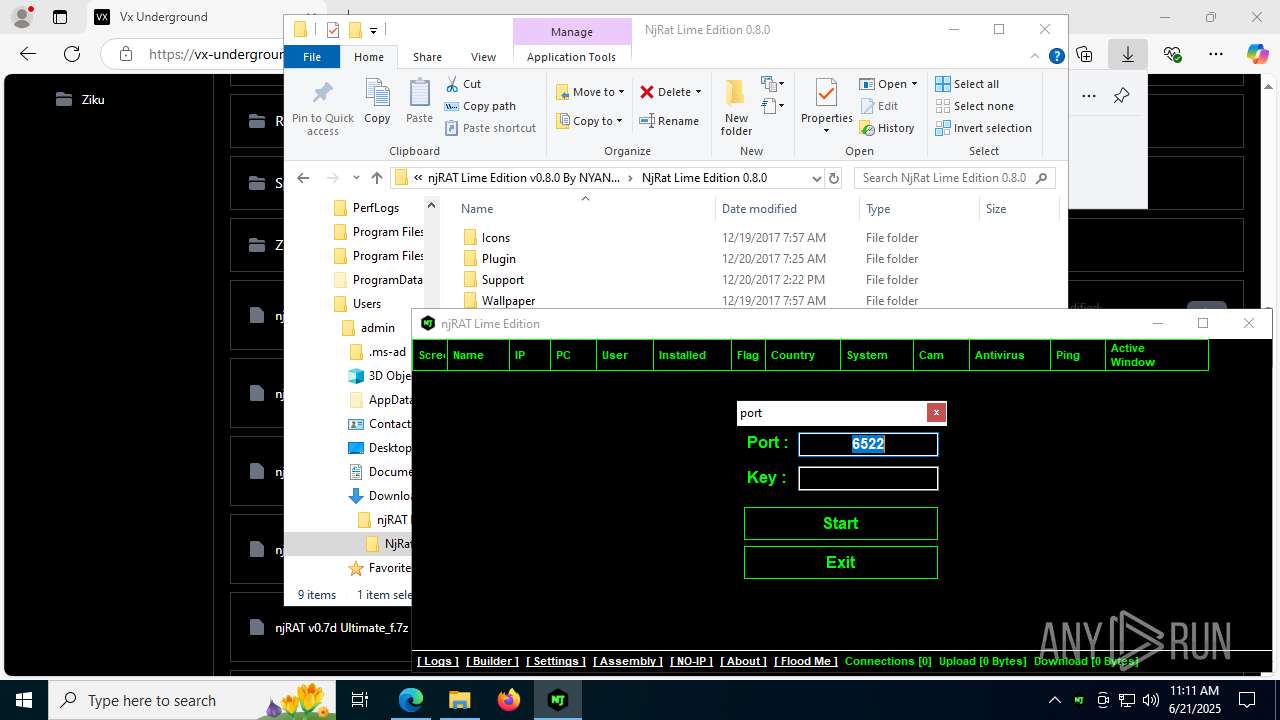
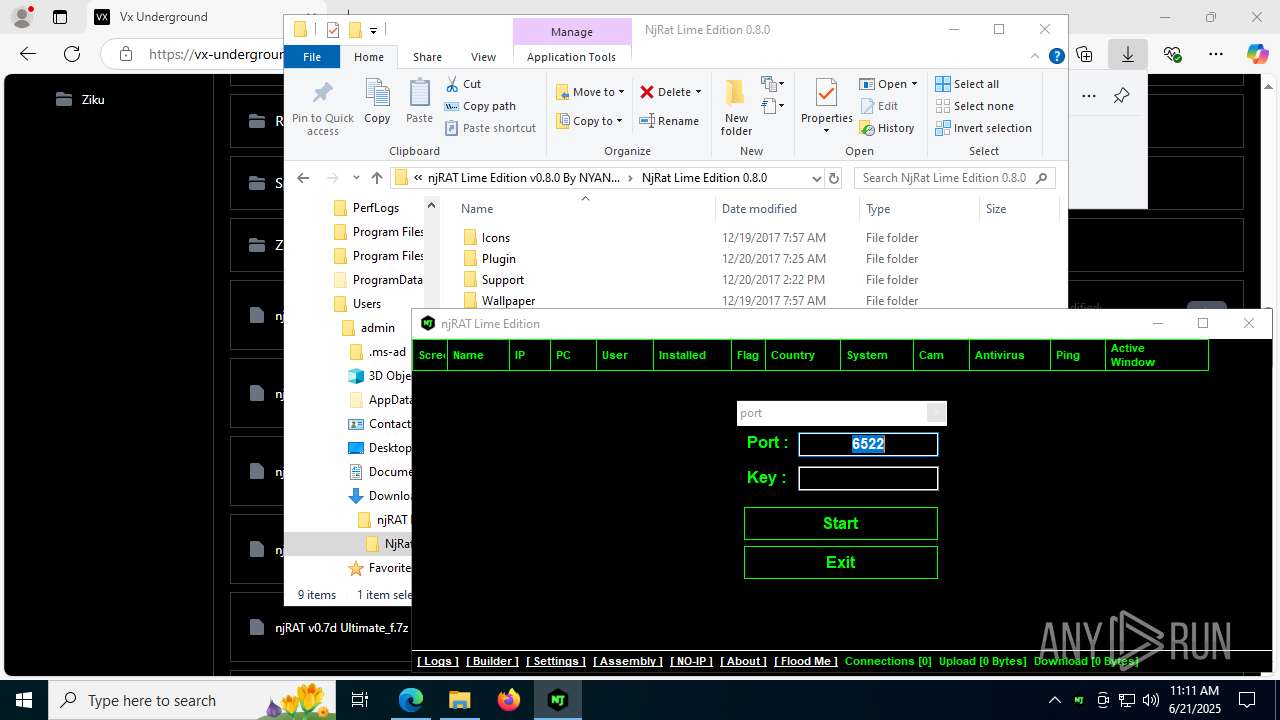
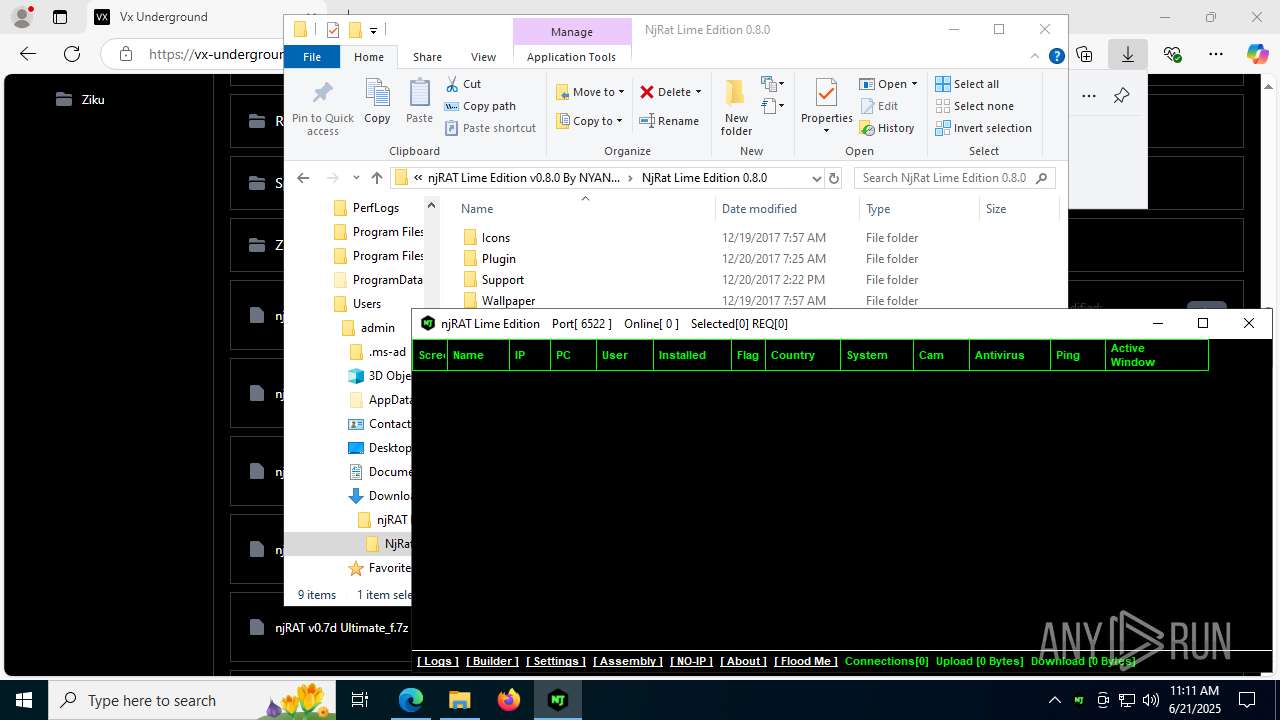
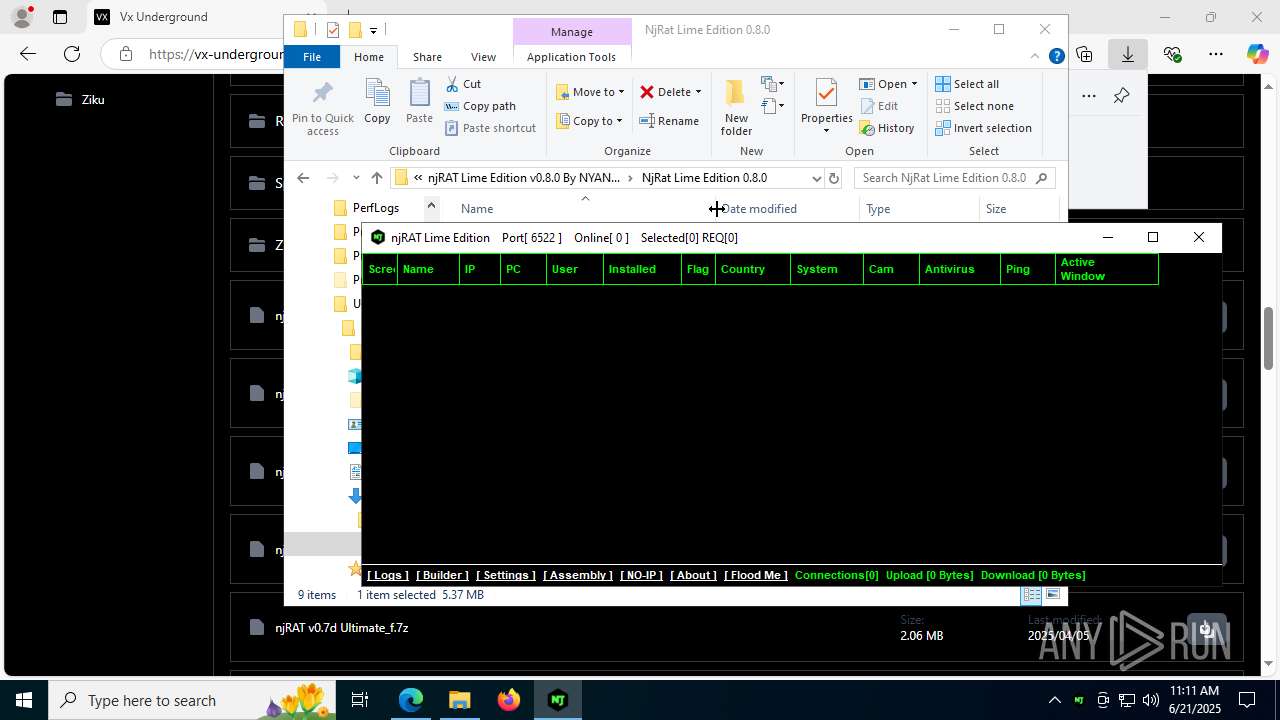
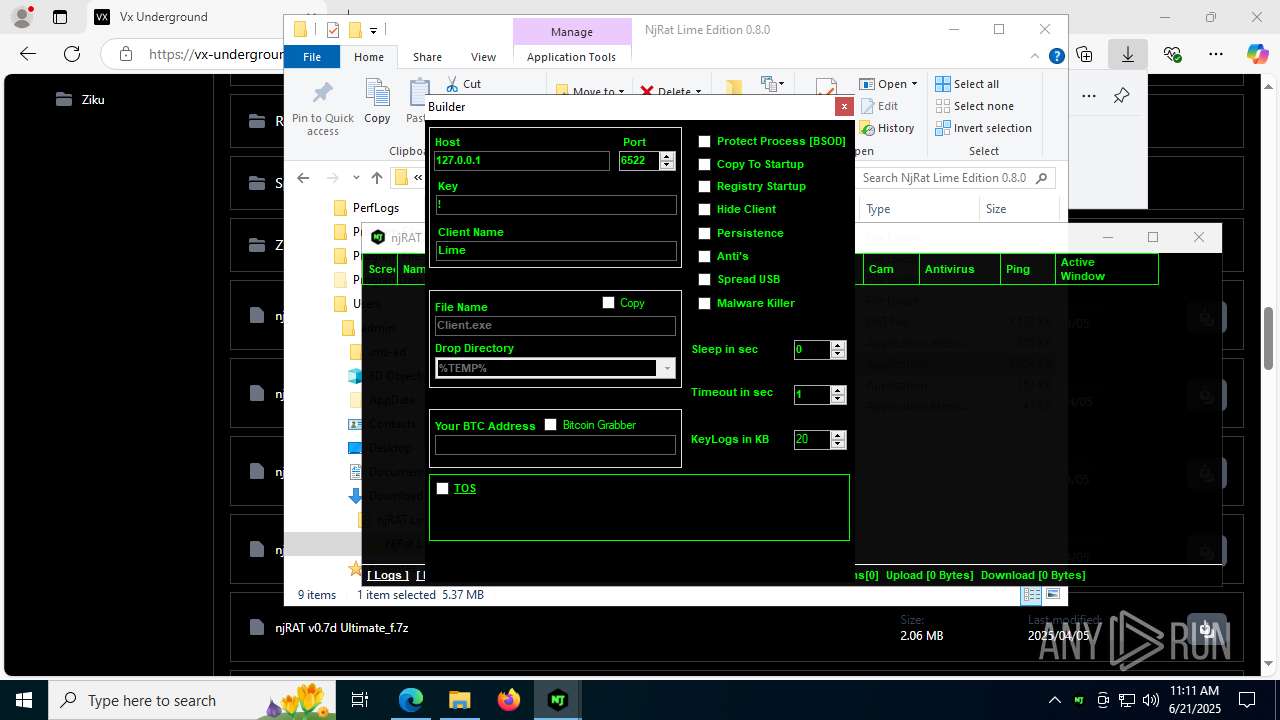
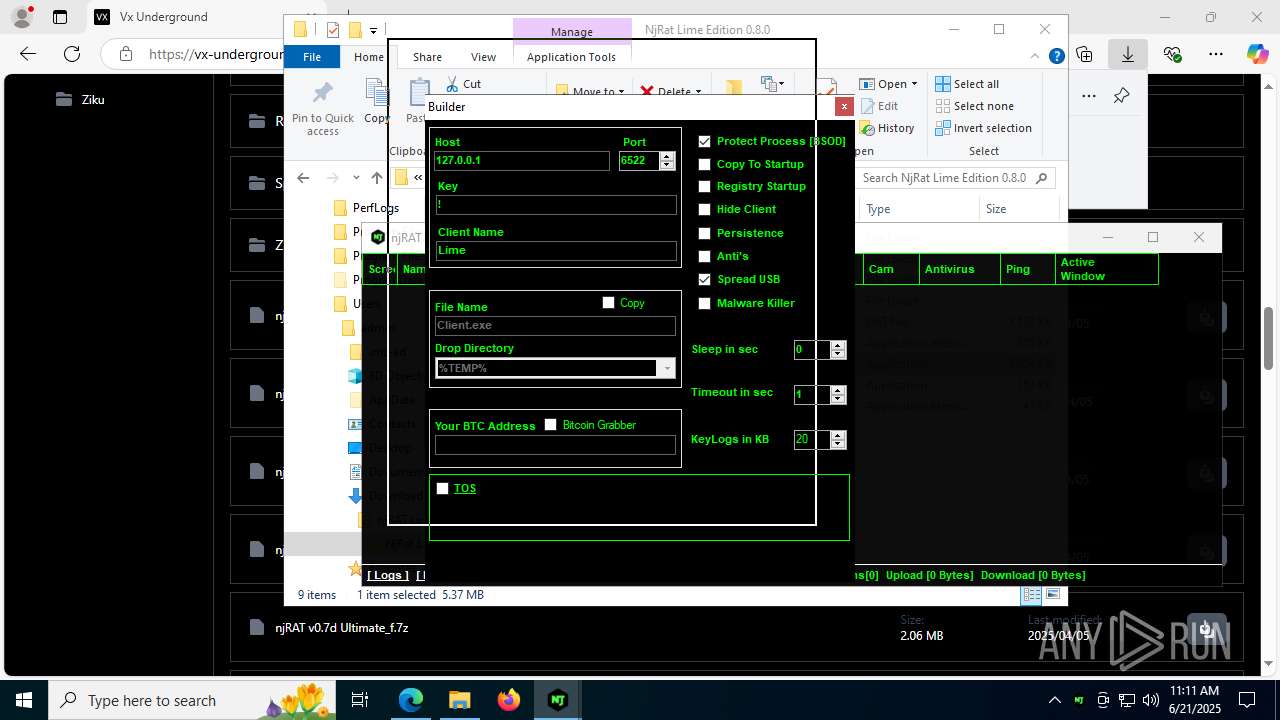
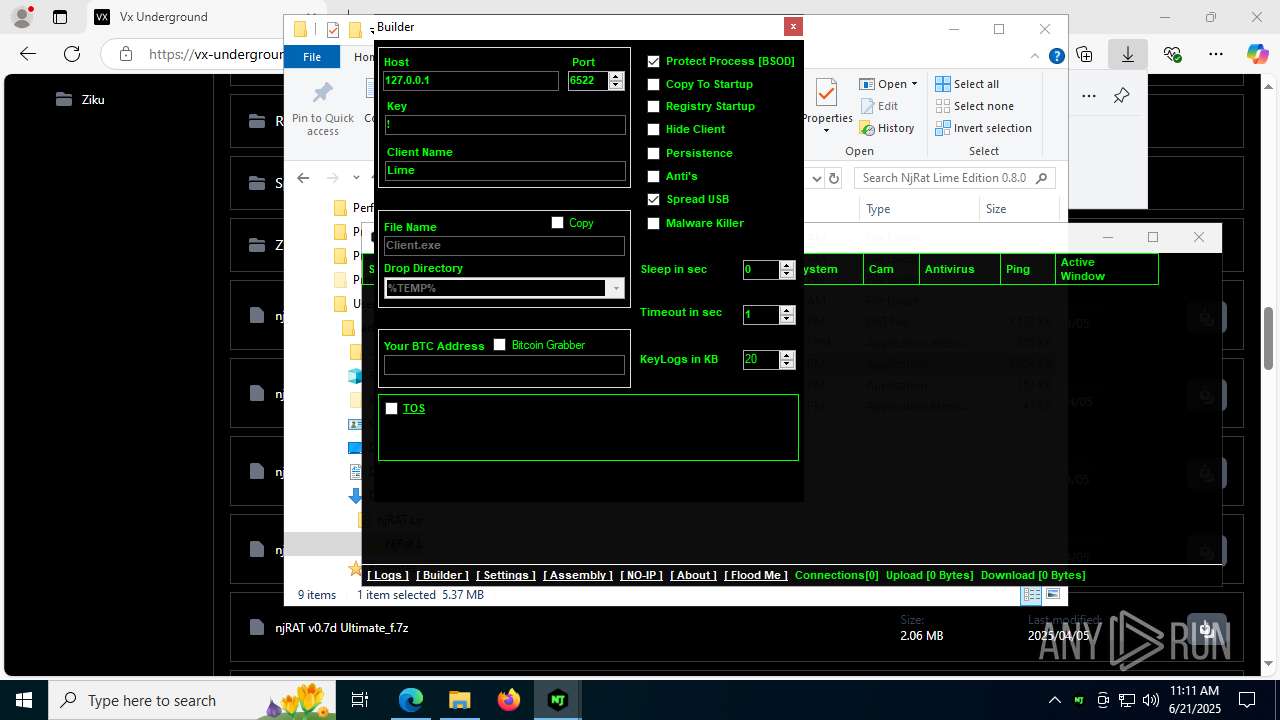
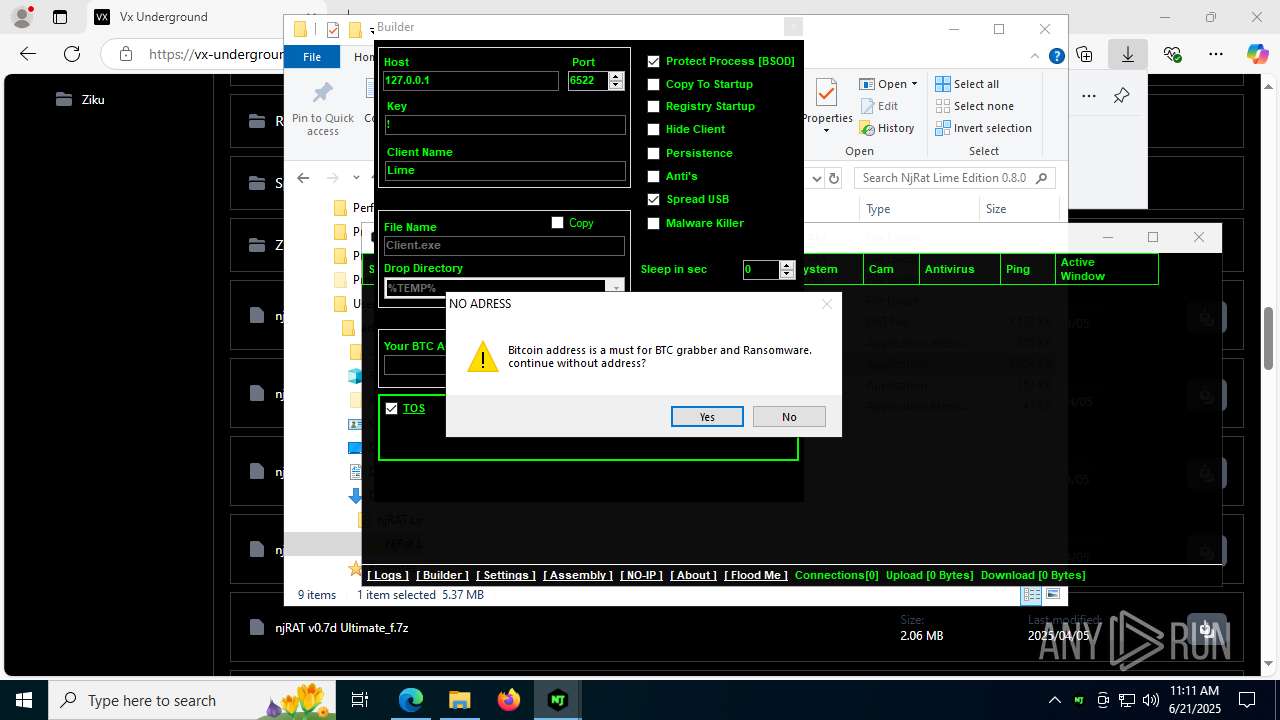
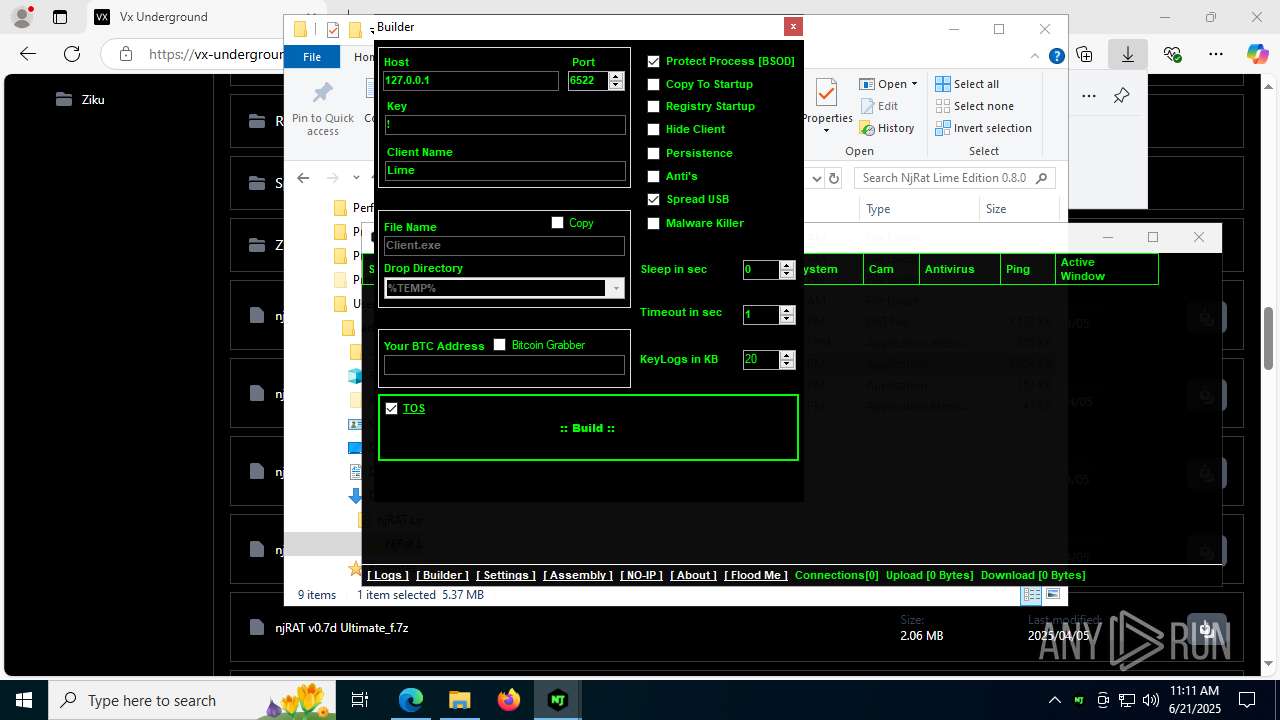
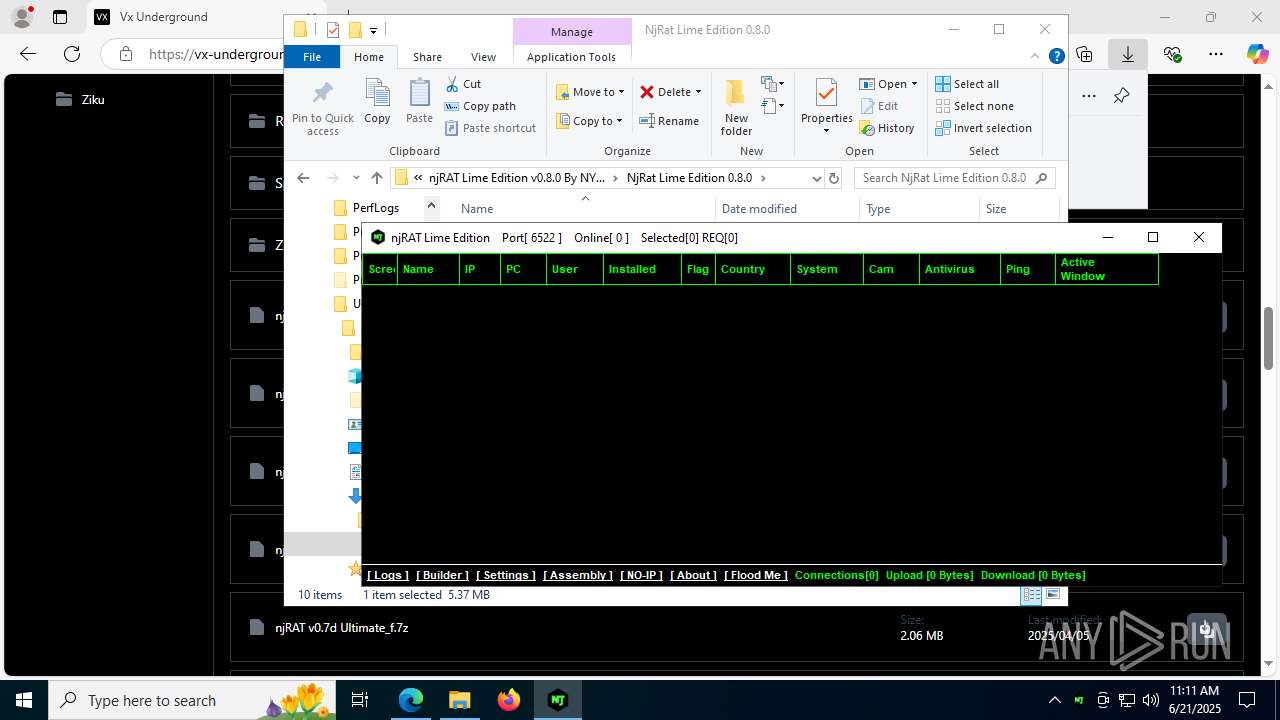
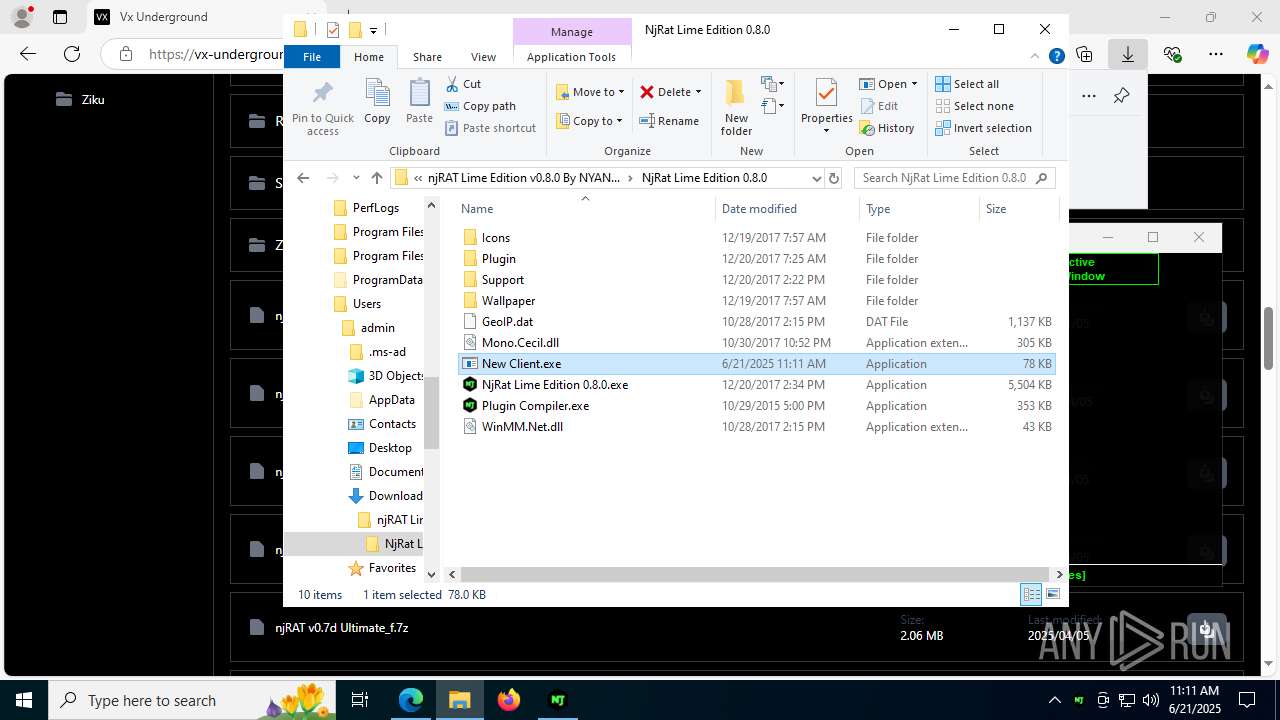
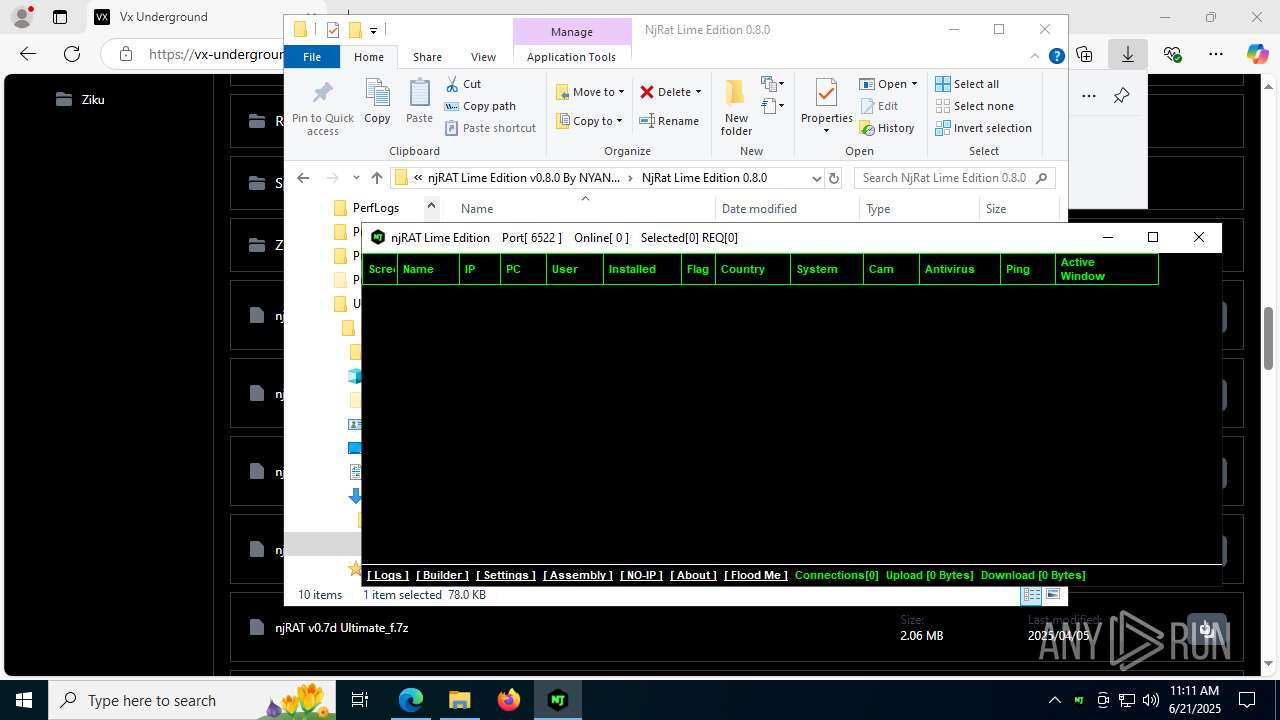
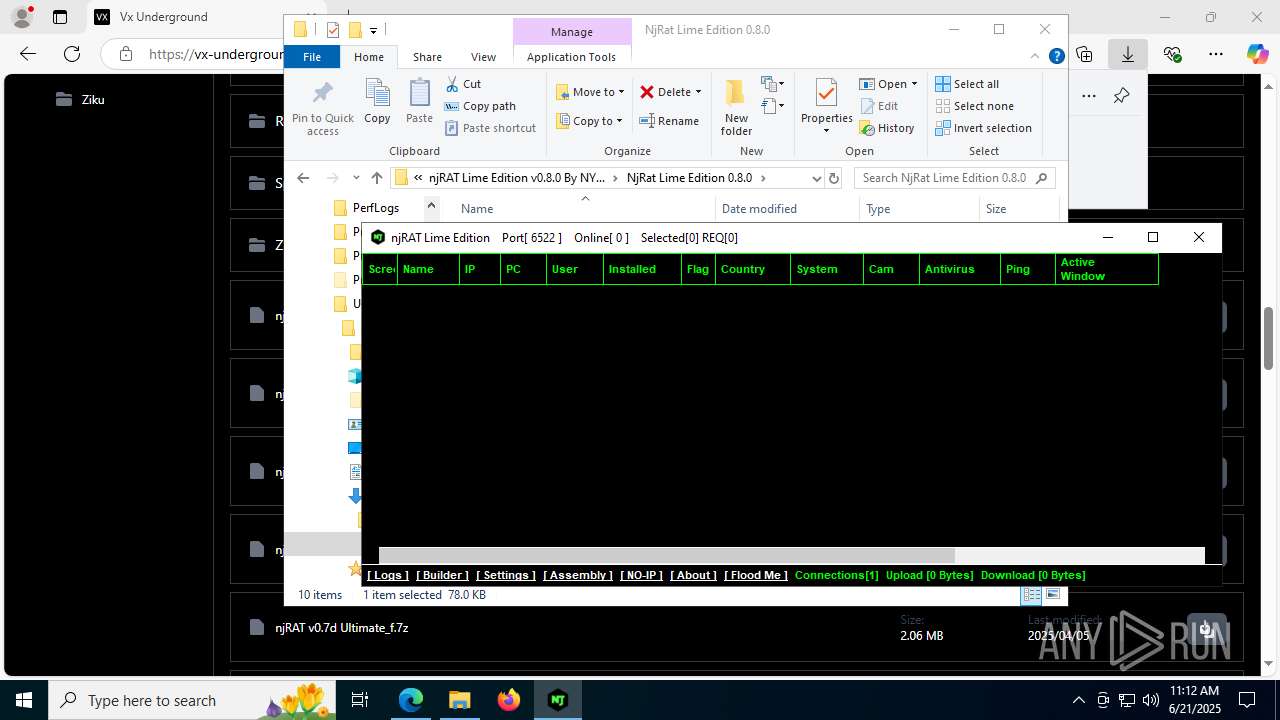
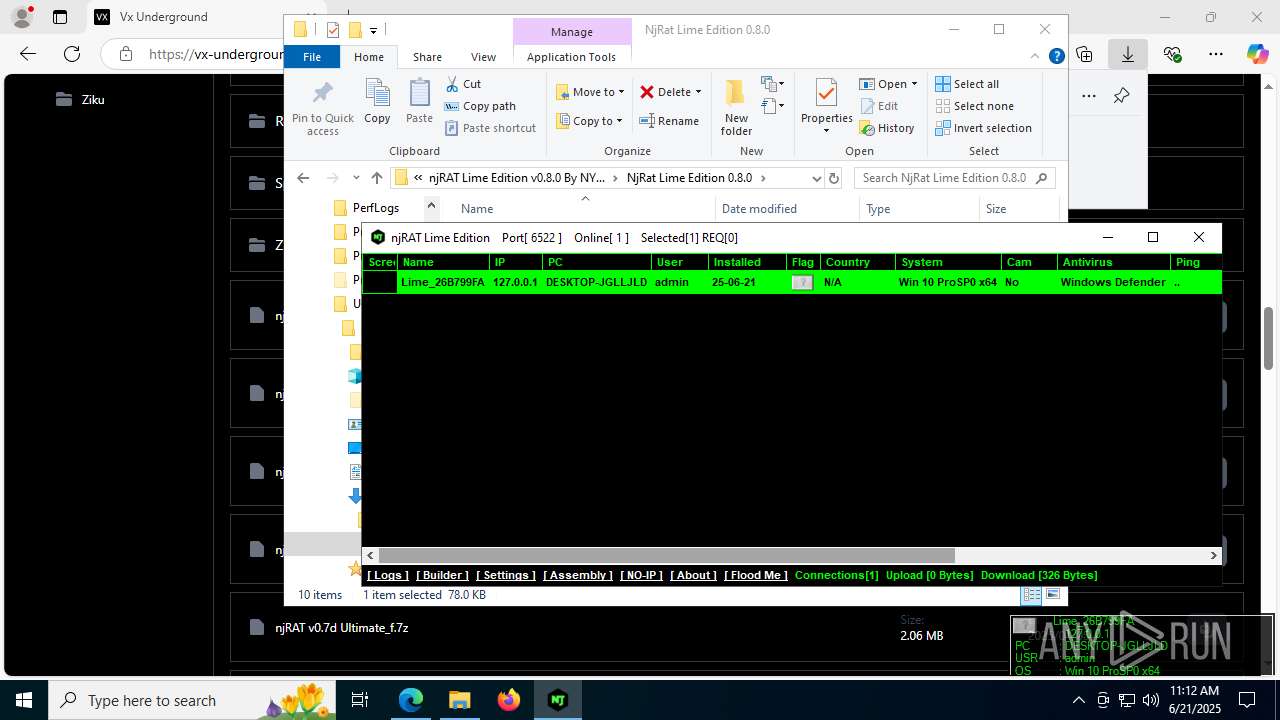
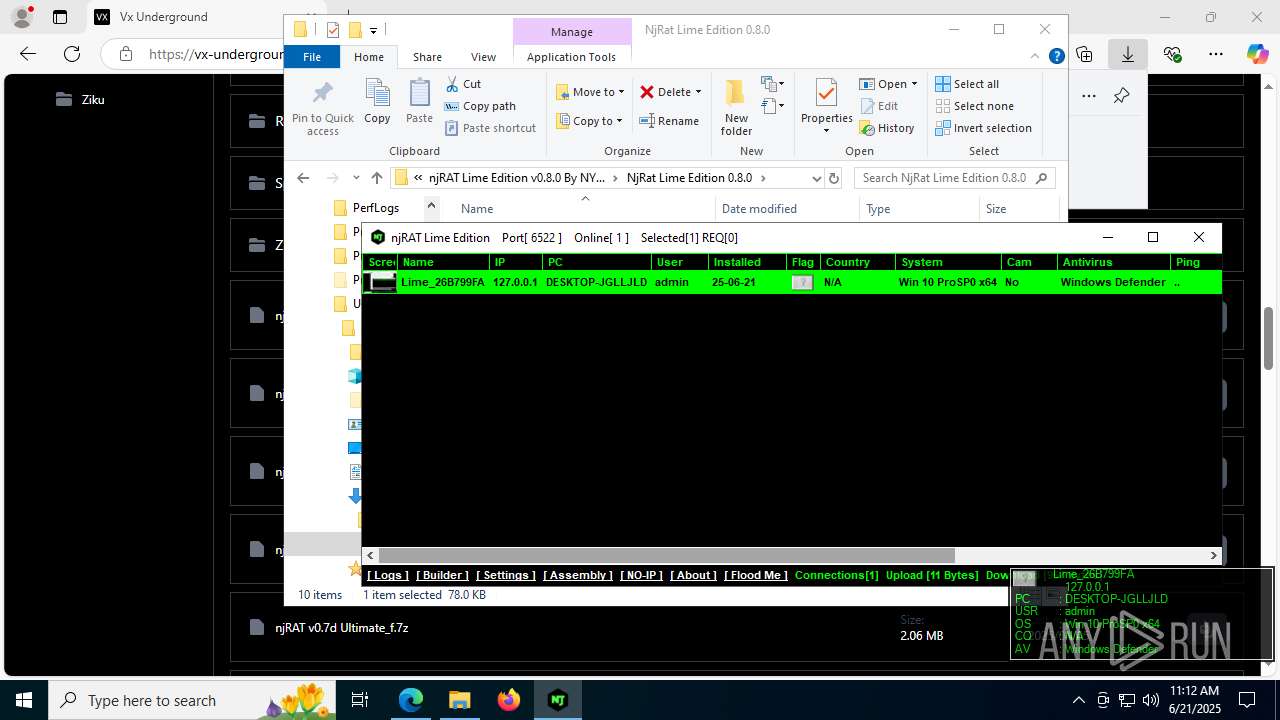
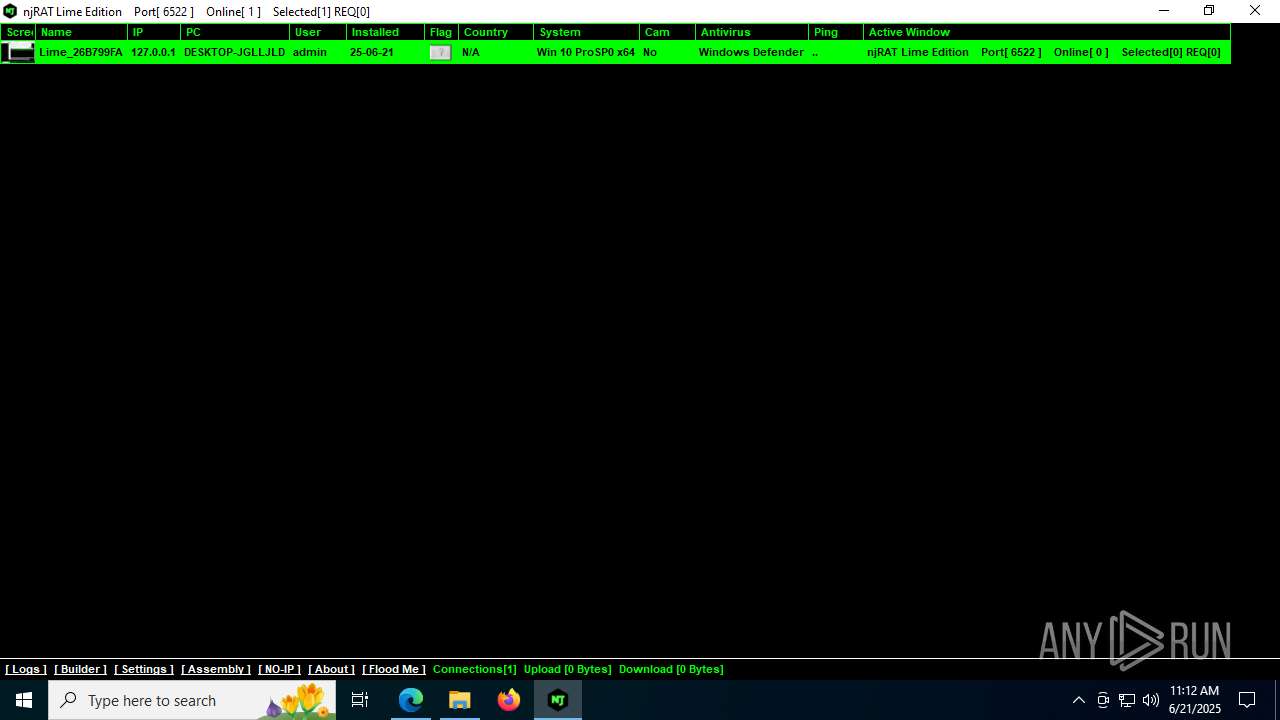
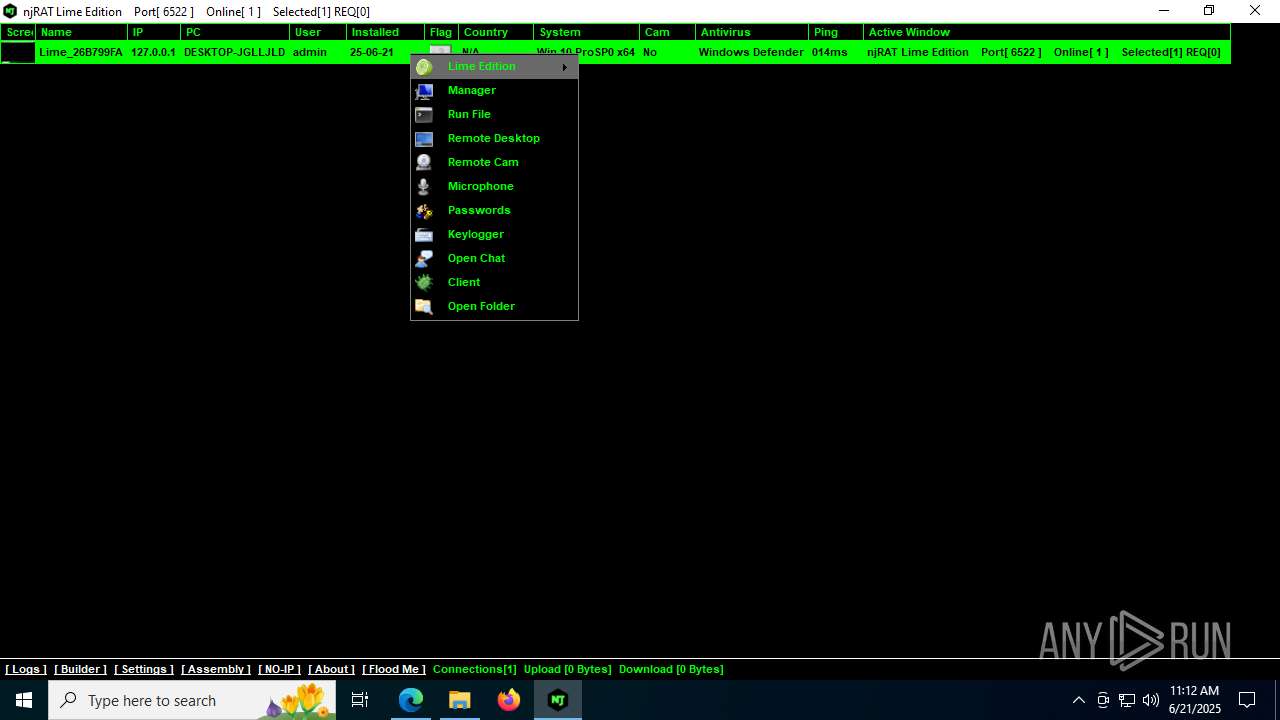
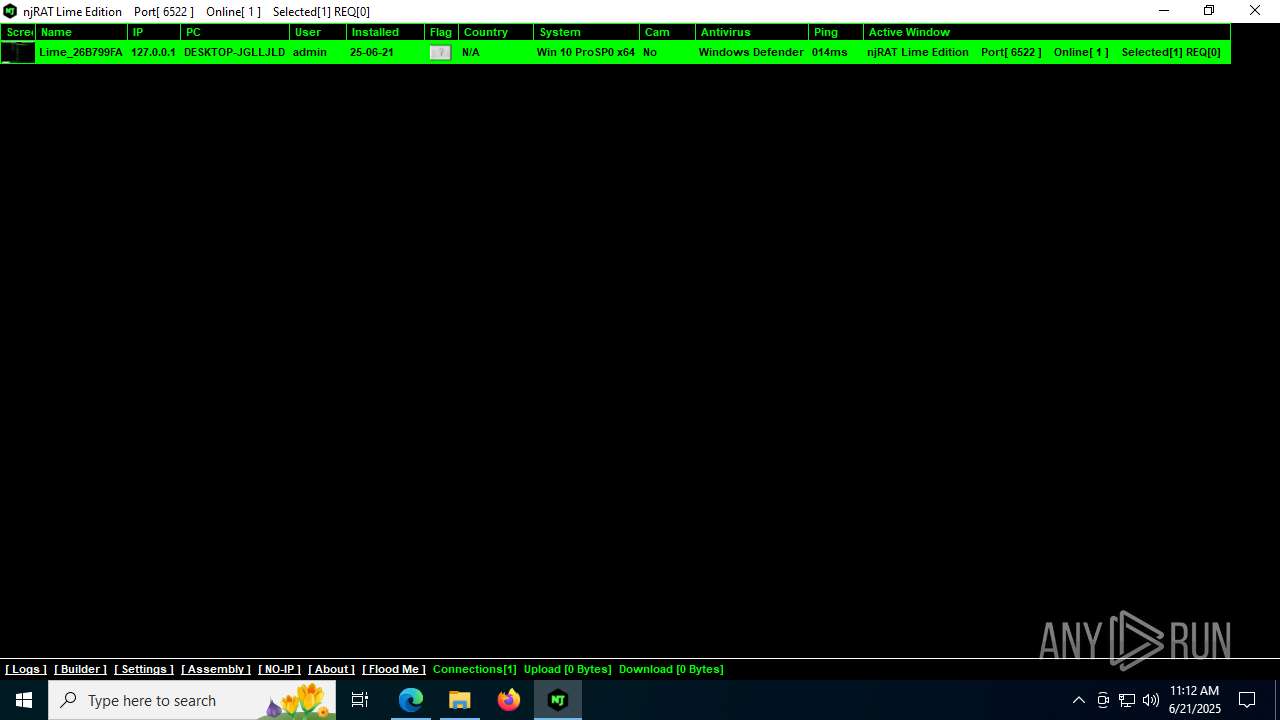
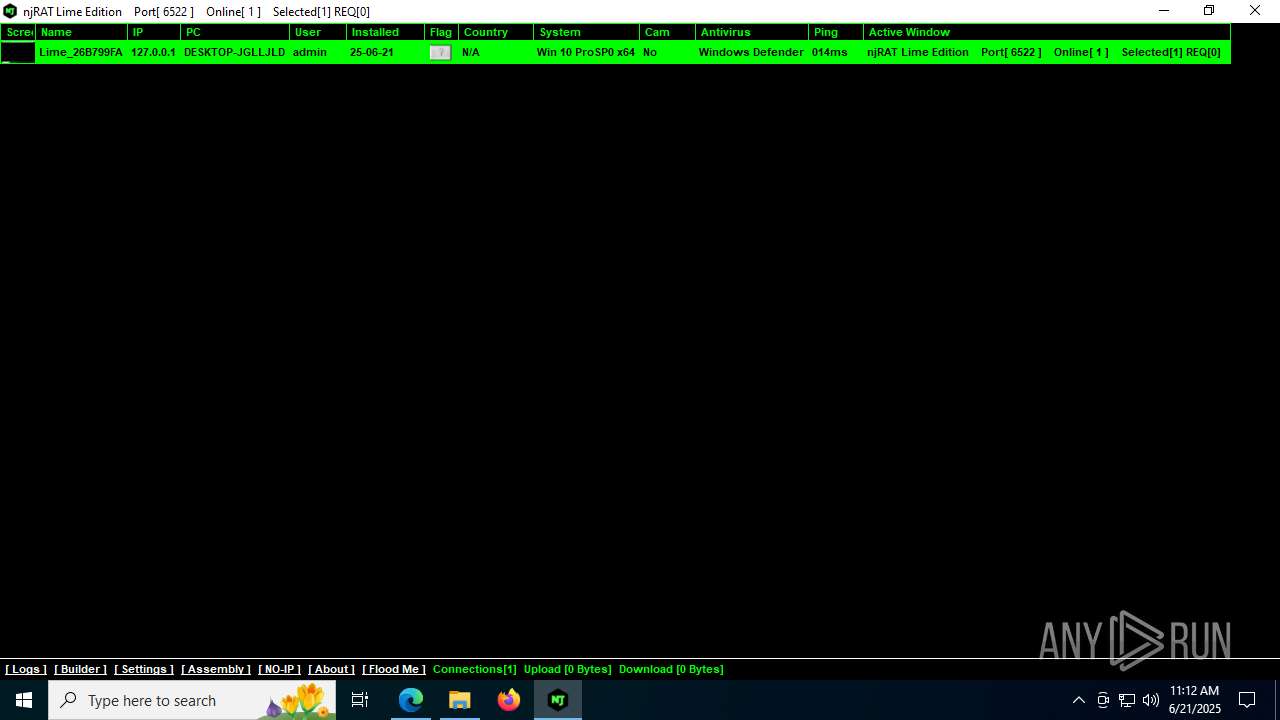
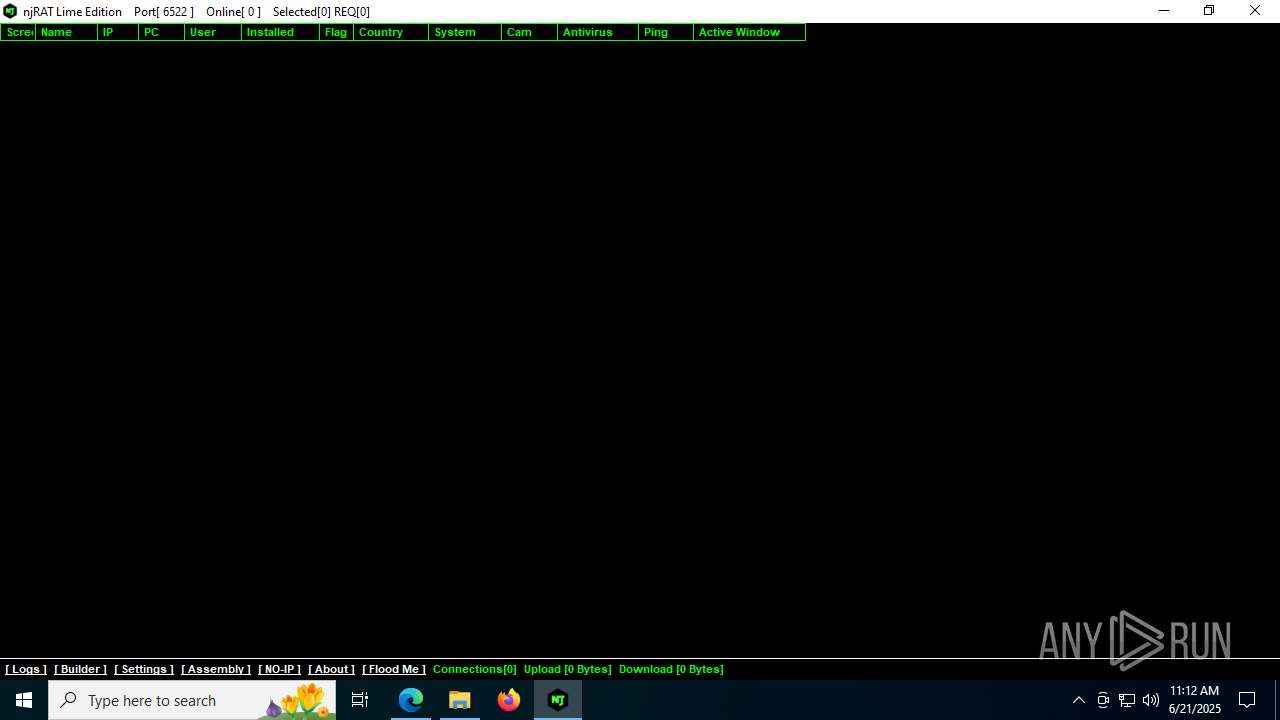
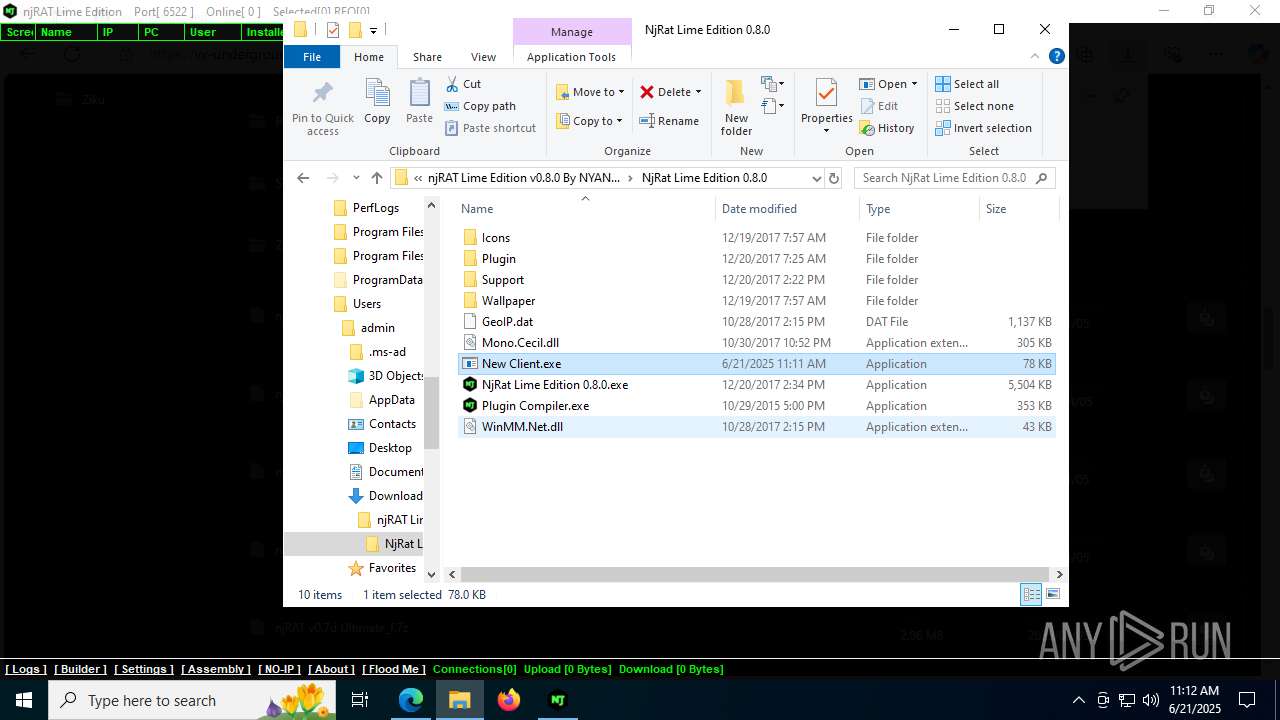
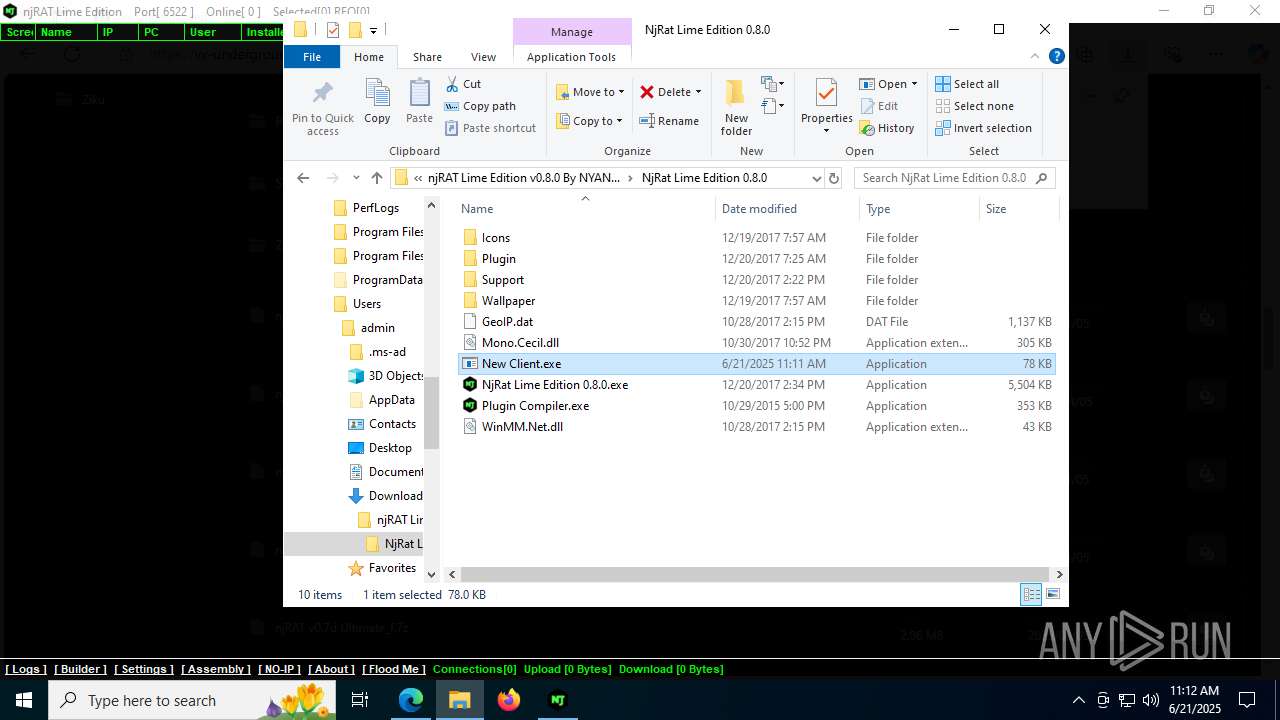
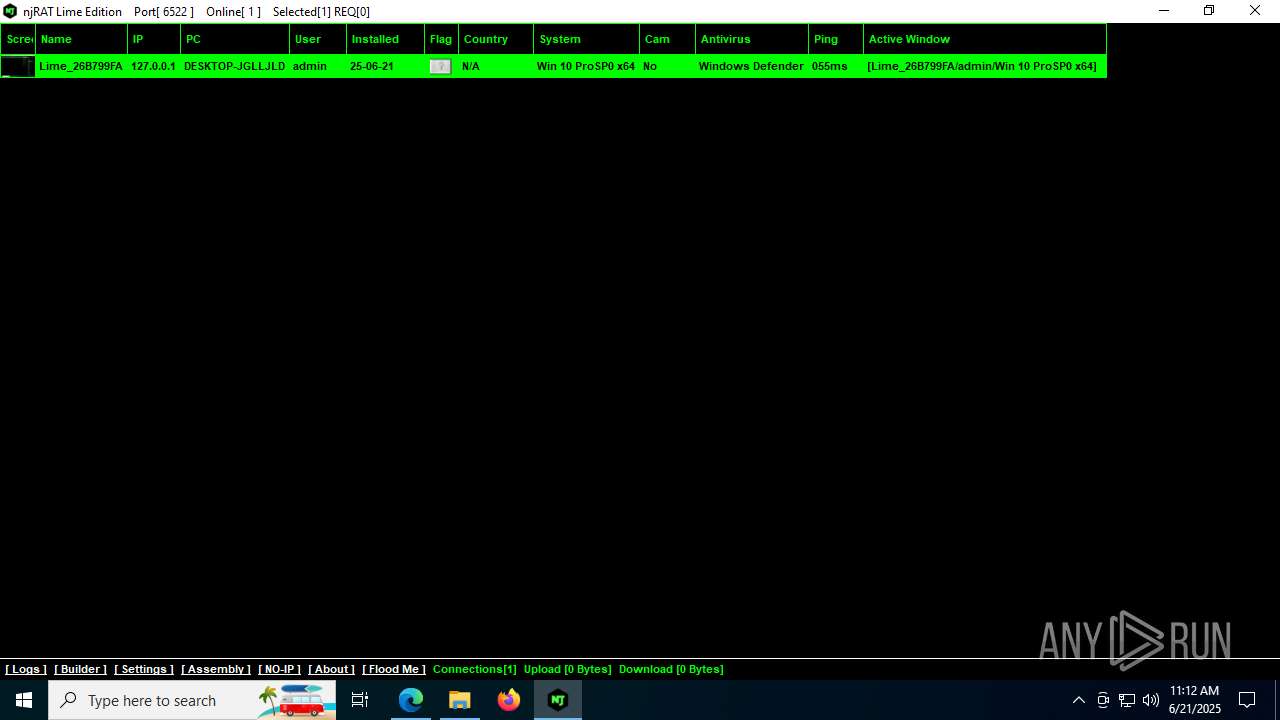
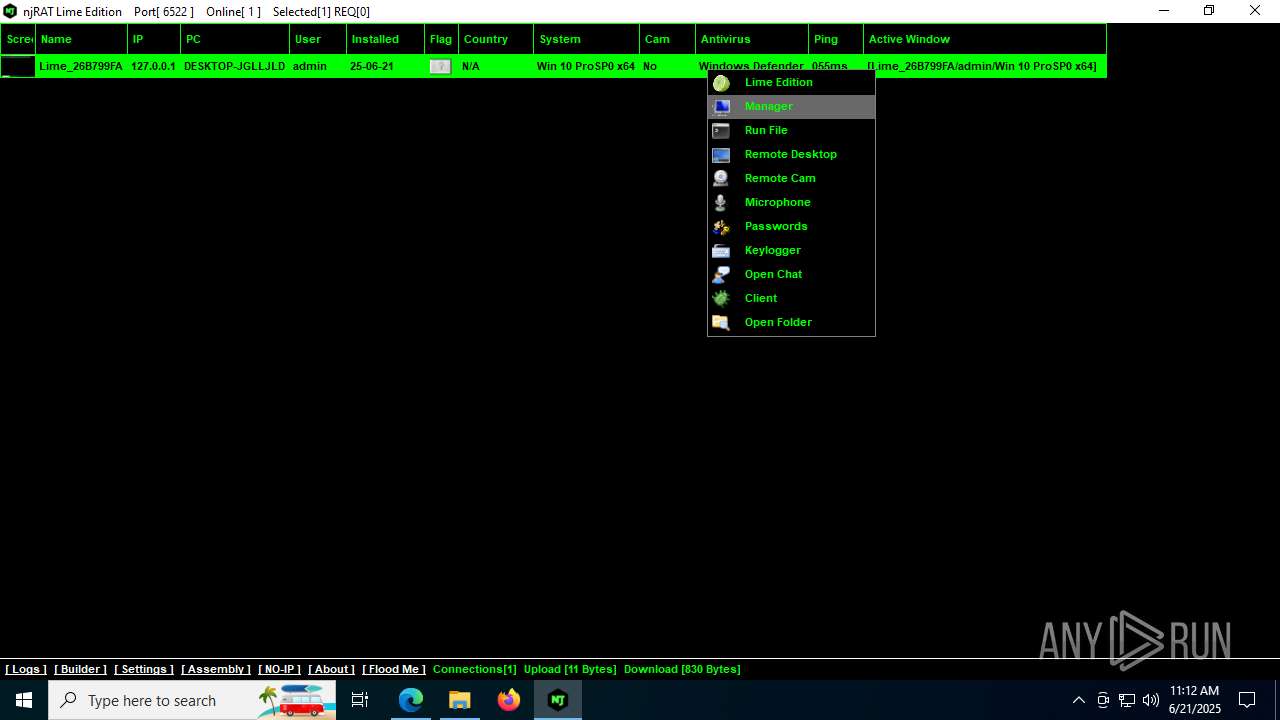
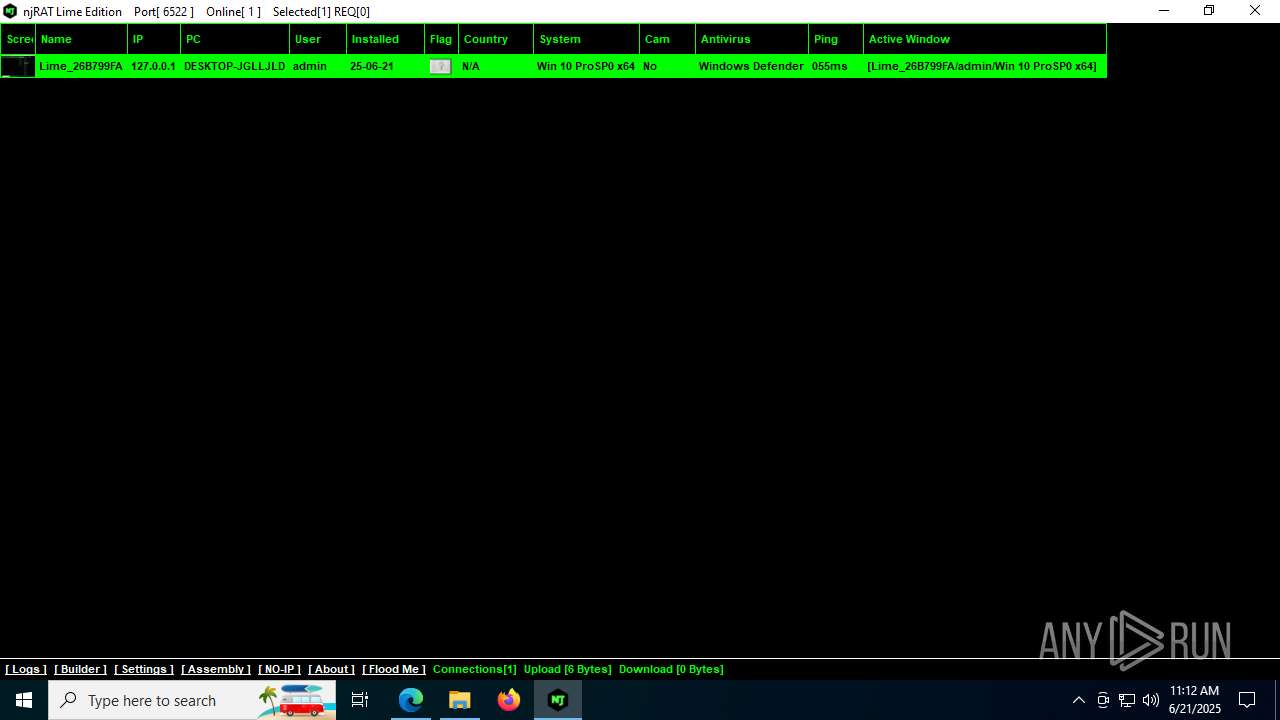
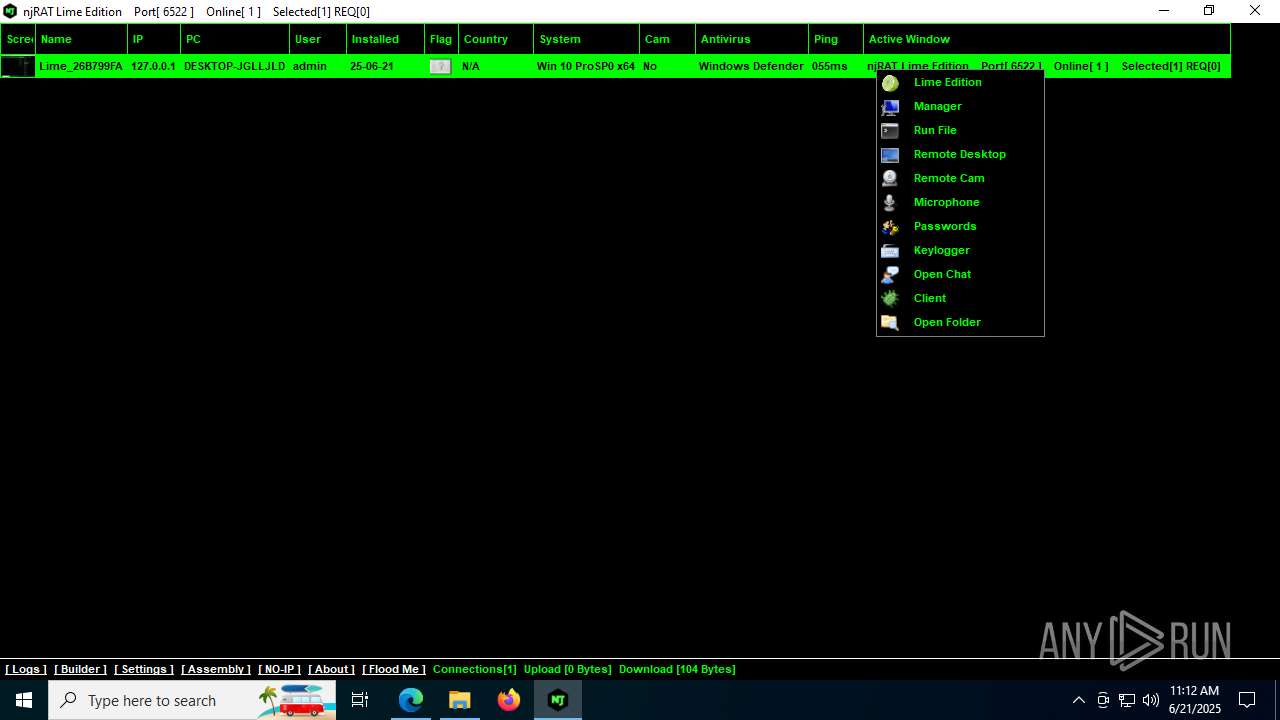
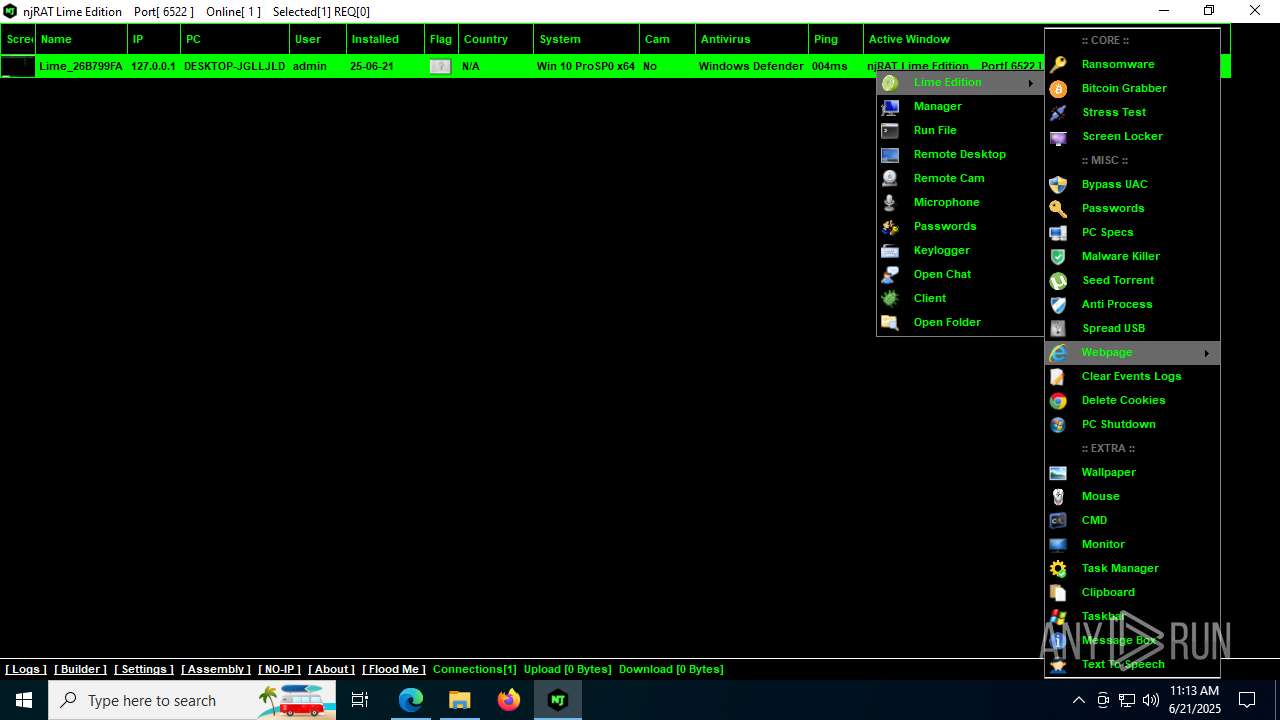
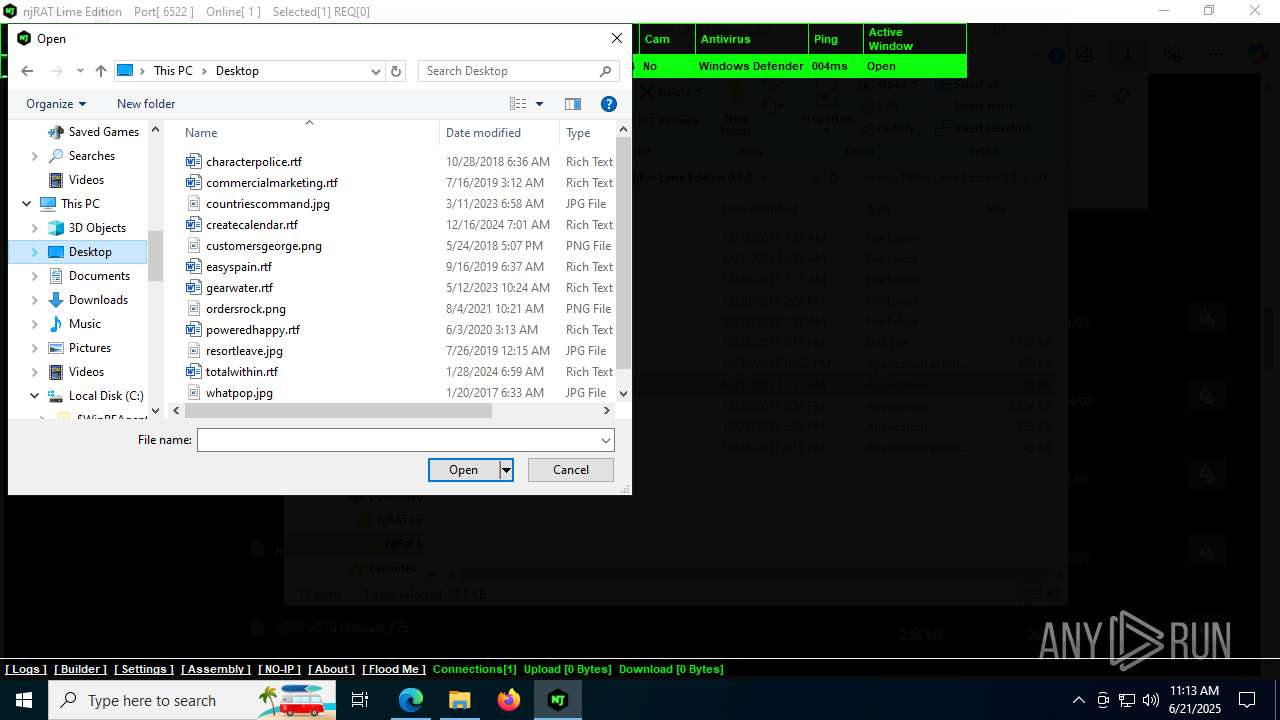
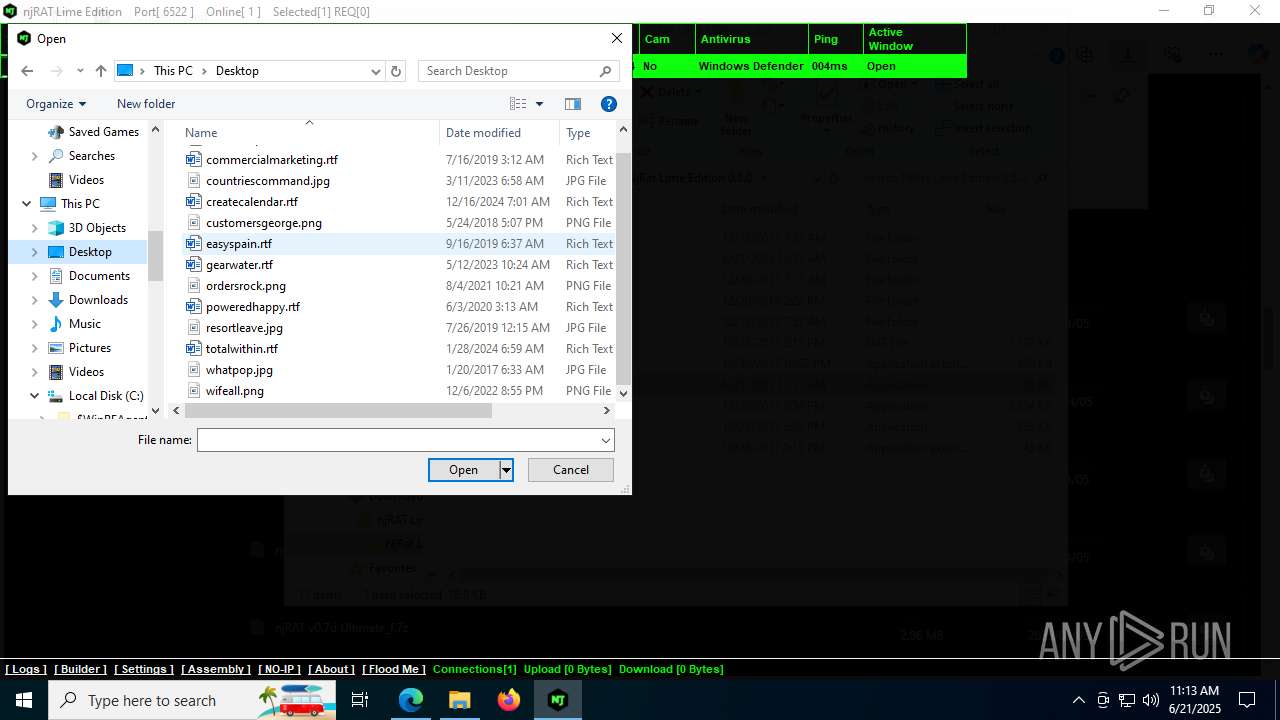
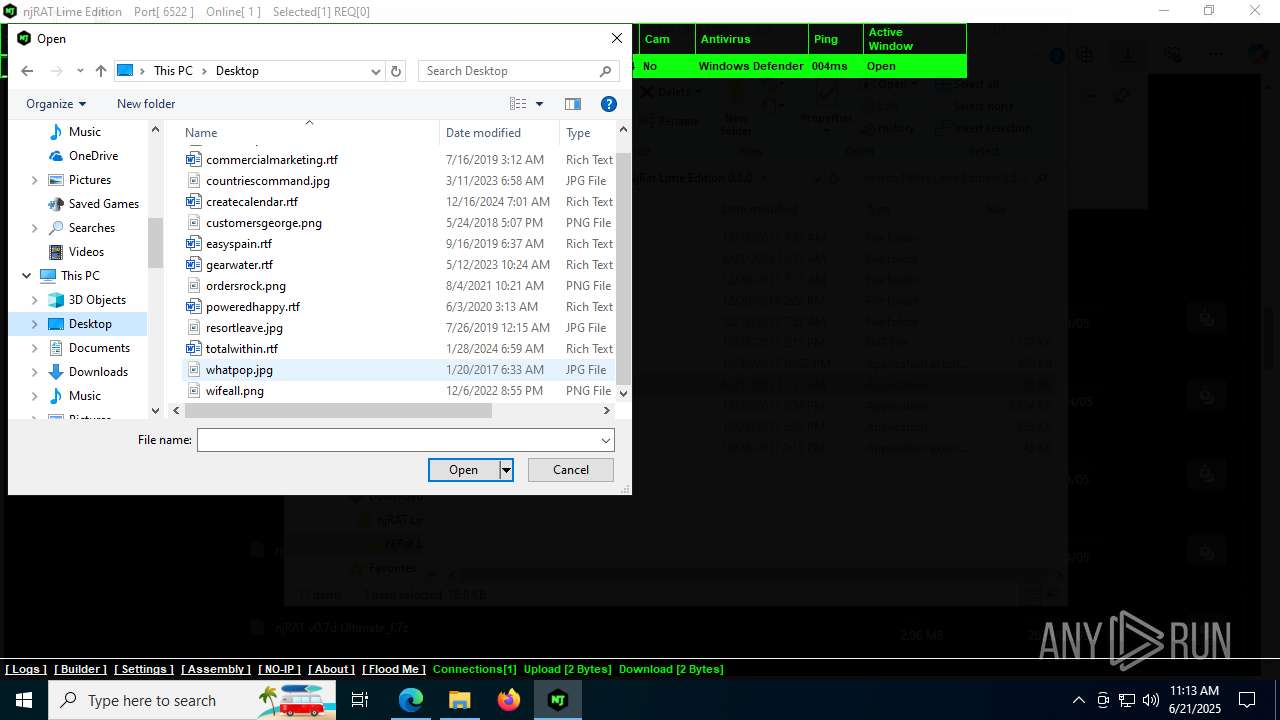
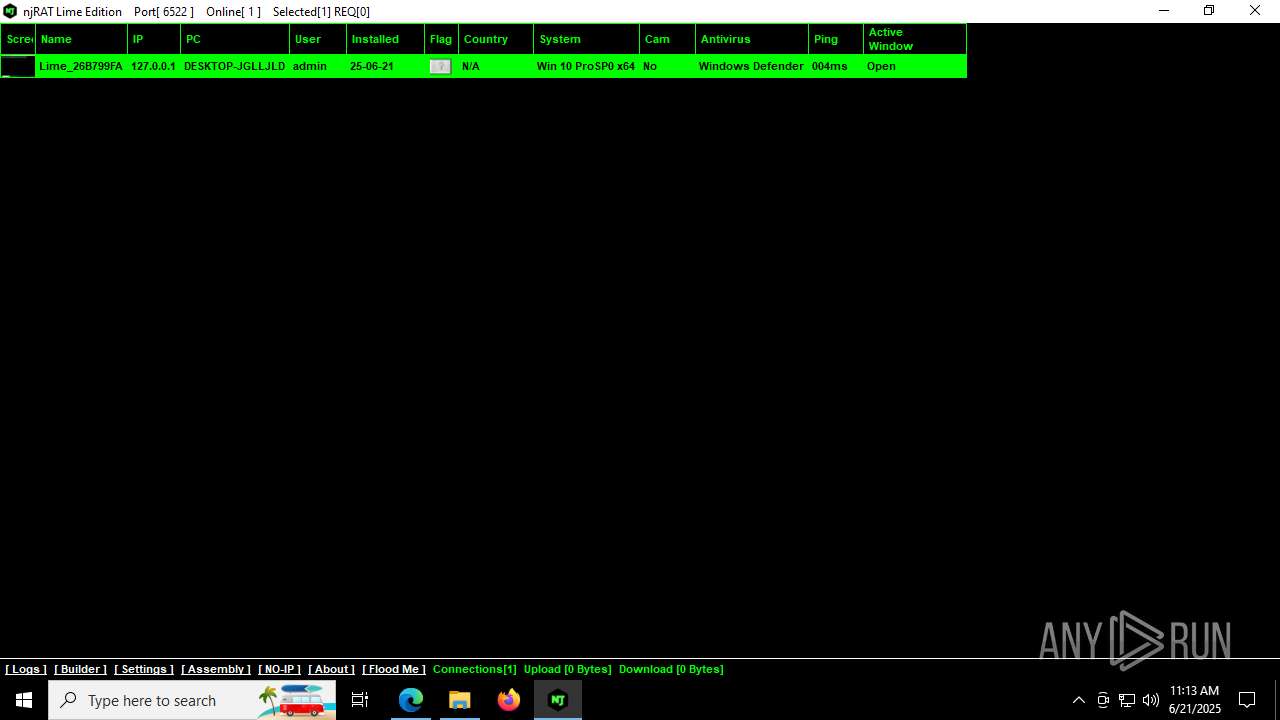
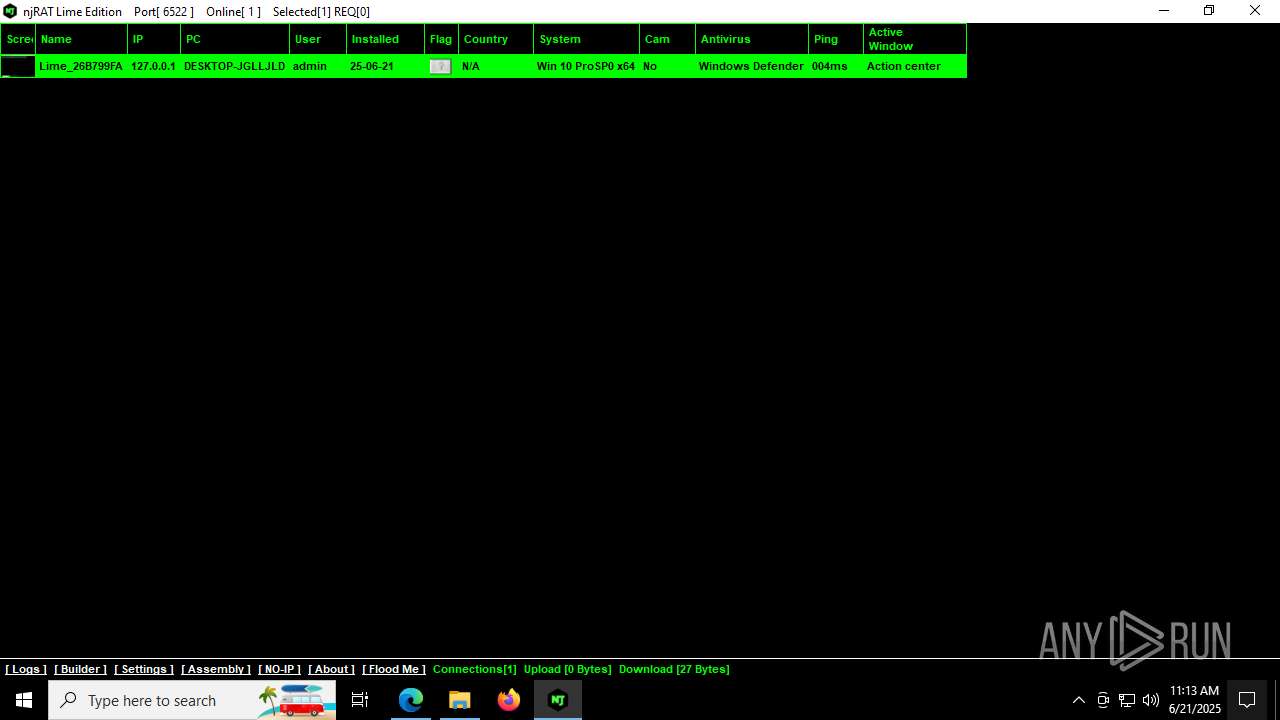
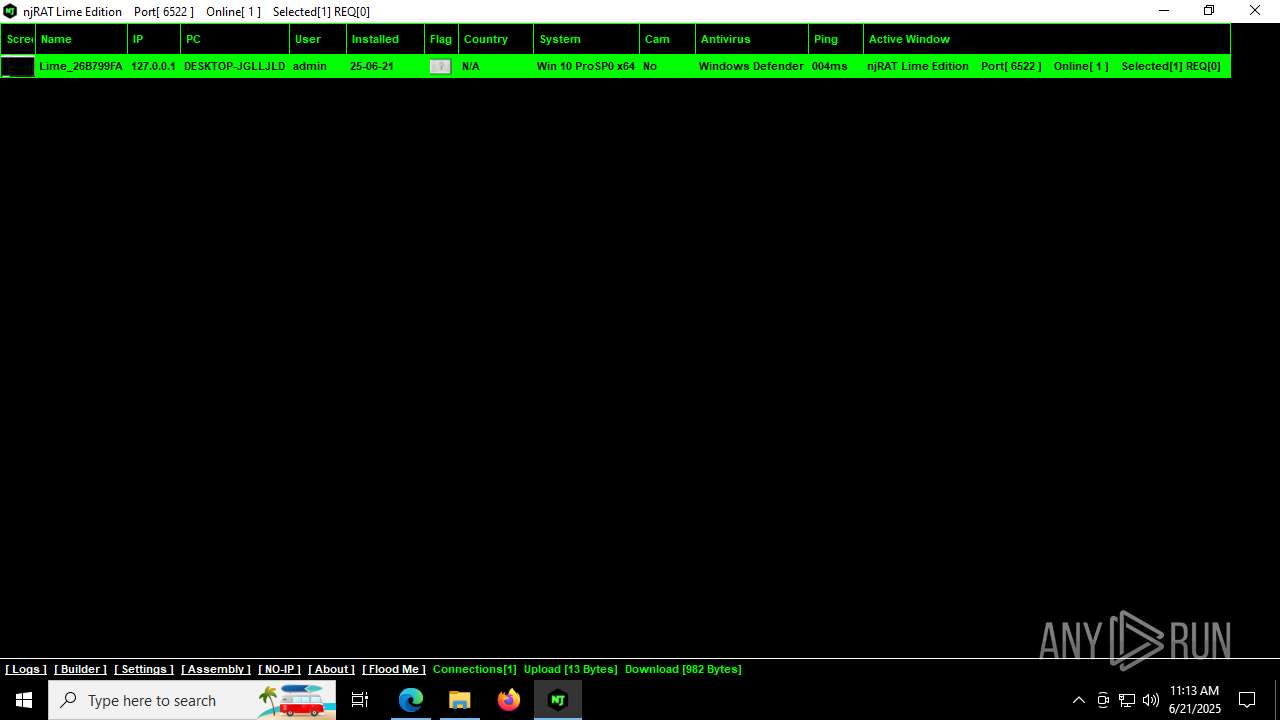
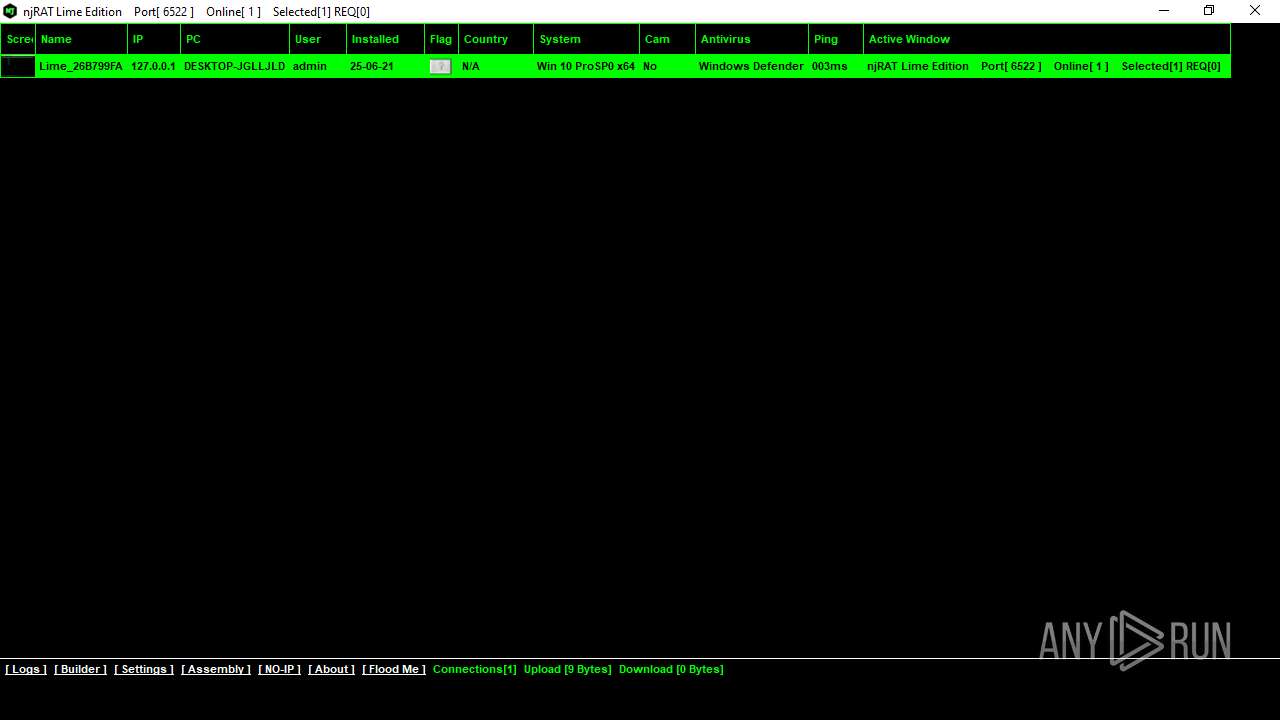
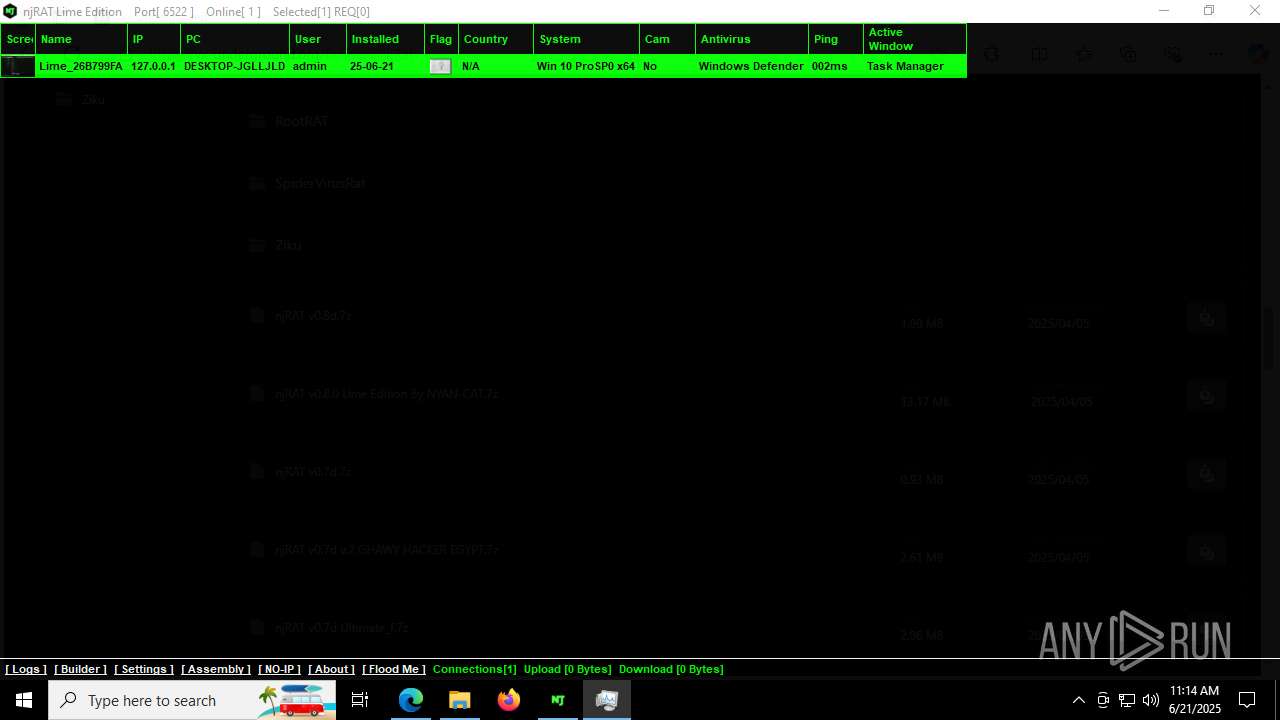
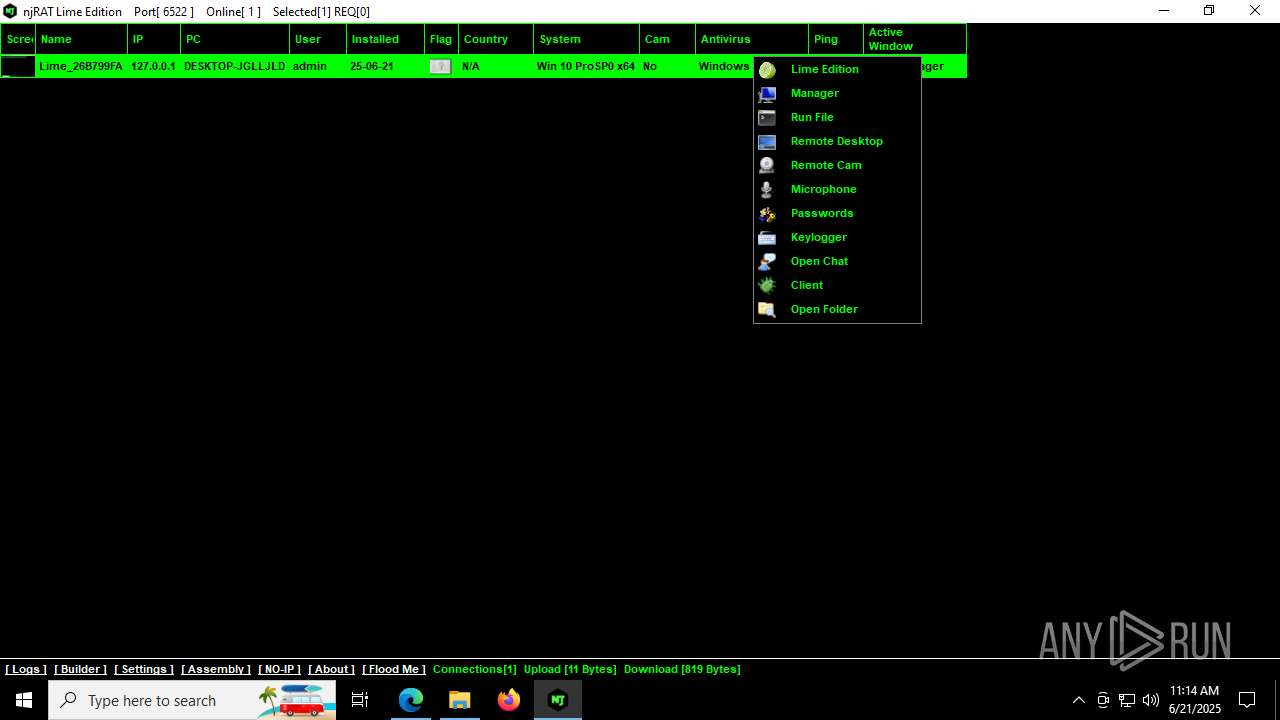
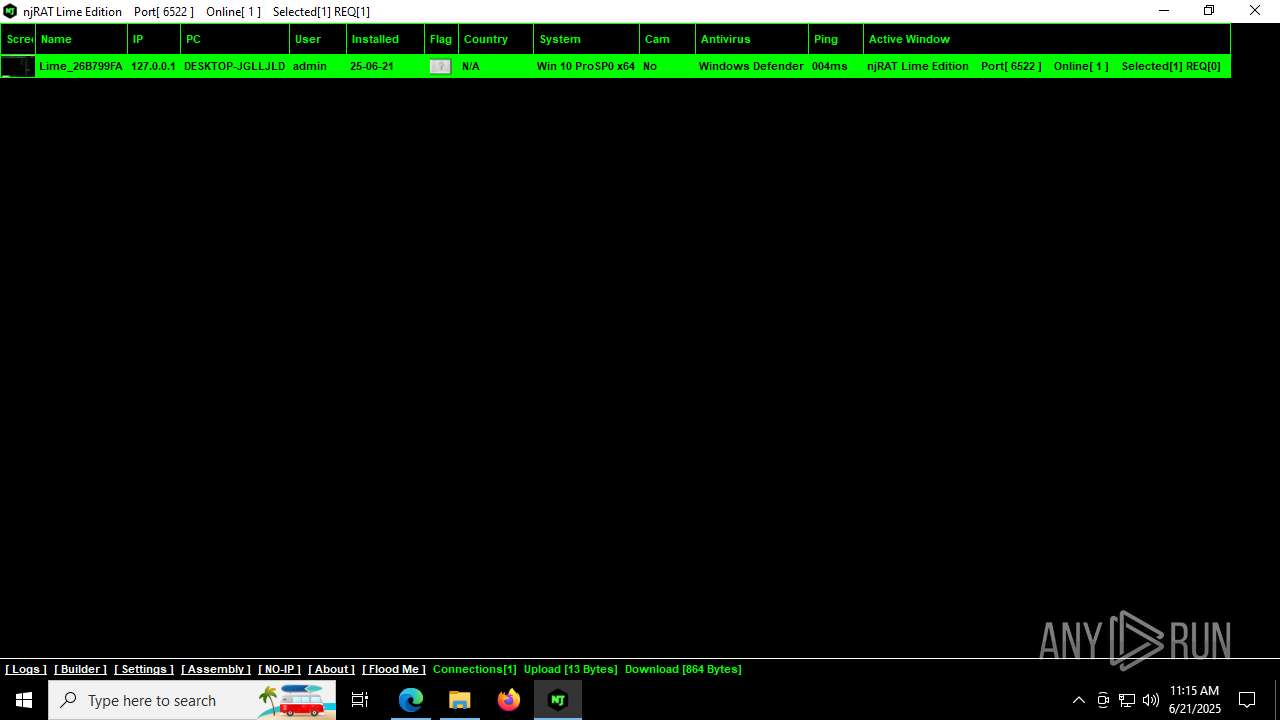
NjRat
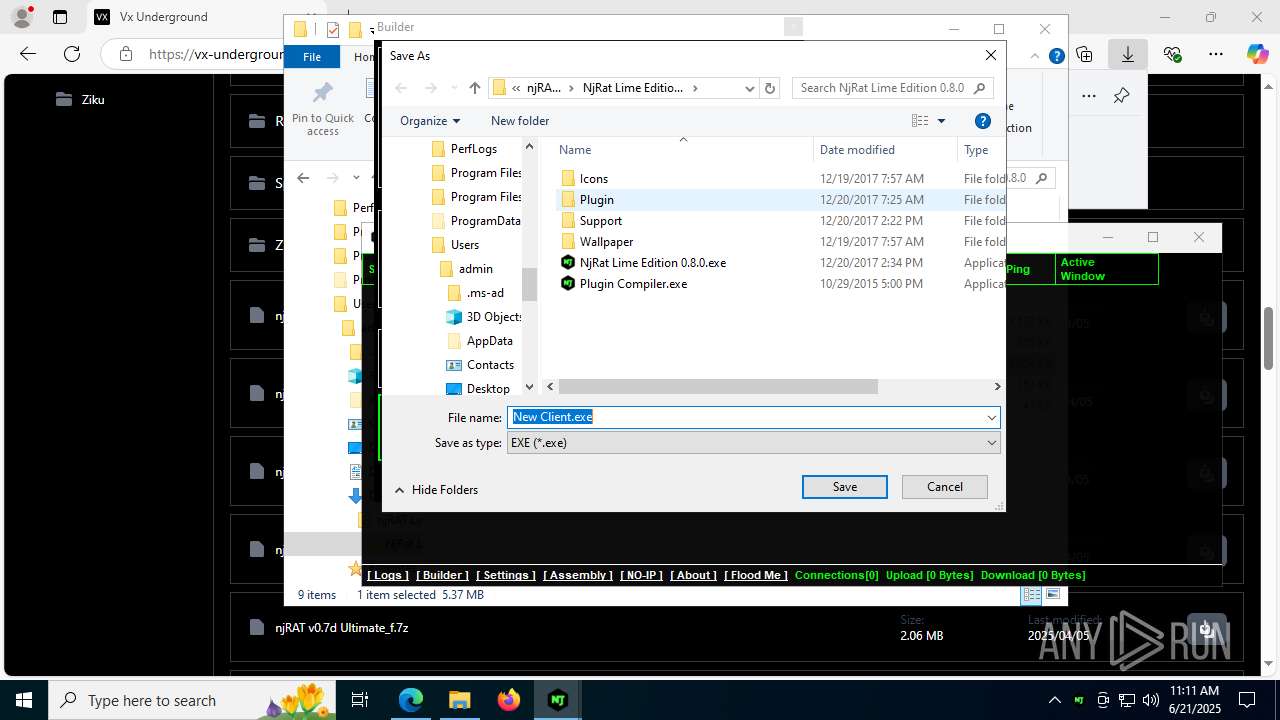
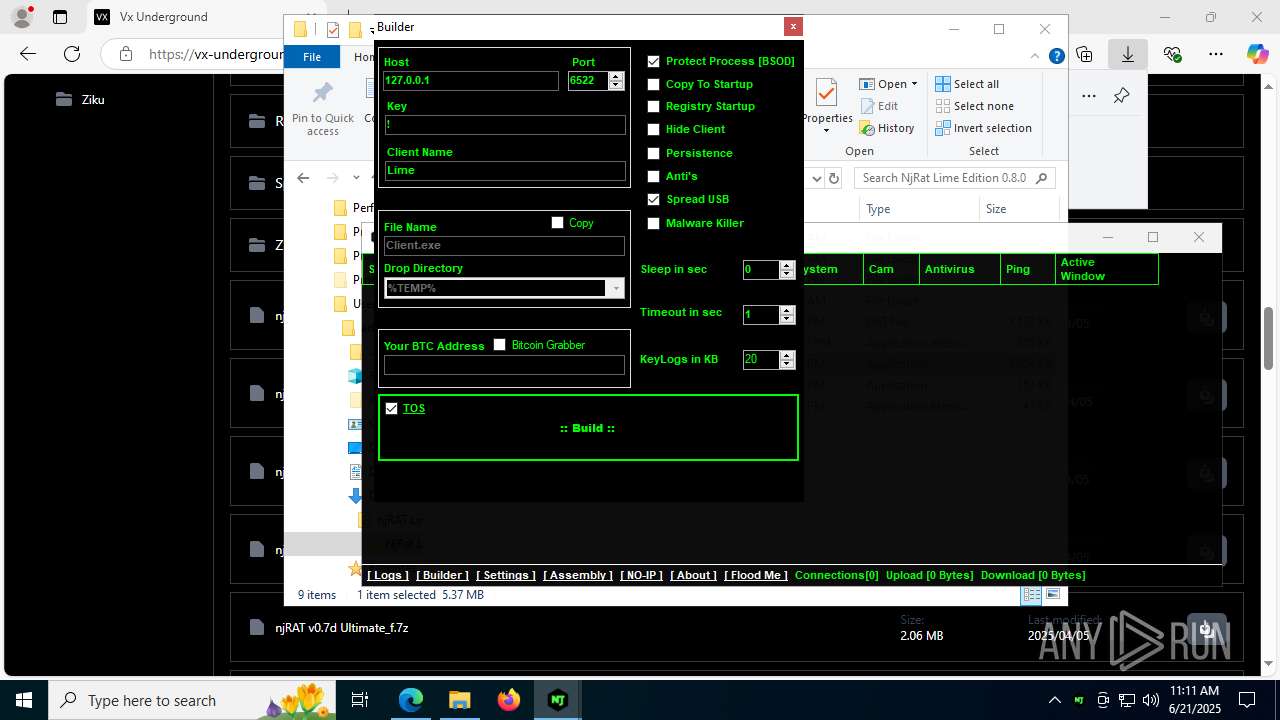
(PID) Process(7420) New Client.exe
C2127.0.0.1
Ports6522
BotnetLime
Options
Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\Client.exe
Splitter!
Version0.7.3
(PID) Process(504) New Client.exe
C2127.0.0.1
Ports6522
BotnetLime
Options
Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\Client.exe
Splitter!
Version0.7.3
Total processes
233
Monitored processes
75
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4892,i,6727261558776229158,3291424612196345115,262144 --variations-seed-version --mojo-platform-channel-handle=3900 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Version: 133.0.3065.92 Modules
| |||||||||||||||
| 504 | "C:\Users\admin\Downloads\njRAT Lime Edition v0.8.0 By NYAN-CAT\NjRat Lime Edition 0.8.0\New Client.exe" | C:\Users\admin\Downloads\njRAT Lime Edition v0.8.0 By NYAN-CAT\NjRat Lime Edition 0.8.0\New Client.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
NjRat(PID) Process(504) New Client.exe C2127.0.0.1 Ports6522 BotnetLime Options Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\Client.exe Splitter! Version0.7.3 | |||||||||||||||
| 892 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4084,i,11679002150250264642,16400539979736286721,262144 --variations-seed-version --mojo-platform-channel-handle=7108 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1068 | "C:\WINDOWS\system32\taskmgr.exe" /7 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4968,i,11679002150250264642,16400539979736286721,262144 --variations-seed-version --mojo-platform-channel-handle=7260 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1100 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6624,i,11679002150250264642,16400539979736286721,262144 --variations-seed-version --mojo-platform-channel-handle=1520 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1216 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5560,i,11679002150250264642,16400539979736286721,262144 --variations-seed-version --mojo-platform-channel-handle=5712 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4184,i,11679002150250264642,16400539979736286721,262144 --variations-seed-version --mojo-platform-channel-handle=6192 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1508 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5260,i,11679002150250264642,16400539979736286721,262144 --variations-seed-version --mojo-platform-channel-handle=5252 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 1 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1580 | C:\Users\admin\AppData\Local\Temp\\dump456\browser.exe -f C:\Users\admin\AppData\Local\Temp\\dump456\pass1.txt | C:\Users\admin\AppData\Local\Temp\dump456\browser.exe | tmp8459.tmp.exe | ||||||||||||
User: admin Company: SecurityXploded Integrity Level: MEDIUM Description: Browser Password Dump Exit code: 0 Version: 6.0.0.0 Modules
| |||||||||||||||
Total events
39 808
Read events
39 374
Write events
418
Delete events
16
Modification events
| (PID) Process: | (5328) SearchApp.exe | Key: | \REGISTRY\A\{33bbf253-2489-7544-6fed-a8e530b47e4d}\LocalState\ConstraintIndex |
| Operation: | write | Name: | CurrentConstraintIndexCabPath |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C005000610063006B0061006700650073005C004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E005300650061007200630068005F006300770035006E003100680032007400780079006500770079005C004C006F00630061006C00530074006100740065005C0043006F006E00730074007200610069006E00740049006E006400650078005C0049006E007000750074005F007B00380033003200620036003800640032002D0037006600650032002D0034006500370031002D0061003300610064002D003200360031003600360062003600350036006500630036007D000000A45E19139DE2DB01 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | \REGISTRY\A\{33bbf253-2489-7544-6fed-a8e530b47e4d}\LocalState\AppsConstraintIndex |
| Operation: | write | Name: | LatestConstraintIndexFolder |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C005000610063006B0061006700650073005C004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E005300650061007200630068005F006300770035006E003100680032007400780079006500770079005C004C006F00630061006C00530074006100740065005C0043006F006E00730074007200610069006E00740049006E006400650078005C0041007000700073005F007B00650066003200300034003500360034002D0063003900320037002D0034006200360031002D0039003800640063002D003600330035003700360066003800300035003200390034007D000000A45E19139DE2DB01 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | \REGISTRY\A\{33bbf253-2489-7544-6fed-a8e530b47e4d}\LocalState\AppsConstraintIndex |
| Operation: | write | Name: | LastConstraintIndexBuildCompleted |
Value: E1DA1A139DE2DB01A45E19139DE2DB01 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Microsoft.Windows.Search_cw5n1h2txyewy\AppsConstraintIndex |
| Operation: | write | Name: | CurrentConstraintIndexCabPath |
Value: C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Input_{832b68d2-7fe2-4e71-a3ad-26166b656ec6} | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Microsoft.Windows.Search_cw5n1h2txyewy\AppsConstraintIndex |
| Operation: | write | Name: | LatestConstraintIndexFolder |
Value: C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Apps_{ef204564-c927-4b61-98dc-63576f805294} | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | SafeSearchMode |
Value: 1 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Microsoft.Windows.Search_cw5n1h2txyewy\AppsConstraintIndex |
| Operation: | write | Name: | IndexedLanguage |
Value: en-US | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | \REGISTRY\A\{33bbf253-2489-7544-6fed-a8e530b47e4d}\LocalState\AppIndexer |
| Operation: | write | Name: | LatestCacheFileName |
Value: 410070007000430061006300680065003100330033003900340039003700370038003100380032003600390035003300360036002E007400780074000000A45E19139DE2DB01 | |||
| (PID) Process: | (5328) SearchApp.exe | Key: | \REGISTRY\A\{33bbf253-2489-7544-6fed-a8e530b47e4d}\LocalState\AppIndexer |
| Operation: | write | Name: | InstalledWin32AppsRevision |
Value: 7B00420032003700390045003300340042002D0044004400370039002D0034003100360035002D0039004100370039002D003800370045003600430030003000370034003400370041007D000000ACC31B139DE2DB01 | |||
| (PID) Process: | (2044) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
35
Suspicious files
299
Text files
286
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF176e5a.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF176e5a.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176e5a.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF176e5a.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Apps_{ef204564-c927-4b61-98dc-63576f805294}\0.0.filtertrie.intermediate.txt | text | |
MD5:8C4DFB28DEB8DB4897B5E156091964AF | SHA256:9E61BCD8147F88EF3AE653DCF1CE0C52F280E1E143311B7A54B09C2CF7E3BF0A | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF176e98.TMP | — | |
MD5:— | SHA256:— | |||
| 2044 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176e98.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
113
DNS requests
97
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1380 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5244 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:zv3yBiUuW7W4_Gcw9TEkNlOeaHJJOo0pgENuzNOSjWs&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7996 | svchost.exe | HEAD | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/03b2d981-4f59-42a6-8f9a-a2b6278a0020?P1=1751013037&P2=404&P3=2&P4=SOcw53EV2kYktJNBTUMELp6Kfc9oQN3Ie60%2fN852GF%2foLwWqiXJUsCPjciRtRbo0Gd9X6adoSN5P99kyYnOrfA%3d%3d | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 96.16.53.133:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7820 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7820 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7996 | svchost.exe | HEAD | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751013037&P2=404&P3=2&P4=LHROlZpWCd7dfac%2bQuflBfYsVq%2bPYXK2p0V6mDgeQpHJf1yeq7I%2biqqF1bsoGRtqaGBOz816DTmIgjt8XII1Tw%3d%3d | unknown | — | — | whitelisted |
7996 | svchost.exe | HEAD | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1751013038&P2=404&P3=2&P4=TLba5Mj3eND%2bpmOQA2SuN2jq4qcAK23hjtrMBy%2fmBml21TQ7cfIthE2I2YcFNYaoACbdkUGY9tFeLyWMu1aP2w%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
472 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5244 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5244 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5244 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5244 | msedge.exe | 104.18.6.192:443 | vx-underground.org | CLOUDFLARENET | — | shared |
5244 | msedge.exe | 2.16.241.220:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
vx-underground.org |
| malicious |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
challenges.cloudflare.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5244 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
5244 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
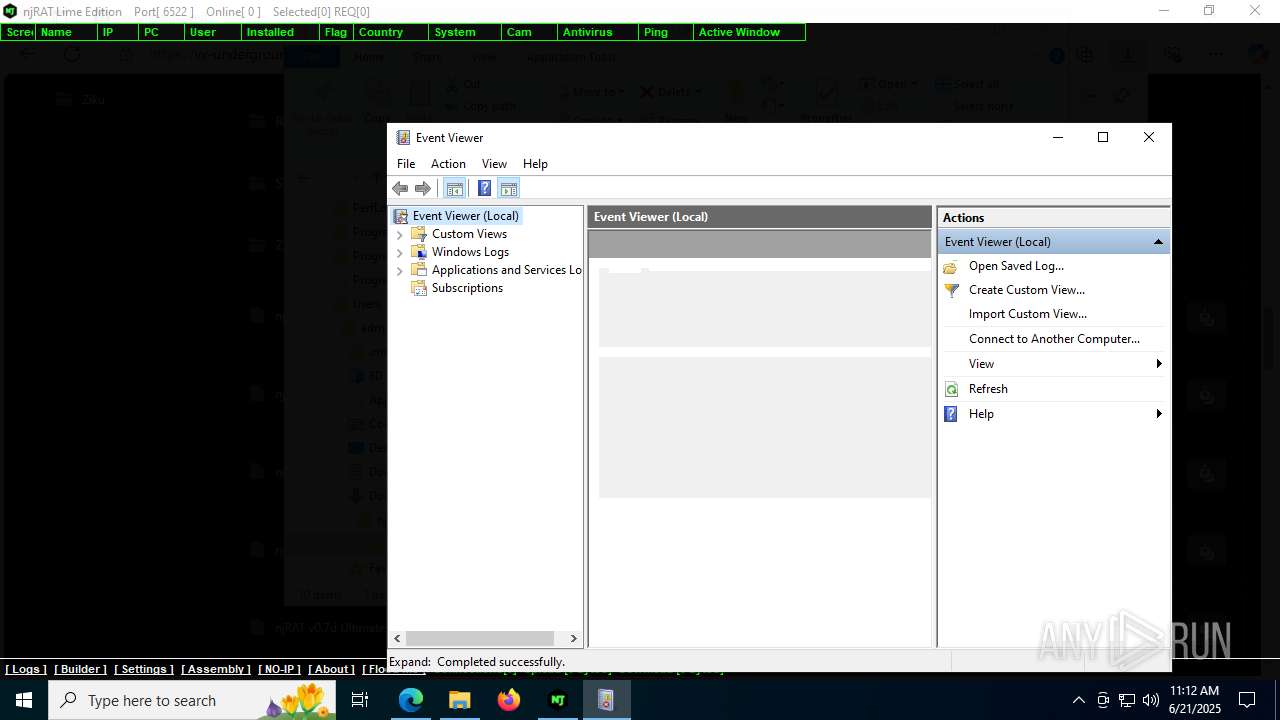
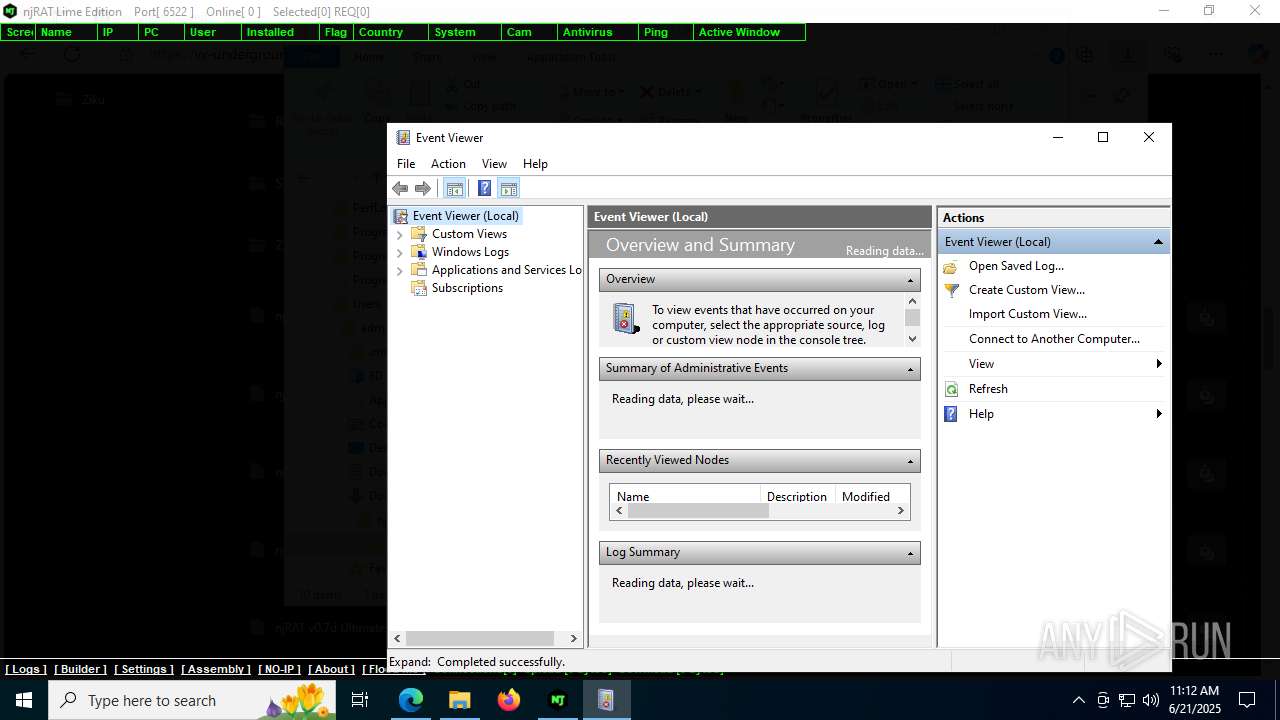
Process | Message |
|---|---|
mmc.exe | "C:\WINDOWS\system32\eventvwr.msc" "C:\WINDOWS\system32\eventvwr.msc" |
mmc.exe | |
mmc.exe | ViewerConfigPath = 'C:\ProgramData\Microsoft\Event Viewer': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerAdminViewsPath = 'C:\ProgramData\Microsoft\Event Viewer\Views\ApplicationViewsRootNode': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerExternalLogsPath = 'C:\ProgramData\Microsoft\Event Viewer\ExternalLogs': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerViewsFolderPath = 'C:\ProgramData\Microsoft\Event Viewer\Views': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | Failed to get ChannelConfigOwningPublisher -122-The data area passed to a system call is too small
|
mmc.exe | Getting next publisher from enum failed-259-No more data is available
|
mmc.exe | Failed to get ChannelConfigOwningPublisher -122-The data area passed to a system call is too small
|
mmc.exe | ExpandNode:After EventsNode:InsertChildren CountOfChildren = 5
|