| File name: | pdf.vbs |
| Full analysis: | https://app.any.run/tasks/b933d202-bc5c-4473-8c4a-9bc56b40a71b |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | July 17, 2019, 07:57:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | F976C522799CB8F6588DA23253C2F6CD |
| SHA1: | 6526E30138A9EF4FBFAD6A55F5DBD236C32346CE |
| SHA256: | A54C5C570DFBF3C738D43E0B8D3CBE17F7B2D34106196564F47187EB0CAABA4E |
| SSDEEP: | 49152:ayPdrWgGZi9pU9Ui7rtKh3IHhr3rW1GZgDILfLAwq20B6LSI:u |
MALICIOUS
Application was dropped or rewritten from another process
- file1name.exe (PID: 864)
- file2name.exe (PID: 2324)
Changes the autorun value in the registry
- file2name.exe (PID: 2324)
- file1name.exe (PID: 864)
NanoCore was detected
- RegAsm.exe (PID: 4020)
AGENTTESLA was detected
- RegAsm.exe (PID: 1500)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 1500)
Connects to CnC server
- RegAsm.exe (PID: 4020)
SUSPICIOUS
Suspicious files were dropped or overwritten
- file1name.exe (PID: 864)
- file2name.exe (PID: 2324)
Creates files in the user directory
- file1name.exe (PID: 864)
- file2name.exe (PID: 2324)
- RegAsm.exe (PID: 4020)
Executable content was dropped or overwritten
- WScript.exe (PID: 3500)
- file1name.exe (PID: 864)
- file2name.exe (PID: 2324)
Executed via COM
- DllHost.exe (PID: 3020)
Checks for external IP
- RegAsm.exe (PID: 1500)
Uses REG.EXE to modify Windows registry
- RegAsm.exe (PID: 1500)
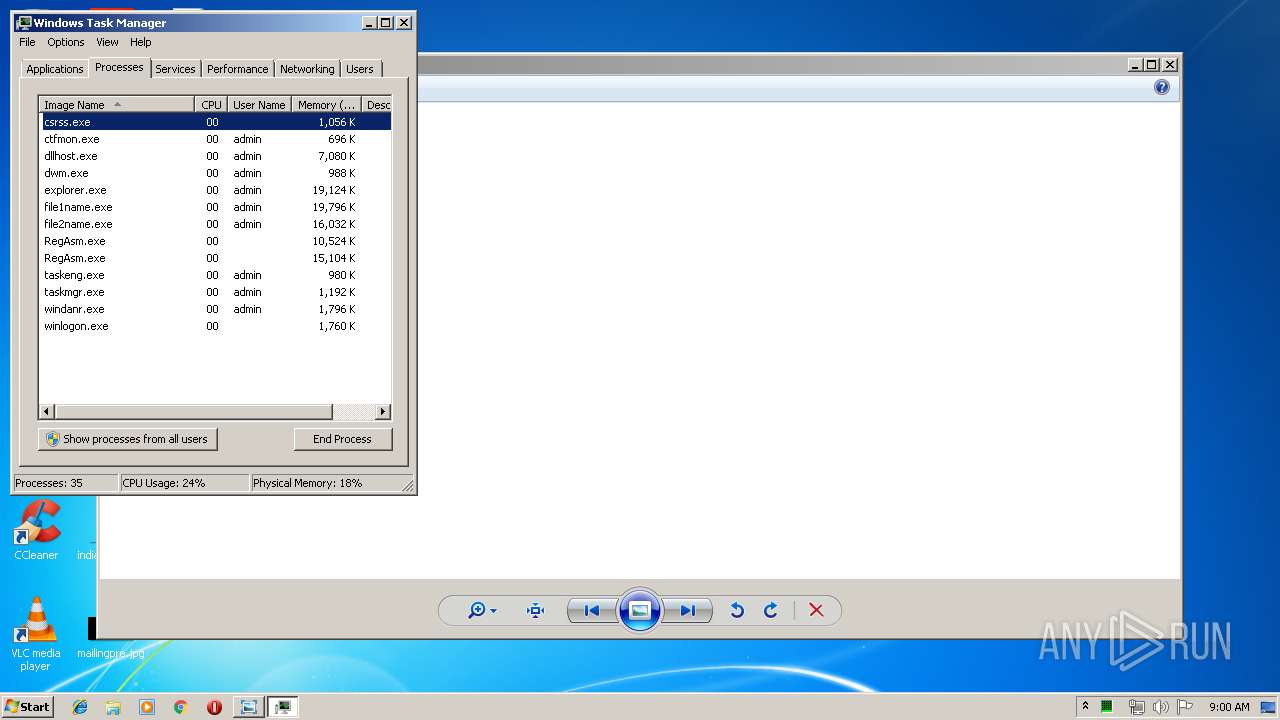
INFO
Manual execution by user
- taskmgr.exe (PID: 2592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | "C:\Users\admin\AppData\Local\Temp\file1name.exe" | C:\Users\admin\AppData\Local\Temp\file1name.exe | WScript.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Update Setup Exit code: 0 Version: ... Modules
| |||||||||||||||
| 1488 | REG add HKCU\Software\Policies\Microsoft\Windows\System /v DisableCMD /t REG_DWORD /d 1 /f | C:\Windows\system32\REG.exe | — | RegAsm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1500 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | file1name.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2240 | REG add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\system32\REG.exe | — | RegAsm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2324 | "C:\Users\admin\AppData\Local\Temp\file2name.exe" | C:\Users\admin\AppData\Local\Temp\file2name.exe | WScript.exe | ||||||||||||
User: admin Company: tpmvscmgr Integrity Level: MEDIUM Description: cemapi Exit code: 0 Version: 216.738.813.879 Modules
| |||||||||||||||
| 2592 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3020 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3500 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\pdf.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 4020 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | file2name.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
564
Read events
533
Write events
31
Delete events
0
Modification events
| (PID) Process: | (3500) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3500) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2324) file2name.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | RRzkLShOyE |
Value: C:\Users\Public\RRzkLShOyE.vbs | |||
| (PID) Process: | (864) file1name.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | yXlEoUtolf |
Value: C:\Users\Public\yXlEoUtolf.vbs | |||
| (PID) Process: | (3020) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (1500) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1500) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1500) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1500) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1500) RegAsm.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RegAsm_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
4
Suspicious files
2
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2324 | file2name.exe | C:\Users\Public\RRzkLShOyE.vbs | text | |
MD5:— | SHA256:— | |||
| 3500 | WScript.exe | C:\Users\admin\AppData\Local\Temp\file1name.exe | executable | |
MD5:— | SHA256:— | |||
| 1500 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\636989507458007500_3c046ad7-81c2-4f55-9be0-da8a26455f50.db | sqlite | |
MD5:— | SHA256:— | |||
| 3500 | WScript.exe | C:\Users\admin\AppData\Local\Temp\file2name.exe | executable | |
MD5:— | SHA256:— | |||
| 2324 | file2name.exe | C:\Users\admin\AppData\Roaming\TsWpfWrp\bidispl.bat | executable | |
MD5:— | SHA256:— | |||
| 864 | file1name.exe | C:\Users\Public\yXlEoUtolf.vbs | text | |
MD5:— | SHA256:— | |||
| 4020 | RegAsm.exe | C:\Users\admin\AppData\Roaming\90059C37-1320-41A4-B58D-2B75A9850D2F\run.dat | text | |
MD5:— | SHA256:— | |||
| 864 | file1name.exe | C:\Users\admin\AppData\Roaming\RuntimeBroker\SystemPropertiesRemote.bat | executable | |
MD5:— | SHA256:— | |||
| 4020 | RegAsm.exe | C:\Users\admin\AppData\Roaming\90059C37-1320-41A4-B58D-2B75A9850D2F\catalog.dat | bs | |
MD5:9E7D0351E4DF94A9B0BADCEB6A9DB963 | SHA256:AAFC7B40C5FE680A2BB549C3B90AABAAC63163F74FFFC0B00277C6BBFF88B757 | |||
| 4020 | RegAsm.exe | C:\Users\admin\AppData\Roaming\90059C37-1320-41A4-B58D-2B75A9850D2F\storage.dat | binary | |
MD5:653DDDCB6C89F6EC51F3DDC0053C5914 | SHA256:83B9CAE66800C768887FB270728F6806CBEBDEAD9946FA730F01723847F17FF9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
9
DNS requests
8
Threats
80
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1500 | RegAsm.exe | GET | 200 | 18.211.215.84:80 | http://checkip.amazonaws.com/ | US | text | 16 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4020 | RegAsm.exe | 69.197.188.187:30303 | — | WholeSale Internet, Inc. | US | malicious |
1500 | RegAsm.exe | 18.211.215.84:80 | checkip.amazonaws.com | — | US | shared |
4020 | RegAsm.exe | 8.8.8.8:53 | — | Google Inc. | US | malicious |
4020 | RegAsm.exe | 96.47.239.239:30303 | justgo.linkpc.net | QuadraNet, Inc | US | malicious |
1500 | RegAsm.exe | 185.159.131.4:587 | mail.thetexeperts.com | IT Outsourcing LLC | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
checkip.amazonaws.com |
| malicious |
justgo.linkpc.net |
| malicious |
mail.thetexeperts.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1500 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
4020 | RegAsm.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 60B |
1500 | RegAsm.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
4020 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
4020 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
4020 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
4020 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
4020 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
4020 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
4020 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore.RAT |
64 ETPRO signatures available at the full report