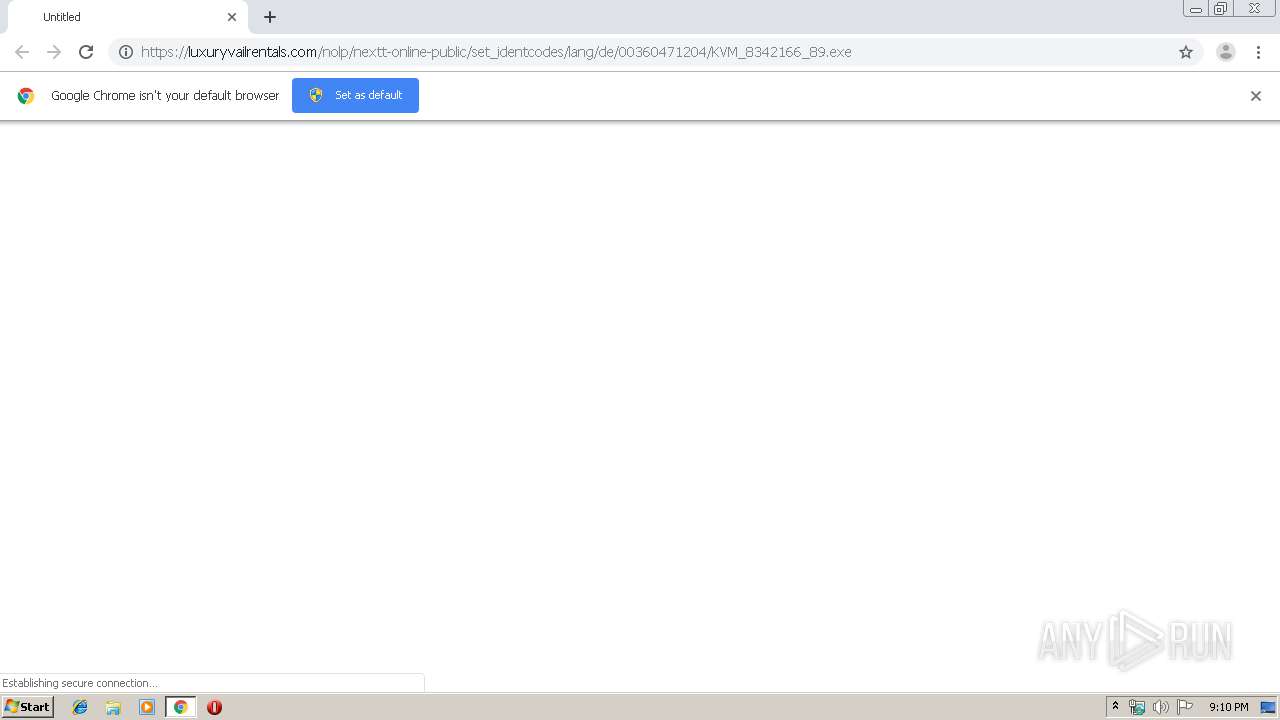
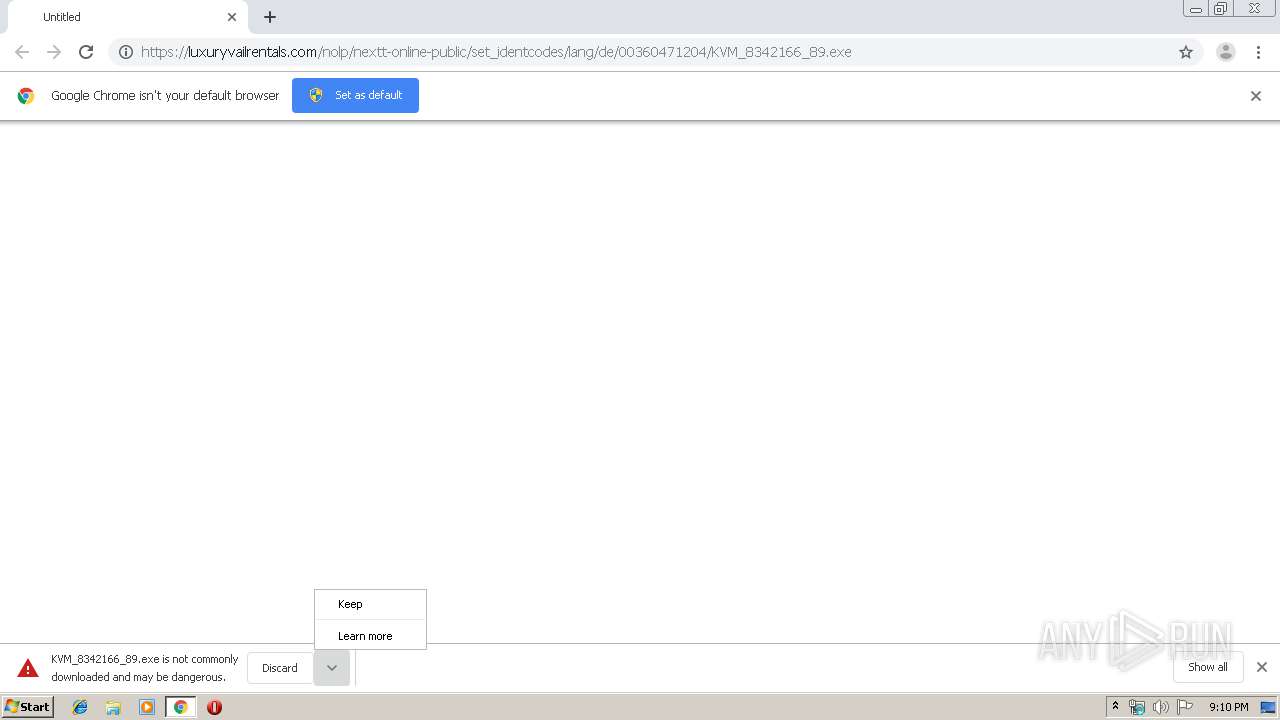
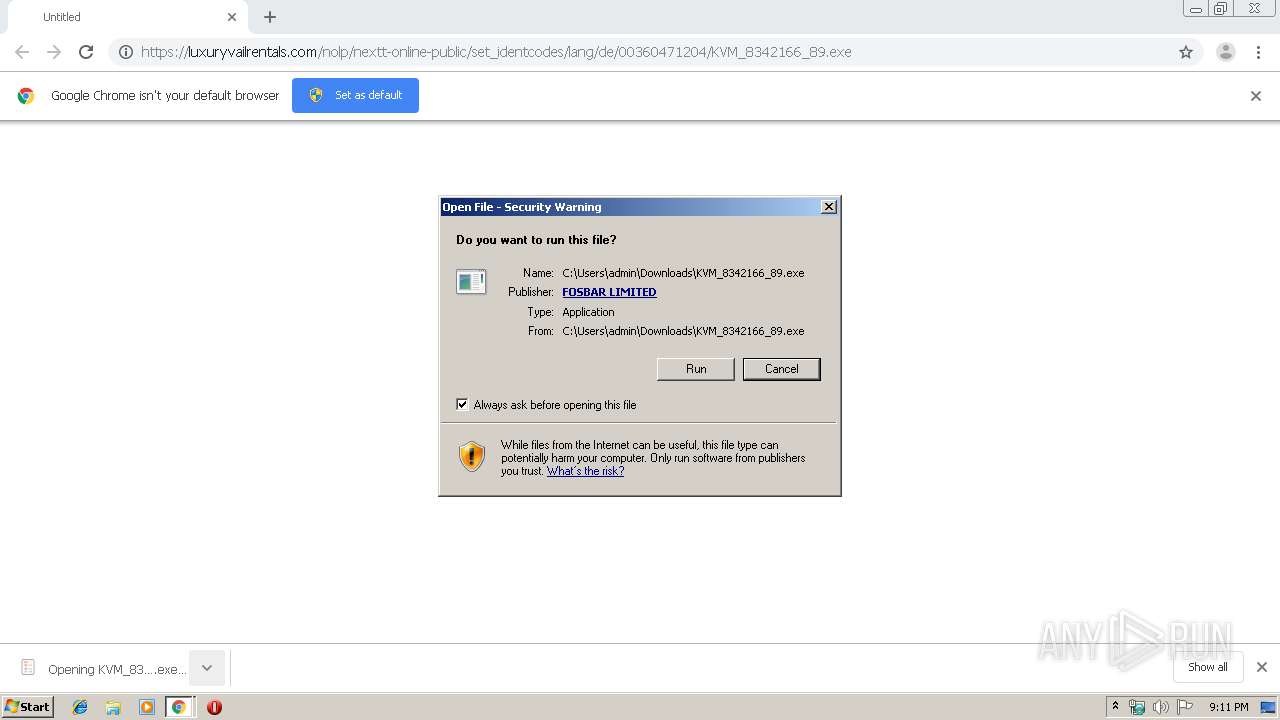
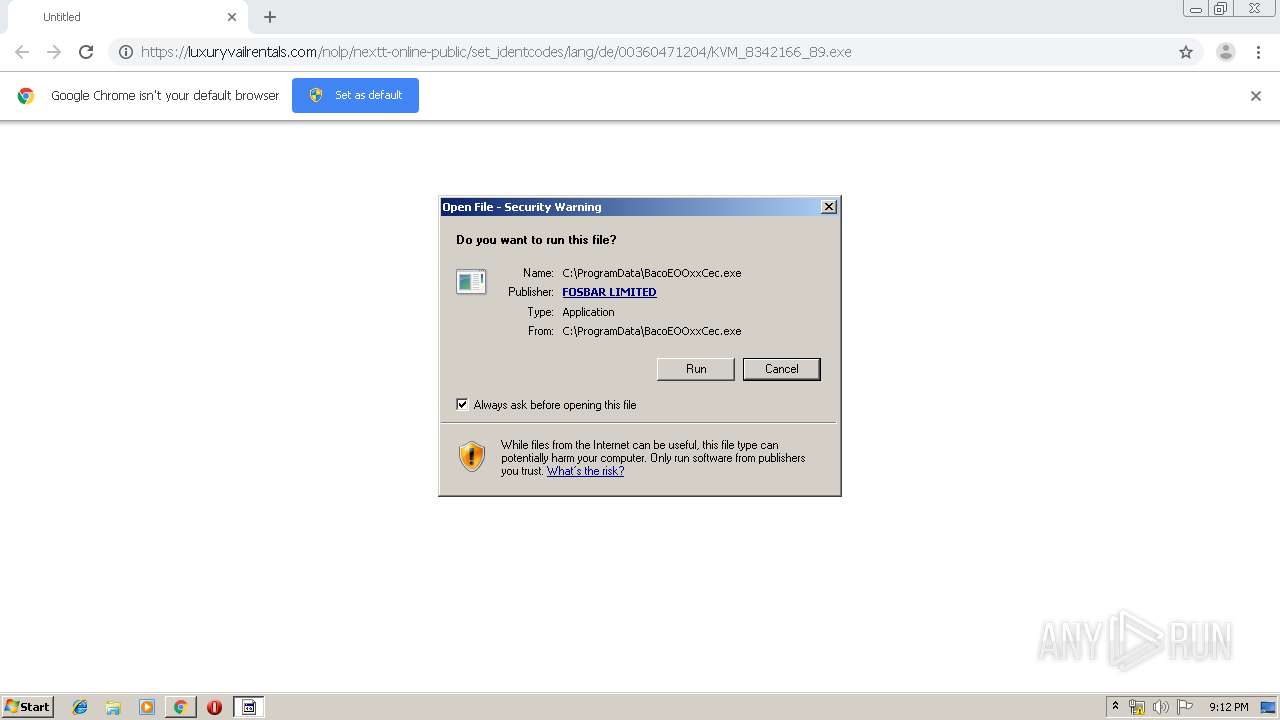
| URL: | https://luxuryvailrentals.com/nolp/nextt-online-public/set_identcodes/lang/de/00360471204/KVM_8342166_89.exe |
| Full analysis: | https://app.any.run/tasks/150bc9b9-27de-4396-be3c-c6a7d5bde25c |
| Verdict: | Malicious activity |
| Threats: | TrickBot is an advanced banking trojan that attackers can use to steal payment credentials from the victims. It can redirect the victim to a fake banking cabinet and retrieve credentials typed in on the webpage. |
| Analysis date: | July 17, 2019, 20:10:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 96B54294E9933708CD2D361D141CA283 |
| SHA1: | 934F91C94AF338323FB3C18738D2EE26DDE38150 |
| SHA256: | A4FA9DAC3C5A0F1F0526A3094D8F8E70D60A7CE5778DC17EF1D0DBC61EA1D3E1 |
| SSDEEP: | 3:N8Qd7STLd7mK09KnSABedIh+Me8oHHeLN:2Q5ScK090vwSAM1qc |
MALICIOUS
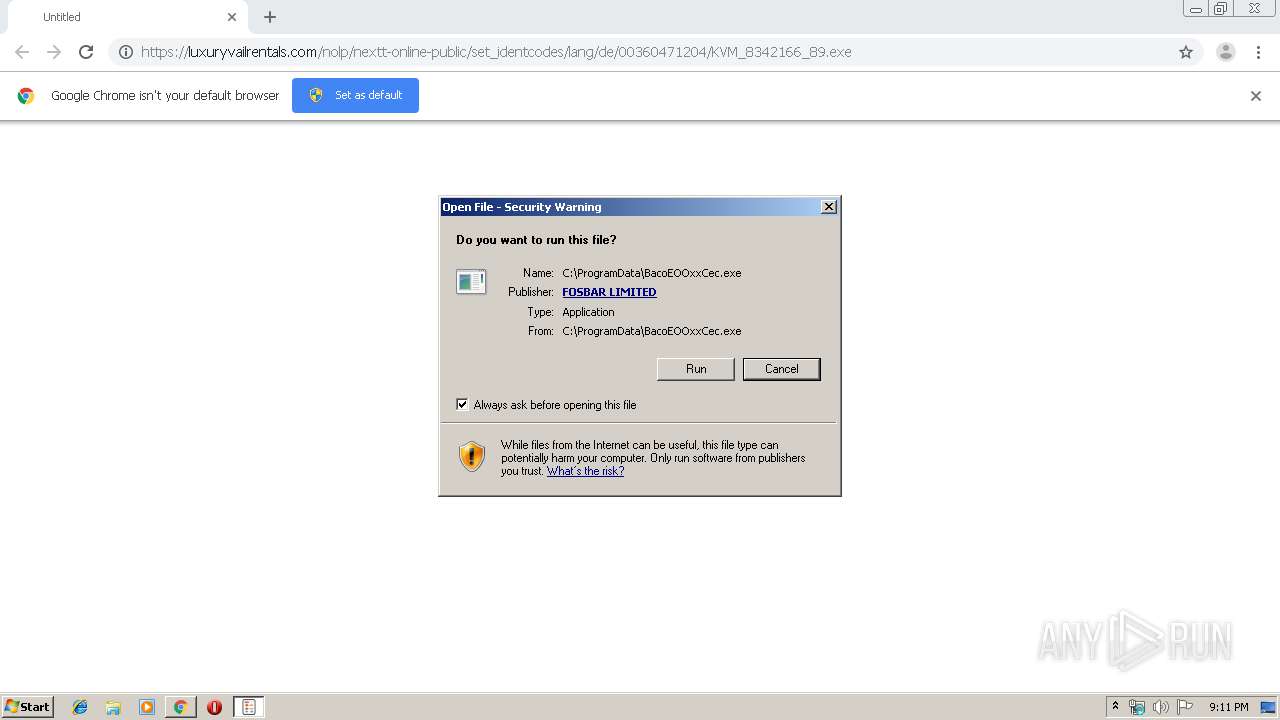
Application was dropped or rewritten from another process
- ВасоЕООххСес.exe (PID: 4020)
- ВасоЕООххСес.exe (PID: 2916)
- KVM_8342166_89.exe (PID: 2864)
- ВасоЕООххСес.exe (PID: 1580)
Disables Windows Defender
- ВасоЕООххСес.exe (PID: 4020)
- ВасоЕООххСес.exe (PID: 1580)
Executes PowerShell scripts
- cmd.exe (PID: 412)
- cmd.exe (PID: 576)
- cmd.exe (PID: 1944)
- cmd.exe (PID: 1860)
- cmd.exe (PID: 2660)
- cmd.exe (PID: 3728)
- cmd.exe (PID: 2064)
- cmd.exe (PID: 2532)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 2108)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 3280)
- cmd.exe (PID: 2820)
- cmd.exe (PID: 2580)
- cmd.exe (PID: 2416)
- cmd.exe (PID: 3892)
- cmd.exe (PID: 556)
- cmd.exe (PID: 1720)
- cmd.exe (PID: 692)
- cmd.exe (PID: 3088)
Stops/Deletes Windows Defender service via SC.exe
- cmd.exe (PID: 3880)
- cmd.exe (PID: 4040)
- cmd.exe (PID: 2940)
- cmd.exe (PID: 2292)
Known privilege escalation attack
- DllHost.exe (PID: 3904)
Loads the Task Scheduler COM API
- ВасоЕООххСес.exe (PID: 4020)
- ВасоЕООххСес.exe (PID: 1580)
TRICKBOT was detected
- ВасоЕООххСес.exe (PID: 1580)
SUSPICIOUS
Executable content was dropped or overwritten
- KVM_8342166_89.exe (PID: 2864)
- chrome.exe (PID: 3524)
- chrome.exe (PID: 2860)
- ВасоЕООххСес.exe (PID: 4020)
Creates files in the program directory
- KVM_8342166_89.exe (PID: 2864)
- ВасоЕООххСес.exe (PID: 1580)
Starts itself from another location
- KVM_8342166_89.exe (PID: 2864)
Executed via COM
- DllHost.exe (PID: 3904)
Starts CMD.EXE for commands execution
- ВасоЕООххСес.exe (PID: 4020)
- ВасоЕООххСес.exe (PID: 1580)
Creates files in the user directory
- powershell.exe (PID: 3068)
- powershell.exe (PID: 976)
- powershell.exe (PID: 3896)
- powershell.exe (PID: 3632)
- powershell.exe (PID: 2792)
- powershell.exe (PID: 3568)
- powershell.exe (PID: 4052)
- powershell.exe (PID: 2904)
- powershell.exe (PID: 3180)
- ВасоЕООххСес.exe (PID: 4020)
- powershell.exe (PID: 3824)
- ВасоЕООххСес.exe (PID: 1580)
Executed via Task Scheduler
- ВасоЕООххСес.exe (PID: 1580)
Removes files from Windows directory
- ВасоЕООххСес.exe (PID: 1580)
Creates files in the Windows directory
- ВасоЕООххСес.exe (PID: 1580)
INFO
Application launched itself
- chrome.exe (PID: 3524)
Reads Internet Cache Settings
- chrome.exe (PID: 3524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
125
Monitored processes
64
Malicious processes
23
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 412 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\cmd.exe | — | ВасоЕООххСес.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 556 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -DisableScriptScanning $true | C:\Windows\System32\cmd.exe | — | ВасоЕООххСес.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 576 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -DisableBlockAtFirstSeen $true | C:\Windows\System32\cmd.exe | — | ВасоЕООххСес.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 692 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -DisablePrivacyMode $true | C:\Windows\System32\cmd.exe | — | ВасоЕООххСес.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 976 | powershell Set-MpPreference -DisableBehaviorMonitoring $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1084 | sc delete WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1580 | C:\Users\admin\AppData\Roaming\NetLibs14\ВасоЕООххСес.exe | C:\Users\admin\AppData\Roaming\NetLibs14\ВасоЕООххСес.exe | taskeng.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1720 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -SevereThreatDefaultAction 6 | C:\Windows\System32\cmd.exe | — | ВасоЕООххСес.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1764 | powershell Set-MpPreference -DisableIntrusionPreventionSystem $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1860 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -DisableBehaviorMonitoring $true | C:\Windows\System32\cmd.exe | — | ВасоЕООххСес.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
3 721
Read events
3 050
Write events
668
Delete events
3
Modification events
| (PID) Process: | (3524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3524-13207867850527875 |
Value: 259 | |||
| (PID) Process: | (3524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3524) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3524) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
6
Suspicious files
32
Text files
72
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\caa16030-37df-4448-b67a-d7de1bd0ec02.tmp | — | |
MD5:— | SHA256:— | |||
| 3524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF10e977.TMP | text | |
MD5:— | SHA256:— | |||
| 3524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF10e987.TMP | text | |
MD5:— | SHA256:— | |||
| 3524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10e977.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
14
DNS requests
11
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2860 | chrome.exe | 172.217.16.142:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
2860 | chrome.exe | 172.217.21.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2860 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2860 | chrome.exe | 212.42.121.51:443 | luxuryvailrentals.com | ElCat Ltd. | KG | suspicious |
— | — | 216.58.207.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
2860 | chrome.exe | 172.217.23.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
— | — | 2.16.186.56:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
1580 | ВасоЕООххСес.exe | 125.99.253.34:449 | — | Hathway IP Over Cable Internet | IN | malicious |
— | — | 172.217.22.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2860 | chrome.exe | 216.58.210.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
luxuryvailrentals.com |
| suspicious |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1580 | ВасоЕООххСес.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
1 ETPRO signatures available at the full report