| File name: | a4eba8fea147f214a12411a89ba39884225eb8e3421aa73ebd51d502397d364c.bin |
| Full analysis: | https://app.any.run/tasks/f2c95784-6fdc-4578-93ce-80ccd3e0e417 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | June 21, 2025, 13:20:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
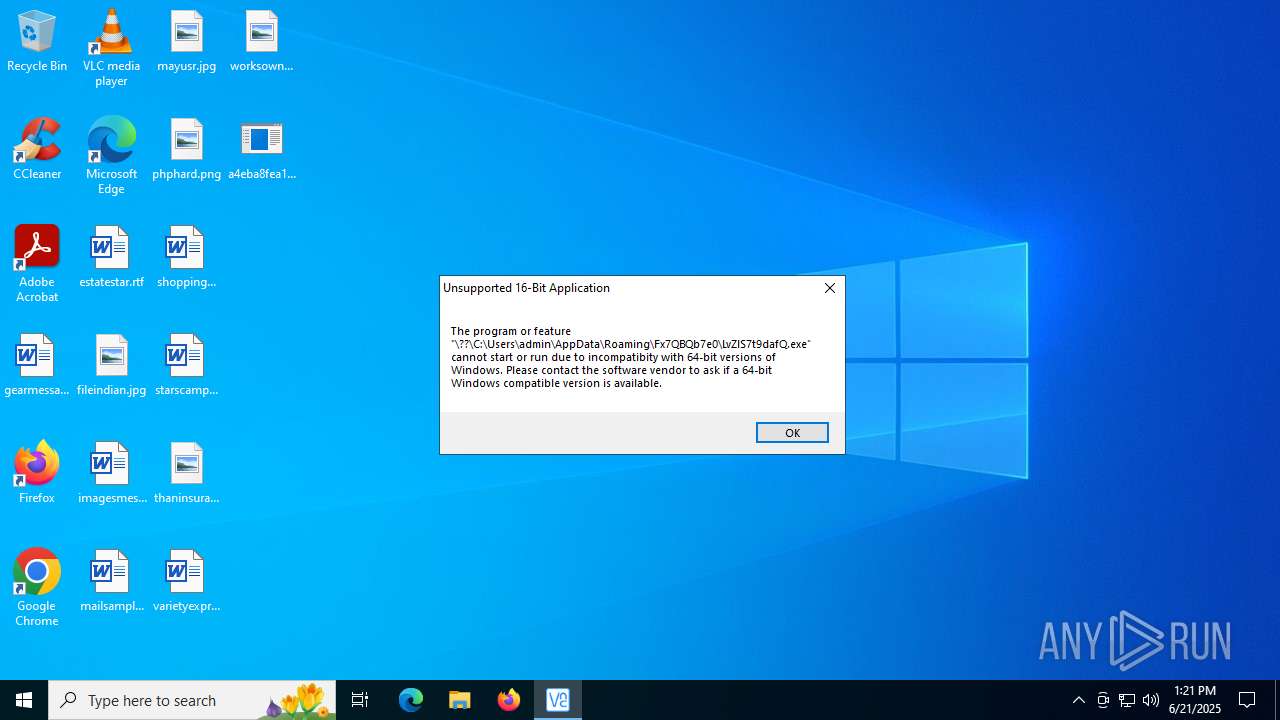
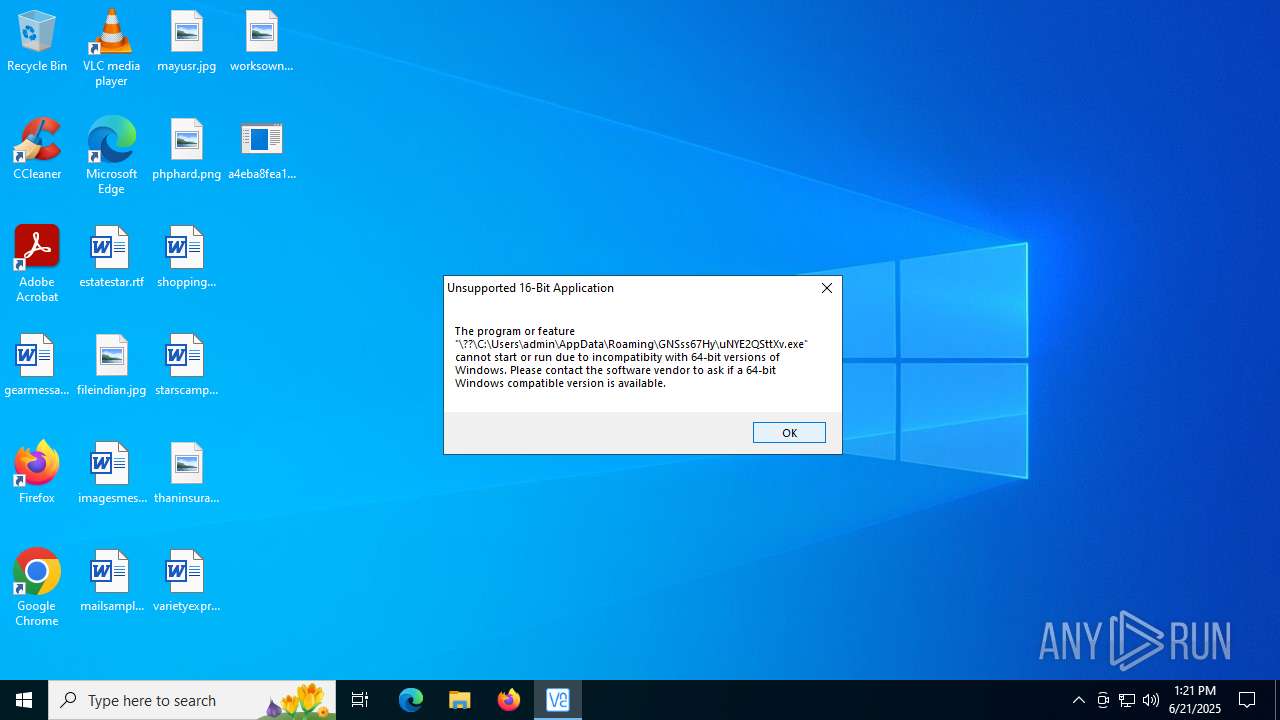
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 797D1730309CD0E651E70CA720E5BA13 |
| SHA1: | 74329EBC161F767E8BFA65D420A08635506411BA |
| SHA256: | A4EBA8FEA147F214A12411A89BA39884225EB8E3421AA73EBD51D502397D364C |
| SSDEEP: | 98304:FiRrKhVspLN5n0rT3HeOhRsKVsrDe77BoGpzhoYQwY+csyQh6OjVEq7jyGnwD9oa:lLEBAfM |
MALICIOUS
Executing a file with an untrusted certificate
- a4eba8fea147f214a12411a89ba39884225eb8e3421aa73ebd51d502397d364c.bin.exe (PID: 1984)
- svchost015.exe (PID: 7164)
- MRPwLrUo7r.exe (PID: 7092)
- RRubpPl7UYSo.exe (PID: 2160)
- RRubpPl7UYSo.exe (PID: 1028)
GCLEANER has been detected (SURICATA)
- svchost015.exe (PID: 7164)
LUMMA mutex has been found
- hRdpta7p5O.exe (PID: 3196)
- Oc.com (PID: 2628)
Registers / Runs the DLL via REGSVR32.EXE
- RRubpPl7UYSo.tmp (PID: 6776)
AutoIt loader has been detected (YARA)
- Oc.com (PID: 2628)
LUMMA has been detected (YARA)
- hRdpta7p5O.exe (PID: 3196)
Steals credentials from Web Browsers
- hRdpta7p5O.exe (PID: 3196)
- Oc.com (PID: 2628)
Actions looks like stealing of personal data
- hRdpta7p5O.exe (PID: 3196)
- Oc.com (PID: 2628)
GENERIC has been found (auto)
- svchost015.exe (PID: 7164)
AMADEY mutex has been found
- 8BUYX1GAJ6H3DO191.exe (PID: 2028)
- ramez.exe (PID: 6748)
- DO6Nk9ro.exe (PID: 7576)
- DO6Nk9ro.exe (PID: 7964)
- RoamingWR17ZGG356RHPDQ1SD6YNWA8XCLXJT4H.EXE (PID: 7848)
AMADEY has been detected (SURICATA)
- ramez.exe (PID: 6748)
Connects to the CnC server
- ramez.exe (PID: 6748)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 4520)
- cmd.exe (PID: 7256)
- cmd.exe (PID: 728)
- cmd.exe (PID: 7280)
Changes the autorun value in the registry
- Python.exe (PID: 8064)
- ramez.exe (PID: 6748)
QUASAR mutex has been found
- AddInProcess32.exe (PID: 4012)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 7376)
- NSudoLG.exe (PID: 3936)
- cmd.exe (PID: 7912)
- NSudoLG.exe (PID: 5692)
Changes Windows Defender settings
- NSudoLG.exe (PID: 3936)
- NSudoLG.exe (PID: 5692)
Run PowerShell with an invisible window
- powershell.exe (PID: 8124)
- powershell.exe (PID: 1268)
- powershell.exe (PID: 8012)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 8124)
Changes powershell execution policy
- wscript.exe (PID: 4708)
SUSPICIOUS
Executable content was dropped or overwritten
- a4eba8fea147f214a12411a89ba39884225eb8e3421aa73ebd51d502397d364c.bin.exe (PID: 1984)
- QwQsIra3vu.tmp (PID: 6652)
- svchost015.exe (PID: 7164)
- QwQsIra3vu.exe (PID: 6948)
- openfilesviewer.exe (PID: 4688)
- RRubpPl7UYSo.exe (PID: 2160)
- RRubpPl7UYSo.tmp (PID: 5552)
- RRubpPl7UYSo.exe (PID: 1028)
- RRubpPl7UYSo.tmp (PID: 6776)
- hRdpta7p5O.exe (PID: 3196)
- 8BUYX1GAJ6H3DO191.exe (PID: 2028)
- ramez.exe (PID: 6748)
- lab.exe (PID: 7188)
- lab.exe (PID: 6780)
- index.exe (PID: 5080)
- hDdBQfyw.exe (PID: 7980)
- u0cyrNRq.exe (PID: 3716)
- Python.exe (PID: 8064)
- hDdBQfyw.exe (PID: 1204)
- 7z.exe (PID: 6172)
- powershell.exe (PID: 8124)
- Unlocker.exe (PID: 7508)
- Unlocker.exe (PID: 5368)
There is functionality for taking screenshot (YARA)
- a4eba8fea147f214a12411a89ba39884225eb8e3421aa73ebd51d502397d364c.bin.exe (PID: 1984)
- svchost015.exe (PID: 7164)
- MRPwLrUo7r.exe (PID: 7092)
- Oc.com (PID: 2628)
Reads security settings of Internet Explorer
- svchost015.exe (PID: 7164)
- MRPwLrUo7r.exe (PID: 7092)
- openfilesviewer.exe (PID: 4688)
- RRubpPl7UYSo.tmp (PID: 5552)
- 8BUYX1GAJ6H3DO191.exe (PID: 2028)
- ramez.exe (PID: 6748)
- index.exe (PID: 5080)
- u0cyrNRq.exe (PID: 3716)
- nircmd.exe (PID: 8032)
- index.exe (PID: 2976)
- u0cyrNRq.exe (PID: 7224)
- nircmd.exe (PID: 5884)
- Unlocker.exe (PID: 7508)
- Unlocker.exe (PID: 1688)
- Unlocker.exe (PID: 5368)
- Unlocker.exe (PID: 6780)
- Unlocker.exe (PID: 7984)
- Unlocker.exe (PID: 5116)
Connects to the server without a host name
- svchost015.exe (PID: 7164)
- hRdpta7p5O.exe (PID: 3196)
- ramez.exe (PID: 6748)
- powershell.exe (PID: 8124)
Potential Corporate Privacy Violation
- svchost015.exe (PID: 7164)
- hRdpta7p5O.exe (PID: 3196)
- ramez.exe (PID: 6748)
- powershell.exe (PID: 8124)
Reads the Windows owner or organization settings
- QwQsIra3vu.tmp (PID: 6652)
- RRubpPl7UYSo.tmp (PID: 5552)
- RRubpPl7UYSo.tmp (PID: 6776)
The process drops C-runtime libraries
- QwQsIra3vu.tmp (PID: 6652)
- lab.exe (PID: 6780)
- lab.exe (PID: 7188)
- Python.exe (PID: 8064)
Process drops legitimate windows executable
- QwQsIra3vu.tmp (PID: 6652)
- lab.exe (PID: 7188)
- lab.exe (PID: 6780)
- Python.exe (PID: 8064)
- ramez.exe (PID: 6748)
Starts CMD.EXE for commands execution
- MRPwLrUo7r.exe (PID: 7092)
- lab.exe (PID: 6780)
- Na6f8Rwc.exe (PID: 2188)
- u0cyrNRq.exe (PID: 3716)
- nircmd.exe (PID: 8032)
- NSudoLG.exe (PID: 7276)
- cmd.exe (PID: 7376)
- Na6f8Rwc.exe (PID: 6304)
- 9b98b29933.exe (PID: 3844)
- u0cyrNRq.exe (PID: 7224)
- NSudoLG.exe (PID: 1872)
- nircmd.exe (PID: 5884)
- cmd.exe (PID: 7912)
- Unlocker.exe (PID: 1688)
- Unlocker.exe (PID: 7508)
- 4TQHprw.exe (PID: 7244)
- Unlocker.exe (PID: 5368)
- 9b98b29933.exe (PID: 7836)
- Unlocker.exe (PID: 6780)
- Unlocker.exe (PID: 7984)
- Unlocker.exe (PID: 5116)
Executing commands from a ".bat" file
- MRPwLrUo7r.exe (PID: 7092)
- lab.exe (PID: 6780)
- u0cyrNRq.exe (PID: 3716)
- nircmd.exe (PID: 8032)
- NSudoLG.exe (PID: 7276)
- u0cyrNRq.exe (PID: 7224)
- nircmd.exe (PID: 5884)
- NSudoLG.exe (PID: 1872)
Get information on the list of running processes
- cmd.exe (PID: 4088)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 5988)
- cmd.exe (PID: 7912)
- cmd.exe (PID: 1132)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4088)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 7912)
Starts POWERSHELL.EXE for commands execution
- openfilesviewer.exe (PID: 4688)
- regsvr32.exe (PID: 6796)
- NSudoLG.exe (PID: 3936)
- mshta.exe (PID: 7644)
- NSudoLG.exe (PID: 5692)
- wscript.exe (PID: 4708)
- mshta.exe (PID: 6548)
Starts application with an unusual extension
- cmd.exe (PID: 4088)
- cmd.exe (PID: 6612)
- cmd.exe (PID: 1800)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 7040)
- cmd.exe (PID: 7912)
The executable file from the user directory is run by the CMD process
- Oc.com (PID: 2628)
- Python.exe (PID: 8064)
- nircmd.exe (PID: 3520)
- nircmd.exe (PID: 8032)
- nircmd.exe (PID: 8168)
- NSudoLG.exe (PID: 7276)
- nircmd.exe (PID: 1268)
- NSudoLG.exe (PID: 3936)
- nircmd.exe (PID: 424)
- nircmd.exe (PID: 5884)
- nircmd.exe (PID: 6548)
- NSudoLG.exe (PID: 1872)
- nircmd.exe (PID: 8088)
- NSudoLG.exe (PID: 5692)
- 7z.exe (PID: 6172)
- Unlocker.exe (PID: 1688)
- Unlocker.exe (PID: 7508)
- Unlocker.exe (PID: 5368)
- Unlocker.exe (PID: 6780)
- 7z.exe (PID: 7084)
- Unlocker.exe (PID: 7984)
- Unlocker.exe (PID: 5116)
Reads the BIOS version
- hRdpta7p5O.exe (PID: 3196)
- 8BUYX1GAJ6H3DO191.exe (PID: 2028)
- ramez.exe (PID: 6748)
Starts the AutoIt3 executable file
- cmd.exe (PID: 4088)
The process bypasses the loading of PowerShell profile settings
- regsvr32.exe (PID: 6796)
The process hide an interactive prompt from the user
- regsvr32.exe (PID: 6796)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Oc.com (PID: 2628)
Connects to SMTP port
- regsvr32.exe (PID: 6796)
Searches for installed software
- hRdpta7p5O.exe (PID: 3196)
- Oc.com (PID: 2628)
Process requests binary or script from the Internet
- hRdpta7p5O.exe (PID: 3196)
- ramez.exe (PID: 6748)
- powershell.exe (PID: 8124)
Detected use of alternative data streams (AltDS)
- regsvr32.exe (PID: 6796)
Starts itself from another location
- 8BUYX1GAJ6H3DO191.exe (PID: 2028)
Contacting a server suspected of hosting an CnC
- ramez.exe (PID: 6748)
Application launched itself
- lab.exe (PID: 7188)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 7912)
Process drops python dynamic module
- lab.exe (PID: 7188)
Drops 7-zip archiver for unpacking
- index.exe (PID: 5080)
- u0cyrNRq.exe (PID: 3716)
The process creates files with name similar to system file names
- u0cyrNRq.exe (PID: 3716)
Reads the date of Windows installation
- nircmd.exe (PID: 8032)
- nircmd.exe (PID: 5884)
- Unlocker.exe (PID: 1688)
- Unlocker.exe (PID: 7508)
- Unlocker.exe (PID: 5368)
- Unlocker.exe (PID: 6780)
- Unlocker.exe (PID: 7984)
- Unlocker.exe (PID: 5116)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1800)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 7040)
- cmd.exe (PID: 7912)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 6356)
- powershell.exe (PID: 7388)
Script adds exclusion path to Windows Defender
- NSudoLG.exe (PID: 3936)
- NSudoLG.exe (PID: 5692)
Checks for external IP
- svchost.exe (PID: 2200)
- AddInProcess32.exe (PID: 4012)
Connects to unusual port
- AddInProcess32.exe (PID: 4012)
The process executes via Task Scheduler
- regsvr32.exe (PID: 7796)
Probably download files using WebClient
- mshta.exe (PID: 7644)
- mshta.exe (PID: 6548)
Starts process via Powershell
- powershell.exe (PID: 8124)
- powershell.exe (PID: 8012)
Manipulates environment variables
- powershell.exe (PID: 8124)
- powershell.exe (PID: 8012)
Found IP address in command line
- powershell.exe (PID: 8124)
- powershell.exe (PID: 8012)
Starts SC.EXE for service management
- cmd.exe (PID: 7740)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 5716)
- cmd.exe (PID: 1840)
- cmd.exe (PID: 8164)
- cmd.exe (PID: 8084)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 3688)
- cmd.exe (PID: 7436)
Windows service management via SC.EXE
- sc.exe (PID: 7880)
- sc.exe (PID: 3876)
- sc.exe (PID: 4752)
- sc.exe (PID: 516)
- sc.exe (PID: 7256)
- sc.exe (PID: 7240)
- sc.exe (PID: 7420)
- sc.exe (PID: 304)
- sc.exe (PID: 6392)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1872)
- cmd.exe (PID: 8164)
Drops a system driver (possible attempt to evade defenses)
- Unlocker.exe (PID: 7508)
- Unlocker.exe (PID: 5368)
Creates or modifies Windows services
- Unlocker.exe (PID: 7508)
- Unlocker.exe (PID: 7984)
- Unlocker.exe (PID: 5116)
Stops a currently running service
- sc.exe (PID: 236)
- sc.exe (PID: 7176)
- sc.exe (PID: 3936)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7376)
Starts a Microsoft application from unusual location
- 4TQHprw.exe (PID: 7244)
The process executes VB scripts
- cmd.exe (PID: 7928)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 4708)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 4708)
Runs shell command (SCRIPT)
- wscript.exe (PID: 4708)
INFO
The sample compiled with chinese language support
- a4eba8fea147f214a12411a89ba39884225eb8e3421aa73ebd51d502397d364c.bin.exe (PID: 1984)
Checks supported languages
- a4eba8fea147f214a12411a89ba39884225eb8e3421aa73ebd51d502397d364c.bin.exe (PID: 1984)
- svchost015.exe (PID: 7164)
- QwQsIra3vu.exe (PID: 6948)
- QwQsIra3vu.tmp (PID: 6652)
- openfilesviewer.exe (PID: 4688)
- MRPwLrUo7r.exe (PID: 7092)
- OpenFilesViewer.exe (PID: 4864)
- extrac32.exe (PID: 2528)
- Oc.com (PID: 2628)
- hRdpta7p5O.exe (PID: 3196)
- RRubpPl7UYSo.tmp (PID: 5552)
- RRubpPl7UYSo.exe (PID: 2160)
- RRubpPl7UYSo.exe (PID: 1028)
- RRubpPl7UYSo.tmp (PID: 6776)
- 8BUYX1GAJ6H3DO191.exe (PID: 2028)
- ramez.exe (PID: 6748)
- lab.exe (PID: 7188)
- lab.exe (PID: 6780)
- Python.exe (PID: 8064)
- index.exe (PID: 5080)
- Na6f8Rwc.exe (PID: 2188)
- hDdBQfyw.exe (PID: 7980)
- DO6Nk9ro.exe (PID: 7576)
- u0cyrNRq.exe (PID: 3716)
- nircmd.exe (PID: 3520)
- chcp.com (PID: 7940)
- nircmd.exe (PID: 8032)
- chcp.com (PID: 2216)
- NSudoLG.exe (PID: 7276)
- nircmd.exe (PID: 8168)
- AddInProcess32.exe (PID: 4012)
- nircmd.exe (PID: 1268)
- chcp.com (PID: 6940)
- mode.com (PID: 5012)
- NSudoLG.exe (PID: 3936)
- index.exe (PID: 2976)
- Na6f8Rwc.exe (PID: 6304)
- hDdBQfyw.exe (PID: 1204)
- DO6Nk9ro.exe (PID: 7964)
- u0cyrNRq.exe (PID: 7224)
- 9b98b29933.exe (PID: 3844)
- Python.exe (PID: 7612)
- chcp.com (PID: 7324)
- nircmd.exe (PID: 424)
- nircmd.exe (PID: 5884)
- nircmd.exe (PID: 6548)
- NSudoLG.exe (PID: 1872)
- nircmd.exe (PID: 8088)
- chcp.com (PID: 6336)
- mode.com (PID: 3628)
- NSudoLG.exe (PID: 5692)
- chcp.com (PID: 7560)
- 7z.exe (PID: 6172)
- Unlocker.exe (PID: 1688)
- RoamingWR17ZGG356RHPDQ1SD6YNWA8XCLXJT4H.EXE (PID: 7848)
- Unlocker.exe (PID: 7508)
- Unlocker.exe (PID: 5368)
- 4TQHprw.exe (PID: 7244)
- 9b98b29933.exe (PID: 7836)
- 7z.exe (PID: 7084)
- Unlocker.exe (PID: 6780)
- Unlocker.exe (PID: 7984)
- IObitUnlocker.exe (PID: 4560)
- Unlocker.exe (PID: 5116)
Create files in a temporary directory
- a4eba8fea147f214a12411a89ba39884225eb8e3421aa73ebd51d502397d364c.bin.exe (PID: 1984)
- QwQsIra3vu.exe (PID: 6948)
- QwQsIra3vu.tmp (PID: 6652)
- MRPwLrUo7r.exe (PID: 7092)
- extrac32.exe (PID: 2528)
- RRubpPl7UYSo.exe (PID: 2160)
- RRubpPl7UYSo.tmp (PID: 5552)
- RRubpPl7UYSo.tmp (PID: 6776)
- RRubpPl7UYSo.exe (PID: 1028)
- svchost015.exe (PID: 7164)
- hRdpta7p5O.exe (PID: 3196)
- 8BUYX1GAJ6H3DO191.exe (PID: 2028)
- ramez.exe (PID: 6748)
- lab.exe (PID: 7188)
- lab.exe (PID: 6780)
- u0cyrNRq.exe (PID: 3716)
- u0cyrNRq.exe (PID: 7224)
- 7z.exe (PID: 6172)
- 4TQHprw.exe (PID: 7244)
Compiled with Borland Delphi (YARA)
- a4eba8fea147f214a12411a89ba39884225eb8e3421aa73ebd51d502397d364c.bin.exe (PID: 1984)
- QwQsIra3vu.tmp (PID: 6652)
The sample compiled with english language support
- a4eba8fea147f214a12411a89ba39884225eb8e3421aa73ebd51d502397d364c.bin.exe (PID: 1984)
- QwQsIra3vu.tmp (PID: 6652)
- openfilesviewer.exe (PID: 4688)
- lab.exe (PID: 7188)
- lab.exe (PID: 6780)
- index.exe (PID: 5080)
- u0cyrNRq.exe (PID: 3716)
- Python.exe (PID: 8064)
- ramez.exe (PID: 6748)
- Unlocker.exe (PID: 7508)
- Unlocker.exe (PID: 5368)
Reads the computer name
- svchost015.exe (PID: 7164)
- QwQsIra3vu.tmp (PID: 6652)
- openfilesviewer.exe (PID: 4688)
- MRPwLrUo7r.exe (PID: 7092)
- OpenFilesViewer.exe (PID: 4864)
- extrac32.exe (PID: 2528)
- Oc.com (PID: 2628)
- hRdpta7p5O.exe (PID: 3196)
- RRubpPl7UYSo.tmp (PID: 5552)
- RRubpPl7UYSo.tmp (PID: 6776)
- 8BUYX1GAJ6H3DO191.exe (PID: 2028)
- ramez.exe (PID: 6748)
- index.exe (PID: 5080)
- Na6f8Rwc.exe (PID: 2188)
- hDdBQfyw.exe (PID: 7980)
- u0cyrNRq.exe (PID: 3716)
- nircmd.exe (PID: 8032)
- NSudoLG.exe (PID: 7276)
- AddInProcess32.exe (PID: 4012)
- Python.exe (PID: 8064)
- NSudoLG.exe (PID: 3936)
- index.exe (PID: 2976)
- hDdBQfyw.exe (PID: 1204)
- u0cyrNRq.exe (PID: 7224)
- 9b98b29933.exe (PID: 3844)
- Na6f8Rwc.exe (PID: 6304)
- nircmd.exe (PID: 5884)
- NSudoLG.exe (PID: 1872)
- NSudoLG.exe (PID: 5692)
- 7z.exe (PID: 6172)
- Unlocker.exe (PID: 1688)
- Unlocker.exe (PID: 7508)
- 4TQHprw.exe (PID: 7244)
- Unlocker.exe (PID: 5368)
- Unlocker.exe (PID: 6780)
- 9b98b29933.exe (PID: 7836)
- 7z.exe (PID: 7084)
- Unlocker.exe (PID: 7984)
- IObitUnlocker.exe (PID: 4560)
- Unlocker.exe (PID: 5116)
Checks proxy server information
- svchost015.exe (PID: 7164)
- slui.exe (PID: 2368)
- ramez.exe (PID: 6748)
- AddInProcess32.exe (PID: 4012)
- powershell.exe (PID: 8124)
- powershell.exe (PID: 8012)
Reads the software policy settings
- svchost015.exe (PID: 7164)
- hRdpta7p5O.exe (PID: 3196)
- Oc.com (PID: 2628)
- slui.exe (PID: 2368)
- ramez.exe (PID: 6748)
Reads the machine GUID from the registry
- svchost015.exe (PID: 7164)
- hRdpta7p5O.exe (PID: 3196)
- Oc.com (PID: 2628)
- ramez.exe (PID: 6748)
- lab.exe (PID: 6780)
- AddInProcess32.exe (PID: 4012)
- Unlocker.exe (PID: 1688)
- Unlocker.exe (PID: 7508)
- Unlocker.exe (PID: 5368)
- Unlocker.exe (PID: 6780)
- Unlocker.exe (PID: 7984)
- Unlocker.exe (PID: 5116)
Creates files or folders in the user directory
- svchost015.exe (PID: 7164)
- QwQsIra3vu.tmp (PID: 6652)
- RRubpPl7UYSo.tmp (PID: 6776)
- ramez.exe (PID: 6748)
Creates a software uninstall entry
- QwQsIra3vu.tmp (PID: 6652)
Creates files in the program directory
- openfilesviewer.exe (PID: 4688)
Changes the registry key values via Powershell
- openfilesviewer.exe (PID: 4688)
Manual execution by a user
- OpenFilesViewer.exe (PID: 4864)
- index.exe (PID: 2976)
- cmd.exe (PID: 1332)
- 9b98b29933.exe (PID: 7836)
Process checks computer location settings
- MRPwLrUo7r.exe (PID: 7092)
- openfilesviewer.exe (PID: 4688)
- svchost015.exe (PID: 7164)
- RRubpPl7UYSo.tmp (PID: 5552)
- 8BUYX1GAJ6H3DO191.exe (PID: 2028)
- ramez.exe (PID: 6748)
- index.exe (PID: 5080)
- u0cyrNRq.exe (PID: 3716)
- nircmd.exe (PID: 8032)
- index.exe (PID: 2976)
- u0cyrNRq.exe (PID: 7224)
- nircmd.exe (PID: 5884)
Reads mouse settings
- Oc.com (PID: 2628)
- Na6f8Rwc.exe (PID: 2188)
- Na6f8Rwc.exe (PID: 6304)
- 9b98b29933.exe (PID: 3844)
- 9b98b29933.exe (PID: 7836)
Detects InnoSetup installer (YARA)
- QwQsIra3vu.exe (PID: 6948)
- QwQsIra3vu.tmp (PID: 6652)
Application launched itself
- chrome.exe (PID: 3608)
- chrome.exe (PID: 4324)
- chrome.exe (PID: 3608)
- chrome.exe (PID: 7636)
- chrome.exe (PID: 5620)
- msedge.exe (PID: 7320)
- msedge.exe (PID: 7880)
- chrome.exe (PID: 7632)
- msedge.exe (PID: 7220)
- msedge.exe (PID: 7936)
- msedge.exe (PID: 3556)
- msedge.exe (PID: 3388)
- chrome.exe (PID: 1352)
- chrome.exe (PID: 6364)
- msedge.exe (PID: 4048)
- msedge.exe (PID: 5772)
- msedge.exe (PID: 3880)
- msedge.exe (PID: 1488)
- msedge.exe (PID: 768)
- msedge.exe (PID: 5348)
- msedge.exe (PID: 7140)
- msedge.exe (PID: 4816)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5552)
- powershell.exe (PID: 7564)
- powershell.exe (PID: 6356)
- powershell.exe (PID: 7388)
Themida protector has been detected
- hRdpta7p5O.exe (PID: 3196)
Python executable
- Python.exe (PID: 8064)
- Python.exe (PID: 7612)
NirSoft software is detected
- nircmd.exe (PID: 3520)
- nircmd.exe (PID: 8032)
- nircmd.exe (PID: 8168)
- nircmd.exe (PID: 1268)
- nircmd.exe (PID: 5884)
- nircmd.exe (PID: 424)
- nircmd.exe (PID: 6548)
- nircmd.exe (PID: 8088)
Changes the display of characters in the console
- cmd.exe (PID: 6612)
- cmd.exe (PID: 1800)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 7040)
- cmd.exe (PID: 7912)
Starts MODE.COM to configure console settings
- mode.com (PID: 5012)
- mode.com (PID: 3628)
Checks operating system version
- cmd.exe (PID: 7376)
- cmd.exe (PID: 7912)
Launching a file from a Registry key
- Python.exe (PID: 8064)
- ramez.exe (PID: 6748)
Disables trace logs
- AddInProcess32.exe (PID: 4012)
- powershell.exe (PID: 8124)
- powershell.exe (PID: 8012)
Reads Internet Explorer settings
- mshta.exe (PID: 7644)
- mshta.exe (PID: 6548)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6356)
- powershell.exe (PID: 7388)
The executable file from the user directory is run by the Powershell process
- RoamingWR17ZGG356RHPDQ1SD6YNWA8XCLXJT4H.EXE (PID: 7848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(3196) hRdpta7p5O.exe
C2 (9)ropyi.xyz/zadf
skjgx.xyz/riuw
gewgb.xyz/axgh
baviip.xyz/twiw
equidn.xyz/xapq
spjeo.xyz/axka
firddy.xyz/yhbc
shaeb.xyz/ikxz
trqqe.xyz/xudu
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 494080 |
| InitializedDataSize: | 2997248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x79814 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.7.0.1220 |
| ProductVersionNumber: | 3.7.0.1220 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | Fl as hGet3 |
| CompanyName: | Tren d Media Corporation Limited |
| FileDescription: | FlashGet3 |
| FileVersion: | 3, 7, 0, 1220 |
Total processes
519
Monitored processes
376
Malicious processes
43
Suspicious processes
14
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | sc stop IObitUnlocker | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 304 | sc query IObitUnlocker | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | nircmd win min process "cmd.exe" | C:\Users\admin\AppData\Local\Temp\Work\nircmd.exe | — | cmd.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: NirCmd Exit code: 0 Version: 2.87 Modules
| |||||||||||||||
| 432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffc4445f208,0x7ffc4445f214,0x7ffc4445f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 516 | reg query HKLM\System\CurrentControlset\Services\WdFilter | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | sc query IObitUnlocker | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | C:\WINDOWS\system32\cmd.exe /c schtasks /create /tn "zAqZESRp5" /tr "C:\Temper\Na6f8Rwc.exe" /sc minute /mo 10 /ru "admin" /f | C:\Windows\SysWOW64\cmd.exe | — | Na6f8Rwc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | reg query HKLM\System\CurrentControlset\Services\WdFilter | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 756 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2212,i,7883925187200030092,14005387043670255066,262144 --variations-seed-version --mojo-platform-channel-handle=2600 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 768 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
112 023
Read events
111 836
Write events
183
Delete events
4
Modification events
| (PID) Process: | (7164) svchost015.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7164) svchost015.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7164) svchost015.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6652) QwQsIra3vu.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Open Files Viewer_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.1 (a) | |||
| (PID) Process: | (6652) QwQsIra3vu.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Open Files Viewer_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Users\admin\AppData\Local\Open Files Viewer 1.16.0.471 | |||
| (PID) Process: | (6652) QwQsIra3vu.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Open Files Viewer_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Open Files Viewer 1.16.0.471\ | |||
| (PID) Process: | (6652) QwQsIra3vu.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Open Files Viewer_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (6652) QwQsIra3vu.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Open Files Viewer_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (6652) QwQsIra3vu.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Open Files Viewer_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: English | |||
| (PID) Process: | (6652) QwQsIra3vu.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Open Files Viewer_is1 |
| Operation: | write | Name: | DisplayName |
Value: Open Files Viewer 1.16.0.471 | |||
Executable files
122
Suspicious files
197
Text files
397
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1984 | a4eba8fea147f214a12411a89ba39884225eb8e3421aa73ebd51d502397d364c.bin.exe | C:\Users\admin\AppData\Local\Temp\svchost015.exe | executable | |
MD5:CEEAE1523C3864B719E820B75BF728AA | SHA256:4E04E2FB20A9C6846B5D693EA67098214F77737F4F1F3DF5F0C78594650E7F71 | |||
| 7164 | svchost015.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\success[1].htm | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 7164 | svchost015.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\info[1].htm | text | |
MD5:FE9B08252F126DDFCB87FB82F9CC7677 | SHA256:E63E7EBE4C2DB7E61FFC71AF0675E870BCDE0A9D8916E5B3BE0CB252478030BF | |||
| 6652 | QwQsIra3vu.tmp | C:\Users\admin\AppData\Local\Open Files Viewer 1.16.0.471\is-OJF4A.tmp | executable | |
MD5:EAE56B896A718C3BC87A4253832A5650 | SHA256:EE1D7D8F396D627FEE7DCF2655FB5ACFE5A1EE2A5DEEDA764EF311E75B94CEA1 | |||
| 7164 | svchost015.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\ONE[1].file | executable | |
MD5:49642CEE0AD99E4882A6F45C478C55B7 | SHA256:CB7DEE0F26CC30B13E5775877D570FCD4CA2E4F1A89614CC12031D6070B78473 | |||
| 7164 | svchost015.exe | C:\Users\admin\AppData\Roaming\YbHxQ0x\QwQsIra3vu.exe | executable | |
MD5:49642CEE0AD99E4882A6F45C478C55B7 | SHA256:CB7DEE0F26CC30B13E5775877D570FCD4CA2E4F1A89614CC12031D6070B78473 | |||
| 6652 | QwQsIra3vu.tmp | C:\Users\admin\AppData\Local\Open Files Viewer 1.16.0.471\uninstall\unins000.exe | executable | |
MD5:25111058A1C6F22EB16782728FDCEEDE | SHA256:DFD545251DCB862882645149F741A619754804244B8F91344596795D78086DBC | |||
| 6652 | QwQsIra3vu.tmp | C:\Users\admin\AppData\Local\Temp\is-UP4BJ.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 6948 | QwQsIra3vu.exe | C:\Users\admin\AppData\Local\Temp\is-08BRU.tmp\QwQsIra3vu.tmp | executable | |
MD5:85F74E5470B61C351EB351EEB1DB465F | SHA256:30EA63950BF5FA275F3A2FBD75B46467272E50C3D715944C372DE1E4D6C7678A | |||
| 6652 | QwQsIra3vu.tmp | C:\Users\admin\AppData\Local\Open Files Viewer 1.16.0.471\uninstall\is-NU173.tmp | executable | |
MD5:25111058A1C6F22EB16782728FDCEEDE | SHA256:DFD545251DCB862882645149F741A619754804244B8F91344596795D78086DBC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
211
TCP/UDP connections
236
DNS requests
227
Threats
61
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.10:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6672 | RUXIMICS.exe | GET | 200 | 184.24.77.10:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6672 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.32.138:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
— | — | POST | 400 | 40.126.32.138:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 200 | 20.190.160.130:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 16.7 Kb | whitelisted |
— | — | POST | 200 | 40.126.32.134:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | GET | 200 | 142.250.185.65:443 | https://drive.usercontent.google.com/download?id=1YBVIDkZgygNfUU2rbJXXCYdrzay5rMdY&export=download&authuser=0&confirm=t | unknown | text | 14 b | whitelisted |
— | — | POST | 200 | 20.190.160.4:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6672 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6672 | RUXIMICS.exe | 184.24.77.10:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 184.24.77.10:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6672 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
drive.usercontent.google.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7164 | svchost015.exe | A Network Trojan was detected | LOADER [ANY.RUN] GCleaner HTTP Header |
7164 | svchost015.exe | A Network Trojan was detected | LOADER [ANY.RUN] GCleaner HTTP Header |
7164 | svchost015.exe | A Network Trojan was detected | LOADER [ANY.RUN] GCleaner HTTP Header |
7164 | svchost015.exe | A Network Trojan was detected | LOADER [ANY.RUN] GCleaner HTTP Header |
7164 | svchost015.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
7164 | svchost015.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
7164 | svchost015.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
7164 | svchost015.exe | A Network Trojan was detected | LOADER [ANY.RUN] GCleaner HTTP Header |
7164 | svchost015.exe | A Network Trojan was detected | LOADER [ANY.RUN] GCleaner HTTP Header |
7164 | svchost015.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
hRdpta7p5O.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
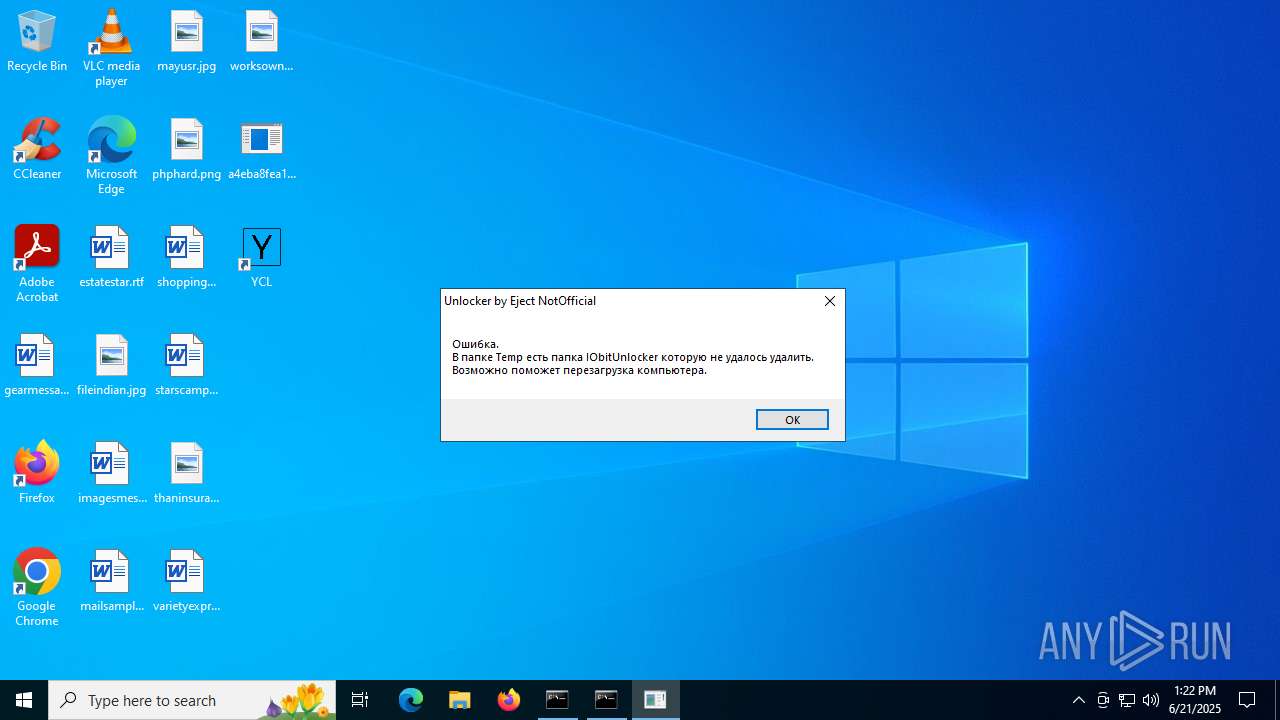
IObitUnlocker.exe | PostAction_Delete |
IObitUnlocker.exe | FileCount:46 |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Defender-------- |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Defender Advanced Threat Protection-------- |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Security Health-------- |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Storage Health-------- |
IObitUnlocker.exe | C:\Program Files\Windows Defender-------- |
IObitUnlocker.exe | C:\Program Files\Windows Defender Advanced Threat Protection-------- |
IObitUnlocker.exe | C:\Program Files\Windows Security-------- |