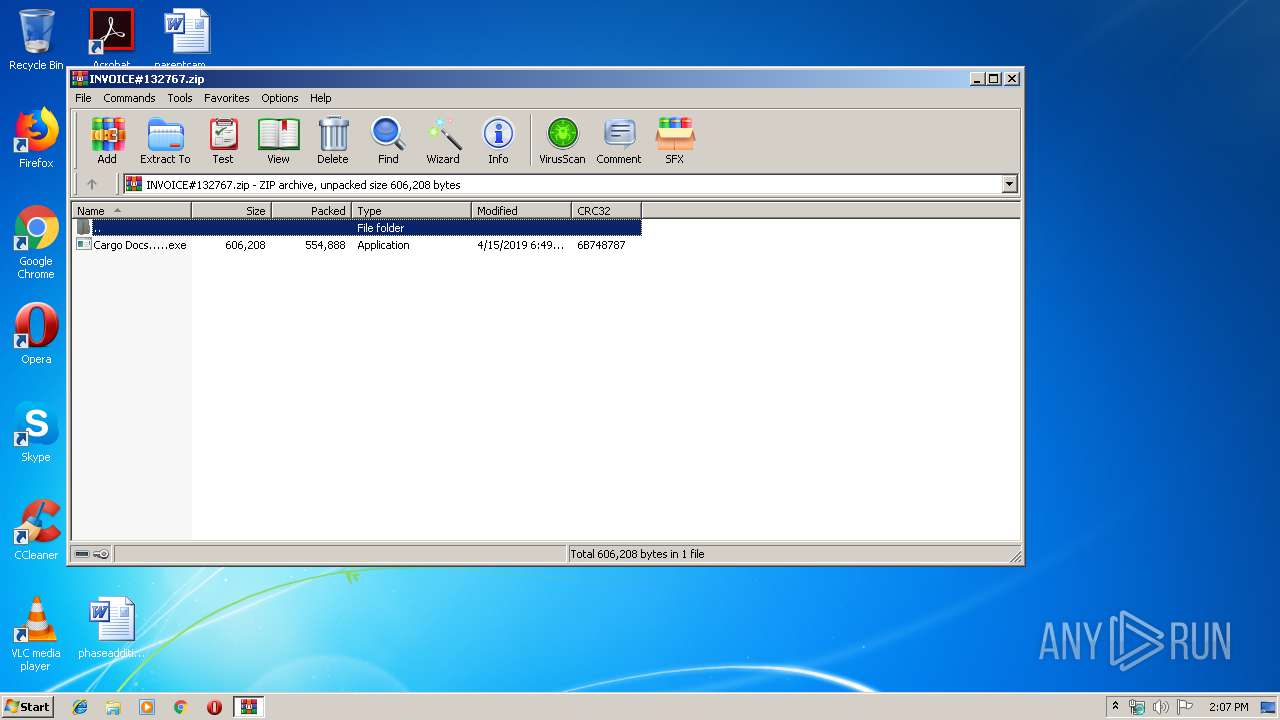
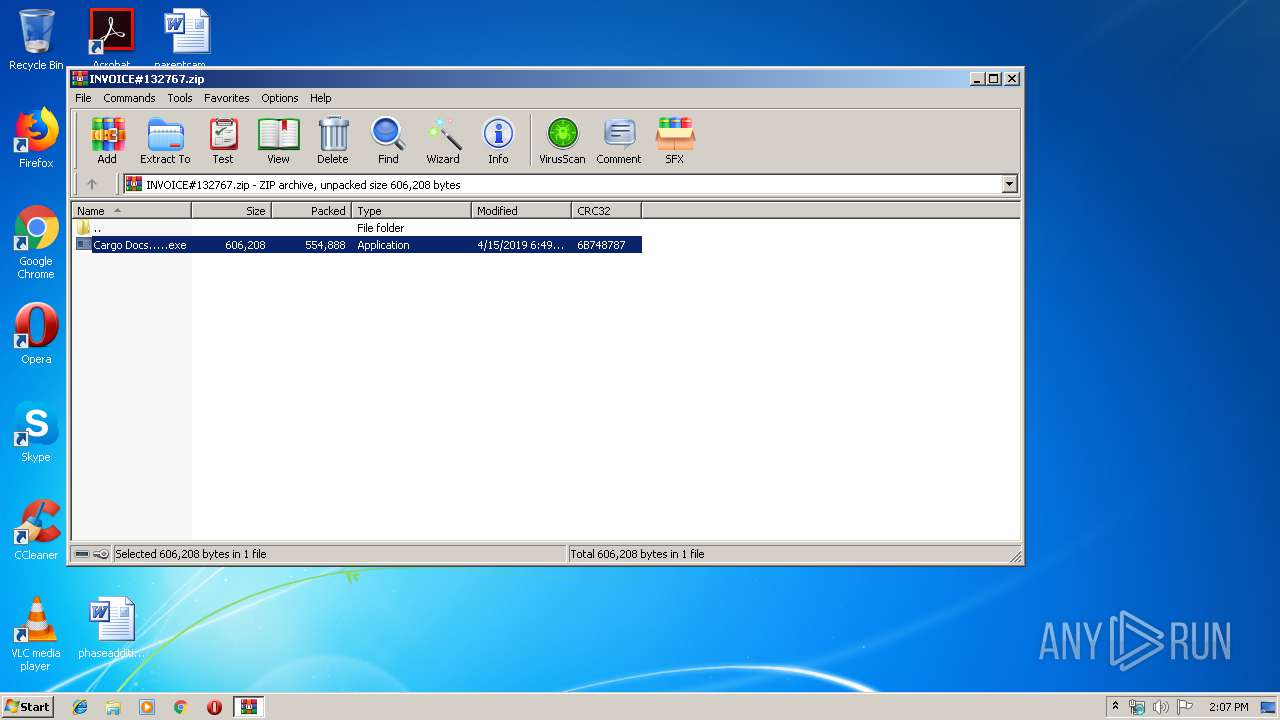
| File name: | INVOICE#132767.zip |
| Full analysis: | https://app.any.run/tasks/b526f9c8-cc58-4f57-9cdc-c4f639ad20ac |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | April 15, 2019, 13:07:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8318C306D0A88CDBCF1B5B2EAF729D28 |
| SHA1: | 634E260885936889BE5E7168560735DF09055BE7 |
| SHA256: | A4CA0AF7E3EC28598D43606C1F46EB9359E970E0E823C087F5BDC22CD8BDFE7F |
| SSDEEP: | 12288:wRbwec4UifIPTygejypVZcc5pp7xKtz6B3VUBbMuz10/jIjdX:wRbwe0qsTQ8cc5LxO6RVkbMu6/oX |
MALICIOUS
Application was dropped or rewritten from another process
- Cargo Docs.....exe (PID: 2520)
- Cargo Docs.....exe (PID: 1772)
Detected AgentTesla Keylogger
- Cargo Docs.....exe (PID: 1772)
Changes the autorun value in the registry
- Cargo Docs.....exe (PID: 1772)
Actions looks like stealing of personal data
- Cargo Docs.....exe (PID: 1772)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2892)
- Cargo Docs.....exe (PID: 1772)
Application launched itself
- Cargo Docs.....exe (PID: 2520)
Checks for external IP
- Cargo Docs.....exe (PID: 1772)
Creates files in the user directory
- Cargo Docs.....exe (PID: 1772)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:15 06:49:17 |
| ZipCRC: | 0x6b748787 |
| ZipCompressedSize: | 554888 |
| ZipUncompressedSize: | 606208 |
| ZipFileName: | Cargo Docs.....exe |
Total processes
35
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1772 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2892.17240\Cargo Docs.....exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2892.17240\Cargo Docs.....exe | Cargo Docs.....exe | ||||||||||||
User: admin Company: Bláscar Integrity Level: MEDIUM Description: IT Auction Exit code: 0 Version: 13.2.9.17 Modules
| |||||||||||||||
| 2520 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2892.17240\Cargo Docs.....exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2892.17240\Cargo Docs.....exe | — | WinRAR.exe | |||||||||||
User: admin Company: Bláscar Integrity Level: MEDIUM Description: IT Auction Exit code: 0 Version: 13.2.9.17 Modules
| |||||||||||||||
| 2892 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\INVOICE#132767.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
502
Read events
477
Write events
25
Delete events
0
Modification events
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\INVOICE#132767.zip | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2892 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2892.17240\Cargo Docs.....exe | executable | |
MD5:— | SHA256:— | |||
| 1772 | Cargo Docs.....exe | C:\Users\admin\AppData\Roaming\MyApp\MyApp.exe | executable | |
MD5:— | SHA256:— | |||
| 1772 | Cargo Docs.....exe | C:\Users\admin\AppData\Roaming\VI82gbsSIQ.jpeg | image | |
MD5:— | SHA256:— | |||
| 1772 | Cargo Docs.....exe | C:\Users\admin\AppData\Roaming\AFT7BqxMyJ.jpeg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
2
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1772 | Cargo Docs.....exe | GET | 200 | 52.200.125.74:80 | http://checkip.amazonaws.com/ | US | text | 13 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1772 | Cargo Docs.....exe | 192.185.73.15:26 | mail.balbaagroup.com | CyrusOne LLC | US | malicious |
1772 | Cargo Docs.....exe | 52.200.125.74:80 | checkip.amazonaws.com | Amazon.com, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mail.balbaagroup.com |
| malicious |
checkip.amazonaws.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1772 | Cargo Docs.....exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
1772 | Cargo Docs.....exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
1772 | Cargo Docs.....exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
1772 | Cargo Docs.....exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2 ETPRO signatures available at the full report