| File name: | map_setup.exe |
| Full analysis: | https://app.any.run/tasks/62765d5a-73de-4e42-a145-ed67ace98c34 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | May 27, 2025, 10:07:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 616E5A3D02CD3D2F596A5E93B200EEAD |
| SHA1: | 1C0F0CEB9B546F2EED0B3E20791D96DB0040C548 |
| SHA256: | A43F215500592D3AF1DA2BCB0963801026059E4391E05D60FAE1BDBA6C69273A |
| SSDEEP: | 98304:7dkjEZtHjwoz21PXlFjuctDYOSbNnp7fzhkJGrdAbfDawnYdDhgZQhHpis1Kjw80:VcYloJ/ftA57S+ |
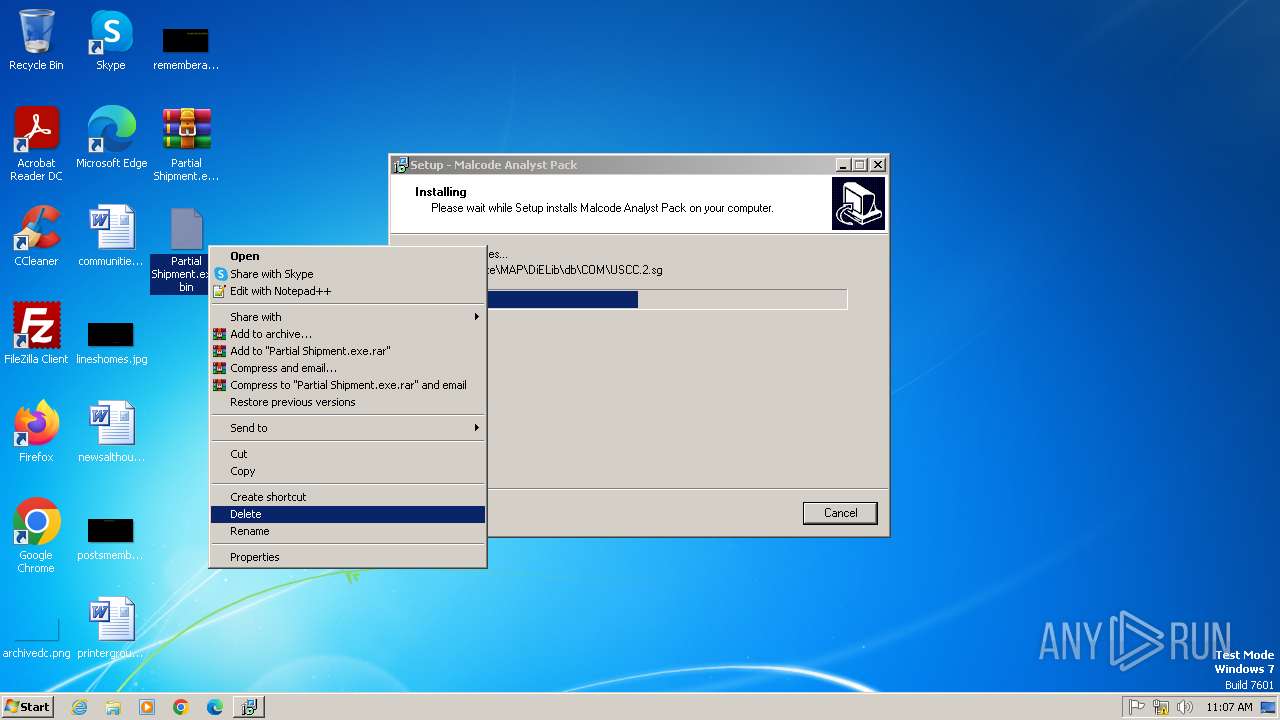
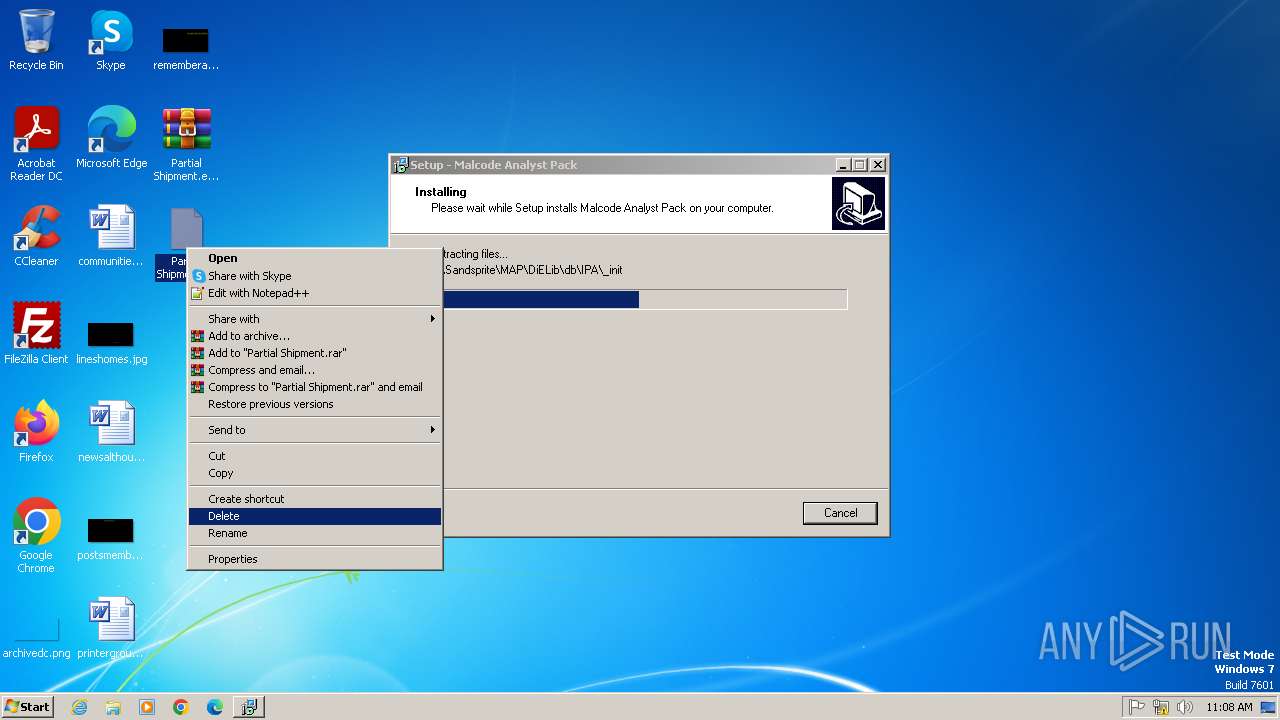
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- map_setup.tmp (PID: 1748)
AGENTTESLA has been detected (YARA)
- Partial Shipment.exe (PID: 1936)
- Partial Shipment.exe (PID: 3508)
- Partial Shipment.exe (PID: 3776)
SUSPICIOUS
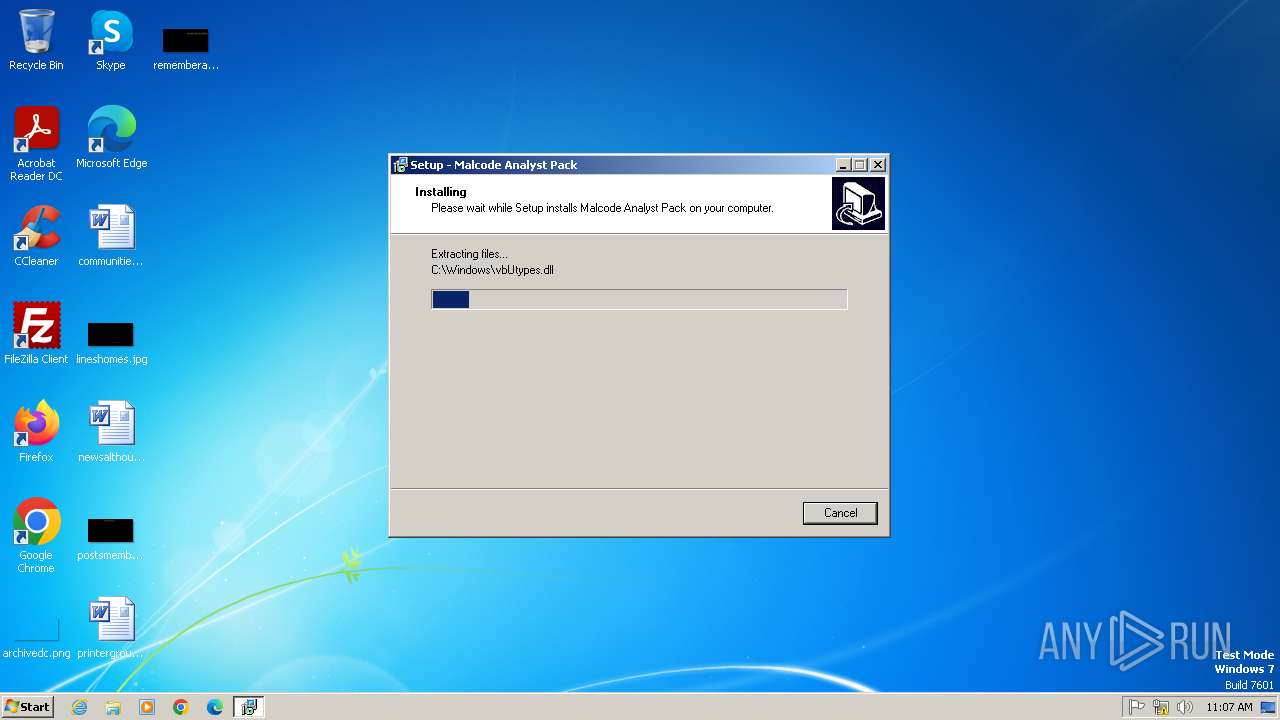
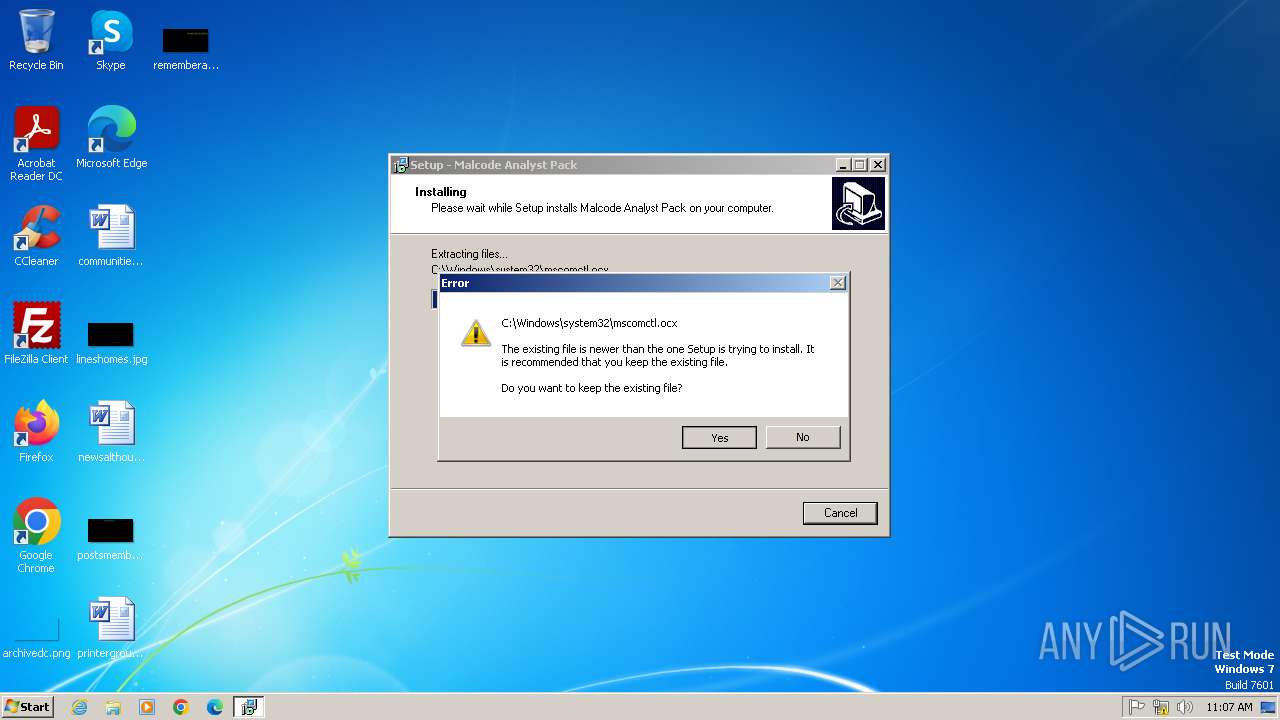
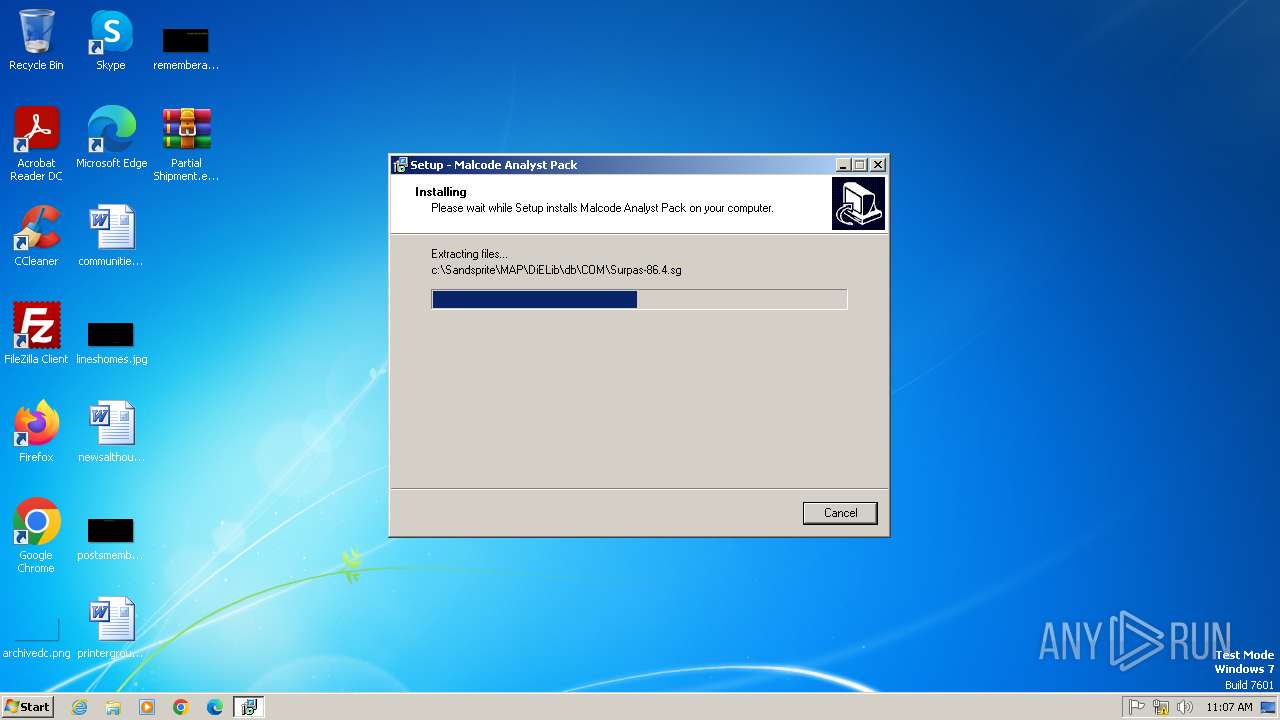
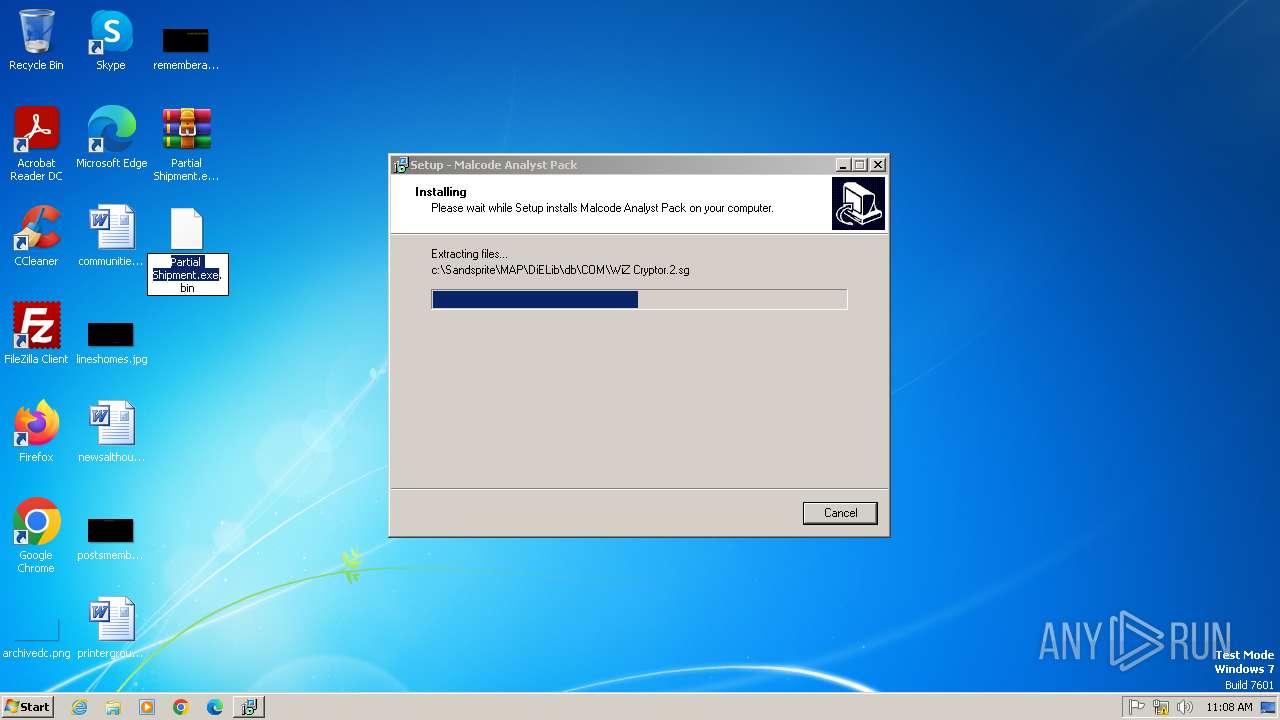
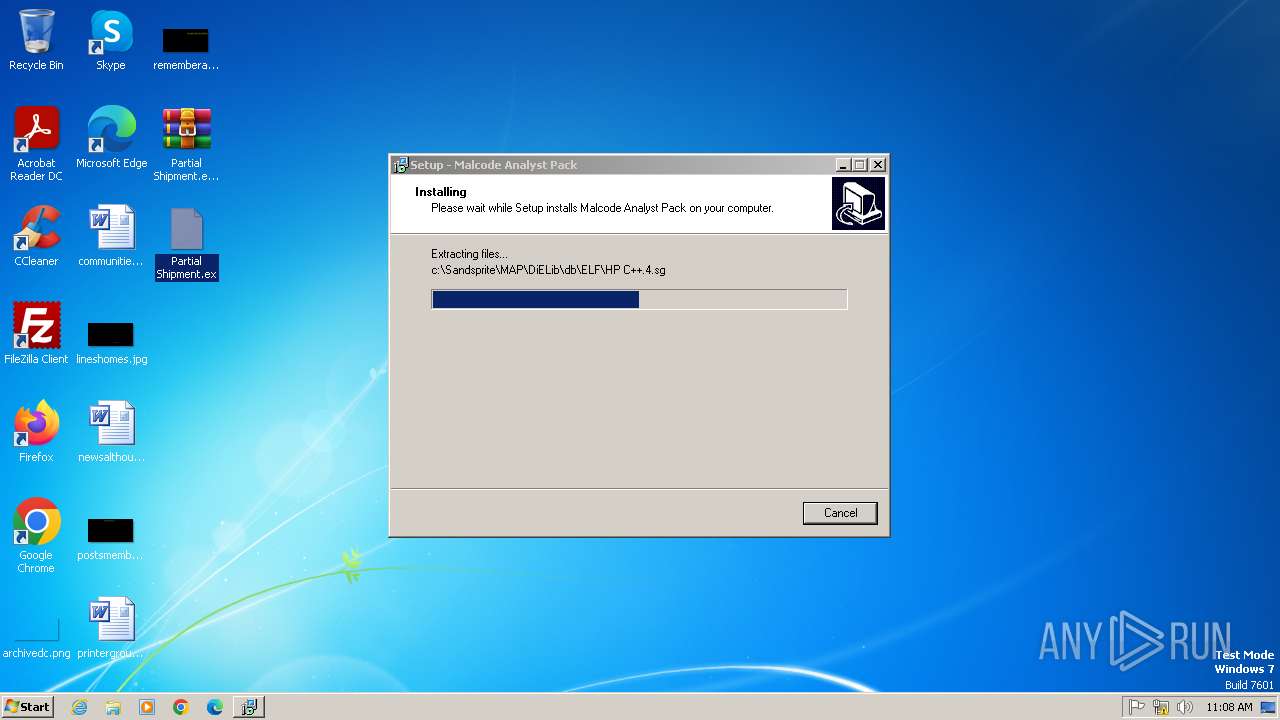
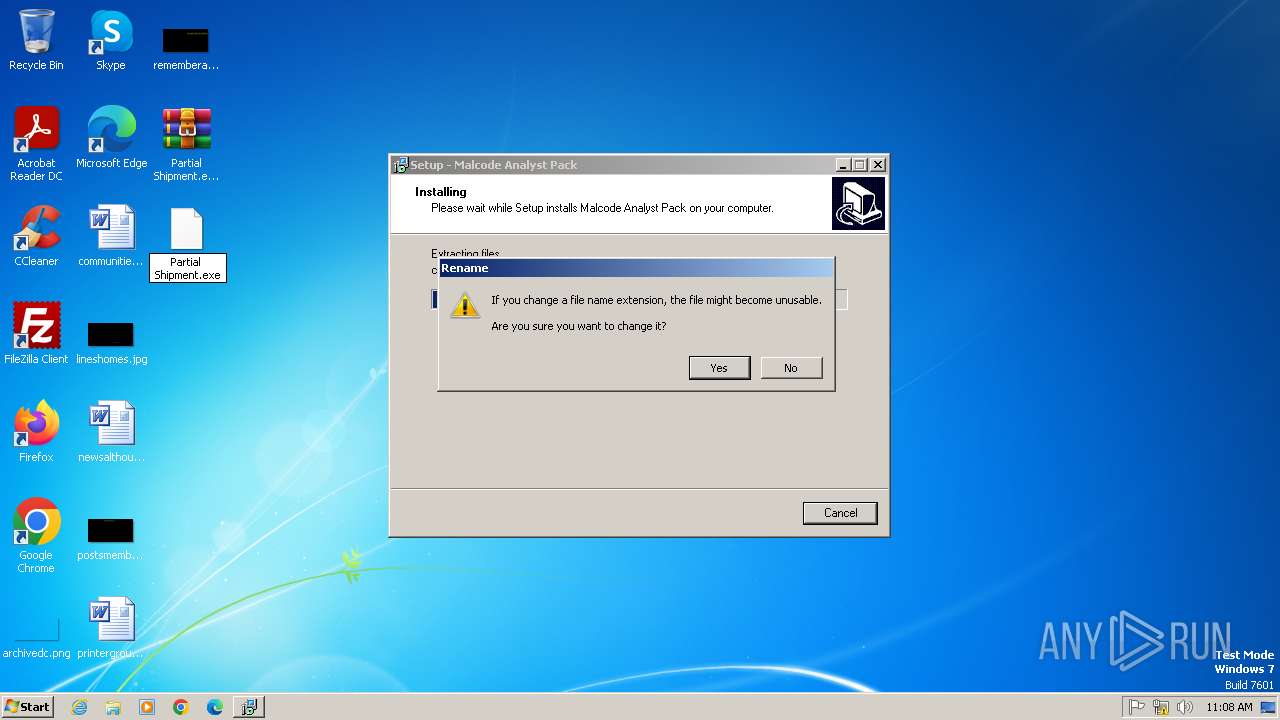
Executable content was dropped or overwritten
- map_setup.exe (PID: 2452)
- map_setup.exe (PID: 2396)
- map_setup.tmp (PID: 1748)
- Partial Shipment.exe (PID: 4076)
- Partial Shipment.exe (PID: 2052)
- Partial Shipment.exe (PID: 1120)
- Partial Shipment.exe (PID: 2000)
- Partial Shipment.exe (PID: 312)
- Partial Shipment.exe (PID: 3824)
- Partial Shipment.exe (PID: 3072)
Process drops legitimate windows executable
- map_setup.tmp (PID: 1748)
Reads the Windows owner or organization settings
- map_setup.tmp (PID: 1748)
The process drops C-runtime libraries
- map_setup.tmp (PID: 1748)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 2996)
- regsvr32.exe (PID: 2616)
- regsvr32.exe (PID: 3644)
- regsvr32.exe (PID: 2984)
- regsvr32.exe (PID: 3904)
Application launched itself
- Partial Shipment.exe (PID: 4076)
- Partial Shipment.exe (PID: 2052)
- Partial Shipment.exe (PID: 2000)
Modifies hosts file to alter network resolution
- Partial Shipment.exe (PID: 1936)
INFO
Create files in a temporary directory
- map_setup.exe (PID: 2452)
- map_setup.exe (PID: 2396)
- map_setup.tmp (PID: 1748)
- ShellExt.exe (PID: 4060)
- Partial Shipment.exe (PID: 4076)
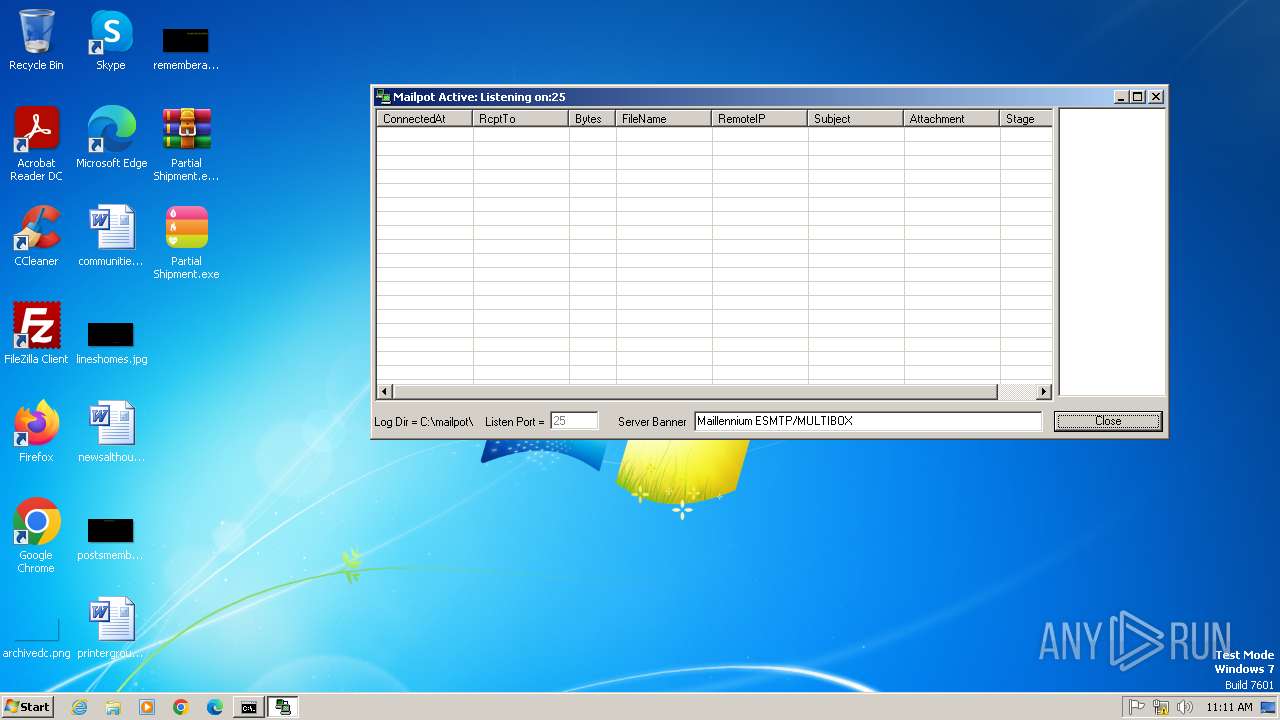
- mail_pot.exe (PID: 3968)
- Partial Shipment.exe (PID: 2052)
- Partial Shipment.exe (PID: 1120)
- Partial Shipment.exe (PID: 2000)
- Partial Shipment.exe (PID: 312)
- Partial Shipment.exe (PID: 3824)
- Partial Shipment.exe (PID: 3072)
Checks supported languages
- map_setup.exe (PID: 2452)
- map_setup.tmp (PID: 2448)
- map_setup.exe (PID: 2396)
- map_setup.tmp (PID: 1748)
- ShellExt.exe (PID: 4060)
- mail_pot.exe (PID: 3968)
- Partial Shipment.exe (PID: 4076)
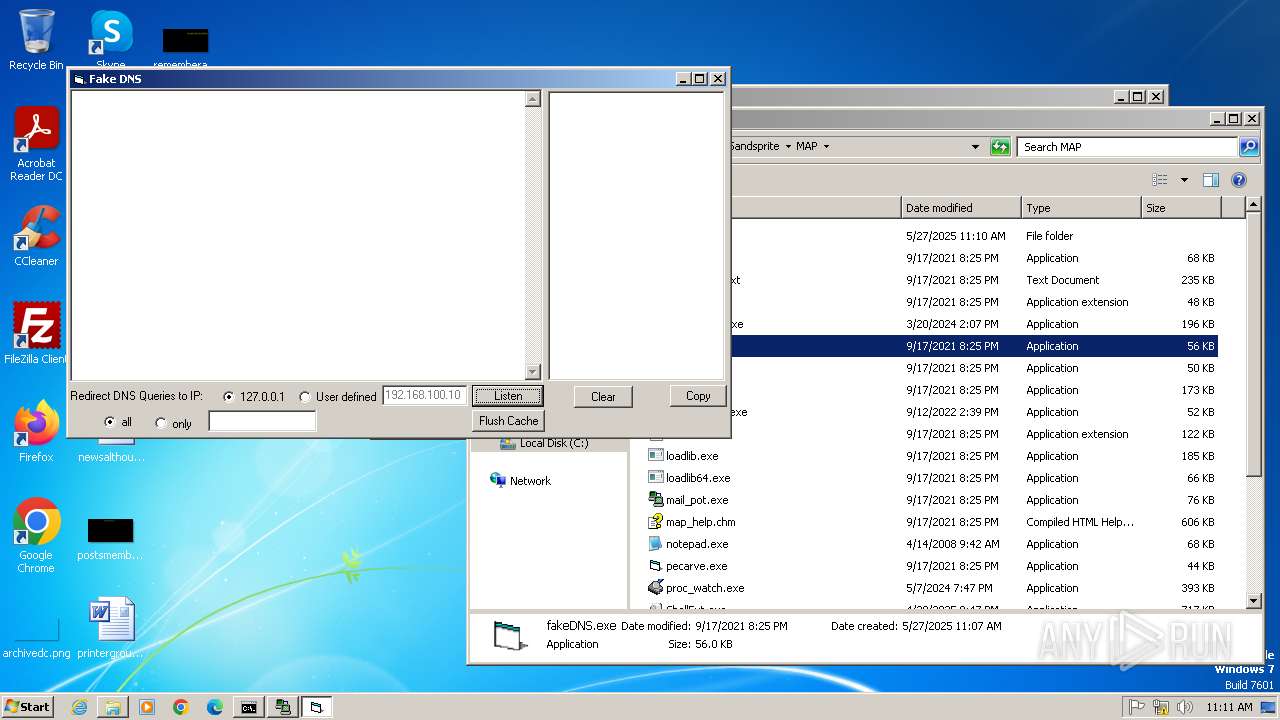
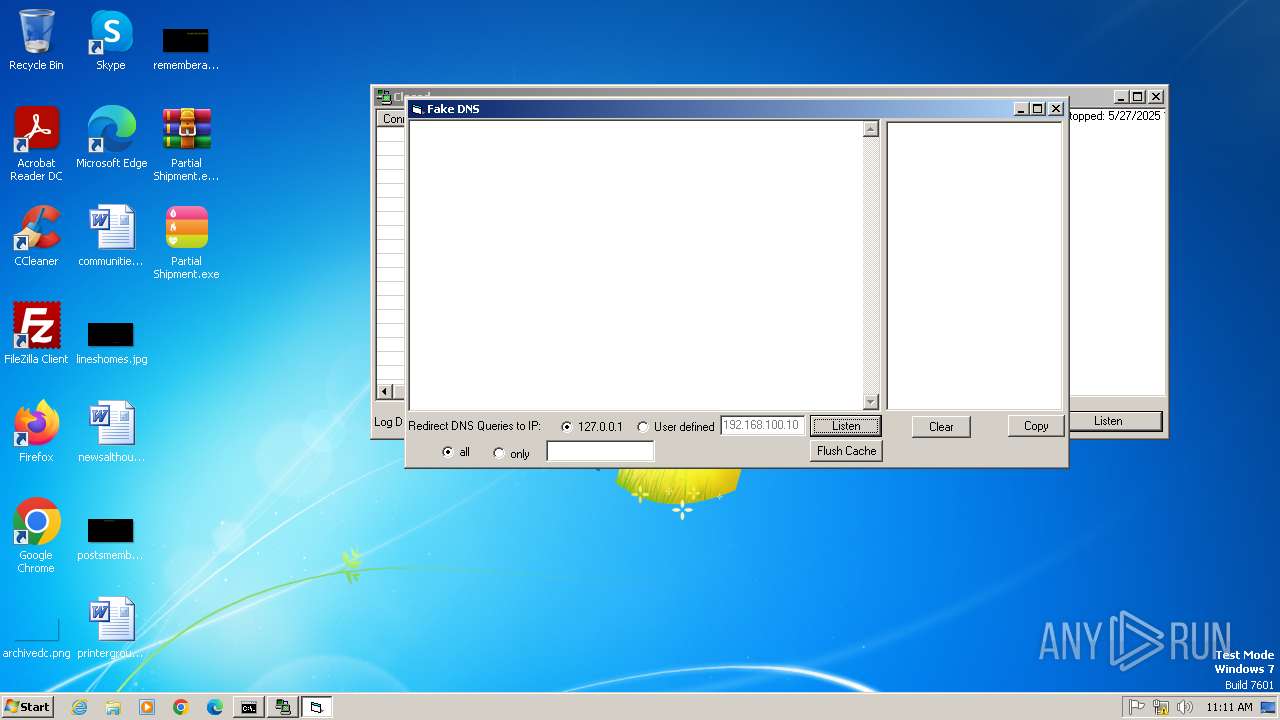
- fakeDNS.exe (PID: 3876)
- Partial Shipment.exe (PID: 2052)
- Partial Shipment.exe (PID: 1120)
- Partial Shipment.exe (PID: 3508)
- Partial Shipment.exe (PID: 1936)
- Partial Shipment.exe (PID: 2000)
- Partial Shipment.exe (PID: 312)
- Partial Shipment.exe (PID: 3776)
- Partial Shipment.exe (PID: 3824)
- Partial Shipment.exe (PID: 3072)
The sample compiled with english language support
- map_setup.exe (PID: 2452)
- map_setup.exe (PID: 2396)
- map_setup.tmp (PID: 1748)
Reads the computer name
- map_setup.tmp (PID: 2448)
- map_setup.tmp (PID: 1748)
- Partial Shipment.exe (PID: 4076)
- Partial Shipment.exe (PID: 1936)
- fakeDNS.exe (PID: 3876)
- Partial Shipment.exe (PID: 2052)
- Partial Shipment.exe (PID: 3508)
- Partial Shipment.exe (PID: 1120)
- Partial Shipment.exe (PID: 2000)
- Partial Shipment.exe (PID: 312)
- Partial Shipment.exe (PID: 3776)
- Partial Shipment.exe (PID: 3824)
- Partial Shipment.exe (PID: 3072)
Compiled with Borland Delphi (YARA)
- map_setup.tmp (PID: 1748)
- map_setup.tmp (PID: 2448)
Detects InnoSetup installer (YARA)
- map_setup.tmp (PID: 1748)
- map_setup.exe (PID: 2452)
- map_setup.tmp (PID: 2448)
- map_setup.exe (PID: 2396)
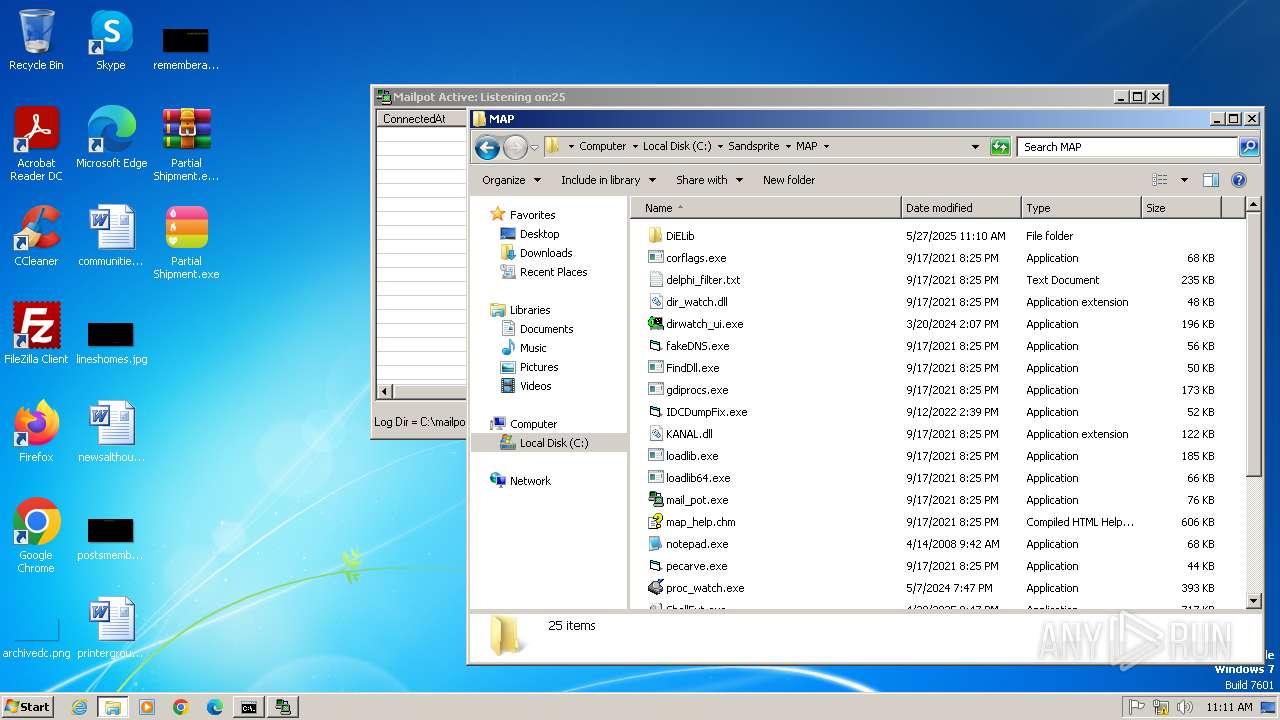
Creates files in the program directory
- map_setup.tmp (PID: 1748)
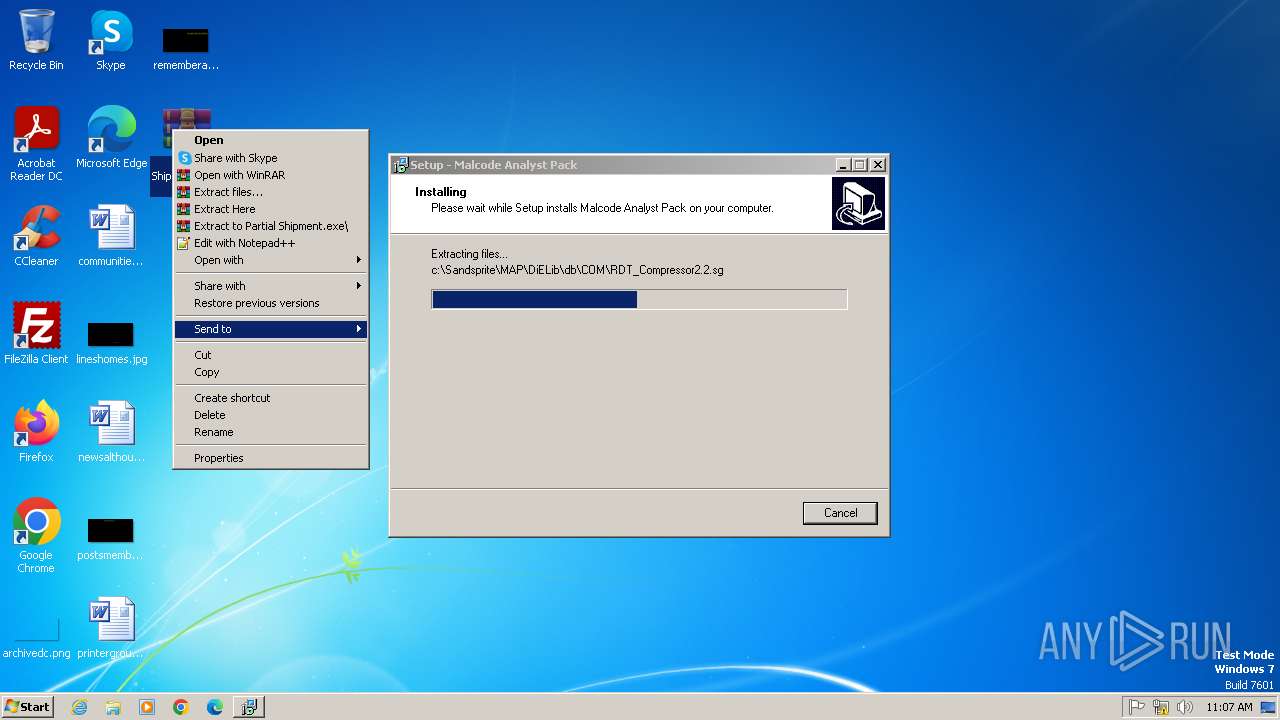
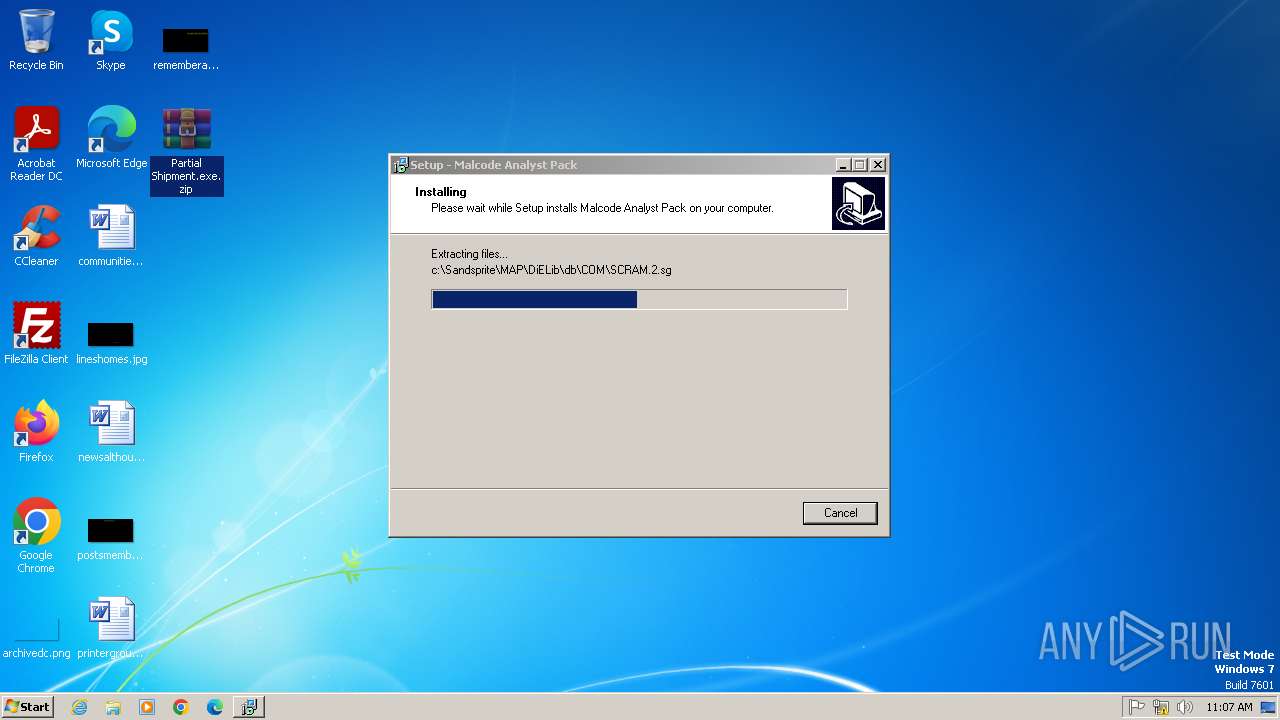
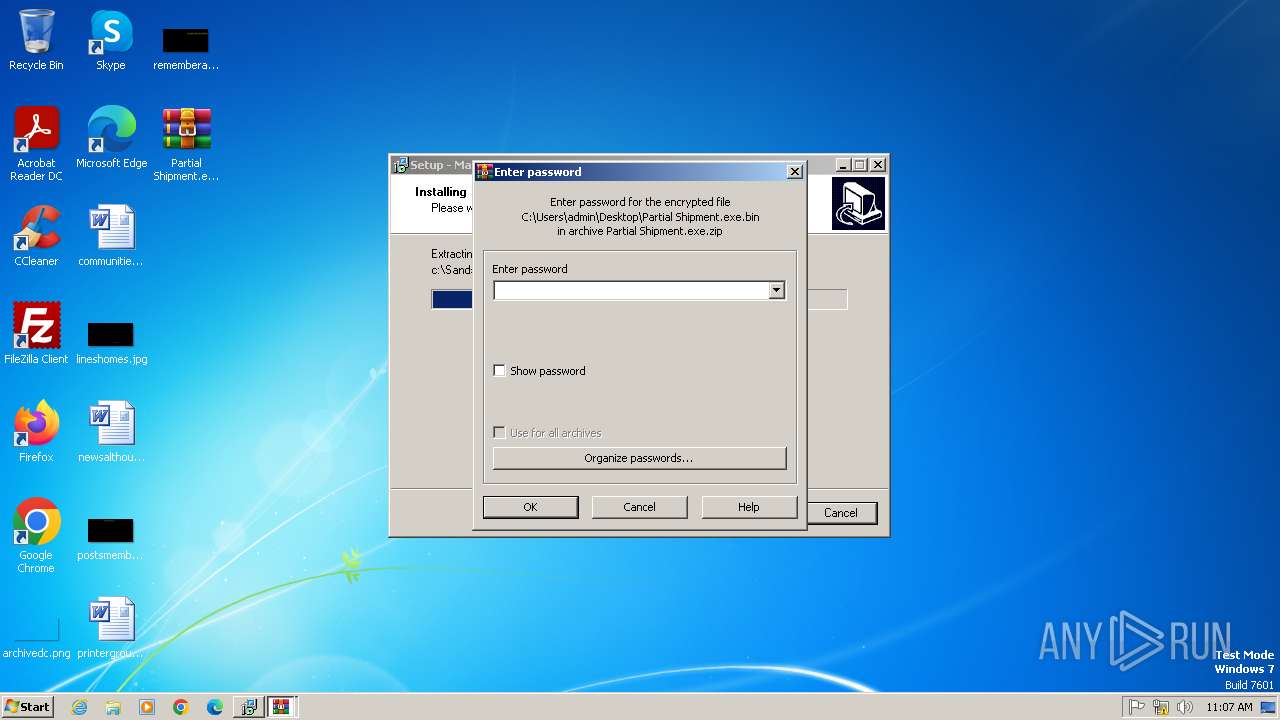
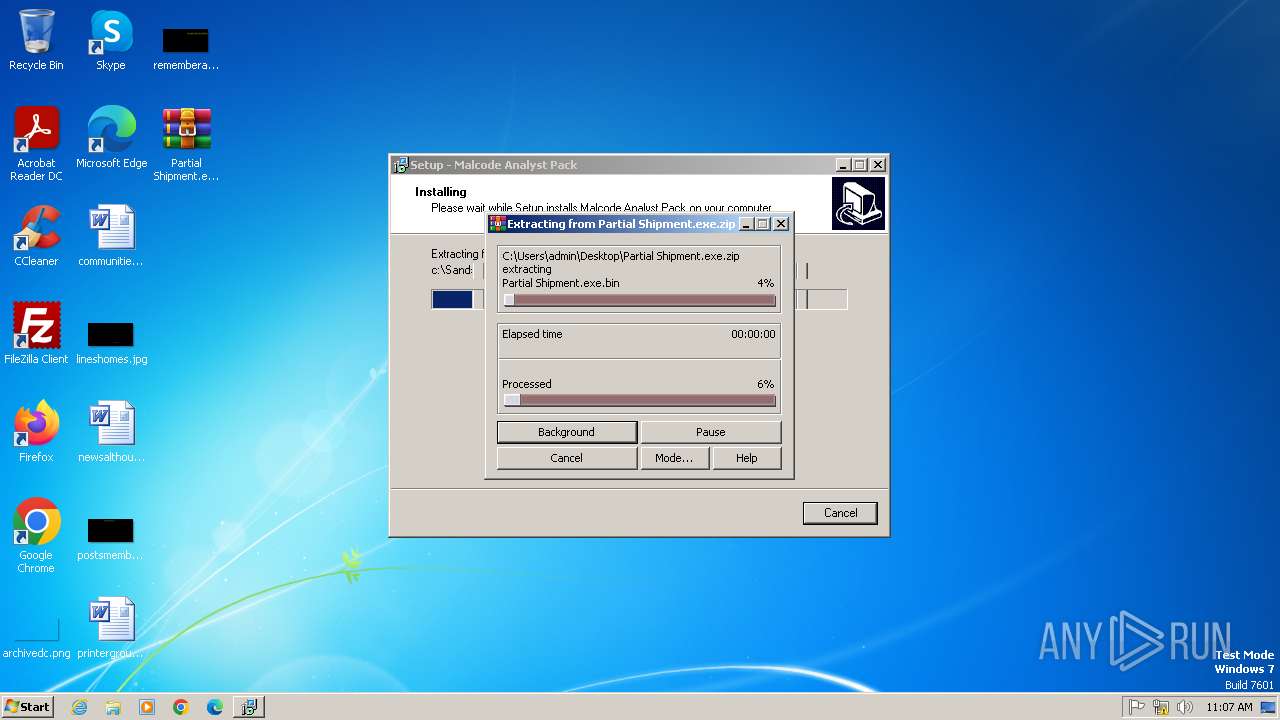
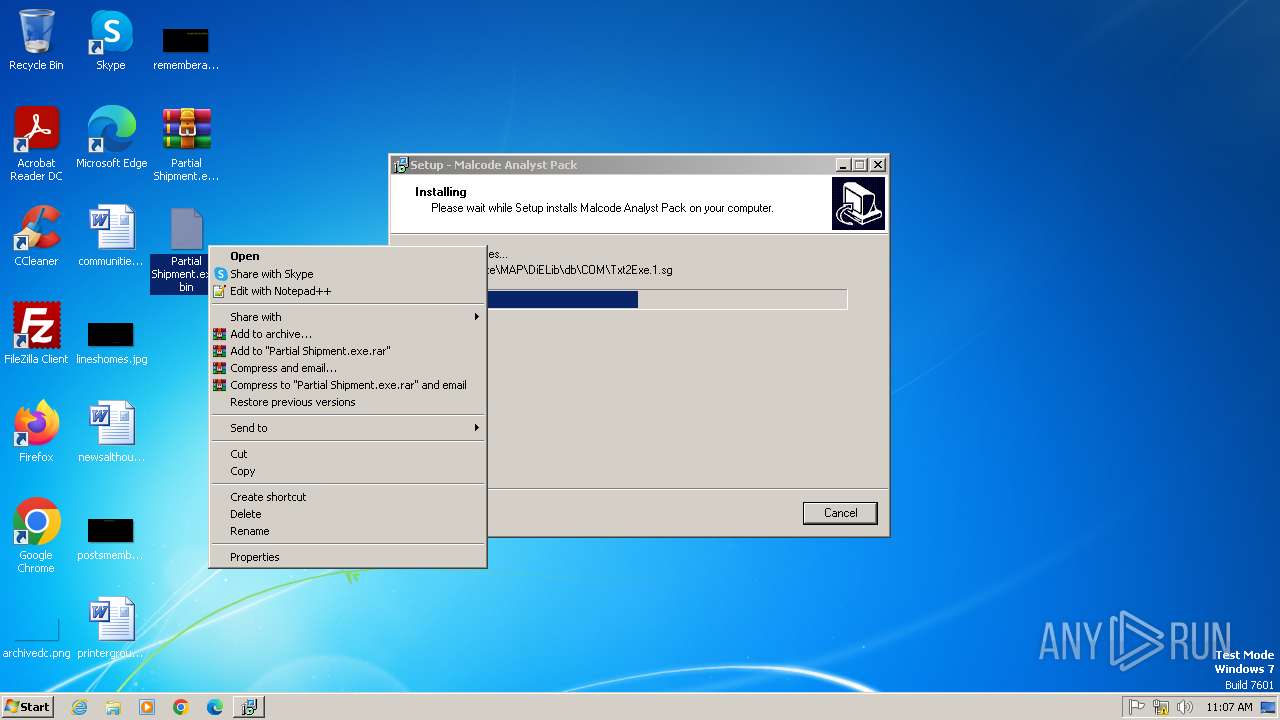
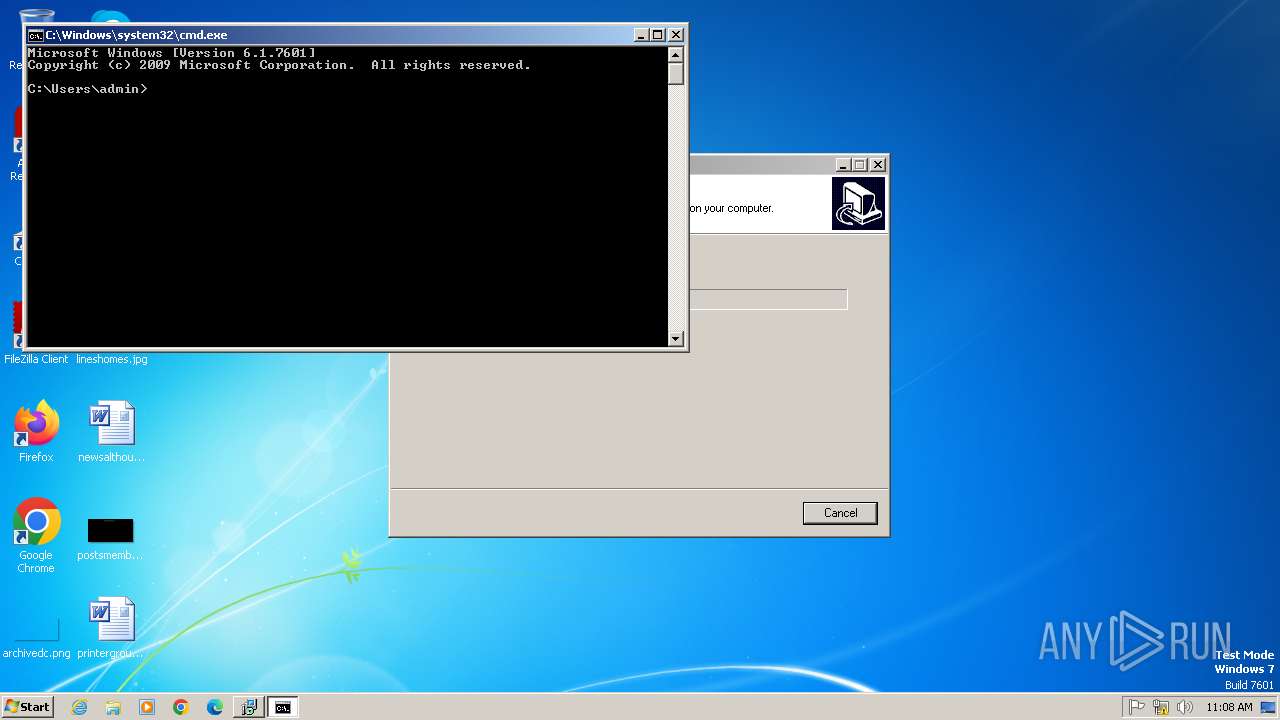
Manual execution by a user
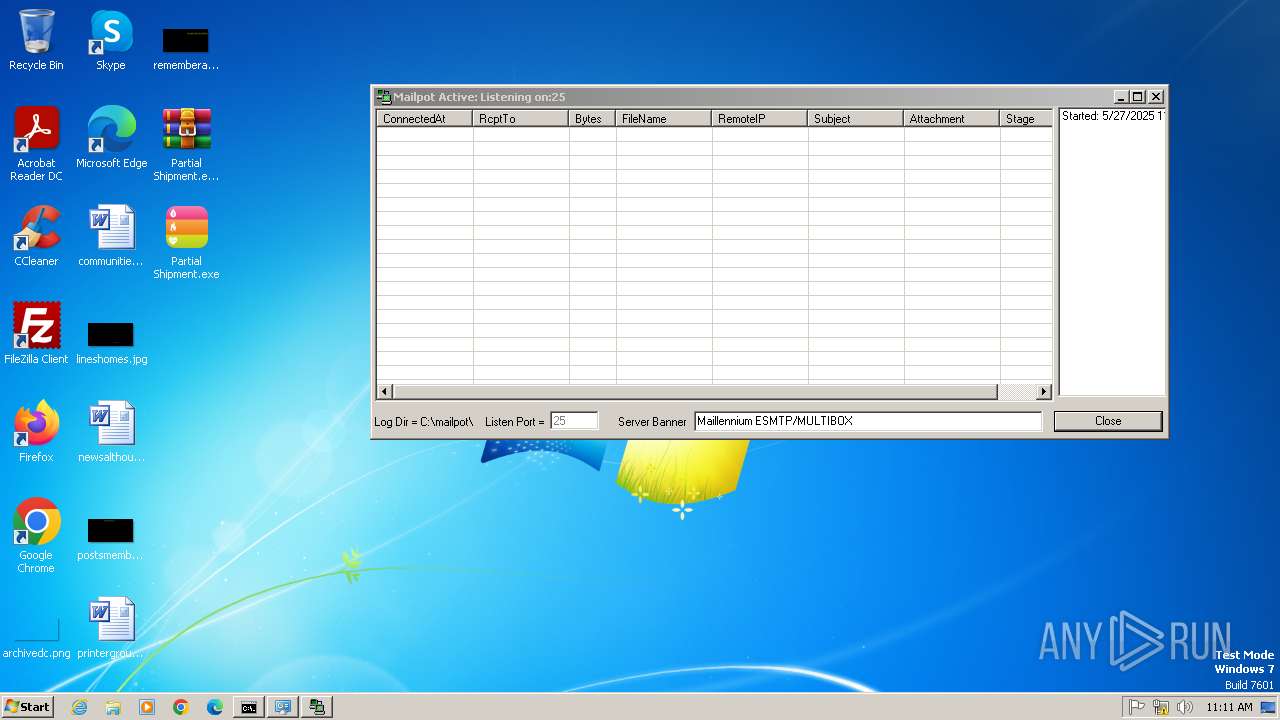
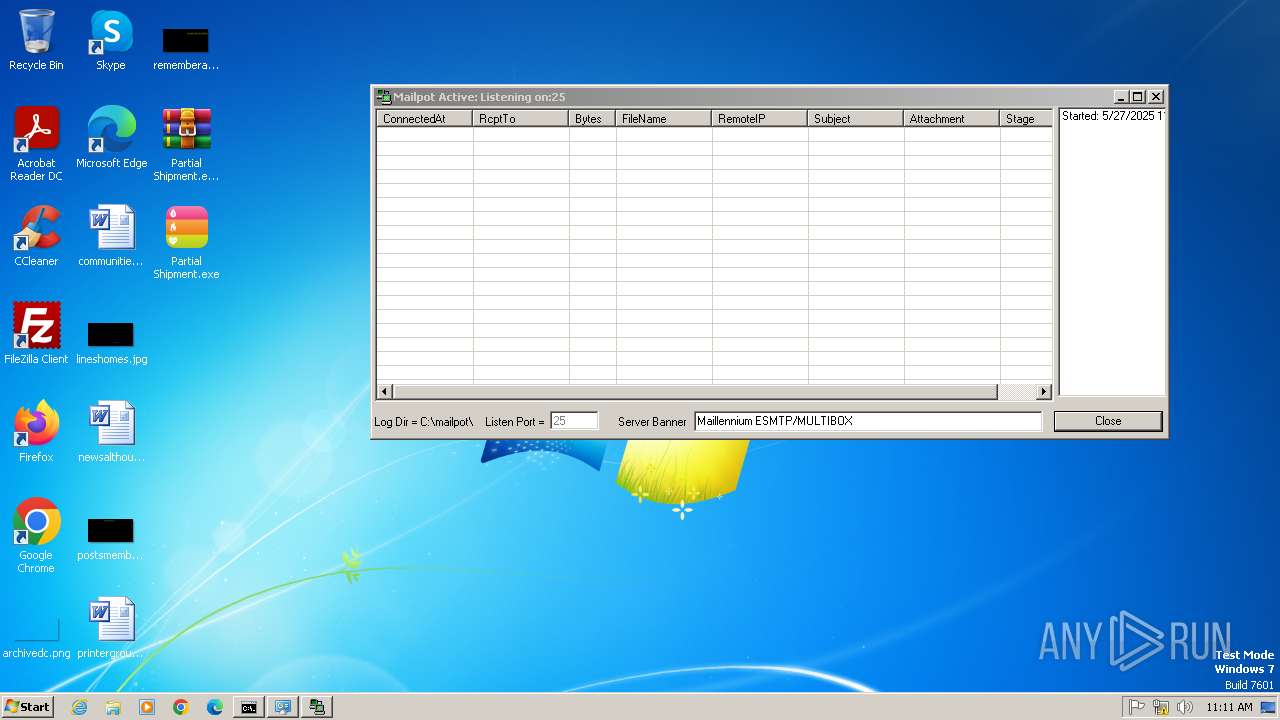
- WinRAR.exe (PID: 3168)
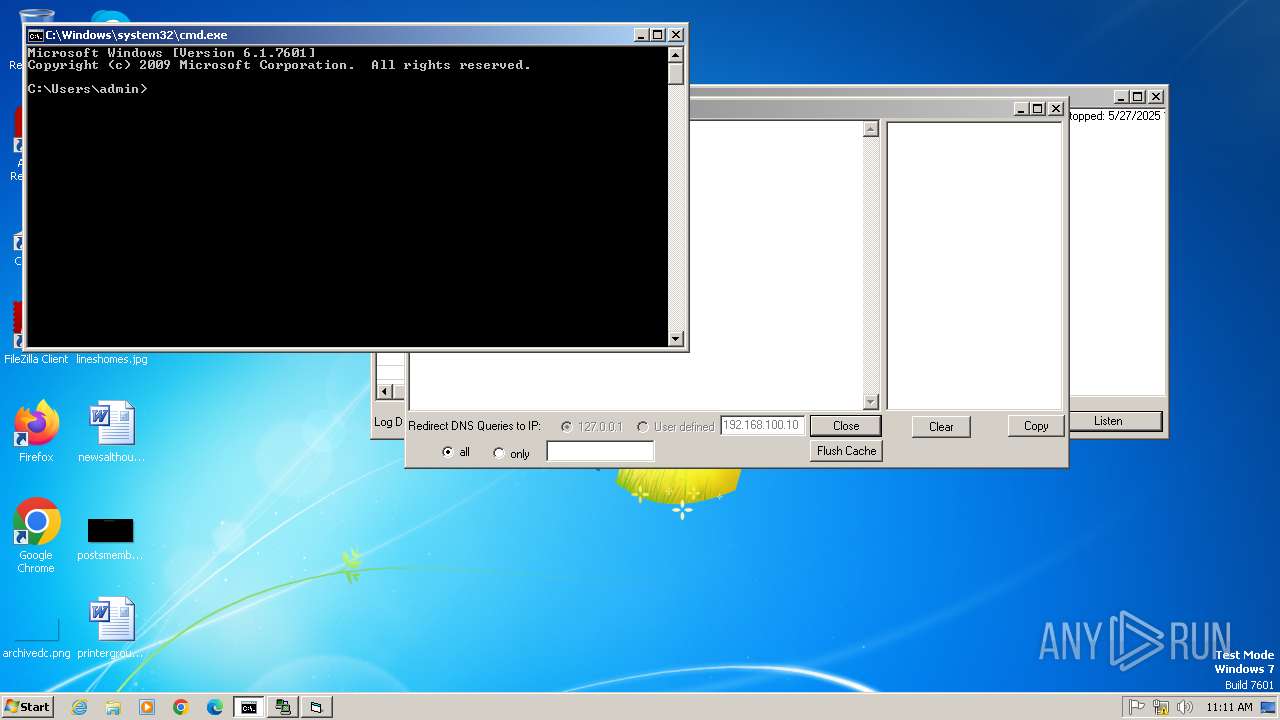
- cmd.exe (PID: 2356)
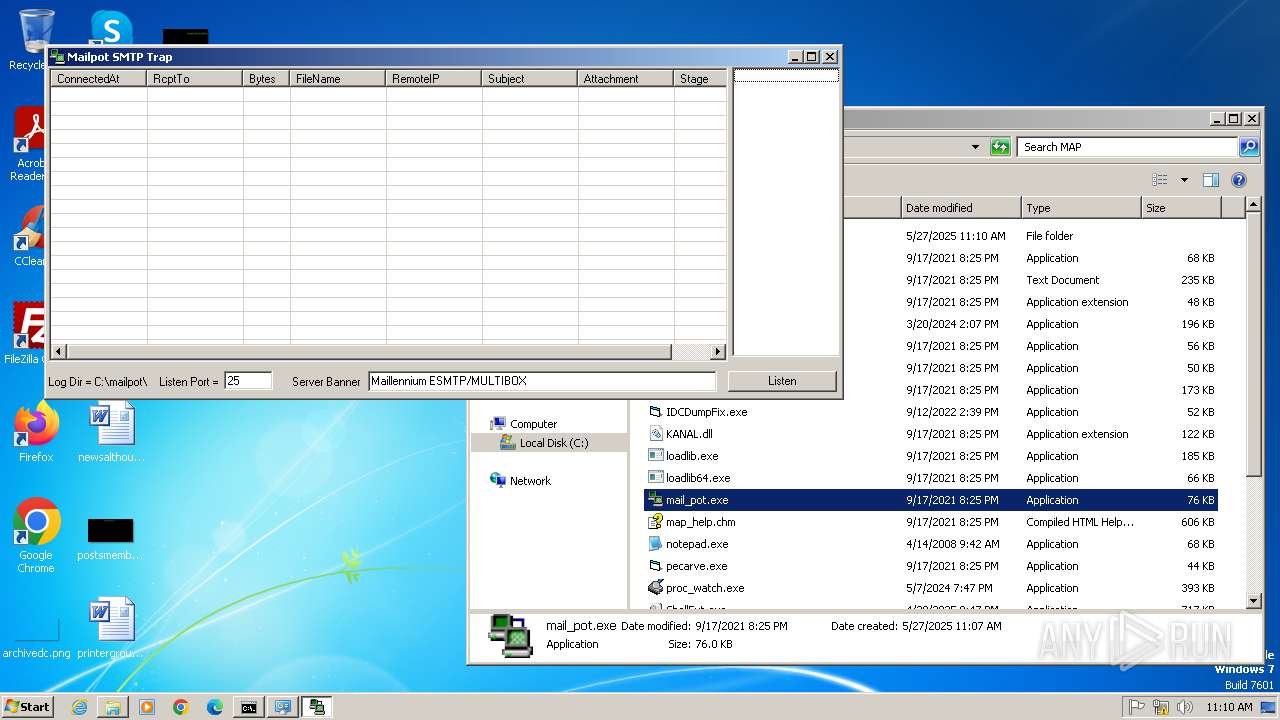
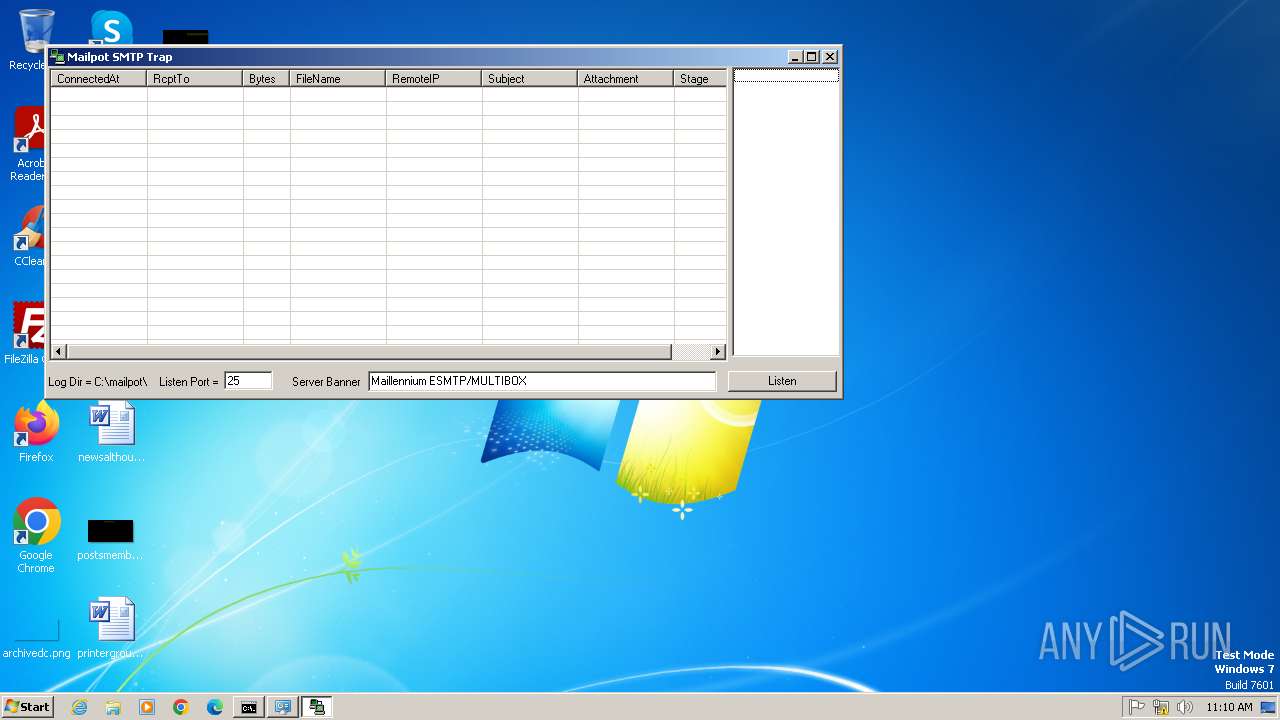
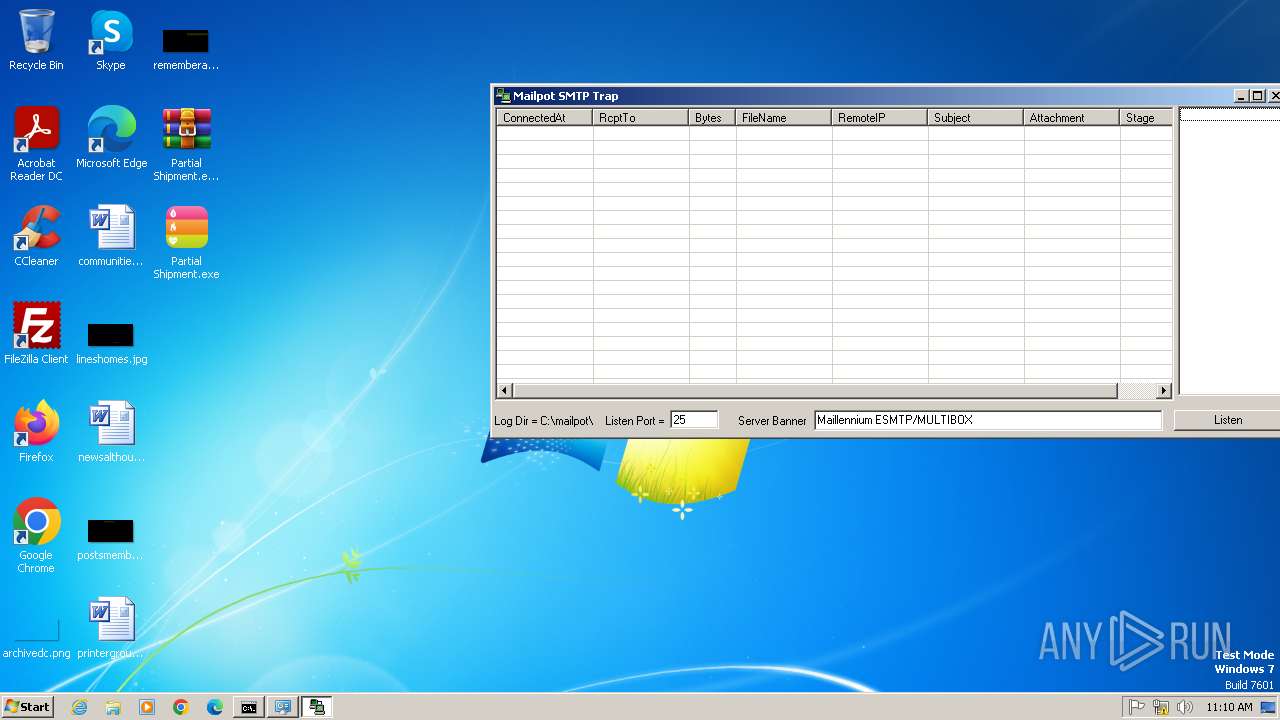
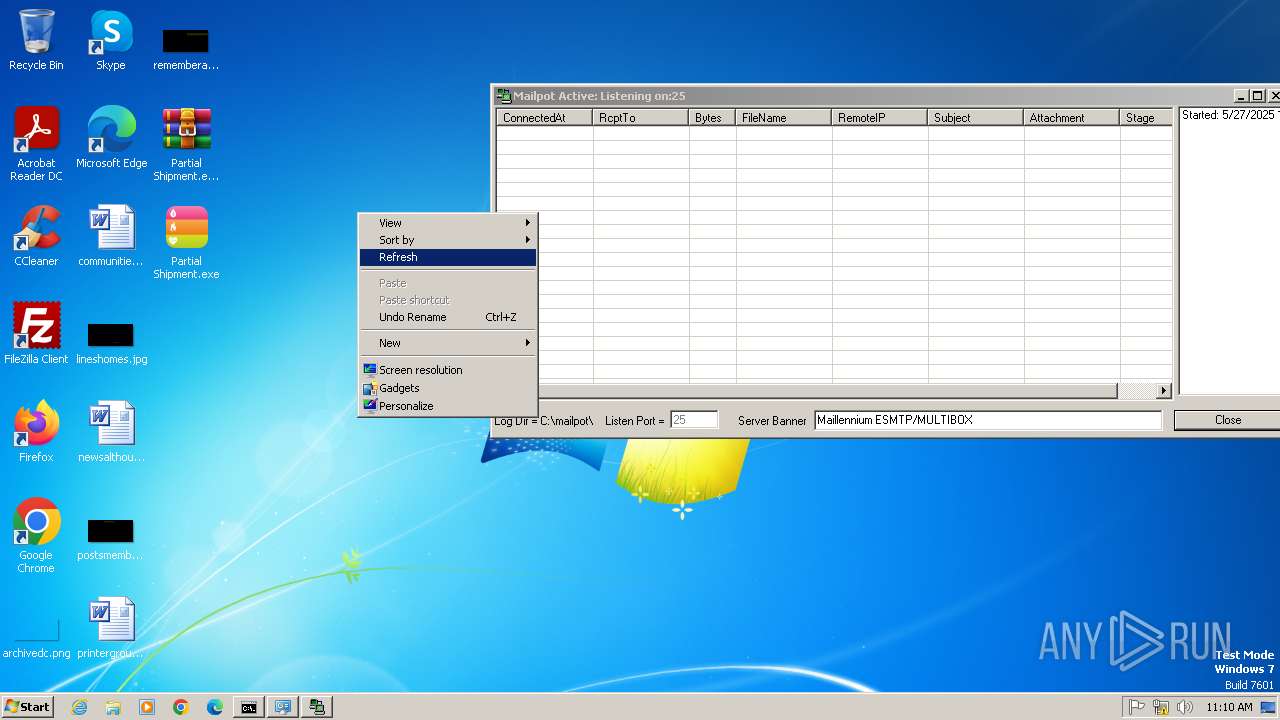
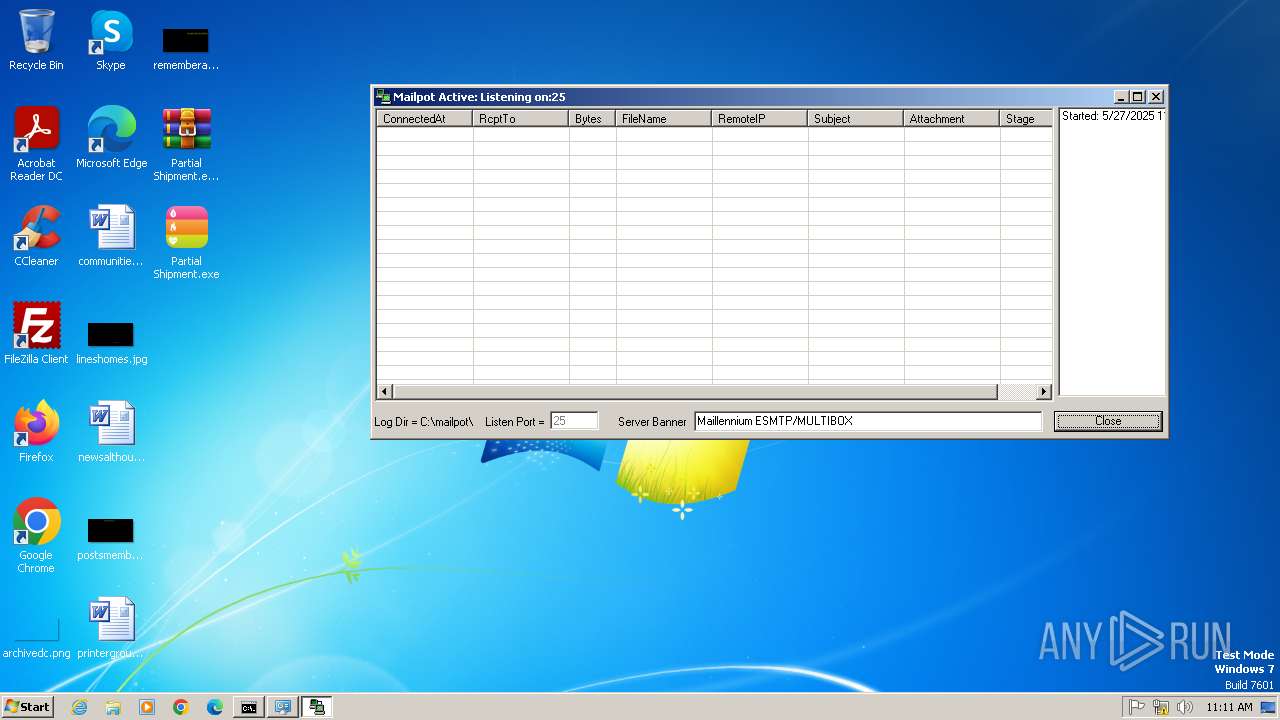
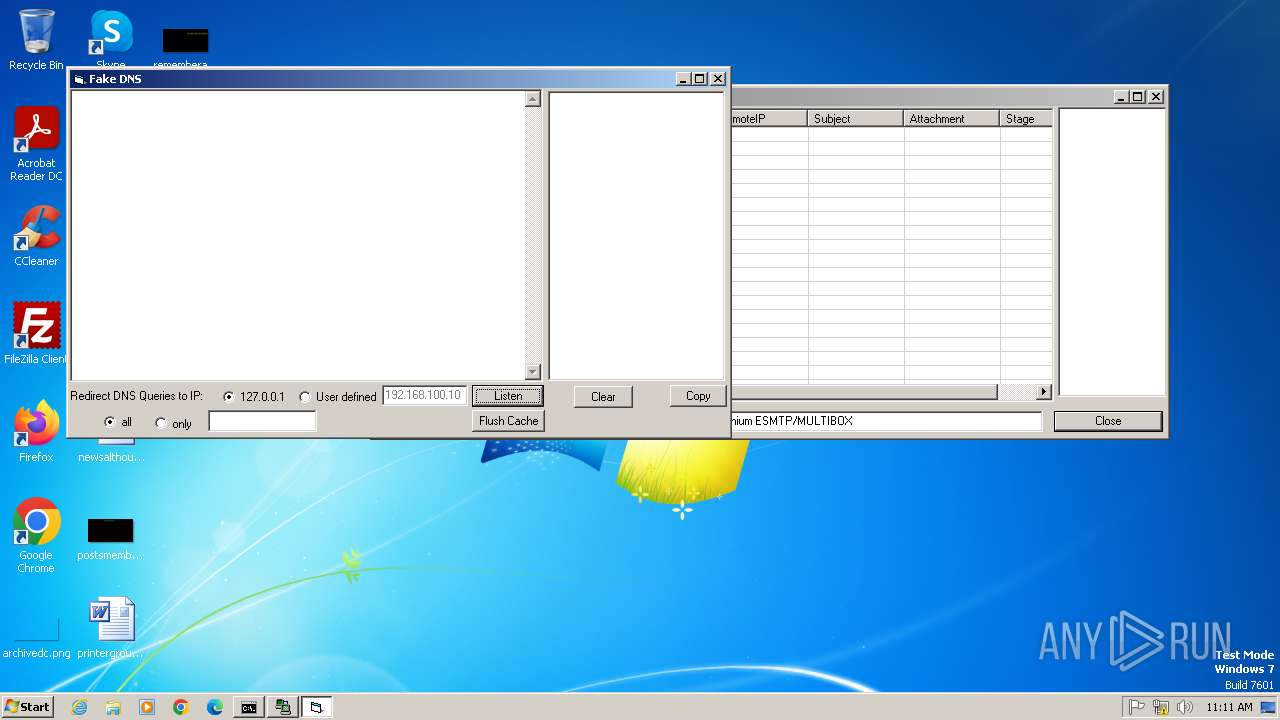
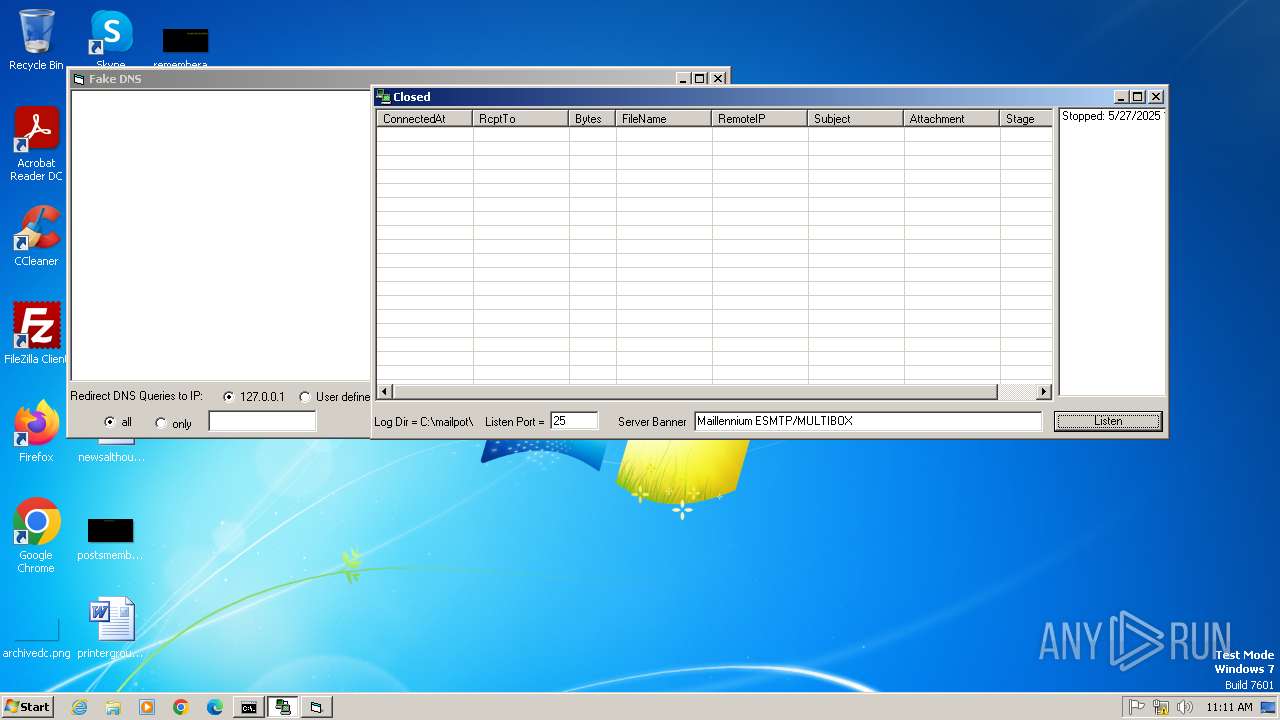
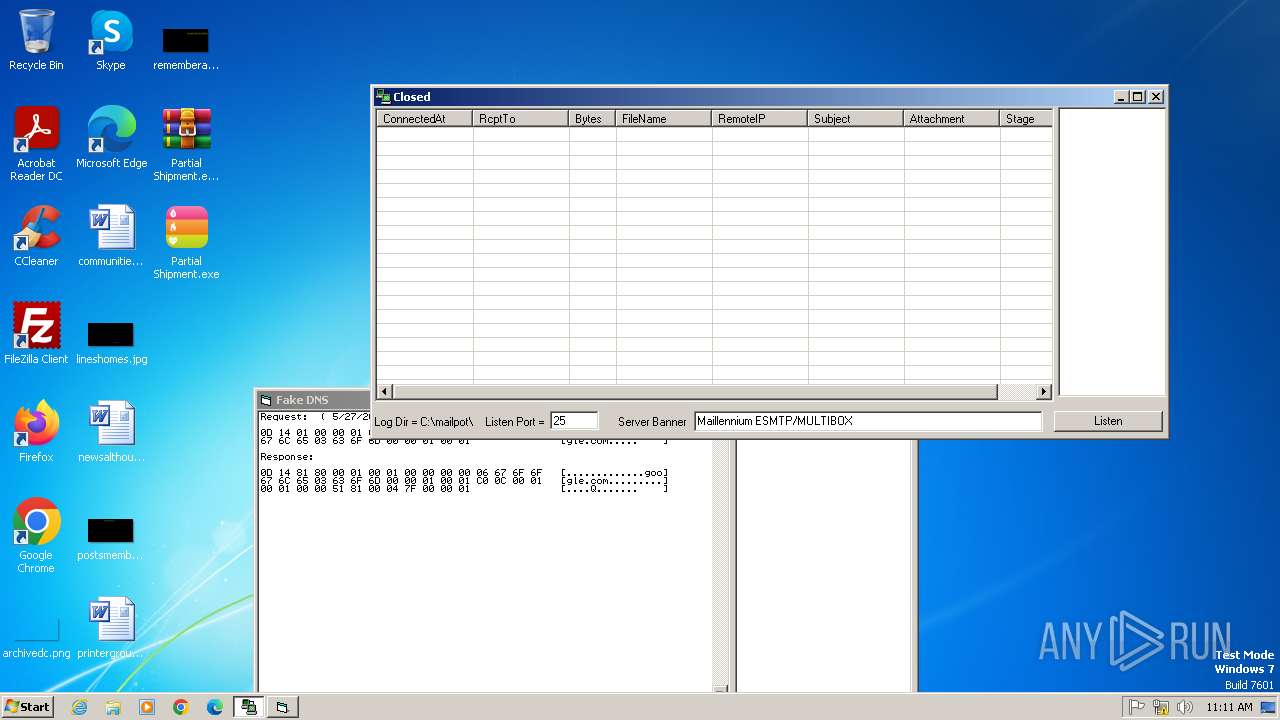
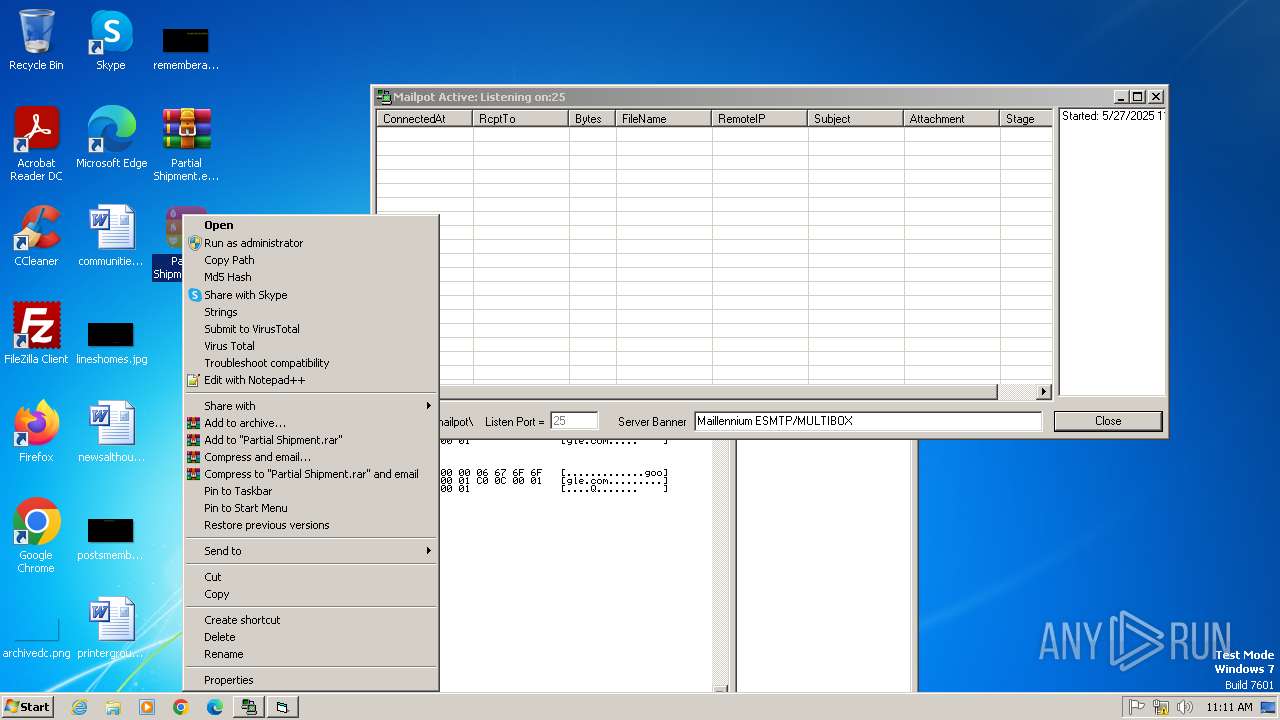
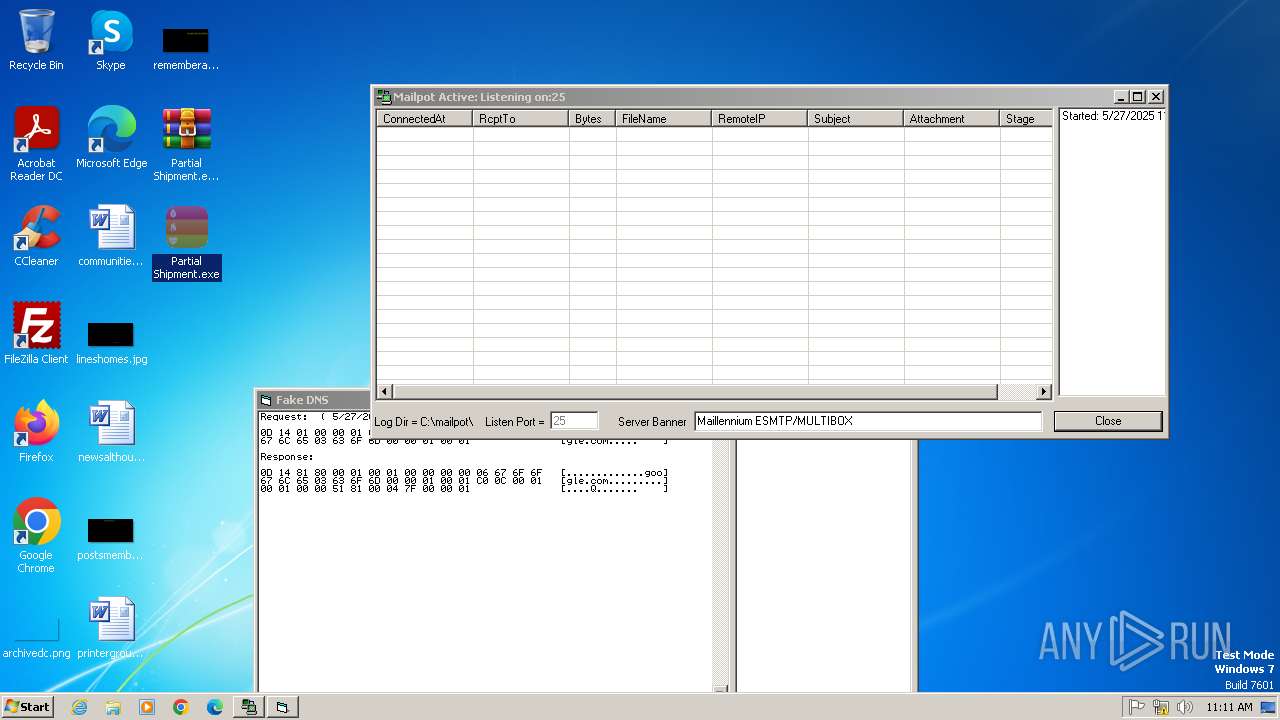
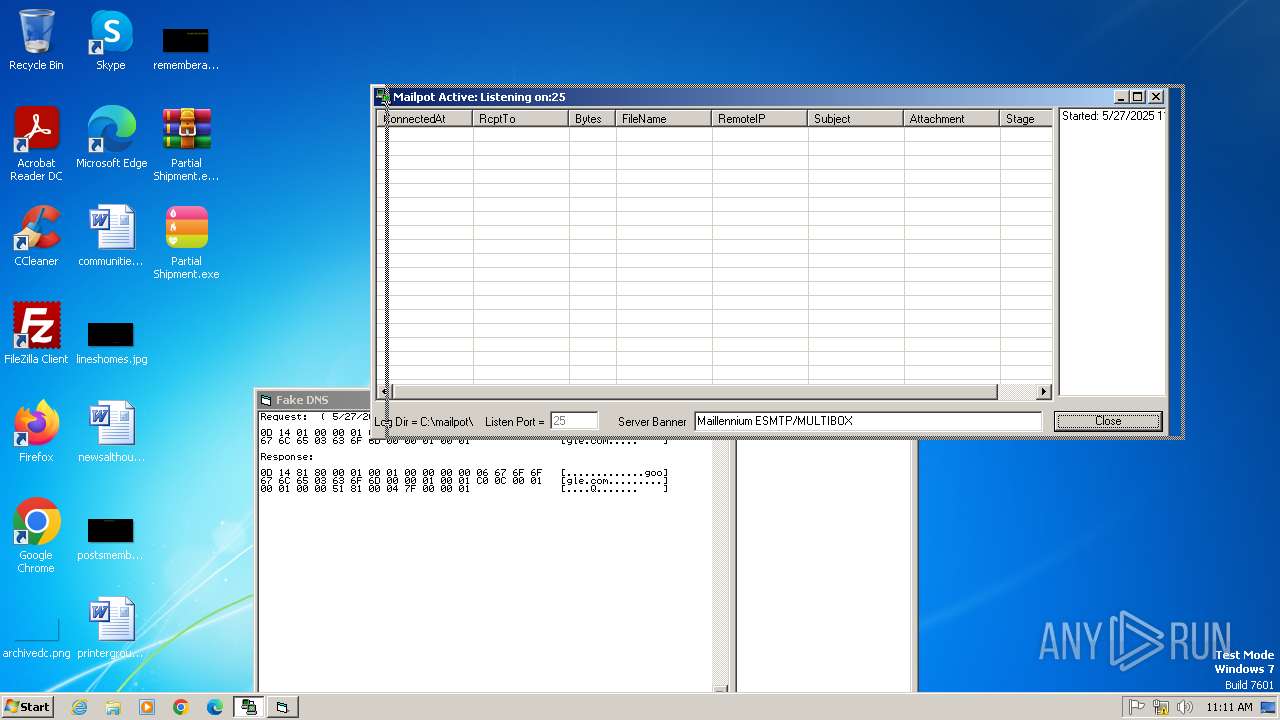
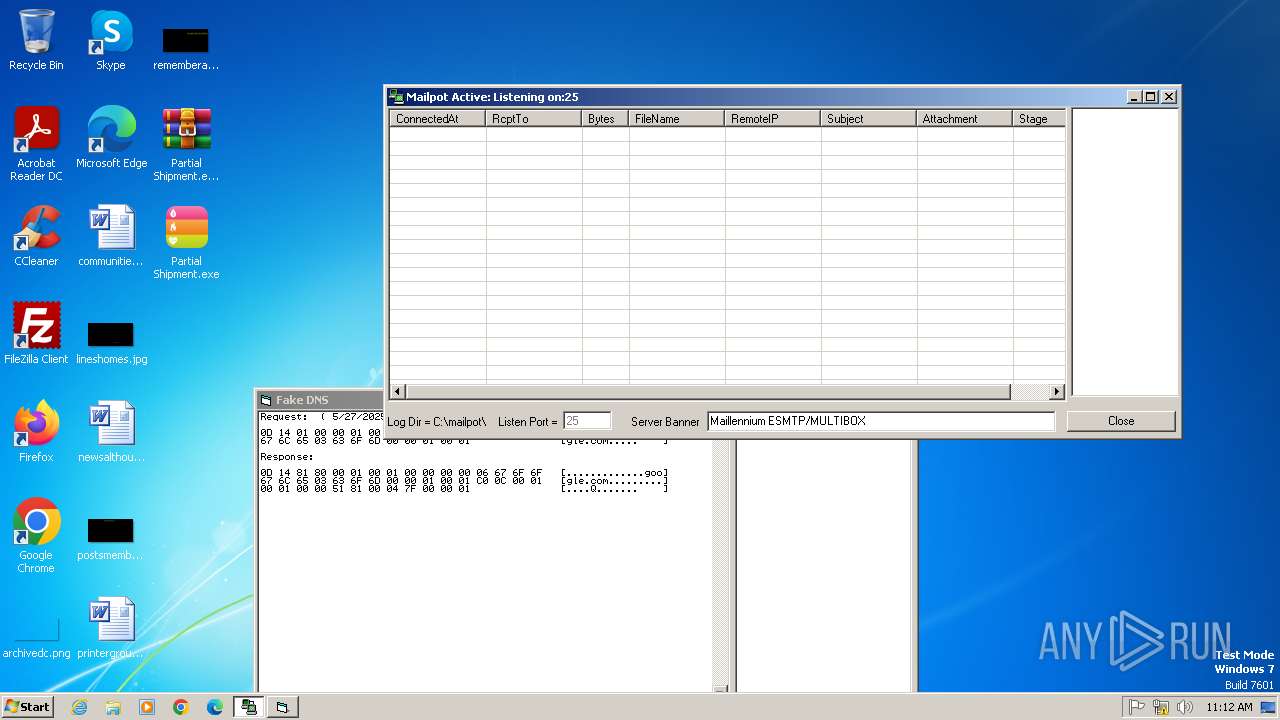
- mail_pot.exe (PID: 3968)
- explorer.exe (PID: 1088)
- Partial Shipment.exe (PID: 4076)
- fakeDNS.exe (PID: 3876)
- explorer.exe (PID: 2196)
- Partial Shipment.exe (PID: 2052)
- Partial Shipment.exe (PID: 1120)
- Partial Shipment.exe (PID: 2000)
- Partial Shipment.exe (PID: 312)
- Partial Shipment.exe (PID: 3824)
- Partial Shipment.exe (PID: 3072)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3168)
Reads mouse settings
- regsvr32.exe (PID: 2984)
- mail_pot.exe (PID: 3968)
Reads the machine GUID from the registry
- mail_pot.exe (PID: 3968)
- ShellExt.exe (PID: 4060)
- Partial Shipment.exe (PID: 1936)
- Partial Shipment.exe (PID: 3508)
- Partial Shipment.exe (PID: 3776)
Reads Microsoft Office registry keys
- mail_pot.exe (PID: 3968)
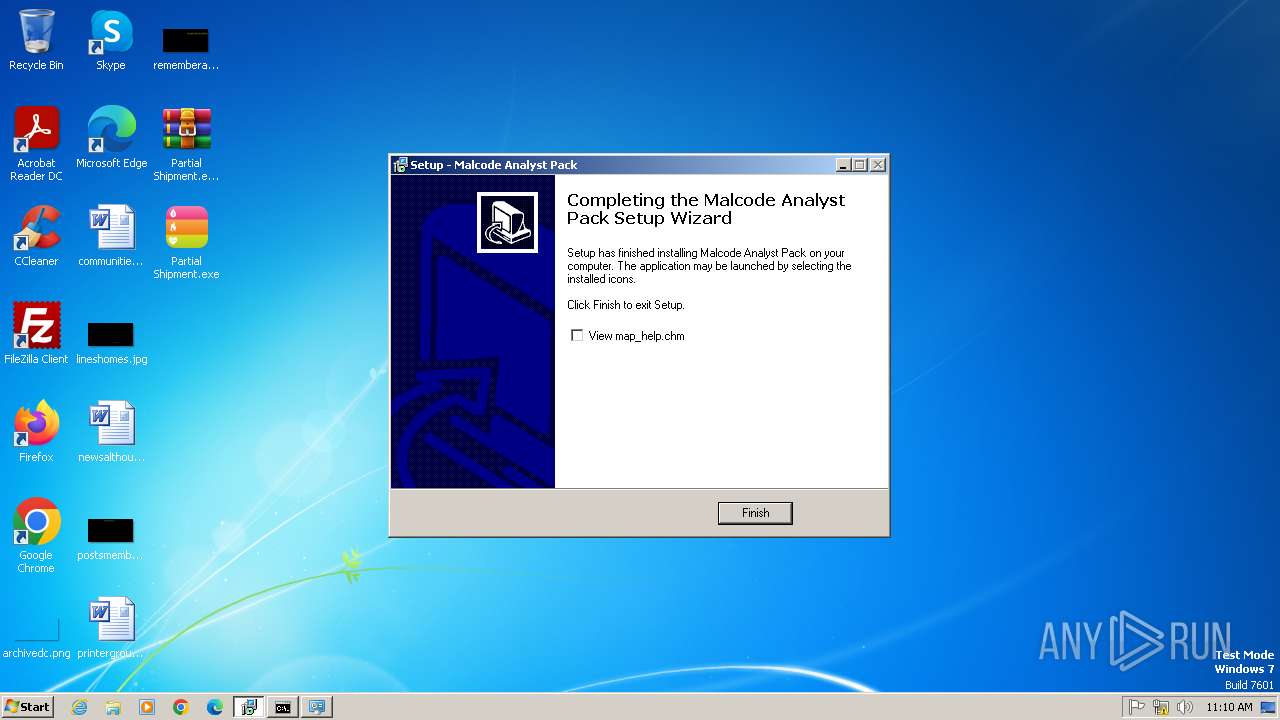
Creates a software uninstall entry
- map_setup.tmp (PID: 1748)
Reads Environment values
- Partial Shipment.exe (PID: 1936)
- fakeDNS.exe (PID: 3876)
- Partial Shipment.exe (PID: 3508)
- Partial Shipment.exe (PID: 3776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(1936) Partial Shipment.exe
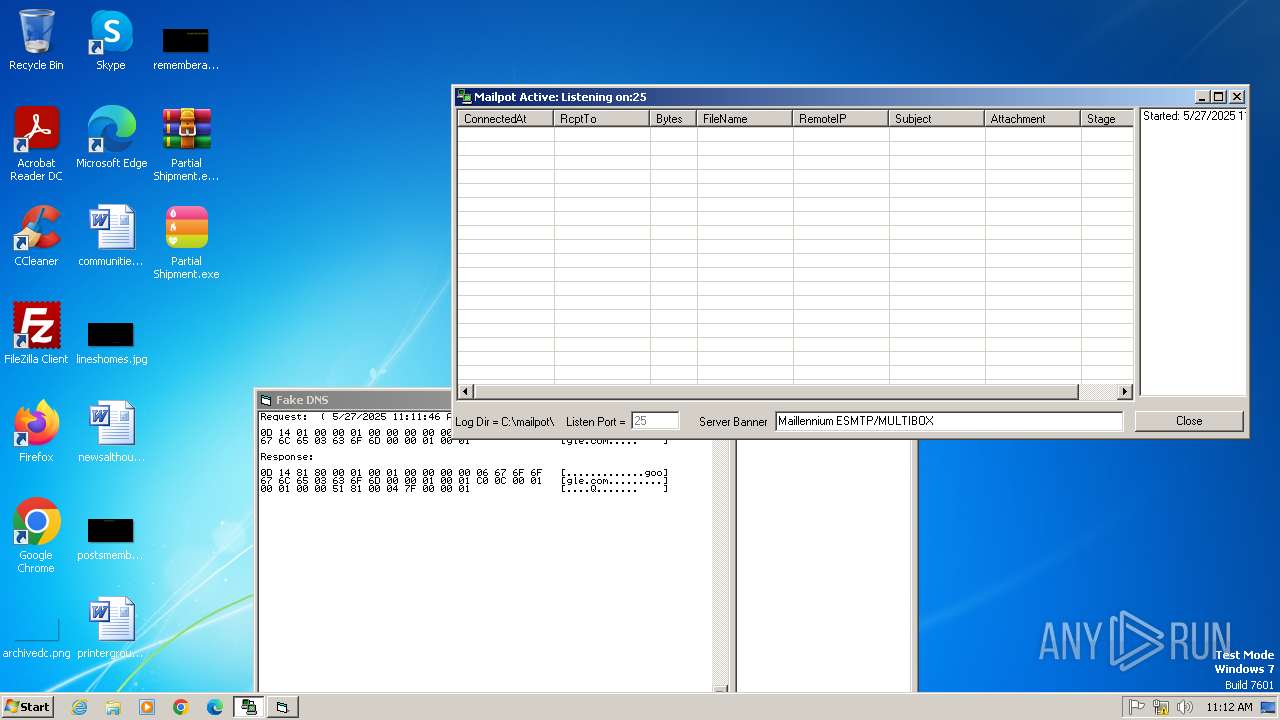
Protocolsmtp
Hostmail.scahe.co.in
Port587
Usernamesj@scahe.co.in
Passwordscaheavy@12345
(PID) Process(3508) Partial Shipment.exe
Protocolsmtp
Hostmail.scahe.co.in
Port587
Usernamesj@scahe.co.in
Passwordscaheavy@12345
(PID) Process(3776) Partial Shipment.exe
Protocolsmtp
Hostmail.scahe.co.in
Port587
Usernamesj@scahe.co.in
Passwordscaheavy@12345
TRiD
| .exe | | | Win32 Executable PowerBASIC/Win 9.x (51.2) |
|---|---|---|
| .exe | | | Inno Setup installer (37.9) |
| .exe | | | Win32 Executable Delphi generic (4.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (2.2) |
| .exe | | | Win32 Executable (generic) (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37376 |
| InitializedDataSize: | 17408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9a54 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
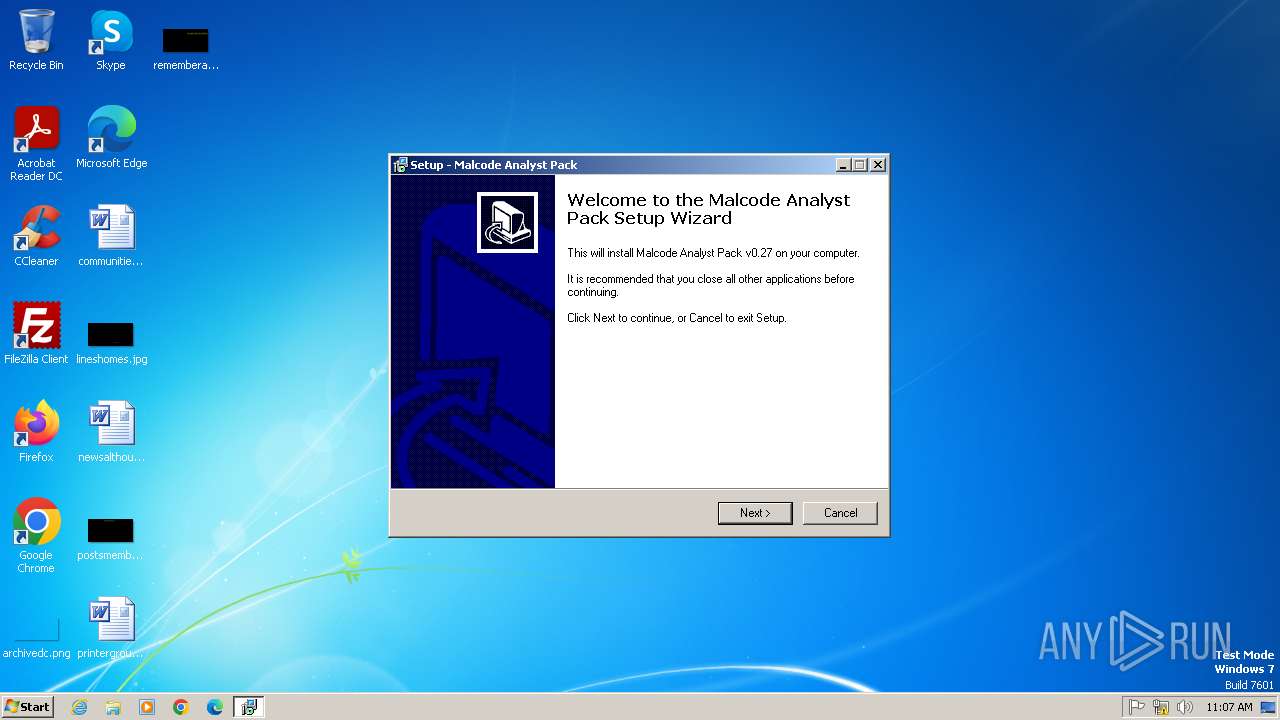
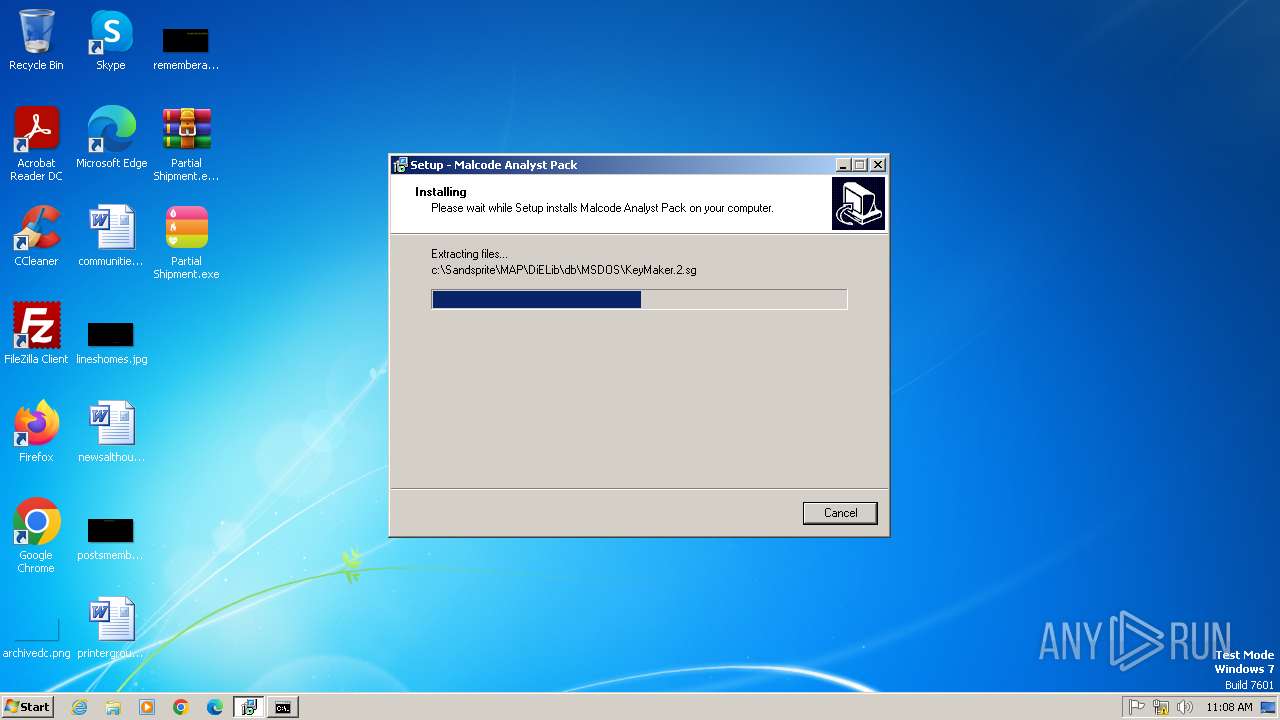
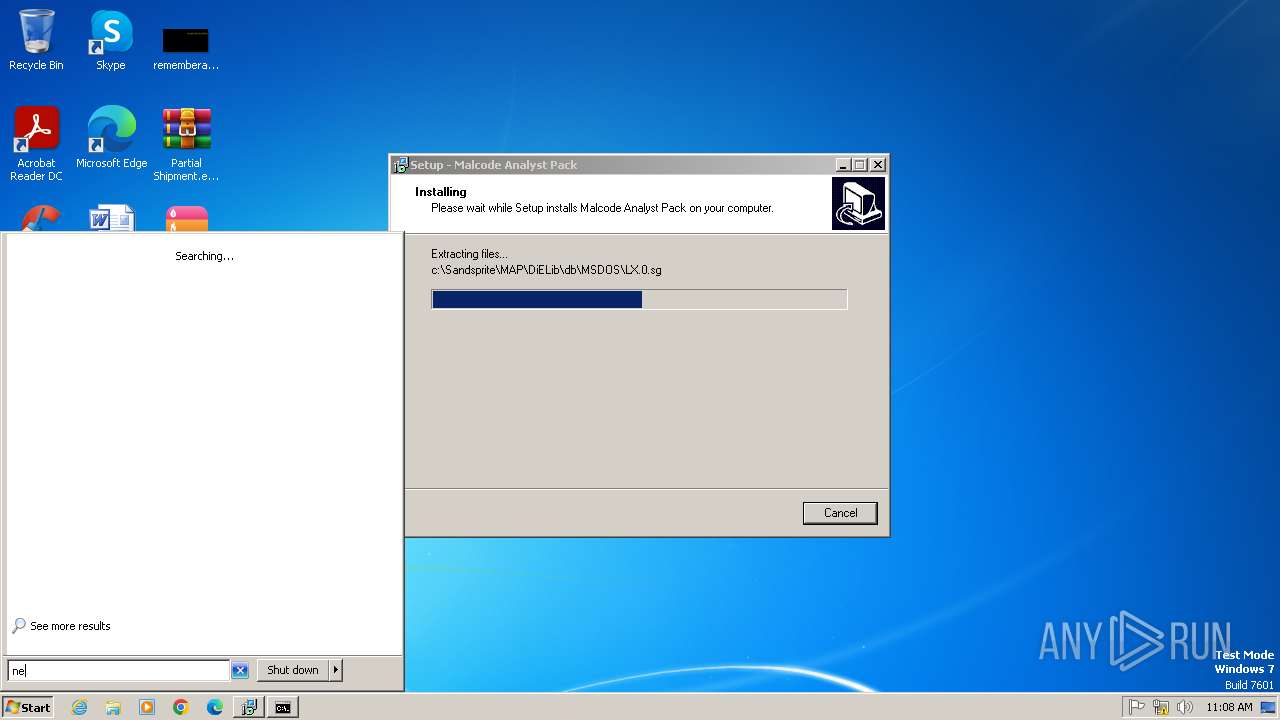
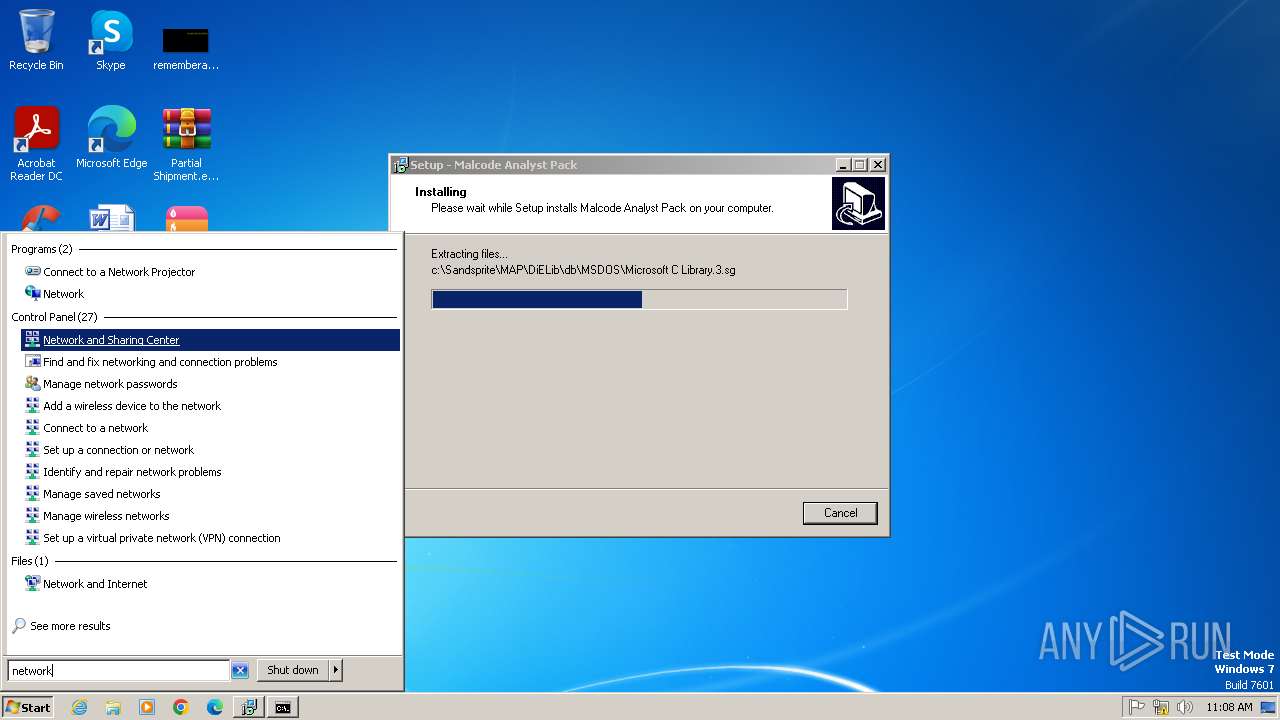
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
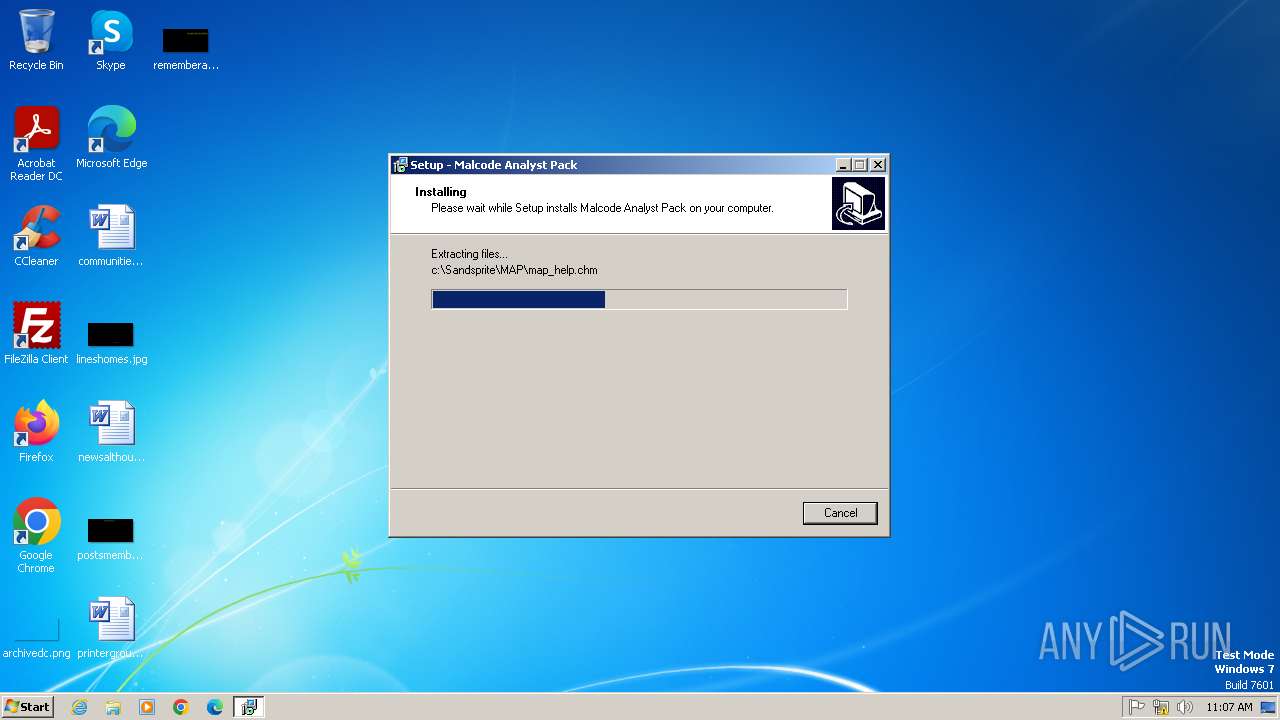
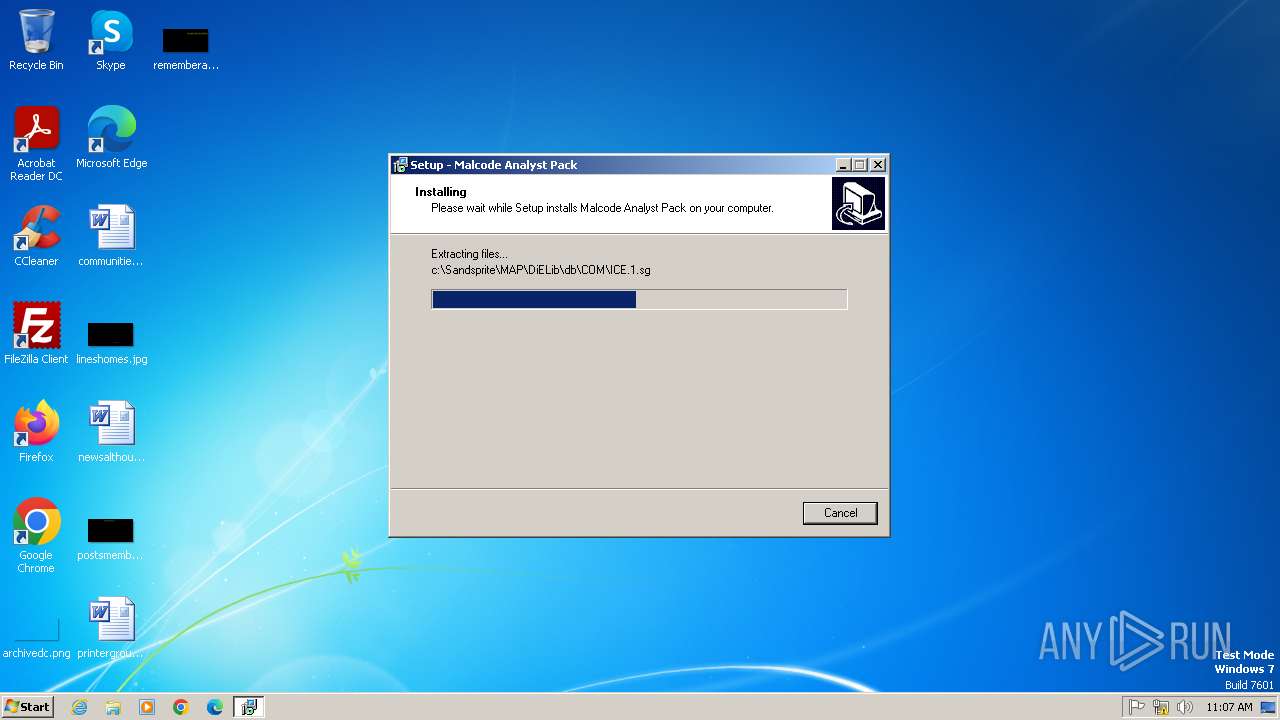
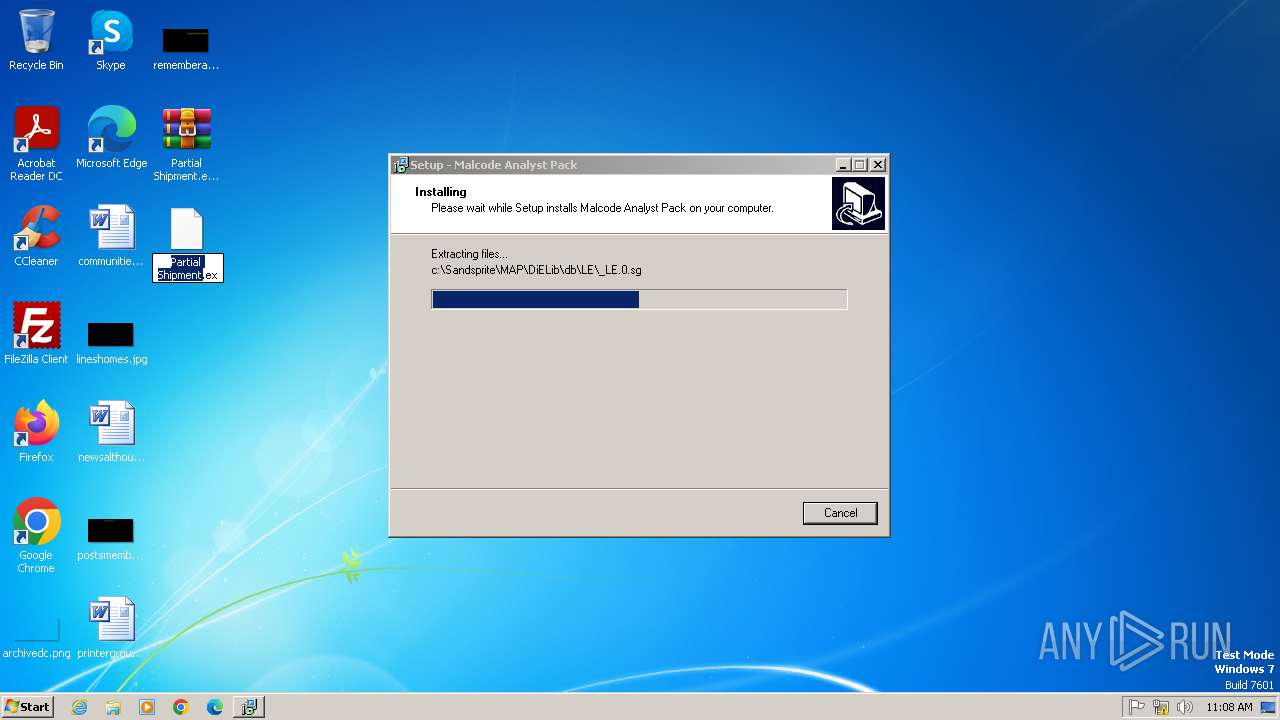
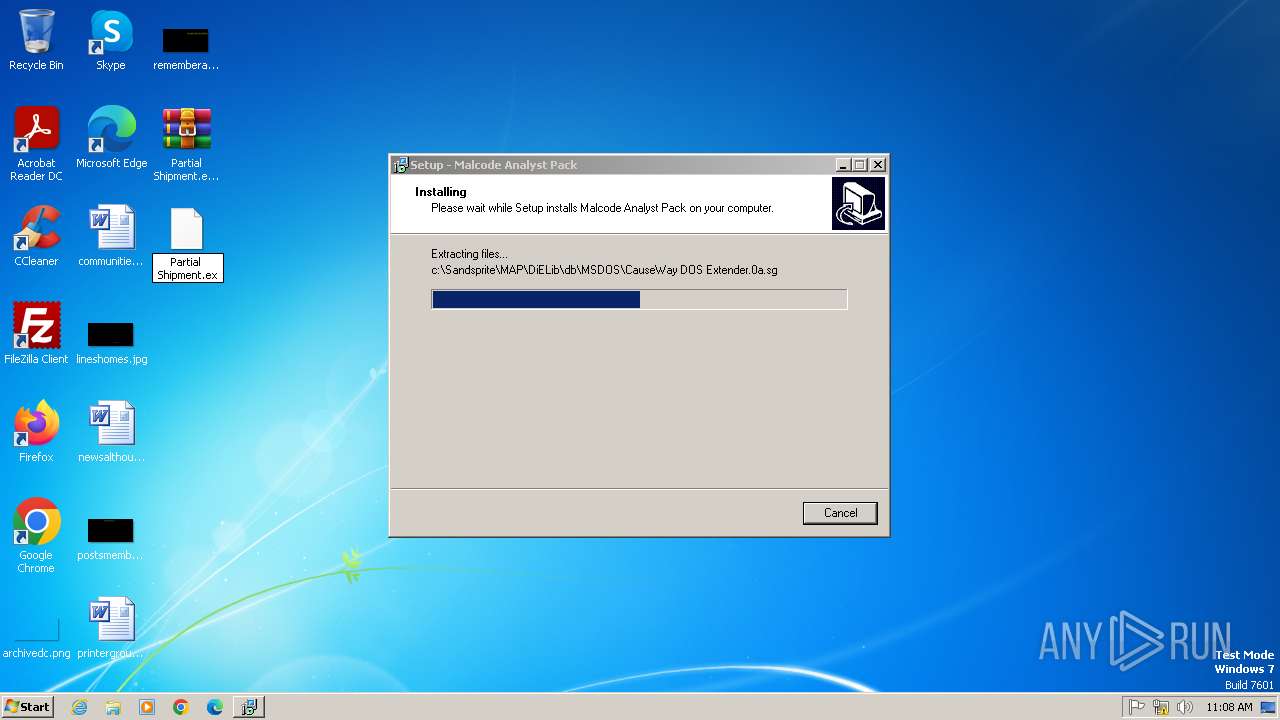
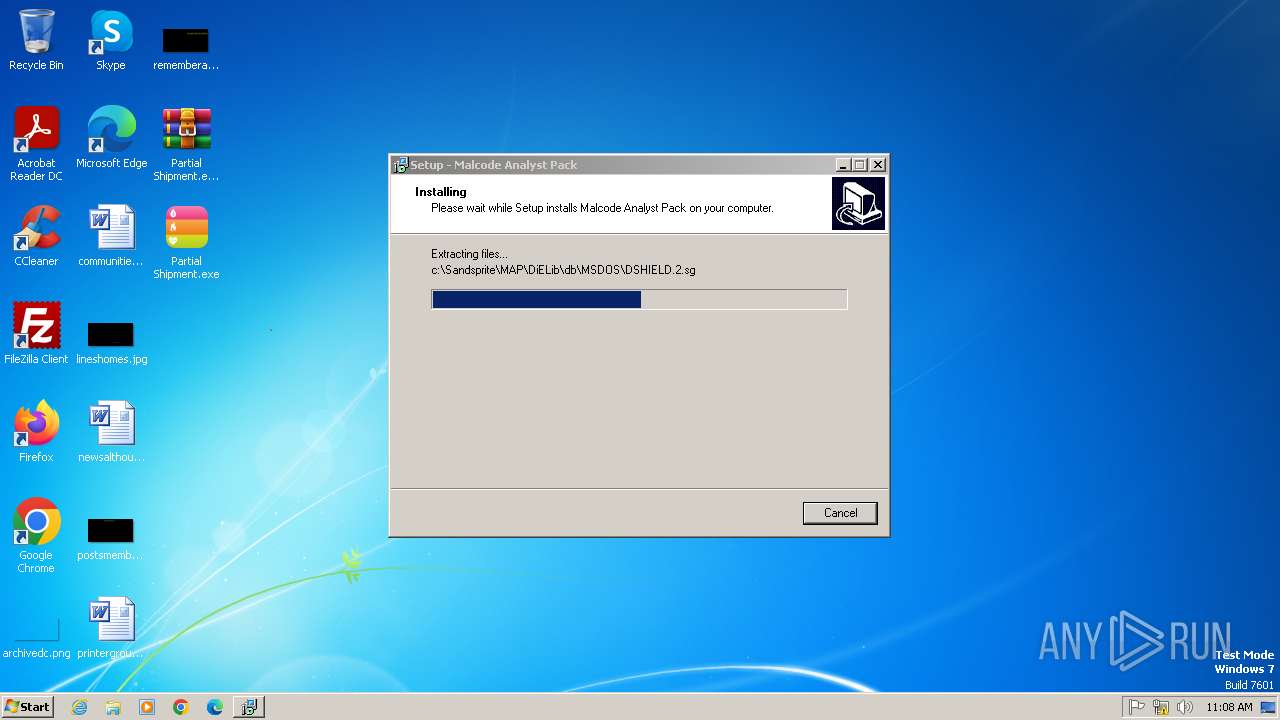
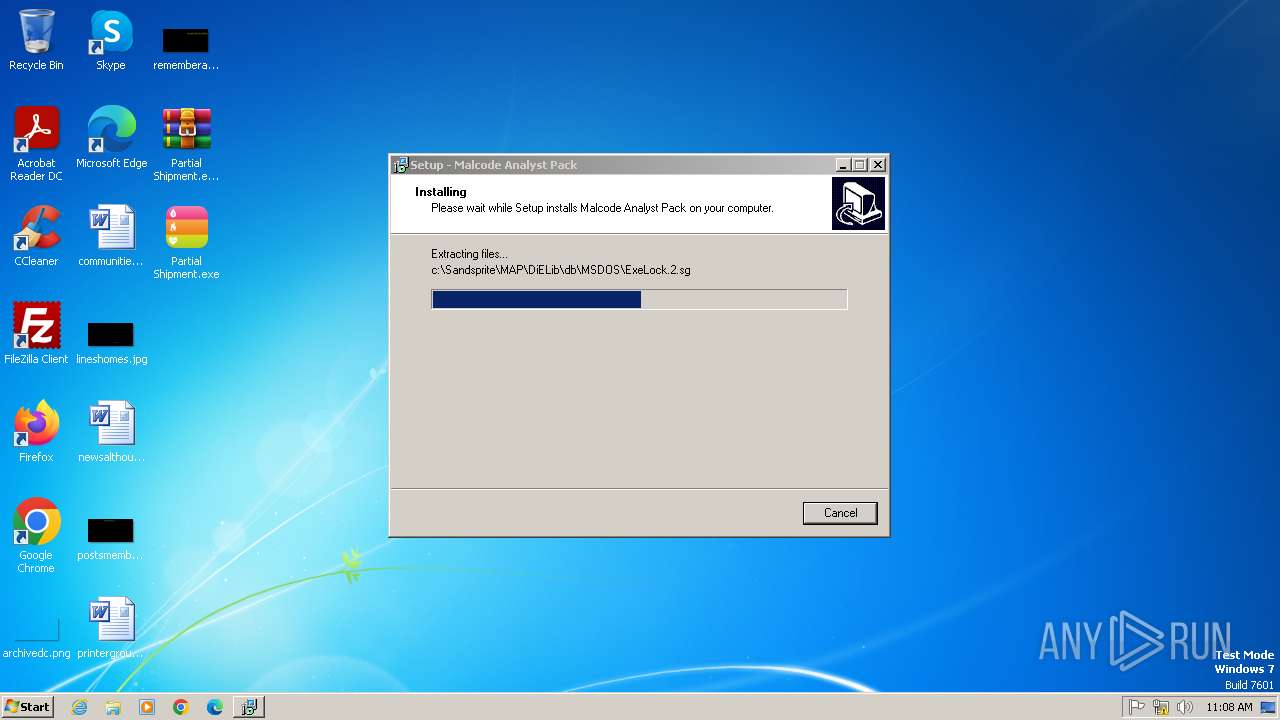
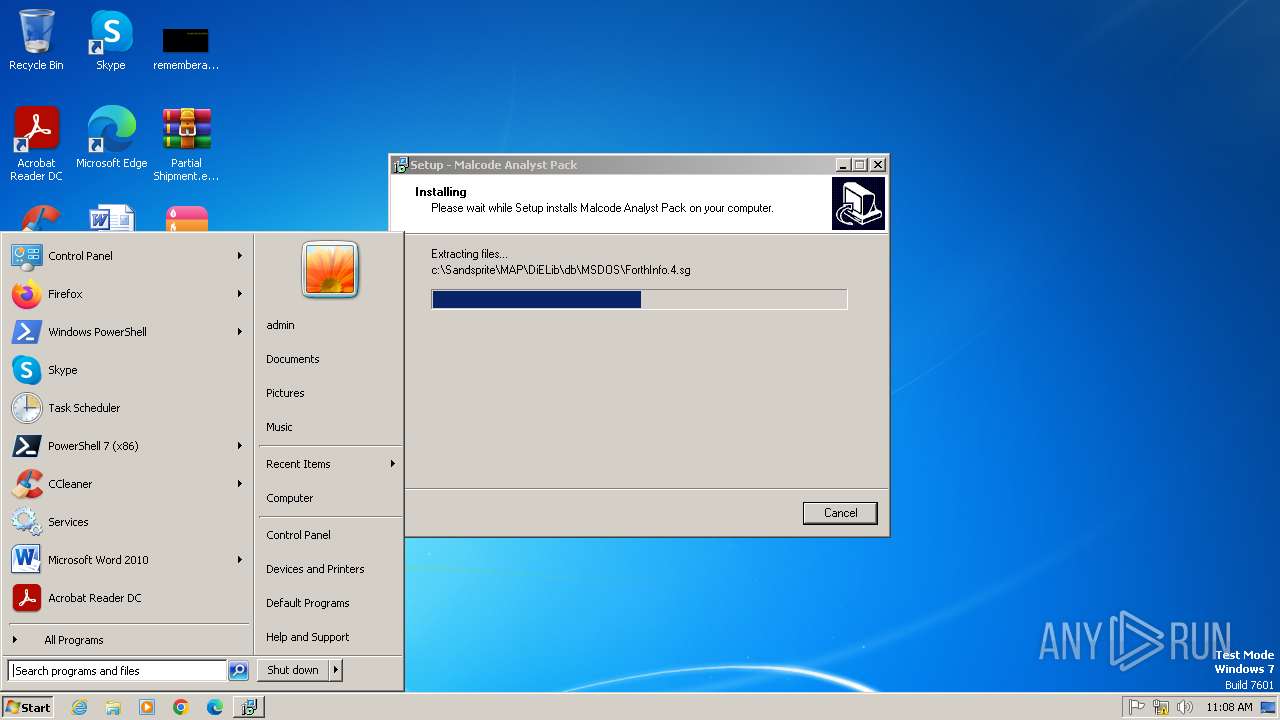
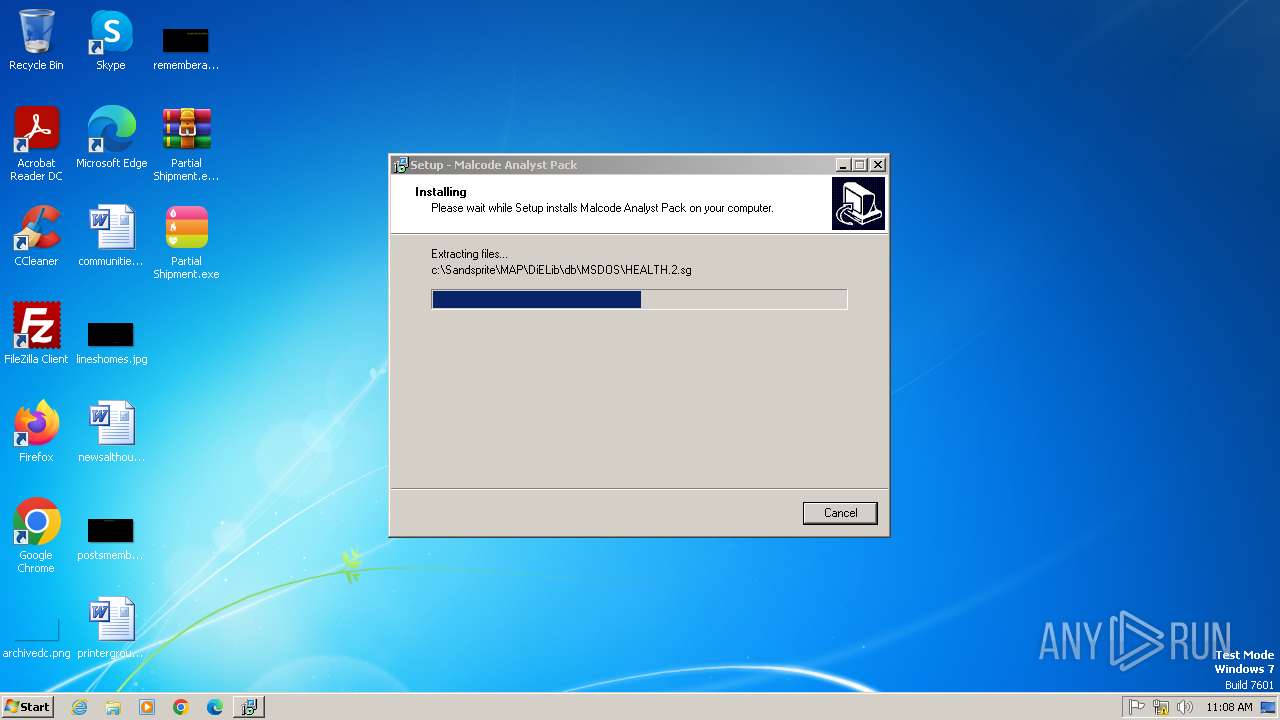
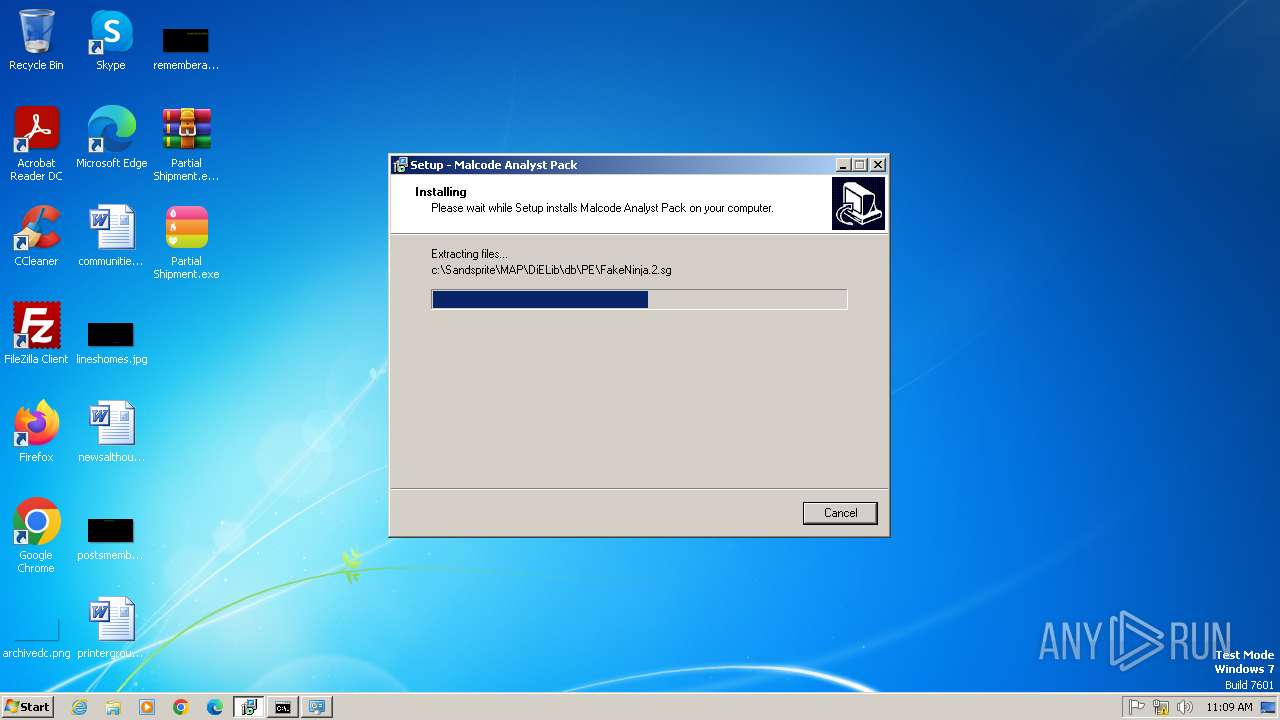
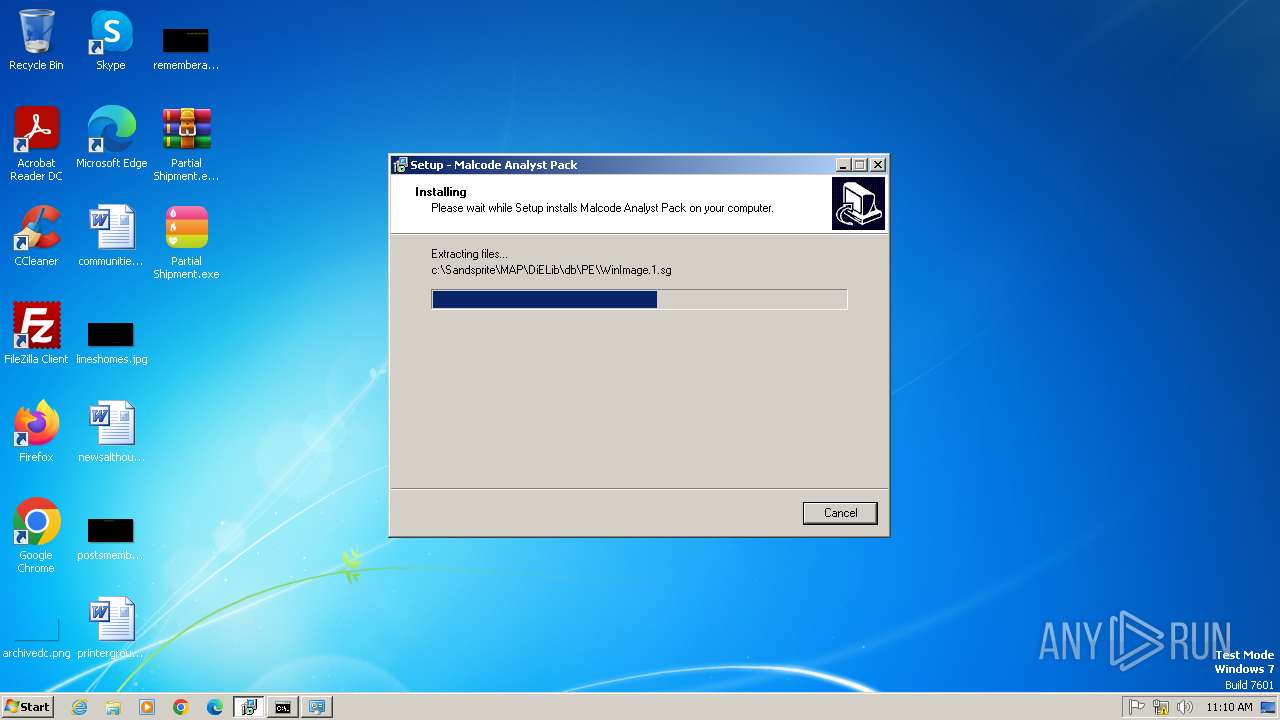
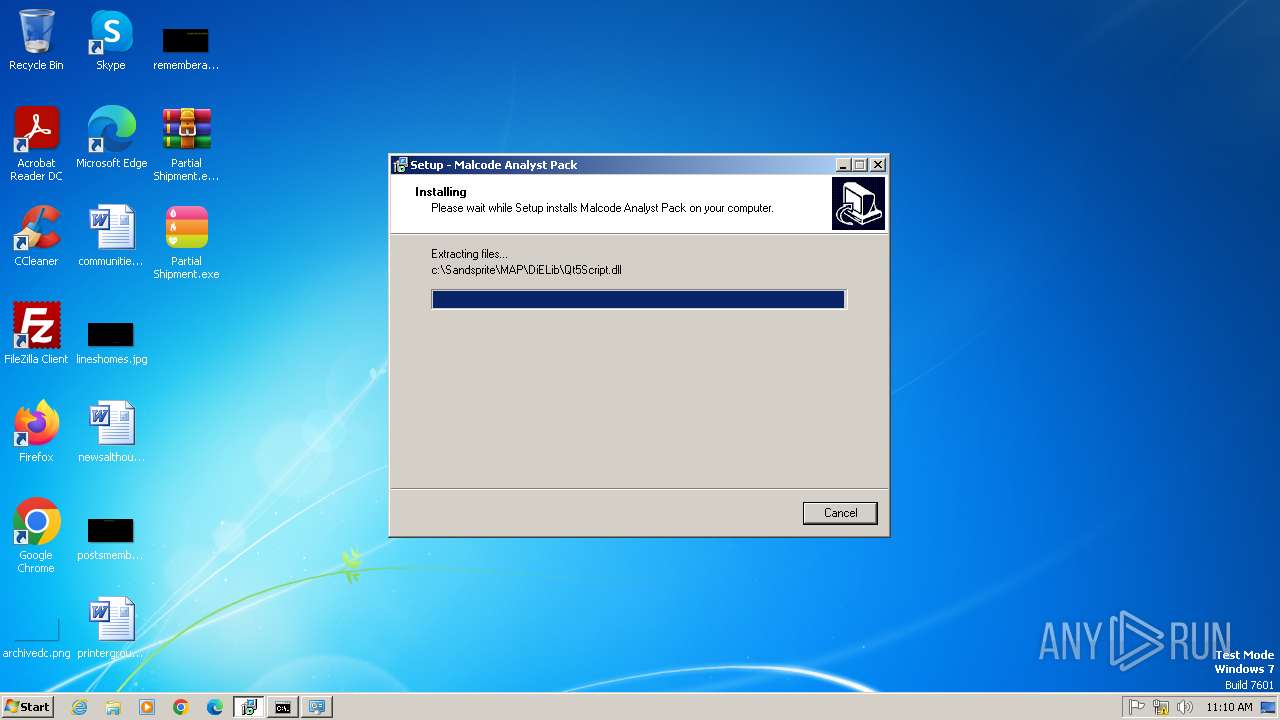
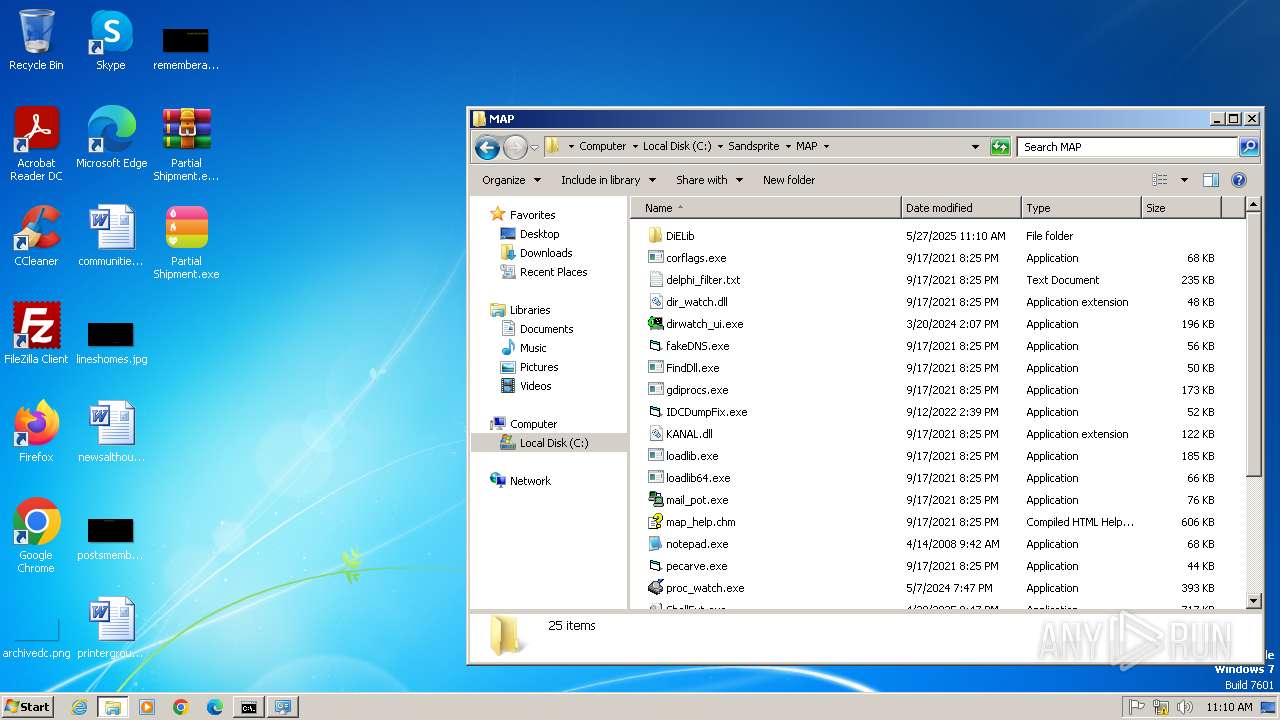
| FileDescription: | Malcode Analyst Pack Setup |
| FileVersion: | |
| LegalCopyright: |
Total processes
88
Monitored processes
35
Malicious processes
11
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Users\admin\Desktop\Partial Shipment.exe" | C:\Users\admin\Desktop\Partial Shipment.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 1088 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1120 | "C:\Users\admin\Desktop\Partial Shipment.exe" | C:\Users\admin\Desktop\Partial Shipment.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 1748 | "C:\Users\admin\AppData\Local\Temp\is-KDGH2.tmp\map_setup.tmp" /SL5="$401B2,5995619,53248,C:\Users\admin\AppData\Local\Temp\map_setup.exe" /SPAWNWND=$301AA /NOTIFYWND=$401AC | C:\Users\admin\AppData\Local\Temp\is-KDGH2.tmp\map_setup.tmp | map_setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
| 1936 | "C:\Users\admin\Desktop\Partial Shipment.exe" | C:\Users\admin\Desktop\Partial Shipment.exe | Partial Shipment.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
AgentTesla(PID) Process(1936) Partial Shipment.exe Protocolsmtp Hostmail.scahe.co.in Port587 Usernamesj@scahe.co.in Passwordscaheavy@12345 | |||||||||||||||
| 2000 | "C:\Users\admin\Desktop\Partial Shipment.exe" | C:\Users\admin\Desktop\Partial Shipment.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2052 | "C:\Users\admin\Desktop\Partial Shipment.exe" | C:\Users\admin\Desktop\Partial Shipment.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2196 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2356 | "C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225547 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2396 | "C:\Users\admin\AppData\Local\Temp\map_setup.exe" /SPAWNWND=$301AA /NOTIFYWND=$401AC | C:\Users\admin\AppData\Local\Temp\map_setup.exe | map_setup.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Malcode Analyst Pack Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
8 962
Read events
8 547
Write events
281
Delete events
134
Modification events
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3168) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3812) dllhost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
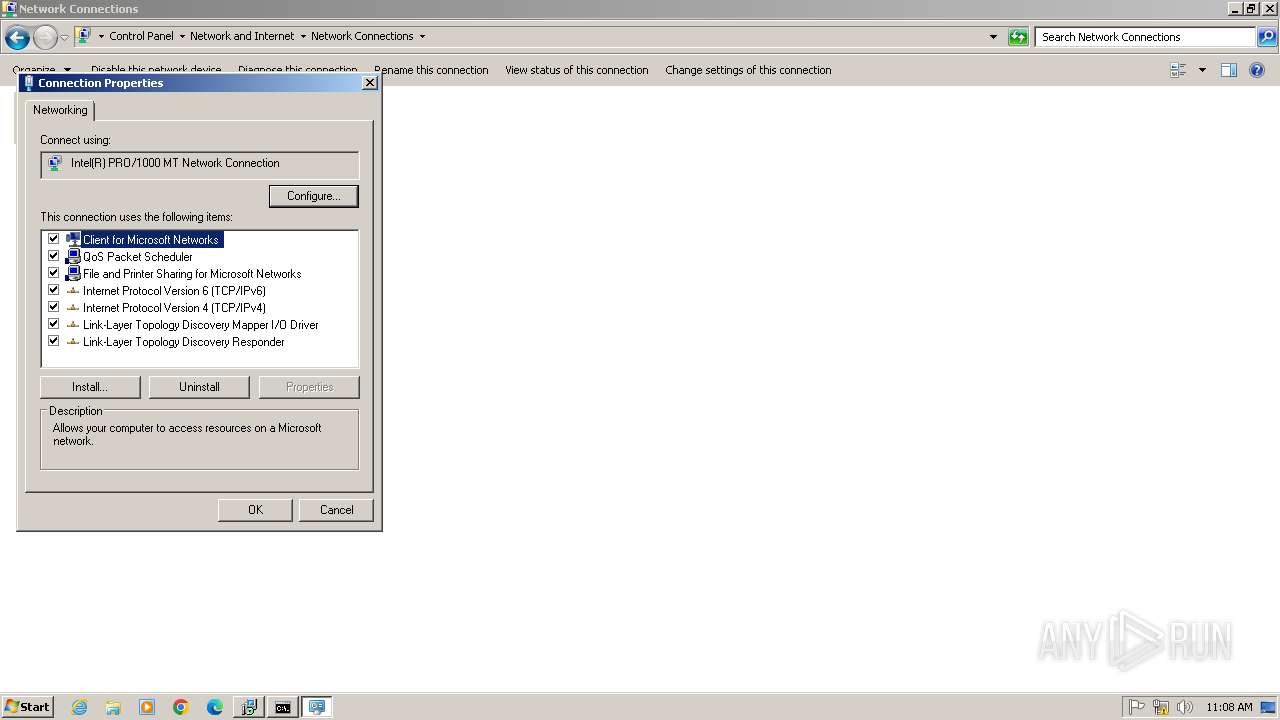
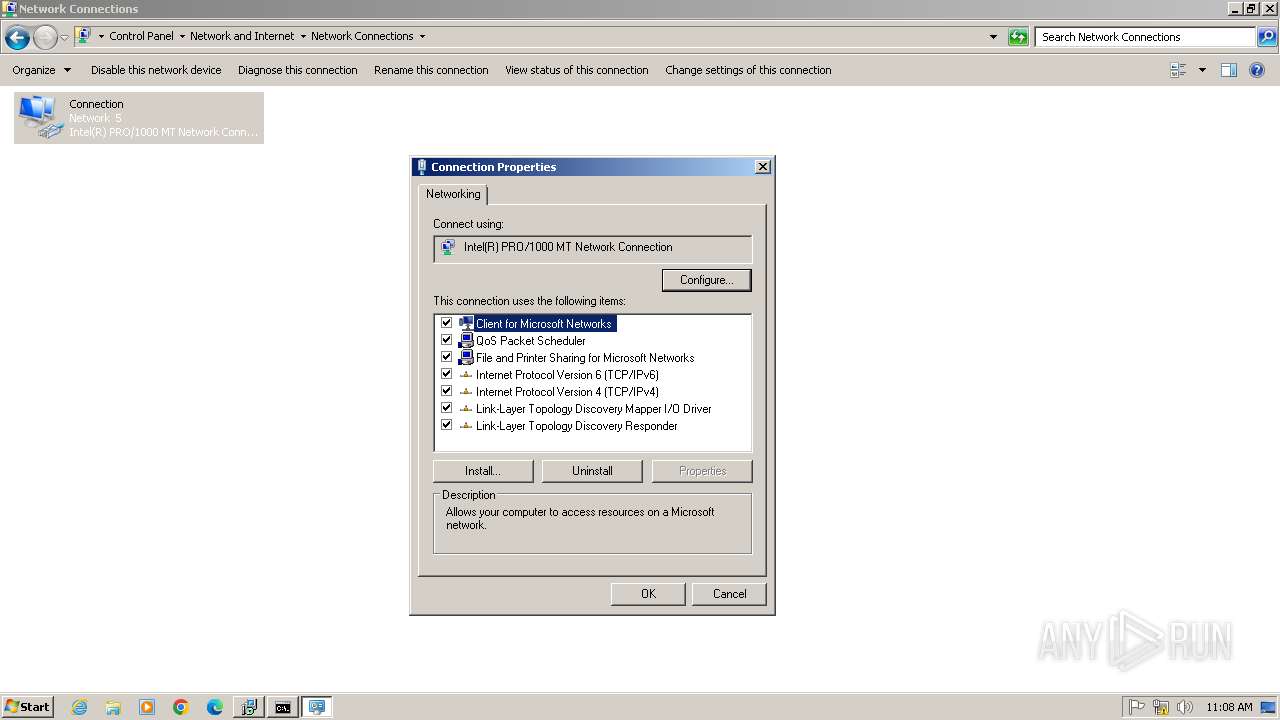
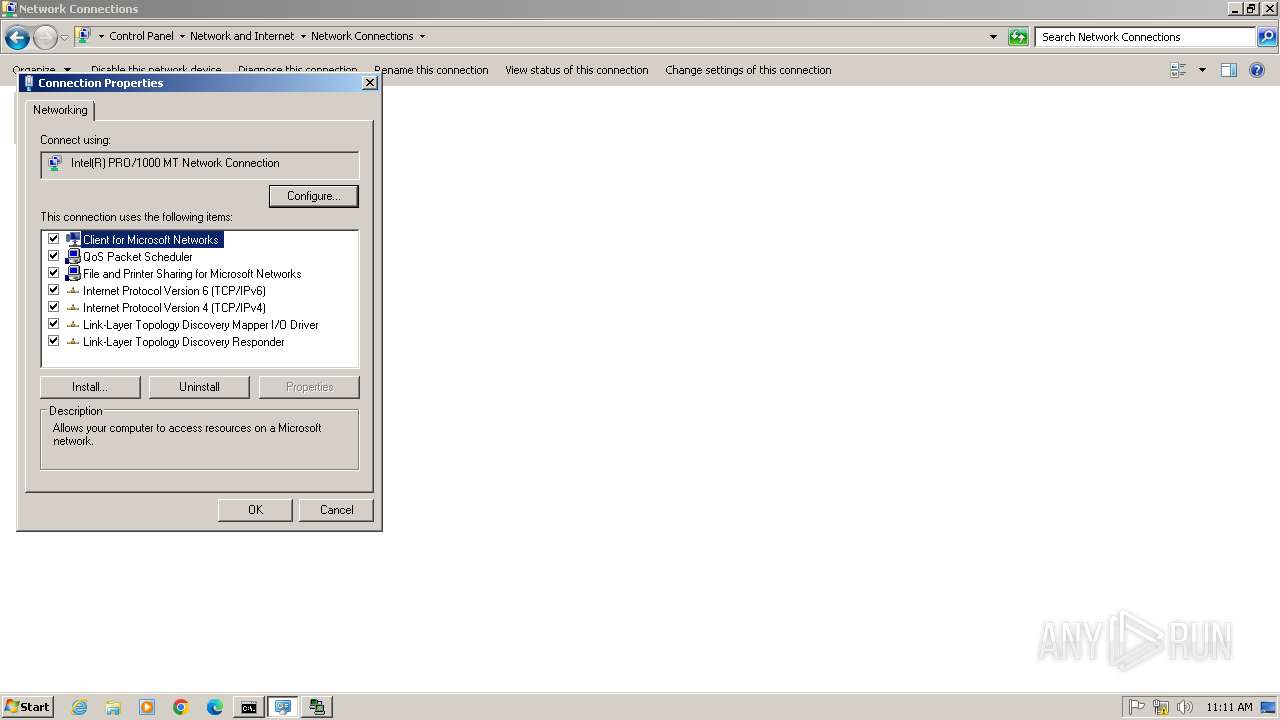
| (PID) Process: | (3812) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Network\NetCfgLockHolder |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1748) map_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | write | Name: | Courier 10,12,15 (120) |
Value: COURF.FON | |||
Executable files
98
Suspicious files
38
Text files
2 962
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1748 | map_setup.tmp | C:\Windows\sppe3.dll | executable | |
MD5:473DB5D8A5FC1FB4B5A435BCA597C3A9 | SHA256:81167418607AFD06660578E33E03995C49EA9BC29DB9095846B1022E5212F64A | |||
| 2396 | map_setup.exe | C:\Users\admin\AppData\Local\Temp\is-KDGH2.tmp\map_setup.tmp | executable | |
MD5:9E30AB5E3F6B43F69F928E6B4FCFD604 | SHA256:AFFBE7F0320F9602D8C51468ECB7BC7960DF4F62AB1A36C05AC2FE2816D175BA | |||
| 1748 | map_setup.tmp | C:\Windows\is-J9CM5.tmp | executable | |
MD5:473DB5D8A5FC1FB4B5A435BCA597C3A9 | SHA256:81167418607AFD06660578E33E03995C49EA9BC29DB9095846B1022E5212F64A | |||
| 2452 | map_setup.exe | C:\Users\admin\AppData\Local\Temp\is-RHIAL.tmp\map_setup.tmp | executable | |
MD5:9E30AB5E3F6B43F69F928E6B4FCFD604 | SHA256:AFFBE7F0320F9602D8C51468ECB7BC7960DF4F62AB1A36C05AC2FE2816D175BA | |||
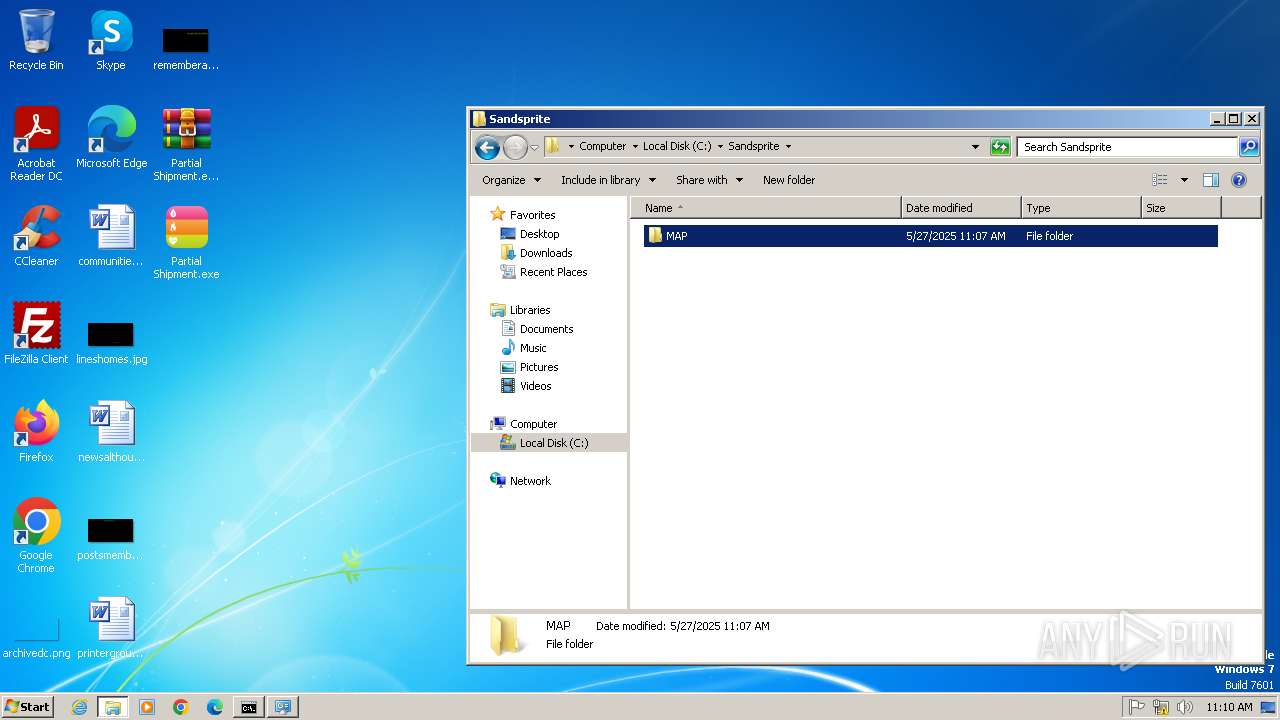
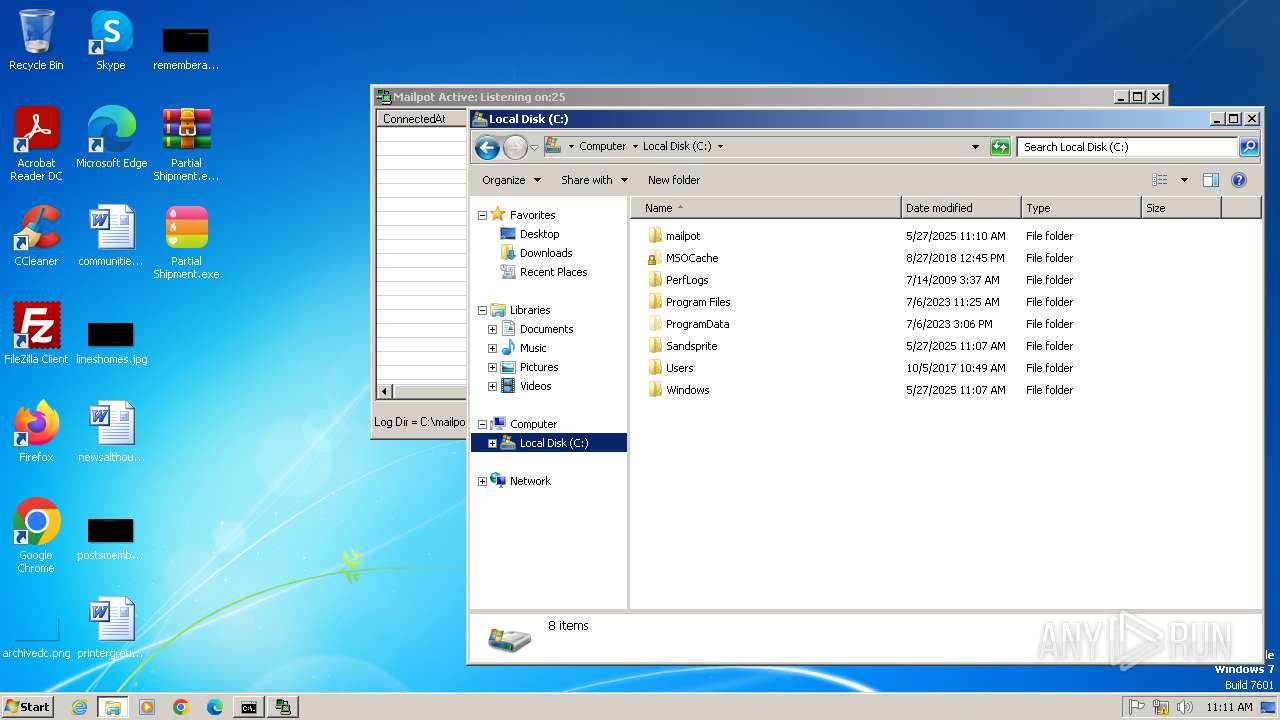
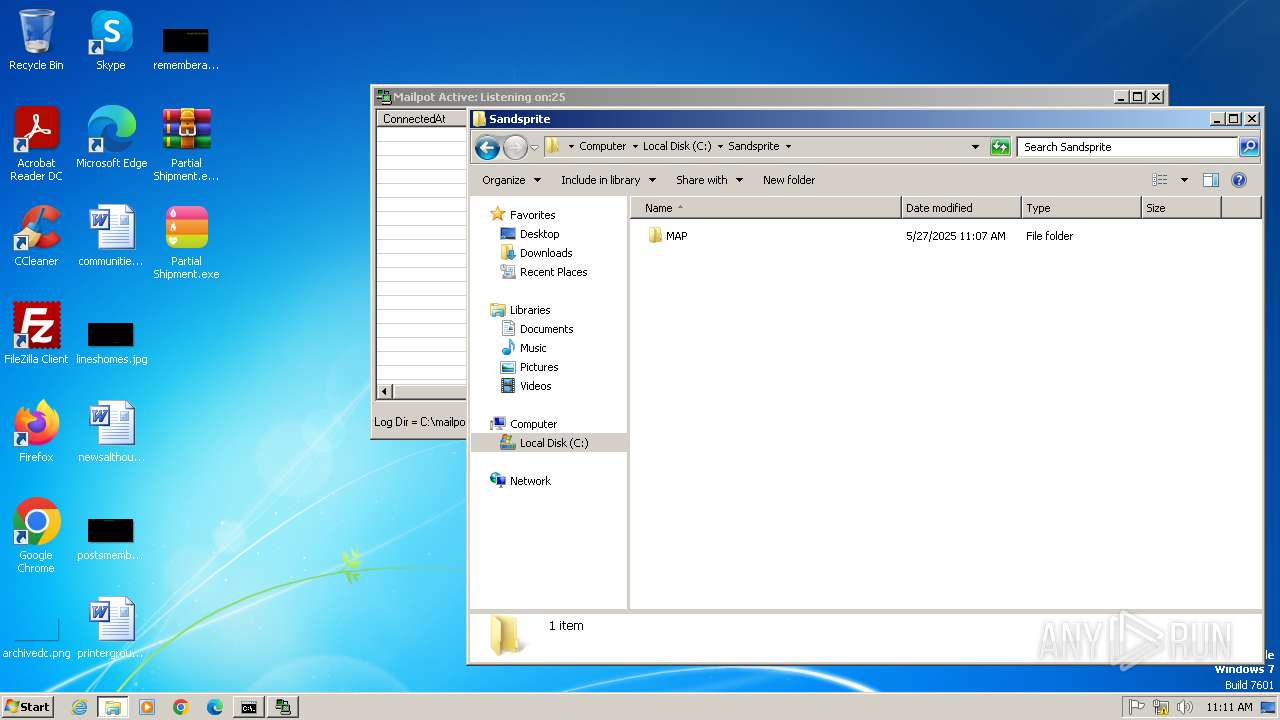
| 1748 | map_setup.tmp | C:\Sandsprite\MAP\unins000.exe | executable | |
MD5:F92285603B19A4928AF4B0B7CD5F2403 | SHA256:6A23972E1C391BA2DADA01FEABCB7CDC8DF2DD3FCA80D7373DF08BE96B5D7A43 | |||
| 1748 | map_setup.tmp | C:\Windows\is-LUFM8.tmp | executable | |
MD5:92781B28FE937464514DE49A89C737F6 | SHA256:AEEDC39C4A7D27CD39B1450DA4C26A4ADE83774EB68E046BD68B918FFD9E532F | |||
| 1748 | map_setup.tmp | C:\Windows\vbUtypes.dll | executable | |
MD5:EF09271336B4B2BF5846929CF0DA8623 | SHA256:81776AA16A70F102E0F4BCF43713BE0BB4C09CD37086C091F91533EB6F2CFDF5 | |||
| 1748 | map_setup.tmp | C:\Sandsprite\MAP\is-BFANN.tmp | executable | |
MD5:F92285603B19A4928AF4B0B7CD5F2403 | SHA256:6A23972E1C391BA2DADA01FEABCB7CDC8DF2DD3FCA80D7373DF08BE96B5D7A43 | |||
| 1748 | map_setup.tmp | C:\Users\admin\AppData\Local\Temp\is-1S0KF.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 1748 | map_setup.tmp | C:\Windows\is-GKR1V.tmp | executable | |
MD5:EF09271336B4B2BF5846929CF0DA8623 | SHA256:81776AA16A70F102E0F4BCF43713BE0BB4C09CD37086C091F91533EB6F2CFDF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
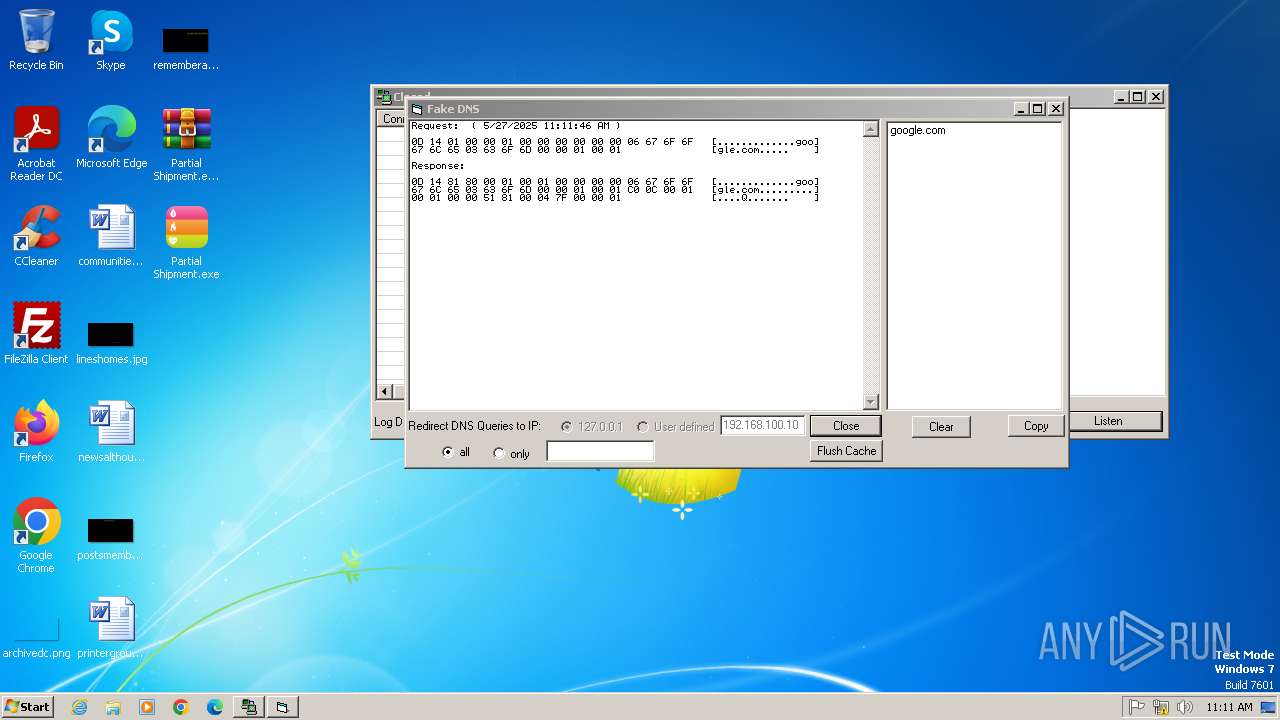
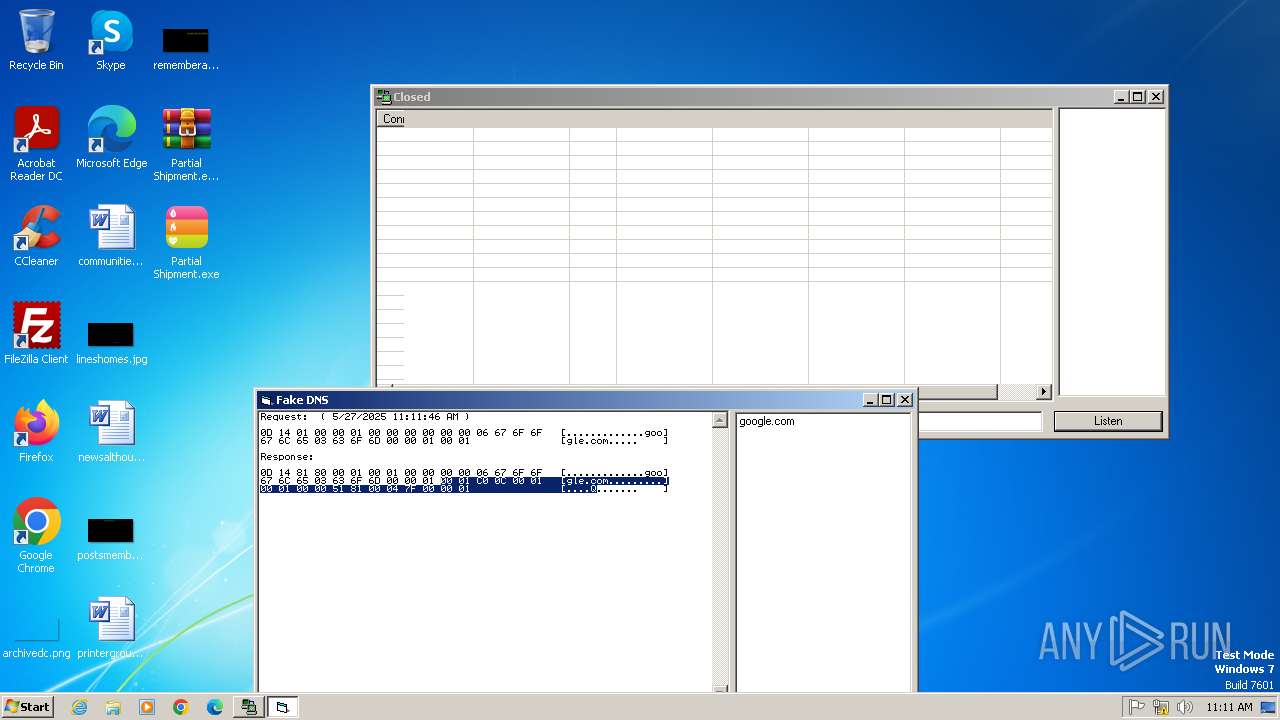
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
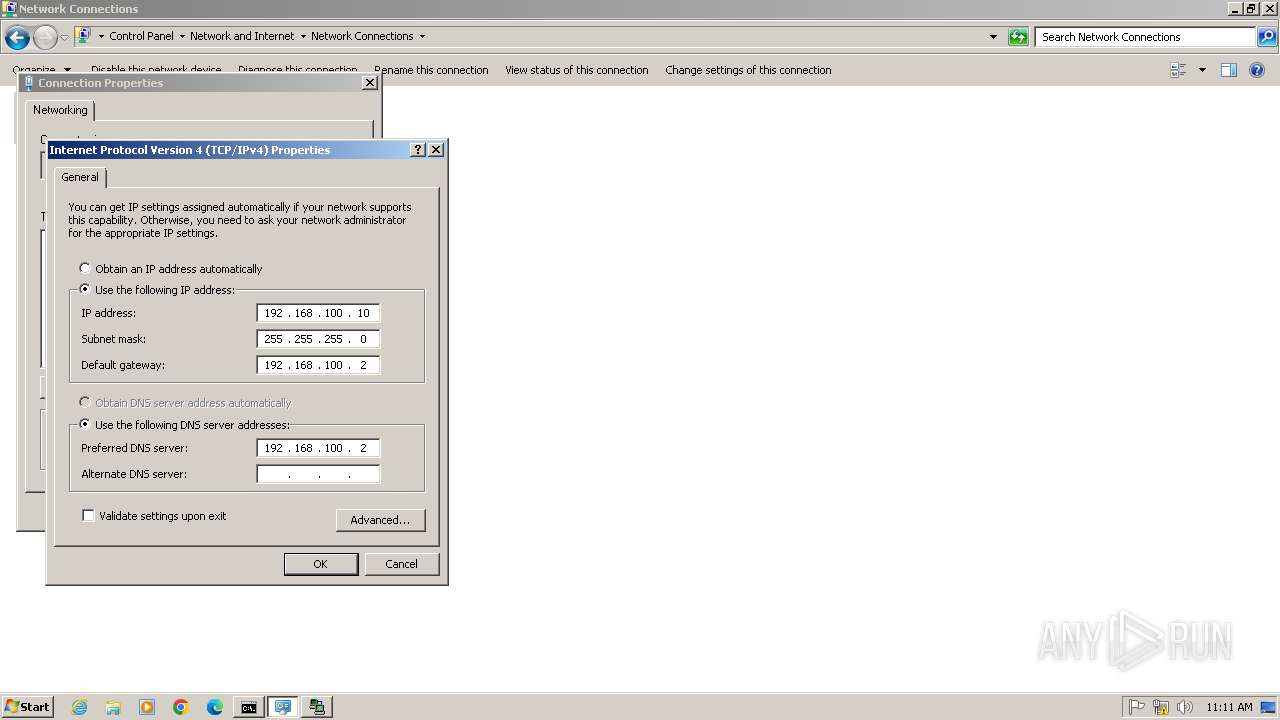
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
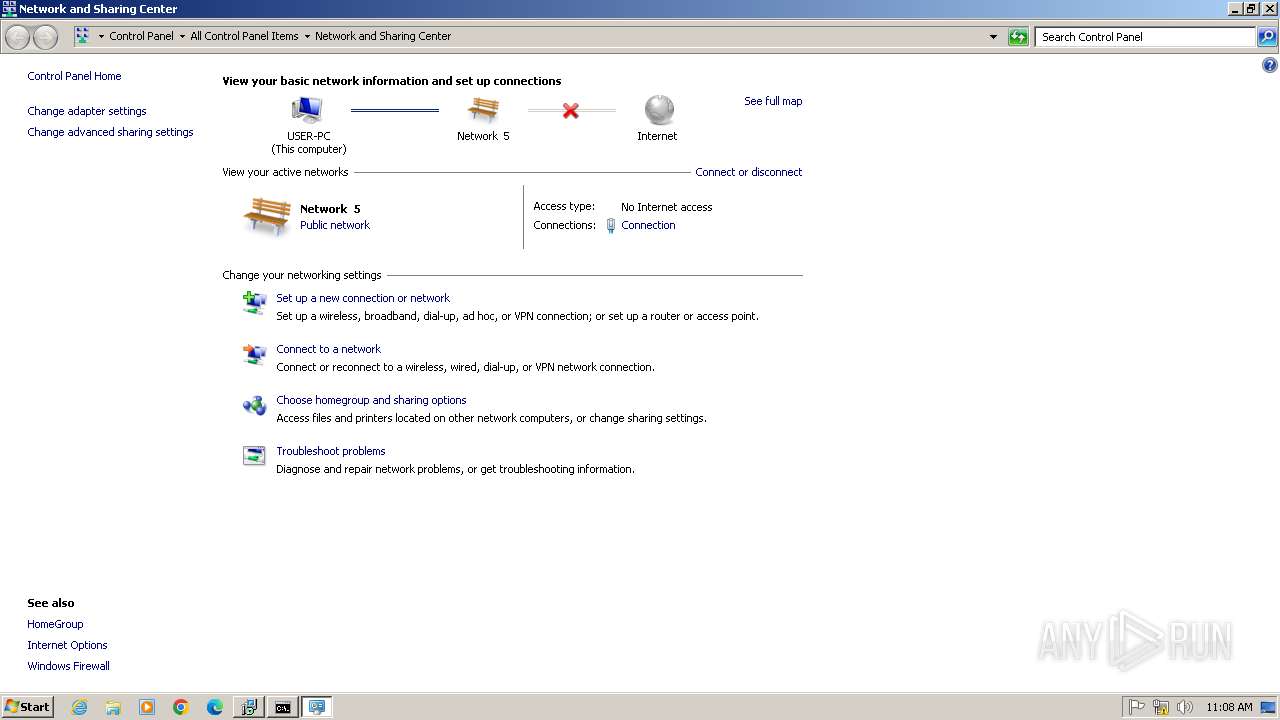
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |