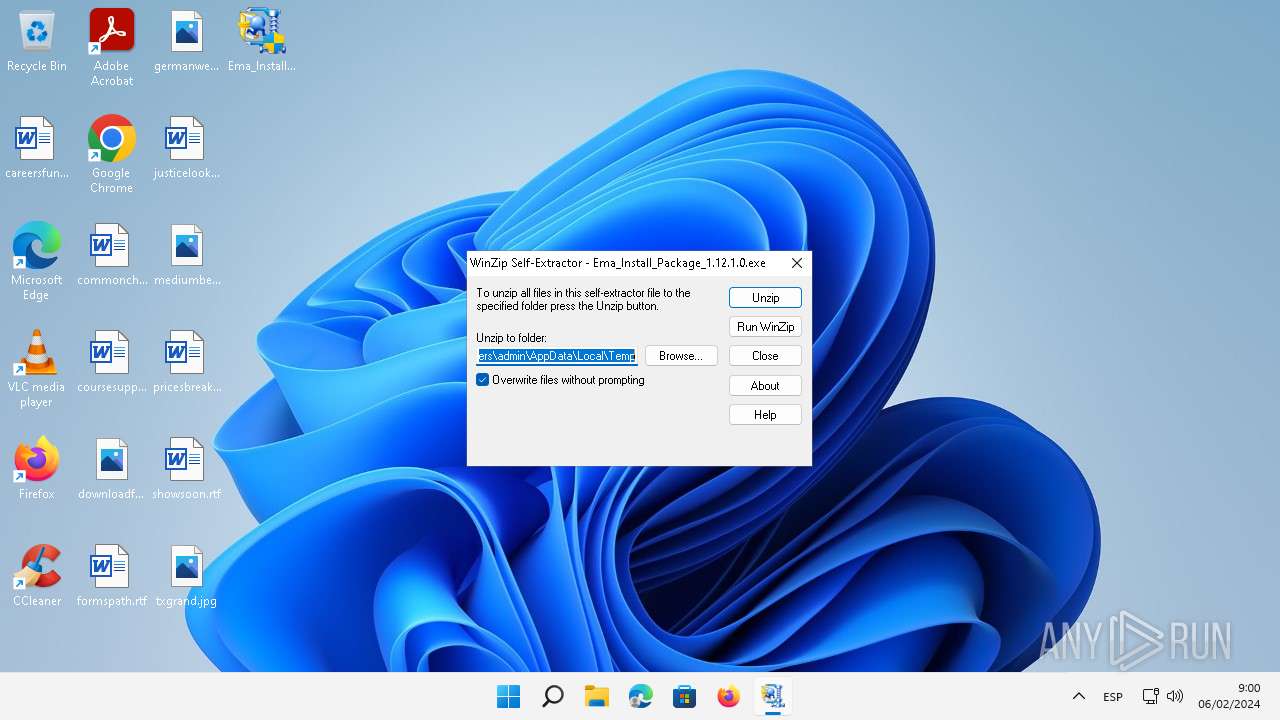
| File name: | Ema_Install_Package_1.12.1.0.exe |
| Full analysis: | https://app.any.run/tasks/8b82ced1-2522-4739-a241-77ac009d9153 |
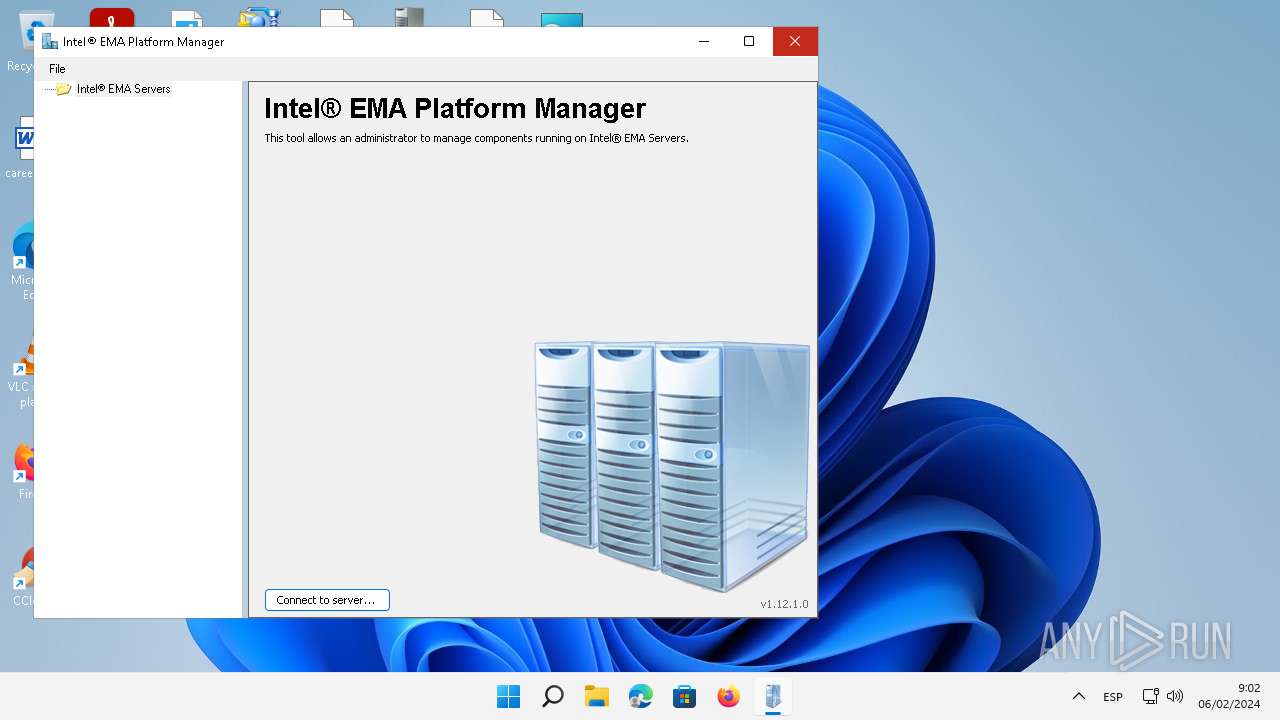
| Verdict: | Malicious activity |
| Threats: | Pikabot is a trojan malware with a focus on loader capabilities. Pikabot is also used for other activities, such as executing commands on the infected system. The earlier versions of the malware made use of extensive code obfuscation to evade detection. Upon infection, it collects system information and sends it to command-and-control servers. |
| Analysis date: | February 06, 2024, 07:59:07 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CA31CC3D93062B8759E82D7663062DD9 |
| SHA1: | 73B597E2708EB140388B932EC2379D9BE5F38A91 |
| SHA256: | A417FCBE7754DB4E2A07CBC3796198F0336DA4FB3D96BB9CC3E27402AC82BAB2 |
| SSDEEP: | 1572864:tJiivlqAQAnC4DaV5qfgvXfkxKwIhUyDV4b:twgRTnC0aV5qfKwsUyDVq |
MALICIOUS
Drops the executable file immediately after the start
- Ema_Install_Package_1.12.1.0.exe (PID: 472)
- Ema_Install_Package_1.12.1.0.exe (PID: 2772)
- msiexec.exe (PID: 3924)
Pikabot has been detected
- rundll32.exe (PID: 5052)
- rundll32.exe (PID: 5152)
- rundll32.exe (PID: 1672)
- rundll32.exe (PID: 2028)
- rundll32.exe (PID: 4732)
Creates a writable file in the system directory
- PlatformManagerServer.exe (PID: 1664)
- WerFault.exe (PID: 3656)
SUSPICIOUS
Starts itself from another location
- Ema_Install_Package_1.12.1.0.exe (PID: 5340)
- Ema_Install_Package_1.12.1.0.exe (PID: 2996)
Process drops legitimate windows executable
- Ema_Install_Package_1.12.1.0.exe (PID: 472)
- Ema_Install_Package_1.12.1.0.exe (PID: 2772)
- msiexec.exe (PID: 3924)
Executable content was dropped or overwritten
- Ema_Install_Package_1.12.1.0.exe (PID: 472)
- Ema_Install_Package_1.12.1.0.exe (PID: 2772)
- rundll32.exe (PID: 5052)
- rundll32.exe (PID: 5152)
- rundll32.exe (PID: 1672)
- rundll32.exe (PID: 2028)
- rundll32.exe (PID: 4732)
Reads the Internet Settings
- msiexec.exe (PID: 5124)
- EMAServerInstaller.exe (PID: 4000)
The process creates files with name similar to system file names
- rundll32.exe (PID: 5052)
Checks Windows Trust Settings
- msiexec.exe (PID: 3924)
Executes application which crashes
- PlatformManagerServer.exe (PID: 1664)
Executes as Windows Service
- PlatformManagerServer.exe (PID: 1664)
INFO
Checks supported languages
- Ema_Install_Package_1.12.1.0.exe (PID: 5340)
- Ema_Install_Package_1.12.1.0.exe (PID: 472)
- Ema_Install_Package_1.12.1.0.exe (PID: 2996)
- Ema_Install_Package_1.12.1.0.exe (PID: 2772)
- EMAServerInstaller.exe (PID: 4000)
- msiexec.exe (PID: 3924)
- msiexec.exe (PID: 1112)
- msiexec.exe (PID: 4332)
- msiexec.exe (PID: 5896)
- PlatformManagerServer.exe (PID: 1664)
- PlatformManager.exe (PID: 2692)
Reads the computer name
- Ema_Install_Package_1.12.1.0.exe (PID: 472)
- Ema_Install_Package_1.12.1.0.exe (PID: 2772)
- EMAServerInstaller.exe (PID: 4000)
- msiexec.exe (PID: 3924)
- msiexec.exe (PID: 1112)
- msiexec.exe (PID: 4332)
- PlatformManagerServer.exe (PID: 1664)
- msiexec.exe (PID: 5896)
- PlatformManager.exe (PID: 2692)
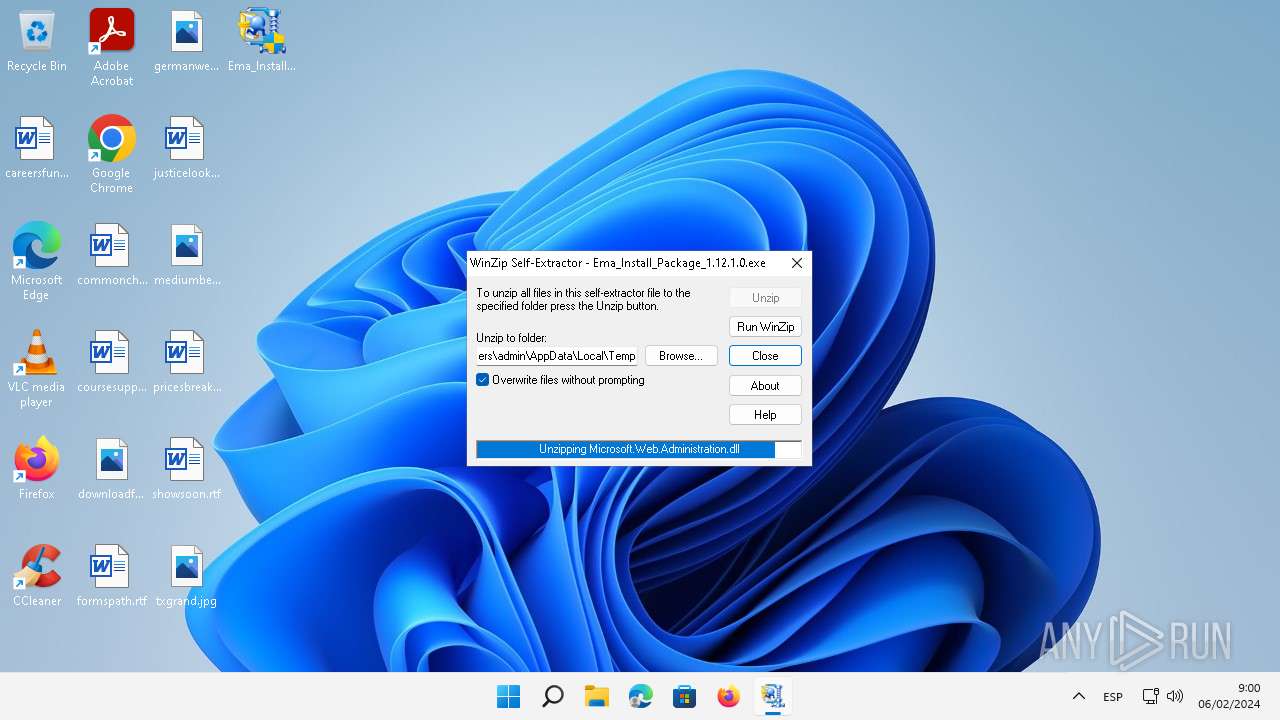
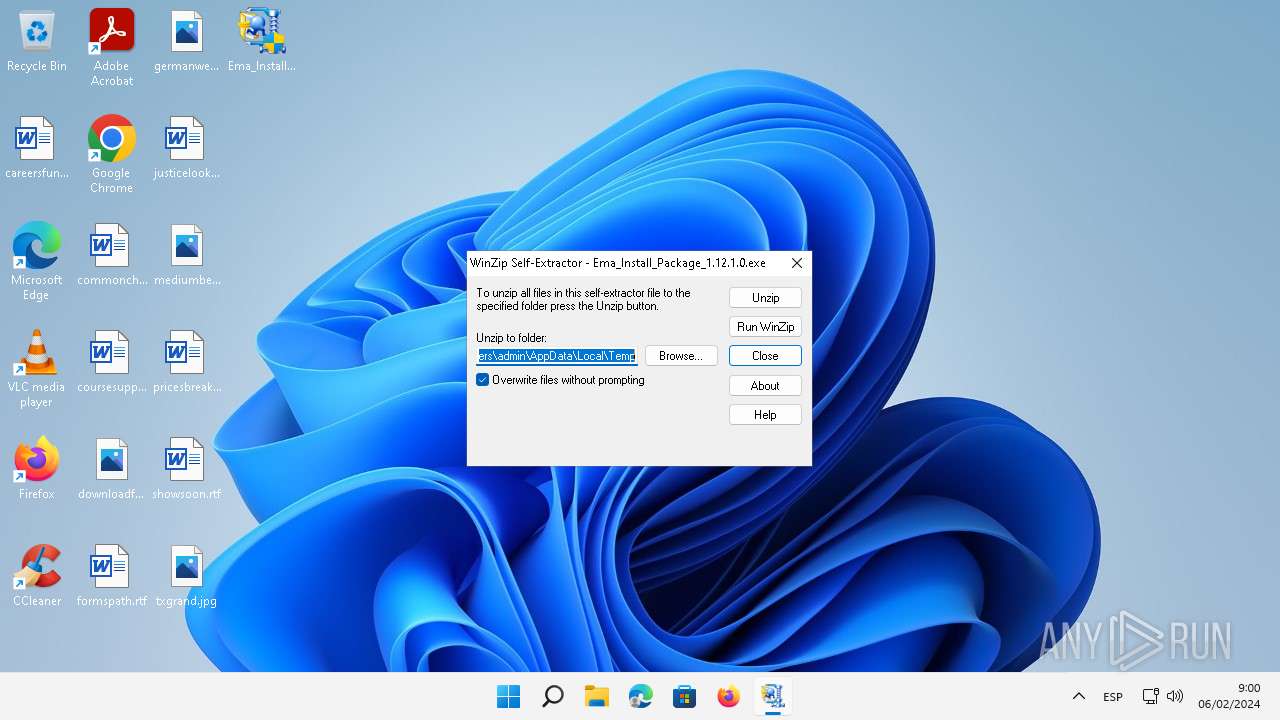
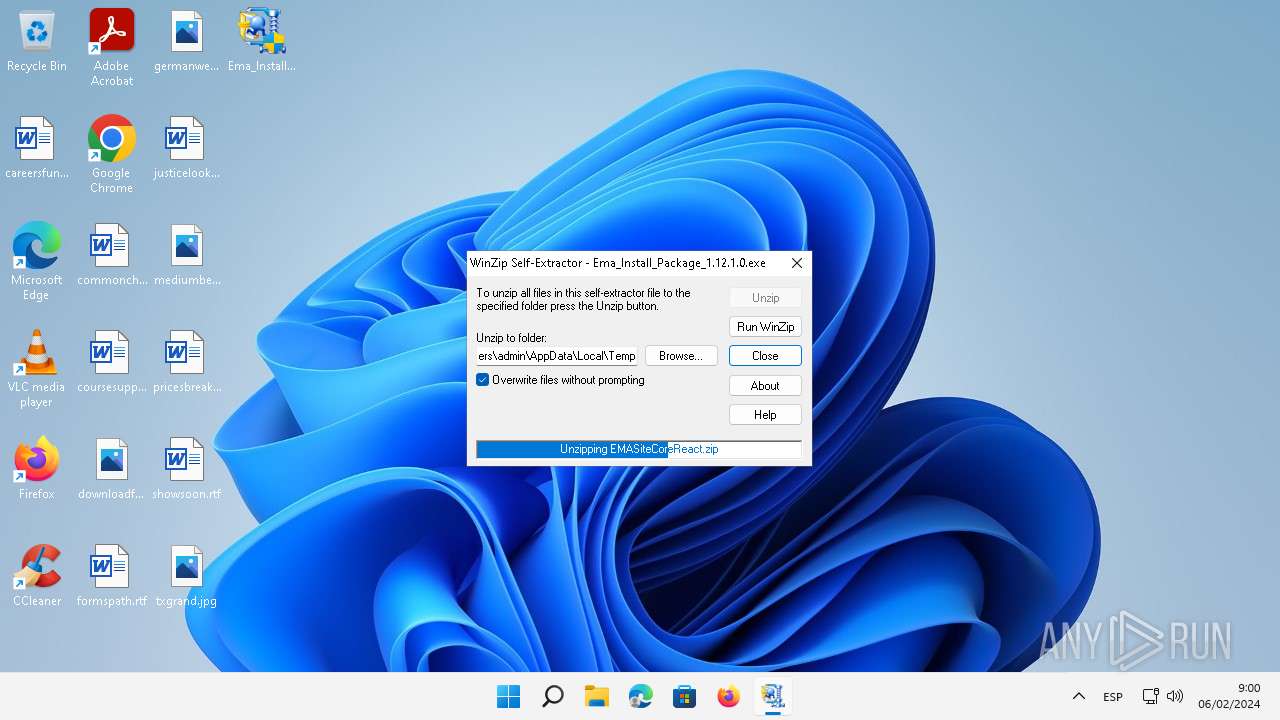
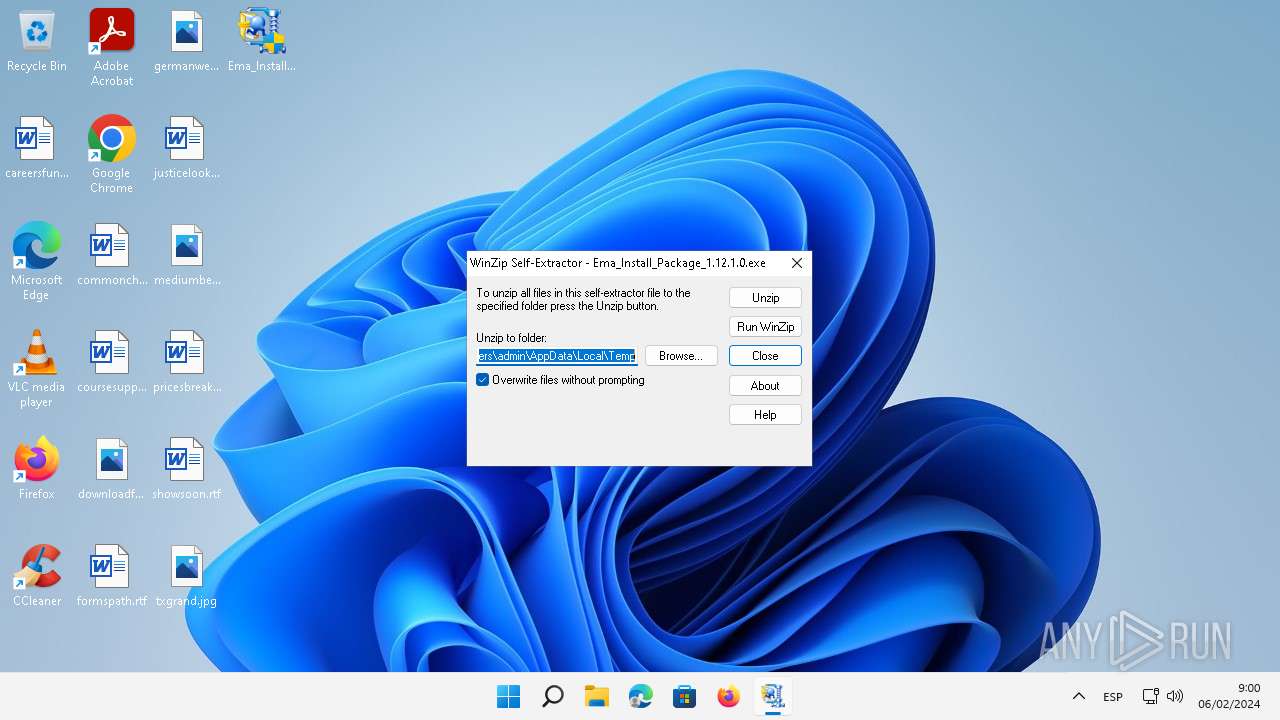
Create files in a temporary directory
- Ema_Install_Package_1.12.1.0.exe (PID: 5340)
- Ema_Install_Package_1.12.1.0.exe (PID: 472)
- Ema_Install_Package_1.12.1.0.exe (PID: 2996)
- rundll32.exe (PID: 5052)
- rundll32.exe (PID: 5152)
- rundll32.exe (PID: 1672)
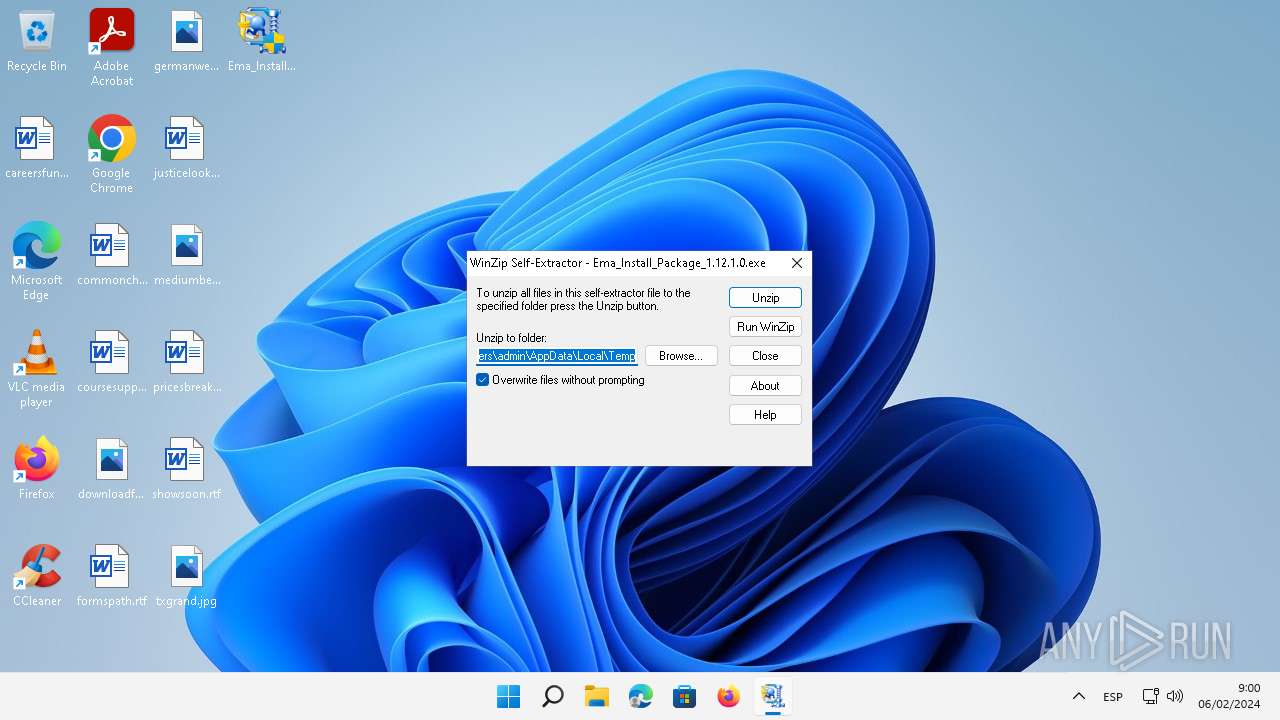
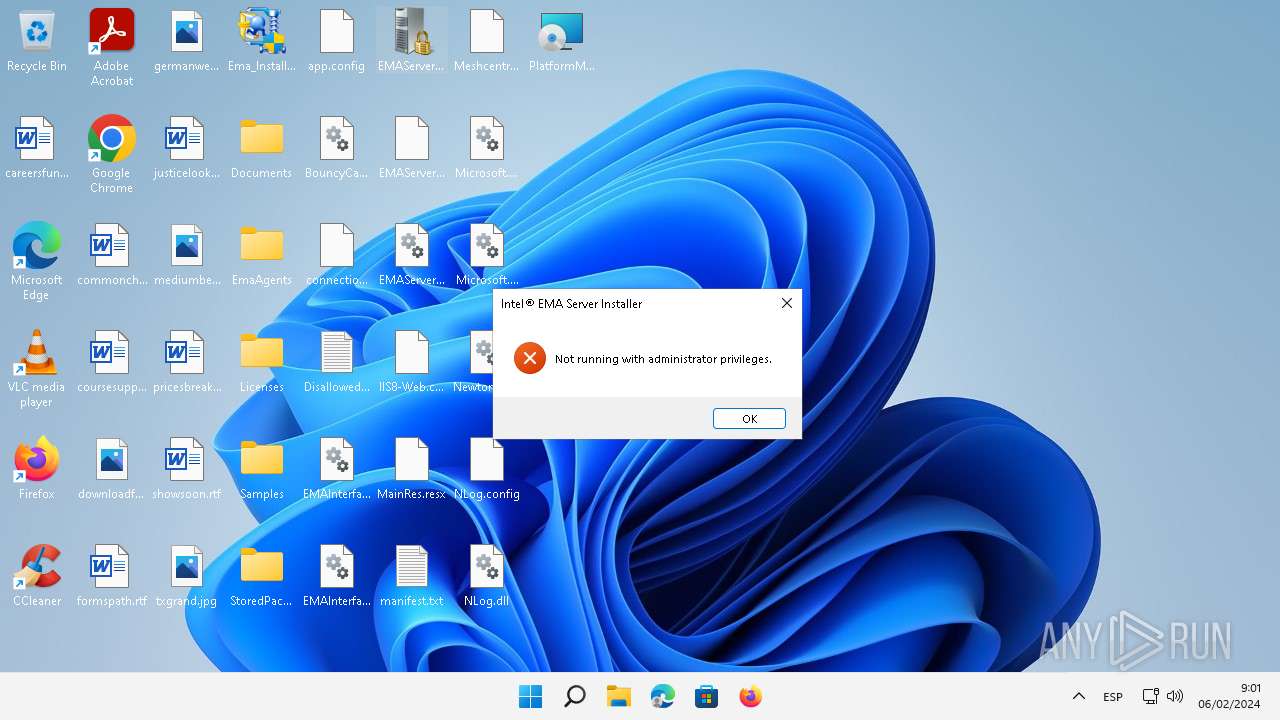
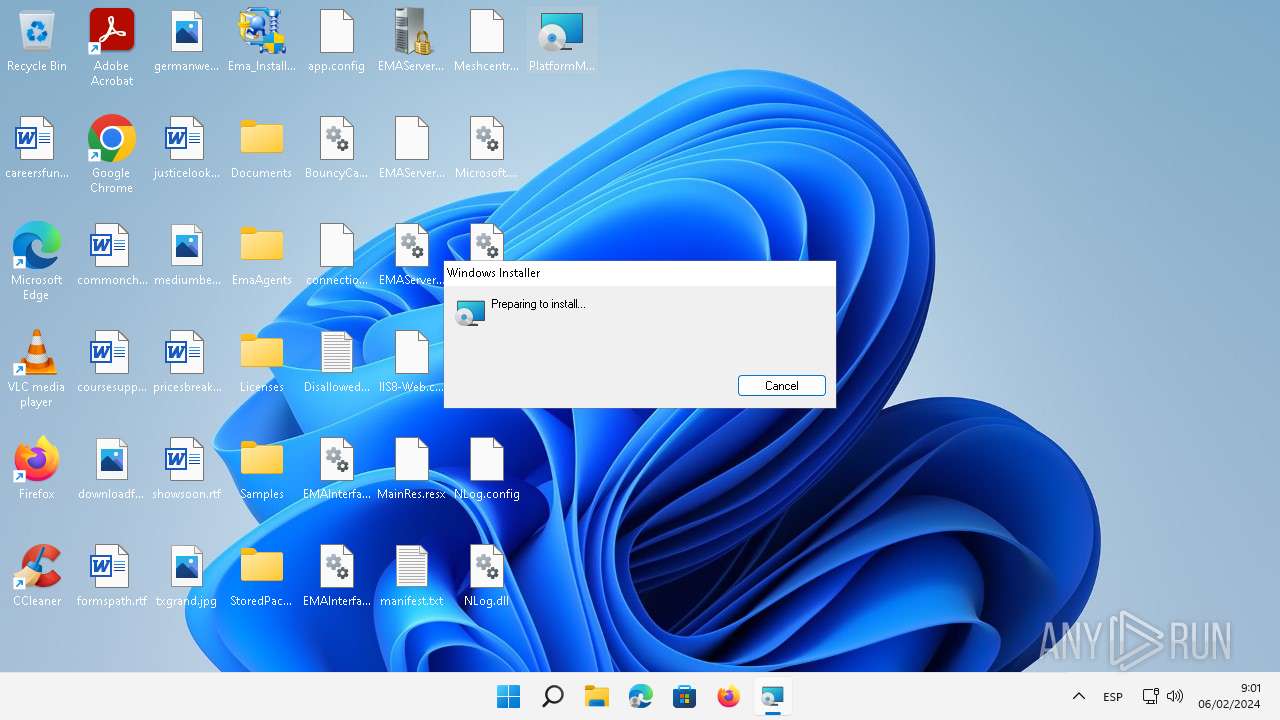
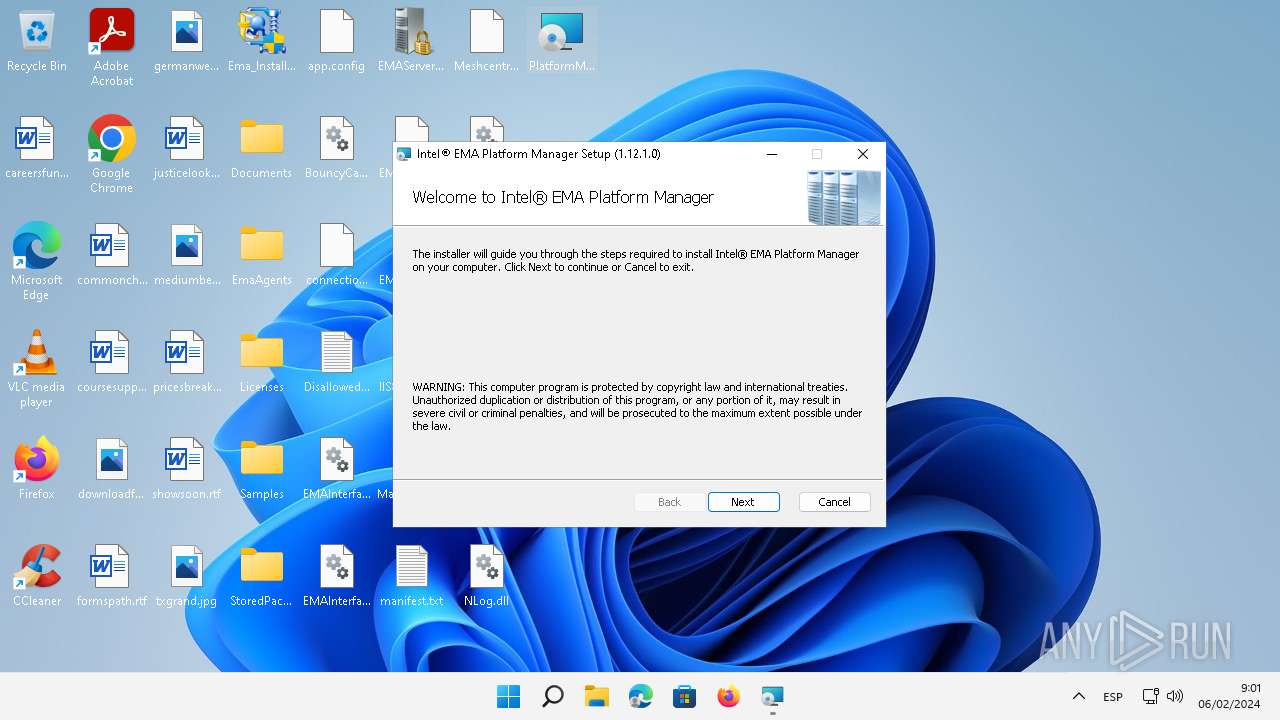
Manual execution by a user
- Ema_Install_Package_1.12.1.0.exe (PID: 1664)
- Ema_Install_Package_1.12.1.0.exe (PID: 2996)
- EMAServerInstaller.exe (PID: 4000)
- msiexec.exe (PID: 5124)
- PlatformManager.exe (PID: 2692)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 5124)
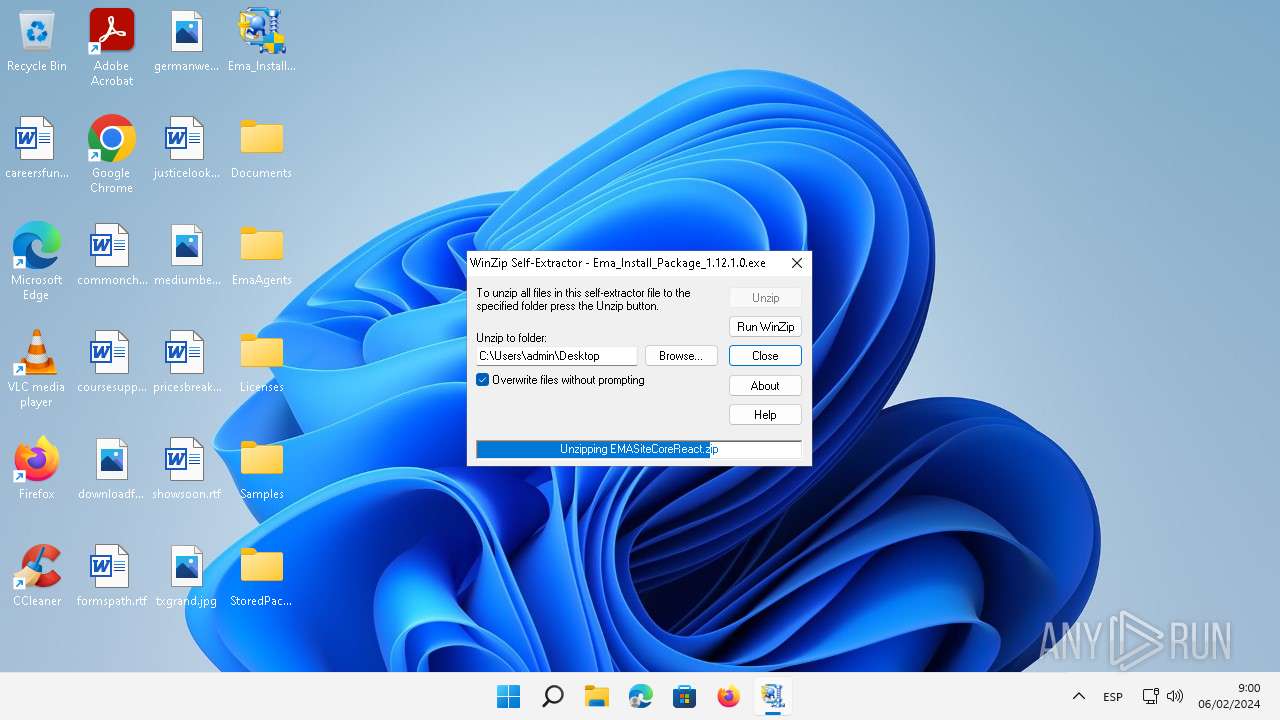
Creates files or folders in the user directory
- EMAServerInstaller.exe (PID: 4000)
- msiexec.exe (PID: 5124)
- rundll32.exe (PID: 5052)
- msiexec.exe (PID: 3924)
- PlatformManager.exe (PID: 2692)
Checks proxy server information
- msiexec.exe (PID: 5124)
Reads Environment values
- EMAServerInstaller.exe (PID: 4000)
- PlatformManagerServer.exe (PID: 1664)
- PlatformManager.exe (PID: 2692)
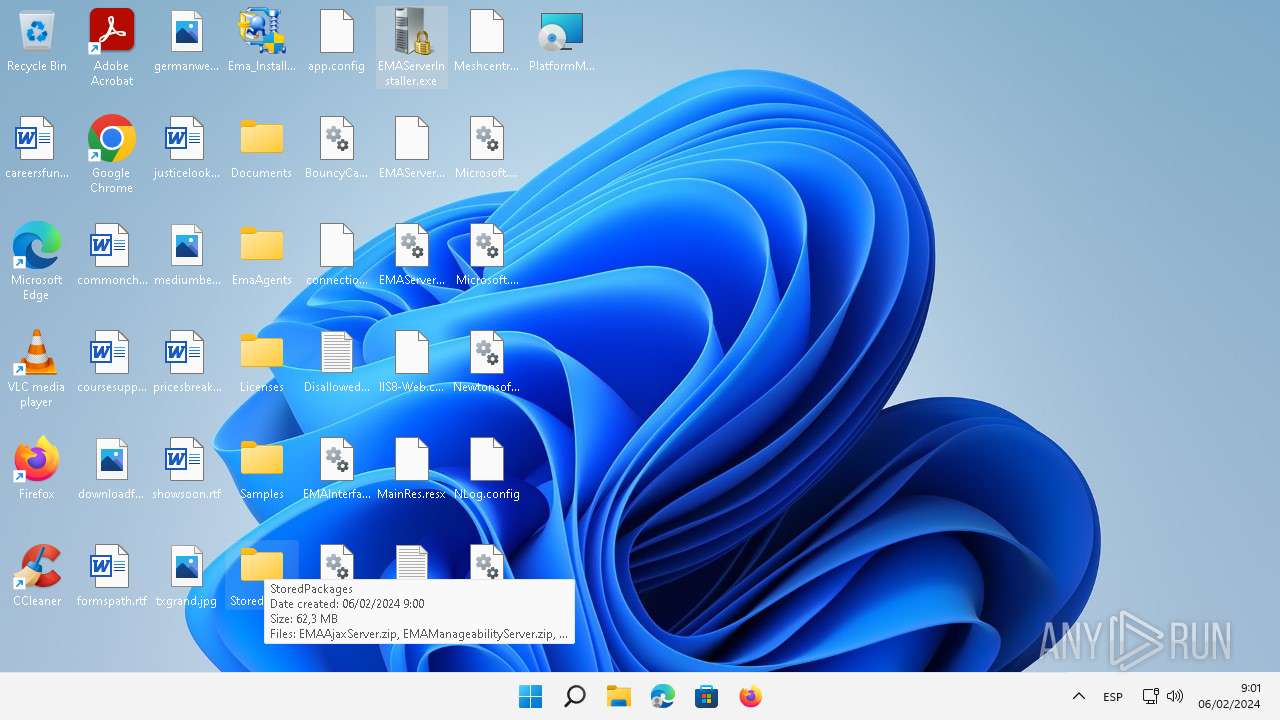
Executable content was dropped or overwritten
- msiexec.exe (PID: 5124)
- msiexec.exe (PID: 3924)
Drops the executable file immediately after the start
- msiexec.exe (PID: 5124)
- rundll32.exe (PID: 5052)
- rundll32.exe (PID: 5152)
- rundll32.exe (PID: 1672)
- rundll32.exe (PID: 4732)
- rundll32.exe (PID: 2028)
Reads the machine GUID from the registry
- EMAServerInstaller.exe (PID: 4000)
- msiexec.exe (PID: 3924)
- PlatformManagerServer.exe (PID: 1664)
- PlatformManager.exe (PID: 2692)
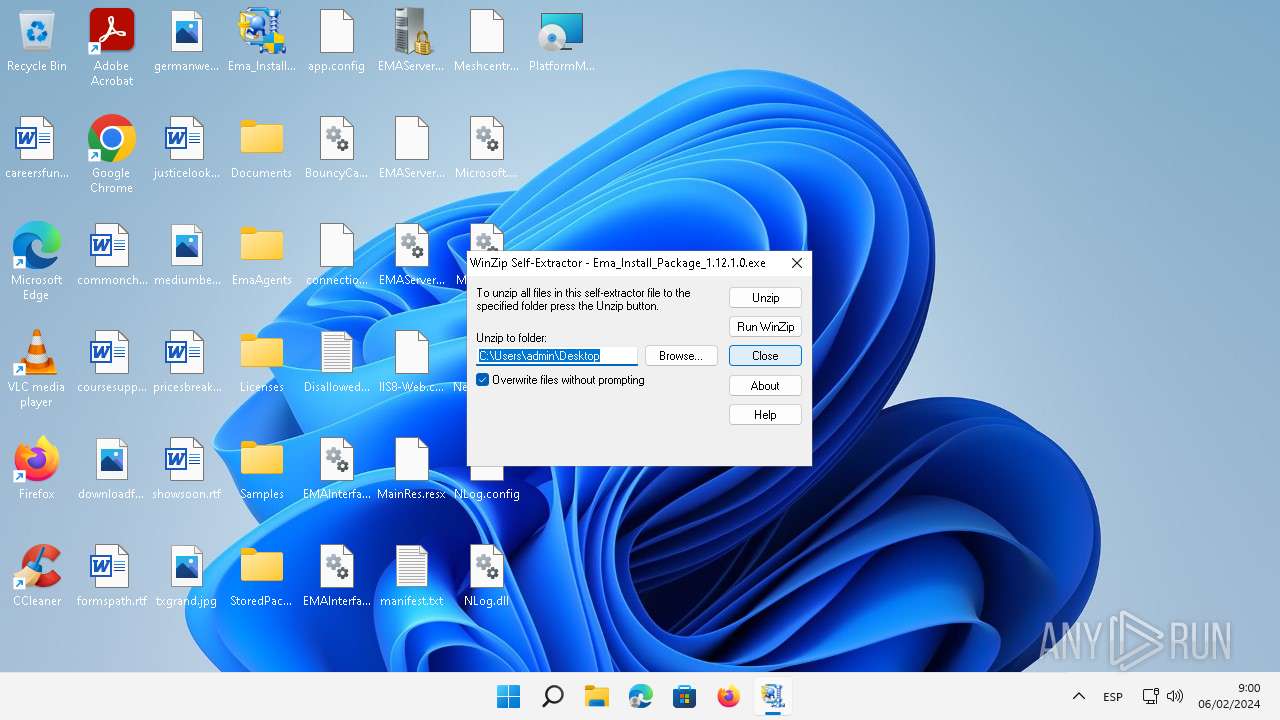
Creates files in the program directory
- rundll32.exe (PID: 2028)
- PlatformManagerServer.exe (PID: 1664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (46.7) |
|---|---|---|
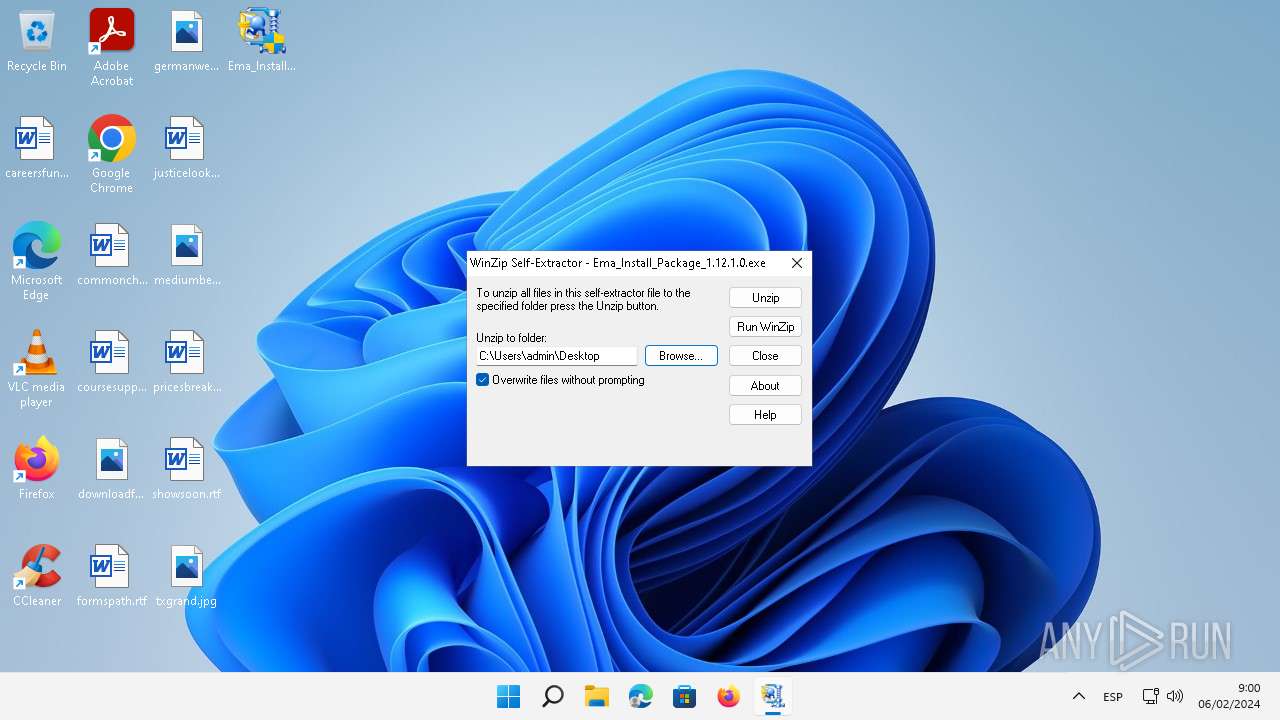
| .exe | | | Winzip Win32 self-extracting archive (generic) (38.8) |
| .exe | | | Win32 Executable (generic) (7.6) |
| .exe | | | Generic Win/DOS Executable (3.3) |
| .exe | | | DOS Executable Generic (3.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:08:05 17:27:28+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 86016 |
| InitializedDataSize: | 65536 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc8e4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
138
Monitored processes
21
Malicious processes
12
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | run=1 shortcut="C:\Users\admin\Desktop\Ema_Install_Package_1.12.1.0.exe" | C:\Users\admin\AppData\Local\Temp\ecb0c\Ema_Install_Package_1.12.1.0.exe | Ema_Install_Package_1.12.1.0.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1112 | C:\Windows\syswow64\MsiExec.exe -Embedding 987226998C2A6526B71DDDF1A2956F07 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.22000.653 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1664 | "C:\Users\admin\Desktop\Ema_Install_Package_1.12.1.0.exe" | C:\Users\admin\Desktop\Ema_Install_Package_1.12.1.0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1664 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | EMAServerInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
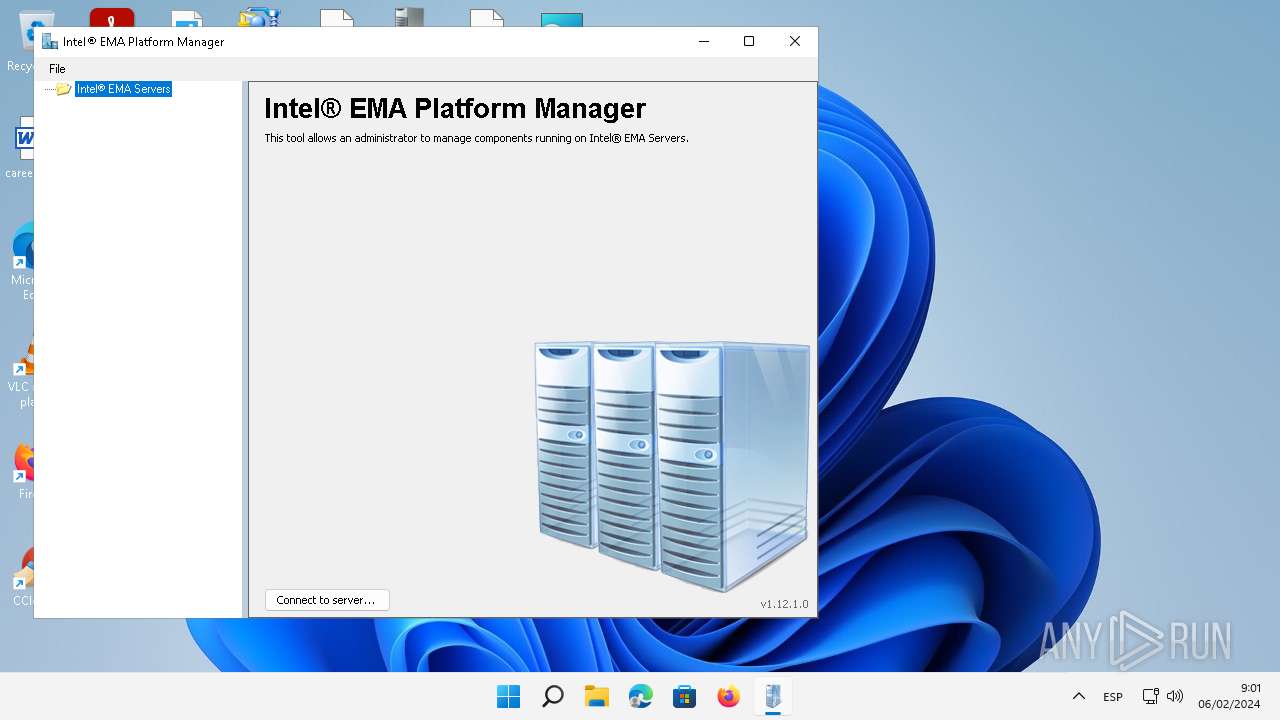
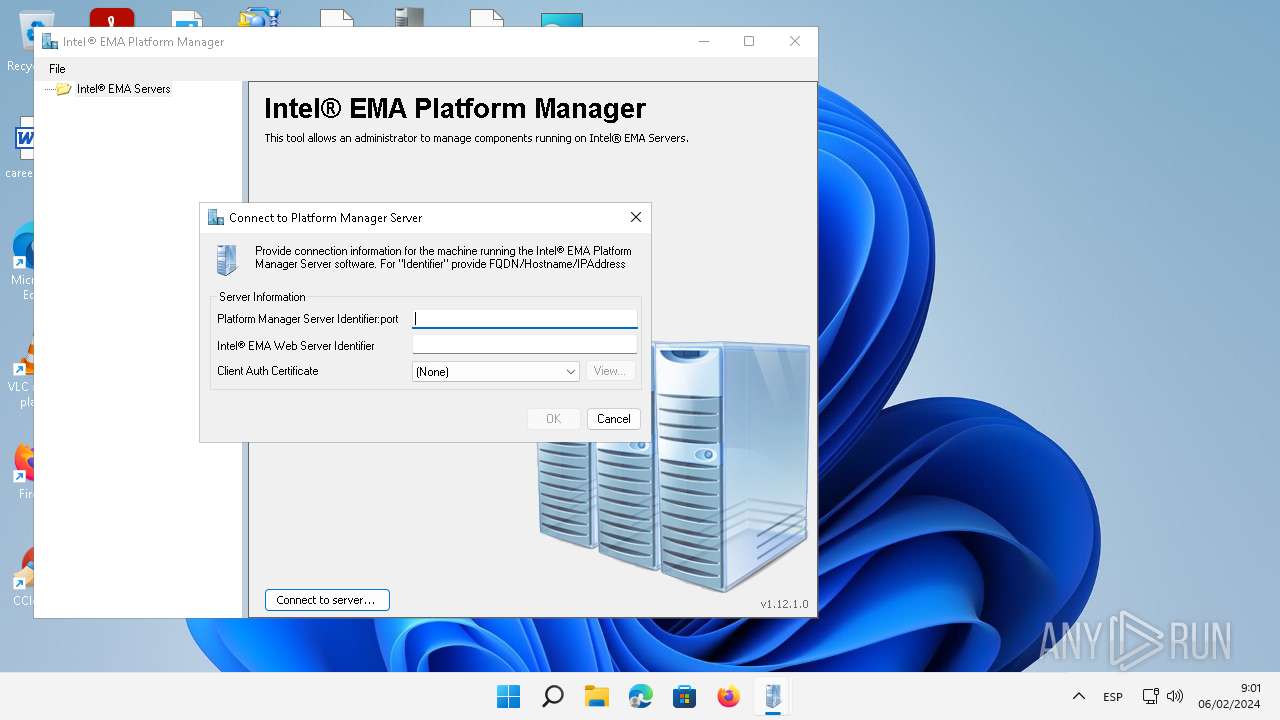
| 1664 | "C:\Program Files (x86)\Intel\Platform Manager\Platform Manager Server\PlatformManagerServer.exe" | C:\Program Files (x86)\Intel\Platform Manager\Platform Manager Server\PlatformManagerServer.exe | services.exe | ||||||||||||
User: SYSTEM Company: Intel(R) Corporation Integrity Level: SYSTEM Description: Intel(R) EMA Platform Manager Server Exit code: 3762504530 Version: 1.12.1.0 Modules
| |||||||||||||||
| 1672 | rundll32.exe "C:\Windows\Installer\MSI3B86.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1063812 6 InstallerCustomActions!CustomActions.CustomAction.CASetPropertyValues | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.22000.653 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2028 | rundll32.exe "C:\Windows\Installer\MSI3E0B.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1064468 23 InstallerCustomActions!CustomActions.CustomAction.CACommit | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.22000.653 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2568 | "C:\Users\admin\Desktop\Ema_Install_Package_1.12.1.0.exe" | C:\Users\admin\Desktop\Ema_Install_Package_1.12.1.0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2692 | "C:\Program Files (x86)\Intel\Platform Manager\PlatformManager.exe" | C:\Program Files (x86)\Intel\Platform Manager\PlatformManager.exe | — | explorer.exe | |||||||||||
User: admin Company: Intel(R) Corporation Integrity Level: MEDIUM Description: Intel(R) EMA Platform Manager Exit code: 0 Version: 1.12.1.0 Modules
| |||||||||||||||
| 2772 | run=1 shortcut="C:\Users\admin\Desktop\Ema_Install_Package_1.12.1.0.exe" | C:\Users\admin\AppData\Local\Temp\f528b\Ema_Install_Package_1.12.1.0.exe | Ema_Install_Package_1.12.1.0.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
12 481
Read events
12 454
Write events
14
Delete events
13
Modification events
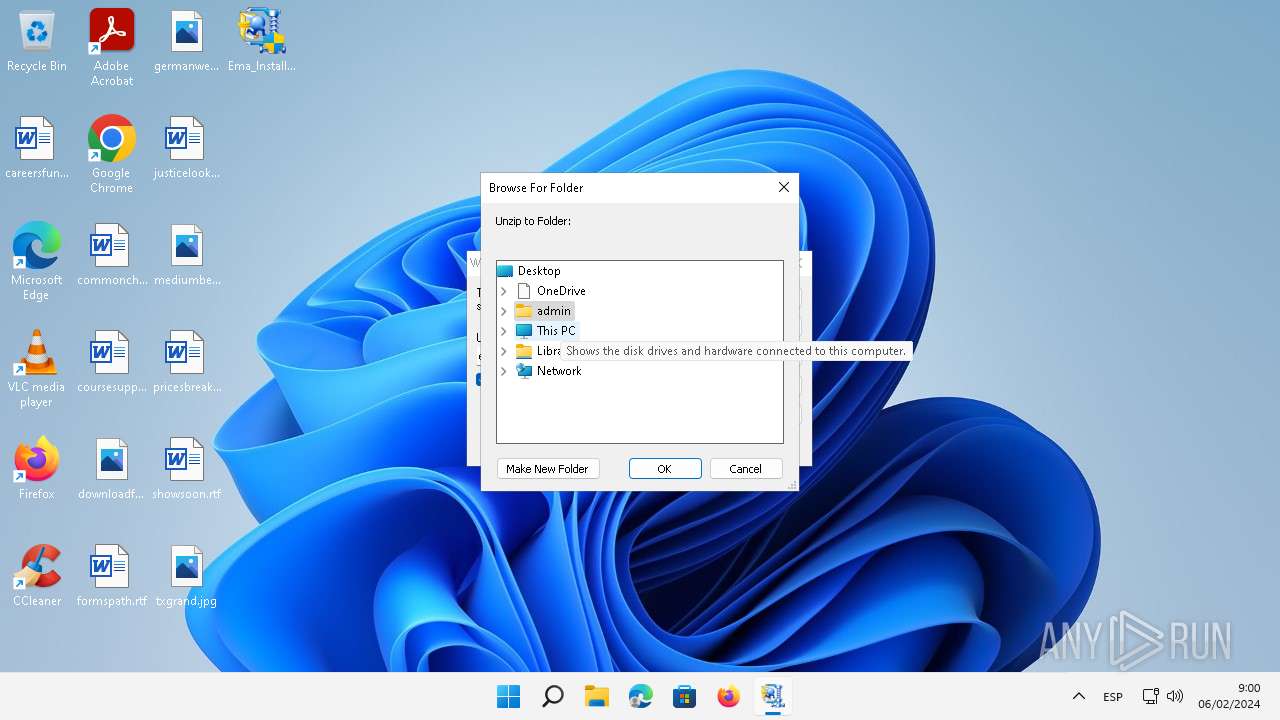
| (PID) Process: | (2772) Ema_Install_Package_1.12.1.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (2772) Ema_Install_Package_1.12.1.0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
| (PID) Process: | (4000) EMAServerInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4000) EMAServerInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4000) EMAServerInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4000) EMAServerInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3924) msiexec.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\48\52C64B7E |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3924) msiexec.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\48 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5124) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 51 | |||
| (PID) Process: | (3924) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | delete value | Name: | C:\Config.Msi\1039a1.rbs |
Value: 31086811 | |||
Executable files
58
Suspicious files
51
Text files
226
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5340 | Ema_Install_Package_1.12.1.0.exe | C:\Users\admin\AppData\Local\Temp\ecb0c\Ema_Install_Package_1.12.1.0.exe | — | |
MD5:— | SHA256:— | |||
| 472 | Ema_Install_Package_1.12.1.0.exe | C:\Users\admin\AppData\Local\Temp\Documents\Intel(R)_EMA_Server_Installation_and_Maintenance_Guide.pdf | — | |
MD5:— | SHA256:— | |||
| 472 | Ema_Install_Package_1.12.1.0.exe | C:\Users\admin\AppData\Local\Temp\Documents\Intel(R)_EMA_Web_Deployment_Guide_for_AWS.pdf | — | |
MD5:— | SHA256:— | |||
| 472 | Ema_Install_Package_1.12.1.0.exe | C:\Users\admin\AppData\Local\Temp\Documents\Intel(R)_EMA_API_Guide.pdf | ||
MD5:58DA02A33FD336DBA1E0ECC609729412 | SHA256:266DC0A7D15A356C914015213BCA1B391FBA29361BD0CAEAD374811BDA7A0282 | |||
| 472 | Ema_Install_Package_1.12.1.0.exe | C:\Users\admin\AppData\Local\Temp\Documents\Intel(R)_EMA_Admin_and_Usage_Guide.pdf | ||
MD5:904AEF6558384FD339D719CABAD07413 | SHA256:27E32960572946B71FDCA647C48B2903F572EFAC32CA819ABE9041CC6A35E171 | |||
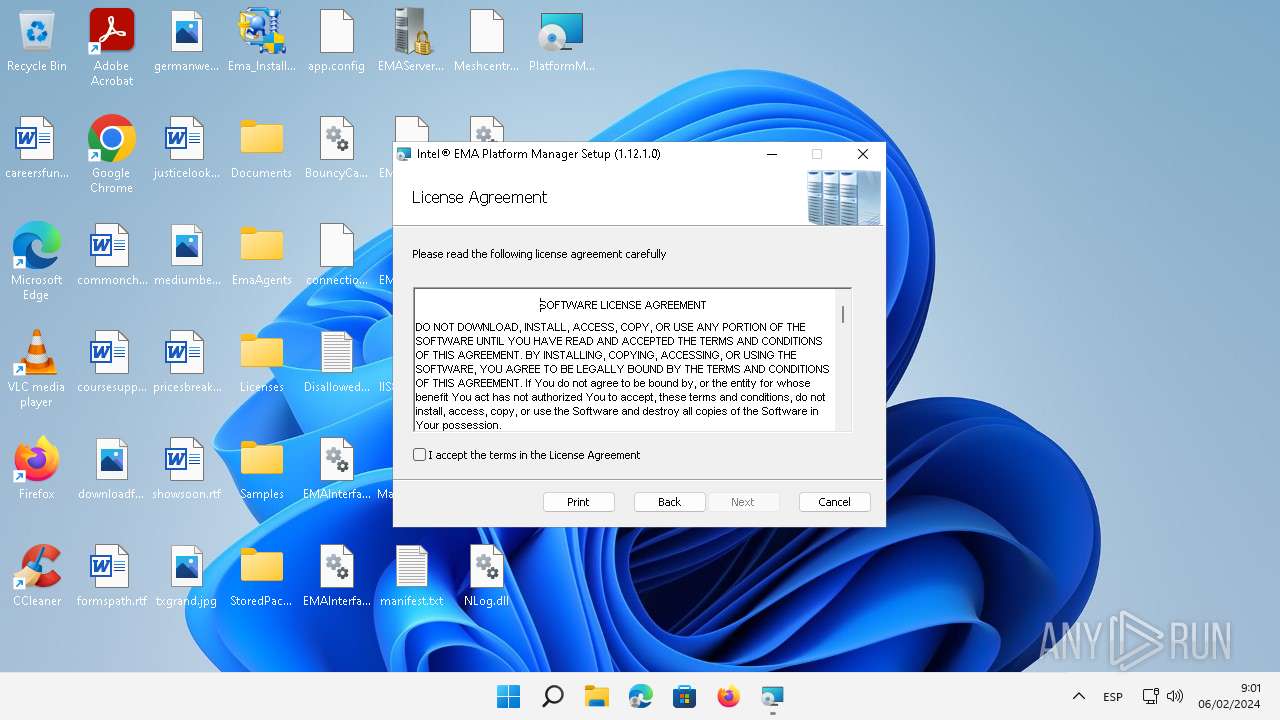
| 472 | Ema_Install_Package_1.12.1.0.exe | C:\Users\admin\AppData\Local\Temp\Licenses\Intel_EMA_Commercial_Use_License.rtf | text | |
MD5:9726D7224B81AD7D4B74F1FA200EA8DE | SHA256:938979763B6B2CCCE9FD74E52BCCB6B43B9CF53728CA6A89E0E147F5B9B88820 | |||
| 472 | Ema_Install_Package_1.12.1.0.exe | C:\Users\admin\AppData\Local\Temp\EmaAgents\EmaAgent-1120.2.bin | executable | |
MD5:05081578D47AB3854F05741C974852C9 | SHA256:EAE2B57E75B4CAC6BEFEFD62A55787758B783456006BD183113D1B15356D773F | |||
| 472 | Ema_Install_Package_1.12.1.0.exe | C:\Users\admin\AppData\Local\Temp\Documents\Intel(R)_EMA_QuickStart_Guide.pdf | ||
MD5:0BD6EF43917006EFD0799A078F23BC43 | SHA256:CBC344D6EA37ADD40994C5AC48CE9E8AF282E30125AF0E9B8AF39AA5F5F536E2 | |||
| 472 | Ema_Install_Package_1.12.1.0.exe | C:\Users\admin\AppData\Local\Temp\Documents\Intel(R)_EMA_Privacy_Notice.pdf | ||
MD5:3B94FBF275AFAB92BA7F5B165BB1A991 | SHA256:75257562102209B5D49012F612EE8BC663E4C23C89BAF0F708E101C3A41DB579 | |||
| 472 | Ema_Install_Package_1.12.1.0.exe | C:\Users\admin\AppData\Local\Temp\Documents\Intel(R)_EMA_Web_Deployment_Guide_for_GCP.pdf | ||
MD5:3D89A5A1EAD66786FC1F7224BB7E0863 | SHA256:4B5CDFA8559A29C685790FE7364CE4D429E883B19762CE9401A0E055E207F2E5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
41
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a67d46ce-b81f-4726-9f44-b52dfc73b956?P1=1707786052&P2=404&P3=2&P4=CTfJRNPZH9%2fmADM0wZaw34RbzMljQfEpxUUqYEZtWYA68tP9G3ZhBQ0nPeYVTiqiYENOijfnNiXi208h9IEe5w%3d%3d | unknown | binary | 180 Kb | unknown |
5944 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a67d46ce-b81f-4726-9f44-b52dfc73b956?P1=1707786052&P2=404&P3=2&P4=CTfJRNPZH9%2fmADM0wZaw34RbzMljQfEpxUUqYEZtWYA68tP9G3ZhBQ0nPeYVTiqiYENOijfnNiXi208h9IEe5w%3d%3d | unknown | binary | 339 Kb | unknown |
5124 | msiexec.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | binary | 1.42 Kb | unknown |
5944 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a67d46ce-b81f-4726-9f44-b52dfc73b956?P1=1707786052&P2=404&P3=2&P4=CTfJRNPZH9%2fmADM0wZaw34RbzMljQfEpxUUqYEZtWYA68tP9G3ZhBQ0nPeYVTiqiYENOijfnNiXi208h9IEe5w%3d%3d | unknown | binary | 1.18 Mb | unknown |
5944 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a67d46ce-b81f-4726-9f44-b52dfc73b956?P1=1707786052&P2=404&P3=2&P4=CTfJRNPZH9%2fmADM0wZaw34RbzMljQfEpxUUqYEZtWYA68tP9G3ZhBQ0nPeYVTiqiYENOijfnNiXi208h9IEe5w%3d%3d | unknown | binary | 68.6 Kb | unknown |
5124 | msiexec.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | binary | 765 b | unknown |
5944 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a67d46ce-b81f-4726-9f44-b52dfc73b956?P1=1707786052&P2=404&P3=2&P4=CTfJRNPZH9%2fmADM0wZaw34RbzMljQfEpxUUqYEZtWYA68tP9G3ZhBQ0nPeYVTiqiYENOijfnNiXi208h9IEe5w%3d%3d | unknown | binary | 518 Kb | unknown |
5124 | msiexec.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEBJGntpPoZRk71h%2B2mUYlhk%3D | unknown | binary | 637 b | unknown |
3752 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3e599422b26cc699 | unknown | compressed | 4.66 Kb | unknown |
1412 | svchost.exe | GET | 200 | 2.21.20.140:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | text | 22 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4588 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
2664 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
1412 | svchost.exe | 2.21.20.155:80 | — | Akamai International B.V. | DE | unknown |
5944 | svchost.exe | 2.18.97.153:443 | — | Akamai International B.V. | FR | unknown |
1412 | svchost.exe | 2.21.20.140:80 | — | Akamai International B.V. | DE | unknown |
3752 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
3752 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3752 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2664 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
5944 | svchost.exe | 152.199.19.161:80 | msedge.b.tlu.dl.delivery.mp.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
msedge.b.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
umwatson.events.data.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| shared |
fp.msedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1412 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |