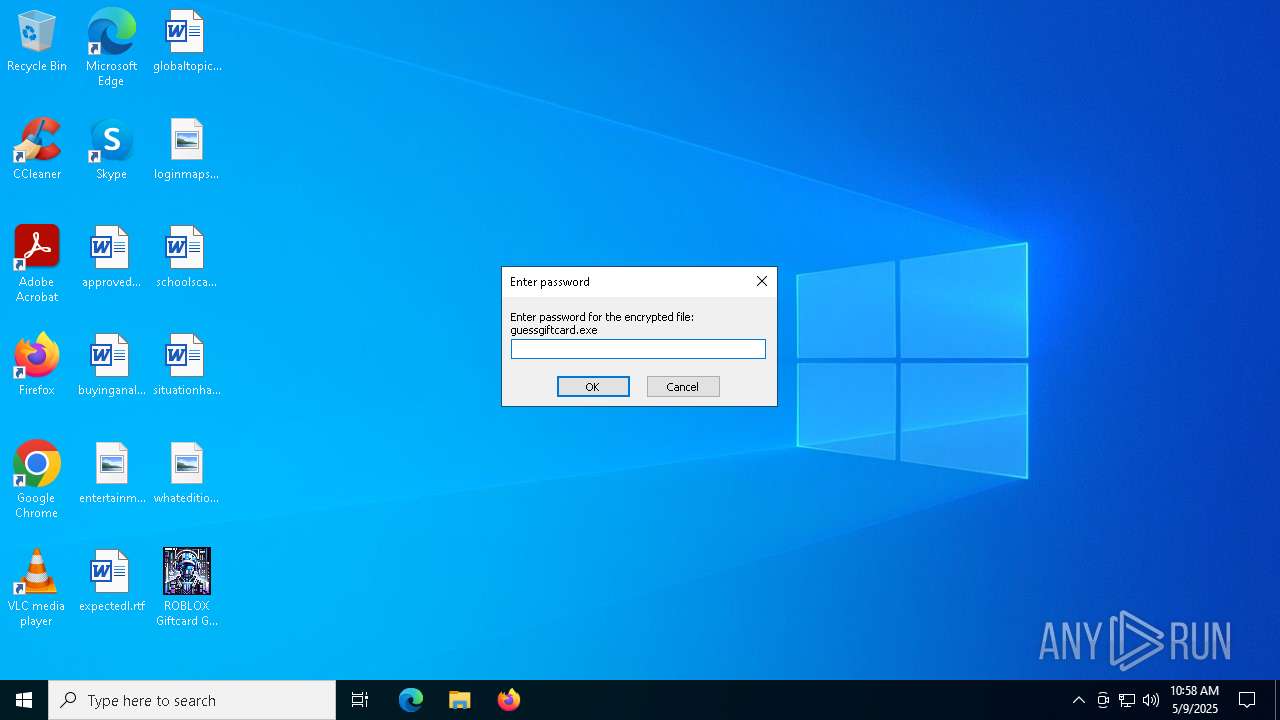
| File name: | ROBLOX Giftcard Guesser.exe |
| Full analysis: | https://app.any.run/tasks/ca9d81c1-4949-4c99-8d8a-491a16df13a3 |
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
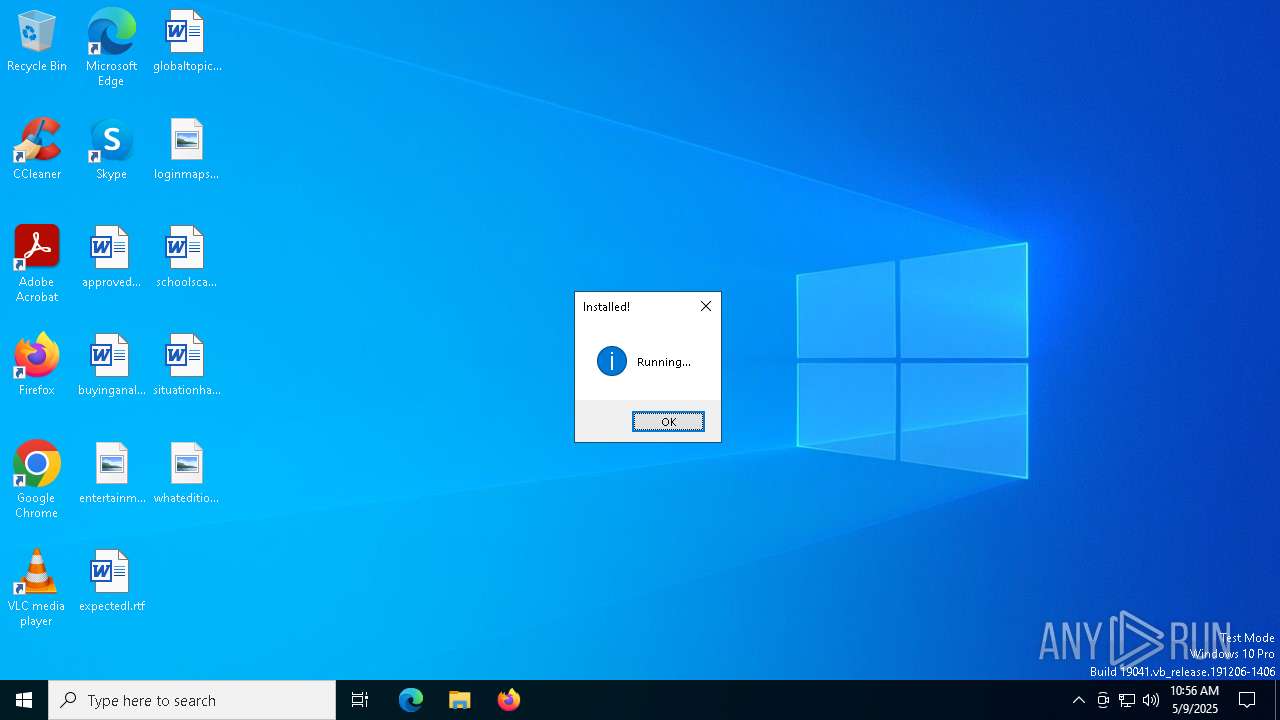
| Analysis date: | May 09, 2025, 10:56:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 5B1878291847545B1DF5D00C913F9C56 |
| SHA1: | 77242BACD5B9EF170BB8E5B2FE8F9949CC559AB0 |
| SHA256: | A3865DF55C5C081FF2C89BC5E08A06A94D9A085341954CFC336261A63F1B3C63 |
| SSDEEP: | 98304:mZtMjYglbfzt+rKmbxGHDqOnmzh4jOhjTgtgKDTq/dt6E5NKbtx6K973qypEel1h:3brVxpx/TcgLeS2dr/Dq6a |
MALICIOUS
Executing a file with an untrusted certificate
- guessgiftcard.exe (PID: 7048)
- guessgiftcard.exe (PID: 6476)
- guessgiftcard.exe (PID: 4464)
- guessgiftcard.exe (PID: 2088)
- guessgiftcard.exe (PID: 2852)
- guessgiftcard.exe (PID: 6800)
- guessgiftcard.exe (PID: 4056)
- guessgiftcard.exe (PID: 4112)
- guessgiftcard.exe (PID: 2796)
- guessgiftcard.exe (PID: 3800)
- guessgiftcard.exe (PID: 5552)
- guessgiftcard.exe (PID: 3156)
BlankGrabber has been detected
- guessgiftcard.exe (PID: 7048)
- guessgiftcard.exe (PID: 4464)
- guessgiftcard.exe (PID: 2852)
- guessgiftcard.exe (PID: 4056)
- guessgiftcard.exe (PID: 2796)
- guessgiftcard.exe (PID: 5552)
Bypass User Account Control (Modify registry)
- reg.exe (PID: 2904)
- reg.exe (PID: 4300)
- reg.exe (PID: 6960)
Bypass User Account Control (ComputerDefaults)
- ComputerDefaults.exe (PID: 2392)
- ComputerDefaults.exe (PID: 2288)
- ComputerDefaults.exe (PID: 4996)
Changes Windows Defender settings
- cmd.exe (PID: 2960)
- cmd.exe (PID: 2904)
- cmd.exe (PID: 5892)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 2104)
- cmd.exe (PID: 3976)
- cmd.exe (PID: 5776)
- cmd.exe (PID: 2504)
- cmd.exe (PID: 4988)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 2104)
- cmd.exe (PID: 4988)
Adds path to the Windows Defender exclusion list
- guessgiftcard.exe (PID: 2088)
- cmd.exe (PID: 2904)
- cmd.exe (PID: 5892)
- guessgiftcard.exe (PID: 4112)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 3976)
- guessgiftcard.exe (PID: 3156)
- cmd.exe (PID: 5776)
- cmd.exe (PID: 2504)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 4896)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 6040)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 4896)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 6040)
Changes Controlled Folder Access settings
- powershell.exe (PID: 4896)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 6040)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 4896)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 6040)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 4896)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 6040)
Changes settings for real-time protection
- powershell.exe (PID: 4896)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 6040)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 4896)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 6040)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 1300)
- MpCmdRun.exe (PID: 5960)
- MpCmdRun.exe (PID: 1348)
SUSPICIOUS
Process drops legitimate windows executable
- ROBLOX Giftcard Guesser.exe (PID: 6068)
- guessgiftcard.exe (PID: 7048)
- guessgiftcard.exe (PID: 4464)
- guessgiftcard.exe (PID: 2852)
- guessgiftcard.exe (PID: 4056)
- guessgiftcard.exe (PID: 2796)
- guessgiftcard.exe (PID: 5552)
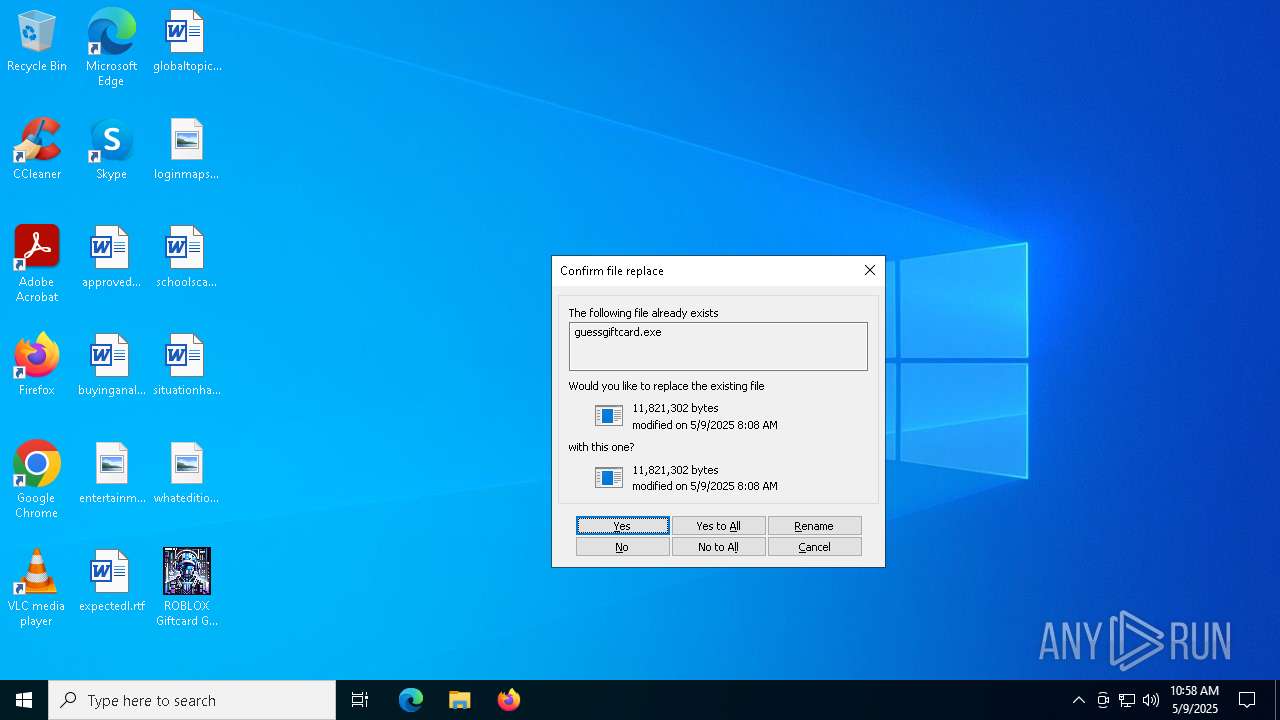
Executable content was dropped or overwritten
- ROBLOX Giftcard Guesser.exe (PID: 6068)
- guessgiftcard.exe (PID: 7048)
- guessgiftcard.exe (PID: 4464)
- guessgiftcard.exe (PID: 2088)
- guessgiftcard.exe (PID: 2852)
- guessgiftcard.exe (PID: 4056)
- guessgiftcard.exe (PID: 4112)
- guessgiftcard.exe (PID: 2796)
- guessgiftcard.exe (PID: 5552)
- guessgiftcard.exe (PID: 3156)
Reads security settings of Internet Explorer
- ROBLOX Giftcard Guesser.exe (PID: 6068)
- ROBLOX Giftcard Guesser.exe (PID: 728)
Reads the date of Windows installation
- ROBLOX Giftcard Guesser.exe (PID: 6068)
- ROBLOX Giftcard Guesser.exe (PID: 728)
Starts a Microsoft application from unusual location
- guessgiftcard.exe (PID: 7048)
- guessgiftcard.exe (PID: 6476)
- guessgiftcard.exe (PID: 4464)
- guessgiftcard.exe (PID: 2088)
- guessgiftcard.exe (PID: 2852)
- guessgiftcard.exe (PID: 6800)
- guessgiftcard.exe (PID: 4056)
- guessgiftcard.exe (PID: 4112)
- guessgiftcard.exe (PID: 2796)
- guessgiftcard.exe (PID: 3800)
- guessgiftcard.exe (PID: 5552)
- guessgiftcard.exe (PID: 3156)
Starts CMD.EXE for commands execution
- guessgiftcard.exe (PID: 6476)
- guessgiftcard.exe (PID: 2088)
- guessgiftcard.exe (PID: 6800)
- guessgiftcard.exe (PID: 4112)
- guessgiftcard.exe (PID: 3800)
- guessgiftcard.exe (PID: 3156)
Application launched itself
- guessgiftcard.exe (PID: 7048)
- guessgiftcard.exe (PID: 4464)
- guessgiftcard.exe (PID: 2852)
- guessgiftcard.exe (PID: 4056)
- guessgiftcard.exe (PID: 2796)
- guessgiftcard.exe (PID: 5552)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 672)
- cmd.exe (PID: 5256)
- cmd.exe (PID: 6872)
- cmd.exe (PID: 1088)
- cmd.exe (PID: 4108)
- cmd.exe (PID: 5036)
- cmd.exe (PID: 3032)
- cmd.exe (PID: 1388)
- cmd.exe (PID: 4868)
The process drops C-runtime libraries
- guessgiftcard.exe (PID: 7048)
- guessgiftcard.exe (PID: 4464)
- guessgiftcard.exe (PID: 2852)
- guessgiftcard.exe (PID: 4056)
- guessgiftcard.exe (PID: 2796)
- guessgiftcard.exe (PID: 5552)
Process drops python dynamic module
- guessgiftcard.exe (PID: 7048)
- guessgiftcard.exe (PID: 4464)
- guessgiftcard.exe (PID: 2852)
- guessgiftcard.exe (PID: 4056)
- guessgiftcard.exe (PID: 2796)
- guessgiftcard.exe (PID: 5552)
Changes default file association
- reg.exe (PID: 2904)
- reg.exe (PID: 4300)
- reg.exe (PID: 6960)
Found strings related to reading or modifying Windows Defender settings
- guessgiftcard.exe (PID: 6476)
- guessgiftcard.exe (PID: 2088)
- guessgiftcard.exe (PID: 6800)
- guessgiftcard.exe (PID: 4112)
- guessgiftcard.exe (PID: 3800)
- guessgiftcard.exe (PID: 3156)
Uses WEVTUTIL.EXE to query events from a log or log file
- cmd.exe (PID: 6964)
- cmd.exe (PID: 5228)
- cmd.exe (PID: 6372)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 5772)
There is functionality for taking screenshot (YARA)
- ROBLOX Giftcard Guesser.exe (PID: 6068)
- ROBLOX Giftcard Guesser.exe (PID: 728)
Get information on the list of running processes
- guessgiftcard.exe (PID: 2088)
- cmd.exe (PID: 5112)
- guessgiftcard.exe (PID: 4112)
- cmd.exe (PID: 776)
- guessgiftcard.exe (PID: 3156)
- cmd.exe (PID: 632)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2960)
- cmd.exe (PID: 2904)
- cmd.exe (PID: 5892)
- cmd.exe (PID: 2104)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 3976)
- cmd.exe (PID: 5776)
- cmd.exe (PID: 4988)
- cmd.exe (PID: 2504)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 2904)
- cmd.exe (PID: 5892)
- cmd.exe (PID: 3976)
- cmd.exe (PID: 6980)
- cmd.exe (PID: 5776)
- cmd.exe (PID: 2504)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 2960)
- cmd.exe (PID: 2104)
- cmd.exe (PID: 4988)
Script disables Windows Defender's IPS
- cmd.exe (PID: 2960)
- cmd.exe (PID: 2104)
- cmd.exe (PID: 4988)
Checks for external IP
- svchost.exe (PID: 2196)
- guessgiftcard.exe (PID: 2088)
- guessgiftcard.exe (PID: 4112)
- guessgiftcard.exe (PID: 3156)
The executable file from the user directory is run by the CMD process
- bound.exe (PID: 5244)
- bound.exe (PID: 5984)
- bound.exe (PID: 4740)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 2240)
- cmd.exe (PID: 7036)
- cmd.exe (PID: 856)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 2152)
- WMIC.exe (PID: 4844)
INFO
Reads the computer name
- ROBLOX Giftcard Guesser.exe (PID: 6068)
- guessgiftcard.exe (PID: 7048)
- guessgiftcard.exe (PID: 4464)
- guessgiftcard.exe (PID: 2088)
- bound.exe (PID: 5244)
- MpCmdRun.exe (PID: 1300)
- ROBLOX Giftcard Guesser.exe (PID: 728)
- guessgiftcard.exe (PID: 2852)
- guessgiftcard.exe (PID: 4056)
- guessgiftcard.exe (PID: 4112)
- MpCmdRun.exe (PID: 5960)
- bound.exe (PID: 5984)
- guessgiftcard.exe (PID: 2796)
- guessgiftcard.exe (PID: 5552)
Checks supported languages
- ROBLOX Giftcard Guesser.exe (PID: 6068)
- guessgiftcard.exe (PID: 7048)
- guessgiftcard.exe (PID: 6476)
- guessgiftcard.exe (PID: 4464)
- guessgiftcard.exe (PID: 2088)
- bound.exe (PID: 5244)
- MpCmdRun.exe (PID: 1300)
- ROBLOX Giftcard Guesser.exe (PID: 728)
- guessgiftcard.exe (PID: 2852)
- guessgiftcard.exe (PID: 6800)
- guessgiftcard.exe (PID: 4056)
- guessgiftcard.exe (PID: 4112)
- MpCmdRun.exe (PID: 5960)
- bound.exe (PID: 5984)
- guessgiftcard.exe (PID: 2796)
- guessgiftcard.exe (PID: 3800)
- guessgiftcard.exe (PID: 5552)
- guessgiftcard.exe (PID: 3156)
Process checks computer location settings
- ROBLOX Giftcard Guesser.exe (PID: 6068)
- ROBLOX Giftcard Guesser.exe (PID: 728)
The sample compiled with english language support
- ROBLOX Giftcard Guesser.exe (PID: 6068)
- guessgiftcard.exe (PID: 7048)
- guessgiftcard.exe (PID: 4464)
- guessgiftcard.exe (PID: 2852)
- guessgiftcard.exe (PID: 4056)
- guessgiftcard.exe (PID: 2796)
- guessgiftcard.exe (PID: 5552)
Create files in a temporary directory
- ROBLOX Giftcard Guesser.exe (PID: 6068)
- guessgiftcard.exe (PID: 6476)
- guessgiftcard.exe (PID: 7048)
- guessgiftcard.exe (PID: 4464)
- guessgiftcard.exe (PID: 2088)
- MpCmdRun.exe (PID: 1300)
- ROBLOX Giftcard Guesser.exe (PID: 728)
- guessgiftcard.exe (PID: 2852)
- guessgiftcard.exe (PID: 6800)
- guessgiftcard.exe (PID: 4056)
- guessgiftcard.exe (PID: 4112)
- guessgiftcard.exe (PID: 2796)
- guessgiftcard.exe (PID: 3800)
- guessgiftcard.exe (PID: 5552)
- guessgiftcard.exe (PID: 3156)
Reads security settings of Internet Explorer
- ComputerDefaults.exe (PID: 2392)
- WMIC.exe (PID: 2152)
- ComputerDefaults.exe (PID: 2288)
- WMIC.exe (PID: 4844)
- ComputerDefaults.exe (PID: 4996)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5548)
- powershell.exe (PID: 4692)
- powershell.exe (PID: 4896)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 664)
- powershell.exe (PID: 1764)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5548)
- powershell.exe (PID: 4692)
- powershell.exe (PID: 4896)
- powershell.exe (PID: 664)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 1764)
Reads the software policy settings
- slui.exe (PID: 6264)
- slui.exe (PID: 7152)
Manual execution by a user
- ROBLOX Giftcard Guesser.exe (PID: 728)
- guessgiftcard.exe (PID: 2796)
Checks proxy server information
- slui.exe (PID: 7152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:02:12 14:02:25+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 307200 |
| InitializedDataSize: | 303104 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x32680 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
271
Monitored processes
138
Malicious processes
33
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | wevtutil qe "Microsoft-Windows-Windows Defender/Operational" /f:text | C:\Windows\System32\wevtutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Eventing Command Line Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | tasklist /FO LIST | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | C:\WINDOWS\system32\cmd.exe /c "tasklist /FO LIST" | C:\Windows\System32\cmd.exe | — | guessgiftcard.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | powershell -Command Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Temp\guessgiftcard.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | C:\WINDOWS\system32\cmd.exe /c "reg add hkcu\Software\Classes\ms-settings\shell\open\command /d "C:\Users\admin\AppData\Local\Temp\guessgiftcard.exe" /f" | C:\Windows\System32\cmd.exe | — | guessgiftcard.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\Users\admin\Desktop\ROBLOX Giftcard Guesser.exe" | C:\Users\admin\Desktop\ROBLOX Giftcard Guesser.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
55 116
Read events
55 089
Write events
15
Delete events
12
Modification events
| (PID) Process: | (2904) reg.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\shell\open\command |
| Operation: | write | Name: | DelegateExecute |
Value: | |||
| (PID) Process: | (2392) ComputerDefaults.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (2392) ComputerDefaults.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2392) ComputerDefaults.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2392) ComputerDefaults.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1452) reg.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\shell\open\command |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1452) reg.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\shell\open |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1452) reg.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\shell |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1452) reg.exe | Key: | HKEY_CLASSES_ROOT\ms-settings |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4300) reg.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\shell\open\command |
| Operation: | write | Name: | DelegateExecute |
Value: | |||
Executable files
388
Suspicious files
20
Text files
102
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7048 | guessgiftcard.exe | C:\Users\admin\AppData\Local\Temp\_MEI70482\VCRUNTIME140_1.dll | executable | |
MD5:C0C0B4C611561F94798B62EB43097722 | SHA256:497A280550443E3E9F89E428E51CB795139CA8944D5DEDD54A7083C00E7164E5 | |||
| 6068 | ROBLOX Giftcard Guesser.exe | C:\Users\admin\AppData\Local\Temp\guessgiftcard.exe | executable | |
MD5:829538485353F1A7FC93193B2294B240 | SHA256:B02A2AD50BAF8C2D6D740B6221D10C47055BA298484CAB495346F18C5D89F3D5 | |||
| 7048 | guessgiftcard.exe | C:\Users\admin\AppData\Local\Temp\_MEI70482\_asyncio.pyd | executable | |
MD5:EBAA926303F81E8DB85D6523208B336E | SHA256:9F51191EBAFA85CA5AB3C9B78A85D814F39CCA12EF7A5A3CF09DE256E38C10B9 | |||
| 7048 | guessgiftcard.exe | C:\Users\admin\AppData\Local\Temp\_MEI70482\_ssl.pyd | executable | |
MD5:0940325D7409D9D7D06DEF700EA2B96E | SHA256:8E4490CB83A98BFE287FA188647EFB65040EC9B6B85C3E164A2F2B19ABD14560 | |||
| 7048 | guessgiftcard.exe | C:\Users\admin\AppData\Local\Temp\_MEI70482\_ctypes.pyd | executable | |
MD5:8AB8AF95F0000BFD777D2E9832414D71 | SHA256:75CE9F065CE713218DFF44E990081FE307B571BDB944B47D4CA622CD9821F548 | |||
| 7048 | guessgiftcard.exe | C:\Users\admin\AppData\Local\Temp\_MEI70482\_bz2.pyd | executable | |
MD5:D445B66C80C38F484DFD22C5BC99BFD6 | SHA256:8DC70347CE9DA41B43FDA9442B74CFCAEBD3B3BBF5C679FA776787D10676926F | |||
| 7048 | guessgiftcard.exe | C:\Users\admin\AppData\Local\Temp\_MEI70482\_decimal.pyd | executable | |
MD5:423D3C24A162C2F70E9862A446C5969A | SHA256:EB0CB61D3275ECE3FDEE62726C546C13B43C6AE450295DD1A2E1245DCB068958 | |||
| 7048 | guessgiftcard.exe | C:\Users\admin\AppData\Local\Temp\_MEI70482\_wmi.pyd | executable | |
MD5:CC959A1C6686822F47460826FCB6B3F1 | SHA256:5F9ACF702C1267D41DAB38863D4D28BDD1A49BEB1D2DC64E23ED0BC5141FF9D1 | |||
| 7048 | guessgiftcard.exe | C:\Users\admin\AppData\Local\Temp\_MEI70482\_sqlite3.pyd | executable | |
MD5:0EA6BB0D33C7BA53EA512292F03DC40D | SHA256:5F7733F7AB2473C9C34FCAAEC60F1329FC1B4A3EF24E338D076A8CD000E99B58 | |||
| 7048 | guessgiftcard.exe | C:\Users\admin\AppData\Local\Temp\_MEI70482\_overlapped.pyd | executable | |
MD5:C3D95DEDDAD7D4E6C891AB3DF5C0159A | SHA256:7103AEE3D458E6DA49366A6EC506B5174EF6FA13AB9107F078E873121D6C0232 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
23
DNS requests
21
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2088 | guessgiftcard.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
6080 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6080 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3156 | guessgiftcard.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
4112 | guessgiftcard.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.164.17:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.31.1:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2088 | guessgiftcard.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
6080 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
blank-syr60.in |
| unknown |
ip-api.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2088 | guessgiftcard.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
4112 | guessgiftcard.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
3156 | guessgiftcard.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |